Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
53results about How to "Meet efficiency" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
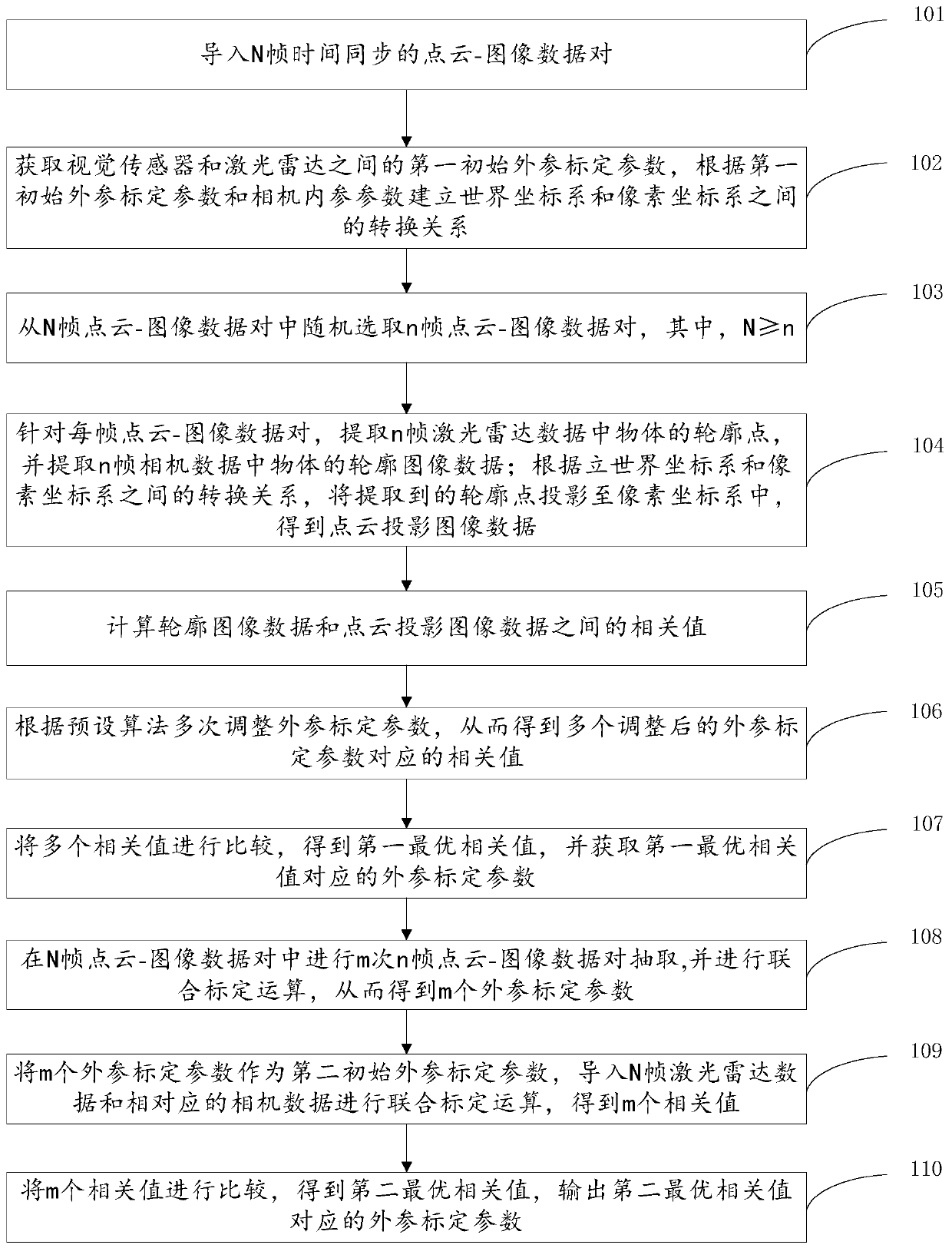
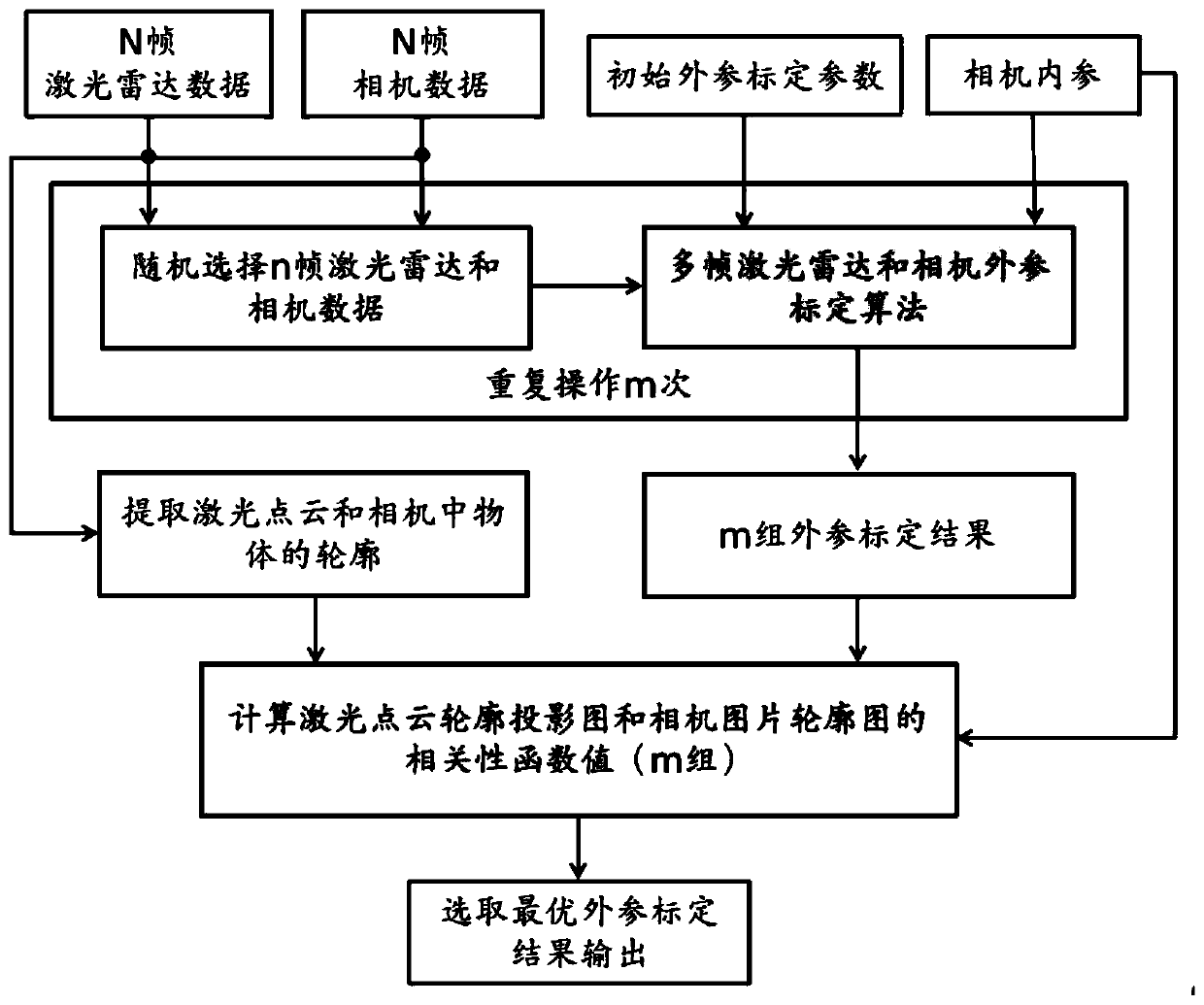
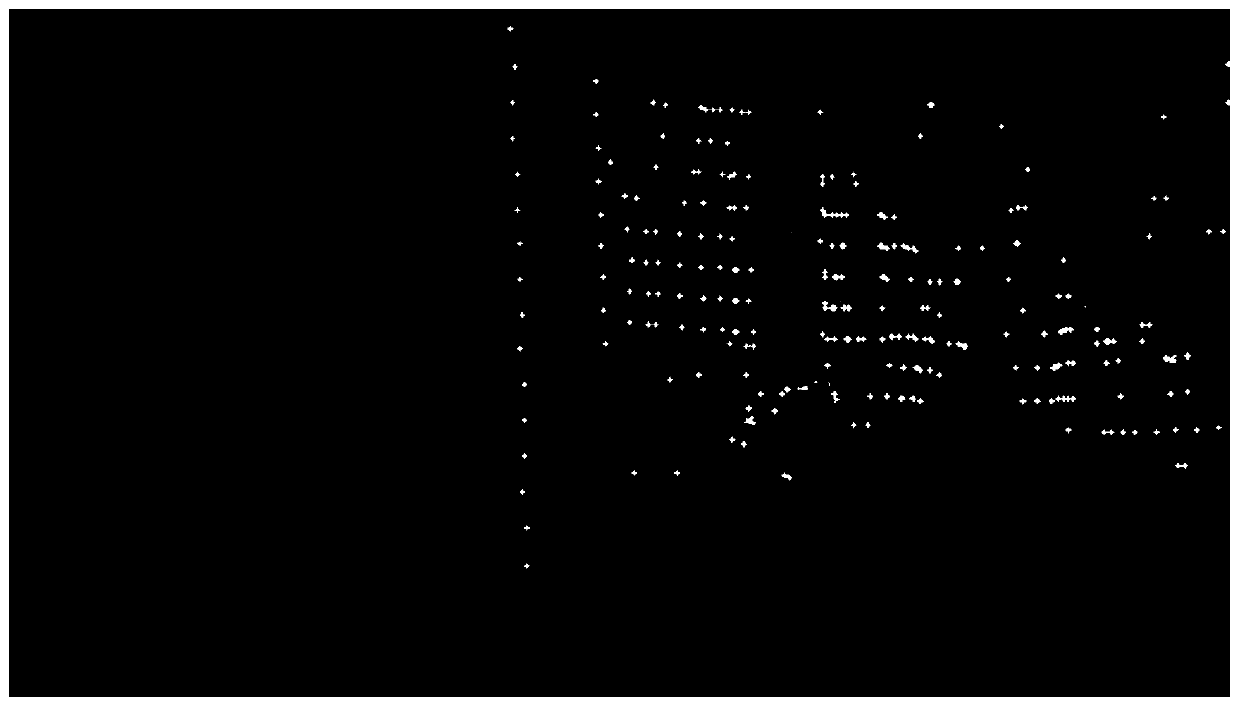
A calibration method for laser radar and camera data
PendingCN109949371AHigh precisionImprove consistencyWave based measurement systemsImage analysisRadarData acquisition
The embodiment of the invention relates to a calibration method for data of a laser radar and a camera, which comprises three parts, namely automatic data acquisition of the laser radar and the camera, external parameter calibration of the laser radar and the camera and external parameter calibration result evaluation, and the method is simple in process, easy to operate and high in efficiency; for external parameter calibration of a low-wire-harness laser radar and a camera, relatively high external parameter calibration precision is achieved; external parameter calibration results are good in consistency, and the requirements of automatic driving vehicle calibration task process, high efficiency, good consistency, high precision and the like can be met.
Owner:BEIJING ZHIXINGZHE TECH CO LTD
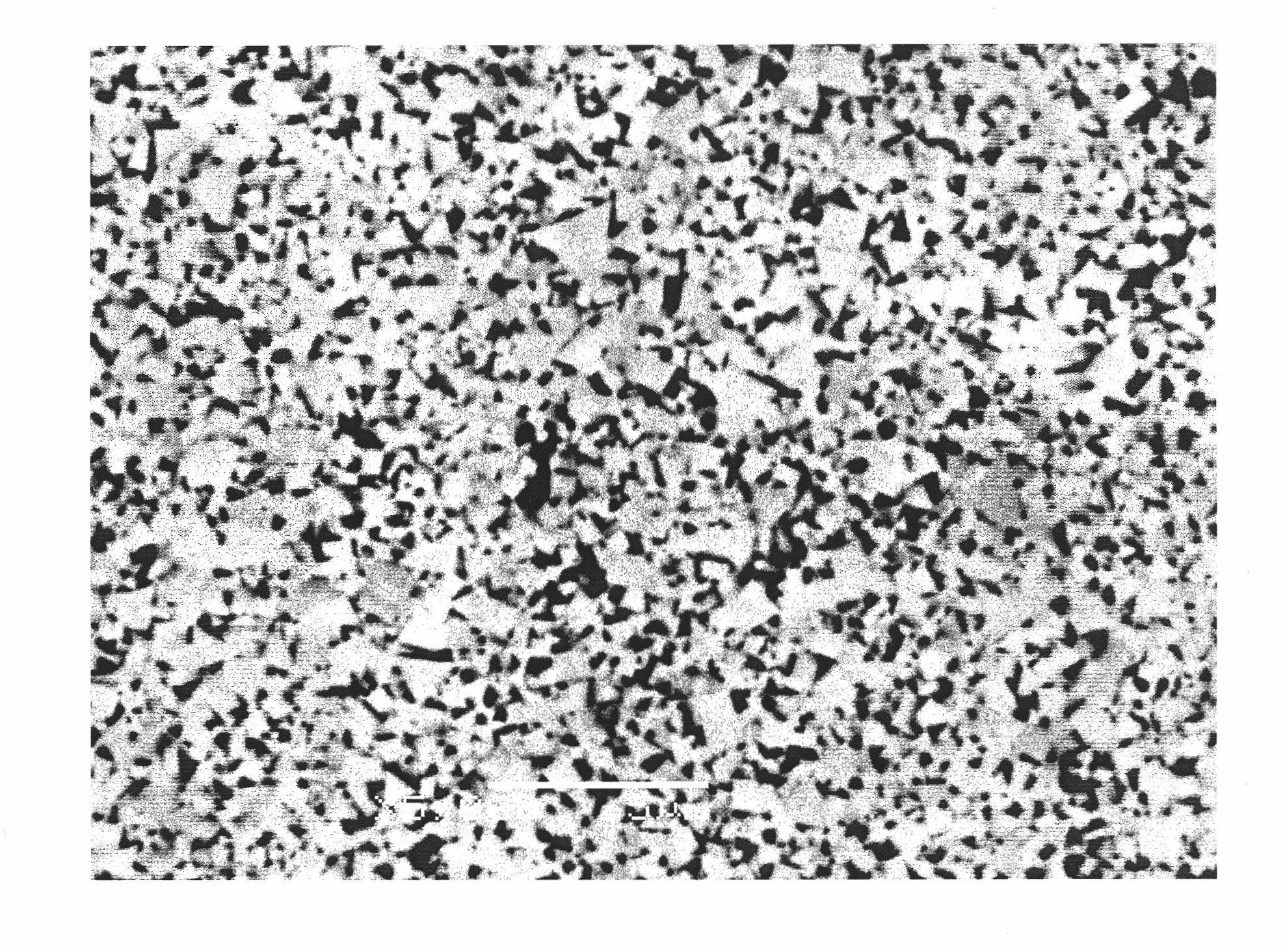
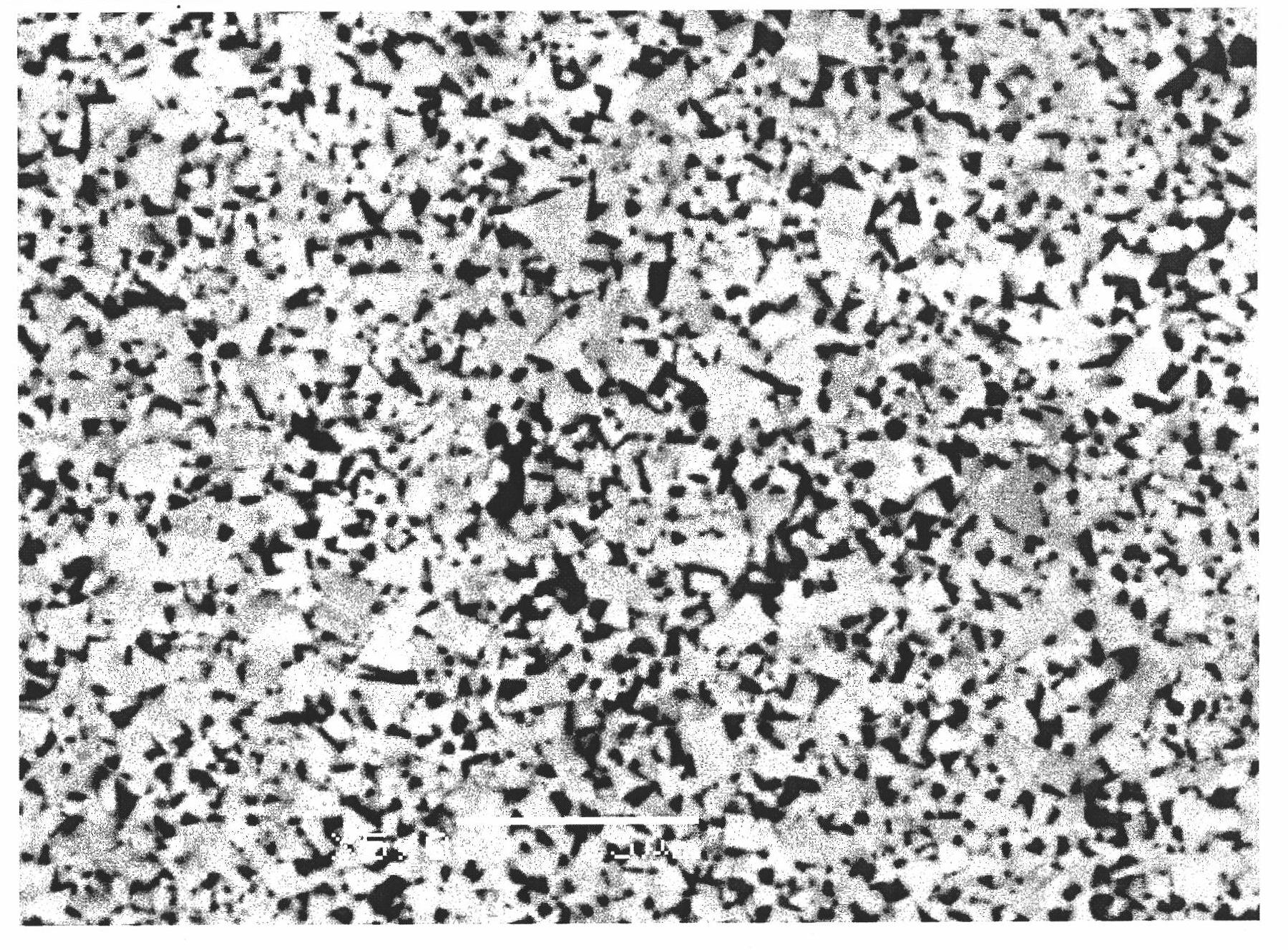
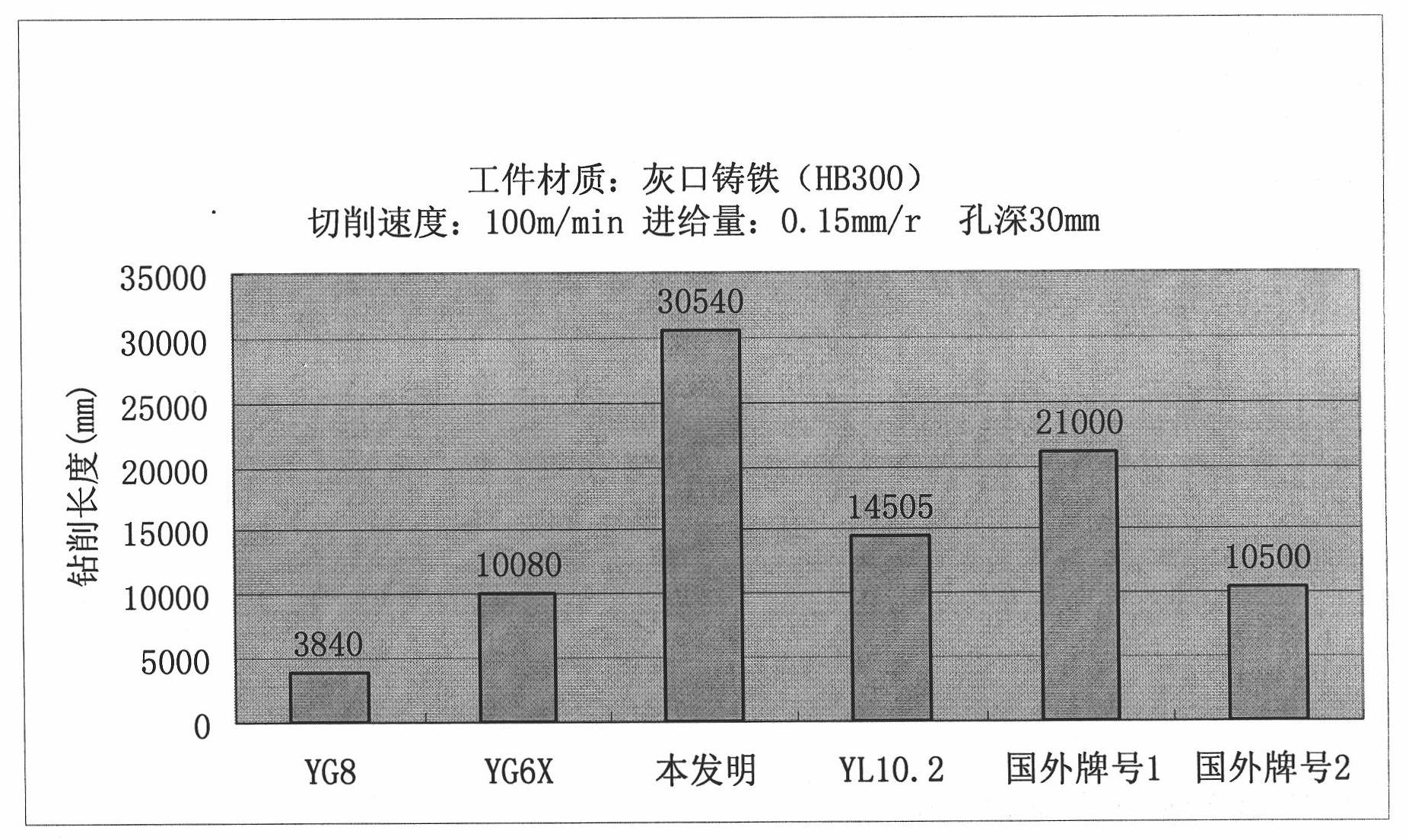
Submicron hard alloy and preparation method
The invention discloses a submicron hard alloy and a preparation method thereof. The alloy comprises the following components in percentage by weight: 7 to 9 percent of C, 0.2 to 0.5 percent of Cr3C2, 0.1 to 0.4 percent of VC, and the balance of WC of 0.7-0.9 mu m. The preparation method comprises the steps of material blending, wet grinding, drying, forming and sintering, wherein the ratio of grinding media to material of the wet grinding is (4.5-6):1, the rotating speed of a wet grinder is 30 to 40 revolutions per minute, and the grinding time is 28 to 45 hours; a mixed material is dried, a molded blank is sintered at the temperature of between 1,400 and 1,450 DEG C, the sintered pressure is between 58 to 100 bar, and the heat insulation time is 30 to 60 minutes; and the WC grain size in the alloy is 0.7 to 0.9 mu m, the hardness is HV31730-1860, and the bending strength is not smaller than 4,000N / mm<2>. A cutting tool manufactured by using the alloy can also ensure enough strength and flexibility while increasing the abrasion resistance, can meet requirements on high efficiency and high durability of the cutting tool, is used in the fields of cutting cast irons, aluminum alloys and non-ferrous metals and drilling steel pieces, and can realize large-scale industrial production.
