Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
4292 results about "Plaintext" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
In cryptography, plaintext usually means unencrypted information pending input into cryptographic algorithms, usually encryption algorithms. Cleartext usually refers to data that is transmitted or stored unencrypted ('in the clear').
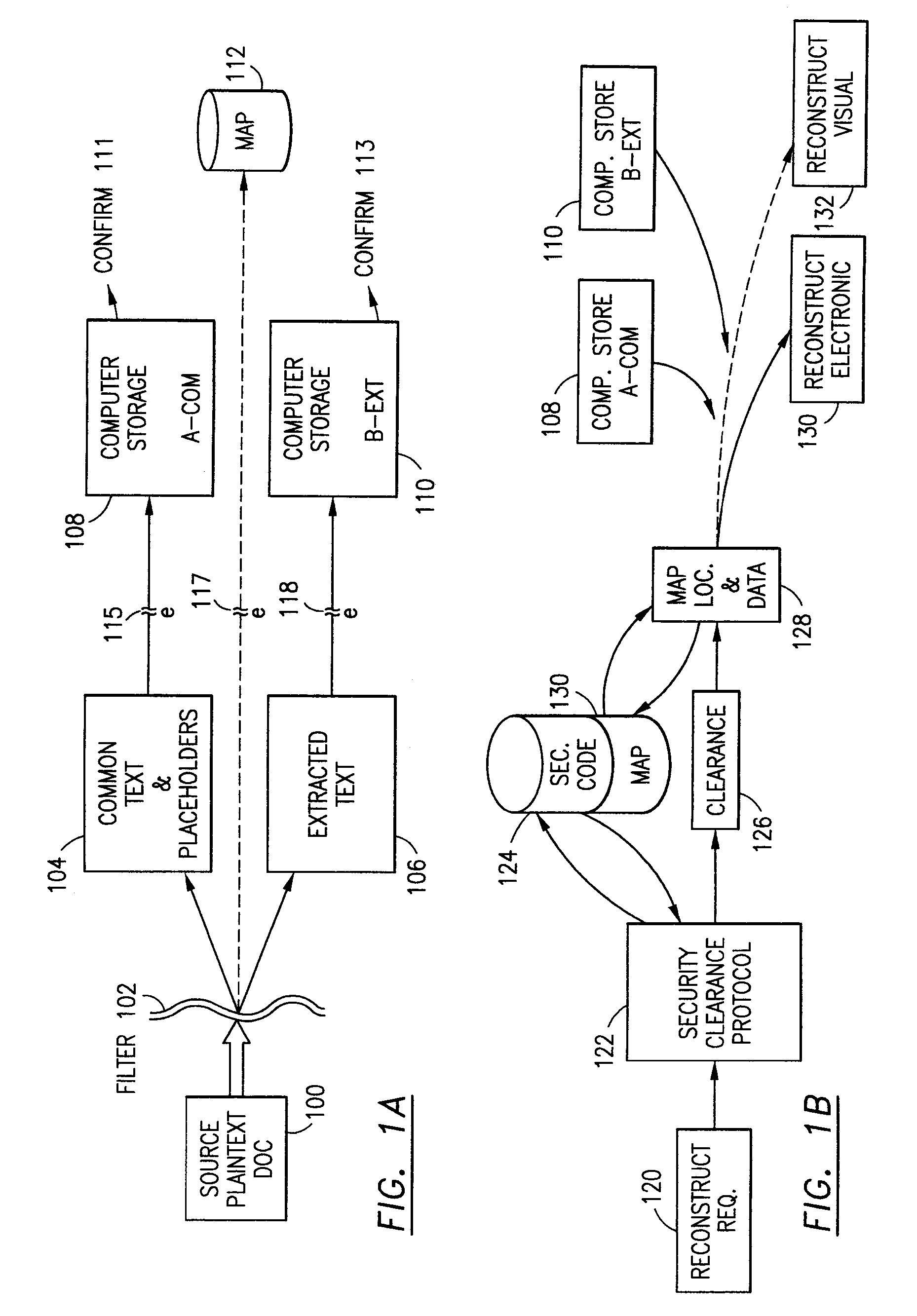
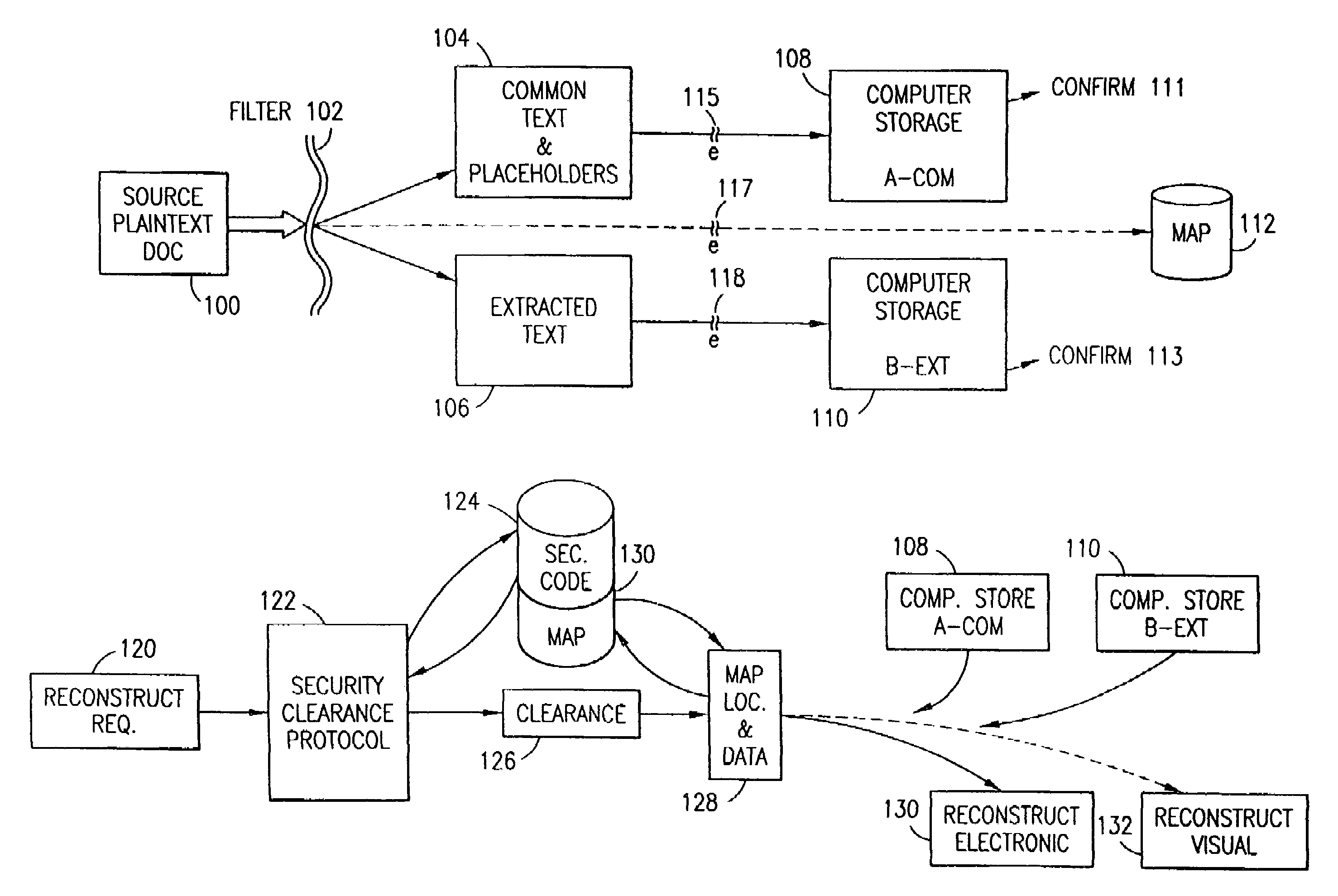
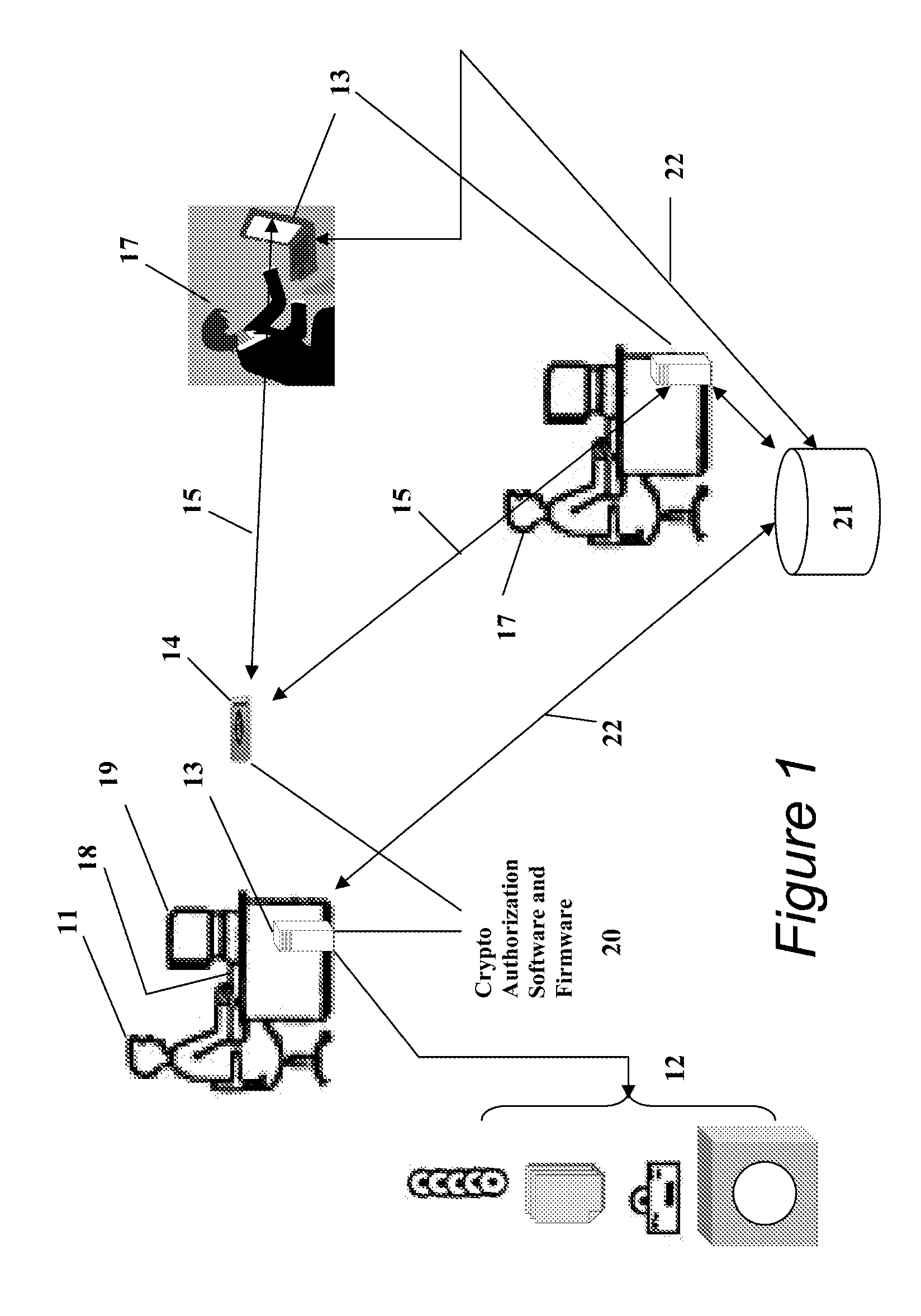
Data security system and method for separation of user communities
