Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
1468 results about "Secure authentication" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
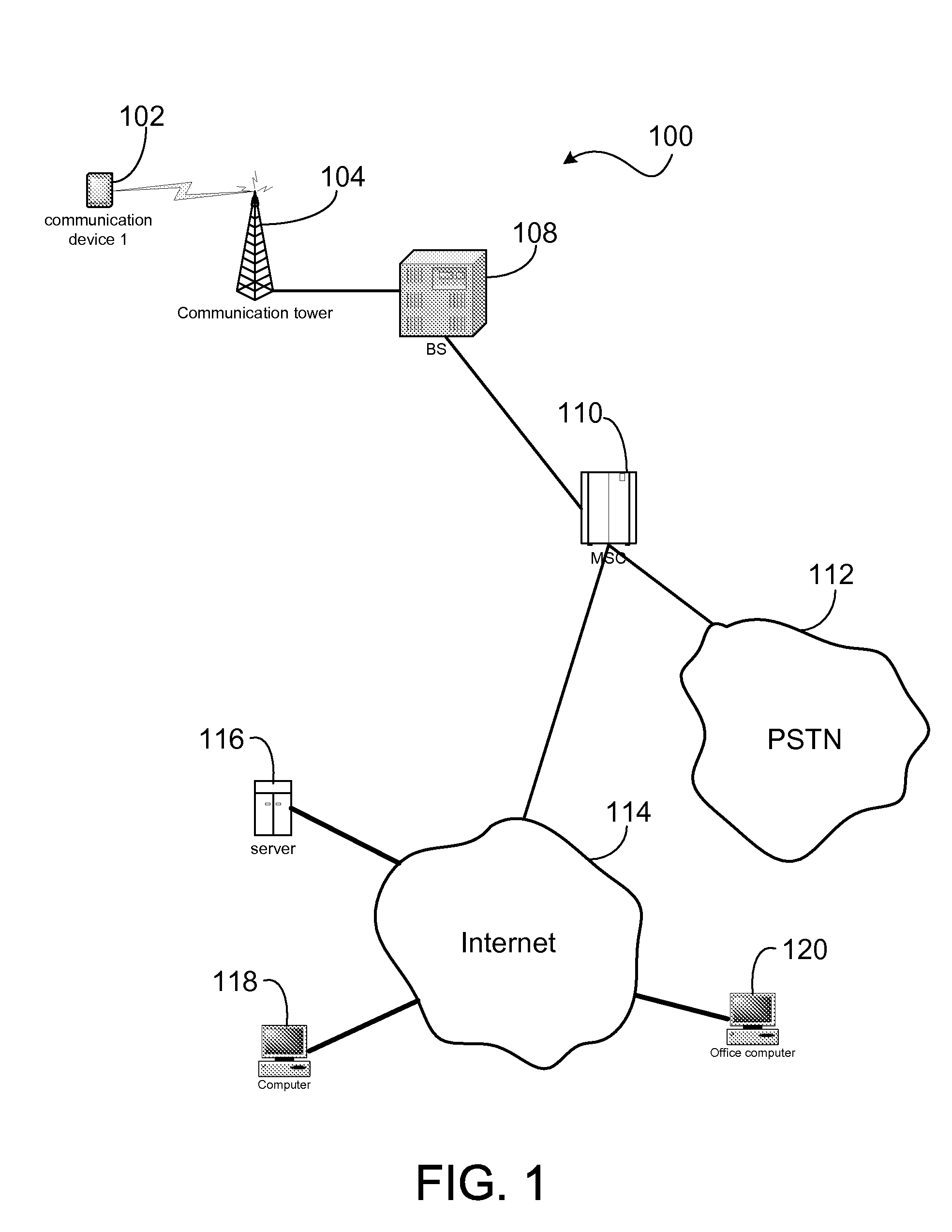
Authentication in cybersecurity. Authentication is important because it enables organizations to keep their networks secure by permitting only authenticated users (or processes) to access its protected resources, which may include computer systems, networks, databases, websites and other network-based applications or services.
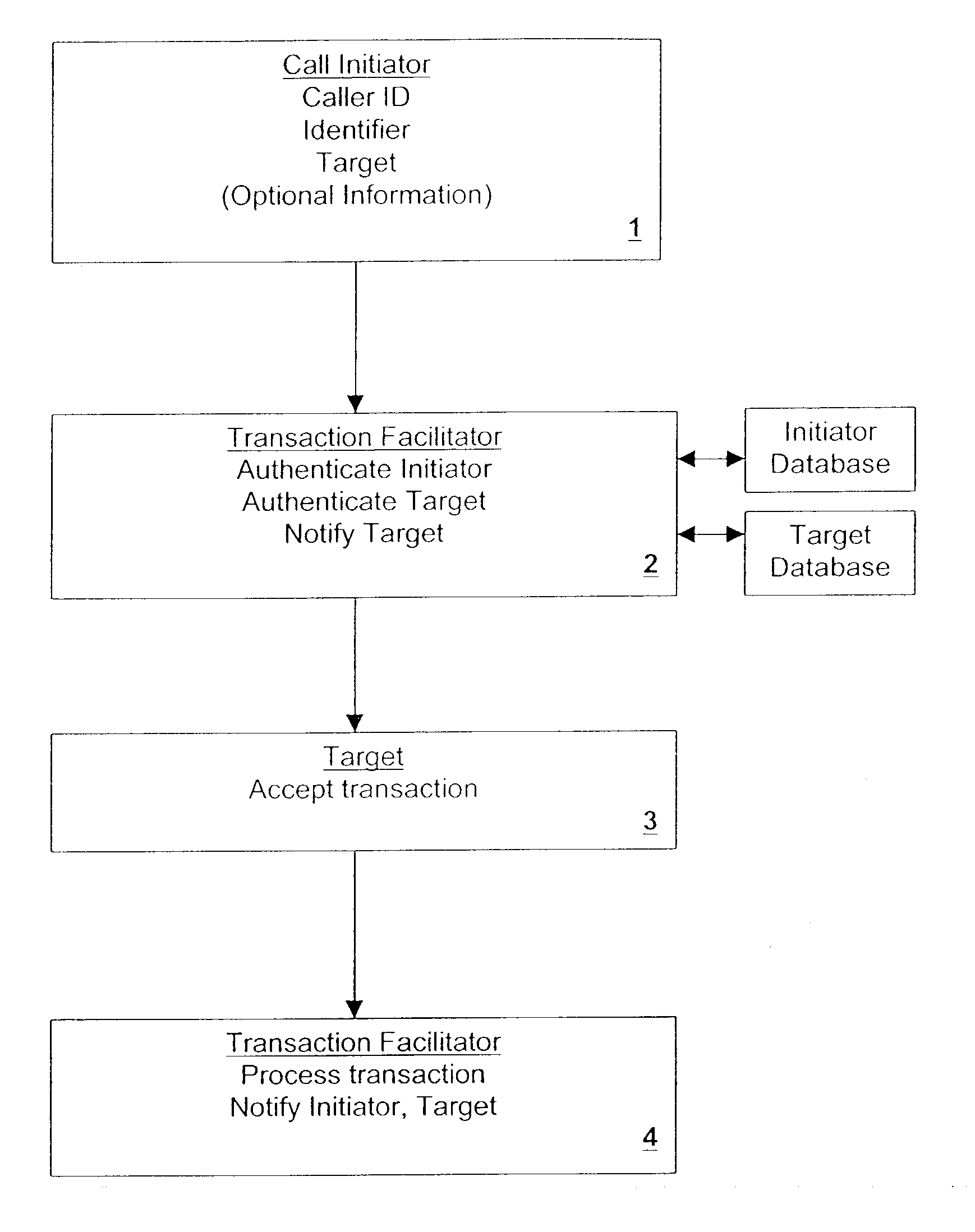
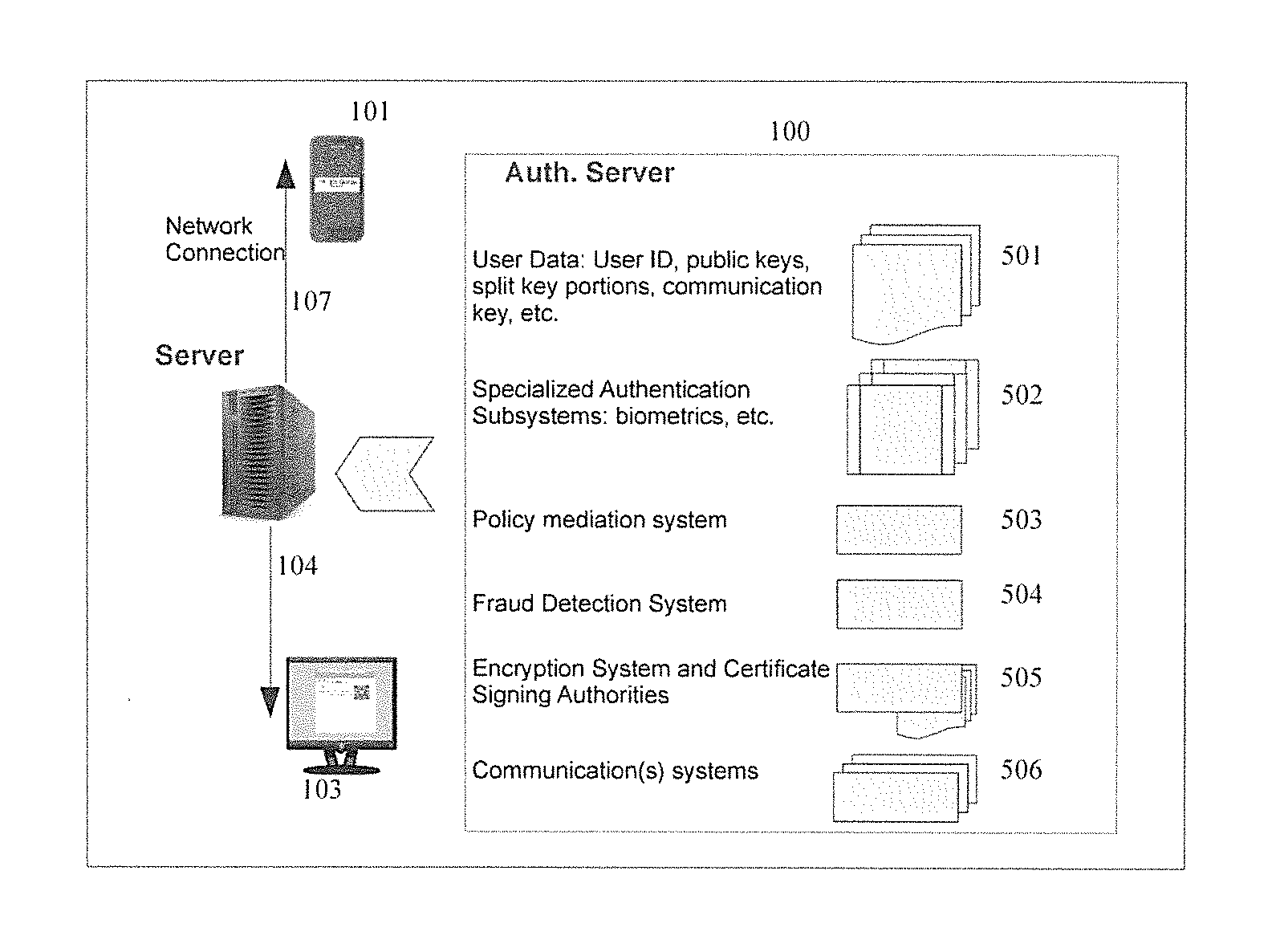
Secure authentication in a multi-party system
ActiveUS20130262857A1Web data indexingPublic key for secure communicationUser inputAuthentication server
A network user is authenticated to another network entity by using a first program to receive user input validation information, and store a user credential. A second program receives information, such as a random number, from the other entity. The first program receives an input transferring the information to it, transmits the information to the authentication server, and receives an identifier of the other entity, other information, and authentication policy requirements from the authentication server. It then transmits the input validation information corresponding to the received authentication policy requirements to the authentication server, and in response receives a request for a user credential. It signs a message, including the transferred information and the received other information, with the stored user credential, and transmits the signed message to the authentication server to authenticate the user.
Owner:PAYFONE
System and method for authorizing access to access-controlled environments
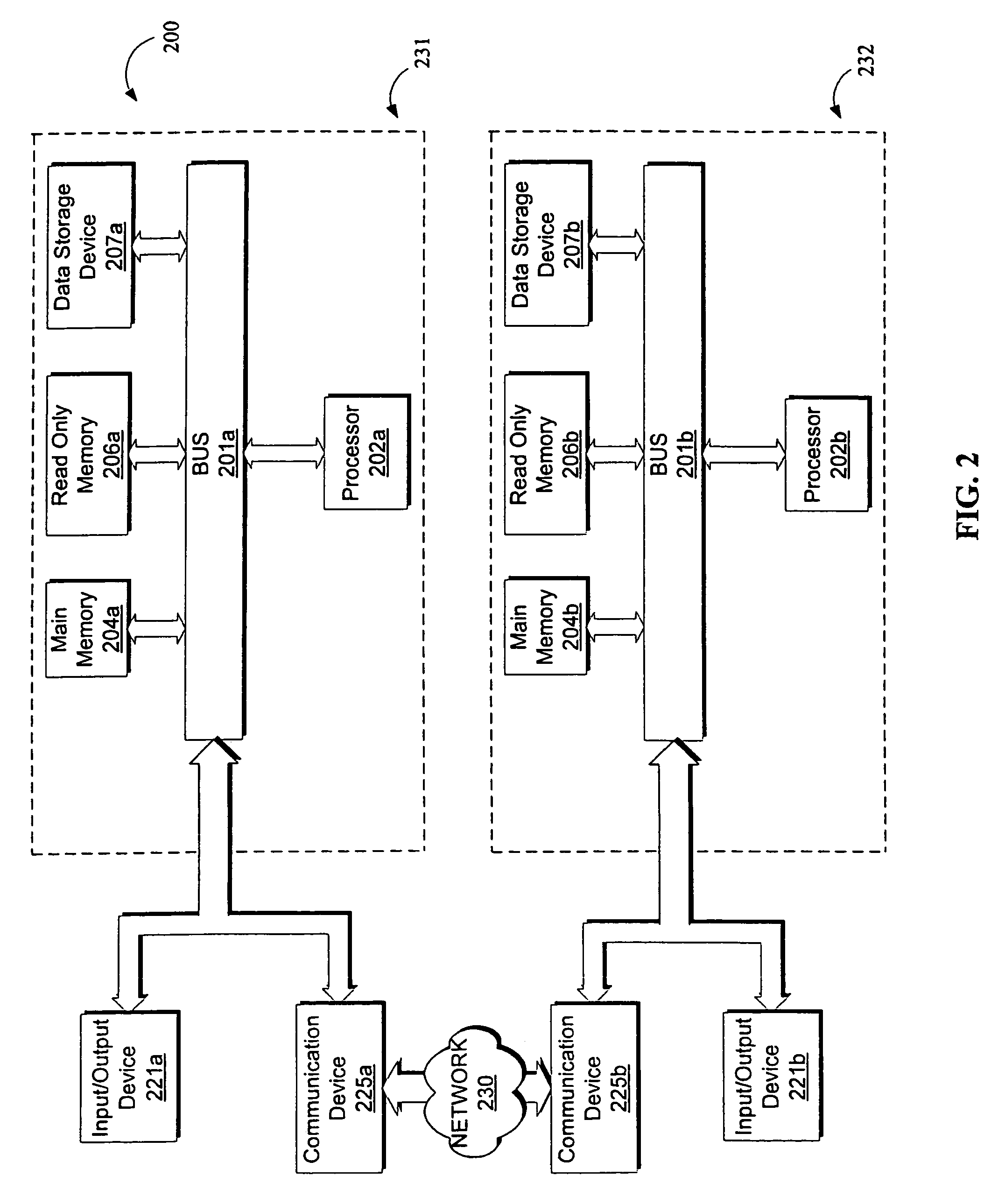
ActiveUS20140337930A1Digital data processing detailsMultiple digital computer combinationsMobile deviceSecure authentication
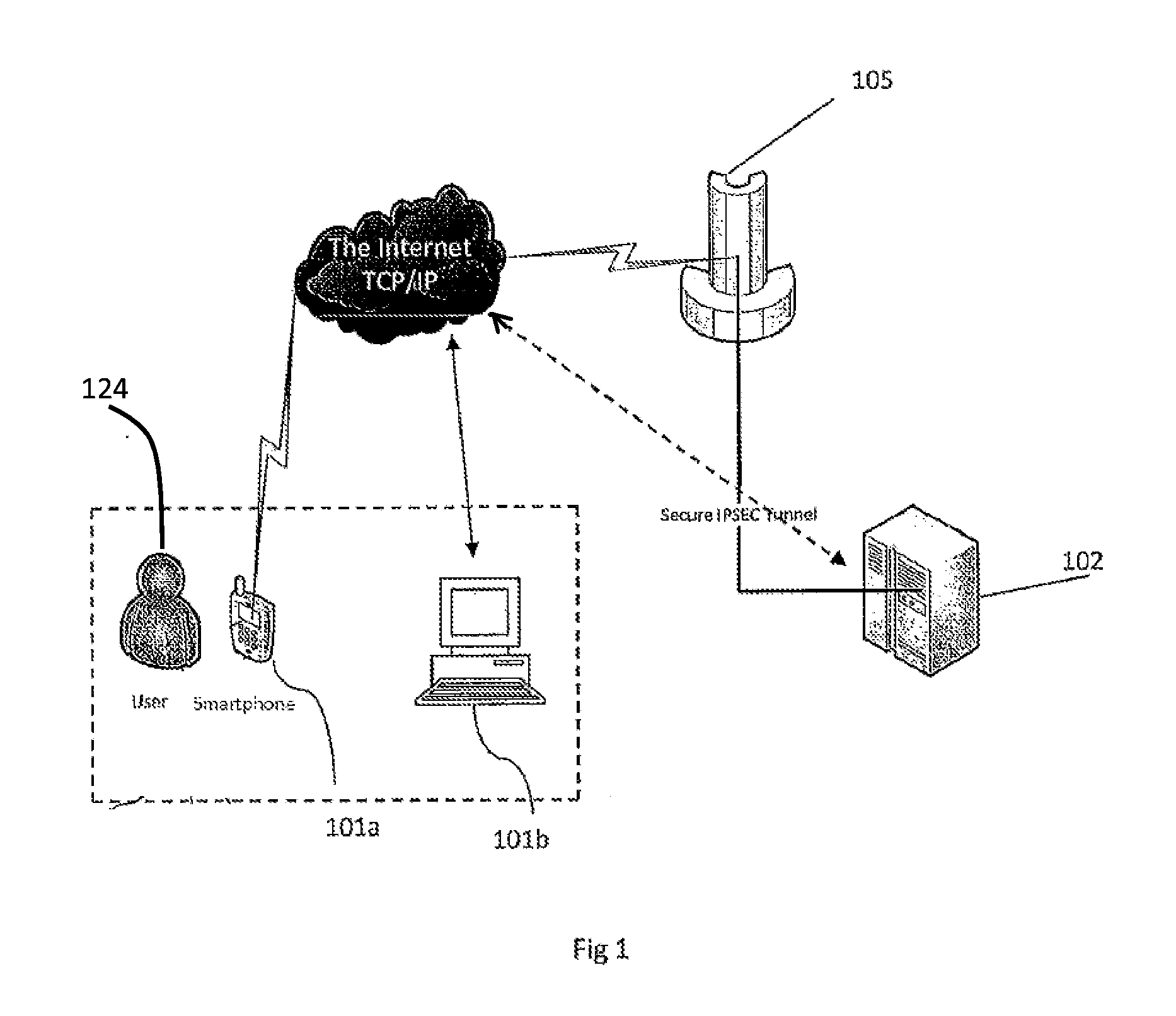
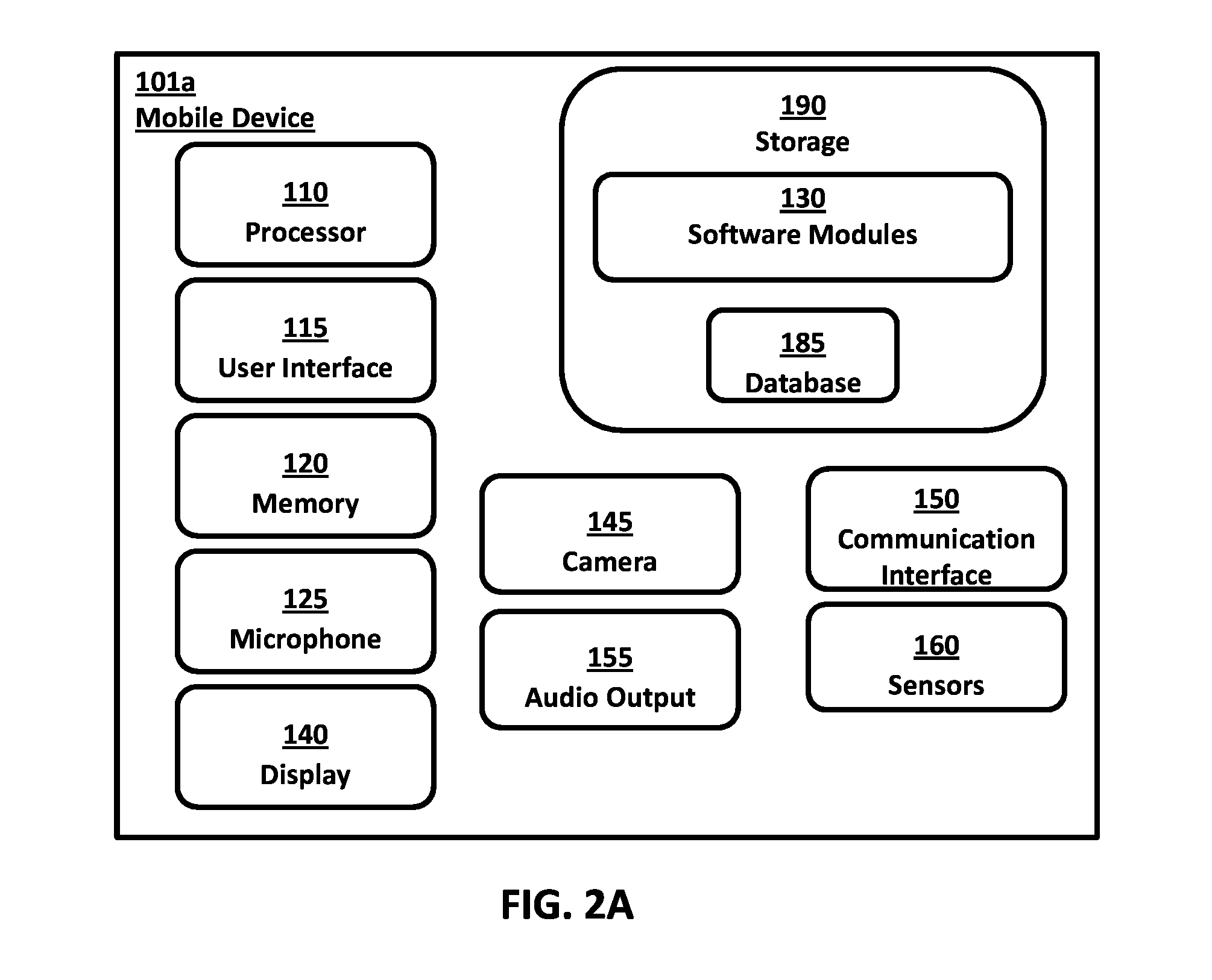
Systems and methods are provided for authorizing a user to access an access-controlled environment. The system includes a system server platform that communicates with fixed PC's, servers and mobile devices (e.g., smartphones) operated by users. The systems and methods described herein enable a series of operations whereby a user attempting to access an access-controlled environment is prompted to biometrically authenticate using the user's preregistered mobile device. Biometric authentication can include capturing images of the user's biometric features, encoding the features as a biometric identifier, comparing the biometric identifier to a previously generated biometric identifier and determining liveness. In addition, the authentication system can further authorize the user and electronically grant access to the access-controlled environment. In this manner the secure authentication system can, based on biometric authentication, authorize a user's access to devices, online services, physical locations or any networked environment that require user authorization.
Owner:VERIDIUM IP LTD
Secure authentication systems and methods
InactiveUS7383570B2Digital data processing detailsUser identity/authority verificationBrute forcePassword
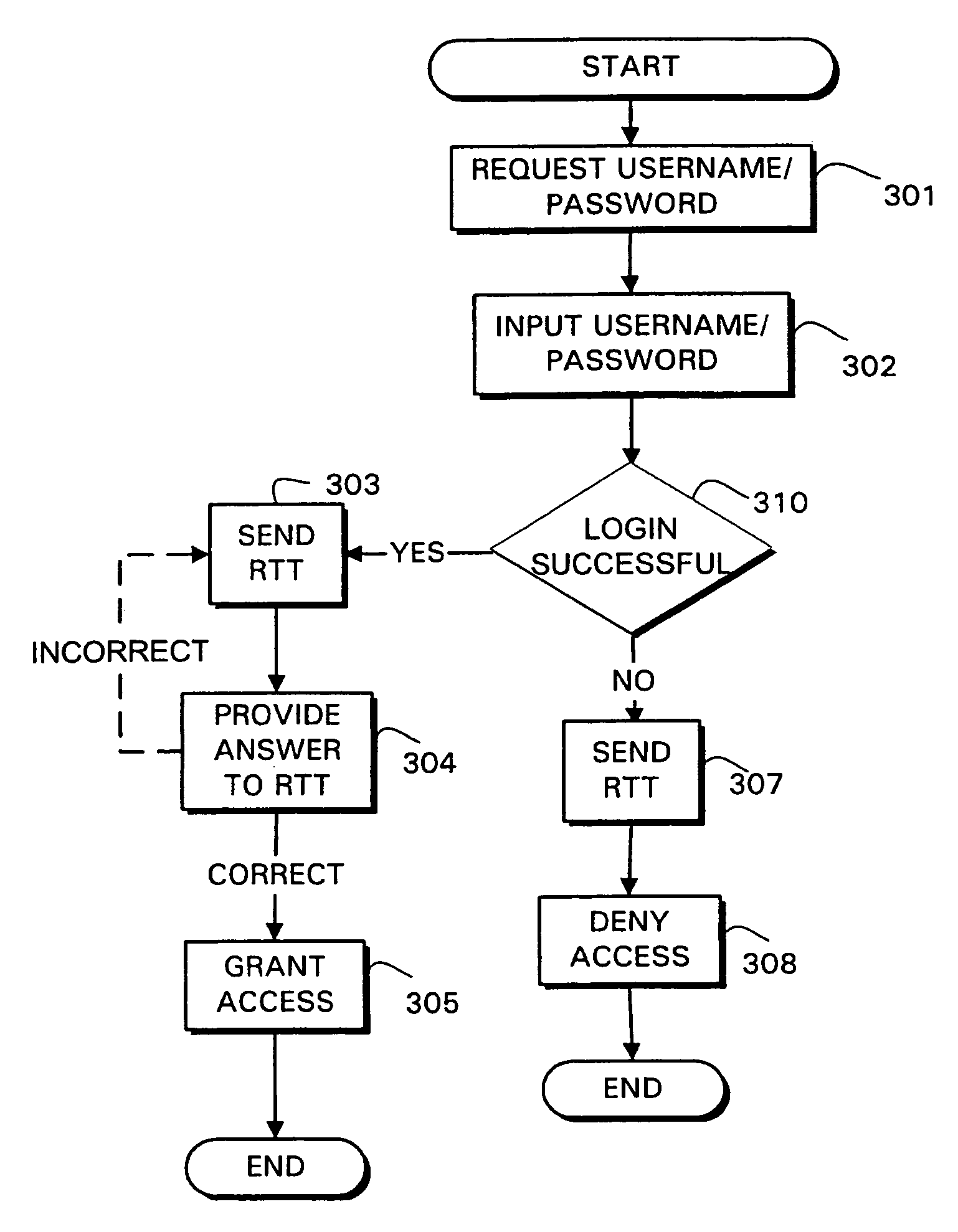
Systems and methods are provided for authentication by combining a Reverse Turing Test (RTT) with password-based user authentication protocols to provide improved resistance to brute force attacks. In accordance with one embodiment of the invention, a method is provided for user authentication, the method including receiving a username / password pair associated with a user; requesting one or more responses to a first Reverse Turing Test (RTT); and granting access to the user if a valid response to the first RTT is received and the username / password pair is valid.
Owner:INTERTRUST TECH CORP
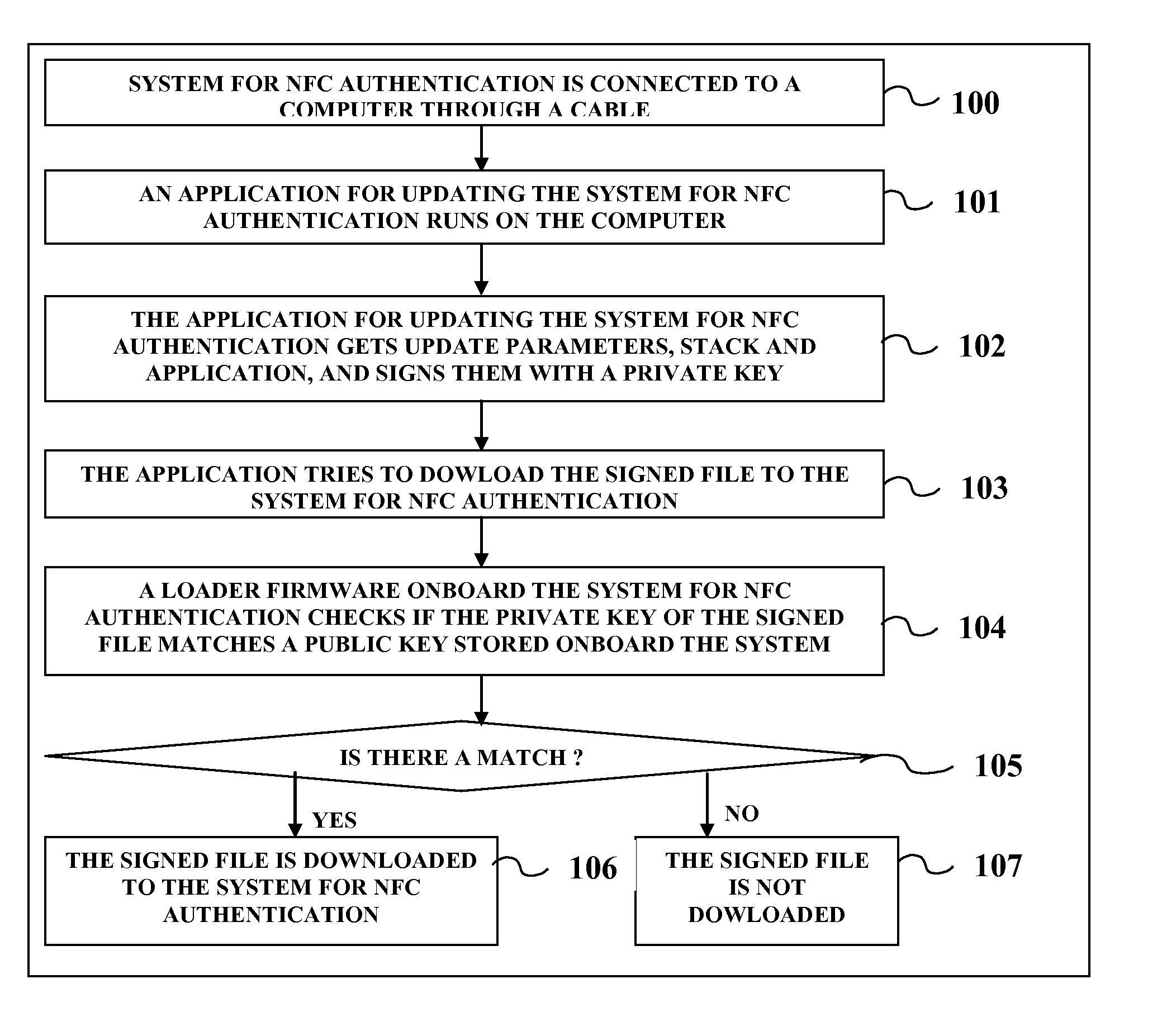
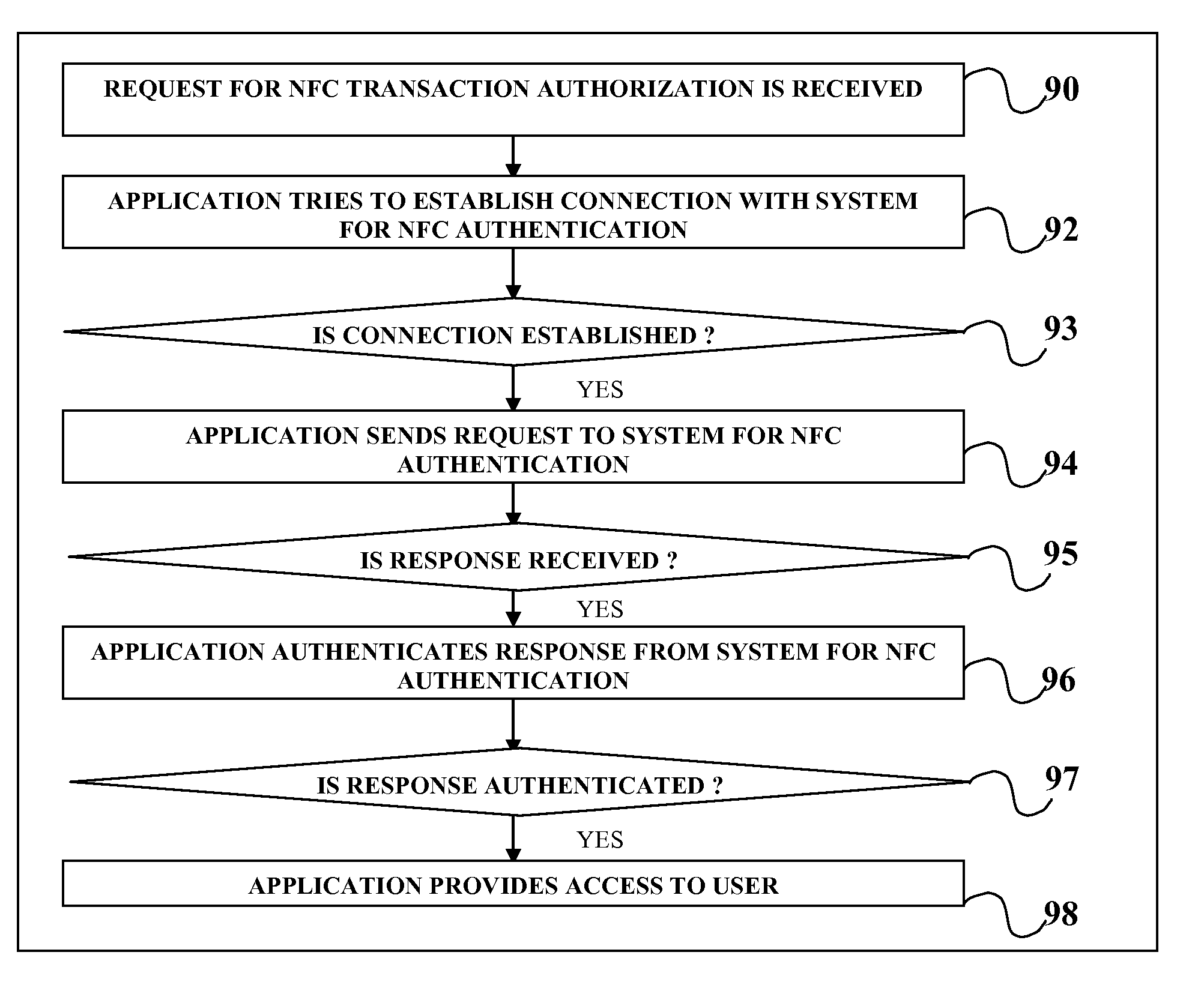
System For NFC Authentication Based on BLUETOOTH Proximity
InactiveUS20110313922A1Service provisioningNear-field transmissionComputer hardwareSecure authentication
A method and apparatus for secure authentication of Near Field Communication transactions based on proximity to a mobile key device.
