Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
22554 results about "Authorization" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Authorization is the function of specifying access rights/privileges to resources, which is related to information security and computer security in general and to access control in particular. More formally, "to authorize" is to define an access policy. For example, human resources staff are normally authorized to access employee records and this policy is usually formalized as access control rules in a computer system. During operation, the system uses the access control rules to decide whether access requests from (authenticated) consumers shall be approved (granted) or disapproved (rejected). Resources include individual files or an item's data, computer programs, computer devices and functionality provided by computer applications. Examples of consumers are computer users, computer Software and other Hardware on the computer.
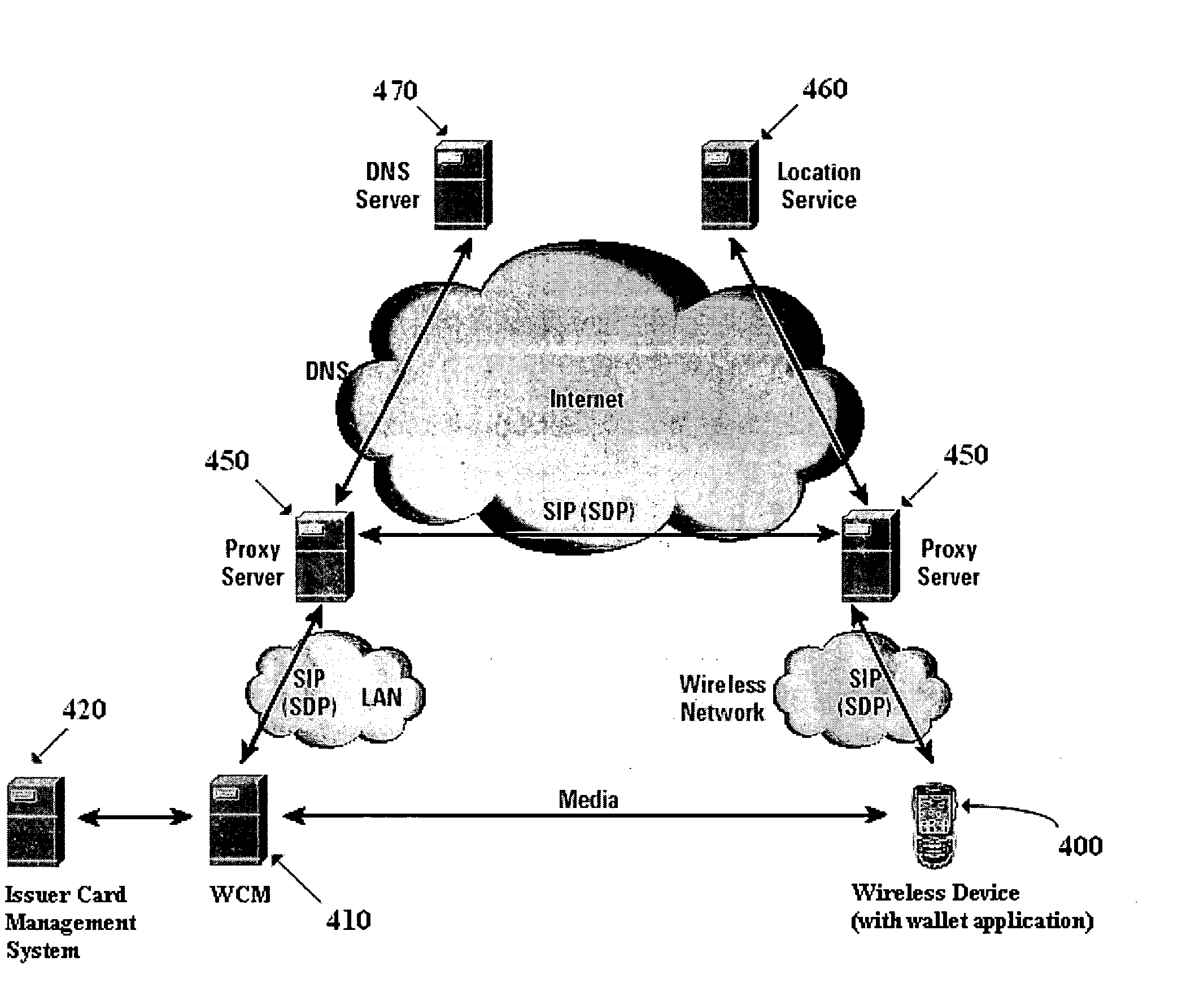
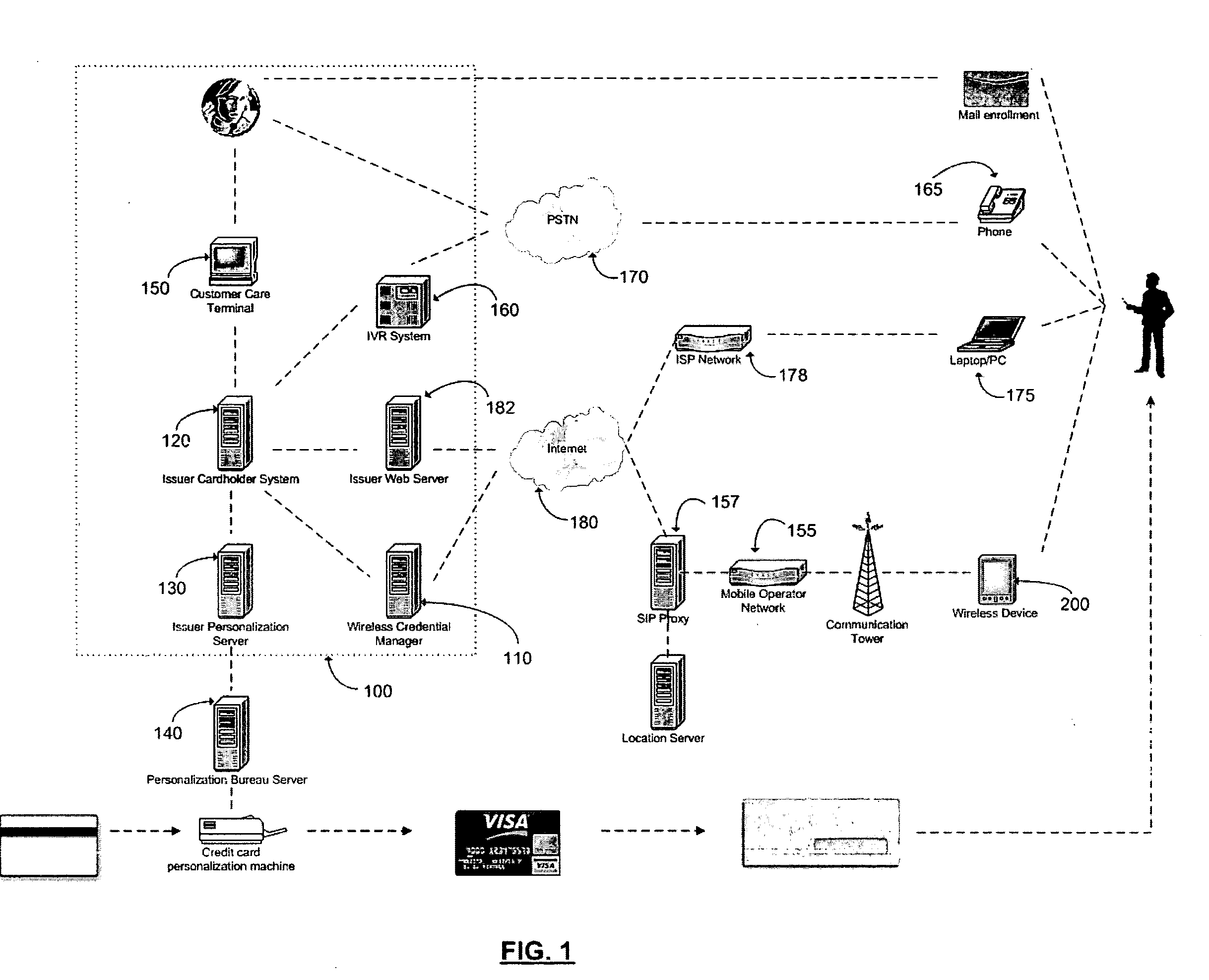
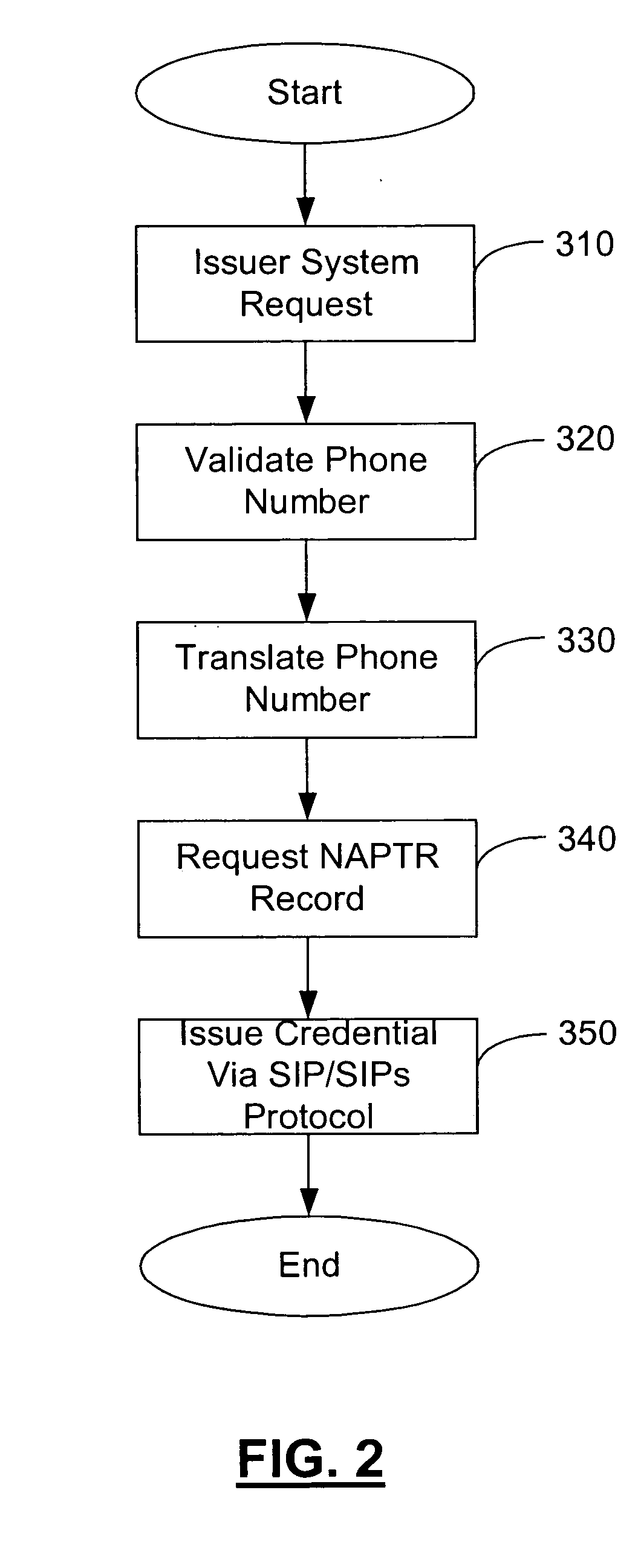
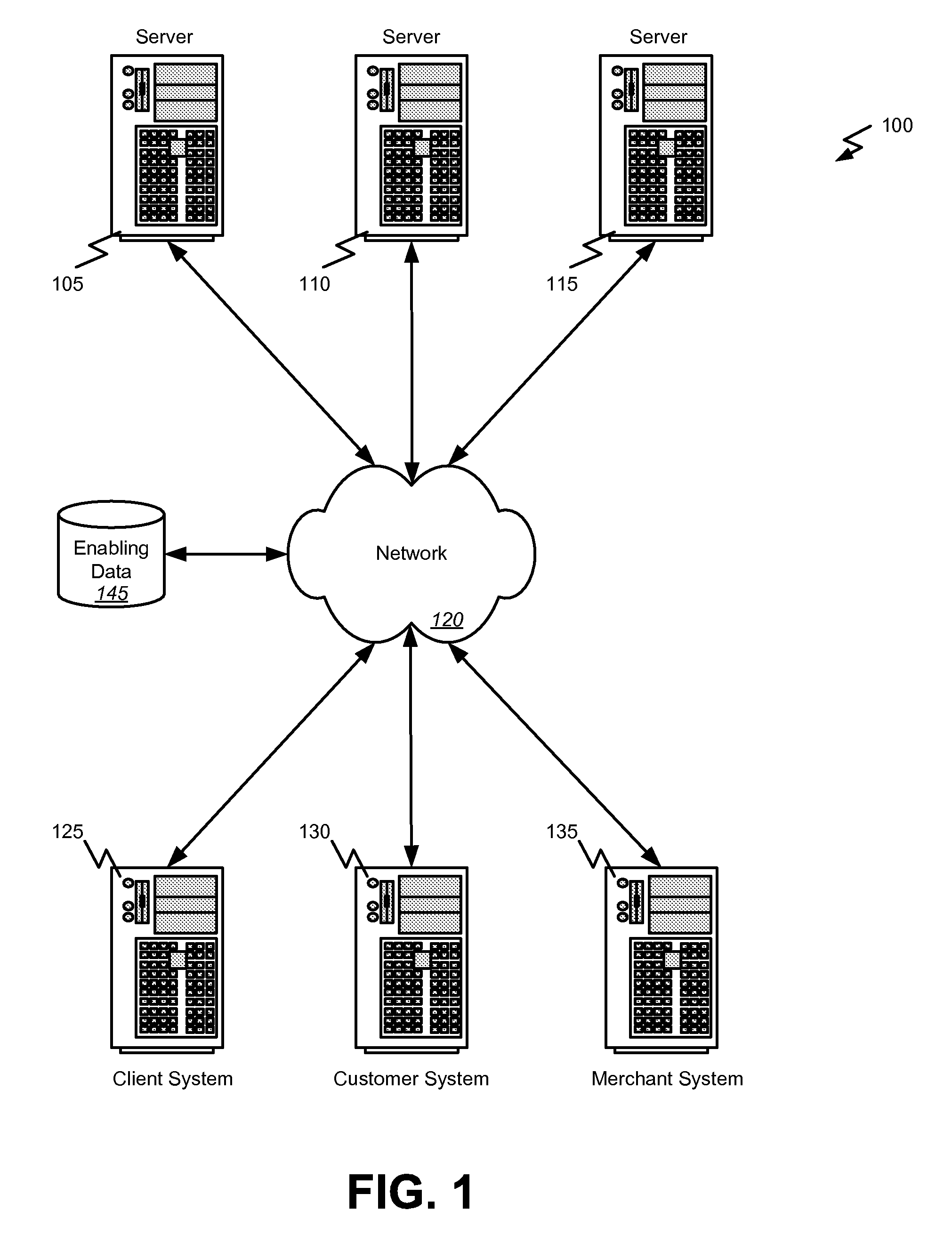
Method and apparatus for managing credentials through a wireless network
ActiveUS20060165060A1Convenient and efficient and secure distributionNear-field in RFIDData switching by path configurationCredit cardWireless mesh network
A novel system and methodology for conducting financial and other transactions using a wireless device. Credentials may be selectively issued by issuers such as credit card companies, banks, and merchants to consumers permitting the specific consumer to conduct a transaction according to the authorization given as reflected by the credential or set of credentials. The preferred mechanism for controlling and distributing credentials according to the present invention is through one or more publicly accessible networks such as the Internet wherein the system design and operating characteristics are in conformance with the standards and other specific requirements of the chosen network or set of networks. Credentials are ultimately supplied to a handheld device such as a mobile telephone via a wireless network. The user holding the credential may then use the handheld device to conduct the authorized transaction or set of transactions via, for example, a short range wireless link with a point-of-sale terminal.
Owner:SAMSUNG ELECTRONICS CO LTD
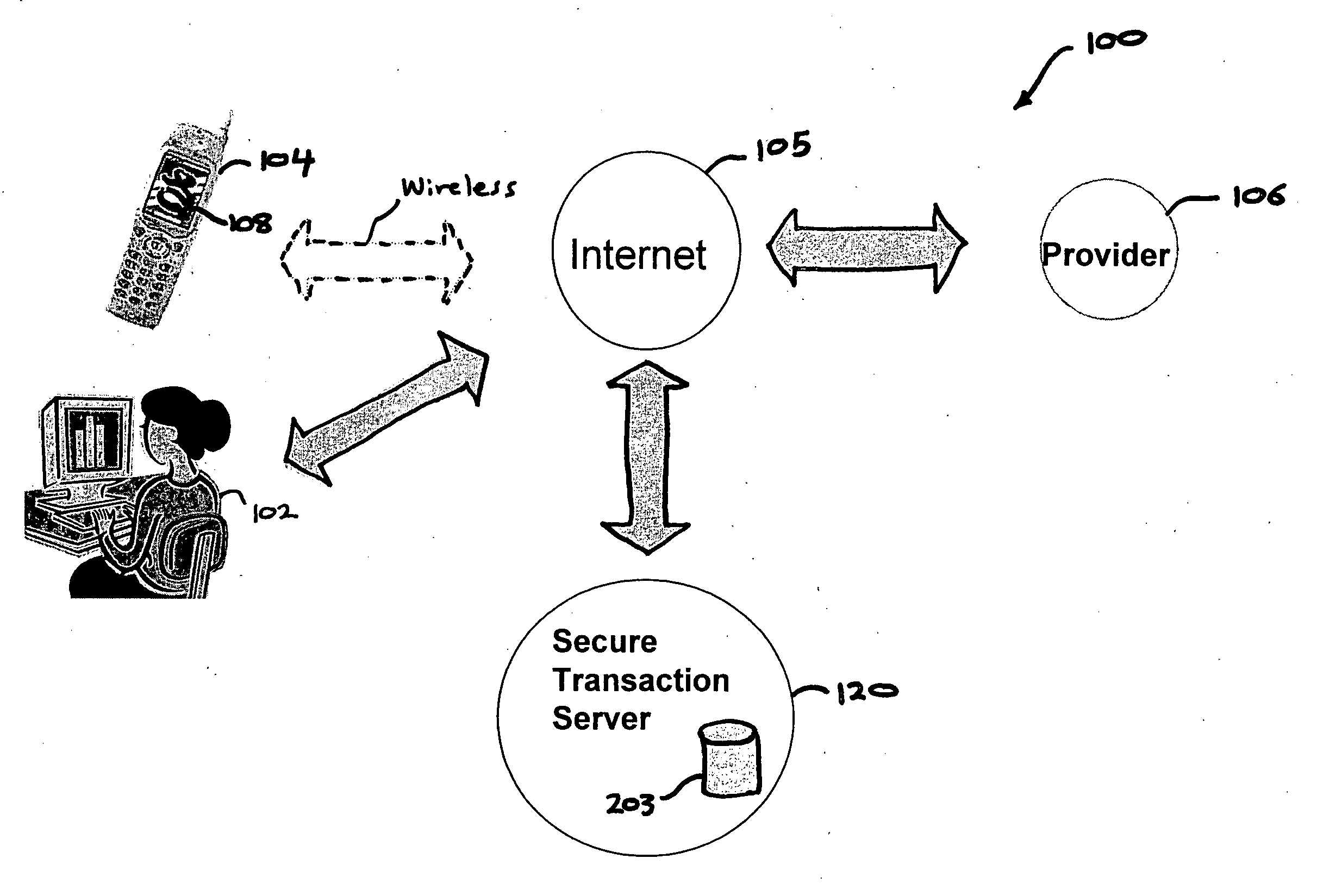
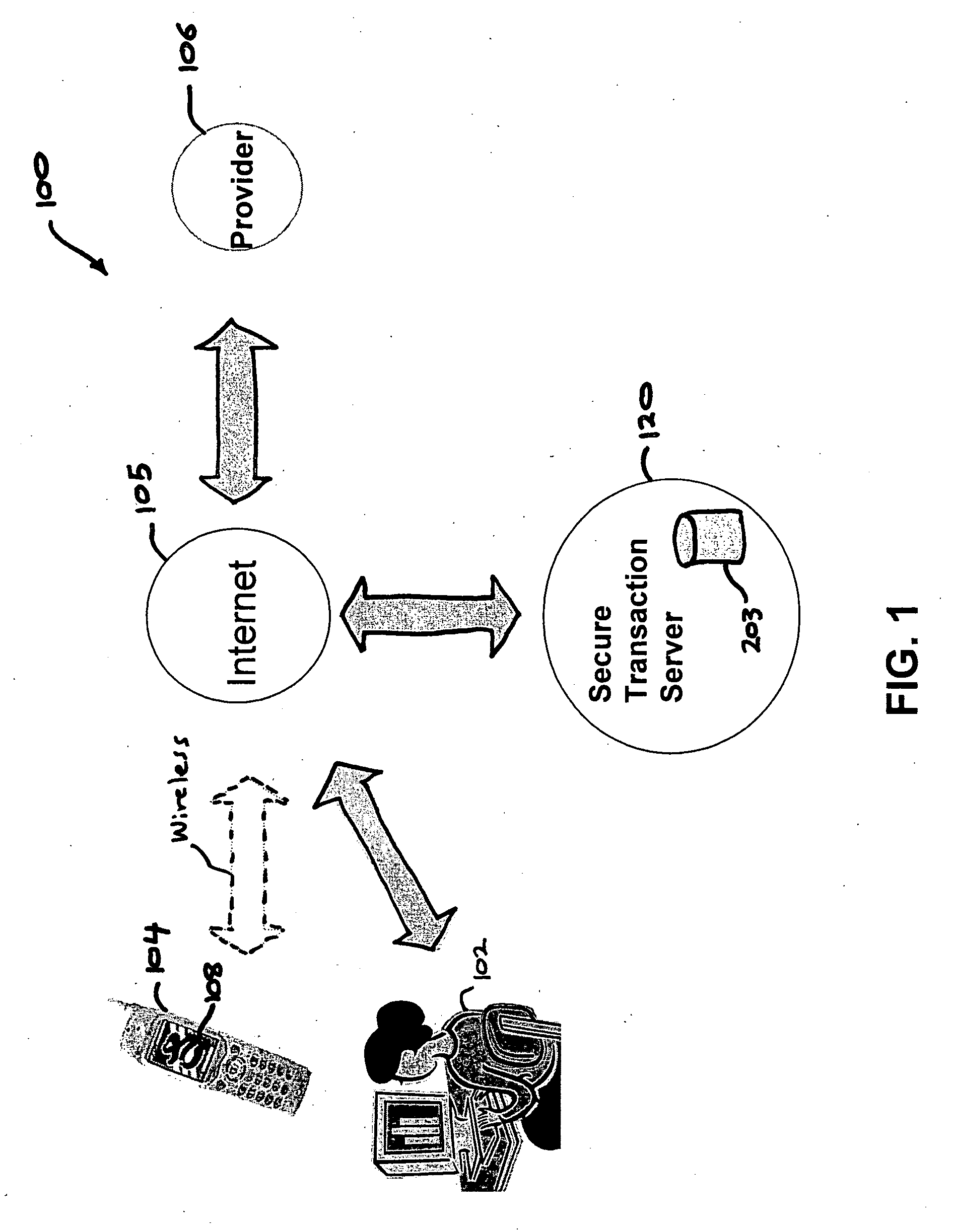
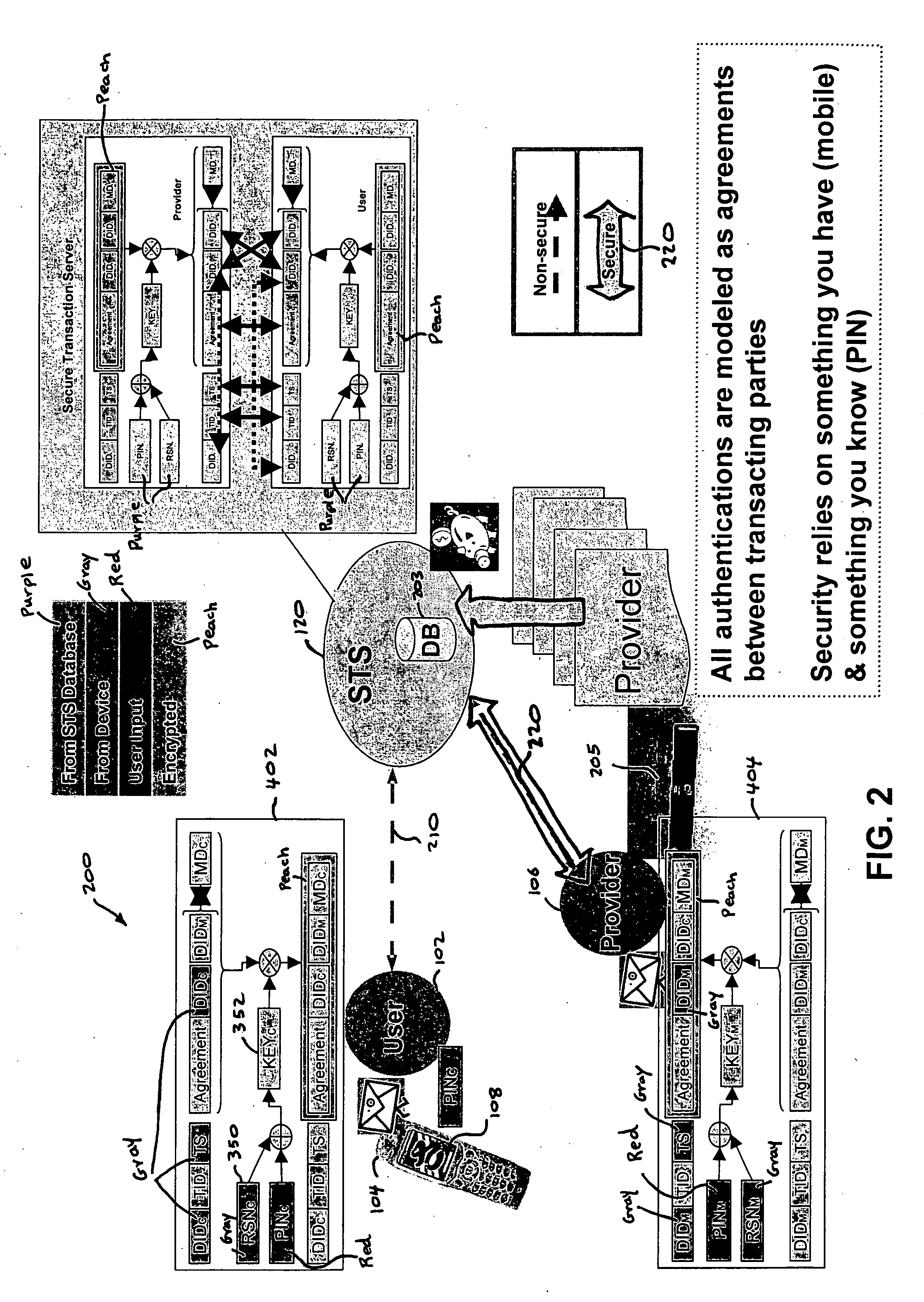
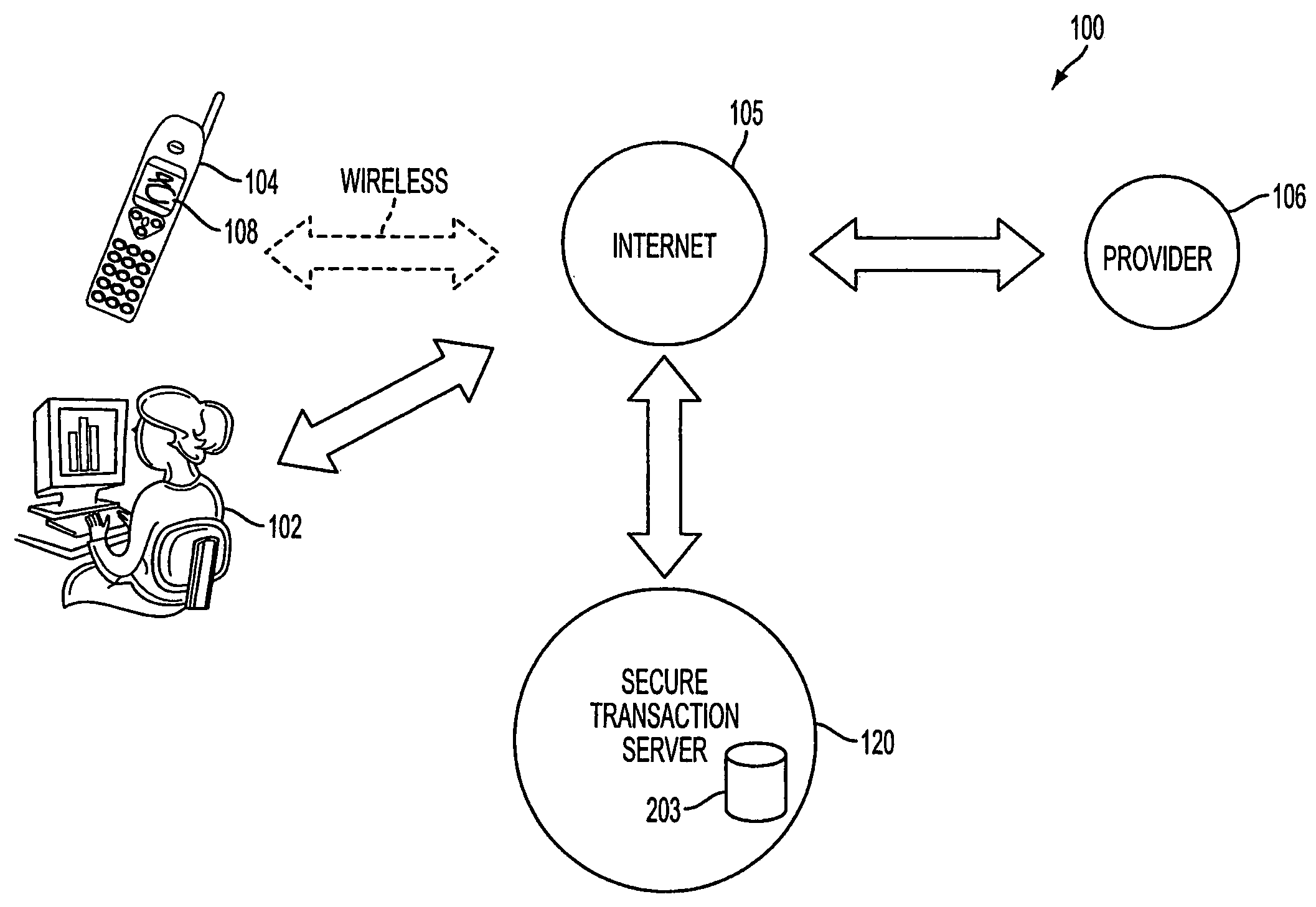
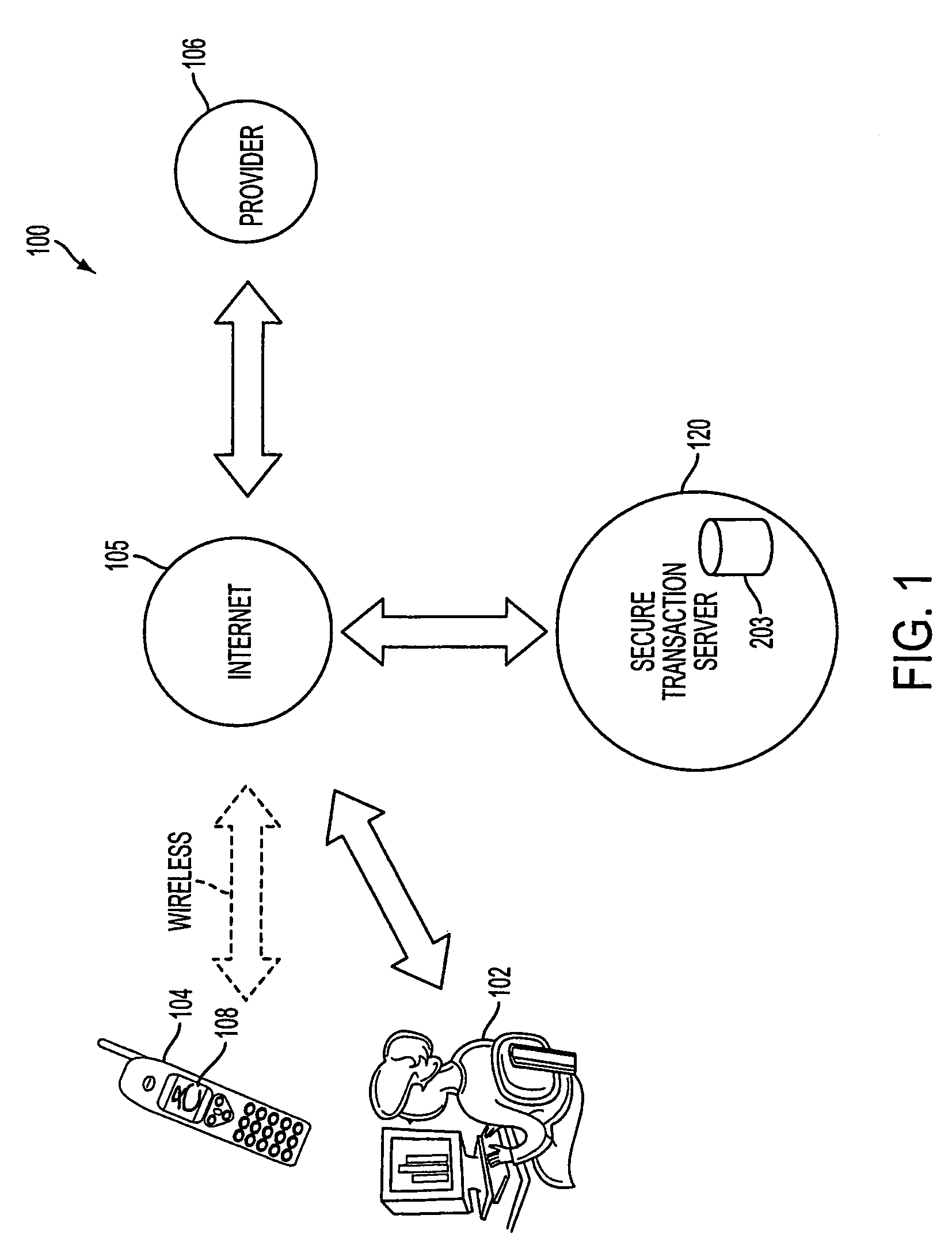
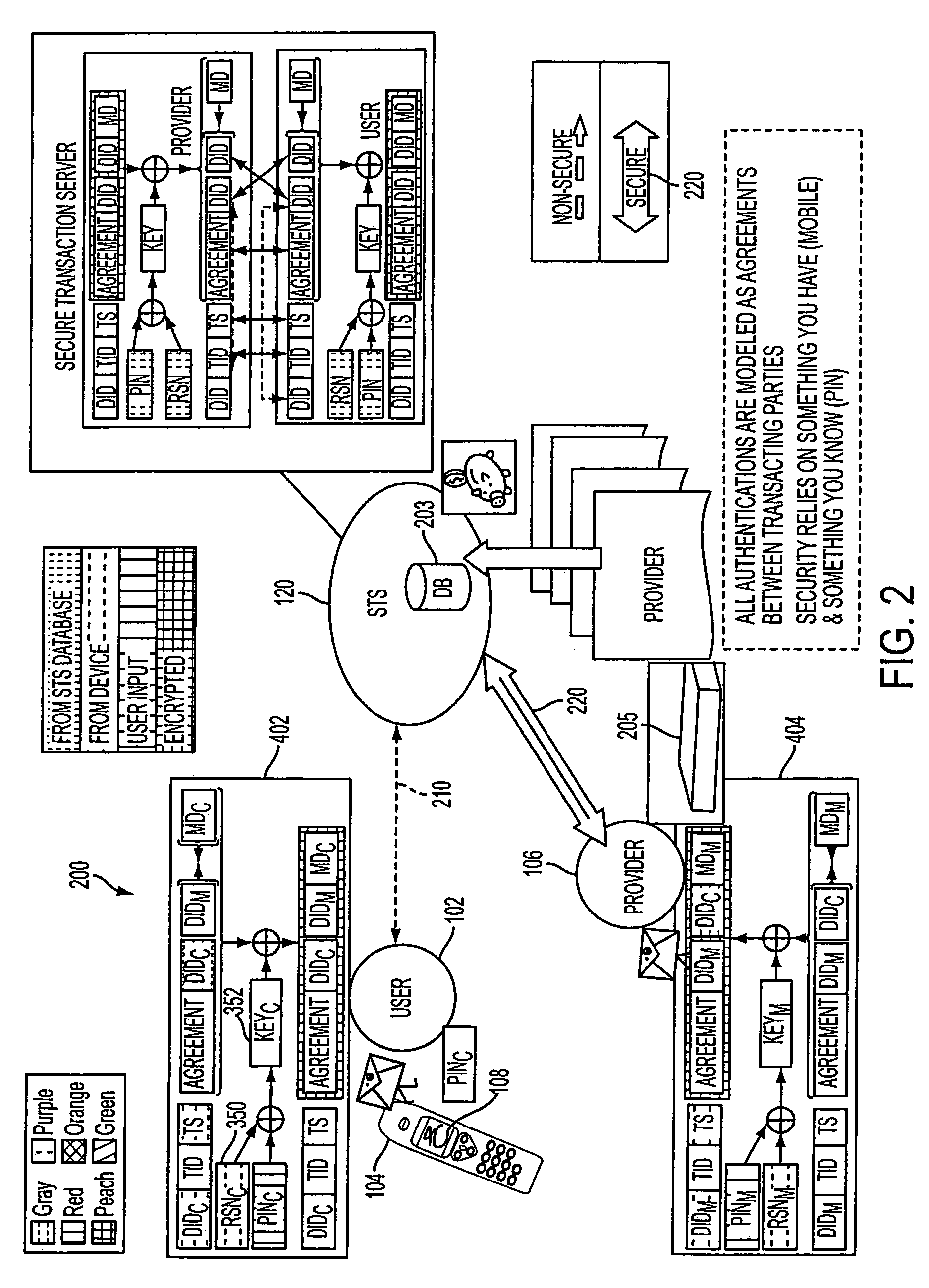
Authentication services using mobile device
InactiveUS20060206709A1Payment architectureATM softwaresInternet Authentication ServiceMobile device
A method, and an apparatus performing the method, is provided by authenticating a mobile device communicably connectable to a wireless network by an authentication parameter from a secure transaction server (STS), as a mobile device authenticator; providing an STS correlation between a personal identification entry (PIE) and the mobile device authenticator; and inputting, by a user, the PIE and a provider action, to the mobile device authenticator to transmit a transformed secure user authenticable authorization request to the STS over the wireless network to authorize an action with a provider.