InactiveUS7140044B2Multiple keys/algorithms usageDigital data processing detailsInformation processingPlaintext
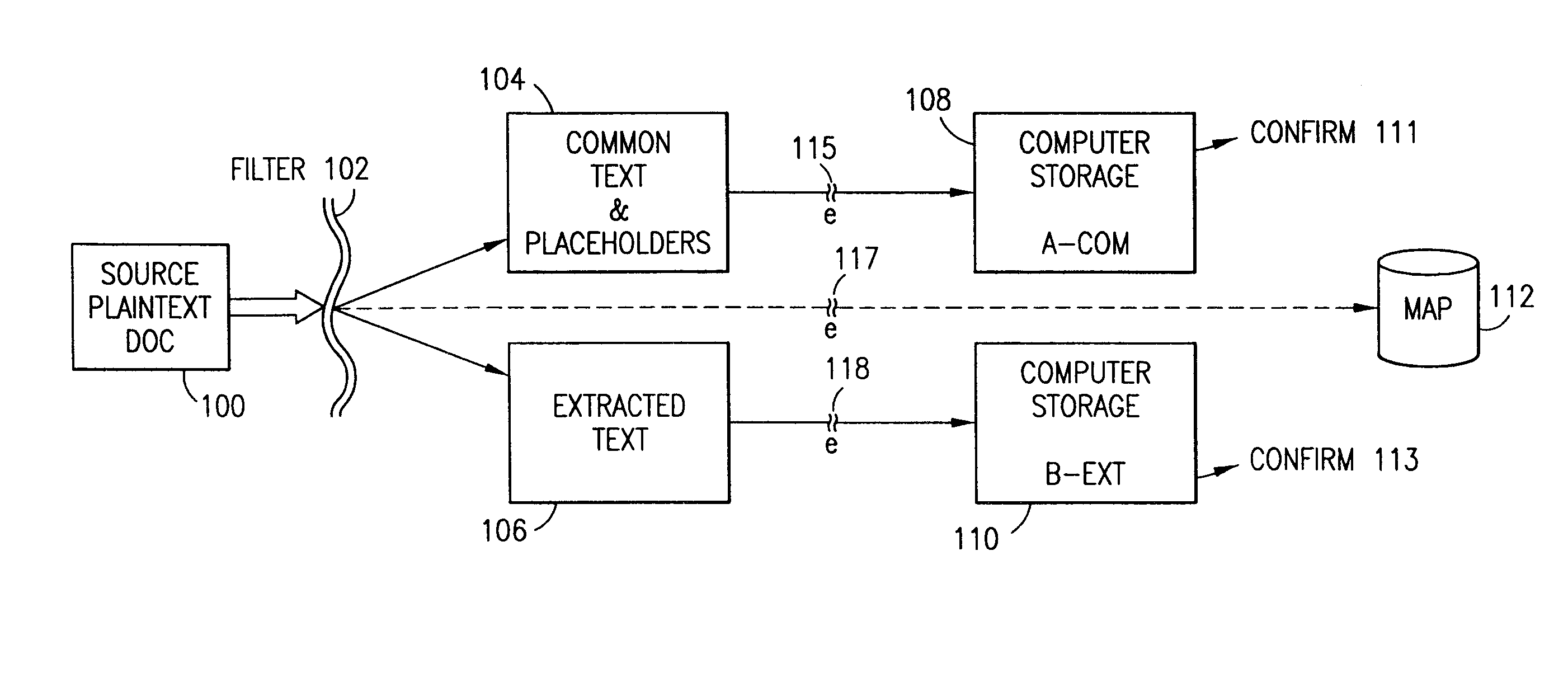
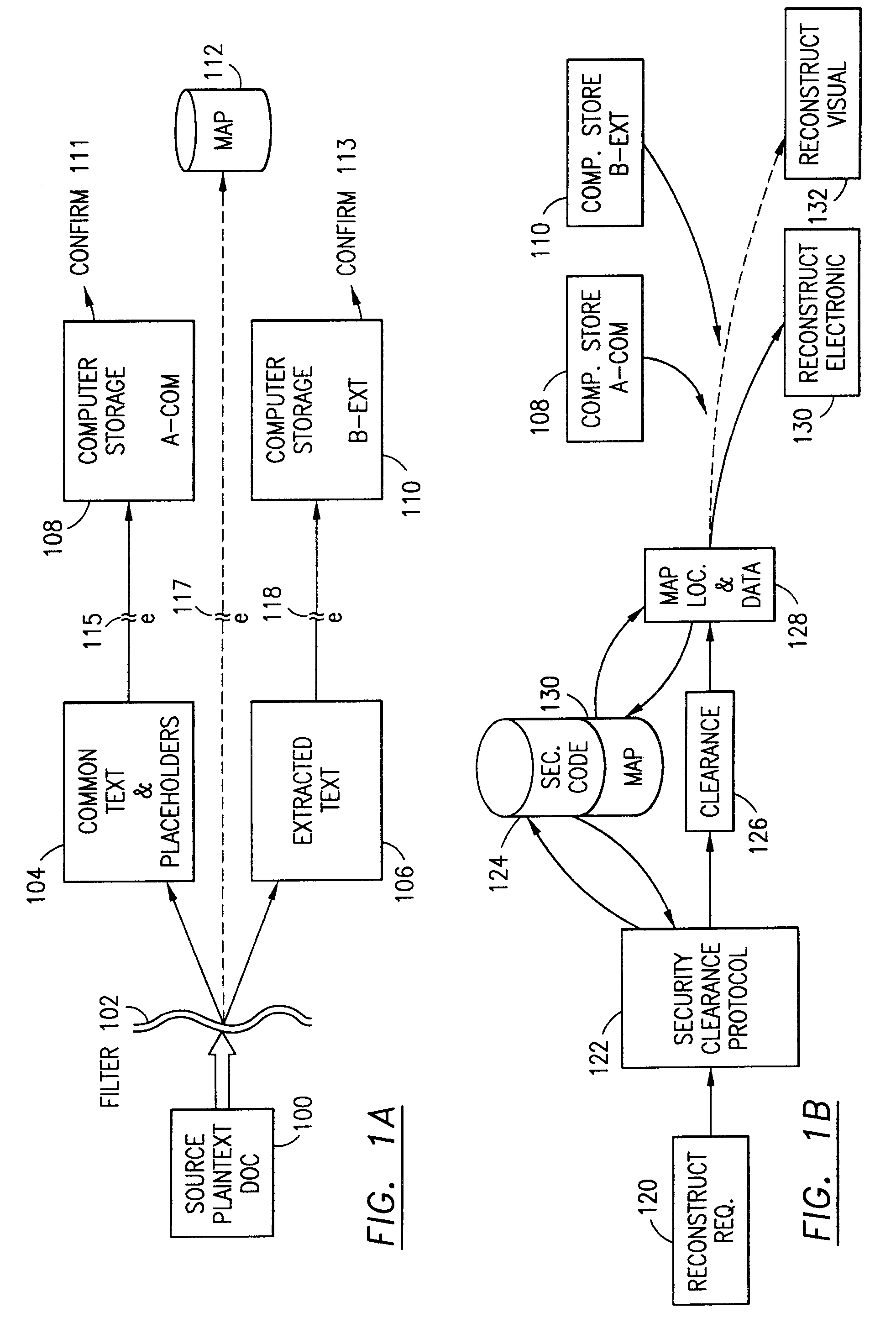
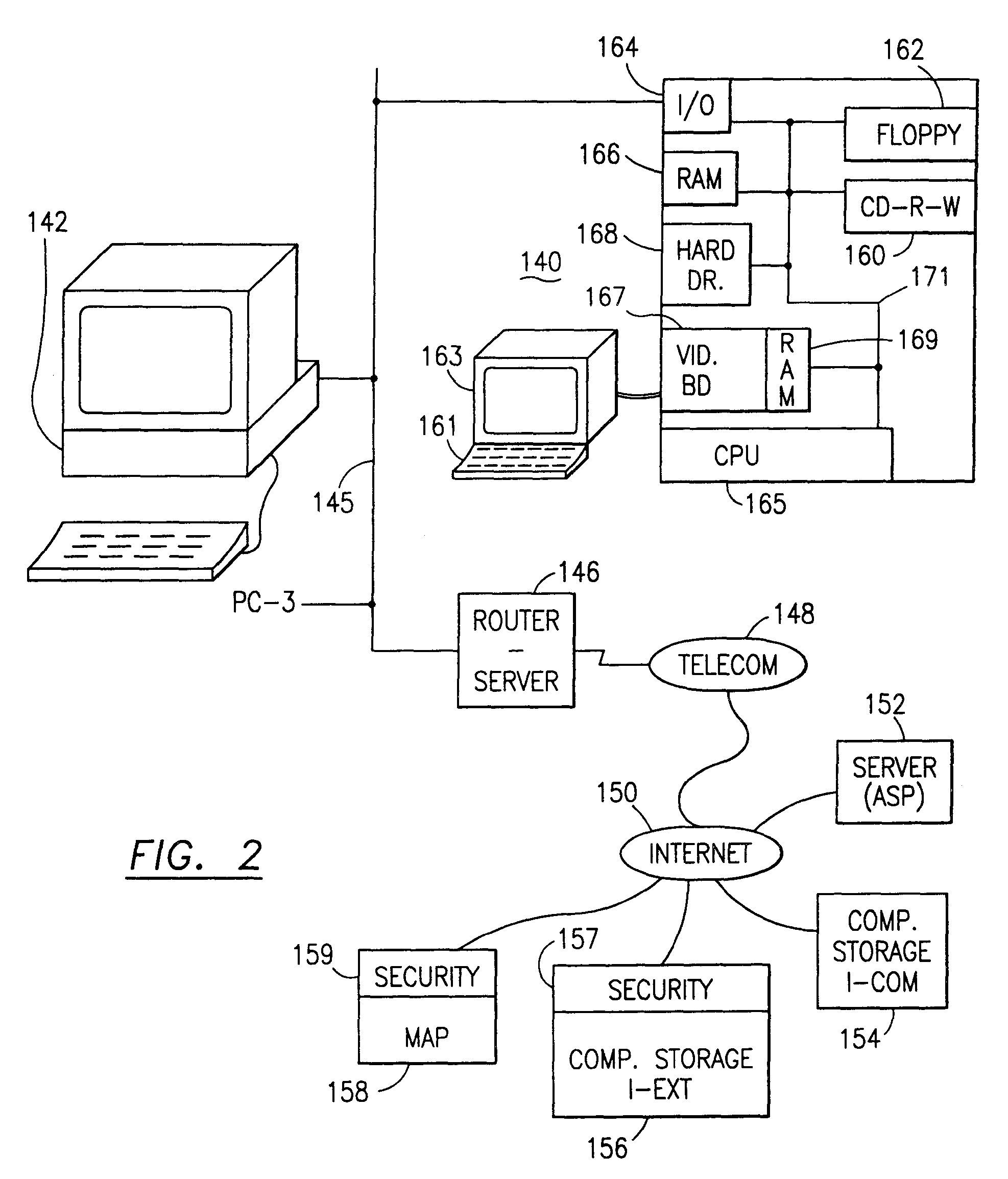
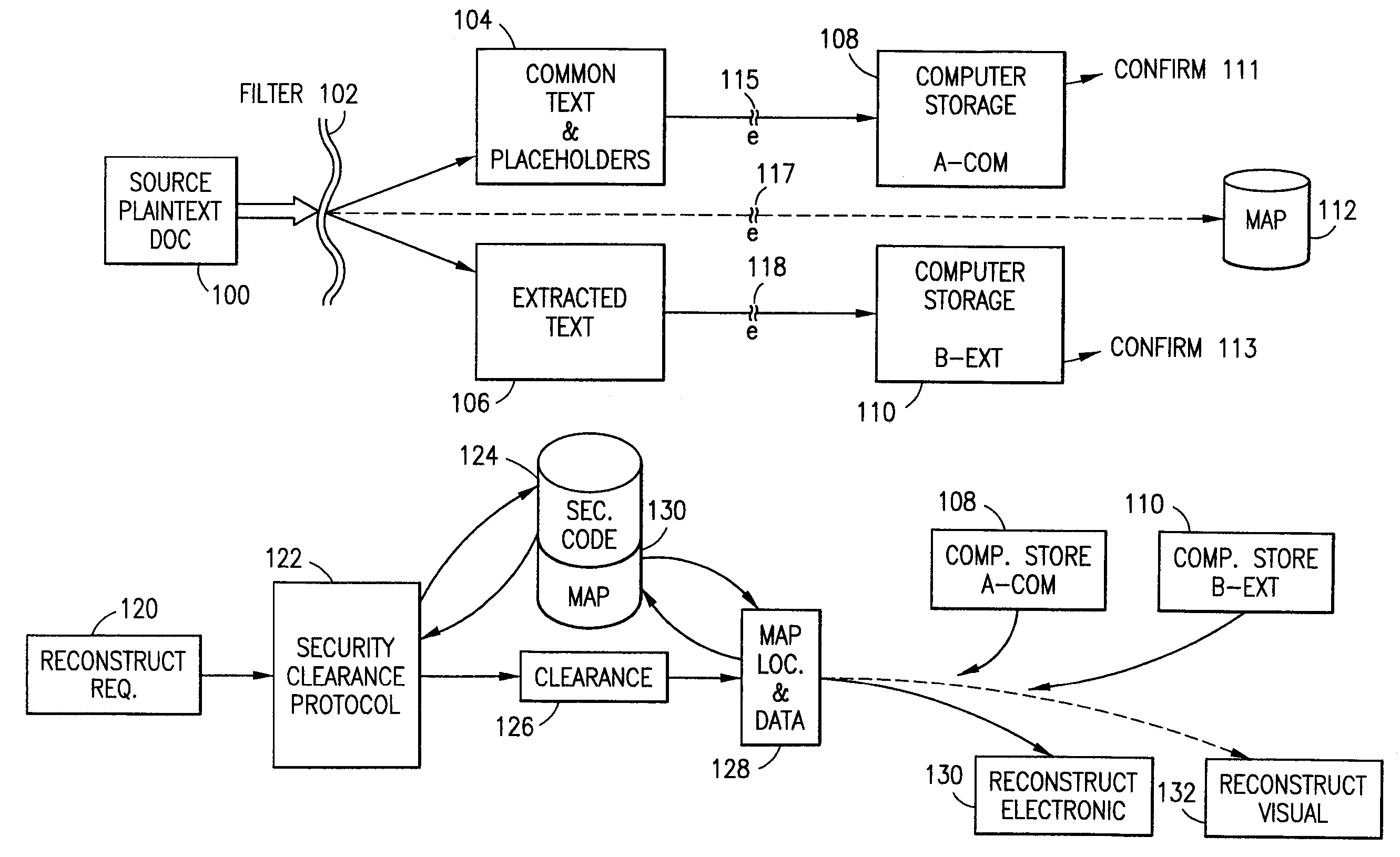
Data is secured in a computer network to transparently establish and manage a separation of user-based communities of interest based upon crypto-graphically separated, need to know, security levels. Data from a source document, data object or data stream is