Owner:ZHUZHOU HARD ALLOY GRP CO LTD
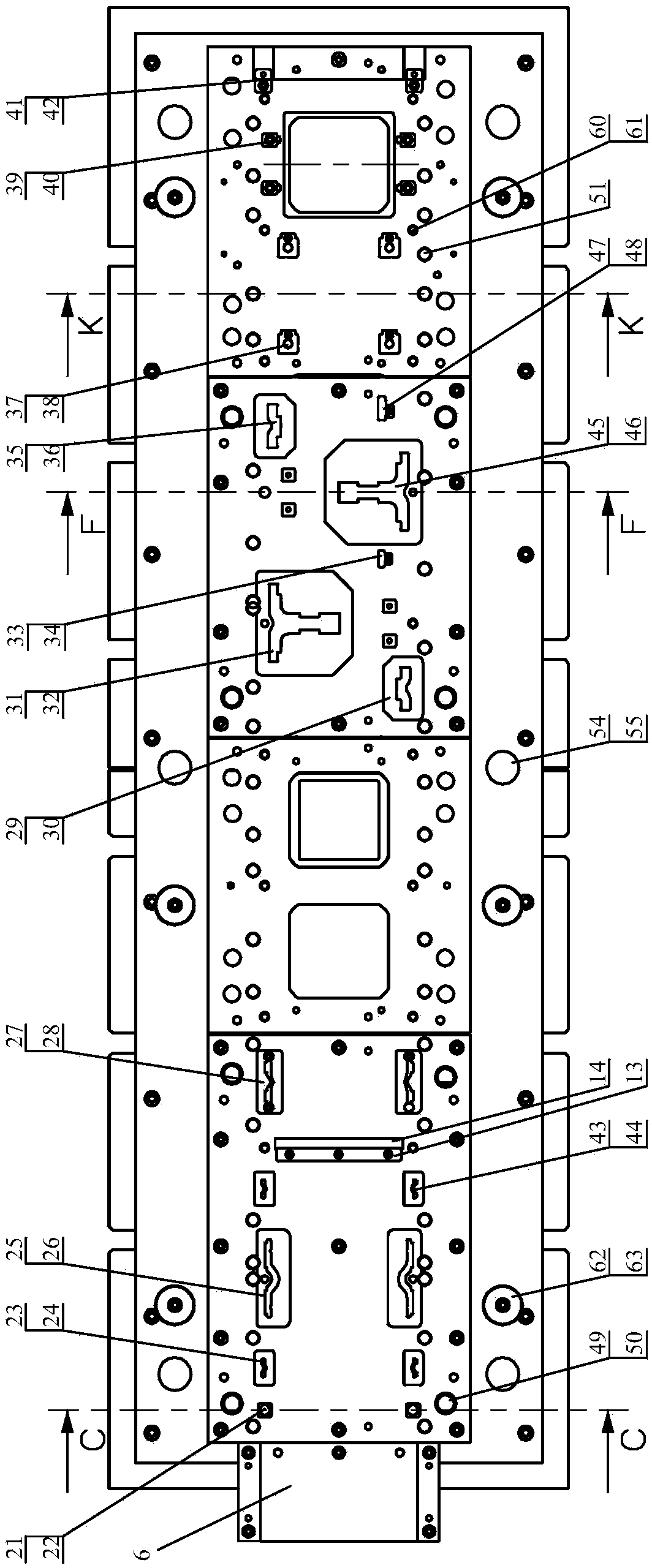
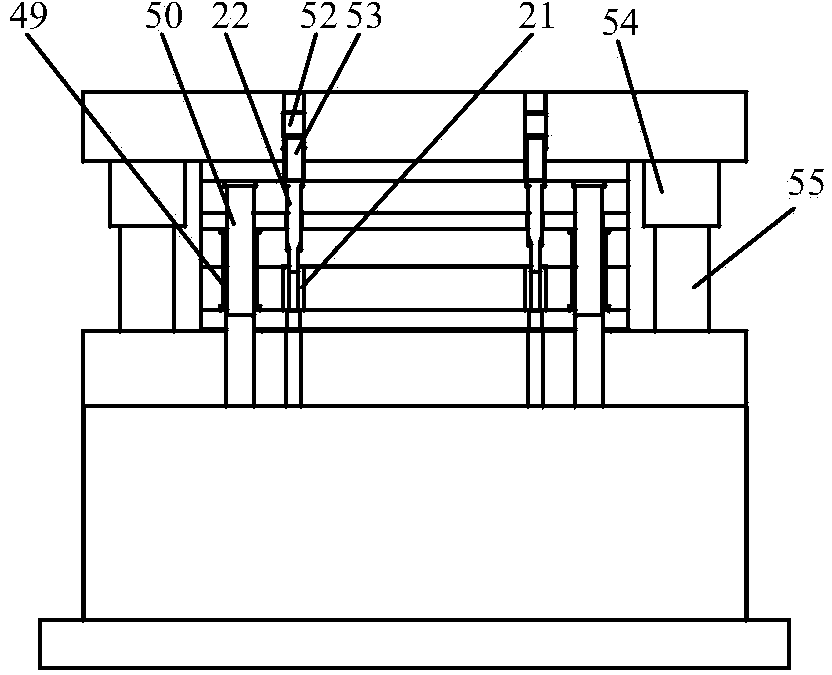
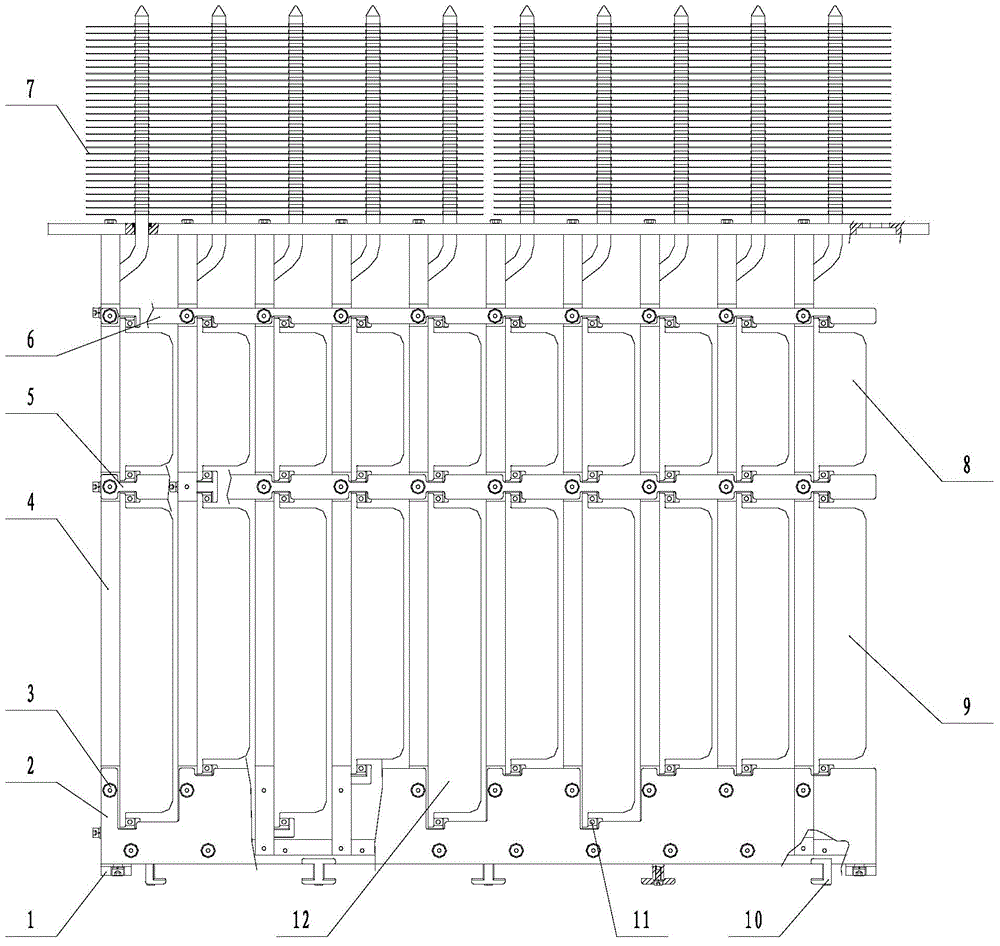
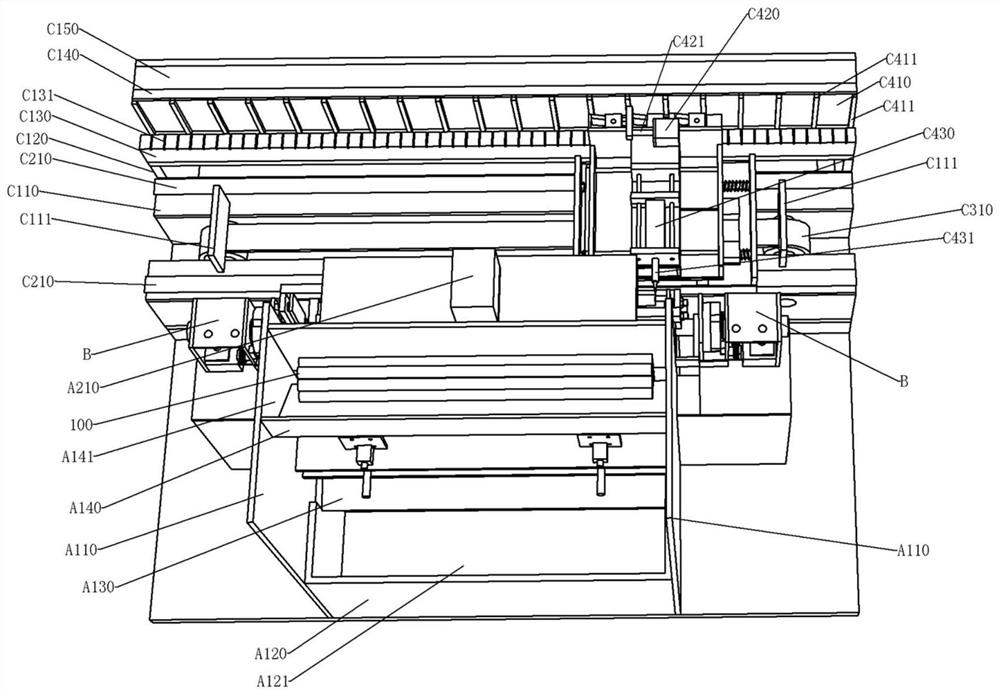
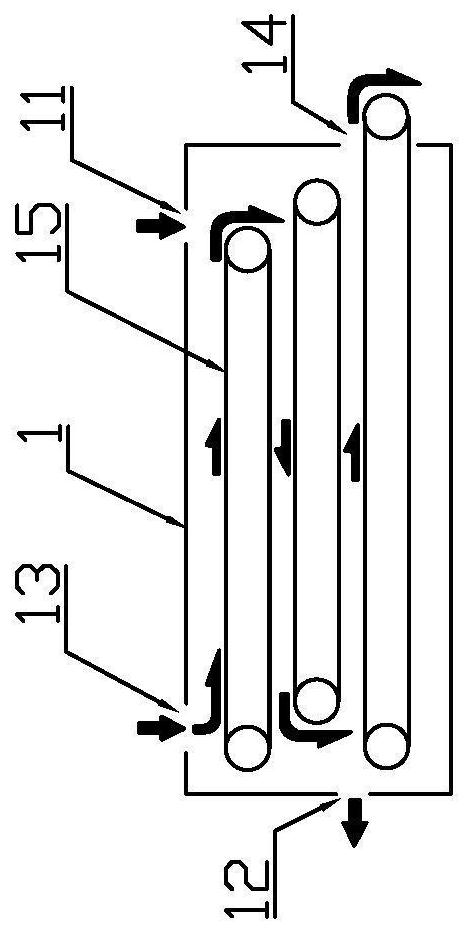
Suspension supporting base multi-station progressive die
ActiveCN103962452ACompact structureHigh guiding precisionShaping toolsPerforating toolsPunchingEngineering
The invention relates to a suspension supporting base multi-station progressive die which comprises an upper die assembly, a lower die assembly, an unloading plate, an unloading plate base plate and a mis-feeding detection device. The upper die assembly is sequentially provided with a corresponding male die in the feeding direction, the lower die assembly is sequentially provided with a female die embedding sleeve matched with the male die of the upper die assembly, corresponding positions on the unloading plate and on the unloading plate base plate are provided with a through hole capable of penetrating through the male die of the upper die assembly, the unloading plate is disposed on the unloading plate base plate, and the unloading plate base plate is arranged on the upper die assembly through an unloading spring. By means of the progressive die, suspension supporting bases are produced in a continuous drawing progressive die mode. The mechanism is compact in structure, high in guide precision, stable in unloading and precise in pitch fixing, and feeding and discharging are convenient to achieve. A quick replacement structure is adopted to a punching male die, and maintenance and replacement time of the die is effectively shortened. After being tried, the mechanism is good in use effect and can meet requirements for high efficiency and high precision of stamping production.
Owner:LIUZHOU VOCATIONAL & TECHN COLLEGE
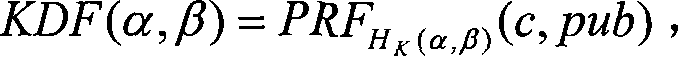
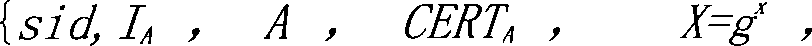
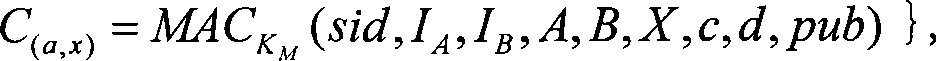
High-efficiency, deniable, safety-unforgeable cryptographic key exchanging protocol of on-line computation
InactiveCN101175076AExcellent online computing efficiencyExponent savingPublic key for secure communicationUser identity/authority verificationKey exchangeHash function
The invention pertains to the field of encrypt protocol technology, in particular pertains to a secure key exchange protocol which can calculate online efficiently, can repudiate, can not be forged. The environment and the method for realizing the protocol is: the public key of the user 'A' is that A is equal to ga, and the DH key component is that X is equal to gx; The public key of the user 'B' is that B is equal to gb, and the DH key component is that Y is equal to gy. The user 'A' verifies that the user 'A' simultaneously know a and x through Bcx+eaYda+fx; The user 'B' verifies that the user 'B' simultaneously know b and y through Aeb+dyXcb+fy. The input inclusion protocol of hash function c, d, e and f implements all relevant public information each time, the input and output mutual nesting and influence. In order to improve the efficiency of online calculation, the input of c does not include Y, the input of d does not include X, e is 1 or 0. The protocol is capable of fulfilling the different needs and the priorities of users to key exchange such as the efficiency of online calculation, repudiatability, security which can not be forged, denial-of-service-attack proof, internal-situation-leakage proof, and explicit or implicit identity and key confirmation.
Owner:赵运磊 +2
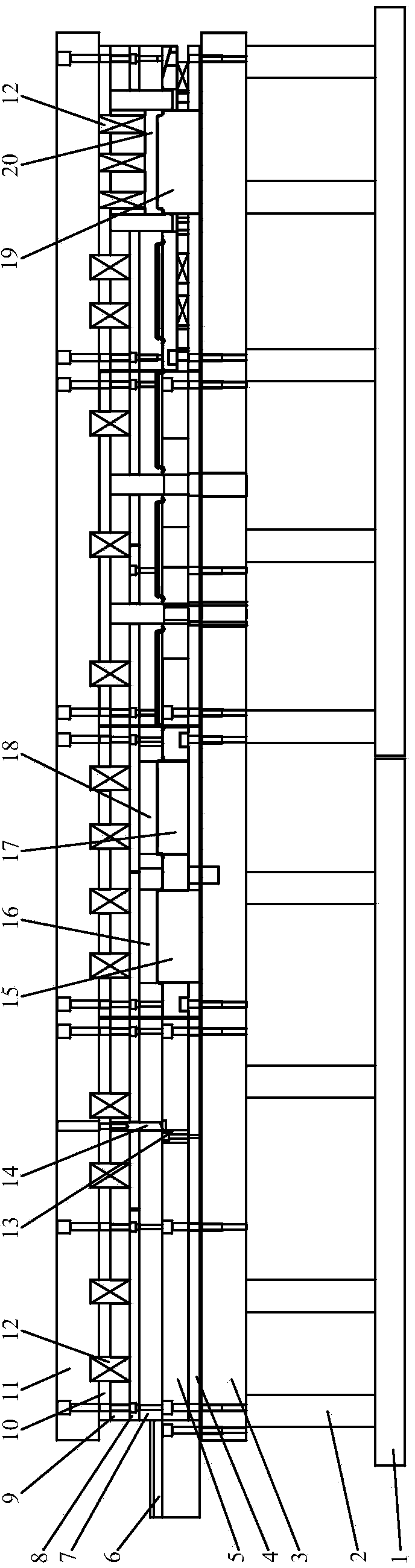
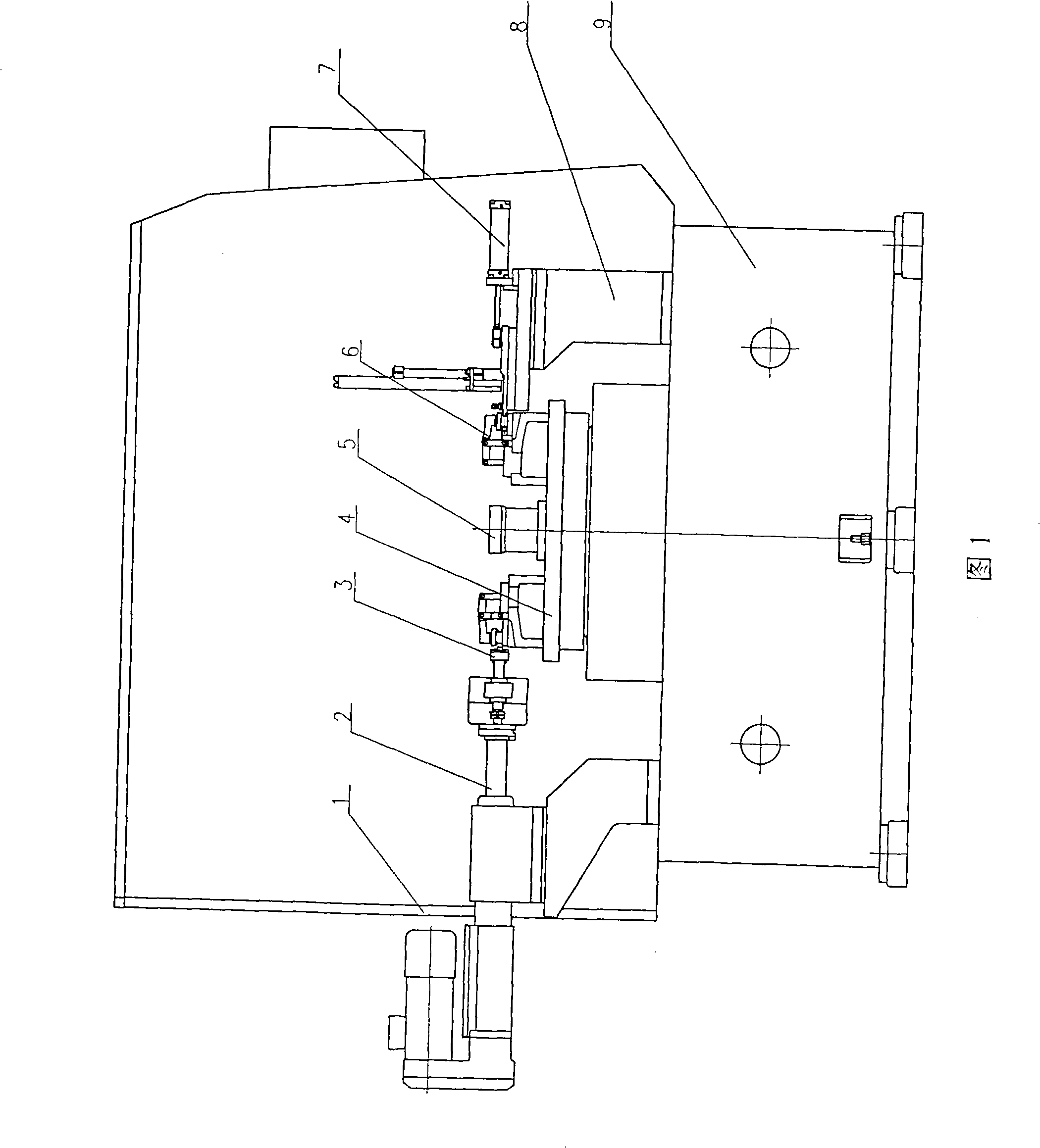
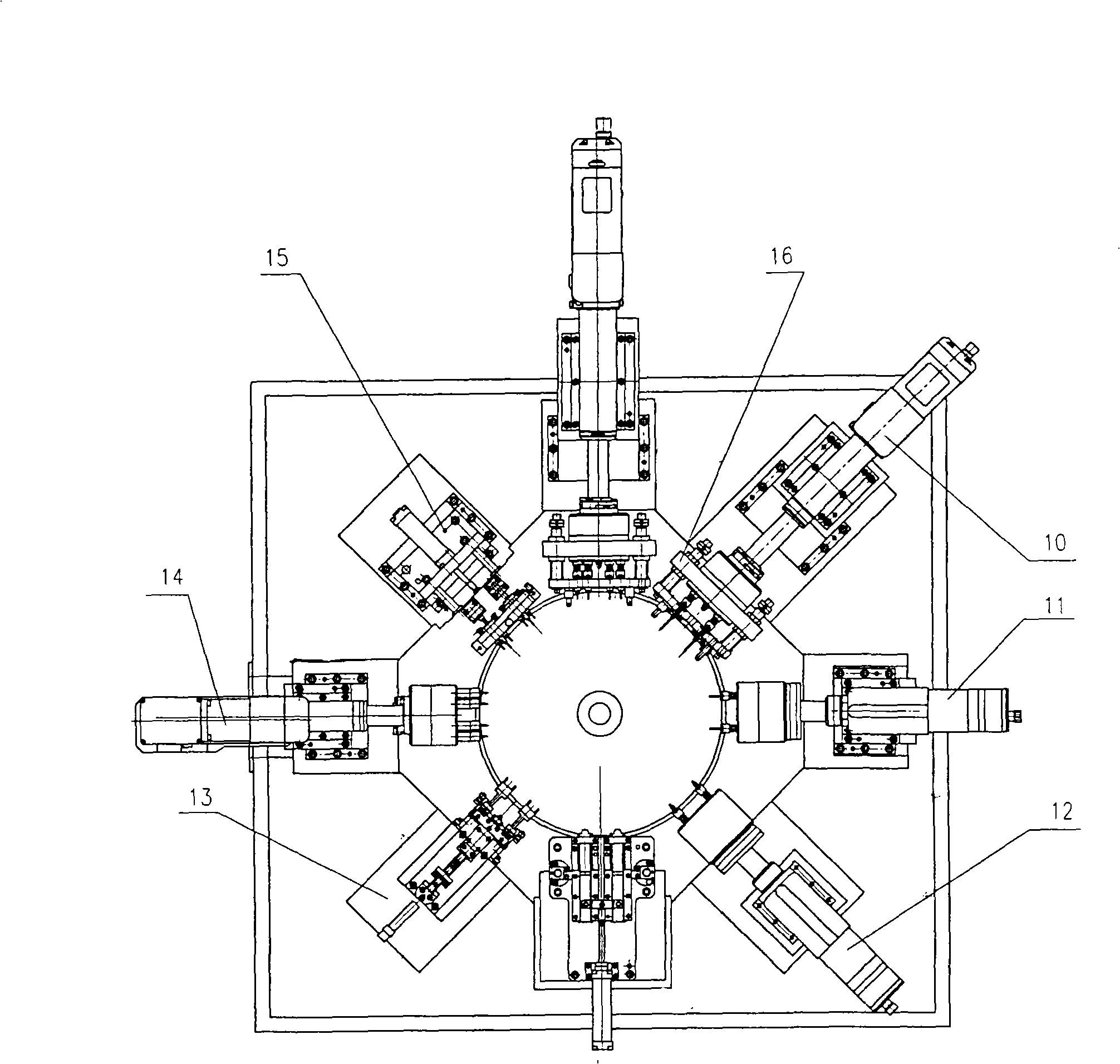
Machine special for link lever eight-station borehole
InactiveCN101318302AMeet efficiencyFulfil requirementsMetal working apparatusEngineeringPosition error
The invention relates to a special connecting rod drilling machine with eight stations. The machine tool is wholly and protectively arranged on an integrated casting machine tool bed, a rotary worktable is fixed on the integrated casting machine tool bed, a fixture part is fixed on the rotary worktable, an oil rotary distributor is fixed in the center the rotary worktable, a unit head and a base seat of a loading and unloading device are fixed on the integrated casting machine tool bed; a loading device, a two-axis drilling through center oil hole unit head, a two-axis drilling and counterboring center oil hole unit head, a two-axis drilling center oil hole unit head, an unloading device, a four-axis tapping unit head and a blowing detecting device are all fixed on the unit head and the base seat of the loading and unloading device; a two-axis running drilling template is connected with the two-axis drilling through center oil hole unit head via a guide rod, and a four-axis running drilling template is connected with a four-axis drilling connecting thread bottom hole unit head via the guide rod. The special drilling machine has the advantages of completing processes that need to be processed by a single device in a machine tool, avoiding repetitive position error, simplifying the process, meeting the processing requirement of high efficiency and high precision of parts and being suitable for mass production.