Owner:PCMS HOLDINGS INC
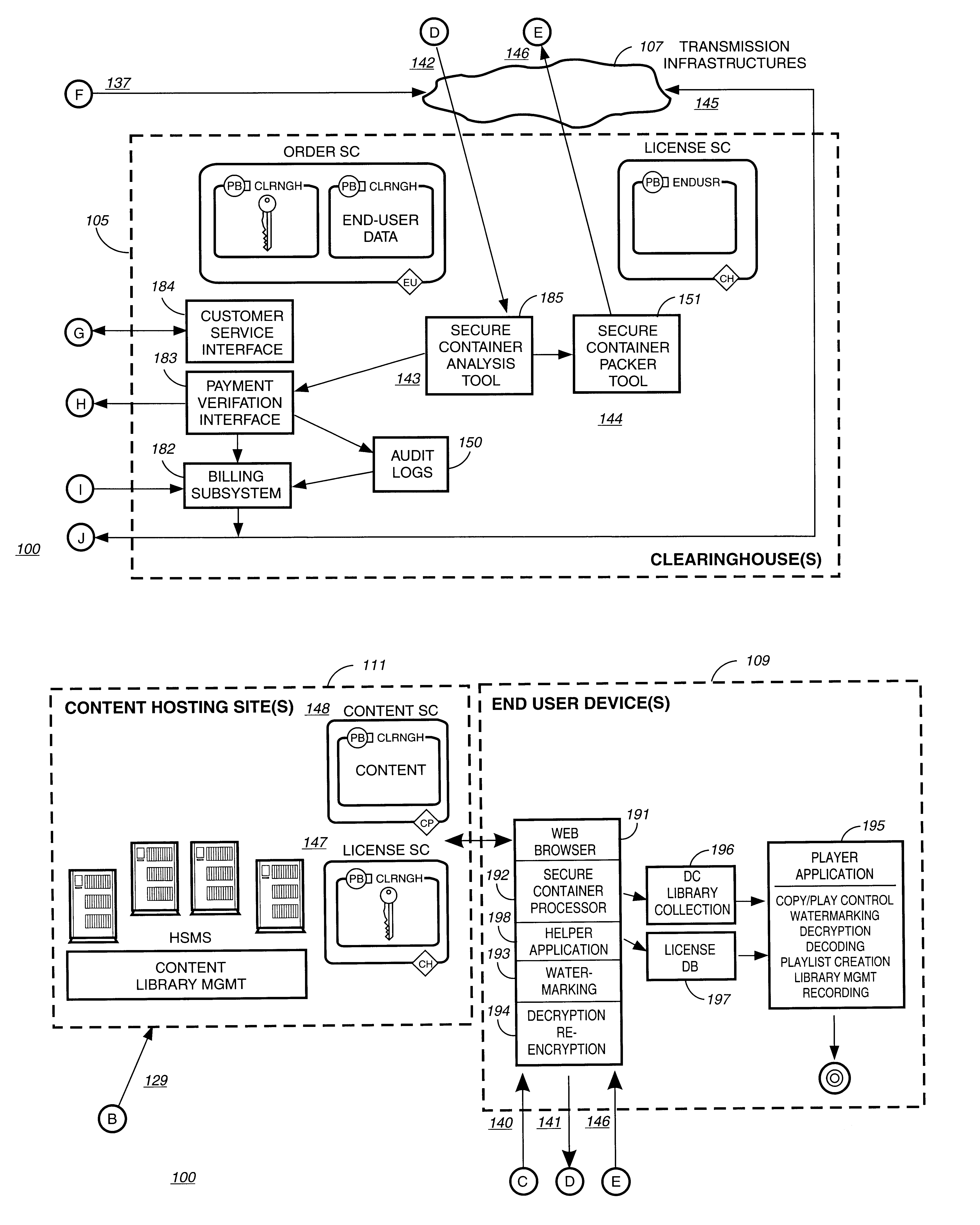
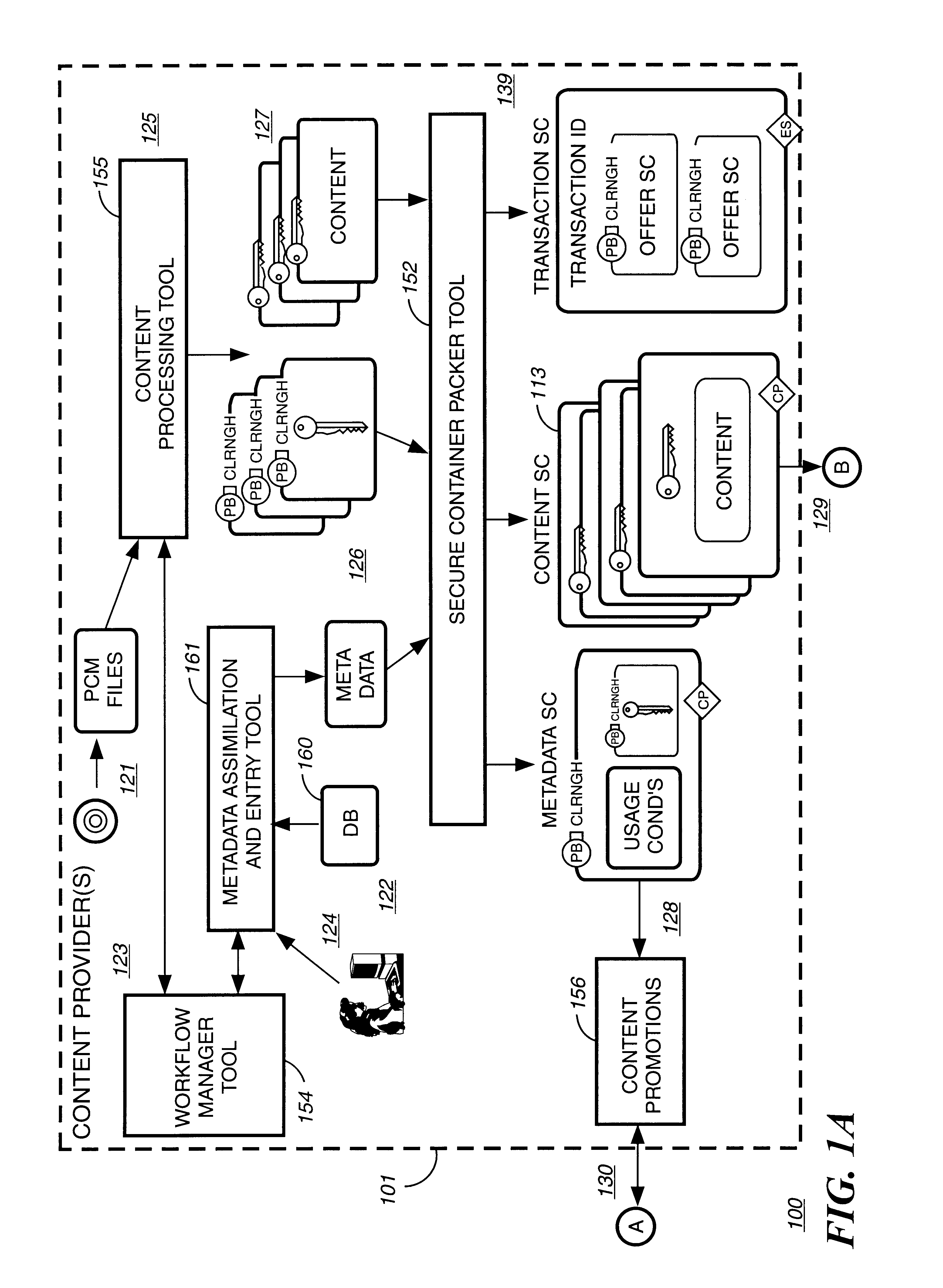
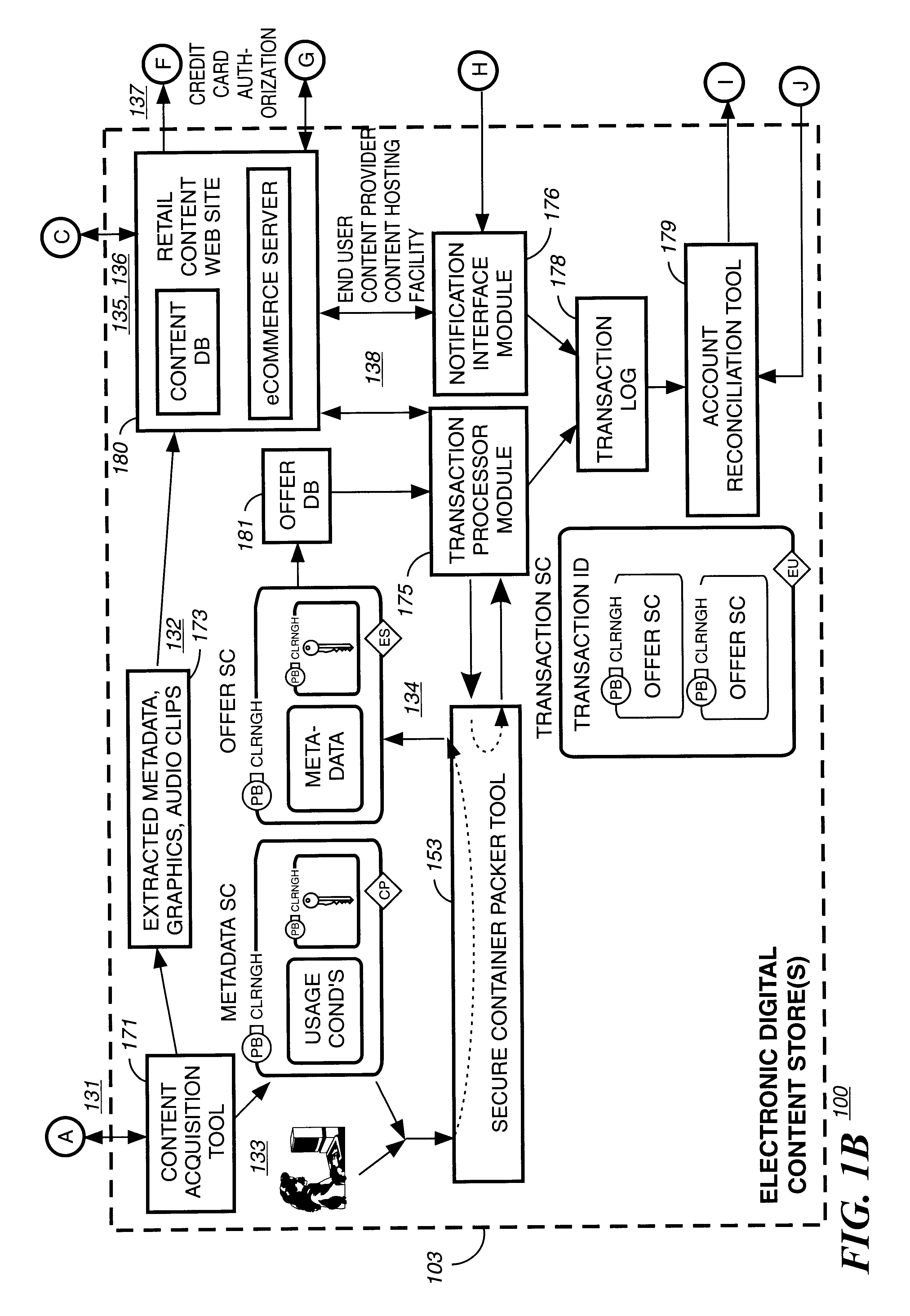
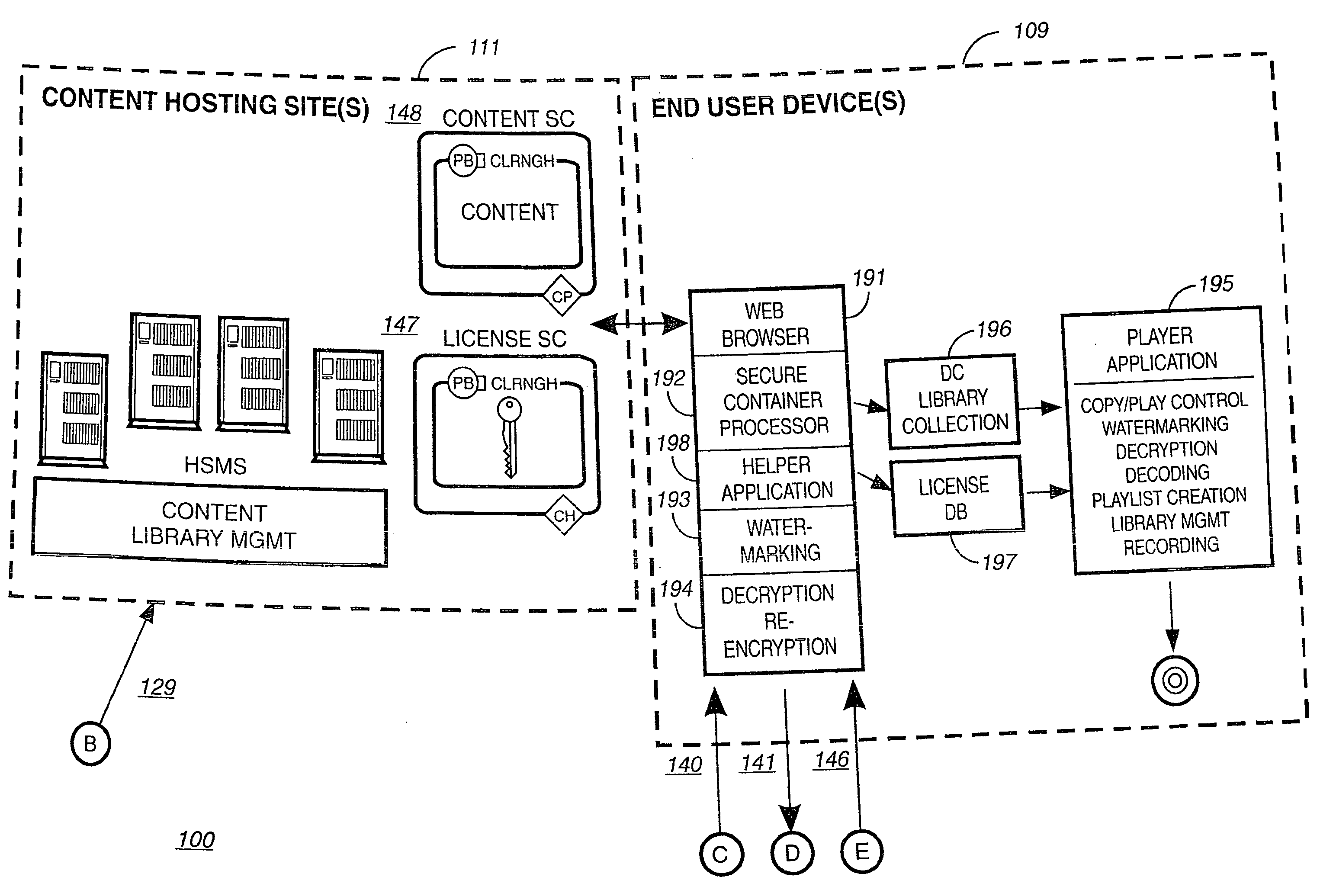
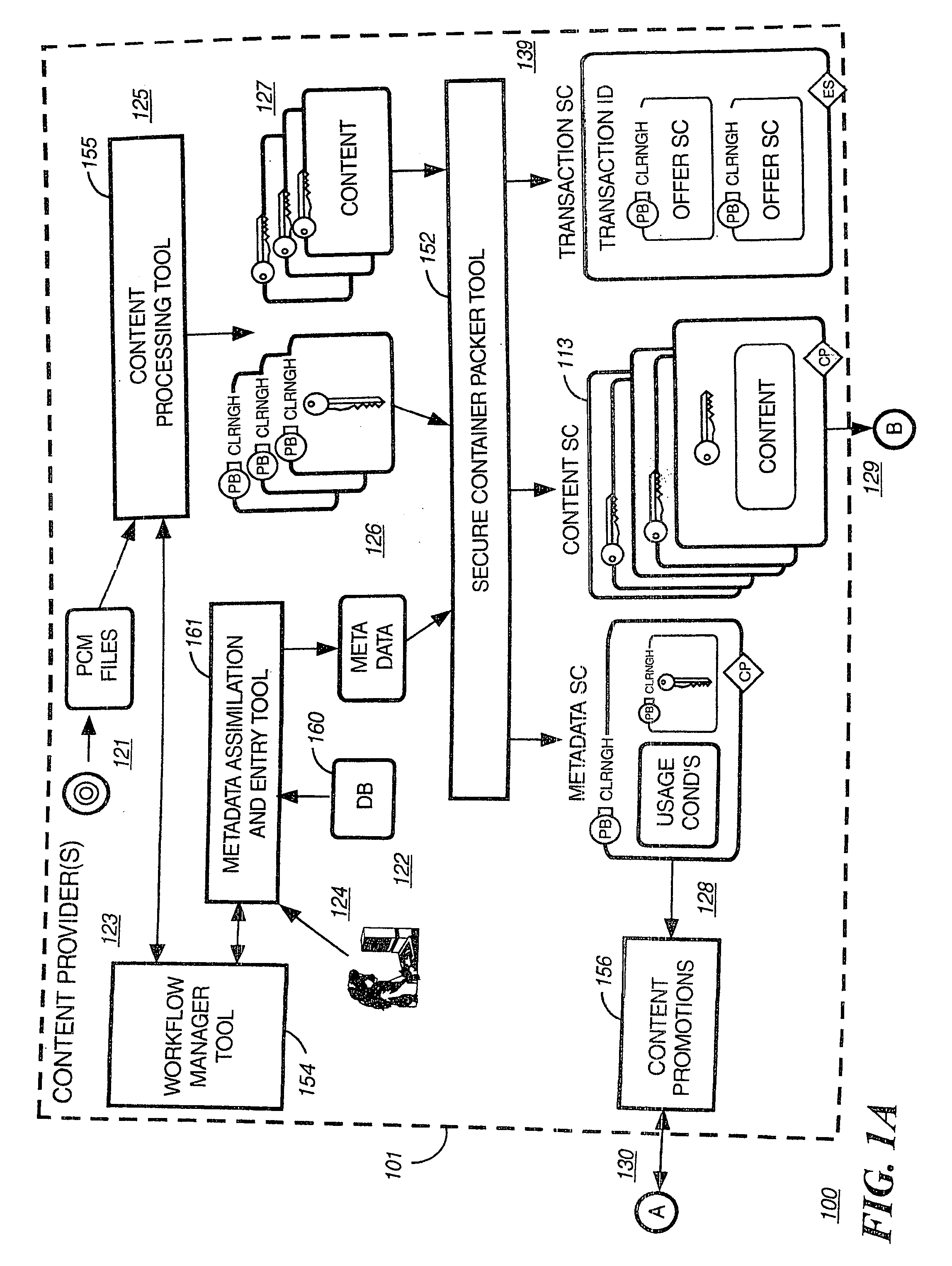
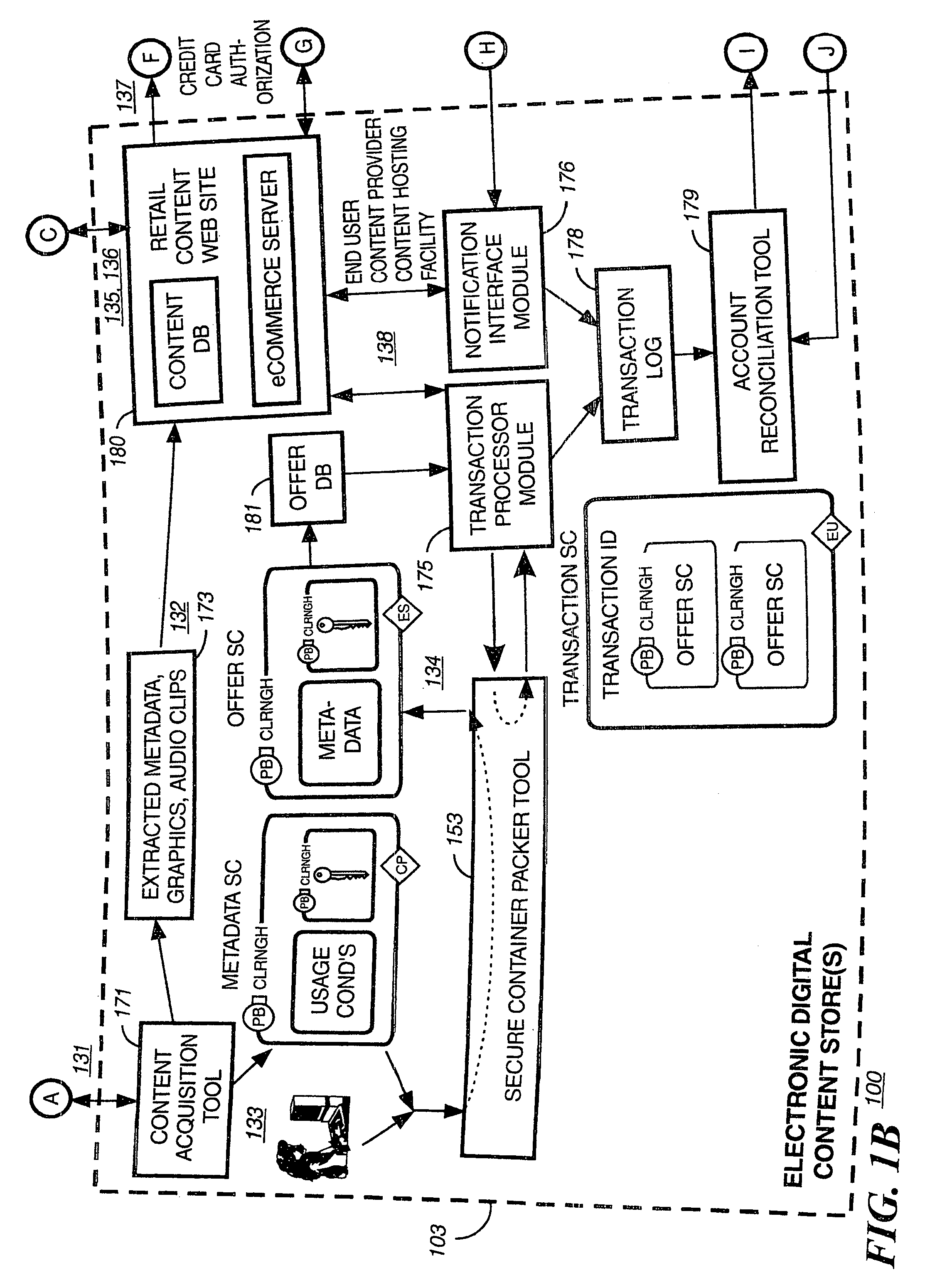
Secure electronic content distribution on CDS and DVDs
InactiveUS6611812B2Key distribution for secure communicationDigital data processing detailsDigital contentComputer terminal
A method to delivery encrypted digital content to a end user system for playing the content comprising the steps of: reading from a computer readable medium metadata which has previously associated with the content. A user selects from the metadata associated content to decrypt and the end user system establishes a secure connection with an authorization authority for decrypting the content. The end user system receives a secure container containing the decrypting key for decrypting at least part of the previously encrypted content as permitted. The system creates a secure container using the encrypting key from a clearing house, wherein the secure container has an encrypting key therein from the end user system; transferring the secure container to the clearing house for authentication of permission to decrypt the content. The system receives from the clearing house, a secure container encrypted using the encrypting key of the end user system containing the decrypting key for decrypting at least part of the previously encrypted content stored on the computer readable medium as permitted; and playing at least part of the previously encrypted content by decrypting the secure container using the encrypting key of the end user system to access the decrypting key for decrypting at least part of the encrypted content.
Owner:WISTRON CORP
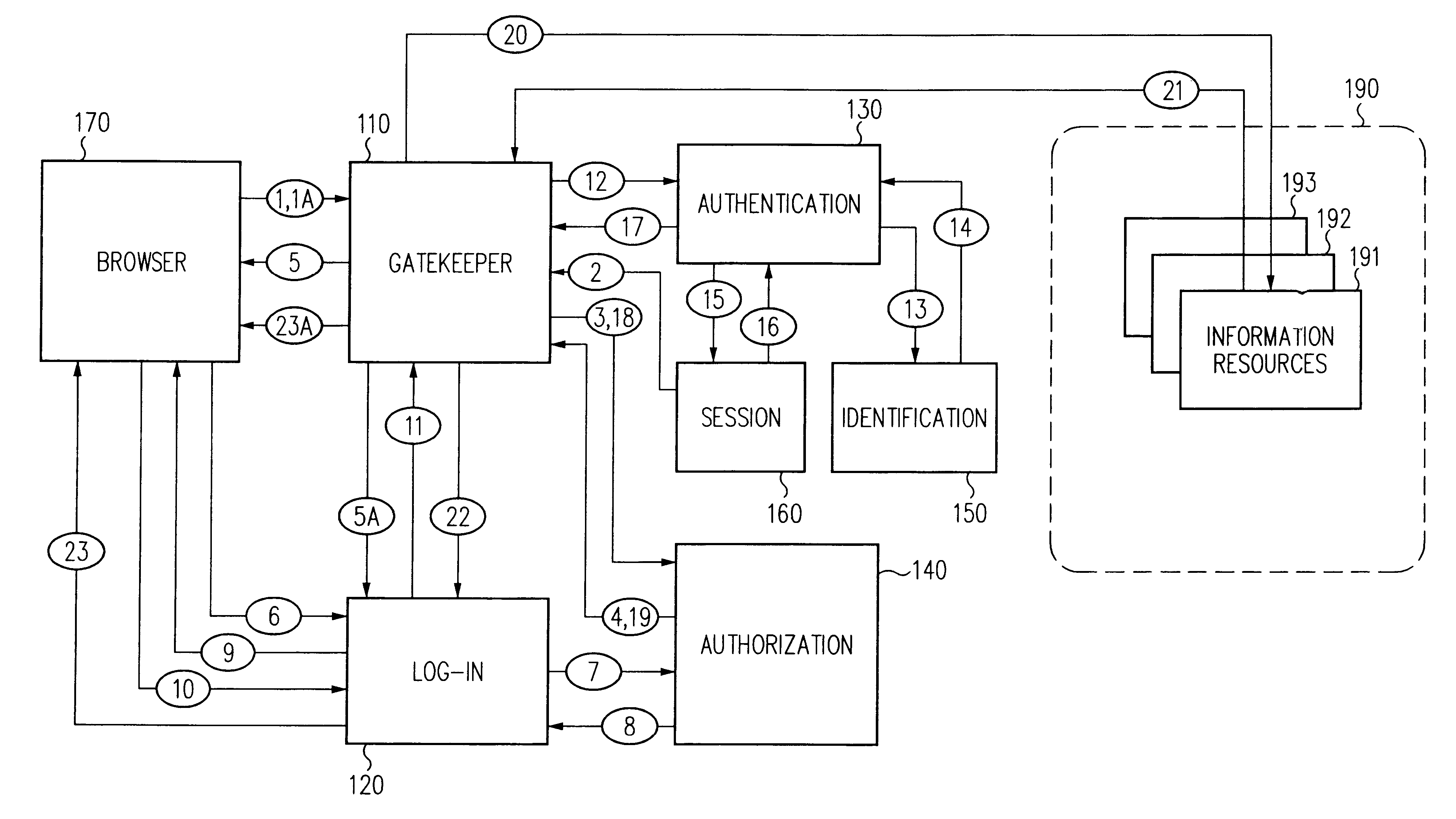
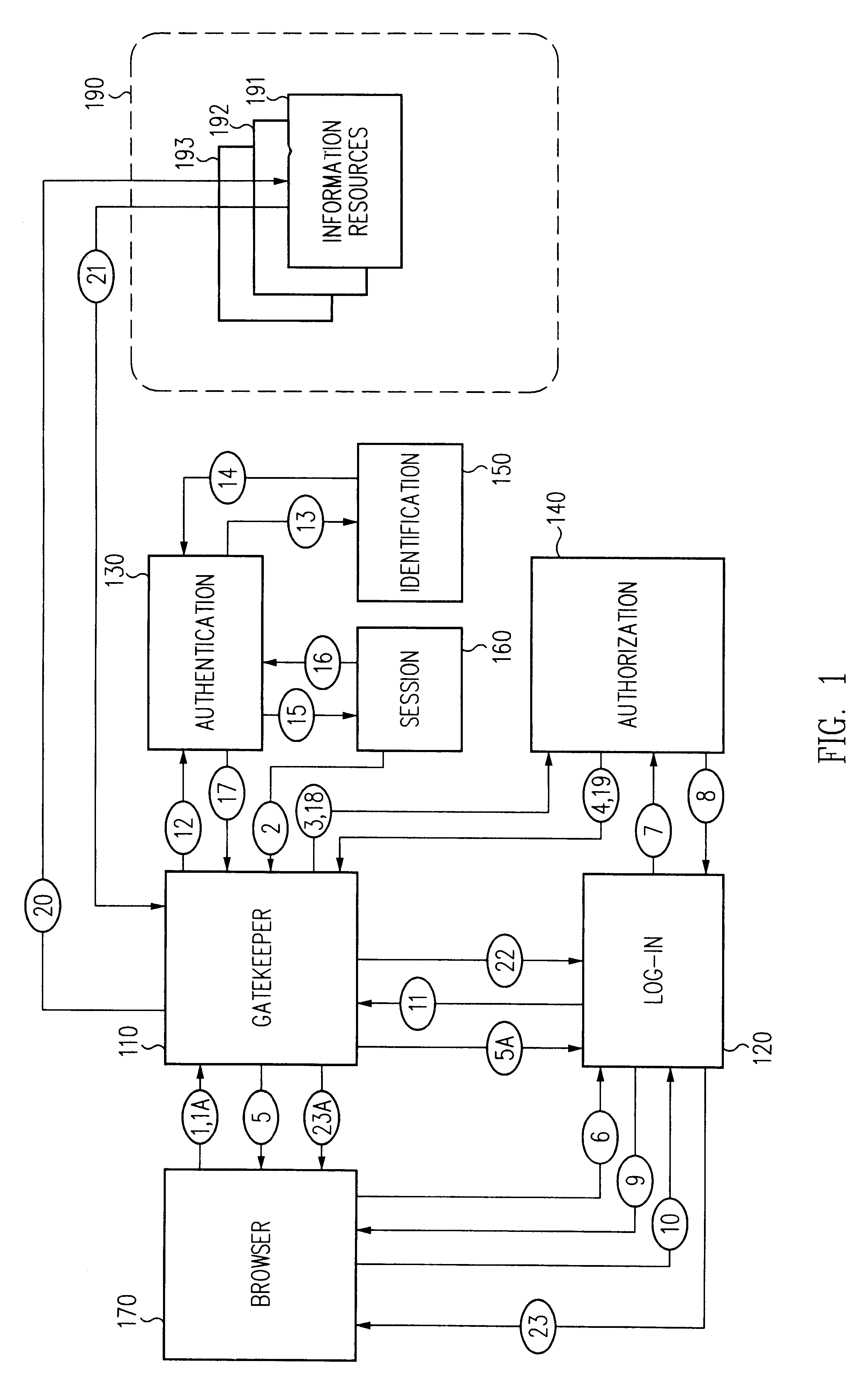
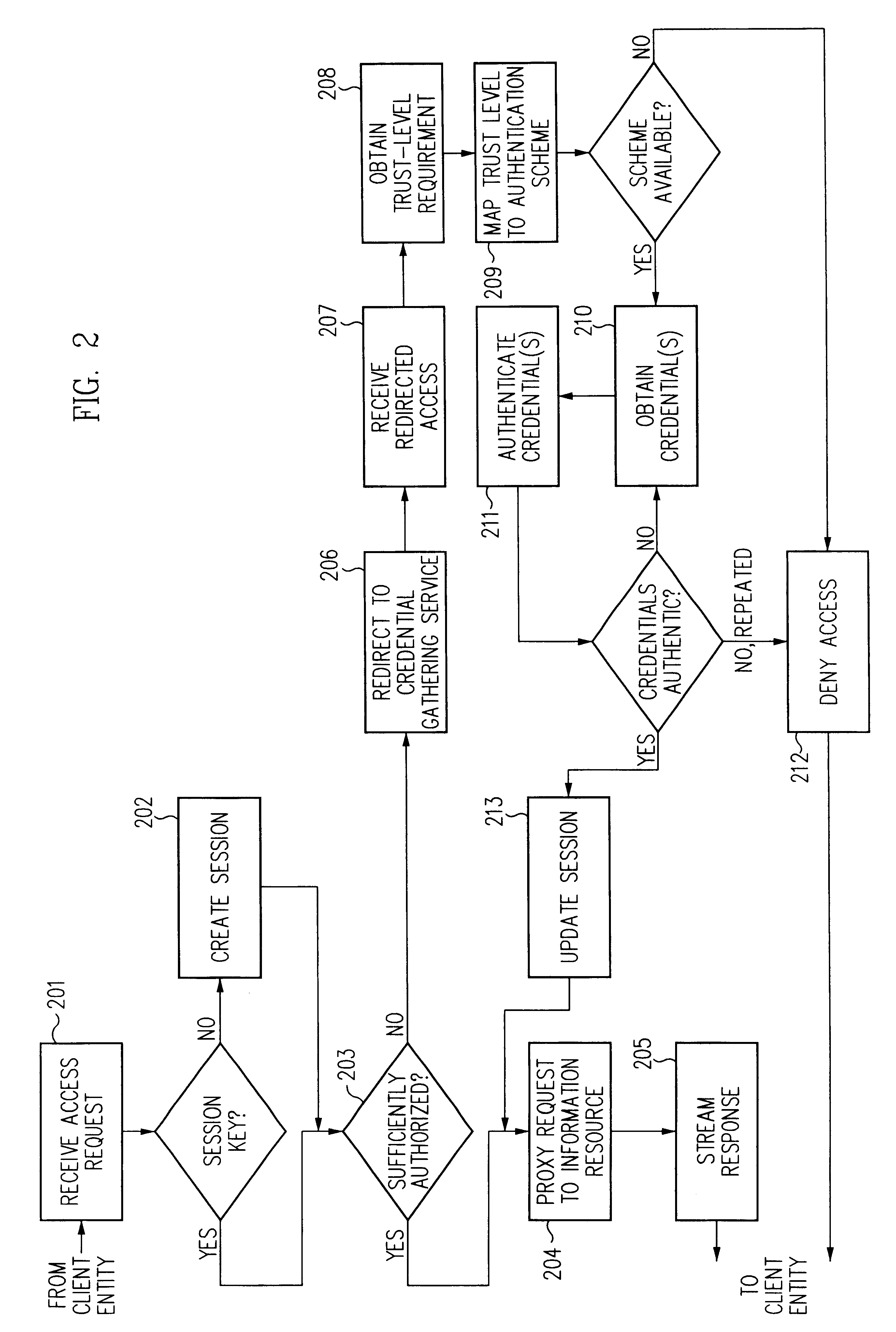
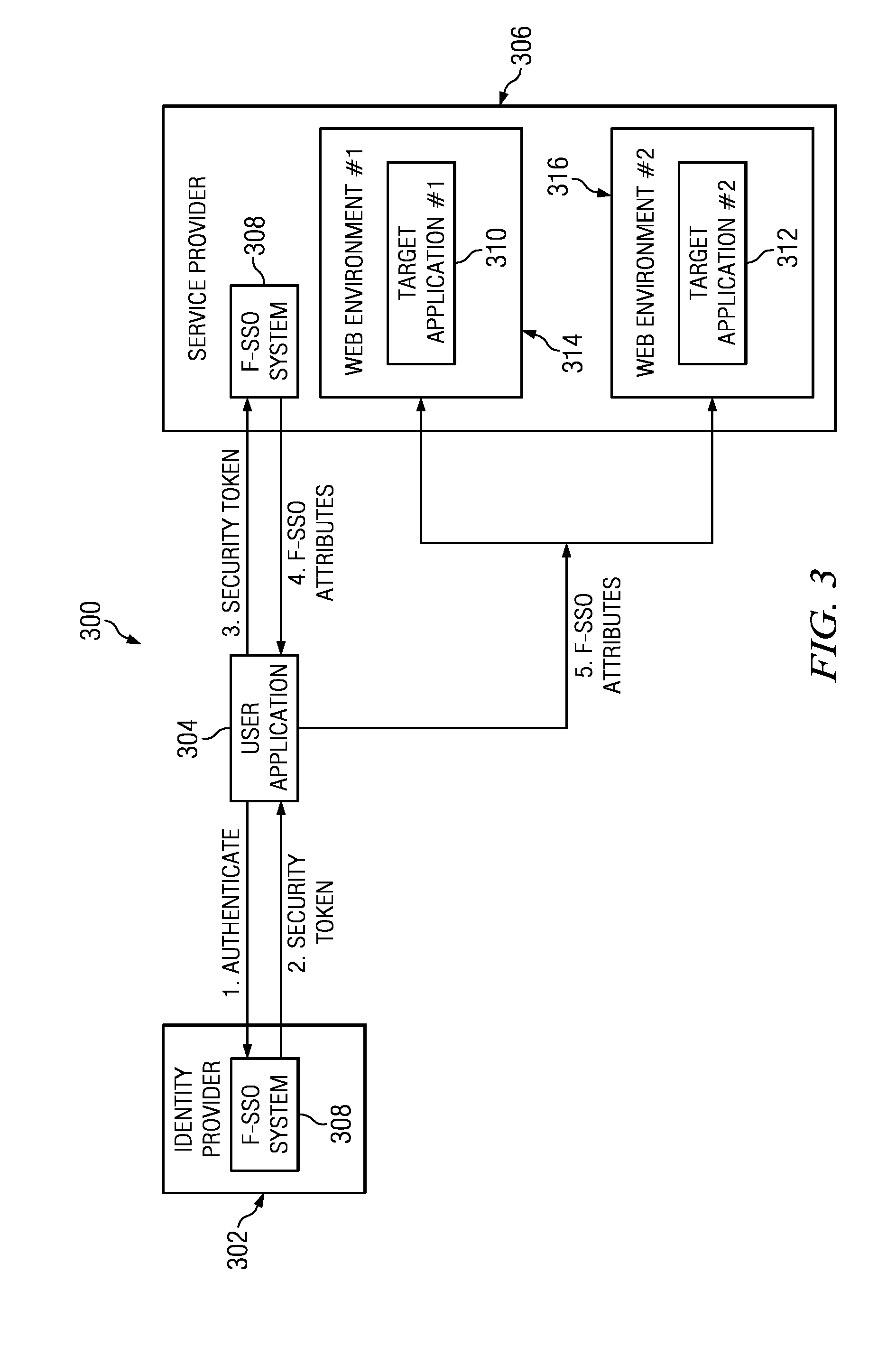
Log-on service providing credential level change without loss of session continuity
InactiveUS6609198B1Volume/mass flow measurementMultiple digital computer combinationsInformation resourceTrust level
A security architecture has been developed in which a single sign-on is provided for multiple information resources. Rather than specifying a single authentication scheme for all information resources, the security architecture associates trust-level requirements with information resources. Authentication schemes (e.g., those based on passwords, certificates, biometric techniques, smart cards, etc.) are employed depending on the trust-level requirement(s) of an information resource (or information resources) to be accessed. Once credentials have been obtained for an entity and the entity has been authenticated to a given trust level, access is granted, without the need for further credentials and authentication, to information resources for which the authenticated trust level is sufficient. The security architecture allows upgrade of credentials for a given session. This capability is particularly advantageous in the context of a single, enterprise-wide log-on. An entity (e.g., a user or an application) may initially log-on with a credential suitable for one or more resources in an initial resource set, but then require access to resource requiring authentication at higher trust level. In such case, the log-on service allows additional credentials to be provided to authenticate at the higher trust level. The log-on service allows upgrading and / or downgrading without loss of session continuity (i.e., without loss of identity mappings, authorizations, permissions, and environmental variables, etc.).
Owner:ORACLE INT CORP
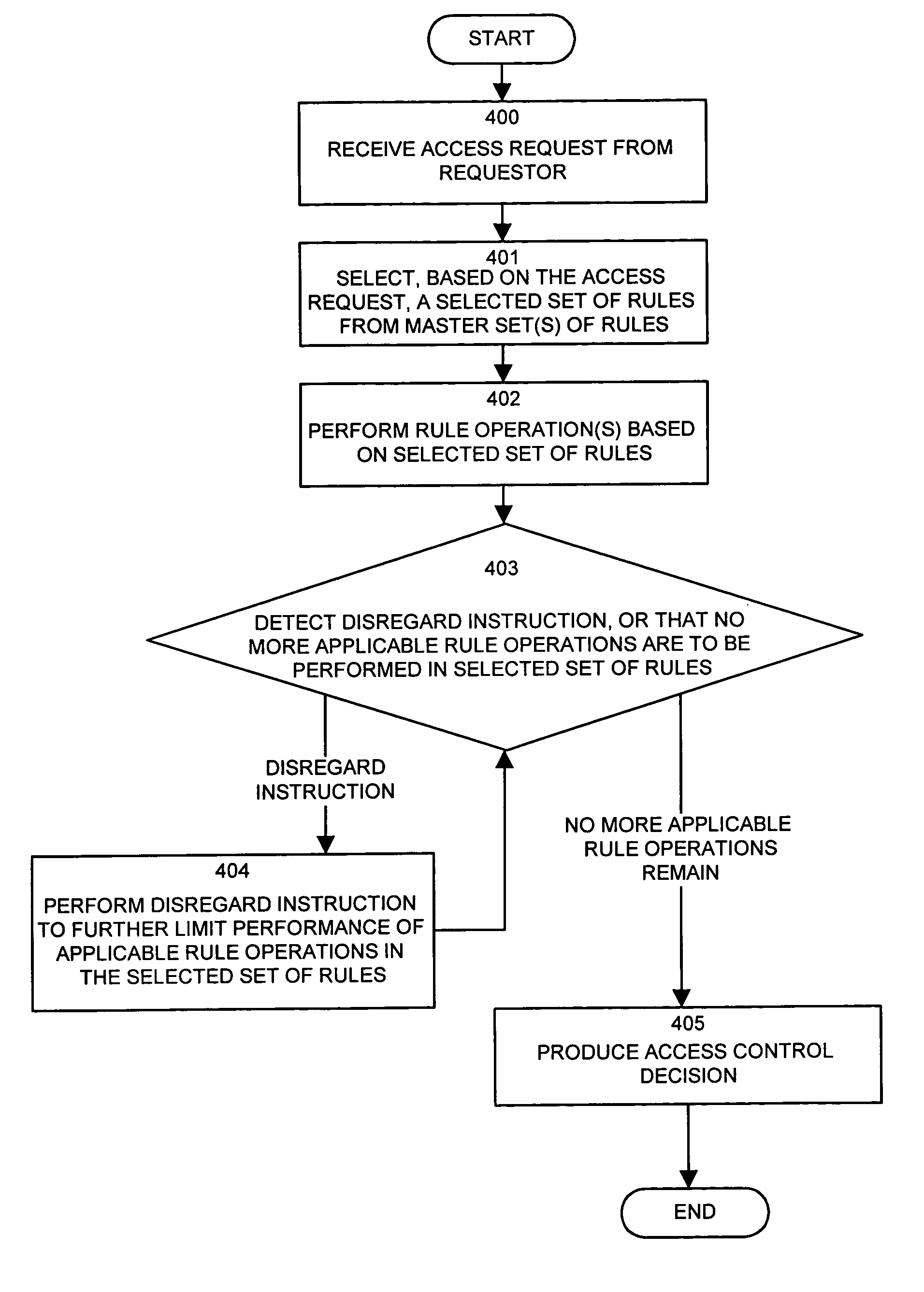
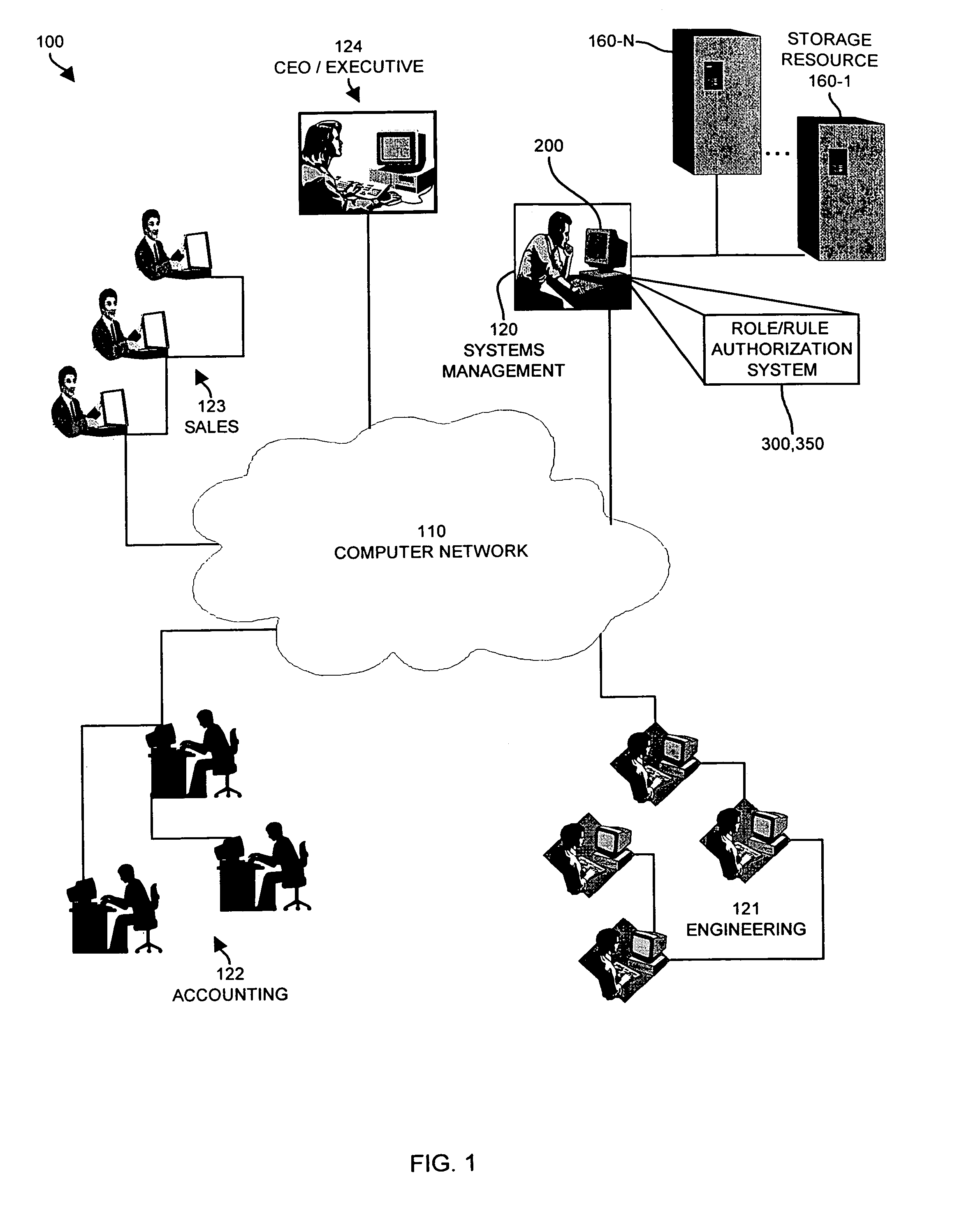
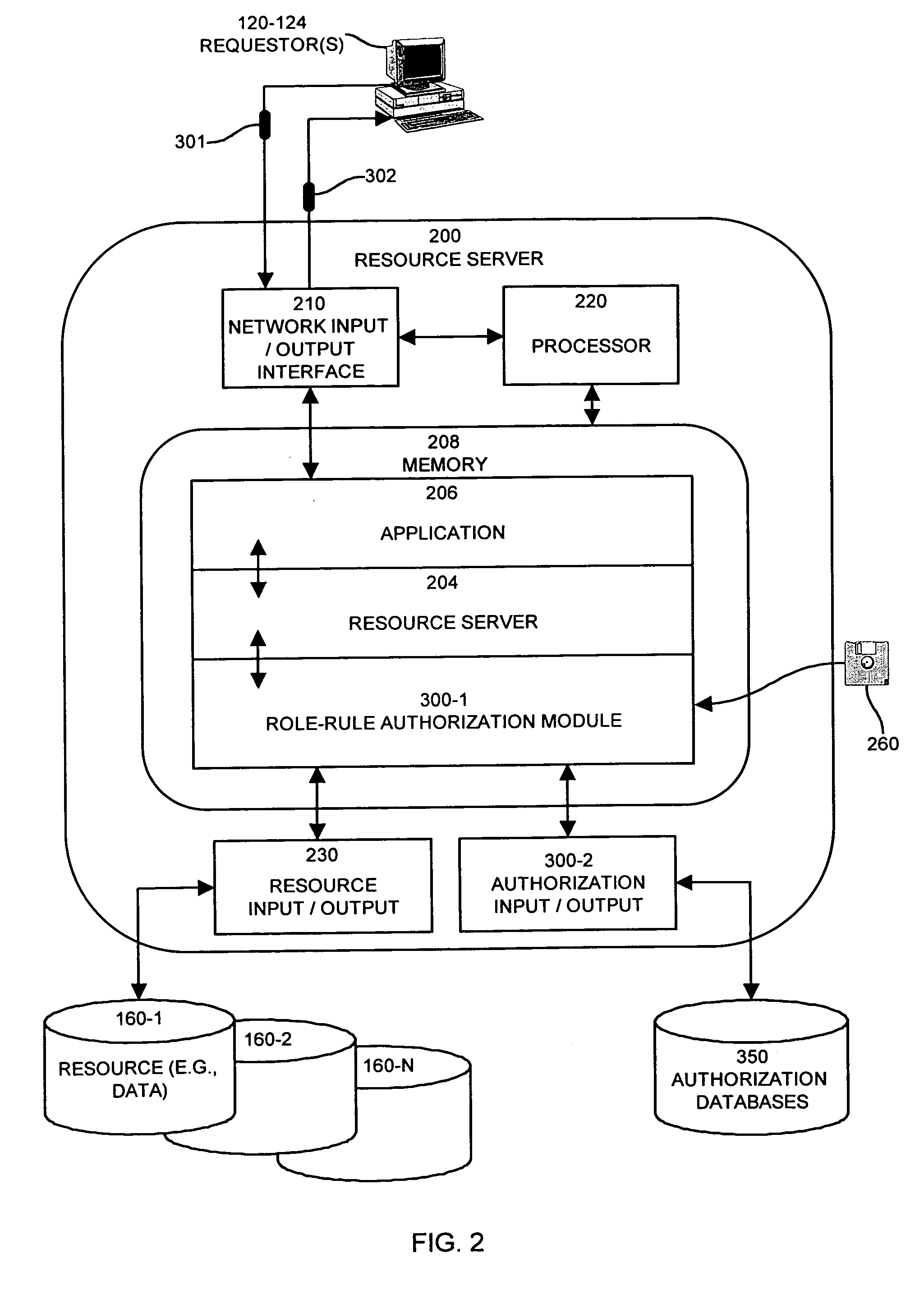
Methods and apparatus for controlling access to a resource
InactiveUS7185192B1Limit staff employee accessVerification of the security policy more straightforwardData processing applicationsDigital data processing detailsProgramming languageDecision taking
An input / output interface receives an access request from a requester. A processor associated with the input / output interface applies a filter operation to select a subset of rules from a master set of rules maintained within an authorization database. Rules can be selected in this manner using filter operations so that all rules in the rule set need not be processed. A rule may include a disregard instruction. The processor further performs at least one rule operation based on the subset of rules to produce an access control decision in the memory system until either a rule operation including a disregard instruction is performed to limit performance of rule operations in the selected set of rules or until all rule operations in the selected set of rules that are applicable to the access control decision are performed.