Owner:OPTIMA DIRECT LLC
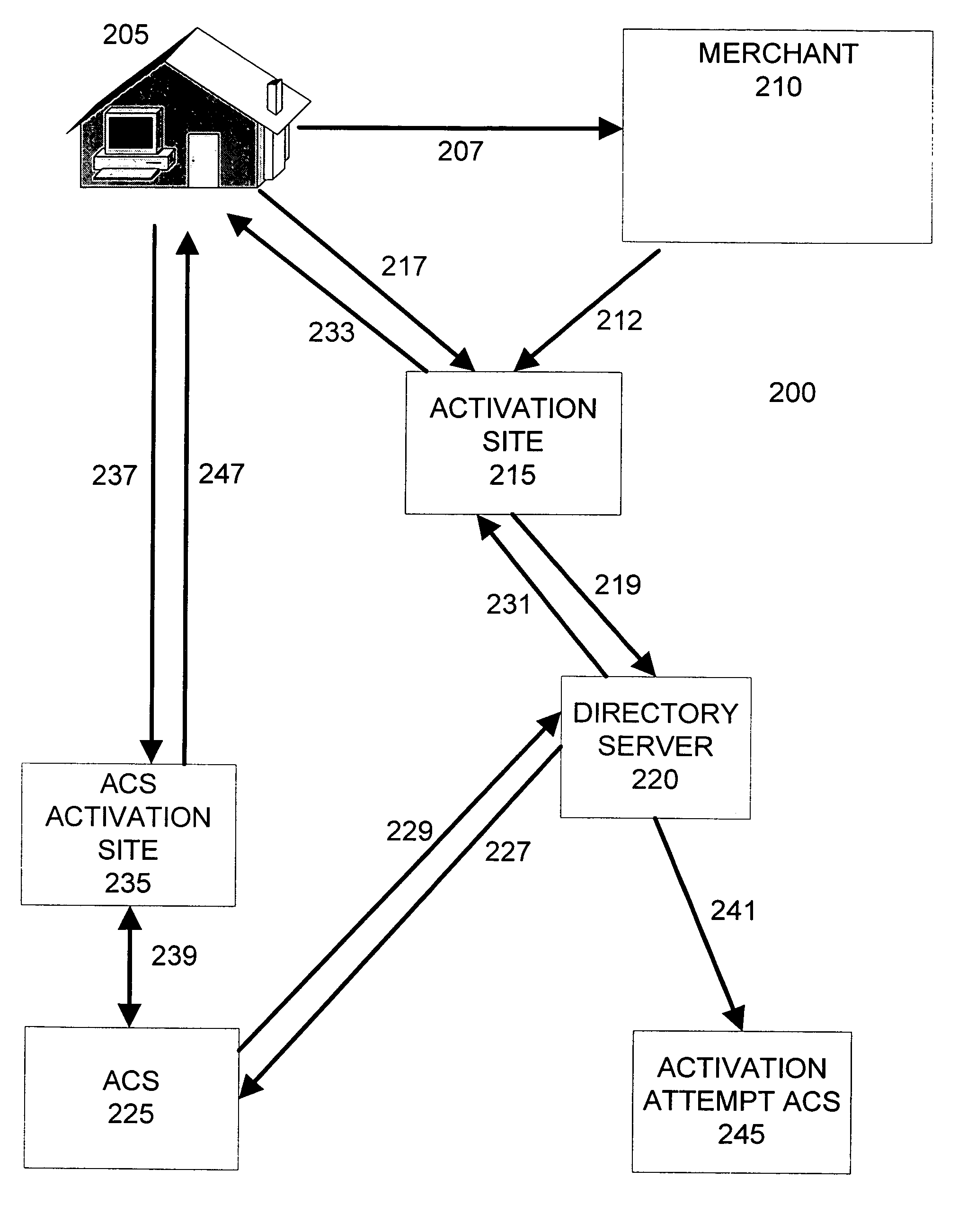
Method and system for secure authentication
ActiveUS20050036611A1Digital data processing detailsMultiple digital computer combinationsPaymentTelecommunications link
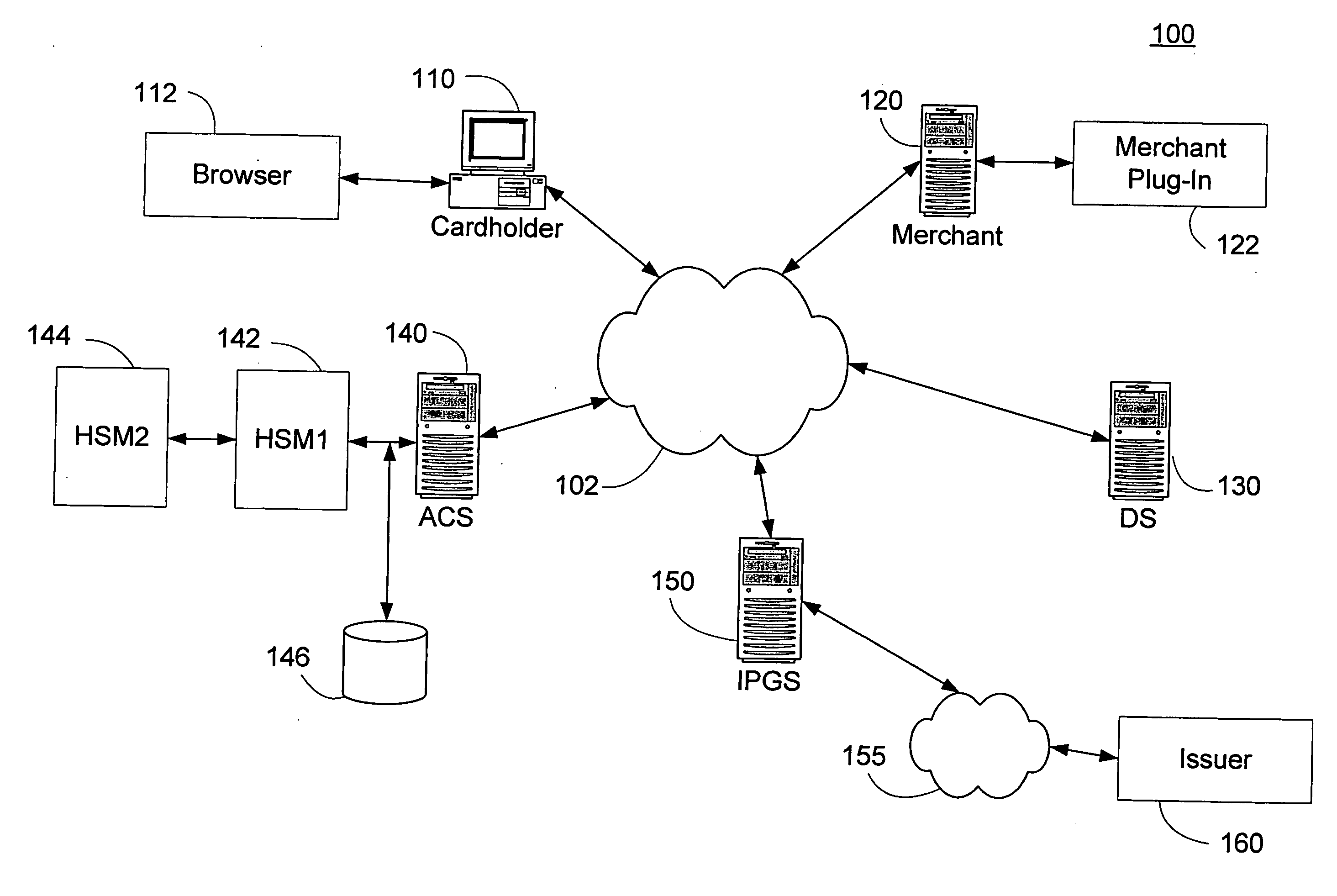
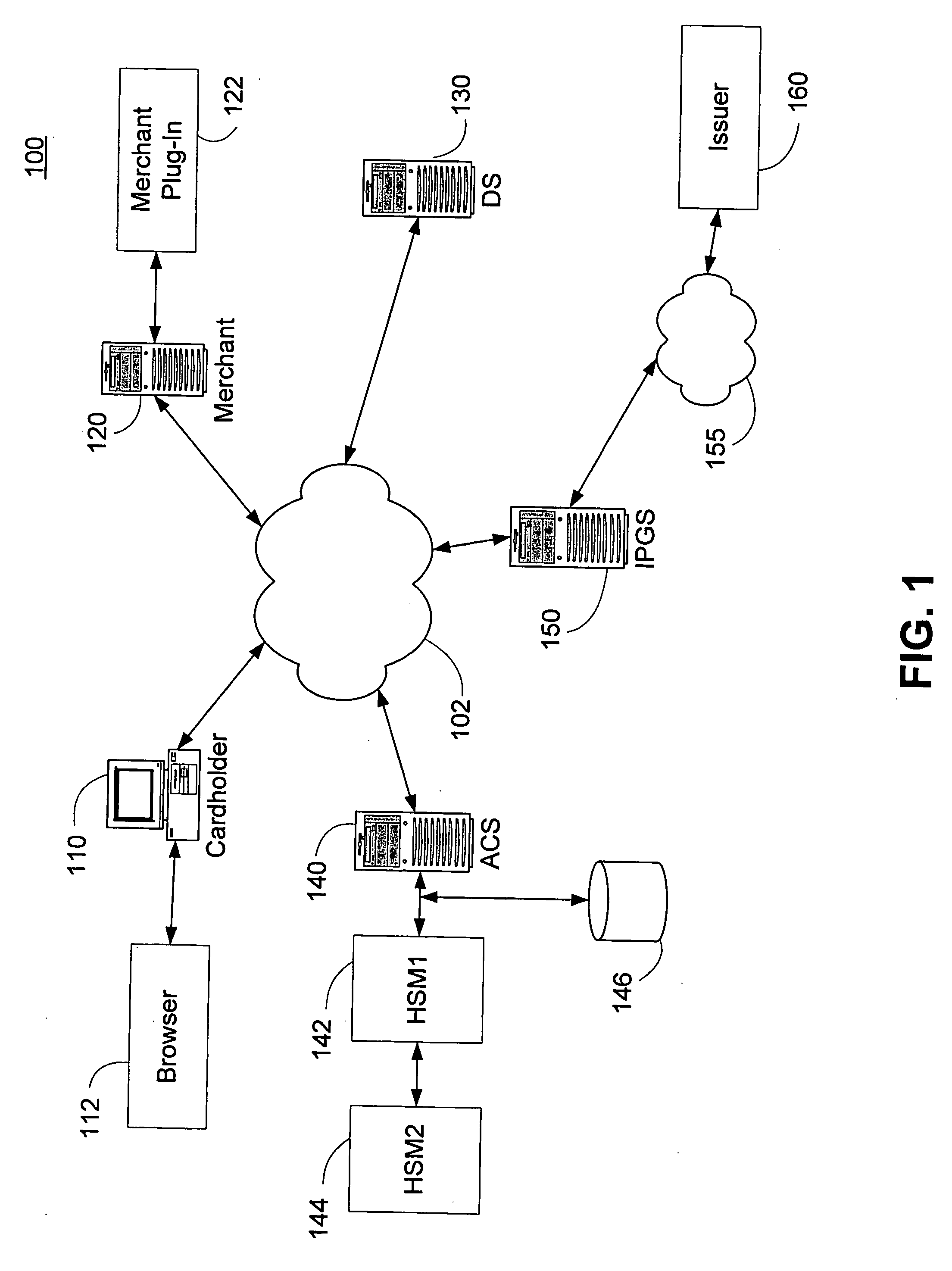
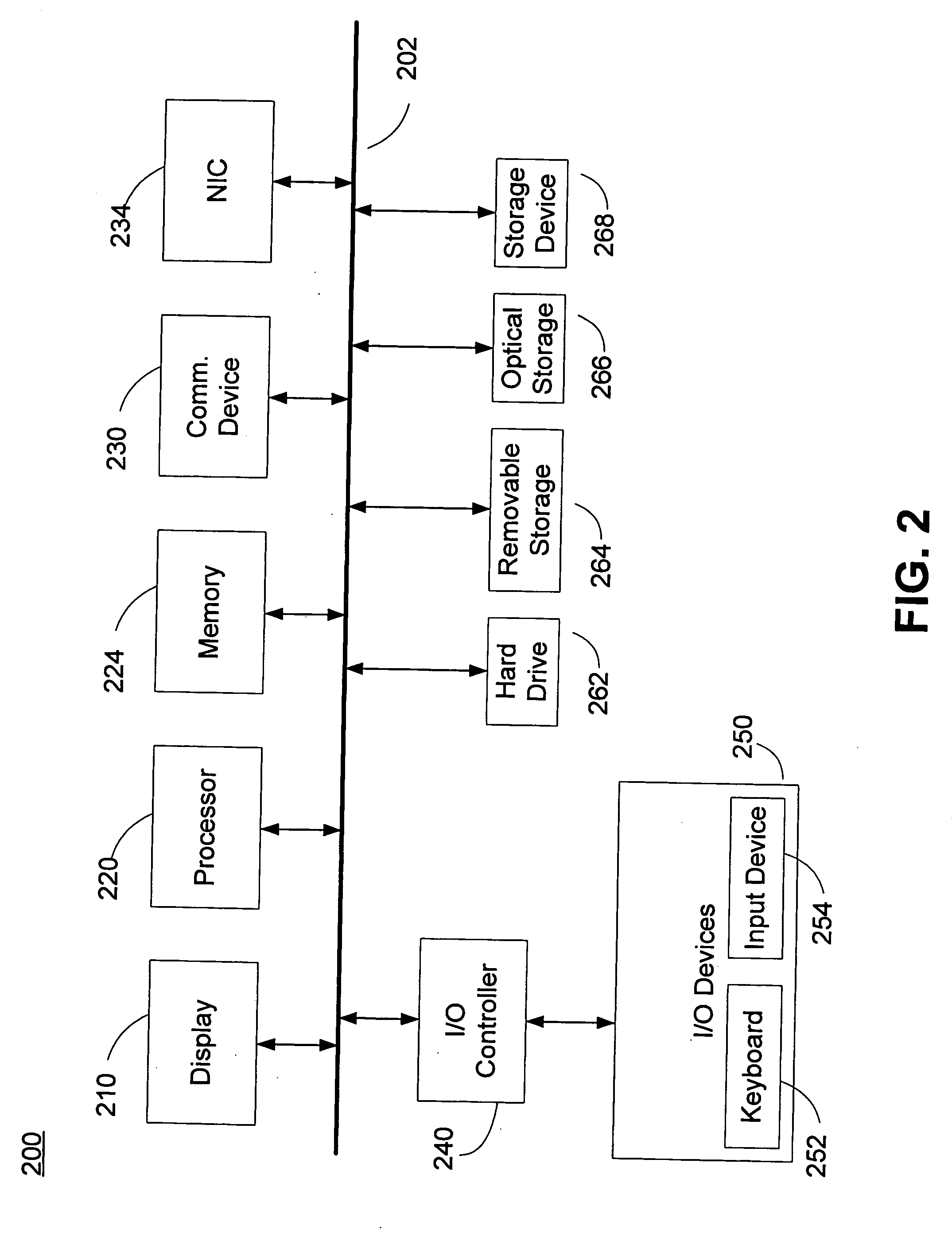
A system and method configured to provide secure Personal Identification Number (PIN) based authentication is disclosed. A passcode or PIN associated with a customer value card can be securely authenticated by an issuer prior to authorizing payment. An Access Control Server (ACS) can receive the PIN or passcode from a customer via a secure connection over a public network. The ACS can generate an encrypted PIN and can communicate the encrypted PIN to a remote issuer for authentication. The ACS can use one or more hardware security modules to generate the encrypted PIN. The hardware security modules can be emulated in software or implemented in hardware. The system can be configured such that the PIN is not exposed in an unencrypted form in a communication link or in hardware other than the originating customer terminal.
Owner:VISA USA INC (US)
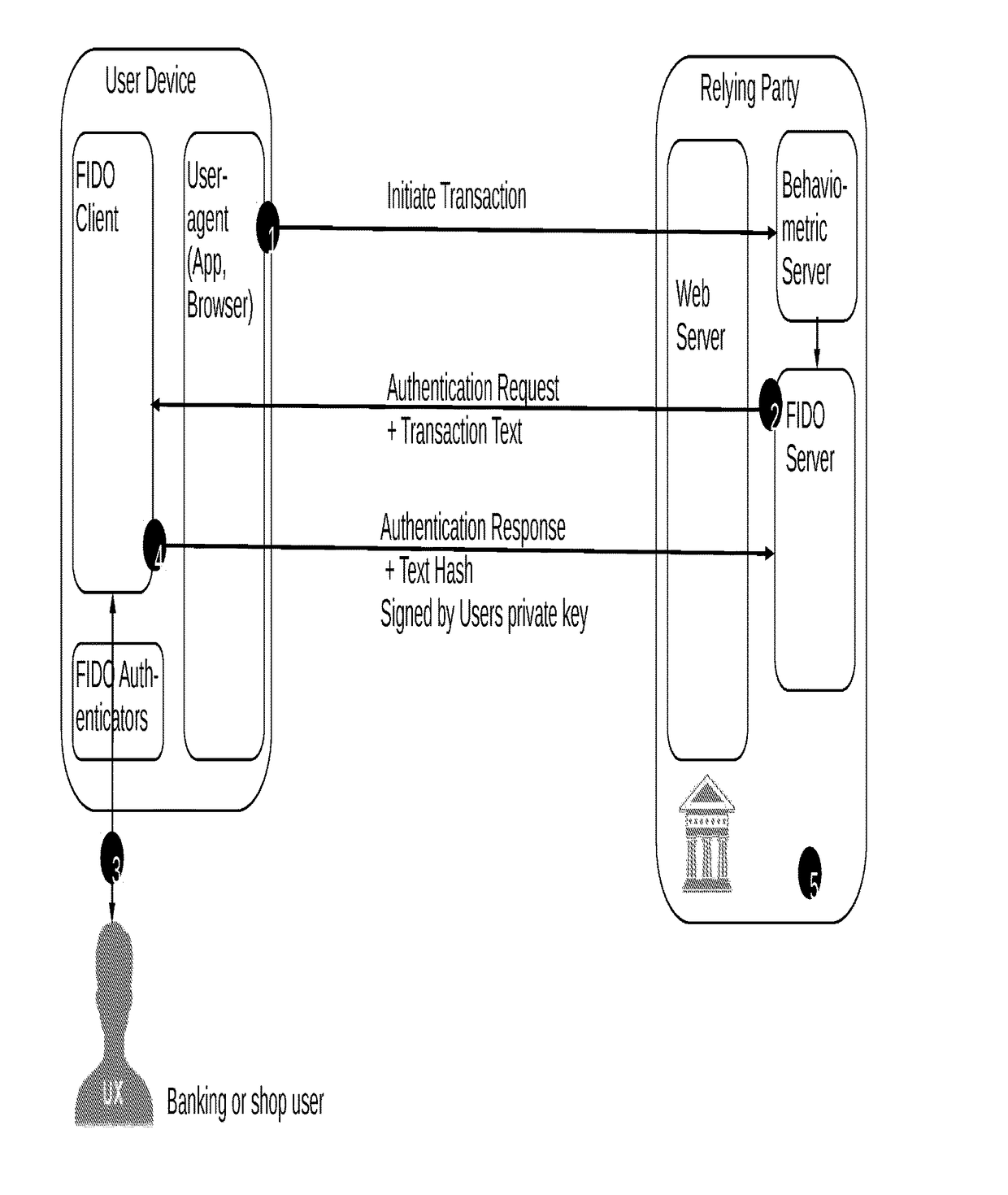
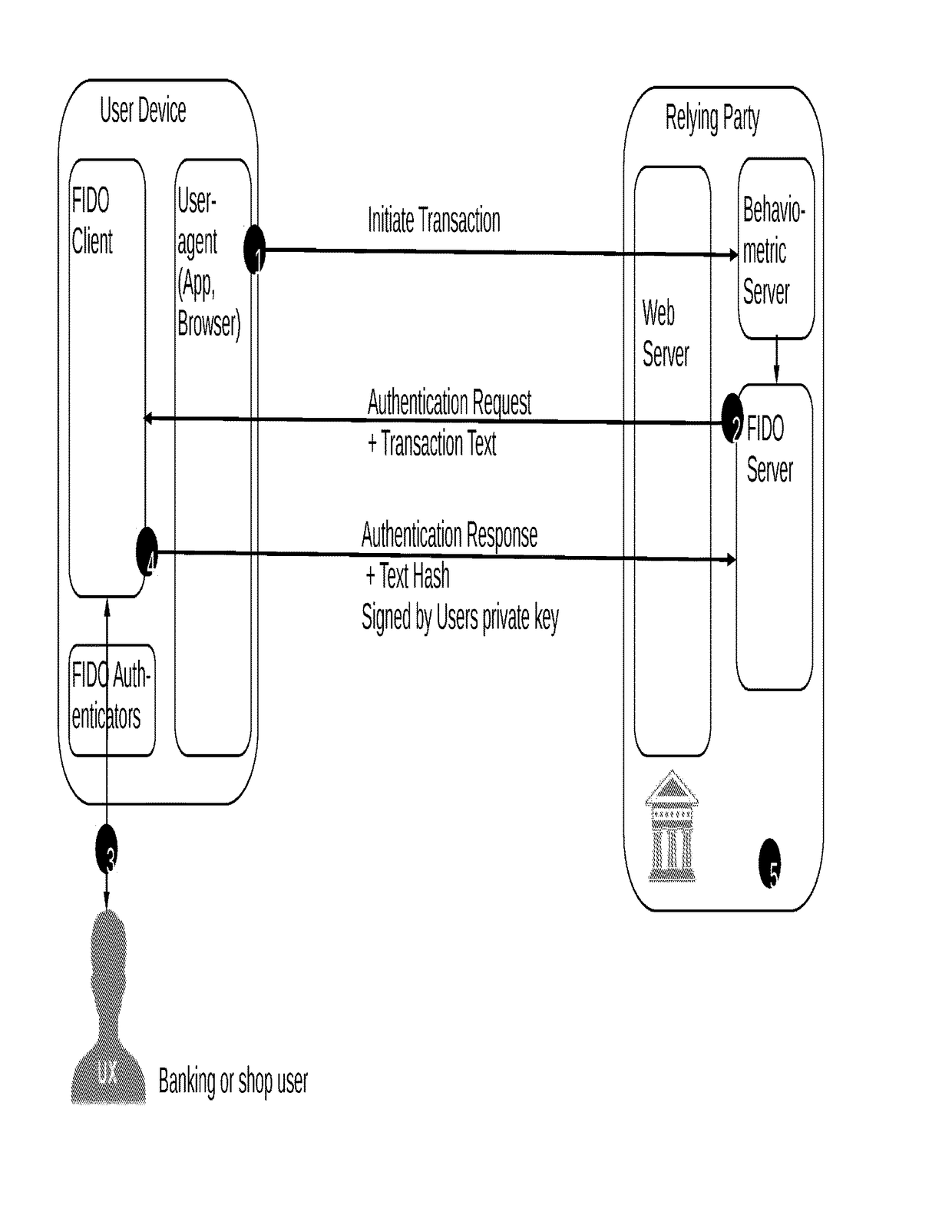
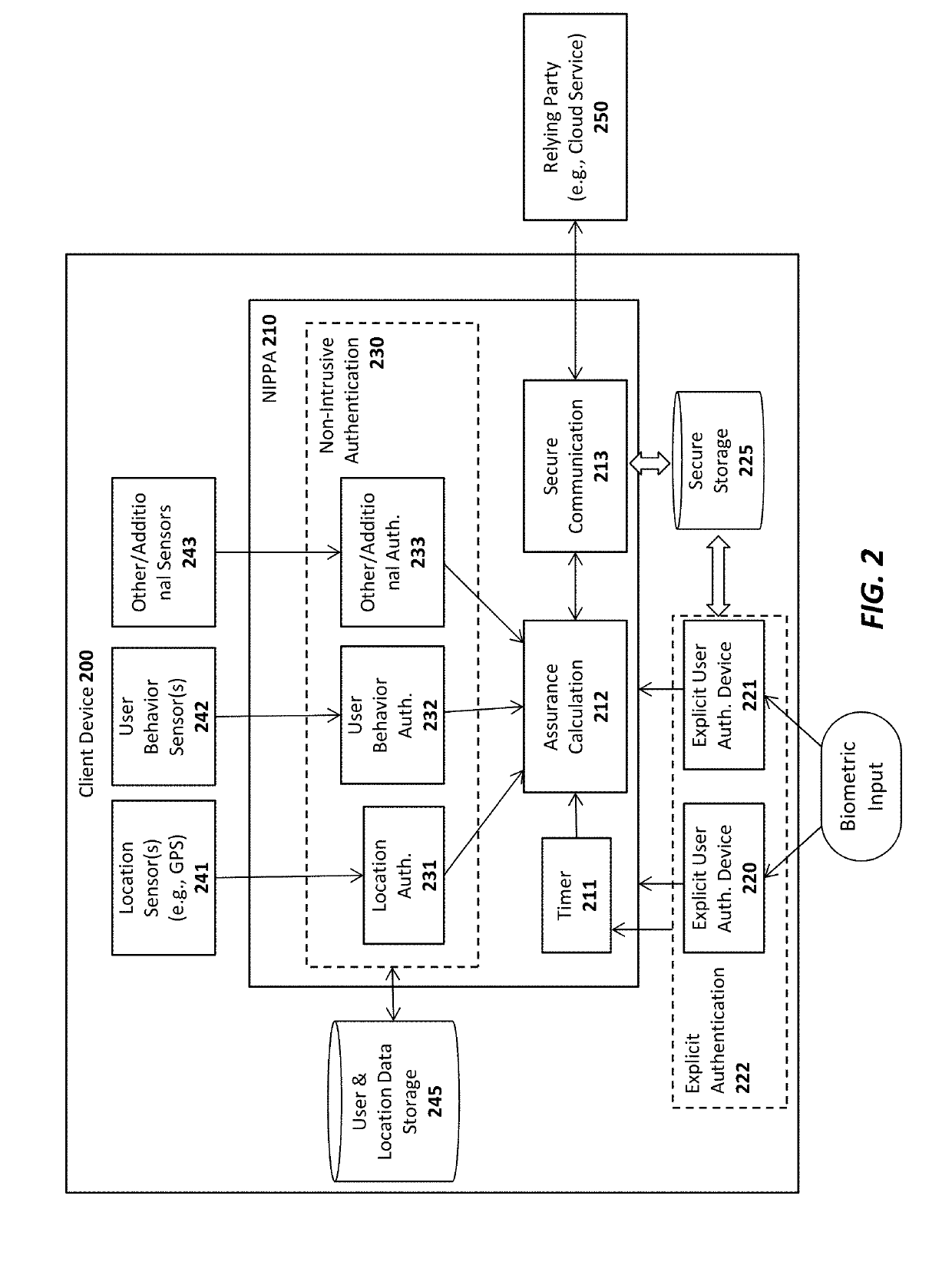
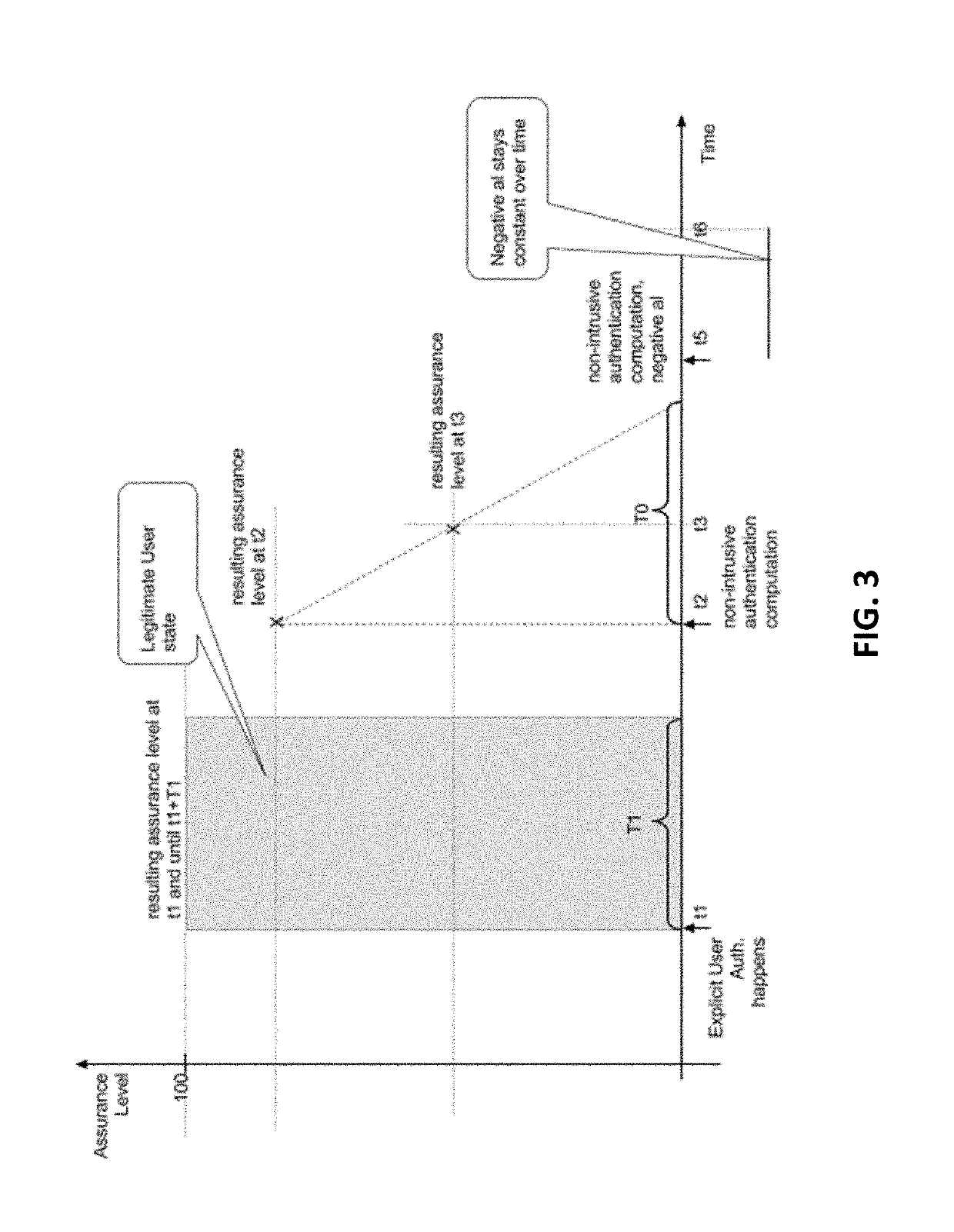
Secure authentication of a user of a device during a session with a connected server
ActiveUS10075437B1Reduce decreaseLow costMultiple keys/algorithms usagePublic key for secure communicationData matchingUser device
A computer-implemented method for secure authentication of a user to a service for executing a transaction, the method being implemented in a system including a user device including a FIDO-client, a FIDO-server of a relying party providing the service, a behaviometric server and a web server associated with the relying party, the method including a preparation stage and an authentication stage. In the preparation stage a TLS-connection is established between the user device and the web-server, behavioral input data is collected from user device, and a transaction initiation message is transmitted to the behaviometric server. In the authentication stage, behaviometric data received in the transaction initiation message is compared to a second set of behaviometric data to determine whether the data matches, and if the data matches, the transaction is authenticated by the FIDO server.
Owner:BEHAVIOSEC
System for NFC authentication based on BLUETOOTH proximity
InactiveUS8112066B2Service provisioningNear-field transmissionComputer hardwareSecure authentication
A method and apparatus for secure authentication of Near Field Communication transactions based on proximity to a mobile key device.
Owner:OPTIMA DIRECT LLC
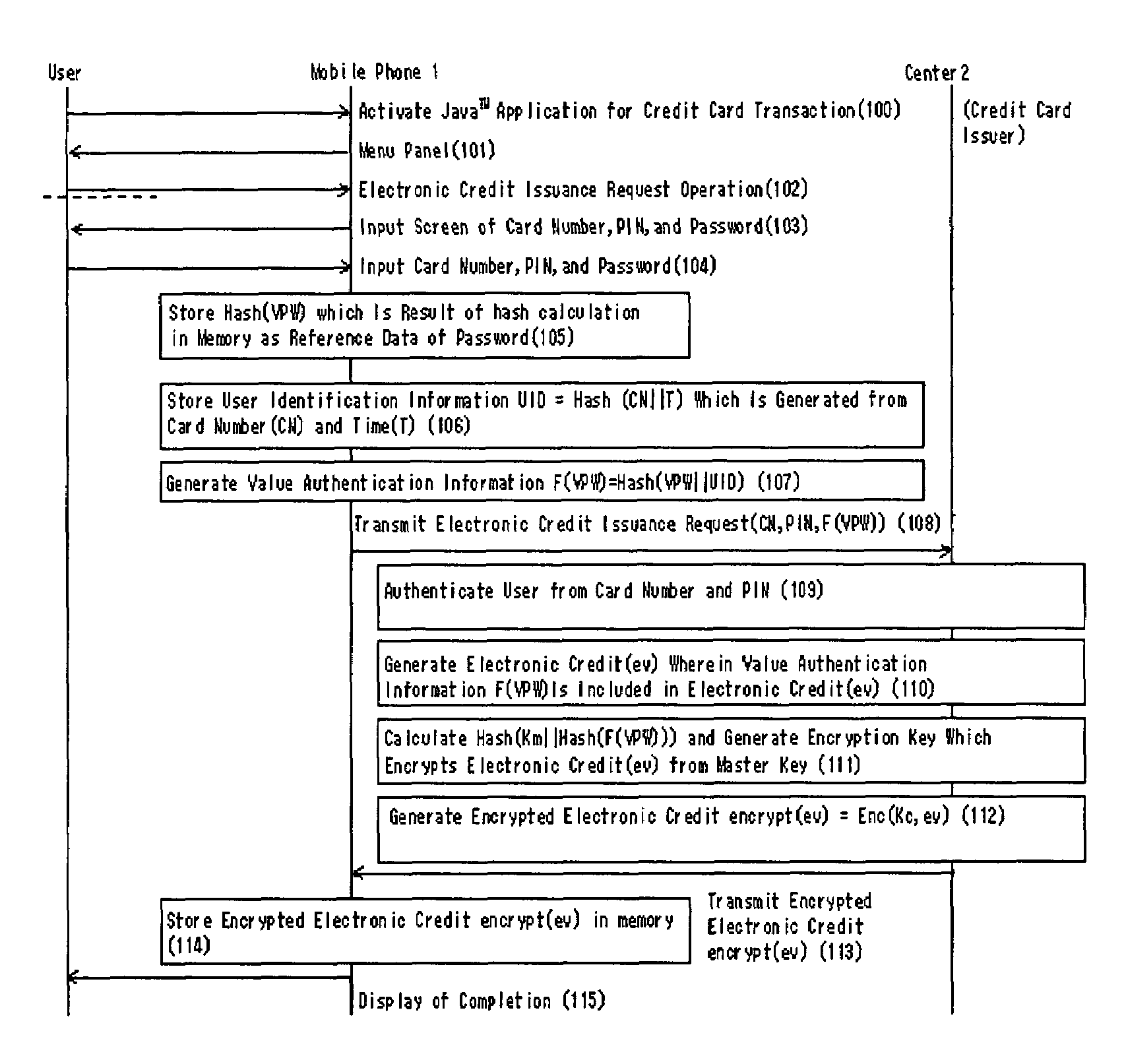
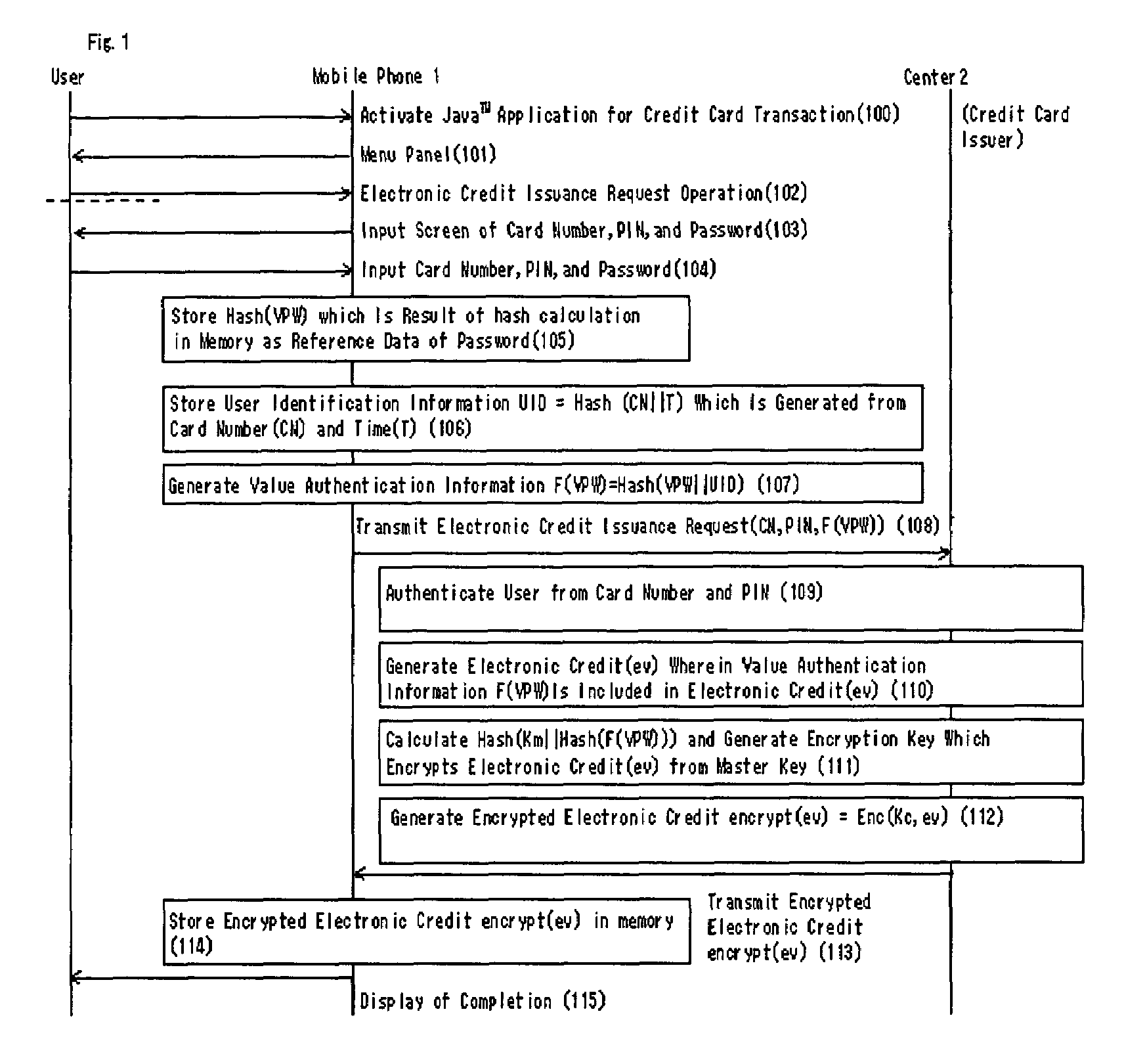
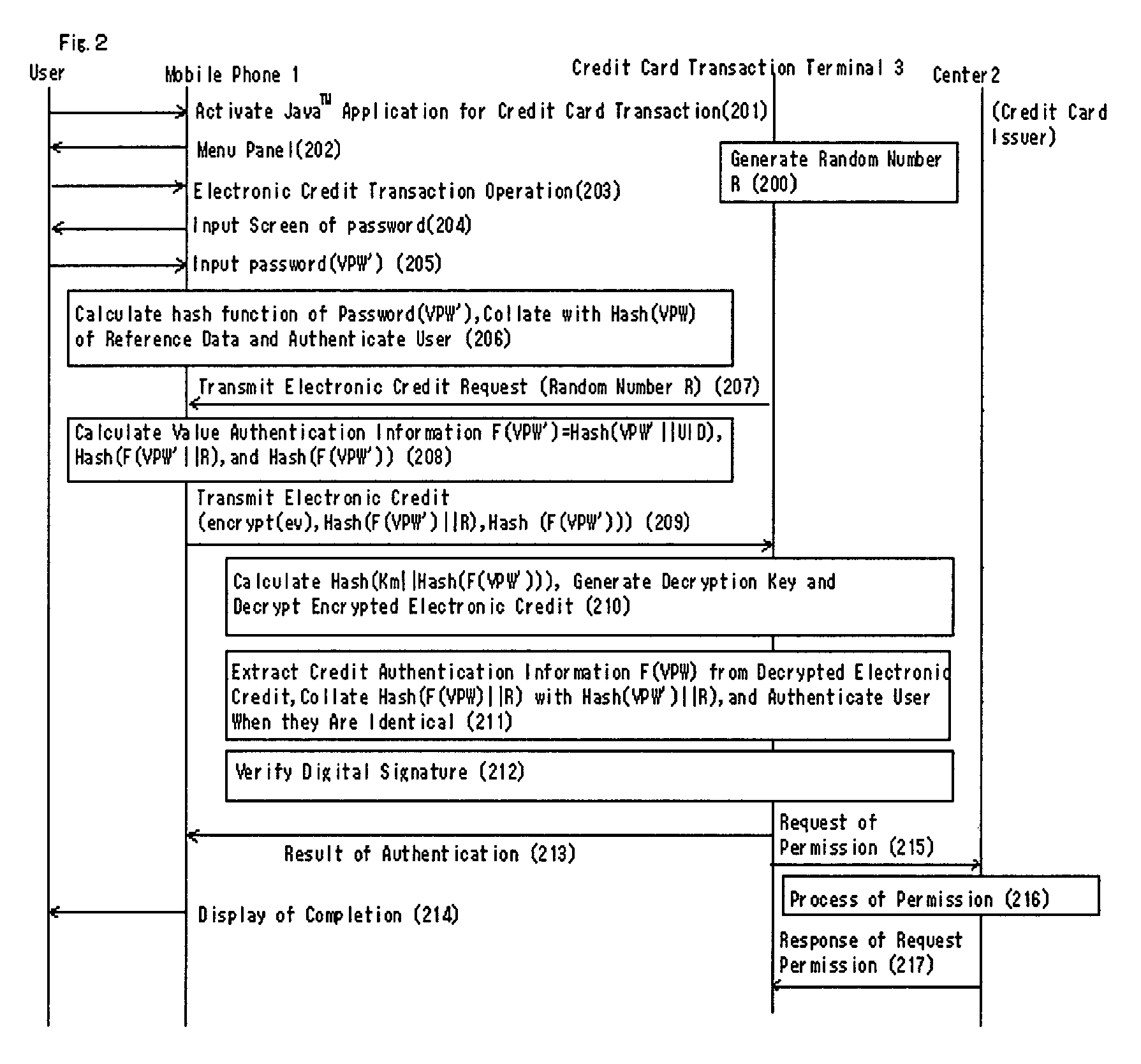
Authentication method, system and apparatus of an electronic value
ActiveUS7325132B2Improve securityAuthenticate the user safelyKey distribution for secure communicationUser identity/authority verificationUser inputUser authentication
An authentication system providing a safety authentication process of electronic values with the use of mobile terminals which do not have a tamper-resistant function. The electronic value including encrypted value authentication information (F(VPW)), wherein an authentication information (VPW) corresponding to an electronic value specified by a user is acquired by the hash calculation, is stored in user's mobile terminal. In the user authentication process; authentication apparatus generates a random number R and transmits it to mobile terminal, mobile terminal generates value authentication information (F(VPW′)) from authentication information (VPW′) corresponding to electronic value input by user, further executes a hash calculation on data wherein value authentication information (F(VPW′)) and the random number R are concatenated, generates authentication information (F(VPW′)∥R), transmits it to the authentication apparatus with the electronic value, authentication apparatus decrypts the received electronic value, extracts the value authentication information (F(VPW)) from the electronic value, executes the hash calculation on data wherein value authentication information (F(VPW)) and the random number R are concatenated, generates the authentication information (F(VPW)∥R), and collates the received authentication information (F(VPW′)∥R) with the authentication information (F(VPW)∥R), so that the user is authenticated.