Owner:南京聚星机械装备股份有限公司
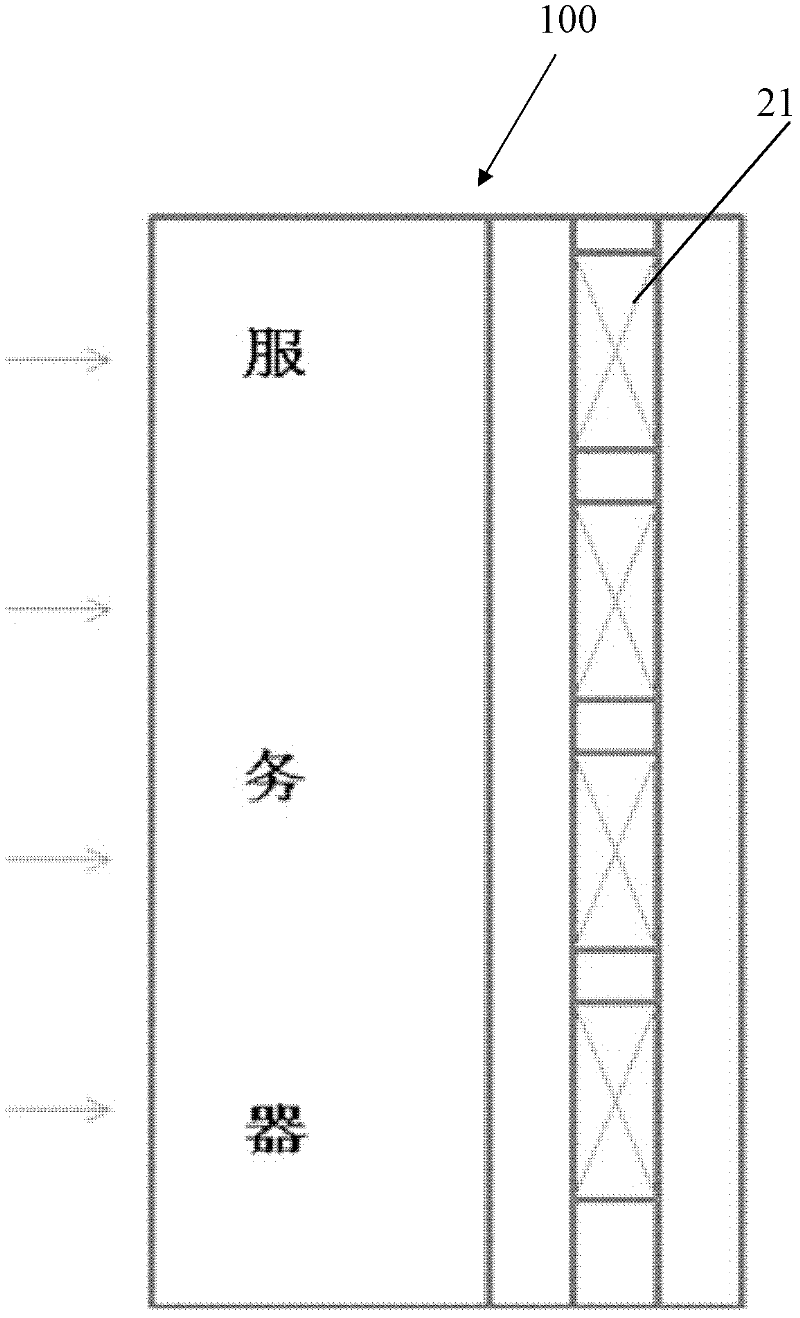
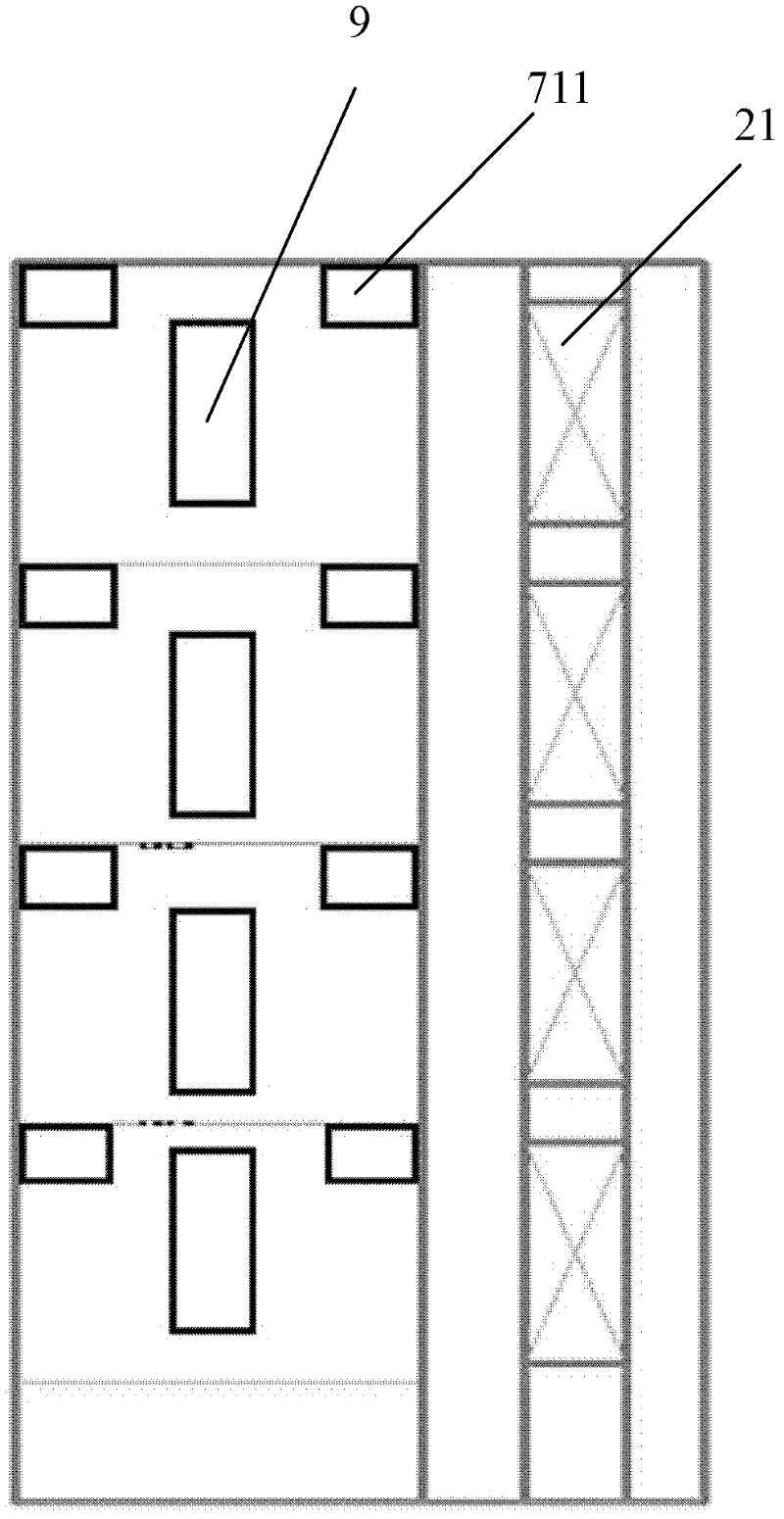
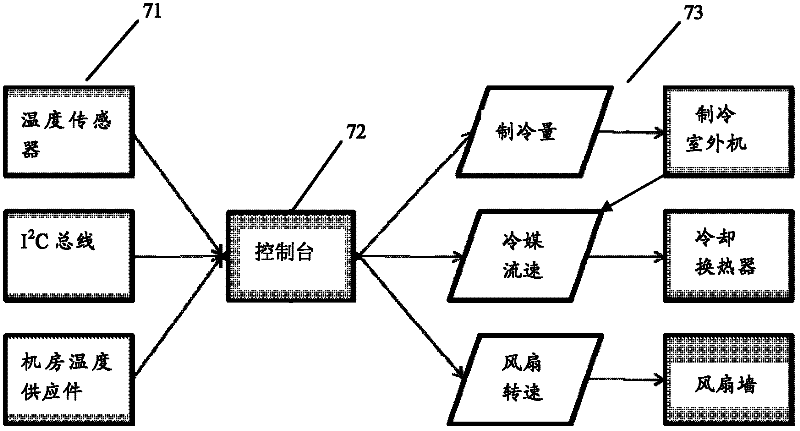
Heat dissipation device for cabinet and method for heat dissipation of cabinet
ActiveCN102340977AHigh densityTimely coolingDigital data processing detailsCooling/ventilation/heating modificationsHeat managementHeat flow
The invention provides a heat dissipation device and a heat dissipation method for a cabinet. Heating parts are arranged in the cabinet. The heat dissipation device comprises a cooling fan wall and control system and a heat dissipation air duct, wherein the cooling fan wall and control system comprises a fan wall which is arranged at the back of the cabinet and is provided with groups of fans, and the heat dissipation air duct is arranged in the cabinet and is communicated with the fan wall. By adopting the heat dissipation device and the heat dissipation method provided by the invention, heat generated by a server in the cabinet can be dissipated in time, and the heat exchange efficiency and the exchanged heat flow rate of a clustered system are improved; by dividing the heat dissipation air duct into a plurality of areas which are isolated from each other, the structure of the air duct can be optimized and the balanced cooling of the cabinet is realized; and by arranging a heat management and health monitoring system, an optimal heat dissipation effect can be reached. Besides, the heat dissipation effect of the server cabinet can be ensured to satisfy the requirements of high efficiency and high density. Moreover, the energy loss of all equipment in the cabinet can be reduced and the maintenance and use costs are reduced.
Owner:中科腾龙信息技术有限公司
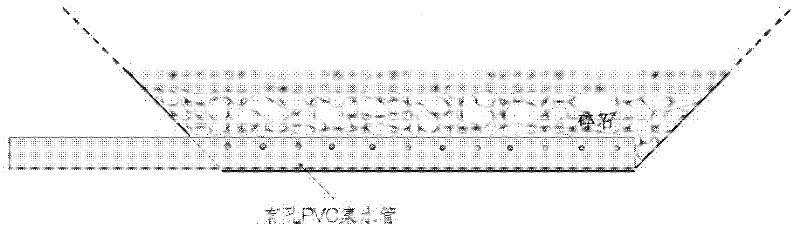
Mechanical excavation method for hard-rock tunnel with medium-short length
The invention discloses a mechanical excavation method for a hard-rock tunnel with the medium-short length and belongs to the field of construction methods. The mechanical excavation method comprises the steps that first, a plurality of parallel and vertical grooves are cut on a tunnel face in a tunnel profile at certain intervals, and each vertical groove enables rock on the two sides of the vertical groove to form a free face with the certain depth; and then crushing equipment is utilized to apply extruding stress to each free face of the two sides of the corresponding vertical groove, so that the rock of the two sides of the vertical grooves is crushed, and excavation of the tunnel is achieved. Compared with the prior art, the requirement of the construction, limited in blasting vibration, of the new built rock tunnel with the medium-short length for the aspects such as the economy, efficiency and the safety risk can be met; and meanwhile the construction efficiency is greatly improved compared with the prior art.
Owner:张华 +1
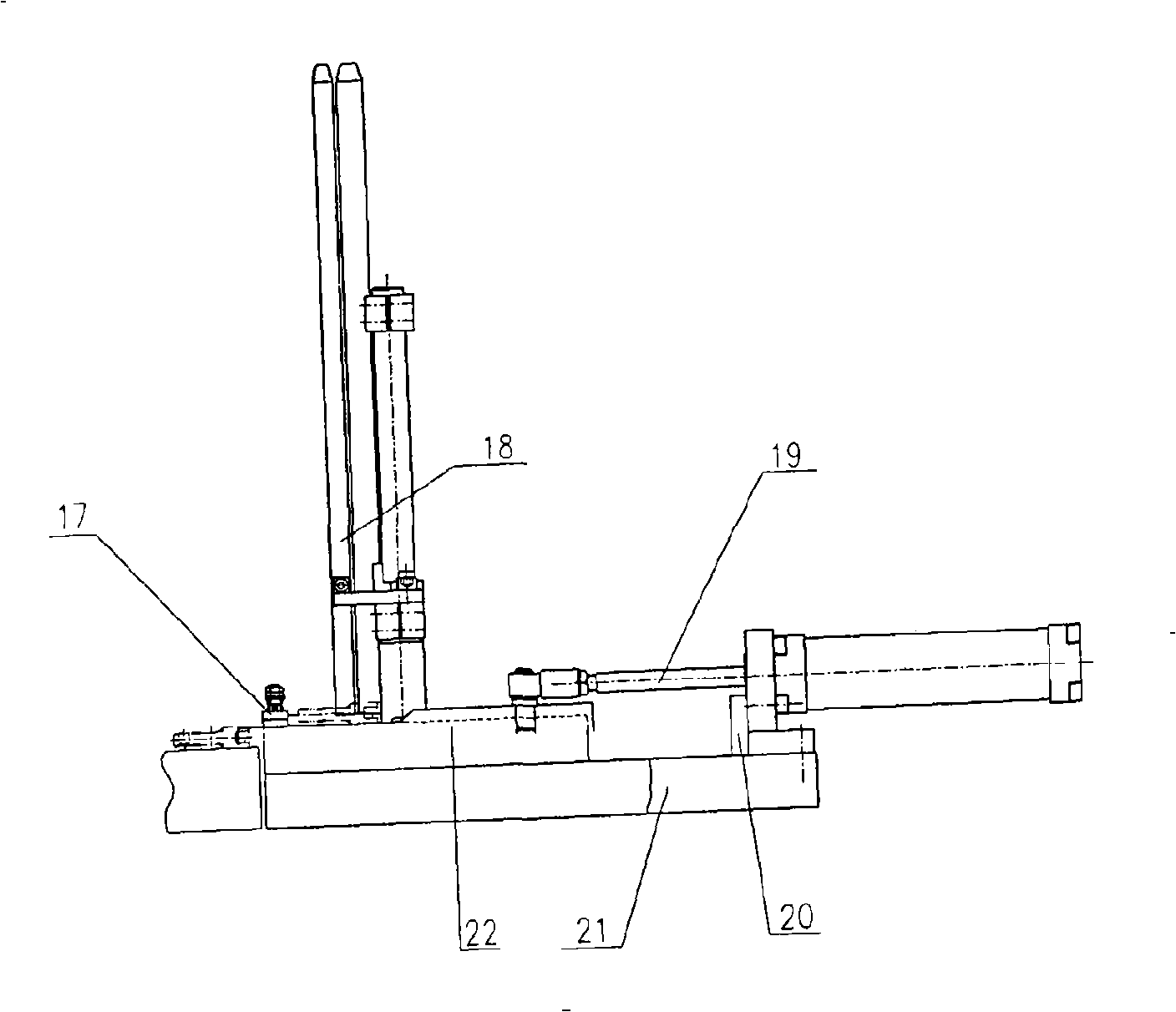
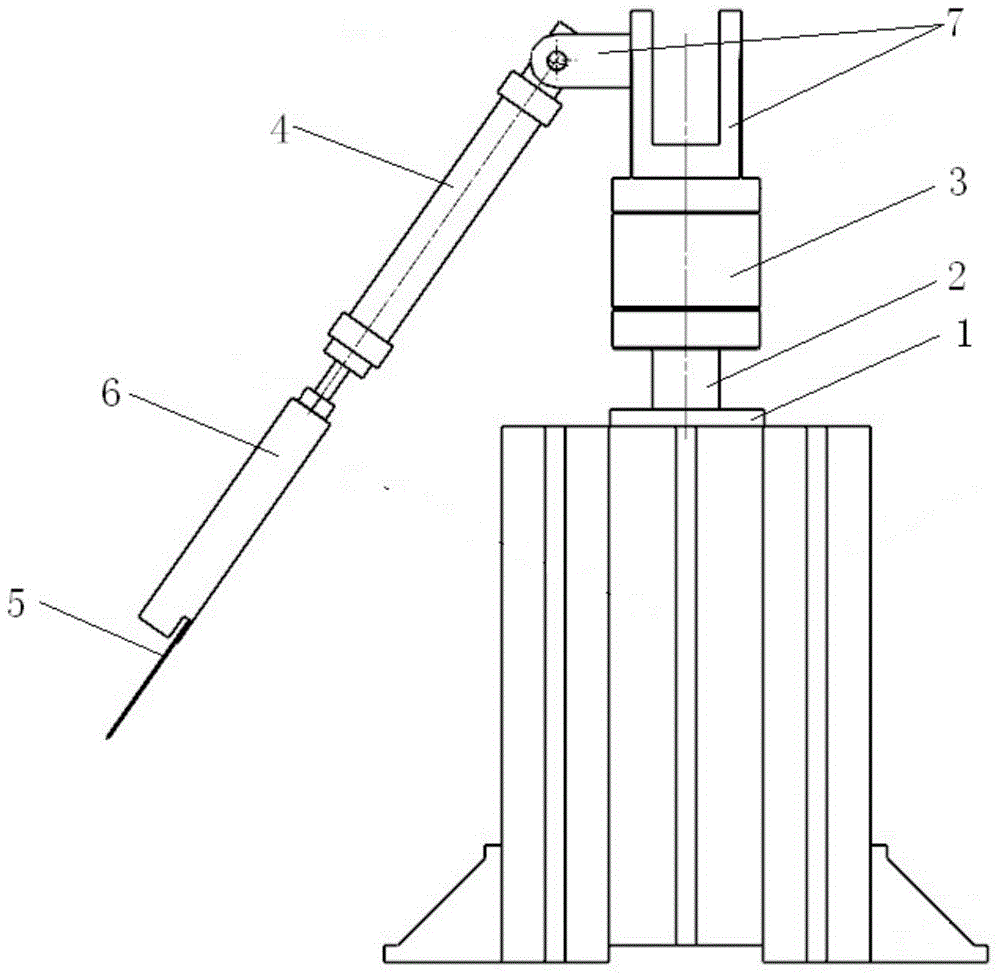
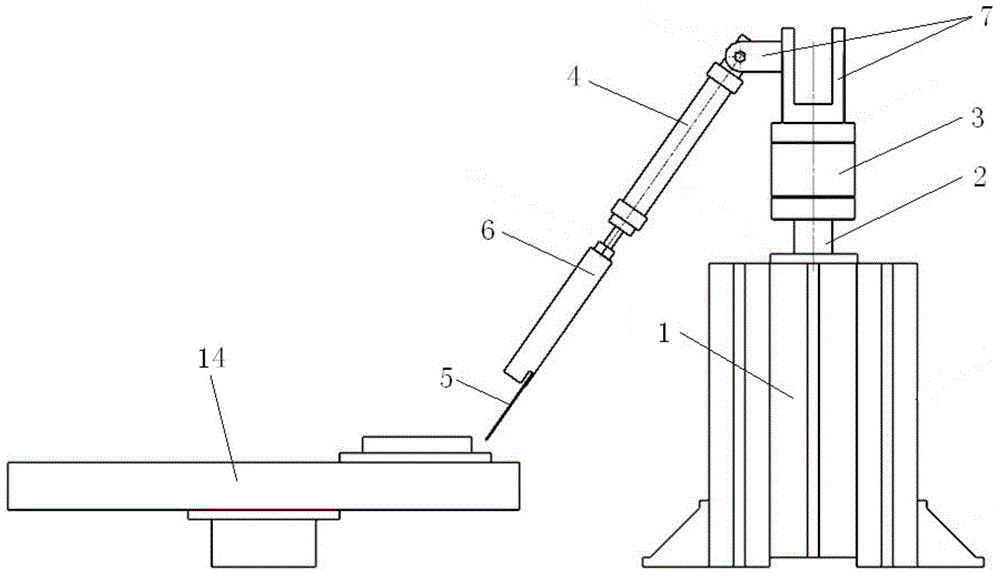
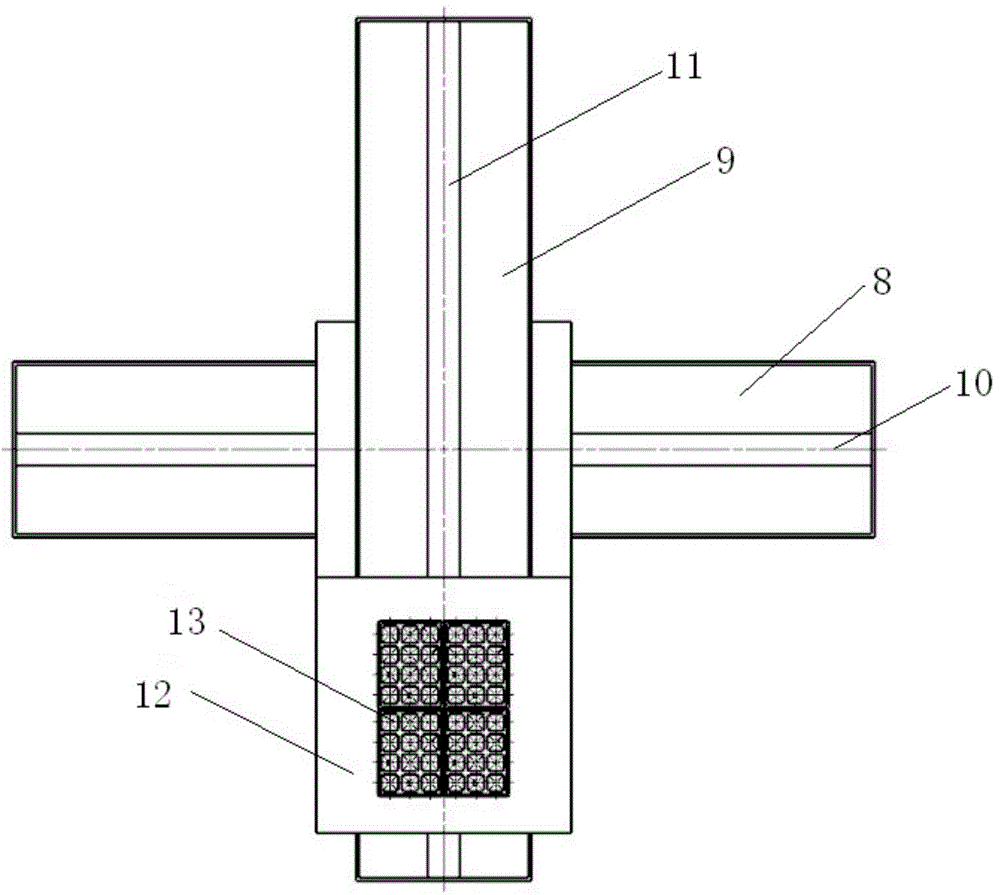
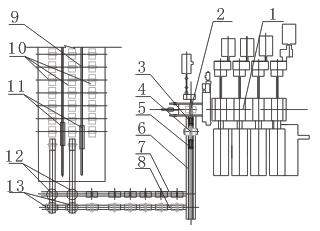
Plug seedling transplantation mechanical hand
ActiveCN103975676ASimple structureReasonable structureProgramme-controlled manipulatorTransplantingEngineeringManipulator
The present invention discloses a plug seedling transplantation mechanical hand, which comprises a mechanical hand, a vertical lifting mechanism, a rotation mechanism, a telescopic mechanism and a PLC controller, wherein the lifting mechanism, the rotation mechanism and the top end of the telescopic mechanism are connected, the mechanical hand is arranged on the bottom end of the telescopic mechanism, the lifting mechanism, the rotation mechanism and the telescopic mechanism respectively form a signal connection with the PLC controller, and an included angle is formed between the telescopic mechanism and the rotation mechanism. According to the plug seedling transplantation mechanical hand, the seedling taking rate can achieve 80-100 / min, the efficiency is 6-8 times the efficiency of the artificial seedling transplantation, the transplantation machine has characteristics of relatively small volume, simple structure and low price, the movement of grabbing of the plug seedlings simulates the finger action, the movement trajectory is flexible and reliable, and the plug seedling transplantation mechanical hand is suitable for grabbing of vegetable plug seedlings with different root system structures, can meet requirements of different plug structures, different plug grid distances, seedling taking efficiency and seedling taking in the side-by-side manner, and has characteristics of high reliability, high flexibility and no damage on seedlings.
Owner:JIANGSU POLYTECHNIC COLLEGE OF AGRI & FORESTRY
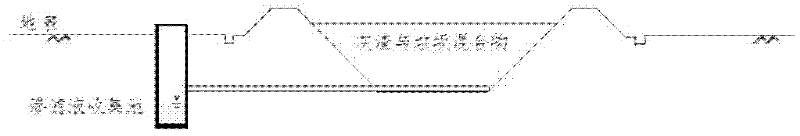
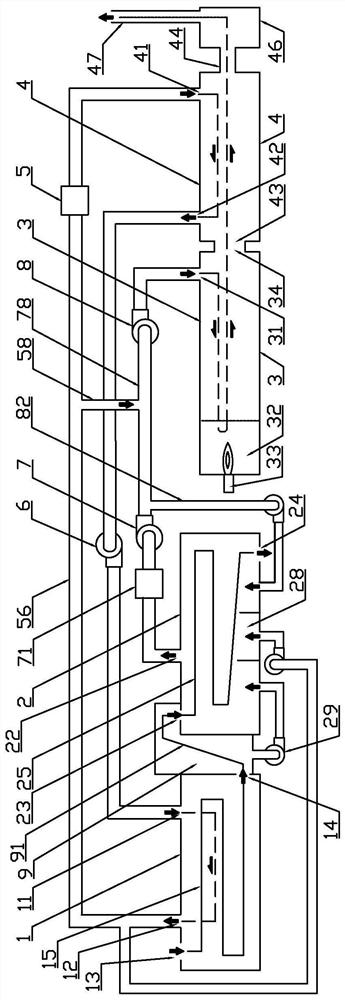
Transportation system of hot rolled coil entering high rack warehouse after coil discharge
InactiveCN102431756AReduce storage timeMeet efficiencyStorage devicesProduction lineTransport engineering
The invention discloses a transportation system of a hot rolled coil entering a high rack warehouse after coil discharge, used for transporting the hot rolled coil in a hot-rolled workshop into the high rack warehouse after discharged at the coil discharge position on a coiler. The transportation system is characterized in that the transportation system comprises a coil transportation rail A with a coil transportation trolley and a transportation line, wherein one end of the coil transportation rail A is relatively connected with the coil discharge position of the coiler, the other end of the coil transportation rail A is connected with one end of the transportation line in a matching way, and the other end of the transportation line extends into the high rack warehouse; and the hot rolled coil is transported to the transportation line through the coil transportation trolley along the coil transportation rail after discharged from the coiler and sent into the high rack warehouse through the action of the transportation line. With the adoption of the transportation system, the high rack warehouse is directly butted to a hot-rolled production line without using a mode of crown block hoisting and transportation, thereby the transportation time of warehousing the hot rolled coil is greatly shortened, the transportation system is rapid and has high efficiency, and the safety hidden dangers existing in the hoisting and transportation process of a crown block are also avoided.
Owner:CHINA NON-FERROUS METALS PROCESSING TECH CO LTD
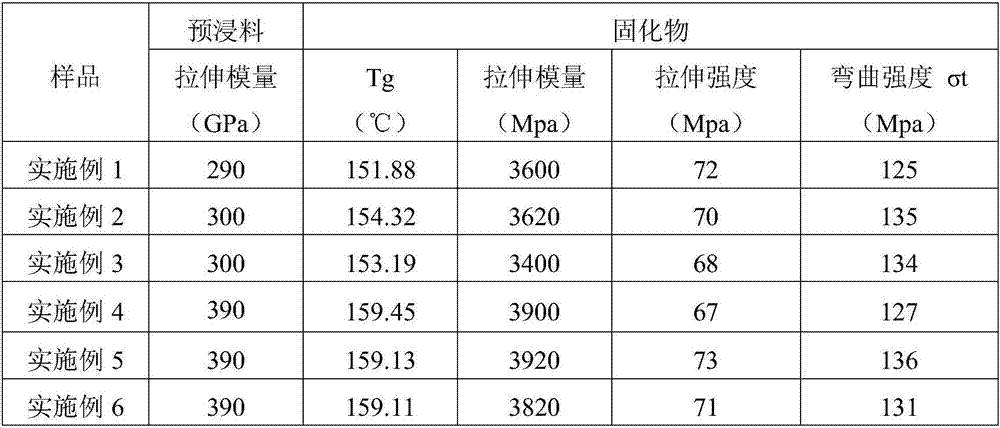
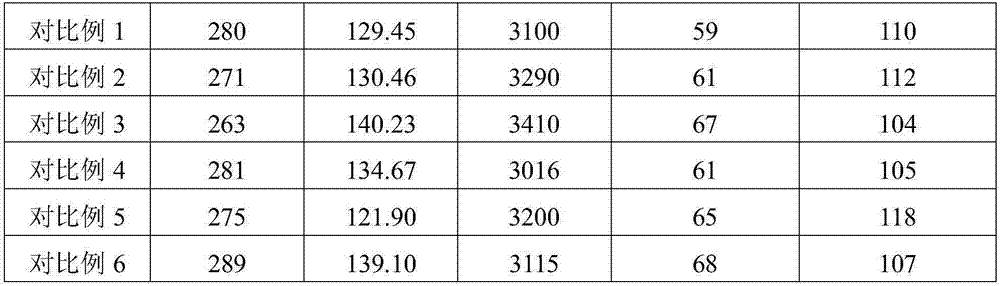
Preparation method of carbon fiber prepreg
The invention discloses a preparation method of carbon fiber prepreg. The method comprises the following steps: 1, uniformly stirring phenolic epoxy resin, solid bisphenol A epoxy resin and liquid bisphenol A epoxy resin at 80-90 DEG C for 20-30 min to obtain a solution A; (2) adding a curing agent dicyandiamide to the mixed solution A, and uniformly stirring the solution A and the curing agent at 70-80 DEG C for 20-30 min to obtain a mixed solution B; (3) adding a promoter urea to the mixed solution B, and stirring and mixing the mixed solution B and the promoter at 70-80 DEG C to obtain a mixed solution C; (4) placing the mixed solution C in a gluing machine to obtain a glue film for the prepreg; and (5) allowing the glue film to pass through a hot pressure roller to melt a resin matrix and make carbon fibers embedded in the resin matrix. The carbon fiber prepreg prepared by the method has the advantages of no cooling or heating in the curing process, reduction of production steps, simplification of the production process and reduction of the production cost.