Owner:EMC IP HLDG CO LLC
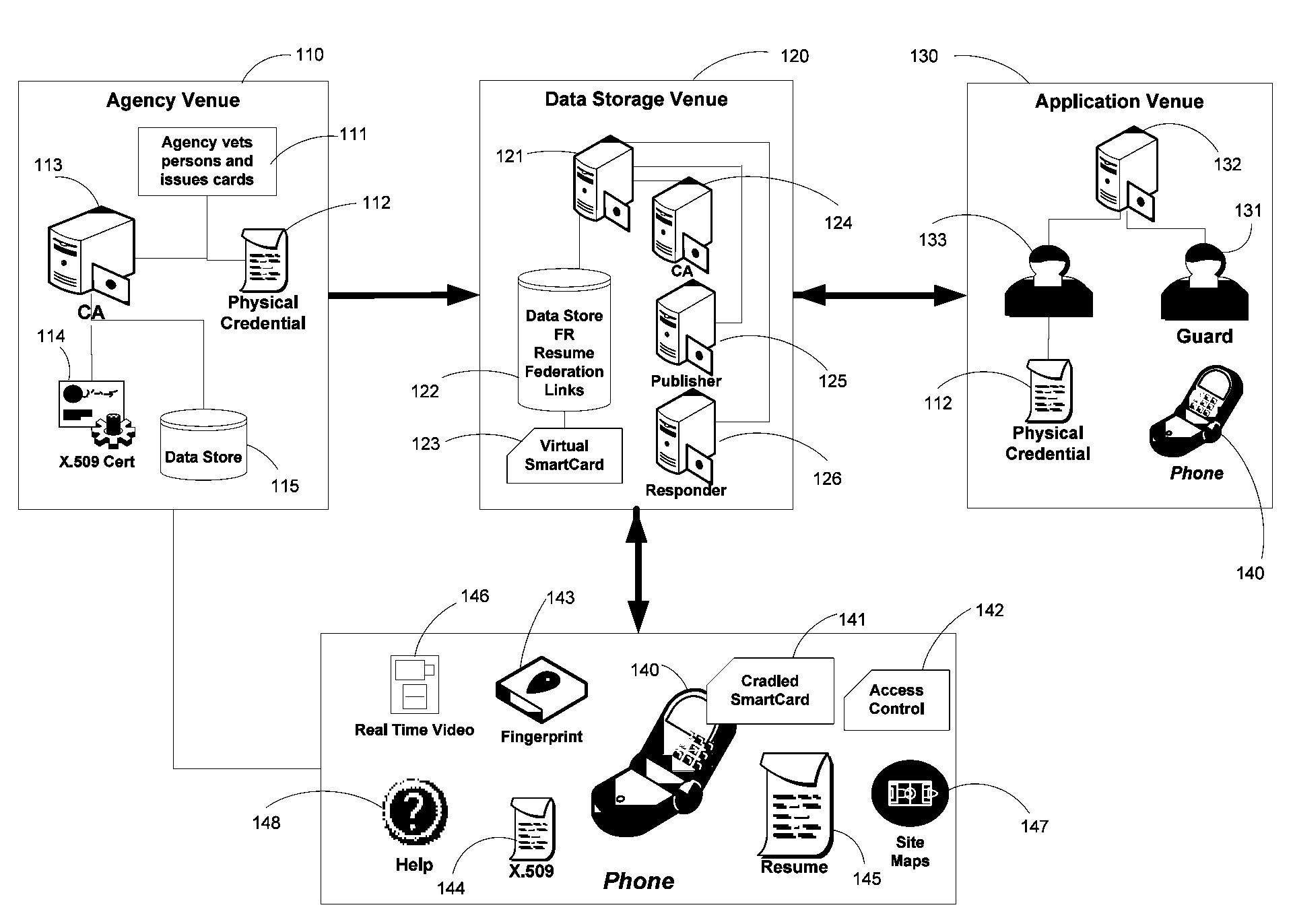
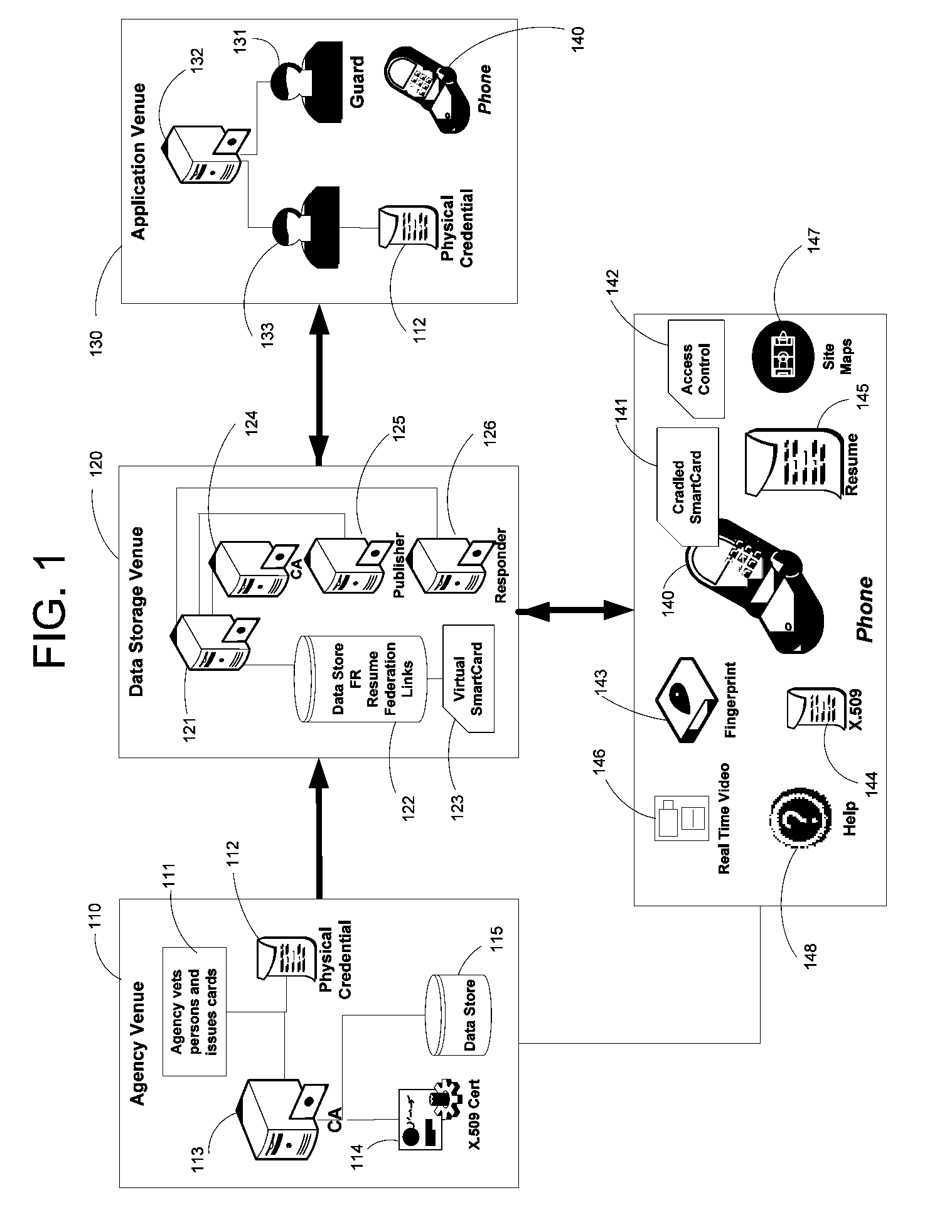
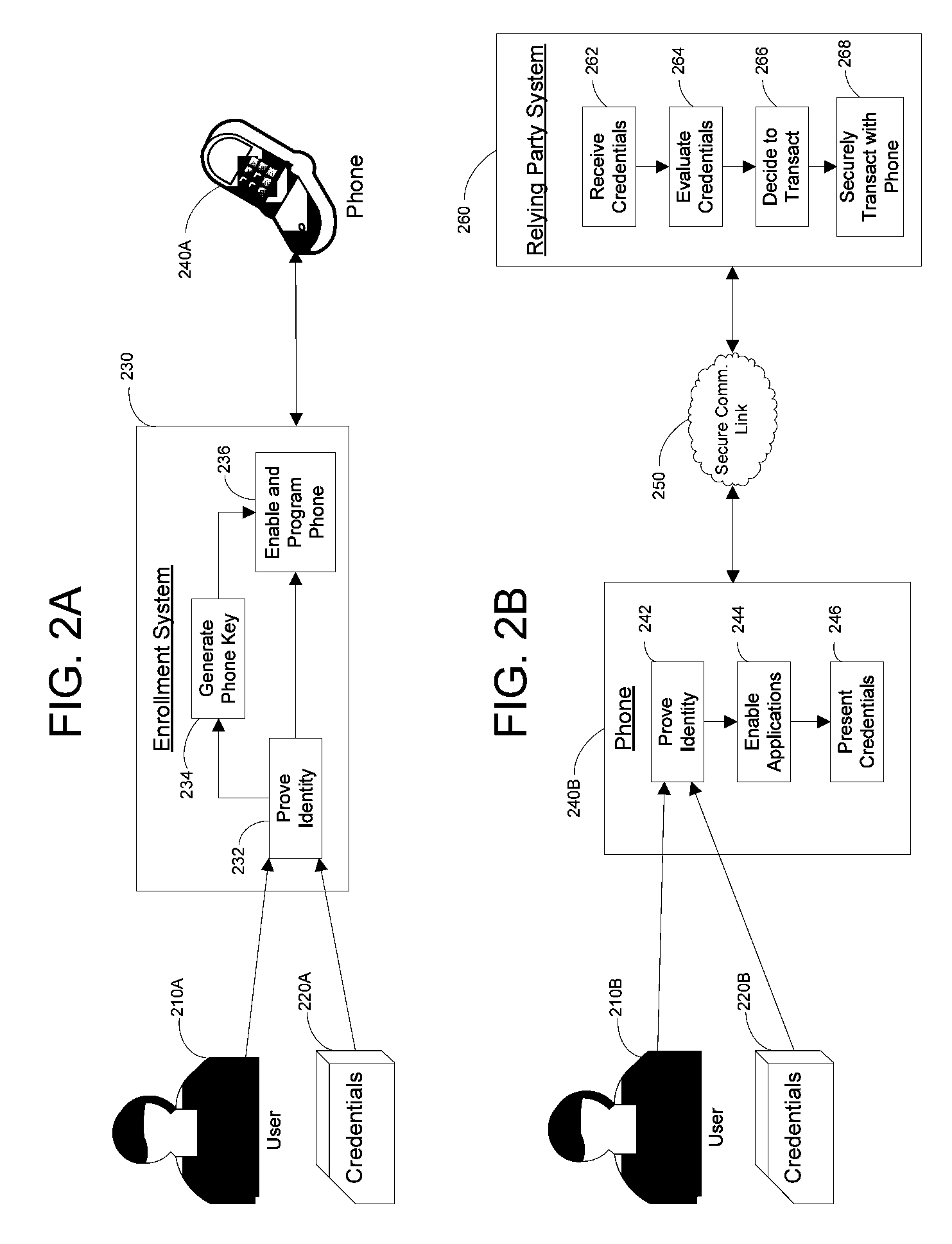
Apparatus and Methods for Providing Scalable, Dynamic, Individualized Credential Services Using Mobile Telephones
InactiveUS20090132813A1Save bandwidthSaving response timeDigital data processing detailsUser identity/authority verificationElectronic systemsFinancial transaction
Apparatus and methods perform transactions in a secure environment between an individual and another party, such as a merchant, in various embodiments. The individual possesses a mobile electronic device, such as a smartphone, that can encrypt data according to a public key infrastructure. The individual authenticates the individual's identity to the device, thereby unlocking credentials that may be used in a secure transaction. The individual causes the device to communicate the credentials, in a secure fashion, to an electronic system of a relying party, in order to obtain the relying party's authorization to enter the transaction. The relying party system determines whether to grant the authorization, and communicates the grant and the outcome of the transaction to the device using encryption according to the public key infrastructure.
Owner:SURIDX
Payments using a mobile commerce device
InactiveUS20080208762A1Buying/selling/leasing transactionsPoint-of-sale network systemsPayment transactionAuthorization
Methods, systems, and machine-readable media are disclosed for handling payment transactions in a mobile commerce system. According to one embodiment, a method of processing a payment transaction in a mobile commerce system can comprise receiving at a first acquirer system a communication from a point-of-sale (POS) device. The communication can be related to the payment transaction and can include information identifying a financial account from which a payment is requested. A second acquirer for authorizing the payment can be identified based on the information identifying the financial account. The communication can be sent to the second acquirer system for authorization of the transaction based on the information related to the financial account. An indication of whether the transaction is authorized can be received from the second acquirer system.
Owner:FIRST DATA
Authentication services using mobile device
InactiveUS7606560B2Unauthorised/fraudulent call preventionEavesdropping prevention circuitsInternet Authentication ServiceMobile device
A method, and an apparatus performing the method, is provided by authenticating a mobile device communicably connectable to a wireless network by an authentication parameter from a secure transaction server (STS), as a mobile device authenticator; providing an STS correlation between a personal identification entry (PIE) and the mobile device authenticator; and inputting, by a user, the PIE and a provider action, to the mobile device authenticator to transmit a transformed secure user authenticable authorization request to the STS over the wireless network to authorize an action with a provider.
Owner:PCMS HOLDINGS INC
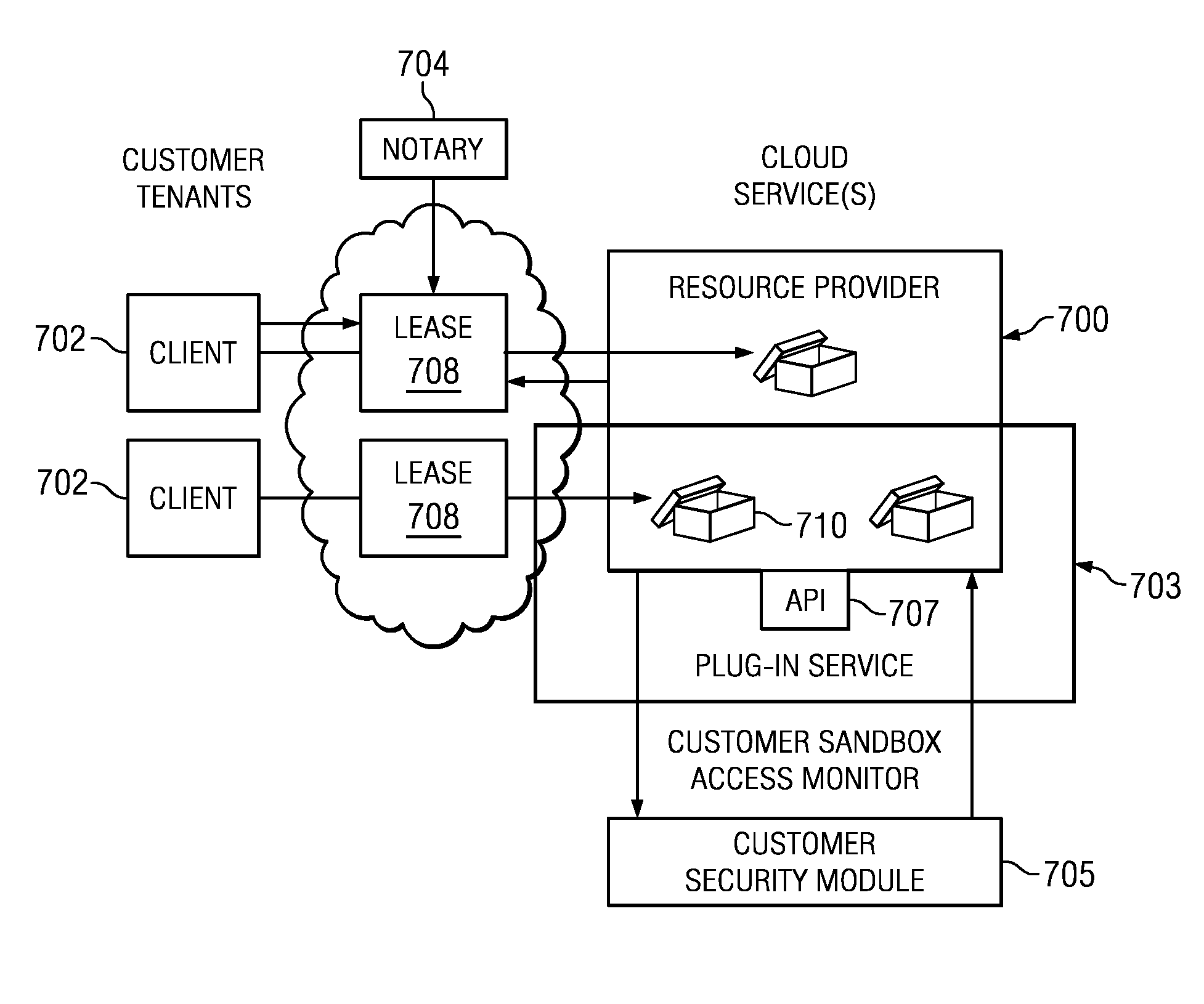
Authentication and authorization methods for cloud computing security
ActiveUS8769622B2Retain controlKey distribution for secure communicationDigital data processing detailsResource poolThird party
An authentication and authorization plug-in model for a cloud computing environment enables cloud customers to retain control over their enterprise information when their applications are deployed in the cloud. The cloud service provider provides a pluggable interface for customer security modules. When a customer deploys an application, the cloud environment administrator allocates a resource group (e.g., processors, storage, and memory) for the customer's application and data. The customer registers its own authentication and authorization security module with the cloud security service, and that security module is then used to control what persons or entities can access information associated with the deployed application. The cloud environment administrator, however, typically is not registered (as a permitted user) within the customer's security module; thus, the cloud environment administrator is not able to access (or release to others, or to the cloud's general resource pool) the resources assigned to the cloud customer (even though the administrator itself assigned those resources) or the associated business information. To further balance the rights of the various parties, a third party notary service protects the privacy and the access right of the customer when its application and information are deployed in the cloud.
Owner:IBM CORP
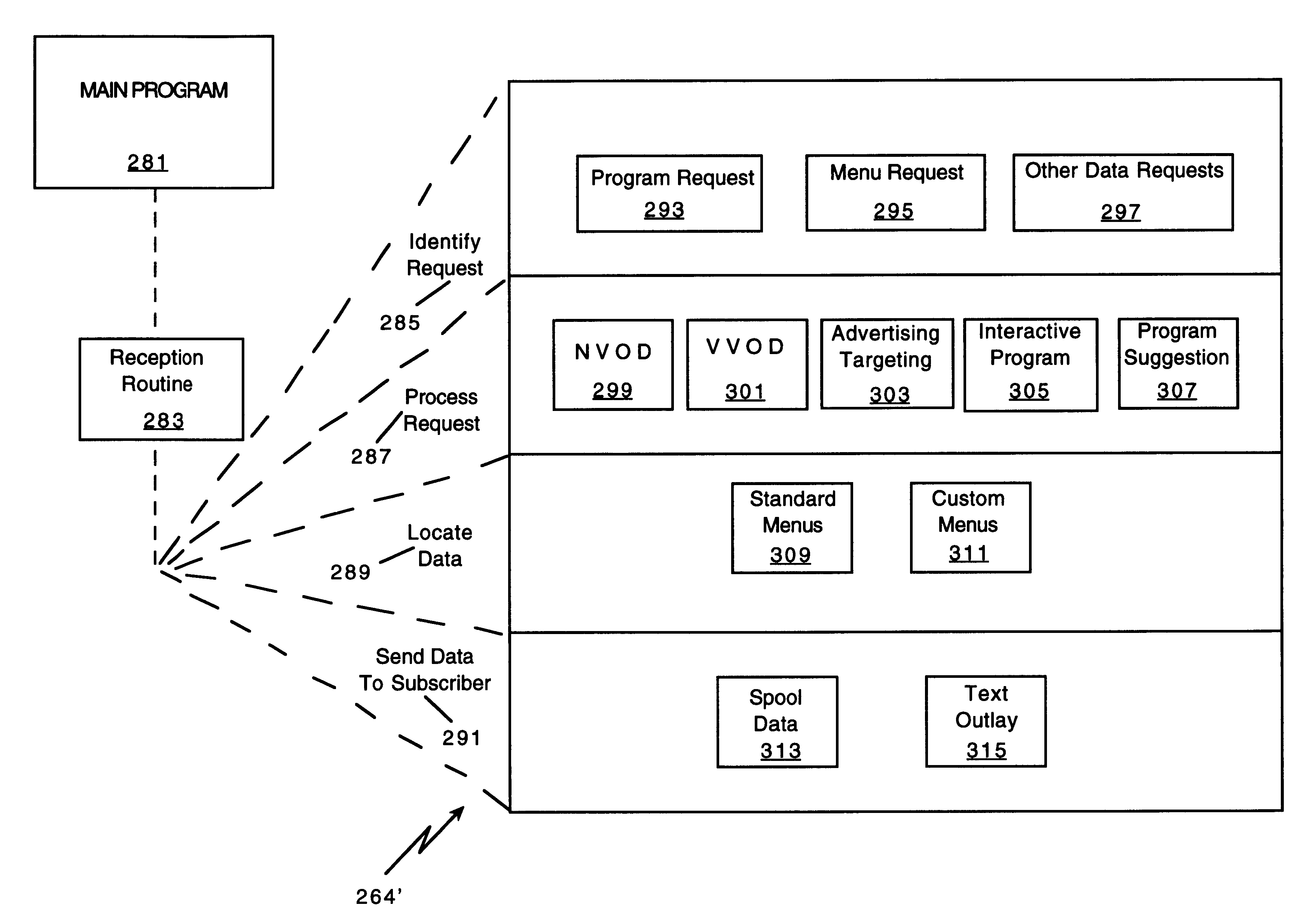
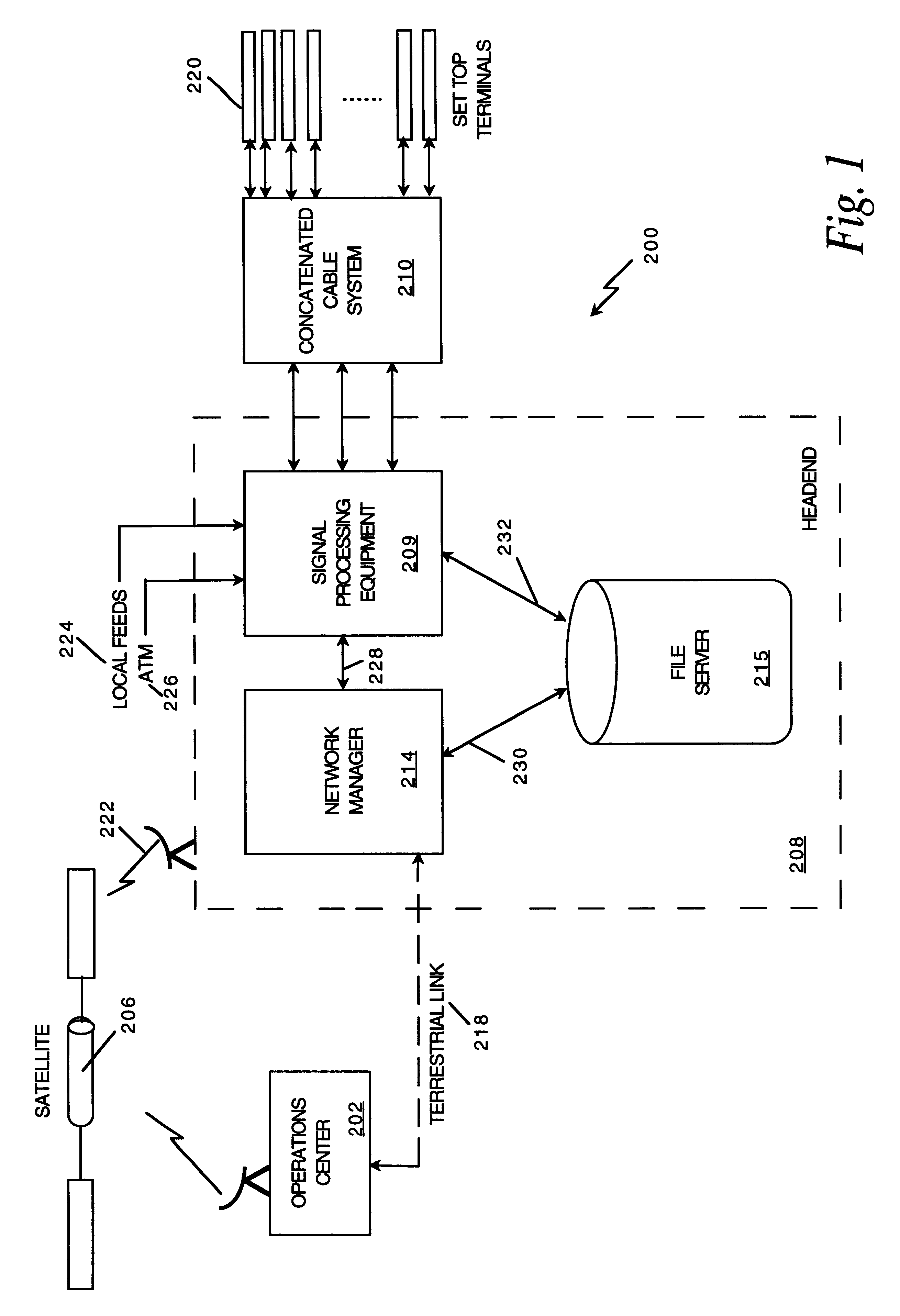
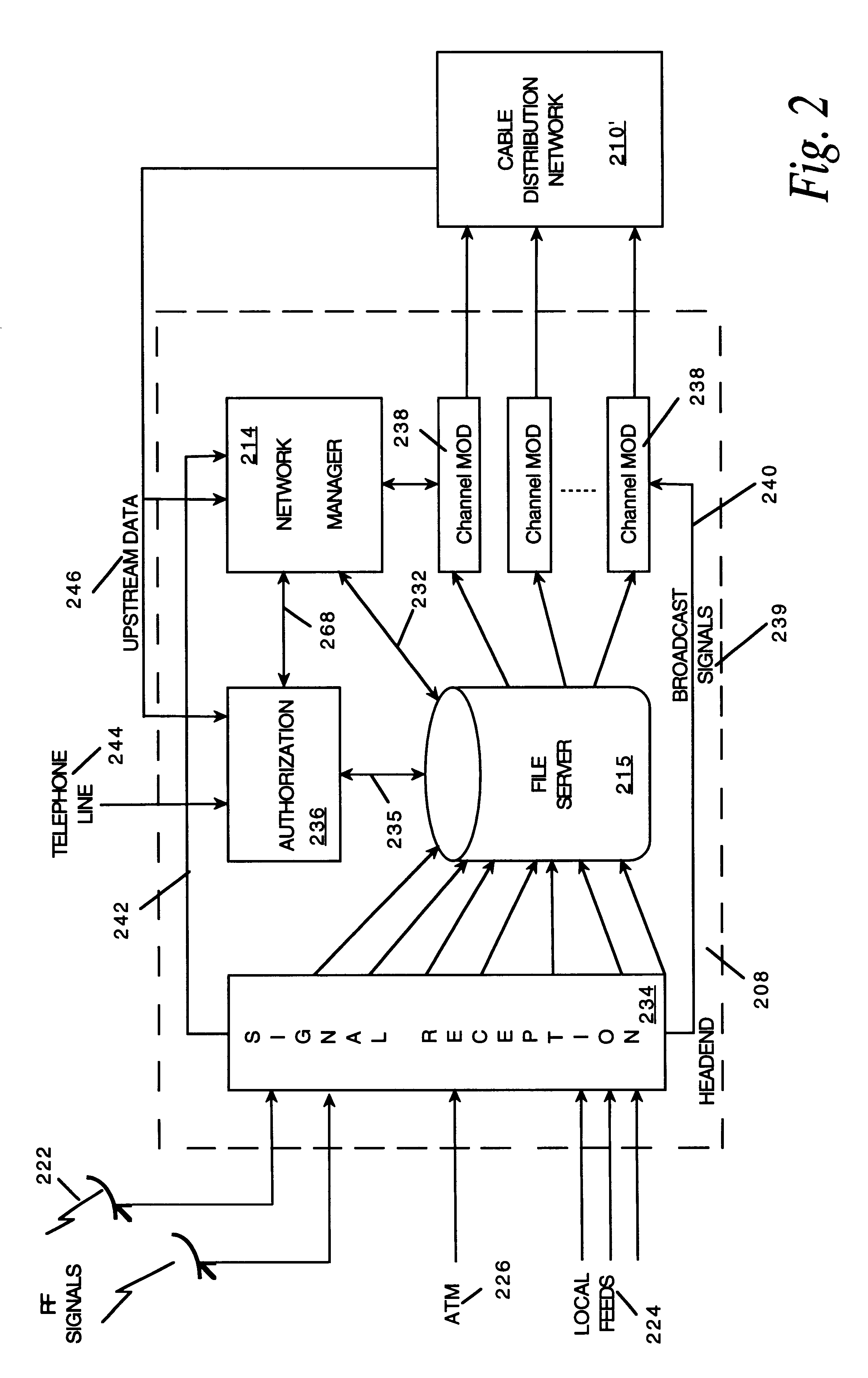
Network manager for cable television system headends
InactiveUS6201536B1Increase flexibilityImprove rendering capabilitiesTelevision system detailsPulse modulation television signal transmissionInformation processingInstruction memory
A novel network manager for use with a cable television system headend capable of monitoring and managing headend components and set top terminals in a television delivery system is described. The invention relates to methods and apparatus that manage and coordinate the reception of various programming and control signals at a headend. The invention manages and coordinates the storage of such signals for intelligent selection and distribution to set top terminals. The invention makes use of a receiver or set of receivers, a work station, a program control information processing component, a network management CPU, databases, control software and an instruction memory. The invention uses these components to manage and monitor certain headend components, such as signal reception equipment, an authorization component, a file server, MPEG decoders, a digital buffer with frame repeat and channel modulators. The invention is particularly useful in processing and responding to upstream information and subscriber communications received from set top terminals. In so doing, the invention accommodates various system services, including (1) near video on demand (NVOD), (2) virtual video on demand (VVOD), (3) video on demand (VOD), (4) interactive program services, (5) program suggestion features, (6) advertisement targeting, (7) generation of standard and custom menus, and (8) data spooling and text overlaying.
Owner:COMCAST IP HLDG I
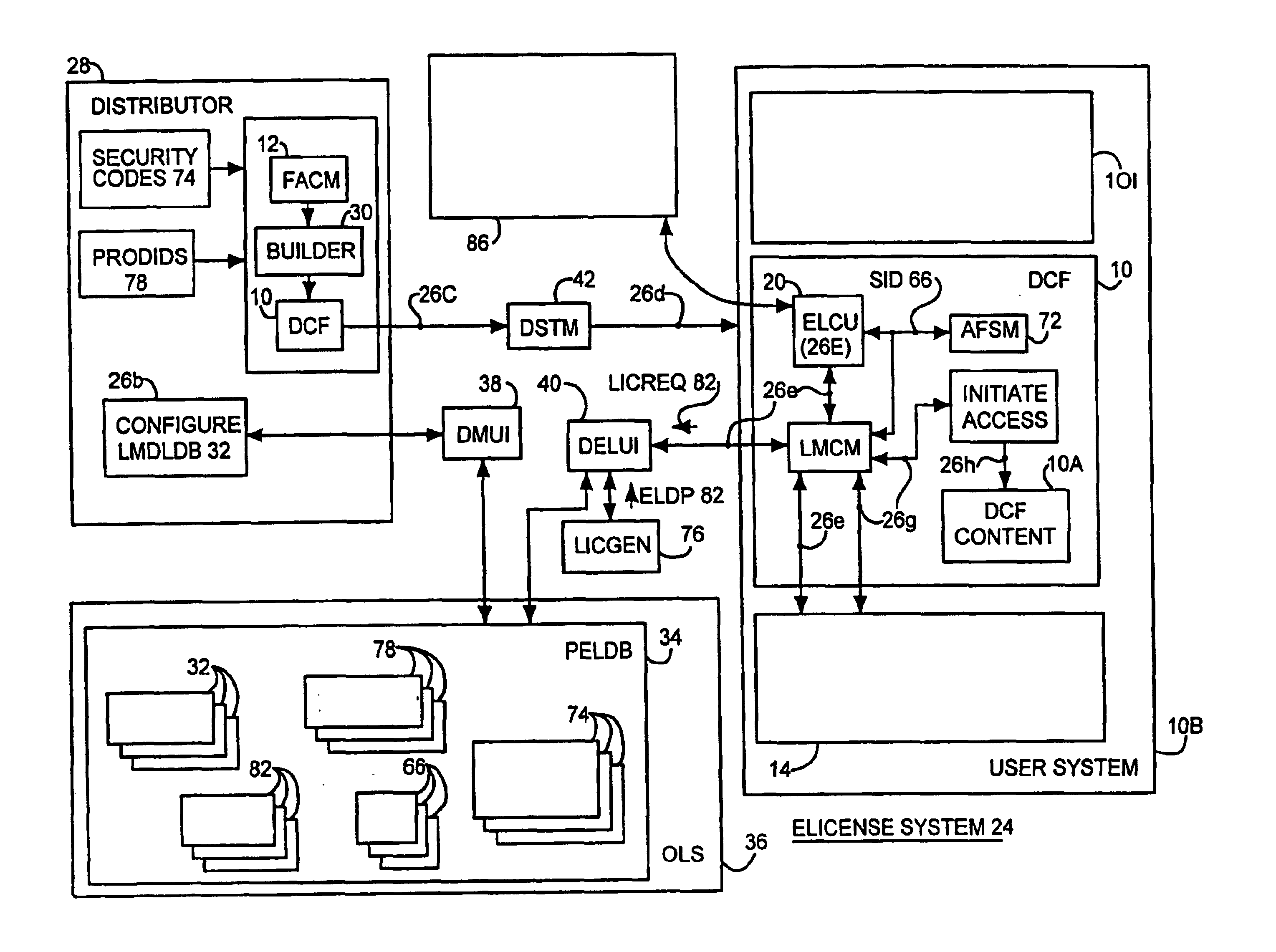
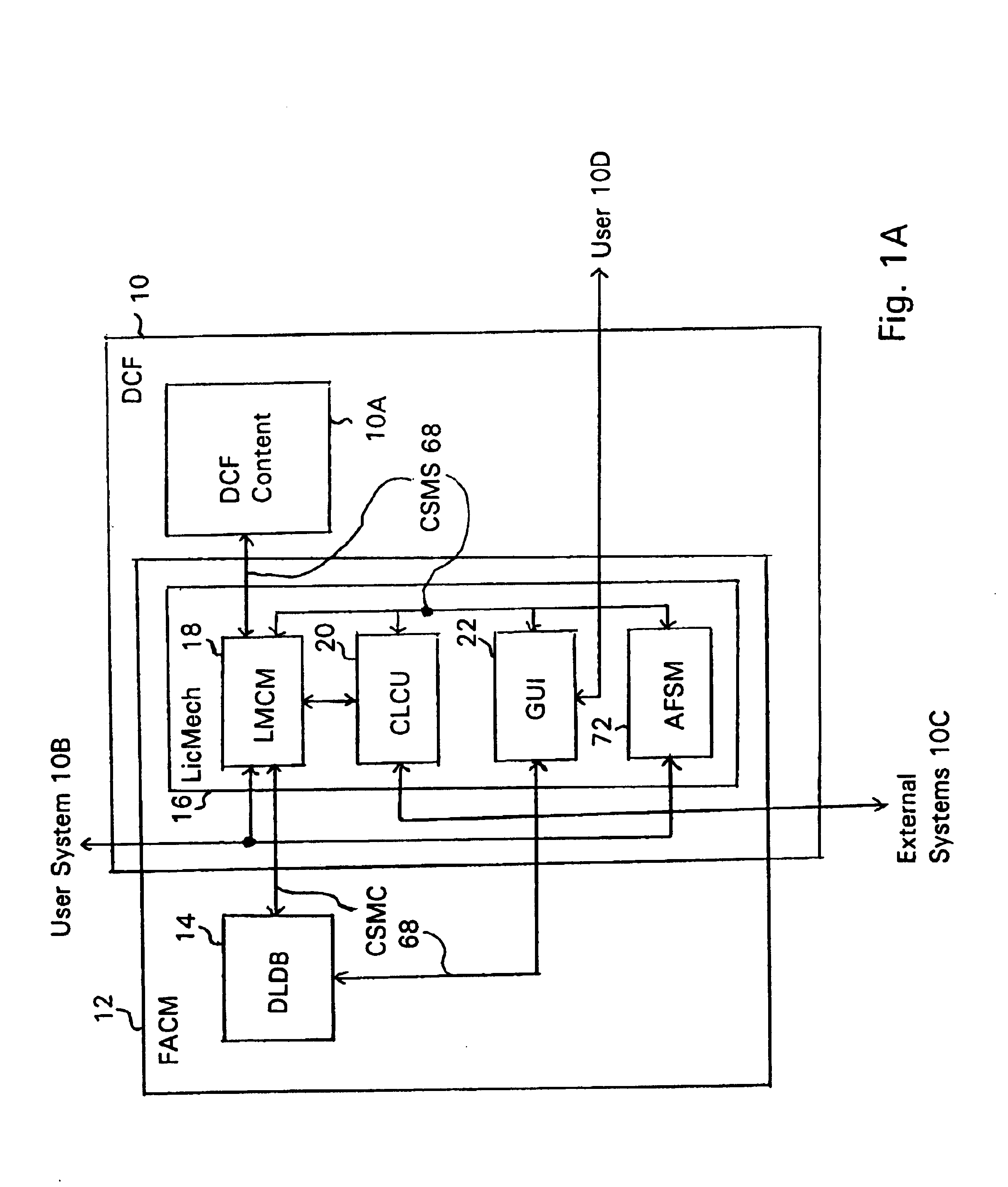
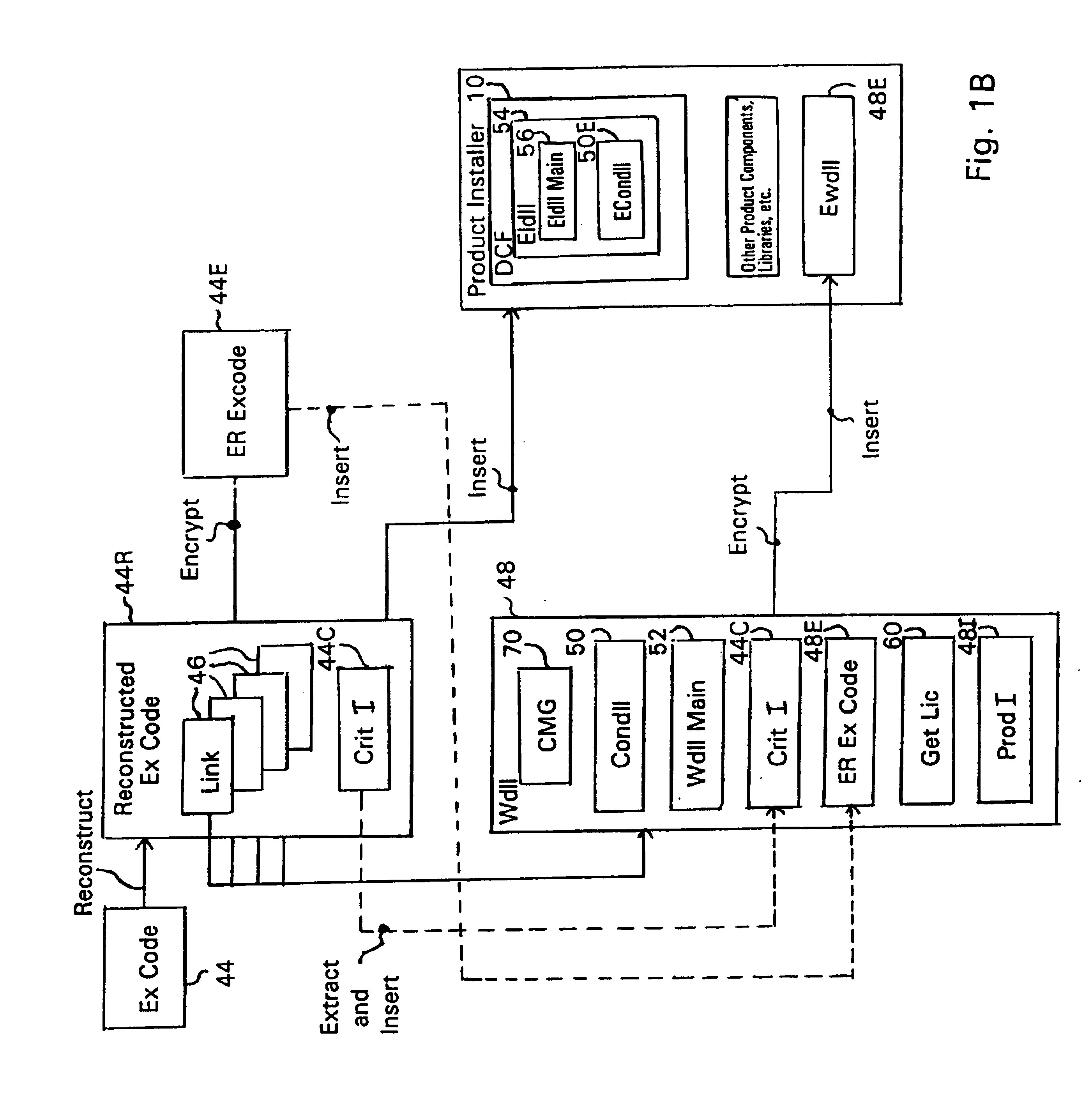
System and embedded license control mechanism for the creation and distribution of digital content files and enforcement of licensed use of the digital content files
A digital content file including a license control mechanism controlling the licensed use of digital content and a system and method for distributing licensable digital content files and licenses. A digital content file includes a digital content, which may be executable code or data, an embedded file access control mechanism and a dynamic license database associated with the file access mechanism for storing license information used by the file access control mechanism in controlling use of the digital content. The file access control mechanism includes a license monitor and control mechanism communicating with the dynamic license database and controlling use of the digital content and a license control utility providing communications between a user system and an external system to communicate license definition information and includes a graphical user interface. License information may be stored initially in the dynamic license database or provided from an external system. The system allows the distribution of digital content files and the acquisition of licenses with seamless transaction processing through an order processing system generating an order identification and authorization for a license and a product configuration and order database containing license management databases associated with the digital content files and containing license information to be transmitted to a user system upon receipt of an order identifier. The product configuration and order database also generates a license record for each transaction.
