Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
57637results about "Security arrangement" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
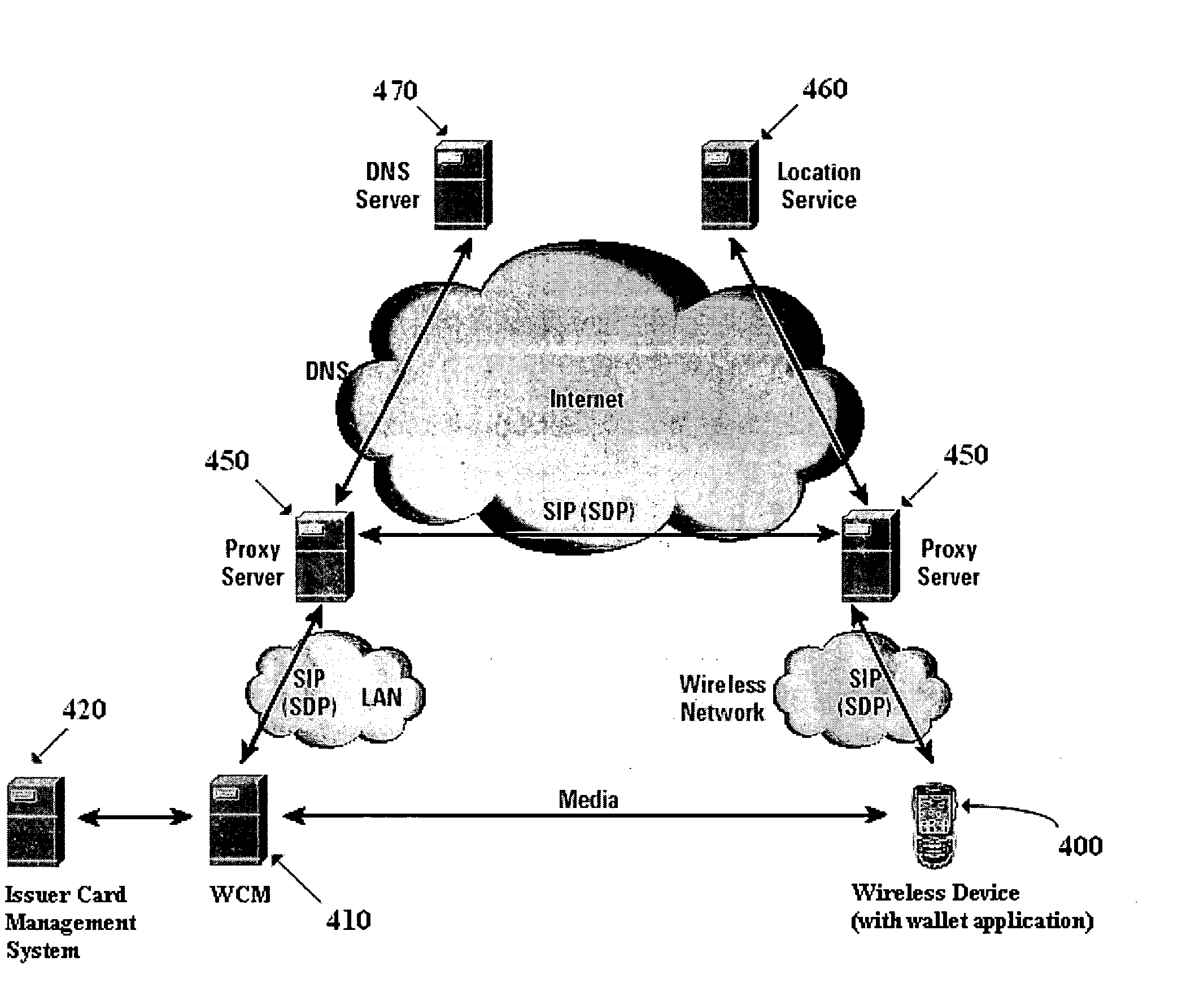
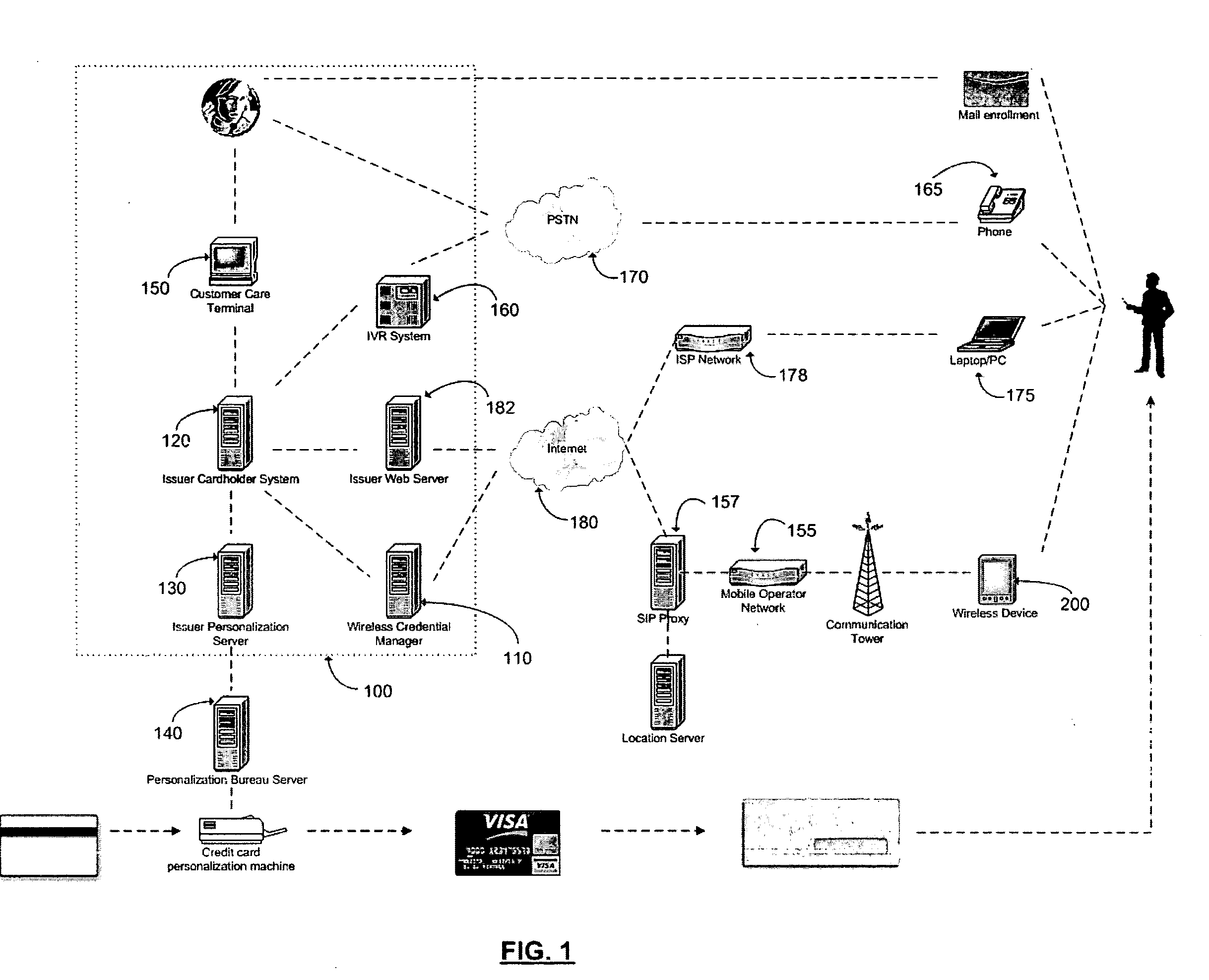
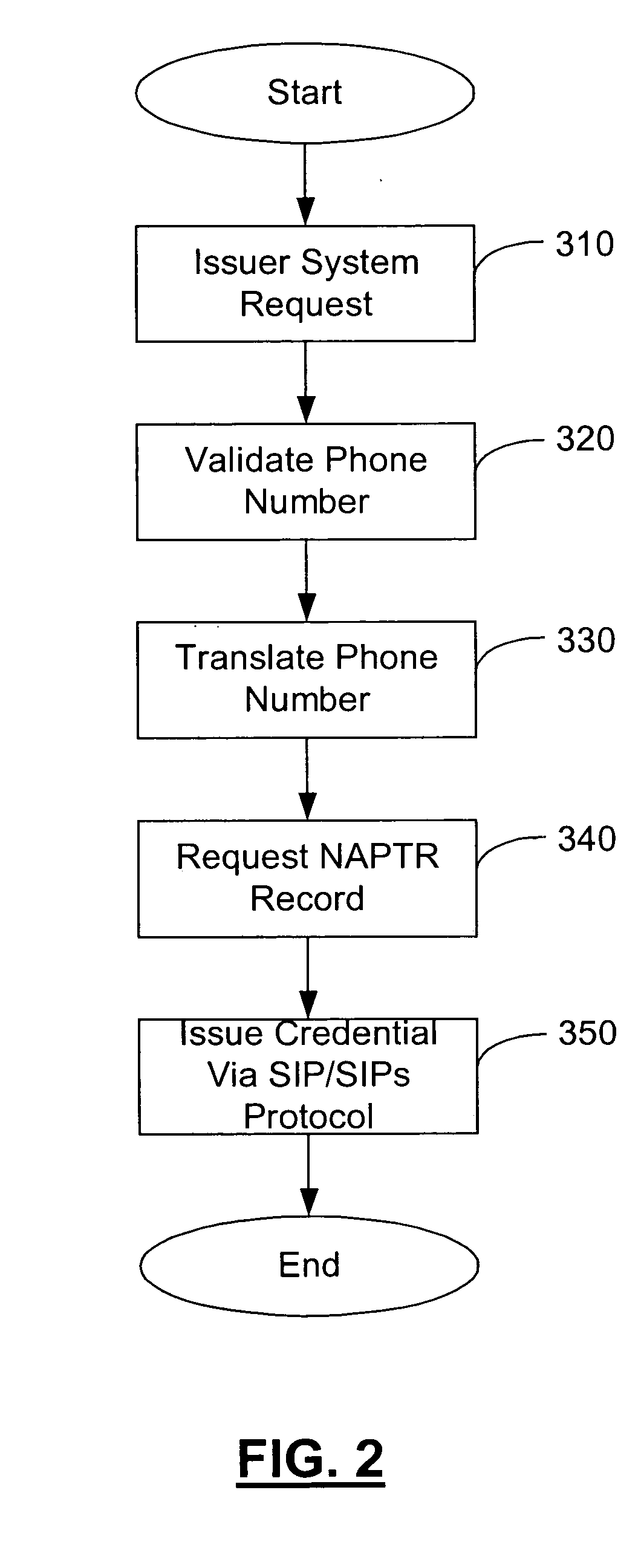
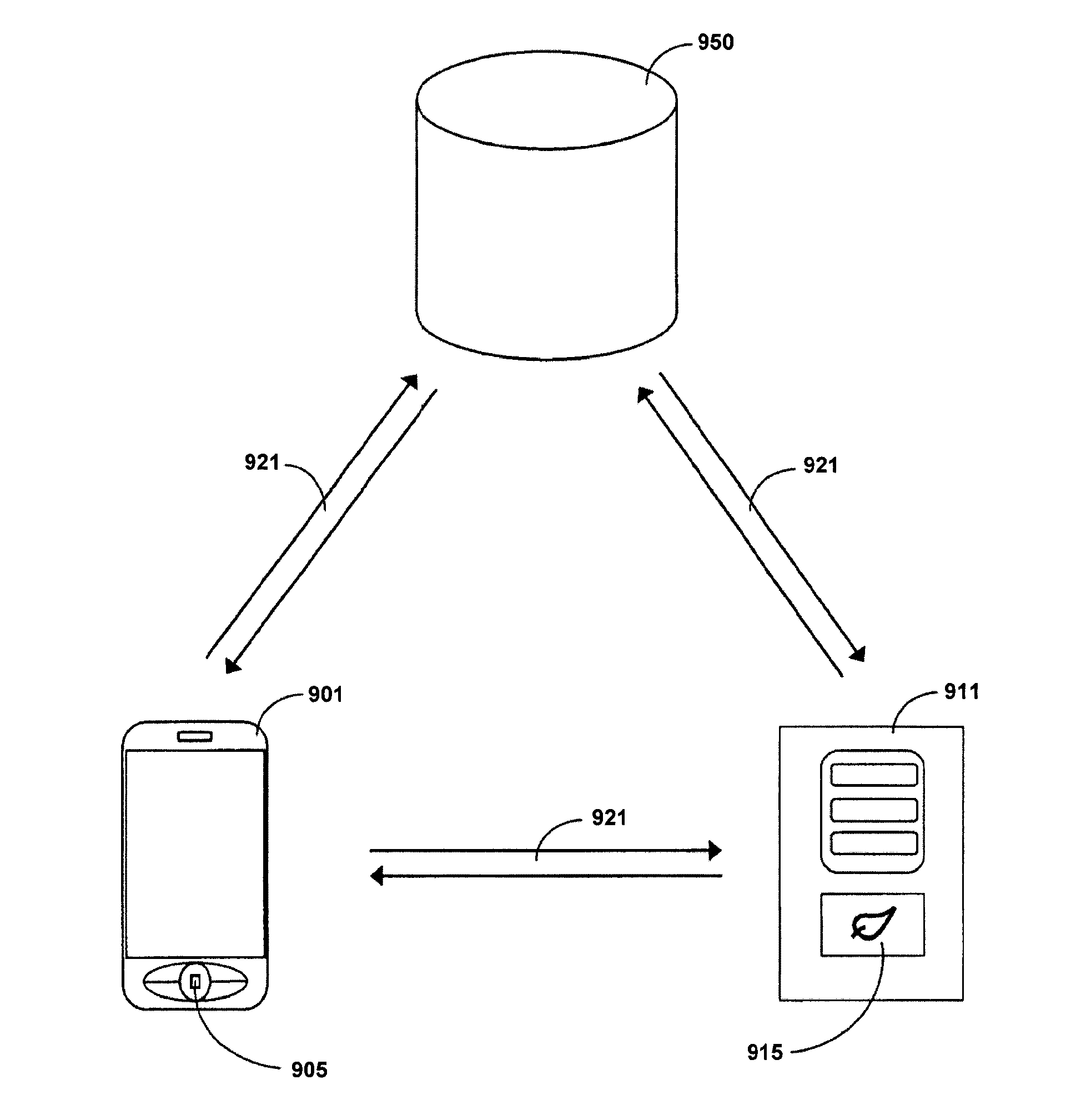
Method and apparatus for managing credentials through a wireless network
ActiveUS20060165060A1Convenient and efficient and secure distributionNear-field in RFIDData switching by path configurationCredit cardWireless mesh network
A novel system and methodology for conducting financial and other transactions using a wireless device. Credentials may be selectively issued by issuers such as credit card companies, banks, and merchants to consumers permitting the specific consumer to conduct a transaction according to the authorization given as reflected by the credential or set of credentials. The preferred mechanism for controlling and distributing credentials according to the present invention is through one or more publicly accessible networks such as the Internet wherein the system design and operating characteristics are in conformance with the standards and other specific requirements of the chosen network or set of networks. Credentials are ultimately supplied to a handheld device such as a mobile telephone via a wireless network. The user holding the credential may then use the handheld device to conduct the authorized transaction or set of transactions via, for example, a short range wireless link with a point-of-sale terminal.
Owner:SAMSUNG ELECTRONICS CO LTD
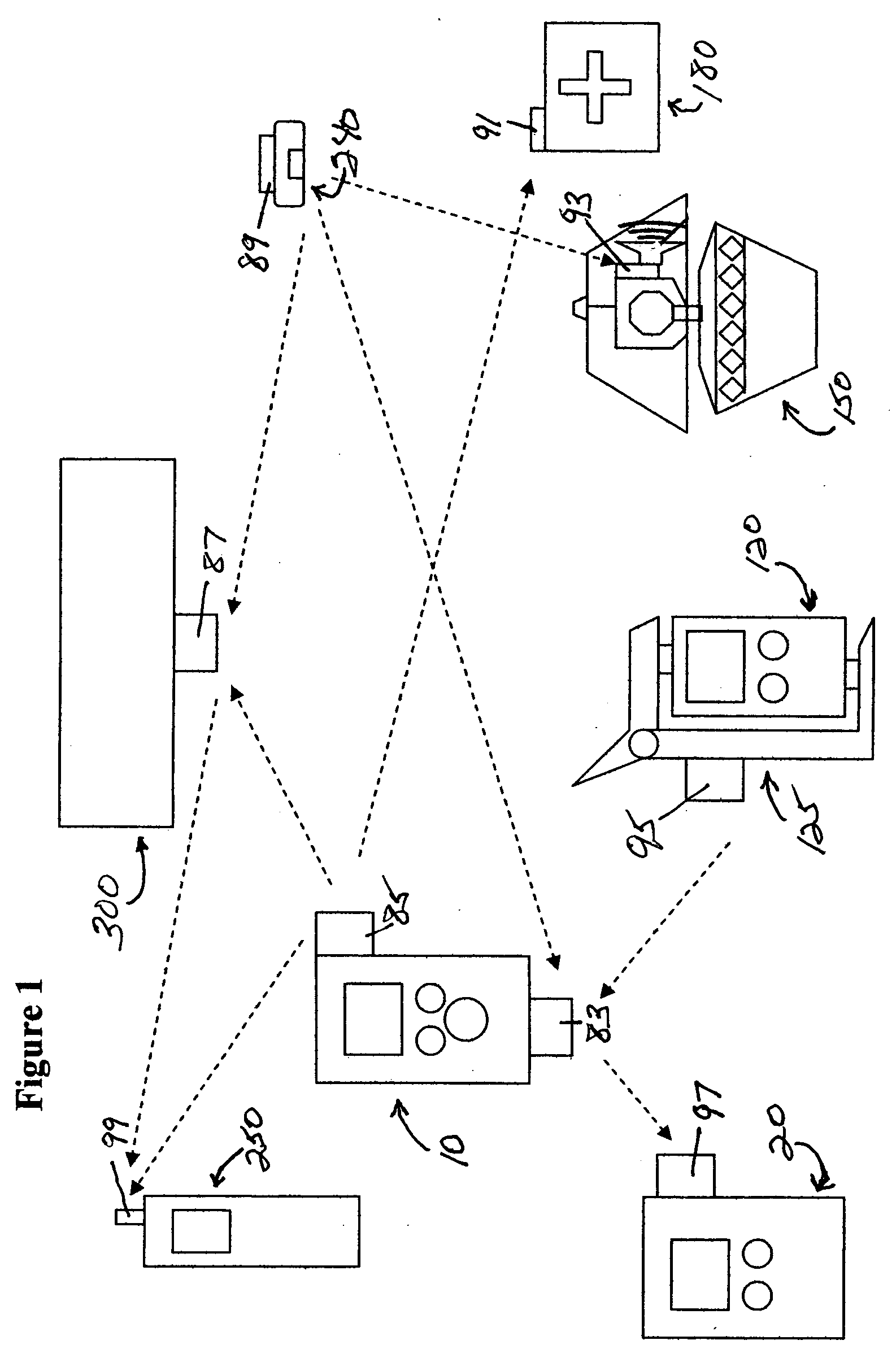
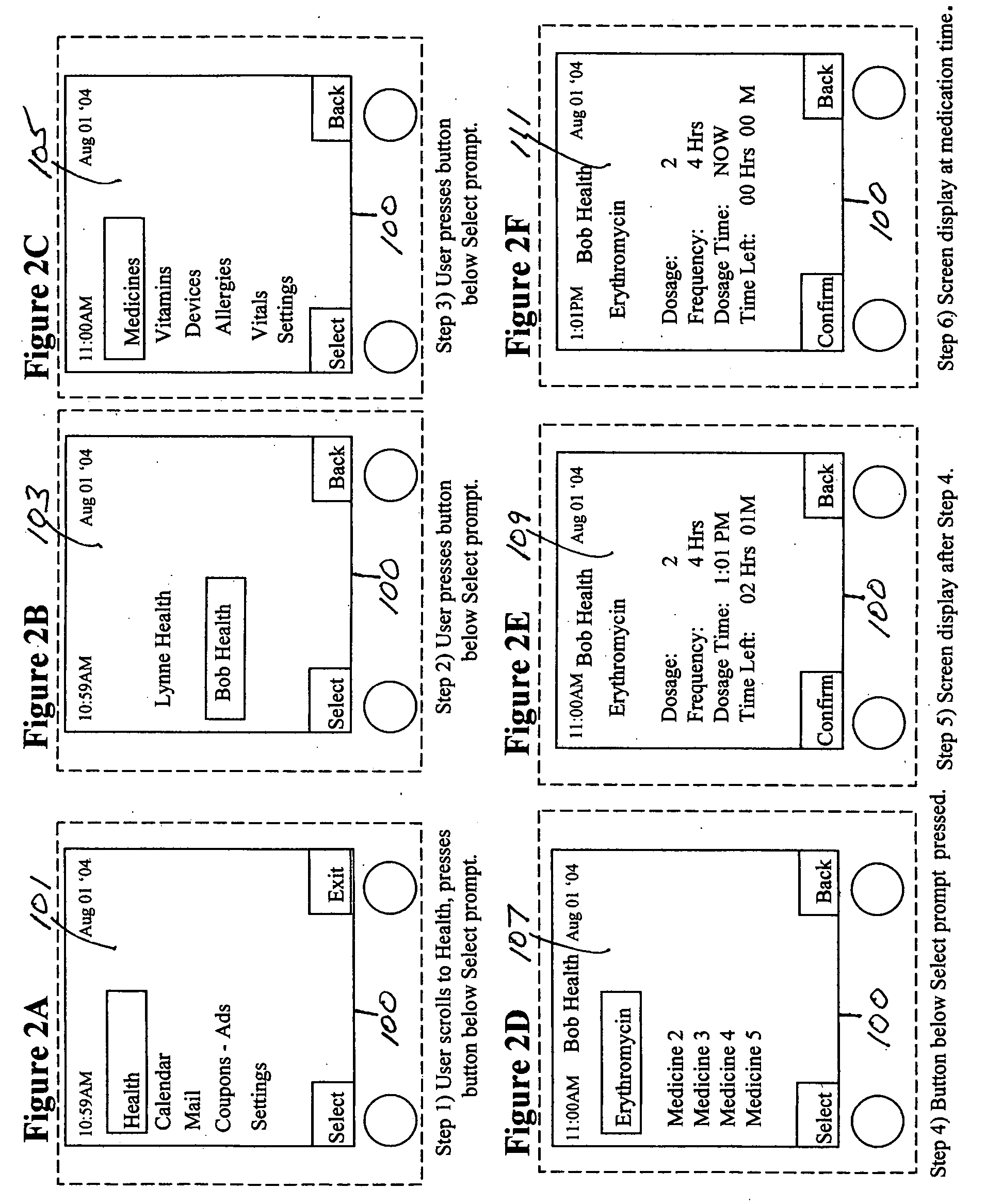
Medication & health, environmental, and security monitoring, alert, intervention, information and network system with associated and supporting apparatuses
InactiveUS20060154642A1Facilitate user and/or occupant well beingExtended stayDispersed particle filtrationDrug and medicationsNetworked systemHealth administration
Systems and apparatuses include devices, biosensors, environmental sensors, security related sensors, networked products, communications processors and components, alert and information components, processors, and software to support: 1) facilitating medication regimen and patient / user health administration, dosage control, tracking, compliance, information inquiry and presentation, reminder and notification; 2) providing monitoring, information, ordering, and intervention; 3) presenting the option of leveraging the preventative care, alert and notification components with other components to facilitate user or occupant well being, along with living, work area and dwelling environmental or security safety; and 4) enhancing the dwelling, living or work area with products that may be networked to support the widespread acceptance of these systems and apparatuses. The systems include a) processing, centralizing and communicating device commands and / or programs, e.g. a multifunctional device controller; b) device administration; c) patient / user information; d) dwelling environmental safety; e) security breach information; f) centralized and remote apparatus and system activations through primary component or at least one backup.
Owner:INSIGNIO TECH
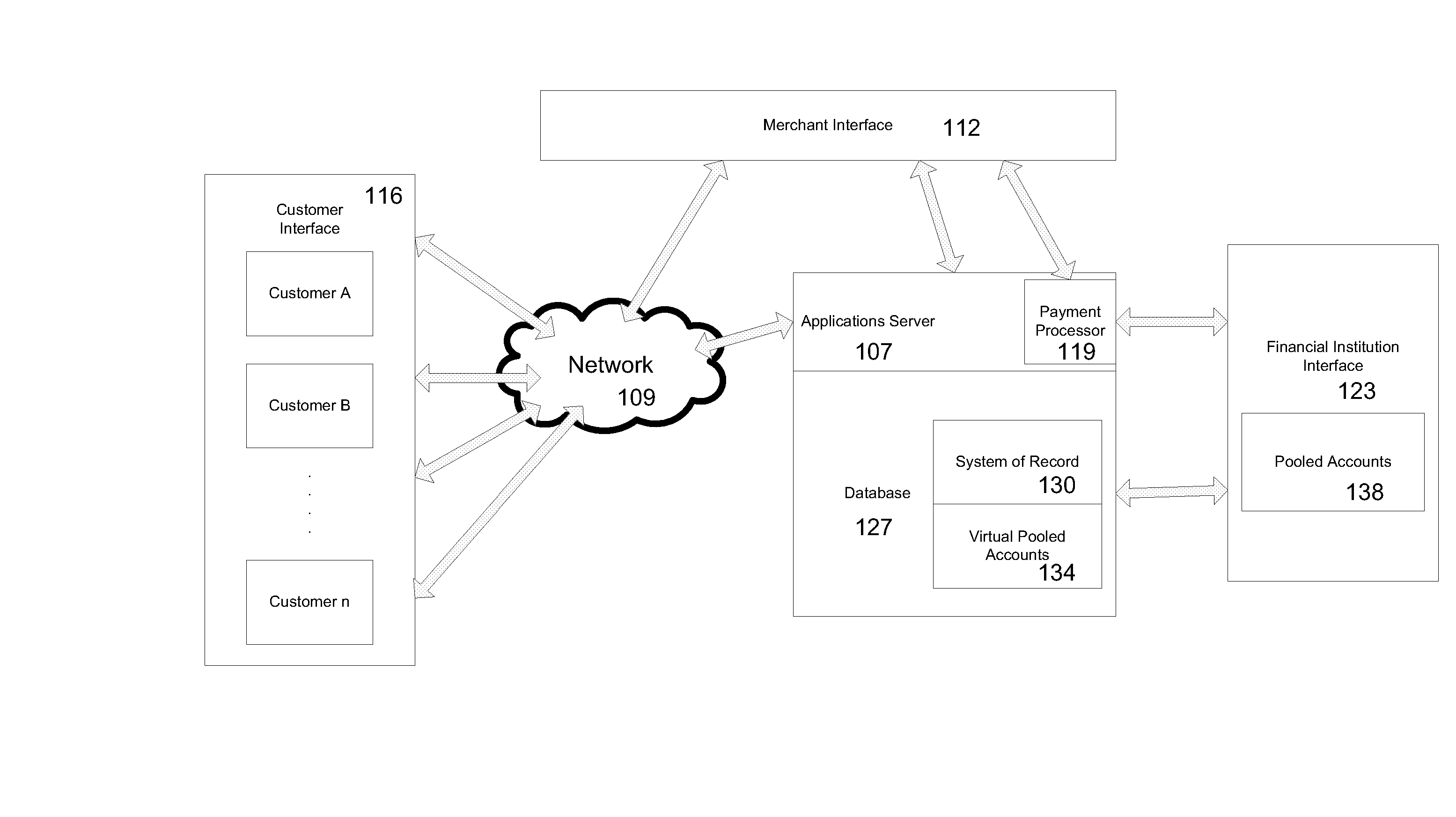
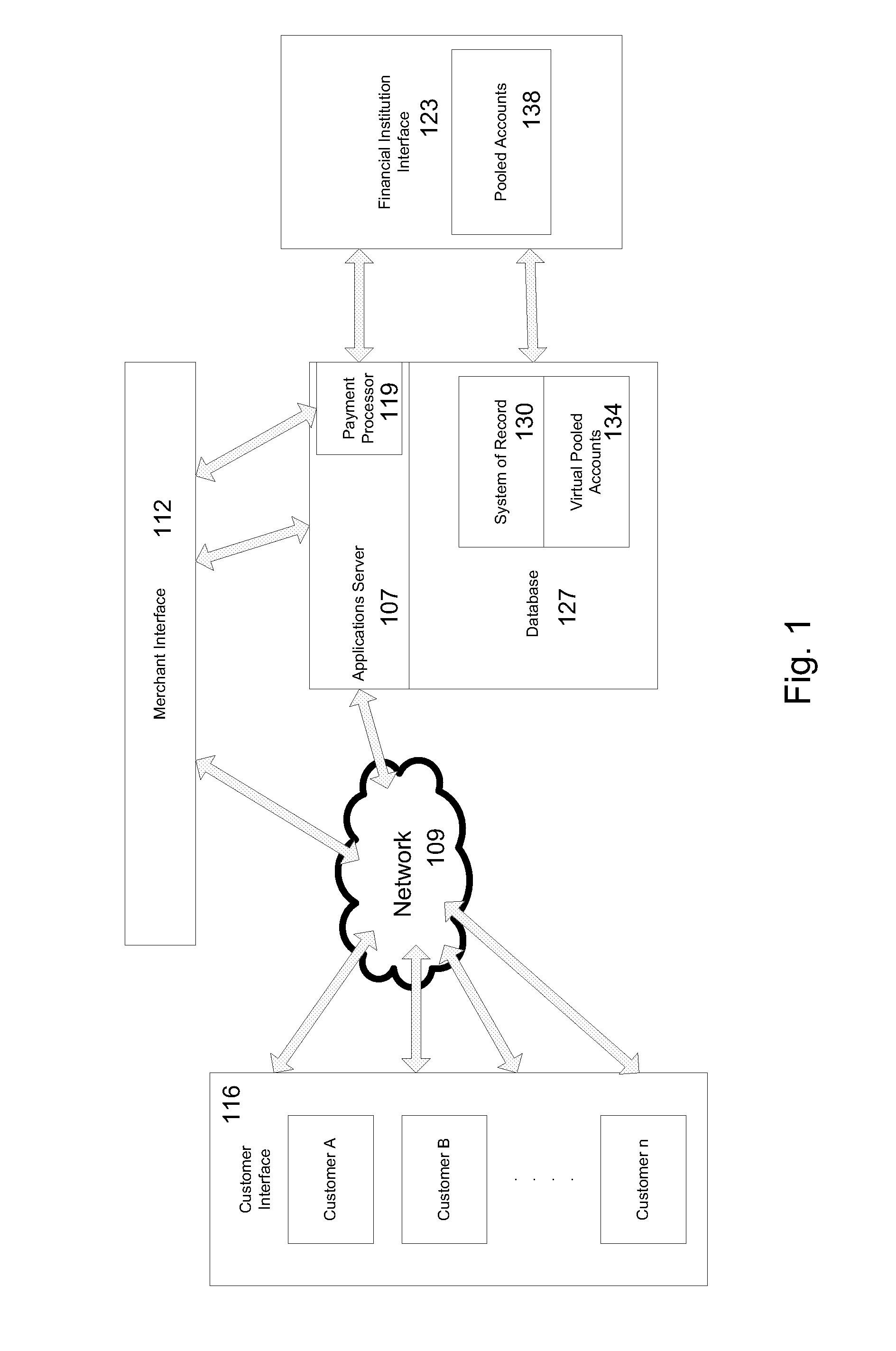
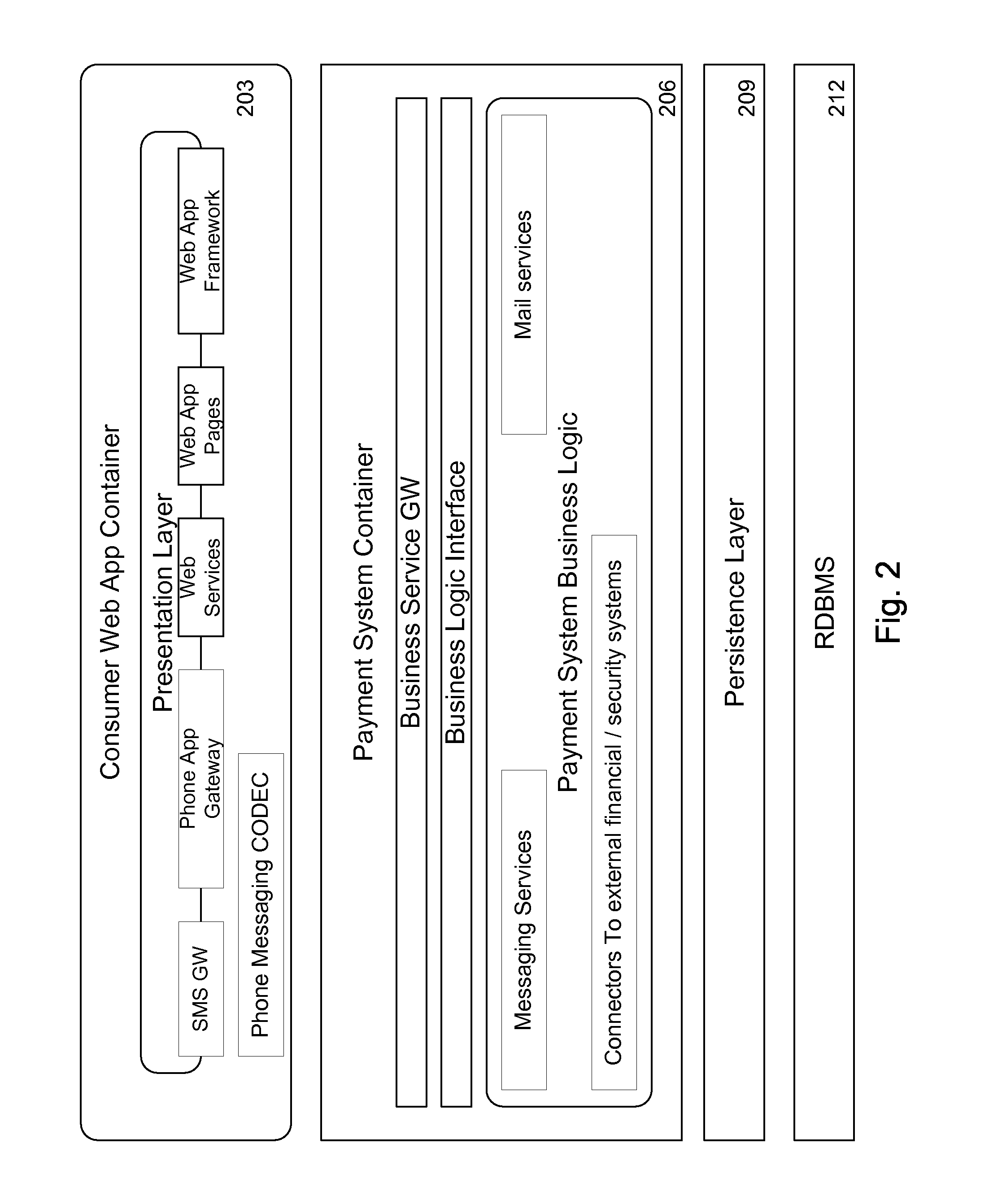
Mobile Person-to-Person Payment System
InactiveUS20070255653A1Easy to useFraudulent transaction is minimizedFinancePayment architectureBarcodeFinancial transaction
A mobile payment platform and service provides a fast, easy way to make payments by users of mobile devices. The platform also interfaces with nonmobile channels and devices such as e-mail, instant messenger, and Web. In an implementation, funds are accessed from an account holder's mobile device such as a mobile phone or a personal digital assistant to make or receive payments. Financial transactions can be conducted on a person-to-person (P2P) or person-to-merchant (P2M) basis where each party is identified by a unique indicator such as a telephone number or bar code. Transactions can be requested through any number of means including SMS messaging, Web, e-mail, instant messenger, a mobile client application, an instant messaging plug-in application or “widget.” The mobile client application, resident on the mobile device, simplifies access and performing financial transactions in a fast, secure manner.