Owner:JIANGSU ZHAOJUN NEW MATERIAL CO LTD
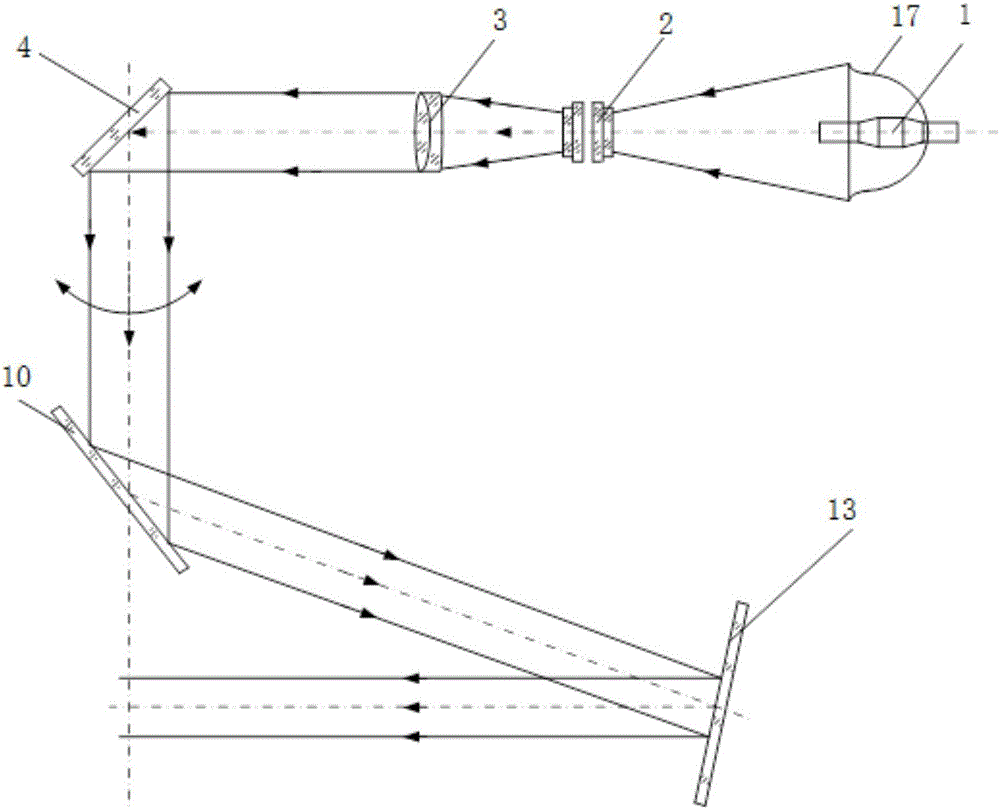
360-degree centripetal scanning type solar simulator
InactiveCN105822957AImprove efficiencySimplify complexityLighting support devicesTesting optical propertiesOptical propertyIntegrator
The invention relates to the technical field of optical measuring equipment, in particular to a 360-degree centripetal scanning solar simulator. It is characterized in that it includes a base, a horizontal arm is arranged above the base, the light source is fixedly connected with the horizontal arm above the base, an integrator is correspondingly arranged on the left side of the light source, and a collimating lens group is correspondingly arranged on the left side of the integrator , the left side of the collimating lens group is correspondingly provided with a first reflector, the fixed sleeve is provided under the end of the horizontal arm, the rotary arm is installed on the fixed sleeve, and the radial circular grating is arranged at the lower end of the fixed sleeve, One side of the radial circular grating is correspondingly equipped with a grating reading head, and the bottom of the radial circular grating is correspondingly provided with a second reflector, and the end of the rotary arm is also provided with a third reflector, and the base is provided with a sample load stage, and the sample stage is set as the sample to be tested. It can meet the high-efficiency and high-accuracy calibration of target optical characteristics under different solar irradiation angles, with a scanning speed of 120° / s and an angle measurement accuracy of 5″.
Owner:NORTH CHINA INST OF AEROSPACE ENG
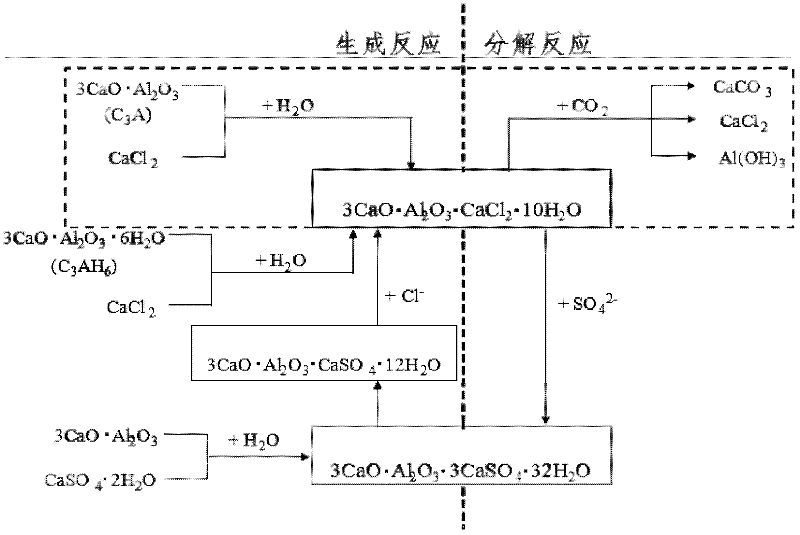
A method for dechlorinating ash by using garbage
InactiveCN102294343AReduce total chlorineReduce heavy metal contentWaste processingSolid waste disposalResource utilizationPollution
The invention belongs to the technical field of environmental protection, and relates to a method for dechlorination of ash by using garbage. The method comprises the following steps: firstly, respectively carrying out pretreatments for ash and garbage; then mixing the pretreated garbage and the pretreated ash according to a certain ratio; finally, carrying out regular water spraying for the resulting mixture. With the method provided by the present invention, the total chlorine content and the total heavy metal content in the ash are substantially reduced, such that the standard and the requirement of the resource utilization of the cement are met in a relatively short time. According to the present invention, the process is simple; the operation cost is low; disadvantages of large amount of water resource consuming and low removal efficiency of insoluble chlorine in the traditional washing process can be overcome; large consumptions of the non-renewable resources such as limestone and clays are reduced, efficient resource utilization of the fly ash from the garbage incineration is realized; the secondary pollution can be effectively controlled; greenhouse gas emission is reduced; the treated ash meets the national policies of energy saving and emission reduction, and sustainable development; an important theoretical and practical significance is provided.
Owner:TONGJI UNIV
Heat pipe radiating module for ship power supply
ActiveCN104869791AAchieving conduction to external space heat dissipation requirementsImprove thermal efficiencyHermetically-sealed casingsCooling/ventilation/heating modificationsInterference fitLocking mechanism
The invention relates to a heat pipe radiating module for a ship power supply. The heat pipe radiating module comprises a fixed base plate, a protection plate, locking screws, a heat pipe radiating unit module, positioning beams I, positioning beams II, radiating fins, a power supply module I, a power supply module II, fan beams, locking mechanisms, and a power supply module III. According to the invention, a protection flange plate is connected to an external case to form an upper heat radiation part and a lower sealing heat conduction part, and the lower part provided with the ship power supply is disposed inside a sealing case, so that sealing, moisture resistance and corrosion resistance problems are solved. Efficient heat pipes arranged on heat conduction substrates in a submerged-arc welding manner extend to the upper portion of the protection flange plate via through holes having a sealing structure in the protection flange plate, and are in interference fit with the radiating fins exposed on the upper portion of the protection flange plate, and the heat generated when the ship power supply works is transmitted outside the sealing chamber, so that the heat of the ship power supply can be rapidly radiated. The heat pipe radiating module has beneficial effects of high heat radiation efficiency, small size and high sealing performance.
Owner:ANSHAN ANMING IND
Solvent-free leather highlighting UV gloss oil and preparation technology thereof
InactiveCN106987203AHigh glossImprove aestheticsPolyurea/polyurethane coatingsEpoxy resin coatingsSolvent freeUrethane acrylate
The invention relates to solvent-free leather highlighting UV gloss oil. The UV gloss oil is prepared from the following raw materials in parts by weight: 70-80 parts of bifunctional aliphatic polyurethane acrylate, 5-15 parts of modified epoxy acrylate, 10-15 parts of monofunctional and bifunctional monomers, 1-5 parts of a photoinitiator and 0.5-1.5 parts of an assistant. The solvent-free leather highlighting UV gloss oil has a high curing speed, the drying time is shorter than 1min, the possibility of reduction of the glossiness due to the fact that dust is attached to a wet film is greatly reduced and a film is excellent in glossiness and aesthetic degree.
Owner:广州从越商贸有限公司
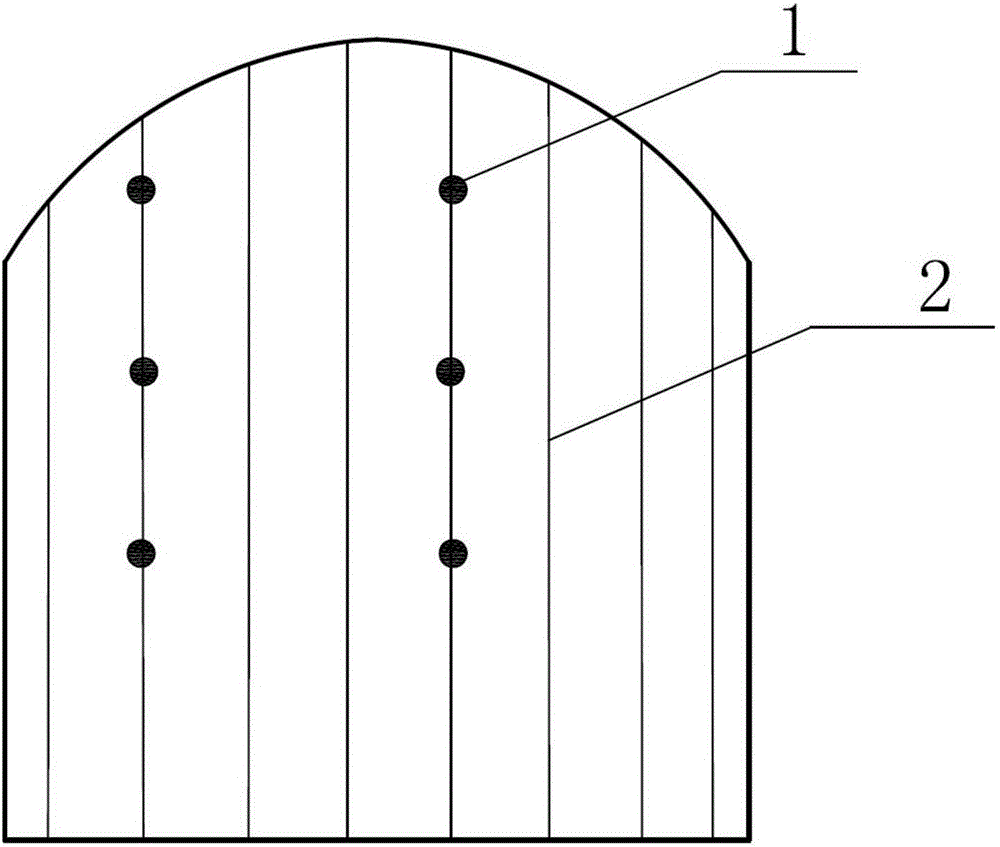
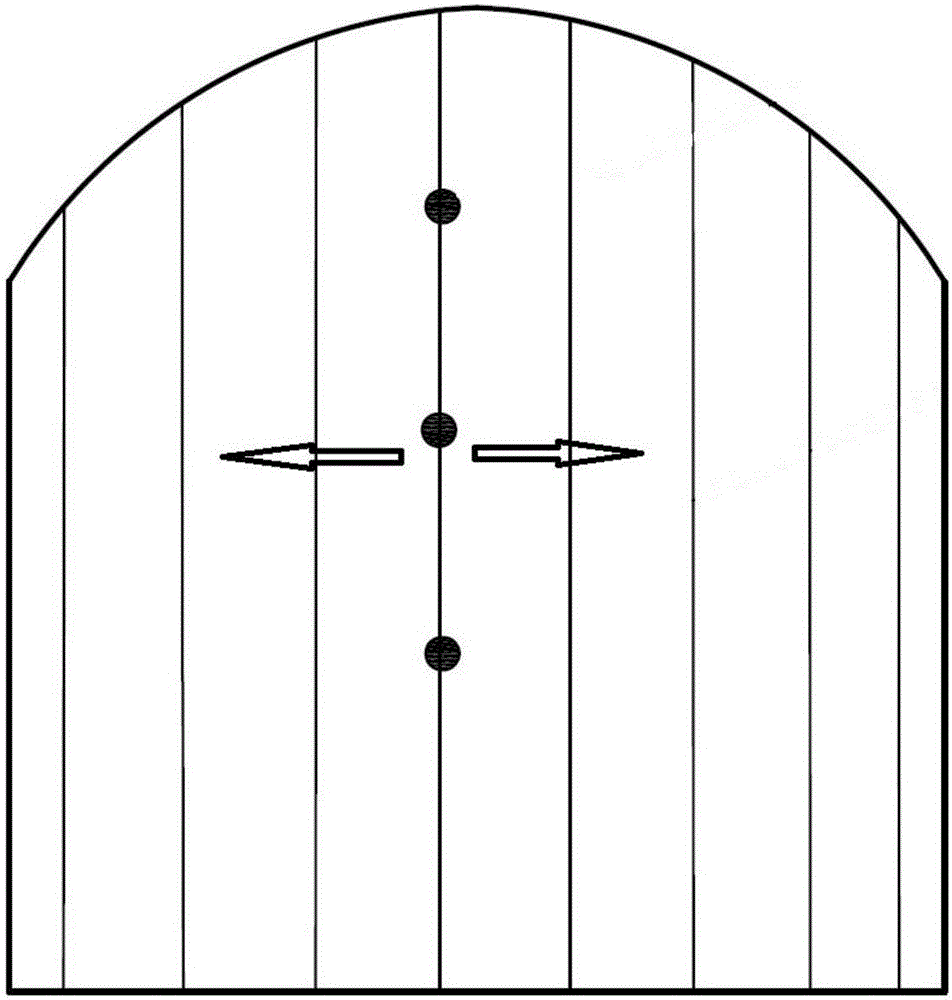
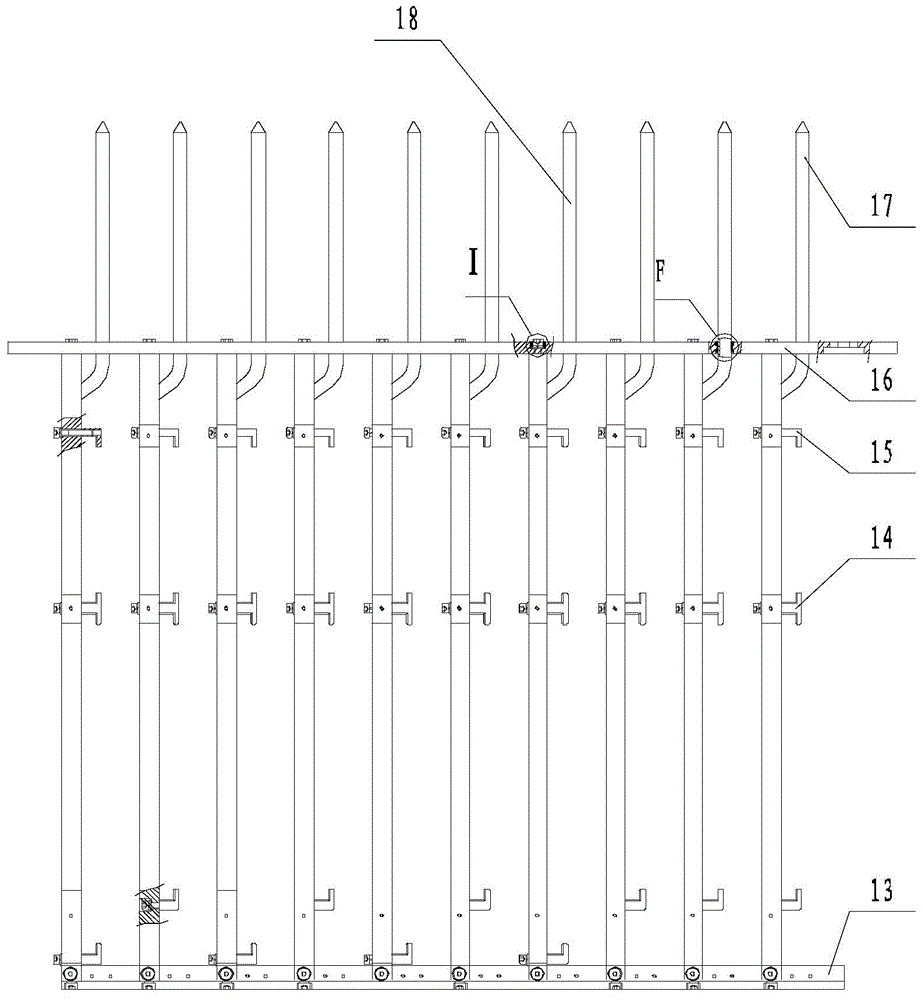
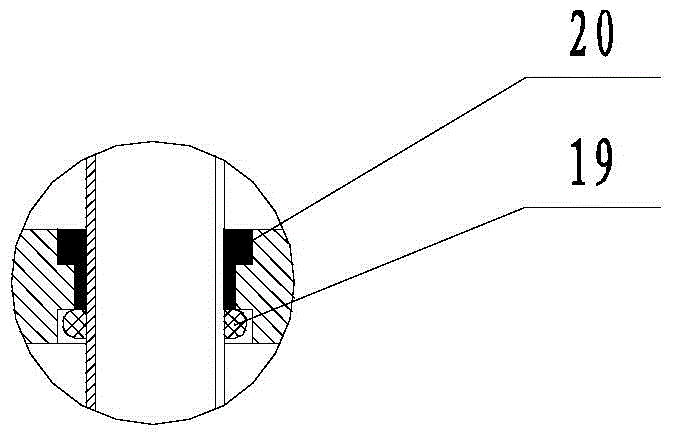
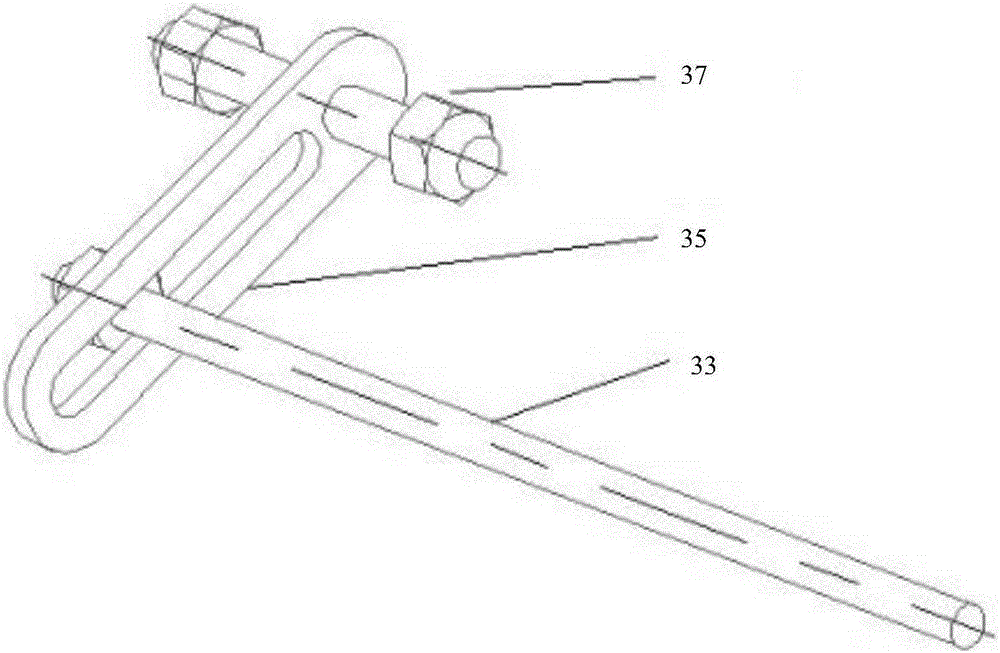
Support for blade testing and blade testing device comprising support
ActiveCN105179288AImprove test accuracyMeet efficiencyPump controlNon-positive displacement fluid enginesEngineeringTest fixture
The invention relates to a support for blade testing and a blade performance testing device comprising the support. The support for blade testing comprises a center shaft. The two ends of the center shaft are supported by end covers. The end covers are fixedly connected through supports. The support further comprises two fastening discs with which the center shaft is sleeved. Fixing rods penetrate the fastening discs to be fixed to the two end covers. Adjusting bolts clamp the fastening discs and are connected with supporting arms. Sliding grooves are formed in the supporting arms. Connecting rods are connected into the sliding grooves in an inserted manner. One end of each connecting rod is fixed through a nut, and the other end of each connecting rod is suspended. The support and the testing device have the beneficial effects that the testing device can effectively determine the reasons of the problems of motor efficiency and fan efficiency, the blade design capacity and developing efficiency are improved, and the design time is shortened; a support shaft system is rapid and accurate in centering, the structural wind resistance is small, the experimental precision is ensured, the universality is high, and the support is applicable to fans of various specifications.
Owner:SHANGHAI MALU RI YONG JEA GATE ELECTRIC +2
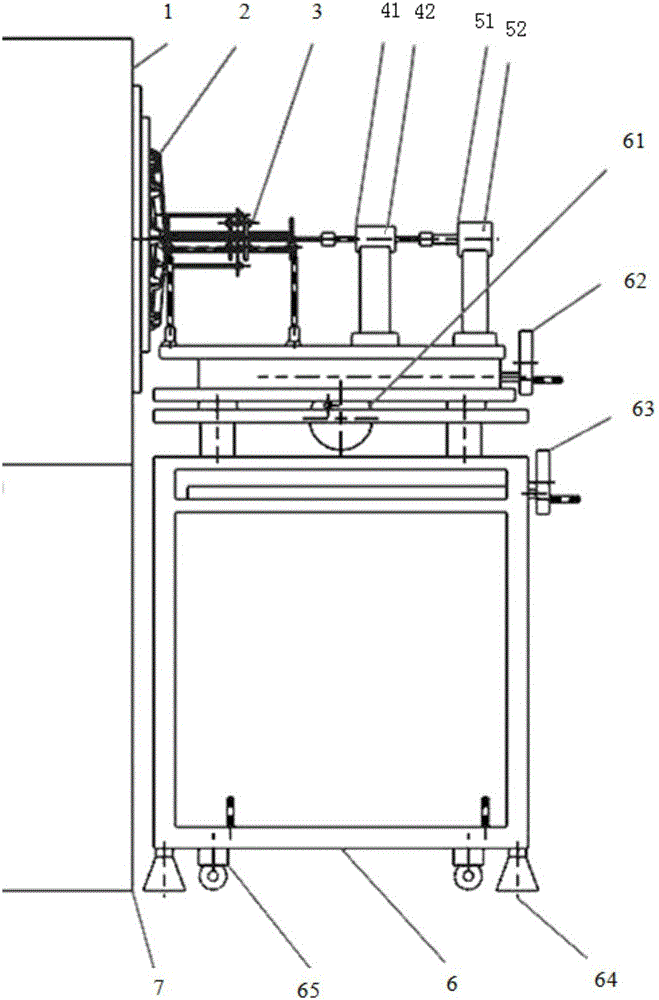
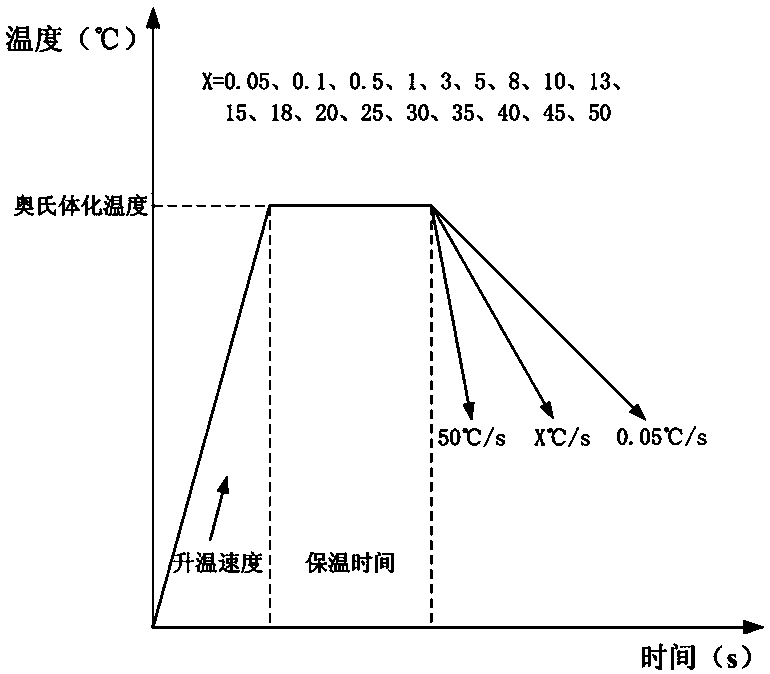
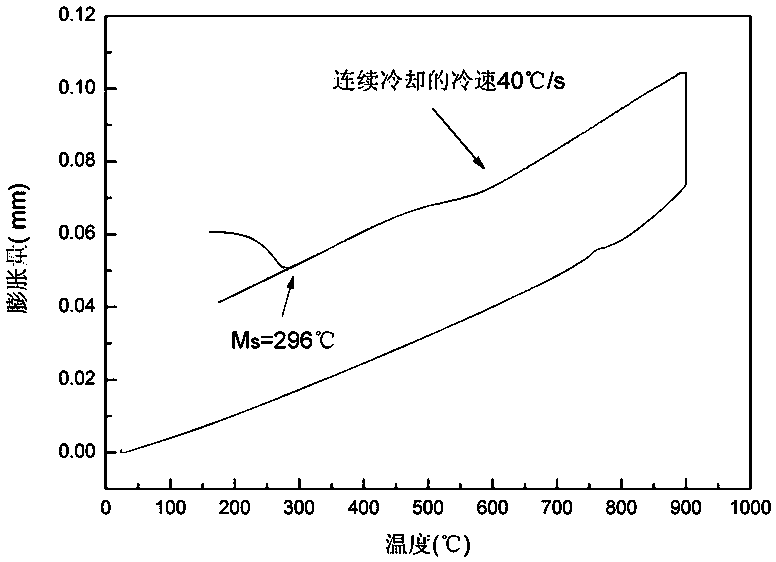
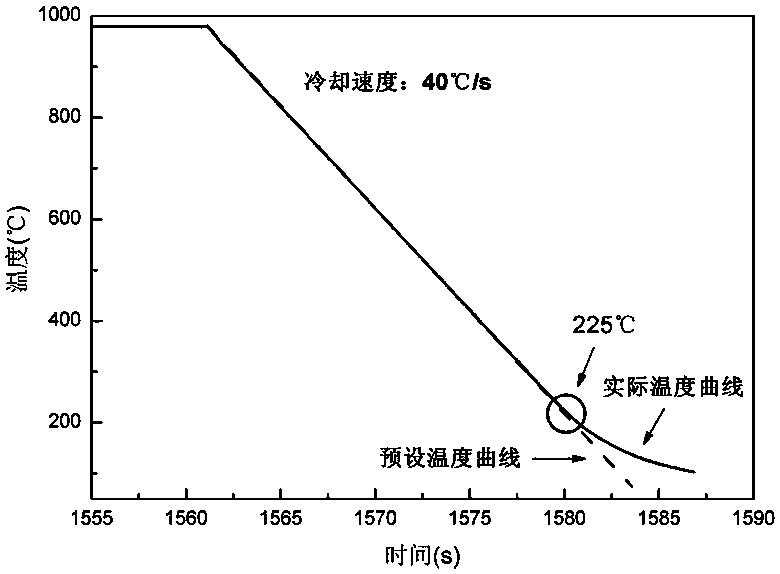
Testing method for auxiliary cooling of thermal simulation test machine
InactiveCN108107069AMeet efficiencyMeet the test requirementsHeating or cooling apparatusInvestigating phase/state changeThermocoupleHot working
The invention relates to a testing method for auxiliary cooling of a thermal simulation test machine, belonging to the field of physical simulation of hot working of metal materials. The testing method comprises the following steps: treating a sample, sleeving the exposed protruding part of a thermocouple with a high-temperature ceramic tube, then welding the positive and negative electrodes of the thermocouple at the central part of a uniform temperature region of the sample by using a spot welder, wherein two welding spots are arranged along a radial isothermal surface at an interval of 1 mm, and then smearing high-temperature cement onto the two welding spots to reinforce the welding spots; installing an auxiliary cooling device in a vacuum chamber of the thermal simulation test machine; starting a control program of the thermal simulation test machine and modifying the control program of the thermal simulation test machine; and opening the vacuum chamber of the thermal simulation test machine, inserting the two ends of the sample into a copper fixture of the thermal simulation test machine tester, and testing the sample by using the modified control program of thermal simulation test machine.