Owner:VIATECH TECH
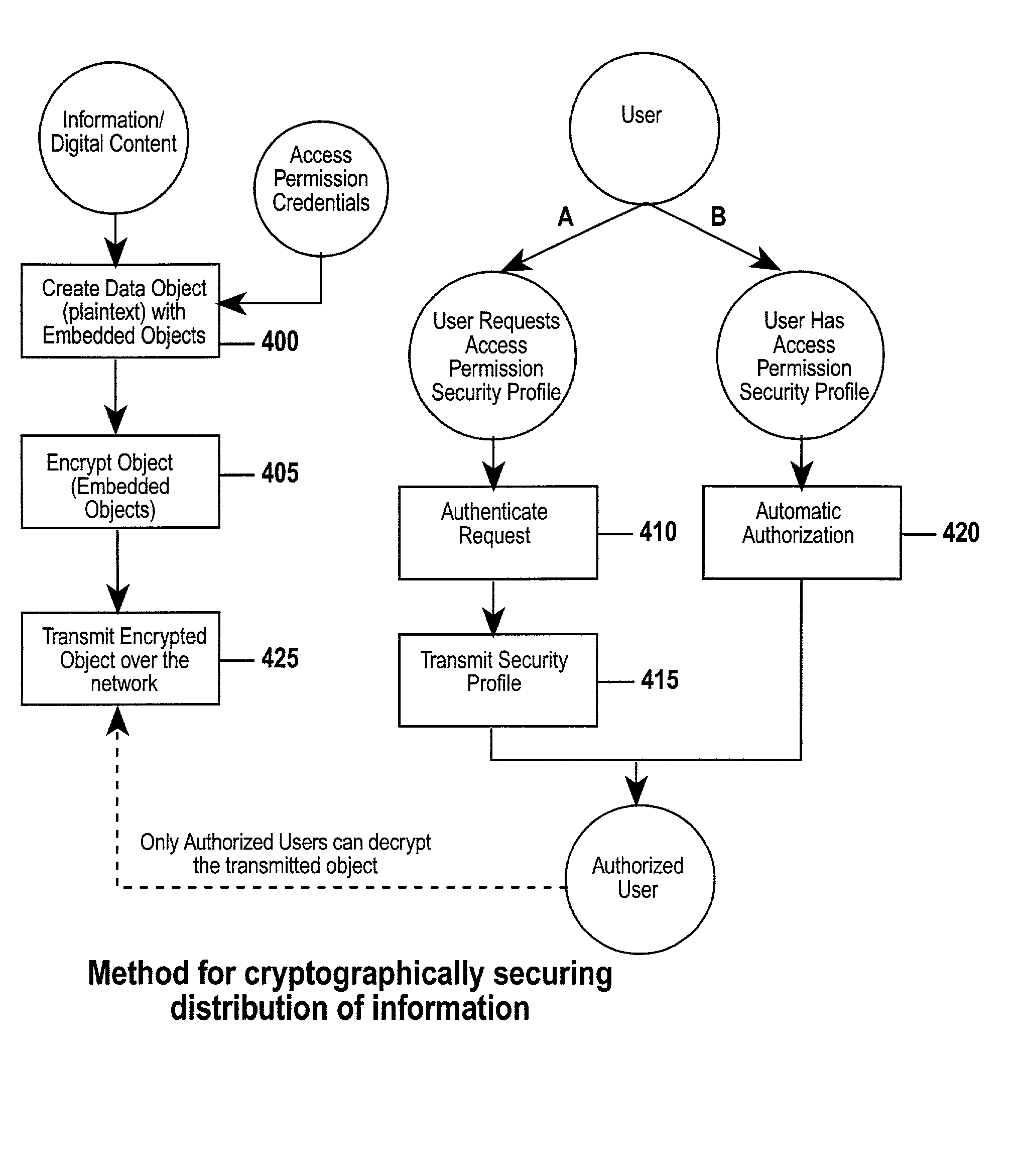
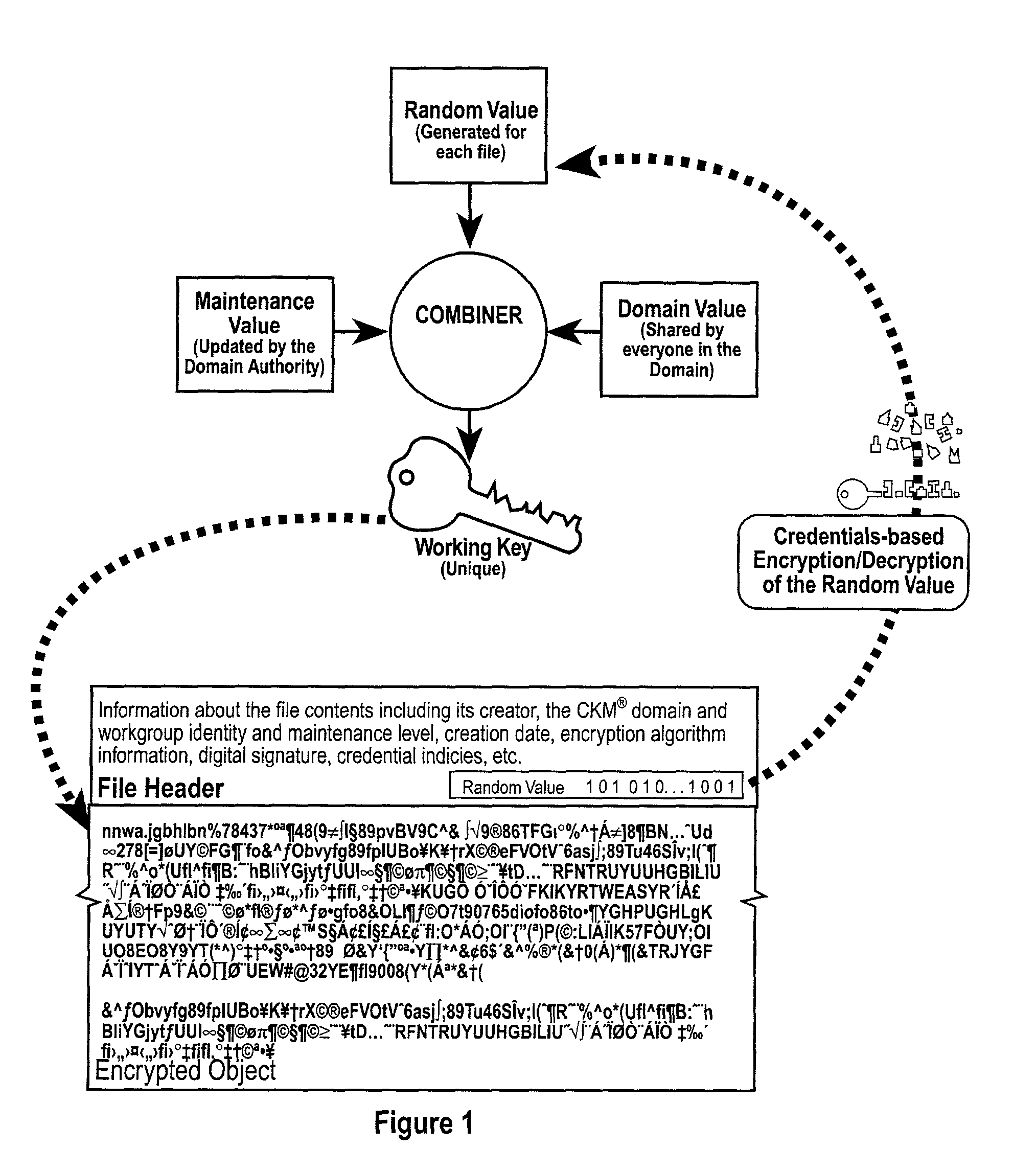
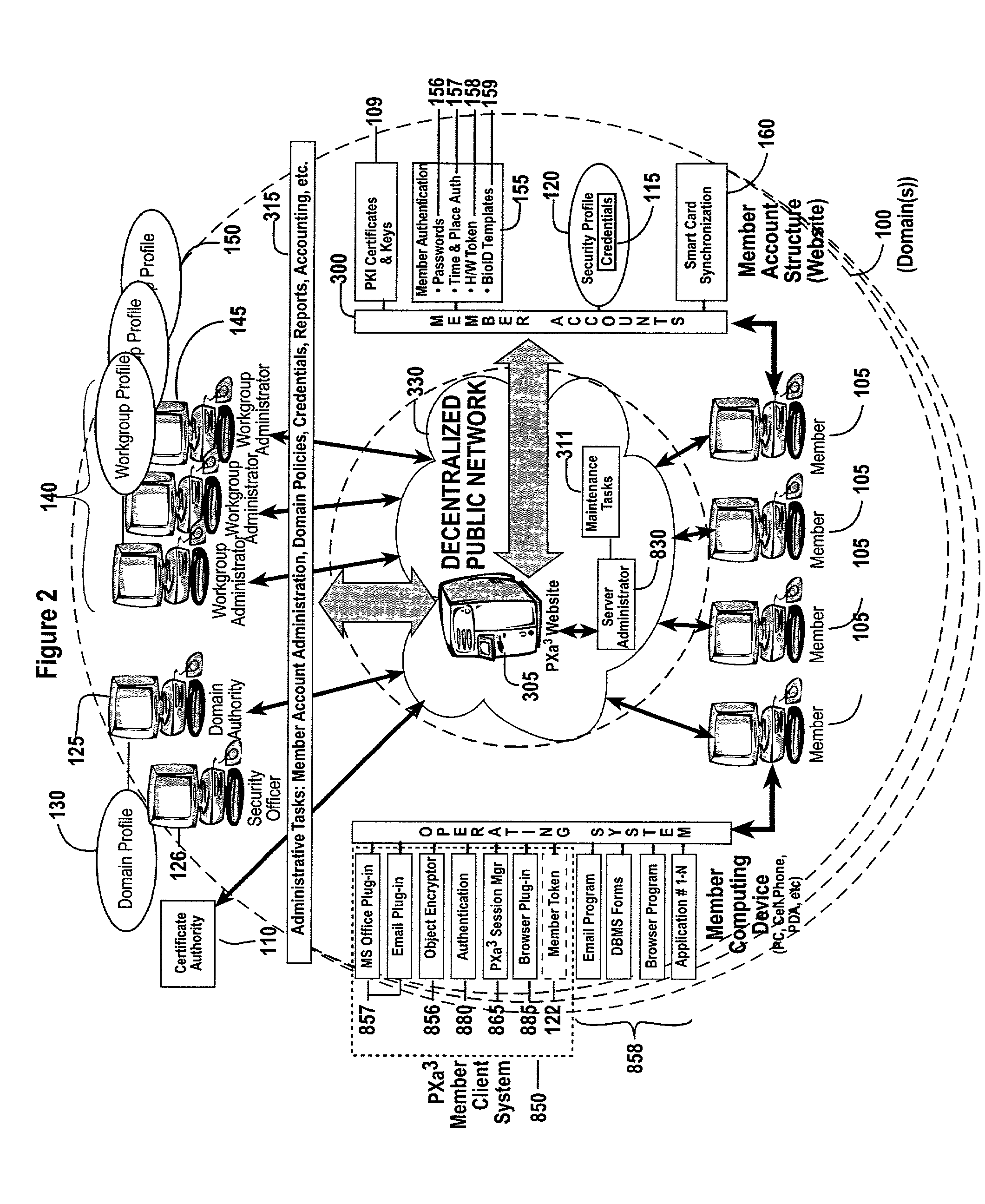
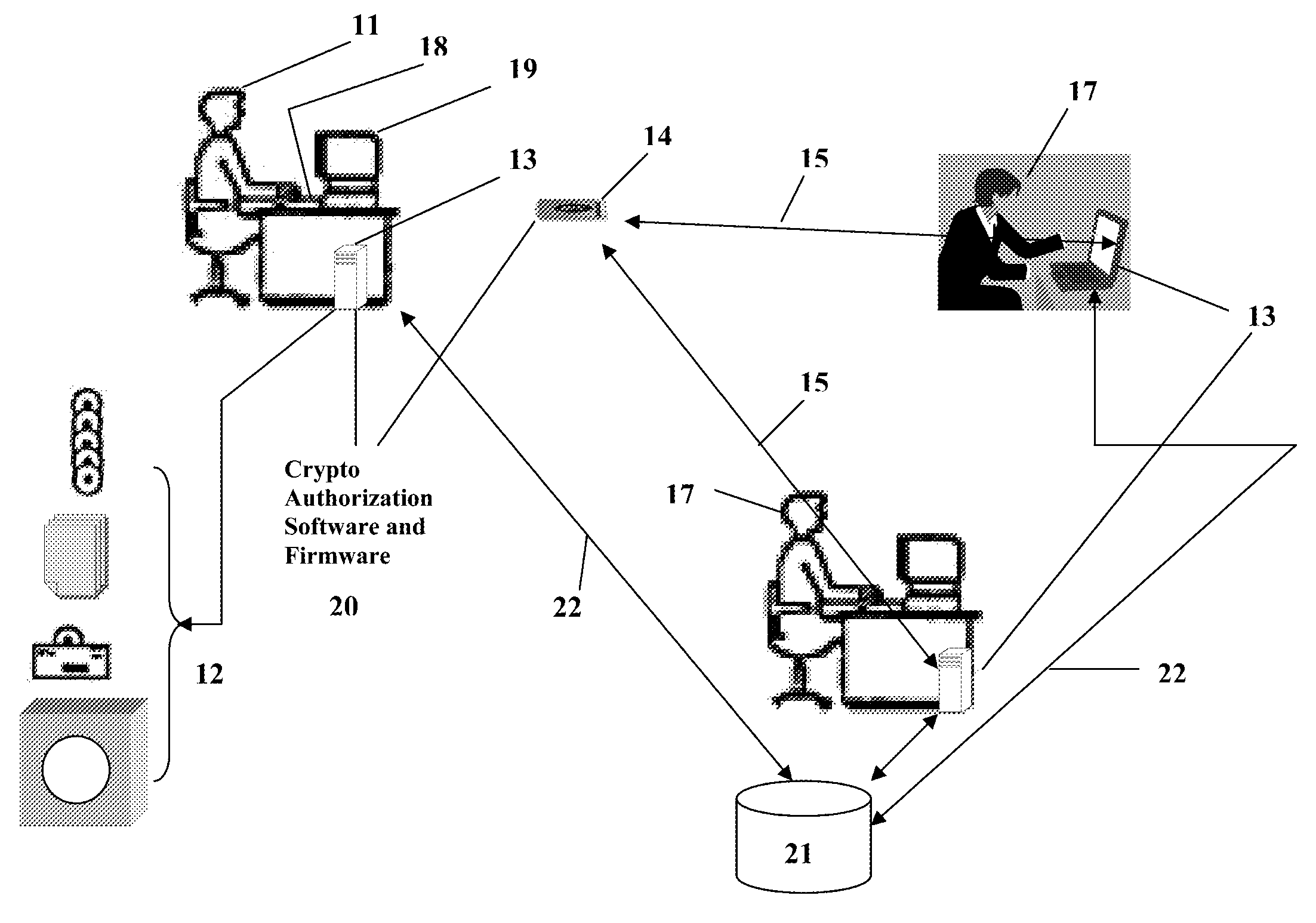
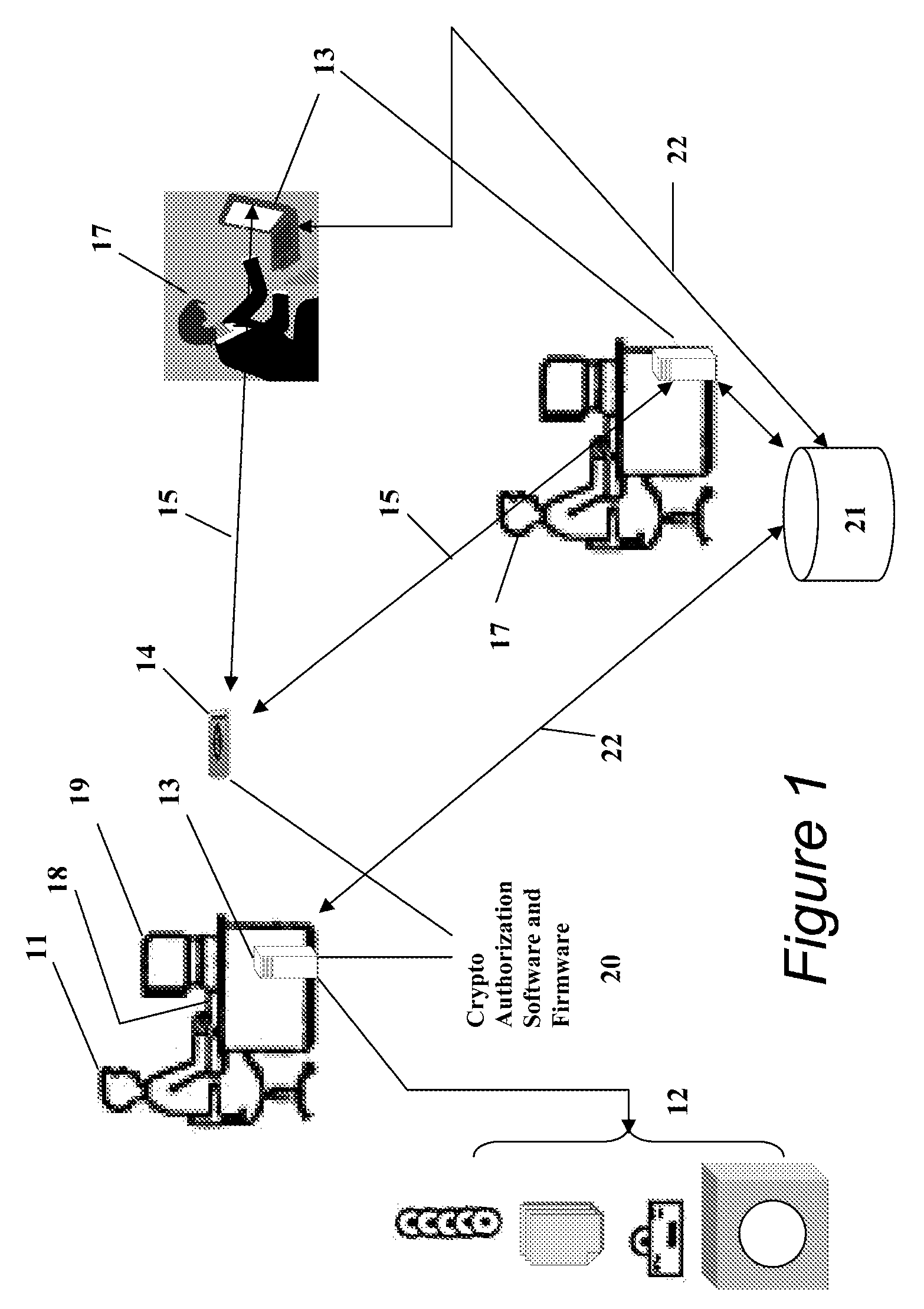
Method and apparatus for a web-based application service model for security management
The invention combines cryptographic key management technology with various authentication options and the use of a companion PKI system in a web-centric cryptographic key management security method and apparatus called PXa3(TM) (Precise eXtensible Authentication, Authorization and Administration). The PXa3 model uses a security profile unique to a network user and the member domain(s) he / she belongs to. A PXa3 server holds all private keys and certificates, the user's security profile, including credentials and the optional authentication enrollment data. The server maintains a security profile for each user, and administrators simply transmitted credential updates and other periodic maintenance updates to users via their PXa3 server-based member accounts. Domain and workgroup administrators also perform administrative chores via a connection to the PXa3 web site, rather than on a local workstation. A member's security profile, containing algorithm access permissions, credentials, domain and maintenance values, a file header encrypting key, optional biometric templates, and domain-specific policies is contained in one of two places: either on a removable cryptographic token (e.g., a smart card), or on a central server-based profile maintained for each member and available as a downloadable "soft token" over any Internet connection.
Owner:SIVAULT INC
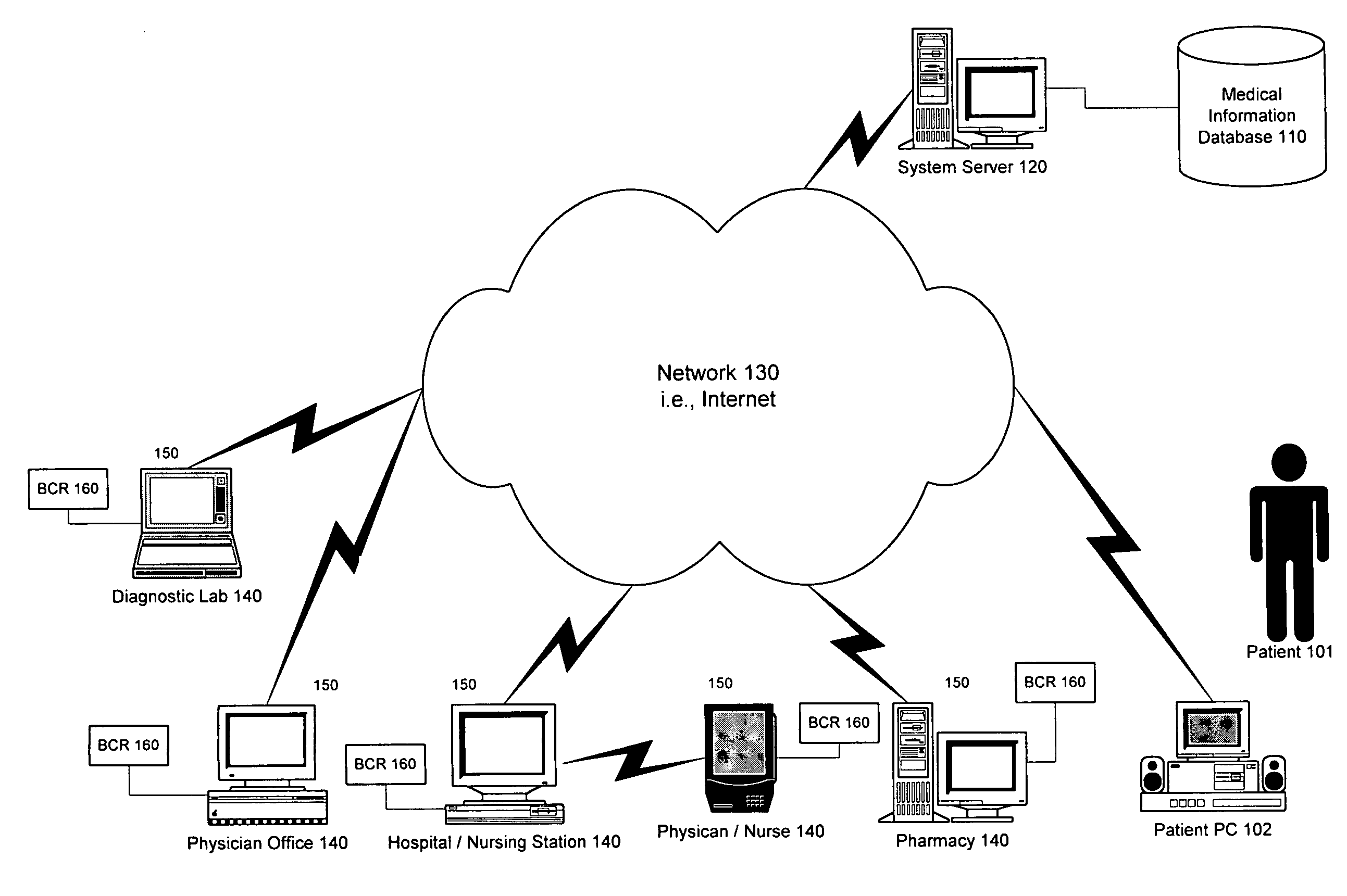
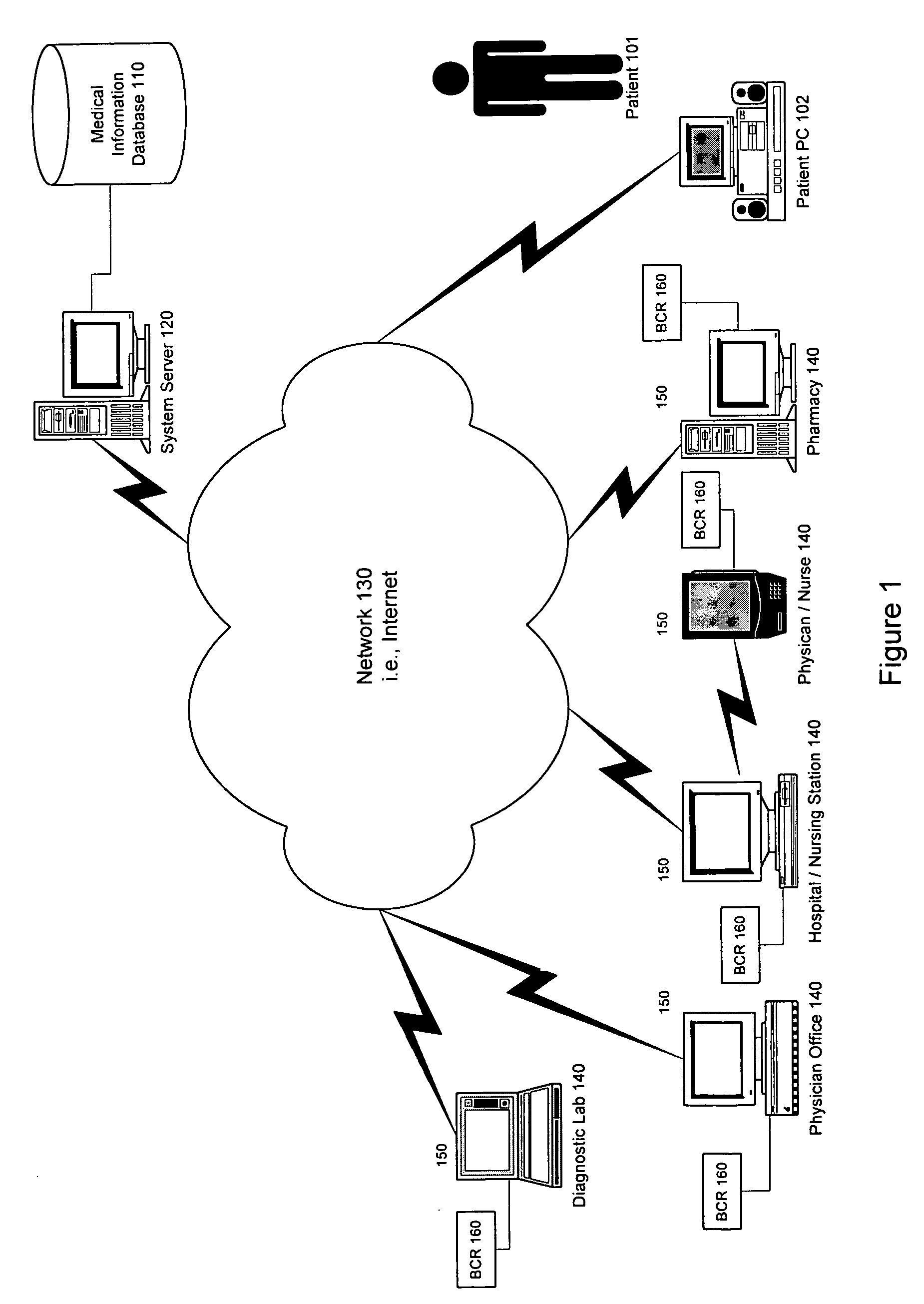
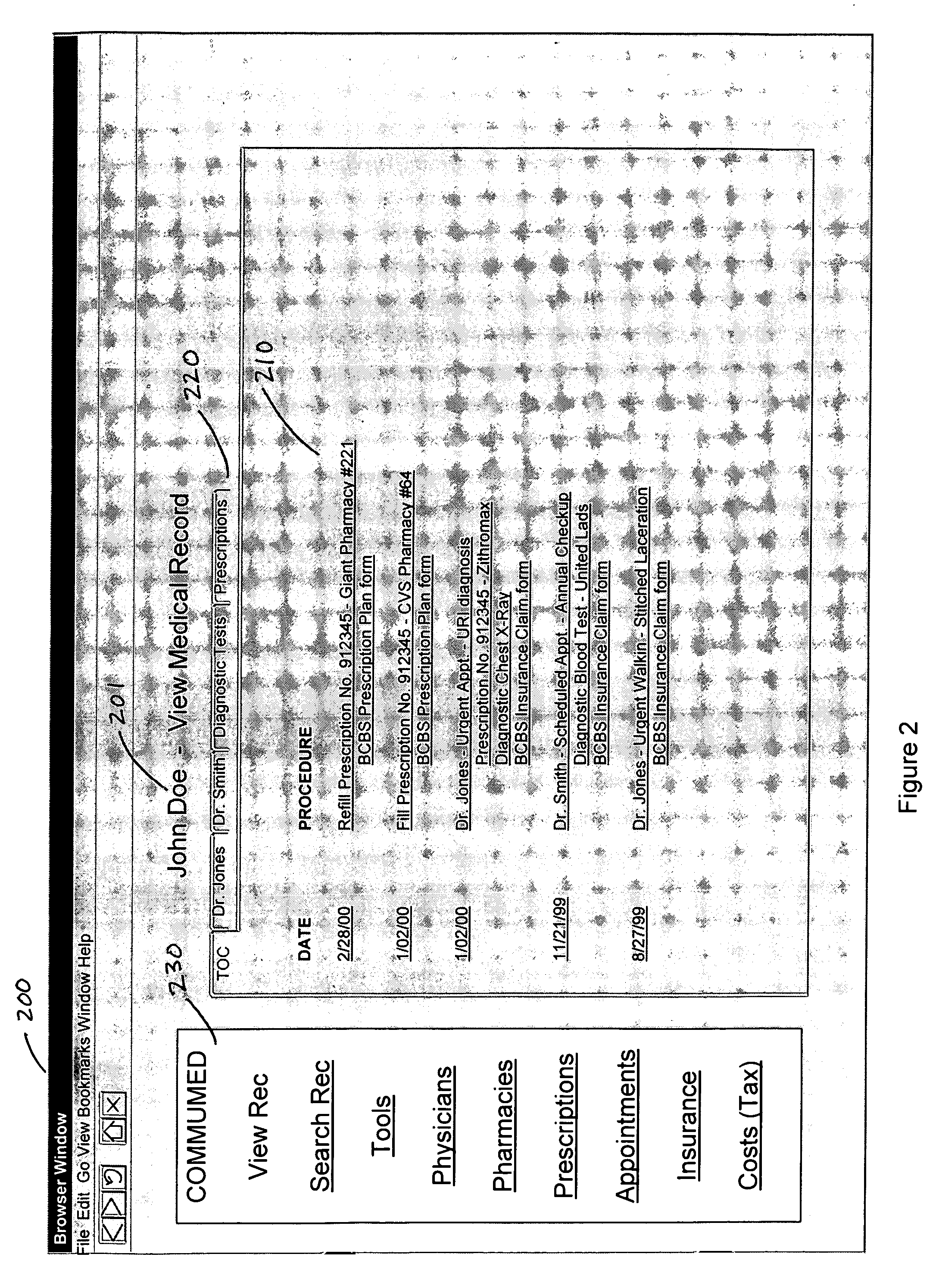
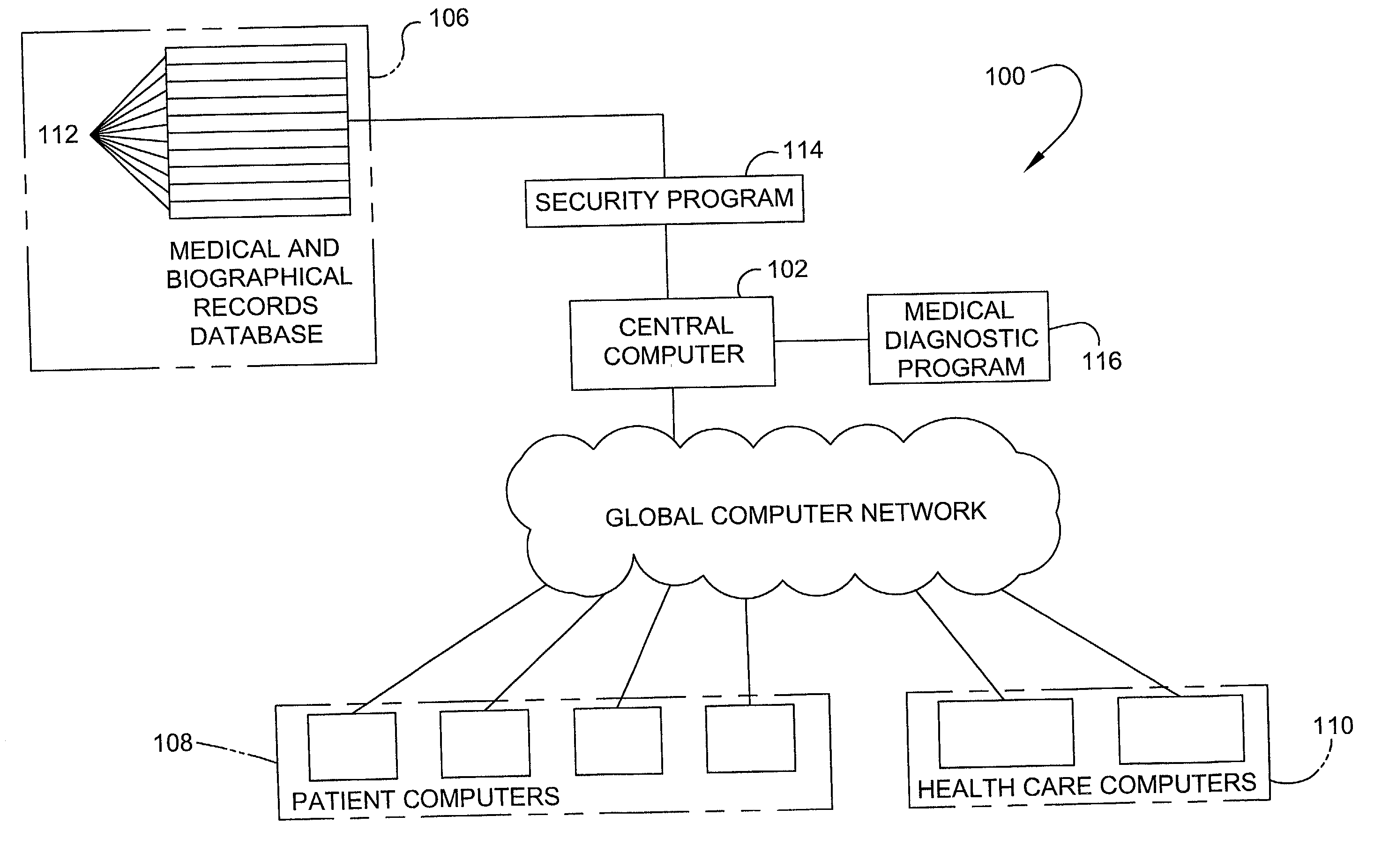
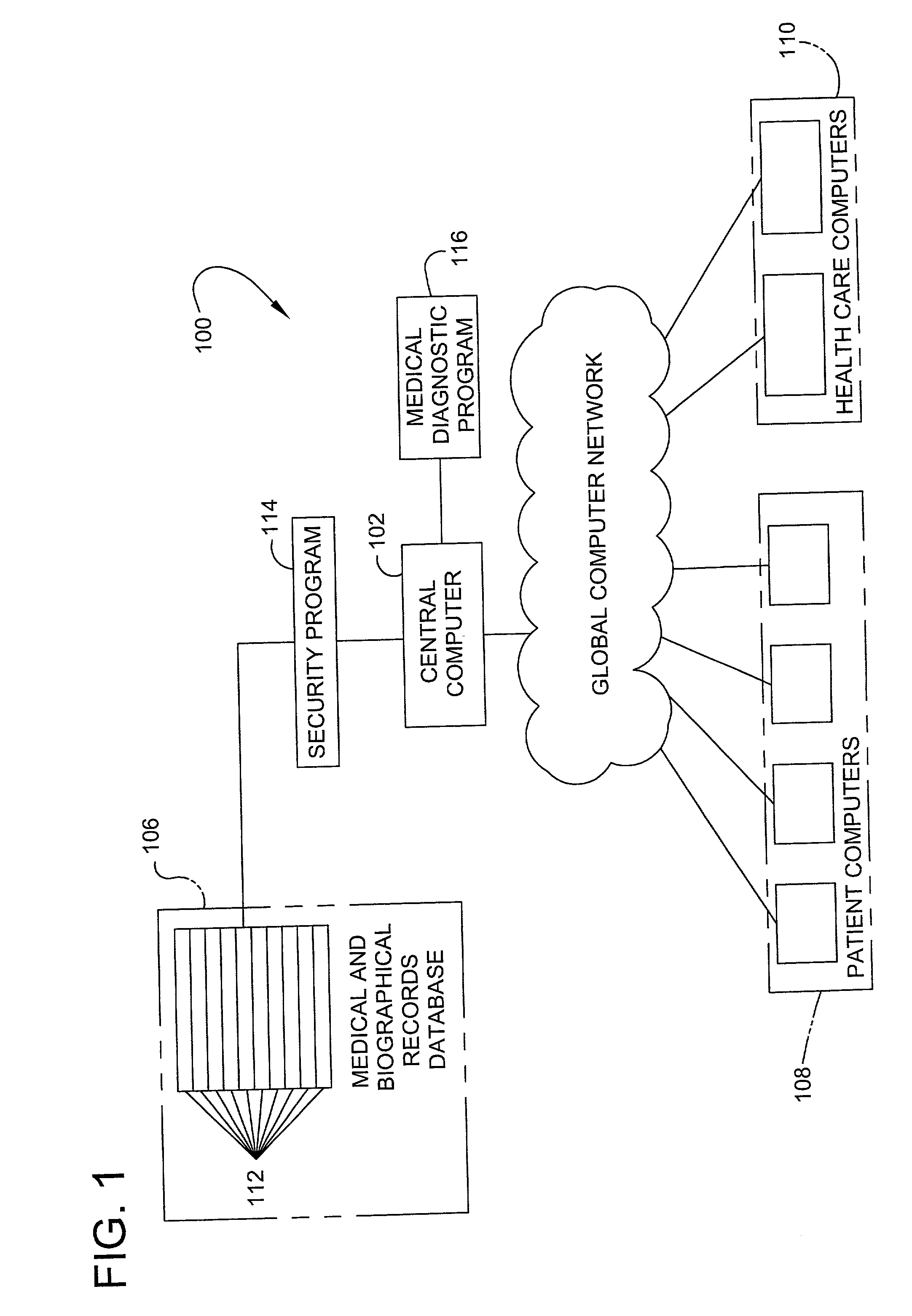
Patient-controlled medical information system and method
InactiveUS6988075B1Increase heightEasy accessDrug and medicationsPatient personal data managementInformation systemAuthorization
An electronic medical record system and service is disclosed for centrally storing patients medical records electronically on a database for patient-controlled remote access by both patients and medical providers. The system stores a plurality of patient medical records on a medical information database via a medical information server connected to a network. A plurality of medical provider computers connected to the network have software to communicate with the medical information server. Patients supply authorization means to allow medical provider computers to access patient-selected portions of the patient's medical record for viewing and updating of the patient's medical record. Additionally, patients can access all portions of their medical record using browser software on any browser-enabled device connected to the network.