Owner:OBOPAY MOBILE TECH INDIA PTE LTD
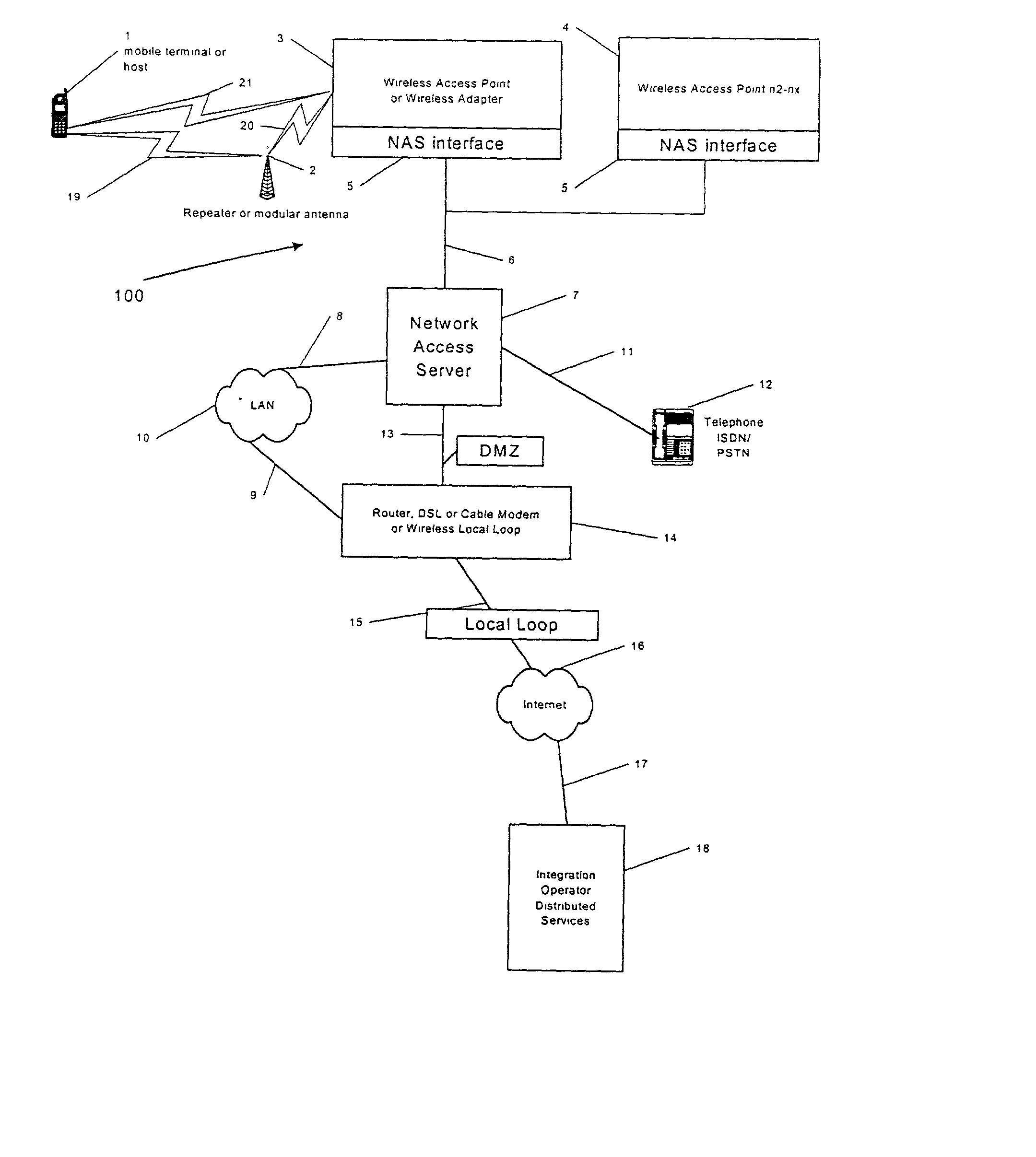
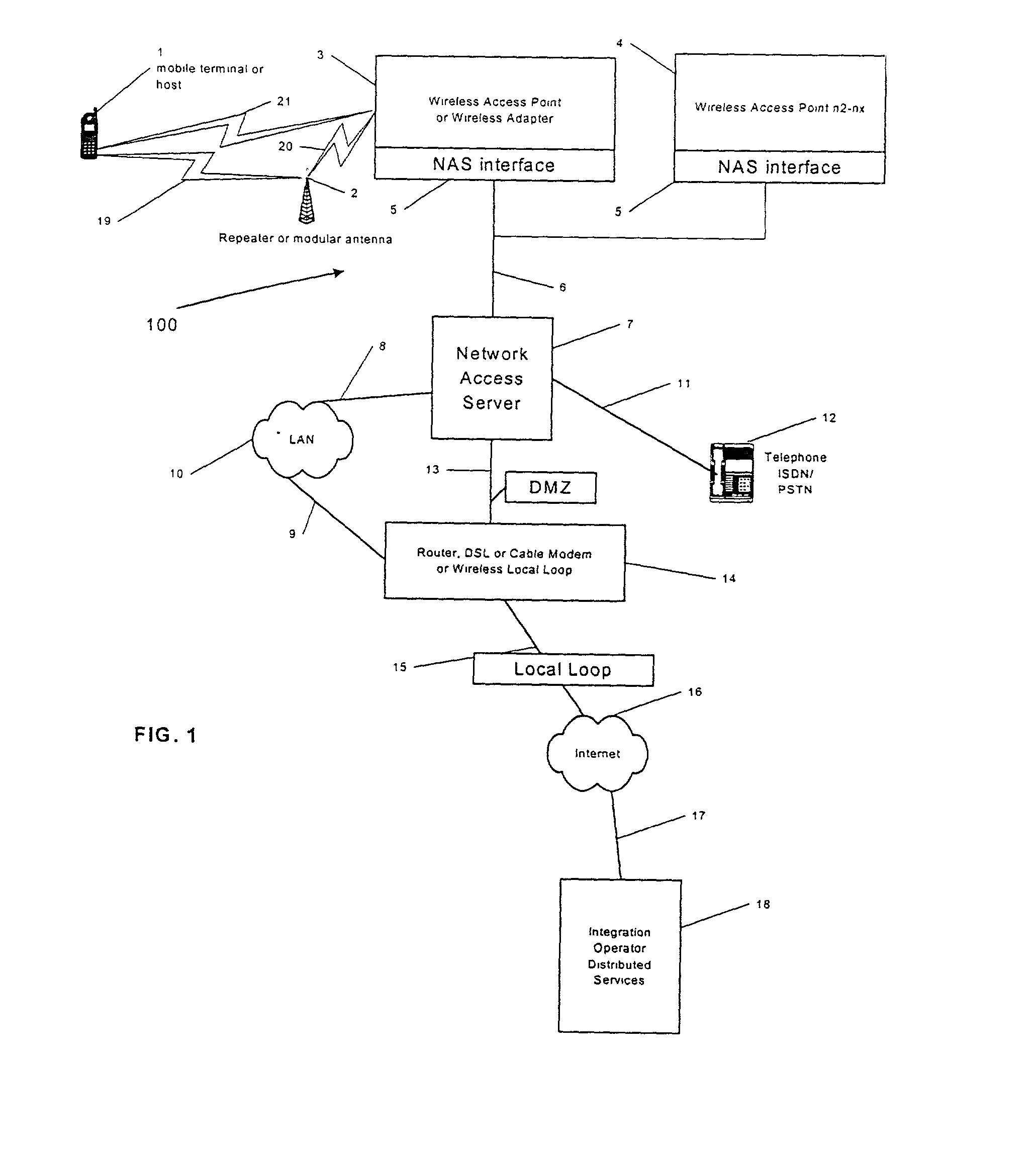
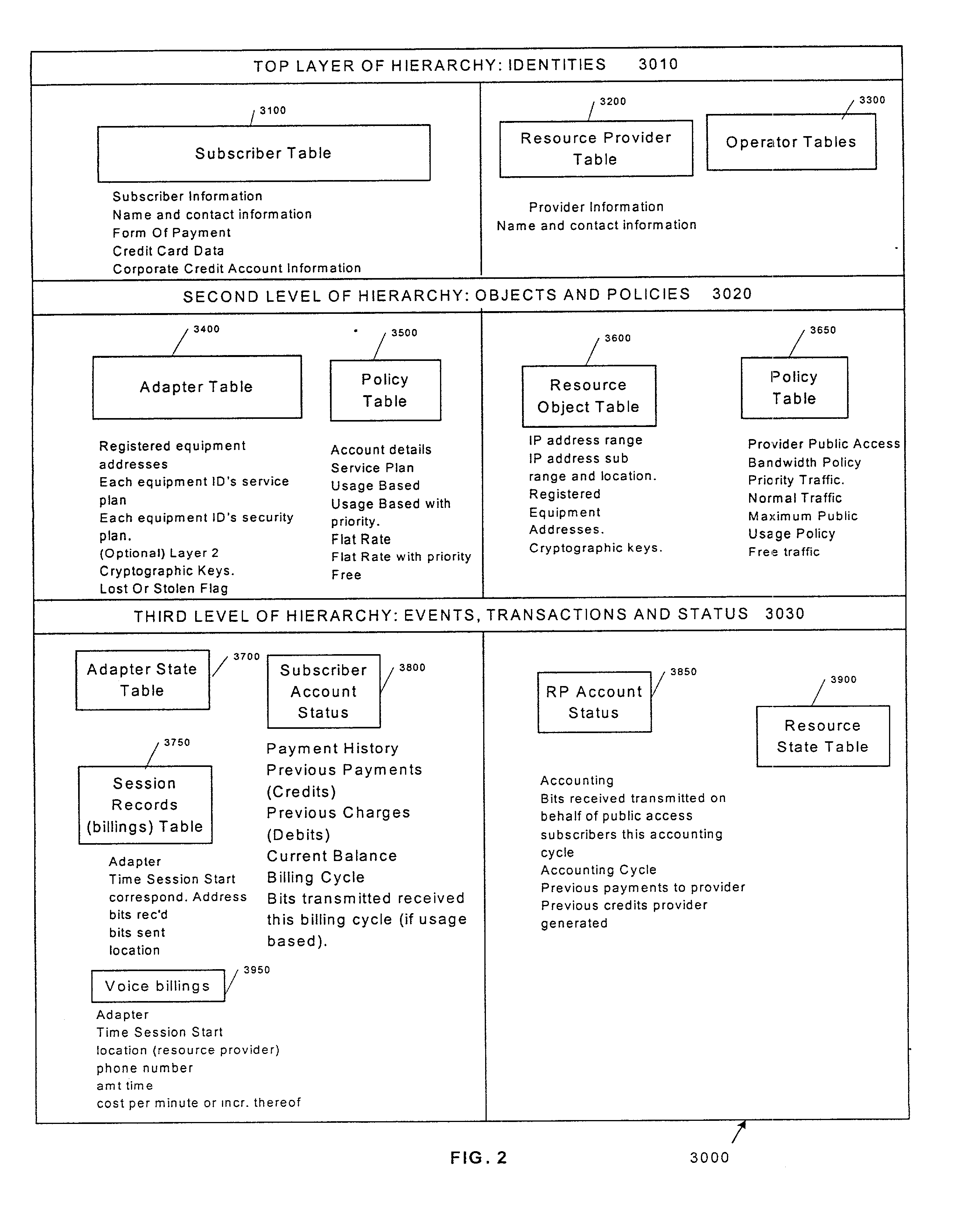
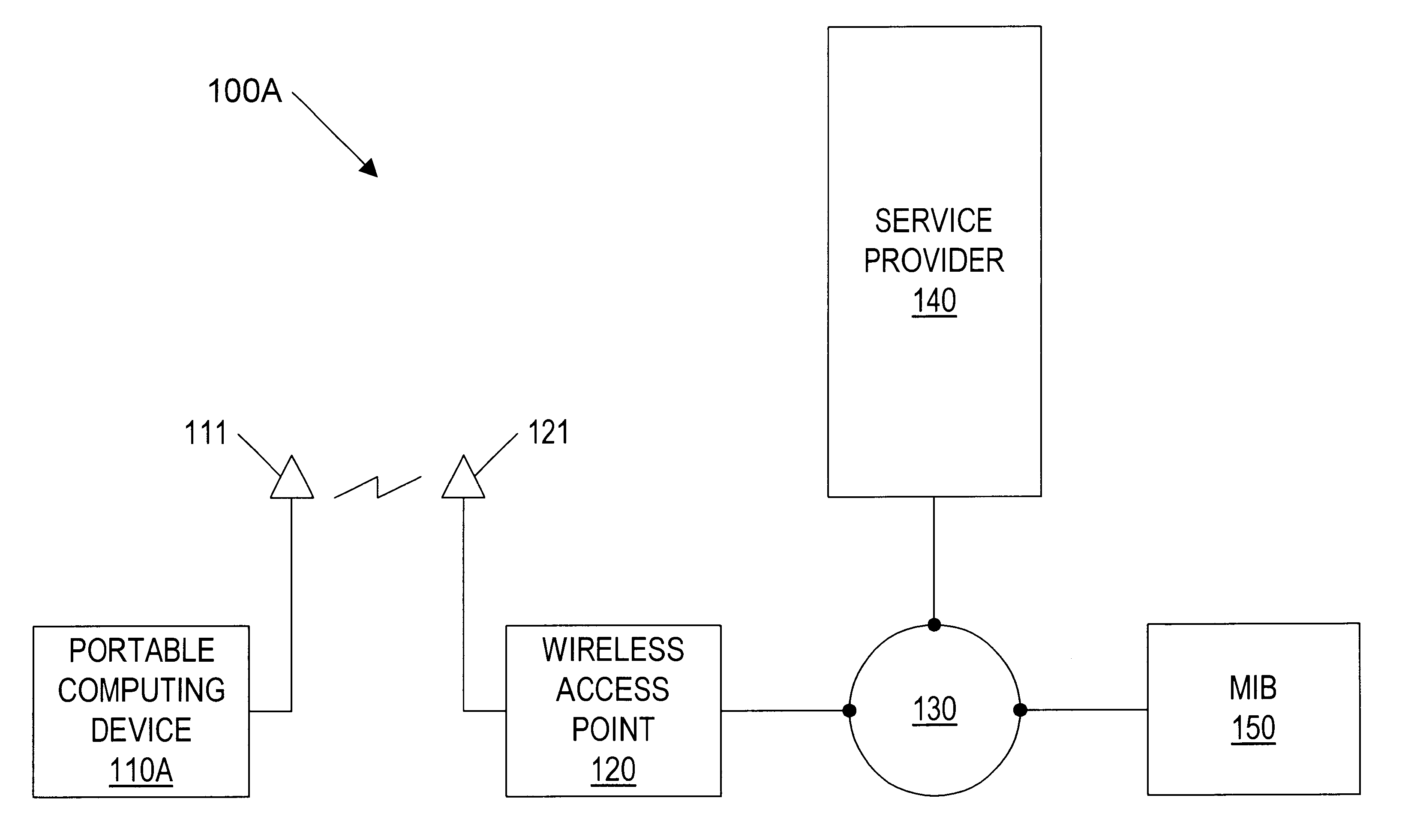
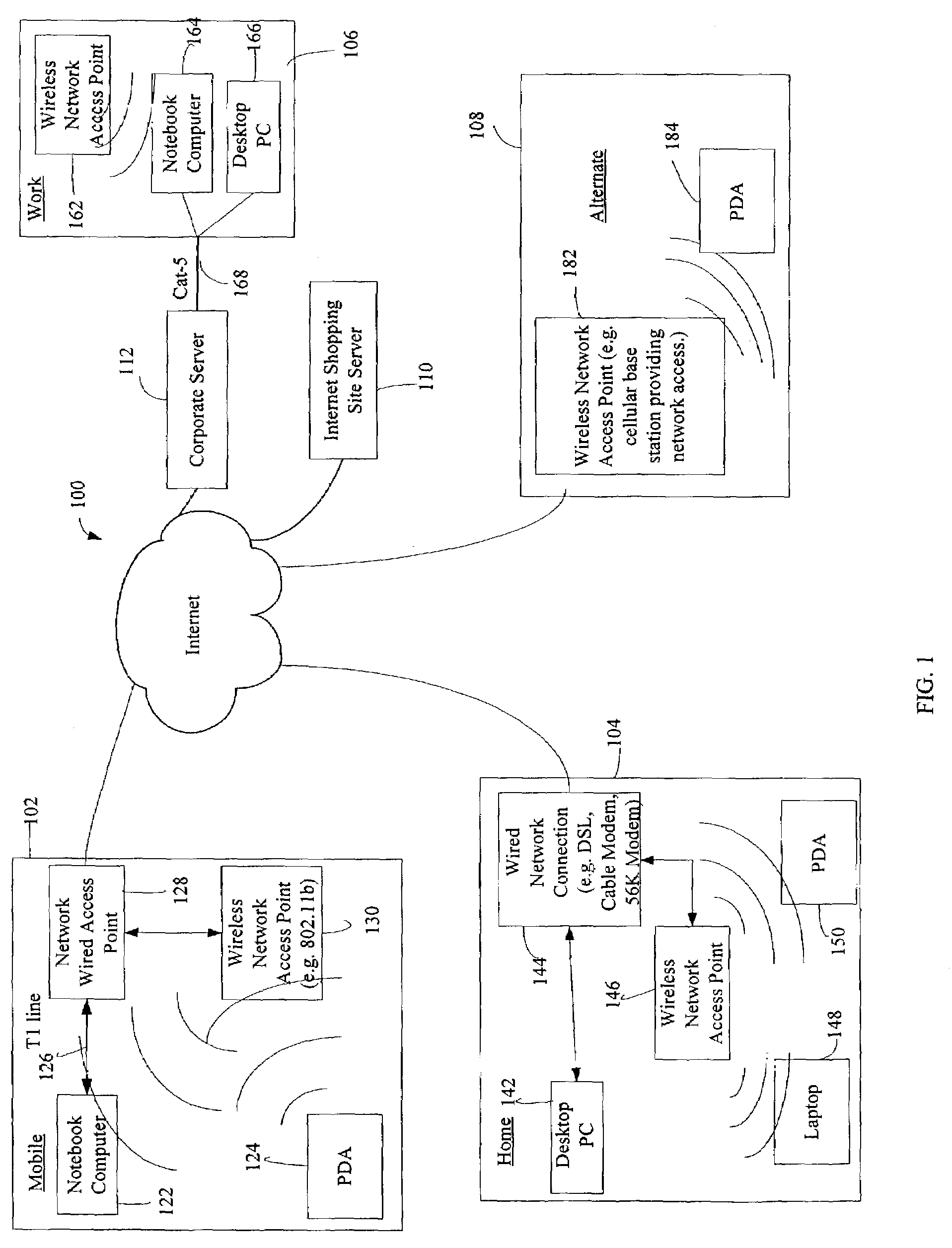
Integrating public and private network resources for optimized broadband wireless access and method
InactiveUS20020075844A1Network traffic/resource managementNetwork topologiesNetwork access serverPrivate network
A system and method are disclosed for providing ubiquitous public network access to wireless, mobile terminals using private networks having private network access points and connections with the public network. The wireless, mobile terminals are permitted to use wireless, radio frequency communication devices comprising private network access points. A network access server (NAS) is associated with each wireless, radio frequency communication device and provides an interface between the wireless, mobile terminals and the private network. The NAS controls registration of wireless, mobile terminals as subscribers, and provides public network access to the mobile terminals through the private network's access point and public network connection. The NAS also restricts access by the mobile terminals to the private network, meters network useage by the mobile terminals, and controls use of bandwidth by the mobile terminals. The NAS also interfaces with integration operator distributed services over the public network. The integration operator services include databases and servers for storing and providing subscriber and network provider information for subscriber registration, network access and useage control, and accounting purposes. The NAS may be provided as a standalone element embodied in a computer, or may be integrated with the wireless radio frequency device and / or a network adaptor device for the private network.
Owner:NTT DOCOMO DCMR COMM LAB USA
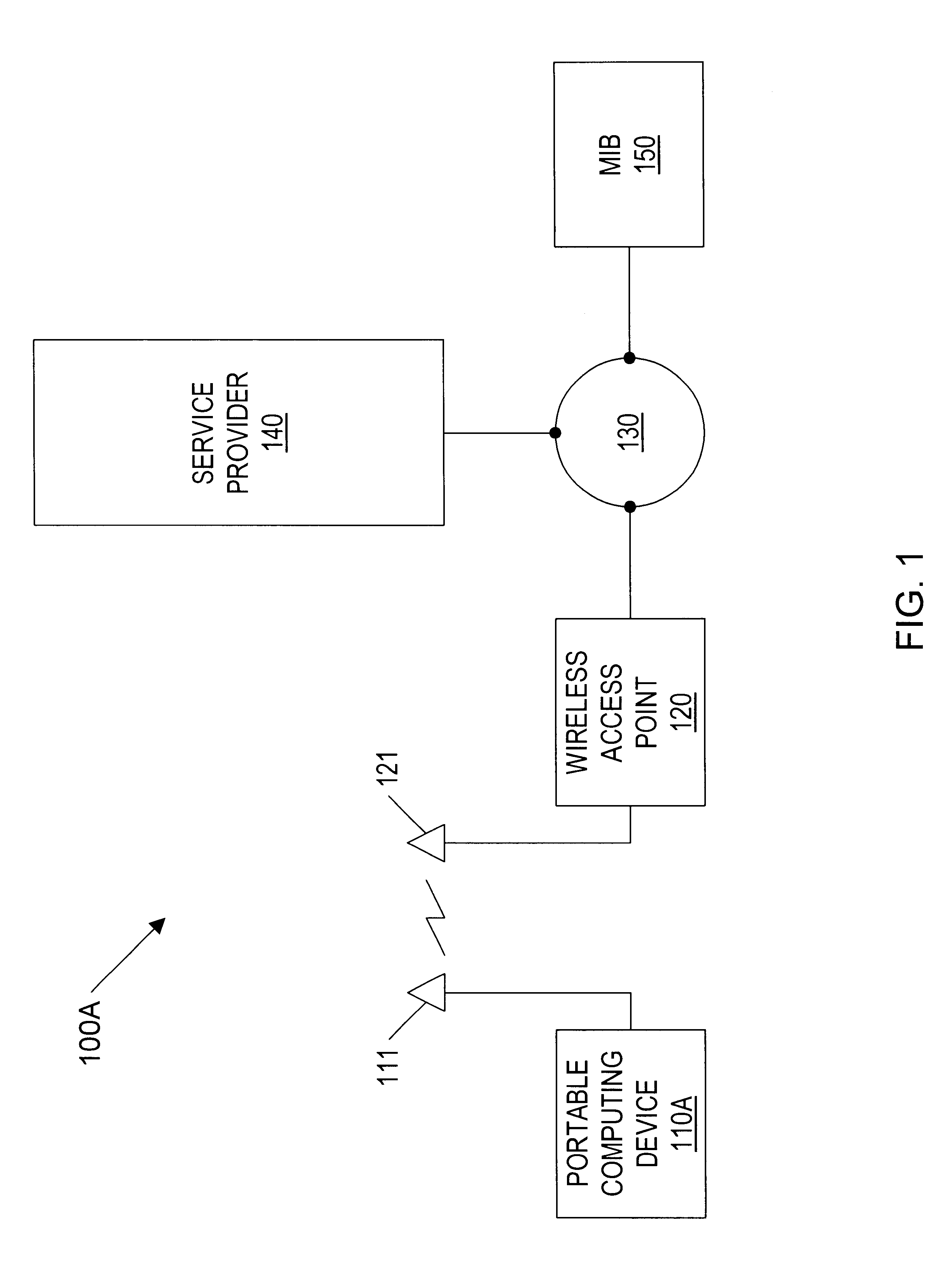
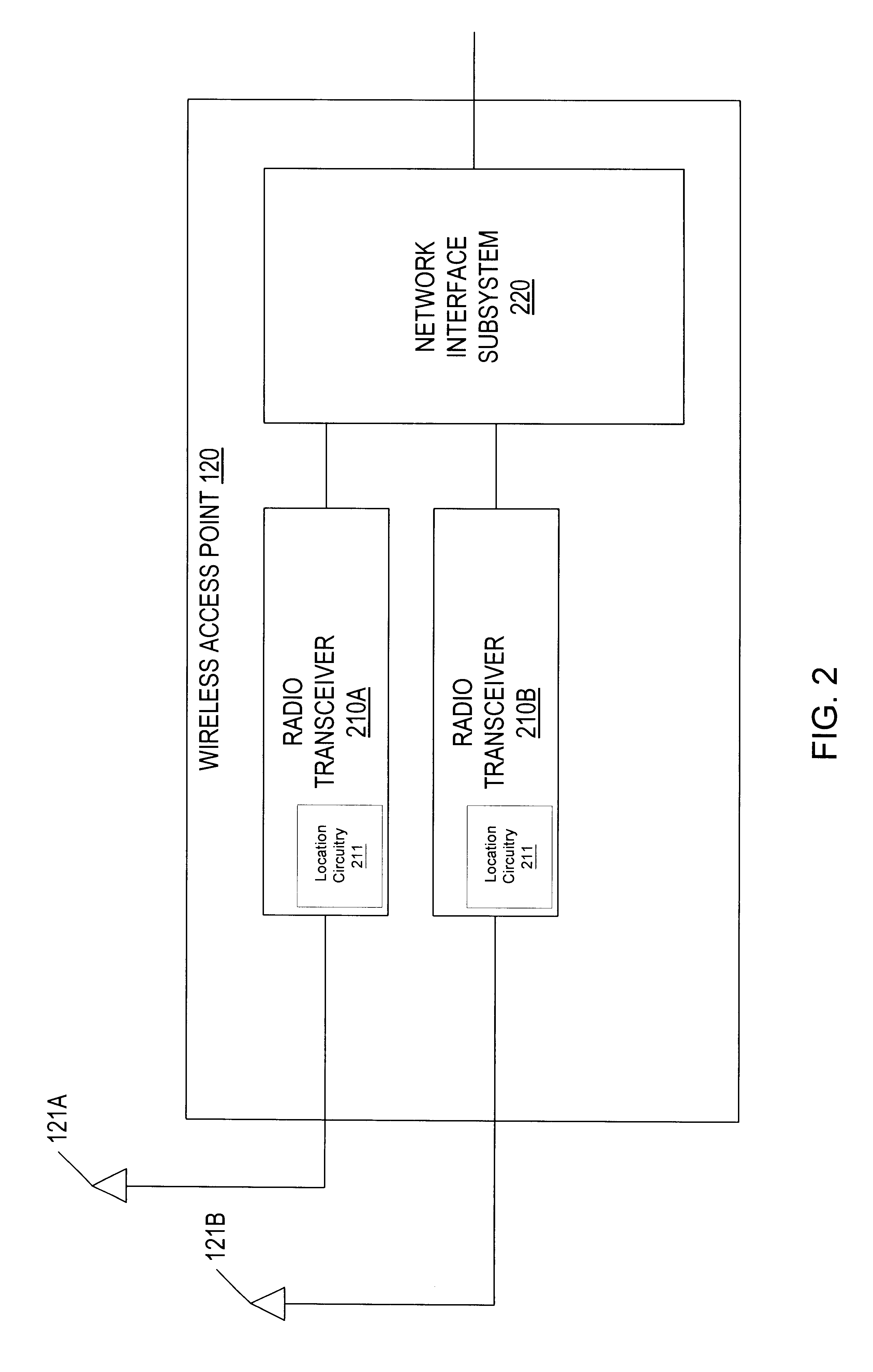
Geographic-based communication service system with more precise determination of a user's known geographic location
InactiveUS6414635B1Direction finders using radio wavesNetwork topologiesGeographic regionsGeolocation
A geographic based communications service system that includes a network and a plurality of access points connected to the network and arranged at known locations in a geographic region. One or more service providers or information providers may be connected to the network to provide services or information on the network. Content provided by the service providers may be based on the known geographic location of the user of a portable computing device (PCD). The known geographic location may be determined with a high degree of precision, using one or more access points and one of several different techniques. In one embodiment, the geographic location of the PCD may be determined within a radius of ten feet. Access points may be configured to determine the bearing of a signal received from a PCD, as well as the strength of the signal transmitted by the PCD. Access points may also be configured to send and receive signals with time stamps. These time stamps may be used to calculate signal travel time, thereby allowing a determination of the distance between an access point and a PCD. Each access point may include location circuitry. The location circuitry may include both analog and digital circuitry configured to perform the various methods used to determine the precise geographic location.
Owner:META PLATFORMS INC
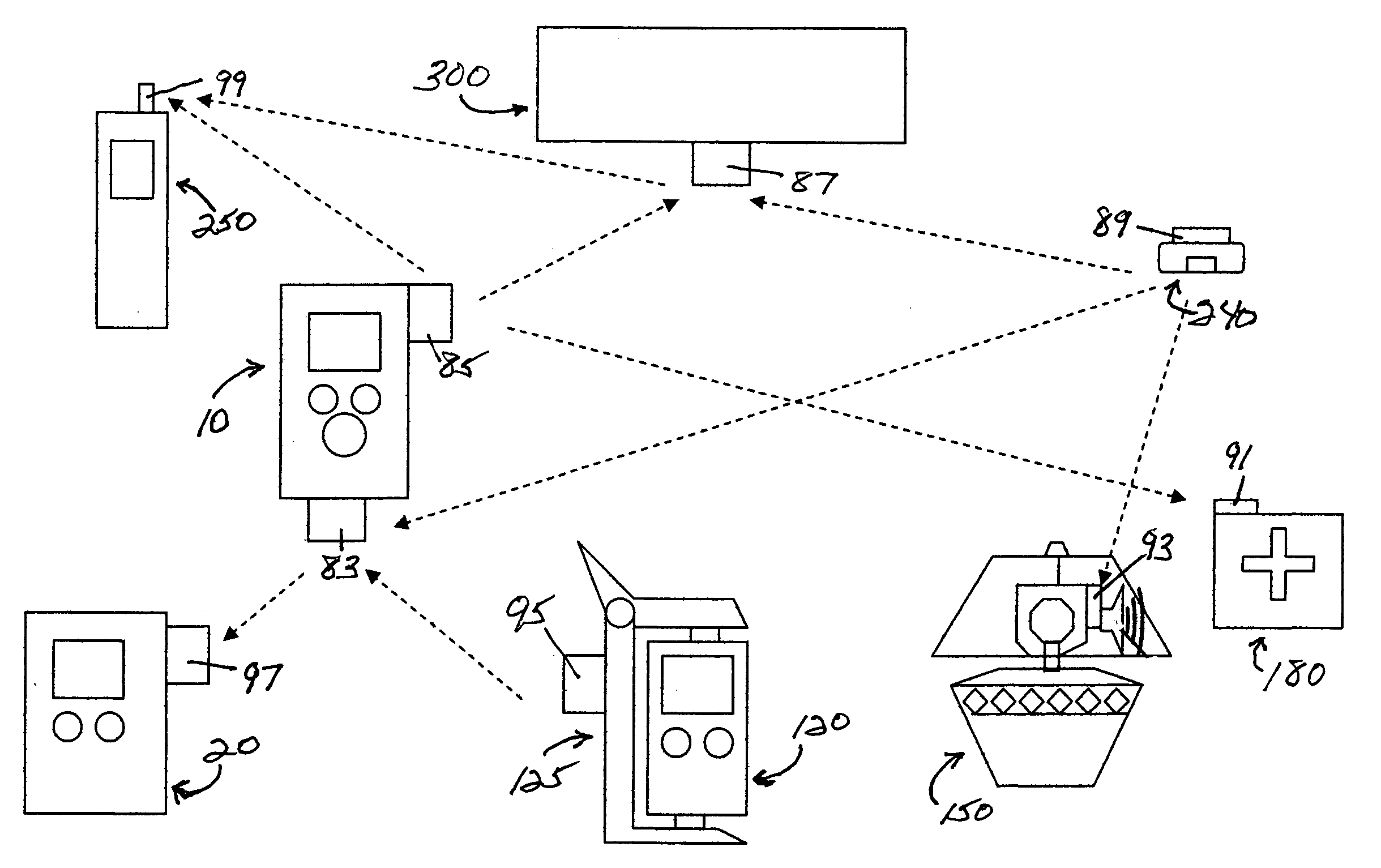
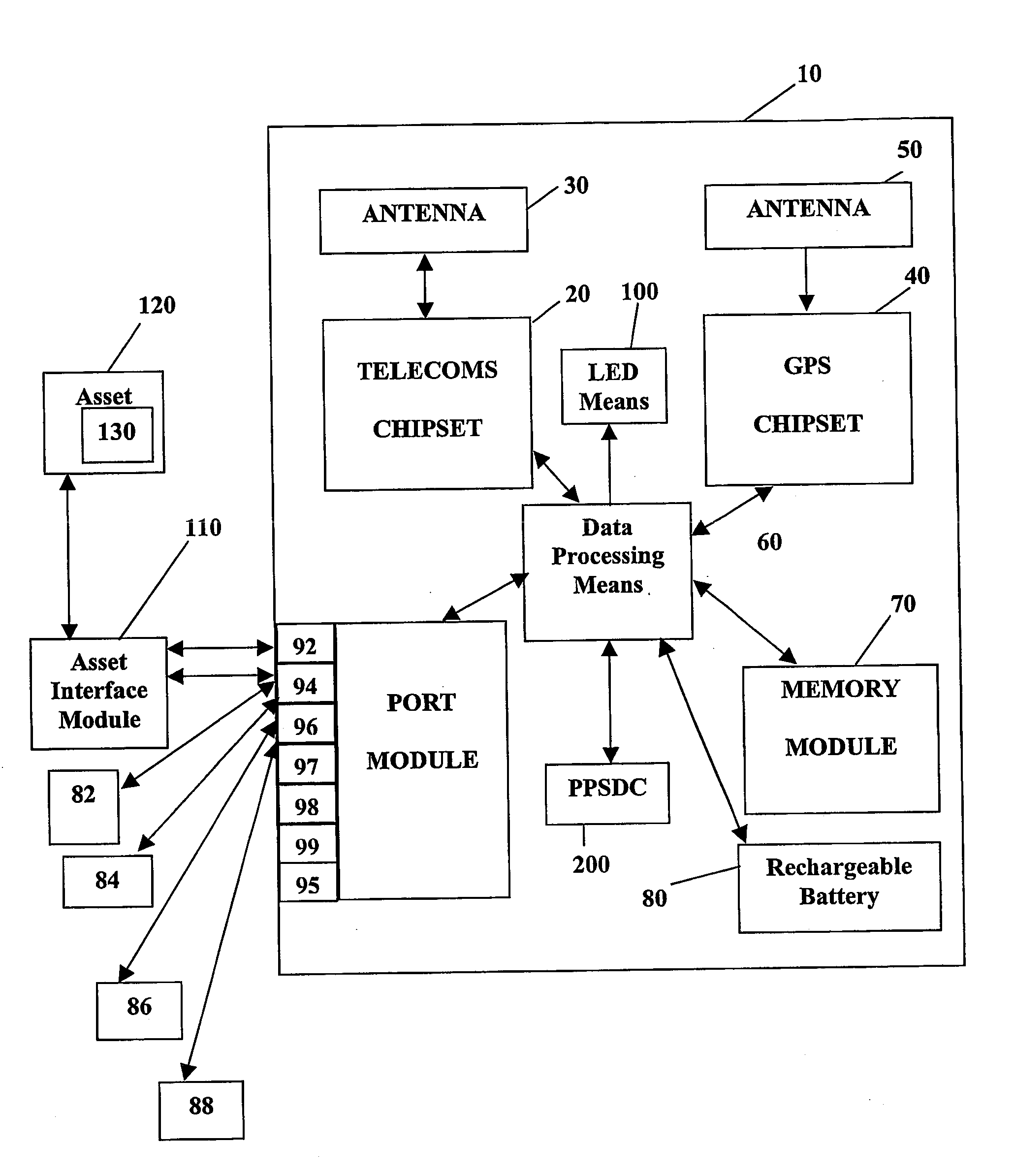
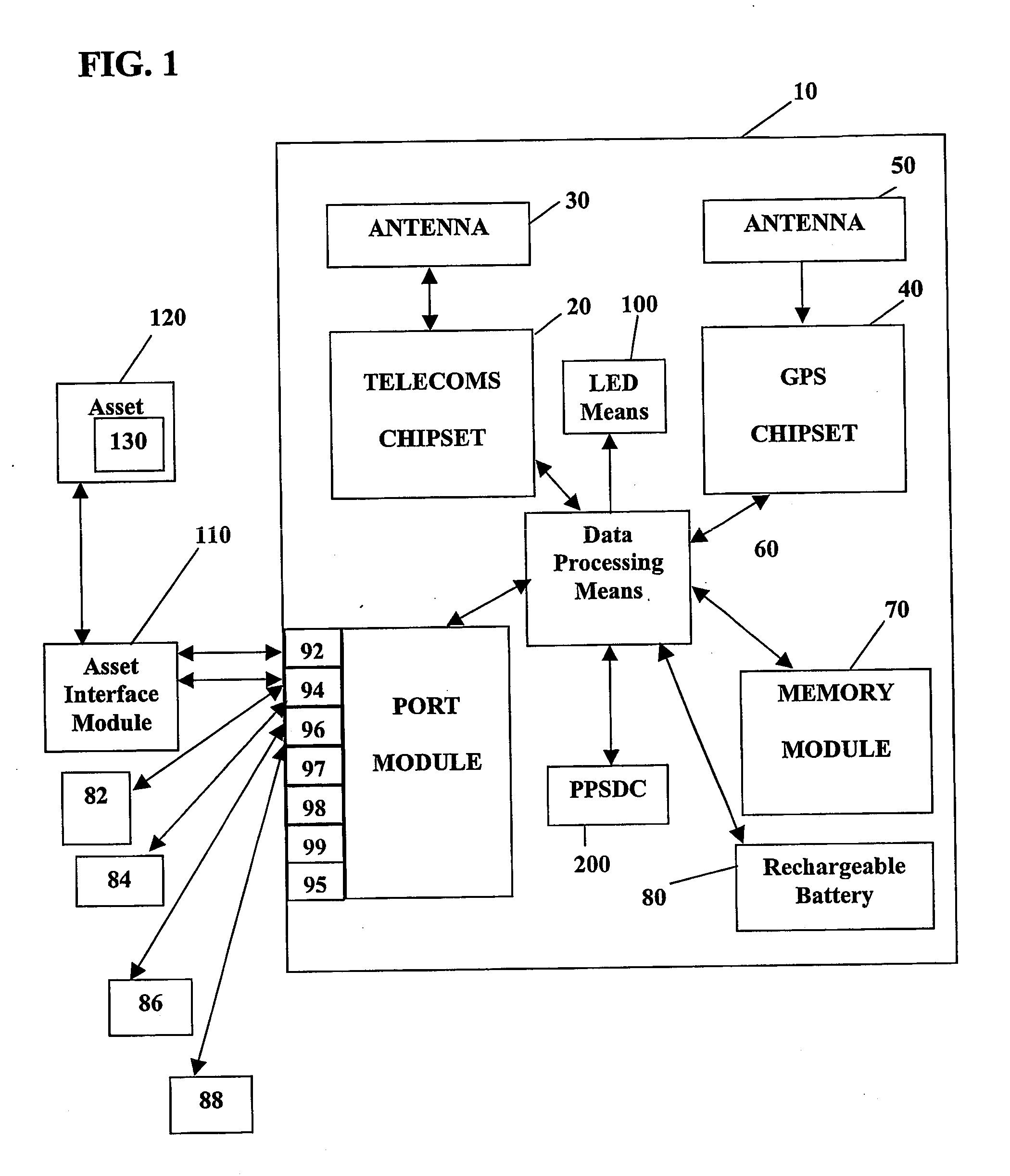
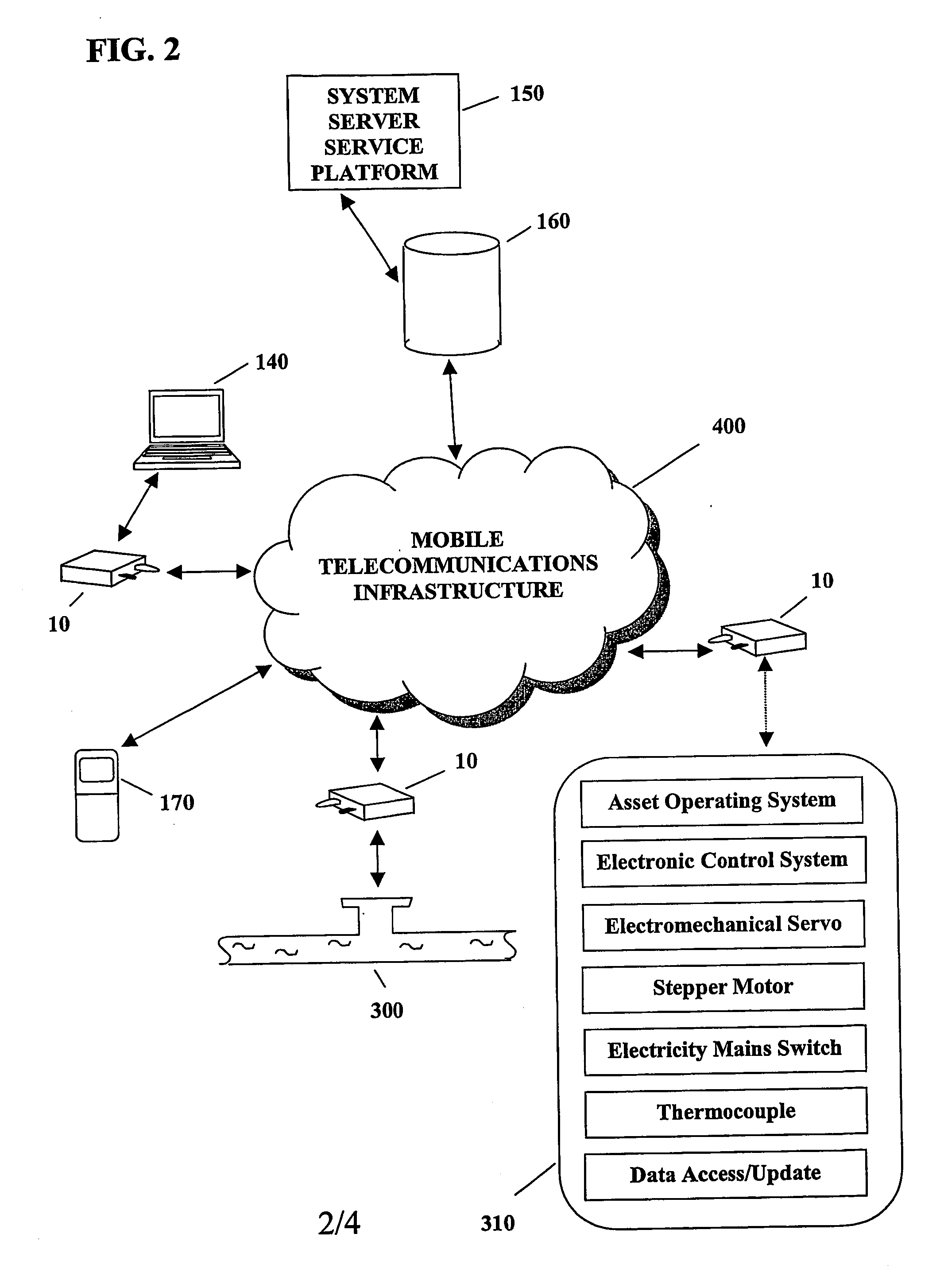
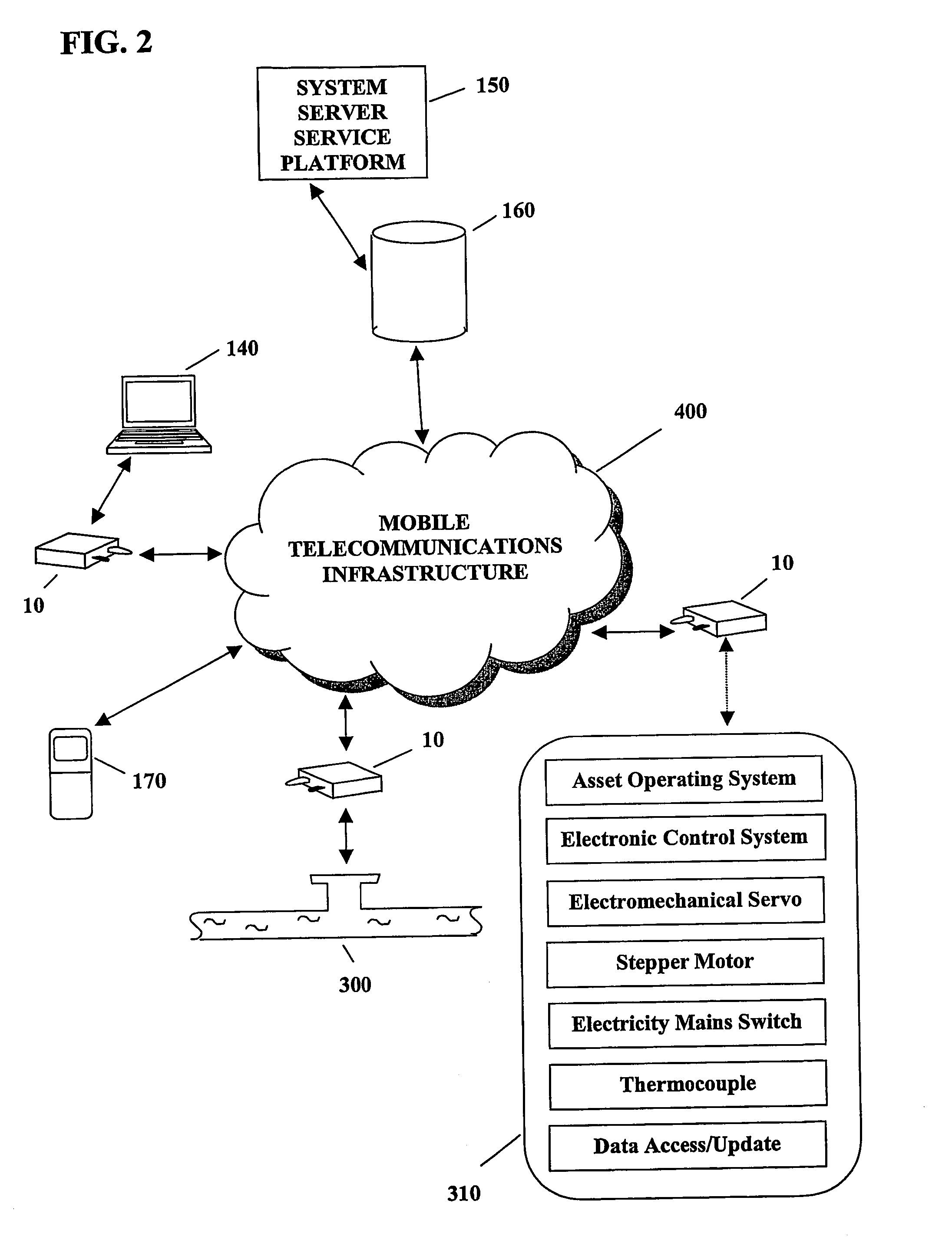
System and method for monitoring and control of wireless modules linked to assets
A system and method for remote asset management is described which can provide the basis for a diverse product group including an improved remote location monitoring system, a means for communicating with and for monitoring the status and or location of a plurality of diverse assets, as well as the means for communicating with said assets for the purpose of modifying the operational status of one or more of said assets according to one or more stored data parameters such as location, use, battery power, and such like. The remote asset management system comprise a wireless module, which is associated with at least one of the plurality of assets and which is interfaced with the operating system of said asset and or with an electromechanical control means, which may control one or more features of the operation of said assets. A supporting network-based, or internet-based service platform controls and manages the status of each of the plurality of assets, either automatically, or in response to received messages from fixed or wireless communication devices, and which is capable of selectively communicating data to said assets for changing the operational status of said assets according to pre-programmed conditions.