Owner:INTERTRUST TECH CORP
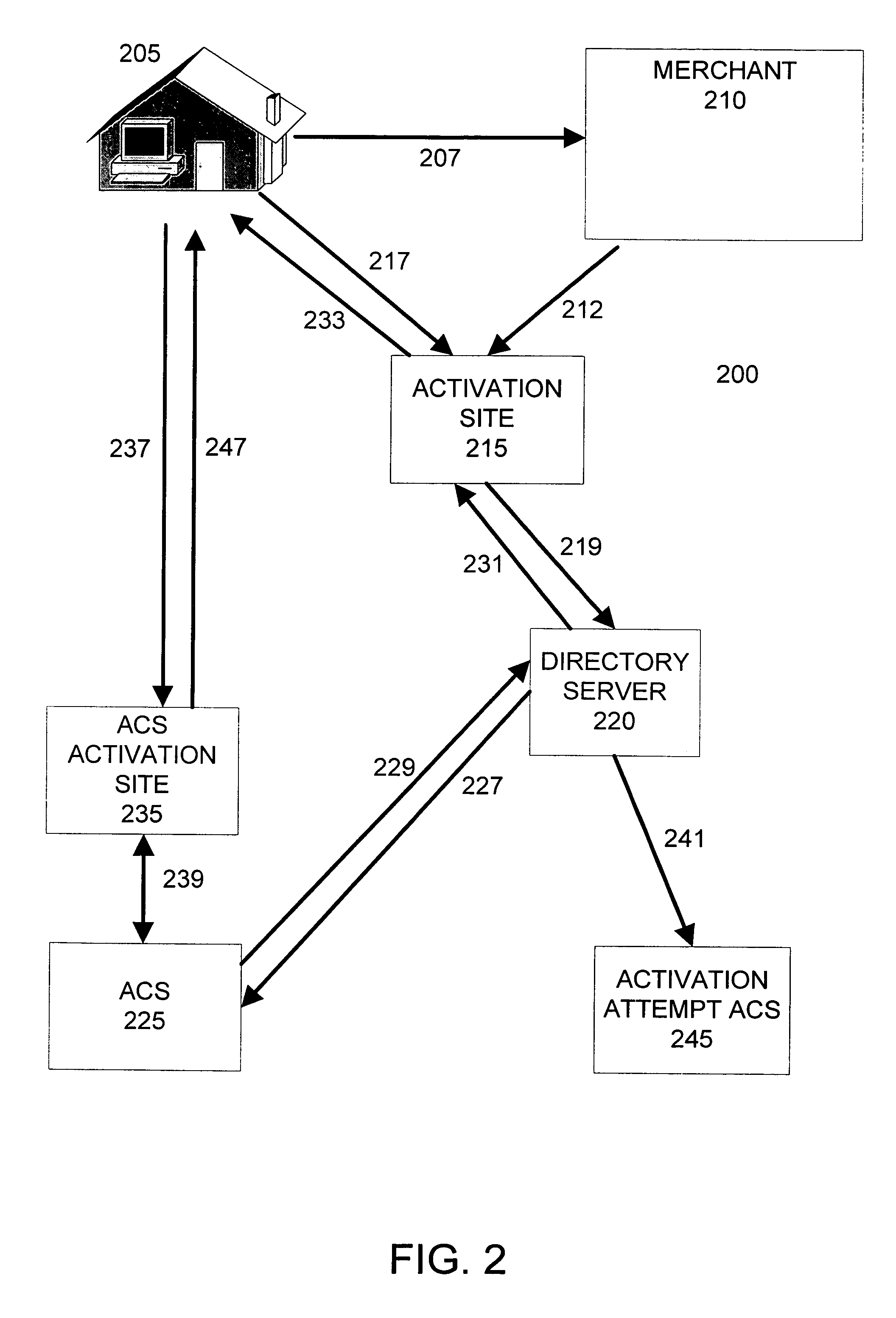
Managing activation of cardholders in a secure authentication program
Owner:VISA USA INC (US)
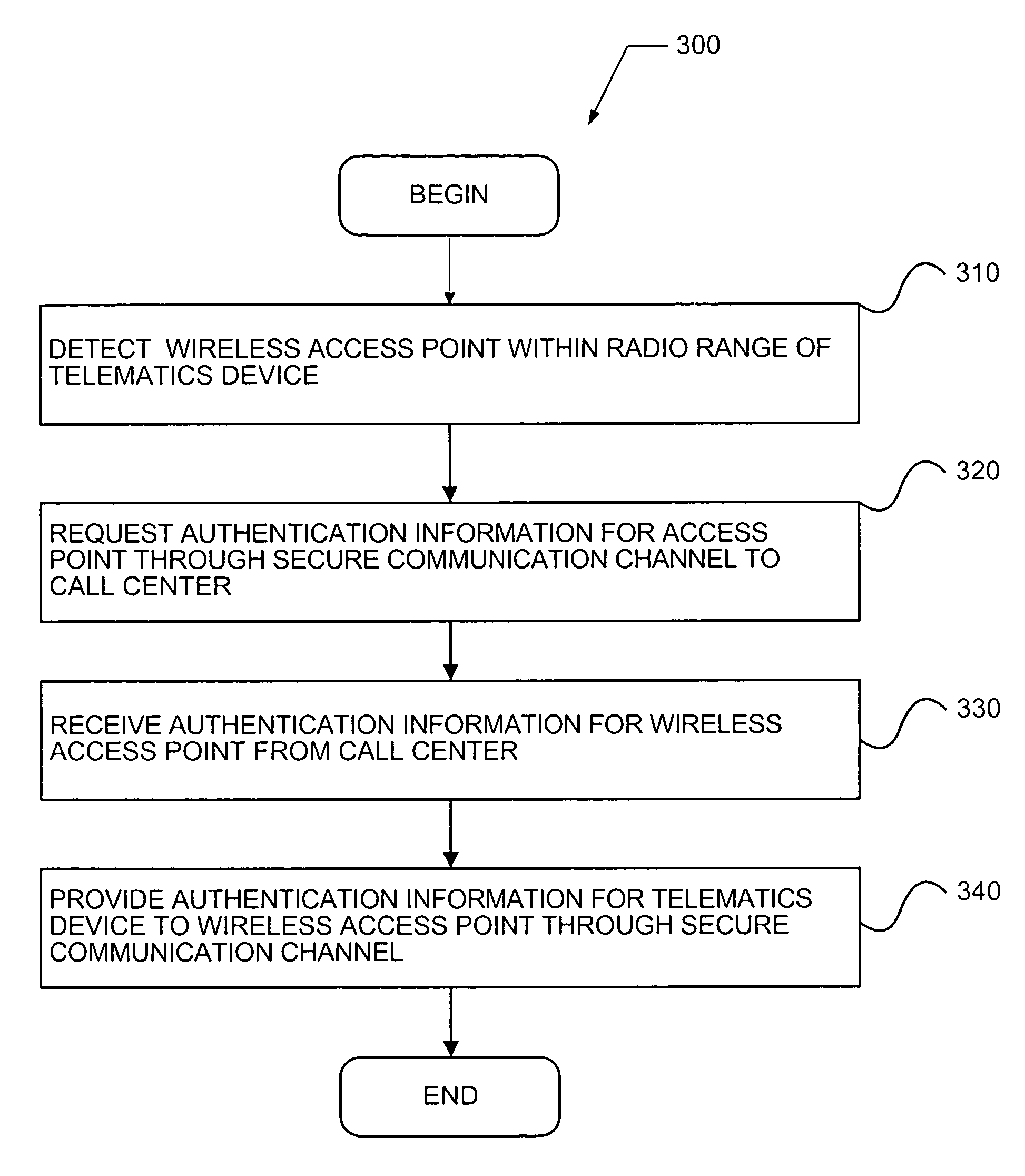
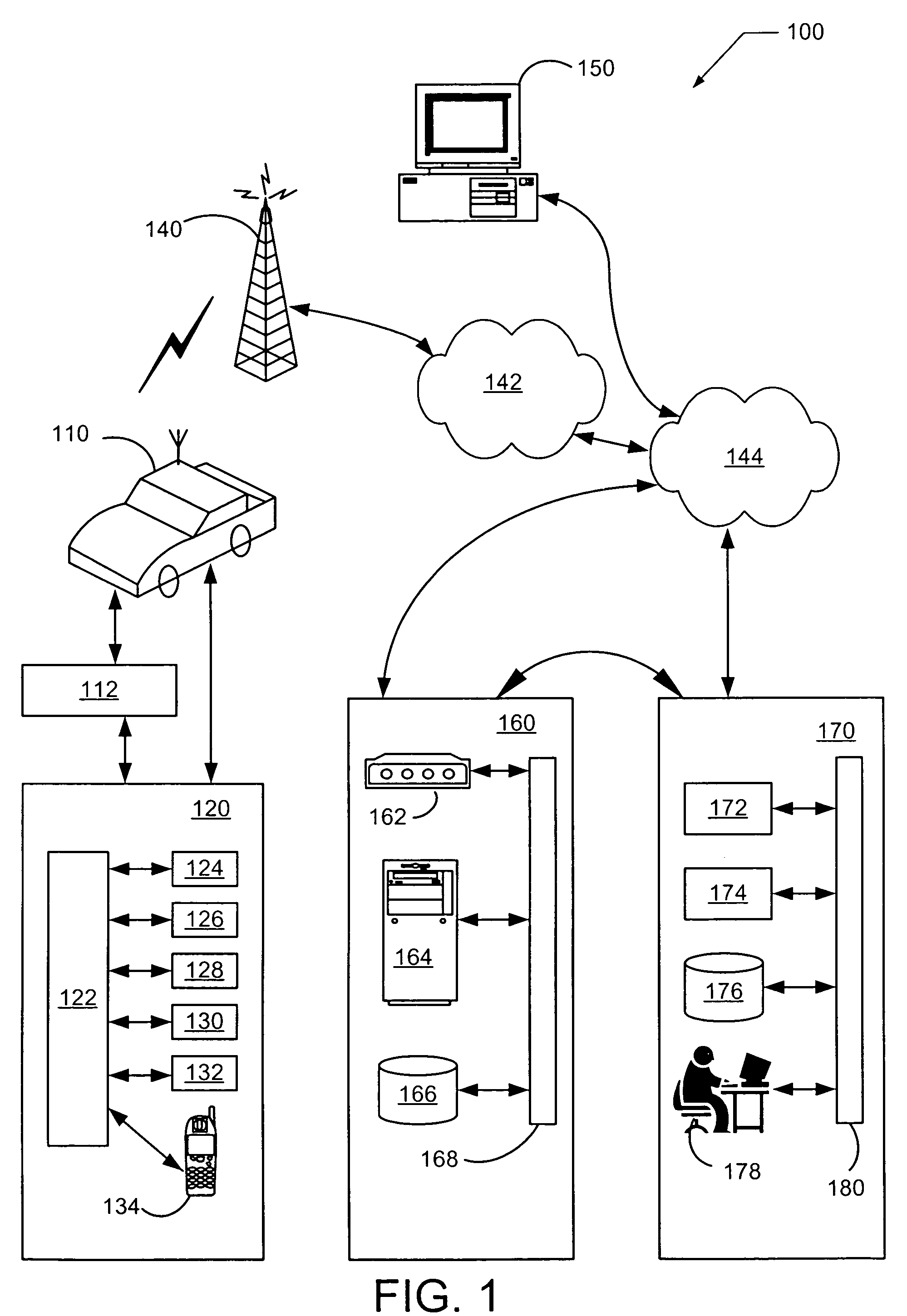
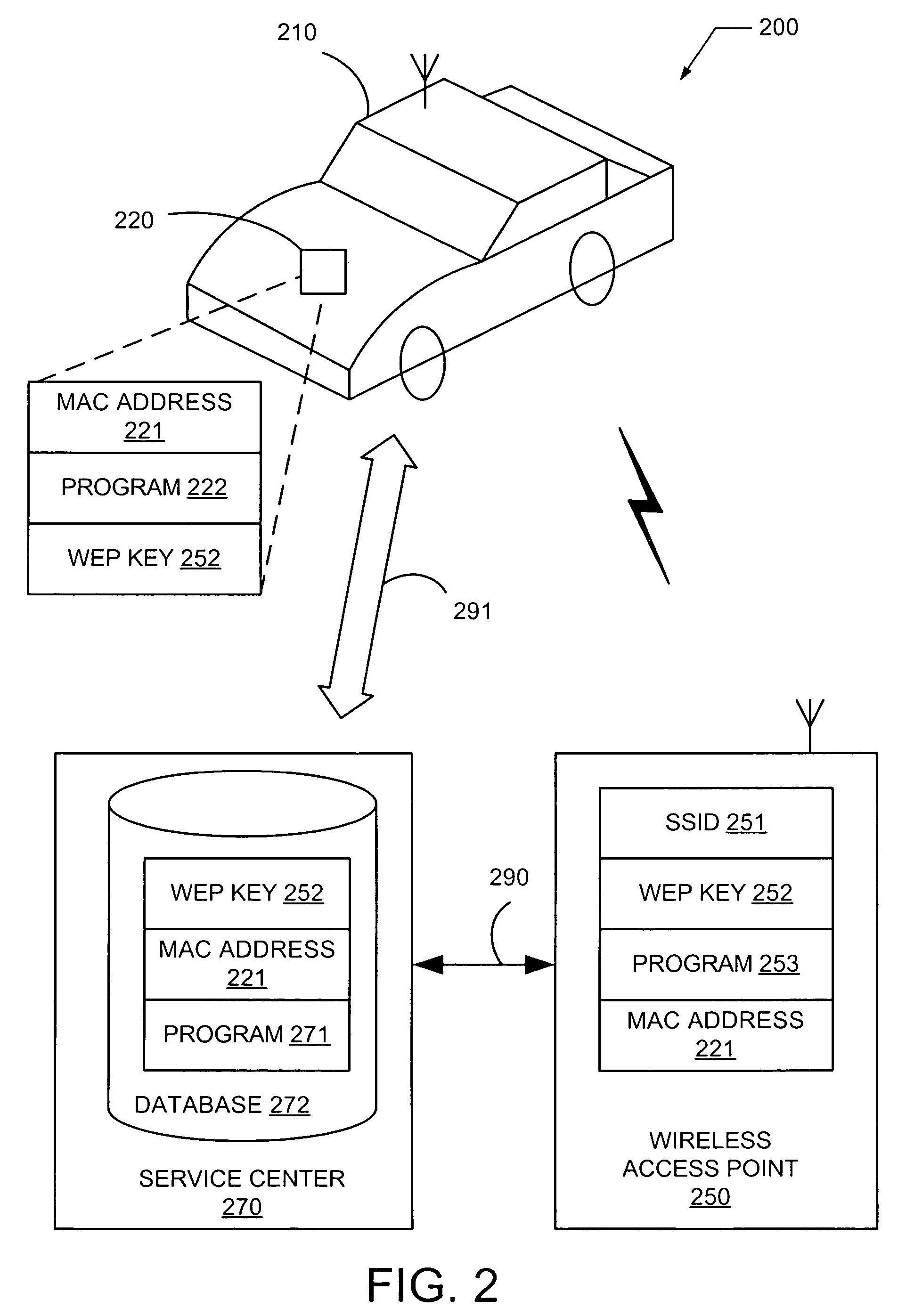
WIFI authentication method
ActiveUS7548744B2Unauthorised/fraudulent call preventionEavesdropping prevention circuitsSecure authenticationTelematics
A system and method provides secure authentication of a wireless communication channel for a vehicle telematics device that includes detecting a wireless access point within radio range of a telematics device, requesting authentication information for the access point through a first secure communication channel to a call center, receiving authentication information for the wireless access point from the call center through the first secure communication channel, and providing authentication information for the telematics device to the wireless access point through a second secure communication channel. A computer readable medium storing a computer program is described for implementing one or more steps of the method.
Owner:GENERA MOTORS LLC
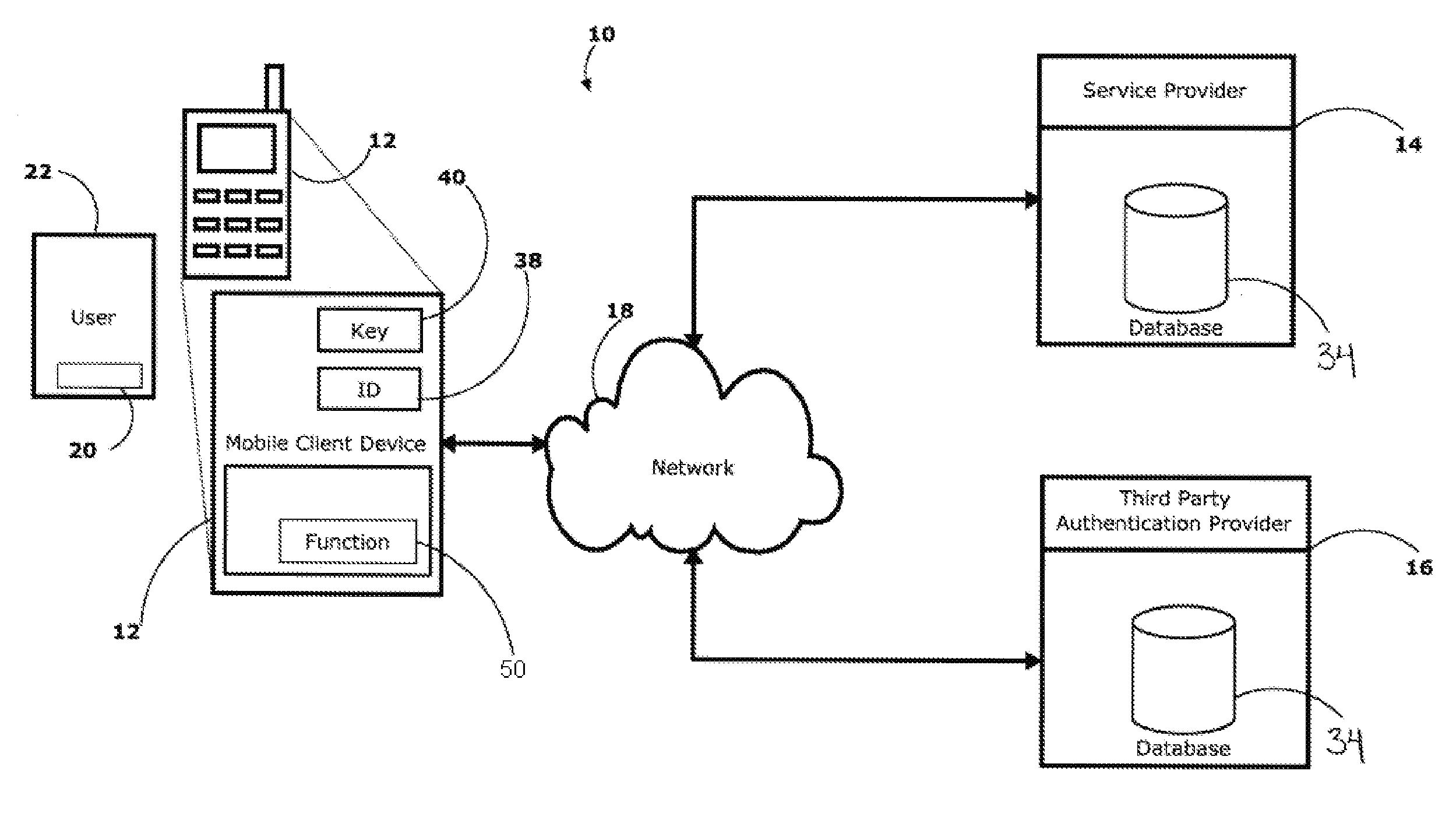
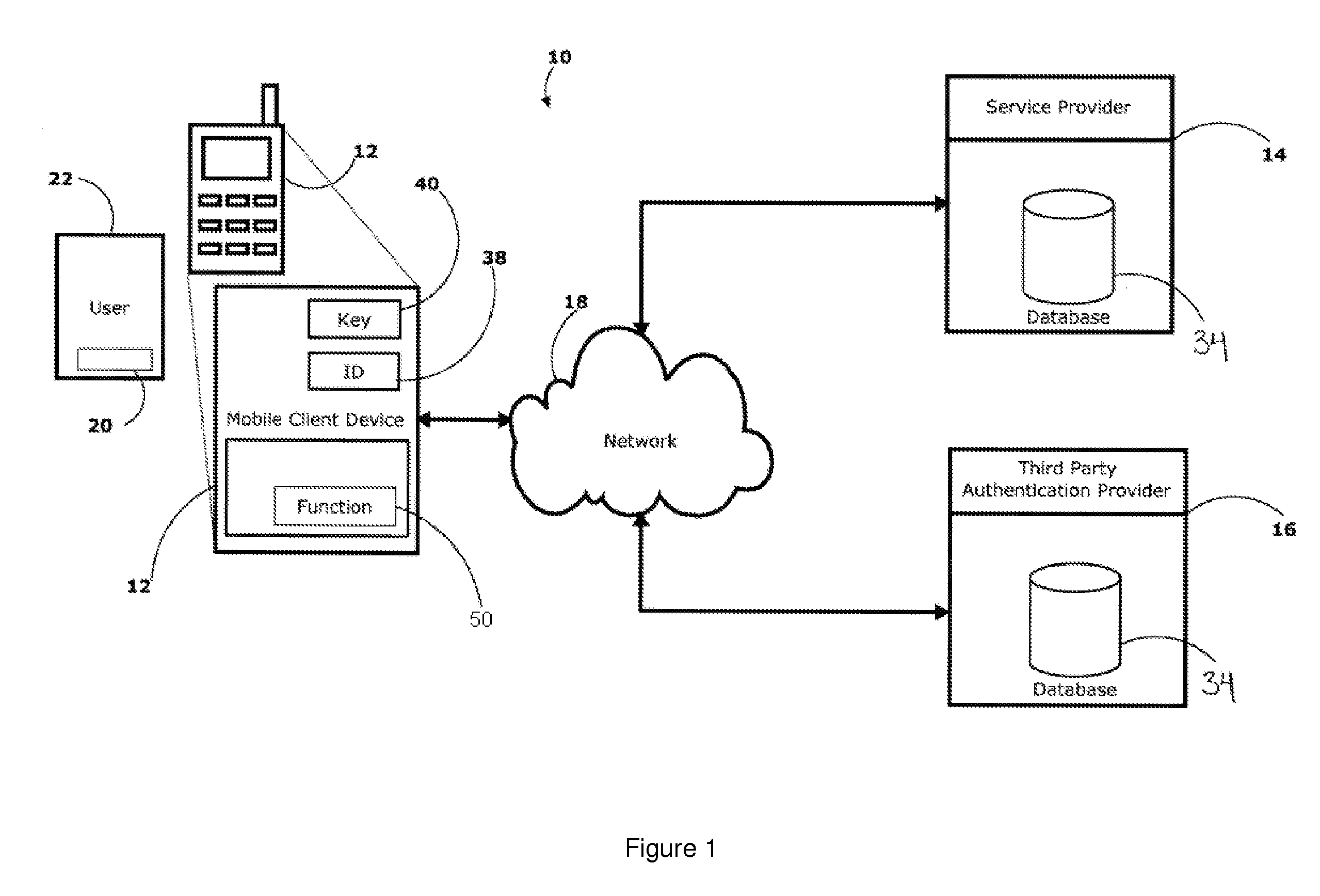
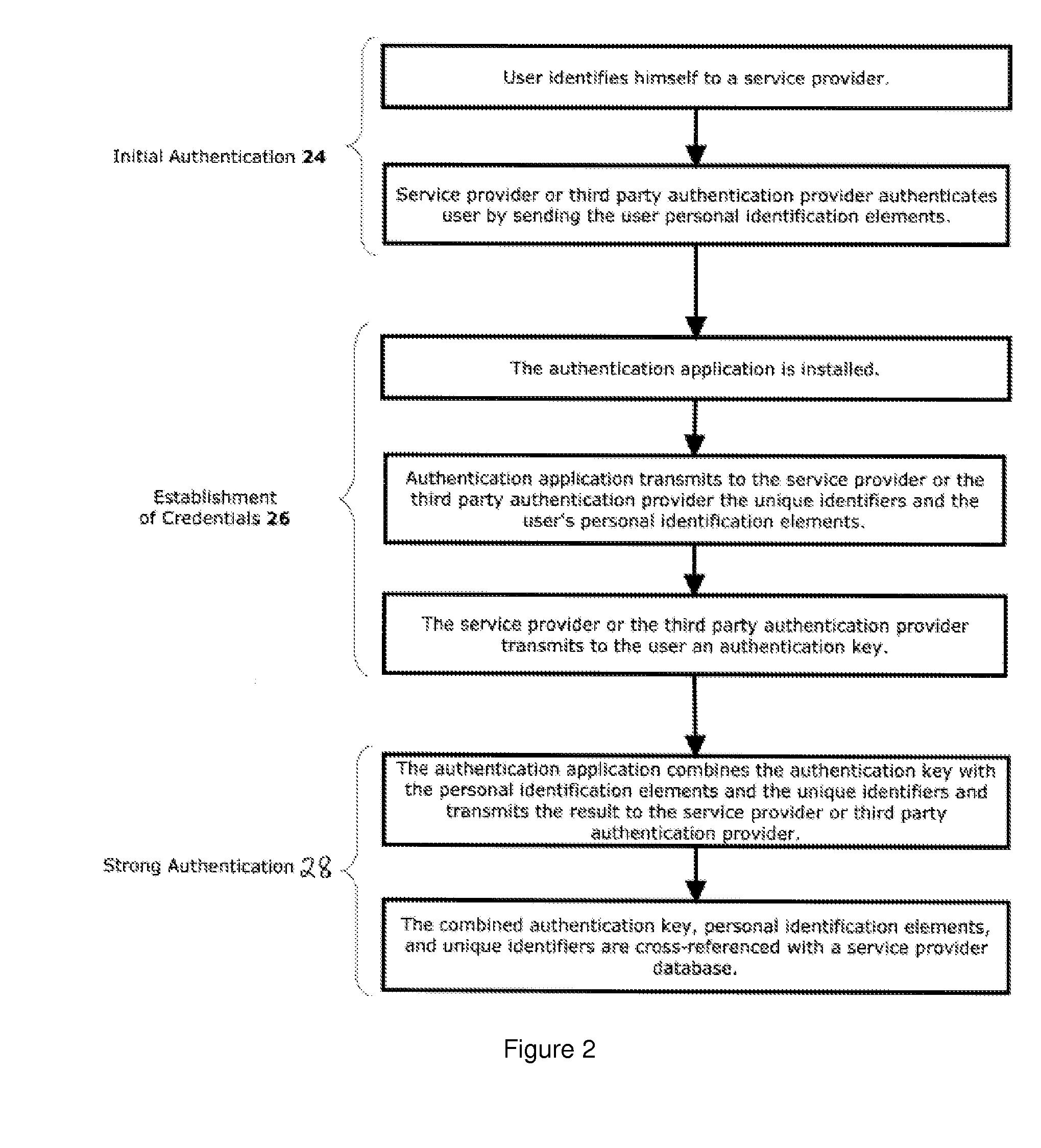
Secure authentication system and method
InactiveUS20110197267A1Digital data processing detailsUser identity/authority verificationWeb authenticationInternet privacy
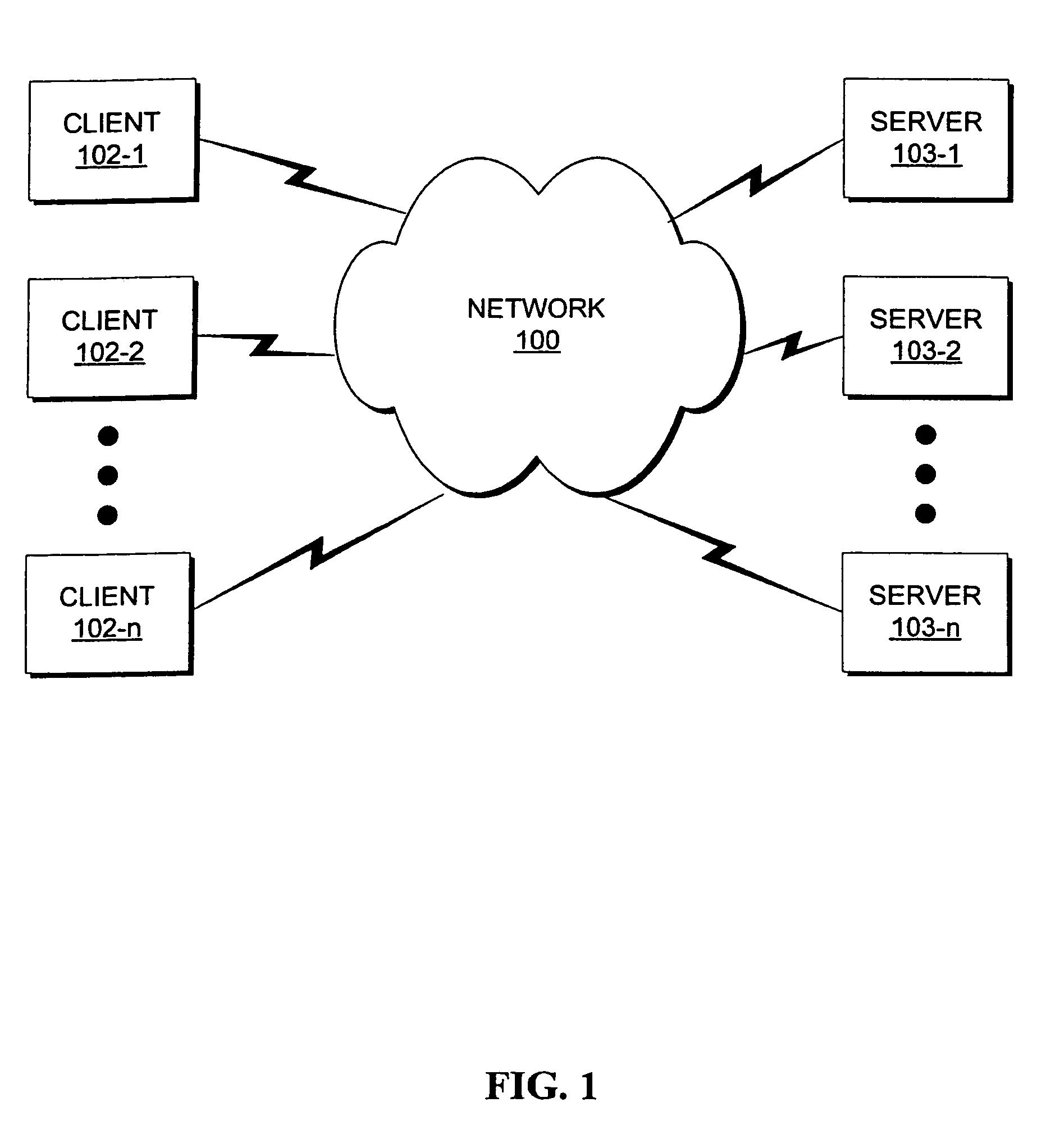
There is disclosed a system and method for authenticating the identity of a user of a client device as part of a transaction between the client device and a server of a service provider over a communications network, the client device comprising a unique identifier. The system and method comprise one or more personal identification elements issued to the user based upon an initial authentication of the identity of the user, a credential issued to the client device by the service provider based upon the personal identification elements and the unique identifiers, and a trigger event for launching an authentication application installed on the client device. When the authentication application is launched by the trigger event, the authentication application transmits the one or more personal identification elements and the unique identifier in a combination with the credential to the server for authentication by the service provider.
Owner:LIPSO SYST INC
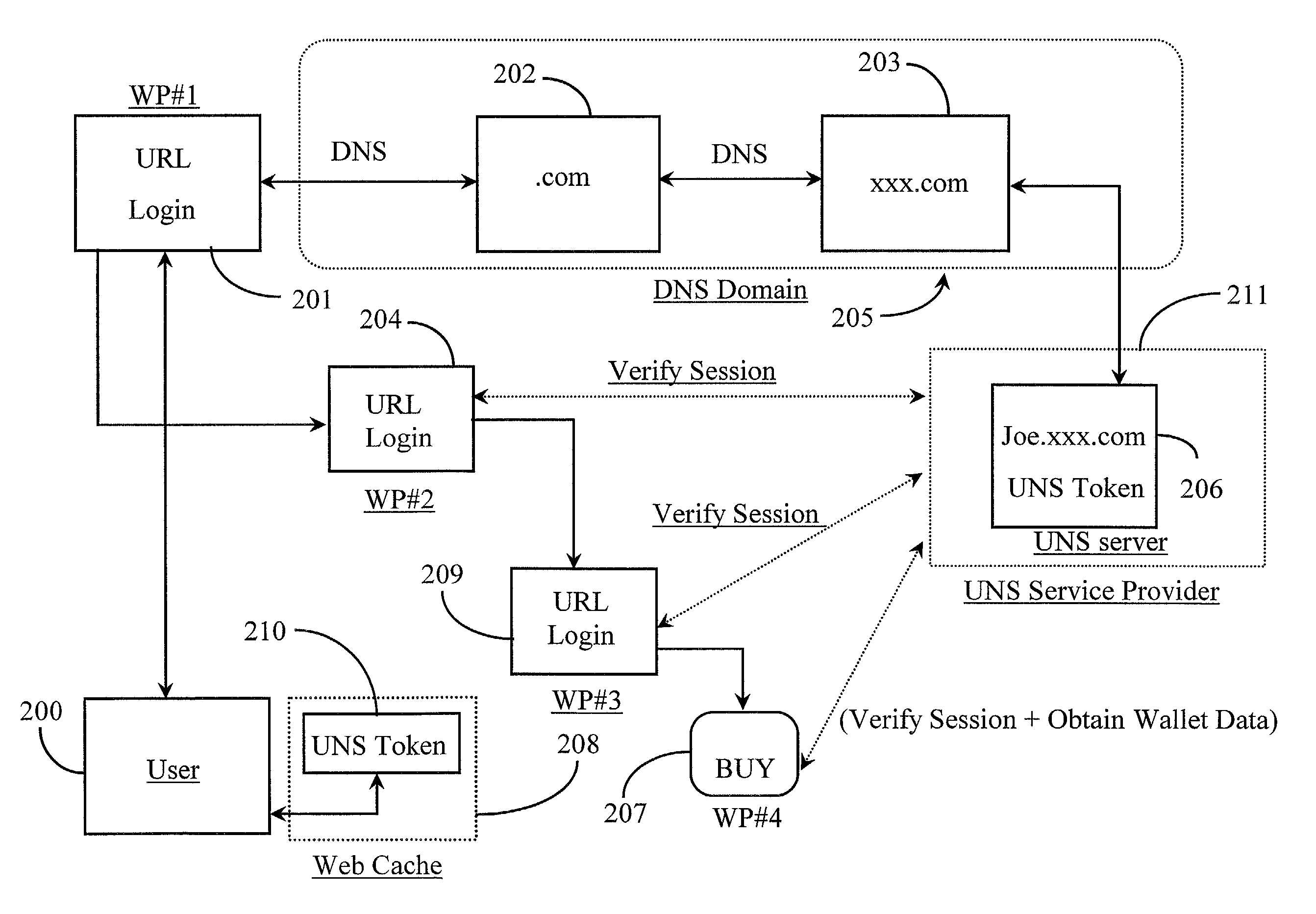
Method for verifying the identity of a user for session authentication purposes during Web navigation
ActiveUS7225464B2Digital data processing detailsMultiple digital computer combinationsWeb siteWeb navigation
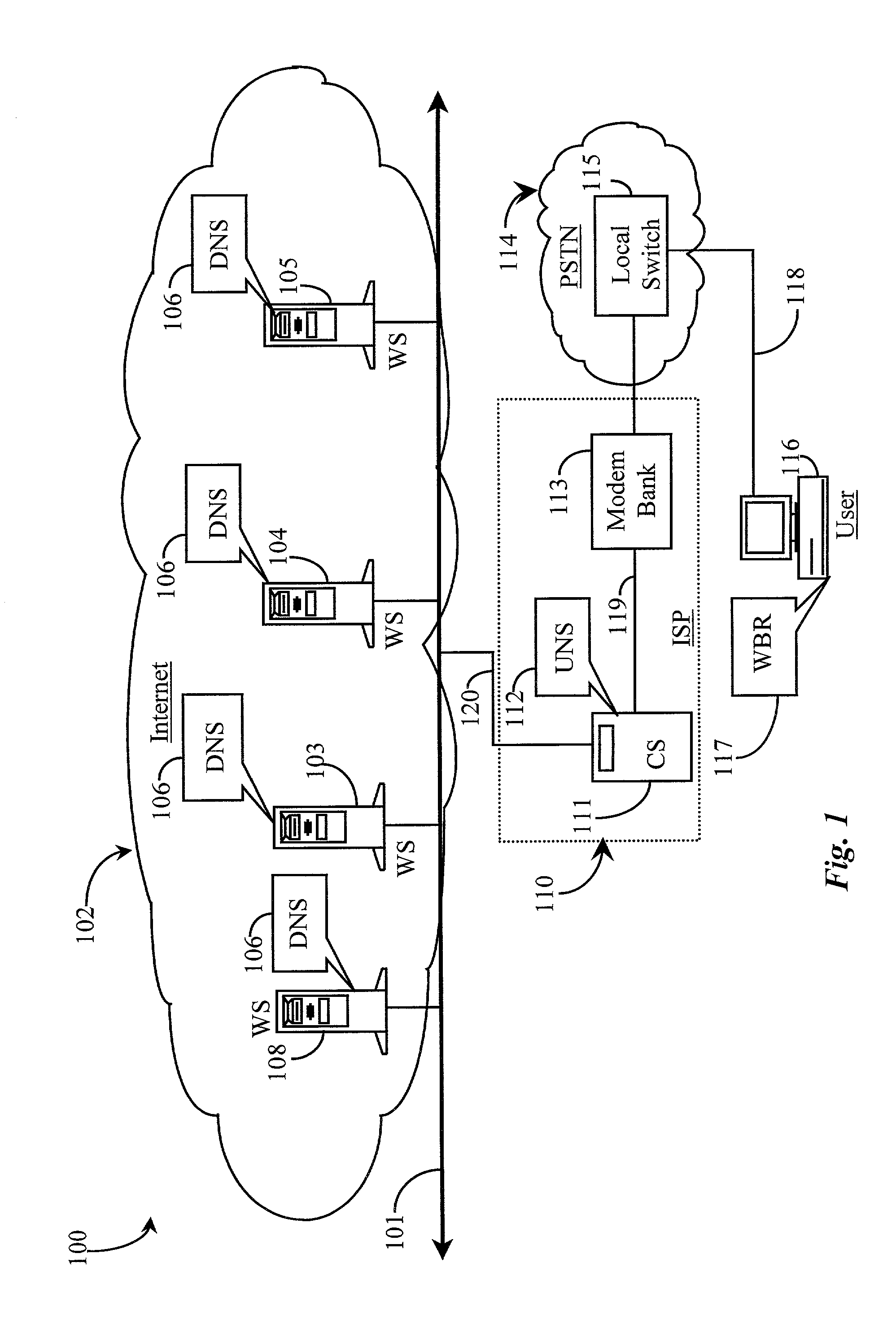
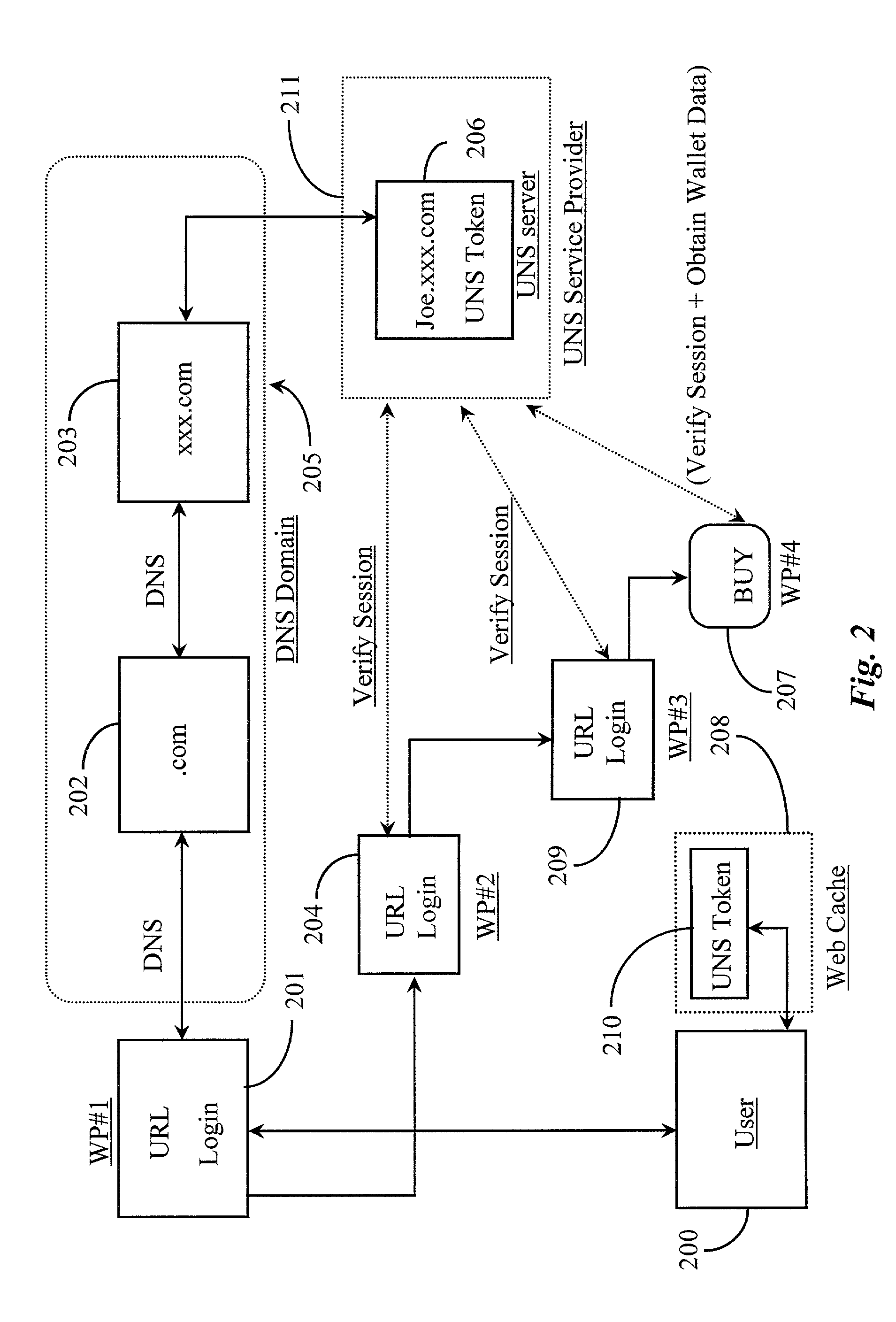
A network-based software application for enabling remote authentication of a user during a network session has a server portion for serving session validation information and additional user information when queried, a client portion for configuring and submitting parameters constraining what and how data is to be shared with a querying entity or entities, and a distributed portion for distribution and application at various connected network nodes for enabling those nodes to recognize and interact with the server portion. The application is characterized in that the server portion generates a temporary session token after a first successful authentication by the user at a web site during a network session, the token cached at the host machine of the server portion and at the user's machine or proxy machine and wherein upon navigation by the user to a next web site or form requiring secure authentication, the token is used to identify the user and a remote call is used to validate the user session instead of requiring manual authentication procedures.