Owner:RPX CORP
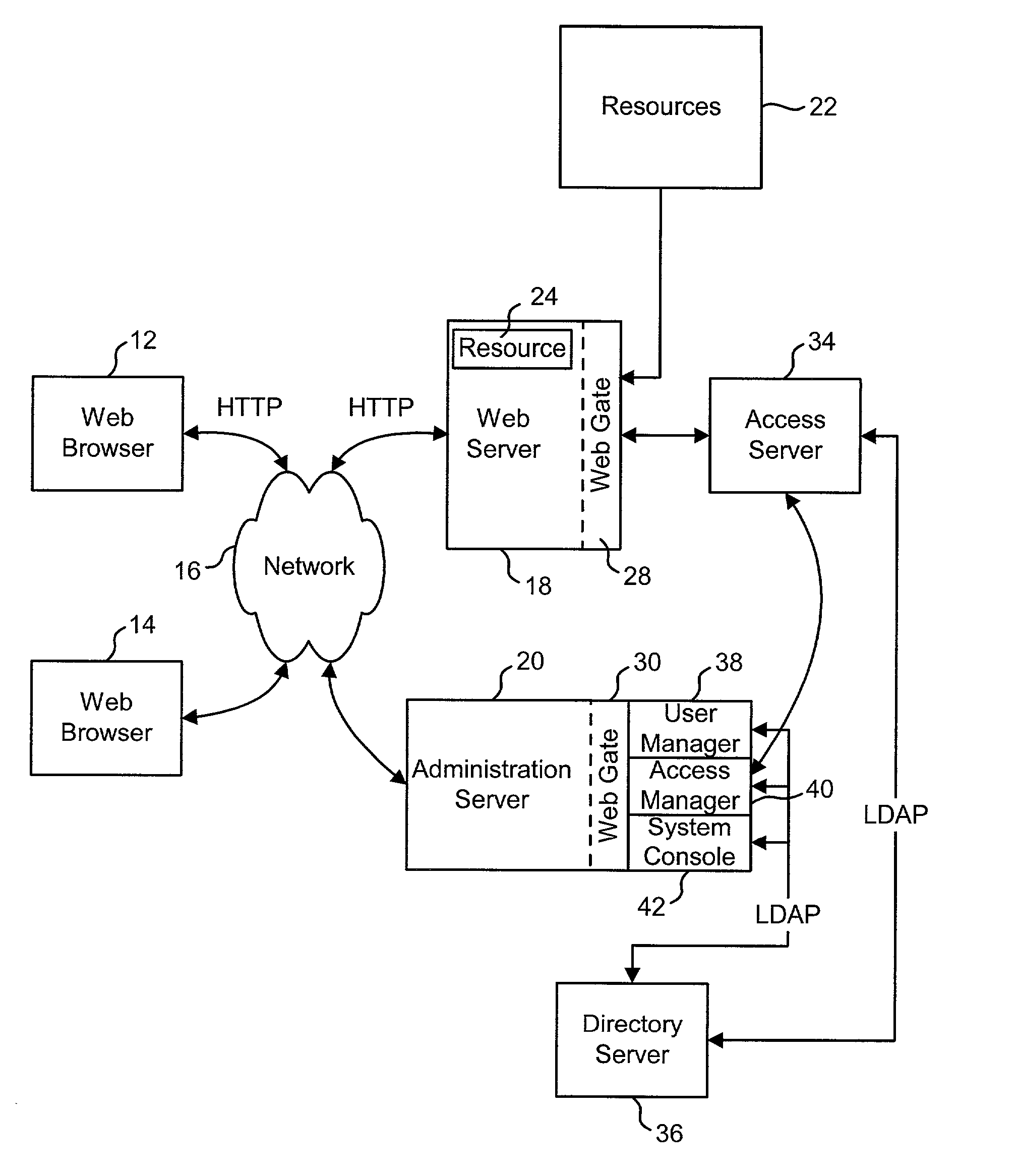
Access system interface
InactiveUS20030074580A1Easy mappingEasy to useDigital data processing detailsUser identity/authority verificationWeb serviceApplication software
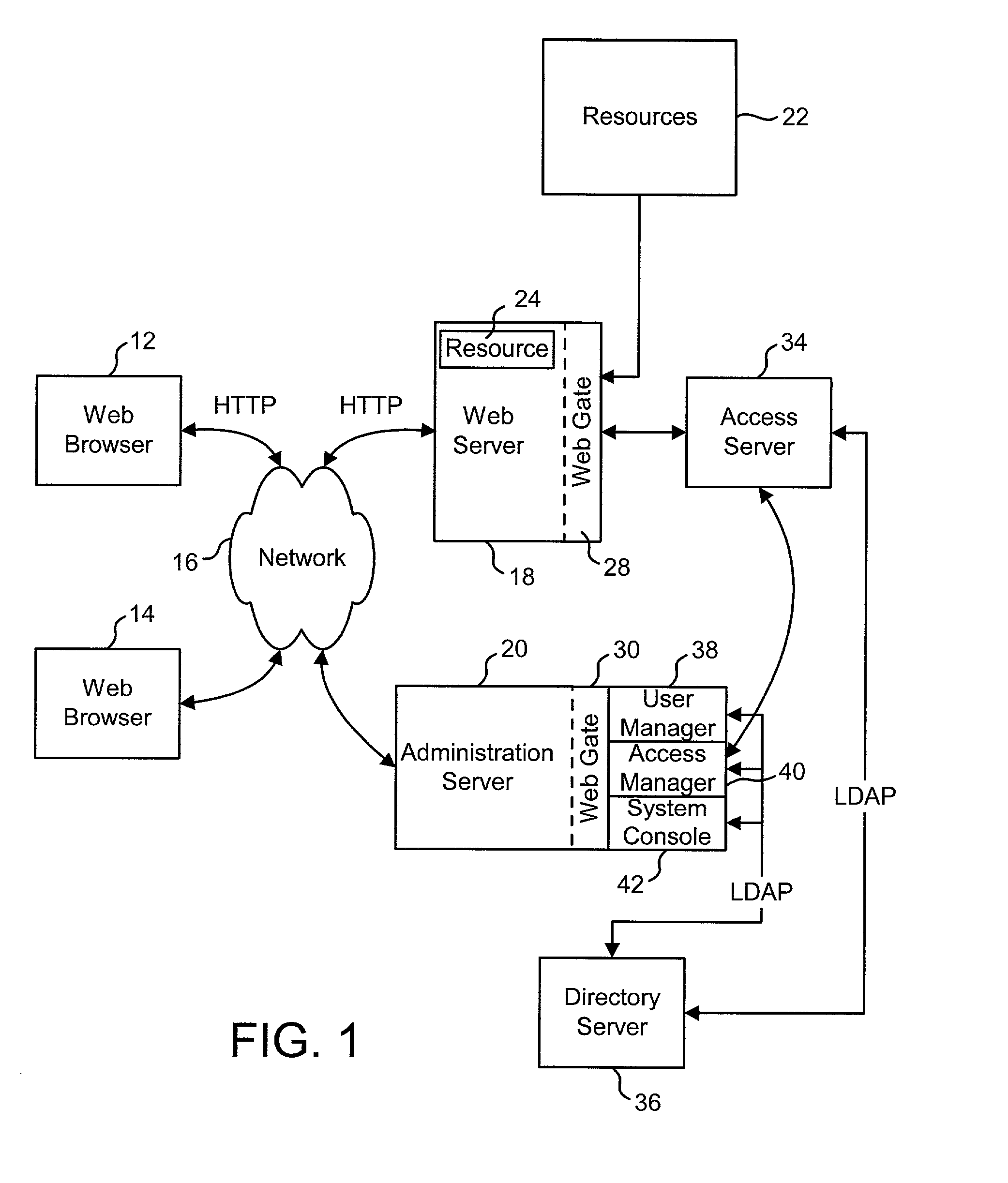
An access system provides identity management and / or access management services for a network An application program interface for the access system enables an application without a web agent front end to read and use contents of an existing encrypted cookie to bypass authentication and proceed to authorization. A web agent is a component (usually software, but can be hardware or a combination of hardware and software) that plugs into (or otherwise integrates with) a web server (or equivalent) in order to participate in providing access services.
Owner:ORACLE INT CORP
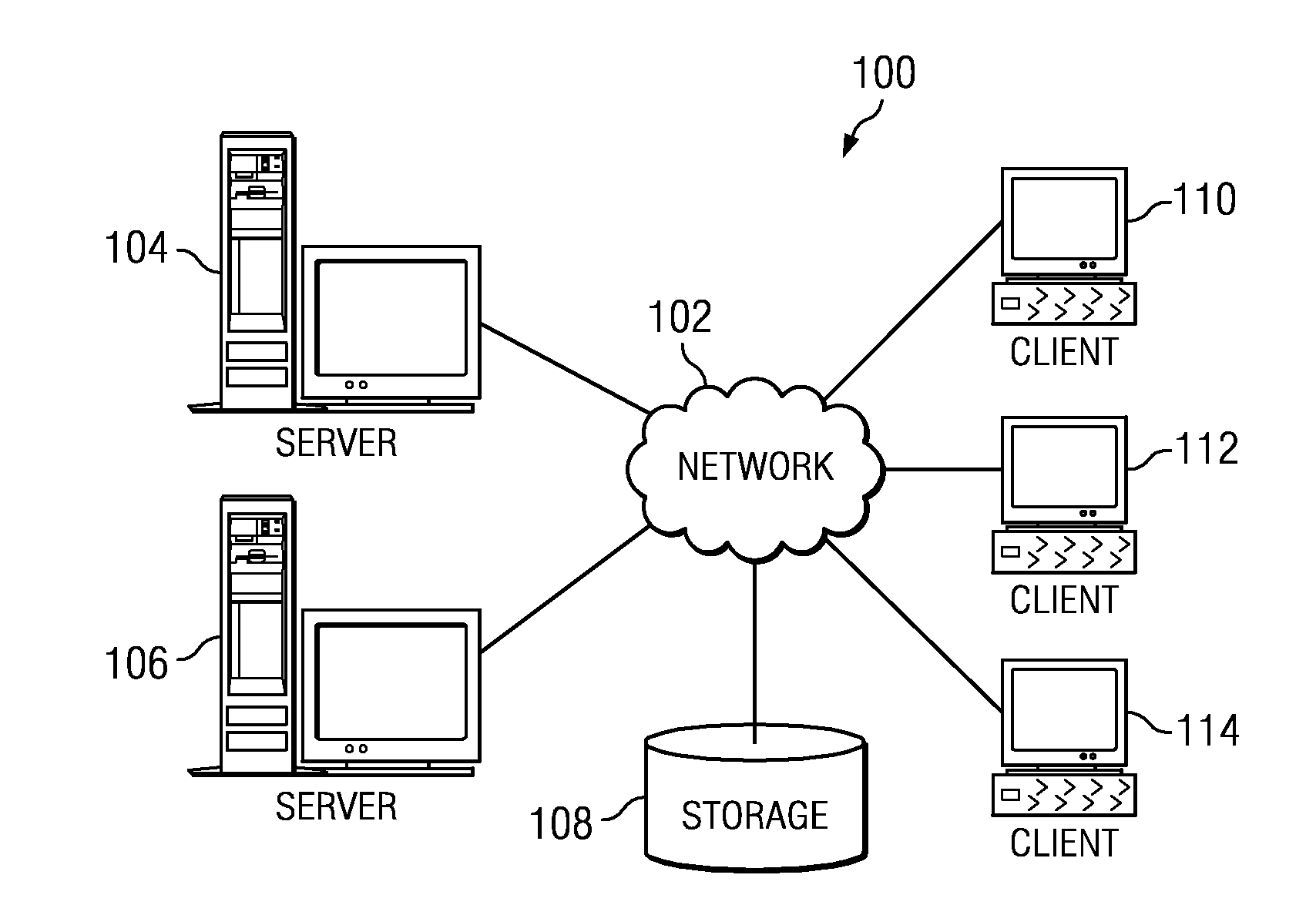
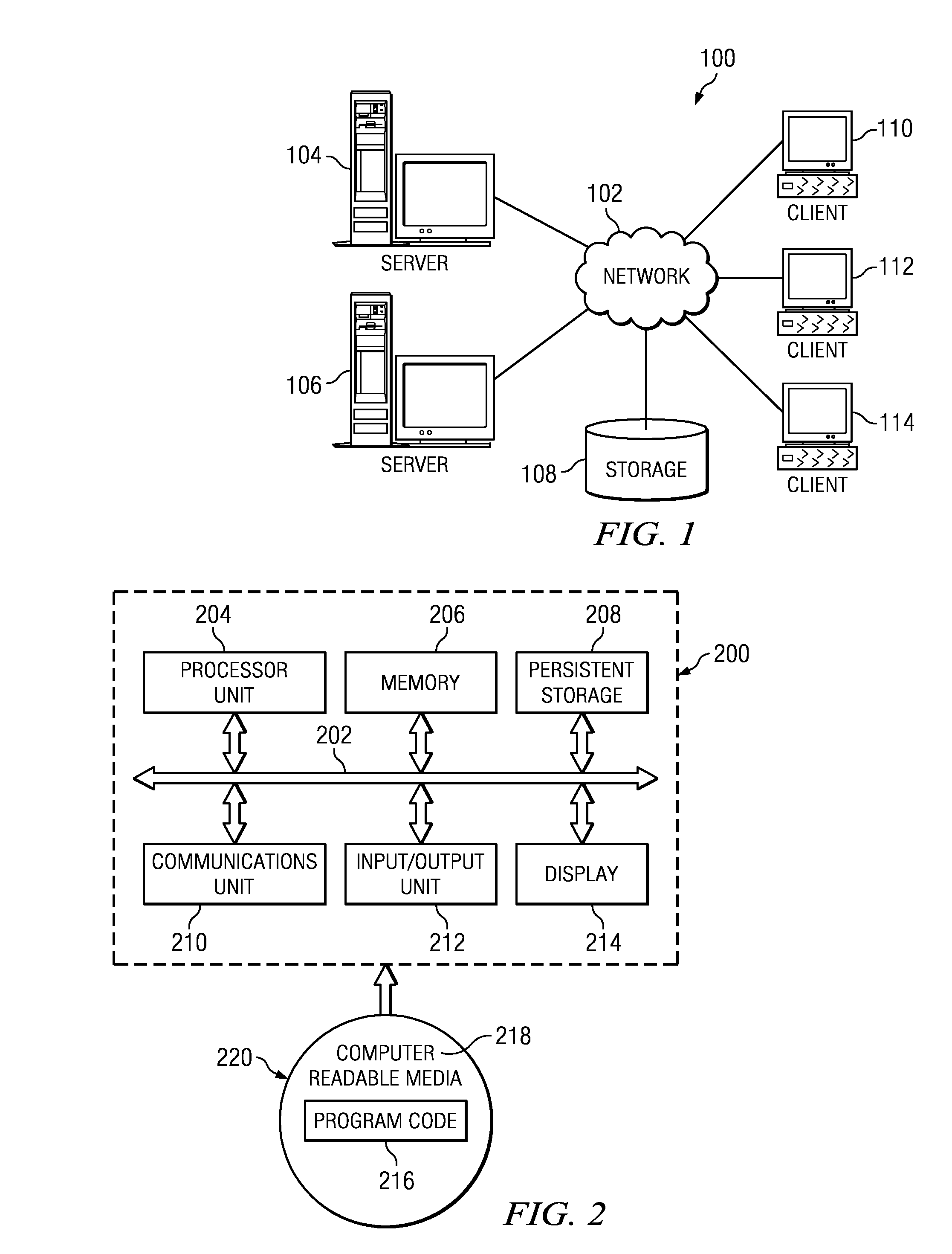
Authentication and authorization methods for cloud computing security platform
ActiveUS20130007845A1Retain controlDigital data processing detailsUser identity/authority verificationThird partyResource pool
An authentication and authorization plug-in model for a cloud computing environment enables cloud customers to retain control over their enterprise information when their applications are deployed in the cloud. The cloud service provider provides a pluggable interface for customer security modules. When a customer deploys an application, the cloud environment administrator allocates a resource group (e.g., processors, storage, and memory) for the customer's application and data. The customer registers its own authentication and authorization security module with the cloud security service, and that security module is then used to control what persons or entities can access information associated with the deployed application. The cloud environment administrator, however, typically is not registered (as a permitted user) within the customer's security module; thus, the cloud environment administrator is not able to access (or release to others, or to the cloud's general resource pool) the resources assigned to the cloud customer (even though the administrator itself assigned those resources) or the associated business information. To further balance the rights of the various parties, a third party notary service protects the privacy and the access right of the customer when its application and information are deployed in the cloud.
Owner:IBM CORP
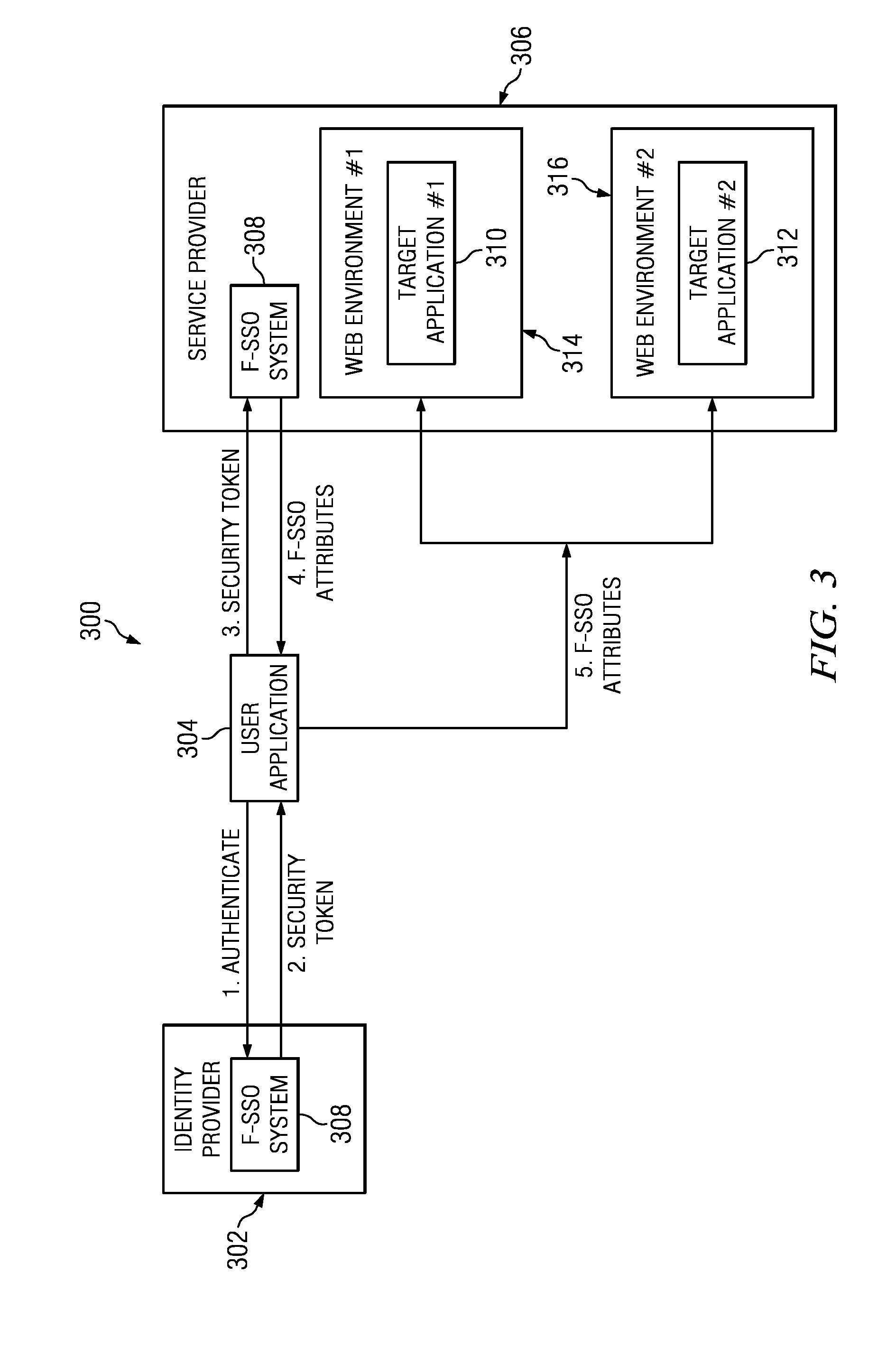
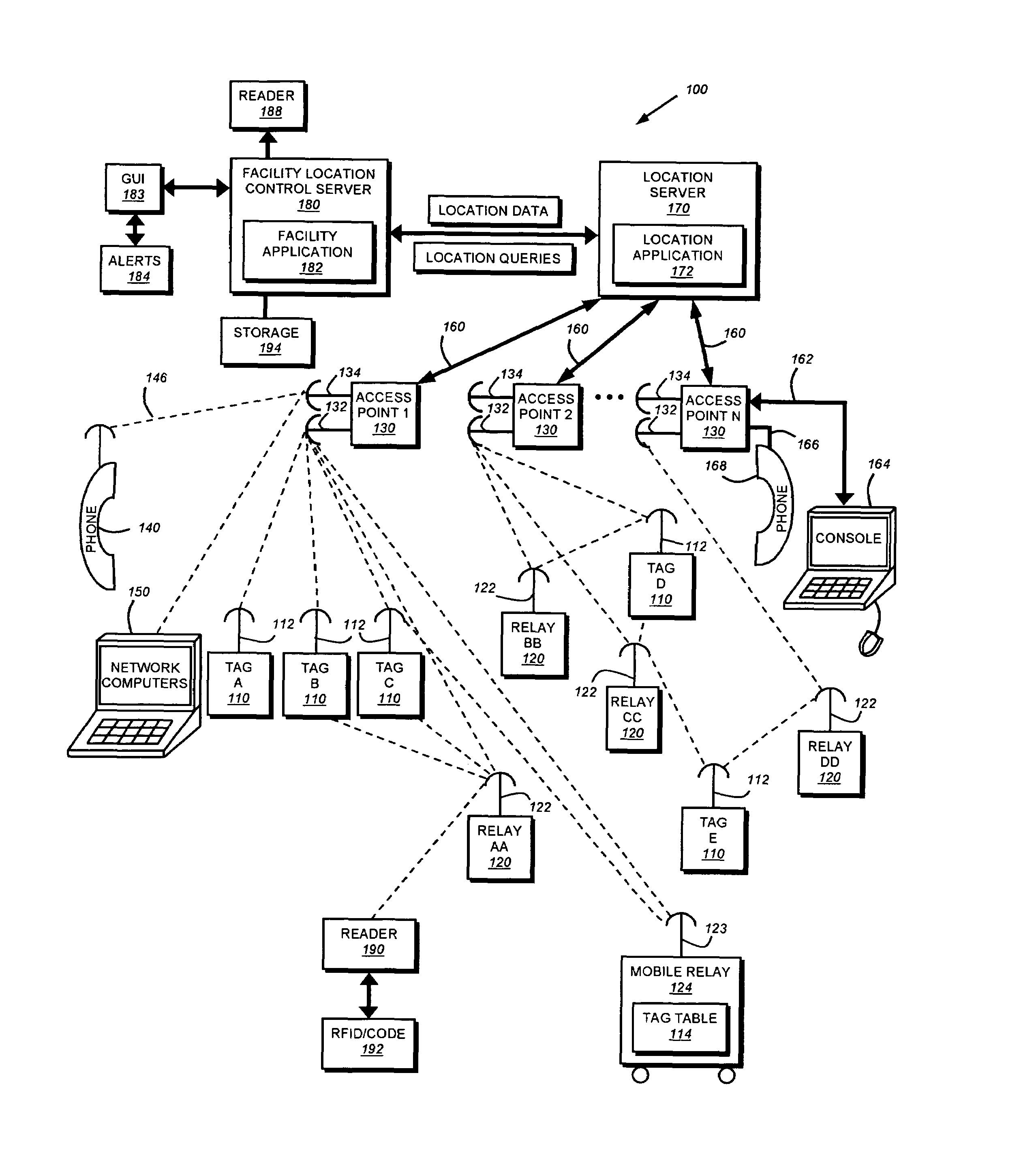
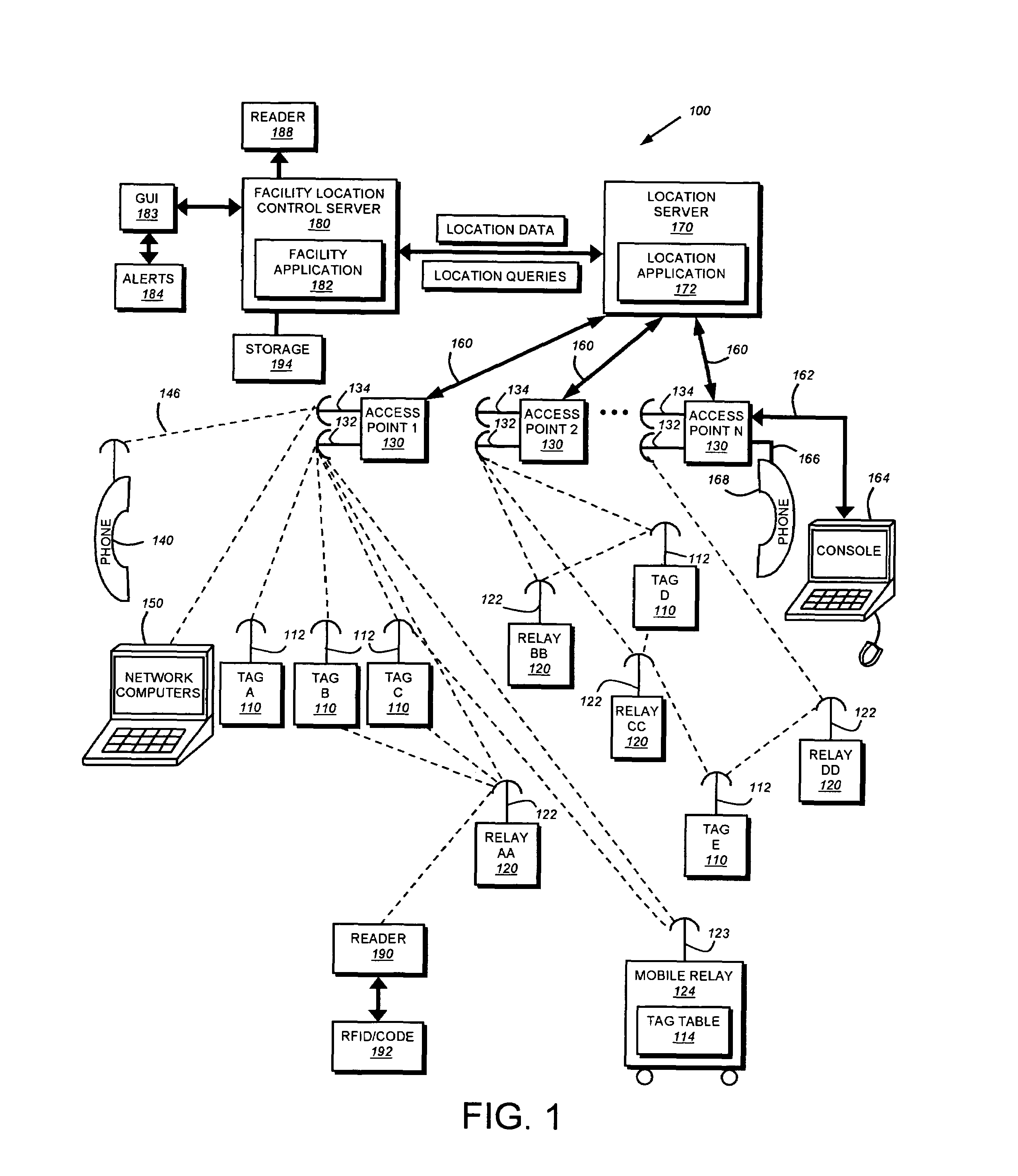
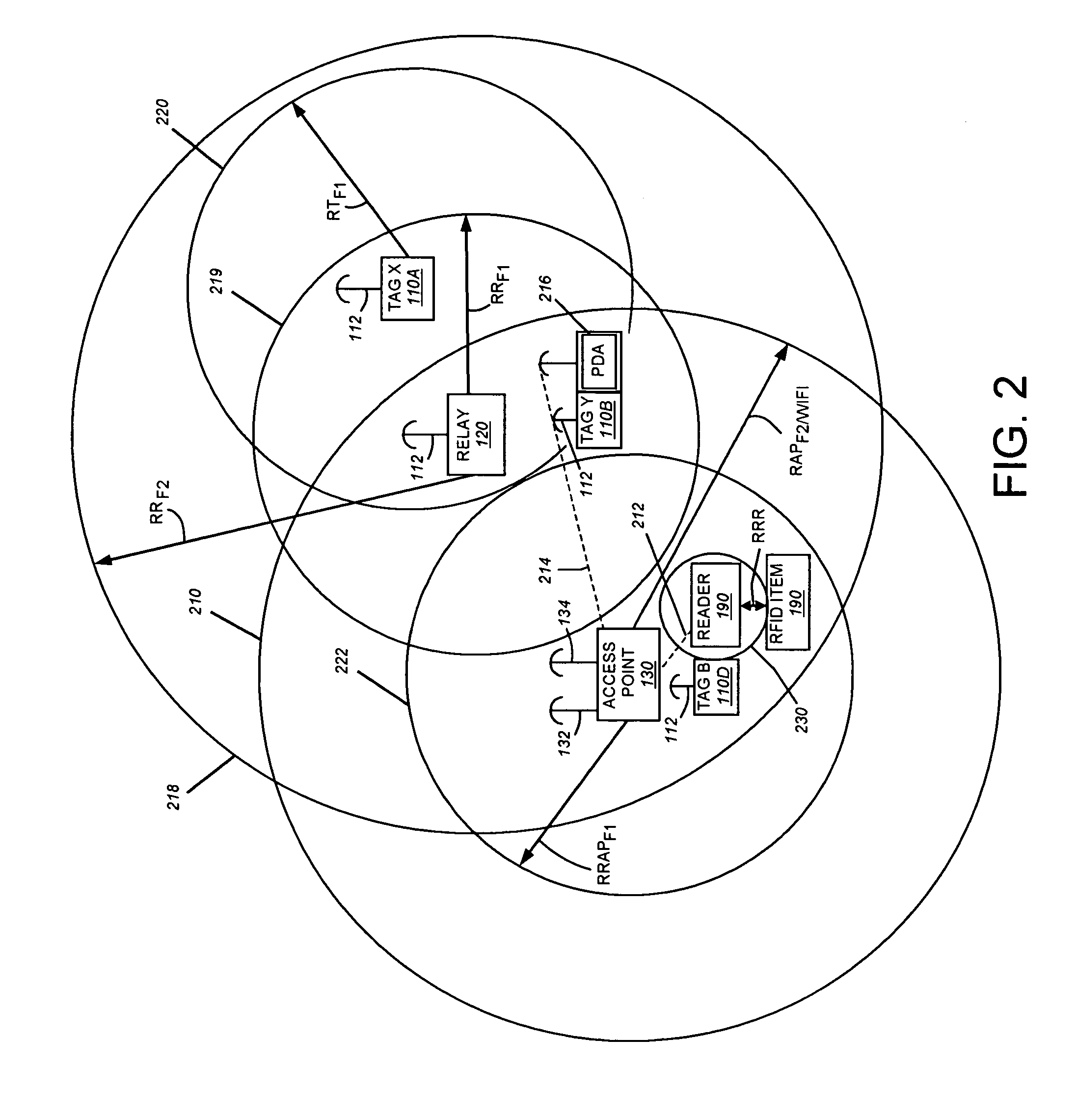
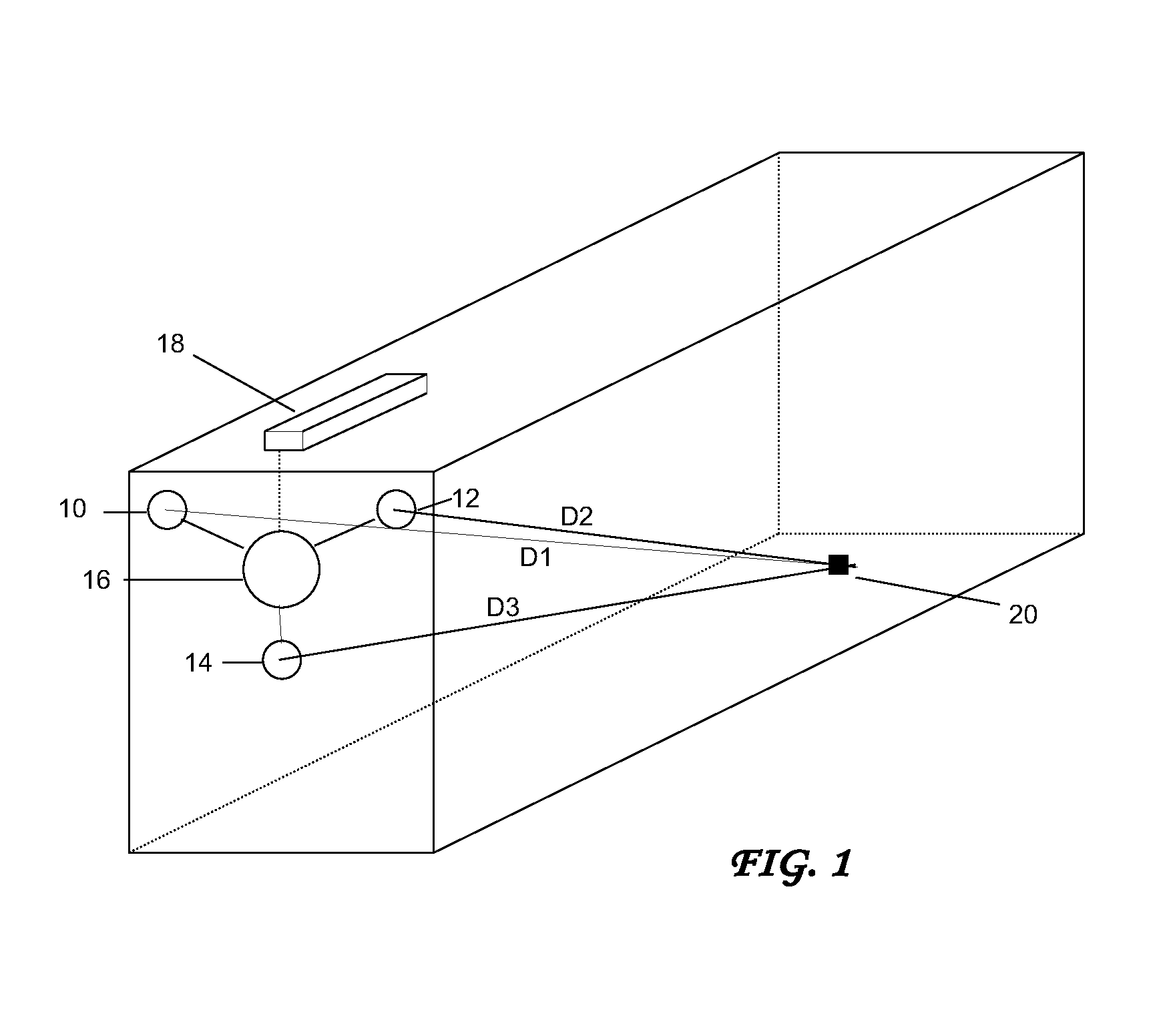
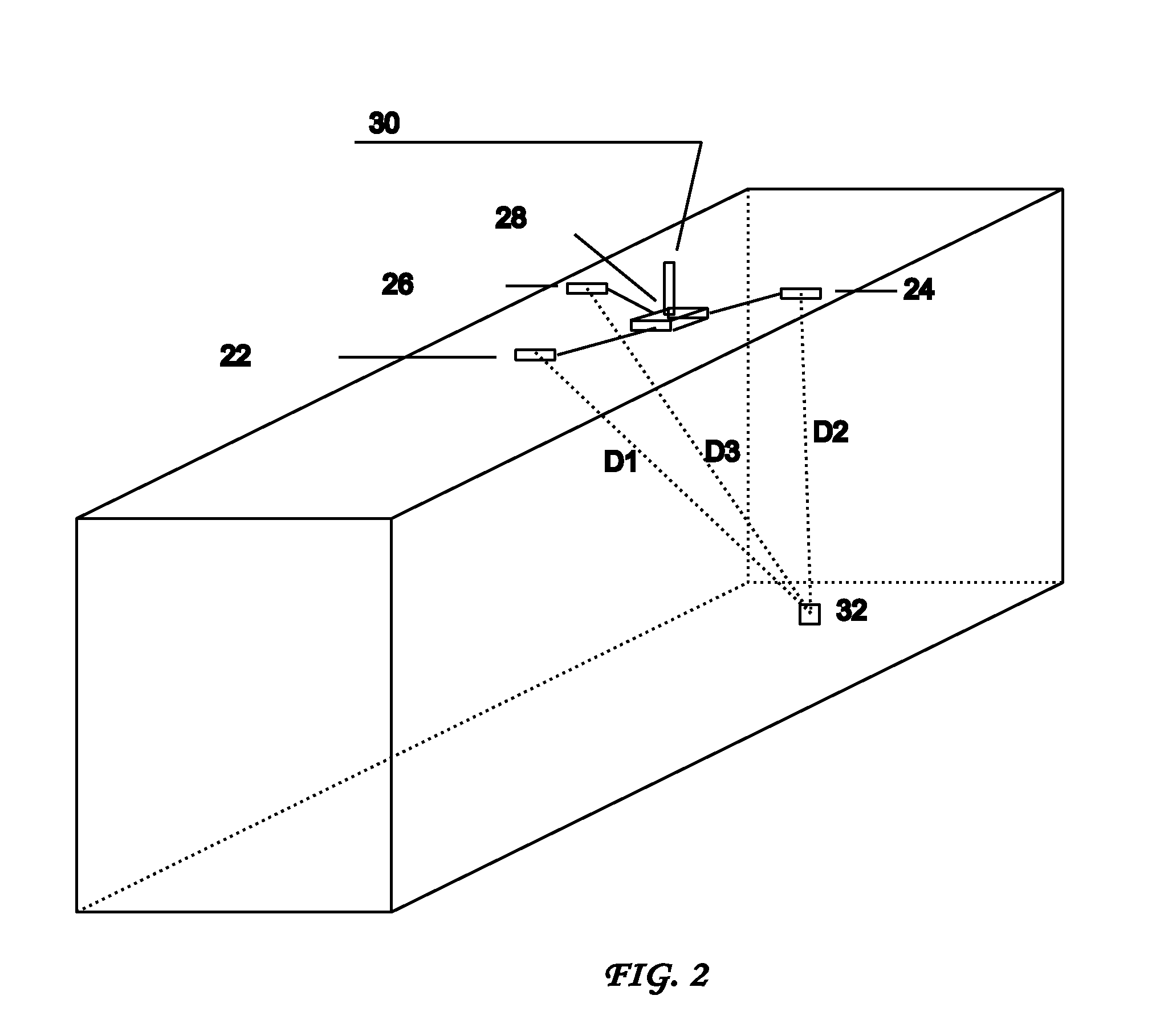
System and method for locating and communicating with personnel and equipment in a facility
InactiveUS7323991B1Increase redundancyQuickly and frequently and continuously updatedElectric signal transmission systemsTicket-issuing apparatusTransceiverWireless data
This invention provides a system and method for identifying, locating, authorizing by proximity and communicating with equipment and personnel in a facility that generally employs a series of limited range transceivers for location determination and a distributed wireless data network for data transfer. The system employs unique RF transceiver tags on personnel and equipment that are each uniquely identified and registered with a facility control application that oversees activities in the facility. The tags are tracked by RF communication based upon their proximity to one or more fixed-base networked access points and relays (which transfer location data by RF back to access points) within four range zones. Location data on all tags is uploaded periodically to a location server that interfaces with the facility control server. Tag data is monitored by the facility control server to track, authorize and deauthorize certain data transfers, movements and activities in accordance with rules established for each tag (or type of tag) within the facility control server's application. Wireless networking (WiFi, for example), in combination with the RF-derived location information, allows the facility control server to correlate and transmit data to staff in conjunction with location and proximity. WiFi can transmit authorizations, deauthorizations and general data based upon triggers established by proximity and location. Likewise, data can be transmitted over WiFi from readers etc. from personnel and equipment located and identified by the system.