Owner:M2M SOLUTIONS
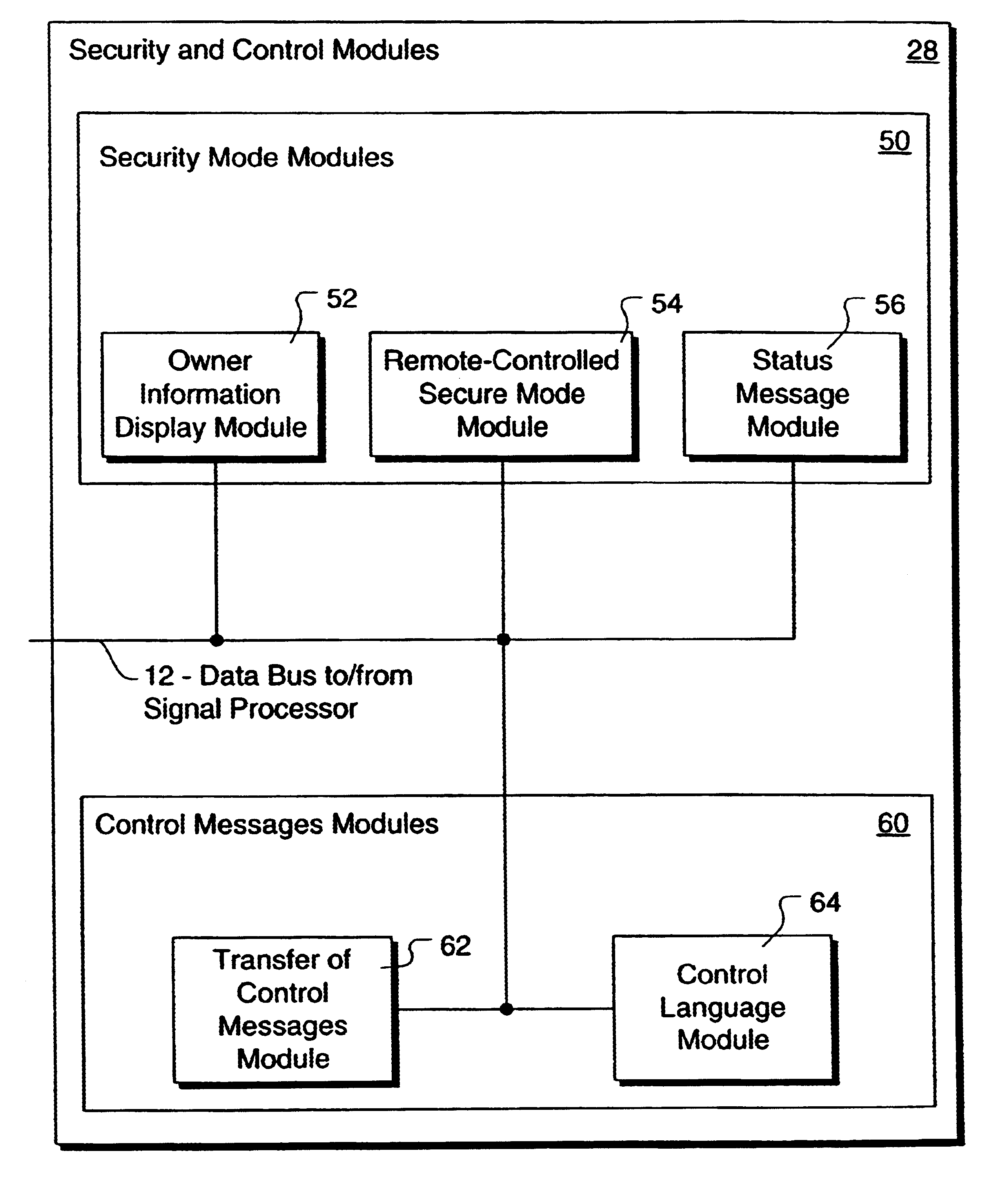
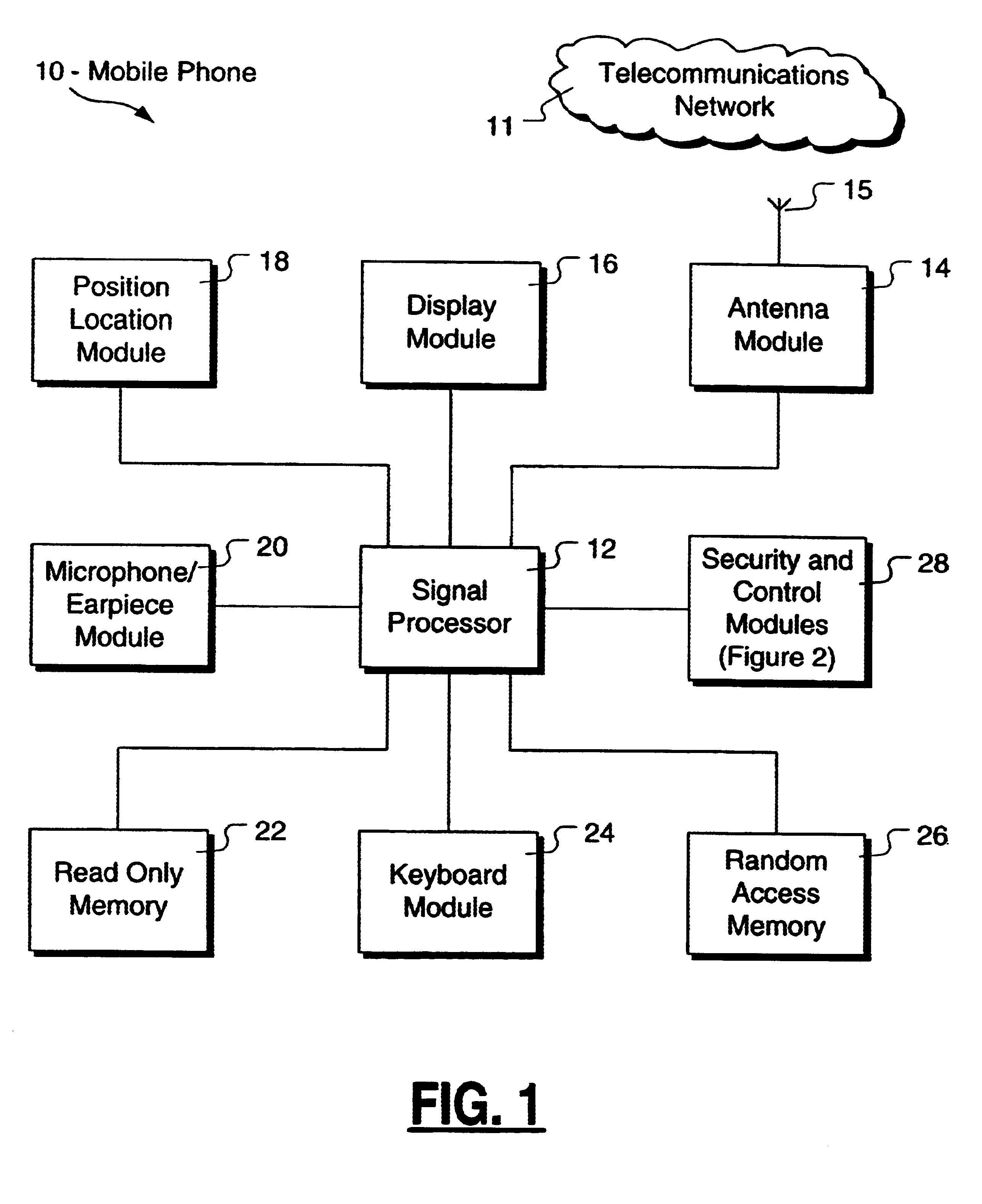
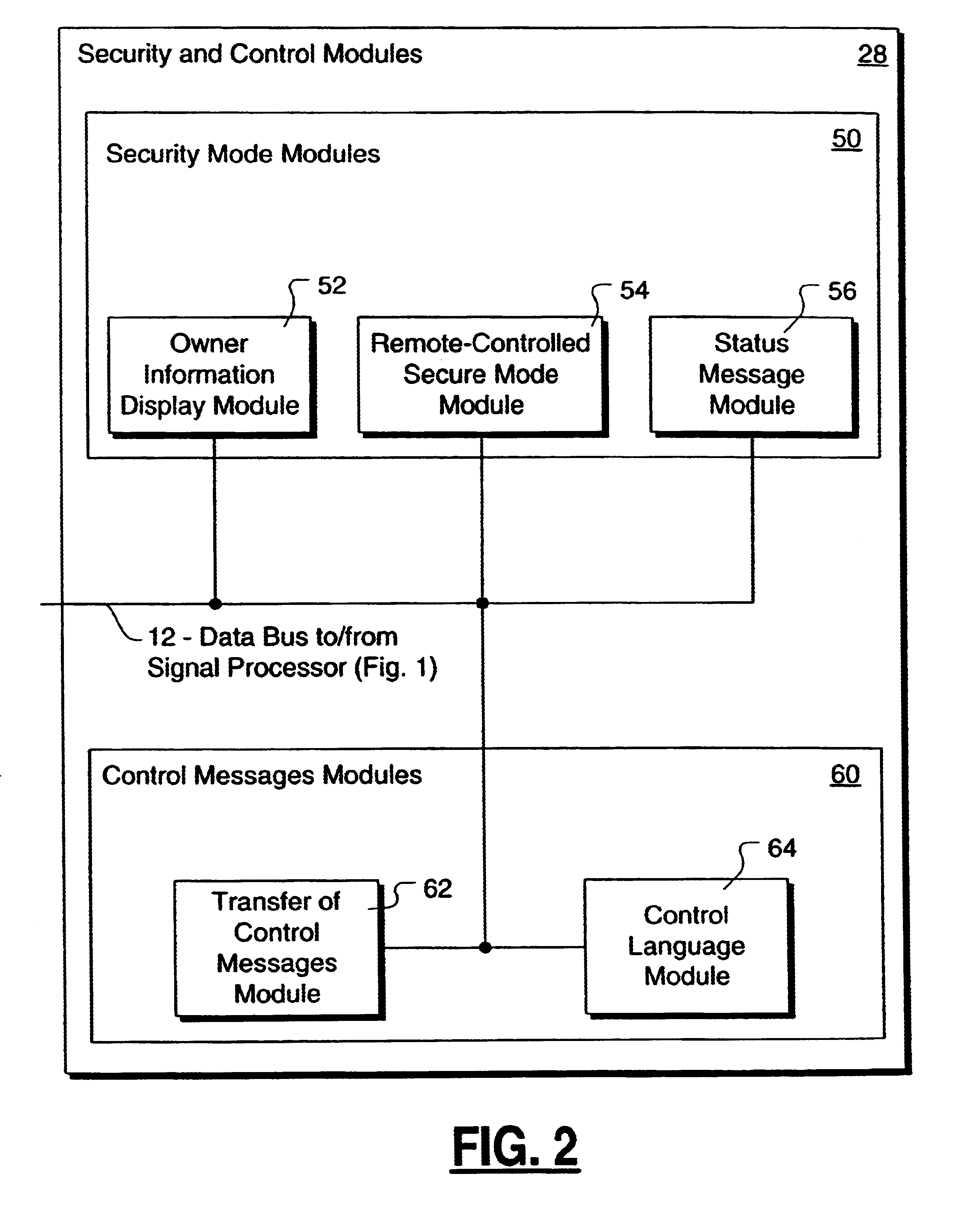
Method and apparatus for controlling and securing mobile phones that are lost, stolen or misused
InactiveUS6662023B1Unauthorised/fraudulent call preventionEavesdropping prevention circuitsSecure stateStart up
A method and apparatus is provided for controlling a mobile phone when it has been lost or stolen in order to prevent its use except to help the owner find it. Controlling the phone remotely may be implemented via a known Short Messaging System, for example. The security features provided are as follows: (1) Displaying contact information (phone number) of the owner on screen when the mobile phone can not start up normally, for example, due to an incorrect security code entry; (2) Setting the mobile phone in a secure state where it can only be used to call one number (Emergency calls are of course always possible.); and (3) Commanding the mobile phone to send information about its location and usage via SMS to a given number.
Owner:NOKIA TECHNOLOGLES OY
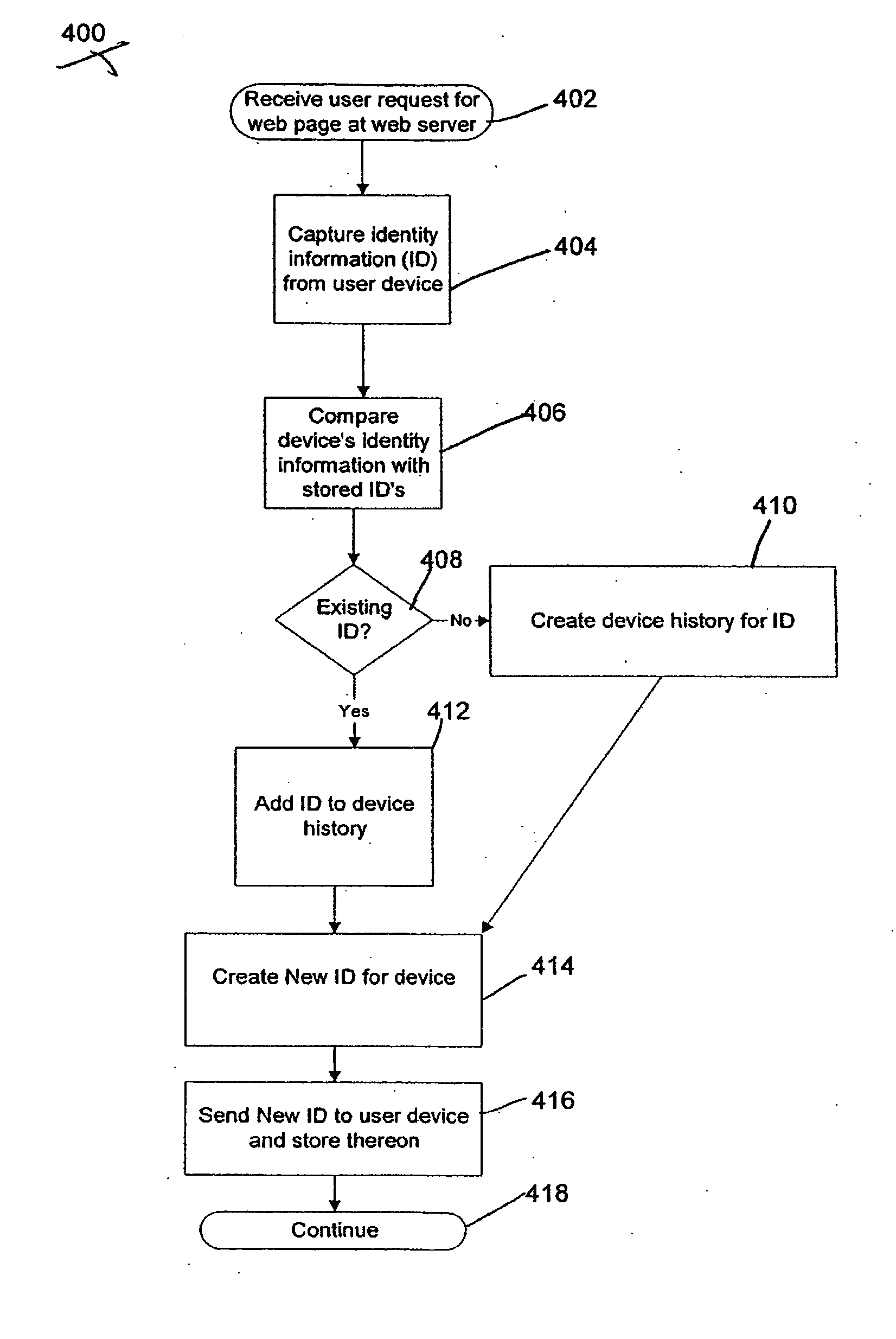
System and method for fraud monitoring, detection, and tiered user authentication
The present invention provides systems and methods for authenticating access requests from user devices by presenting one of a plurality of graphical user interfaces selected depending on a perceived risk of fraud associated with the devices. User devices are identified with fingerprinting information, and their associated risks of fraud are determined from past experience with the device or with similar devices and from third party information. In preferred embodiments, different graphical user interfaces are presented based on both fraud risk and, in the case of a known user, usability. In preferred embodiments, this invention is implemented as a number of communicating modules that identify user devices, assess their risk of fraud, present selected user interfaces, and maintain databases of fraud experiences. This invention also includes systems providing these authentication services.
Owner:ORACLE INT CORP
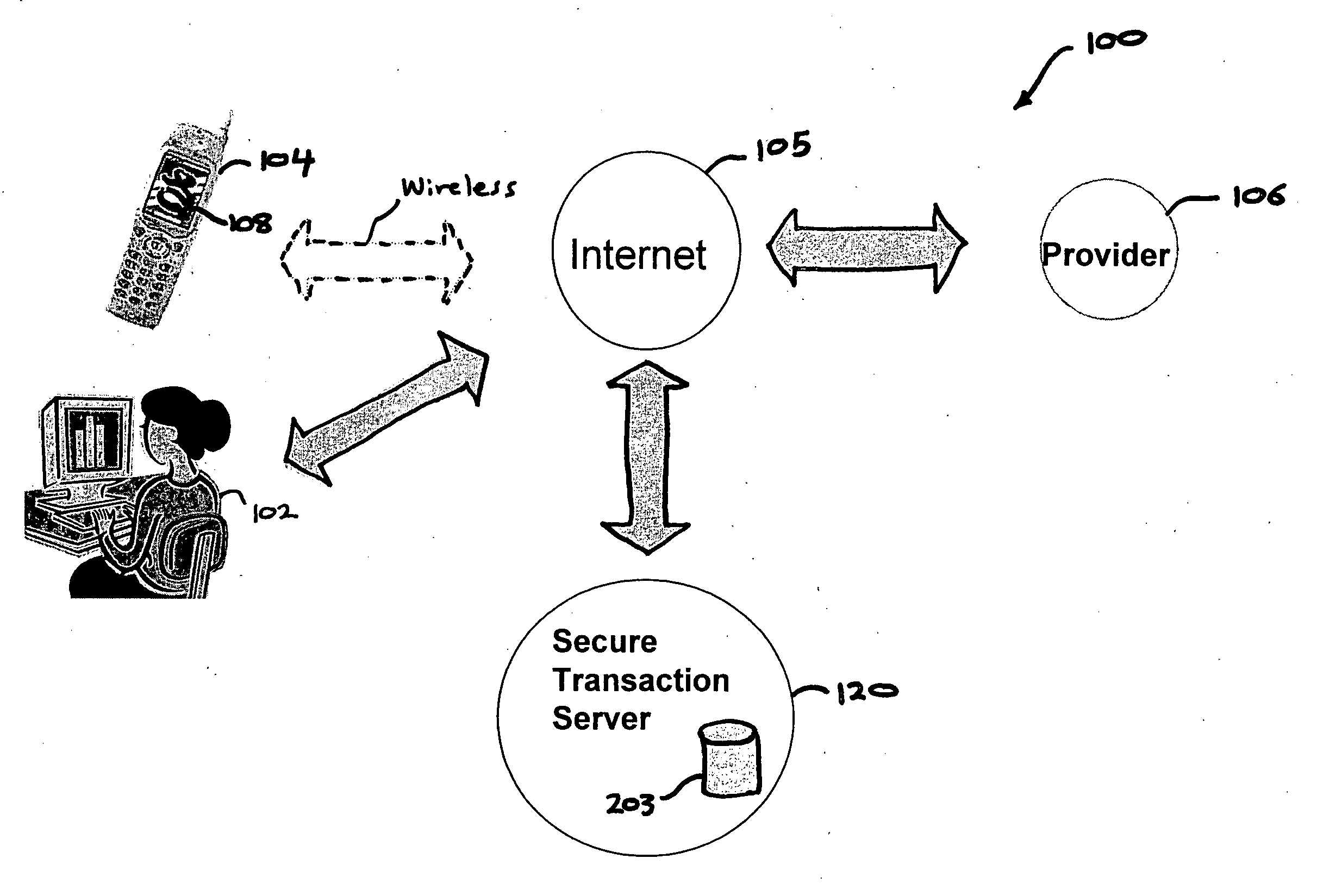
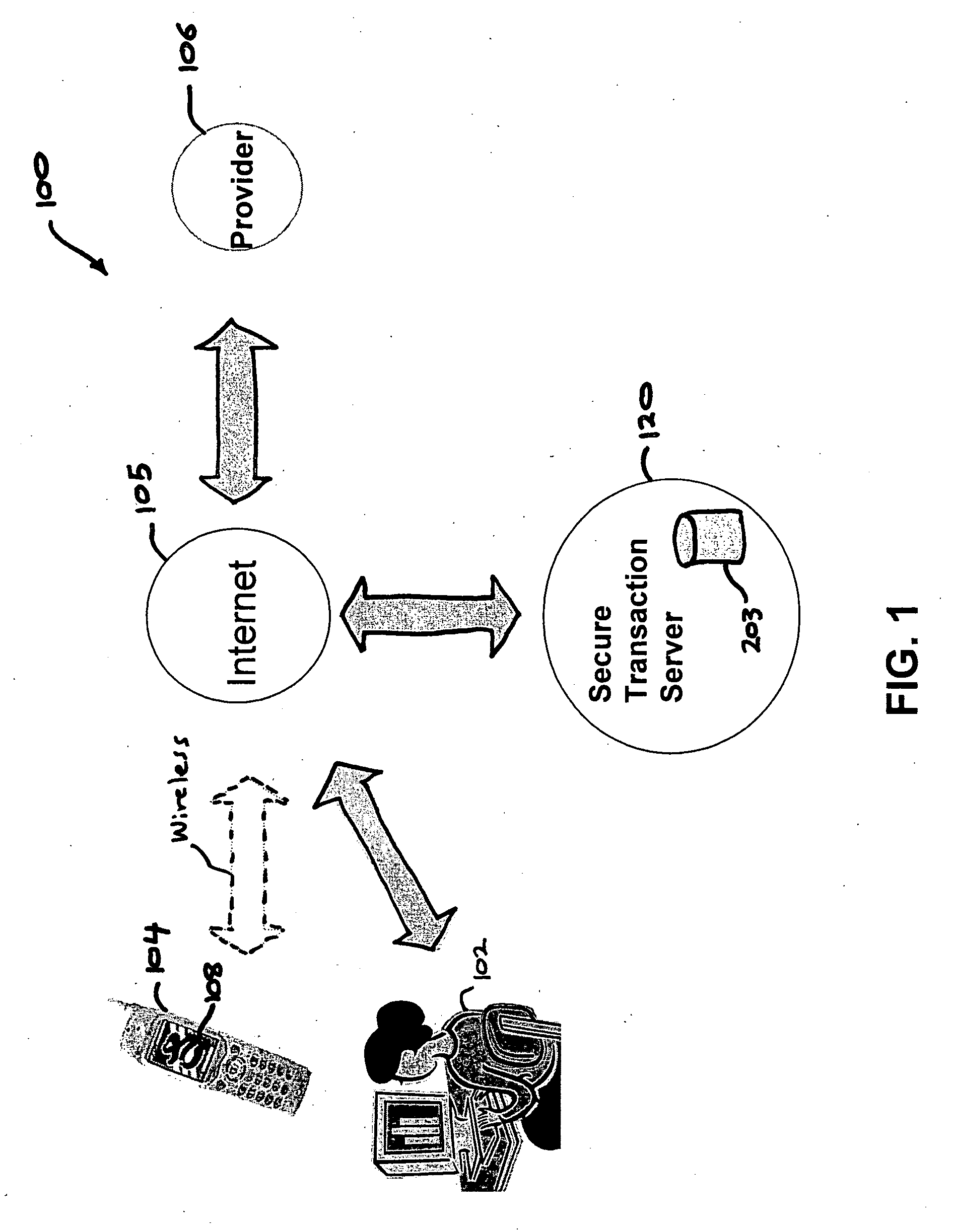
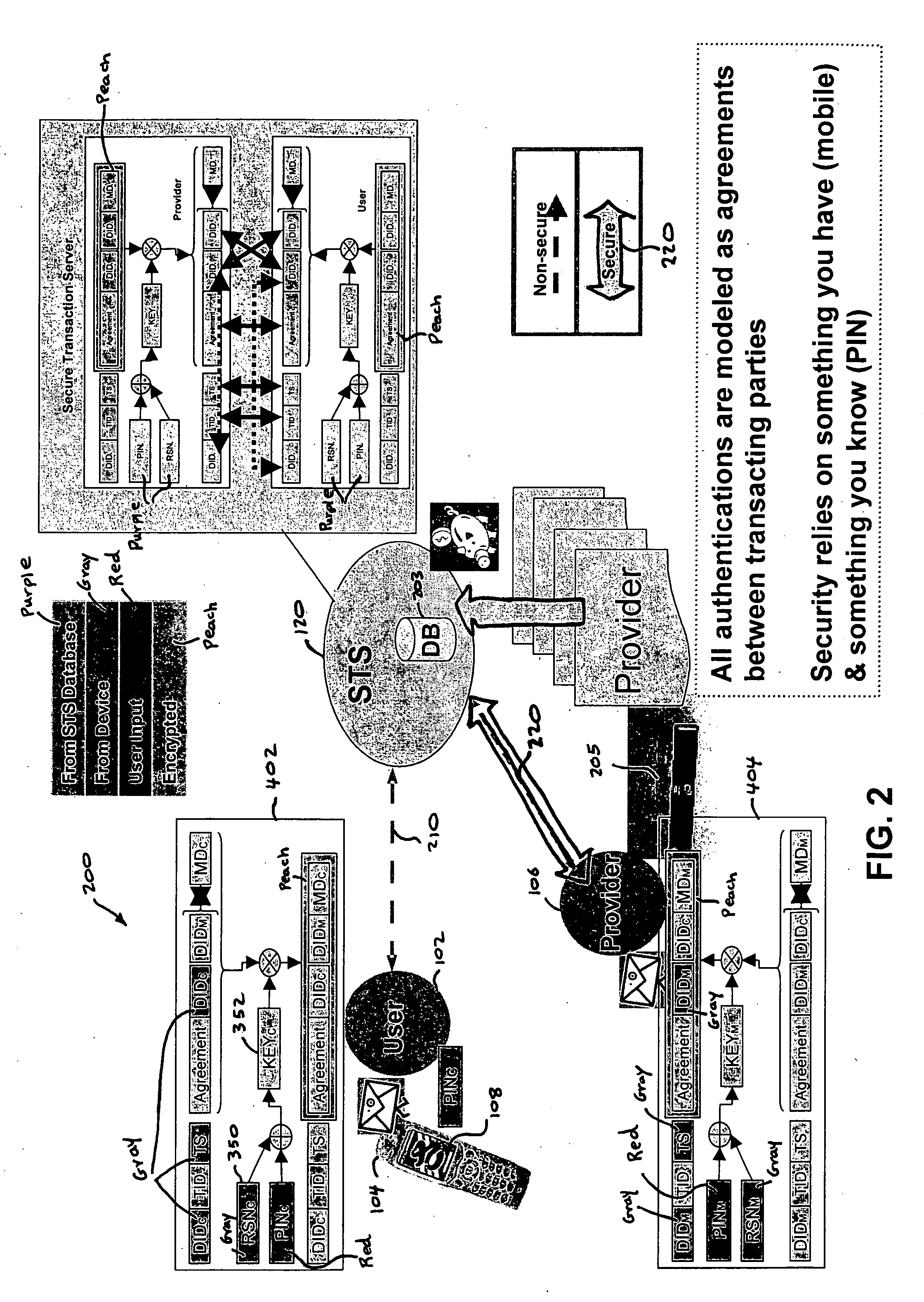
Authentication services using mobile device
InactiveUS20060206709A1Payment architectureATM softwaresInternet Authentication ServiceMobile device
A method, and an apparatus performing the method, is provided by authenticating a mobile device communicably connectable to a wireless network by an authentication parameter from a secure transaction server (STS), as a mobile device authenticator; providing an STS correlation between a personal identification entry (PIE) and the mobile device authenticator; and inputting, by a user, the PIE and a provider action, to the mobile device authenticator to transmit a transformed secure user authenticable authorization request to the STS over the wireless network to authorize an action with a provider.
Owner:PCMS HOLDINGS INC
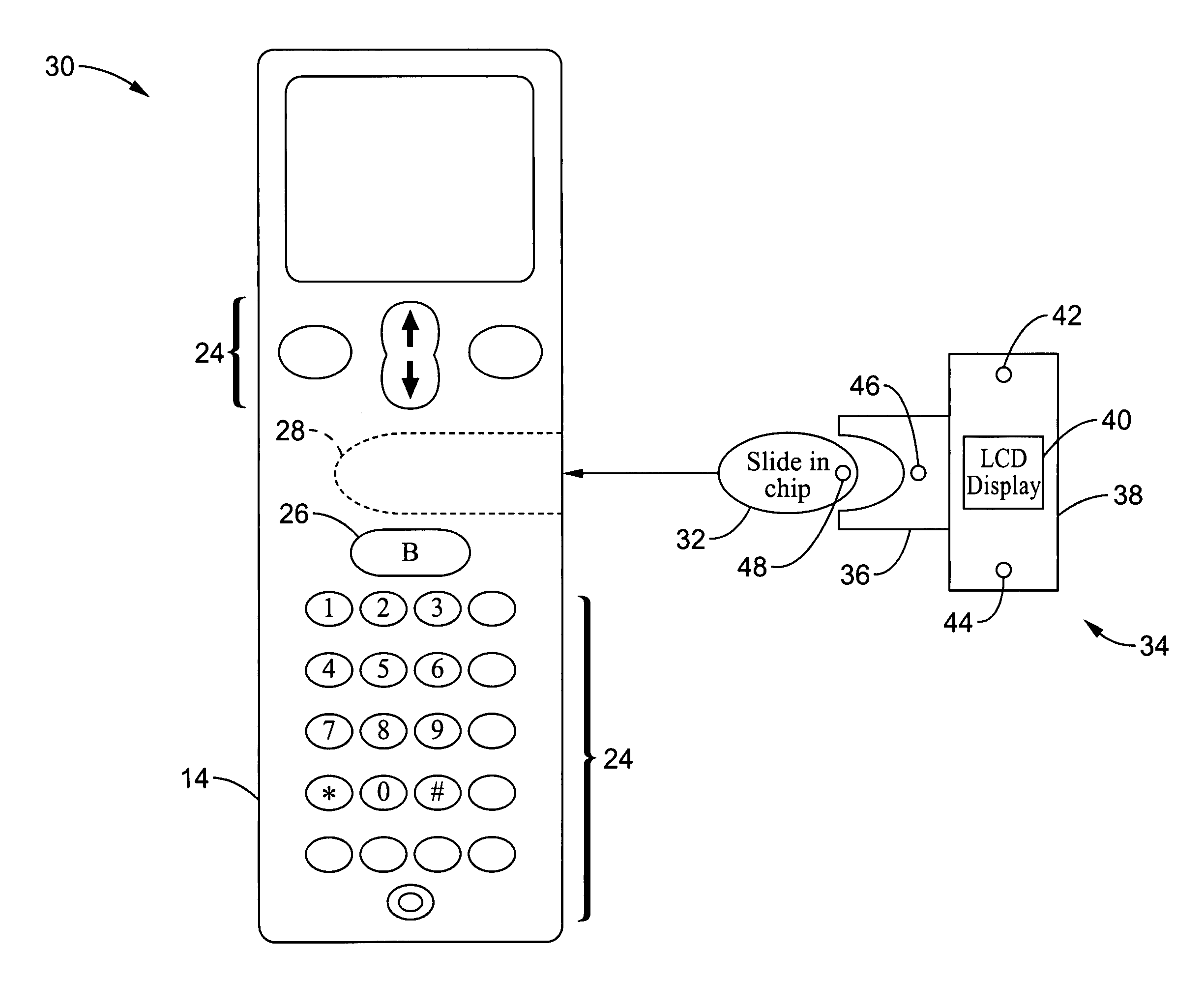
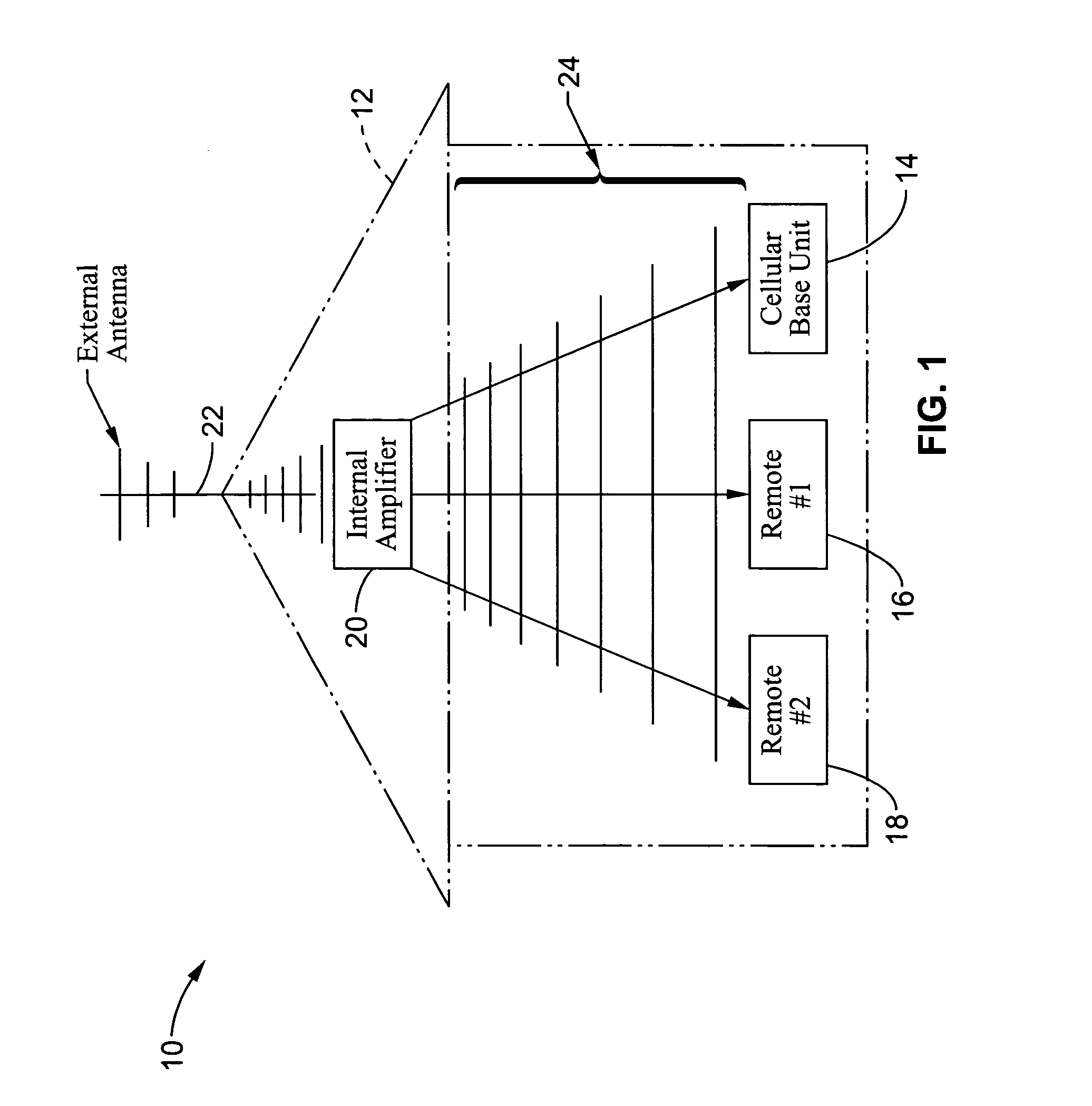
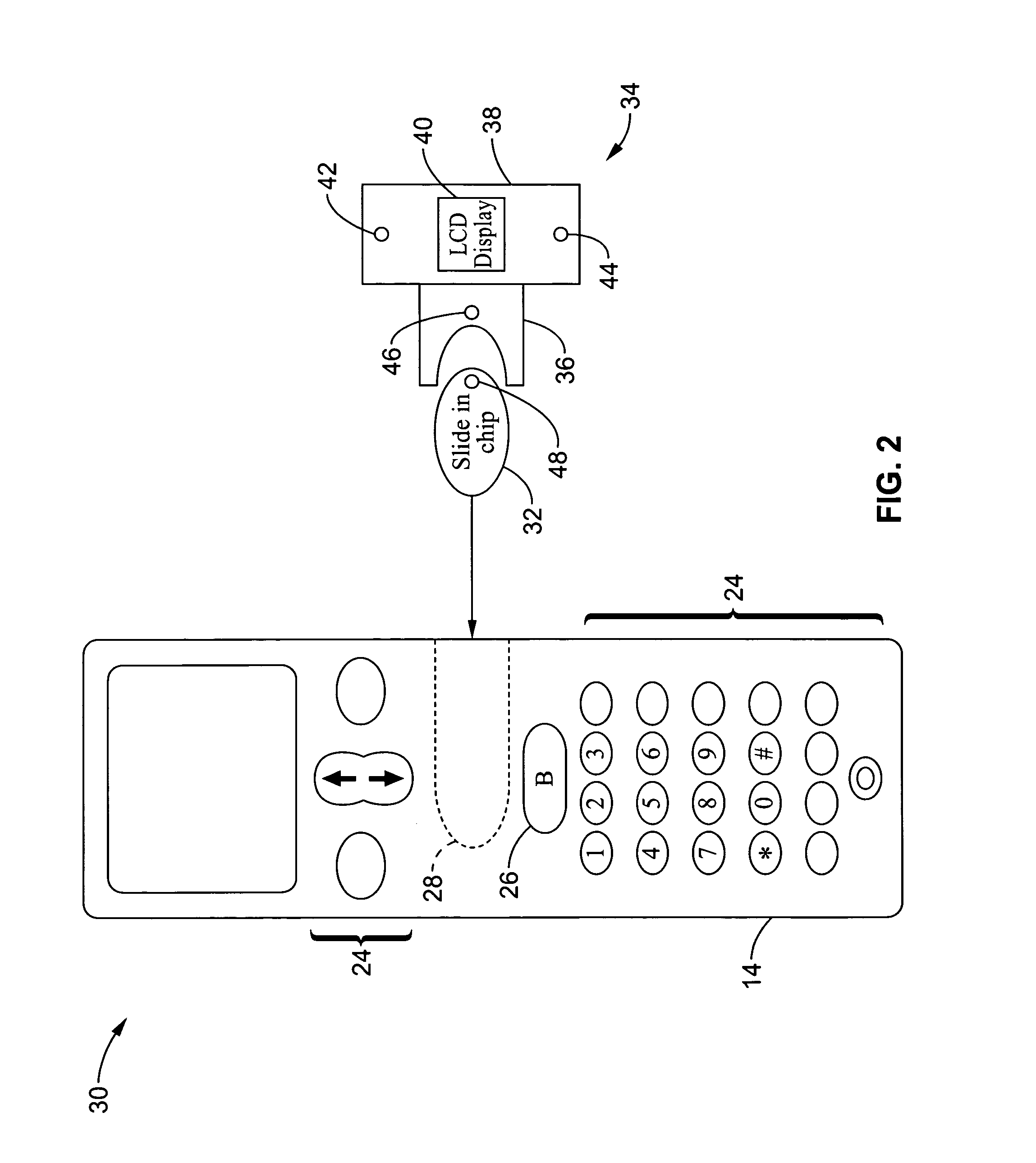
Wireless communications apparatus and method
InactiveUS7146191B2Easy to be stolenProcess safetyUnauthorised/fraudulent call preventionEavesdropping prevention circuitsInterconnectivityDisplay device
A wireless communication method and apparatus are described for increasing security for communication devices utilizing identification chips for accessing wireless networks and the associated billing for services. One aspect of the invention is an enhanced phone chip and a communications device adapted to engage the enhanced phone chip, which then cannot be installed or removed from the wireless communications device by unauthorized users. In one embodiment a security key mates to the identification chip and is utilized for installing and removing the enhanced phone chip. The security key preferably has a display upon which information about the communication device is displayed prior to removing the security key after installing the enhanced phone chip. Other aspects of the invention include wireless base station communication devices which support wired (dedicated and non-dedicated), and more preferably wireless extensions, while providing sharing of wireless network resources and interconnectivity between base station and extensions.