Owner:YODLEE COM INC
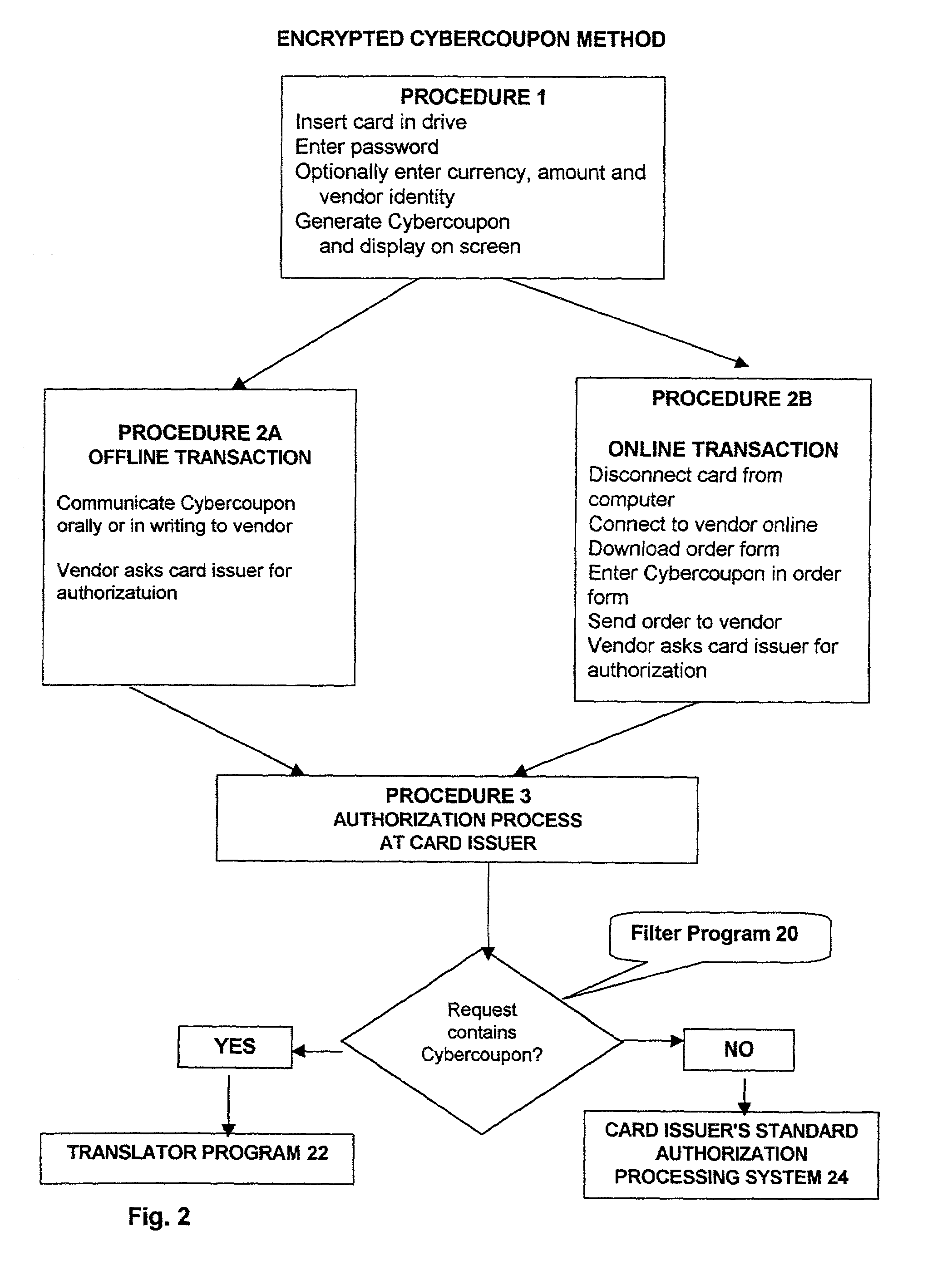
Method for preventing fraudulent use of credit cards and credit card information, and for preventing unauthorized access to restricted physical and virtual sites
InactiveUS7003501B2Preventing fraudulent card transactionOvercome disadvantagesPublic key for secure communicationSecret communicationComputer hardwareCredit card
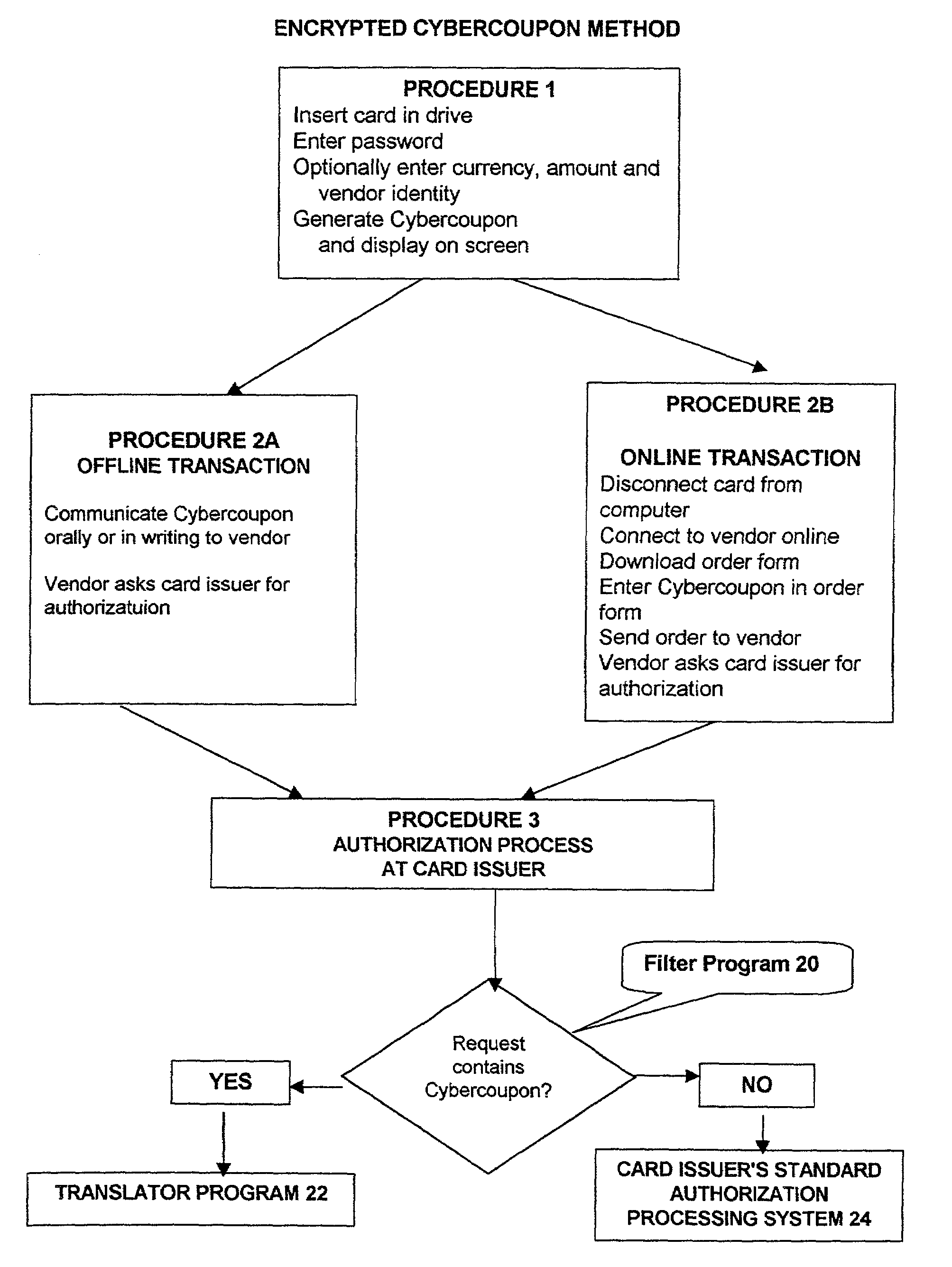
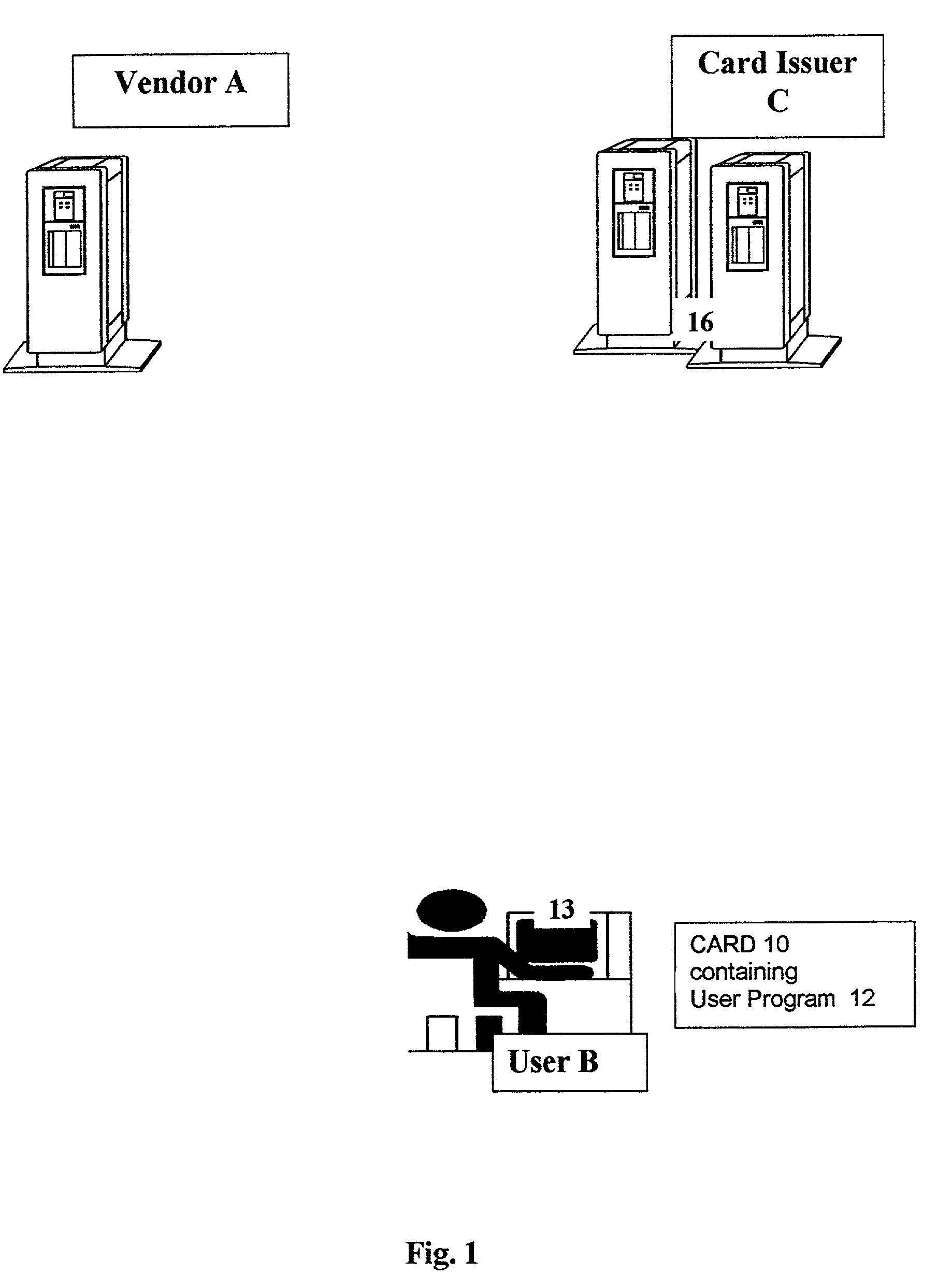
A method and a system for enabling secure authentication of a user in a computerized card access transaction. A card, identified by an identification number is issued to the user, containing software for generating a surrogate number referred to as a Cybercoupon for use in place of the regular card number. Online intrusion is avoided and the system is rendered portable for use on any computer equipped with a compatible operating system, by avoiding storage of any part of the system on the user's computer, placing the entire system instead on the card itself. The card contains advertising which appears on the user's computer screen. The card is protected by a password. If an incorrect password is entered more than a preset number of times, an “alert” Cybercoupon is generated containing a code advising the card issuer that an irregular attempt has been made to access the card.
Owner:OSTROFF MAURICE
Extending a secure key storage for transaction confirmation and cryptocurrency
PendingUS20190164156A1Key distribution for secure communicationSynchronising transmission/receiving encryption devicesInternet privacyEngineering
A system, apparatus, method, and machine readable medium are described for secure authentication. For example, one embodiment of a system comprises: an authenticator on a client device to securely store one or more private keys, at least one of the private keys usable to authenticate a block of a blockchain; and an attestation module of the authenticator or coupled to the authenticator, the attestation module to generate a signature using the block and the private key, the signature usable to attest to the authenticity of the block by a device having a public key corresponding to the private key.
Owner:NOK NOK LABS
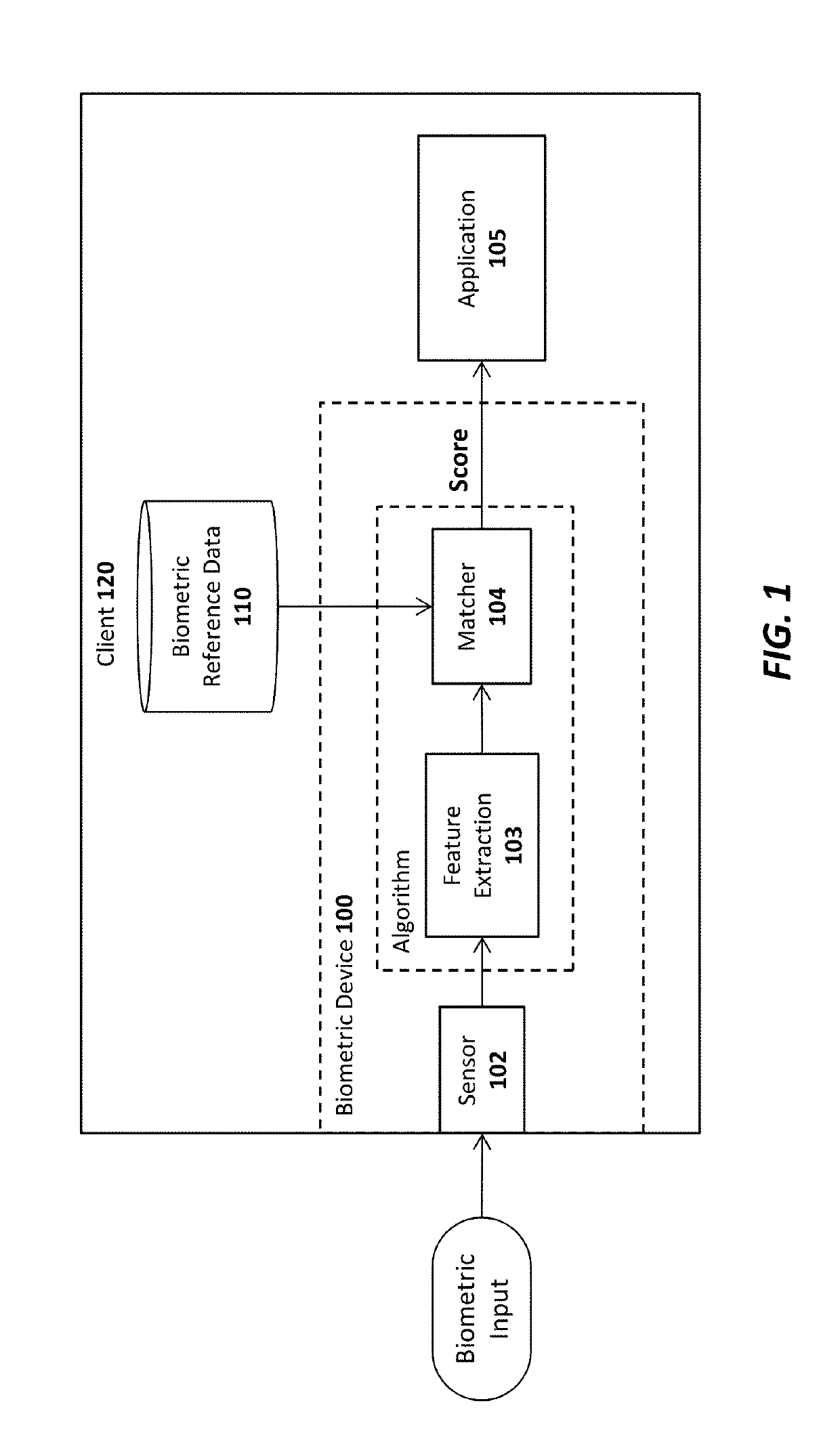
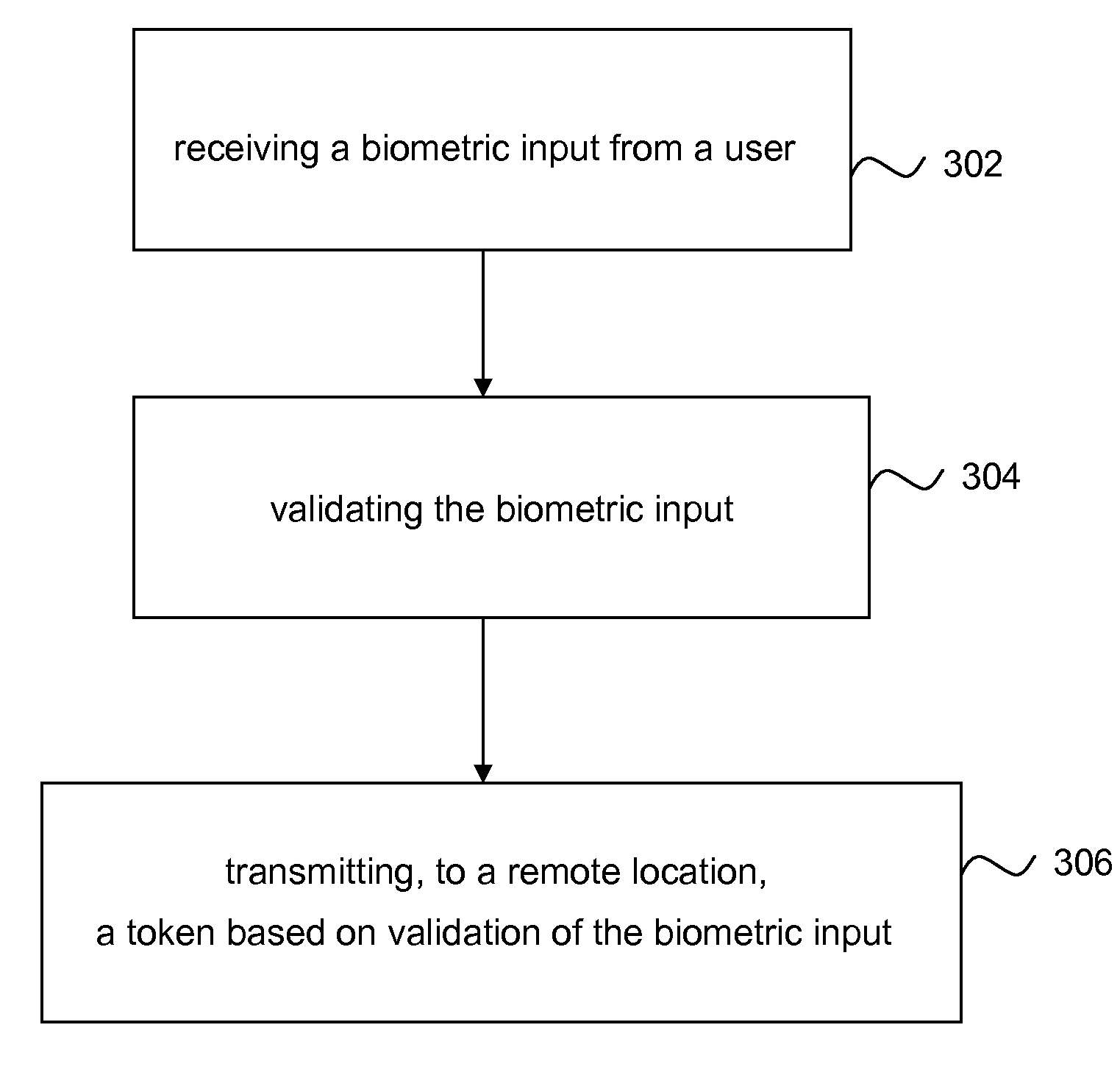
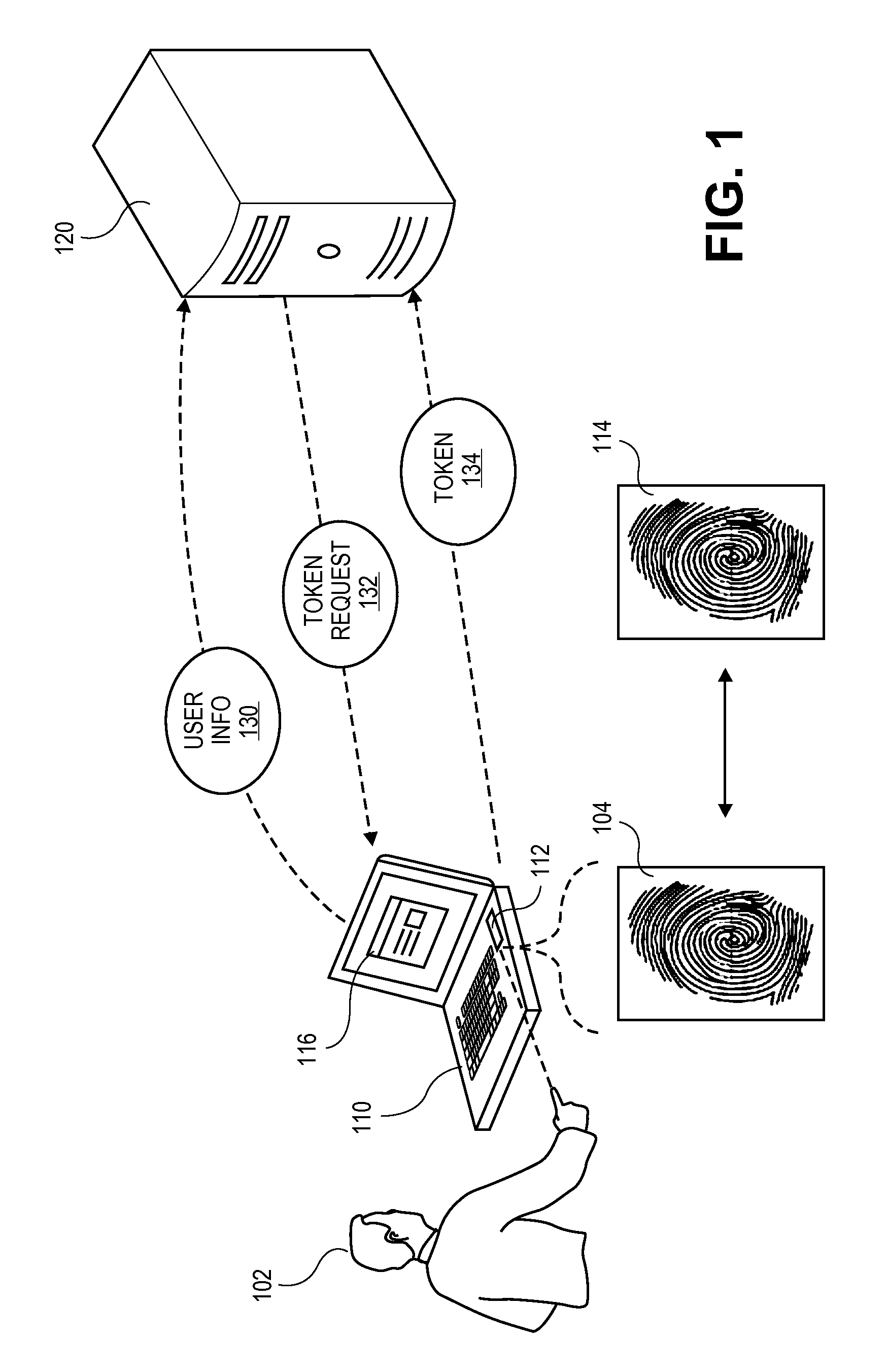
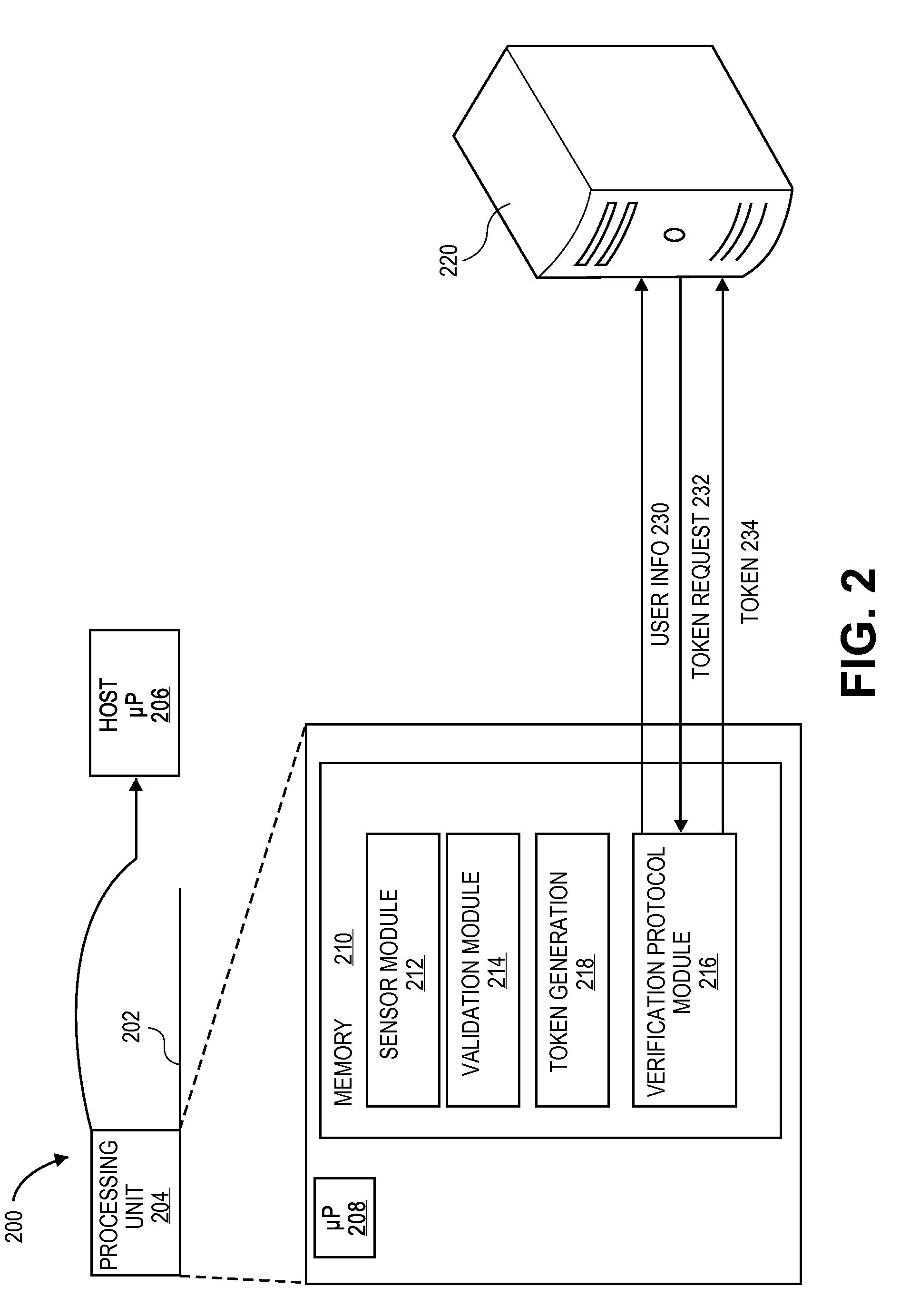
Fingerprint Sensor Device and System with Verification Token and Methods of Using
InactiveUS20100083000A1Electric signal transmission systemsDigital data processing detailsValidation methodsSecure authentication
A method and system of verification is provided for sensing a fingerprint. The present invention offers a secure authentication method and system based on a user's fingerprint data to grant the access to information at a remote location. A biometric input corresponding to the fingerprint is provided by a user and the biometric input is than validated. Based on the validation, a token is transmitted to a remote location. The method and system can be further enhanced by additional security comprising receiving a request based on the authentication of the user information and transmitting, to a second remote location, a token based on the biometric input in response to the request.
Owner:SYNAPTICS INC
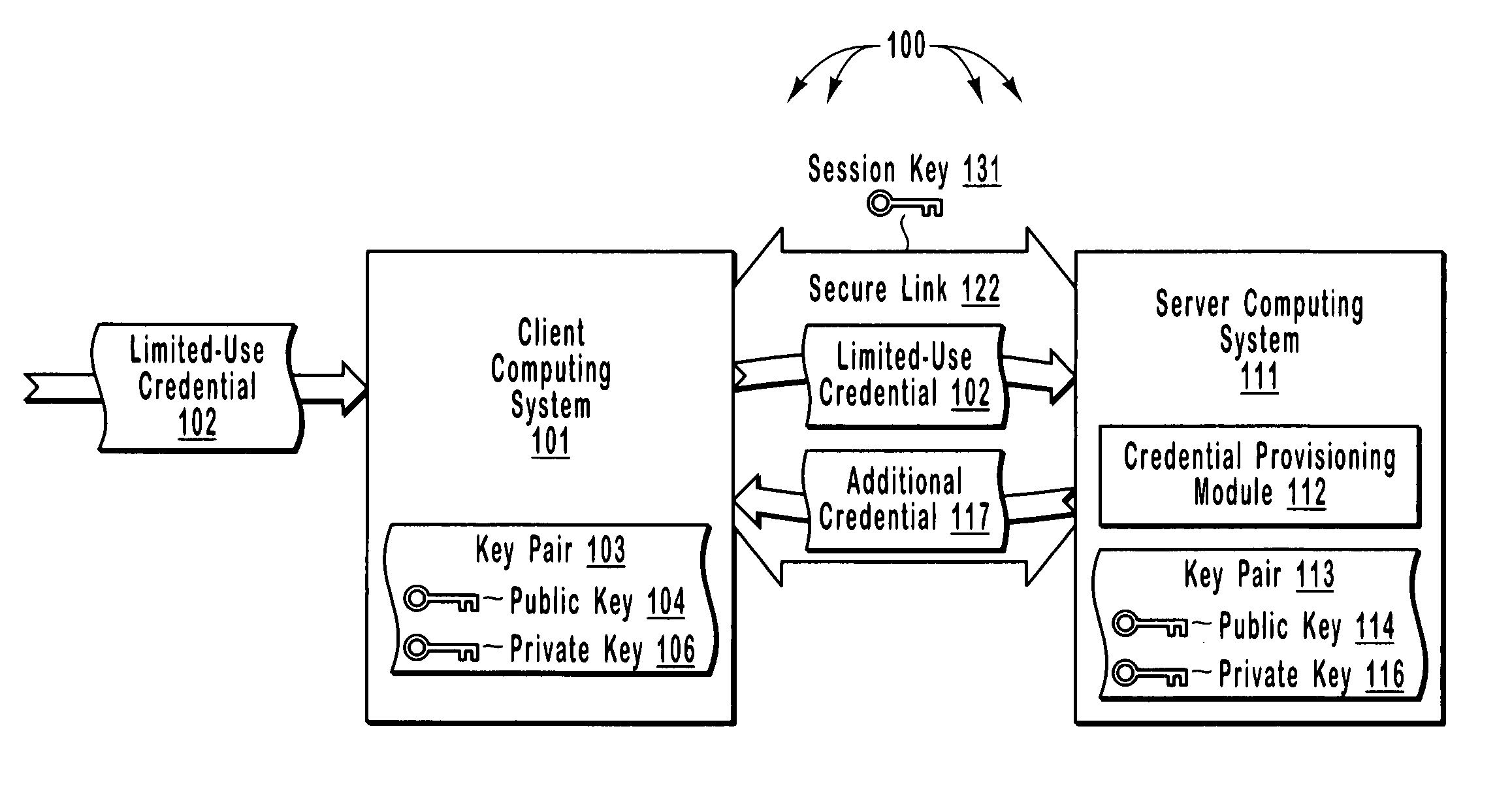
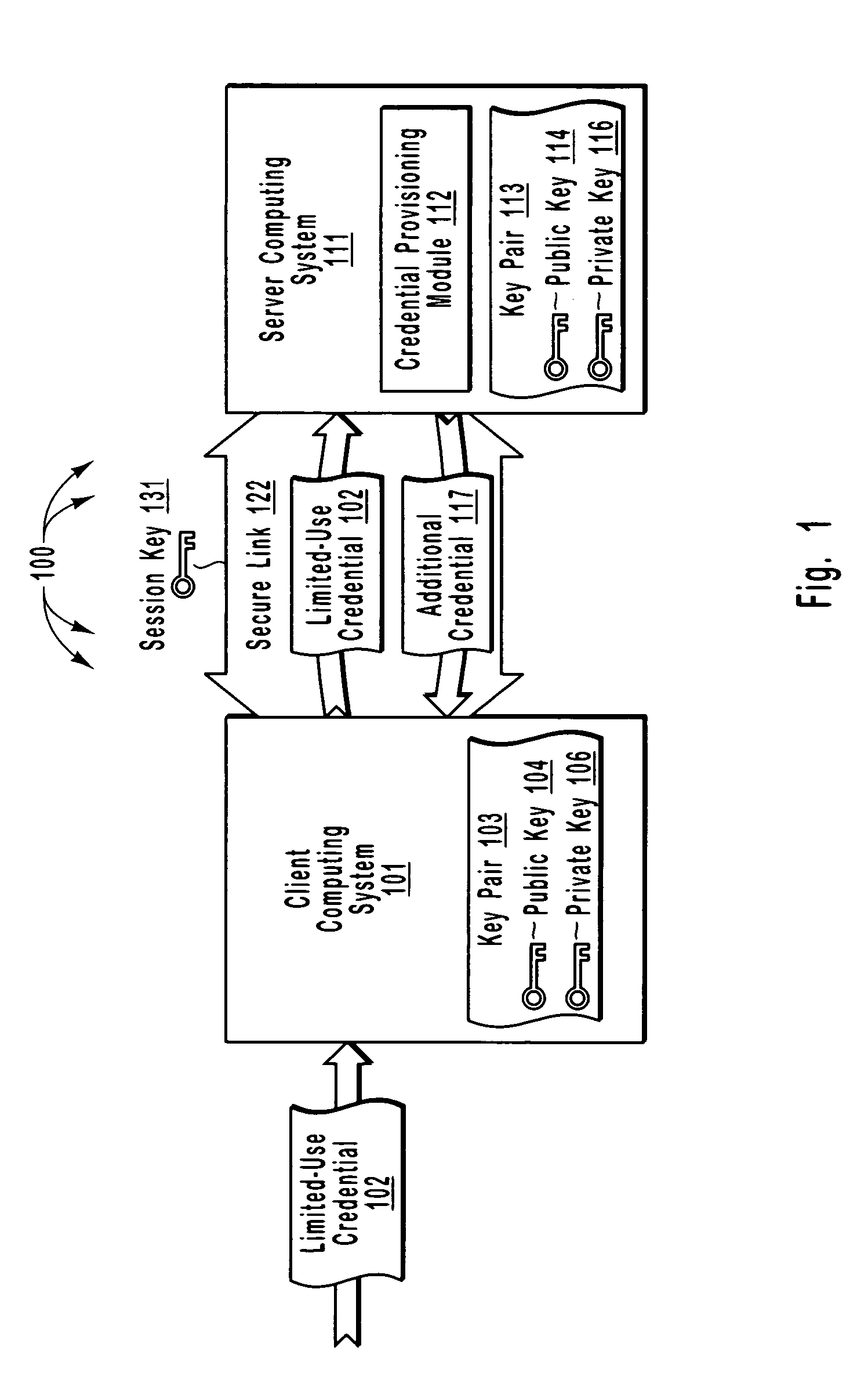
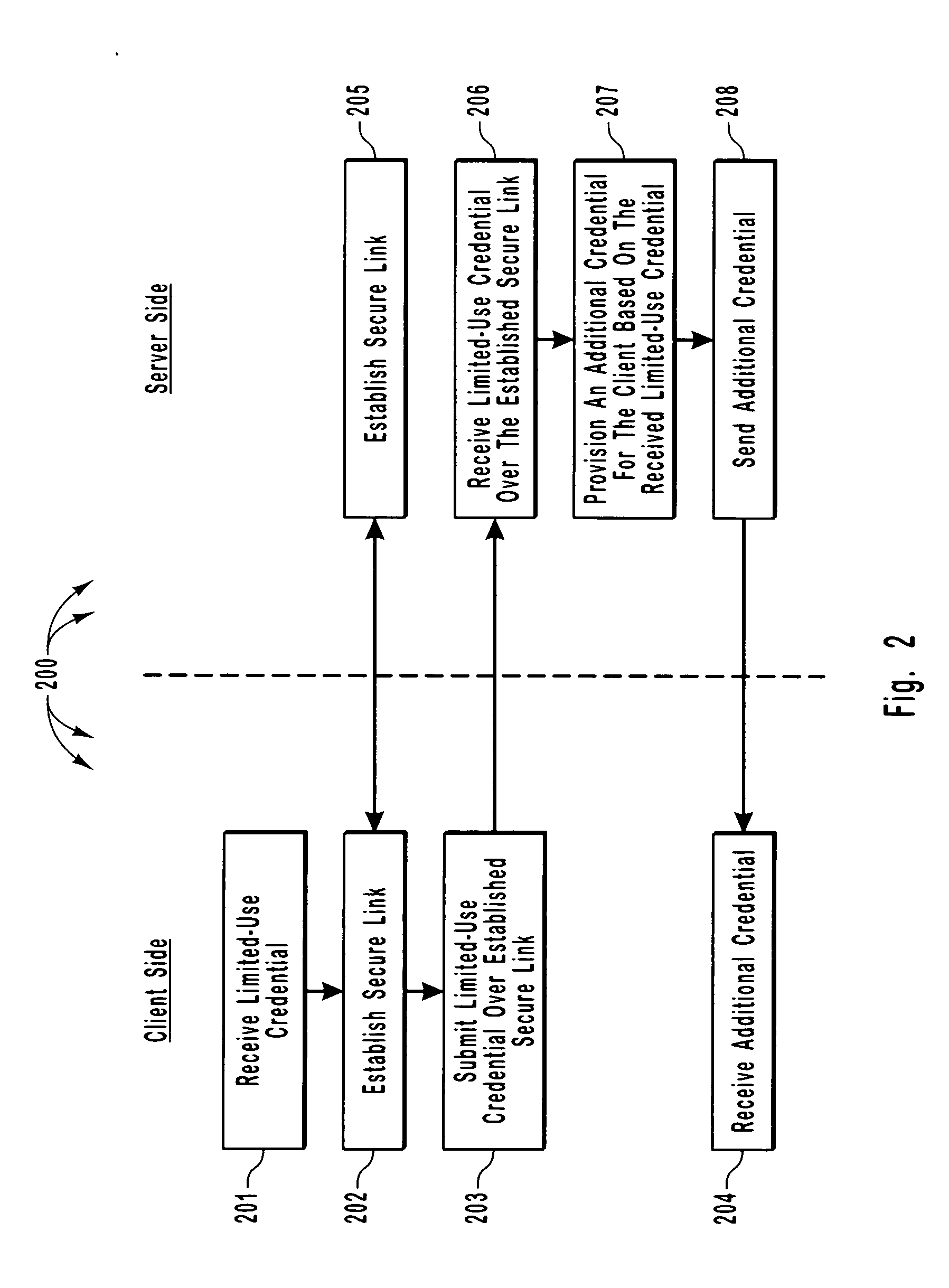
Efficient and secure authentication of computing systems
ActiveUS20050210252A1Efficiently and securely authenticatingKey distribution for secure communicationDigital data processing detailsClient-sideProtocol for Carrying Authentication for Network Access
The principles of the present invention relate to systems, methods, and computer program products for more efficiently and securely authenticating computing systems. In some embodiments, a limited use credential is used to provision more permanent credentials. A client receives a limited-use (e.g., a single-use) credential and submits the limited-use credential over a secure link to a server. The server provisions an additional credential (for subsequent authentication) and sends the additional credential to the client over the secure link. In other embodiments, computing systems automatically negotiate authentication methods using an extensible protocol. A mutually deployed authentication method is selected and secure authentication is facilitated with a tunnel key that is used encrypt (and subsequently decrypt) authentication content transferred between a client and a server. The tunnel key is derived from a shared secret (e.g., a session key) and nonces.