Owner:SHANXI TAIGANG STAINLESS STEEL CO LTD
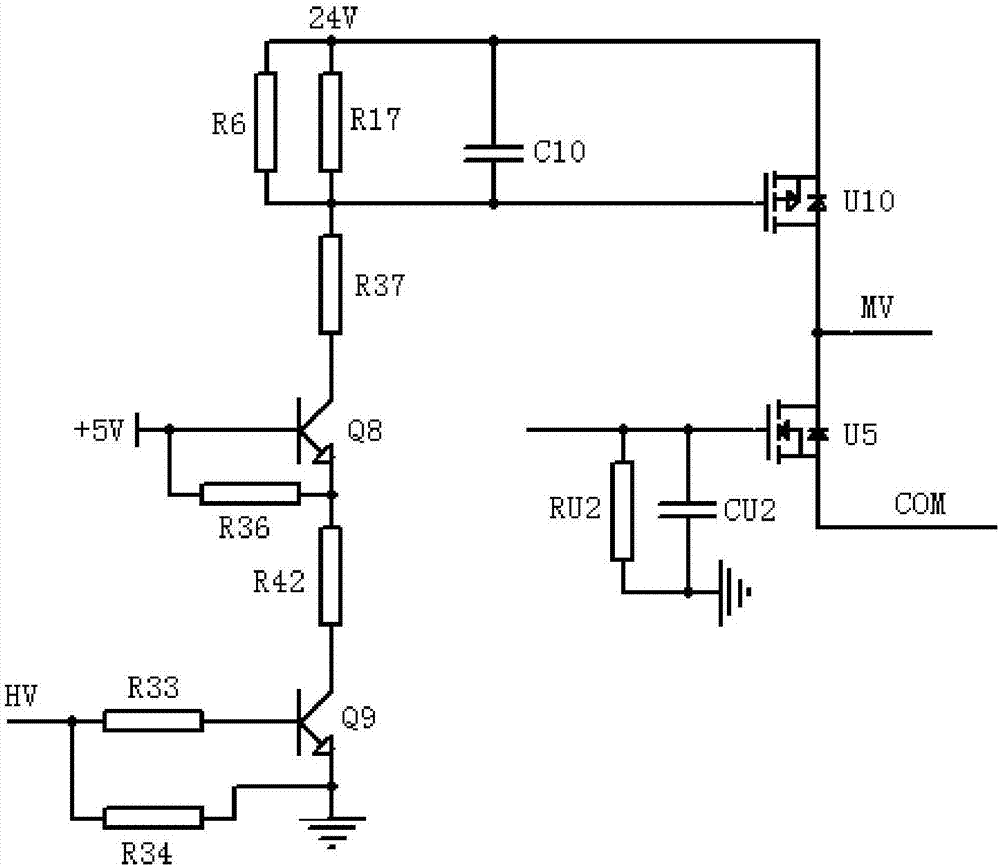
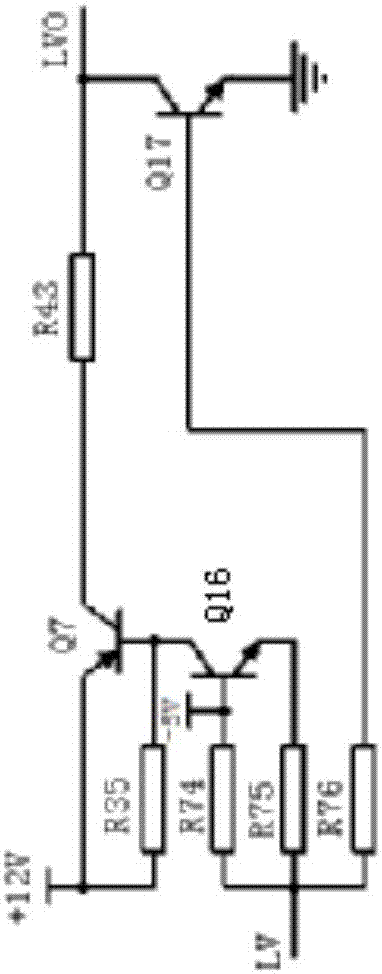
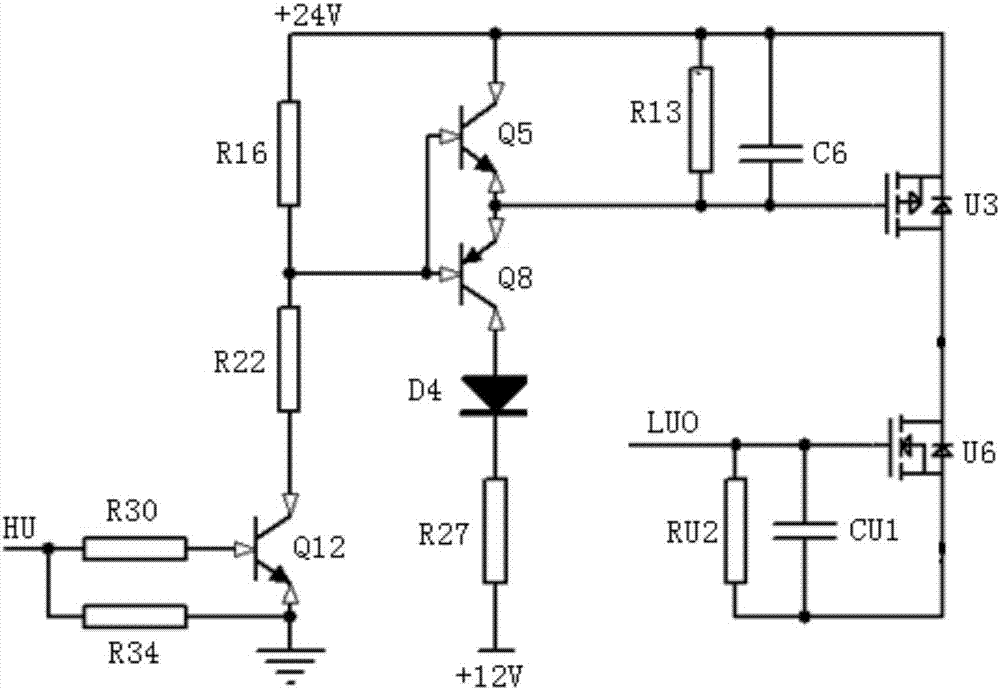
High-efficiency energy-efficient P+N channel drive circuit
PendingCN107959491AMeet efficiencyReduced Power RequirementsElectronic switchingCapacitanceHemt circuits
The invention discloses a high-efficiency energy-efficient P+N channel drive circuit comprising an upper bridge circuit and a lower bridge circuit; the upper bridge circuit comprises a resistor R30, aresistor R34, a NPN type triode Q12, a resistor R22, a resistor R16, a NPN type triode Q5, a PNP type triode Q8, a diode D4, a resistor R27, a resistor R13, a capacitor C6, and a P channel MOS pipe U3; the lower bridge circuit comprises a resistor R43, a resistor R44, a NPN type triode Q18, a resistor R41, a resistor 37, a NPN type triode Q16, a PNP type triode Q17, a resistor R38, a resistor R39, a diode D7, a N channel MOS pipe U6, a capacitor CU1, and a resistor RU2. When the upper bridge circuit is open, the upper bridge open voltage outputted by the upper bridge circuit power supply is charged to the lower bridge circuit for usage, and serves as the open energy of the lower bridge circuit, thus providing high-efficiency energy-efficient effects.
Owner:INTEMOTION TECH WUXI
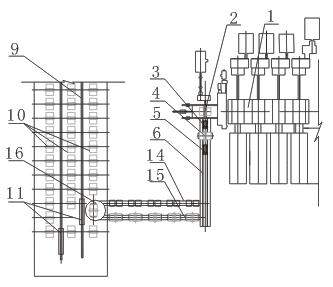
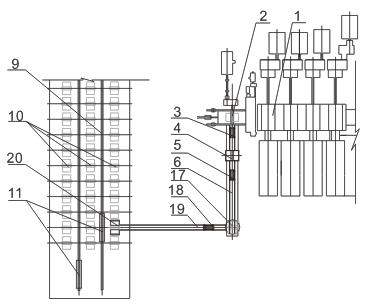
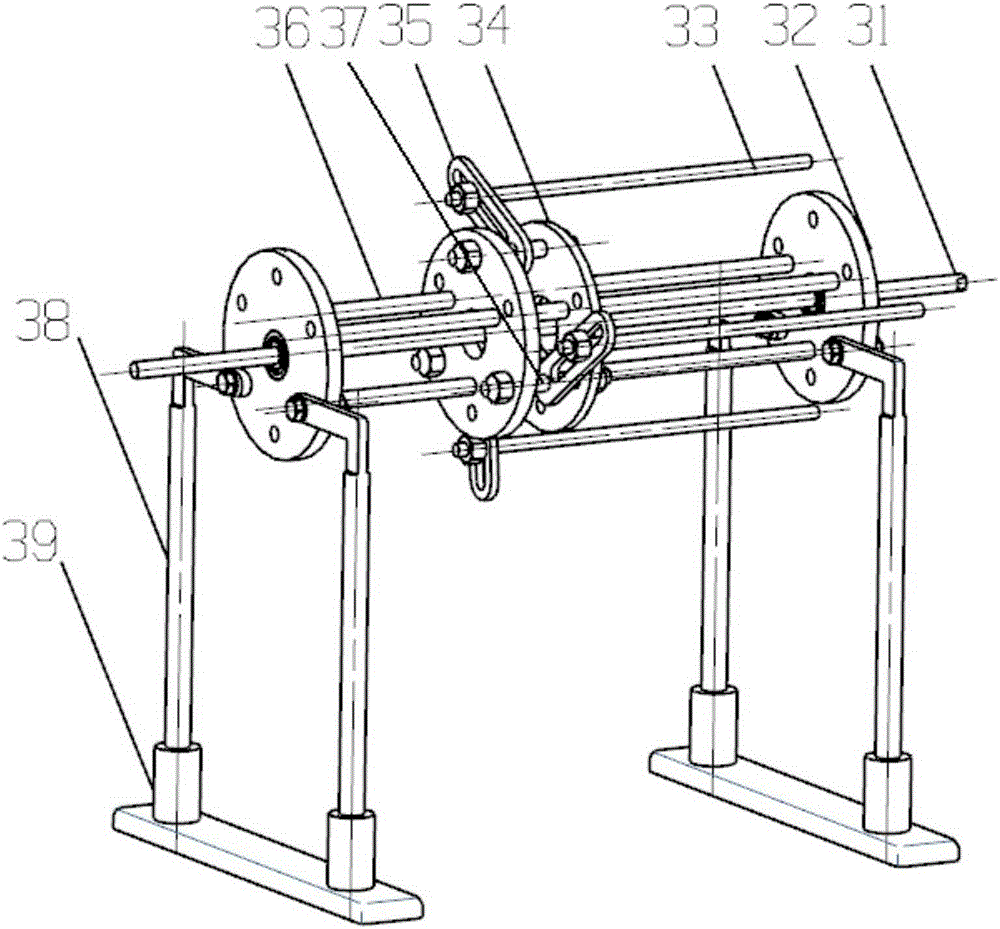
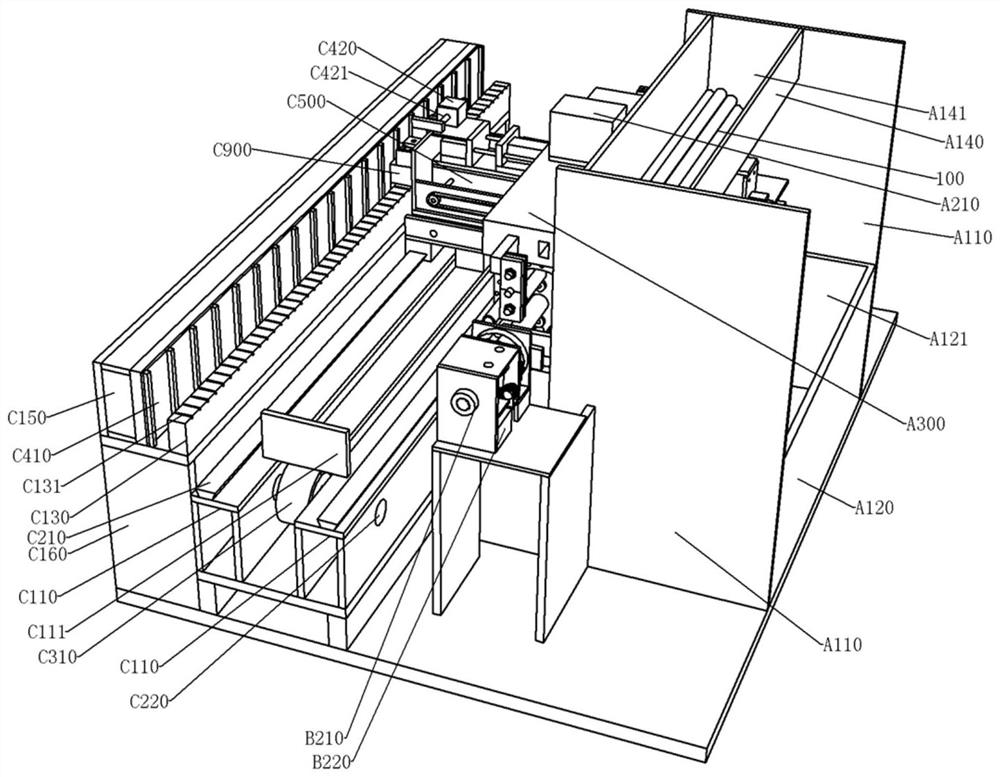
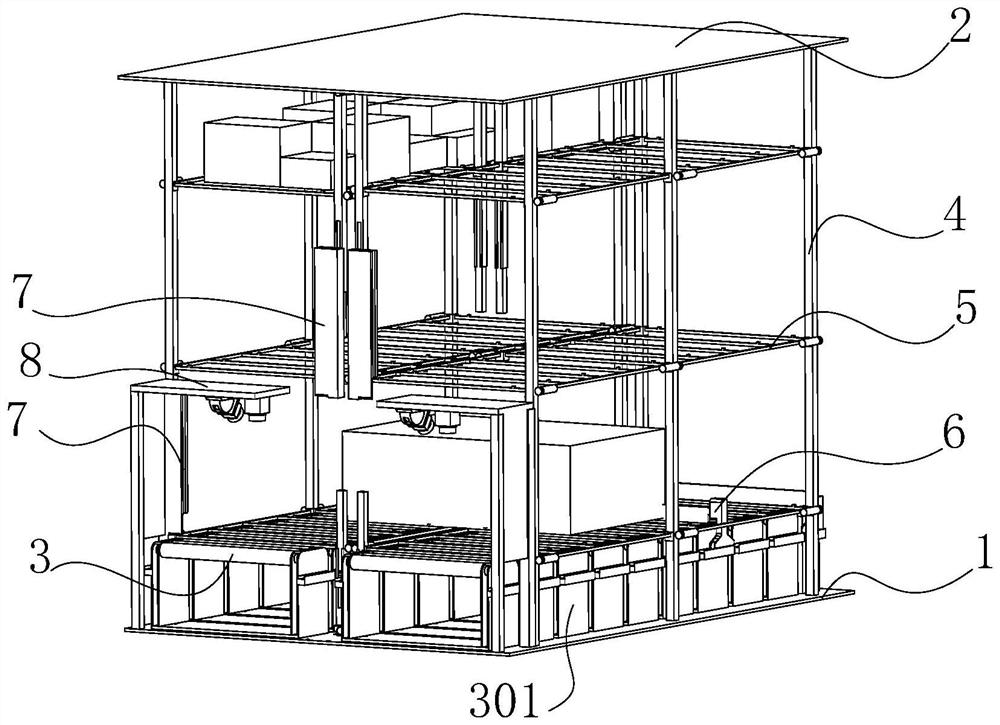
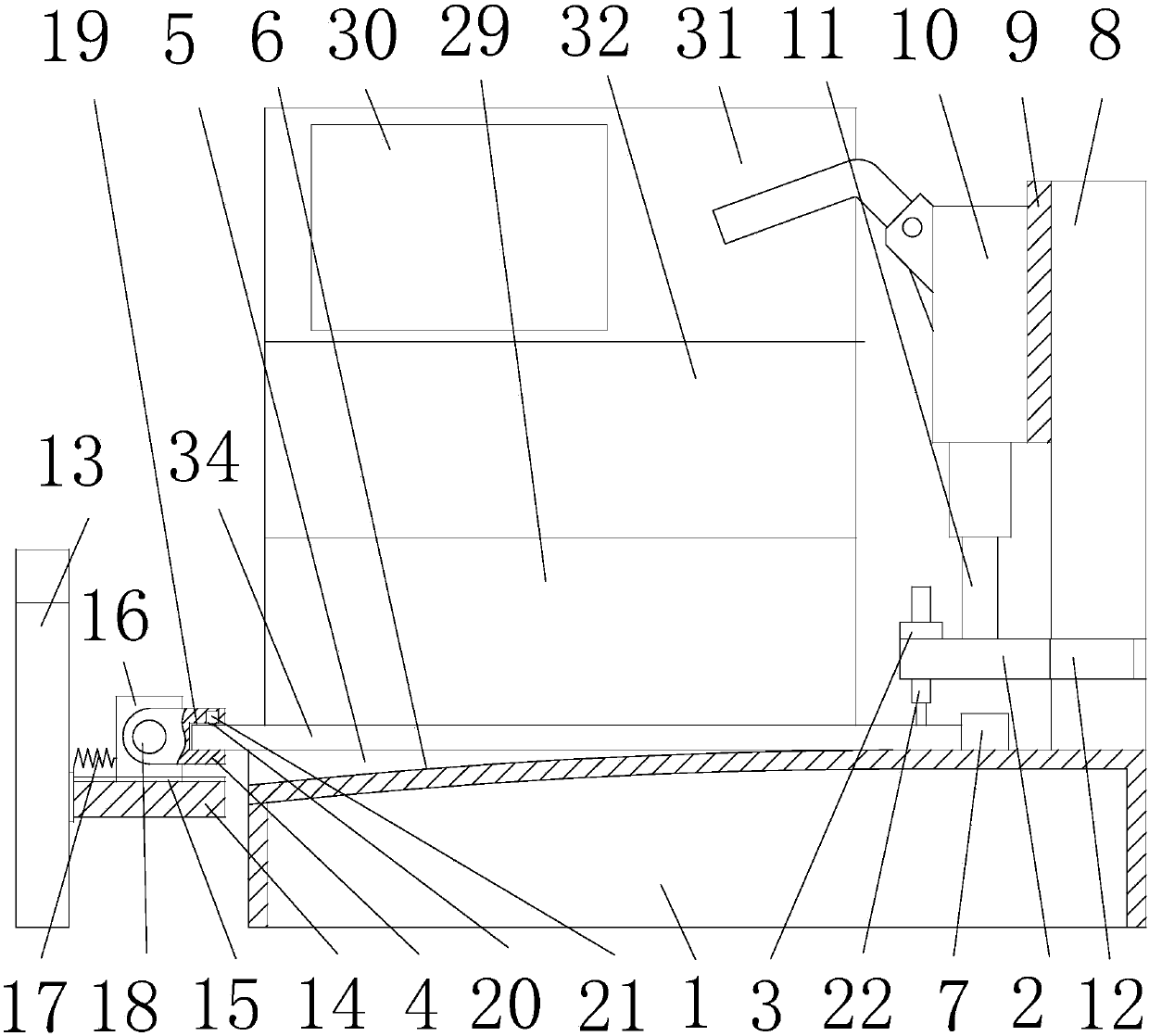
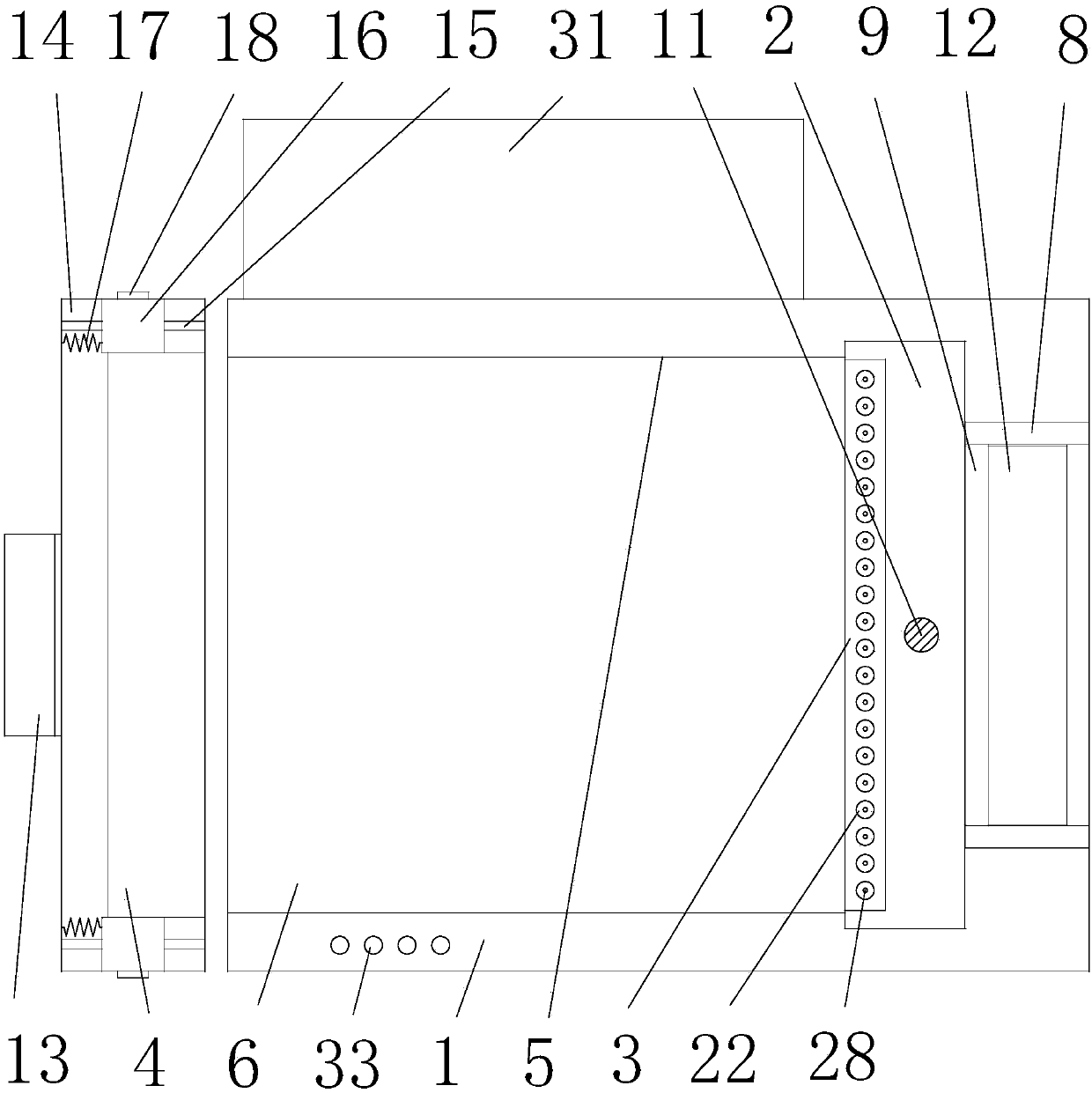
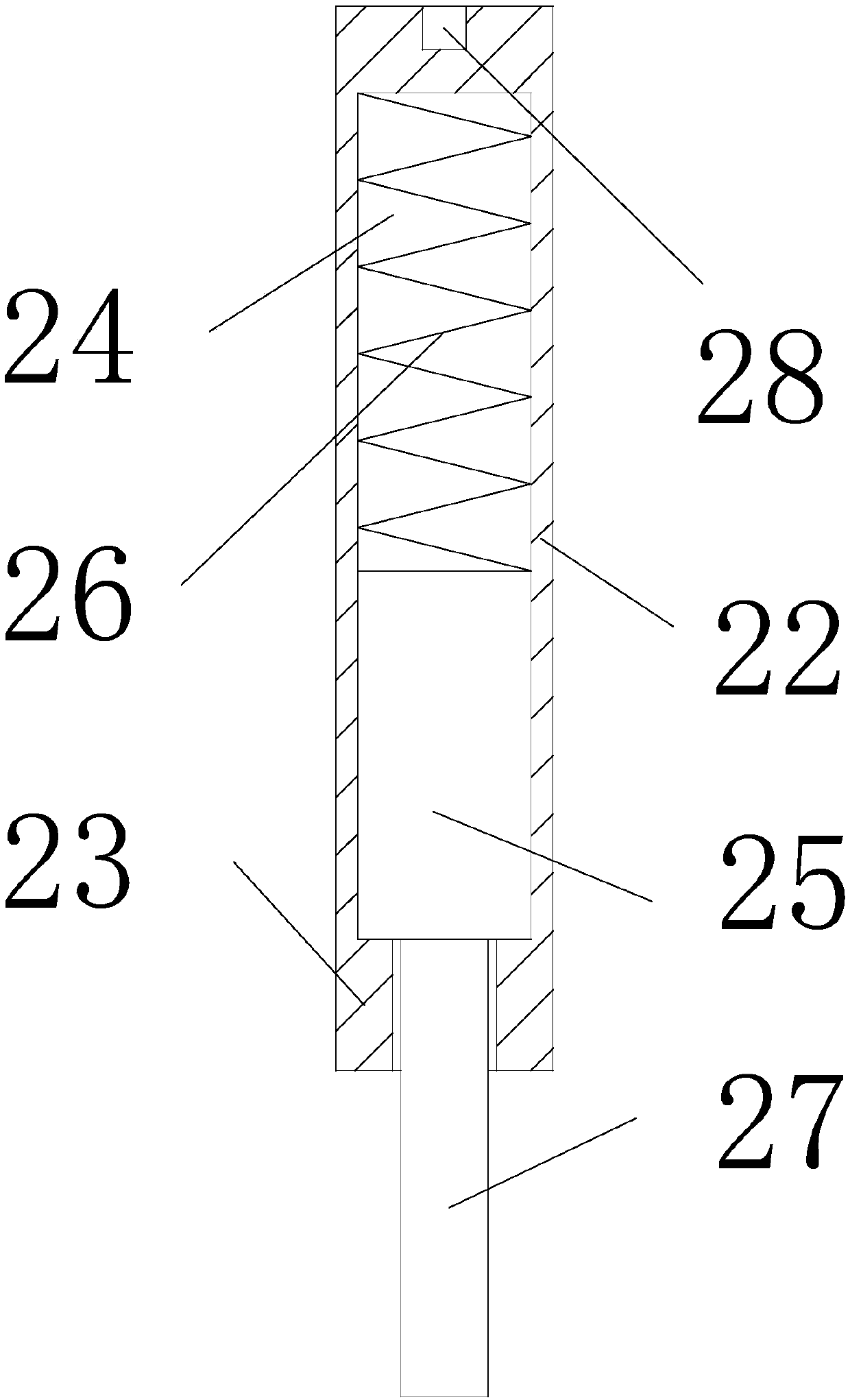
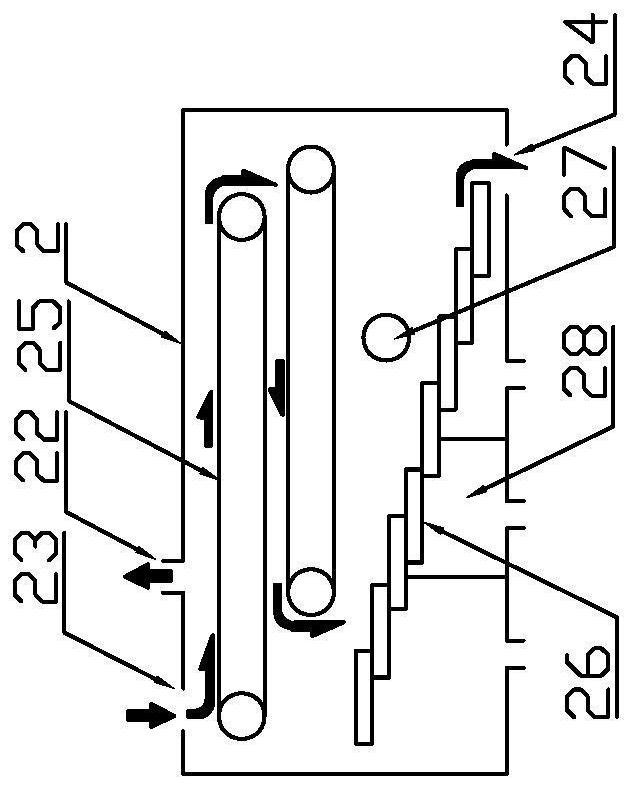
Power module and full-automatic laser pipe cutting machine
ActiveCN112207457ARealize automatic feeding processRealize automated productionMetal working apparatusLaser beam welding apparatusLaser cuttingErbium lasers
The invention discloses a power module and a full-automatic laser pipe cutting machine. The full-automatic laser pipe cutting machine comprises a feeding module, the power module and a cutting module,wherein the feeding module is used for loading pipes to be cut into pipe grooves of a feeding wheel one by one, and then the feeding wheel rotates to enable the pipes to be cut to be sequentially subjected to the procedures of feeding, centering, clamping, section cutting and discharging; the power module is used for driving the pipes at the section cutting procedure to rotate so as to ensure that the whole circles of the pipes are cut off, and intermittently driving the feeding wheel to rotate so as to complete procedure switching; and the cutting module is used for cutting the pipes throughlaser emitted by a laser device, the pipes are relatively fixed in the axial direction, and laser cutting heads move in the axial direction of the pipes and positioning is carried out, so that accurate cutting of the pipes is completed. Automatic feeding can be achieved, and the five procedures of feeding, clamping, axial alignment, section cutting and discharging can be synchronously achieved, so that the production efficiency is improved by at least two times or above. In addition, the mode that the laser device moves while the pipes are fixed is adopted, and the full-automatic laser pipe cutting machine can adapt to pipes with more lengths.