Owner:US THERMOELECTRIC CONSORTIUM
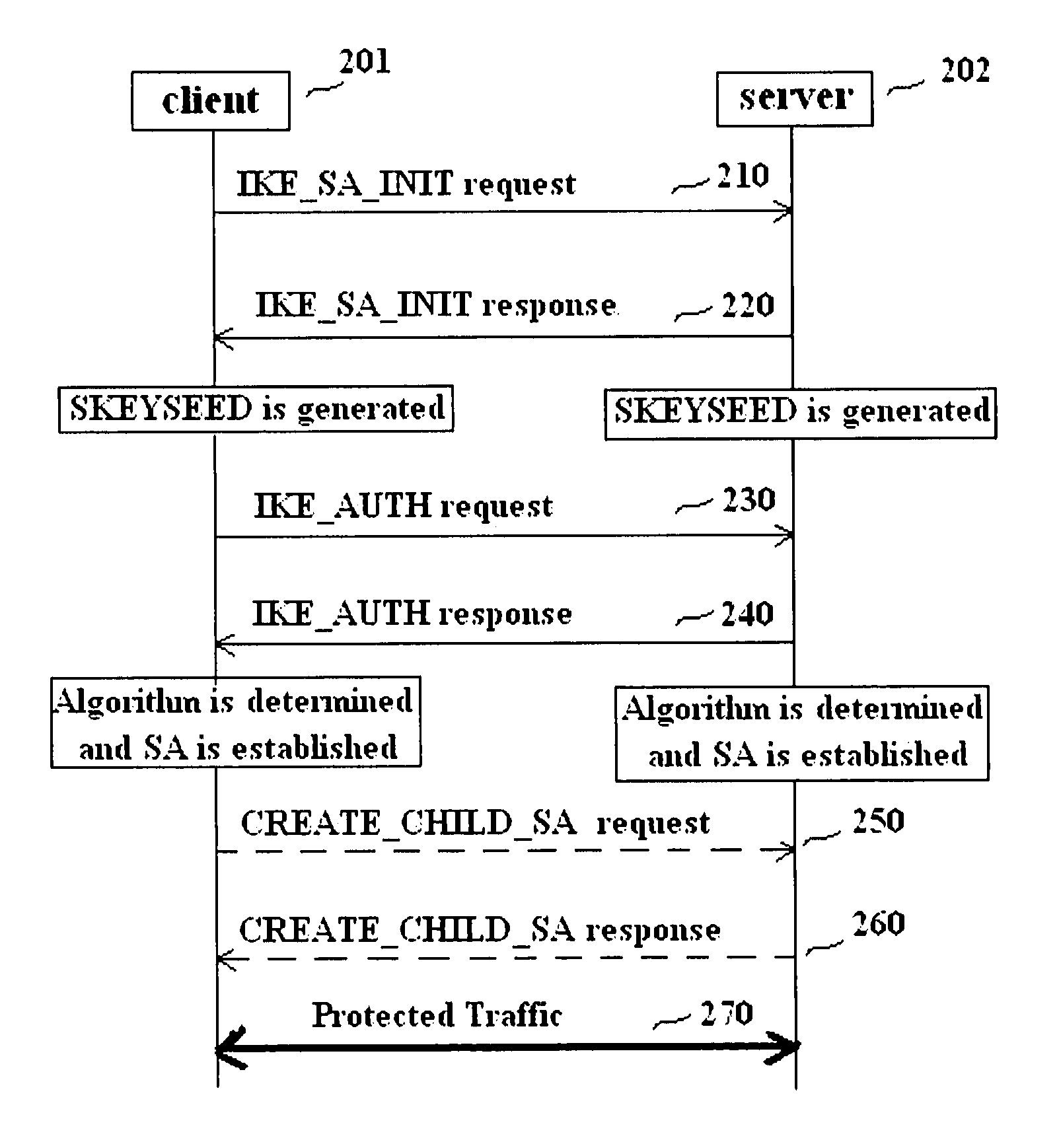
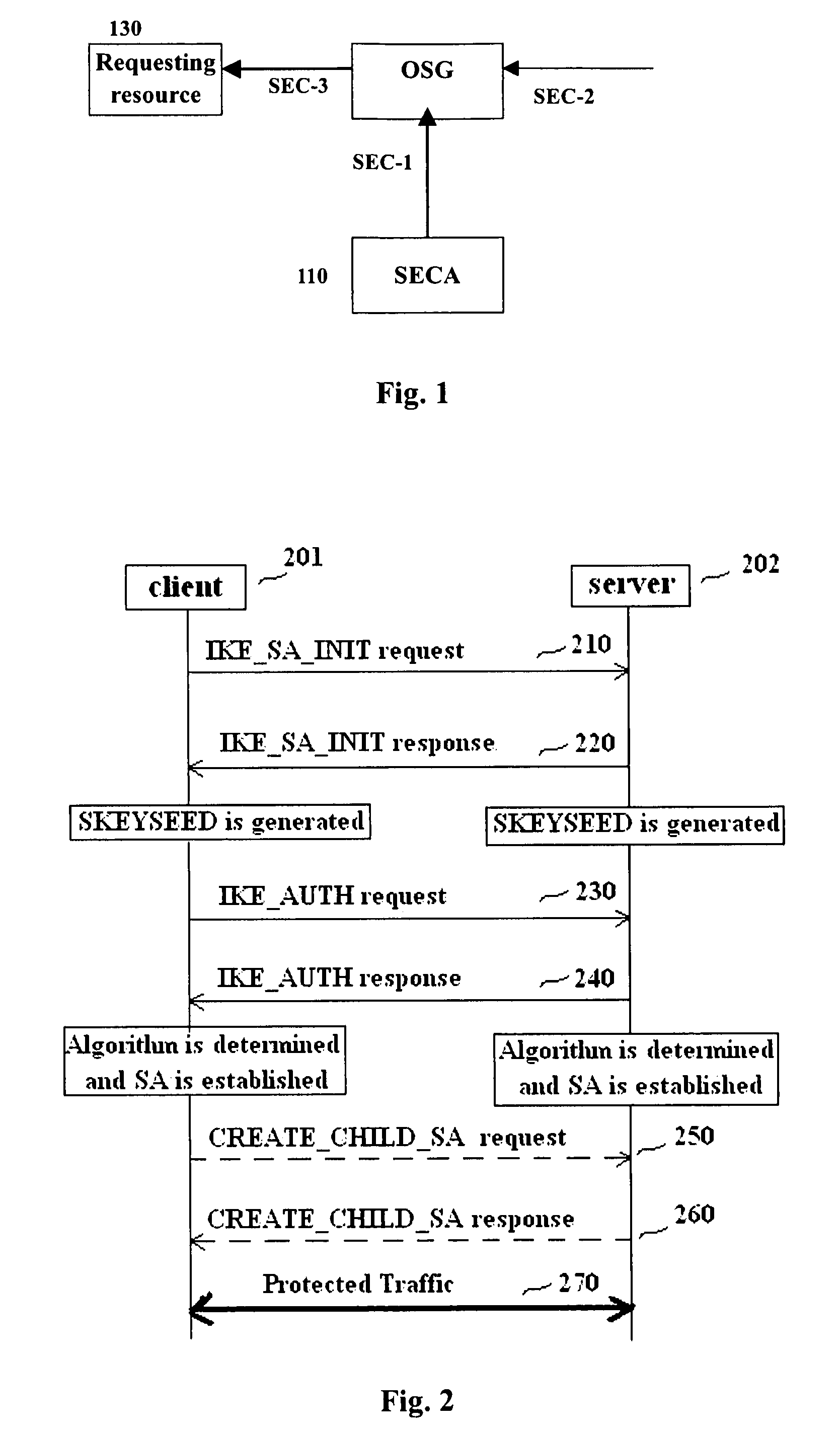
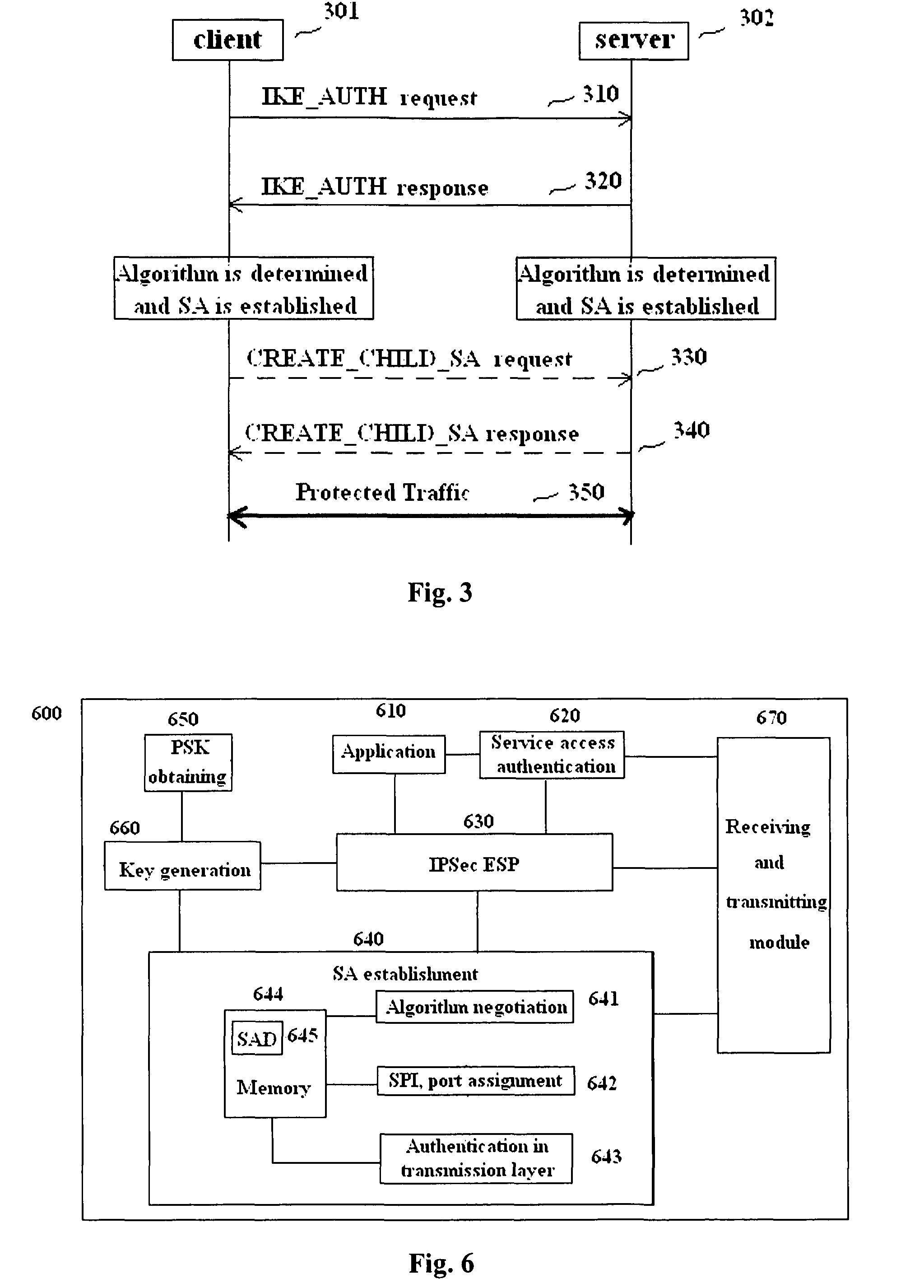
Methods and entities using IPSec ESP to support security functionality for UDP-based traffic
ActiveUS8639936B2Improve efficiencyOptimize procedureUser identity/authority verificationComputer security arrangementsTraffic capacityIPsec
Owner:ALCATEL LUCENT SAS
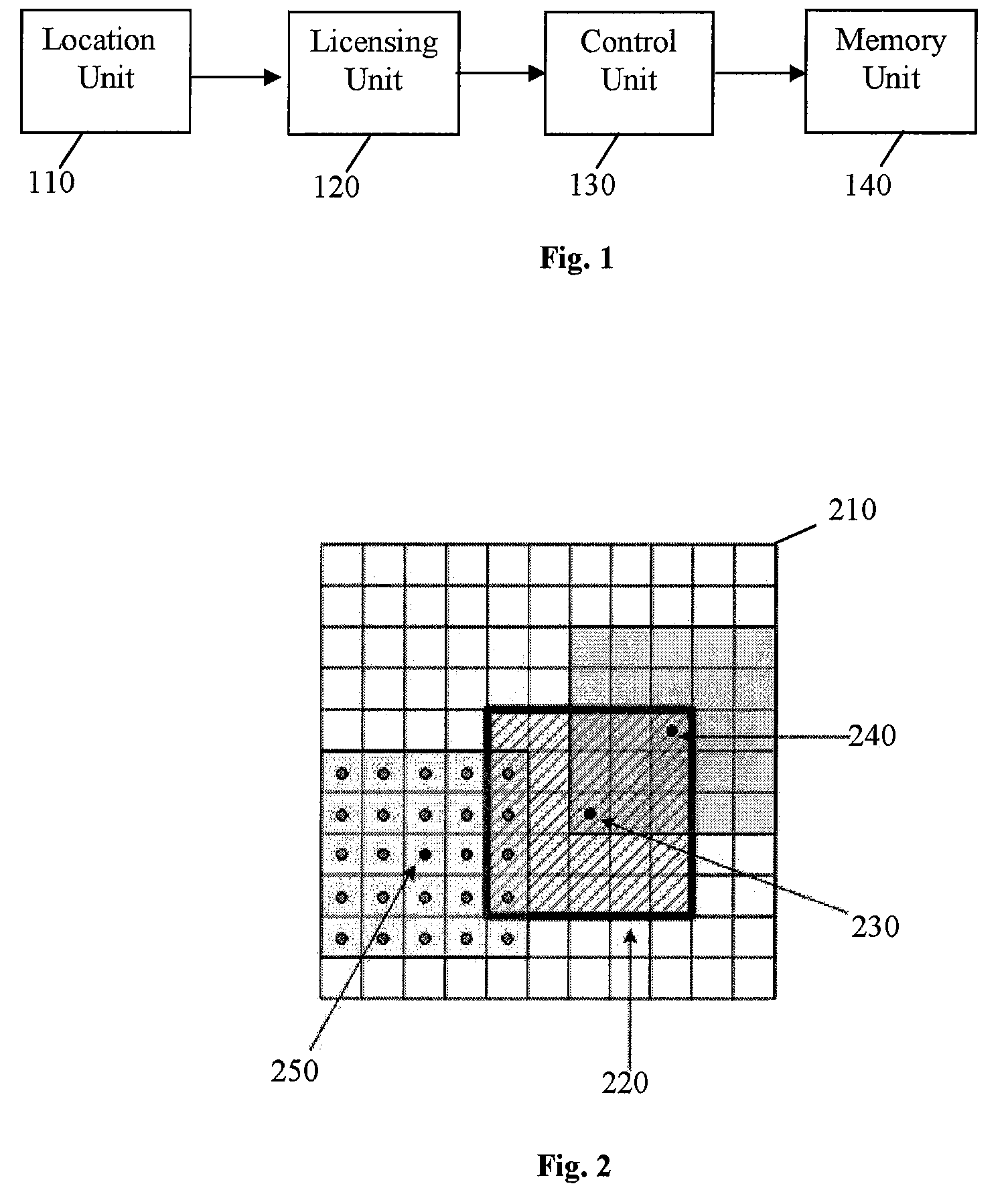
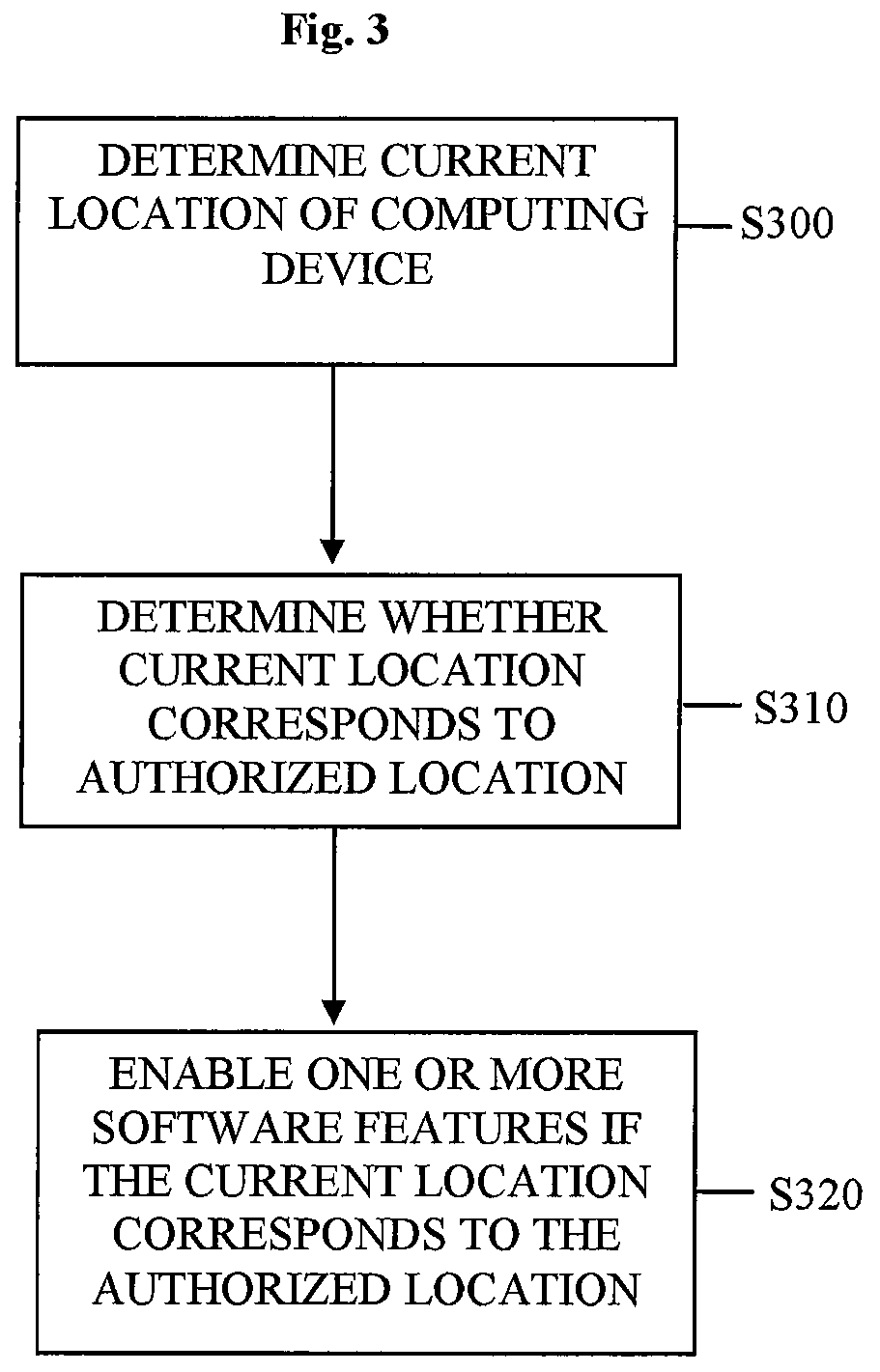
Location-based feature enablement for mobile terminals
ActiveUS8583924B2Digital data processing detailsUser identity/authority verificationComputer terminalComputer science
Owner:HAND HELD PRODS
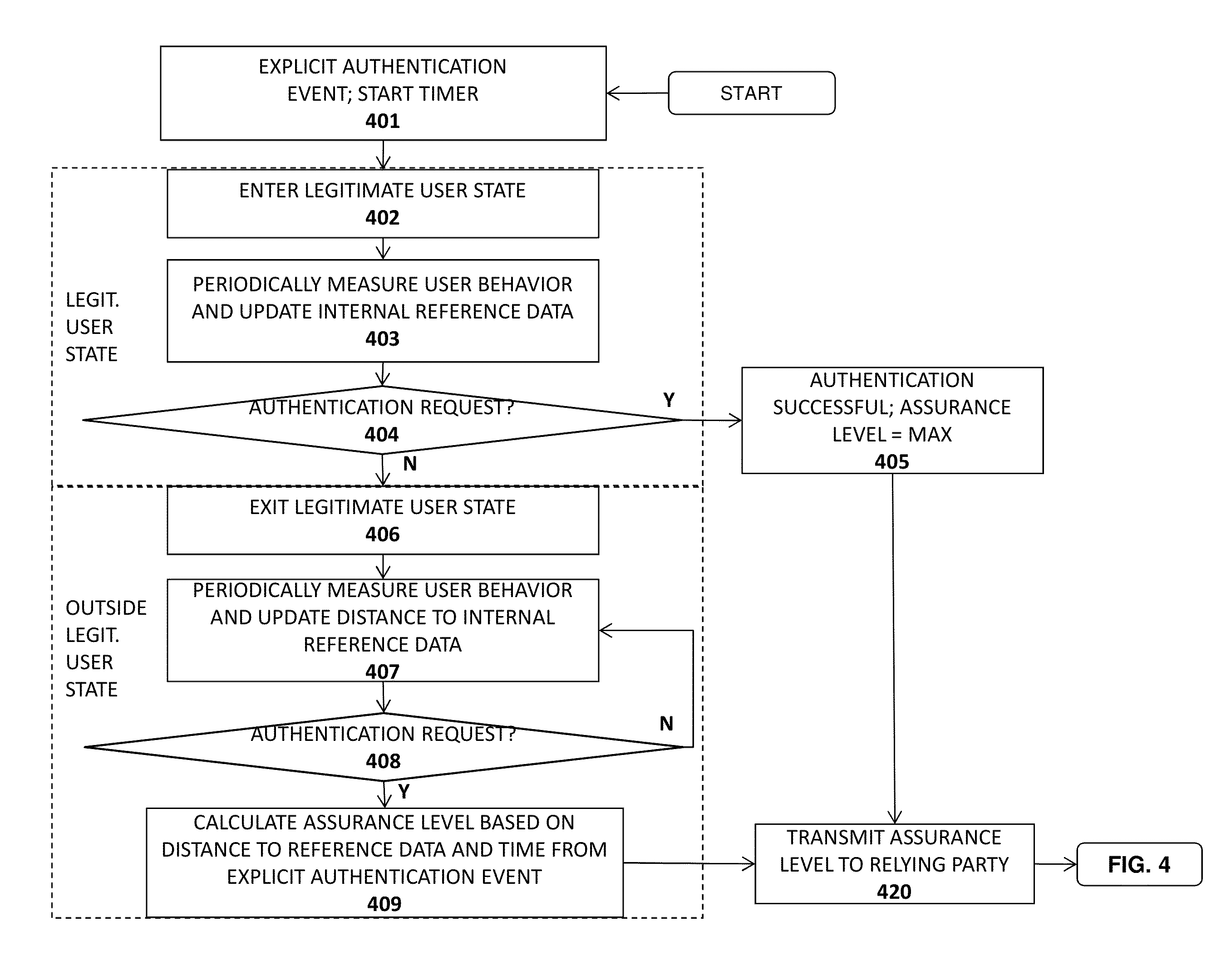
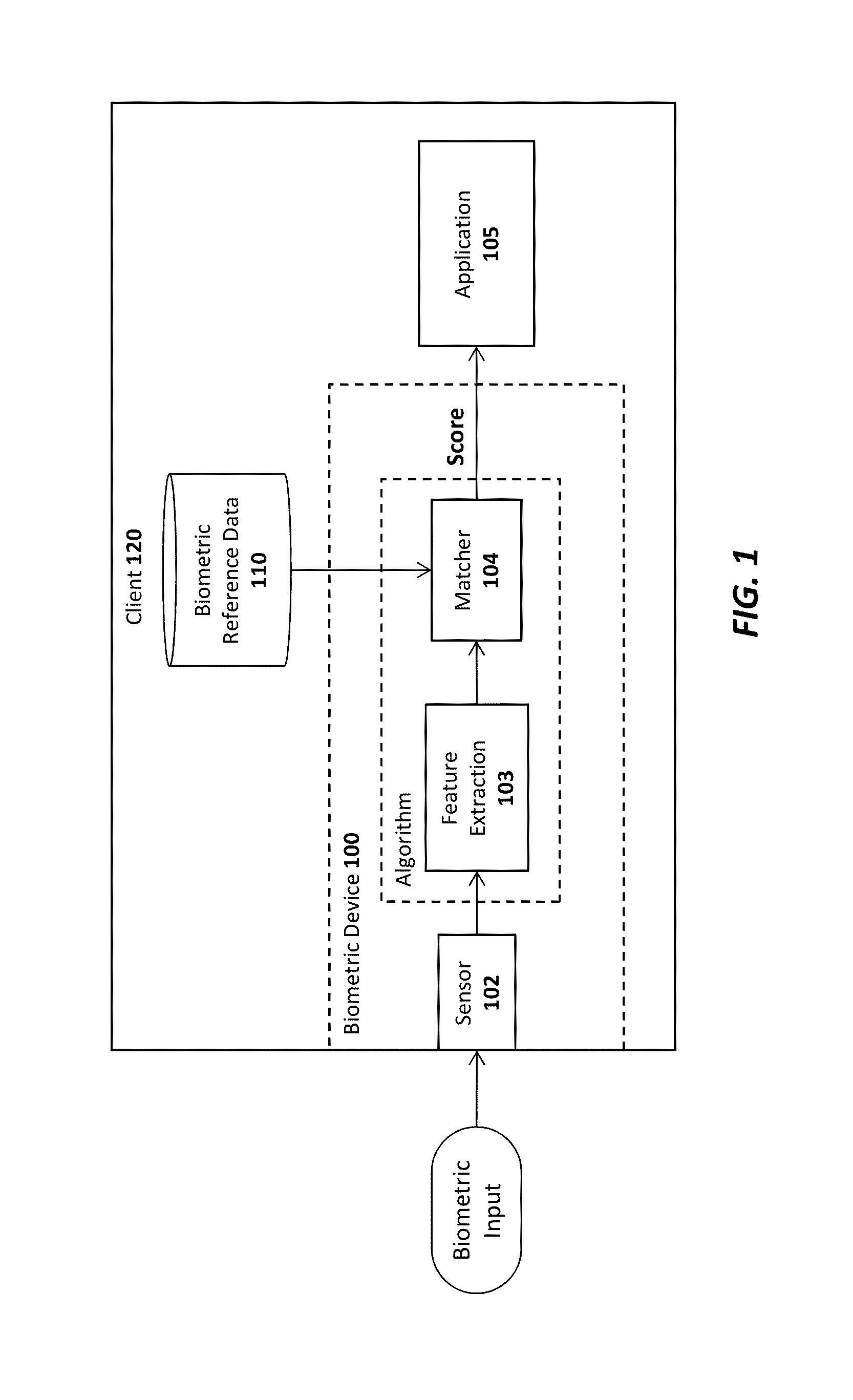
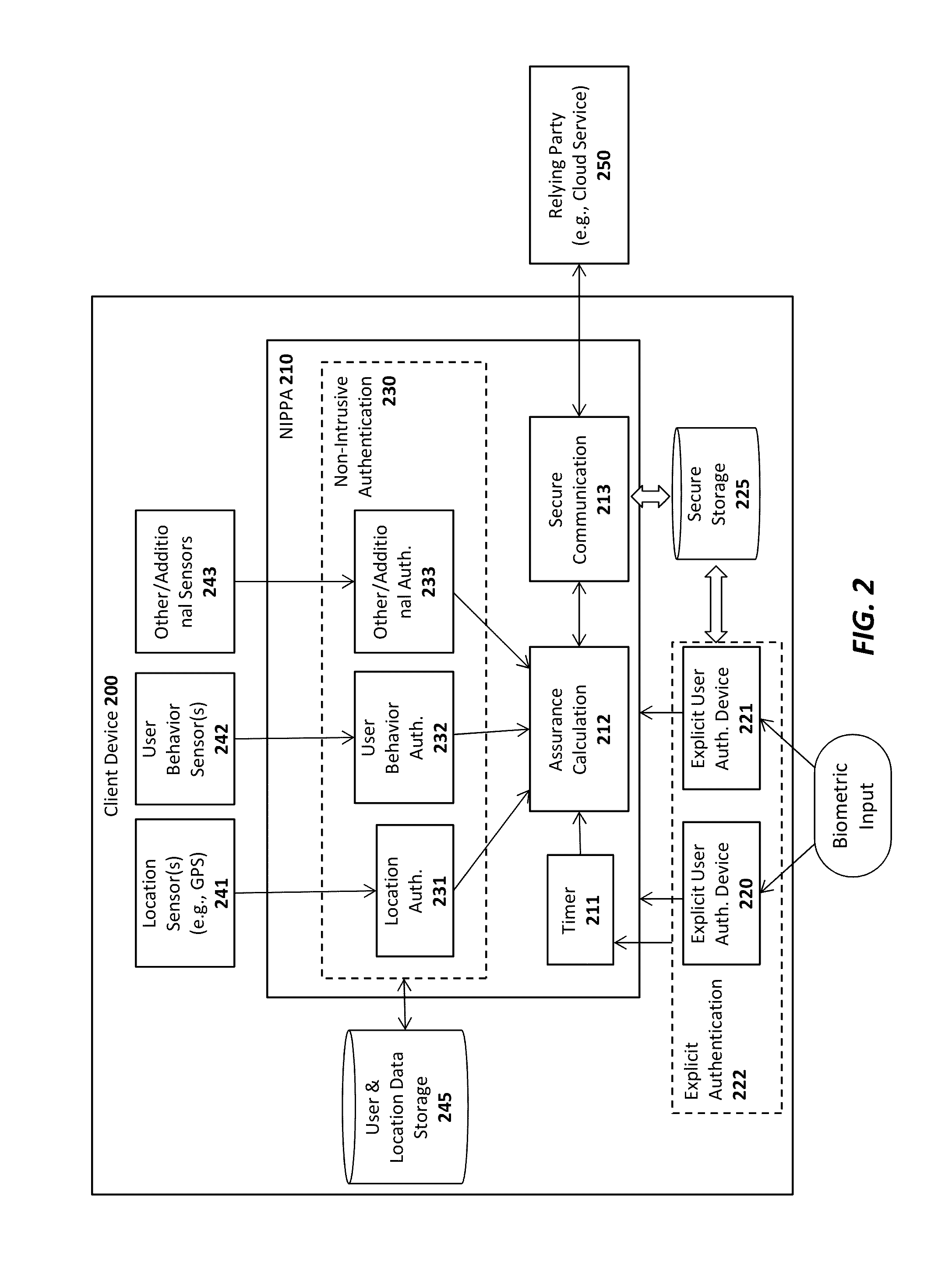
Advanced authentication techniques and applications
ActiveUS20140289833A1Digital data processing detailsMultiple digital computer combinationsEngineeringDatabase
A system, apparatus, method, and machine readable medium are described for performing advanced authentication techniques and associated applications. For example, one embodiment of a method comprises: receiving a policy identifying a set of acceptable authentication capabilities; determining a set of client authentication capabilities; and filtering the set of acceptable authentication capabilities based on the determined set of client authentication capabilities to arrive at a filtered set of one or more authentication capabilities for authenticating a user of the client.
Owner:NOK NOK LABS
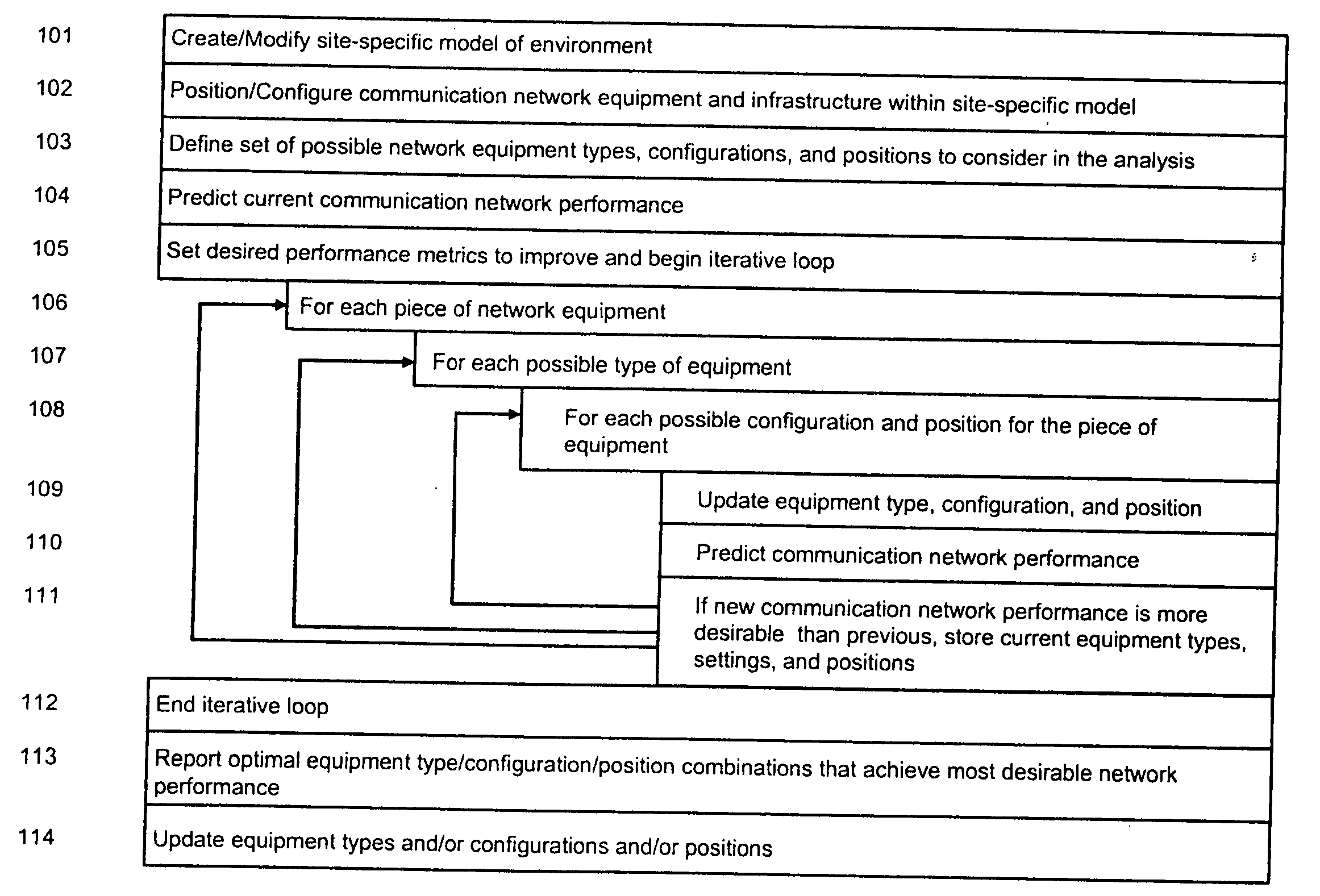
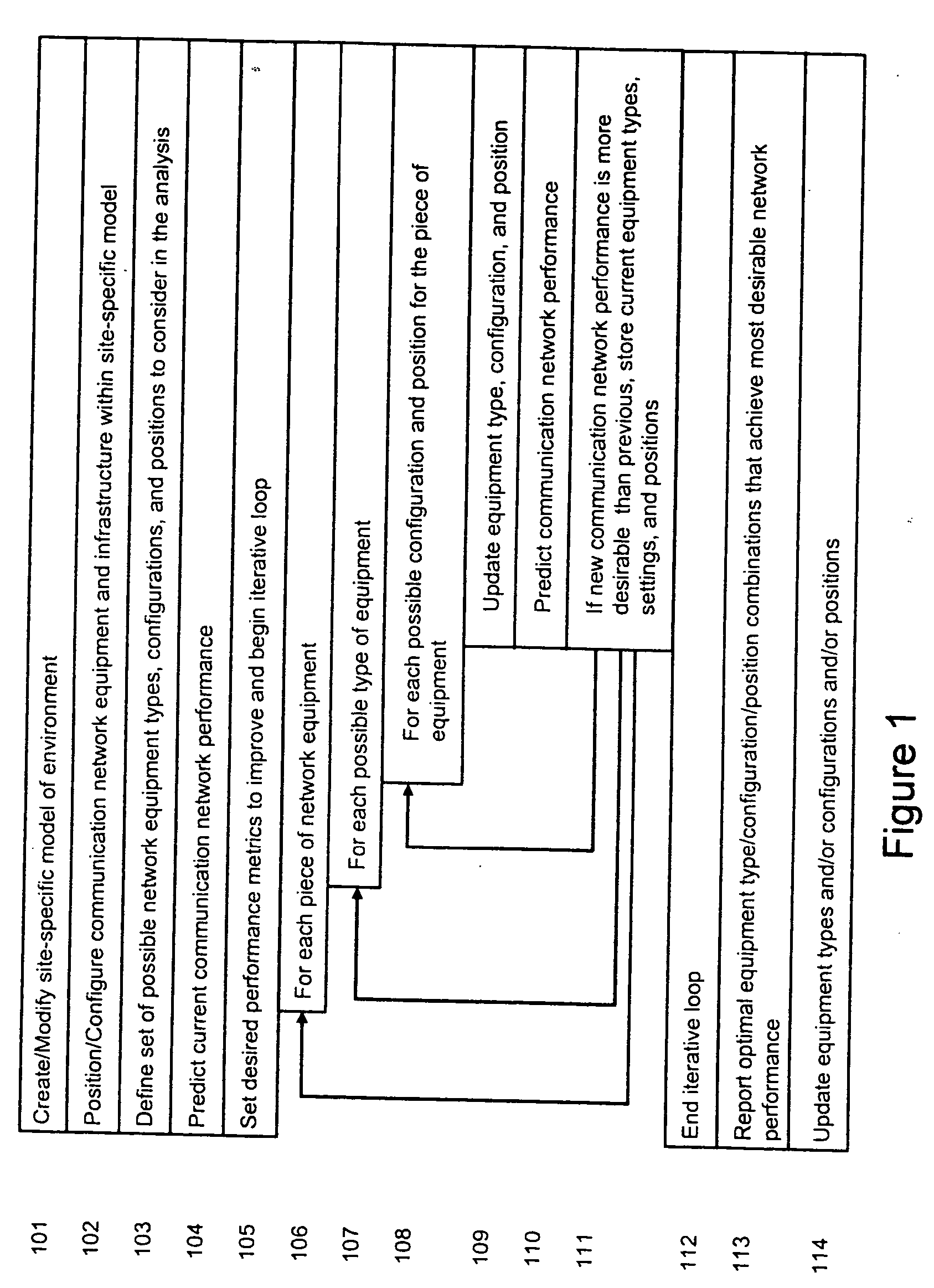
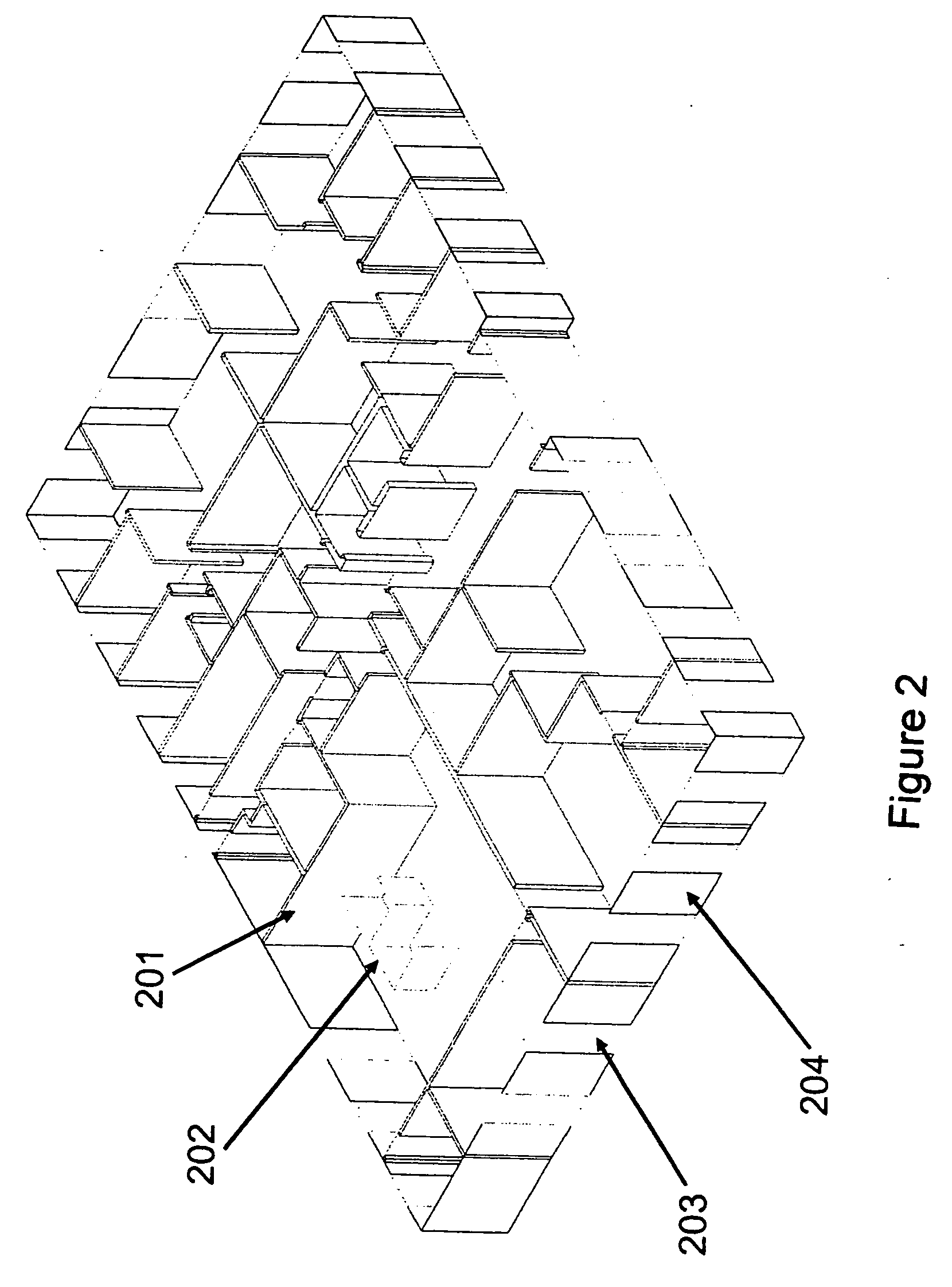
System and method for automated placement or configuration of equipment for obtaining desired network performance objectives and for security, RF tags, and bandwidth provisioning
ActiveUS20040236547A1Significant valueEasy to explainGeometric CADData taking preventionHard disc driveThe Internet
A method is presented for determining optimal or preferred configuration settings for wireless or wired network equipment in order to obtain a desirable level of network performance. A site-specific network model is used with adaptive processing to perform efficient design and on-going management of network performance. The invention iteratively determines overall network performance and cost, and further iterates equipment settings, locations and orientations. Real time control is between a site-specific Computer Aided Design (CAD) software application and the physical components of the network allows the invention to display, store, and iteratively adapt any network to constantly varying traffic and interference conditions. Alarms provide rapid adaptation of network parameters, and alerts and preprogrammed network shutdown actions may be taken autonomously. A wireless post-it note device and network allows massive data such as book contents or hard drive memory to be accessed within a room by a wide bandwidth reader device, and this can further be interconnected to the internet or Ethernet backbone in order to provide worldwide access and remote retrieval to wireless post-it devices.
Owner:EXTREME NETWORKS INC
Methods and systems for sharing risk responses between collections of mobile communications devices
Methods are provided for determining an enterprise risk level, for sharing security risk information between enterprises by identifying a security response by a first enterprise and then sharing the security response to a second enterprise when a relationship database profile for the first collection indicates the security response may be shared. Methods are also provided for determining whether to allow a request from an originating device where the request may have been initiated by a remote device.
Owner:LOOKOUT MOBILE SECURITY
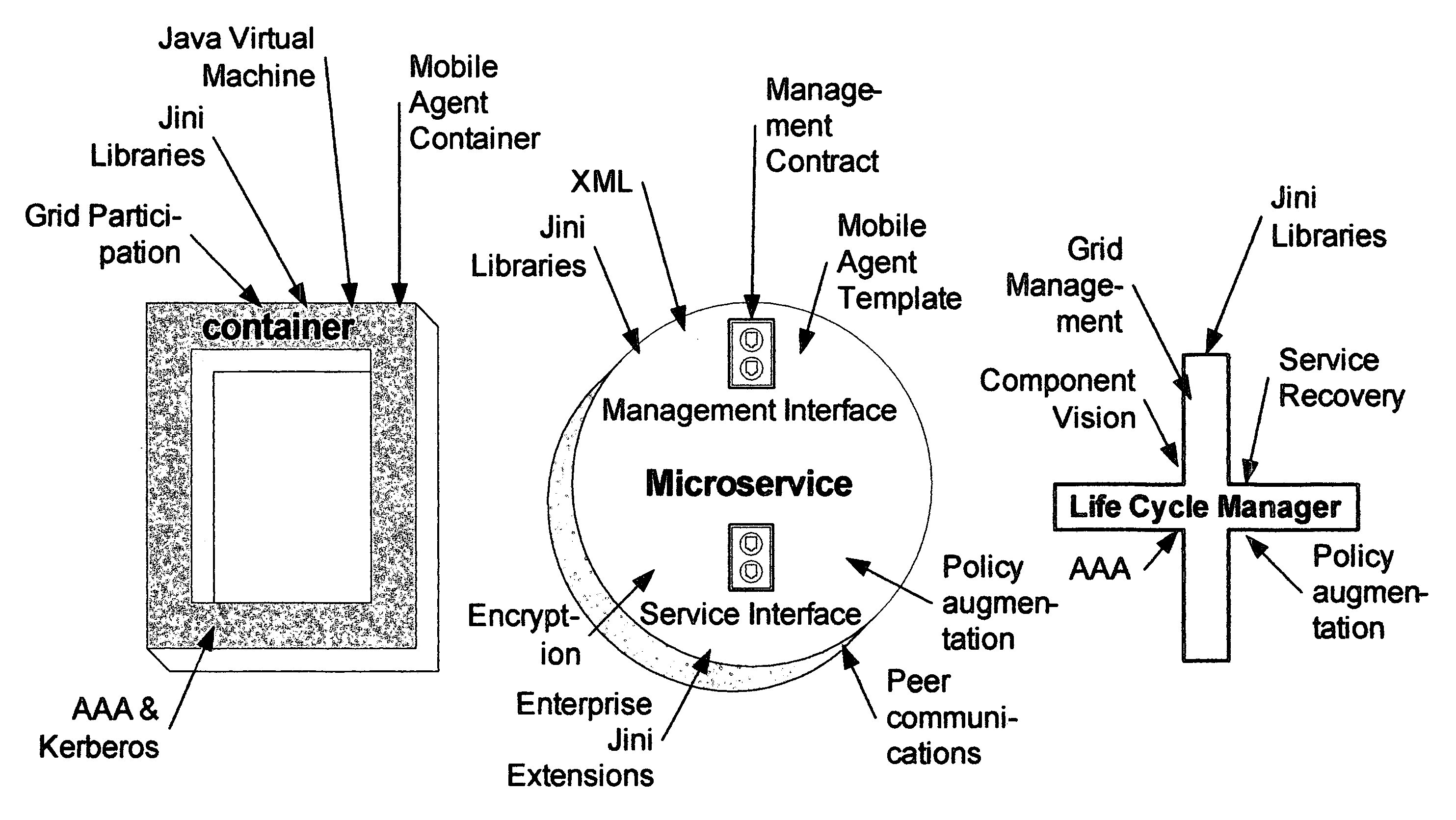
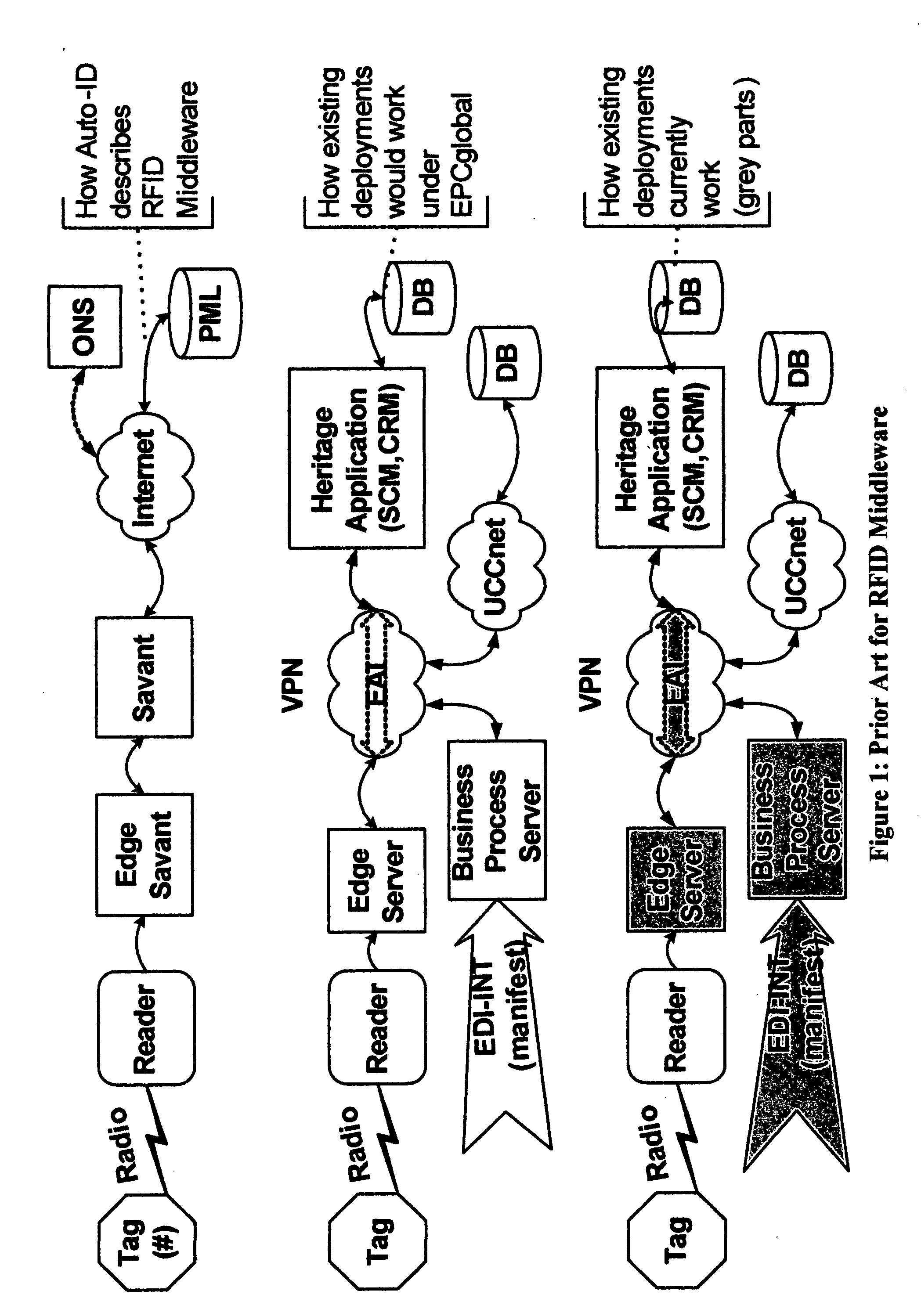
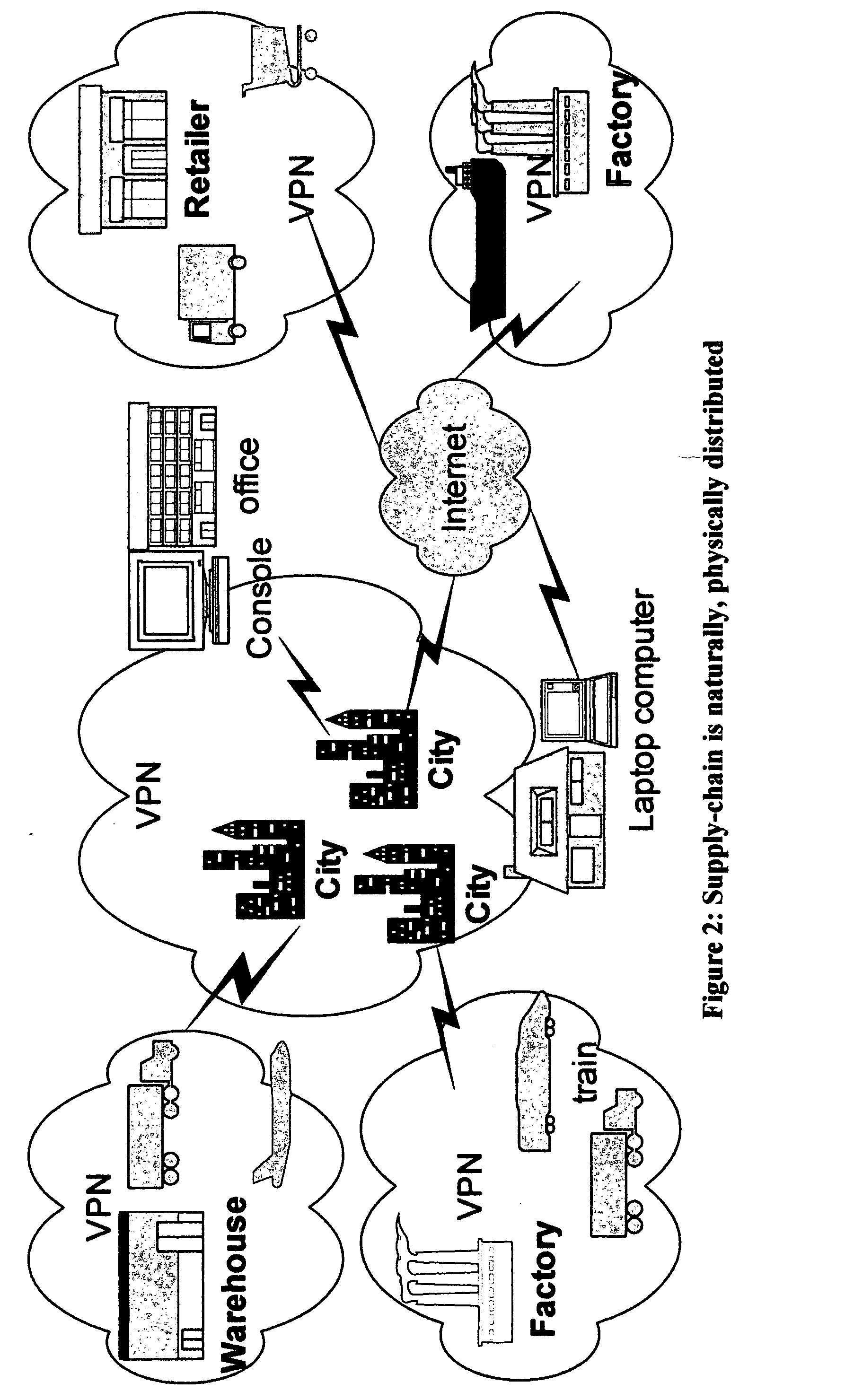
System and method for use of mobile policy agents and local services, within a geographically distributed service grid, to provide greater security via local intelligence and life-cycle management for RFlD tagged items
InactiveUS20070112574A1Low costIntegration costMultiple digital computer combinationsProgram controlDistributed servicesRadio frequency
This invention provides a system, method, and software program for providing software intelligence to Radio Frequency Identity (RFID) tags. Utilizing the unique characteristics of the Service Grid, mobile software agents can relocate in close proximity to RFID tagged items. Once associated with the tag, these RFID agents migrate near where items are identified to provide local control, environmentally responsive policy, and ongoing permanent data capture & history. These RFID agents respond to events as circumstances require. They transport data and policy between supply-chain partners when the partners participate in a secure extranet. Enhanced service grids composed of distributed agents, comprising numerous services, facilitates supply-chain security and integration as virtual software service agents, including virtual RFID tags, are directed from one computer to another computer in response to changing conditions.