Owner:MICROSOFT TECH LICENSING LLC
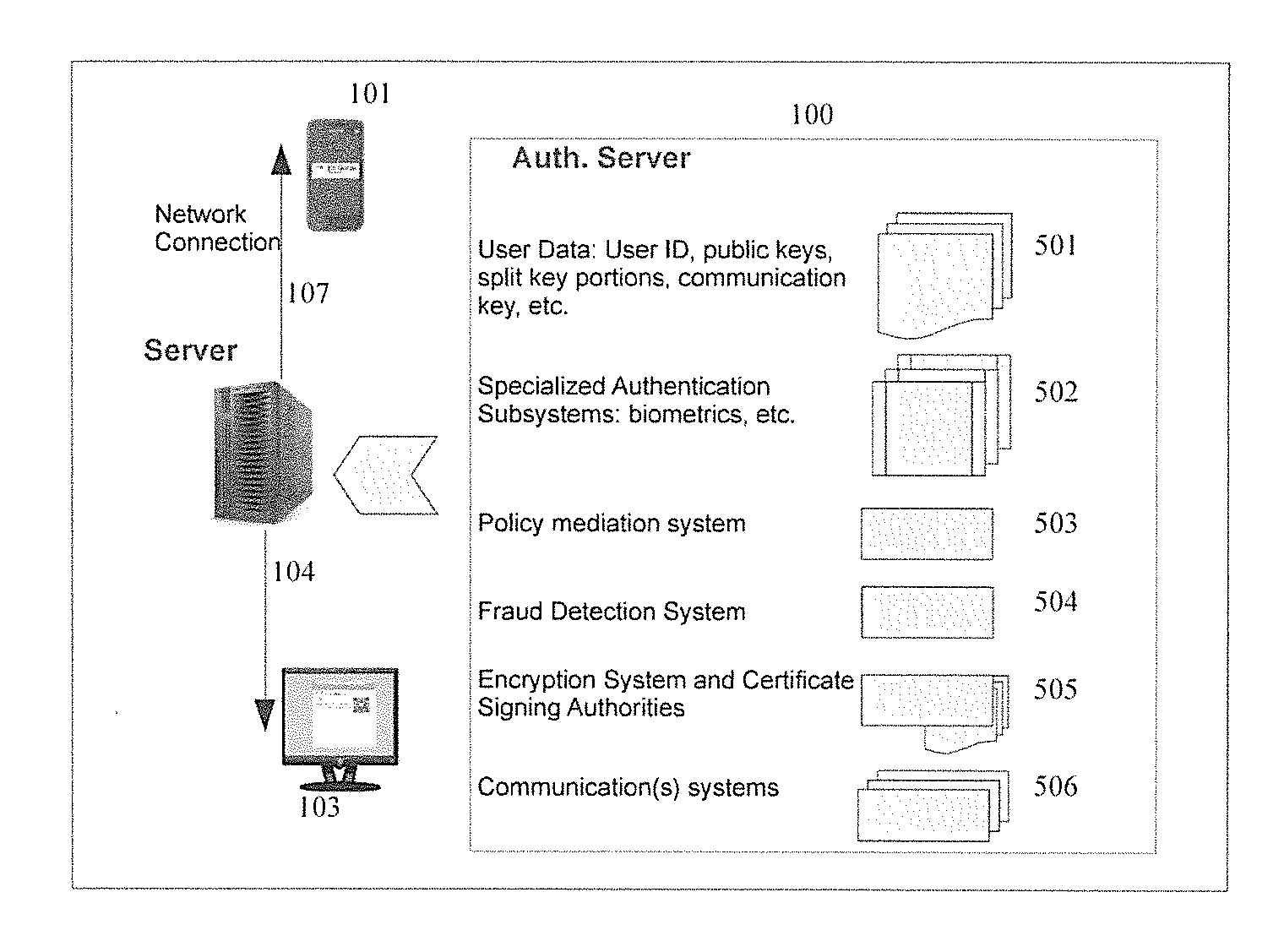
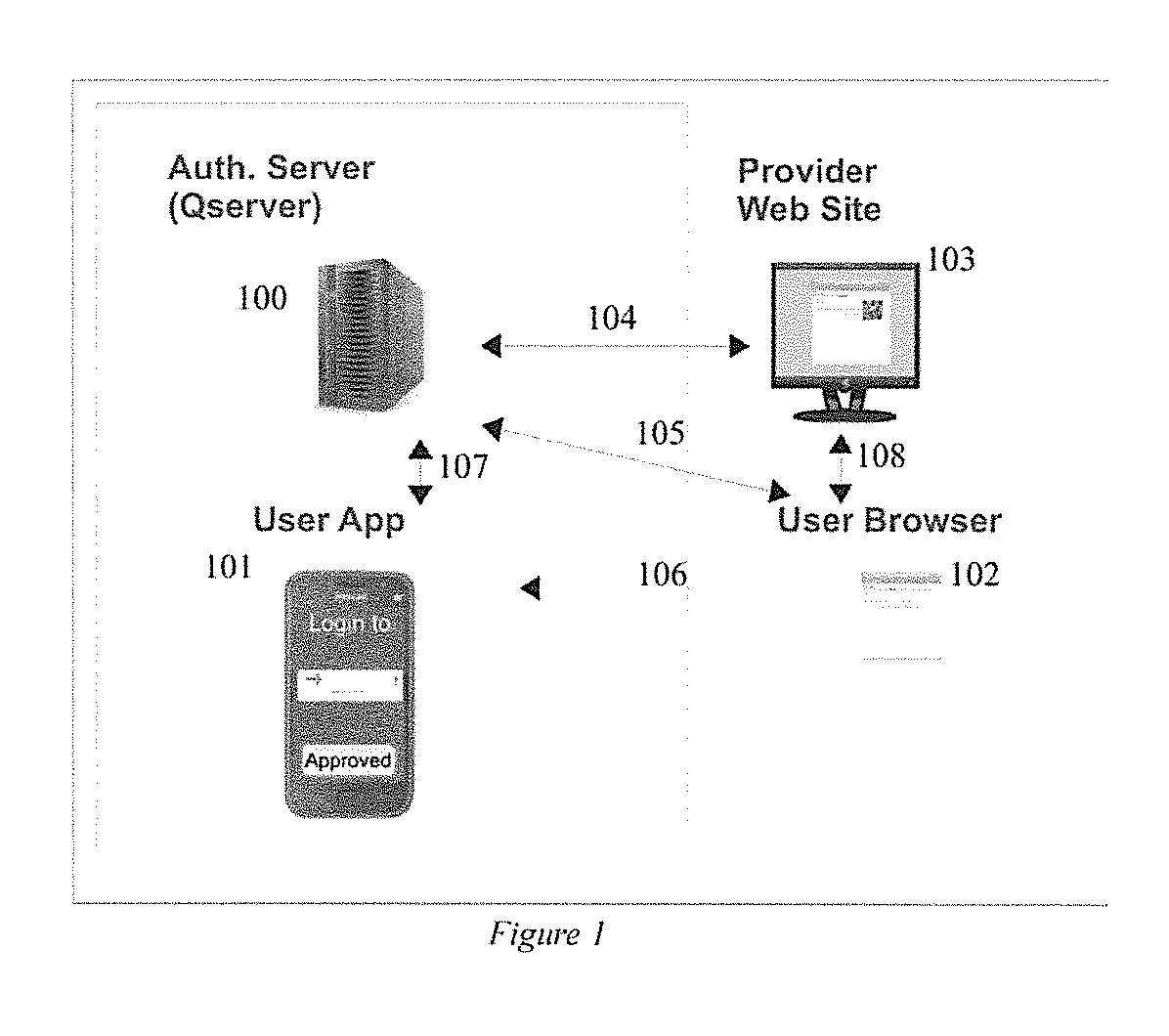
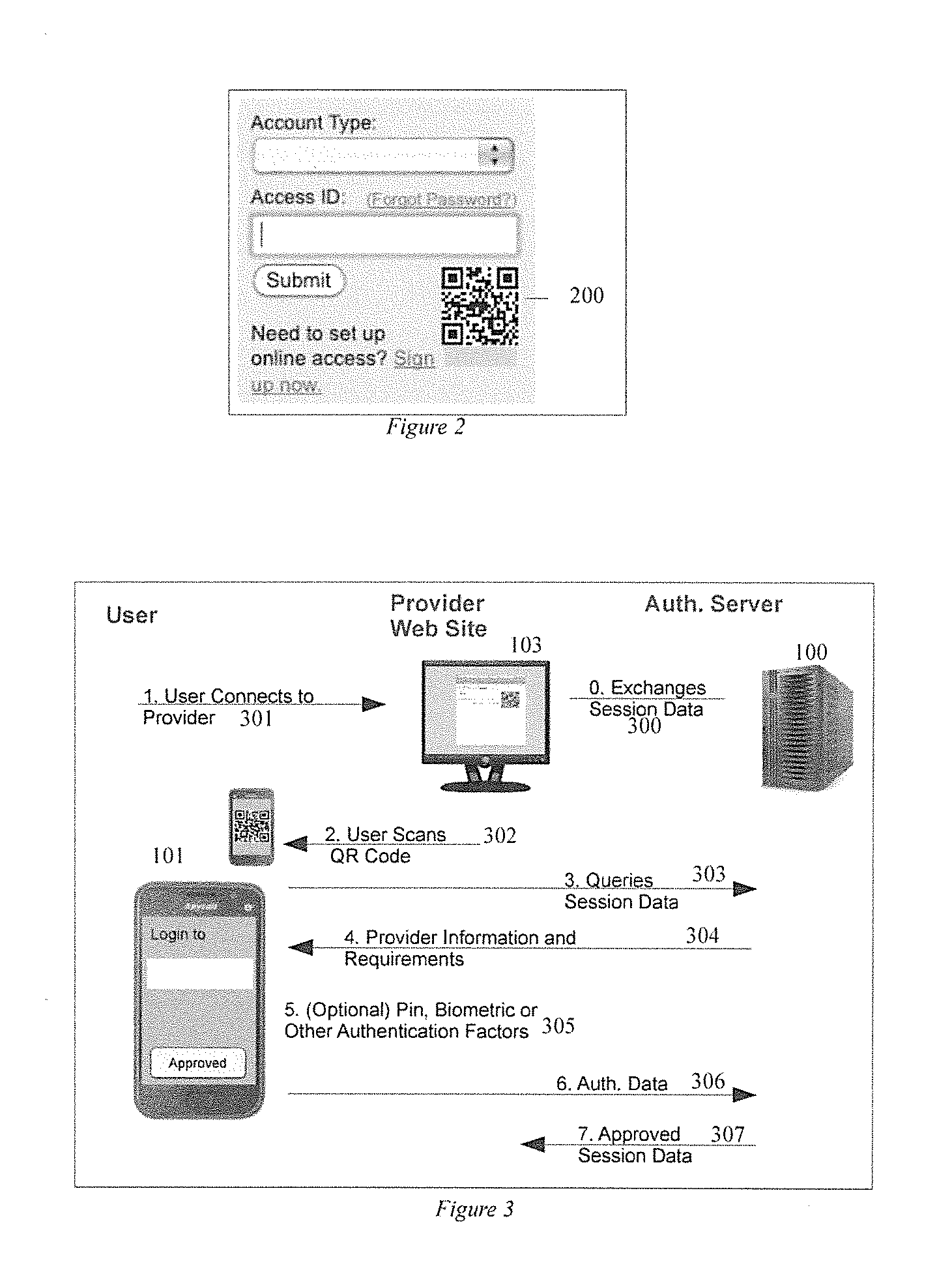
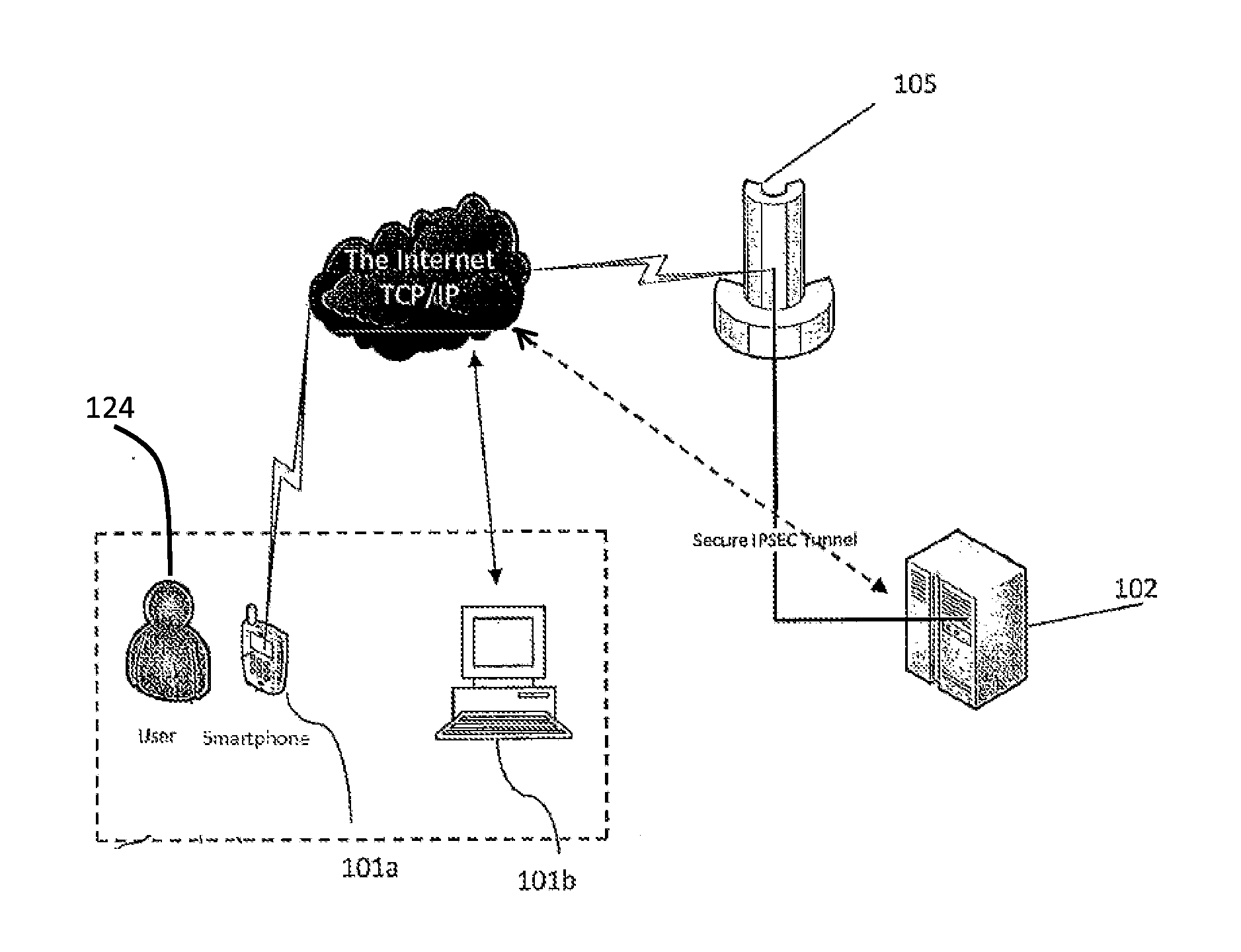
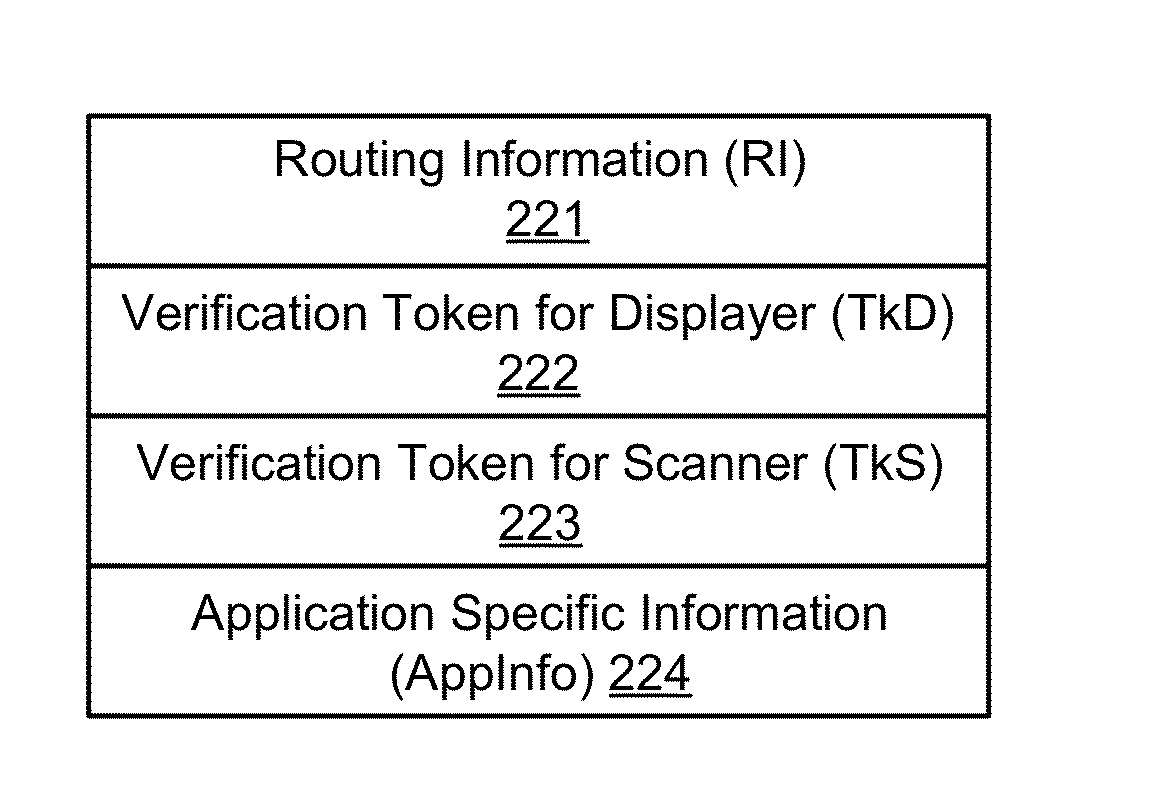
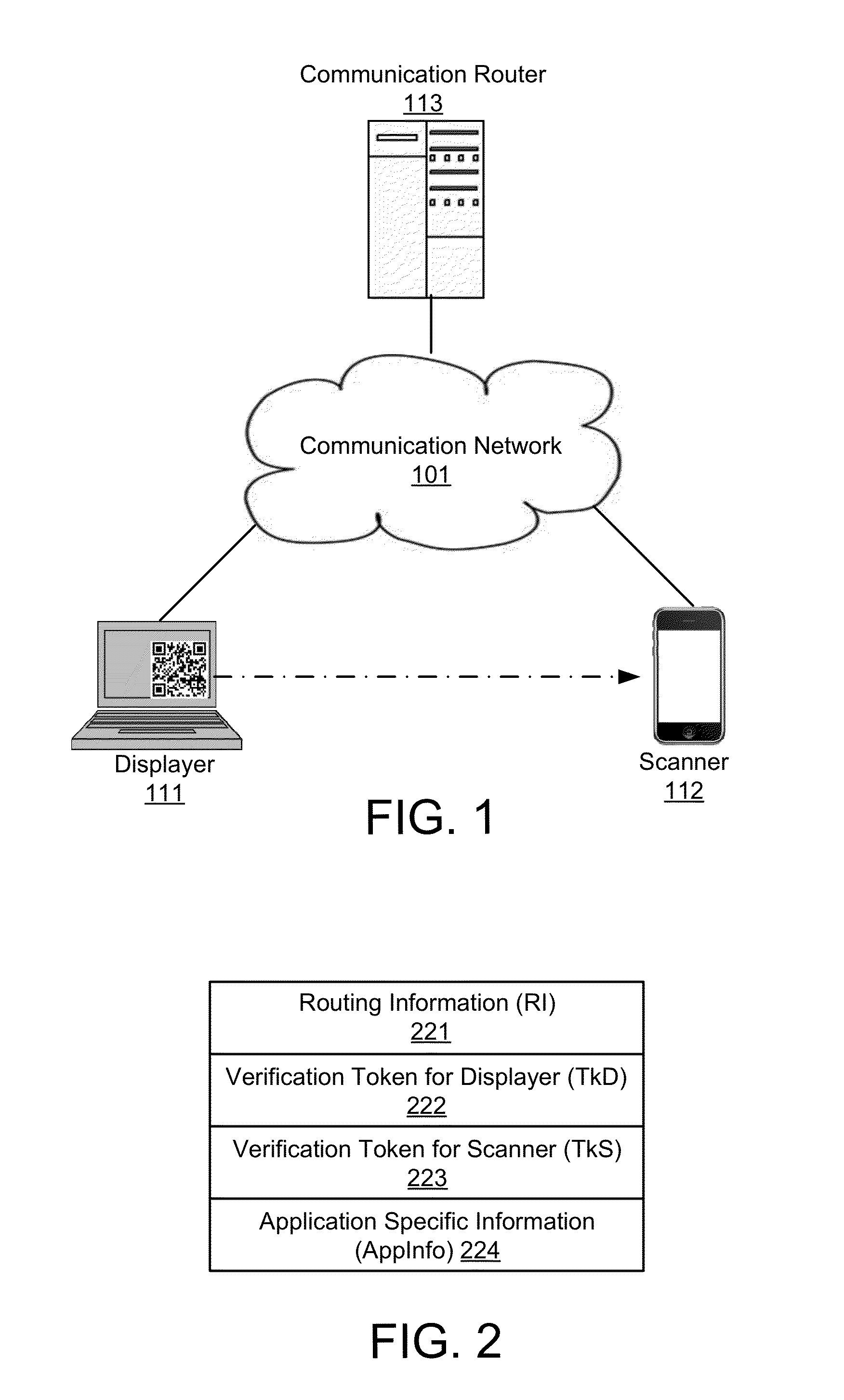
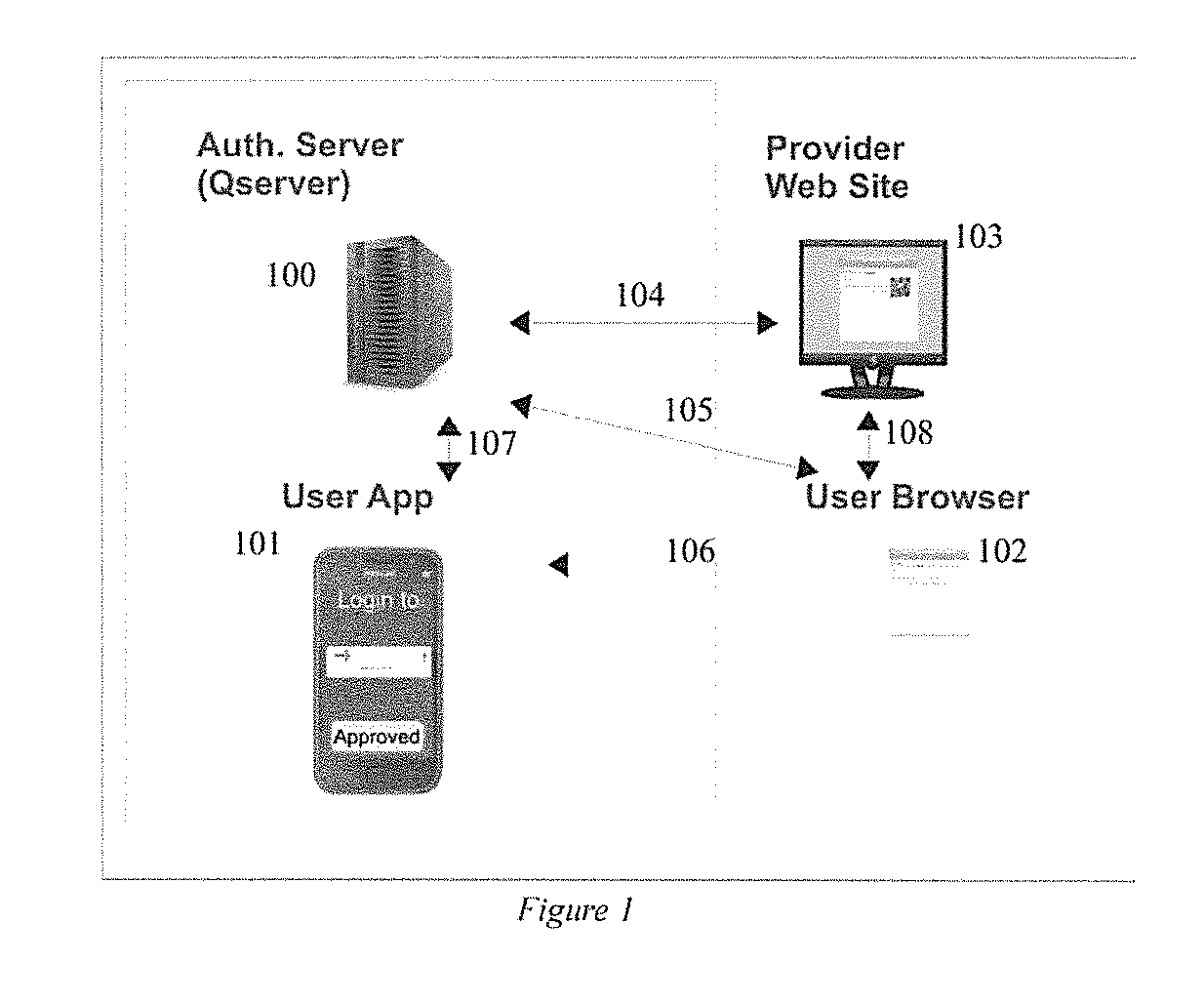
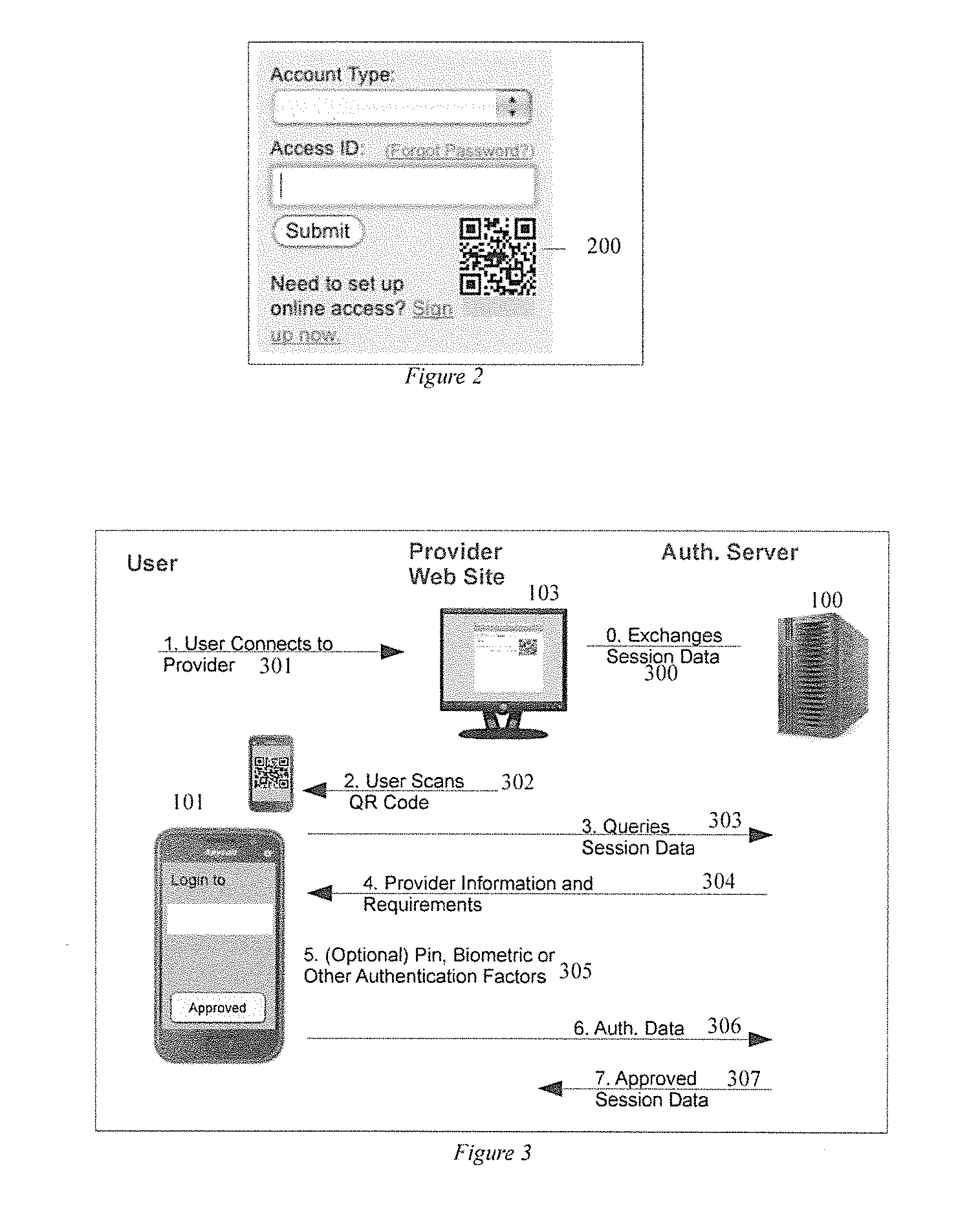
Secure and Authenticated Transactions with Mobile Devices
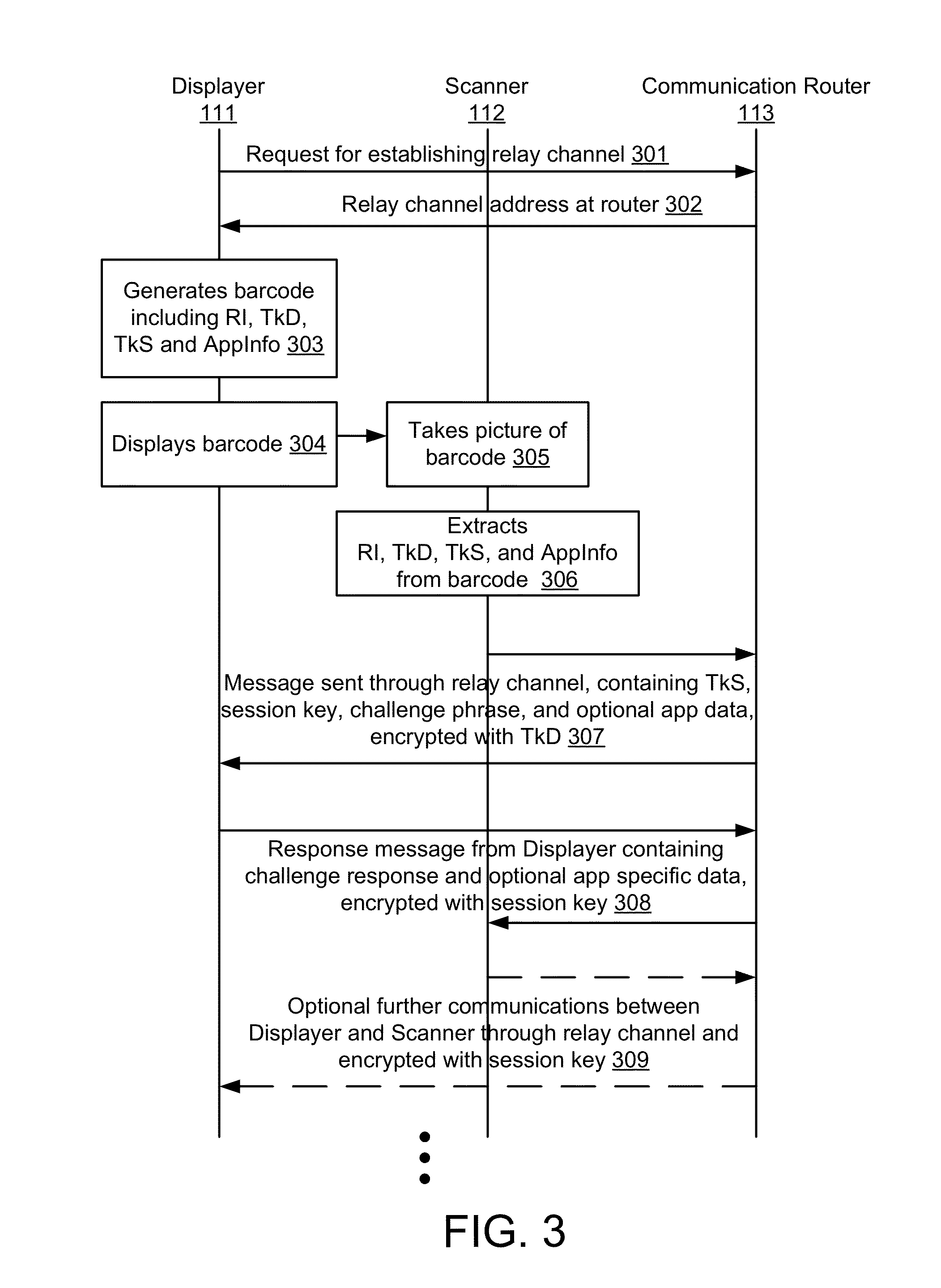
Embodiments of the invention include a platform for using 2D barcodes to establish secure authenticated communication between two computing devices that are in proximity to each other. A two-tier application architecture using a single base app and dynamic add-on applets is used. 2D barcodes can be distinctively visually branded. According to other aspects, the security of mobile payment systems are enhanced by (1) a triangular payment settlement in which the sender and receiver of payment each submit transaction information independently to the same payment server; (2) sensitive information is split into two parts, one of which is stored on a mobile device, and the other of which is stored on a payment server, and the two parts are only combined and exist transiently in the payment server's volatile memory when executing a transaction; and (3) a process to securely update profile pictures associated with payment accounts.
Owner:NETABPECTRUM
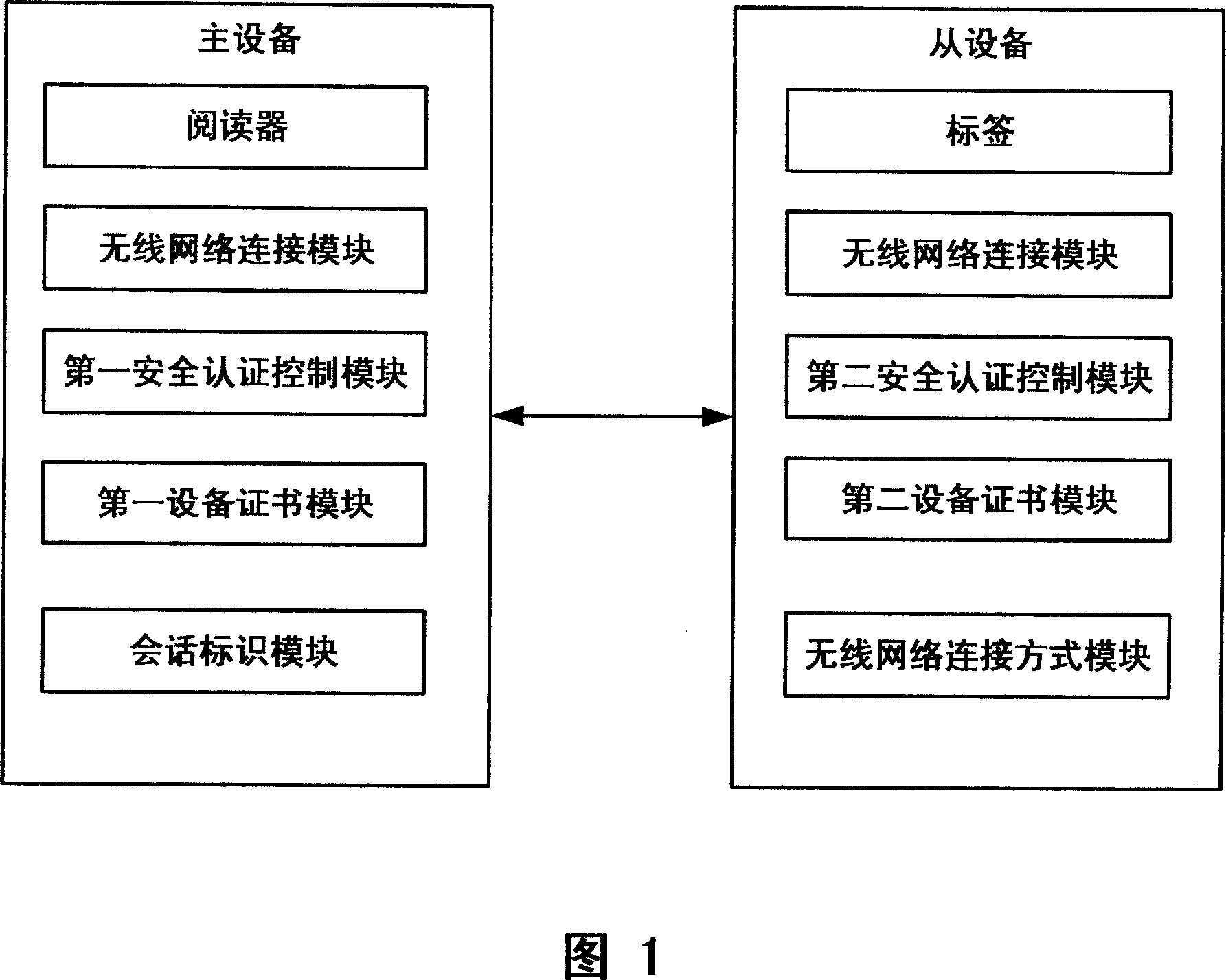
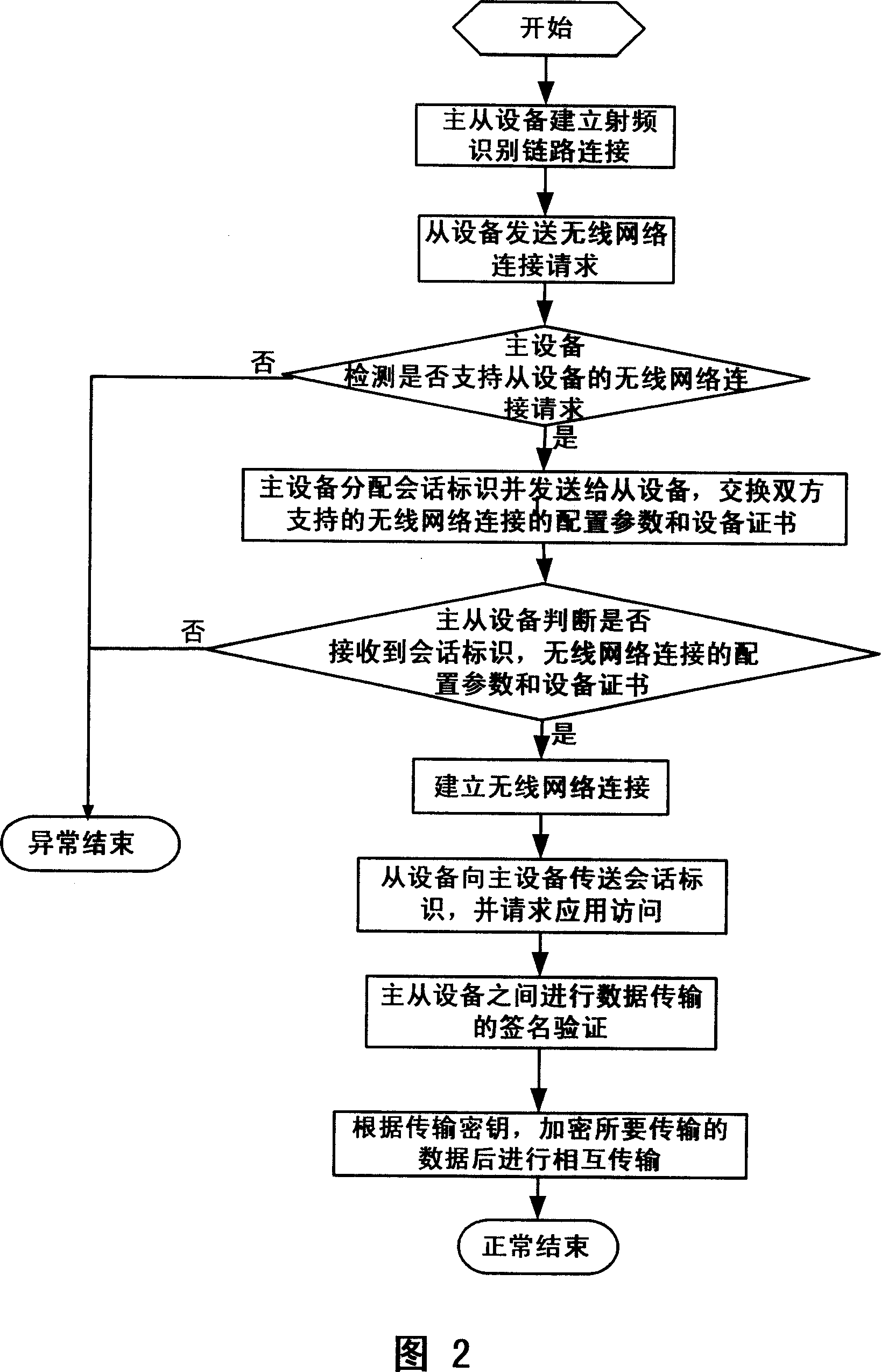
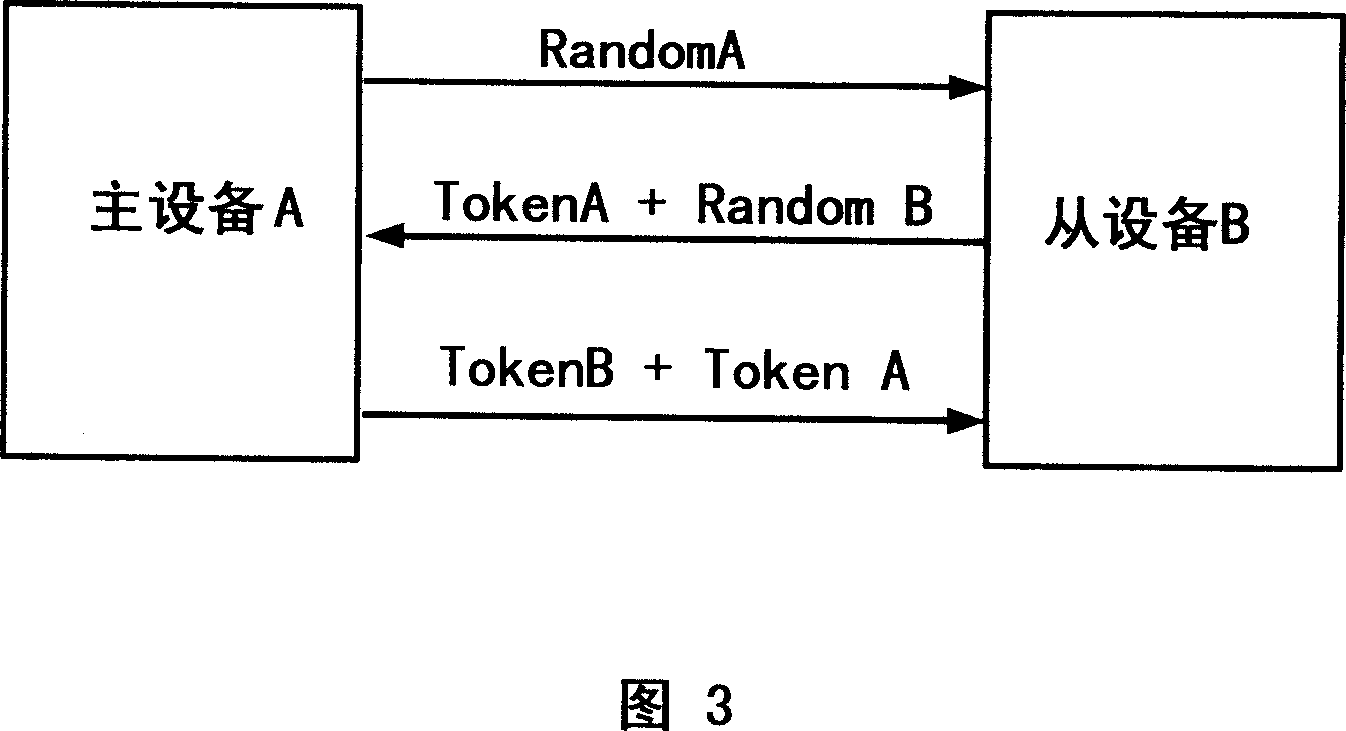
Safety authentication system, apparatus and method for non-contact type wireless data transmission
ActiveCN101114901AReduced usabilityImprove securityNear-field transmissionPublic key for secure communicationContact typeUsability
The invention discloses a system, a device and a method of a non-contact wireless data transmission safety certification. The method comprises the following steps that: when the examination of a main equipment enters a short-range RF-induced (radio frequency) area from the equipment, a radio frequency identification link connection is built between the main equipment and a slave equipment; then the safety certification parameter of the wireless network connection supported by both the main and the slave equipments is exchanged; then the main and the slave equipments judges whether the safety certification parameter is successfully received or not; if so, the wireless network connection is built; if not, users are prompted to restart or end the radio frequency identification communication connection; finally a signature verification of the non-contact equipment wireless data transmission is carried out on the wireless network link connection between the main and the slave equipments. Under the premise of convenience of users, the higher security is ensured.