Owner:TIDEWATER HLDG
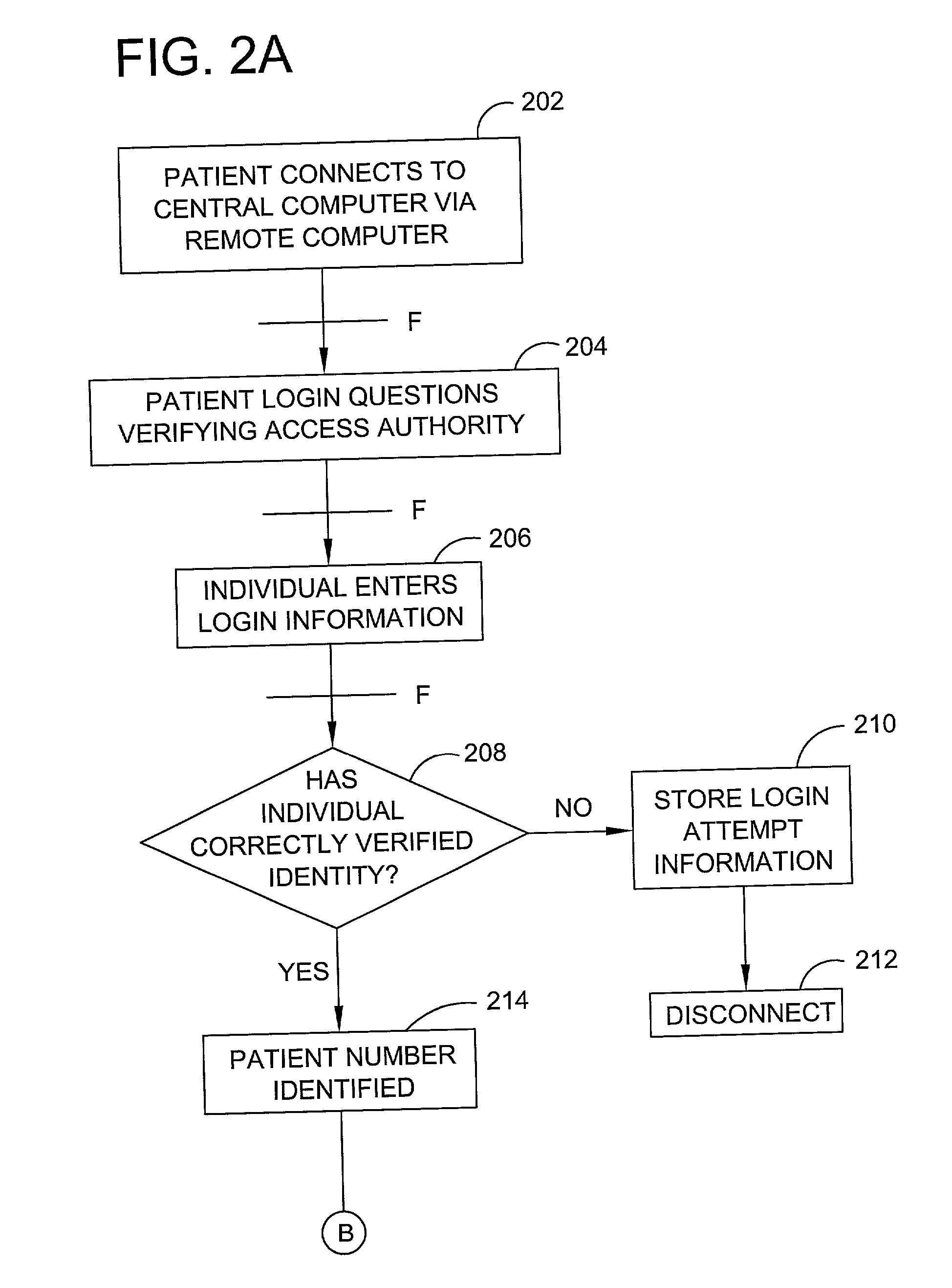
Patient - controlled automated medical record, diagnosis, and treatment system and method
A system and process for providing a computerized medical and biographical records database and diagnostic information. A medical records database and diagnostic program is stored on a central computer that is accessible to individuals using remotely situated computers connected to a computer network. Individual patient medical and biographical records are owned by individual patients who can enter information in their record as well as grant or deny authorization to others, such as health care professionals, insurance providers and other entities, to review part or all of their record. The diagnostic program provides a series of diagnostic questions to an individual who must respond either "yes" or "no" to each question. Each potential response is weighted relative to its importance to a particular disease diagnosis. Relative weights for all responses to diagnostic questions are summed to identify potential diagnoses to connected to the answered questions. The diagnostic program provides the individual with a list of potential diagnoses as well as permitting the individual to save the information to his or her individual medical and biographical record. The information maintained in the above system and process is utilized for health care financing and insurance.
Owner:MARFLY 1 LP
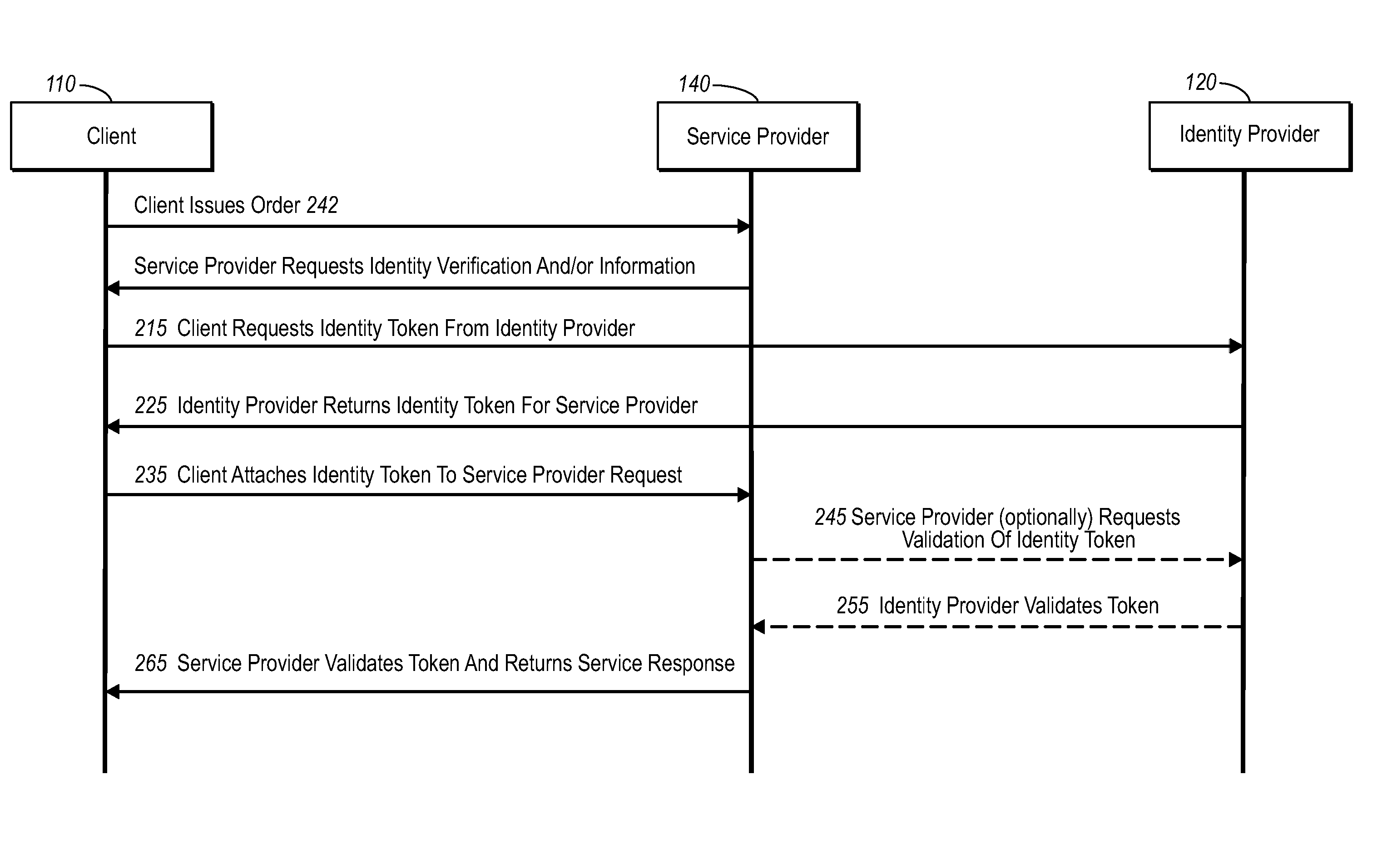
Secure network commercial transactions
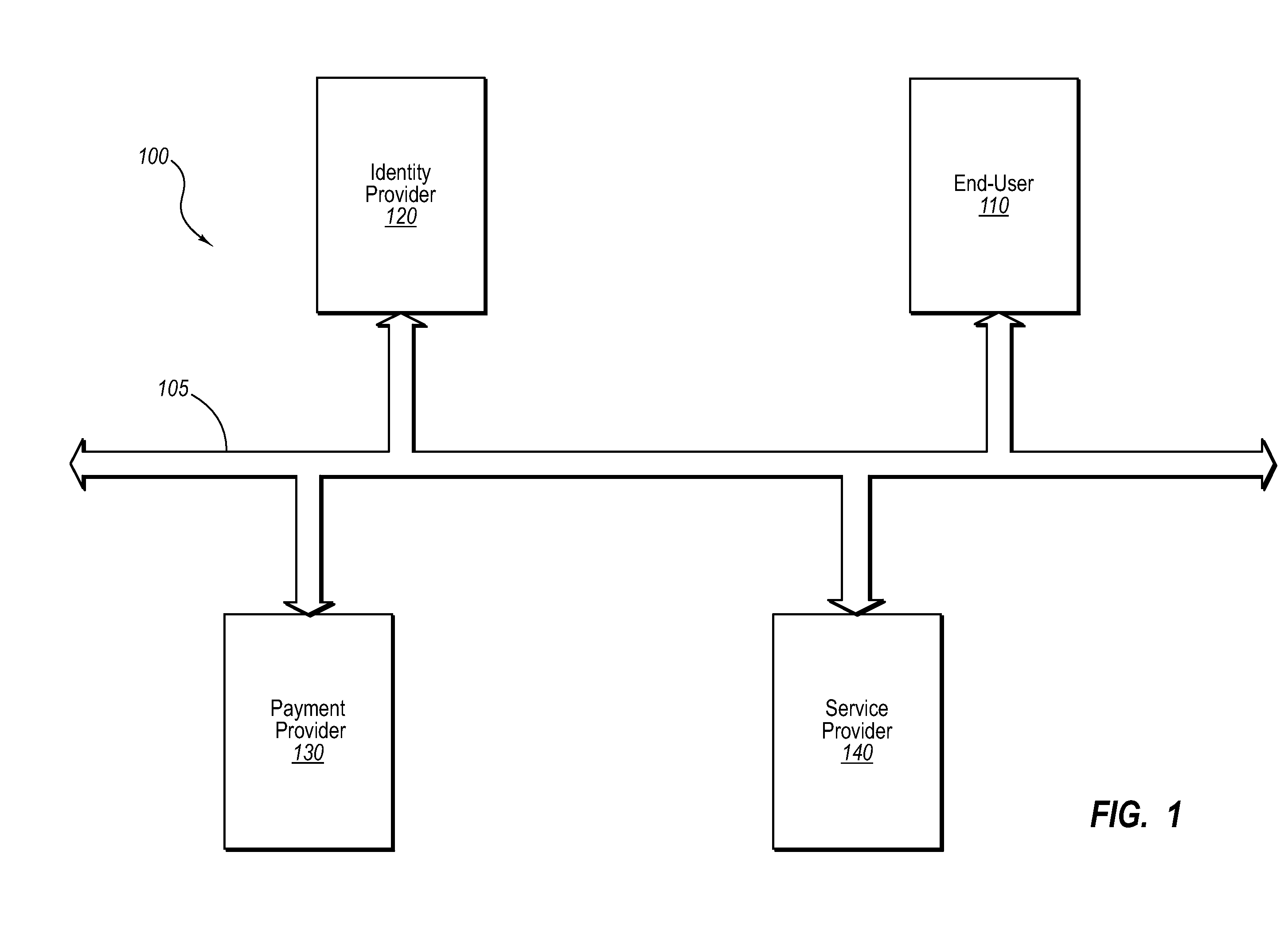
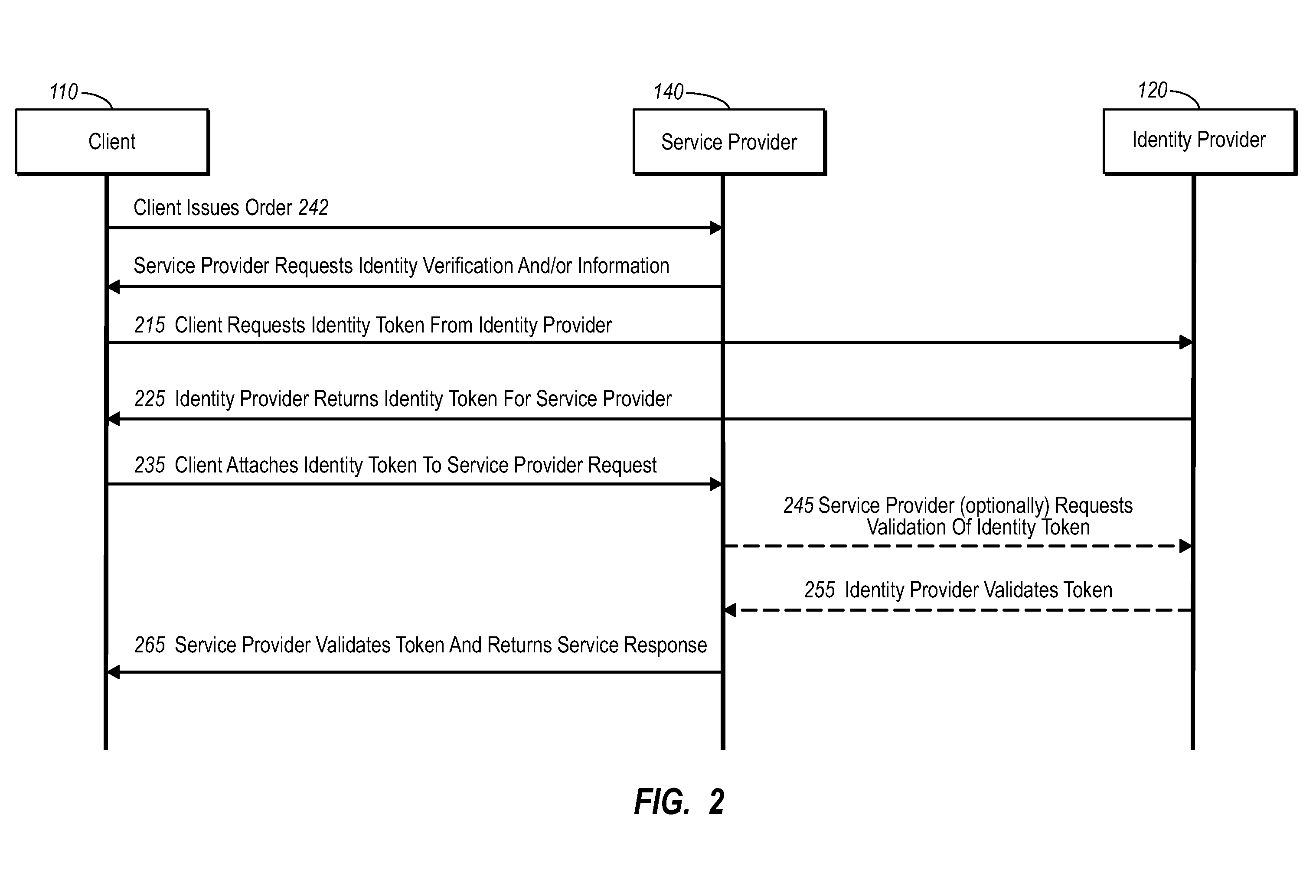
InactiveUS20060235795A1Reduce the burden onSimpler and more secure online commercial transactions frameworkFinanceBuying/selling/leasing transactionsPaymentSecure communication
Current embodiments provide for authorization and payment of an online commercial transaction between a purchaser and a merchant including verification of an identity of the purchaser and verification of an ability of the purchaser to pay for the transaction, where the identity provider and the payment provider are often different network entities. Other embodiments also provide for protocols, computing systems, and other mechanisms that allow for identity and payment authentication using a mobile module, which establishes single or multilevel security over an untrusted network (e.g., the Internet). Still other embodiments also provide for a three-way secure communication between a merchant, consumer, and payment provider such that sensitive account information is opaque to the merchant, yet the merchant is sufficiently confident of the consumer's ability to pay for requested purchases. In yet another embodiment, electronic billing information is used for authorization, auditing, payment federation, and other purposes.
Owner:MICROSOFT TECH LICENSING LLC
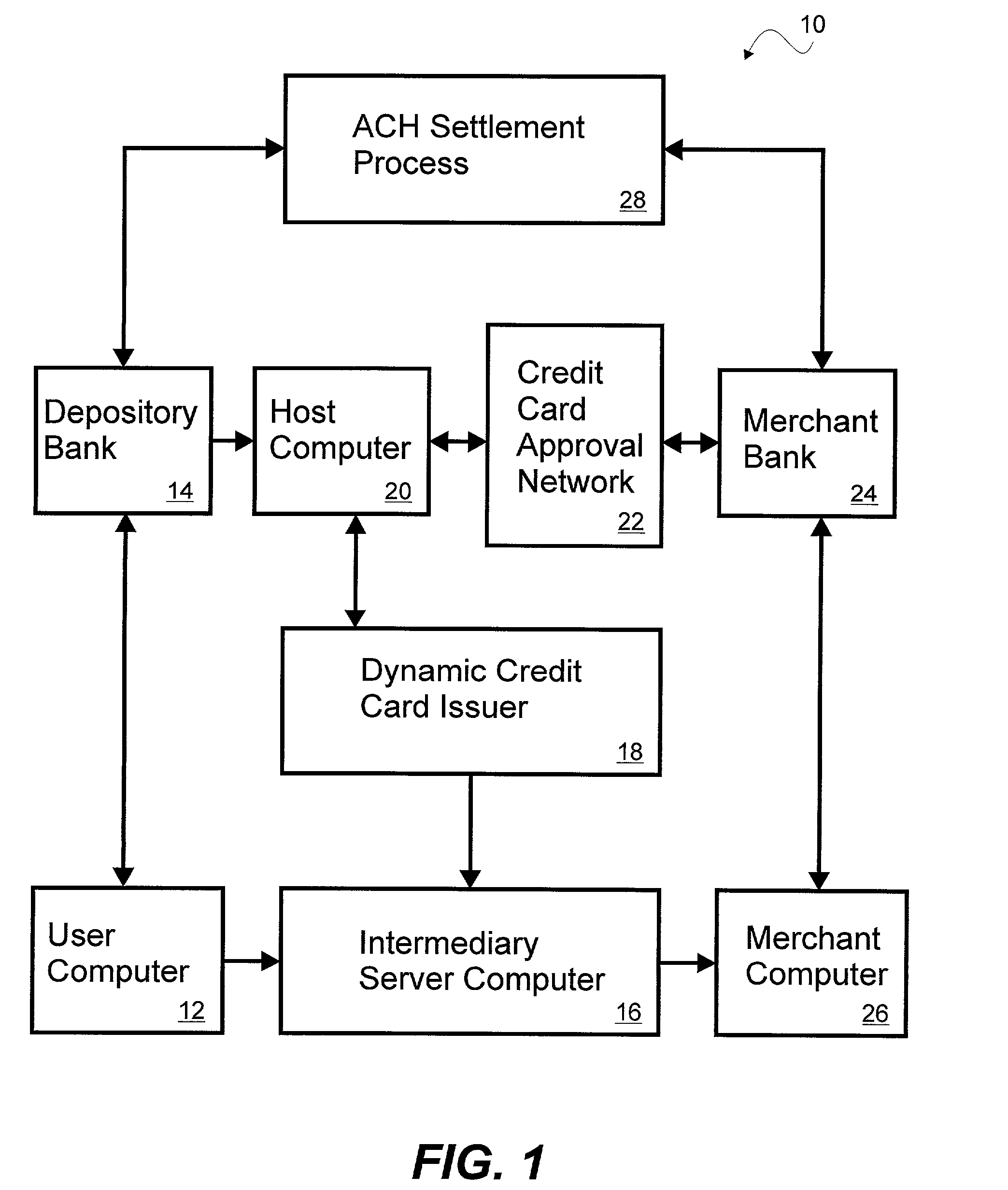
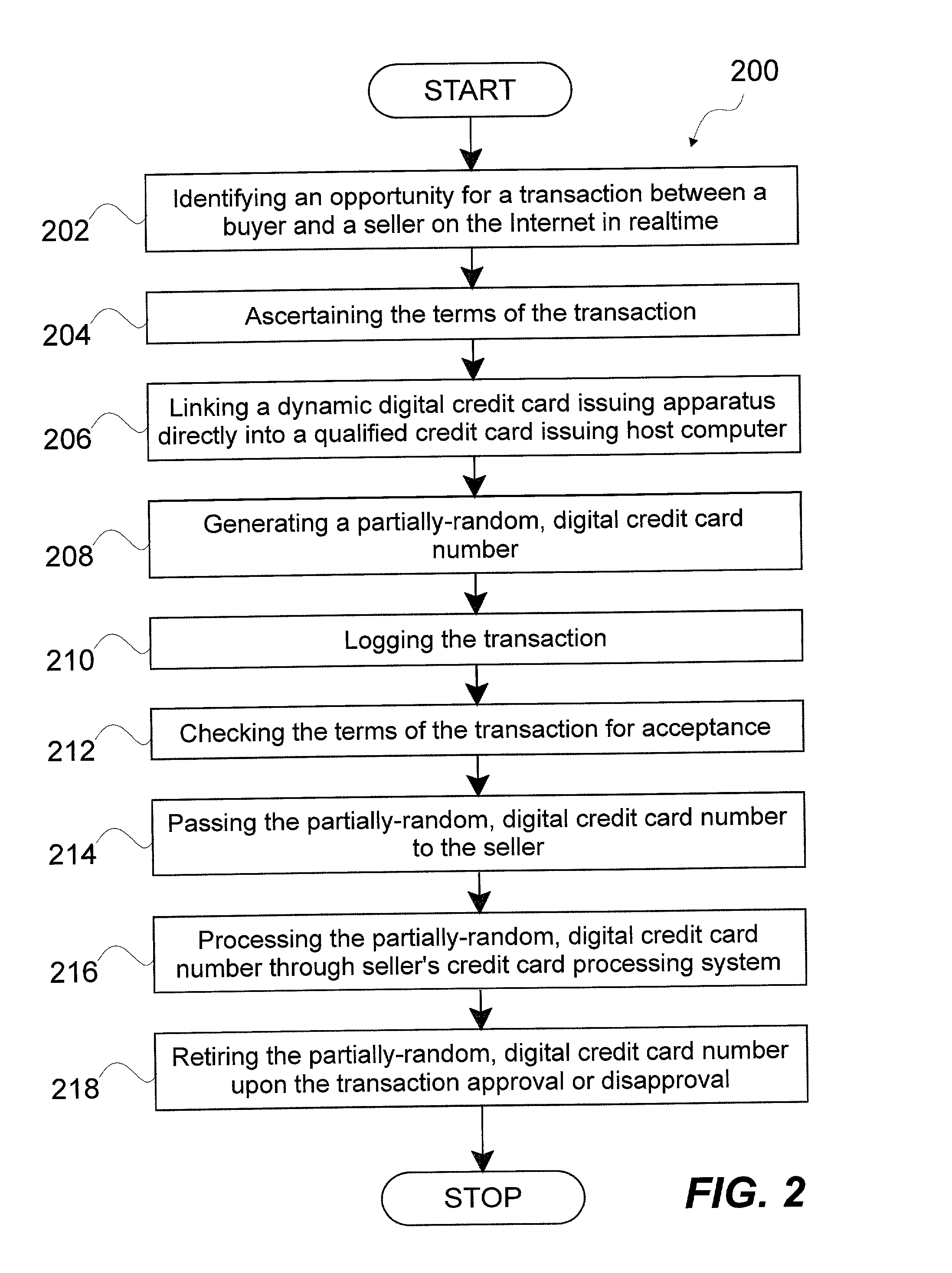
System and method for dynamically issuing and processing transaction specific digital credit or debit cards
A system and method of dynamically issuing credit card numbers and processing transactions using those credit card numbers is disclosed. A method according to the invention includes digitally recognizing a transaction opportunity on the Internet in real-time, recognizing the terms of the transaction, linking a dynamic digital credit card issuing apparatus directly into a qualified credit card issuing host, generating a partially random digital credit card number, logging the transaction, checking the terms of the transaction for acceptance, passing the dynamically issued digital credit card number to the merchant, processing the digital credit card number through the merchant's card processing system, receiving the transaction approval request, participating in credit card validity checking systems, processing the approval request in real-time, sending the requesting party a legitimate authorization code, and retiring the digital credit card number immediately upon transaction approval or disapproval. A system according to the invention implements the method of the invention.
Owner:ORANGATANGO
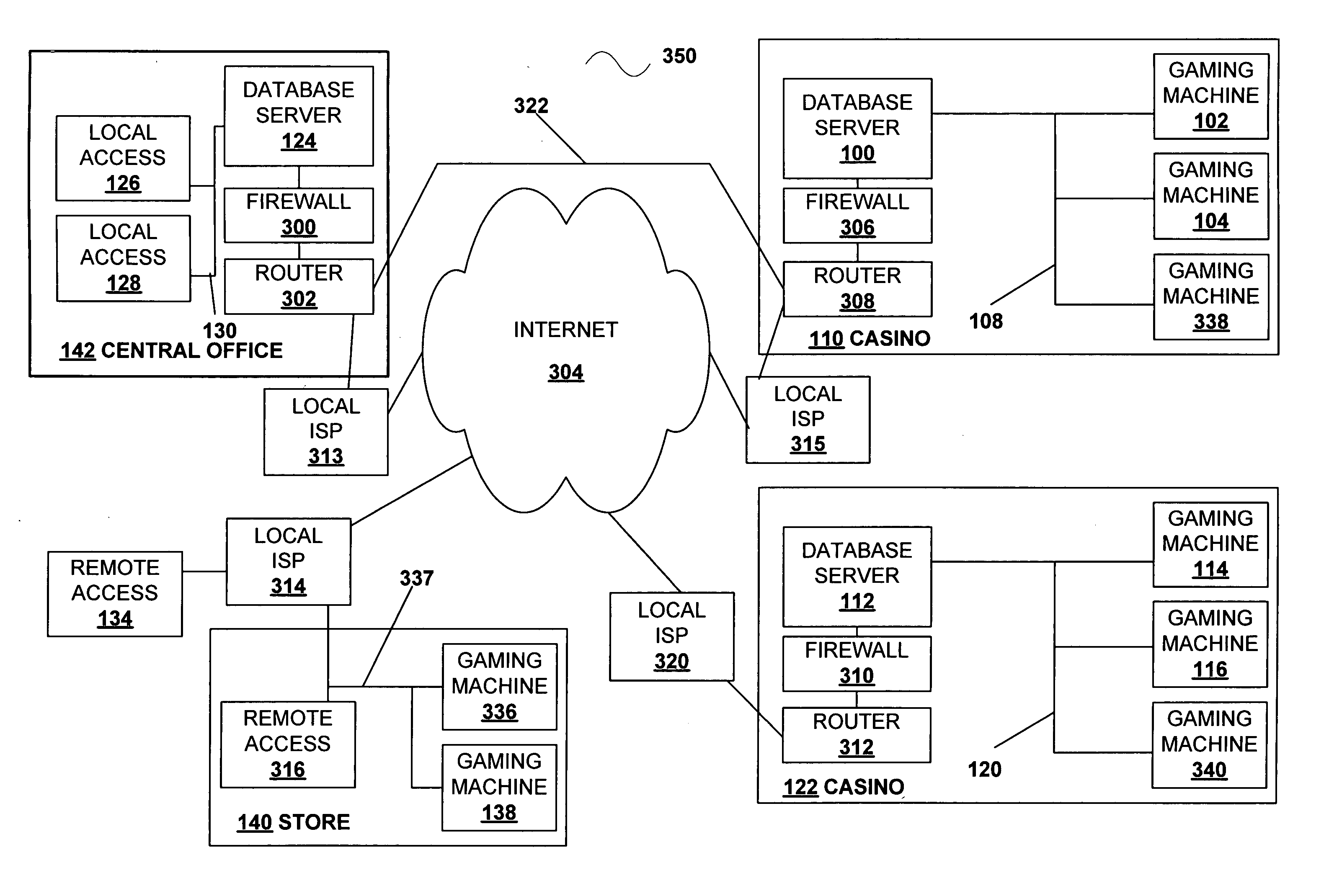
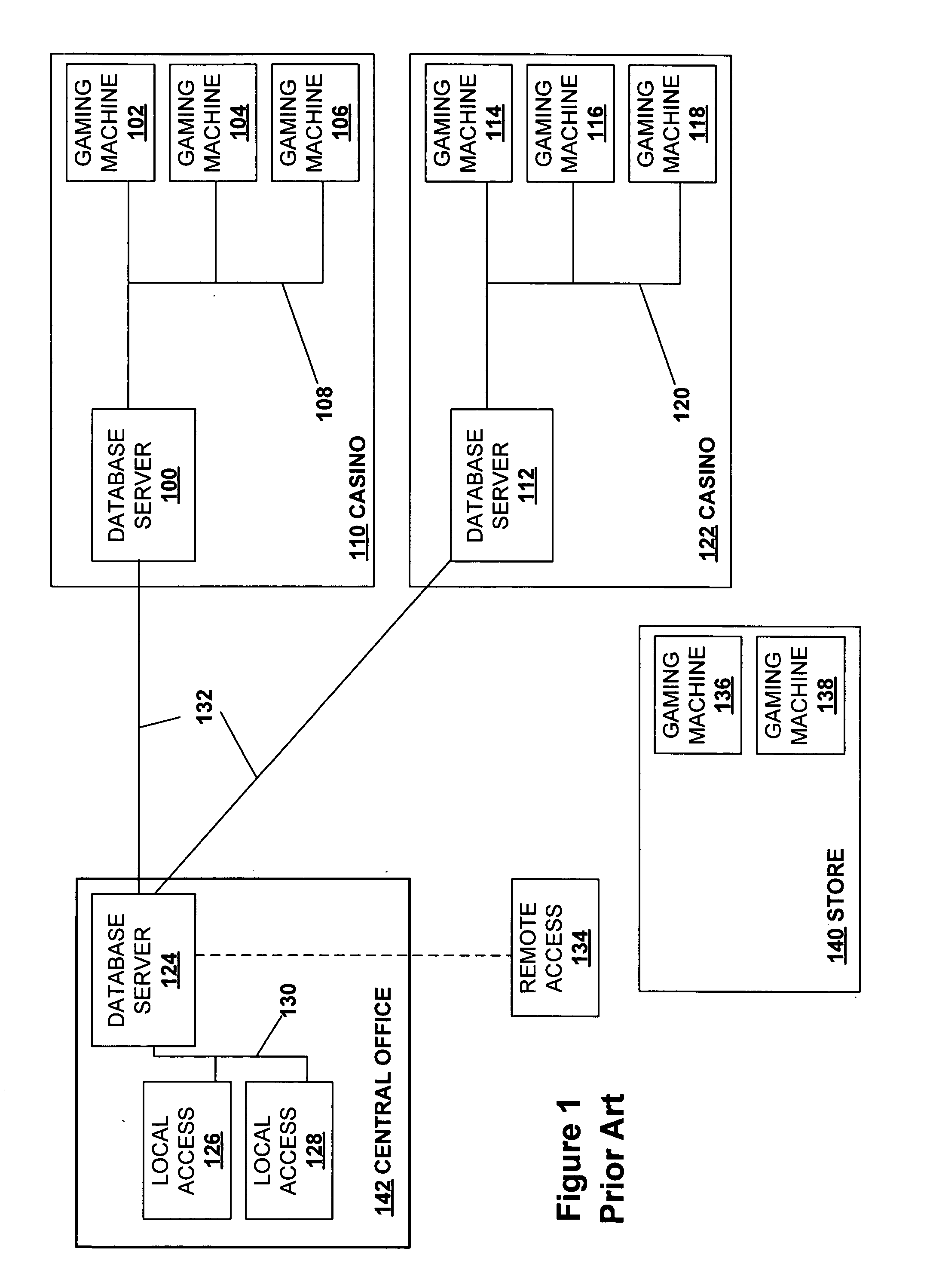
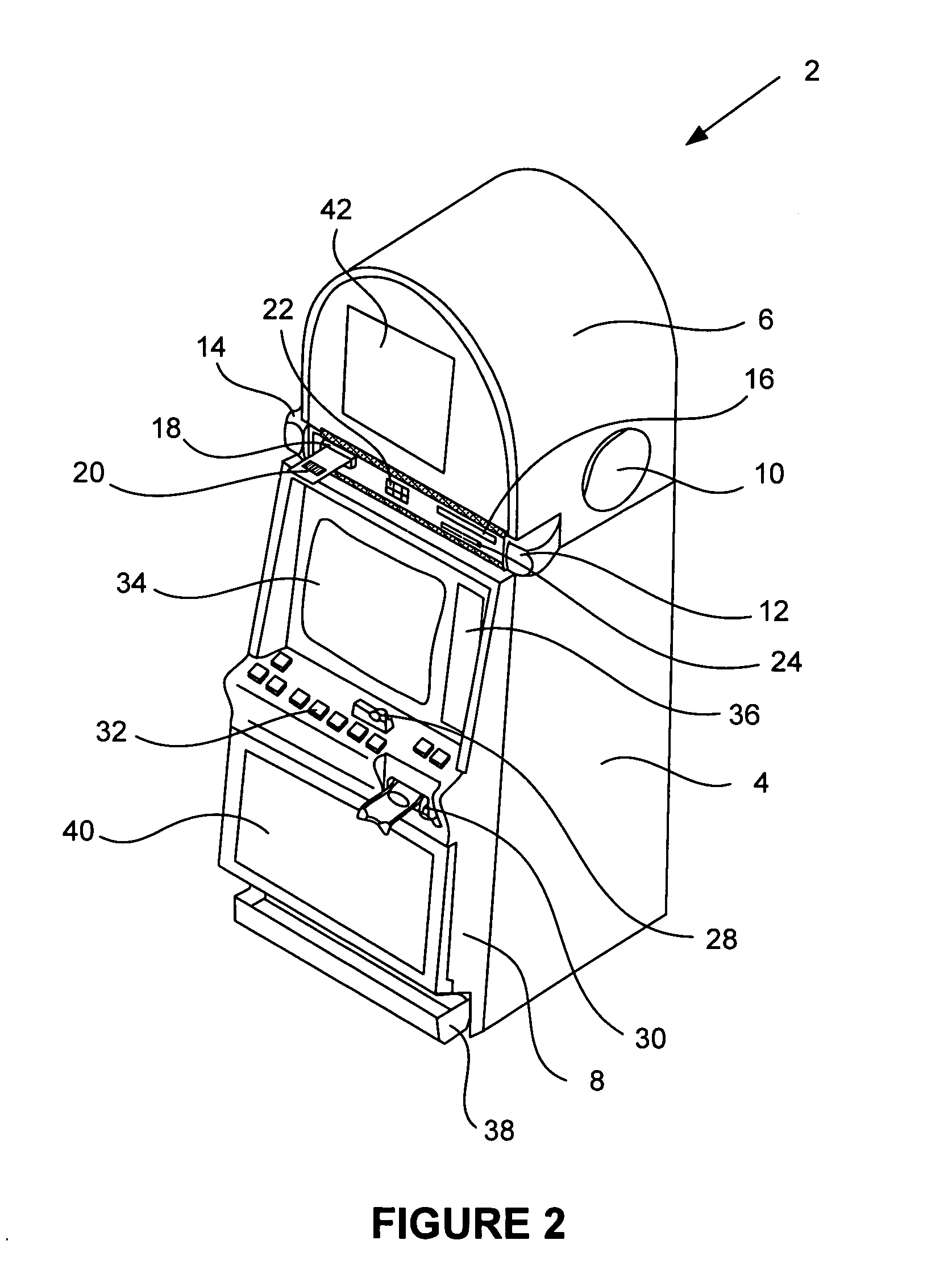
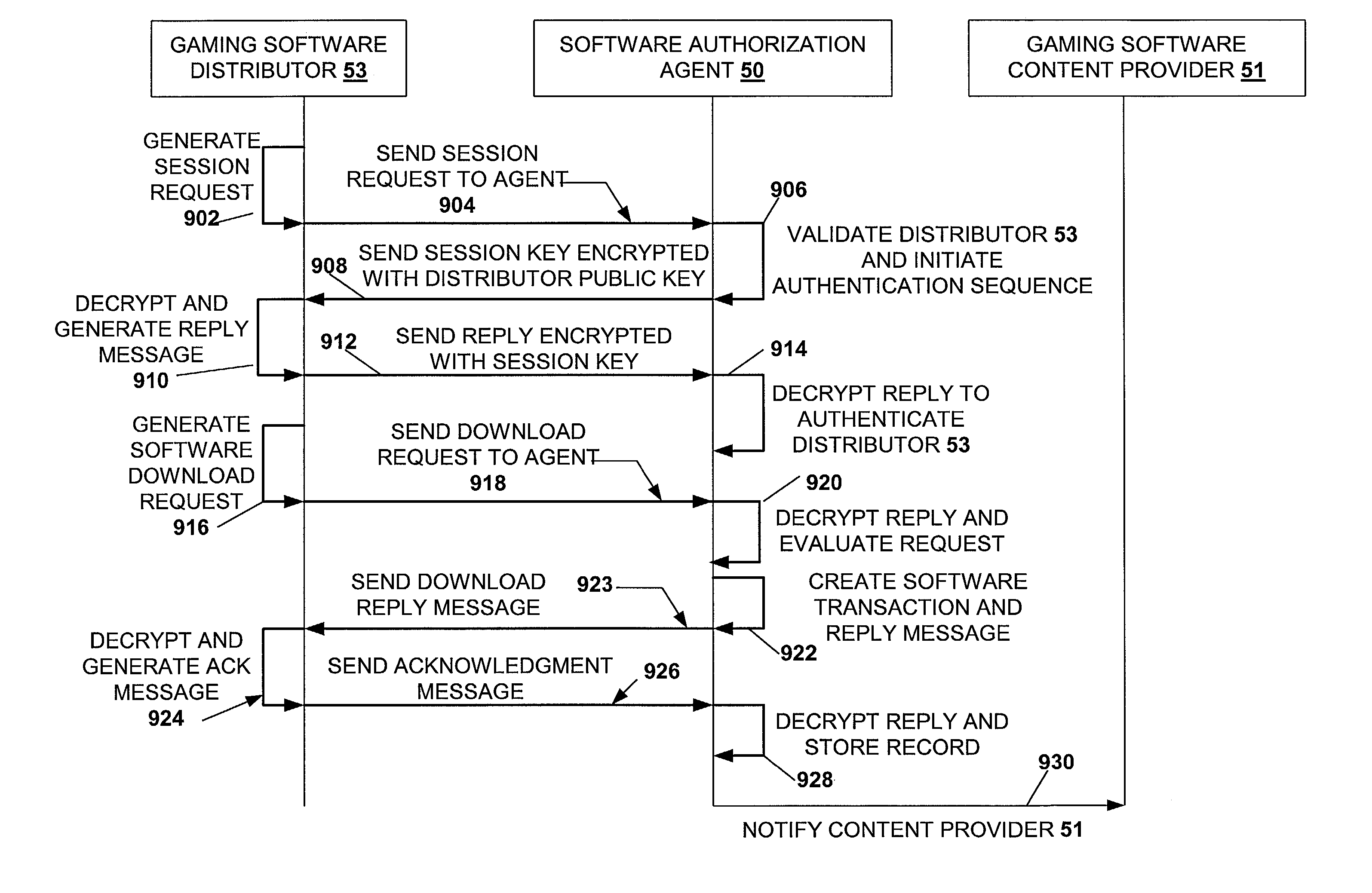
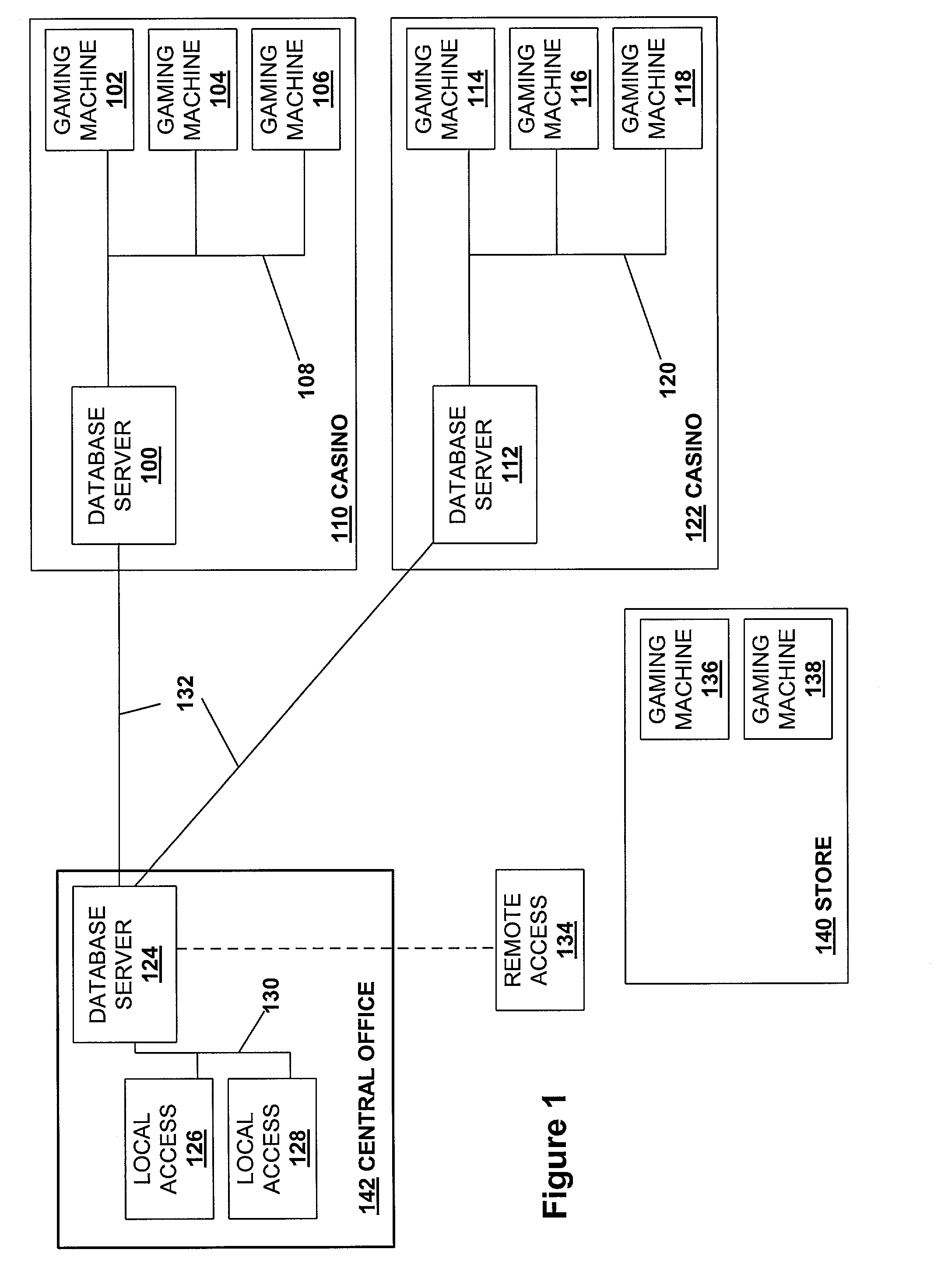
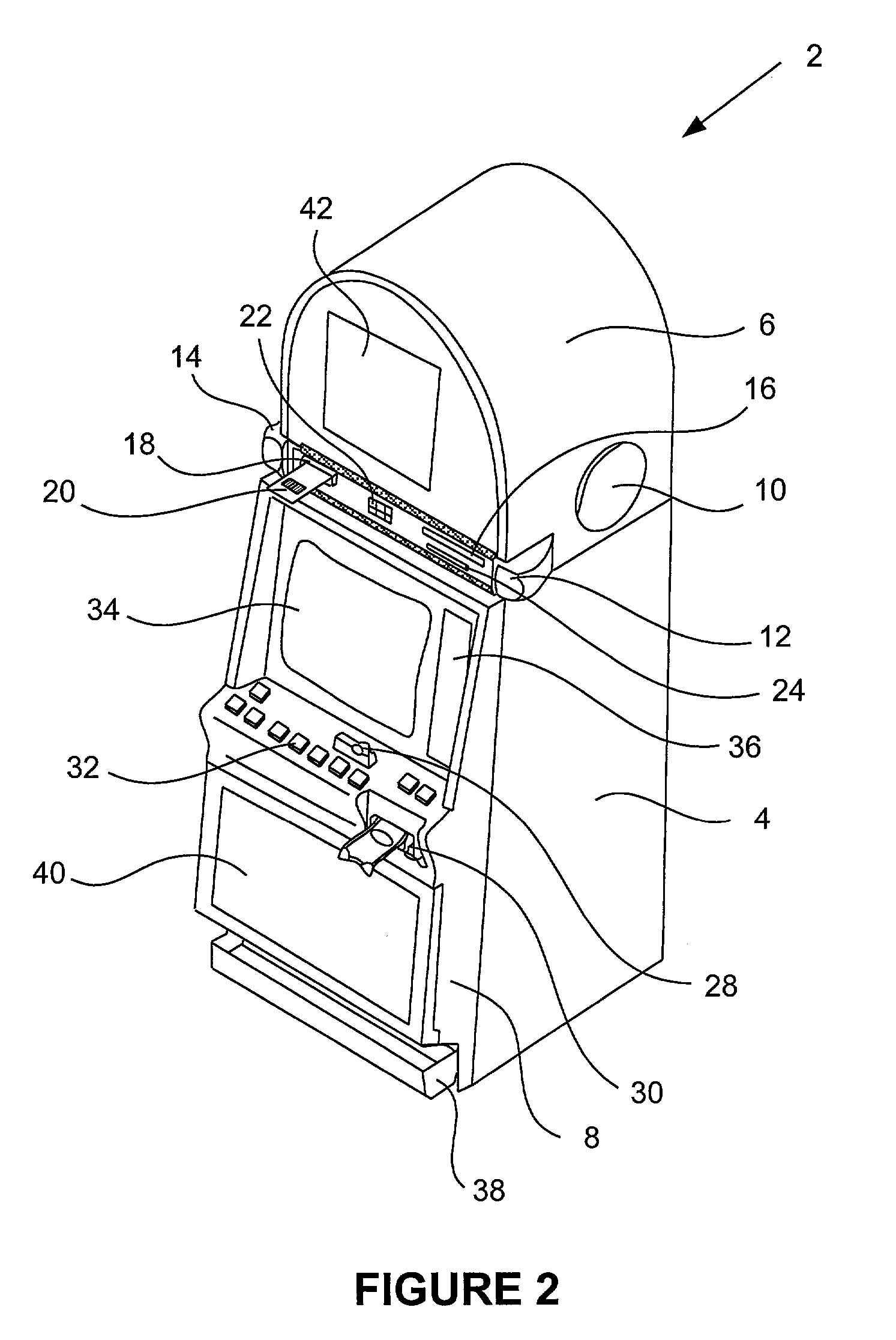
Secured virtual network in a gaming environment
InactiveUS20050192099A1Key distribution for secure communicationApparatus for meter-controlled dispensingSecure communicationThe Internet
A disclosed gaming machine may securely communicate with devices over a public network such as the Internet. The gaming machine utilizes a combination of symmetric and asymmetric encryption that allows a single gaming machine to securely communicate with a remote server using a public network. The secure communication methods may be used to transfer gaming software and gaming information between two gaming devices, such as between a game server and a gaming machine. For regulatory and tracking purposes, the transfer of gaming software between the two gaming devices may be authorized and monitored by a software authorization agent.