Owner:CHONGQING WANCHONGSHAN INTELLIGENT TECH CO LTD
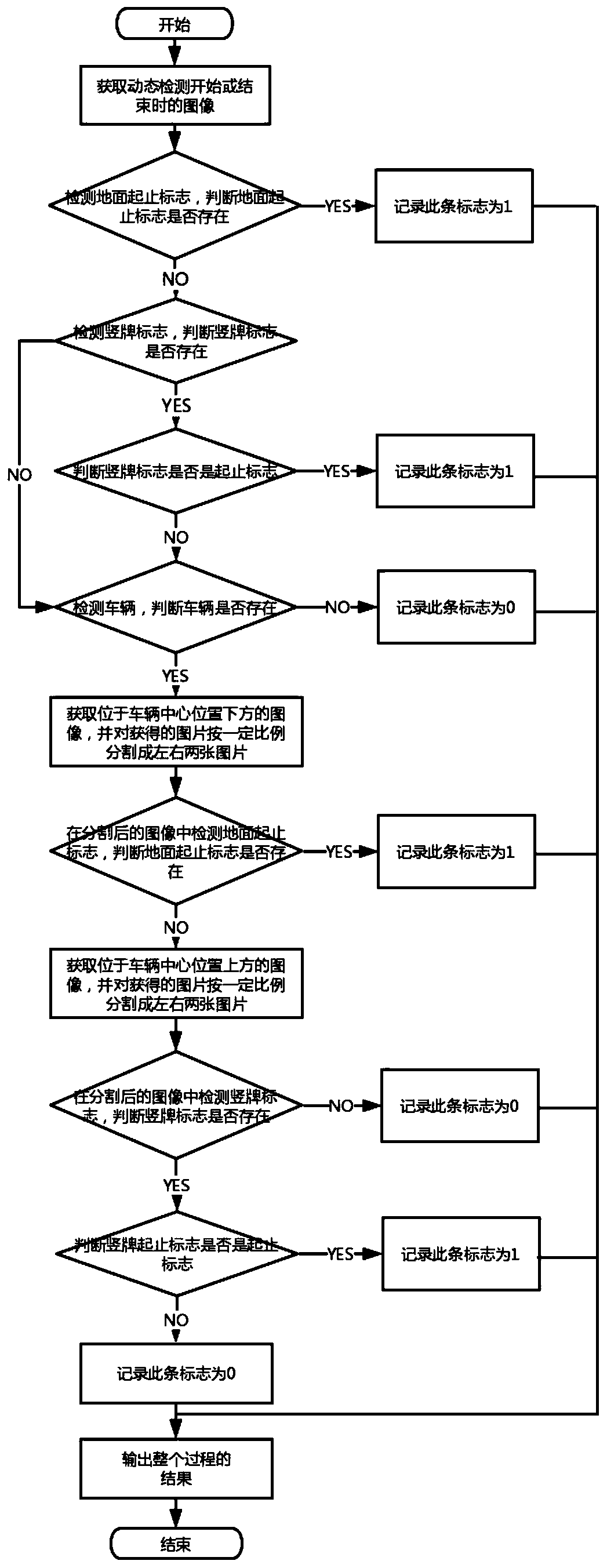
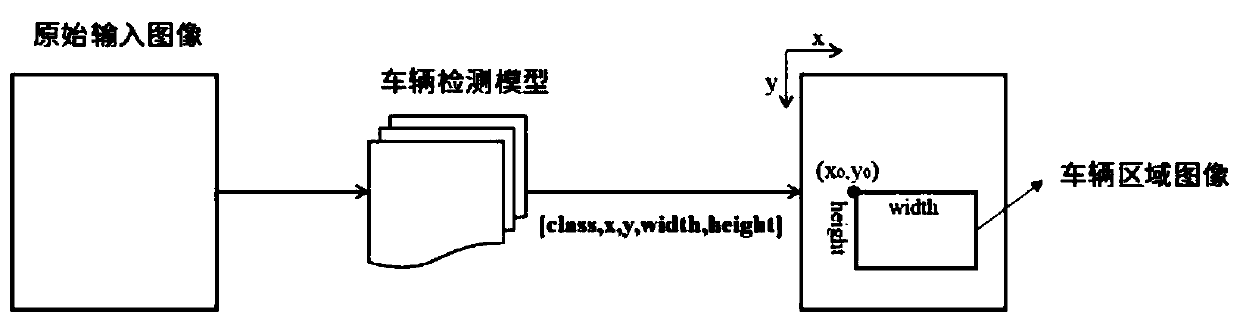
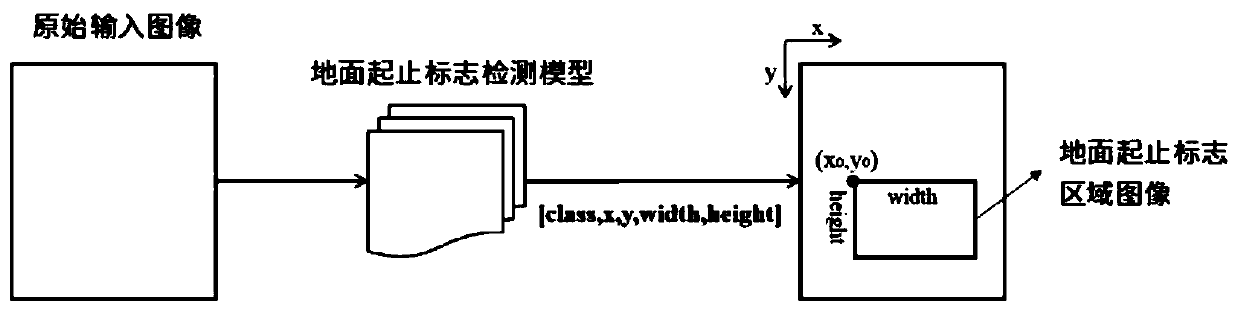
Start-stop sign detection system and method for dynamic detection of vehicle chassis
PendingCN110363761AMeet efficiencyMeet needsImage enhancementImage analysisVehicle dynamicsEngineering
The invention discloses a start-stop sign detection system and a start-stop sign detection method for dynamic detection of a vehicle chassis, and relates to the vehicle detection field. The system andthe method solve the problems that a traditional detection method of a start-stop sign for vehicle chassis dynamic detection is high in labor cost and low in efficiency, the long-time repeated detection operation is easy to cause adverse states such as fatigue, inattention and the like of detection personnel, the detection accuracy is affected and the like in the prior art. According to the technical scheme, a target detection model based on deep learning is used for carrying out start-stop sign detection judgment on images obtained from a server and used for carrying out start-stop sign detection on vehicle dynamic detection start / end. According to the start-stop sign detection system and the start-stop sign detection method for the dynamic detection of the vehicle chassis, whether the start-stop sign exists or not when the chassis starts or ends dynamically is detected automatically, so that the requirements for high efficiency and high accuracy of annual inspection work of the vehicle are met.
Owner:上海眼控科技股份有限公司
Cutting module and full-automatic laser pipe cutting machine
ActiveCN112207456ARealize automatic feeding processRealize automated productionMetal working apparatusLaser beam welding apparatusEngineeringLaser cutting
The invention discloses a cutting module and a full-automatic laser pipe cutting machine. The full-automatic laser pipe cutting machine comprises a feeding module, a power module and the cutting module, wherein the feeding module is used for loading pipes to be cut into pipe grooves of a feeding wheel one by one, and then the feeding wheel rotates to enable the pipes to be cut to be sequentially subjected to the procedures of feeding, centering, clamping, section cutting and discharging; the power module is used for driving the pipes at the section cutting procedure to rotate so as to ensure that the whole circles of the pipes are cut off, and intermittently driving the feeding wheel to rotate so as to complete procedure switching; and the cutting module is used for cutting the pipes through laser emitted by a laser device, the pipes are relatively fixed in the axial direction, and laser cutting heads move in the axial direction of the pipes and positioning is carried out, so that accurate cutting of the pipes is completed. Automatic feeding can be achieved, and the five procedures of feeding, clamping, axial alignment, section cutting and discharging can be synchronously achieved,so that the production efficiency is improved by at least two times or above. In addition, the mode that the laser device moves while the pipes are fixed is adopted, and the full-automatic laser pipecutting machine can adapt to pipes with more lengths.
Owner:CHONGQING WANCHONGSHAN INTELLIGENT TECH CO LTD
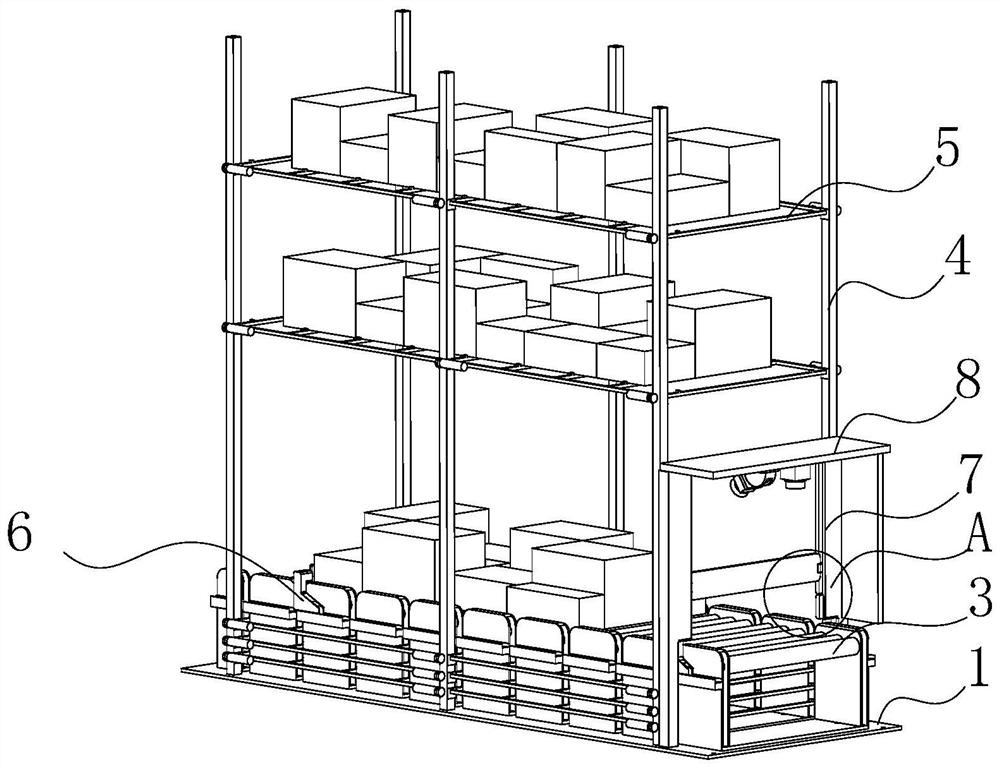
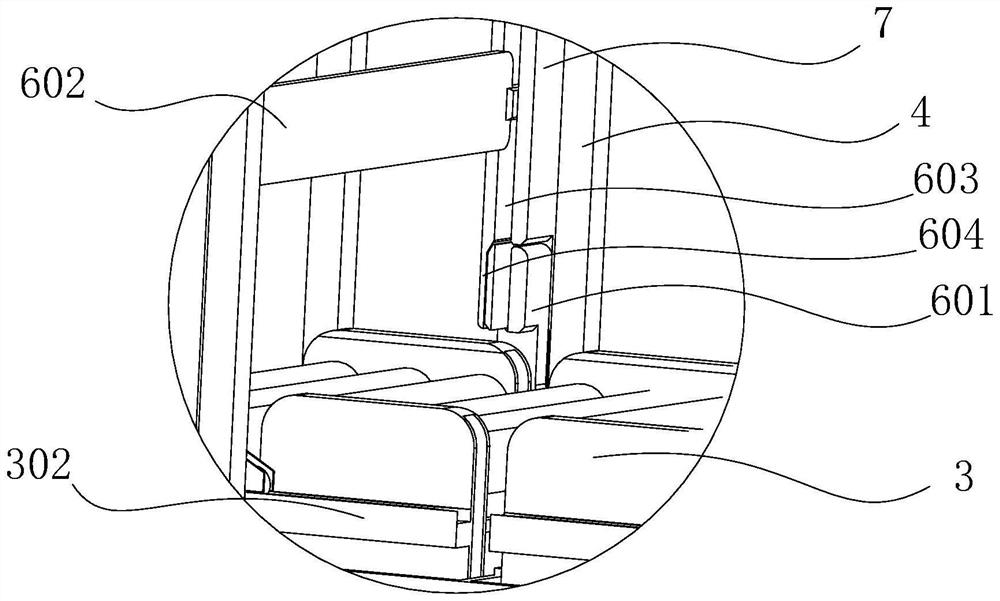
Conveying and anti-stacking assembly of multi-roadway loading and unloading device
ActiveCN114873305AEasy to transportImprove storage efficiencyControl devices for conveyorsLoading/unloadingEngineeringStructural engineering
A conveying and anti-stacking assembly of a multi-roadway loading and unloading device comprises a first base plate, a second base plate and a plurality of conveying roadways used for loading and unloading cargoes, the second base plate is arranged above the first base plate, the conveying roadways are arranged on the first base plate side by side, and the conveying roadways are located between the first base plate and the second base plate. Telescopic stand columns are arranged on the two sides of each conveying roadway, the push plate structures are connected with the conveying roadways in a sliding mode, and the baffle rails are arranged on the telescopic stand columns at the front ends of the conveying roadways. Loading and unloading of goods of different types and sizes are achieved through combination or independent operation of the multiple conveying roadways, and high universality is achieved; and meanwhile, conveying and anti-stacking work of goods of different sizes can be met through the push plate structure and the baffle plate track.
Owner:SOUTHWEST JIAOTONG UNIV
LED flexible light bar tester and testing method
ActiveCN108107334AHigh lighting test efficiencyReduce false positive rateIndividual semiconductor device testingElectricityTest efficiency
The invention aims at providing an LED flexible light bar tester and a testing method. The LED flexible light bar tester comprises a testing device, a stock, a light bar electric connection lifting device arranged at the upper front part of the stock and provided with a lifting plate, a transverse fixing bar provided with a plurality of transversely-arranged pressing electric connection ejection pins and connected with the rear end of the lifting plate, and a light bar bending device provided with a light bar clamp and arranged at the rear side of the rear end of the stock. The LED flexible light bar tester is high in lighting test efficiency and low in misjudgment rate.