Owner:LENOVO (BEIJING) CO LTD
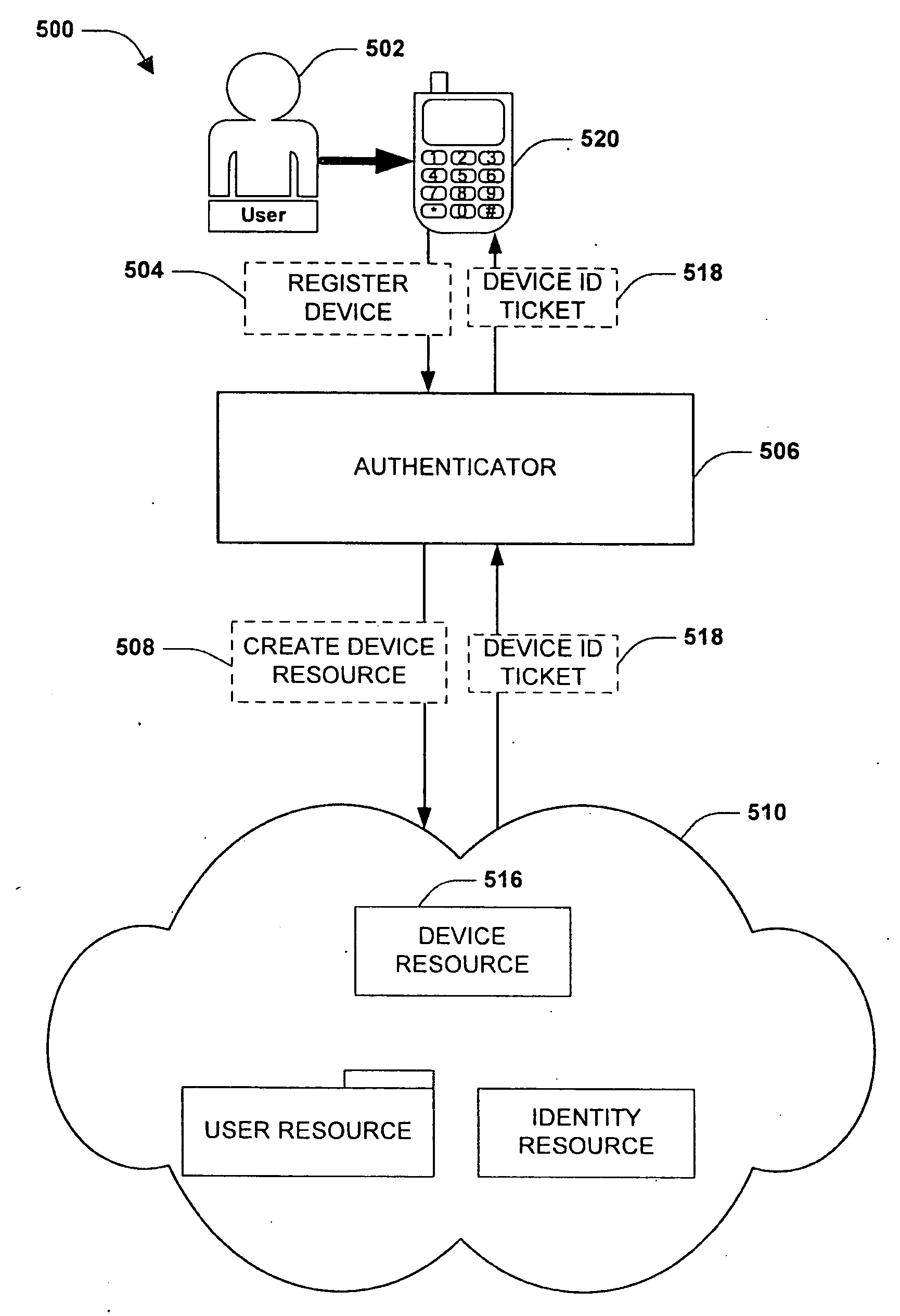
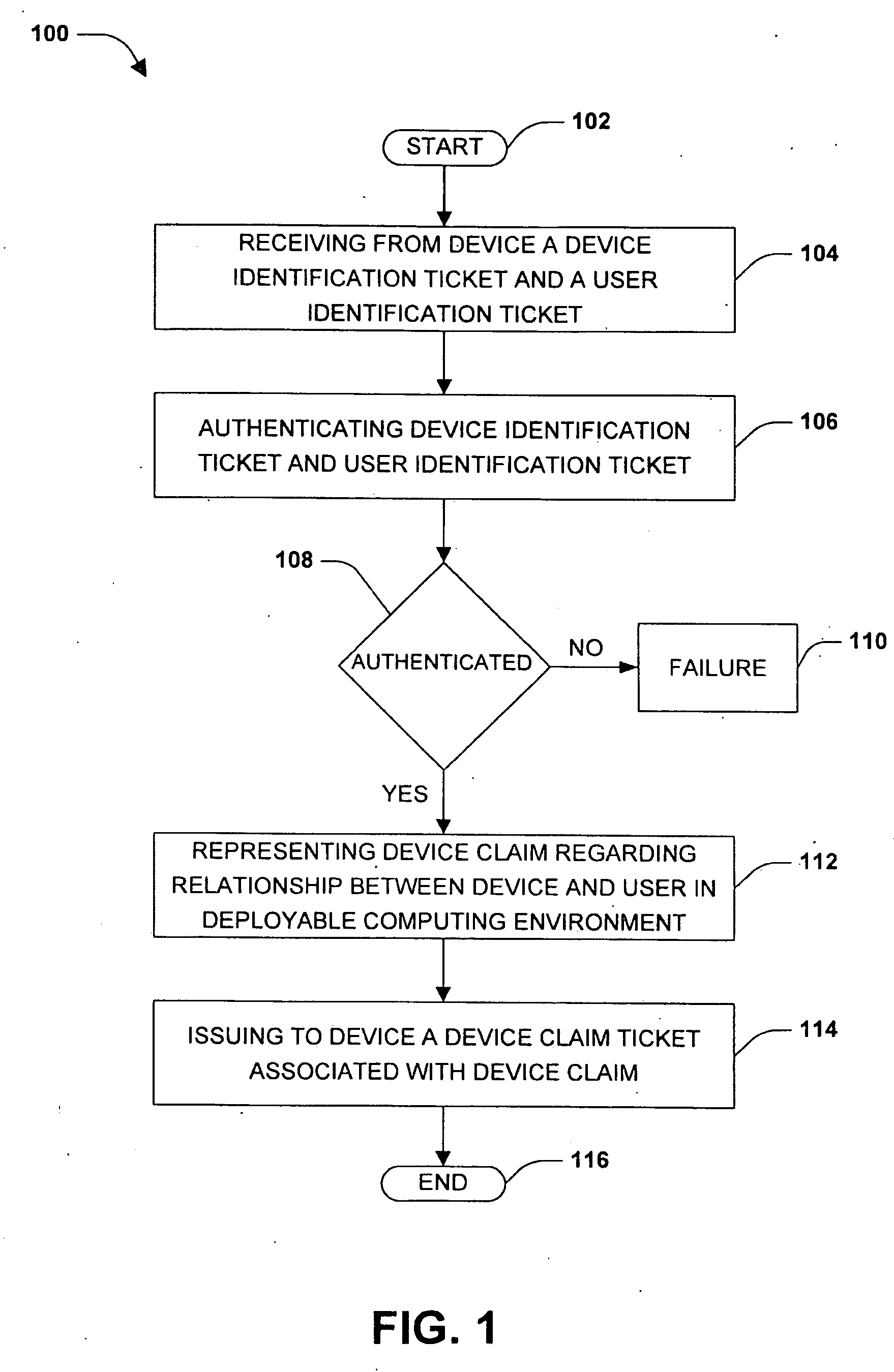
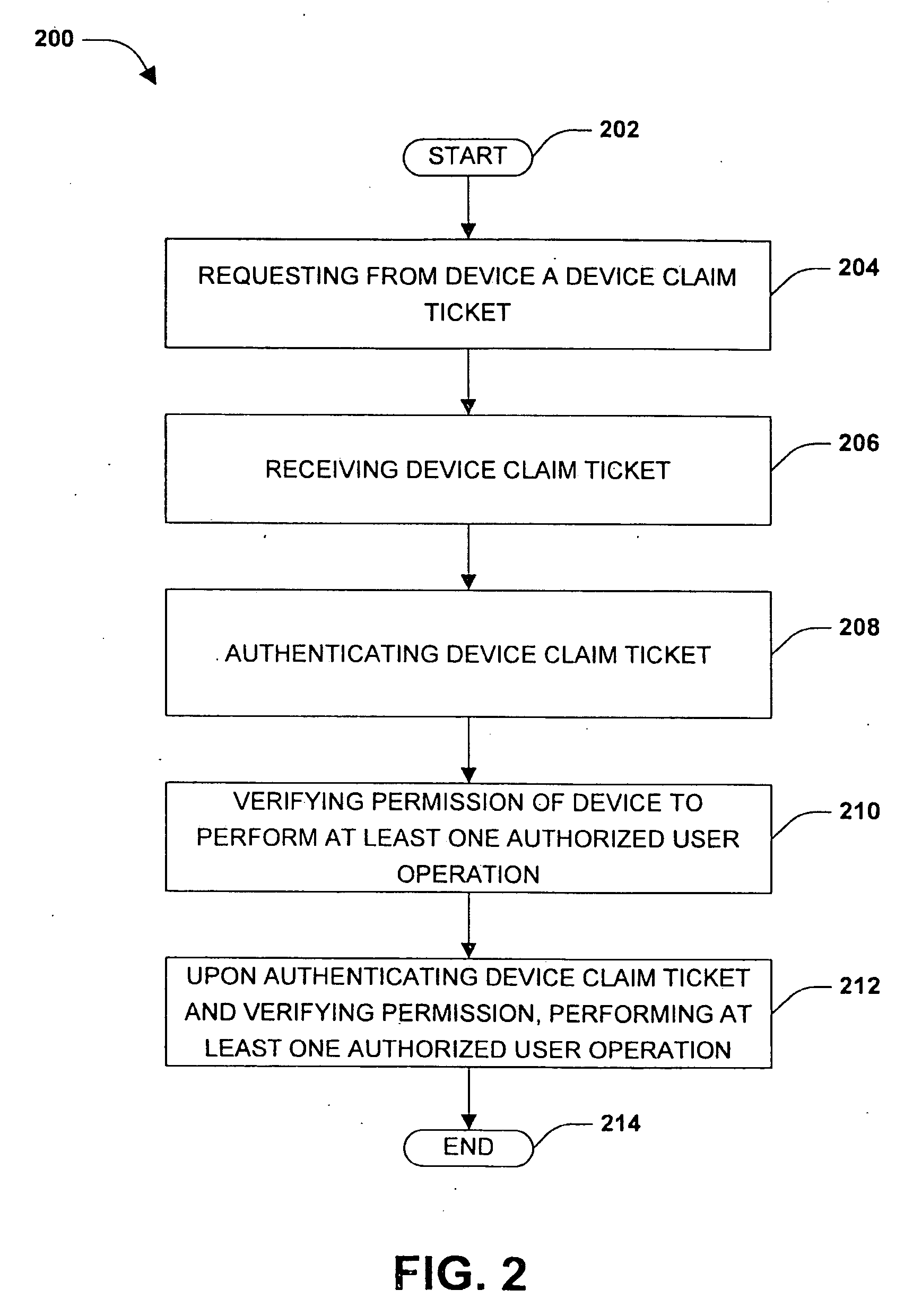
Device authentication within deployable computing environment
ActiveUS20100093310A1Operational securityEnhanced interactionUnauthorised/fraudulent call preventionEavesdropping prevention circuitsComputer hardwareData synchronization
A deployable computing environment may facilitate interaction and data sharing between users and devices. Users, devices, and relationships between the users and devices may be represented within the deployable computing environment. A relationship between a user and a device may specify that the device is owned by the user and that the device is authorized to perform operations within the deployable computing environment on behalf of the user. Secure authentication of devices and users for interaction within the deployable computing environment is achieved by authenticating tickets corresponding to the user, the device, and the relationship. A device identification ticket and a user identification ticket are used to authenticate the device and user for interaction within the deployable computing environment. A device claim ticket allows the device to perform delegated operations (e.g., data synchronization, peer connectivity, etc.) on behalf of the user without the user's credentials (e.g., user identification ticket).
Owner:MICROSOFT TECH LICENSING LLC
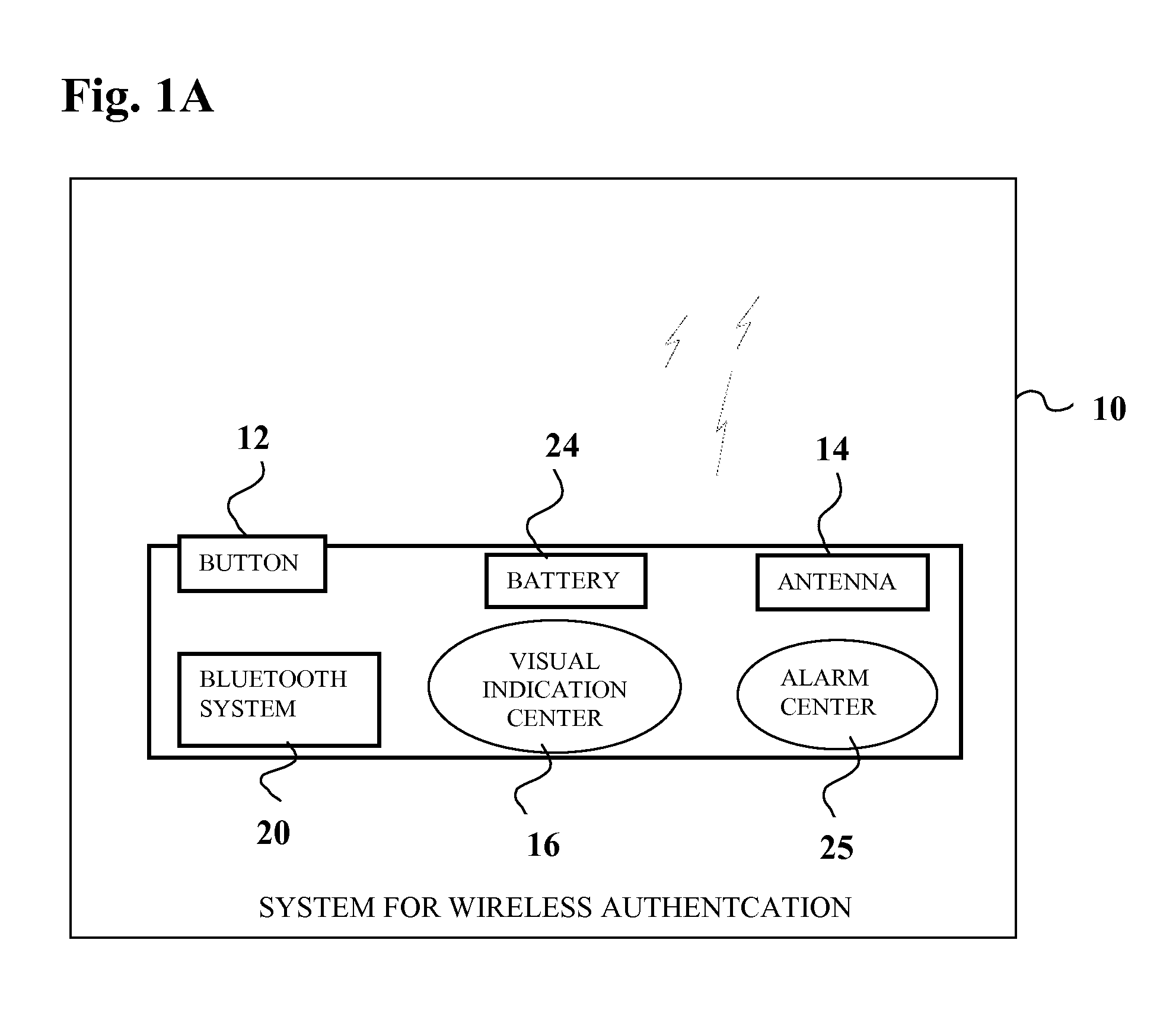
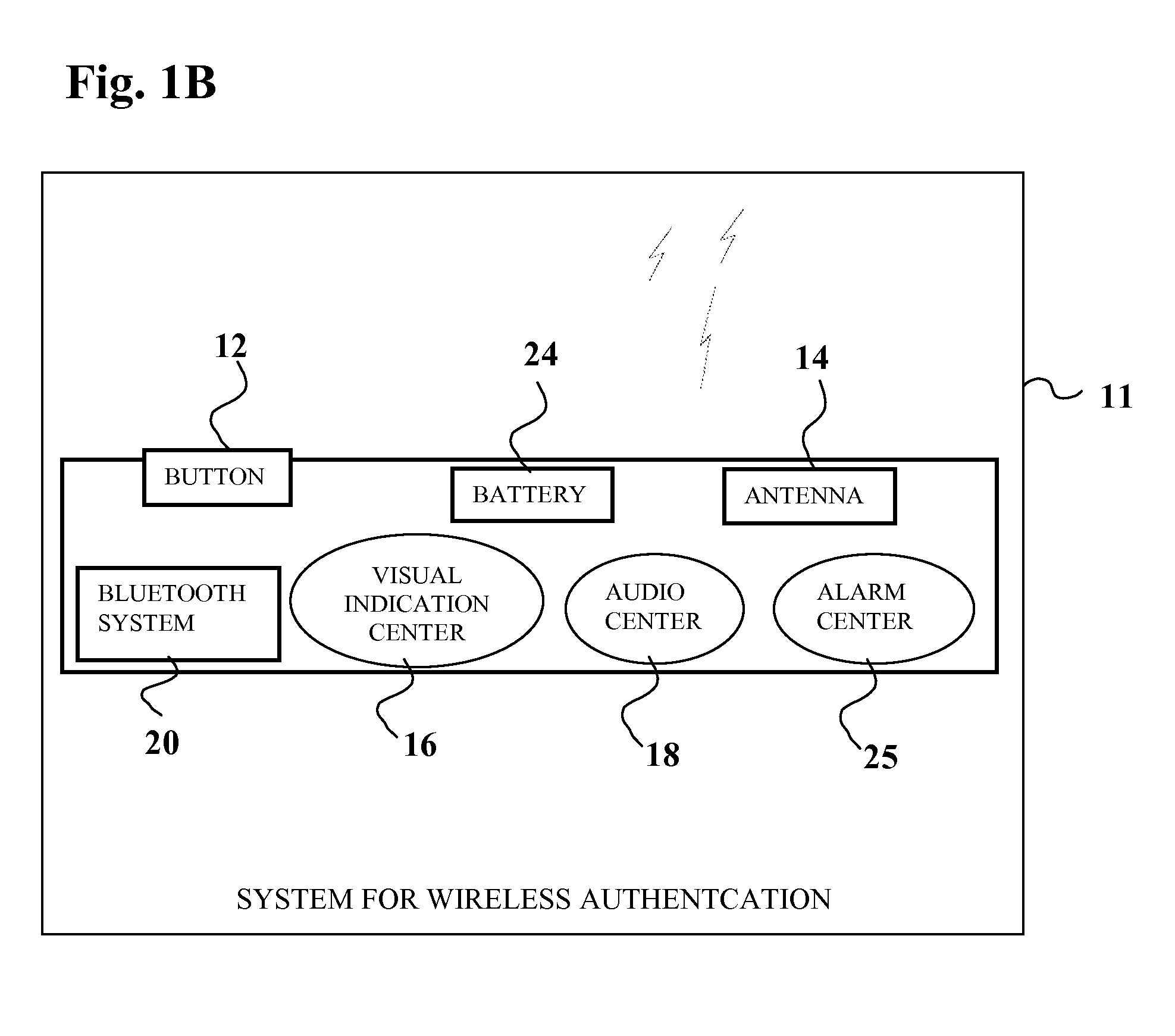
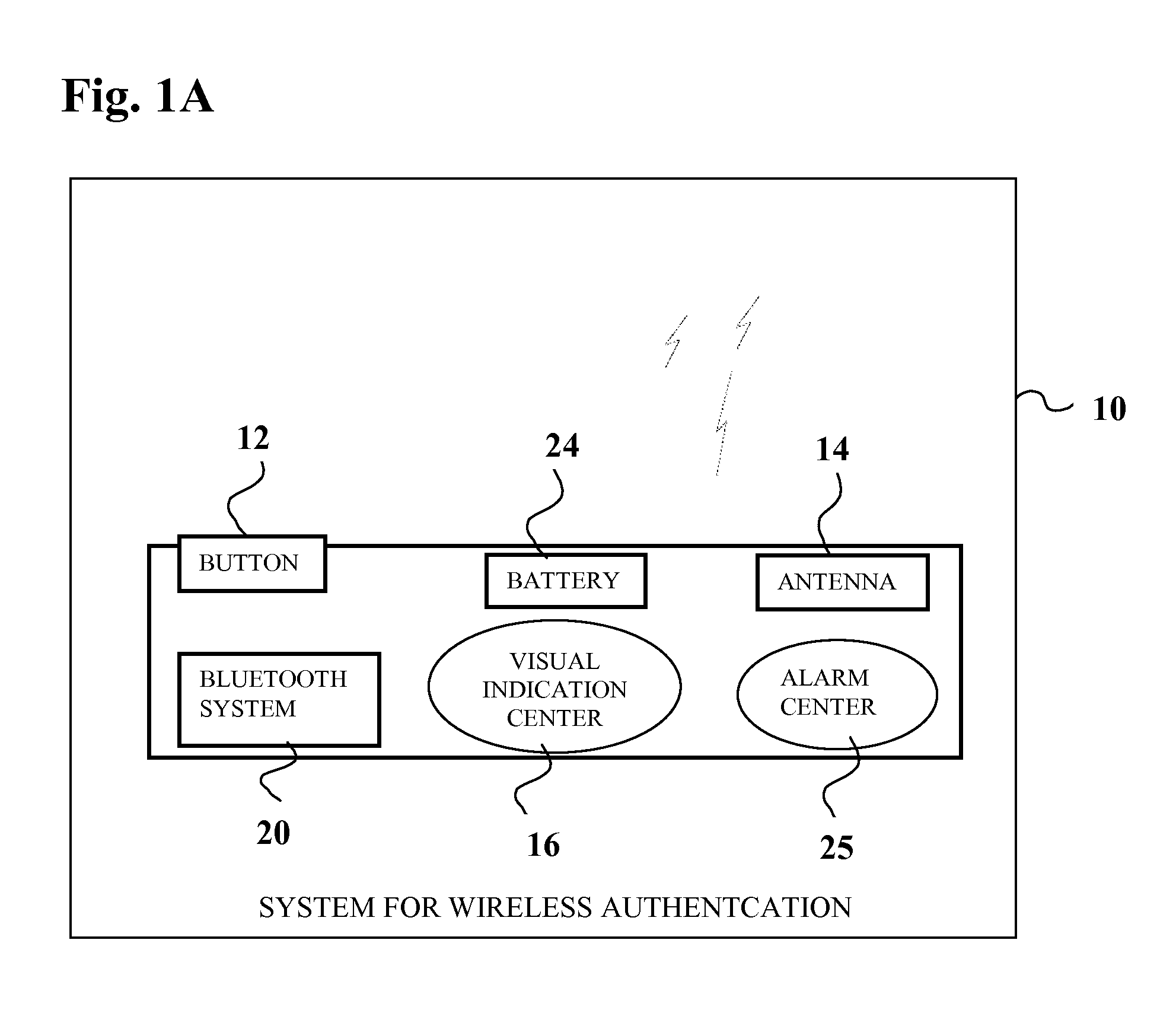
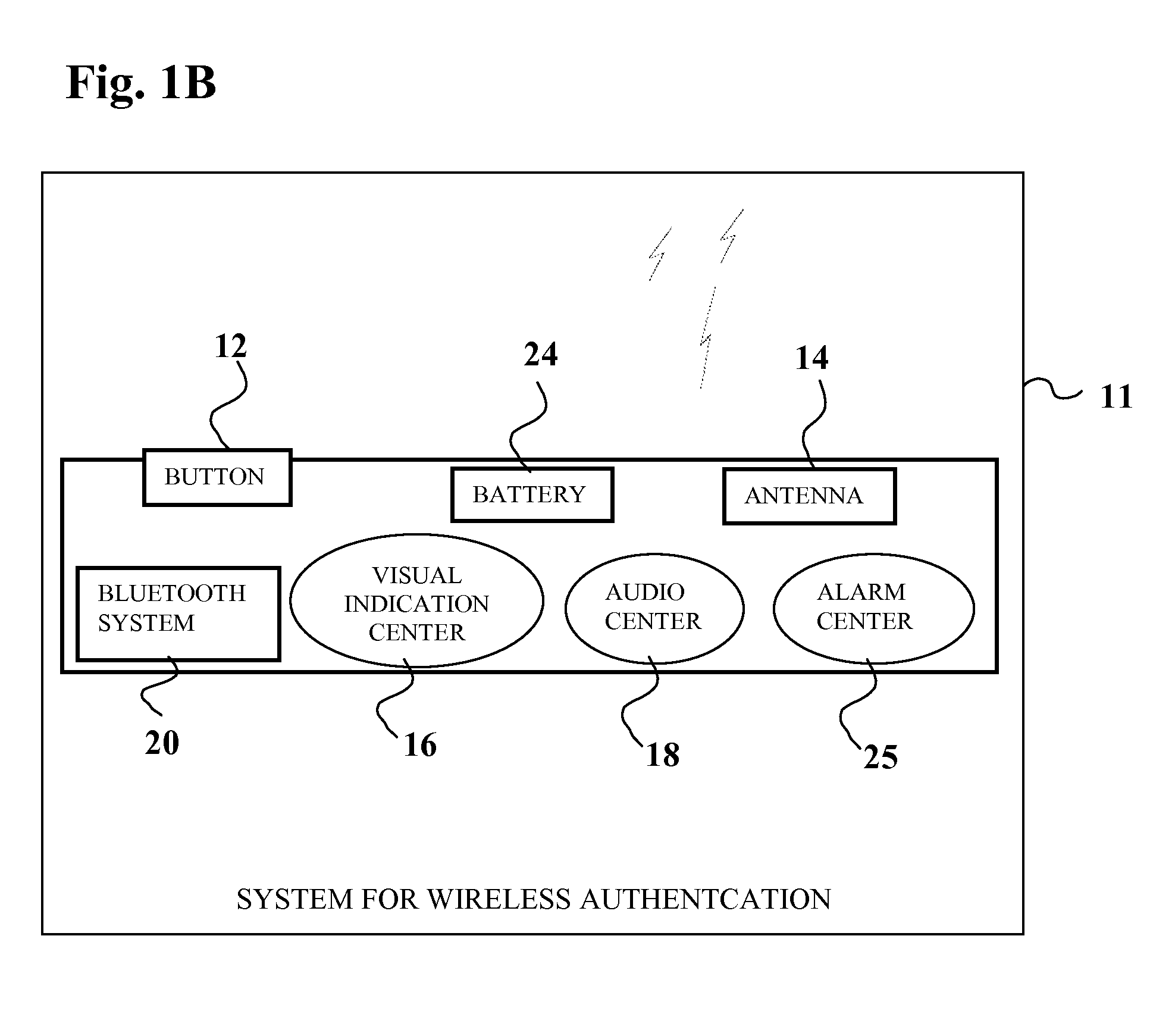
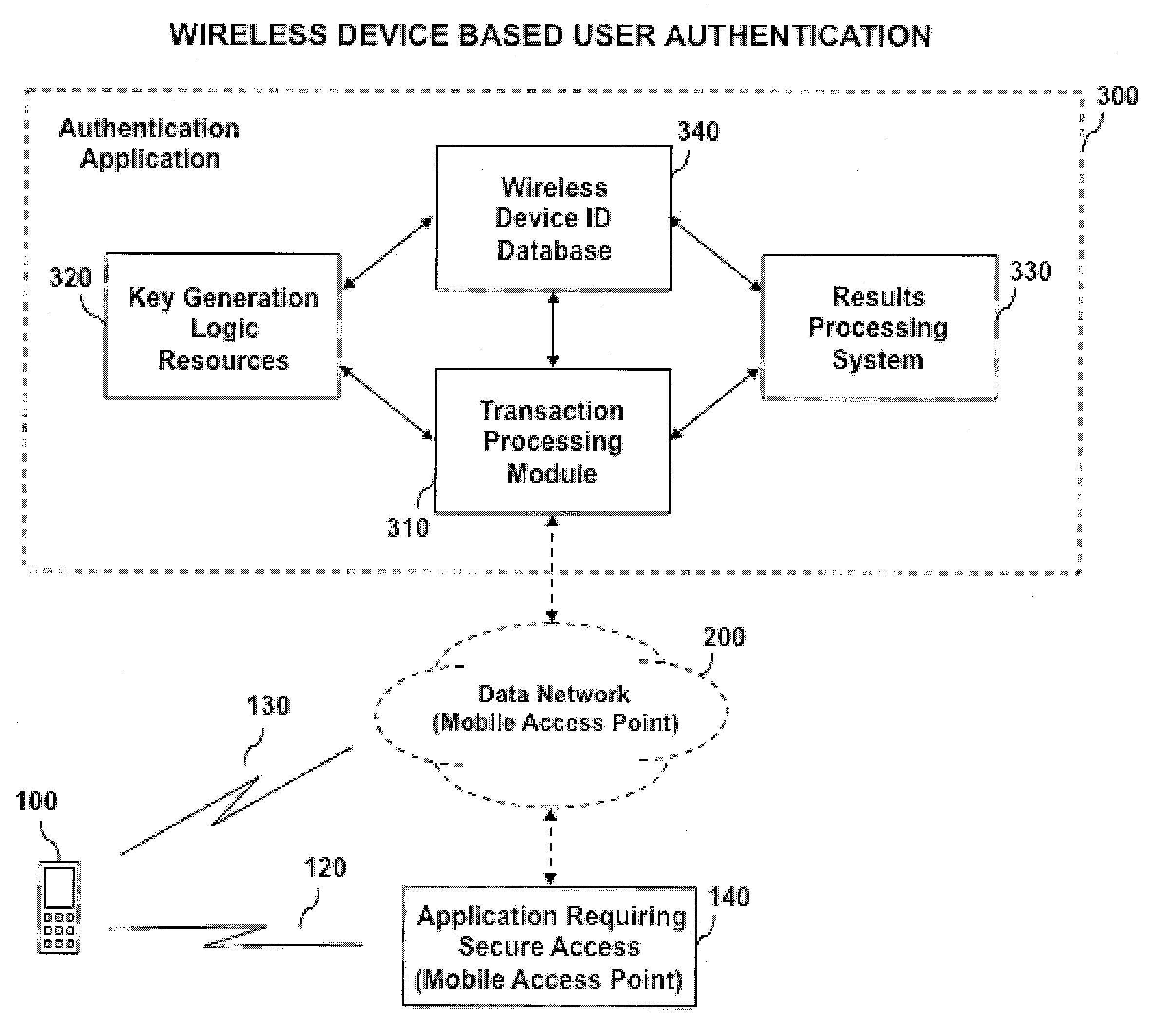
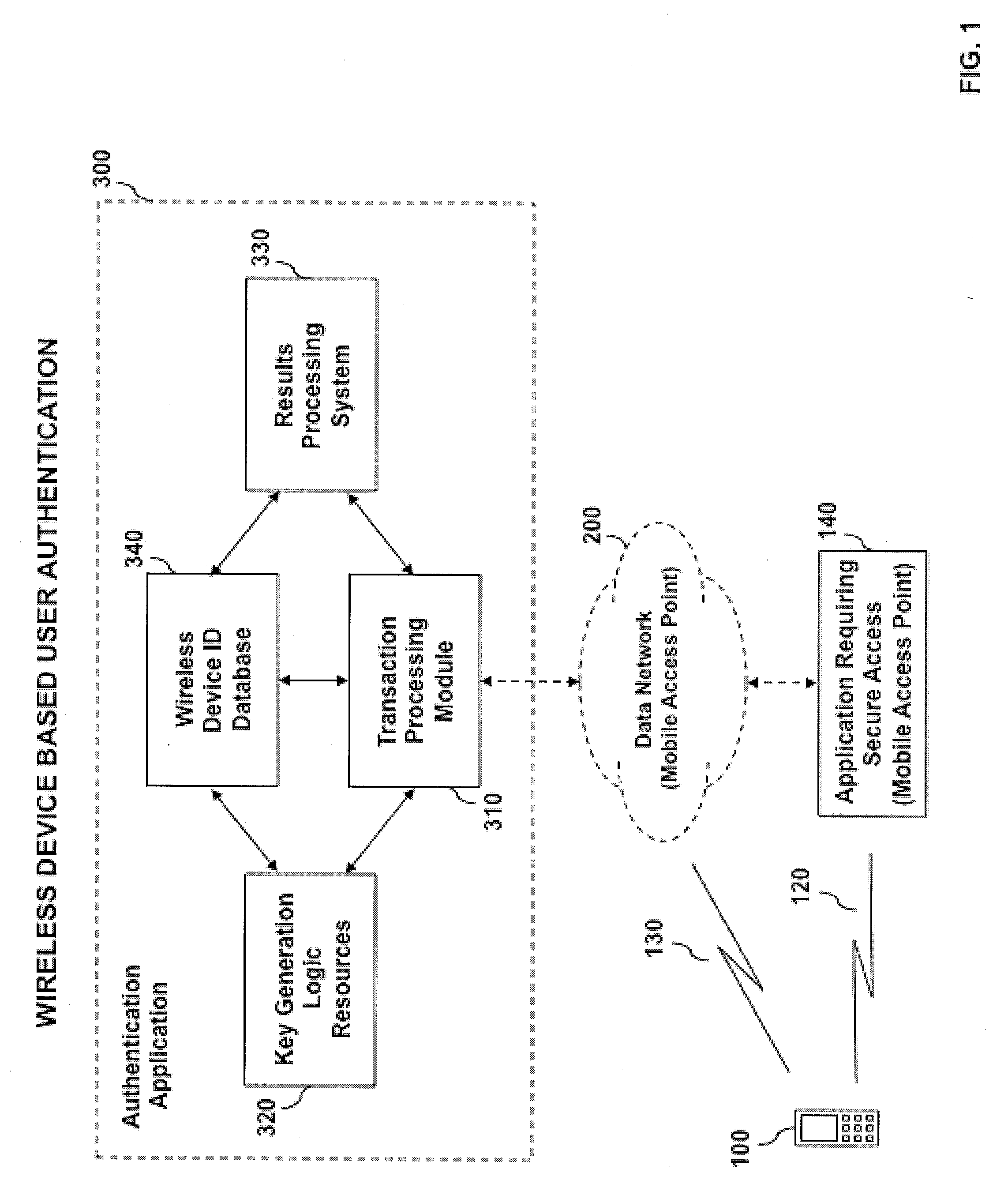
System and method for wireless device based user authentication
ActiveUS20090204815A1Preventing identify theftPrevent theftUser identity/authority verificationNetwork topologiesWi-FiUnique identifier
An automated system and method for authenticating entities or individuals attempting to access a computer application, network, system or device using a wireless device is provided. The system employs one or more short-range wireless interfaces (e.g. BLUETOOTH or Wi-Fi) or long-range wireless interfaces (e.g. cellular or WiMAX) to detect the presence or location of the wireless device and it's proximity to the secure system to be accessed. The wireless device incorporates a unique identifier and secure authentication key information associated with the user of the wireless device. An authentication result is generated and may be used for a variety of applications. The application may process the result and determine the degree of access for which the entity or individual is allowed.