Owner:GREENE WILLIAM SPROTT
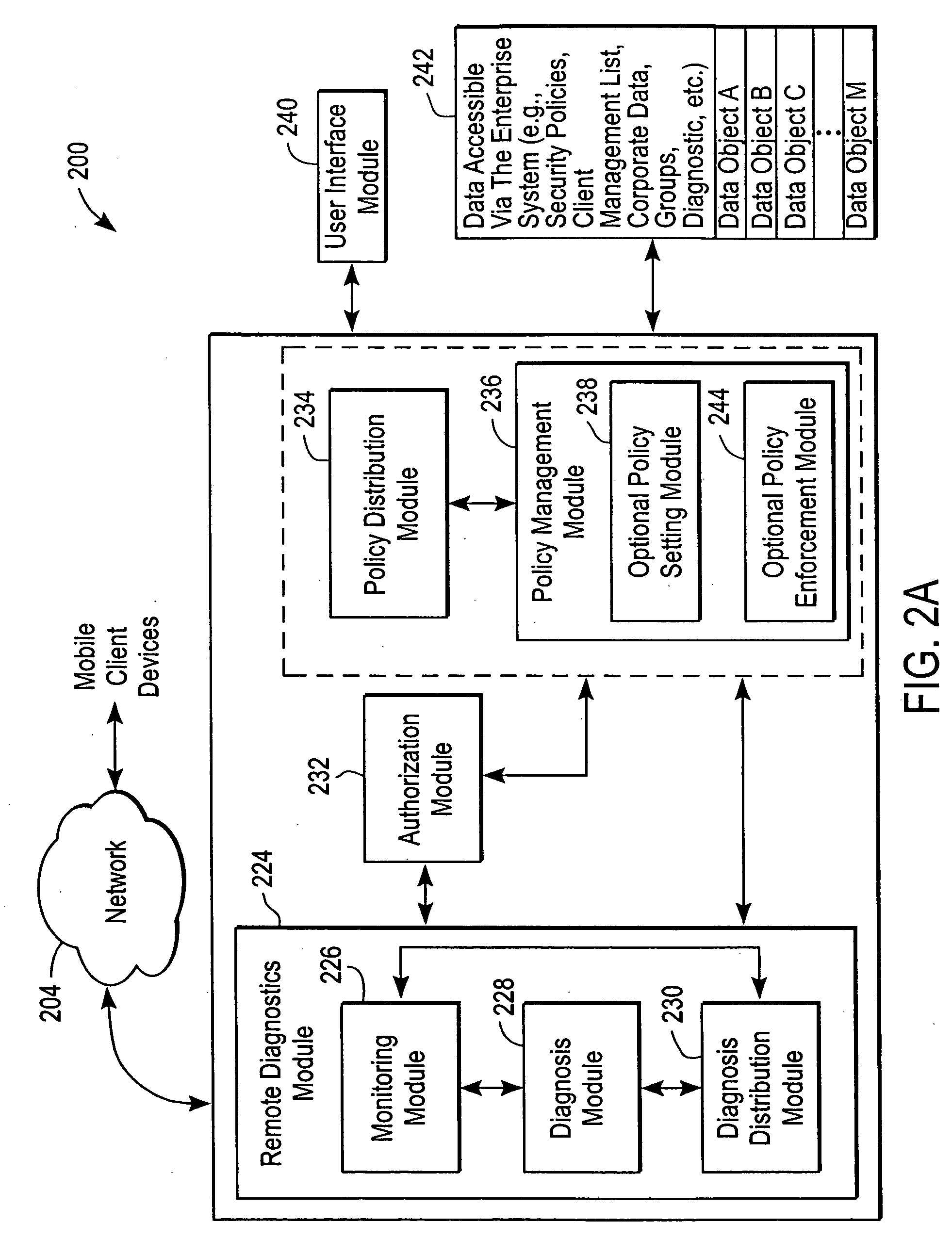
Administration of protection of data accessible by a mobile device
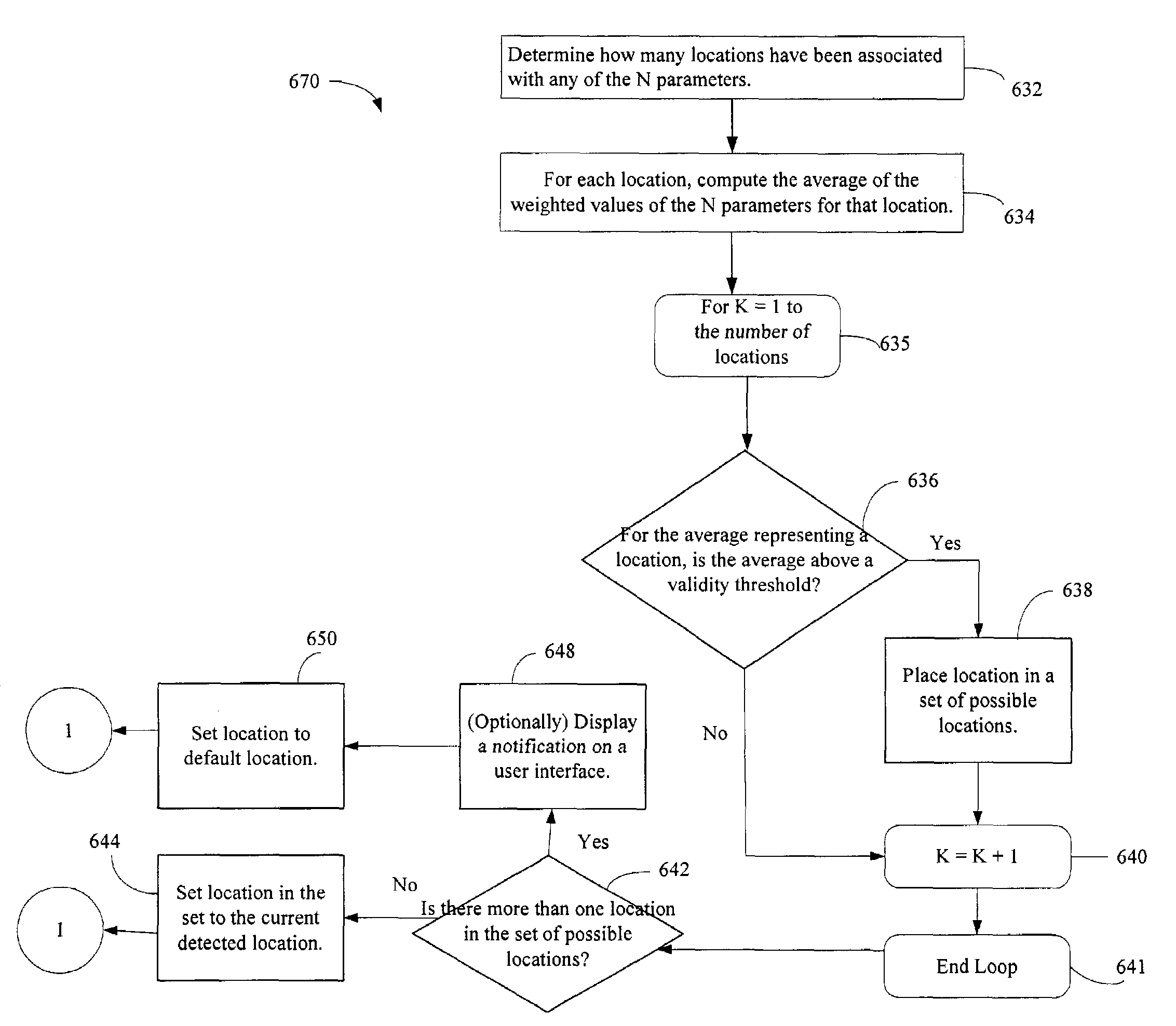
The administration of protection of data on a client mobile computing device by a server computer system such as within an enterprise network or on a separate mobile computing device is described. Security tools are described that provide different security policies to be enforced based on a location associated with a network environment in which a mobile device is operating. Methods for detecting the location of the mobile device are described. Additionally, the security tools may also provide for enforcing different policies based on security features. Examples of security features include the type of connection, wired or wireless, over which data is being transferred, the operation of anti-virus software, or the type of network adapter card. The different security policies provide enforcement mechanisms that may be tailored based upon the detected location and / or active security features associated with the mobile device. Examples of enforcement mechanisms are adaptive port blocking, file hiding and file encryption.
Owner:APPLE INC
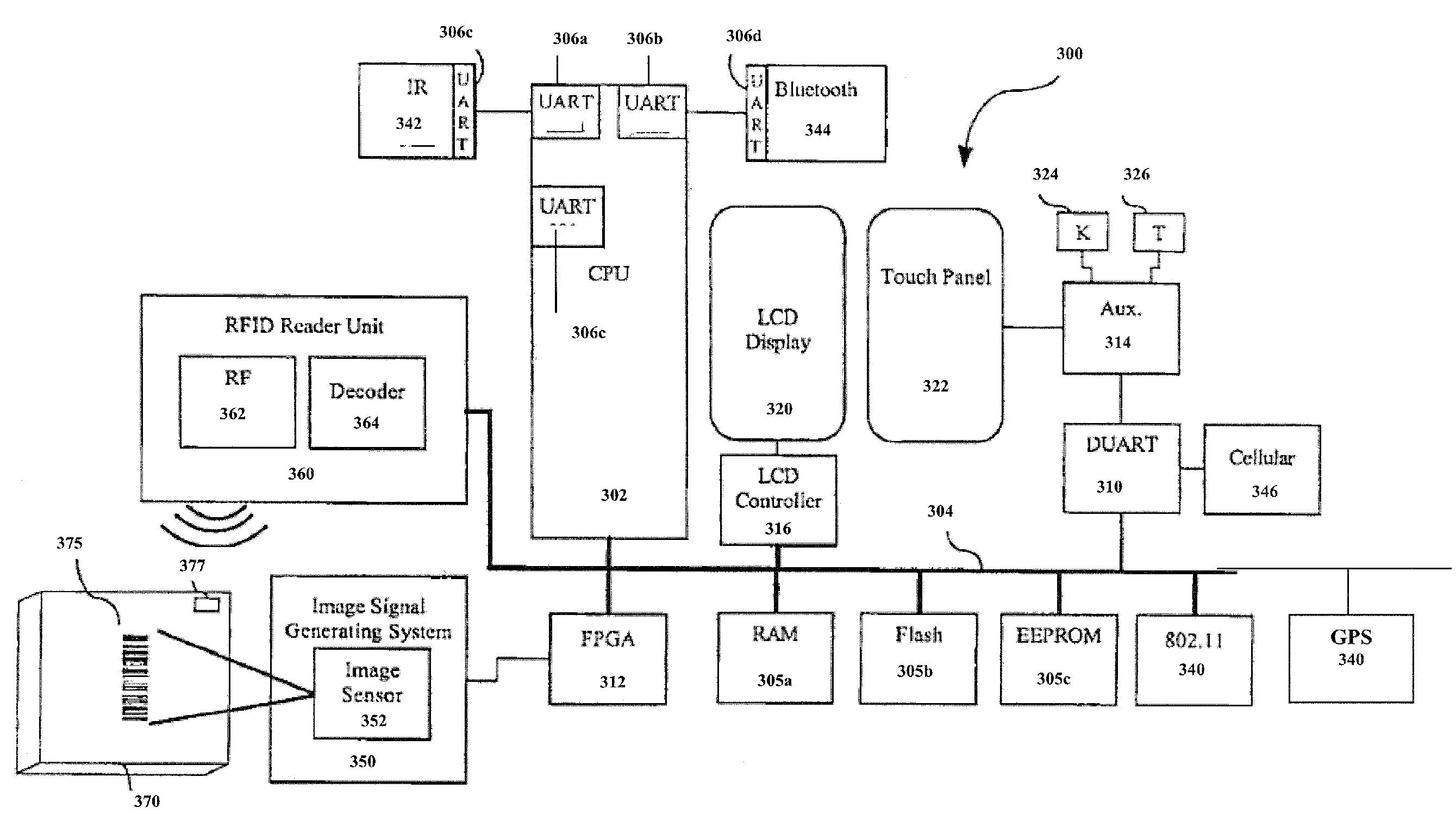
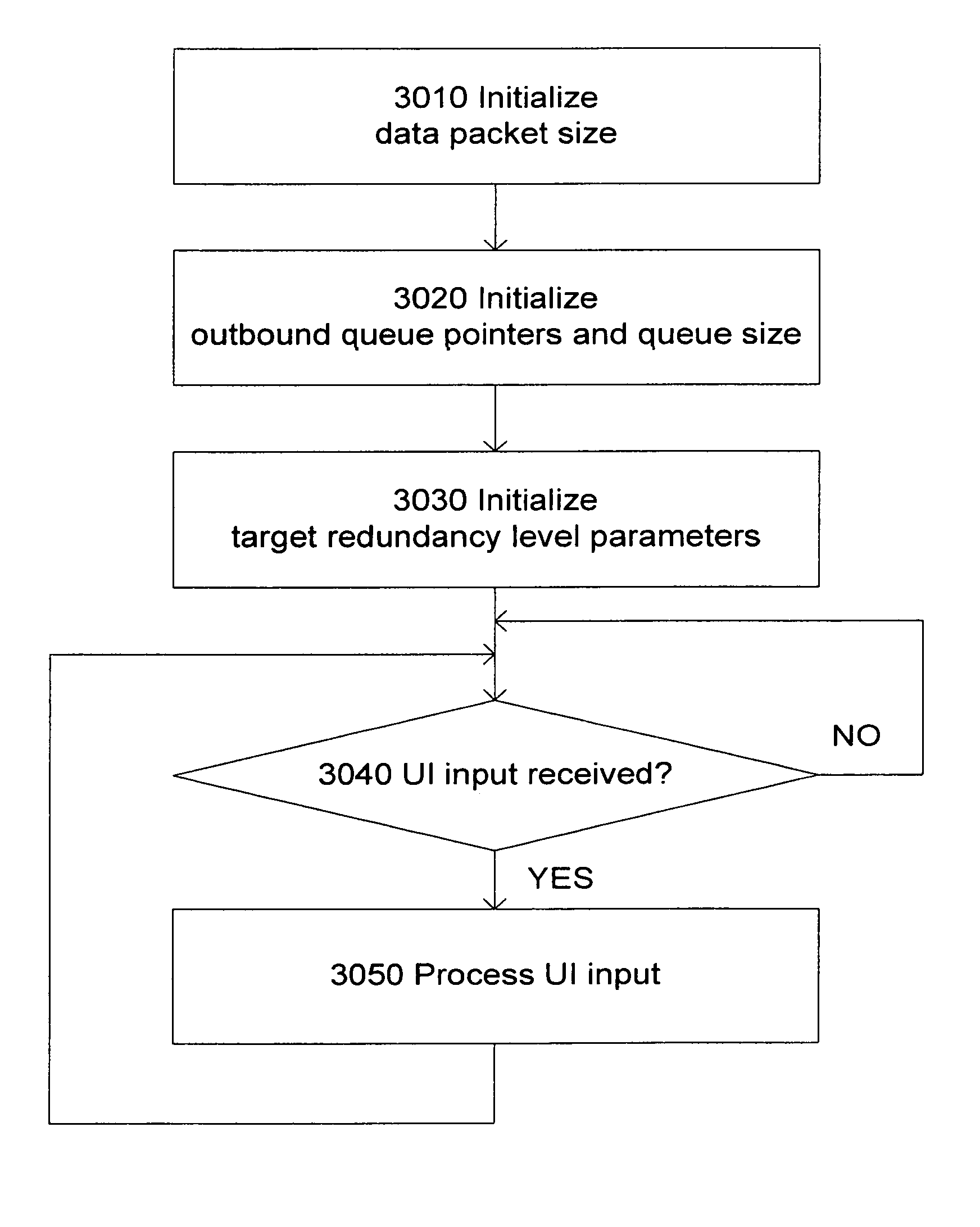
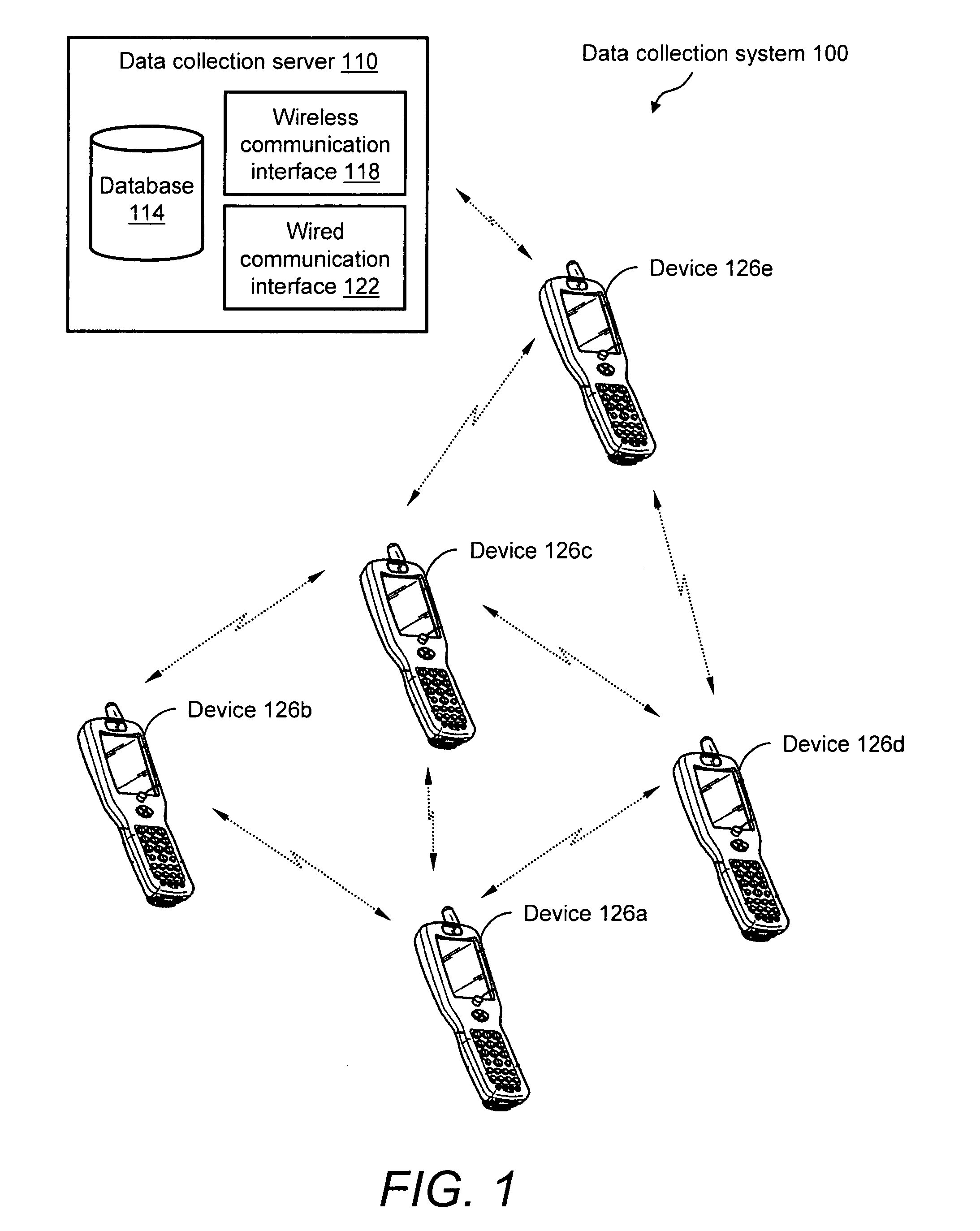
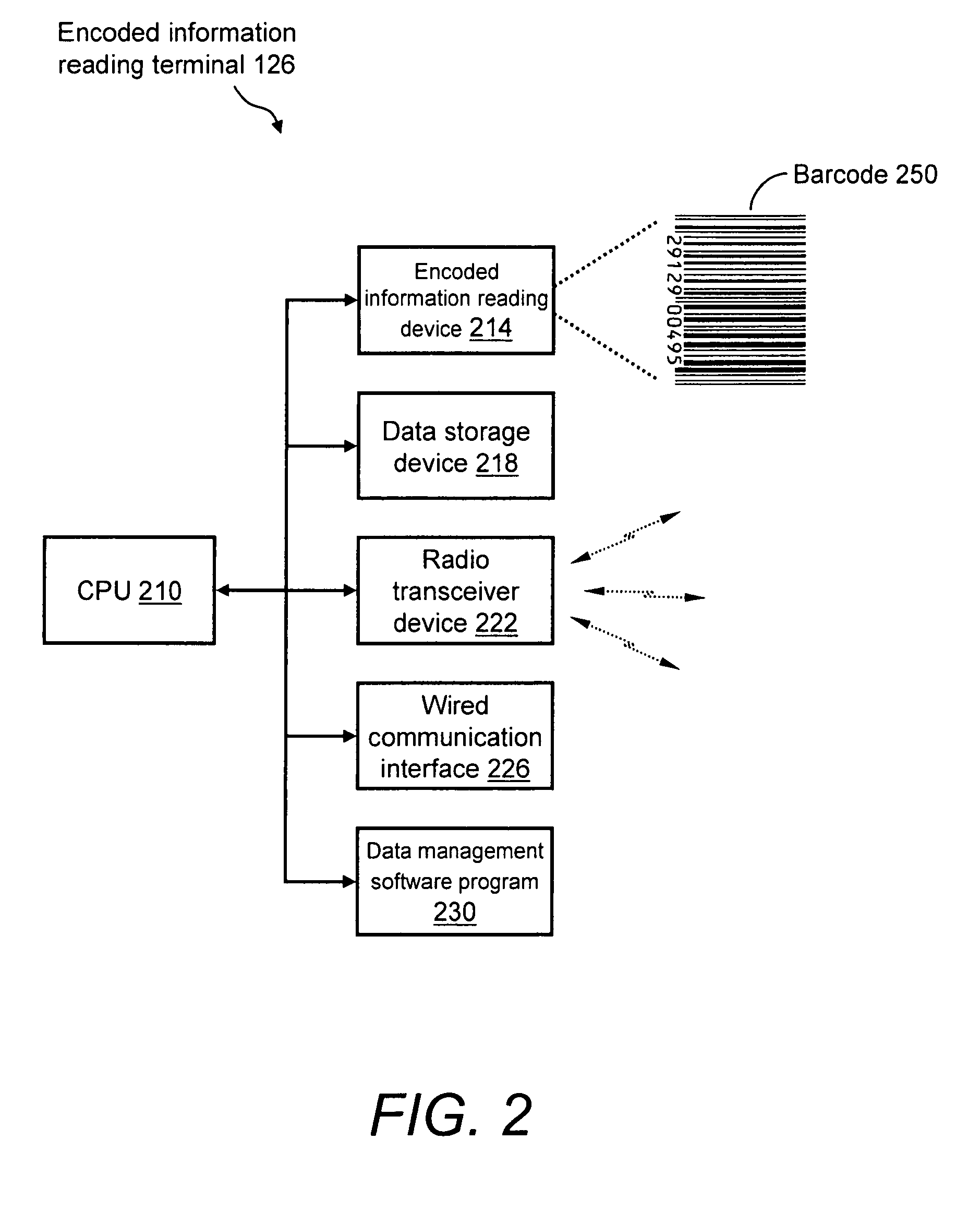
System and method for reliable store-and-forward data handling by encoded information reading terminals
InactiveUS8971346B2Error preventionFrequency-division multiplex detailsStore and forwardComputer terminal
A data collection system for, and methods of, providing reliable store-and-forward data handling by encoded information reading terminals can utilize ad-hoc peer-to-peer (i.e., terminal-to-terminal) connections in order to store data that is normally stored on a single terminal only, in a redundant manner on two or more terminals. Each portable encoded information reading terminal can be configured so that when it captures data, a software application causes the terminal to search out nearby peer terminals that can store and / or forward the data to other peer terminals or to a data collection server, resulting in the data having been stored by one or more peer terminals that are immediately or not immediately accessible by the data-originating terminal.
Owner:HAND HELD PRODS
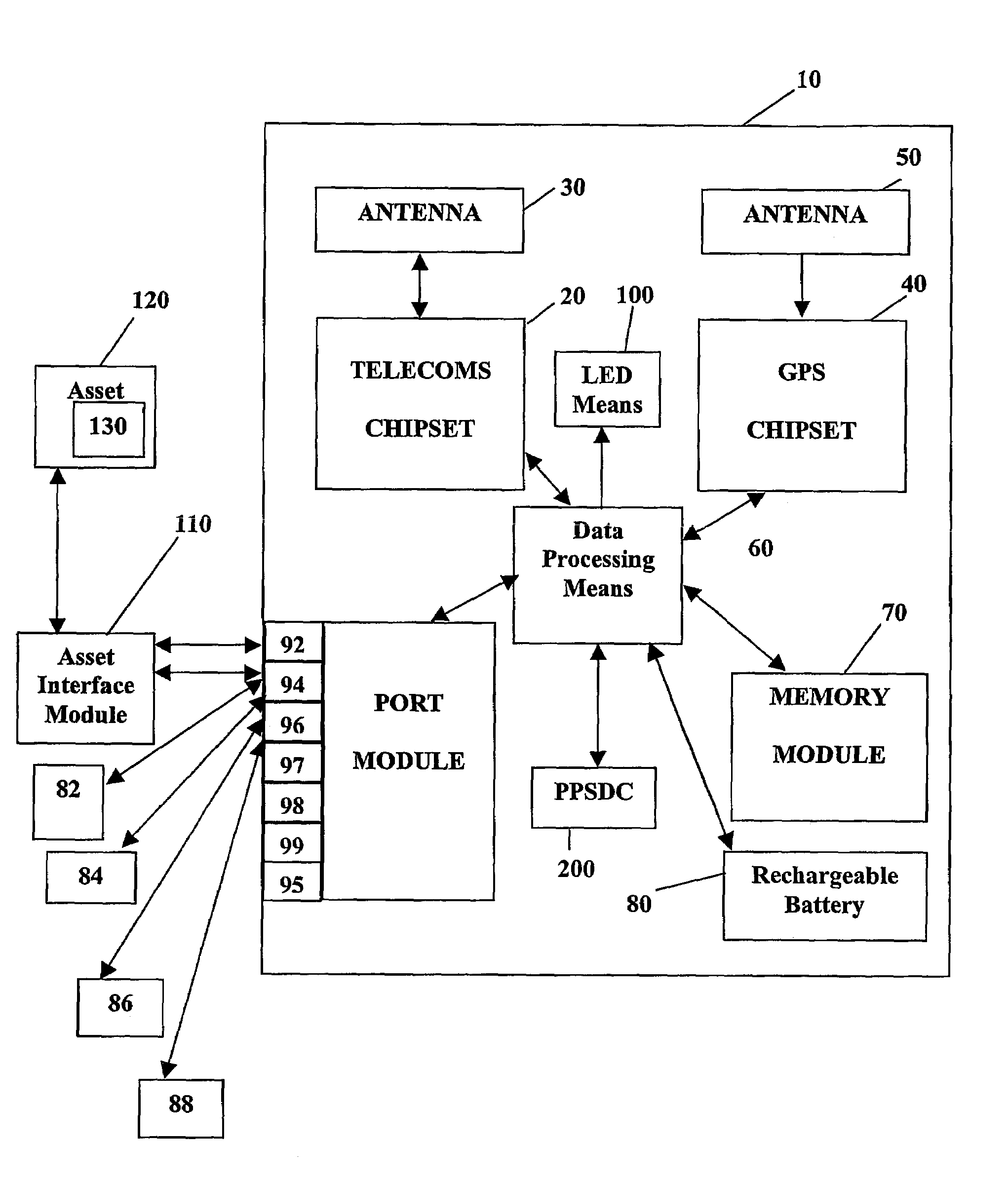
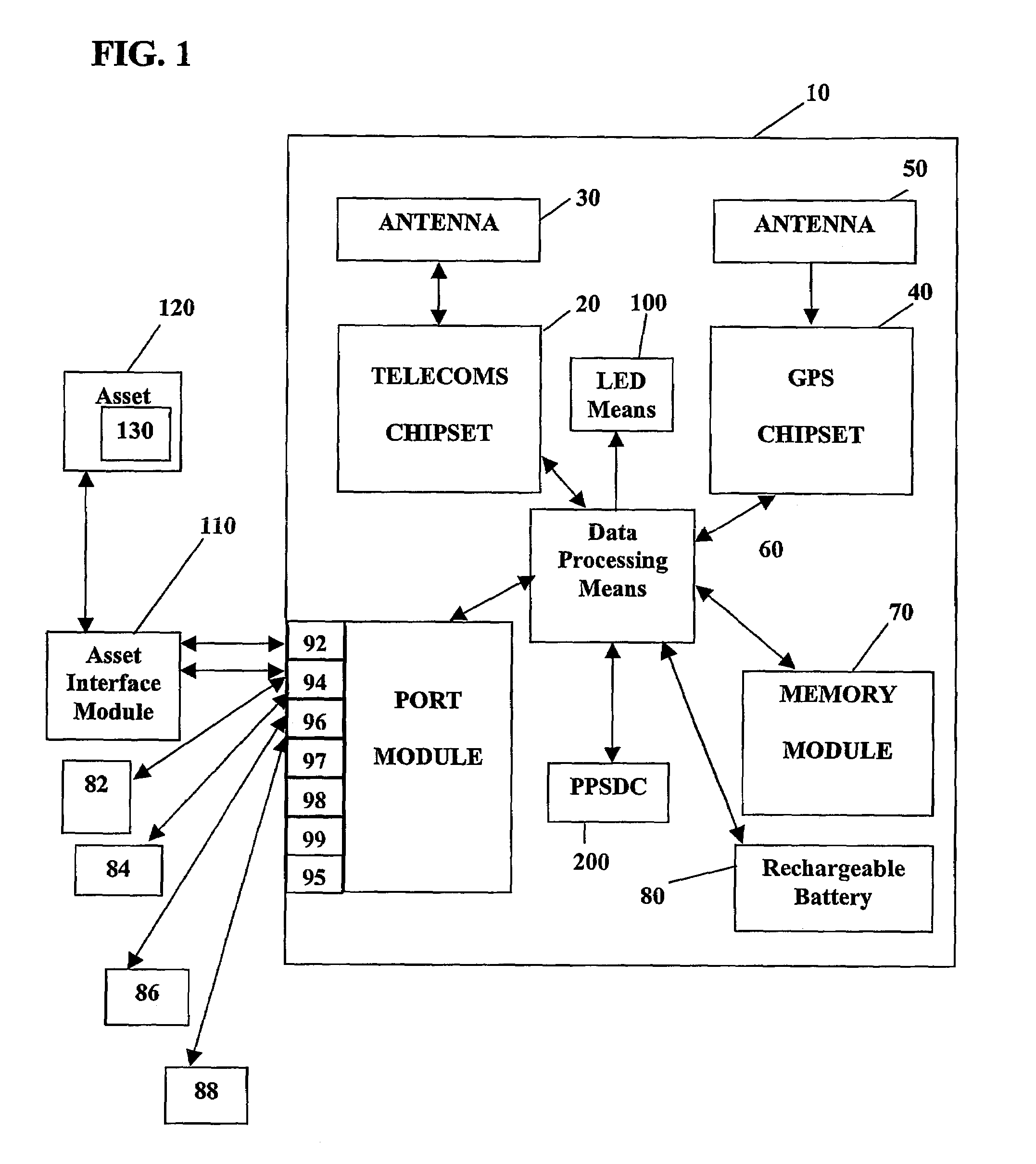
System and method for monitoring and control of wireless modules linked to assets
InactiveUS7027808B2Wireless commuication servicesElectric/magnetic detectionOperational systemComputer module
A system and method for remote asset management is described which can provide the basis for a diverse product group including an improved remote location monitoring system, a means for communicating with and for monitoring the status and or location of a plurality of diverse assets, as well as the means for communicating with said assets for the purpose of modifying the operational status of one or more of said assets according to one or more stored data parameters such as location, use, battery power, and such like. The remote asset management system comprises a wireless module, which is associated with at least one of the plurality of asset and which is interfaced with the operating system of said assert and or with an electromechanical control means, which may control one or more features of the operation of said assets. A supporting network-based, or internet-based service platform, controls and manages the status of each of the plurality of assets, either automatically, or in response to received messages from fixed or wireless communication devices, and which is capable of selectively communicating data to said assets for changing the operational status of said assets according to pre-programmed conditions.
Owner:M2M SOLUTIONS
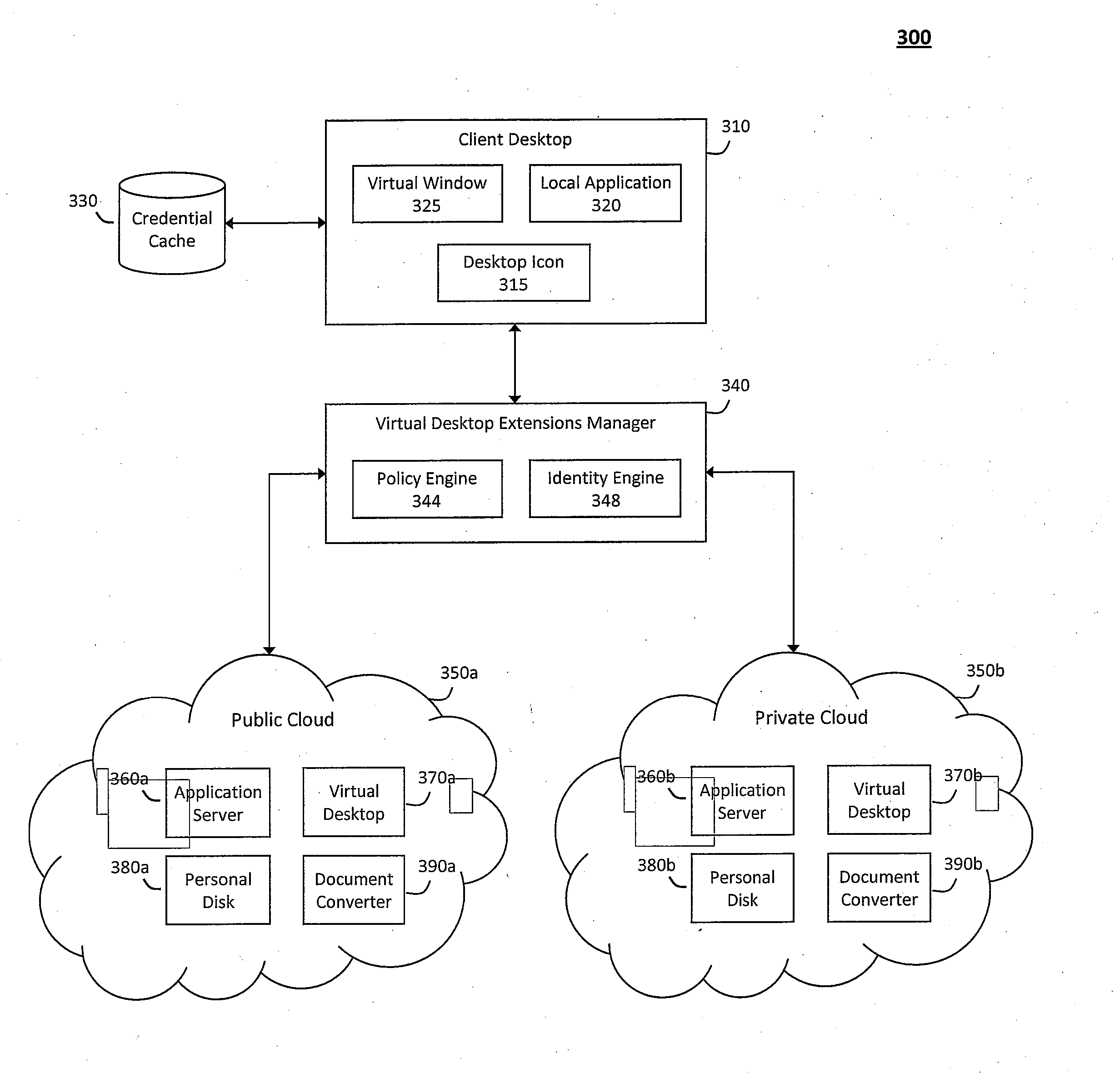
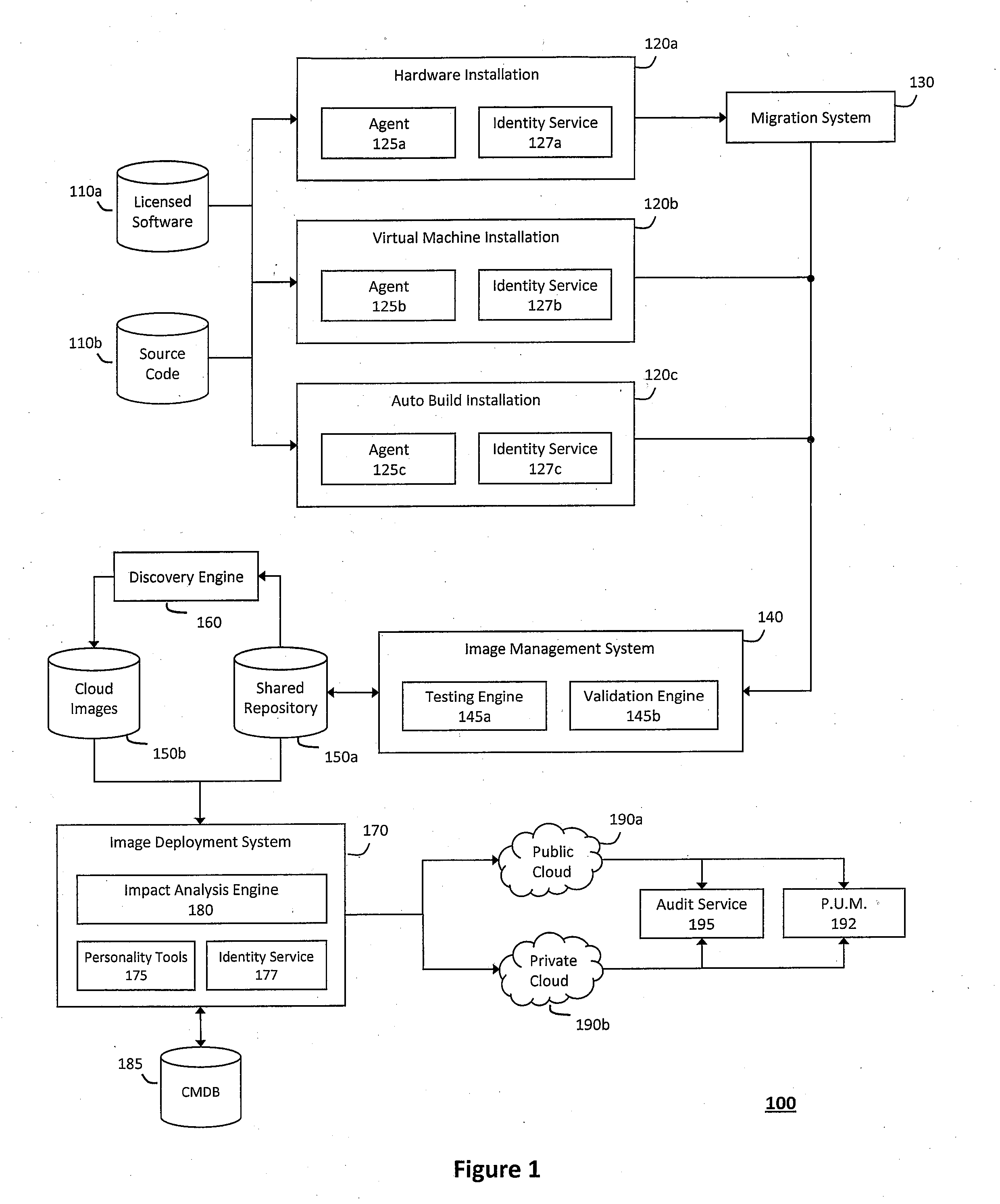
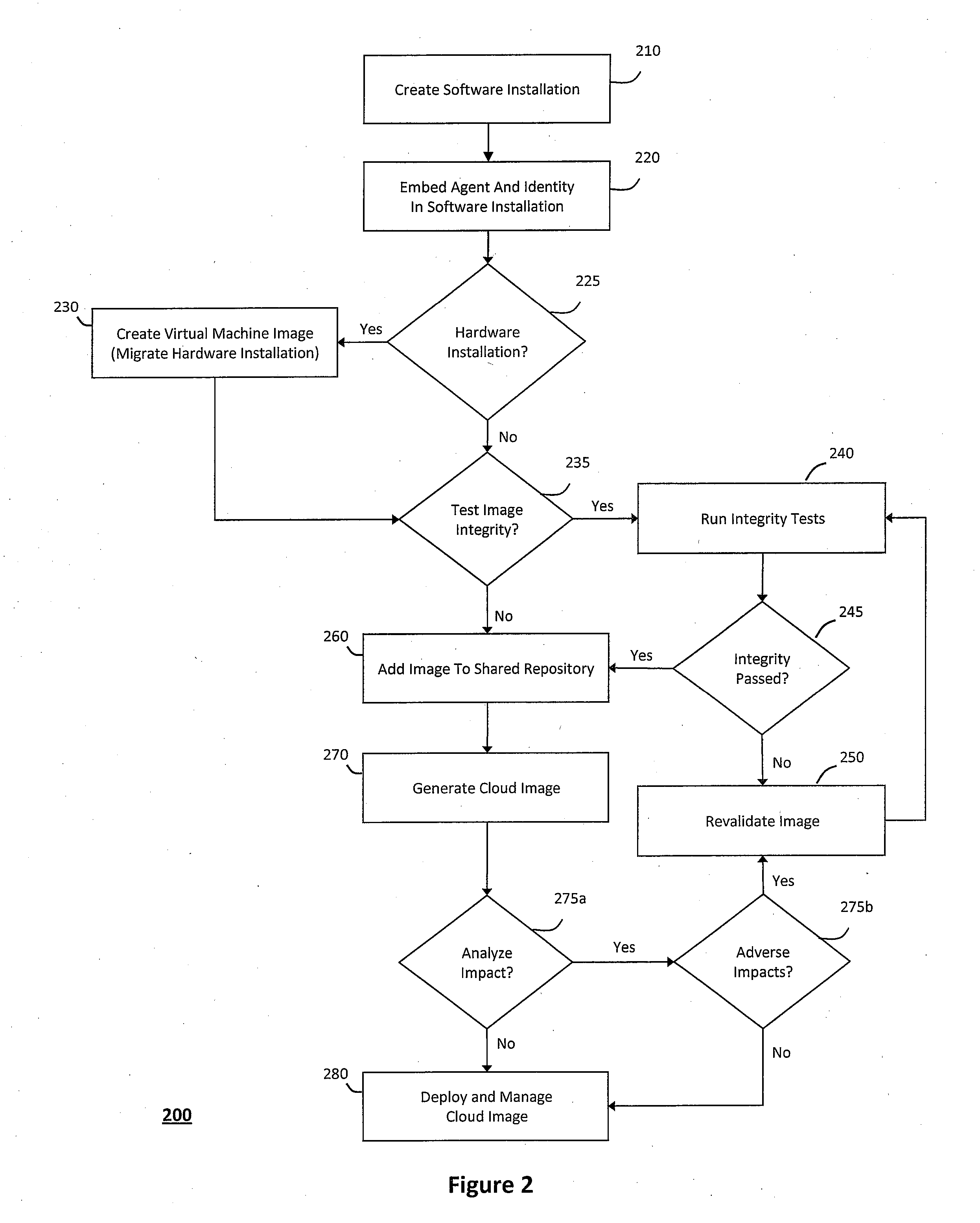
System and method for providing virtual desktop extensions on a client desktop
ActiveUS20110209064A1Simplify complexityProvide capabilityInput/output for user-computer interactionDigital data processing detailsClient-sideCloud computing
The system and method described herein may identify one or more virtual desktop extensions available in a cloud computing environment and launch virtual machine instances to host the available virtual desktop extensions in the cloud. For example, a virtual desktop extension manager may receive a virtual desktop extension request from a client desktop and determine whether authentication credentials for the client desktop indicate that the client desktop has access to the requested virtual desktop extension. In response to authenticating the client desktop, the virtual desktop extension manager may then launch a virtual machine instance to host the virtual desktop extension in the cloud and provide the client desktop with information for locally controlling the virtual desktop extension remotely hosted in the cloud.