Owner:ZHEJIANG KAIYAO LIGHTING
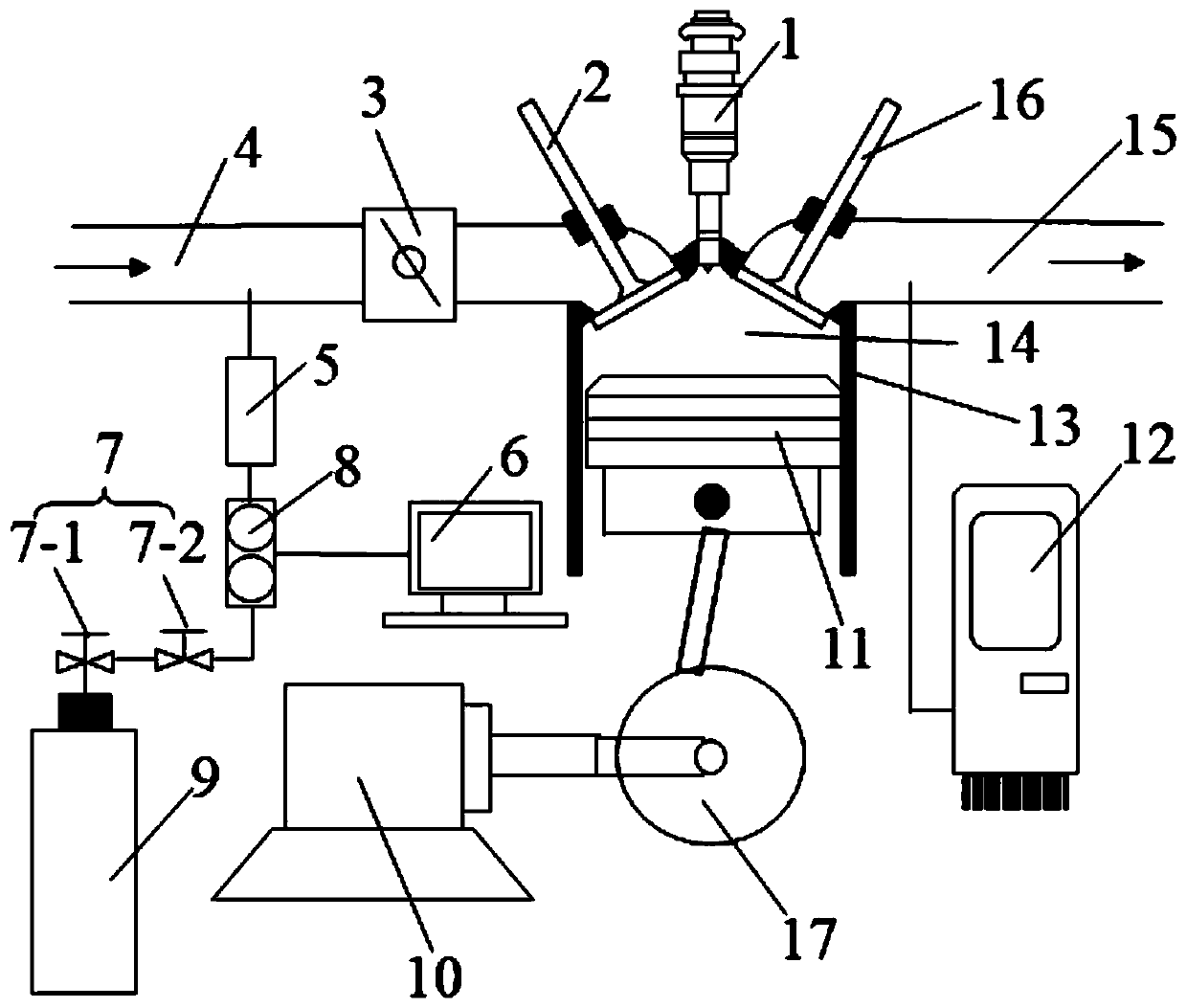
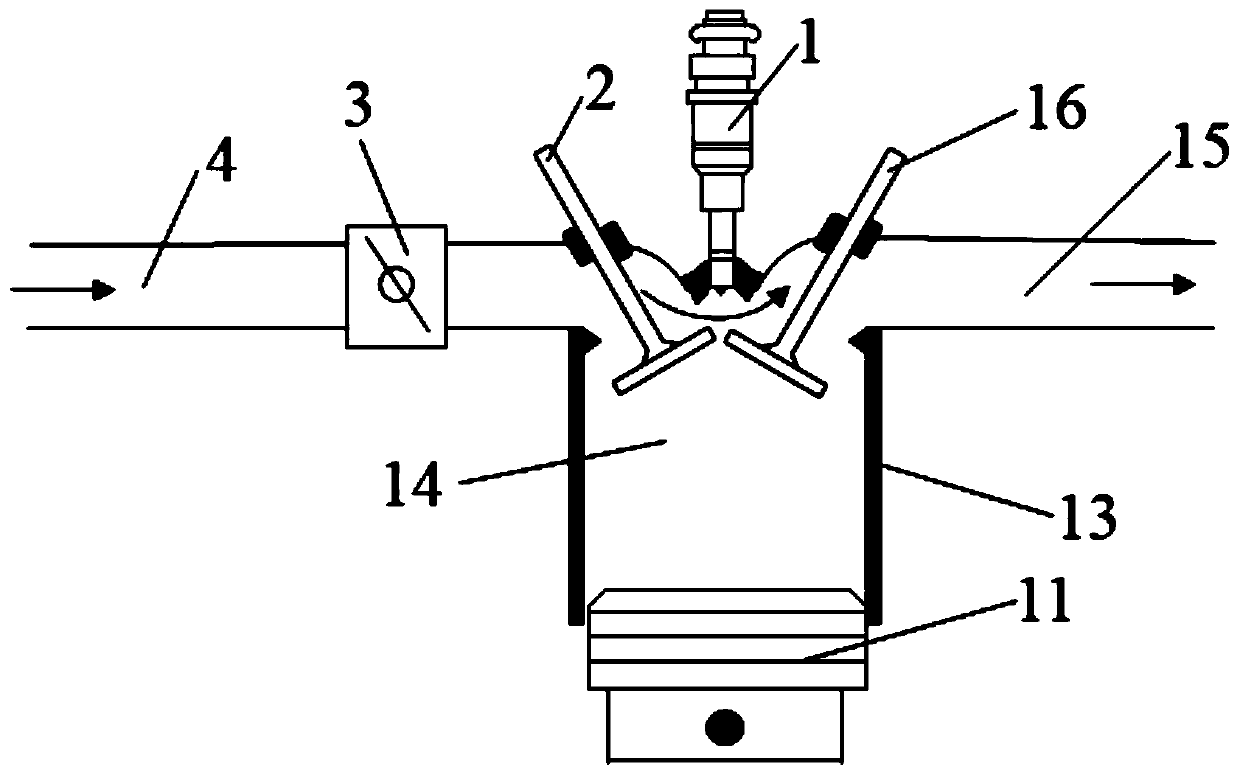
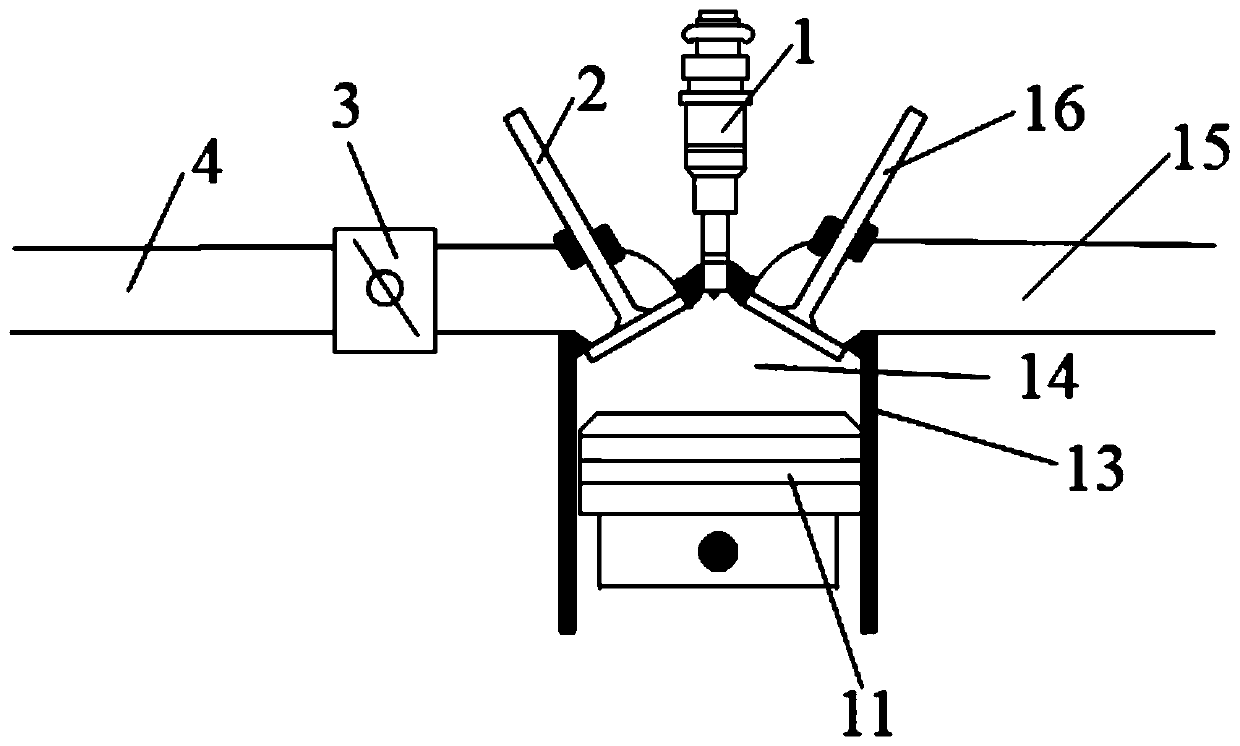
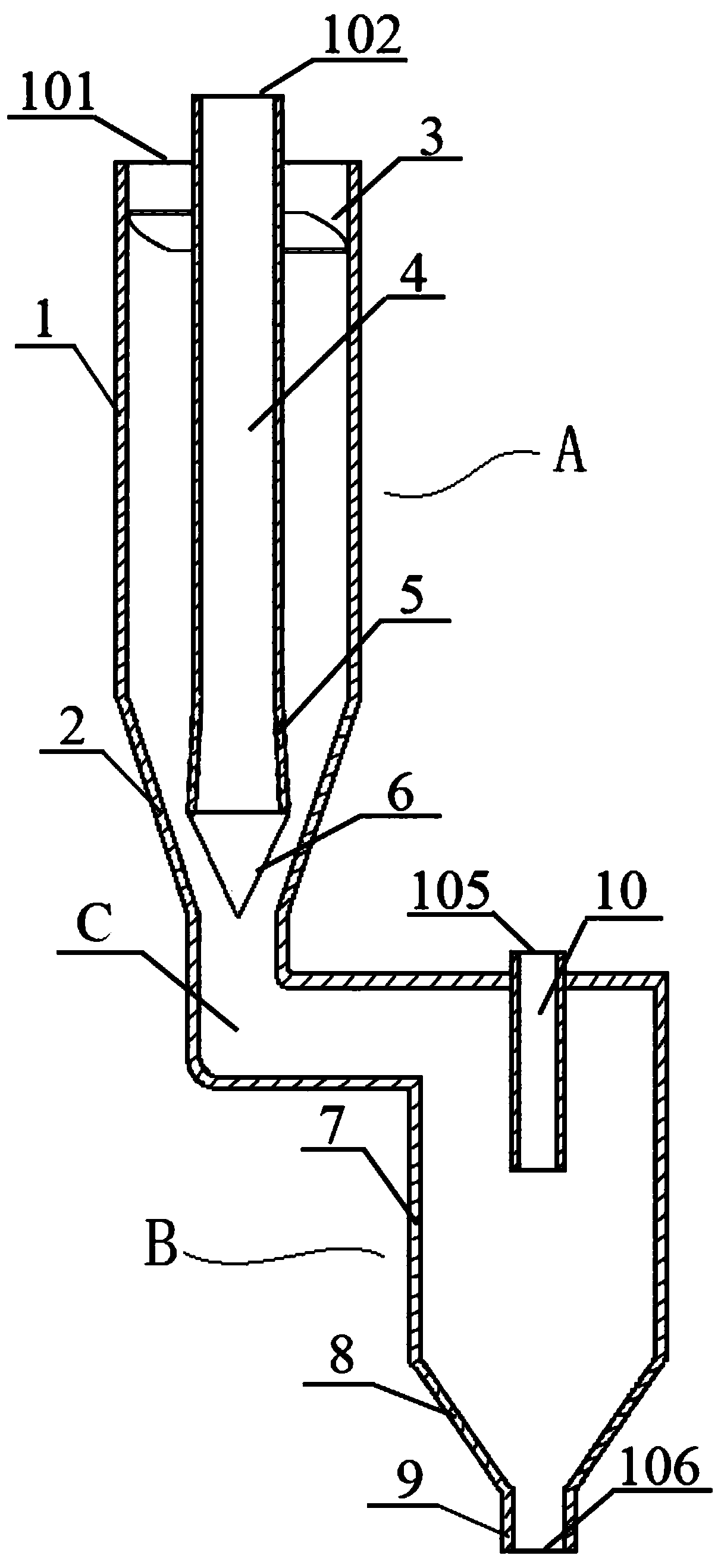
Test system and method for capture rate and scavenging efficiency of two-stroke engine
InactiveCN111140350AAccurately measure and calculate capture ratesAccurately measure and calculate efficiencyMachines/enginesEngine componentsCombustion chamberExhaust valve
The invention discloses a test system for capture rate and scavenging efficiency of a two-stroke engine. The test system acts on a cylinder, wherein the top of the cylinder is provided with a fuel injector, the two sides of the top of a combustion chamber of the cylinder are respectively provided with an air inlet channel and an air outlet channel, tracer gas is introduced into the air inlet channel, and the air outlet channel is connected with a tester to detect the amount of the tracer gas. The invention further discloses a test method. The test method comprises the steps that under the state that an air inlet valve and an air outlet valve are opened at the same time, a part of tracer gas directly enters the air outlet channel from the air inlet channel and is not combusted, the other part of tracer gas is left in the combustion chamber, and when the combustion stage is reached, the tracer gas left in the combustion chamber is completely combusted; and the average volume concentration of the tracer gas in the air outlet channel of the two-stroke engine within the set measurement time is measured by using the tester, so that the capture rate and scavenging efficiency of the two-stroke engine are determined. The system and the method is simple to operate, easy to implement and high in measurement precision.
Owner:TIANJIN UNIV
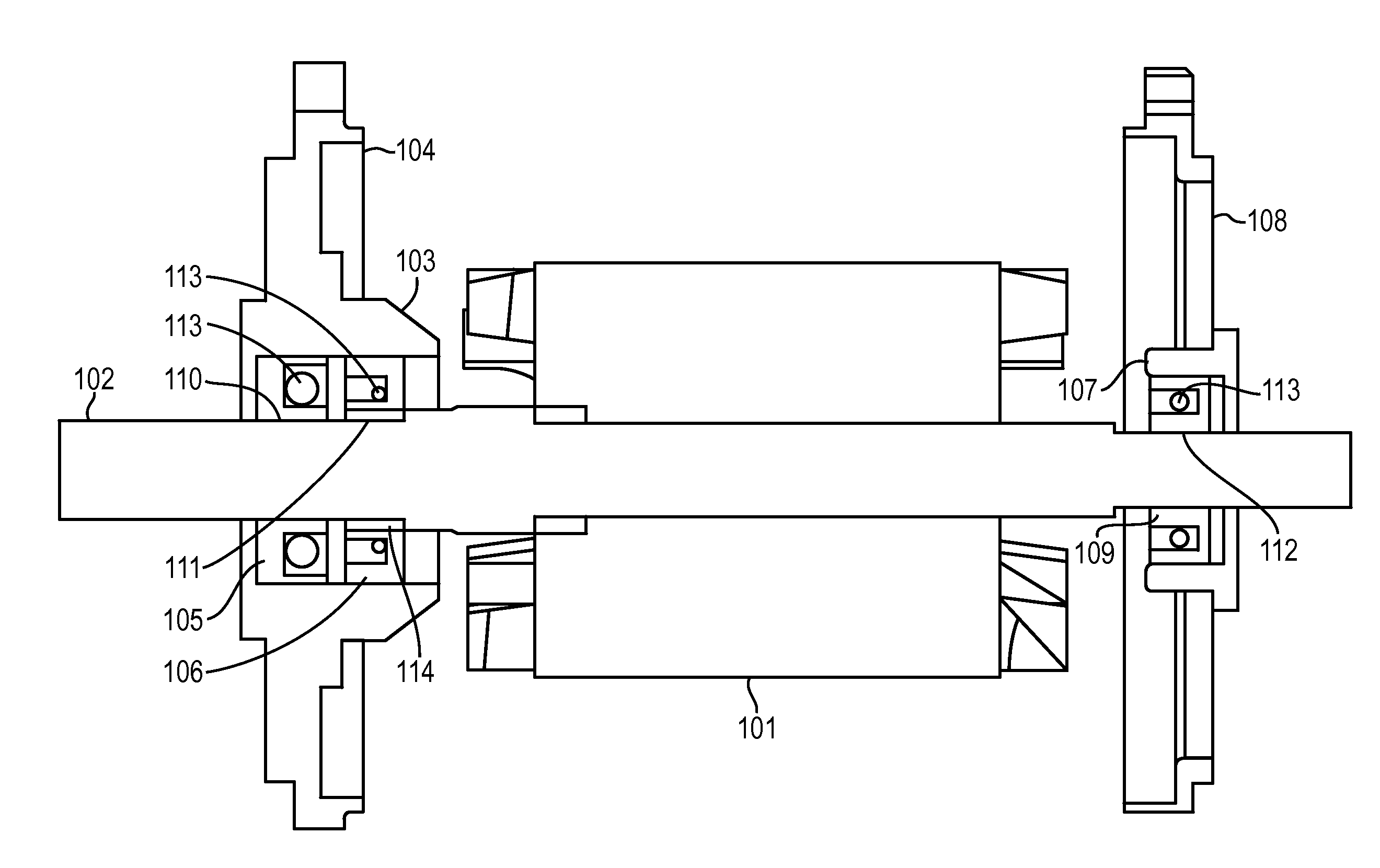
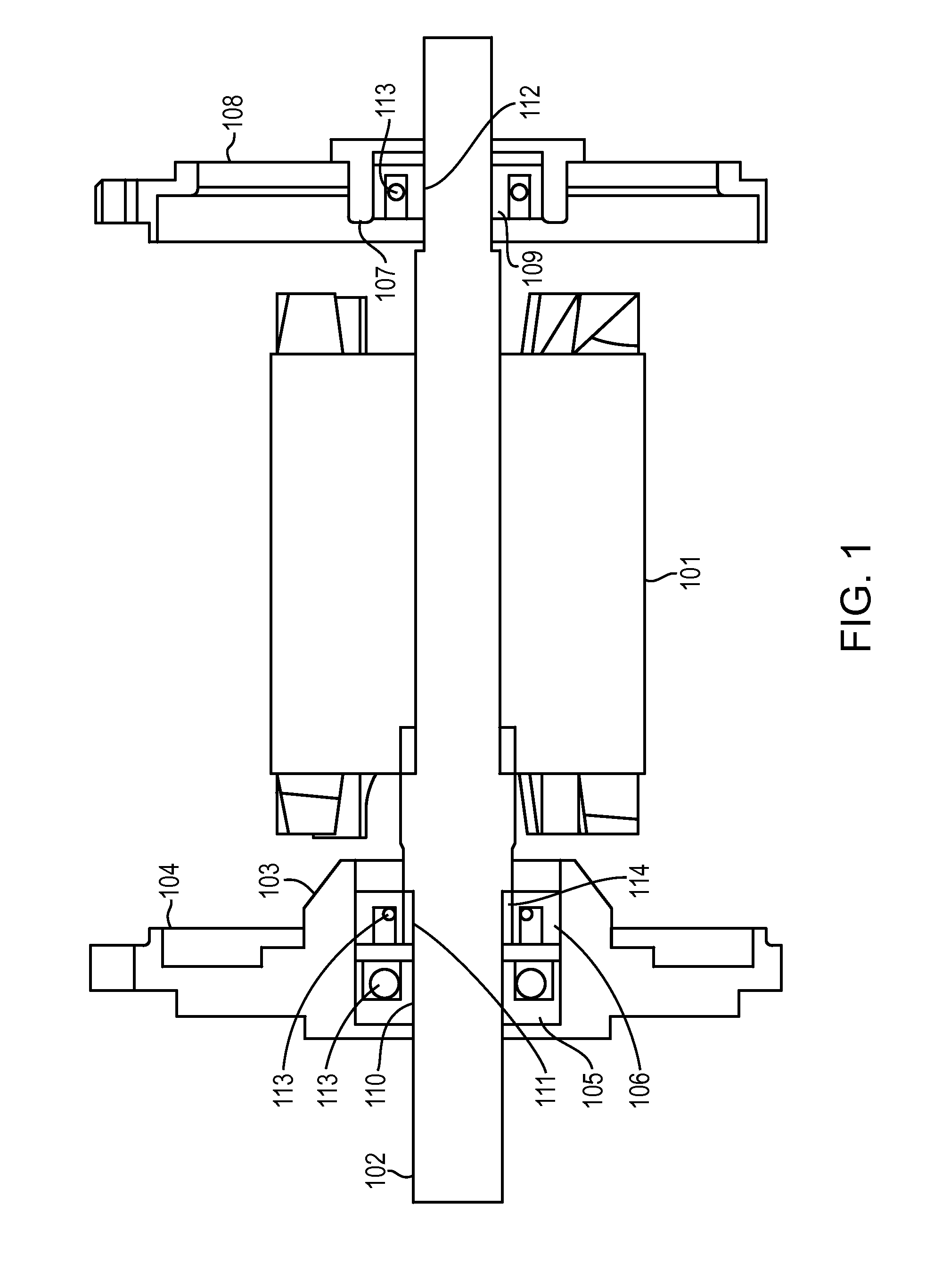
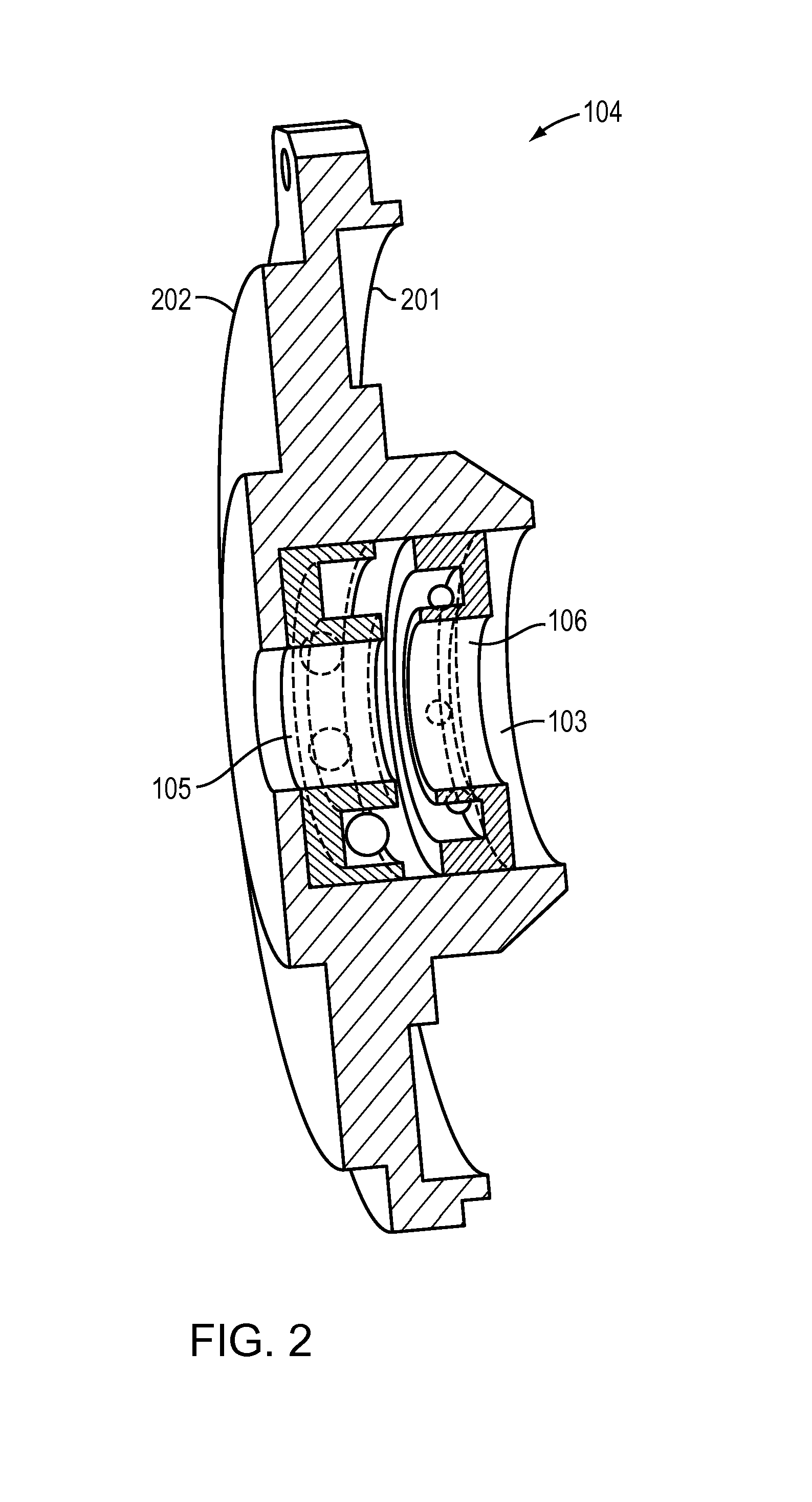
Bearing implementation for a rotating electrical device
InactiveUS20140285071A1Reduce eliminateCost associated with down timeRolling contact bearingsBearing assemblyBall bearingEngineering
In one embodiment, an electric motor includes at least three bearings. The ball bearing utilized in the three bearings may be sized based on benchmark surface areas associated with the ball bearing utilized in a conventional electric motor having two bearings. Moreover, a technique may be implemented to reduce the diameter at a point on the shaft where a backup or second bearing makes contact with the shaft. When the motor begins to operate, for example, at a first time, the at least three bearings together handle a the load coming through the motor. When the front-most bearing degrades to a predetermined point or fails, for example, at a second time, the load transitions from the front most bearing to the second or backup bearing in the front plate.
Owner:FXQ ENG GRP
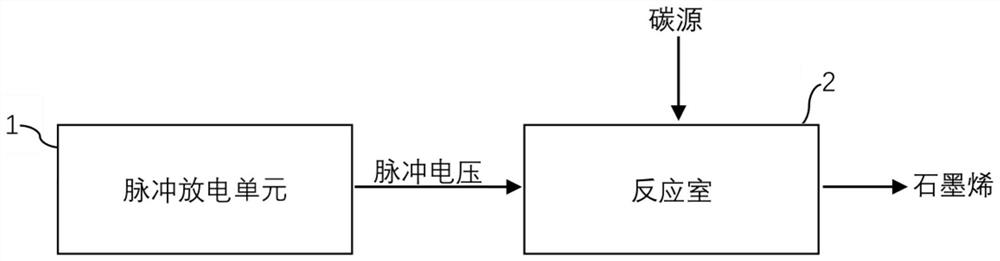
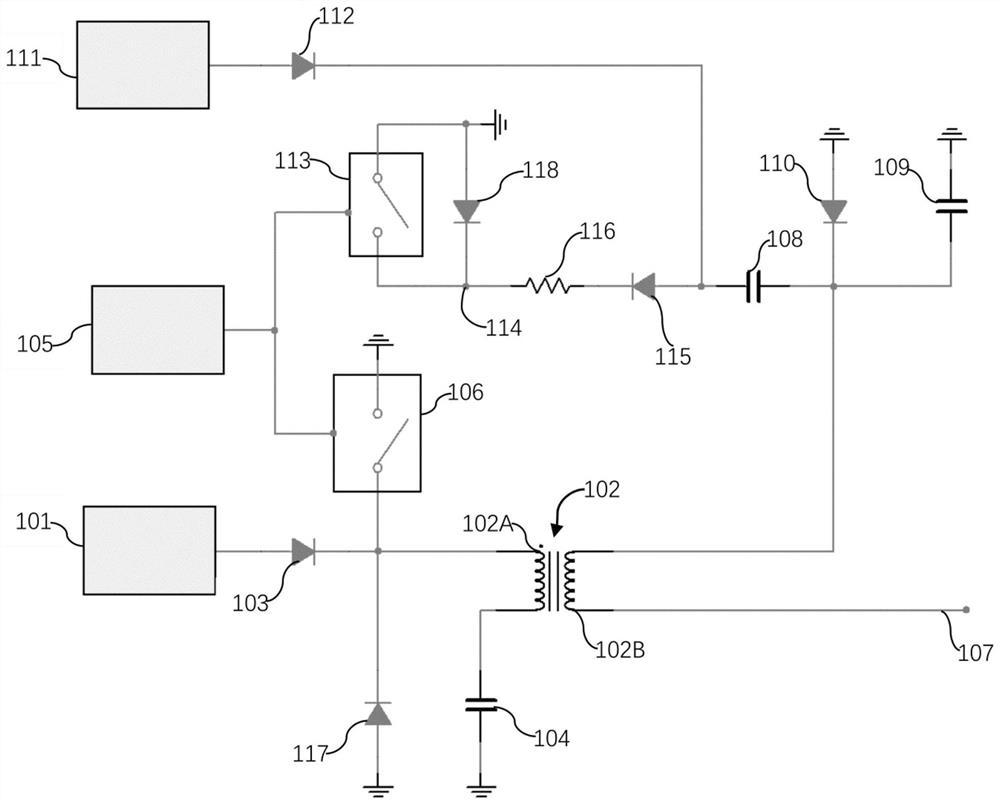
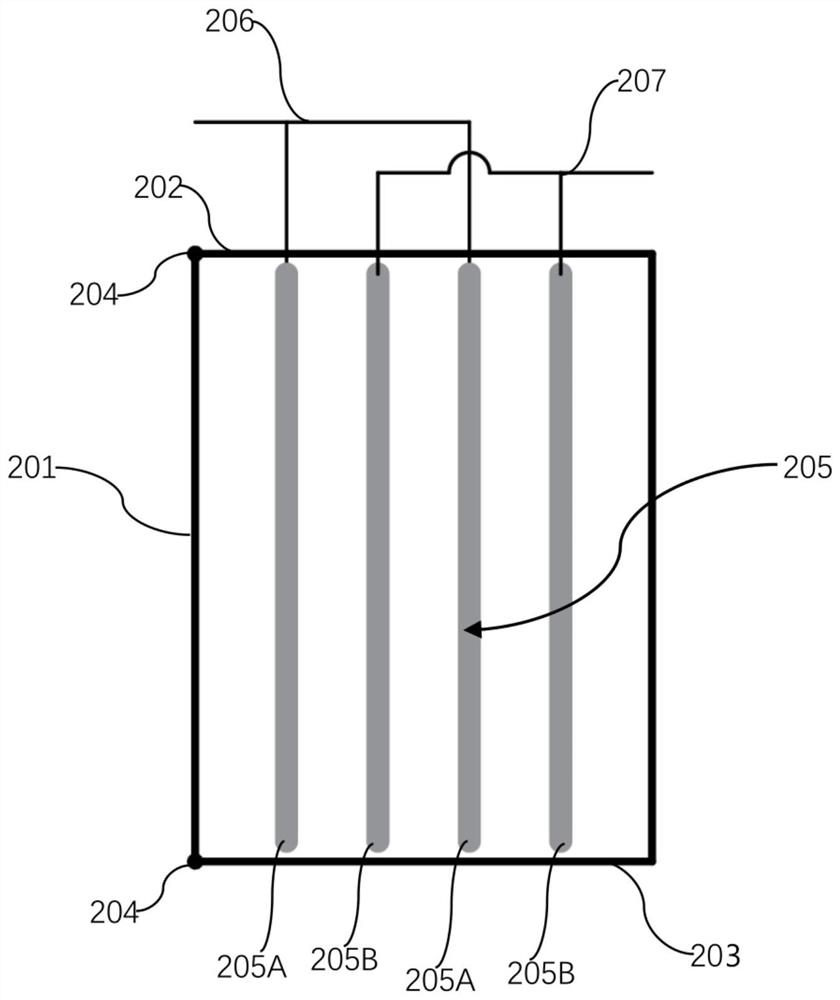
Device and method for producing graphene by electric shock method
ActiveCN112678808AAccurate quality controlQuality improvementGrapheneLow voltageElectrical connection
The invention discloses a device for producing graphene by an electric shock method, wherein the device comprises a rapid discharge unit and a reaction chamber, and the rapid discharge unit is electrically connected with the reaction chamber; the quick discharge unit comprises a high-voltage power supply circuit, a voltage transformation circuit, a protection circuit, a pulse generation circuit and a low-voltage power supply circuit; the output end of the high-voltage power supply circuit is electrically connected with a primary winding of the voltage transformation circuit, and a secondary winding of the voltage transformation circuit is electrically connected with the reaction chamber; the protection circuit is electrically connected with the secondary winding of the voltage transformation circuit; one end of the pulse generation circuit is electrically connected with the protection circuit, and the other end of the pulse generation circuit is electrically connected with the primary winding of the voltage transformation circuit; and one end, electrically connected with the protection circuit, of the pulse generation circuit is electrically connected with the output end of the low-voltage power supply circuit. The invention aims to provide the device and the method for producing the graphene by the electric shock method with low cost, high quality and high efficiency.