Owner:VISA INT SERVICE ASSOC
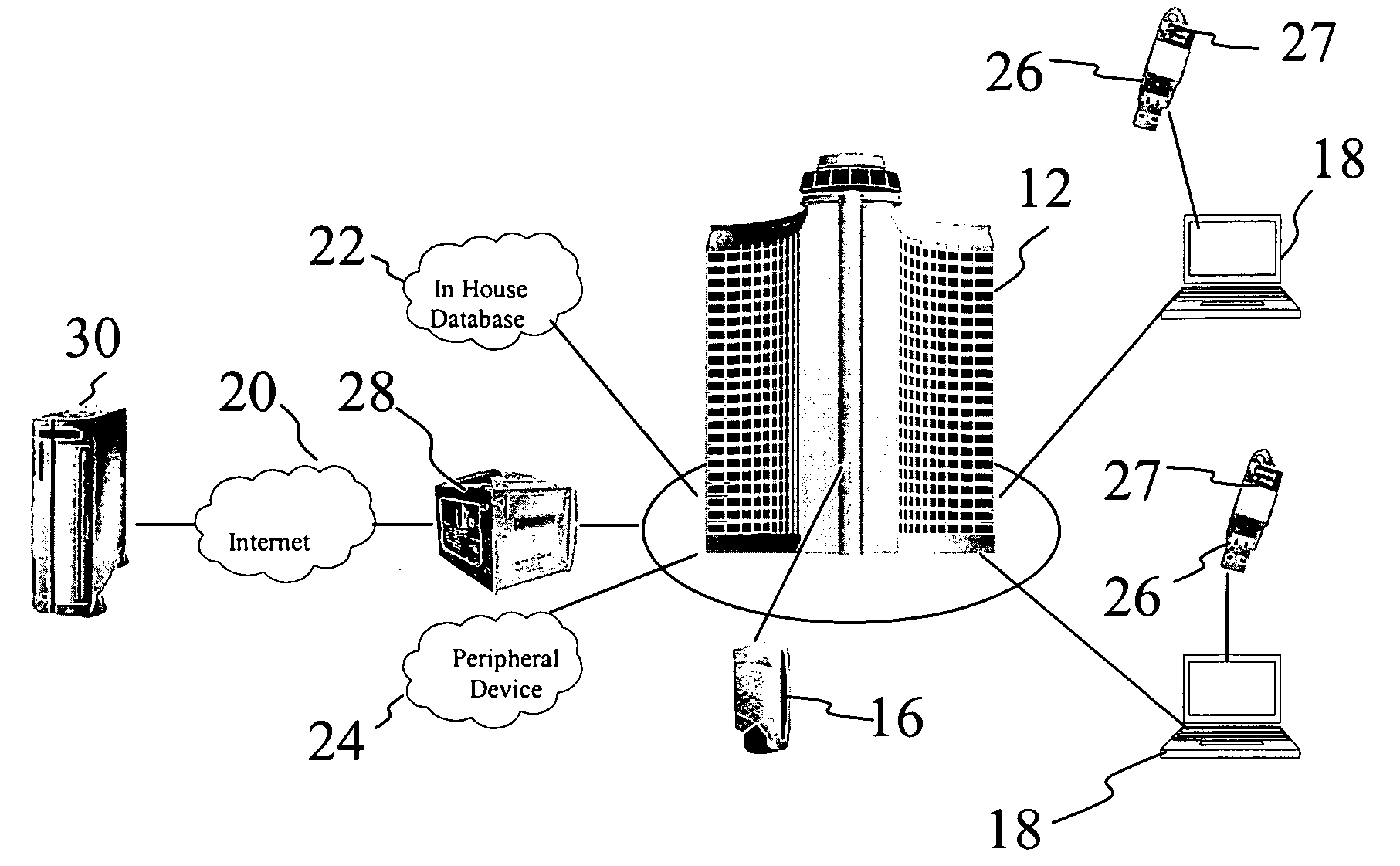
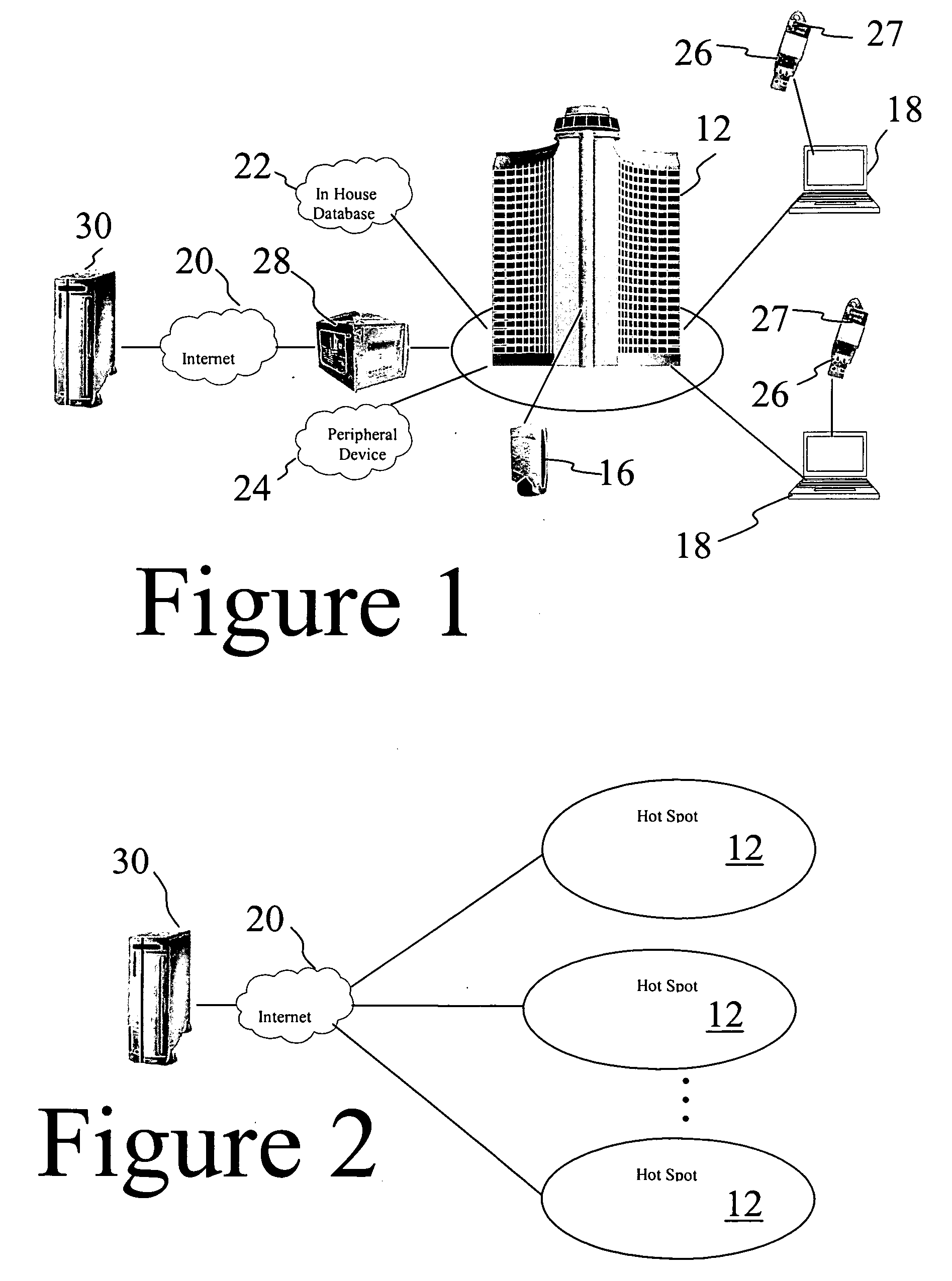
Secure authentication and network management system for wireless LAN applications
InactiveUS20060072527A1Efficient and effectiveProtect healthDigital data processing detailsUser identity/authority verificationWi-FiNetwork management
An authentication and network management system for Wi-Fi local area networks includes a network management device and a plurality of Wi-Fi local area networks coupled to the network management device. Each local network includes at least one access point device having a Wi-Fi radio. A plurality of end user devices are attachable to the network forming nodes thereof, and each end user device has input plugs, such as USB ports and the like, for coupling accessories thereto. An authentication device is provided in the network for authenticating the end user devices attached to the network. A plurality of authenticating keys is provided, with each key attachable to an input plug of an end user device. Each key contains a validation certificate therein, wherein the authentication device verifies the presence of a current validation certificate on a key coupled to the end users device prior to granting access to the network.
Owner:DIRECTPOINTE
Secure authentication and payment system
ActiveUS8346659B1Reduce in quantityLimit their usefulnessFinanceElectronic credentialsTelephone networkSecure authentication
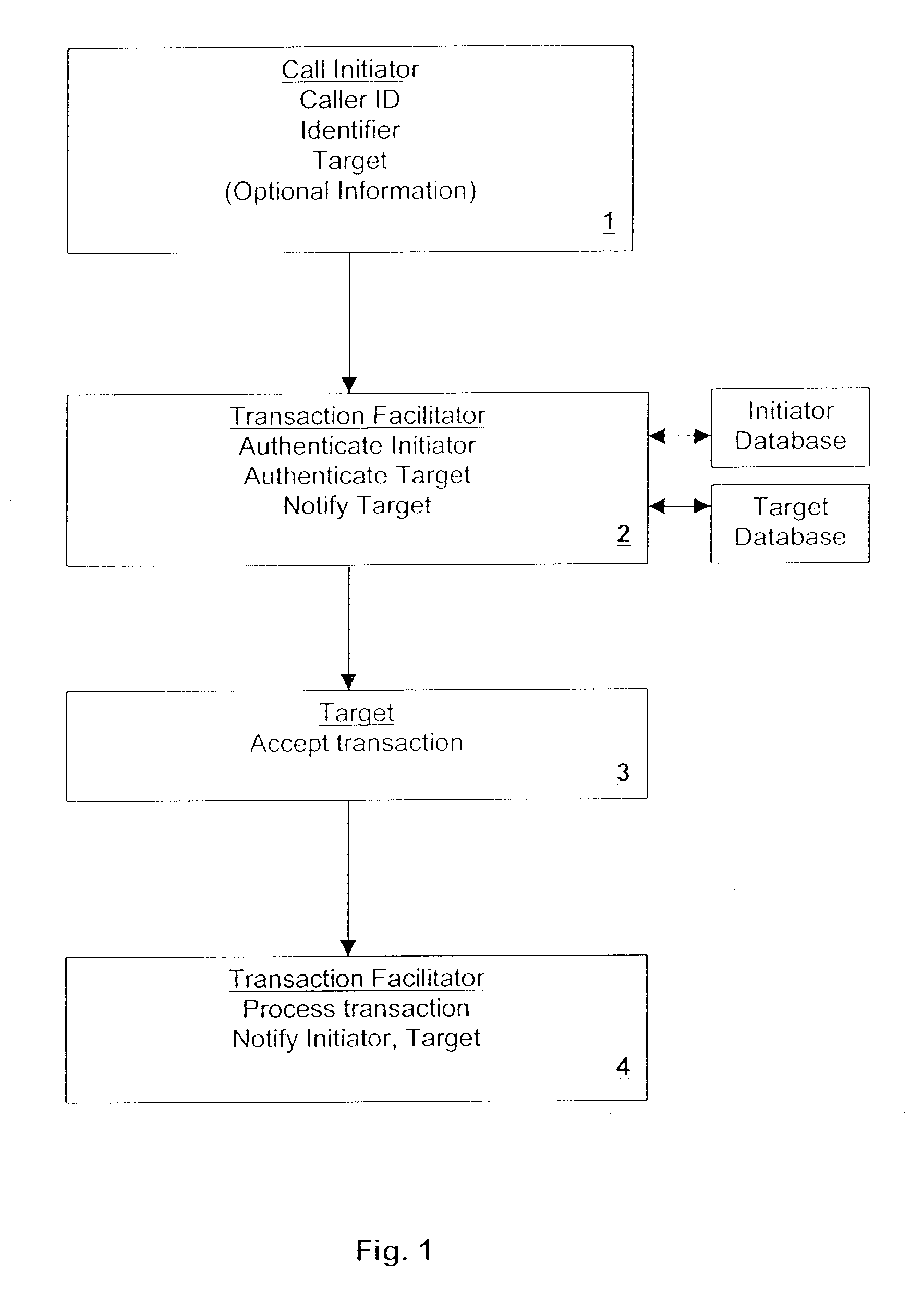
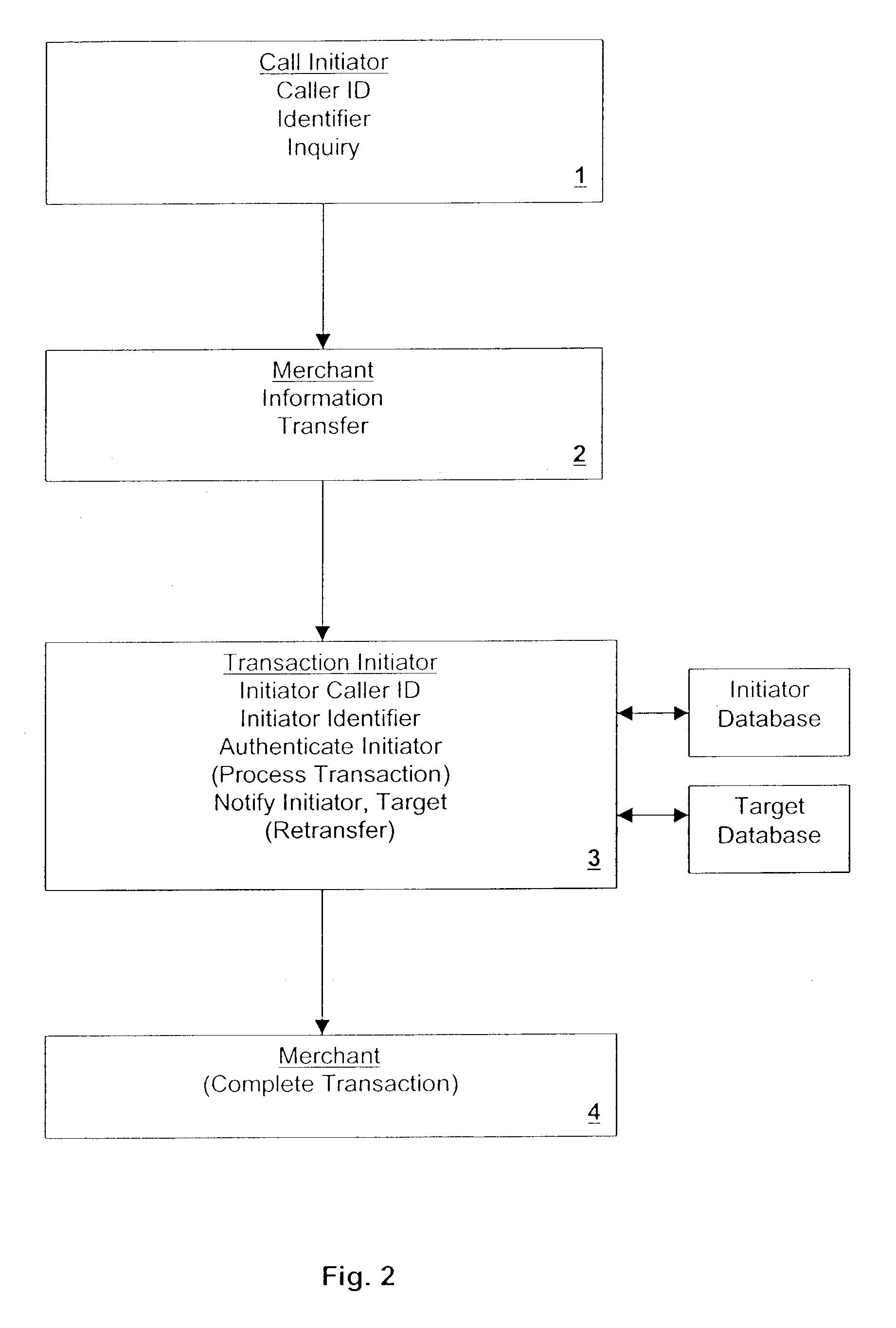
A transaction and payment and processing system securely conducts transactions over the public telephone network. The transactions may be between and among entities of any type such as individuals, merchants, utilities, banks, etc. Nothing more than access to a telephone is required after initial registration of a user.
Owner:ALIASWIRE
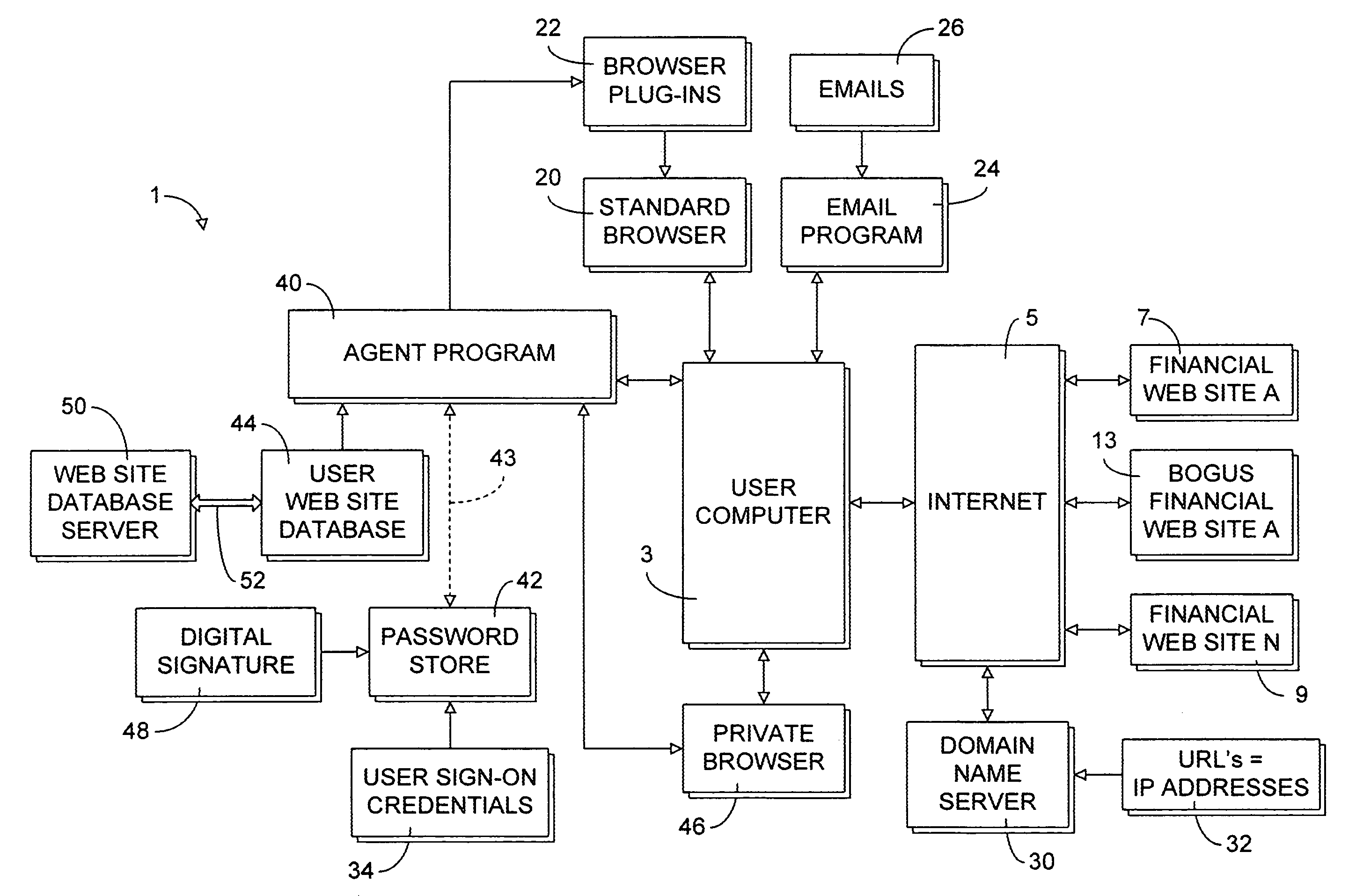
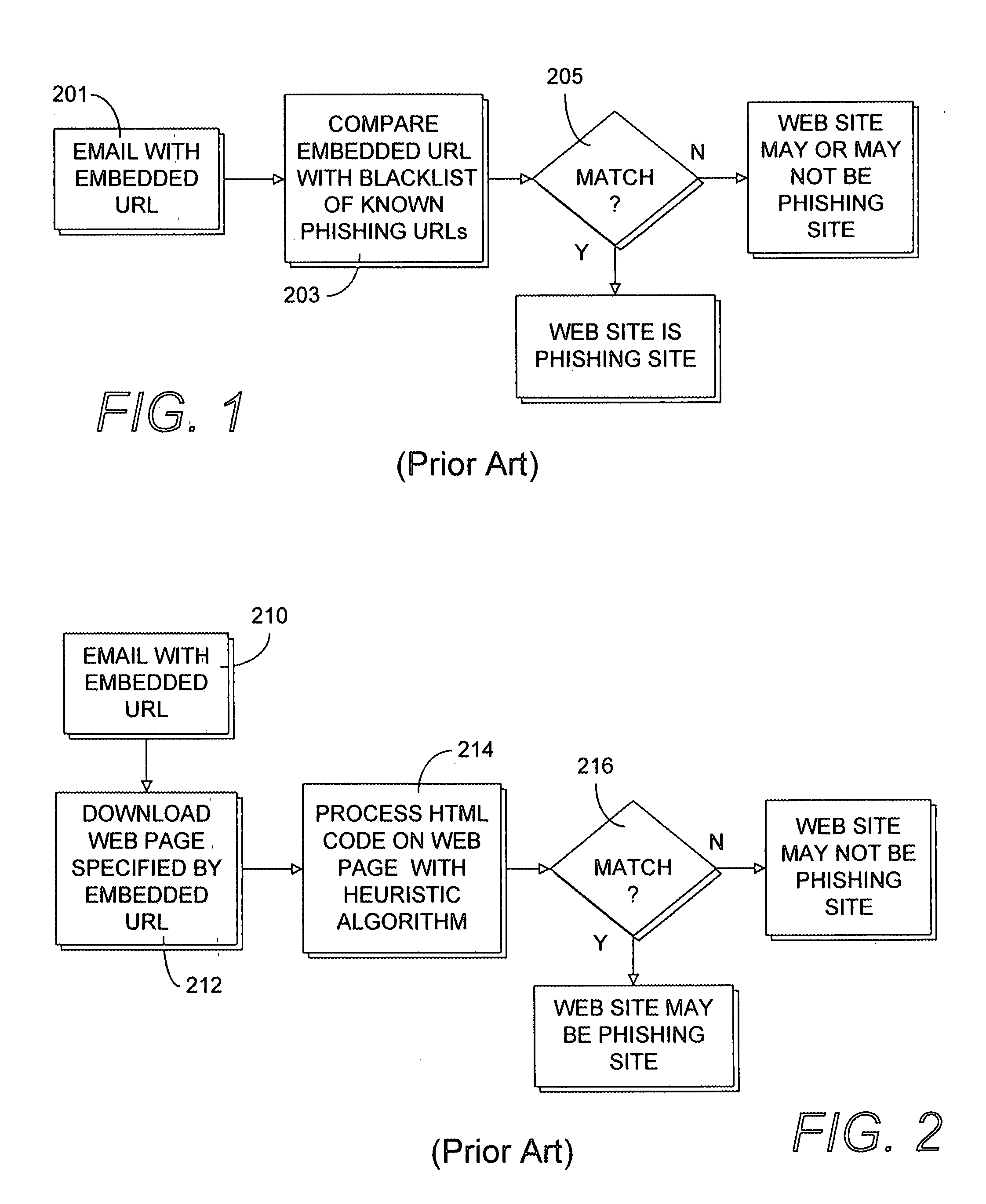
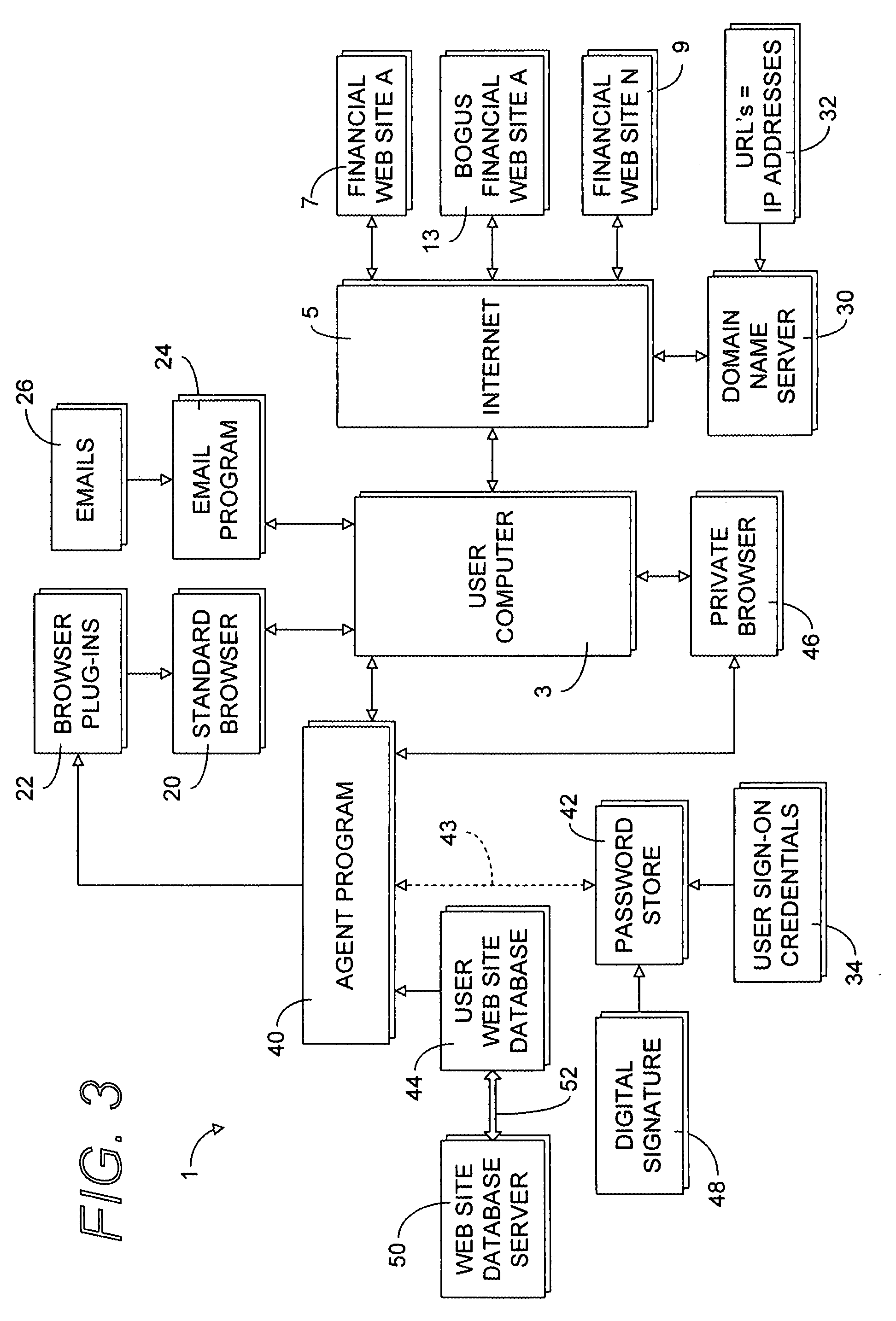
Secure web site authentication using web site characteristics, secure user credentials and private browser
ActiveUS20080028444A1Overcome deficienciesImprove approachDigital data information retrievalMemory loss protectionWeb siteIp address
A secure authentication process detects and prevents phishing and pharming attacks for specific web sites. The process is based on a dedicated secure hardware store for user sign-in credentials, a database of information about specific web sites, and a private secure browser. All user web activity is monitored by an agent program. The agent program checks to make sure that user attempts to send any sign-in credentials stored in secure hardware store of user sign-in credentials, to any web site accessed by the user, is allowed only if the IP address of the web site accessed by the user matches at least one of the IP addresses stored web site database associated with the sign-in credential the user is attempting to send. The process also detects mismatches between a URL and the actual IP address of the web site associated with the URL.
Owner:AURA SUB LLC +1
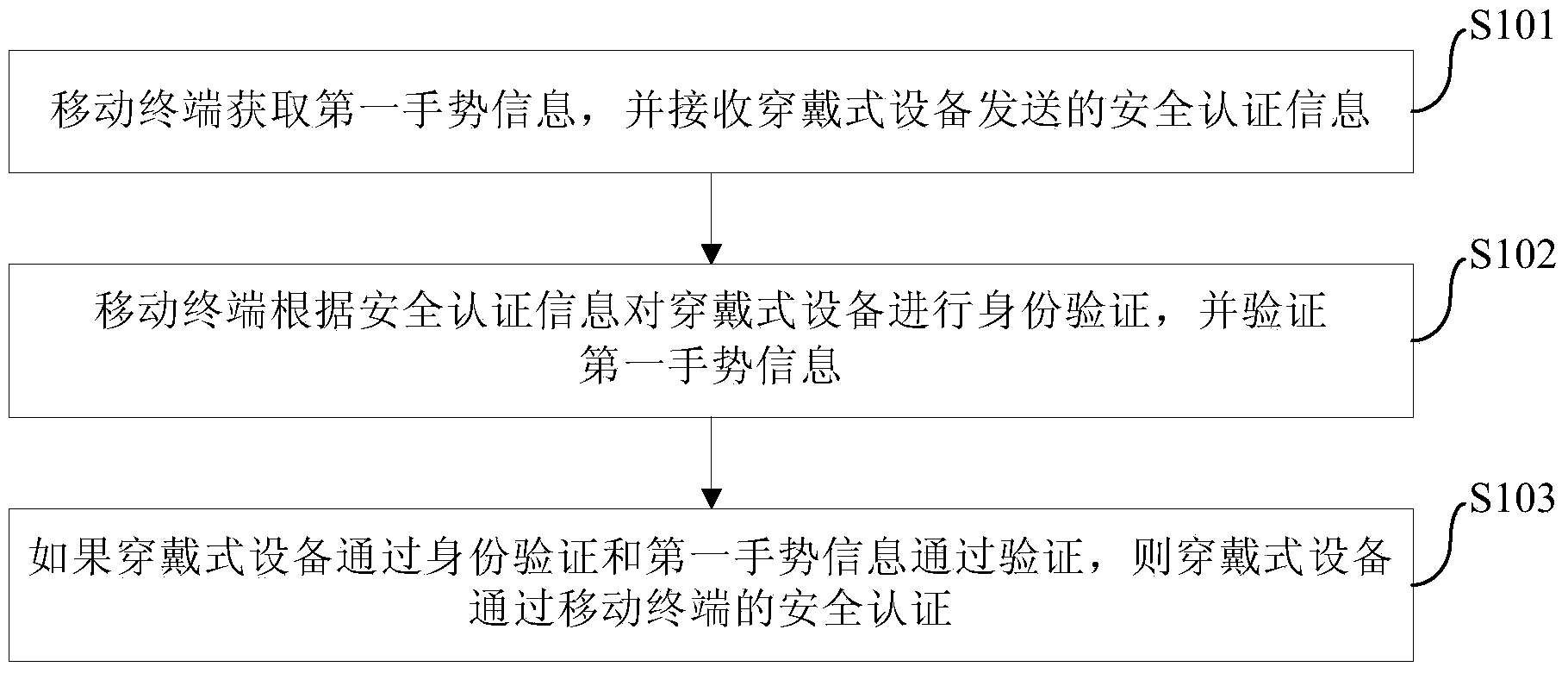
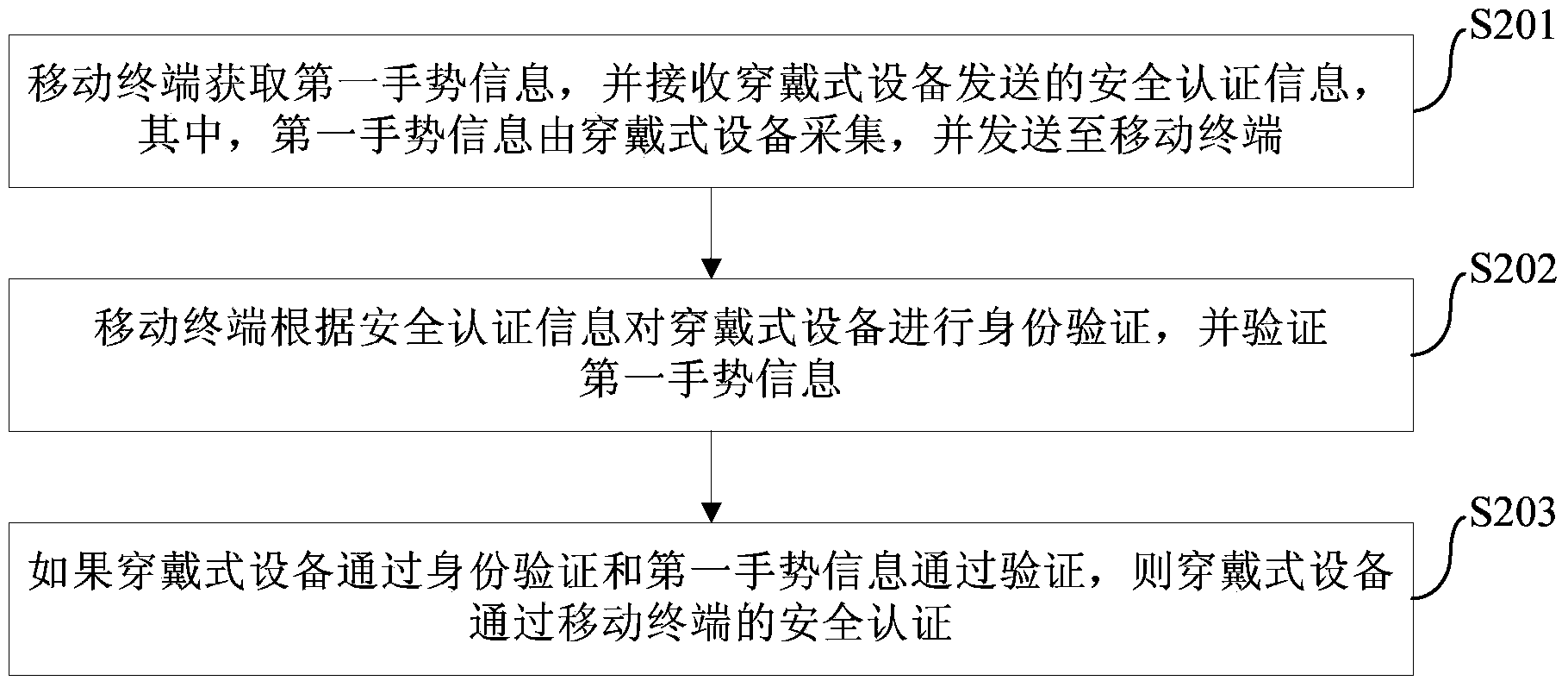
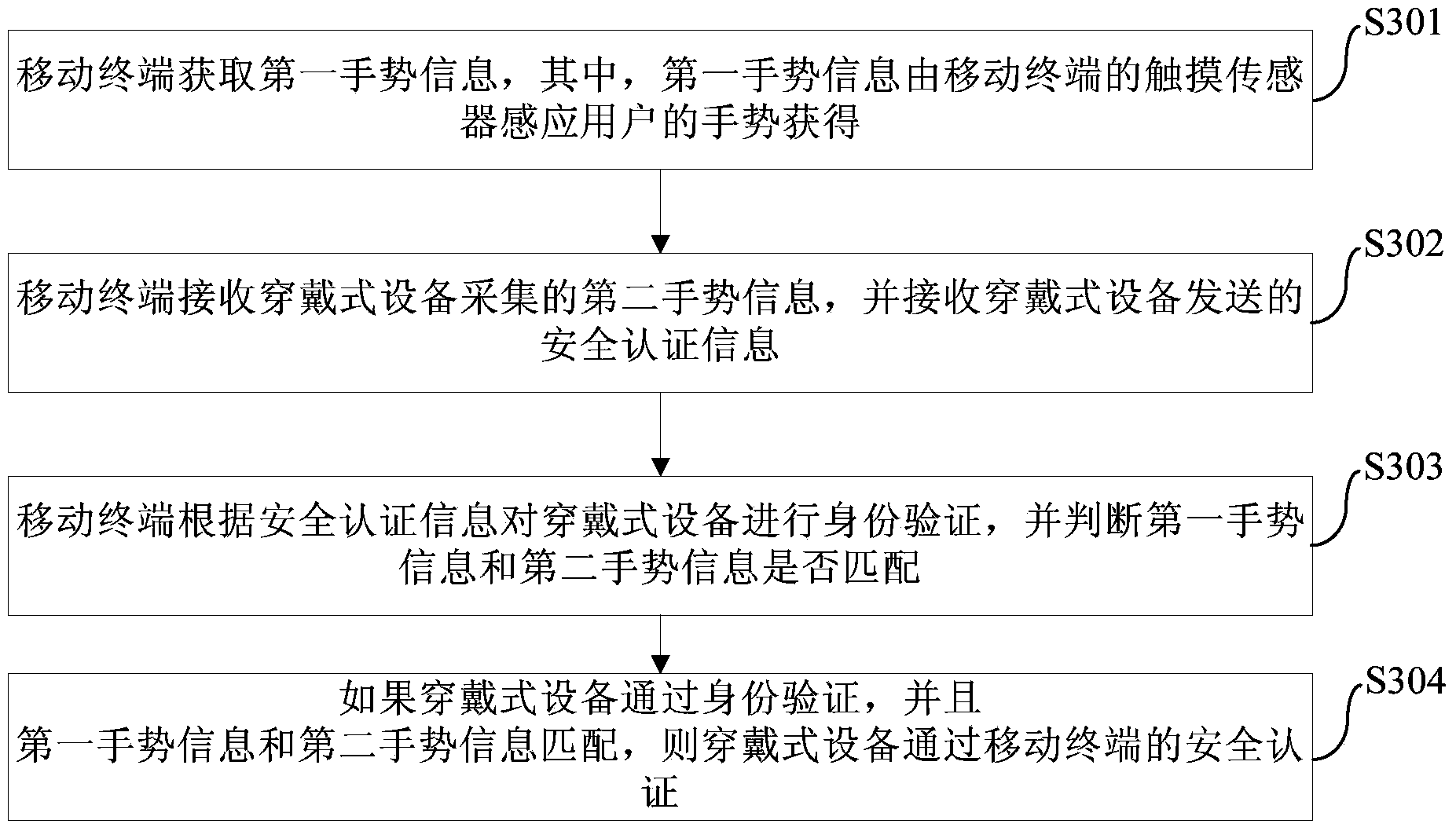
Mobile terminal security certification method and system and mobile terminal
InactiveCN104050402AImprove experienceEnsure safetyInput/output for user-computer interactionDigital data authenticationUser privacyComputer terminal
The invention provides a mobile terminal security certification method and system and a mobile terminal, wherein the method comprises the steps that the mobile terminal obtains first gesture information and receives security certification information sent by a wearable device; the mobile terminal carries out identity authentication on the wearable device according to the security certification information and authenticates the first gesture information; if the wearable device passes the identity authentication and the first gesture information passes the authentication, the wearable device passes the security certification of the mobile terminal. By applying the mobile terminal security certification method disclosed by the embodiment of the invention, security of user data stored in the mobile terminal is guaranteed, the user privacy is avoided being leaked, and the user experience is enhanced.
Owner:SHENZHEN GOODIX TECH CO LTD
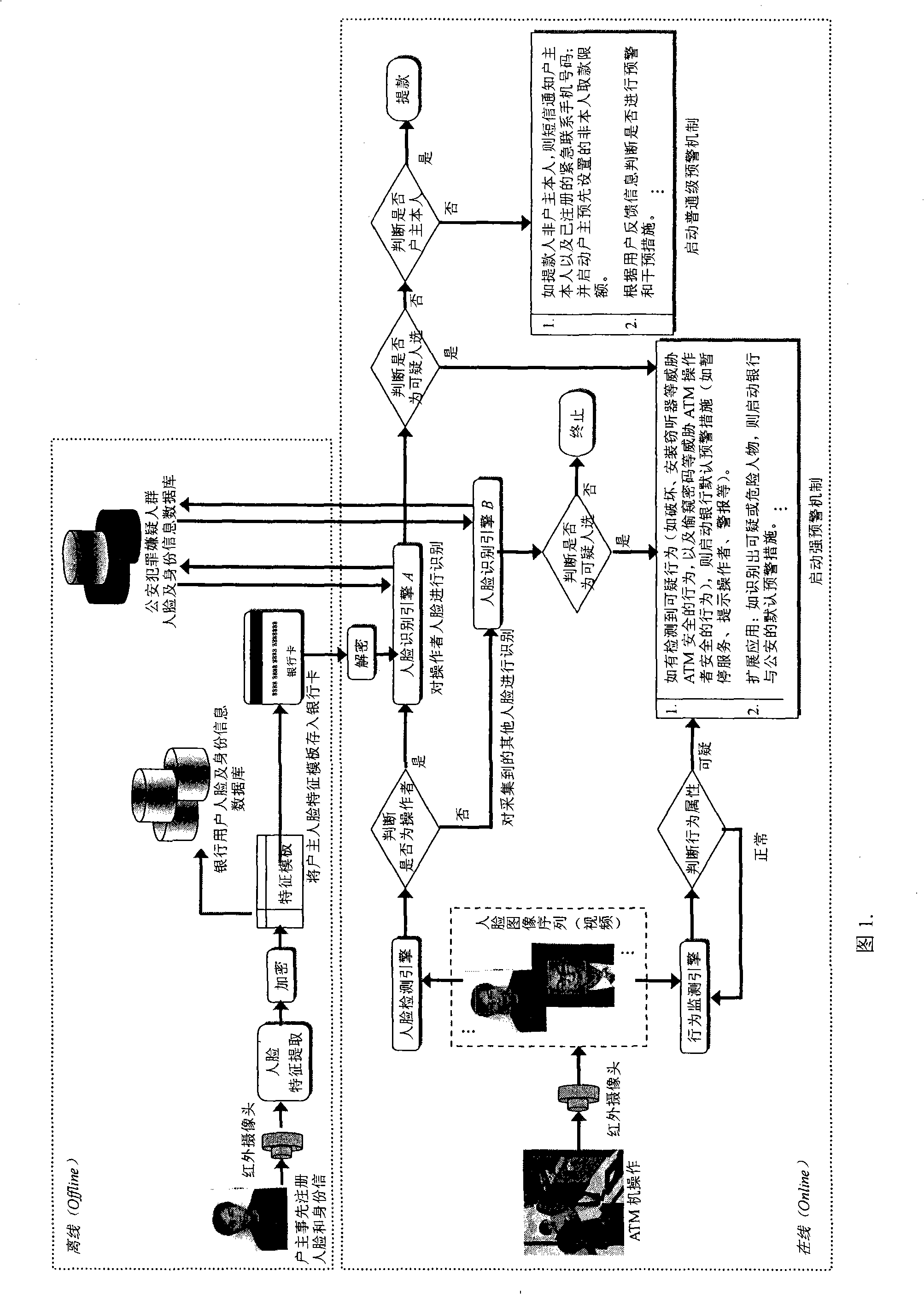
ATM secure authentication and pre-alarming method based on face recognition
ActiveCN101266704AEnsure safetyGuaranteed privacyCharacter and pattern recognitionAlarmsComputer networkAcquisition apparatus
The invention discloses an ATM security certificate and a pre-warning method based on face recognition. The invention introduces face recognition and video detection into the applications of ATM and bank card business for the first time, which can obviously improve the security of ATM financial system, effectively reduce and overawe various ATM fraud and criminal activities. The complete system operation process in the method of the invention is: firstly, registering the face information of a holder at a service window which arranges an infrared face acquisition equipment or with the registration by the users themselves on ATM in bank, and saving the encrypted face information to a bank database and a bank card. Then, determining whether the ATM operator to be recognized is the holder of the bank card or not through verifying the user's identity by a face recognition engine; determining and recognizing whether existing behaviors that threaten ATM and the users though a behavior monitoring engine; and determining whether to trigger corresponding pre-warning mechanism or not according to the recognition result. The invention can extend to the applications of bank book business, public security monitoring and pursuing escaped criminals, etc.