filtered to form subsets of extracted data and remainder data based upon security levels for the communities. Extracts are stored in assigned memories. Full or partial plaintext reconstruction is permitted only in the presence of assigned security clearance for the community of the inquiring party. Encryption, corresponding to security levels, establishes separation of secured data. The information processing system uses a data filter to extract security sensitive words, data objects, etc., a distributed storage system and a compiler is used to reconstruct plaintext based on security clearance. Multiple level encryption in one document is also available.
Owner:DIGITAL DOORS
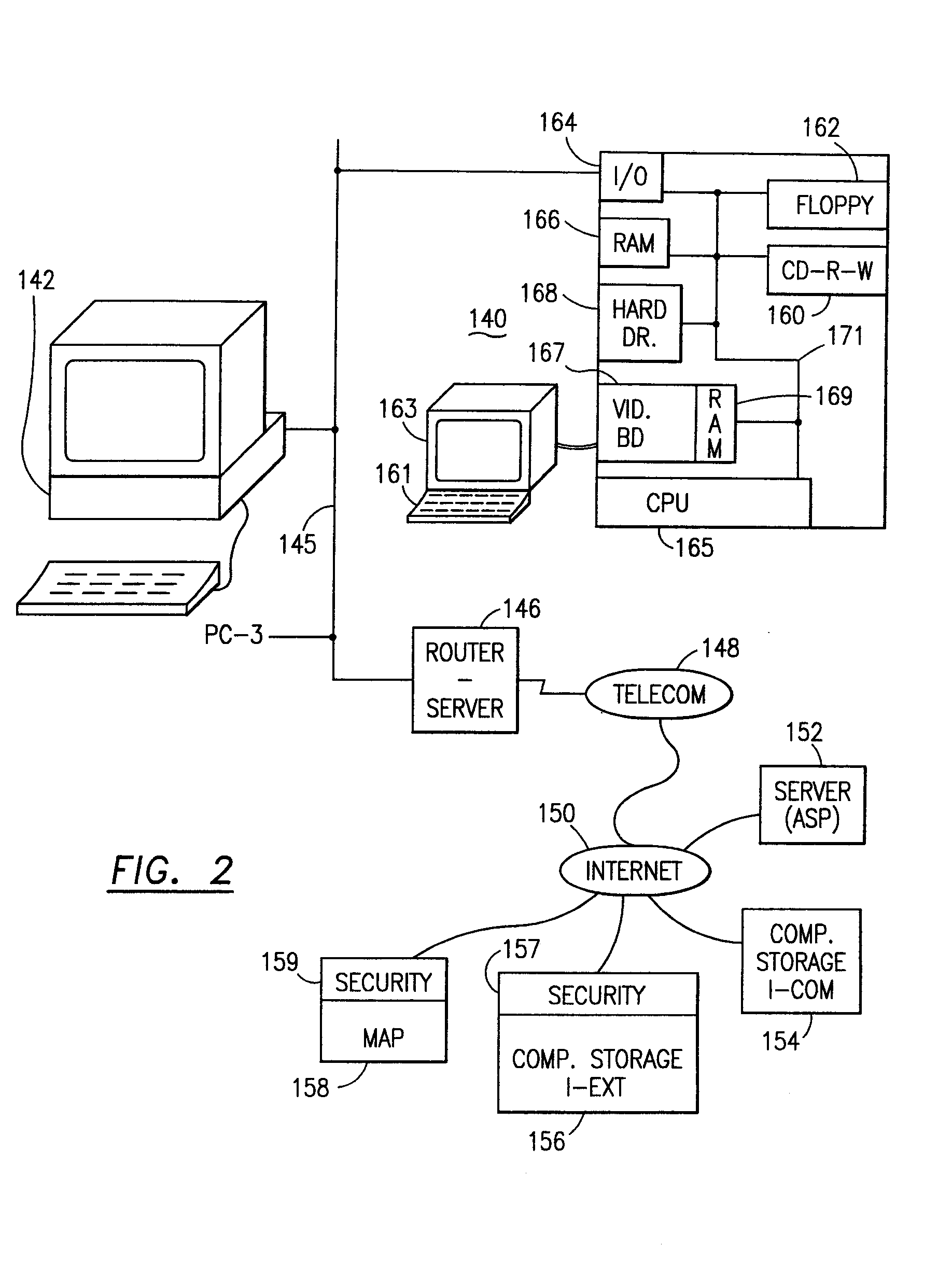
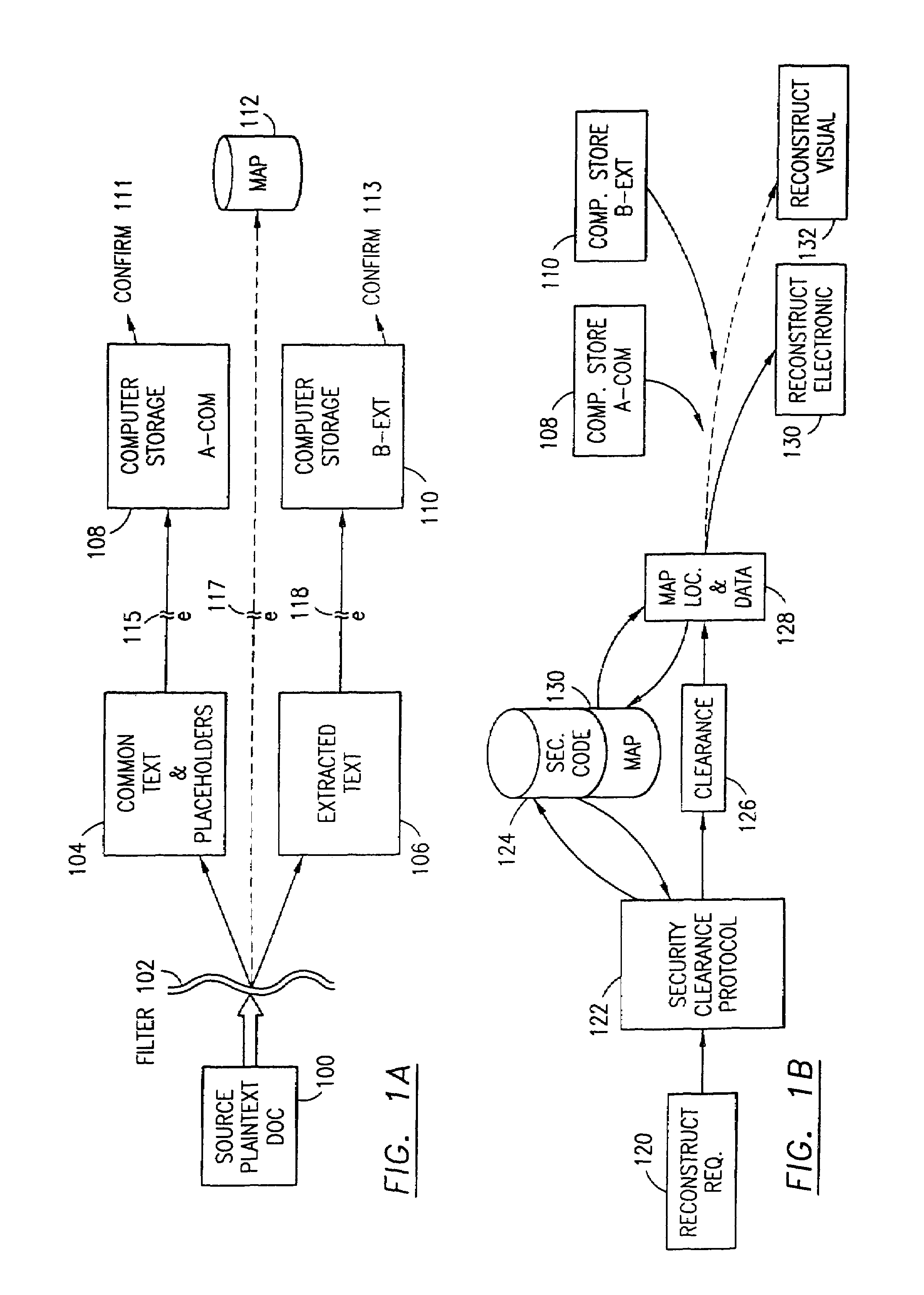
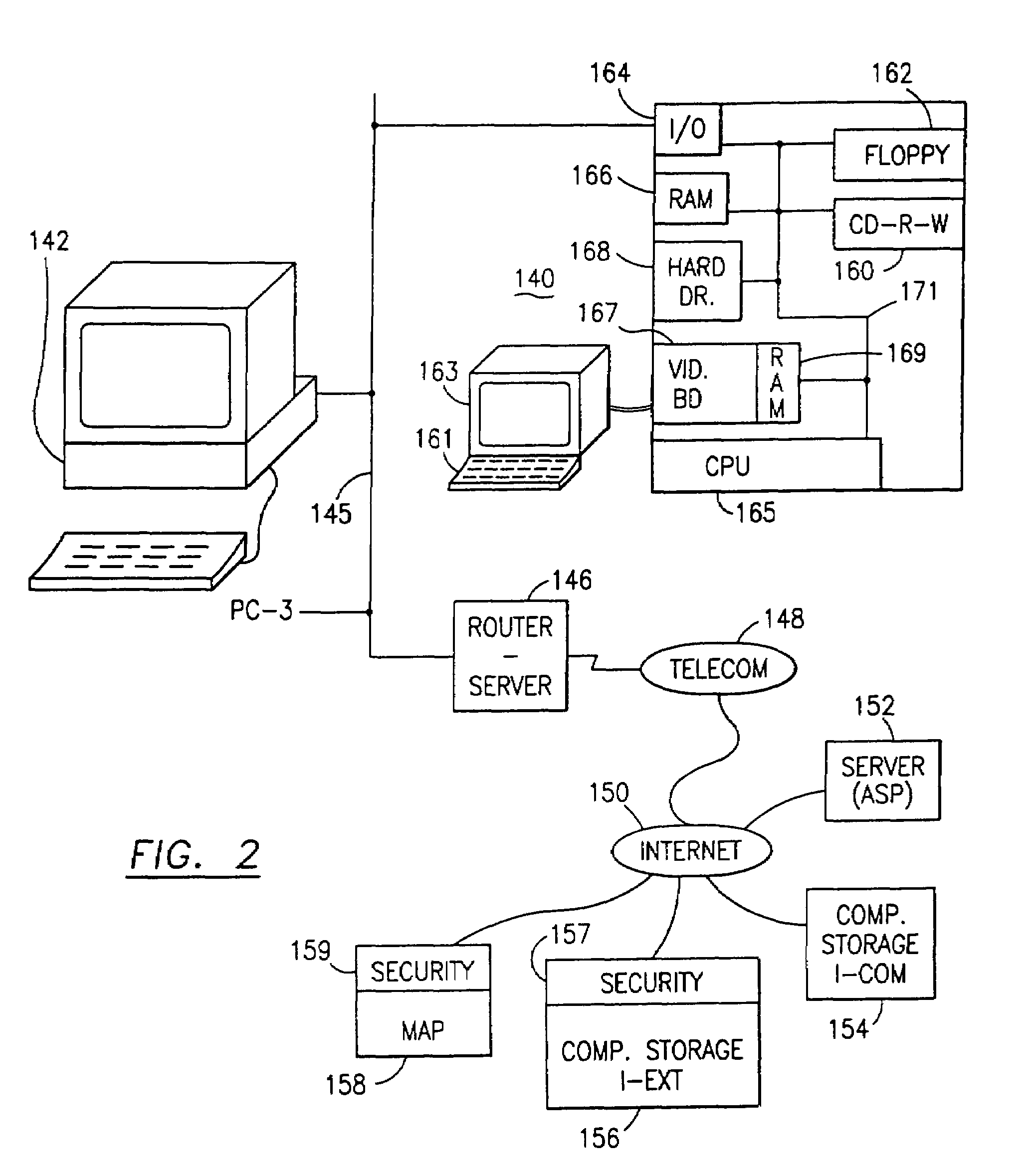
Data security system and method
ActiveUS7103915B2Memory loss protectionDigital data processing detailsPlaintextInformation processing
The method for securing data includes establishing a group of security sensitive items, filtering data and extracting and separating the security items from remainder