Owner:MICRO FOCUS SOFTWARE INC
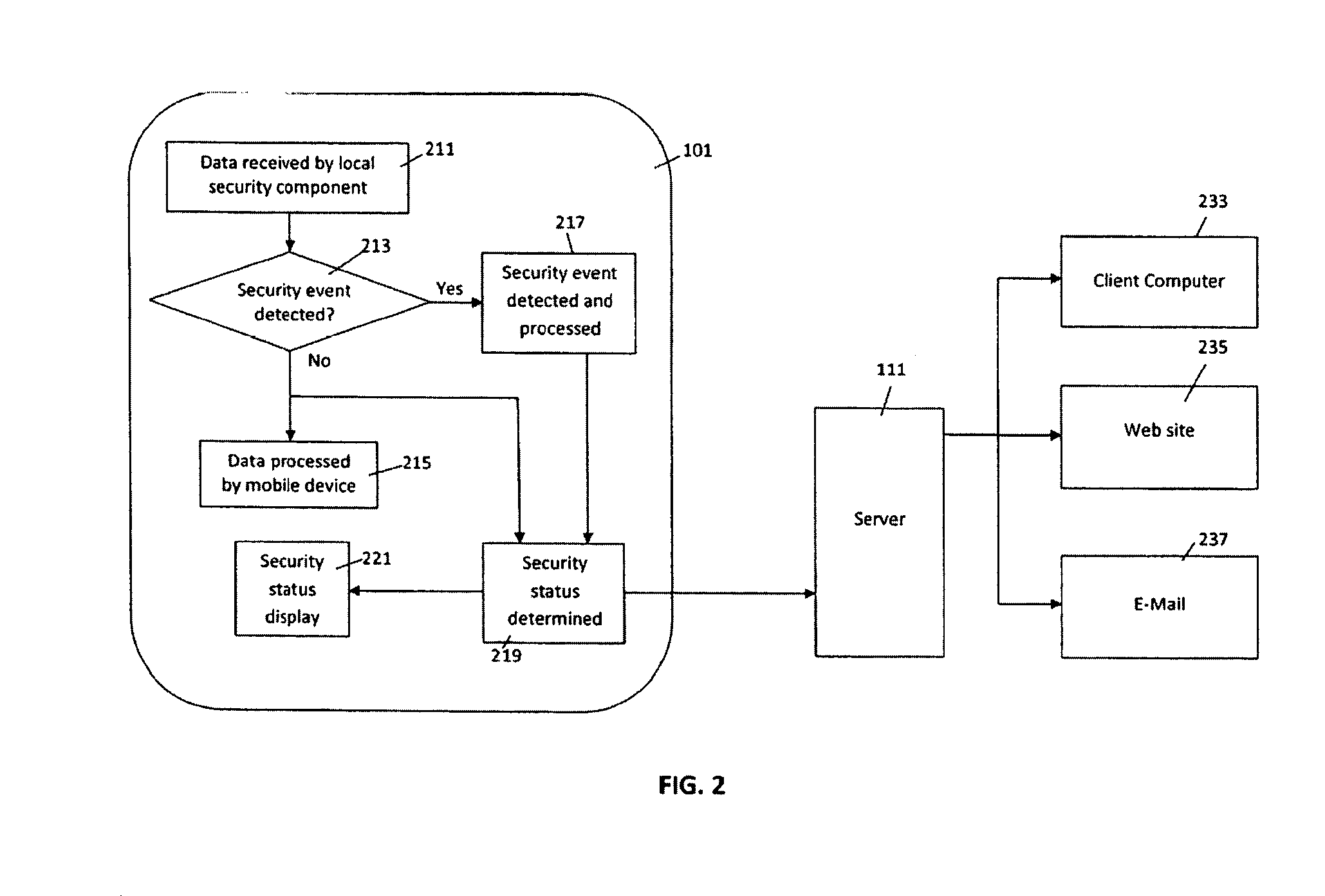
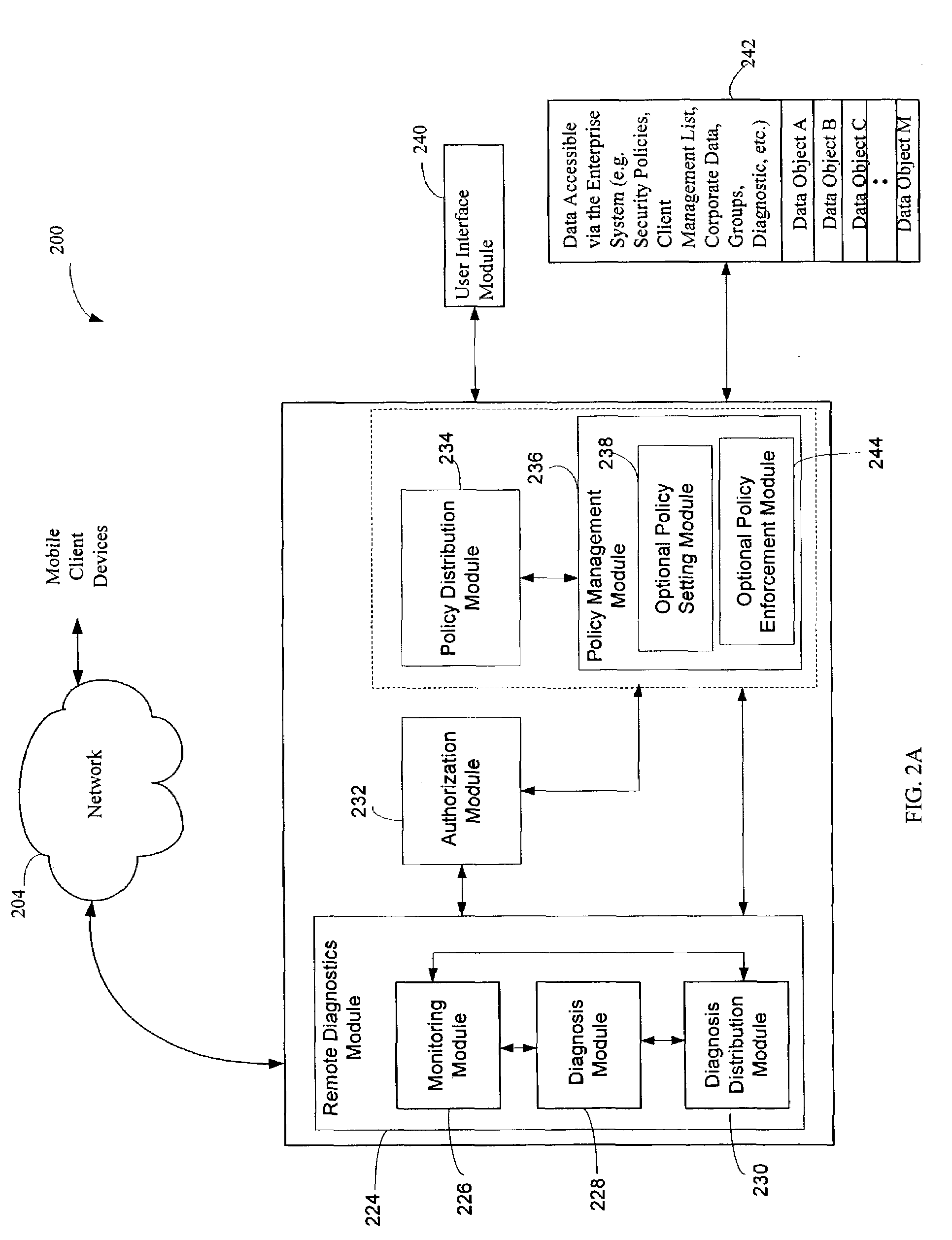
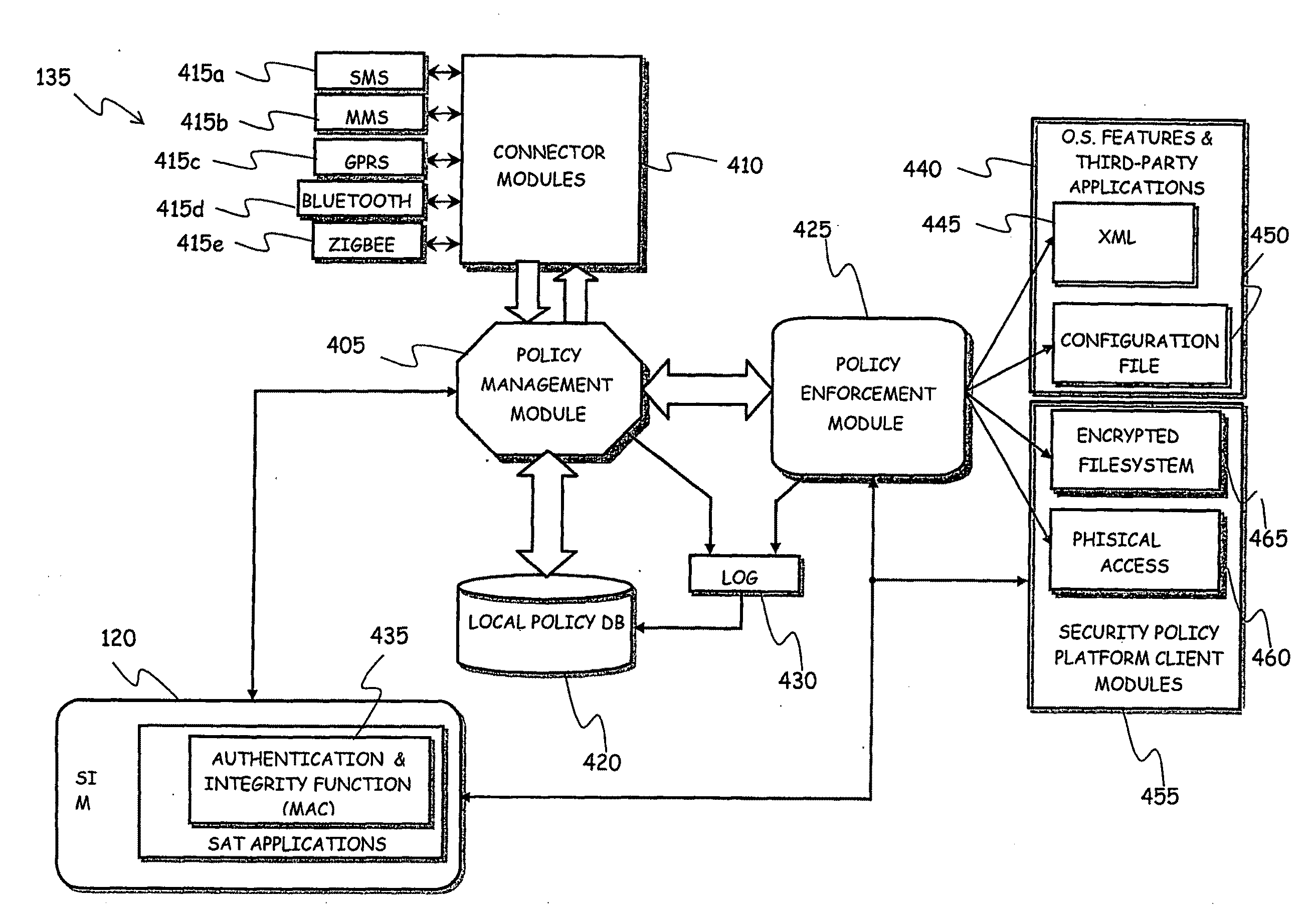
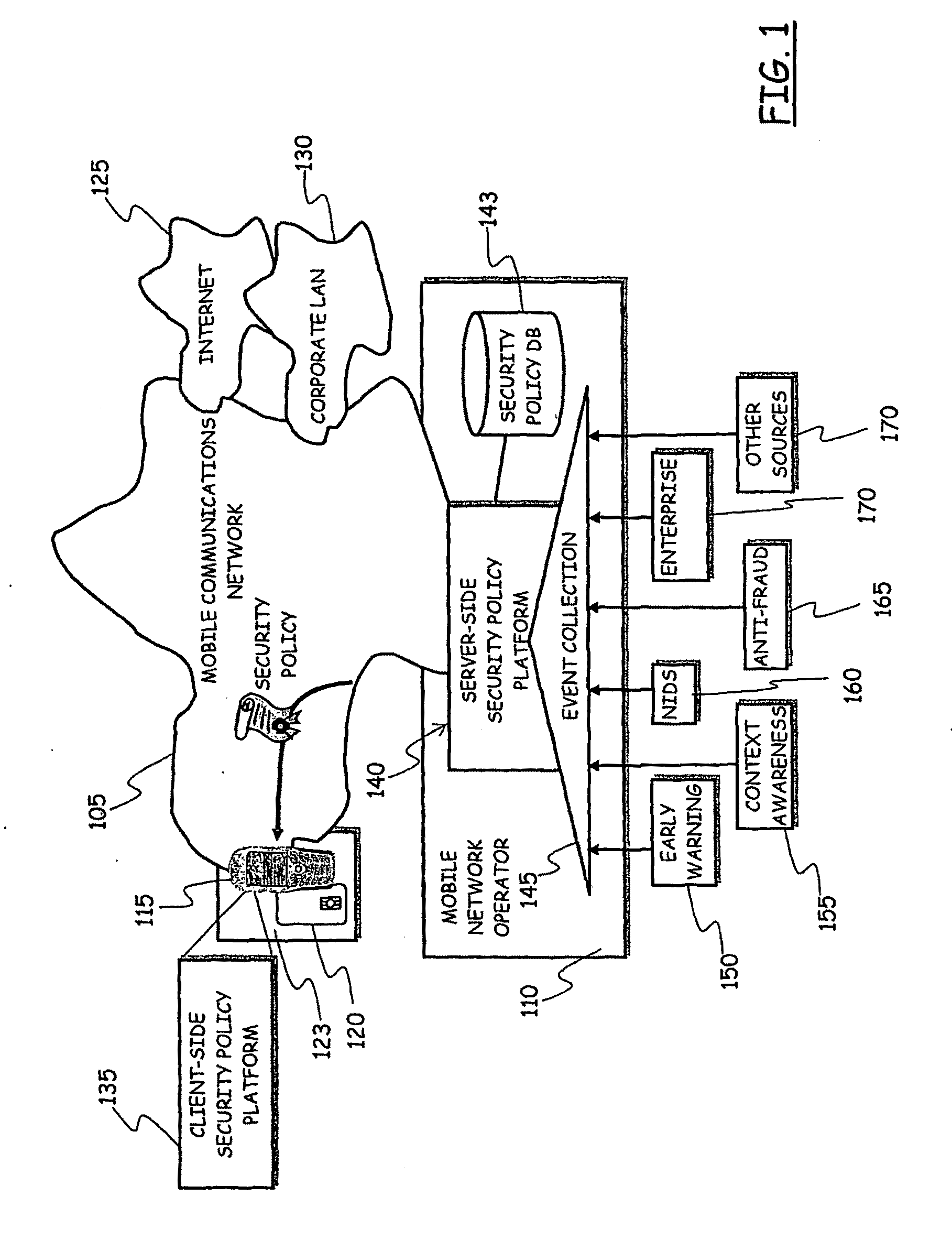
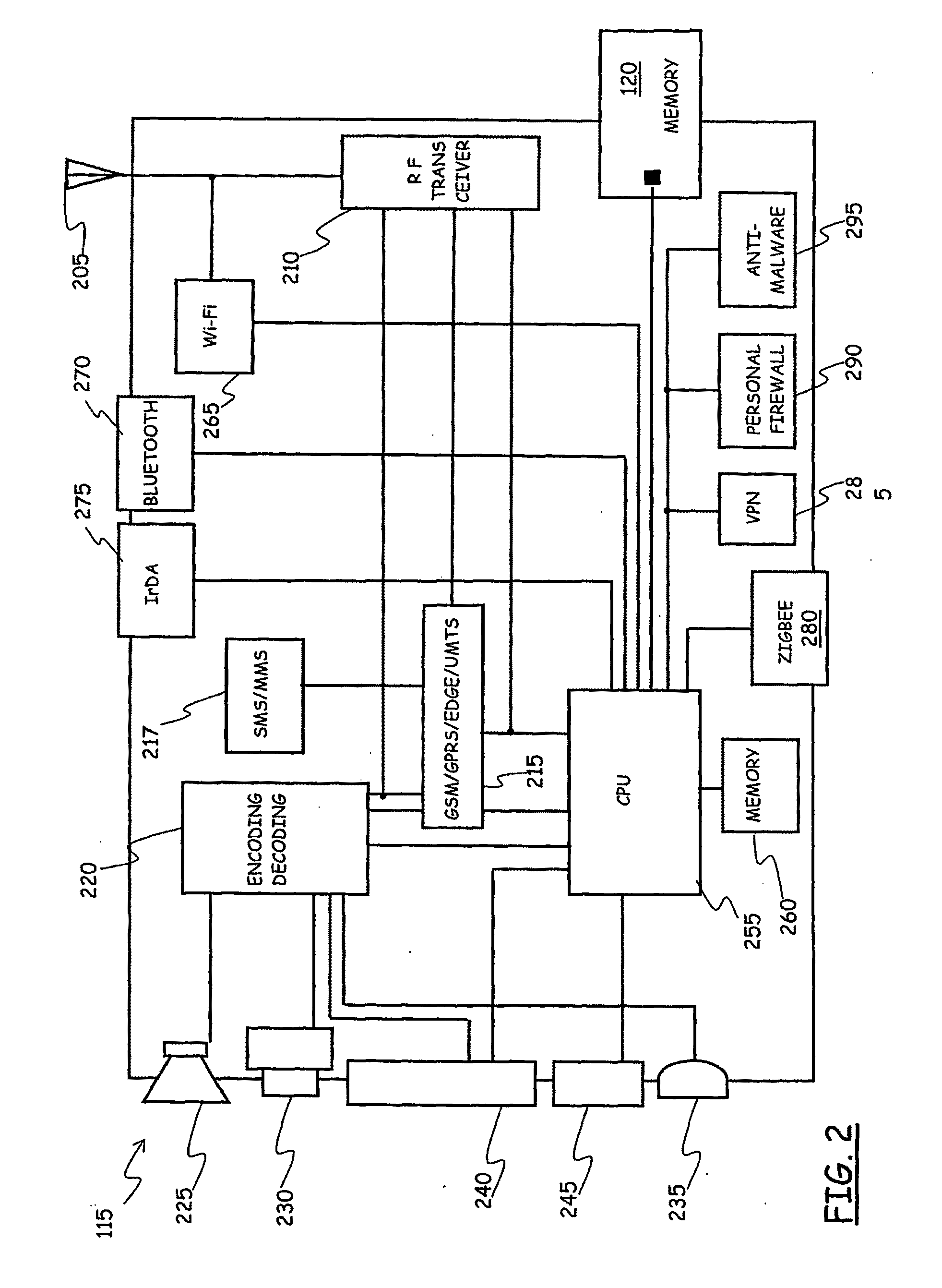
System for Enforcing Security Policies on Mobile Communications Devices
A system for enforcing security policies on mobile communications devices is adapted to be used in a mobile communications network in operative association with a subscriber identity module. The system having a client-server architecture includes a server operated by a mobile communications network operator and a client resident on a mobile communications device on which security policies are to be enforced. The server is adapted to determine security policies to be applied on said mobile communications device, and to send thereto a security policy to be applied. The client is adapted to receive the security policy to be applied from the server, and to apply the received security policy. The server includes a server authentication function adapted to authenticate the security policy to be sent to the mobile communications device; the client is further adapted to assess authenticity of the security policy received from the server by exploiting a client authentication function resident on the subscriber identity module.
Owner:TELECOM ITALIA SPA
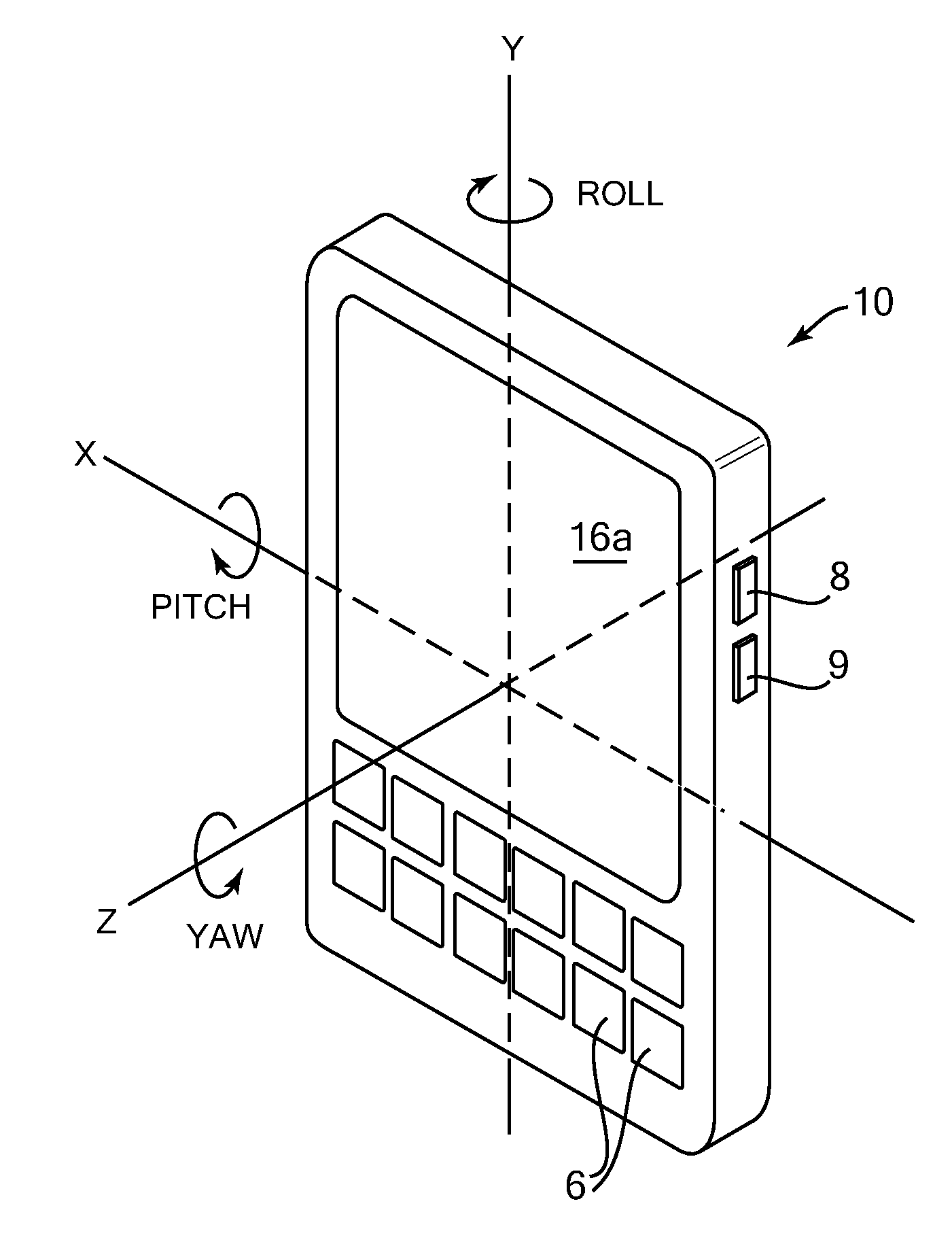
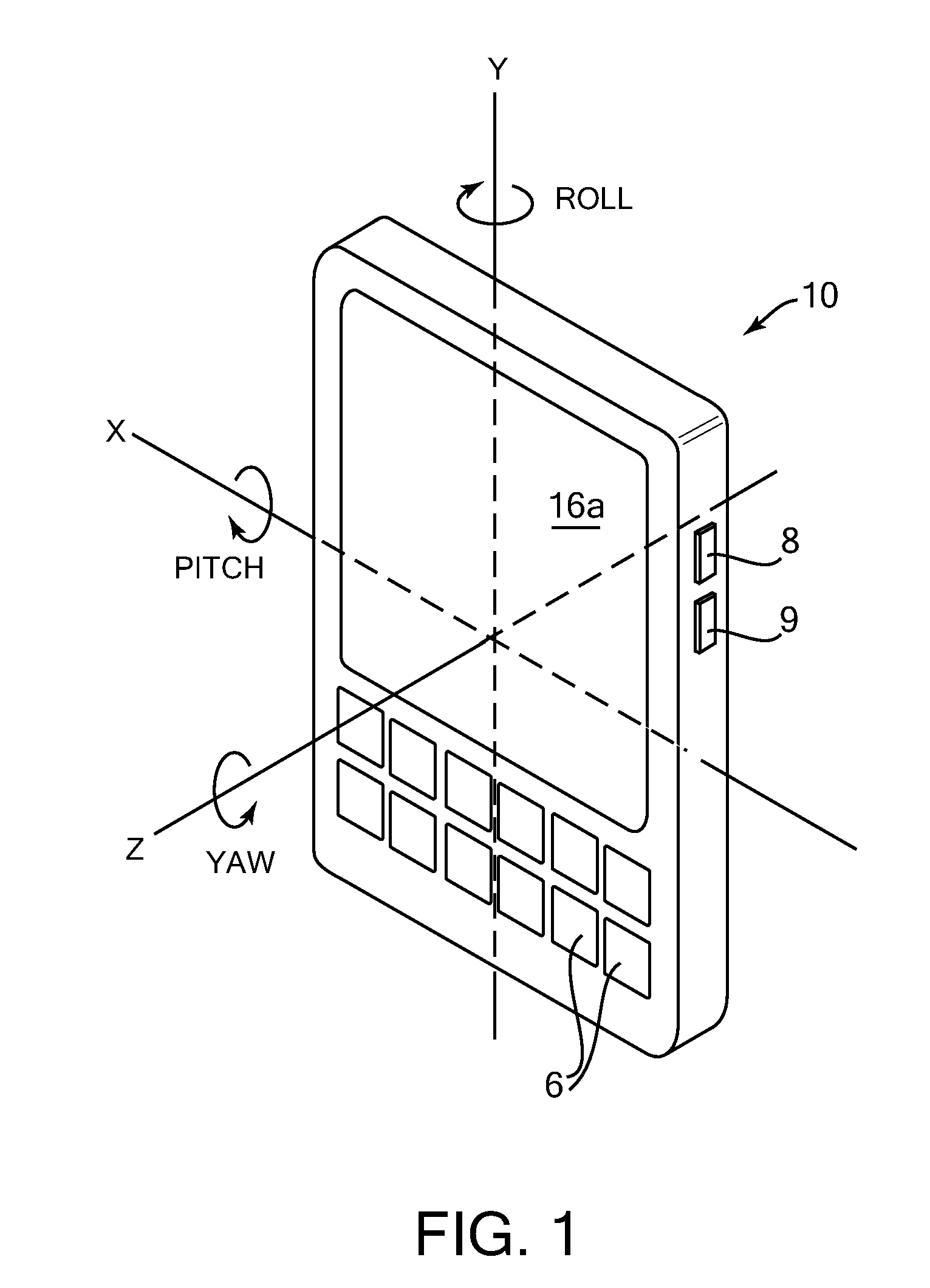
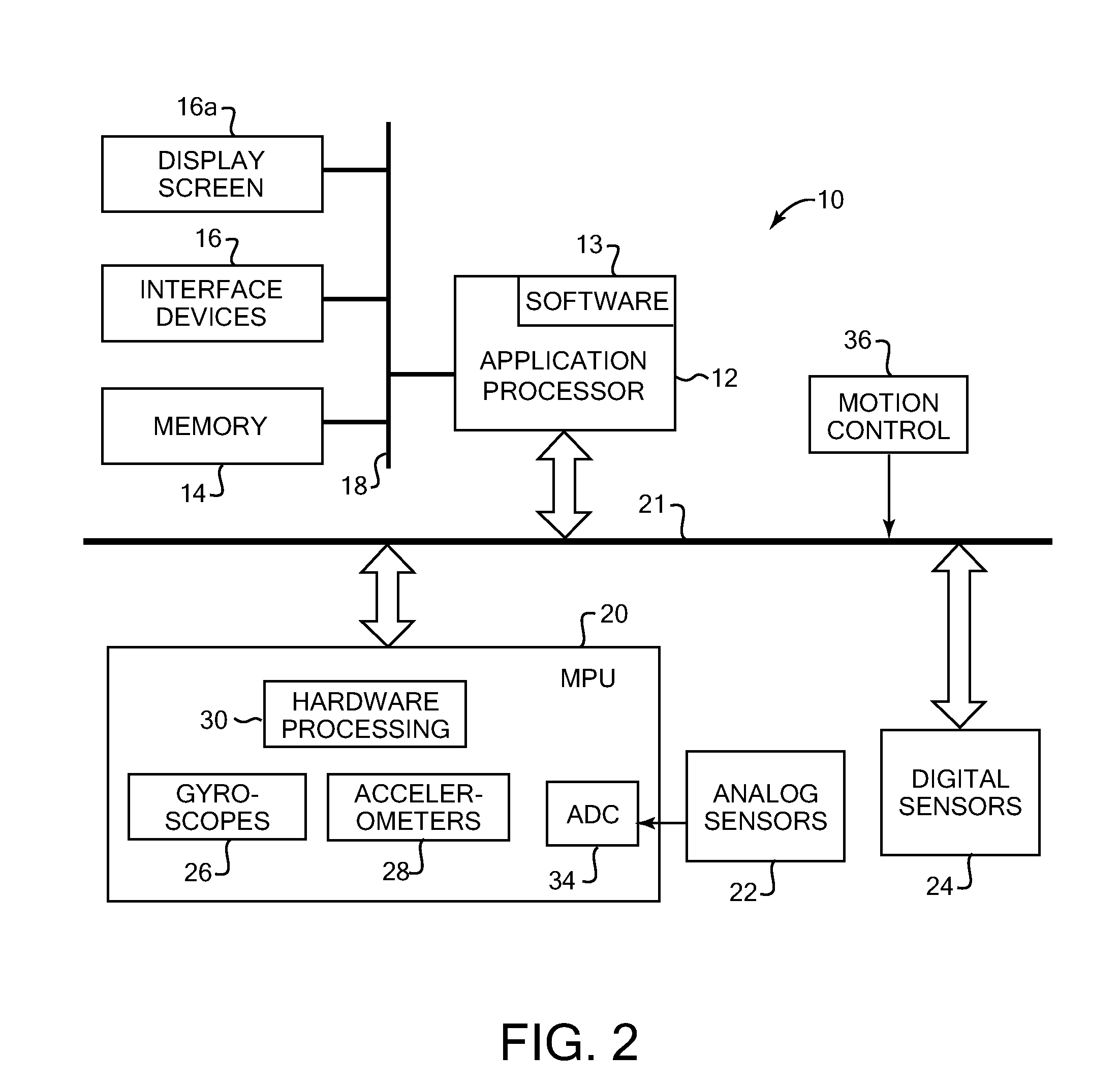
Controlling and accessing content using motion processing on mobile devices
InactiveUS20090262074A1Enhanced interactionAccurate motion dataDigital data processing detailsDevices with sensorMotion processingAnimation
Various embodiments provide systems and methods capable of facilitating interaction with handheld electronics devices based on sensing rotational rate around at least three axes and linear acceleration along at least three axes. In one aspect, a handheld electronic device includes a subsystem providing display capability, a set of motion sensors sensing rotational rate around at least three axes and linear acceleration along at least three axes, and a subsystem which, based on motion data derived from at least one of the motion sensors, is capable of facilitating interaction with the device.
Owner:INVENSENSE
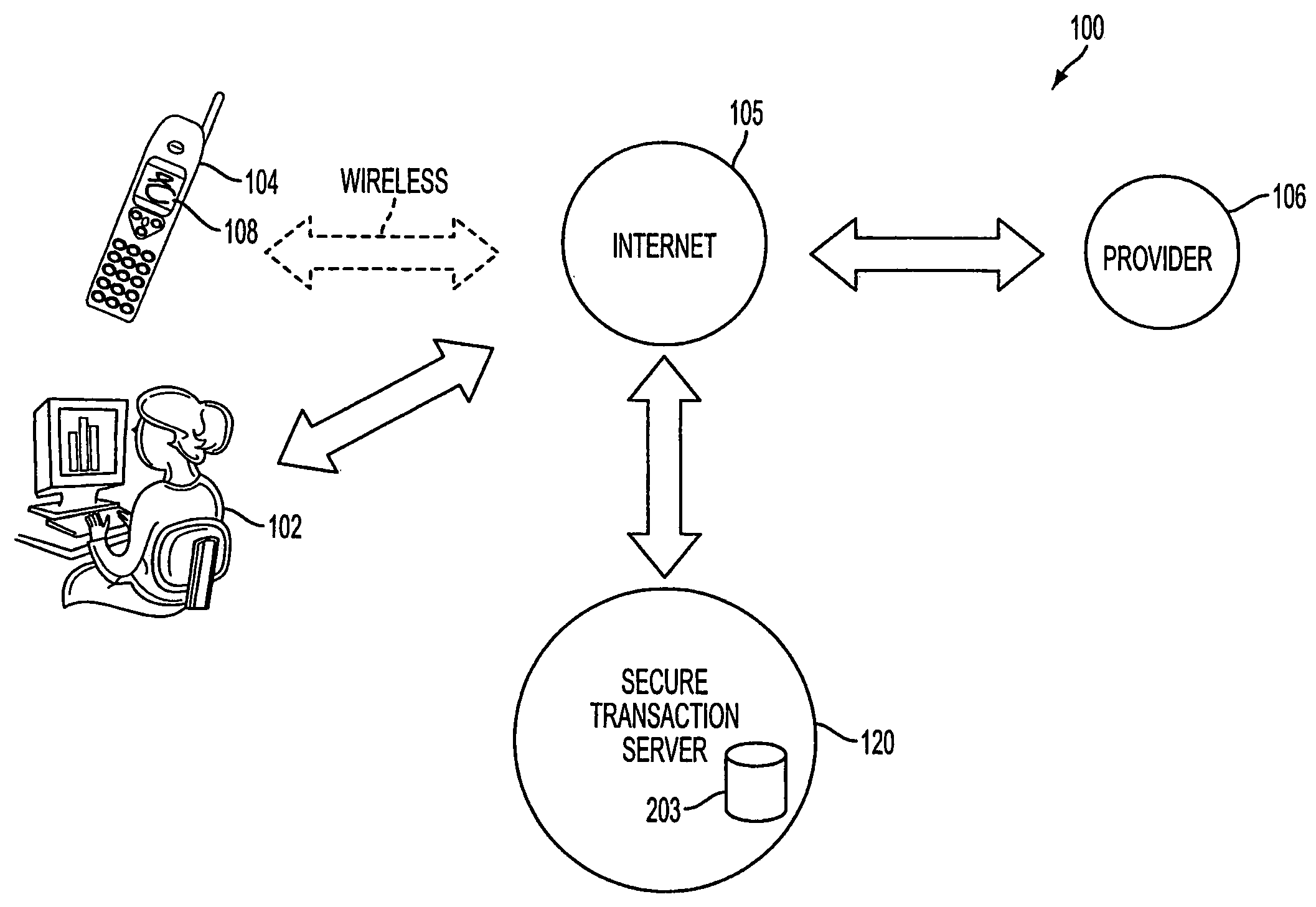
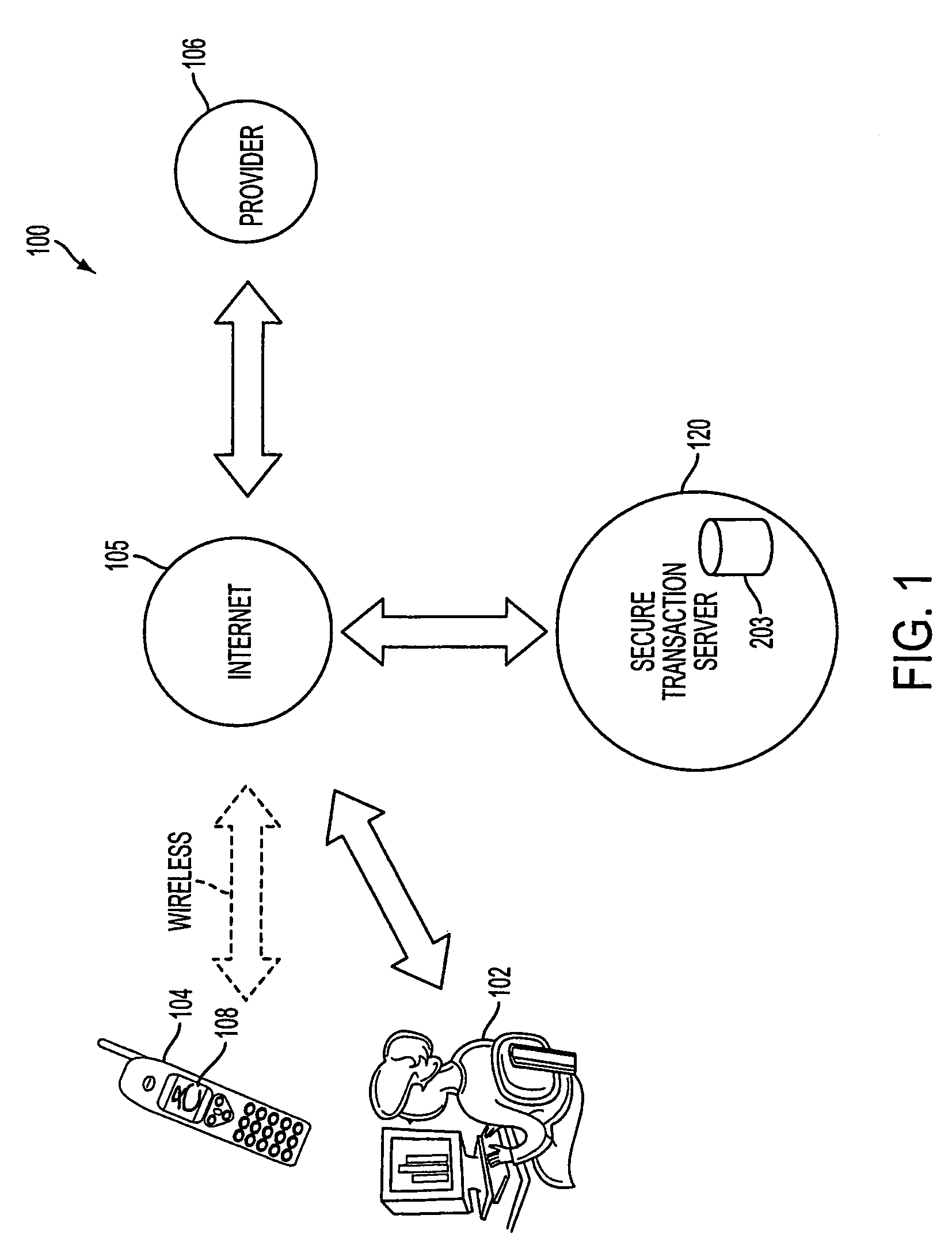
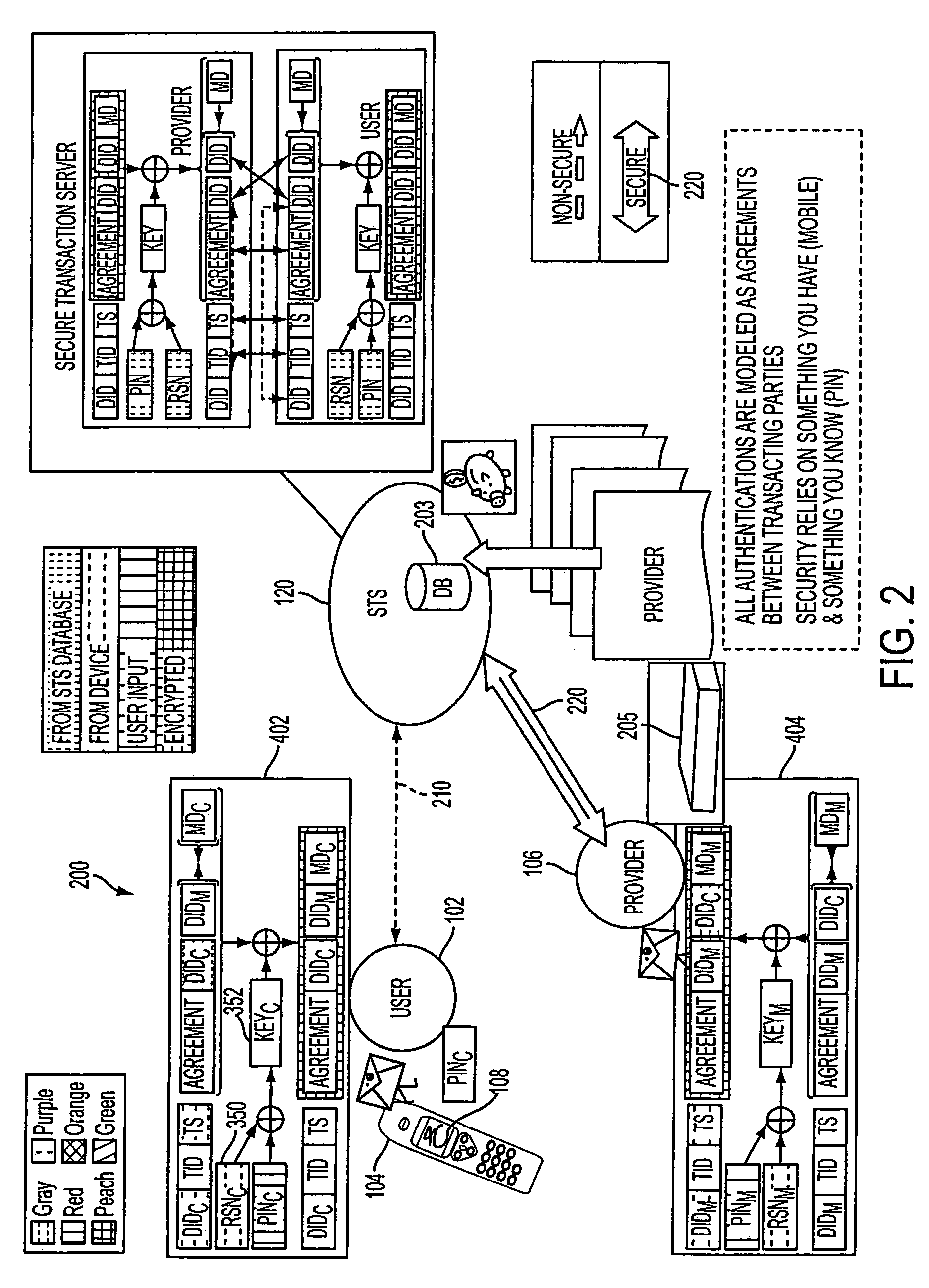
Authentication services using mobile device
InactiveUS7606560B2Unauthorised/fraudulent call preventionEavesdropping prevention circuitsInternet Authentication ServiceMobile device
A method, and an apparatus performing the method, is provided by authenticating a mobile device communicably connectable to a wireless network by an authentication parameter from a secure transaction server (STS), as a mobile device authenticator; providing an STS correlation between a personal identification entry (PIE) and the mobile device authenticator; and inputting, by a user, the PIE and a provider action, to the mobile device authenticator to transmit a transformed secure user authenticable authorization request to the STS over the wireless network to authorize an action with a provider.