Owner:GUANGDONG UNIV OF TECH
Closed negative pressure solid waste oxygen control pyrolysis device
The invention discloses a closed negative pressure solid waste oxygen control pyrolysis device. The device comprises a dryer, a pyrolysis combustor, a low-heating-value gas combustor, a flue gas heat exchanger, a condensation dehumidifier, a hot air circulating fan, a pyrolysis gas exhaust fan and a main fan. A pyrolysis gas outlet of the pyrolysis combustor is connected with an air inlet of the low-heating-value gas combustor through the pyrolysis gas exhaust fan, a pyrolysis gas conveying pipe and the main fan, and a pyrolysis gas conveying pipe at the air inlet end of the main fan is communicated with a hot air circulating pipe through a bypass pipeline; a flue gas outlet of the low-heating-value gas combustor is connected with a flue gas inlet of the flue gas heat exchanger; and a material hoister is arranged in a material conveying sealing area. The device can meet the requirements of efficiency, environmental protection and economy. The solid waste reduction efficiency can be improved by improving the combustion ratio. The working environment is greatly improved, flue gas waste heat is recycled through the flue gas heat exchanger and used for front-section drying of solid waste, and the heat value is fully utilized.
Owner:FOSHAN HUAJIEYUAN THERMAL ENERGY & ENVIRONMENTAL ENG TECH CO
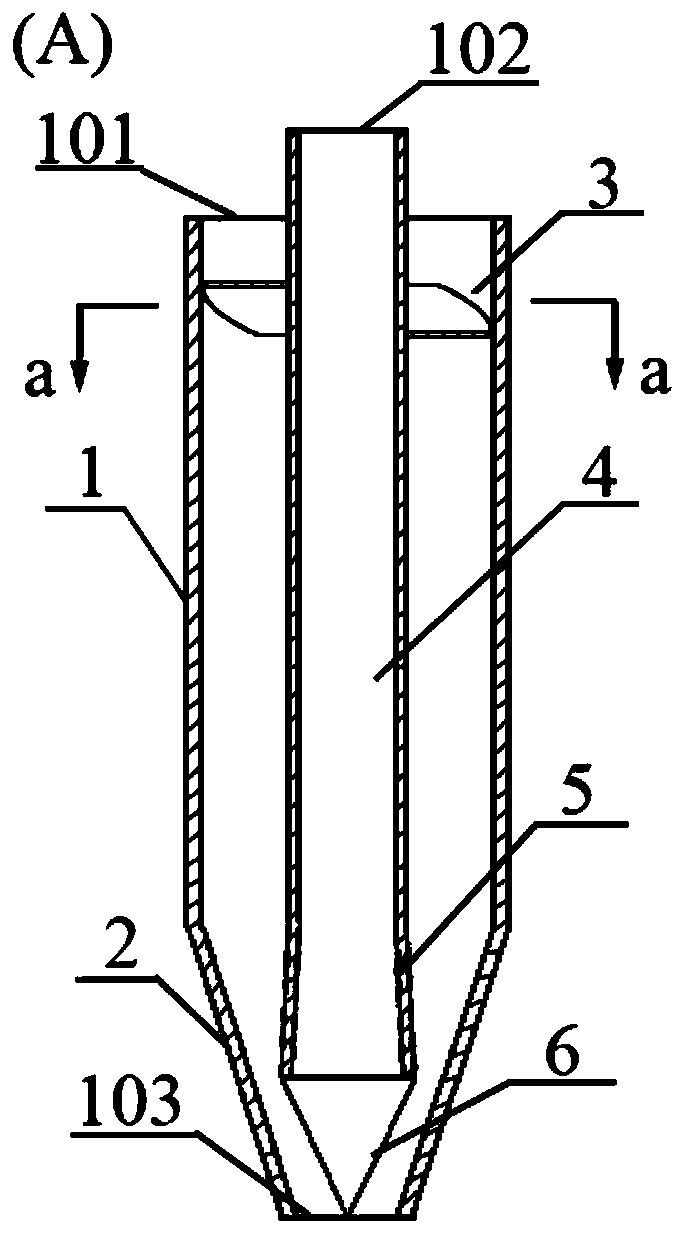
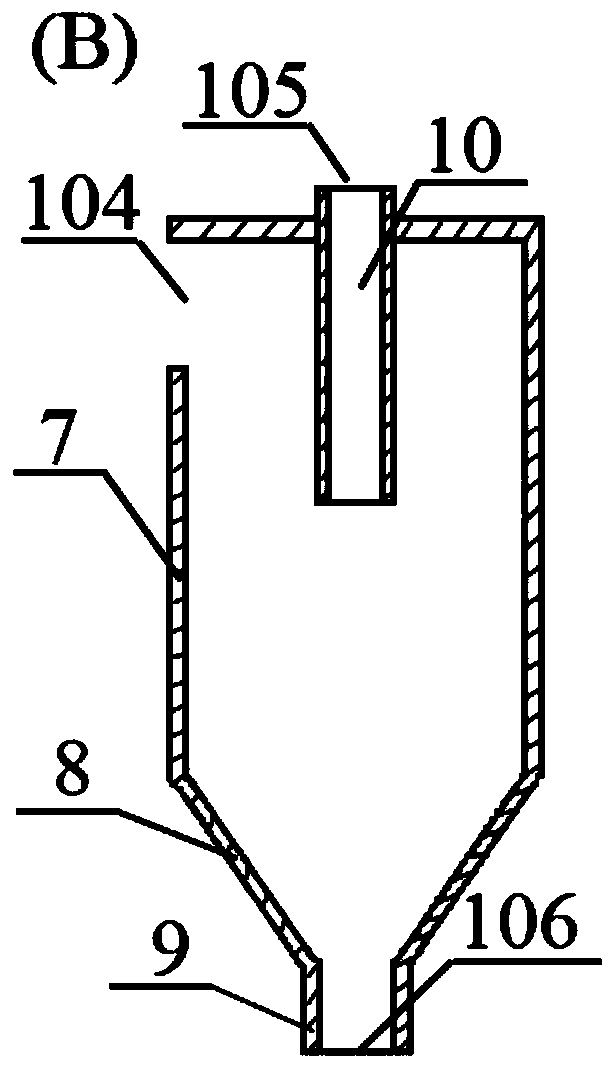
Guide blade type high-pressure cyclone separator
The invention discloses a guide blade type high-pressure cyclone separator with a flow guiding filtration function. A separation unit shell body is composed of an upper column-shaped cylinder body and a lower cone body, flow guide blades serving as cyclone parts are of arc surface structures with a certain thickness and are fixed between an air exhausting pipe and the column-shaped cylinder body, and every two adjacent blades form a spiral flow passage; gaps are reserved between the tops of the blades and the top of the column-shaped cylinder body, the air exhausting pipe penetrates through the top axis of the column-shaped cylinder body and extends downward to the bottom of the cylinder body, a trumpet-shaped filtration component with a special hole form is additionally arranged, a narrow port of the trumpet-shaped filtration component is welded with the tail end of the air exhausting pipe, and the wide port end of the trumpet-shaped filtration component is fixedly connected with a flow guiding cone. A separation unit is communicated with a second-level separation unit through a bent connection pipe, and the second-level separation unit is composed of a second-level air exhausting pipe, a dust discharging pipe and the shell body. Through sleeving arrangement of the filtration component and the flow guiding cone, backmixing particles carried by inward rotation flow are removed, the tail swinging phenomenon occurring on the tail end of the inward rotation flow is inhibited, remaining airflow with dust is guided in entering the second-level separation unit, the airflow stopping phenomenon caused by a vortex at an inlet of the cone body is avoided, and the separation purity is improved.
Owner:XIHUA UNIV
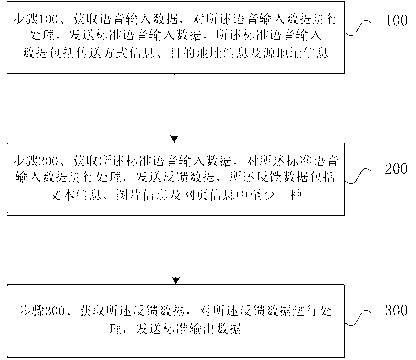
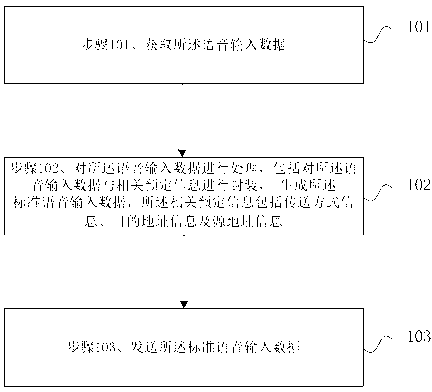
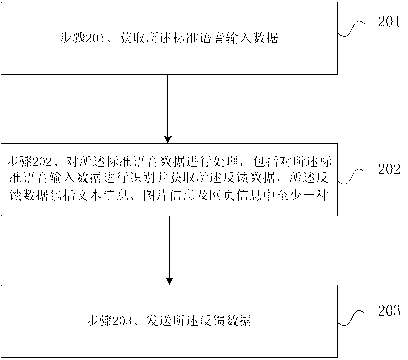
Voice input data processing method and system based on cloud computing
InactiveCN103294440AEasy to useImprove work efficiencySound input/outputTransmissionComputer moduleComputer terminal
The invention provides a voice input data processing method and system based on cloud computing. The method comprises the following steps: step 100, acquiring and processing voice input data, sending standard voice input data which comprises transmission mode information, destination address information and source address information; step 200, acquiring and processing the standard voice input data, sending feedback data which comprises at least one of text information, picture information and webpage information; and step 300, acquiring and processing the feedback data, and sending standard output data. The system comprises a terminal input module, a cloud computing server cluster module and a terminal feedback module. According to the processing method and system, the voice input data is processed through the cloud computing mode, so that the problem that occupied memory space and processor resources are overlarge in a processing procedure is solved, and the working efficiency and convenience are improved.
Owner:上海酷宇通讯技术有限公司
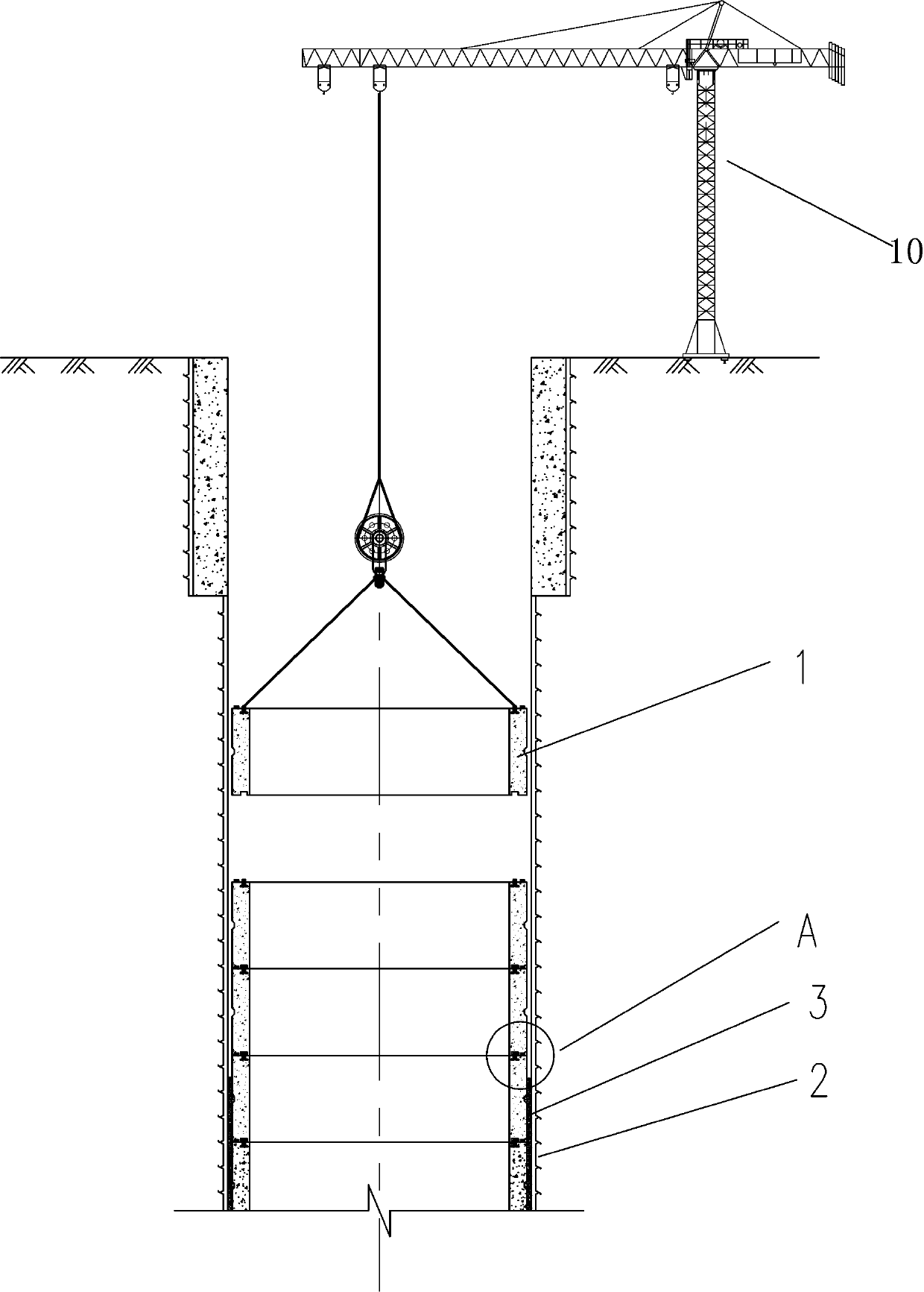
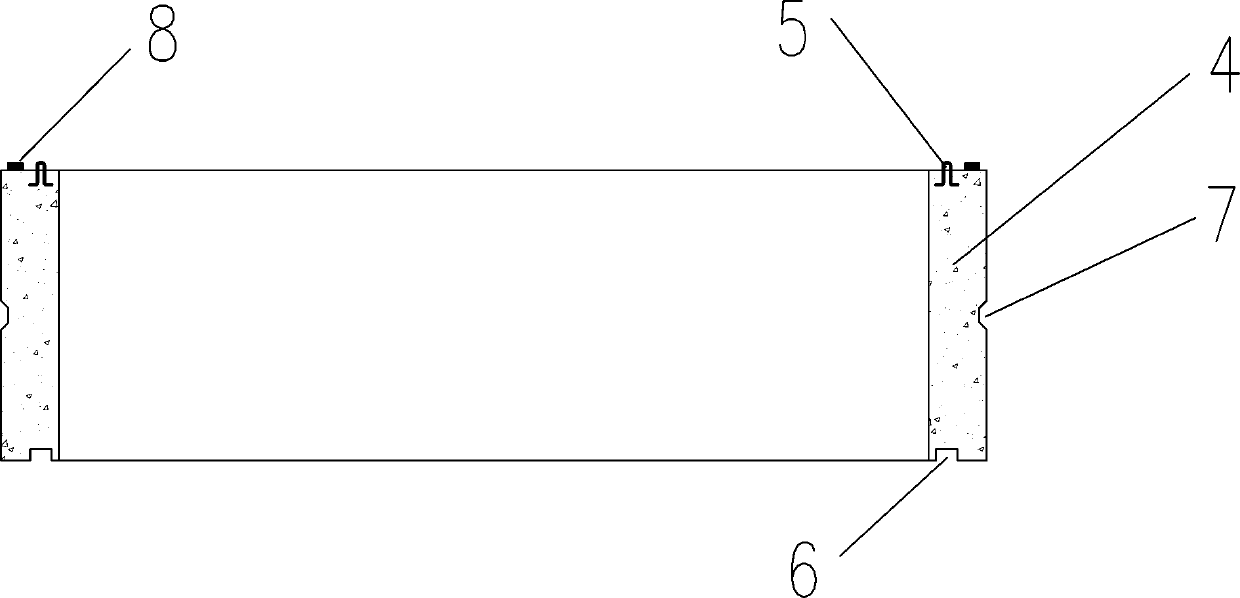
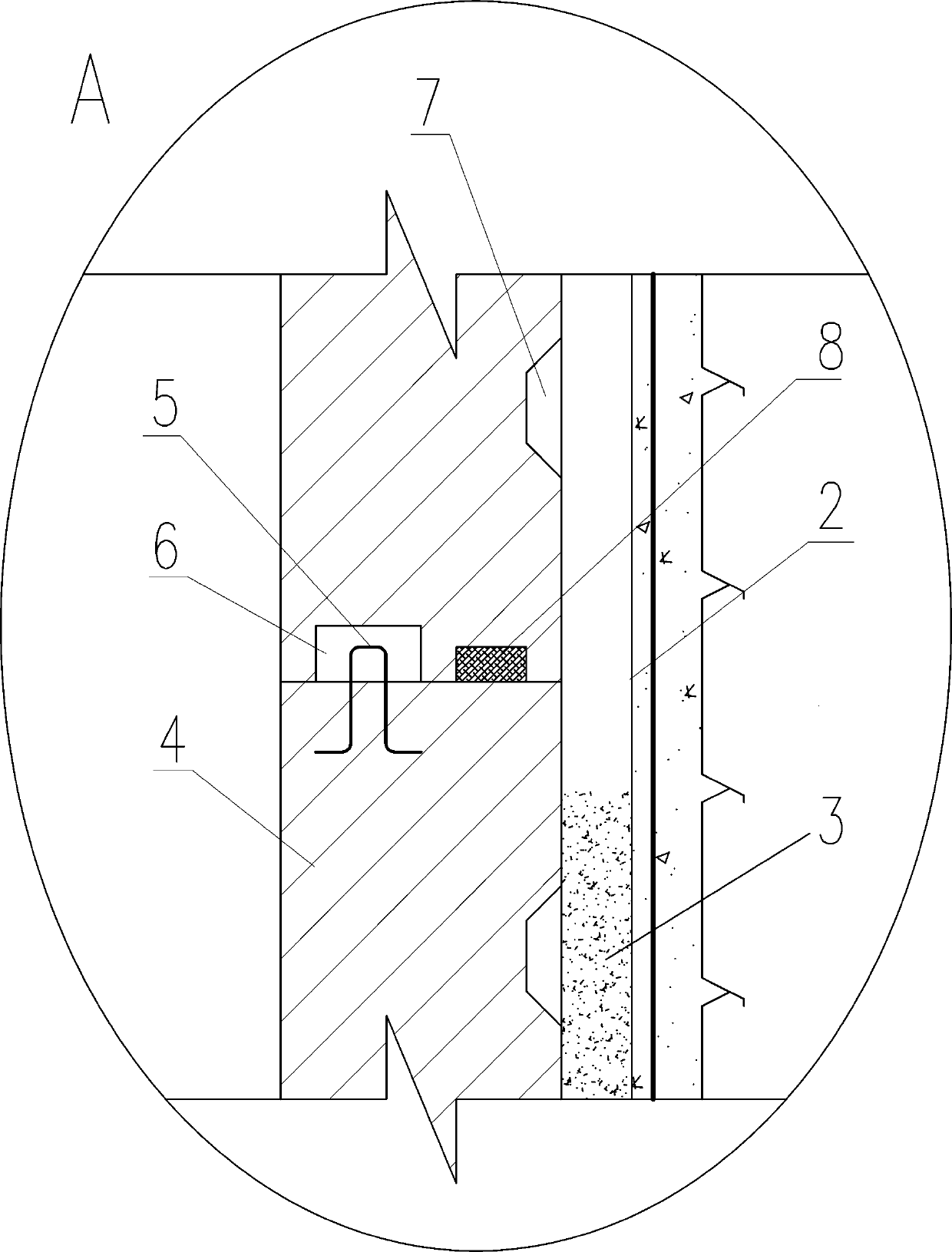
Vertical shaft tunnel concrete lining structure and method
InactiveCN110094206ACheap manufacturingSave on installation costsShaft liningConstruction aggregateSafety risk
The invention discloses a vertical shaft tunnel concrete lining structure and a method. The vertical shaft tunnel concrete lining structure comprises prefabricated pipe sections which are assembled section by section to form a pipe-shaped structure, and a concrete layer is arranged between the pipe-shaped structure and the surrounding rock surface and connects the prefabricated pipe sections withthe surrounding rock surface into a whole. According to the vertical shaft tunnel concrete lining structure and the method, the working efficiency of a concrete lining can be improved, the construction safety risk is reduced, and the separation quality problem of lining concrete aggregate is eliminated.
Owner:SOUTHERN POWER GRID PEAK LOAD & FREQUENCY REGULATION GENERATING CO LTD
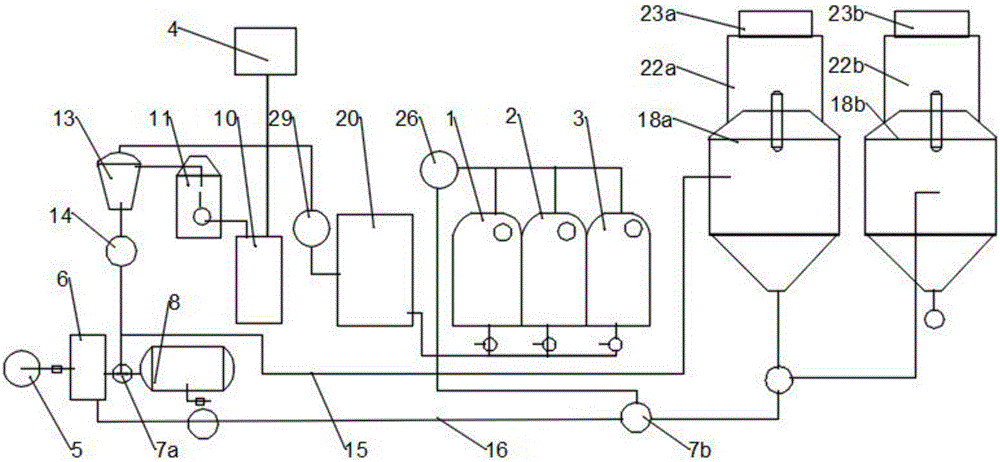
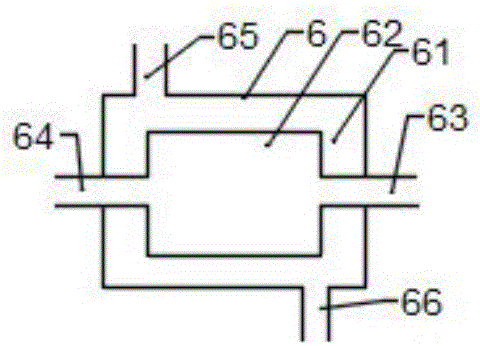
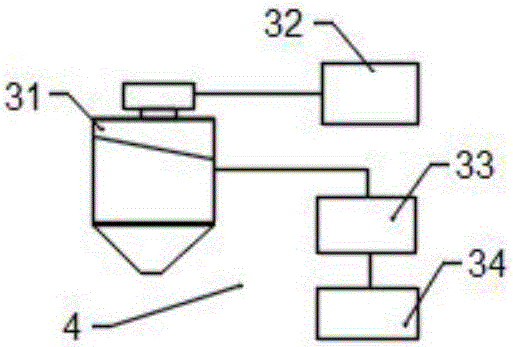
An intelligent integrated pharmaceutical dust-free conveying system
InactiveCN106492963AHigh degree of automationIncrease productivityReversed direction vortexGrain treatmentsProcess engineeringDelivery system
An intelligent integrated pharmaceutical dust-free conveying system is disclosed. The system includes a control device, a raw material feeding device, a gas generator, a sterilization separation device and a cleaning device. The system is characterized in that the raw material feeding device is disposed at one side of the control device and includes a raw material storage, a material lifting and conveying device and a feeding hopper, the raw material storage is connected to a material crushing device, and the material crushing device includes a crushing bin. The system can achieve real dust-free and aseptic material conveying, is high in conveying efficiency, safe and reliable, can effectively avoid primary and secondary pollution, increases the large-scale production degree of an enterprise and increases quality and the production efficiency of products.
Owner:YICHUN WANSHEN PHARMA MACHINERY
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com