data. The filtered data are separately stored (locally on a PC or on another computer in a LAN or WAN or on the Internet.) A map may be generated. The filter and / or map may be destroyed or stored. The data input, extracted data and remainder data may be deleted from the originating computer. Encryption may be utilized to enhance security (including transfers of data, filter and map). Reconstruction of the data is permitted only in the presence of a predetermined security clearance. A plurality of security clearances may be used to enable a corresponding plurality of partial, reconstructed views of the plaintext (omitting higher security words). A computer readable medium containing programming instructions and an information processing system is encompassed.
Owner:DIGITAL DOORS
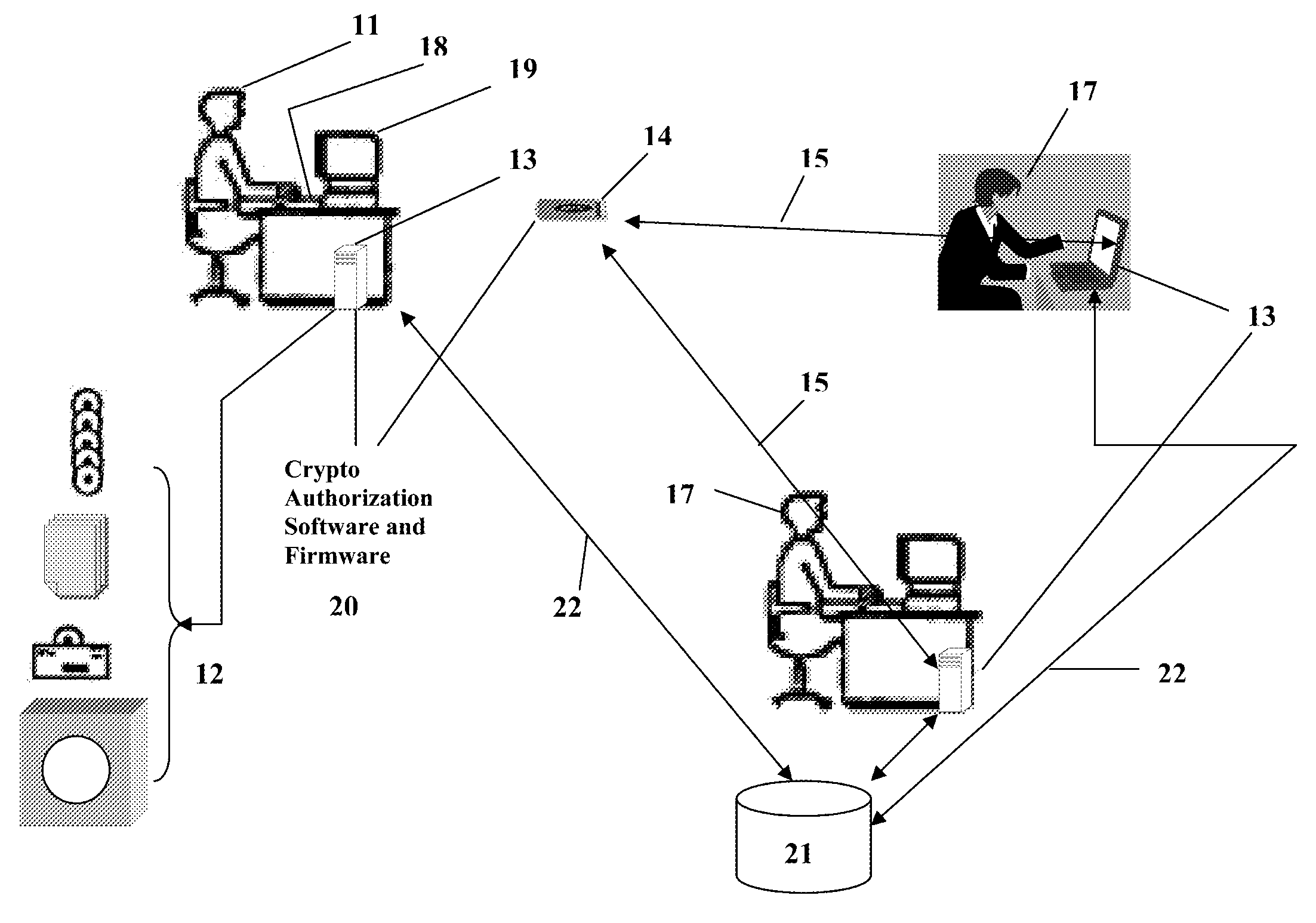
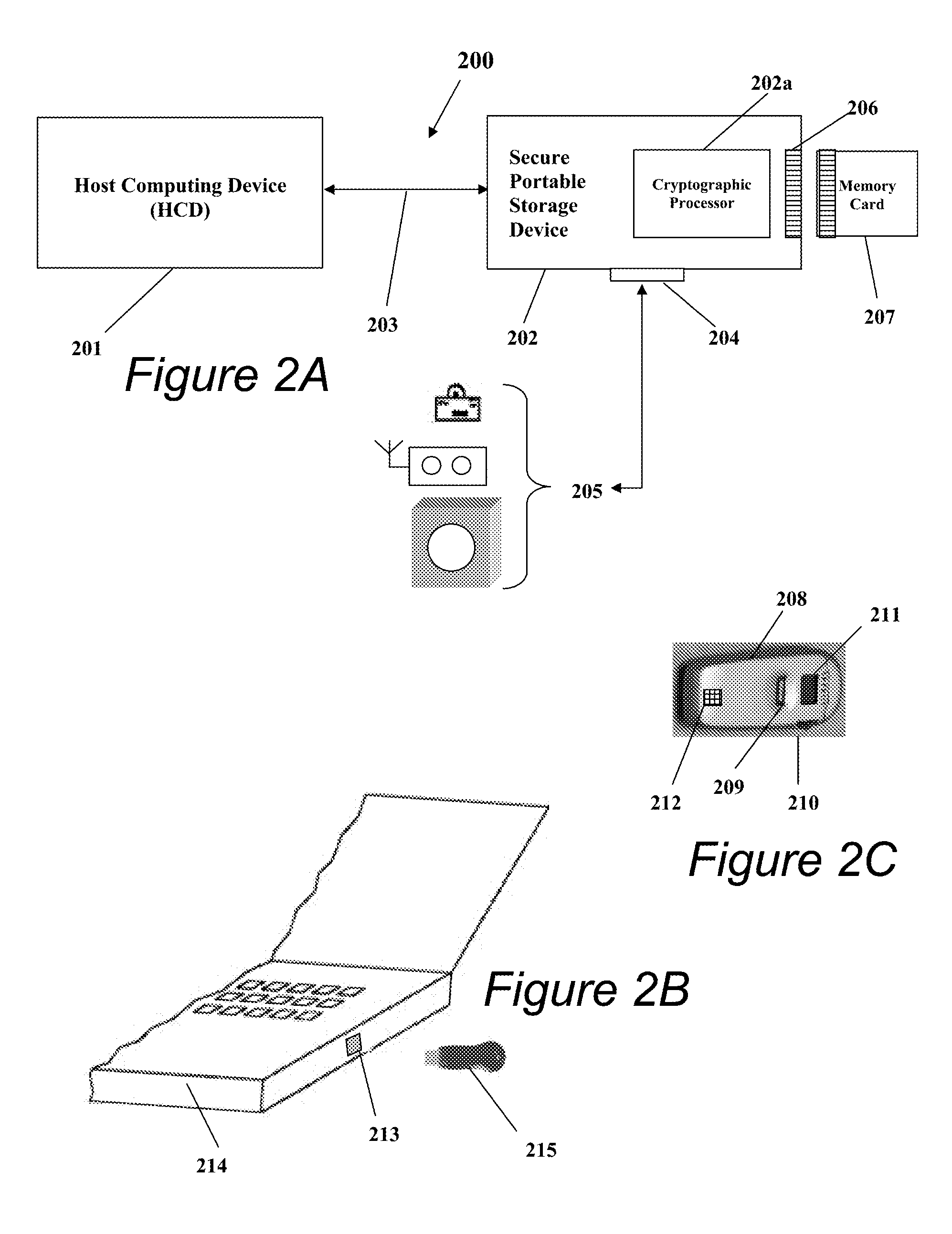
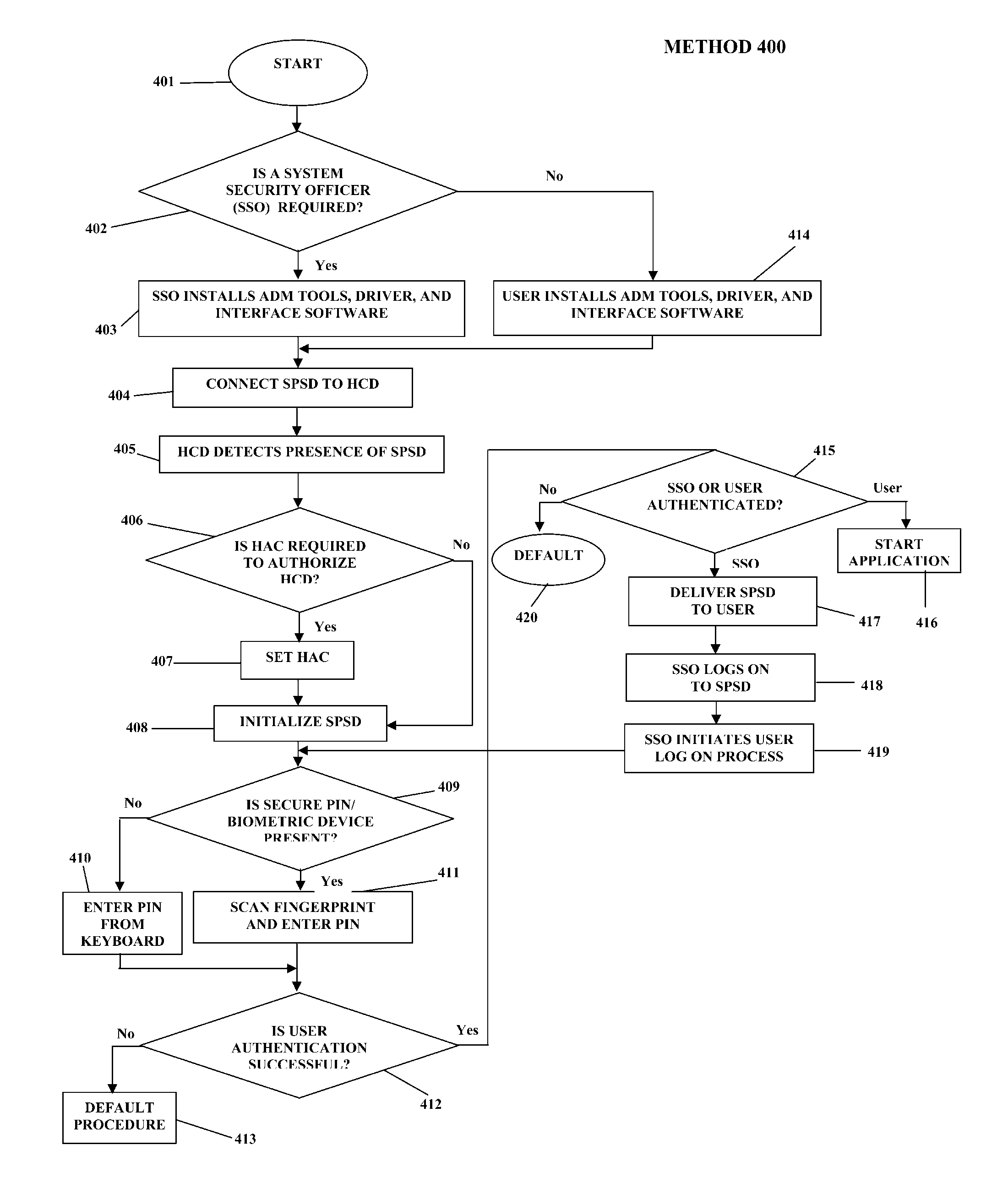
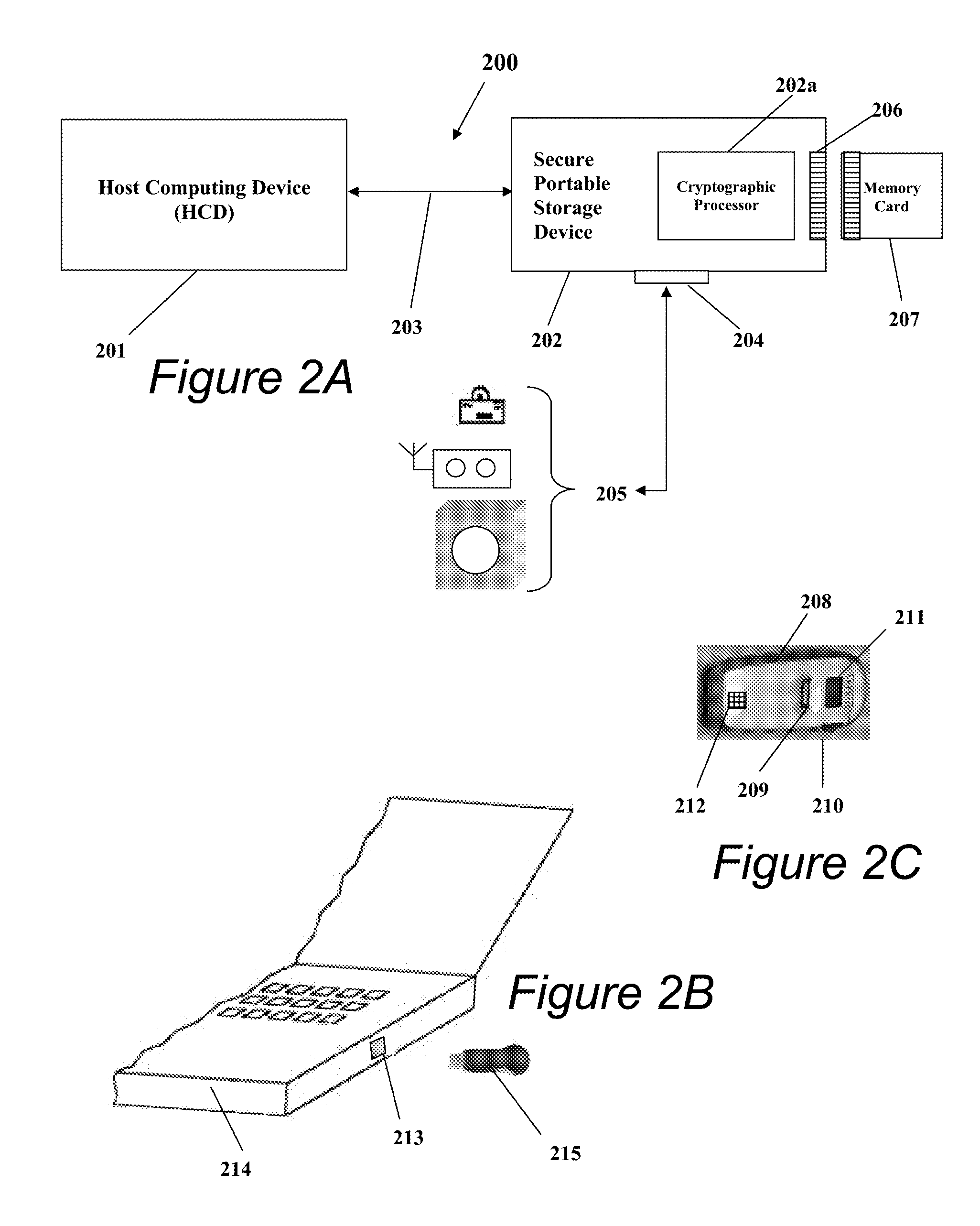
Portable Data Encryption Device with Configurable Security Functionality and Method for File Encryption