Owner:IGT
Super-distribution of protected digital content
Briefly according to the present invention, a system, computer readable medium and method to deliver encrypted digital content to from a first system for playing the content to a second system for playing the content. The method on the first user system comprising the steps of: reading from a computer readable medium metadata which has previously been associated with the content; selecting from the metadata associated content to decrypt; establishing a secure connection with an authorization authority, such as a clearinghouse, for decrypting the key used to encrypt the content; receiving a secure container containing the decrypting key for decrypting at least part of the previously encrypted content as permitted; decrypting the content and then encrypting the content with a new encryption key that is generated locally on the end user system.
Owner:WISTRON CORP
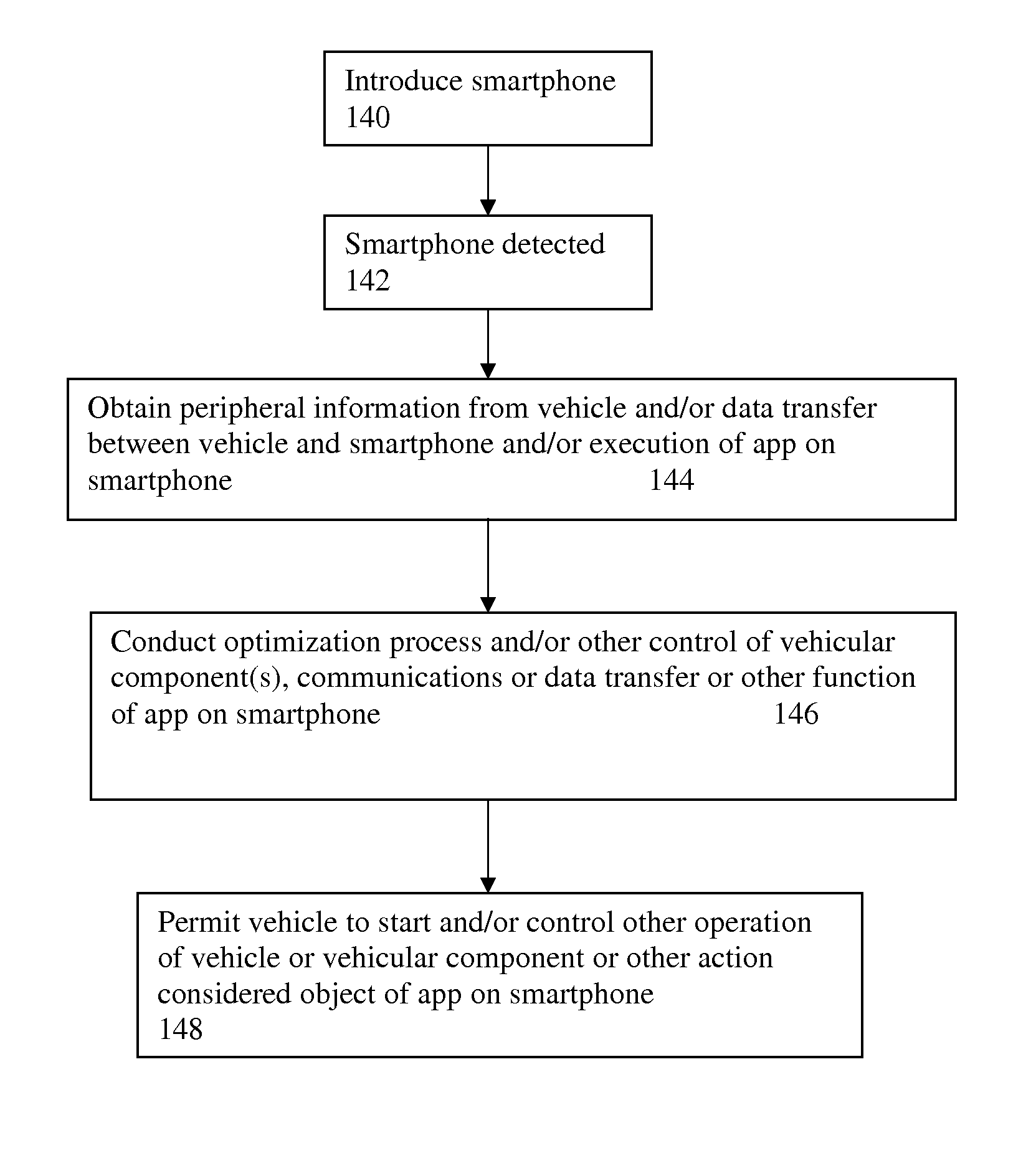
Smartphone-based vehicular interface
Method for enabling interaction with a vehicle including coupling a smartphone to the vehicle via a coupling element whereby the smartphone is removable from the coupling element and thus removable from the vehicle, and transferring data between the smartphone and the vehicle while the smartphone is coupled to the vehicle via the coupling element. The data transfer enables a large number of operations to be performed when the smartphone is coupled to the vehicle, including vehicle ignition authorization, accident prediction, collision avoidance, vehicular diagnostics and prognostics, remote communication capabilities, and optimization of emergency response personnel.
Owner:INTELLIGENT TECH INT
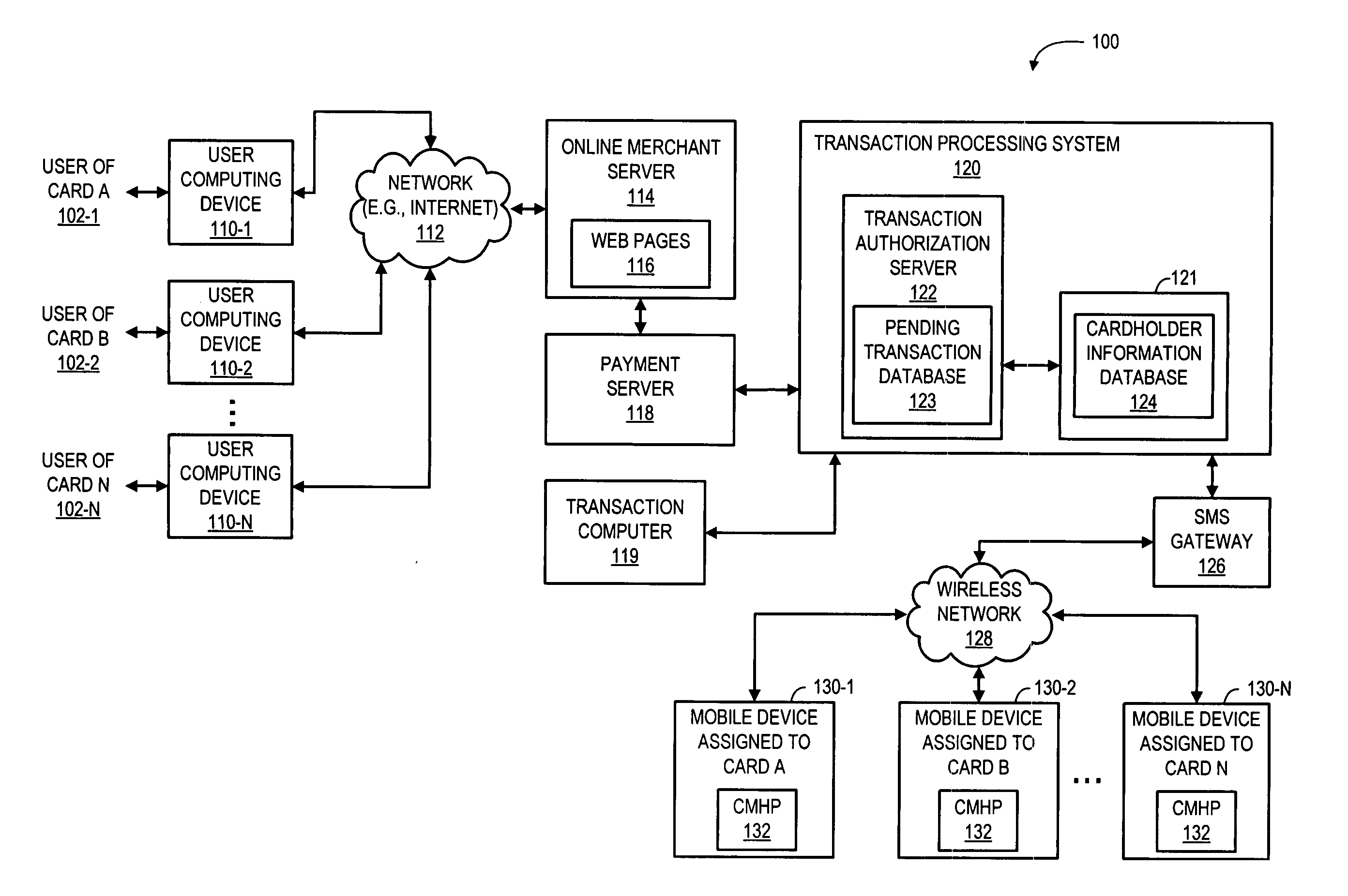
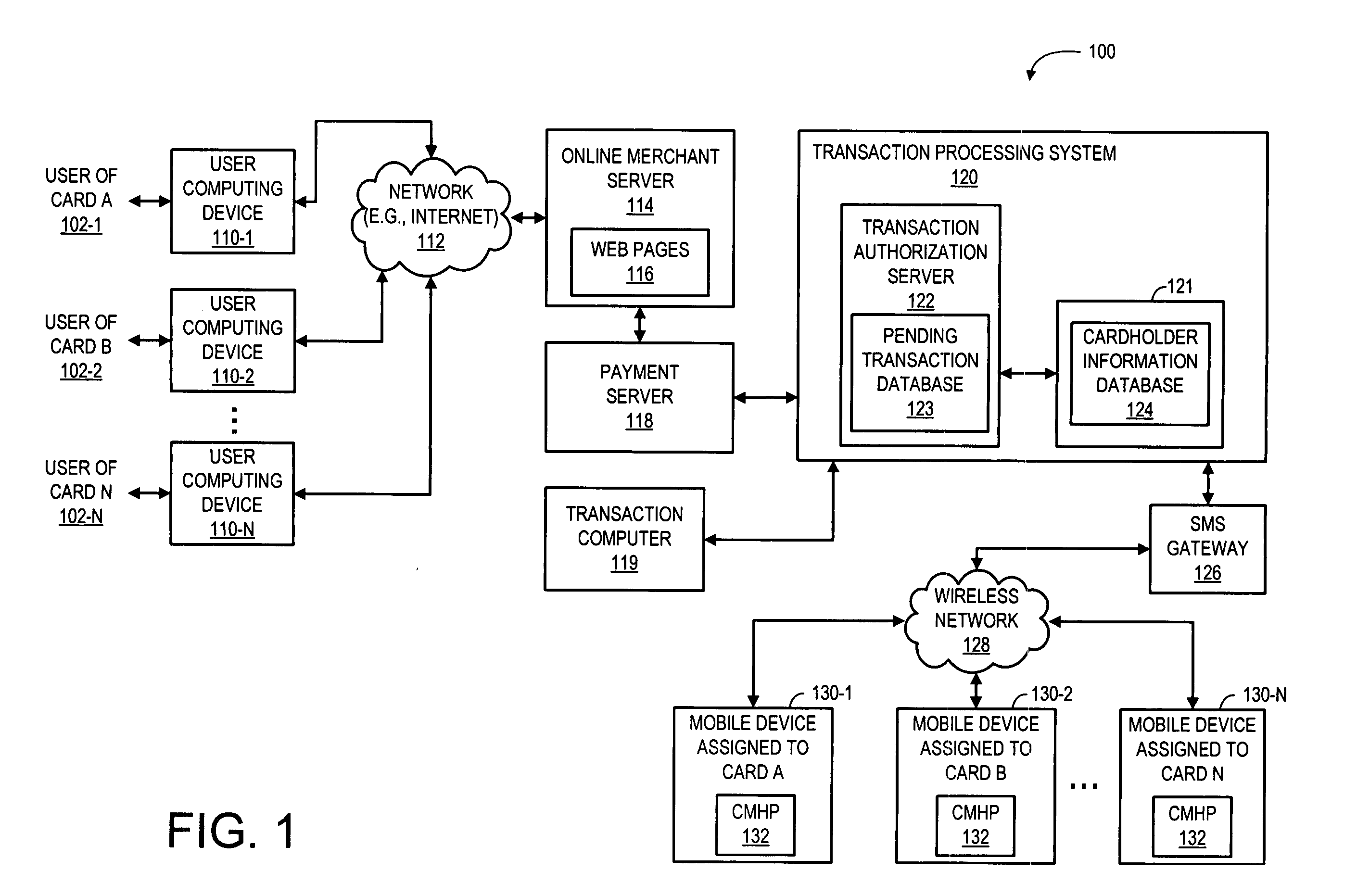
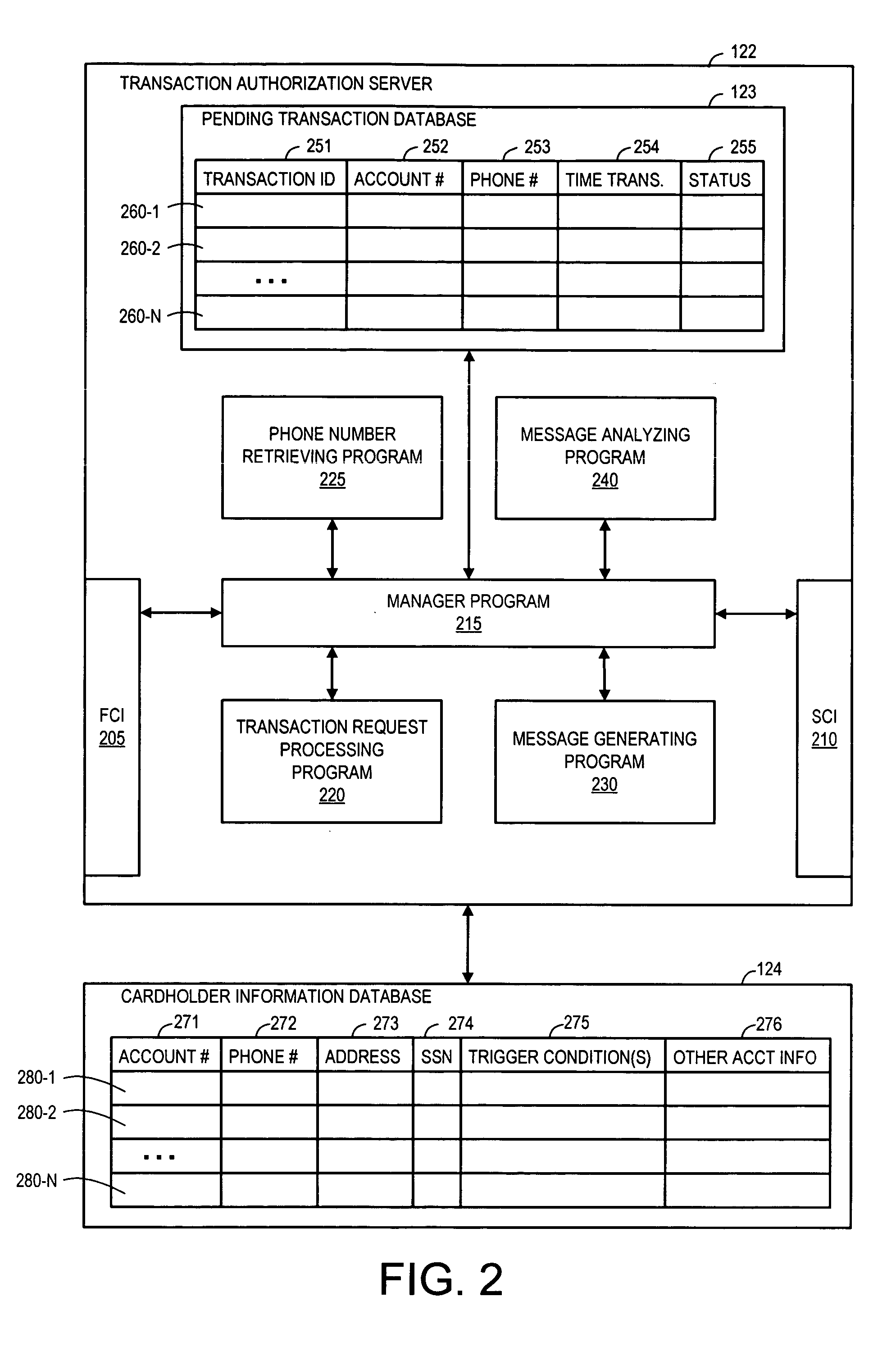
Method and system for providing transaction notification and mobile reply authorization
A system and a corresponding method are described for providing a notification of a pending transaction request and obtaining an authorization from a cardholder. The system maintains a database of account records, each of the account records including a phone number of a mobile device assigned to receive authorization request messages for the respective account. When a transaction request is received, the system determines a phone number of a mobile device assigned to receive authorization request messages for the account requesting the transaction by searching the database. The system generates and transmits an authorization request message to the phone number of the mobile device assigned to the account requesting the transaction. In response to the authorization request message, a reply message is returned from the mobile device, which explicitly indicates if a user of the mobile device approves or denies the transaction.
Owner:KIM MIKE
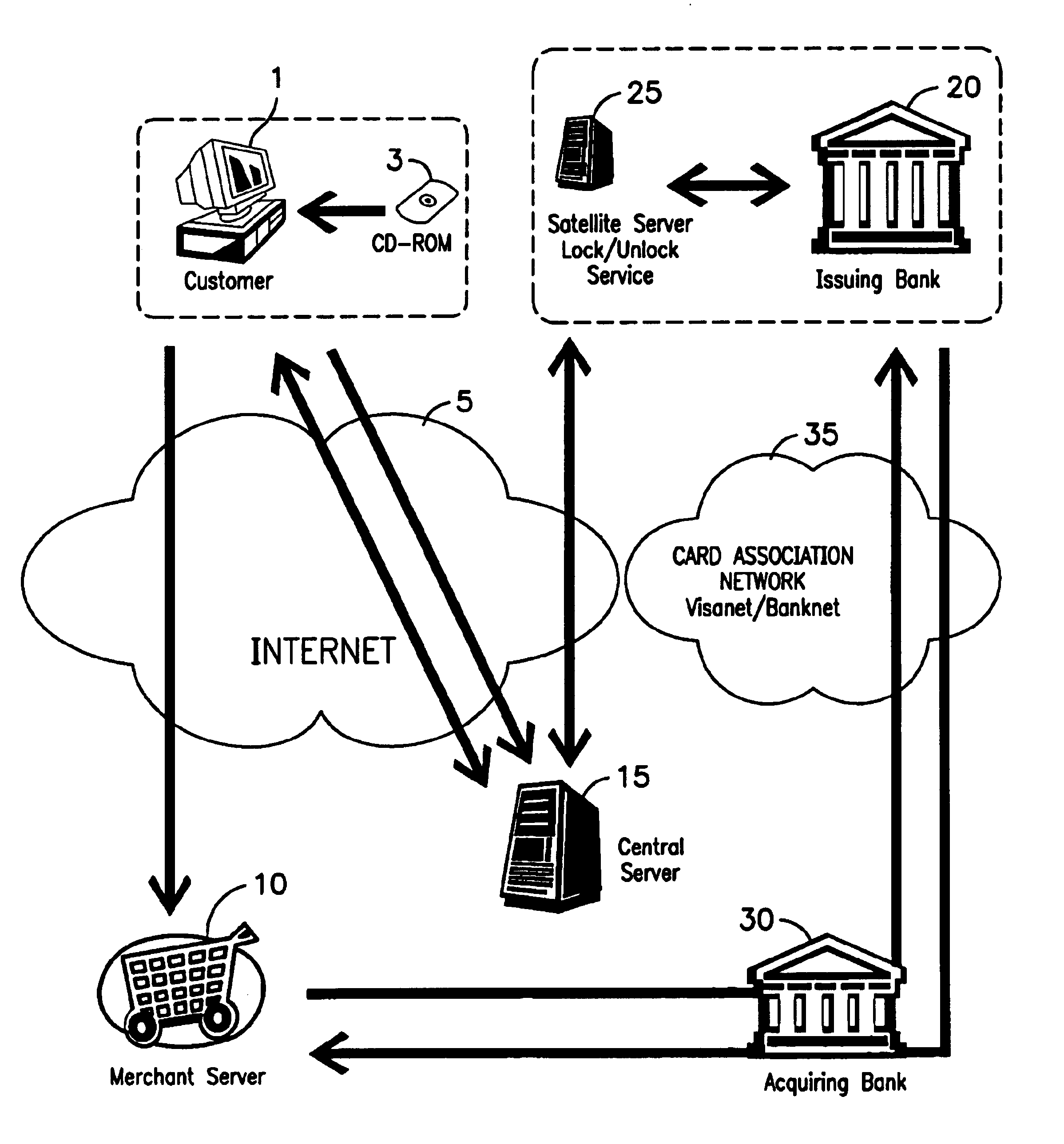
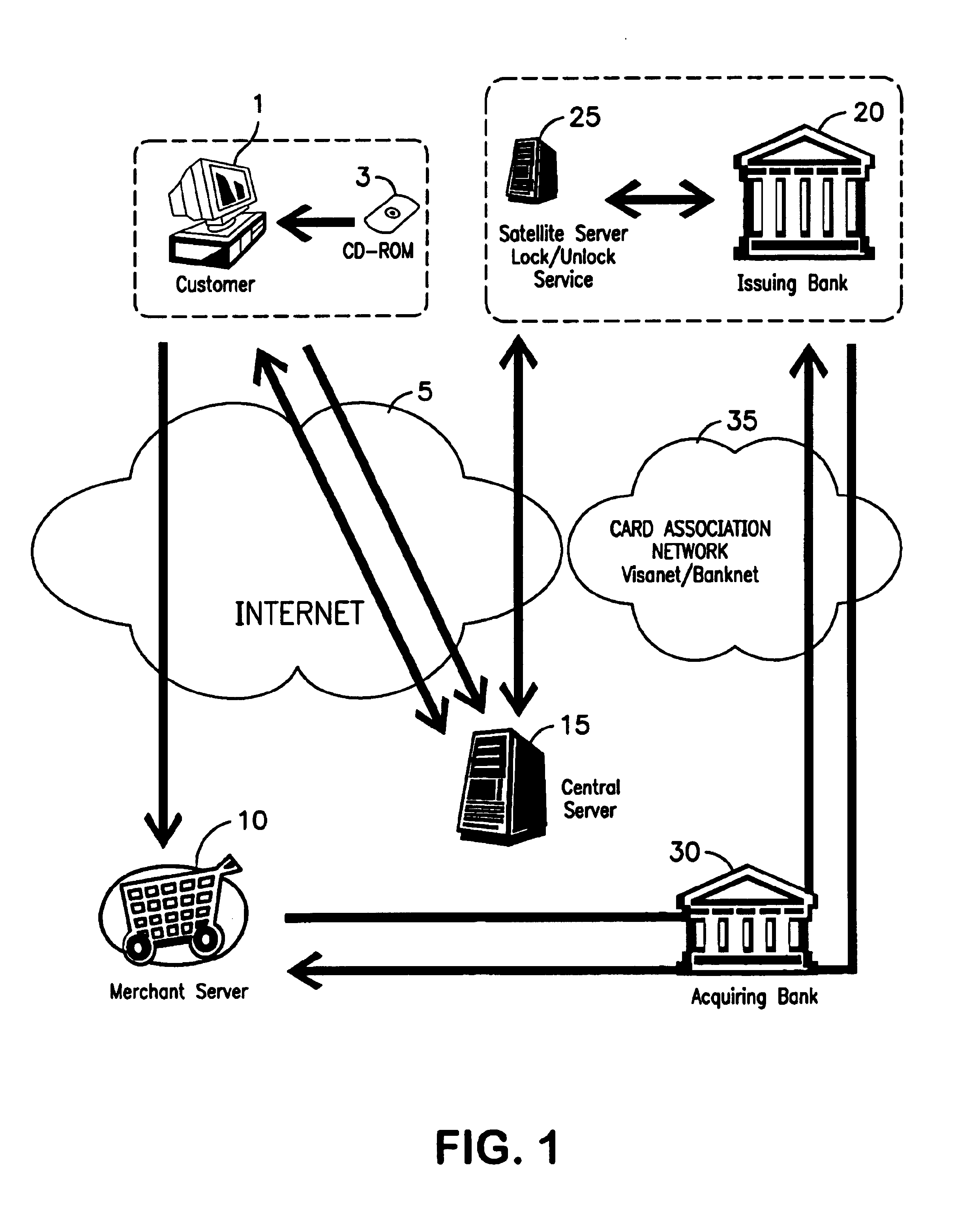
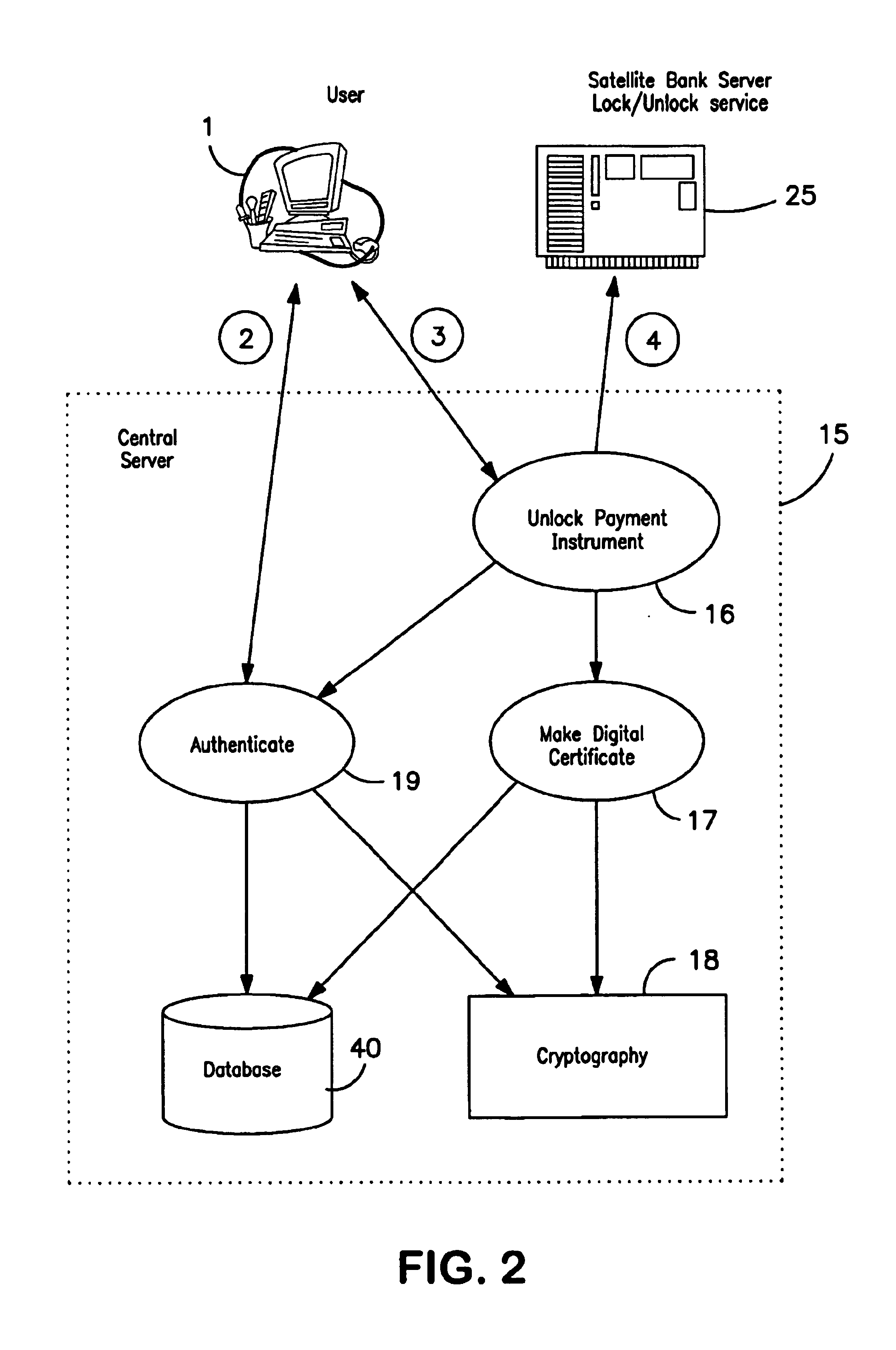
Payment instrument authorization technique
InactiveUS6931382B2Strong authenticationPayment circuitsSpecial data processing applicationsThird partyAuthorization
A method is provided for protecting a payment instrument in non-face-to-face transactions. The payment instrument is issued by an issuing entity and associated with an authorized instrument holder. The authorized instrument holder is subject to authentication by a trusted third party with whom the payment instrument holder has previously registered. The method includes: the authorized instrument holder communicating with the issuing entity to block, on a default basis, authorization of the payment instrument for non-face-to-face transactions unless authorized to unblock the payment instrument by the trusted third party; prior to a non-face-to-face transaction, the authorized instrument holder communicating with the trusted third party to subject him or herself to authentication and to request that the payment instrument be unblocked; and the trusted third party authenticating the authorized instrument holder, and if the authentication result is positive, communicating with the issuing entity to request unblocking of the payment instrument.
Owner:KIOBA PROCESSING LLC
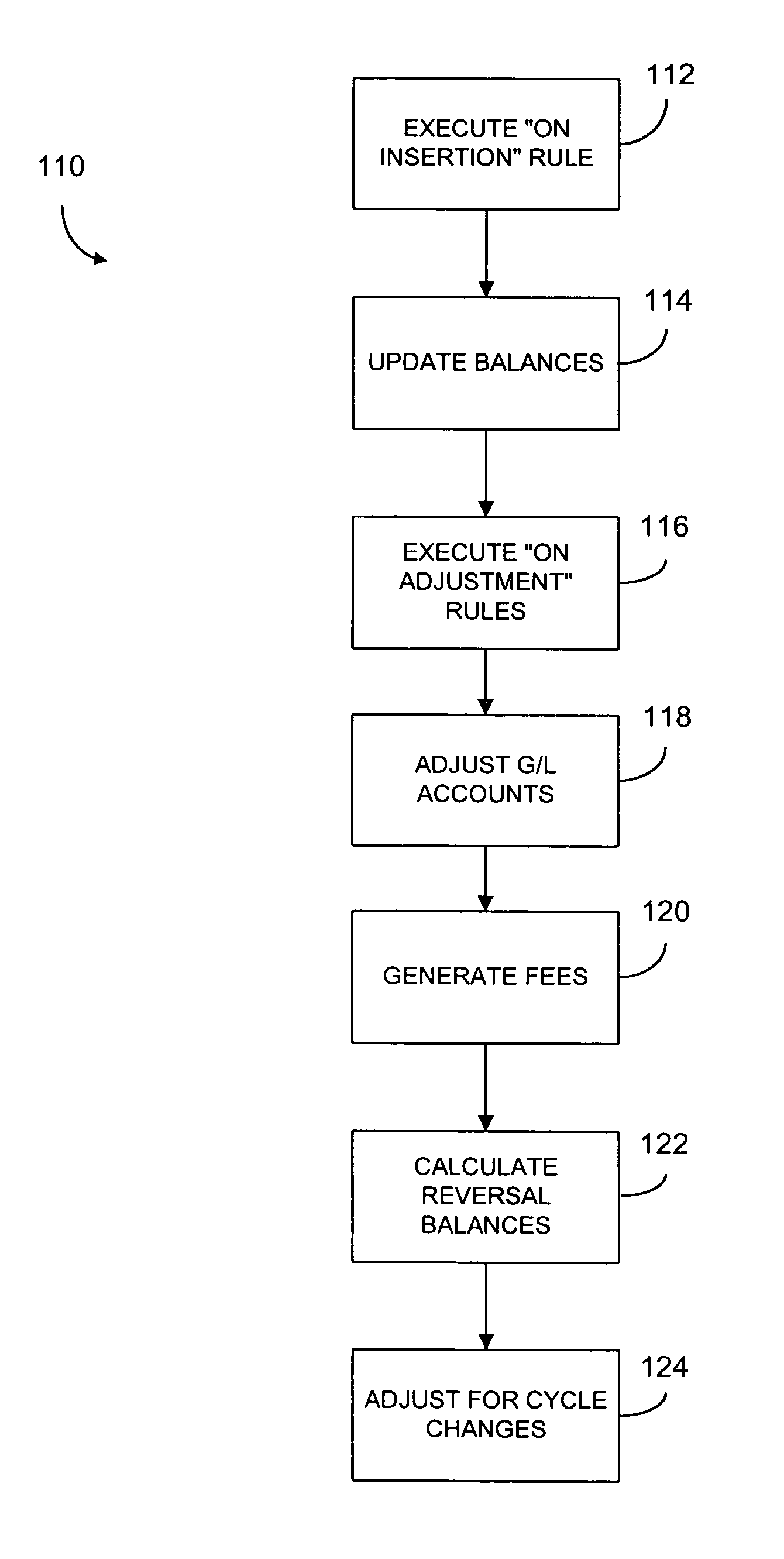
Methods and systems for managing financial accounts
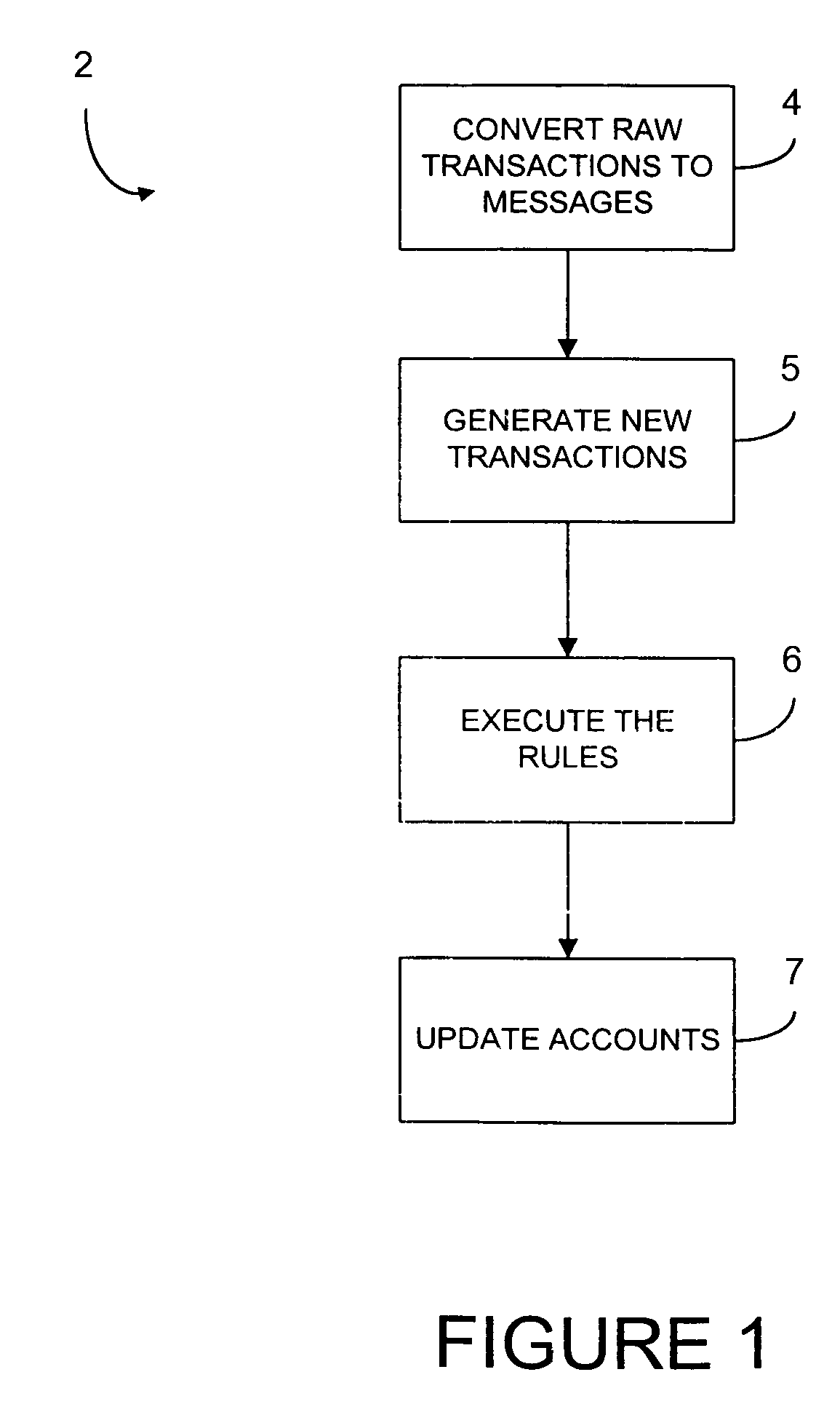
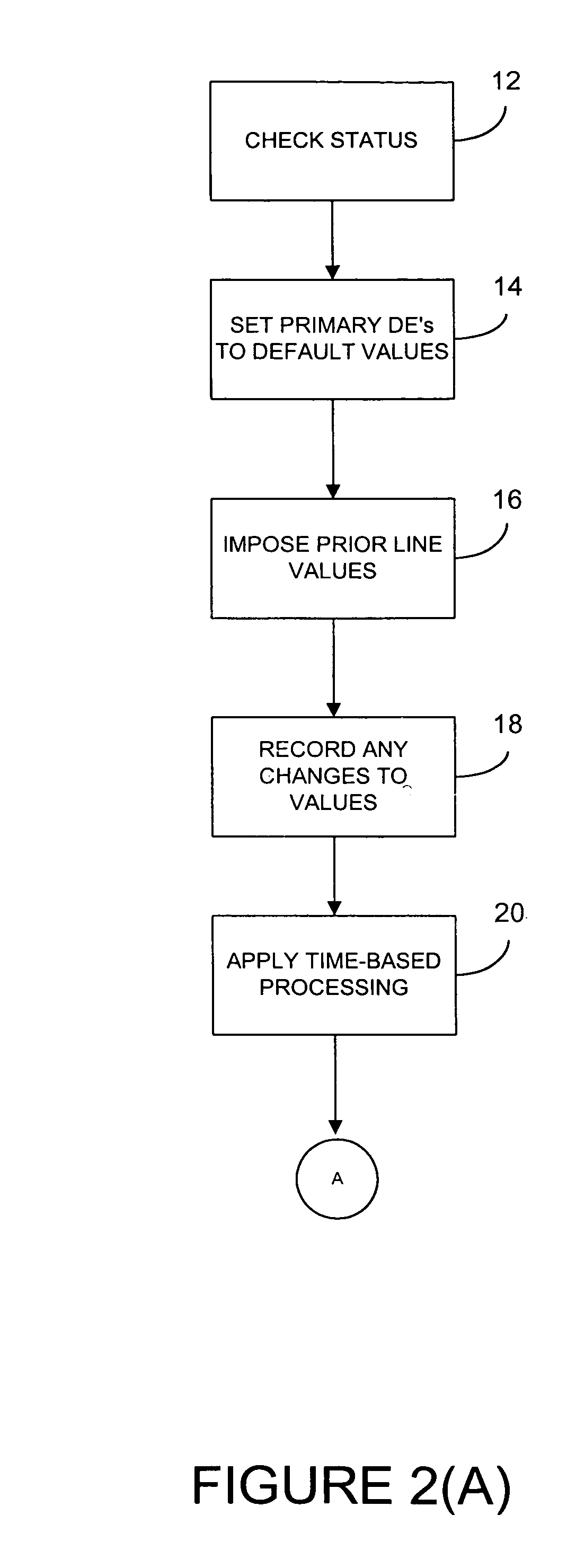
InactiveUS7117172B1Useful managingReduce in quantityComplete banking machinesFinanceSource codeParameter control
Processing systems and methods receive events, such as a transaction to an account, and converts the events into messages. Each message then invokes one or more rules which are executed by a rules engine. The execution of these rules may invoke the execution of additional rules. After all rules have executed, the account associated with the event is updated, such as by projecting the account. The rules have their parameters defined in a repository so that the parameters can be easily changed without any need to recompile. The processing systems receive authorizations and other transactions and runs in real-time as transactions arrive. As a result, balances are updated continuously and accounts are read and updated only when there is activity. Hierarchy is user configurable, including multiple hierarchy to any depth. System operations are controlled by rules and their parameters and most modifications can be accomplished without access to source code.