Owner:PCMS HOLDINGS INC
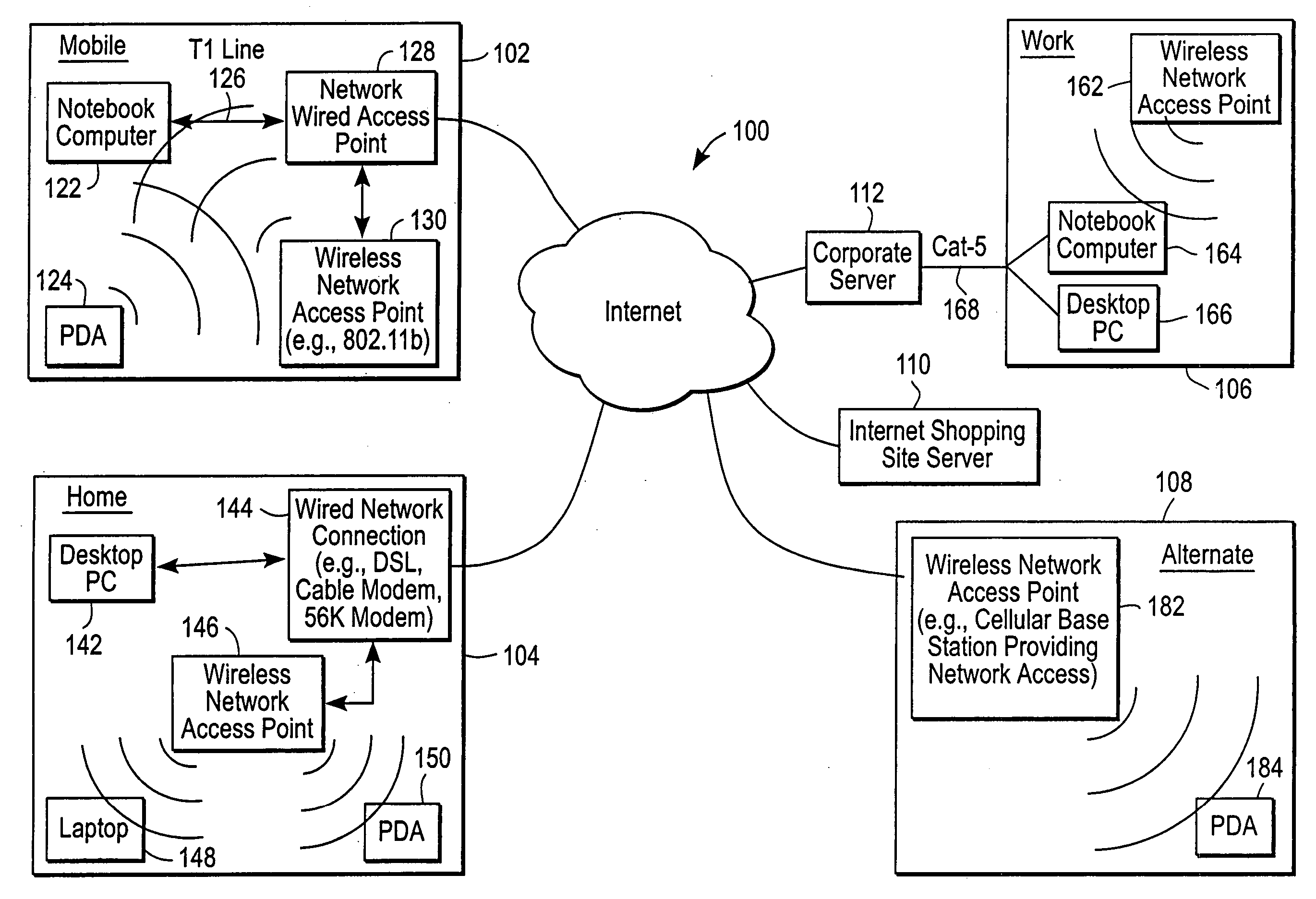
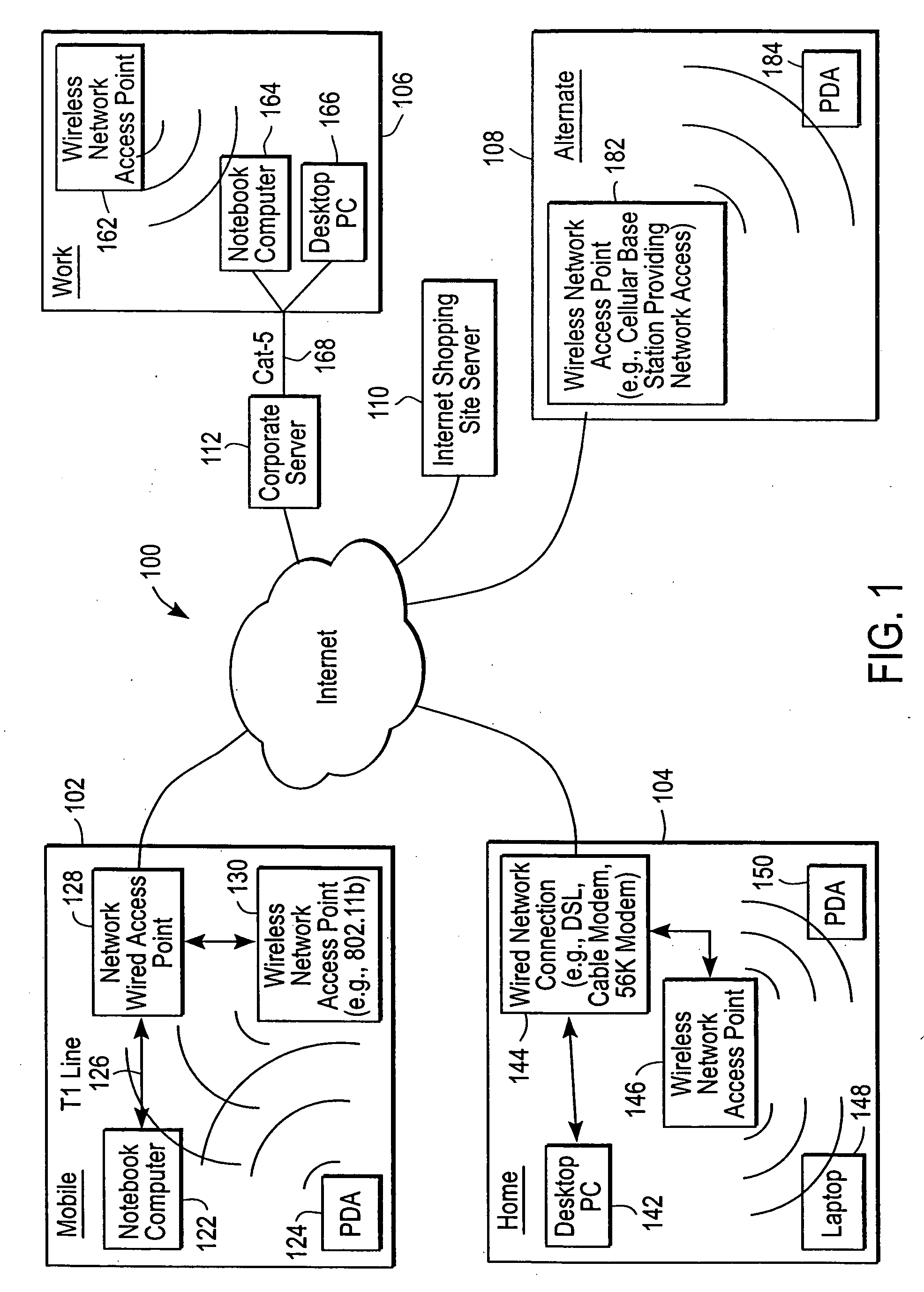
Administration of protection of data accessible by a mobile device
ActiveUS20050055578A1Digital data processing detailsMultiple digital computer combinationsAnti virusEnterprise networking
The protection of data on a client mobile computing device by a server computer system such as within an enterprise network or on a separate mobile computing device is described. Security tools are described that provide different security policies to be enforced based on a location associated with a network environment in which a mobile device is operating. Methods for detecting the location of the mobile device are described. Additionally, the security tools may also provide for enforcing different policies based on security features. Examples of security features include the type of connection, wired or wireless, over which data is being transferred, the operation of anti-virus software, or the type of network adapter card. The different security policies provide enforcement mechanisms that may be tailored based upon the detected location and / or active security features associated with the mobile device. Examples of enforcement mechanisms are adaptive port blocking, file hiding and file encryption.
Owner:APPLE INC
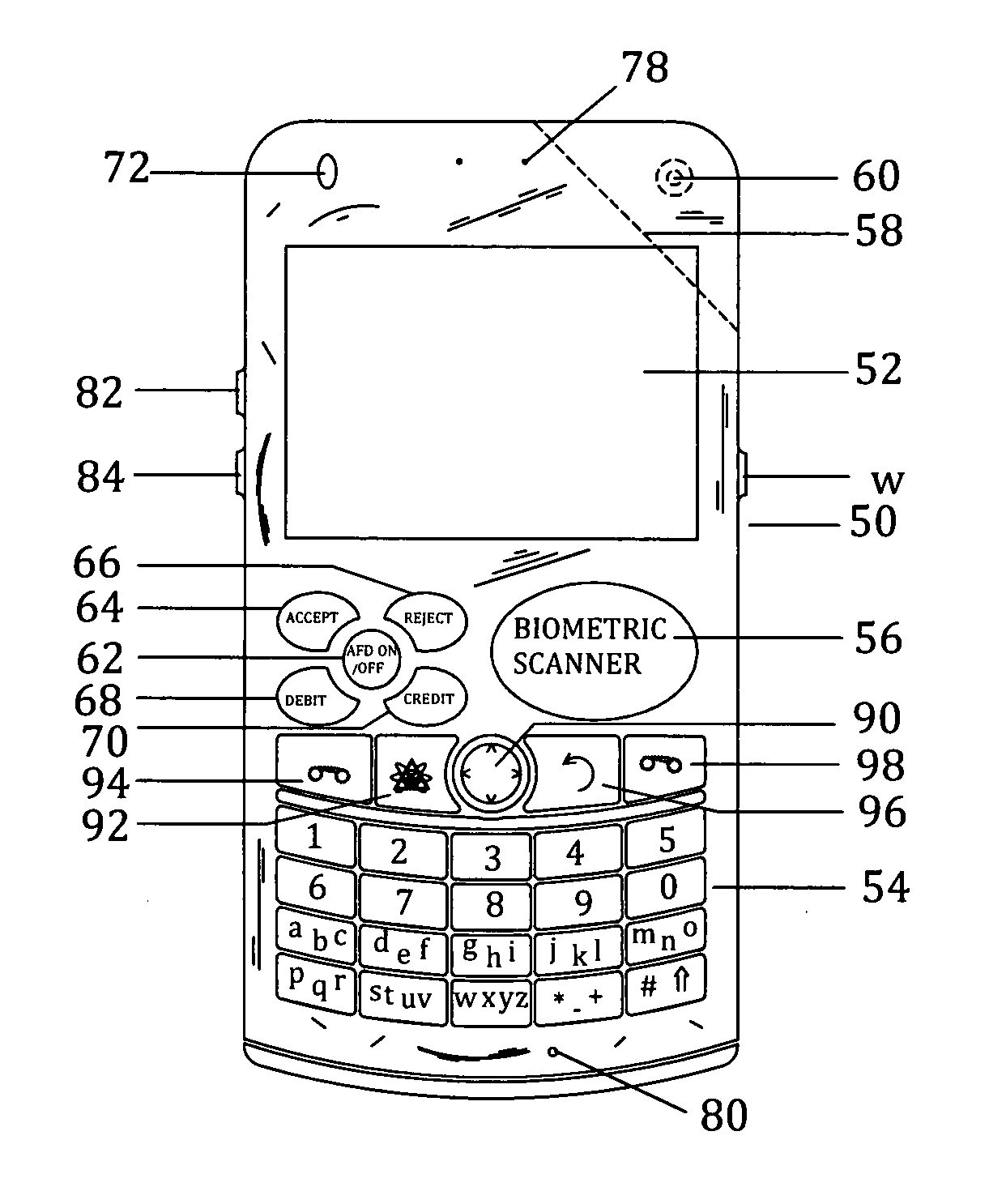
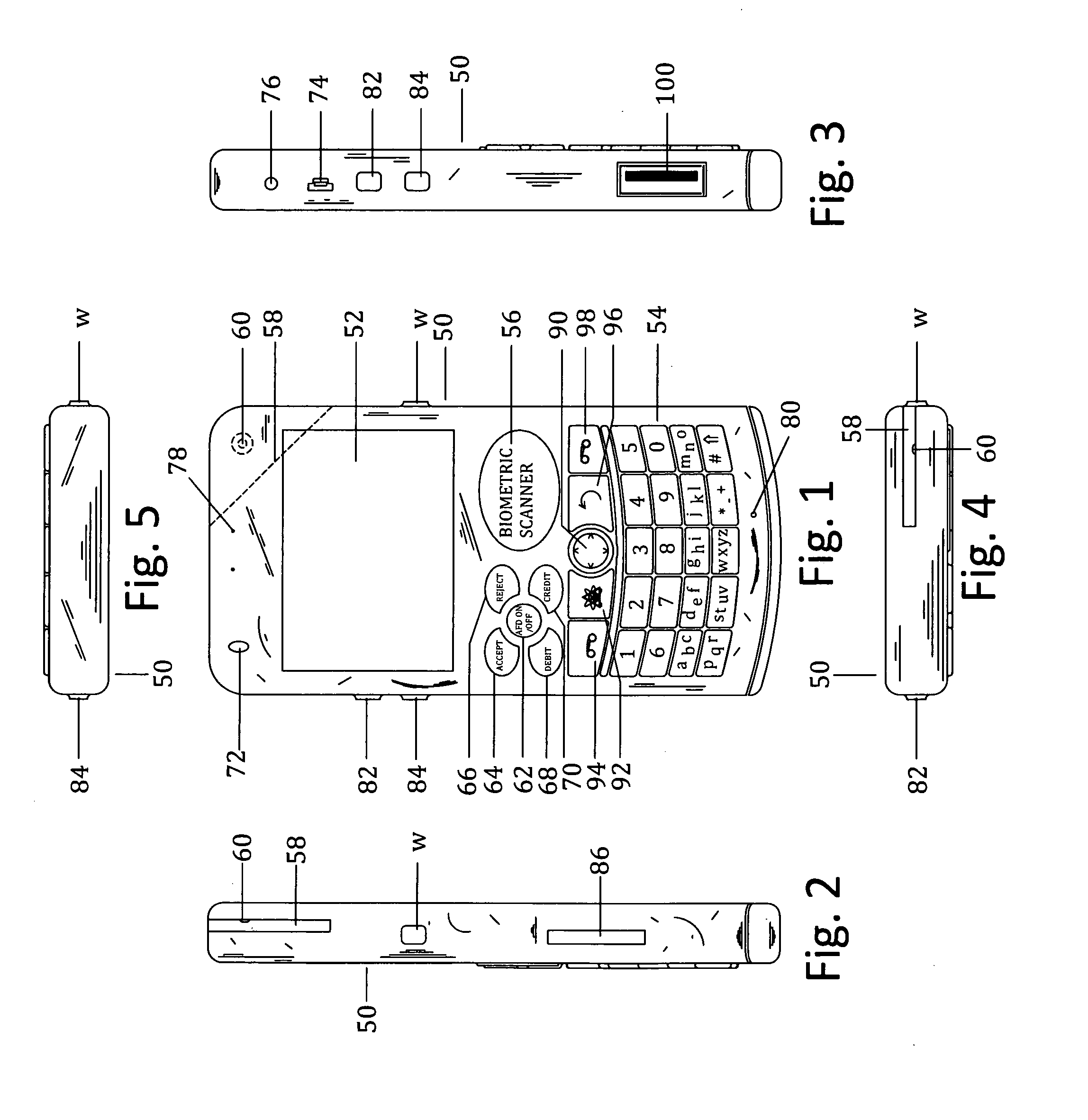
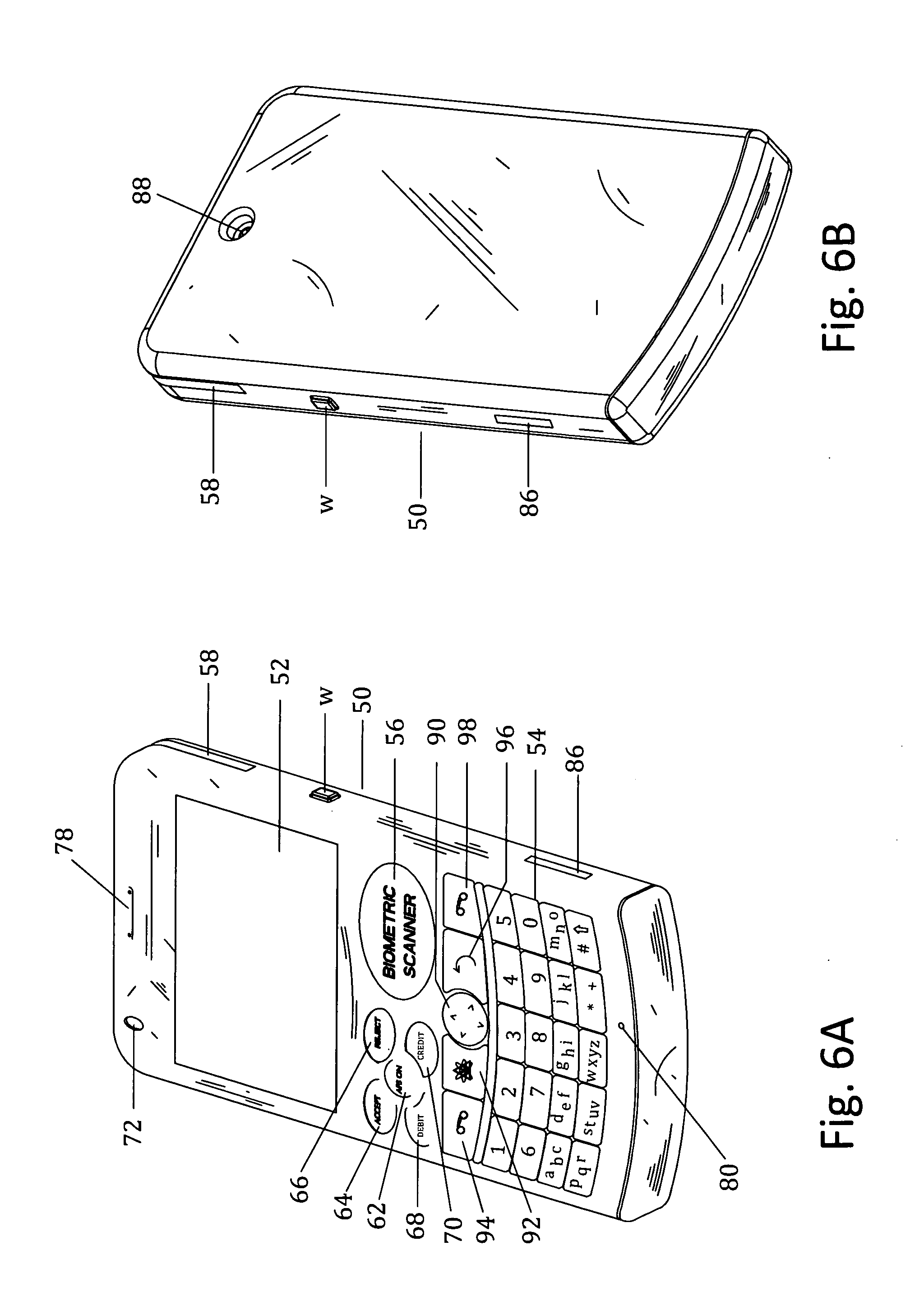
Customer-controlled instant-response anti-fraud/anti-identity theft devices (with true- personal identity verification), method and systems for secured global applications in personal/business e-banking, e-commerce, e-medical/health insurance checker, e-education/research/invention, e-disaster advisor, e-immigration, e-airport/aircraft security, e-military/e-law enforcement, with or without NFC component and system, with cellular/satellite phone/internet/multi-media functions
ActiveUS20140162598A1Prevent fraudulent multiple swipingDevices with card reading facilityUnauthorised/fraudulent call preventionChequeMessage passing
All-in-one wireless mobile telecommunication devices, methods and systems providing greater customer-control, instant-response anti-fraud / anti-identity theft protections with instant alarm, messaging and secured true-personal identity verifications for numerous registered customers / users, with biometrics and PIN security, operating with manual, touch-screen and / or voice-controlled commands, achieving secured rapid personal / business e-banking, e-commerce, accurate transactional monetary control and management, having interactive audio-visual alarm / reminder preventing fraudulent usage of legitimate physical and / or virtual credit / debit cards, with cheques anti-forgery means, curtailing medical / health / insurance frauds / identity thefts, having integrated cellular and / or satellite telephonic / internet and multi-media means, equipped with language translations, GPS navigation with transactions tagging, currency converters, with or without NFC components, minimizing potential airport risks / mishaps, providing instant aid against school bullying, kidnapping, car-napping and other crimes, applicable for secured military / immigration / law enforcements, providing guided warning / rescue during emergencies and disasters.
Owner:VILLA REAL ANTONY EUCLID C
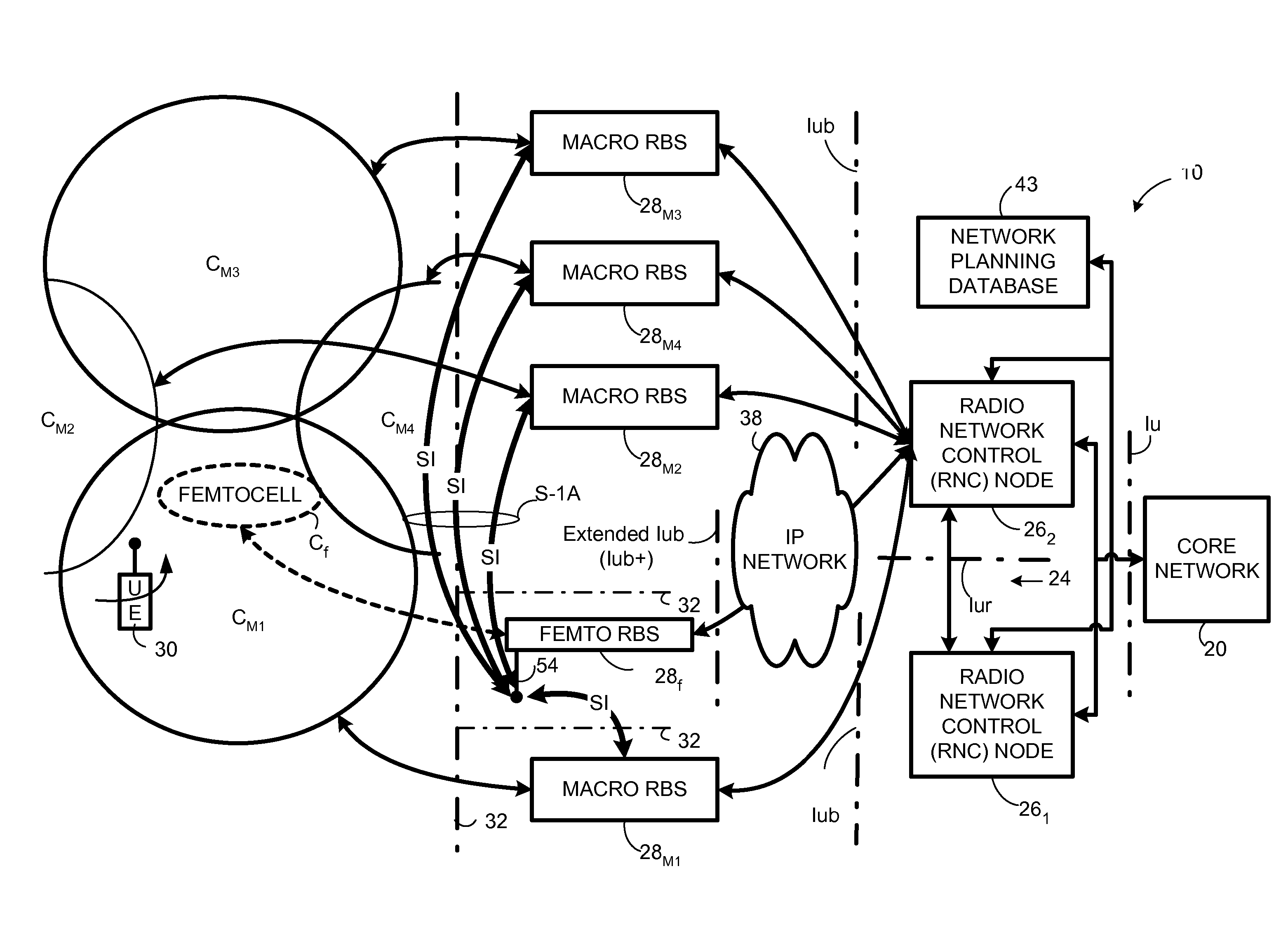
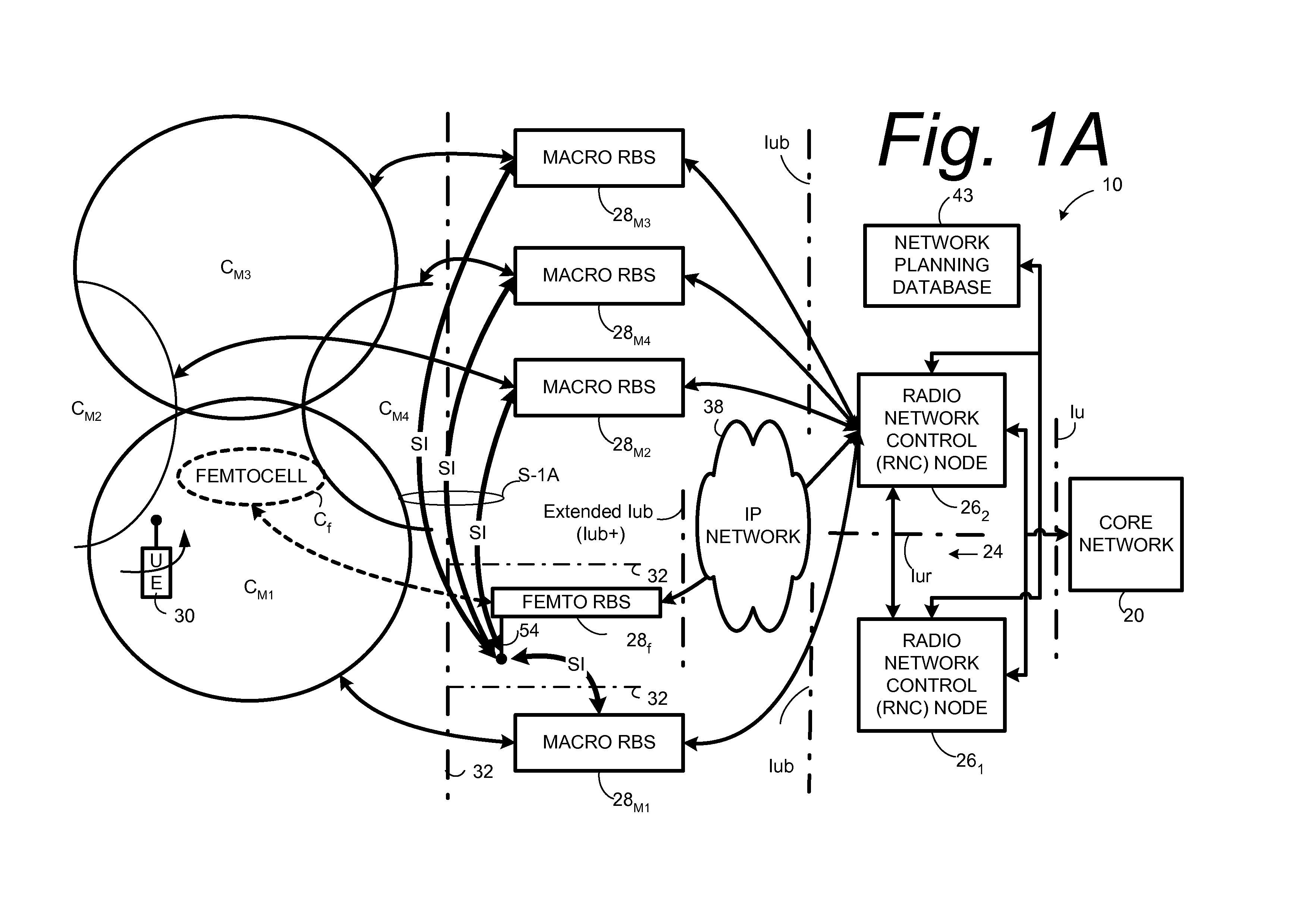
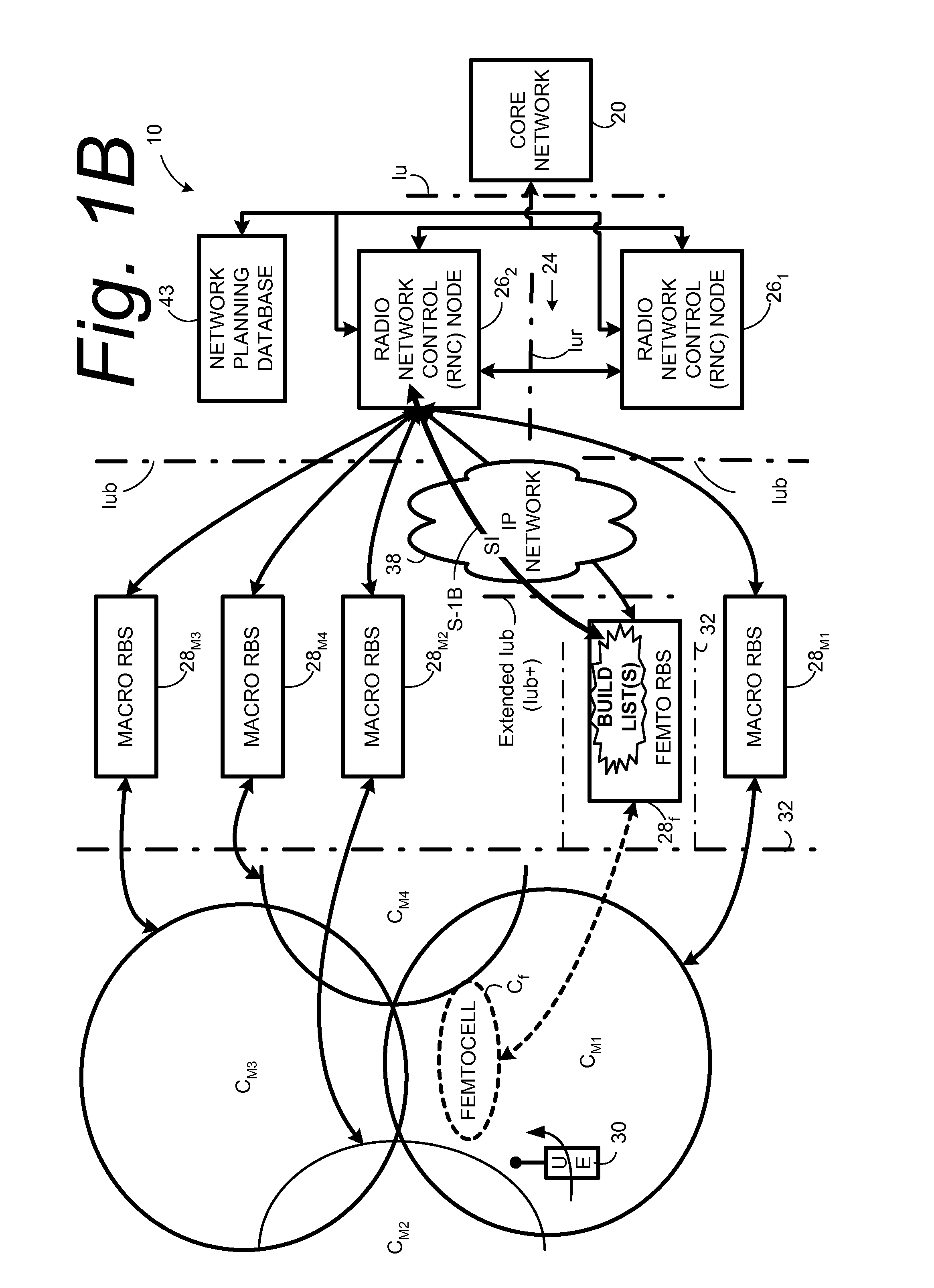
Automatic configuration of pico radio base station
Methods and apparatus configure a femto radio base station ( 28 f). A macro receiver of the femto radio base station ( 28 f) is used to acquire detected coverage information of a radio access network ( 24 ). The detected coverage information is used to determine an operation parameter for use by the macro transceiver ( 52 ) of the femto radio base station ( 28 f). In one embodiment, the detected coverage information is transmitted to a control node ( 26 ) of the radio access network. The control node ( 26 ) determines the operation parameter and communicates the operation parameter to the femto radio base station ( 28 f). The femto radio base station ( 28 f) is accordingly configured using the operation parameter for further operation towards UEs ( 30 ) accessing the femto radio base station ( 28 f).
Owner:TELEFON AB LM ERICSSON (PUBL)
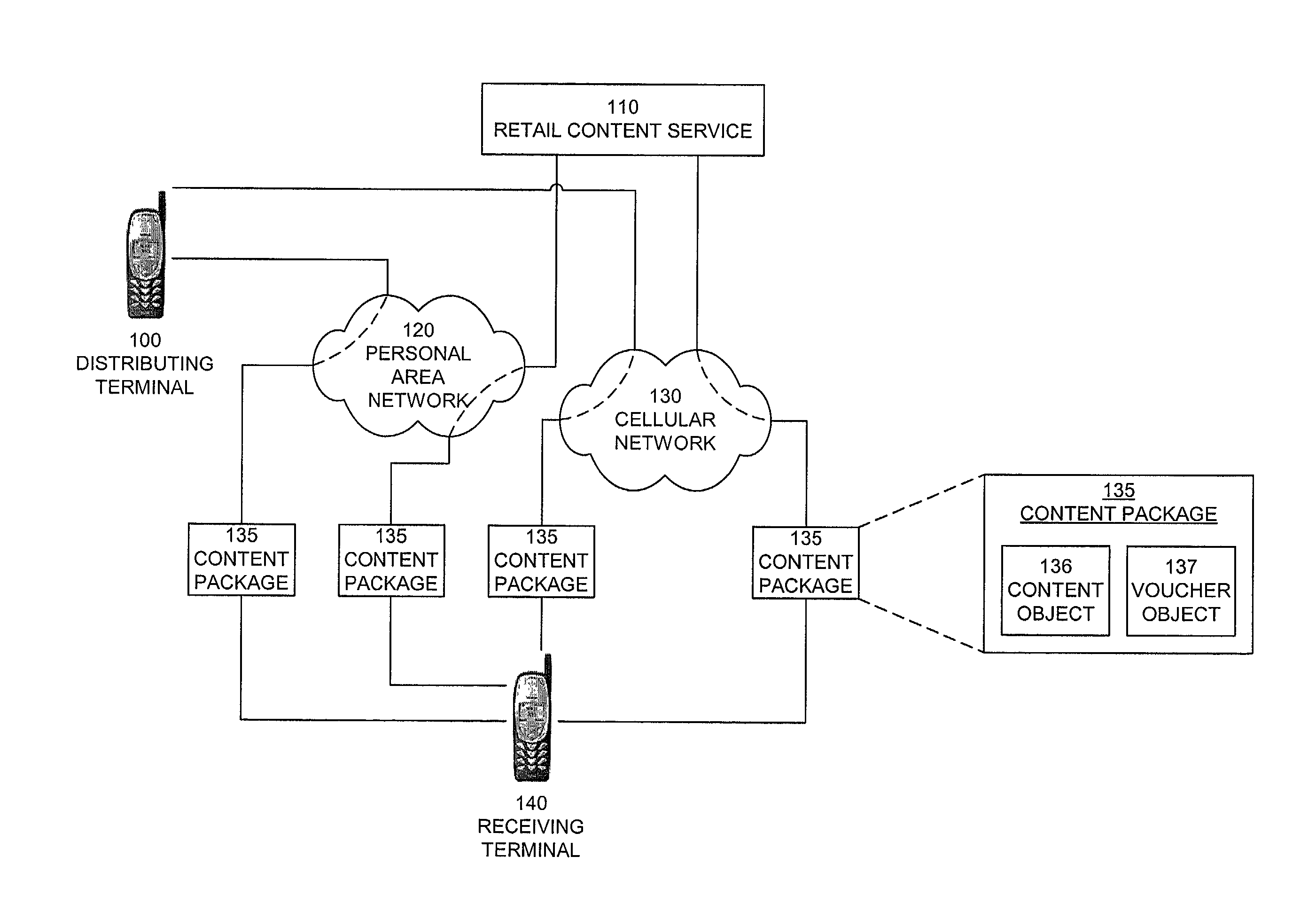
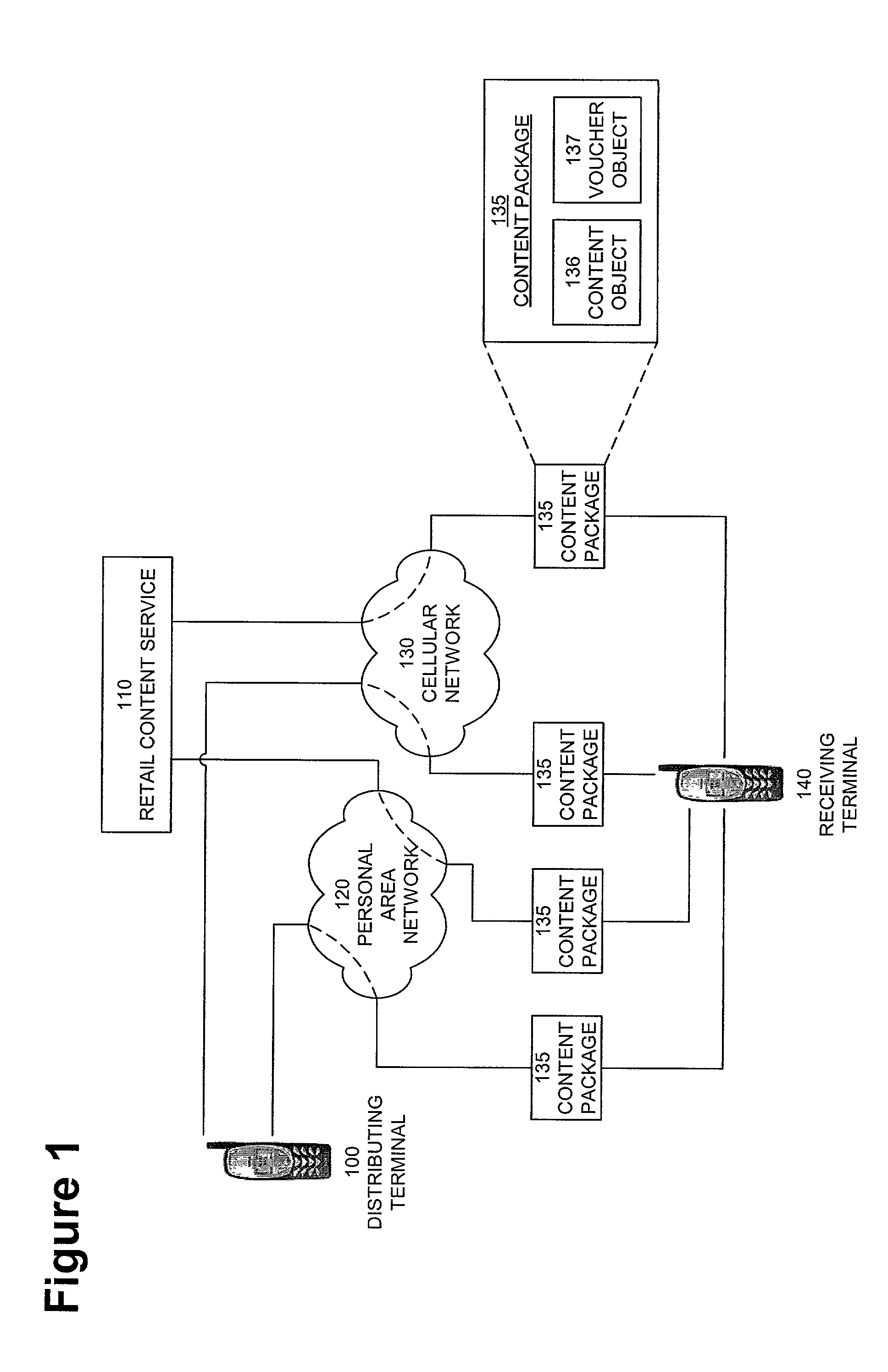
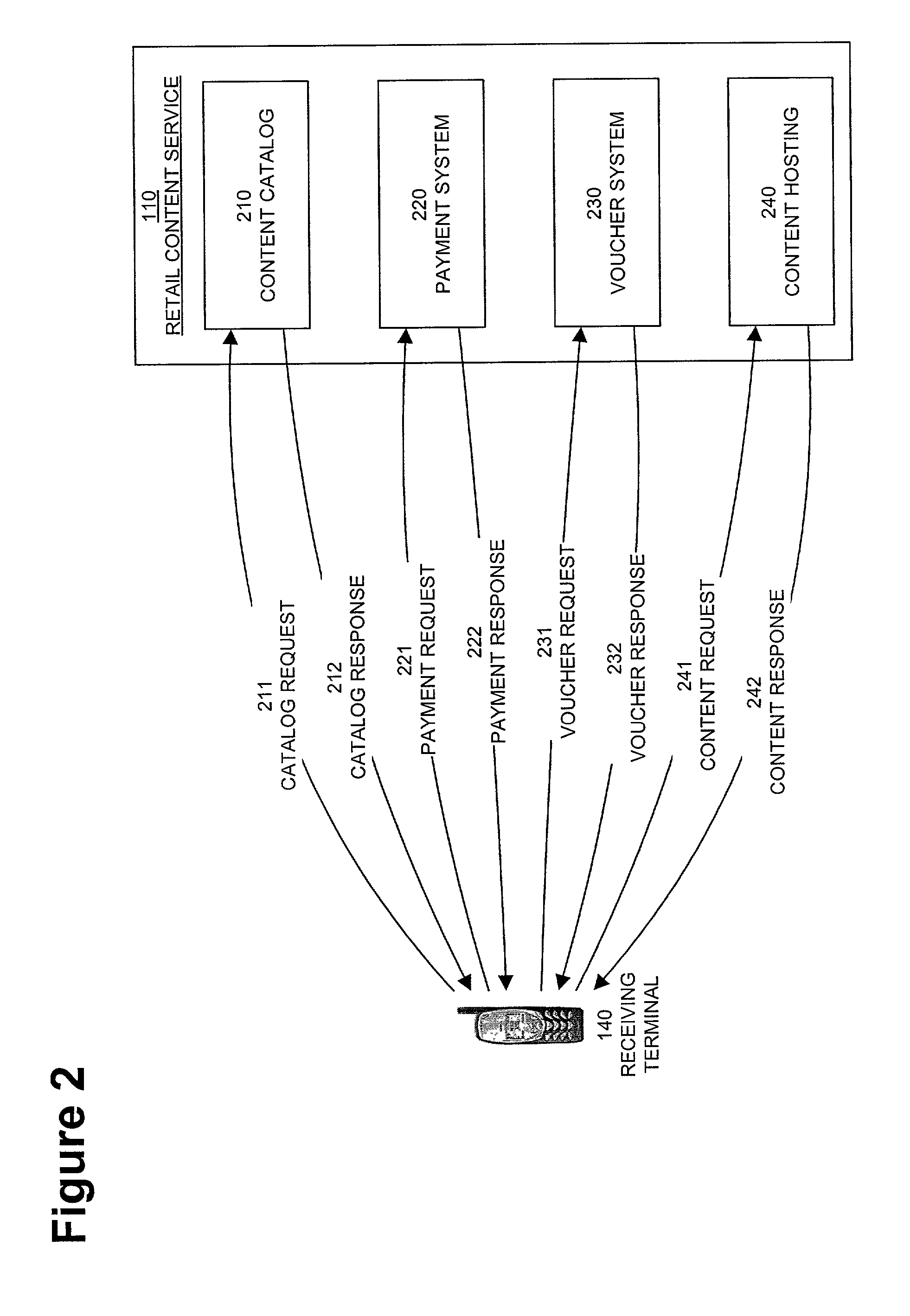
Digital rights management in a mobile communications environment
InactiveUS20050004875A1Payment architectureProgram/content distribution protectionVoucherDigital rights management
A method, system, and computer program product for enabling a wireless device in a mobile communication environment to obtain rights to protected content of a digital asset. The digital asset is downloaded to the wireless device from any one of a plurality of content servers or other wireless devices. The digital asset comprising a content ID, content encrypted with a content key, and information on obtaining rights to the content being expressed in a voucher generated by a voucher server in the network. The method, system, and computer program product also creates the digital asset for downloading to a wireless device from one of a plurality of content servers in a network and generates a voucher at the voucher server.