Owner:哈尔滨维科智能系统有限公司
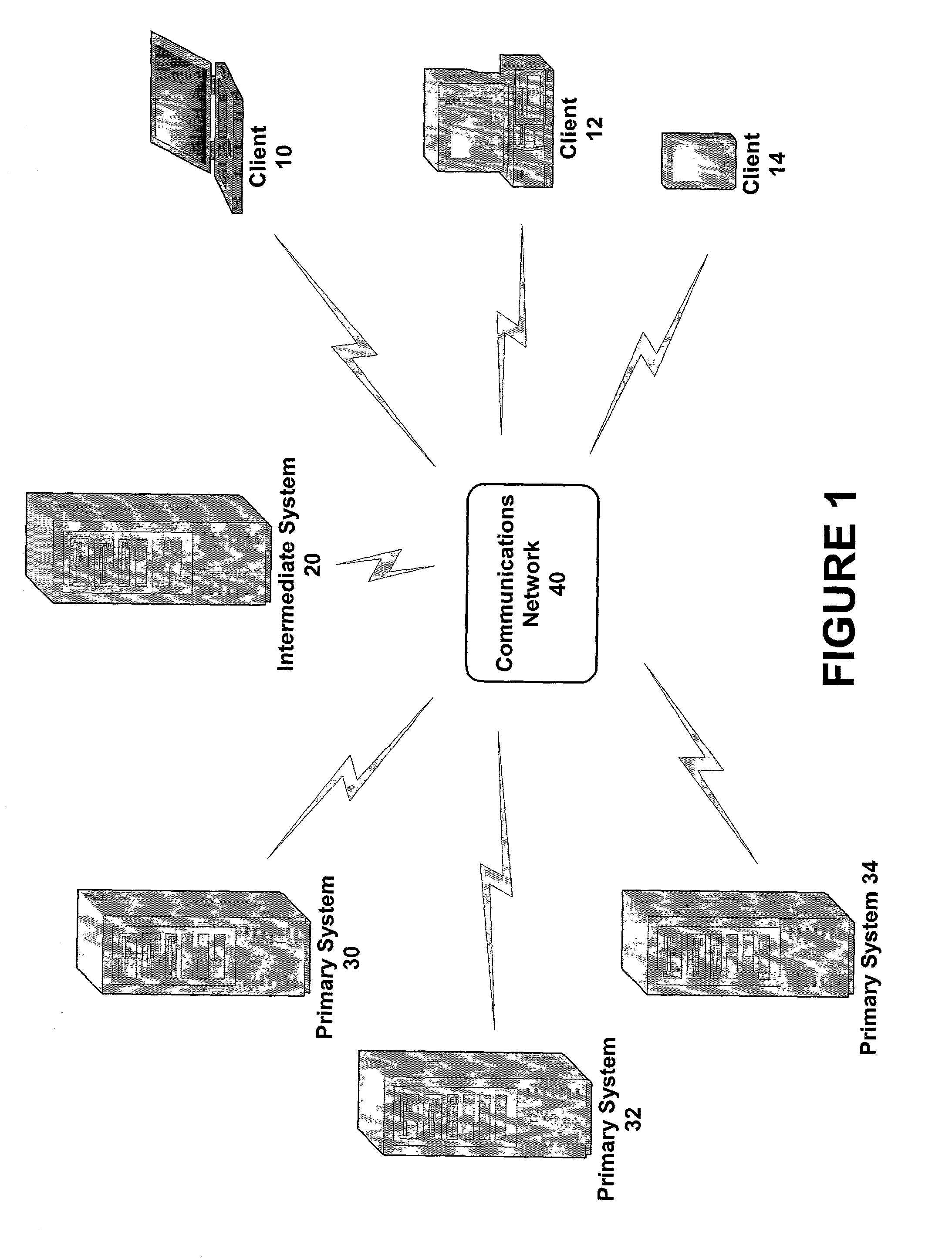
Secure authentication in a multi-party system
ActiveUS20130263211A1Easy to modifyWeb data indexingDigital data processing detailsUser verificationInternet privacy
An authentication server transmits a random number to and receives a other information from a service provider. Later, the first random number is received from a requester and a provider identifier, the received other information and provider authentication policy requirements are transmitted to the requester. A user identifier and validation information are received from the requester. The received validation information is determined to correspond to the provider authentication policy requirements, and compared with stored user validation information associated with the received user identifier to authenticate the requester. A message, including both the random number and other information, signed with a credential of the requesting user is received and transmitted to the first provider.
Owner:PAYFONE
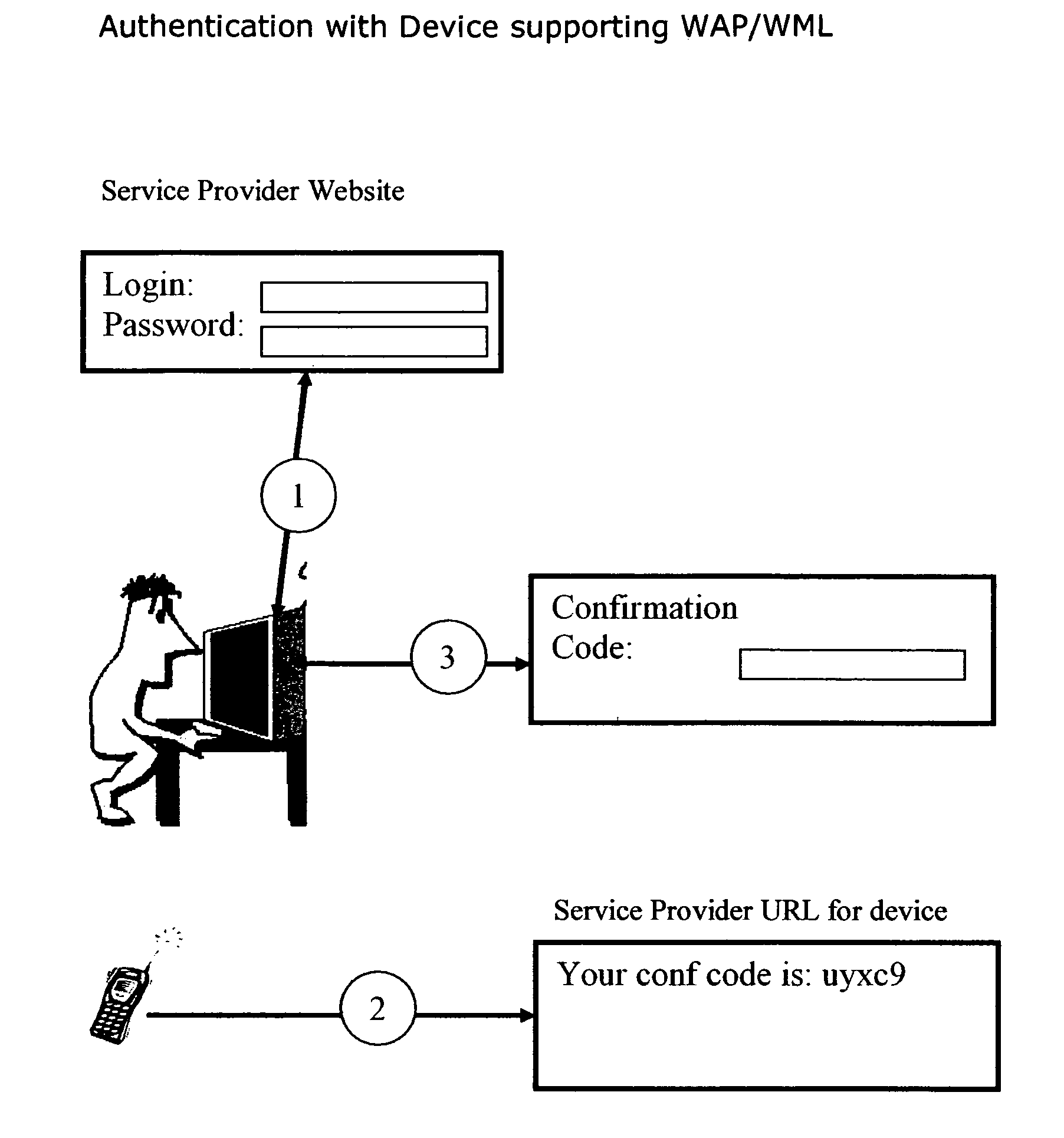
Simple two-factor authentication
InactiveUS20070107050A1Eliminate Internet fraudEasy accessRandom number generatorsUser identity/authority verificationPasswordThe Internet
Internet Security is increasingly of concern as more and more cases of identity theft of online data is reported. Simple login and password authentication for access to sensitive websites like financial, health or other personal data is no longer sufficient. Several mechanisms for additional security, called two-factor authentication have been proposed. Most of them involve the use of a physical device like a card which is read by a card reader or suggest the use of biometric authentication. Although, these are very secure, the cost of implementation of these “physical” authentications is high. This invention outlines the use of a simple two factor authentication using mobile phones, PDAs or Credit and Debit cards that most users already have, without the need for any special hardware.
Owner:JEXP
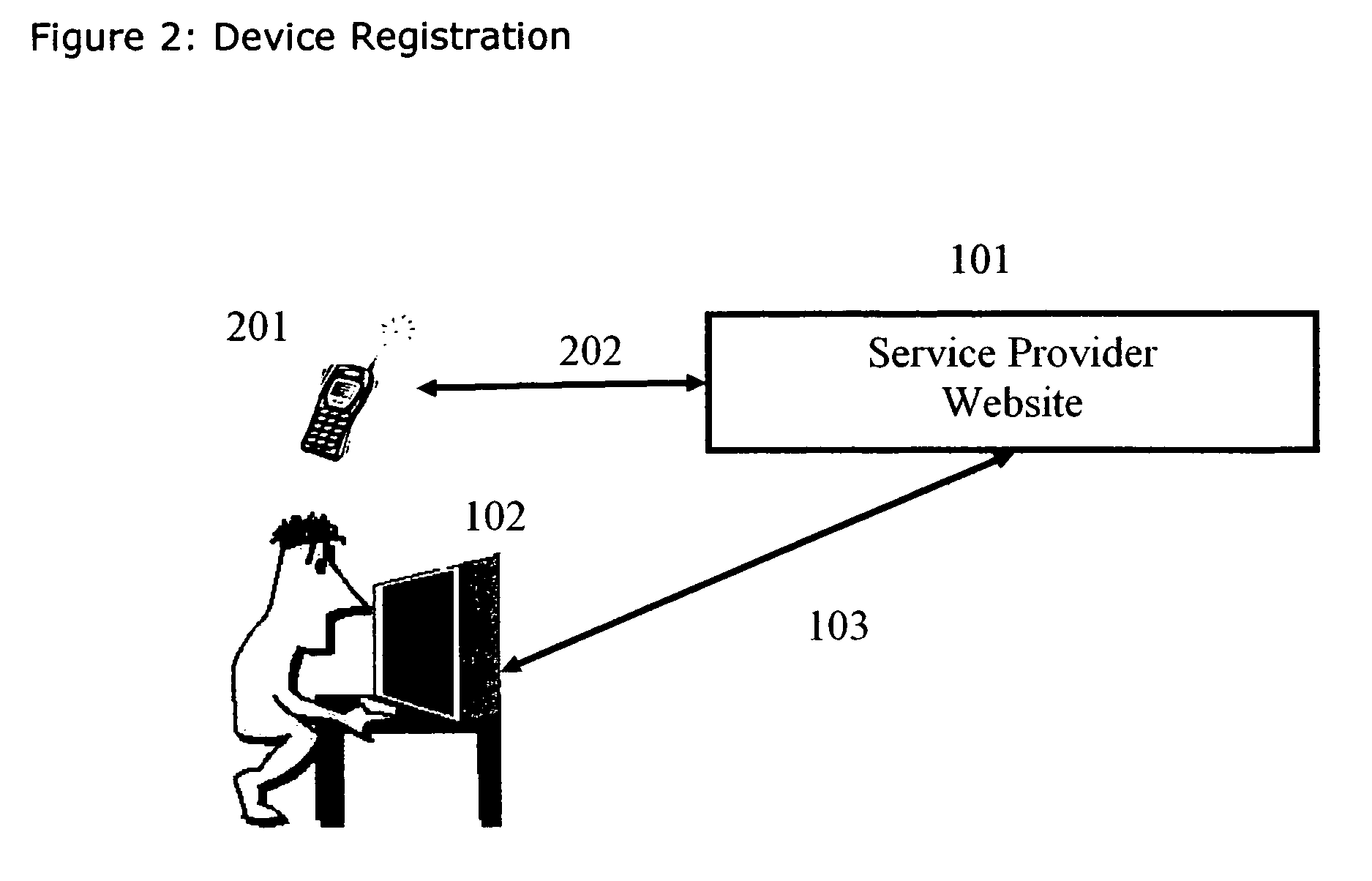
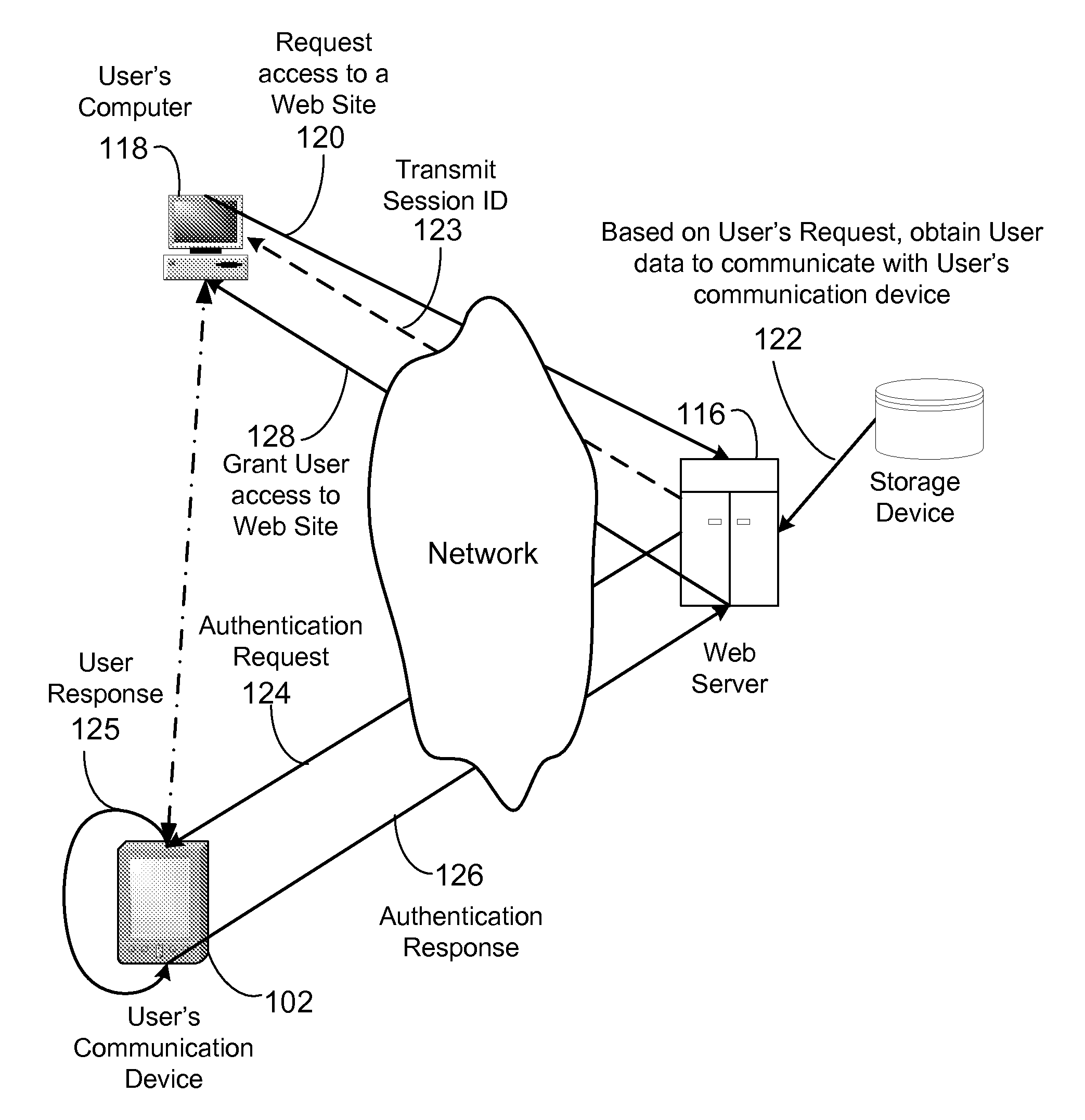
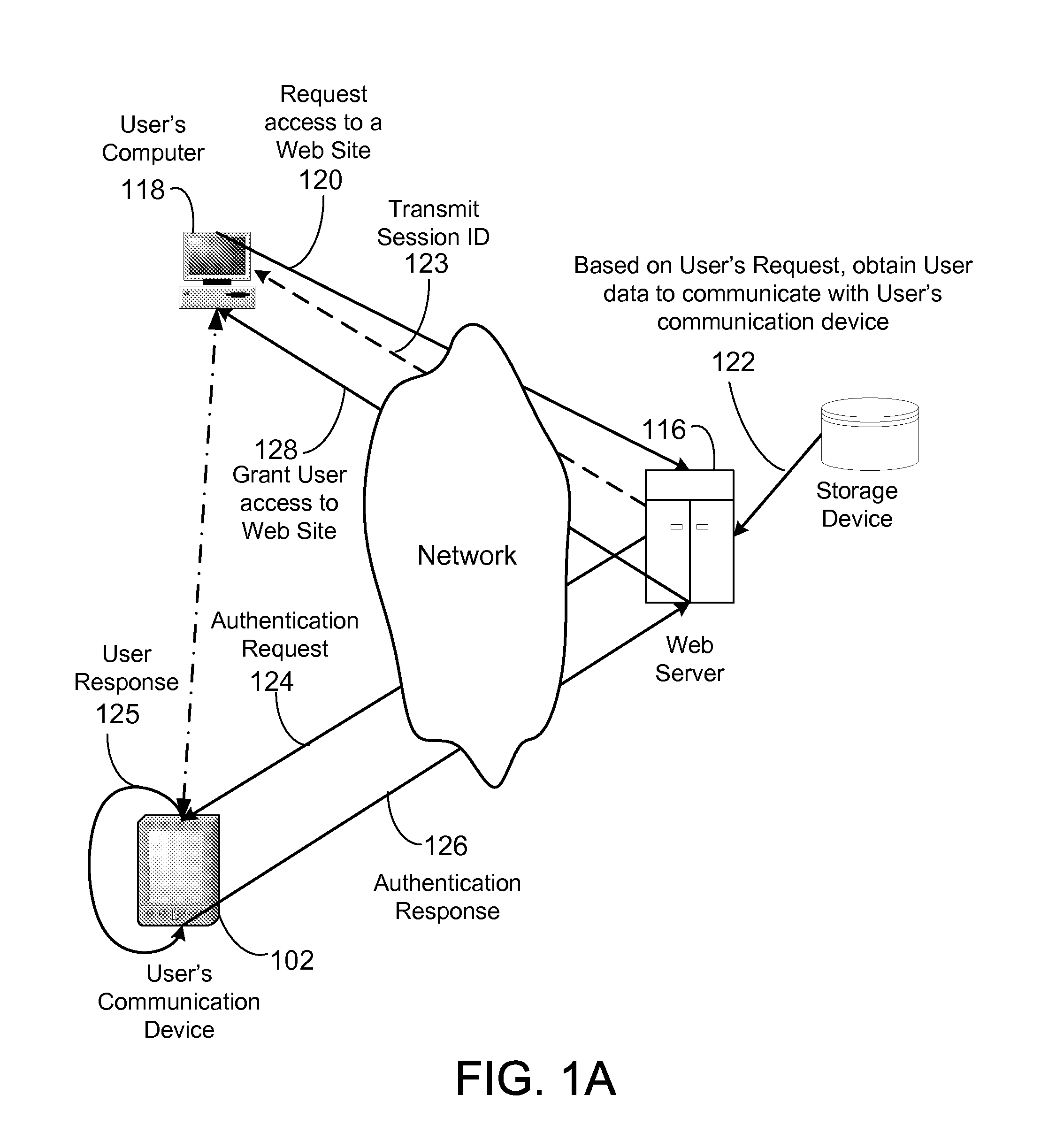
System and method for authenticating remote server access
ActiveUS20080098225A1User identity/authority verificationDigital data authenticationWeb serviceSecure authentication
A system and method for providing secure authentication for website access or other secure transaction. In one embodiment, when a user accesses a website, the web server identifies the user, and sends an authentication request to the user's mobile device. The mobile device receives the authentication requests and sends back authentication key to the web server. Upon verifying the authentication key, the web server grants the access to the user.
Owner:QUALCOMM INC
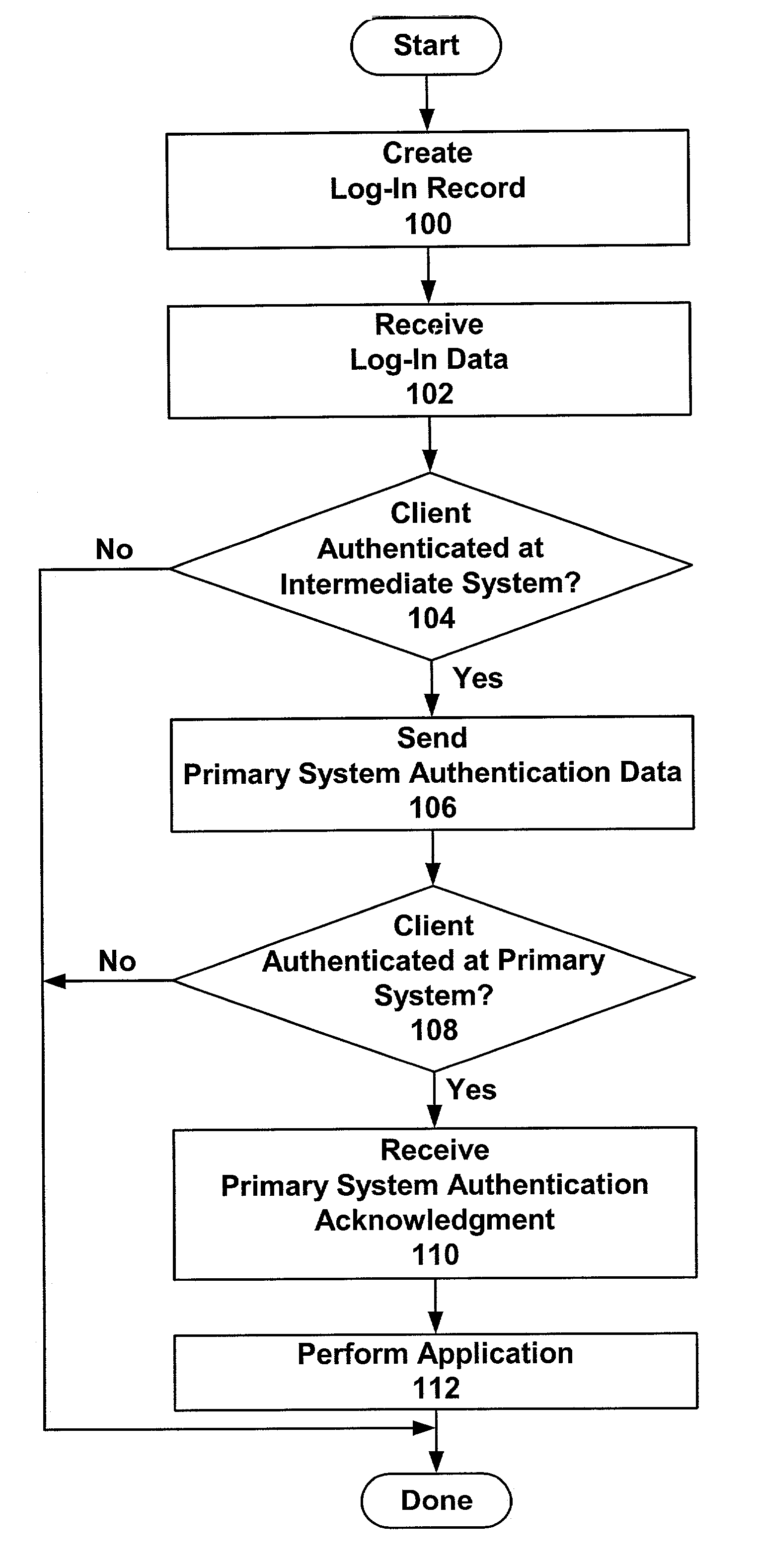
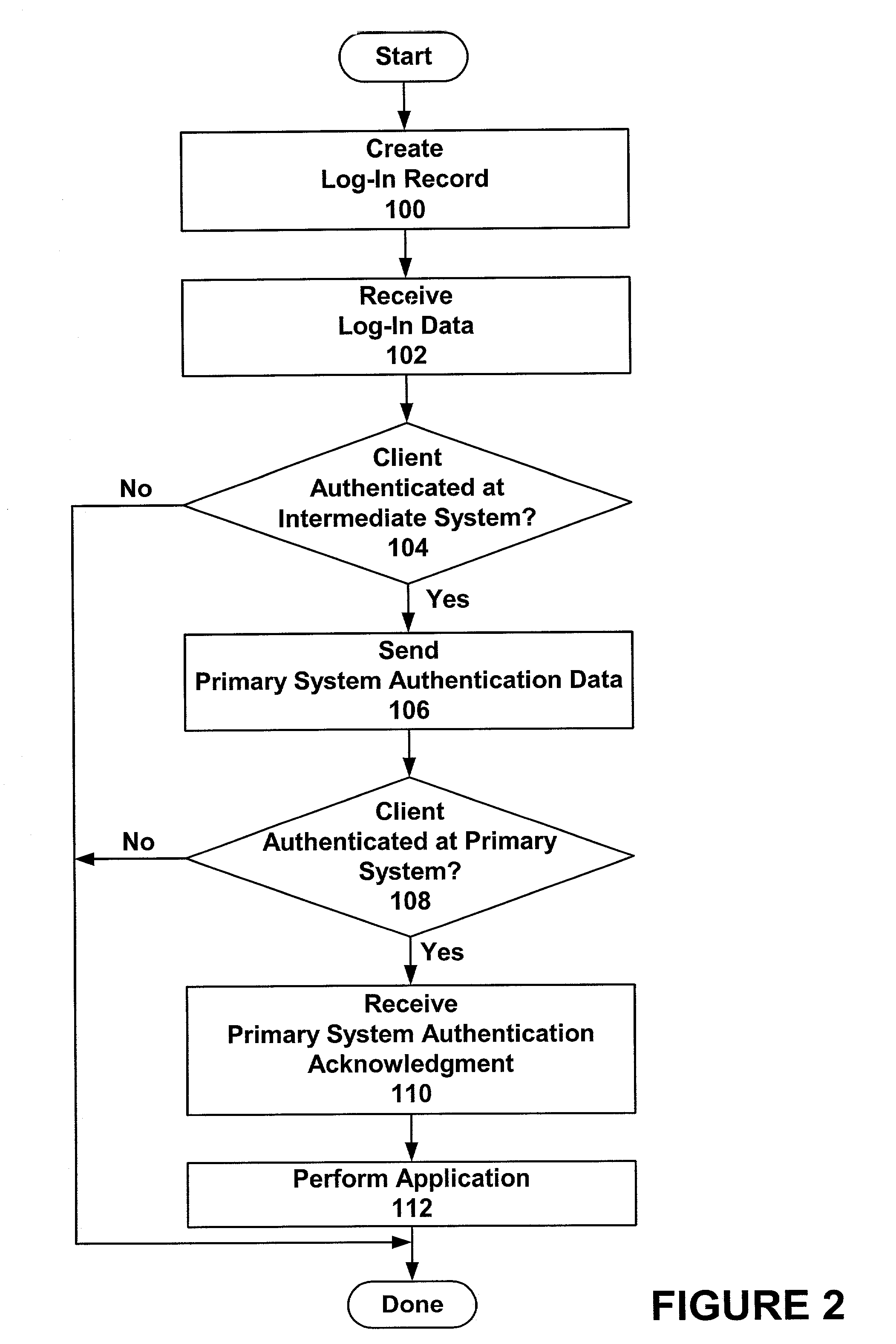
Secure authentication of users via intermediate parties
InactiveUS7003668B2Eliminate storageDigital data processing detailsUser identity/authority verificationClient-sideSecure authentication
Owner:SYNCHRONOSS TECH
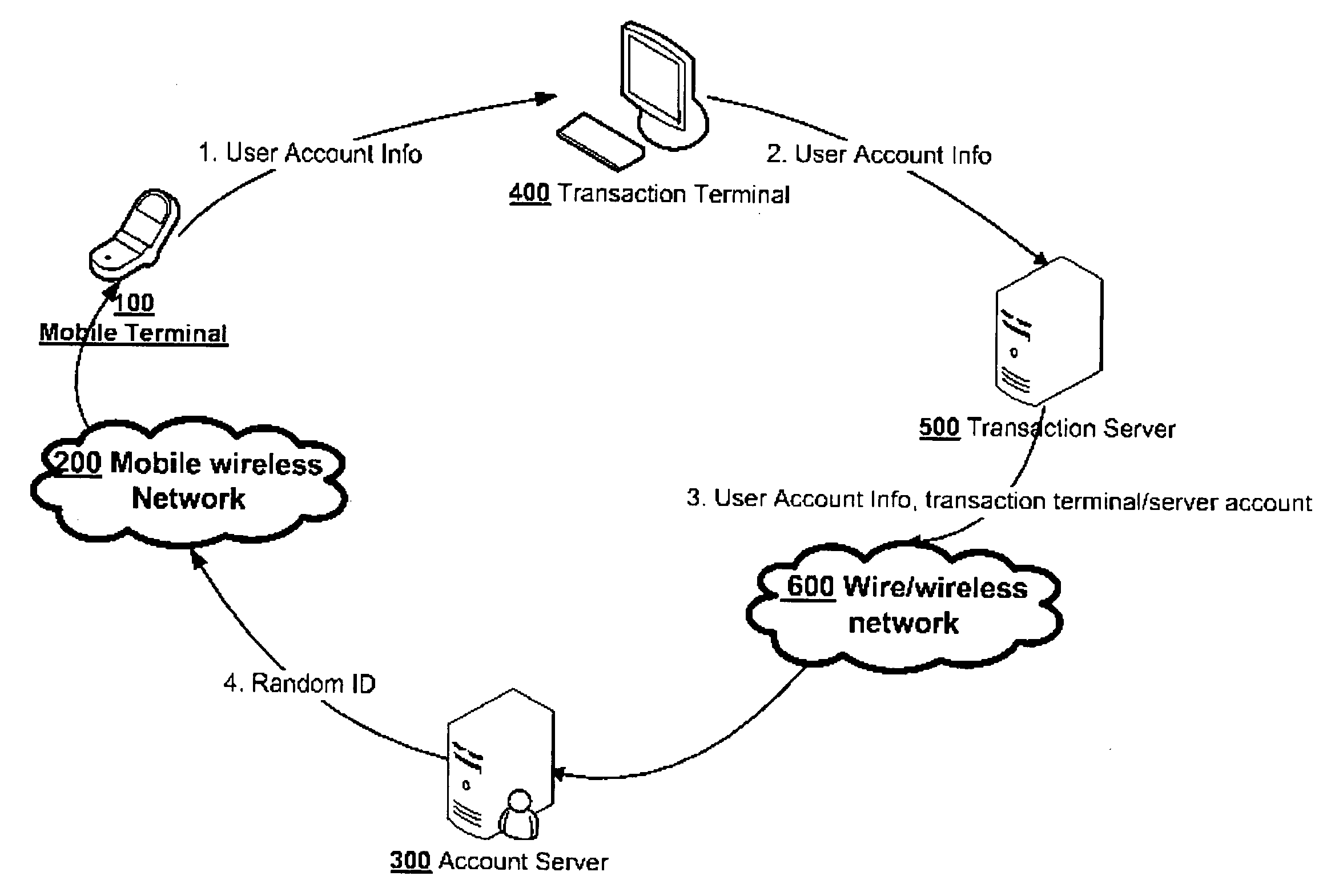
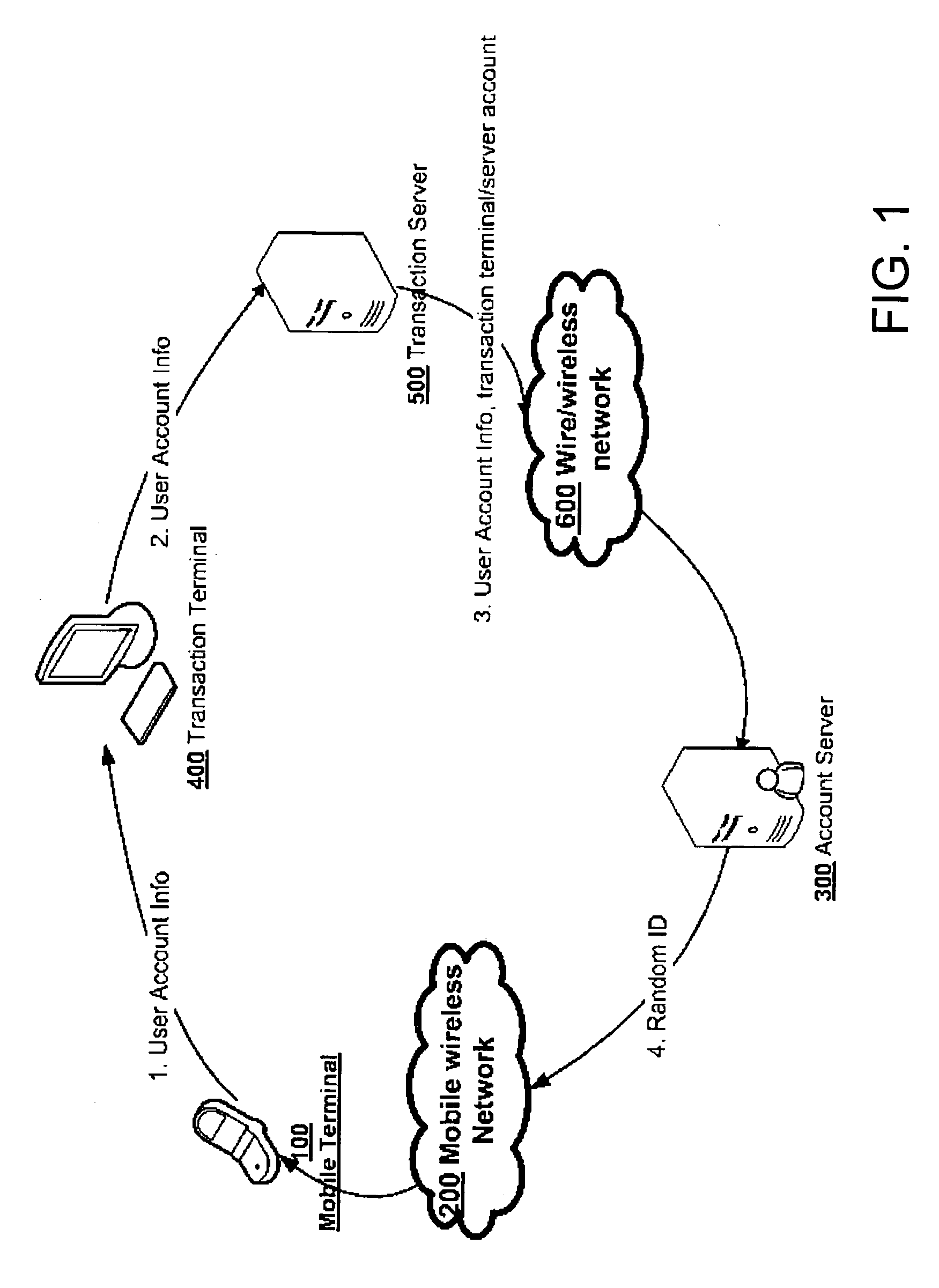
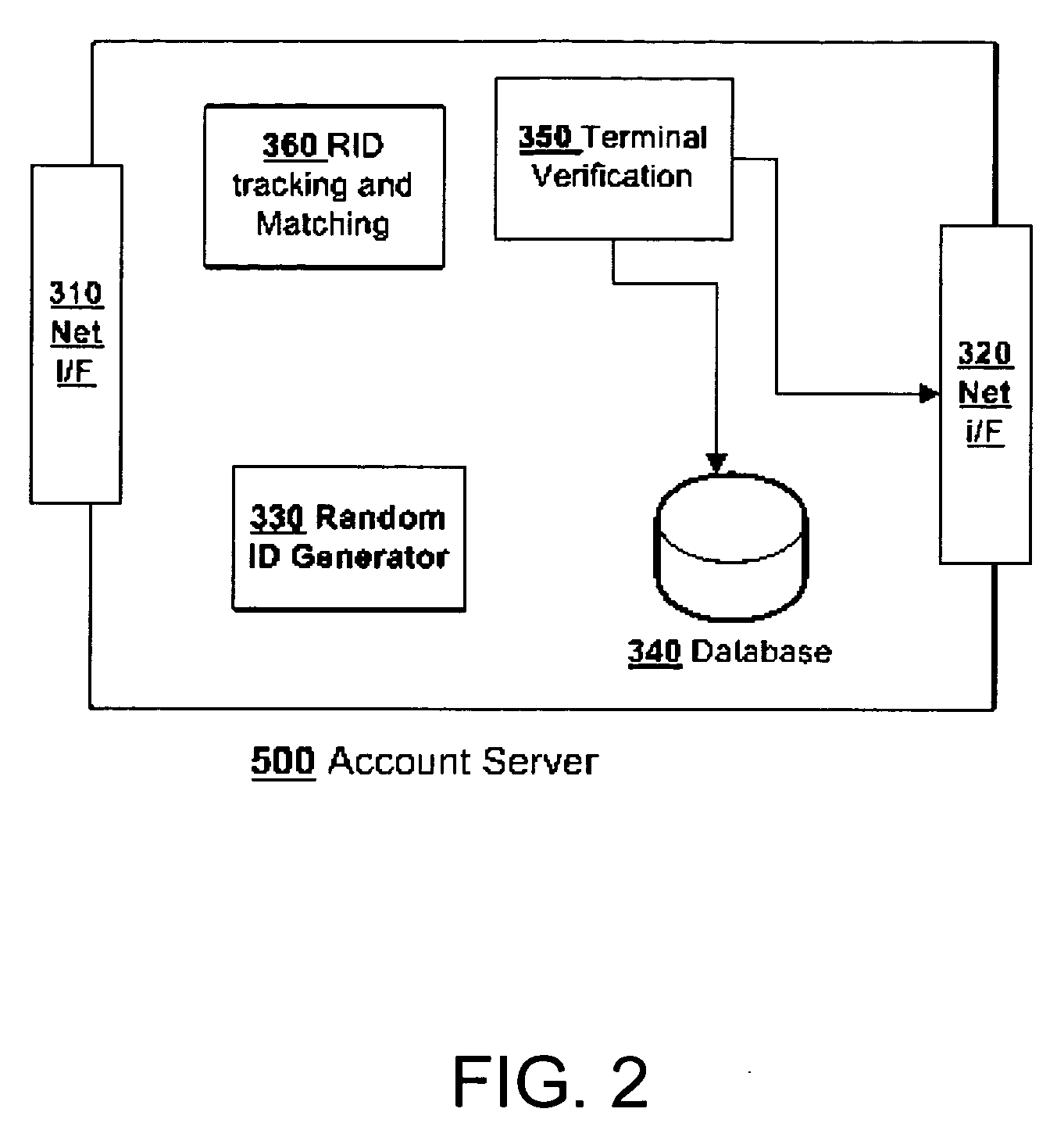
Method and apparatus of secure authentication and electronic payment through mobile communication tool
InactiveUS20070130085A1Easy to solveComputer security arrangementsPayment architecturePaymentComputer terminal
The present invention relates to apparatus and method utilizing a mobile terminal as a tool for secure authentication and electronic payment. A random ID code is passed through a circle path to verify the nodes along the path. If the RID sent back matches the one generated for the current transaction, the user is authenticated and the transaction is approved for further action. The user's account server generates a Random ID code when a transaction request is received. This RID will be passed to the user's mobile terminal and then passed to the terminal where the user request access or purchasing. The terminal will send the RID back to the account server. If the RID received and the original RID generated for this transaction matches the user is authenticated. The RID can also be passed through a reverse direction.
Owner:ZHU XI
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com