Owner:CORECARD SOFTWARE
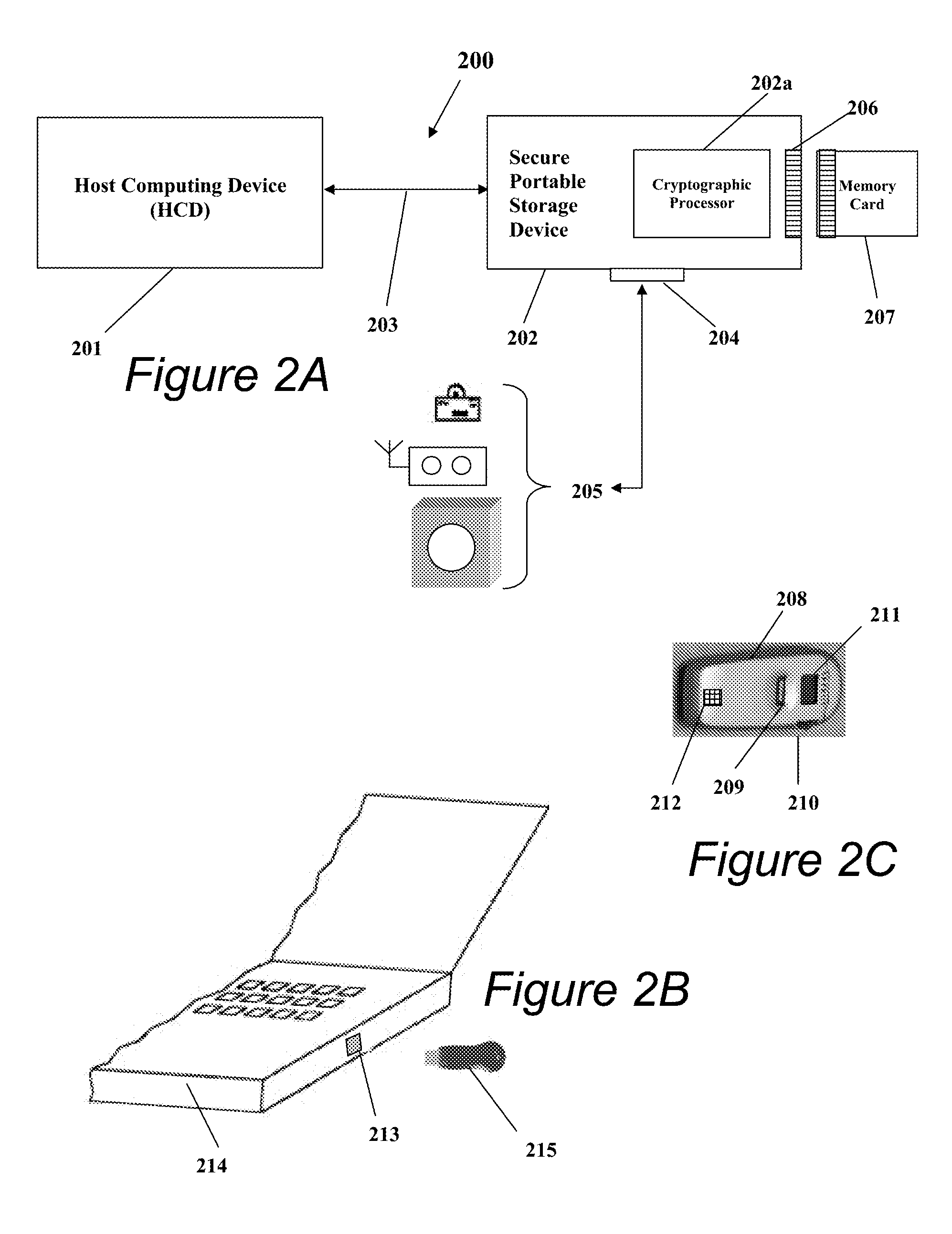
Portable Data Encryption Device with Configurable Security Functionality and Method for File Encryption
InactiveUS20080263363A1Mitigates and eliminates vulnerabilityUser identity/authority verificationInternal/peripheral component protectionComputer hardwarePlaintext
A portable encryption device with logon access controlled by an encryption key, with an on board cryptographic processor for reconstituting the encryption key from a plurality of secrets generated by a secret sharing algorithm, optionally shrouded with external secrets using an invertible transform resistant to quantum computing attacks. Another embodiment provides file decryption controlled by a file encryption key, with the on board cryptographic processor reconstituting the file encryption key from a version of the file encryption key which has been shrouded with a network authorization code. A method for encryption of a plaintext file by hashing, compressing, and encrypting the plaintext file, hashing the ciphertext, hashing the plaintext hash and the ciphertext hash, and sealing the ciphertext together with the resulting hash. A portable encryption device for performing the method is also disclosed.
Owner:SPYRUS
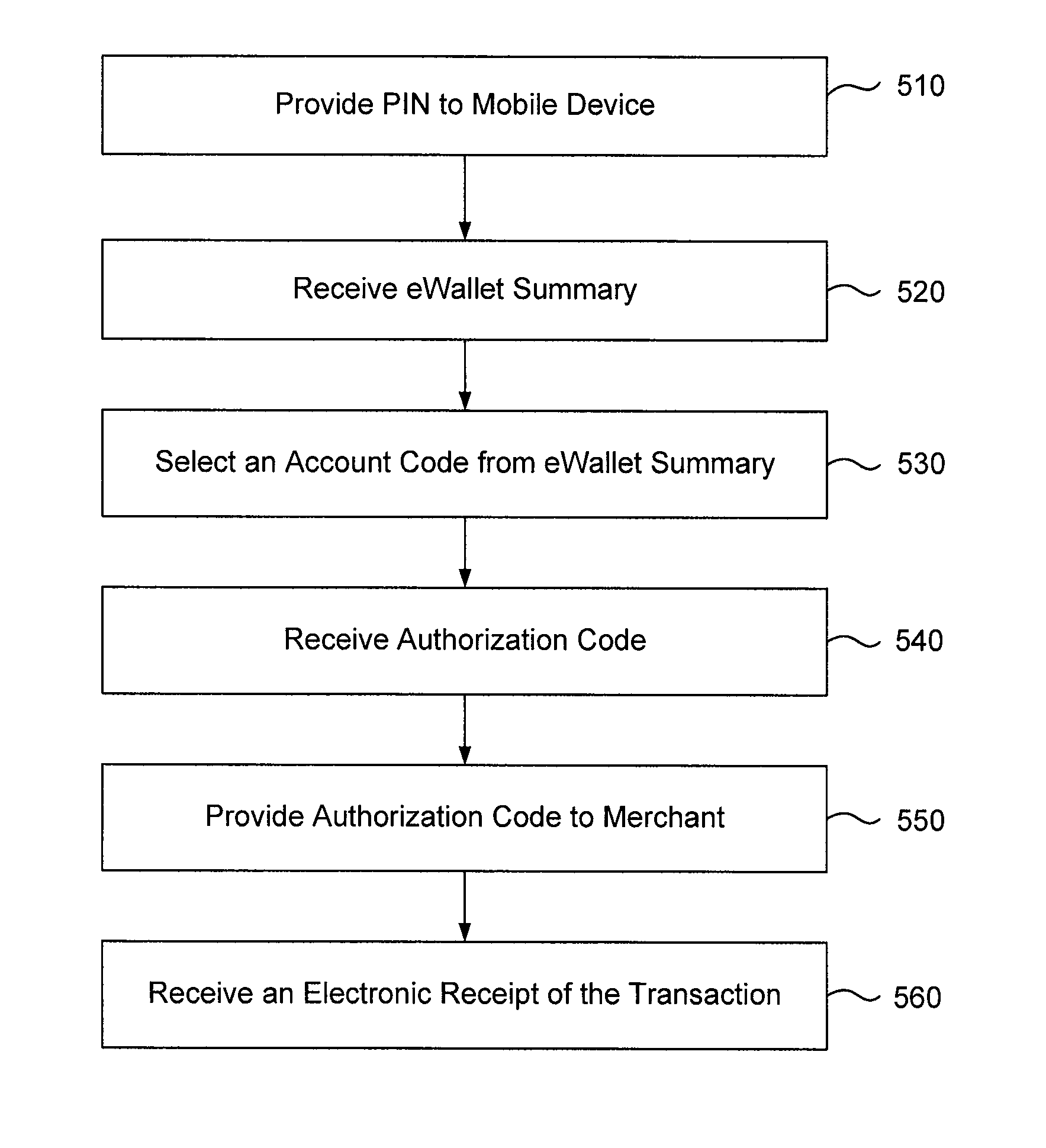
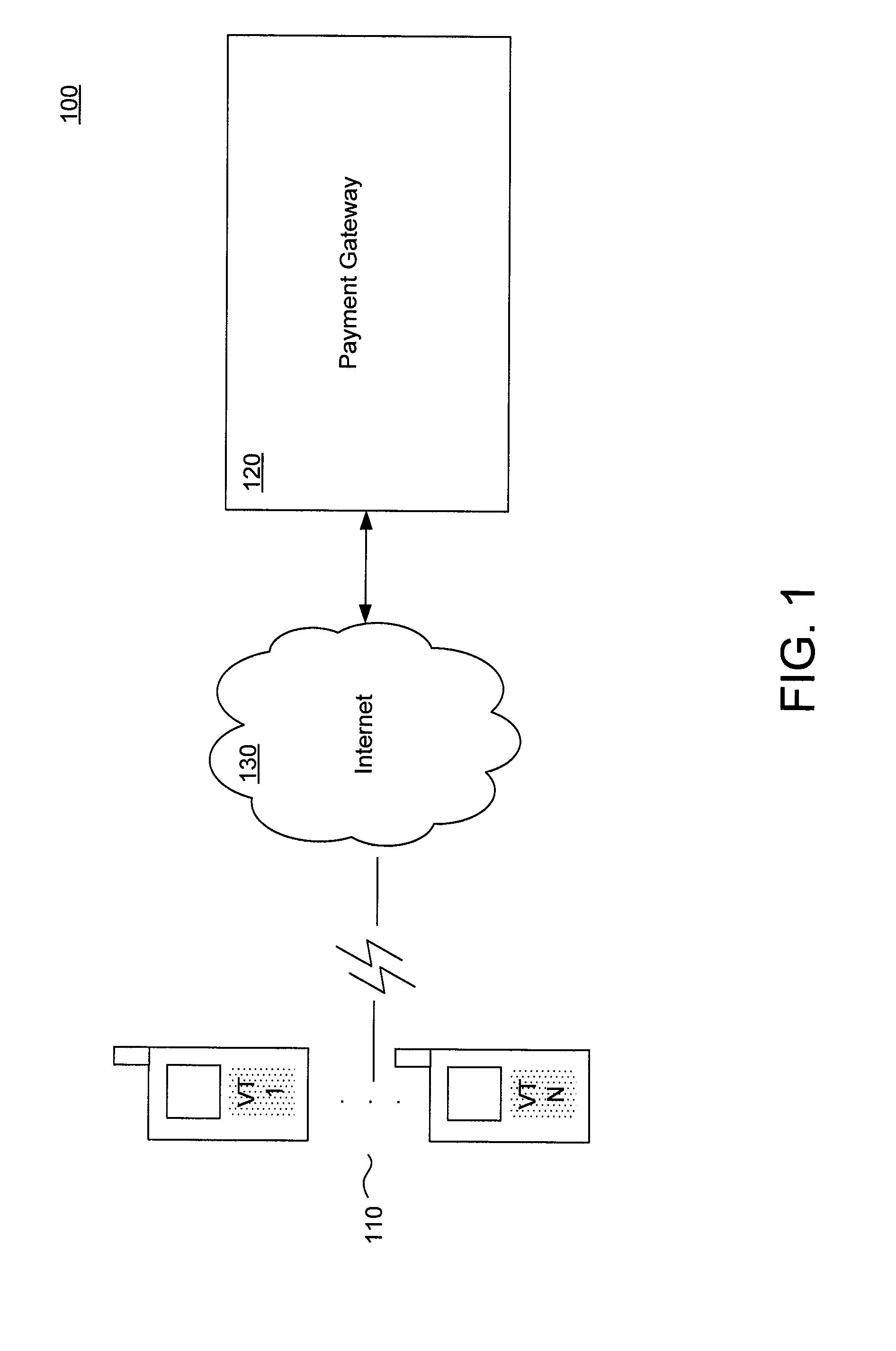
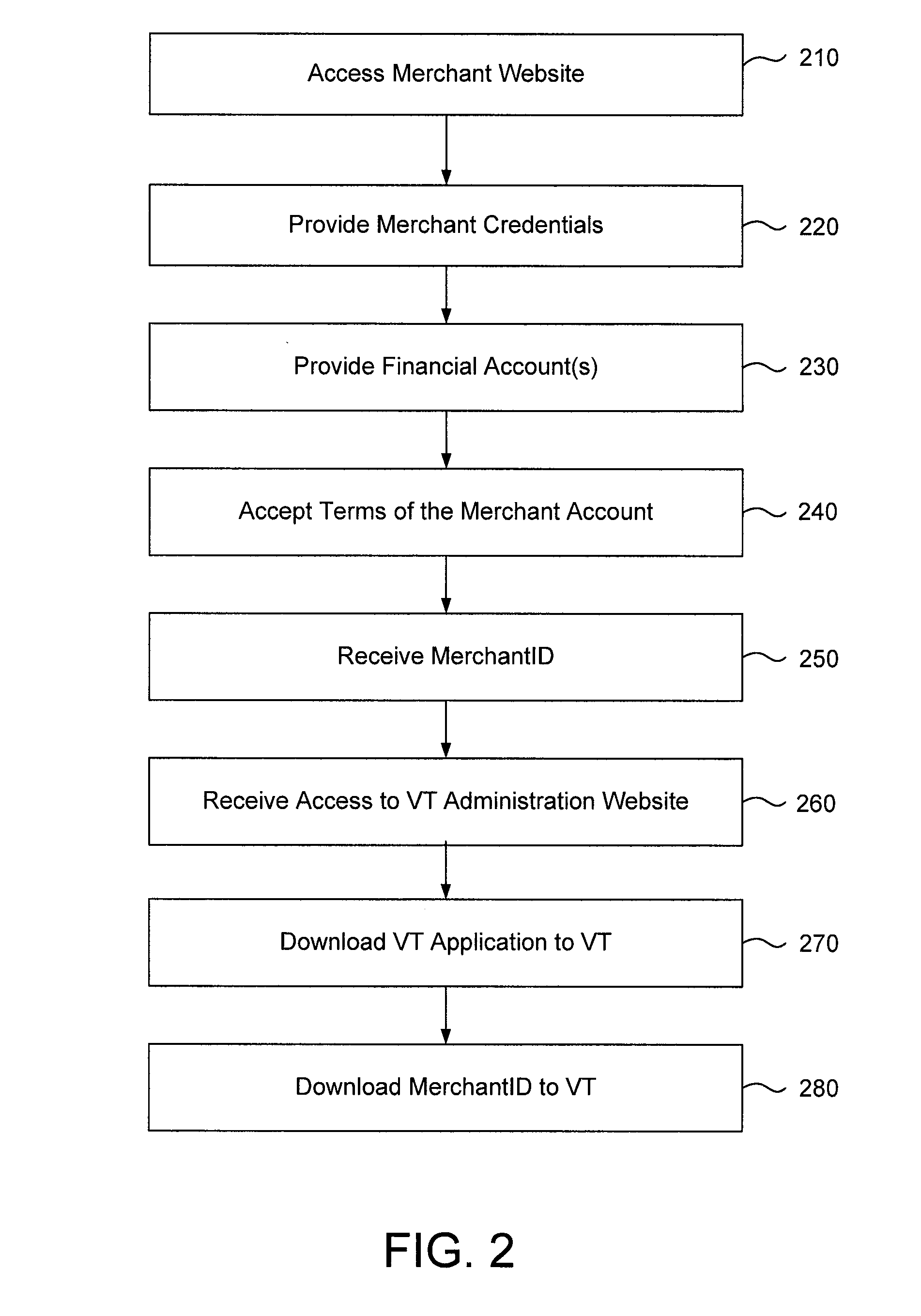
Method and System for Processing Secure Wireless Payment Transactions and for Providing a Virtual Terminal for Merchant Processing of Such Transactions
A system and method for processing a wireless electronic payment transaction is described. One embodiment comprises receiving a transaction authorization request for an electronic payment transaction from a customer, the authorization request submitted from a mobile communication device of the customer; authenticating the transaction authorization request; authorizing the transaction authorization request and transmitting an authorization code to the mobile communication device, the authorization code being communicated to a merchant from the customer; receiving a transaction approval request from the merchant, the transaction approval request submitted from a virtual terminal associated with the merchant, the virtual terminal being a wireless communication device having a point of sale processing application installed therein; authenticating the transaction approval request; approving the transaction approval request and transmitting an approval code to the virtual terminal; and generating and executing transaction settlement instructions between a financial account of the customer and a financial account of the merchant.
Owner:MOCAPAY
Secured virtual network in a gaming environment
InactiveUS7168089B2Digital data processing detailsUser identity/authority verificationSecure communicationThe Internet
A disclosed gaming machine may securely communicate with devices over a public network such as the Internet. The gaming machine utilizes a combination of symmetric and asymmetric encryption that allows a single gaming machine to securely communicate with a remote server using a public network. The secure communication methods may be used to transfer gaming software and gaming information between two gaming devices, such as between a game server and a gaming machine. For regulatory and tracking purposes, the transfer of gaming software between the two gaming devices may be authorized and monitored by a software authorization agent.
Owner:IGT
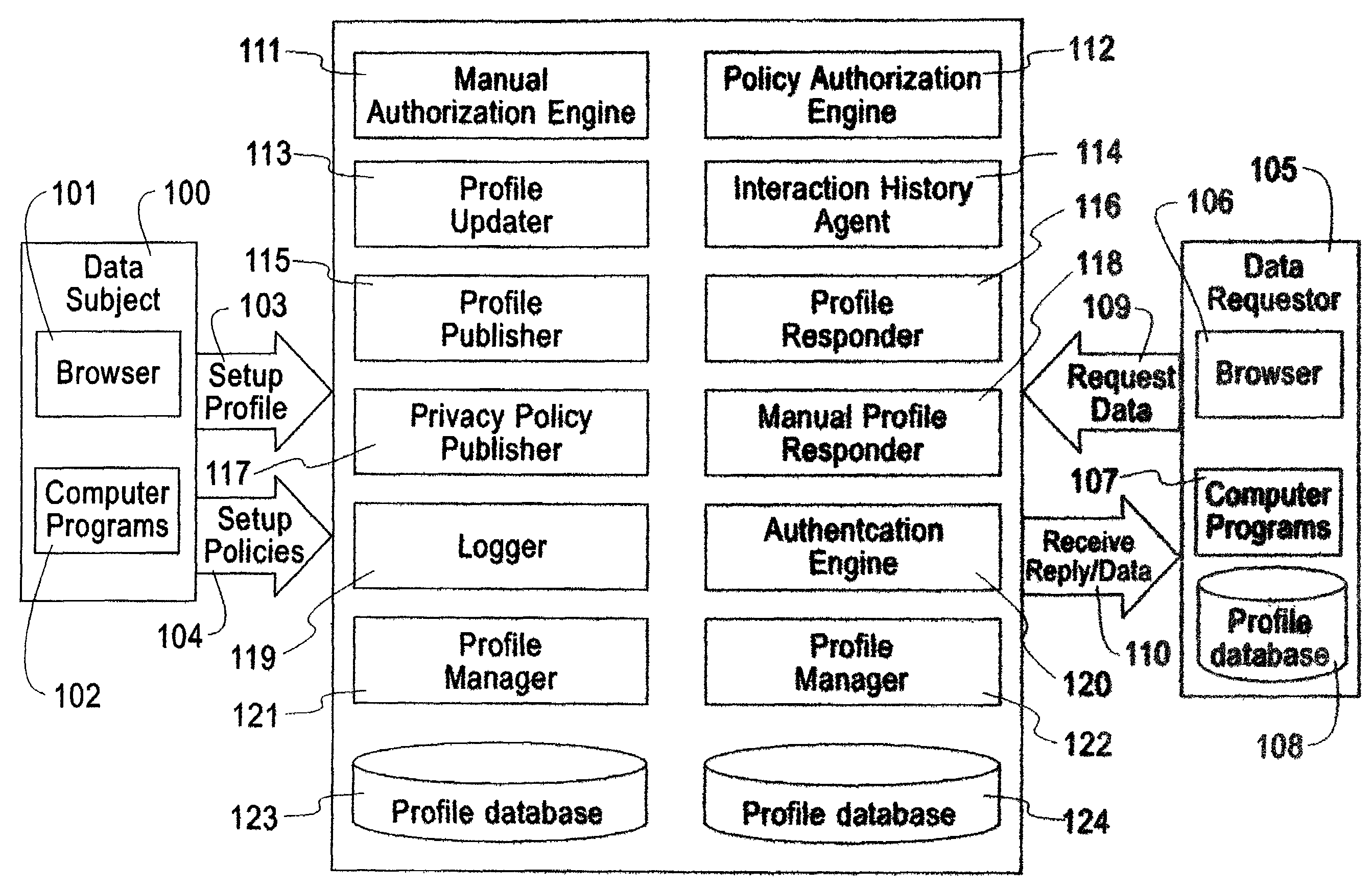
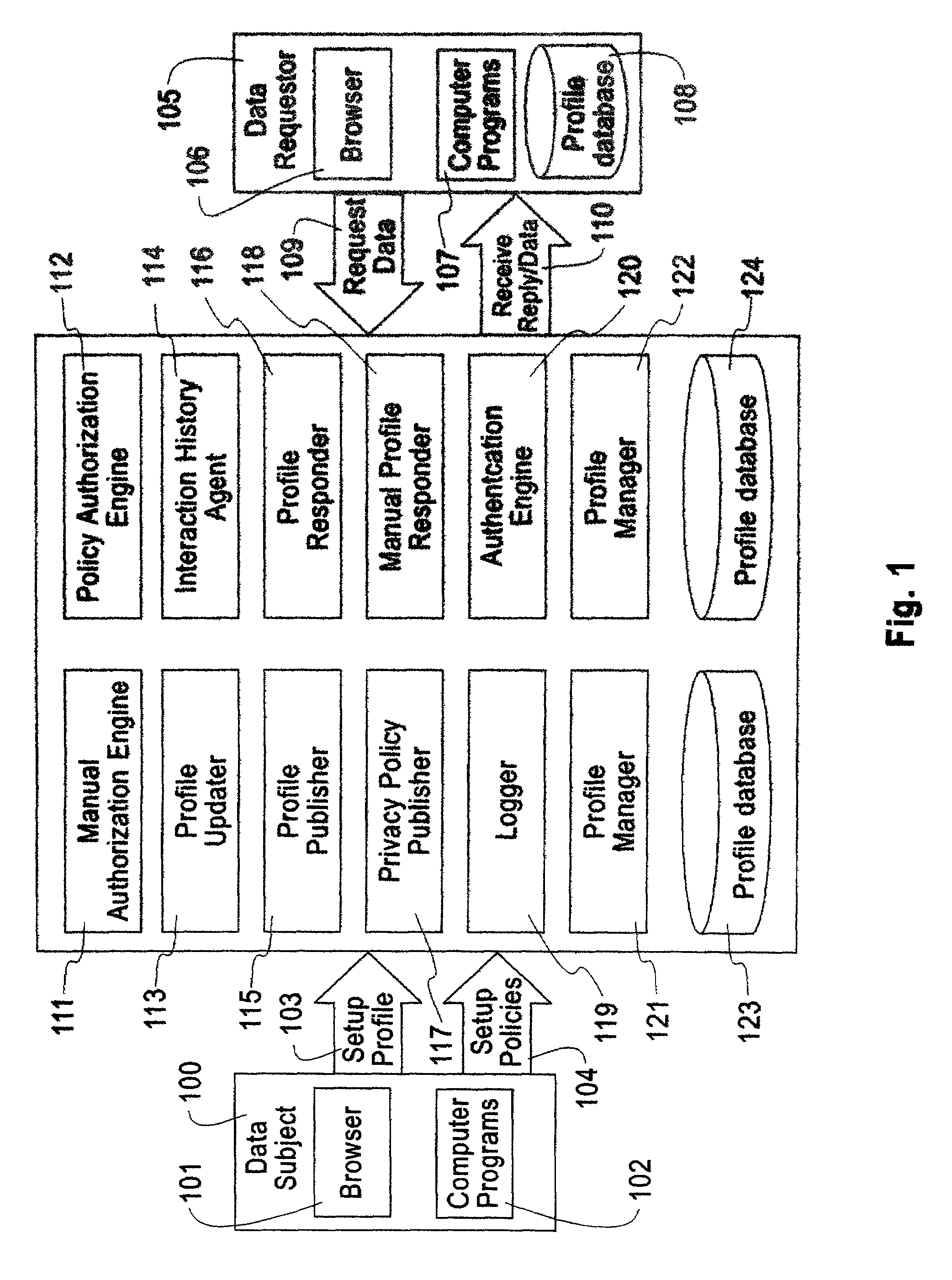
System, method, and business methods for enforcing privacy preferences on personal-data exchanges across a network
ActiveUS7478157B2Digital data processing detailsDigital computer detailsInternet privacyData exchange
An exemplary embodiment of the present invention includes a method to enforce privacy preferences on exchanges of personal data of a data-subject. The method comprises the steps of: specifying data-subject authorization rule sets having subject constraints, receiving a request message from a requester and a requester privacy statement, comparing the requester privacy statement to the subject constraints, and releasing the data-subject data in a response message to the requester only if the subject constraints are satisfied. The requester privacy statement includes purpose, retention, recipient, and access information, wherein the purpose information specifies the purpose for which the requested data is acquired, the retention information specifies a retention policy for the requested data, the recipient information specifies the recipients of the requested data, and the access information specifies whether the requested data should be accessing to the data-subject after the data has been released.
Owner:IBM CORP
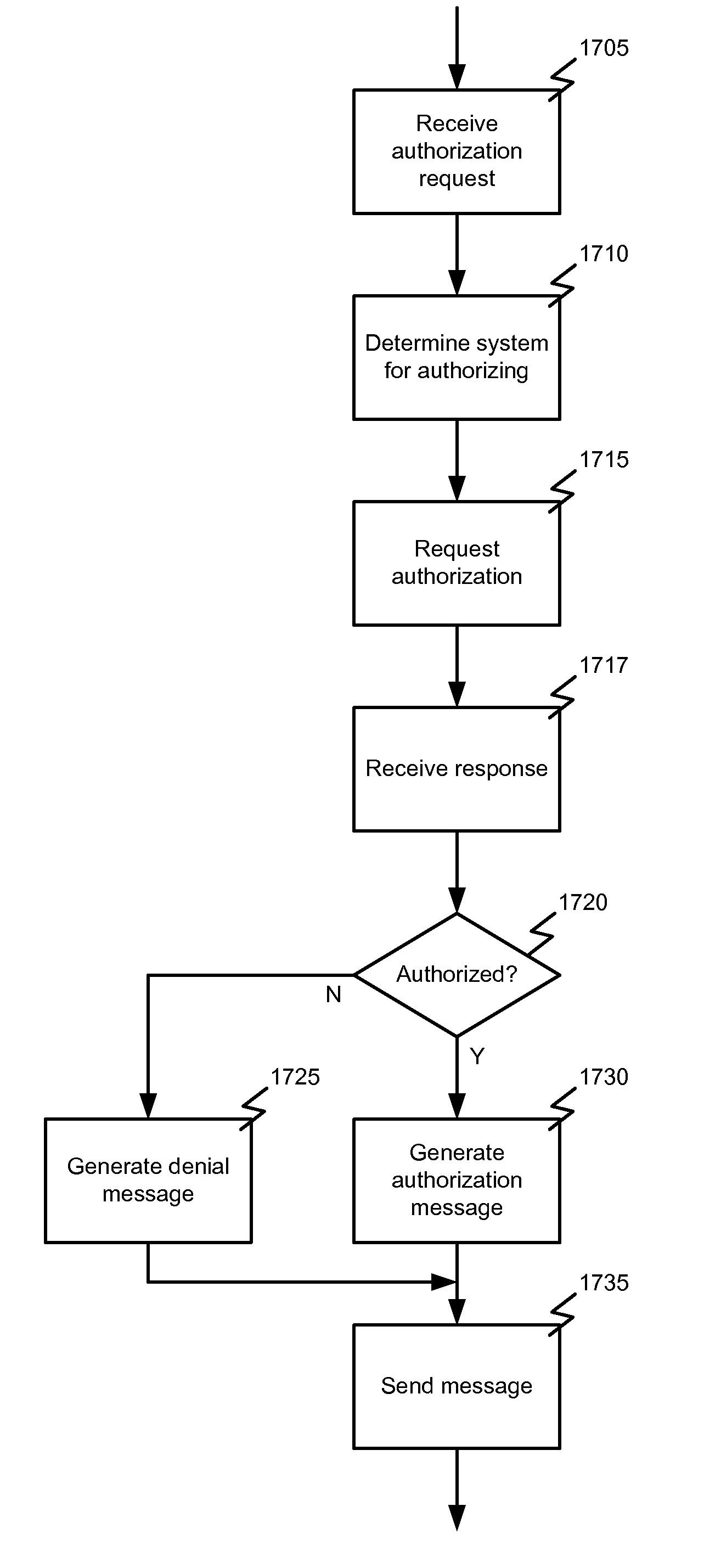
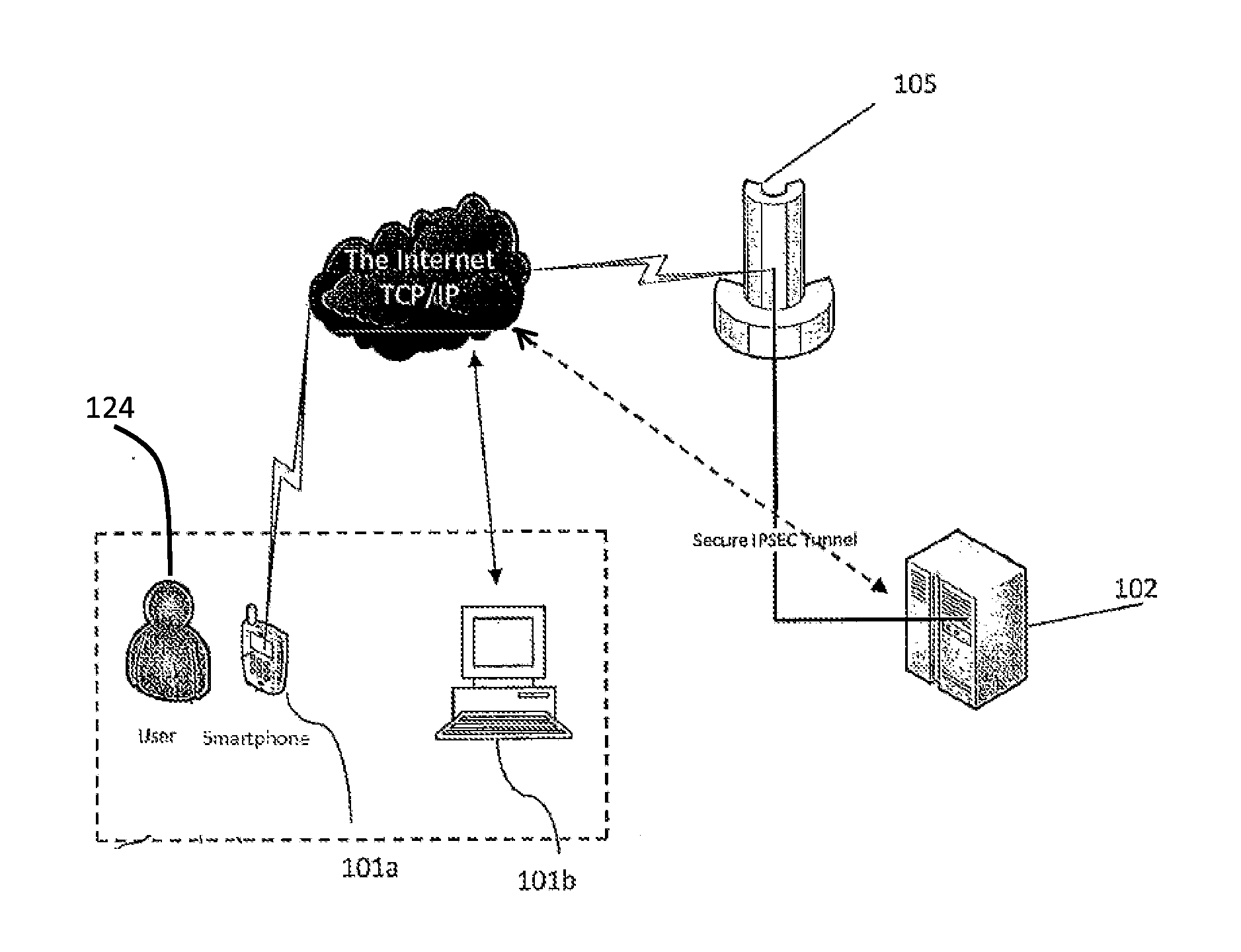
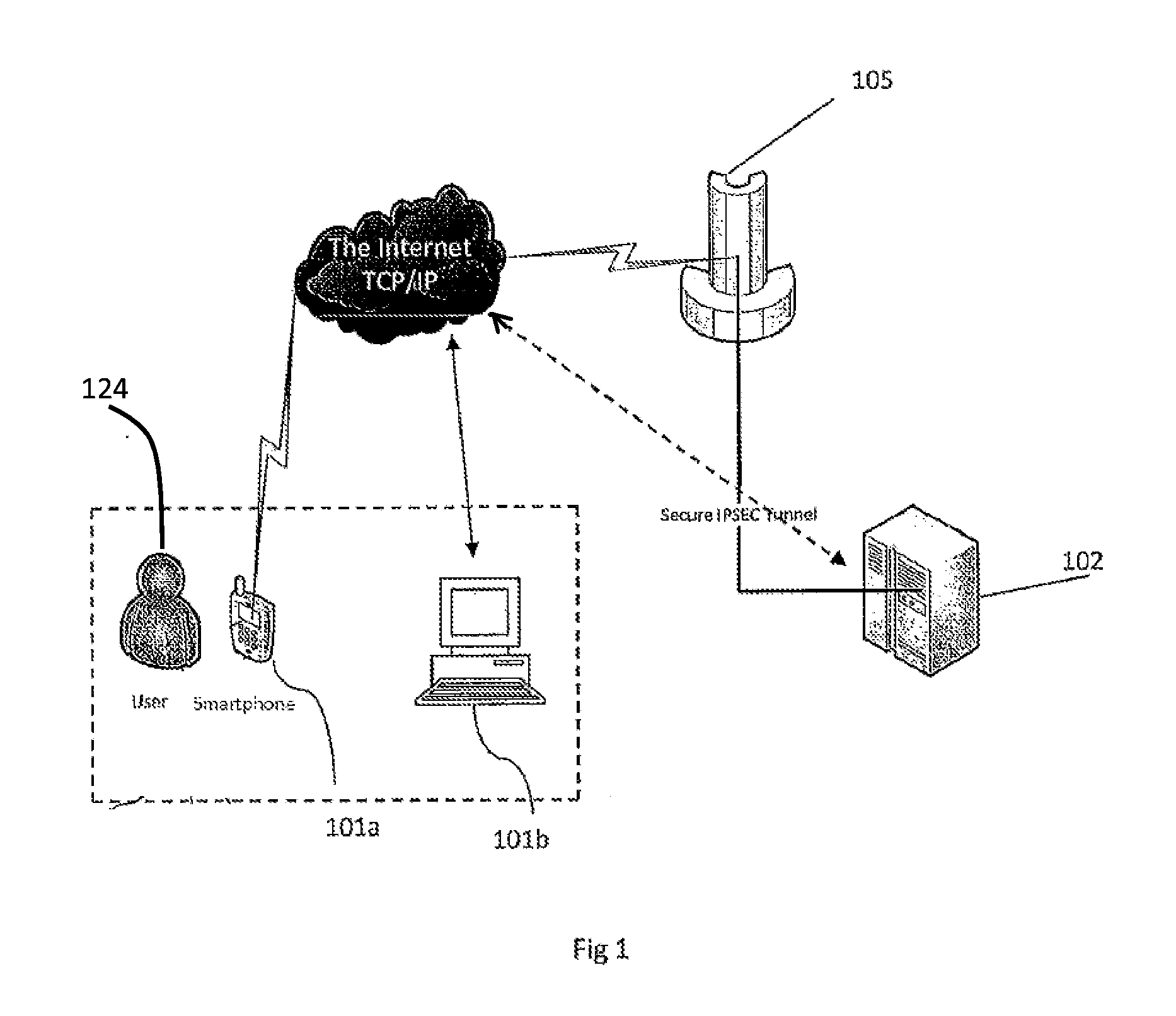
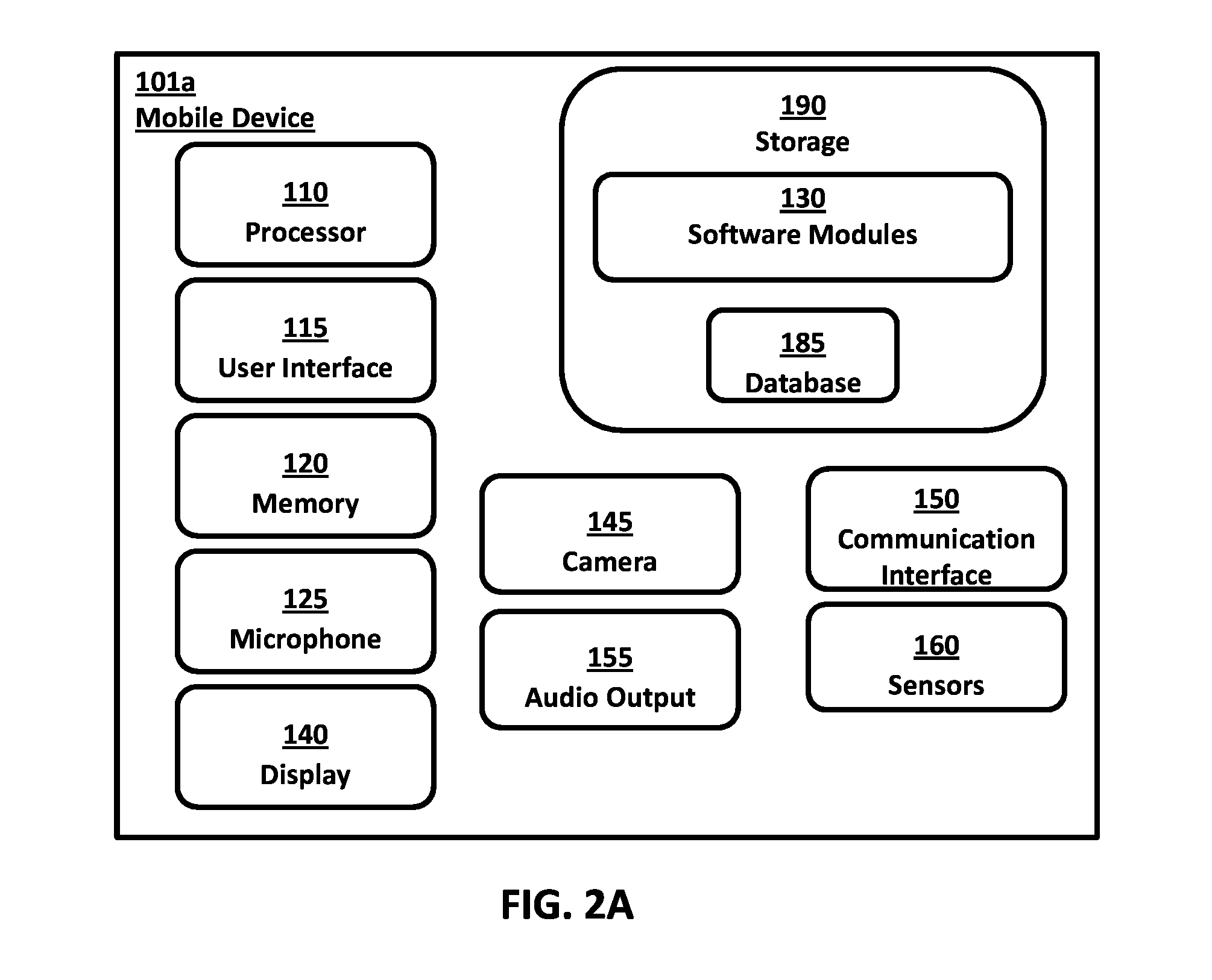
System and method for authorizing access to access-controlled environments
ActiveUS20140337930A1Digital data processing detailsMultiple digital computer combinationsMobile deviceSecure authentication
Systems and methods are provided for authorizing a user to access an access-controlled environment. The system includes a system server platform that communicates with fixed PC's, servers and mobile devices (e.g., smartphones) operated by users. The systems and methods described herein enable a series of operations whereby a user attempting to access an access-controlled environment is prompted to biometrically authenticate using the user's preregistered mobile device. Biometric authentication can include capturing images of the user's biometric features, encoding the features as a biometric identifier, comparing the biometric identifier to a previously generated biometric identifier and determining liveness. In addition, the authentication system can further authorize the user and electronically grant access to the access-controlled environment. In this manner the secure authentication system can, based on biometric authentication, authorize a user's access to devices, online services, physical locations or any networked environment that require user authorization.
Owner:VERIDIUM IP LTD
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com