Owner:NOKIA TECHNOLOGLES OY
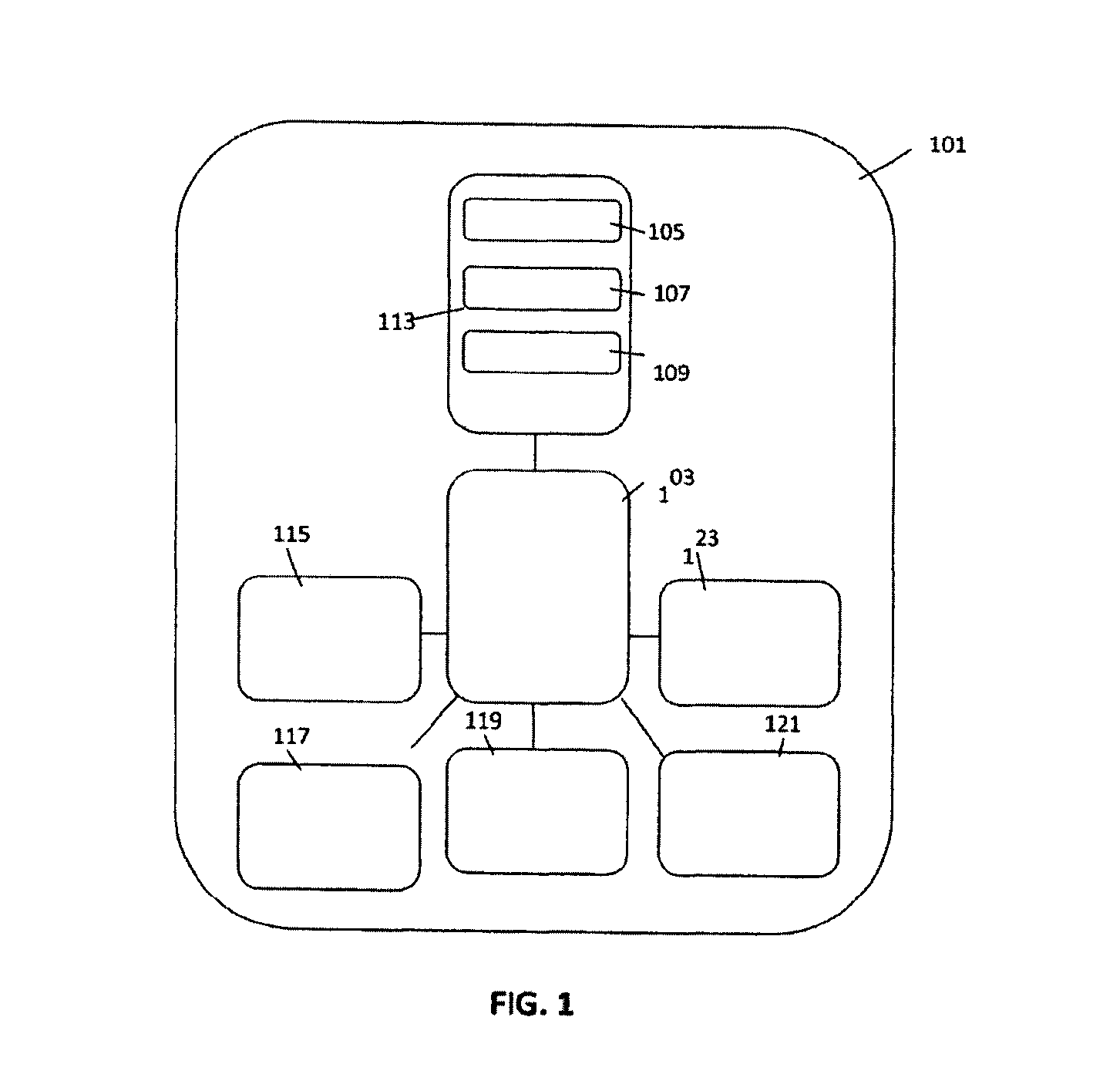
Method and system for managing data traffic in wireless networks
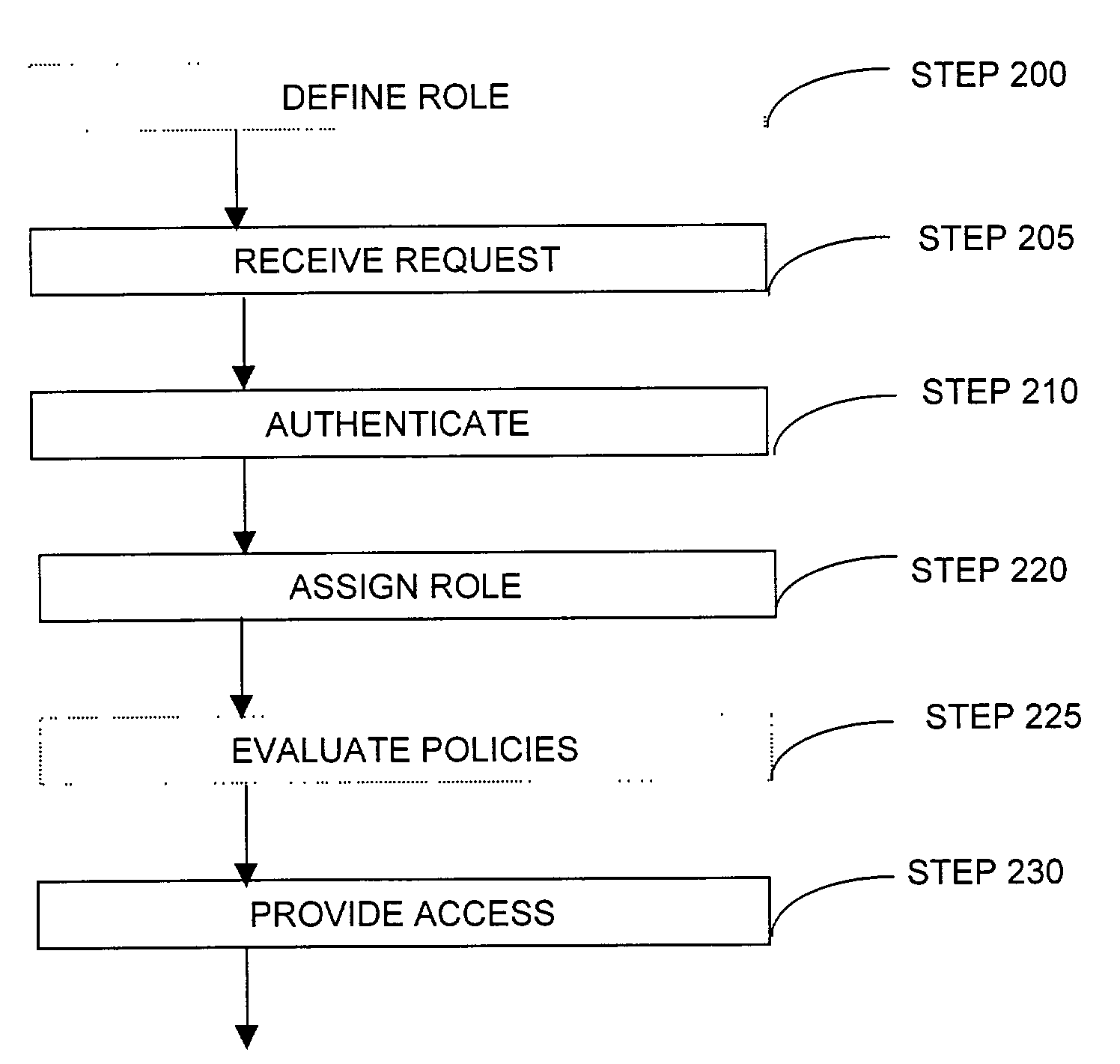
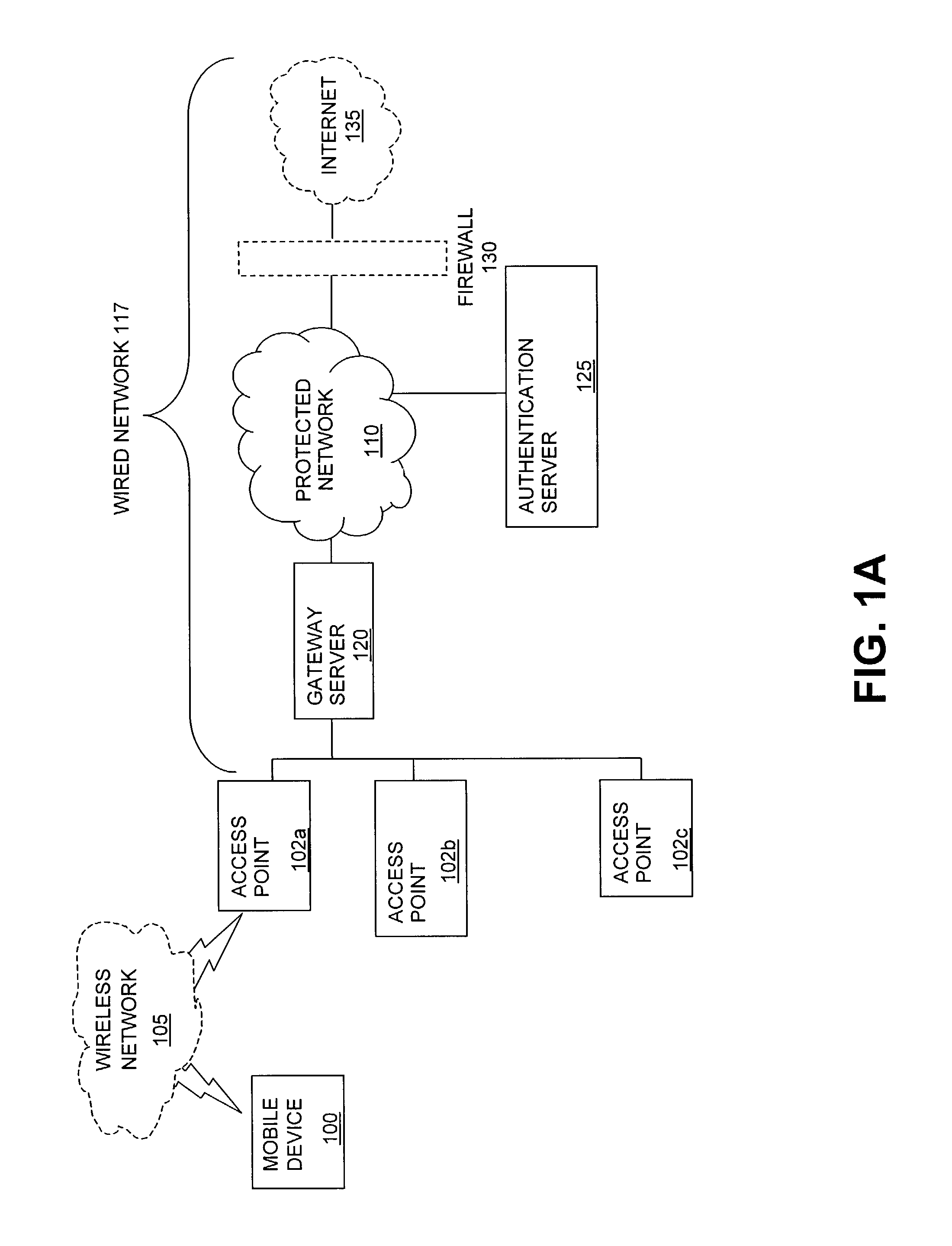
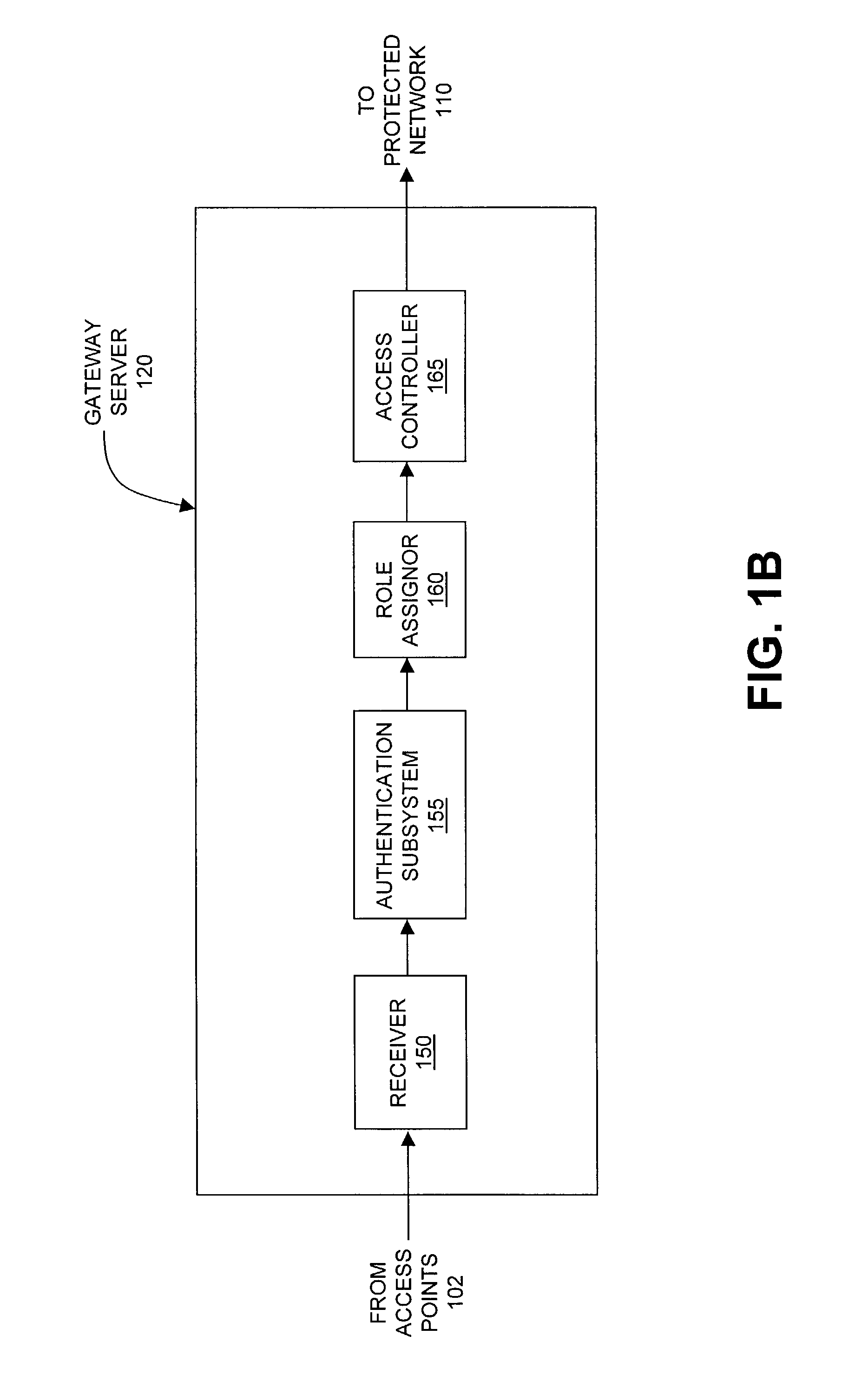
ActiveUS7042988B2Facilitate secure integrationExtensive controlError preventionUnauthorised/fraudulent call preventionWireless mesh networkNetwork architecture
The present invention can be used to facilitate the integration of wireless capability provided by wireless access points into an enterprise computer network. A gateway server is interposed between wireless access points and protected networks to provide security and integration functions, for example, authentication, access control, link privacy, link integrity, and bandwidth metering in various embodiments. Use of such a gateway server allows substantial control to be gained over network access even with the use of relatively simple access points. In general, such a gateway server receives a request to access the protected network. An authentication subsystem of the gateway server authenticates the user, preferably by accessing an external authentication server and returns a role to the authenticated user. An access controller in the gateway server provides differential access to the protected network based on the user's assigned role. A multiple gateway servers can be connected together to form a mesh network architecture.
Owner:BLUESOCKET
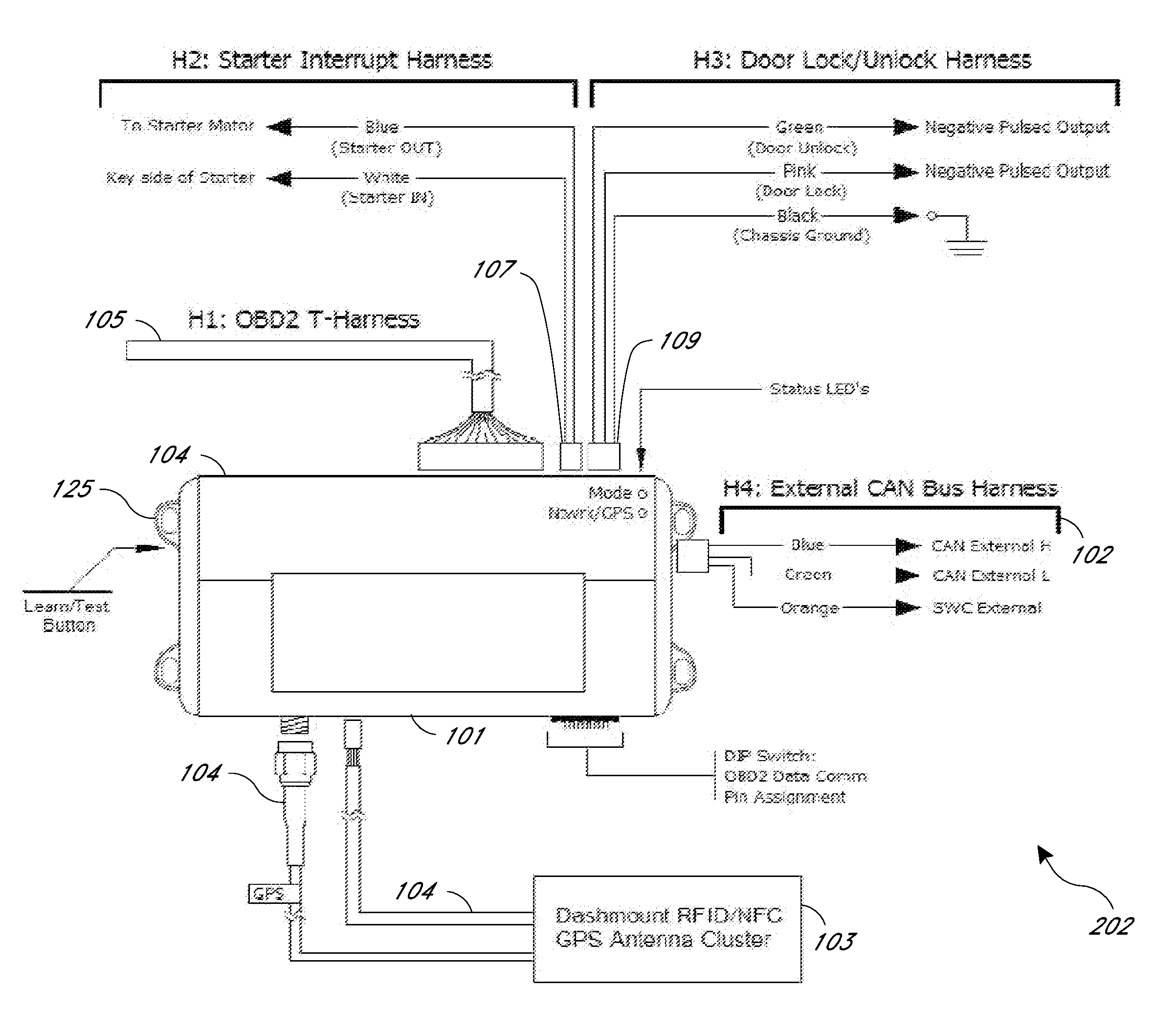
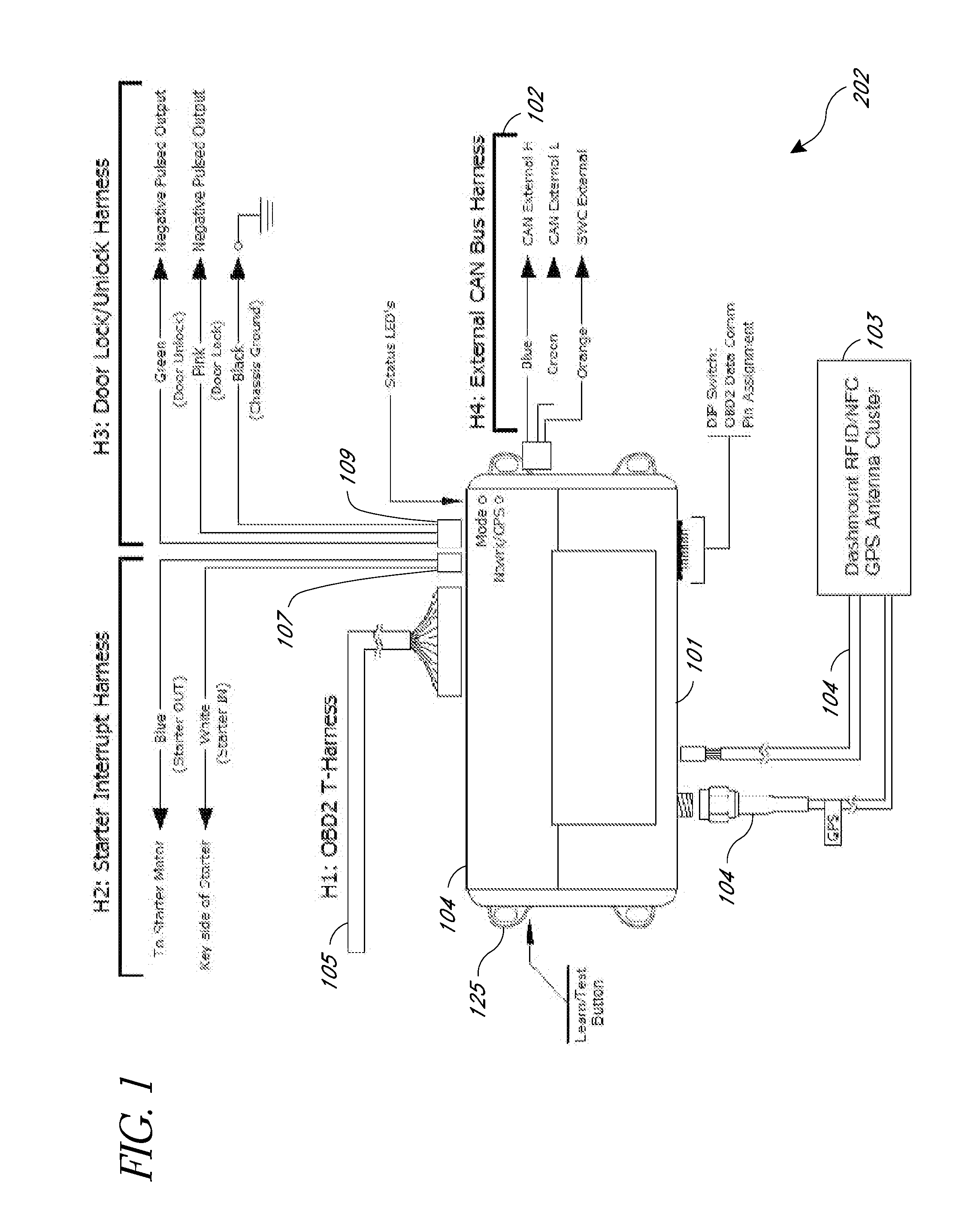
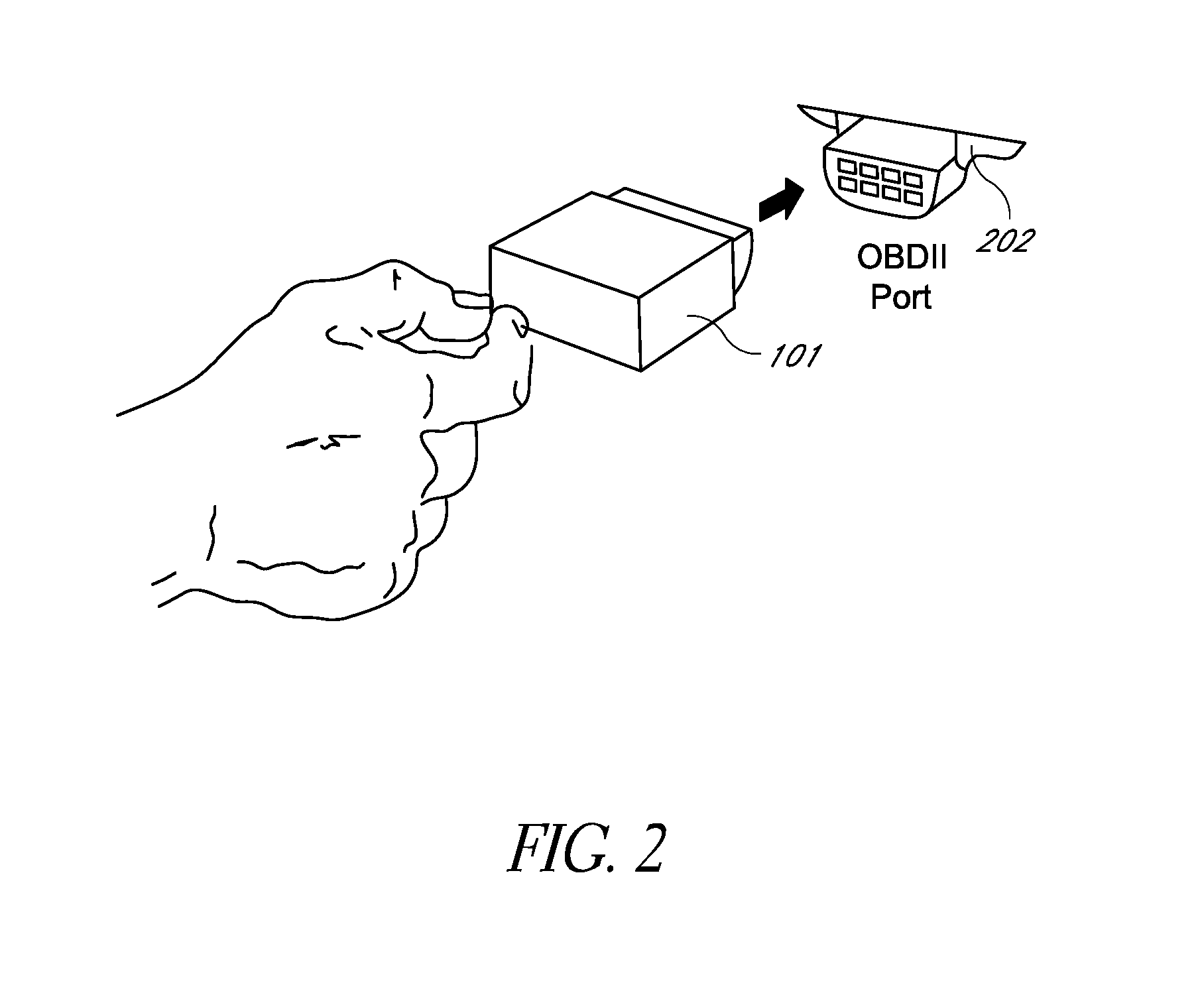
Rental/car-share vehicle access and management system and method
ActiveUS20130317693A1Reduce the time required for installationImprove reliabilityVehicle testingTicket-issuing apparatusMobile appsTablet computer
A rental / car-share (RCS) vehicle access and management system and method, in some embodiments, utilizes barcodes, QR codes (or NFC / RFID), GPS, and a mobile app coupled with a wireless network to enable customers to bypass the reservation desk and pickup and drop off reserved RCS vehicles using a mobile phone, tablet or laptop. The QR code, RFID, or NFC communication with the mobile application allows for identification of the vehicle by a mobile application, which, if authorized, can access the vehicle via a temporary access code issued by remote servers. The remote servers and / or mobile application communicates with a control module that plugs into the on-board diagnostics module of the rental / car-share (RCS) vehicle and includes a host processing unit with a processor, an accelerometer, data storage, a GPS with internal GPS antenna; a wireless modem with internal antenna, and CAN bus transceivers connected with the processor, and a USB programmable interface.
Owner:ENTERPRISE HOLDINGS
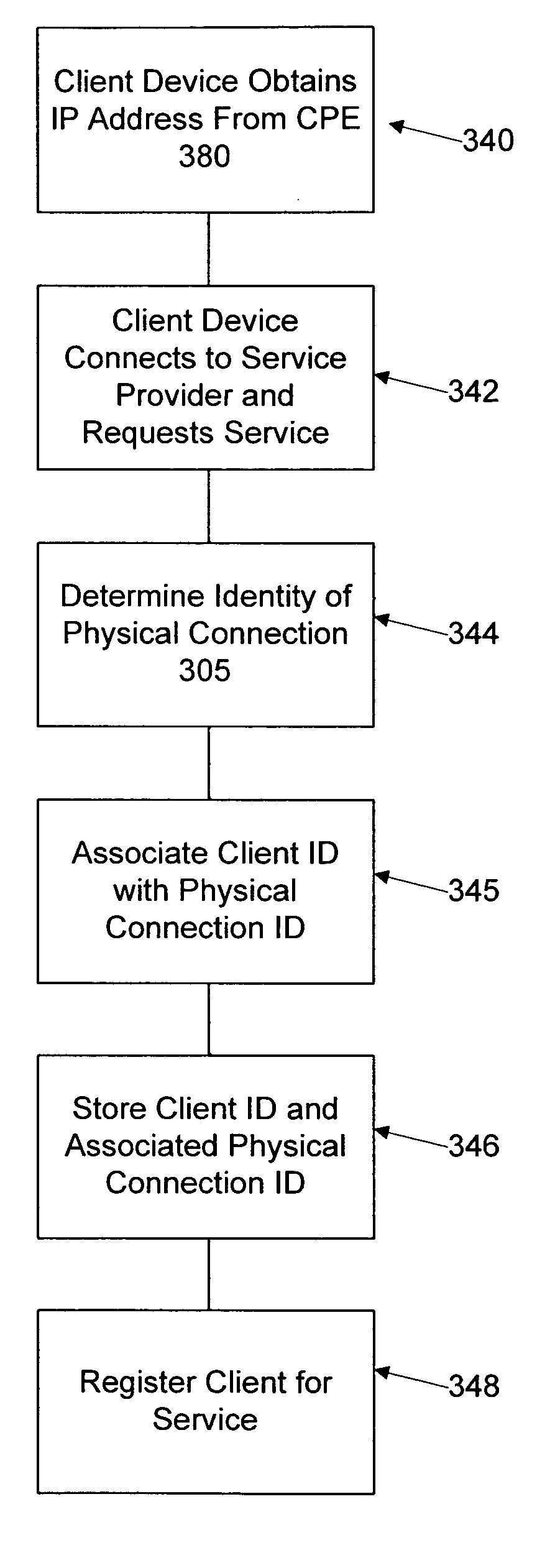
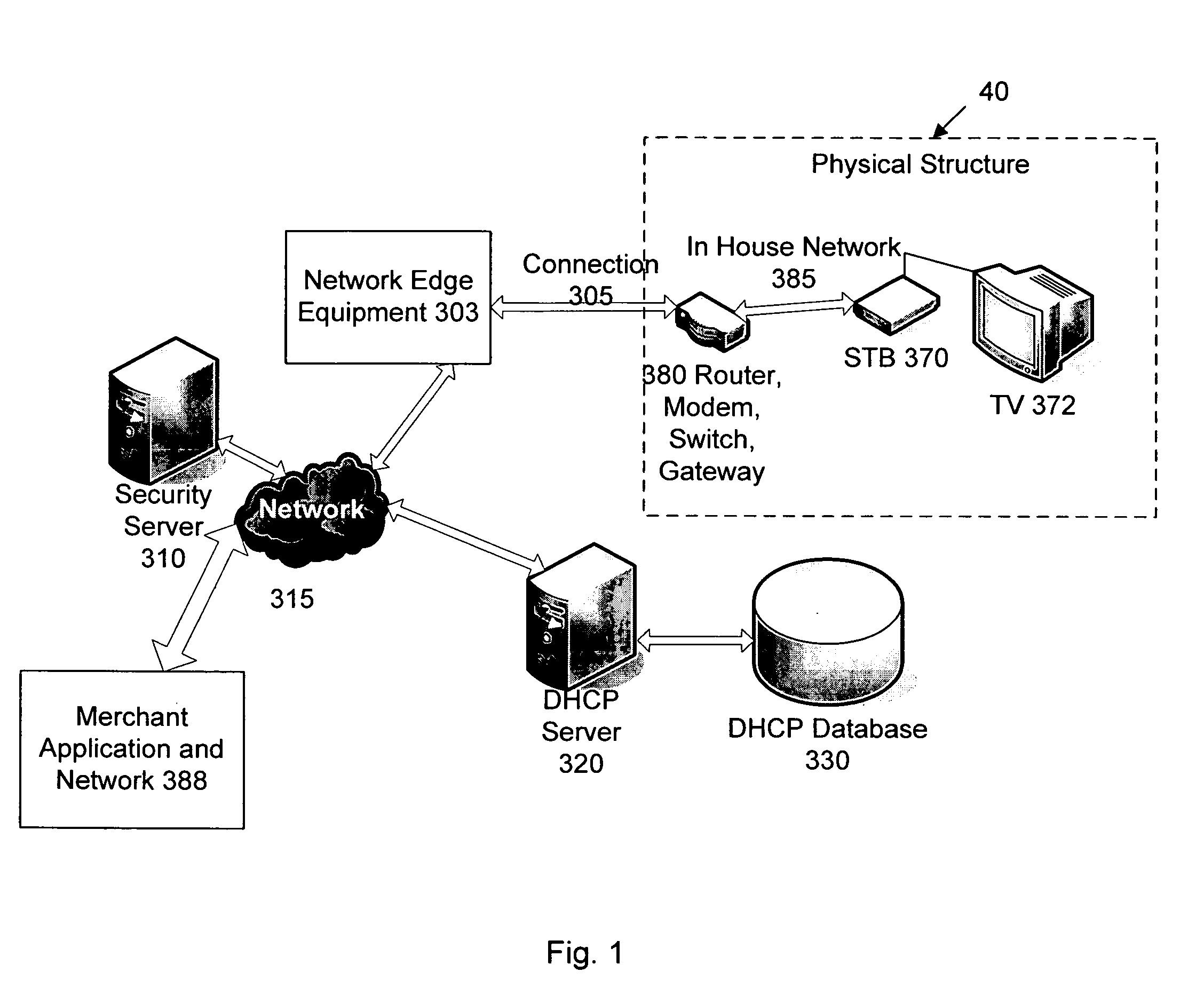
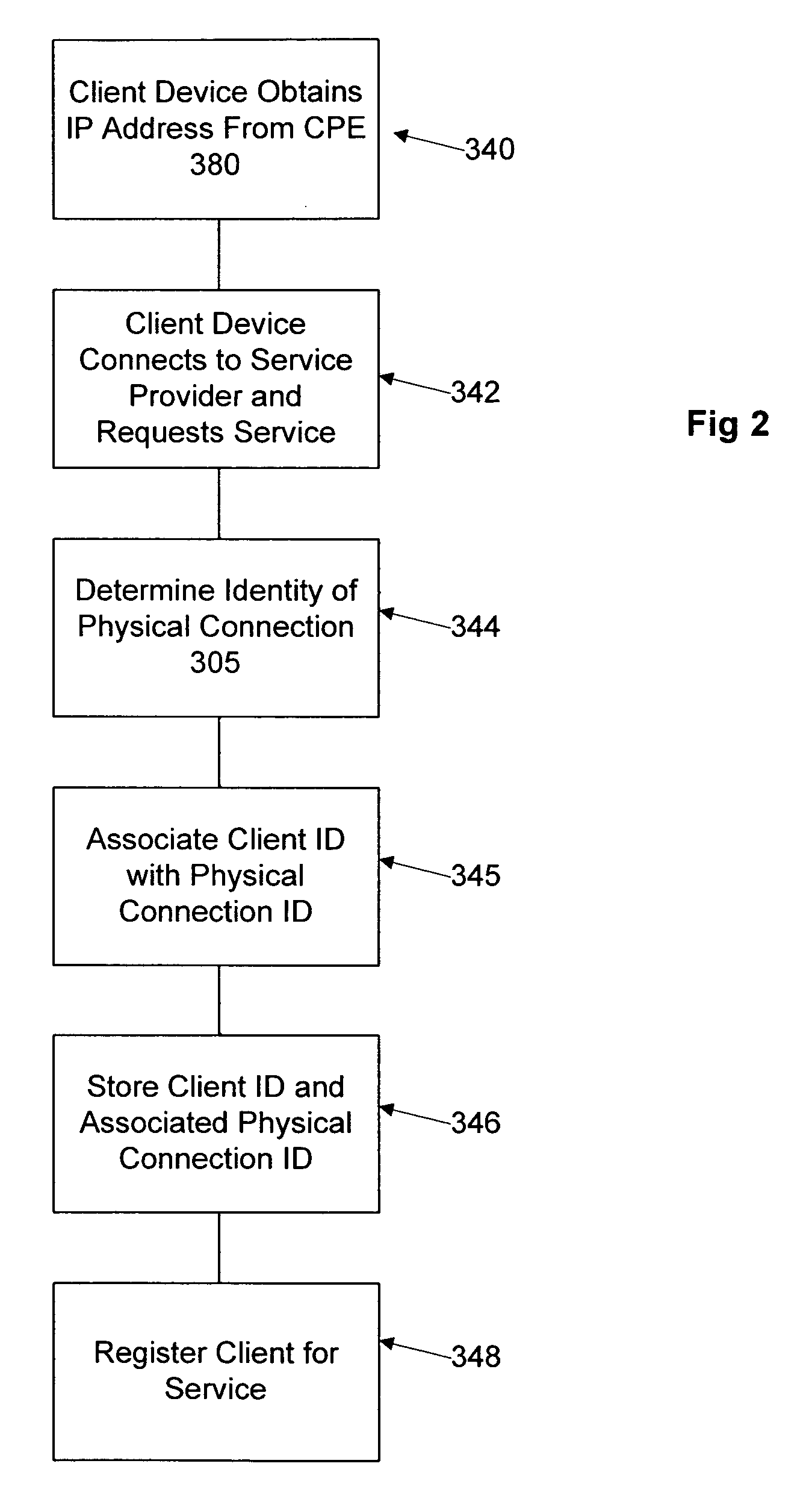
Network user authentication system and method
ActiveUS20070022469A1Removal difficult and impossibleThe certification process is reliableDigital data processing detailsUser identity/authority verificationUnique identifierAuthentication server
In a network user authentication system, a network user is identified for authentication purposes using the unique identifier for a dedicated physical communication line associated with the building in which the network user is located or a digital certificate which is associated with a secure component or communication line physically attached to a building. An authentication server initially verifies the identification of the dedicated communication line to be associated with a network service subscriber or issues a unique digital certificate to be associated with the dedicated communication line for authentication purposes. The digital certificate may be stored in a building gateway or in an edge site module which is connected to the secure components of a plurality of buildings and stores unique digital certificates for each building.
Owner:VERIMATRIX INC
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com