InactiveUS20080263363A1Mitigates and eliminates vulnerabilityUser identity/authority verificationInternal/peripheral component protectionComputer hardwarePlaintext
A portable encryption device with logon access controlled by an encryption key, with an on board cryptographic processor for reconstituting the encryption key from a plurality of secrets generated by a secret sharing algorithm, optionally shrouded with external secrets using an invertible transform resistant to quantum computing attacks. Another embodiment provides file decryption controlled by a file encryption key, with the on board cryptographic processor reconstituting the file encryption key from a version of the file encryption key which has been shrouded with a network authorization code. A method for encryption of a plaintext file by hashing, compressing, and encrypting the plaintext file, hashing the ciphertext, hashing the plaintext hash and the ciphertext hash, and sealing the ciphertext together with the resulting hash. A portable encryption device for performing the method is also disclosed.
Owner:SPYRUS
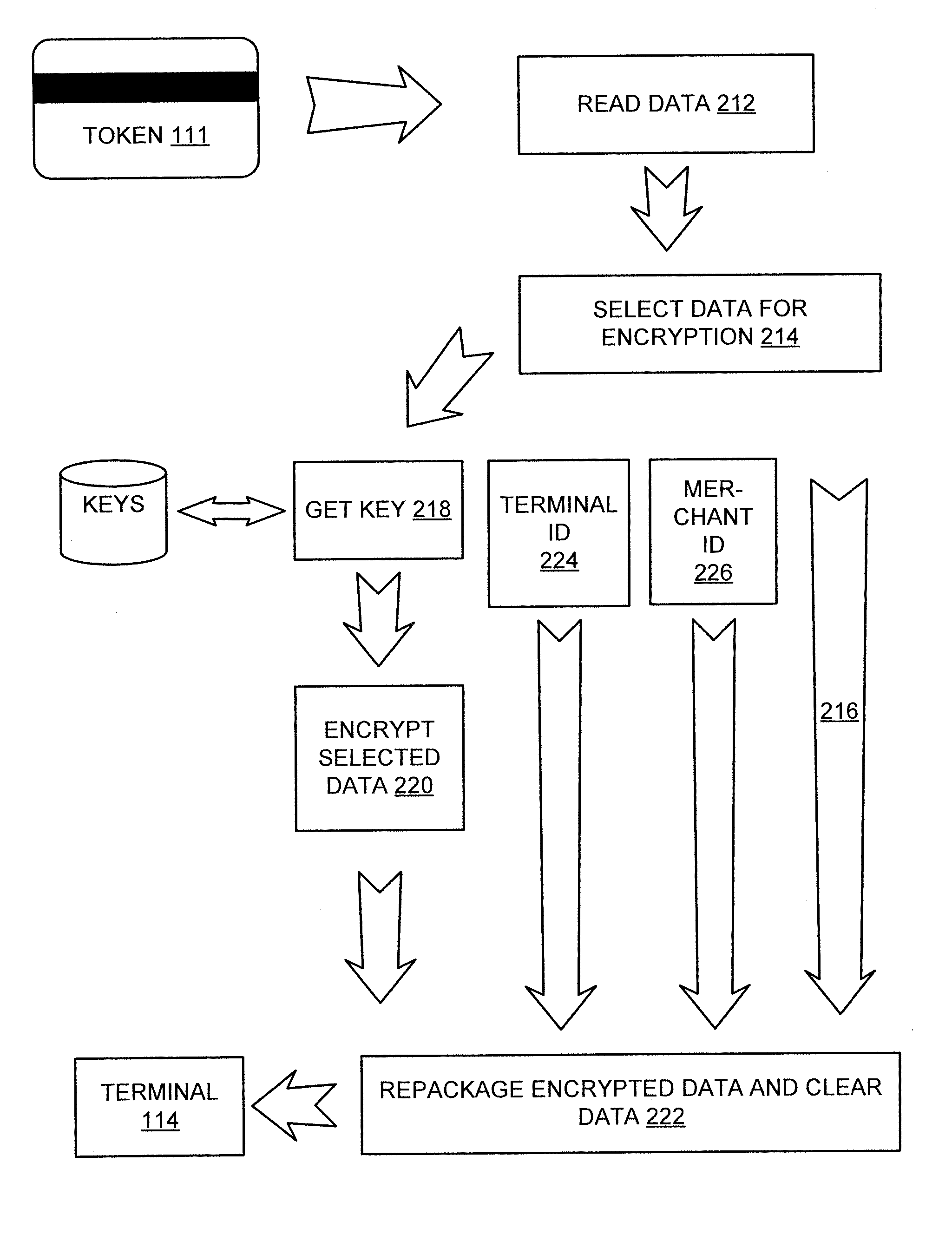
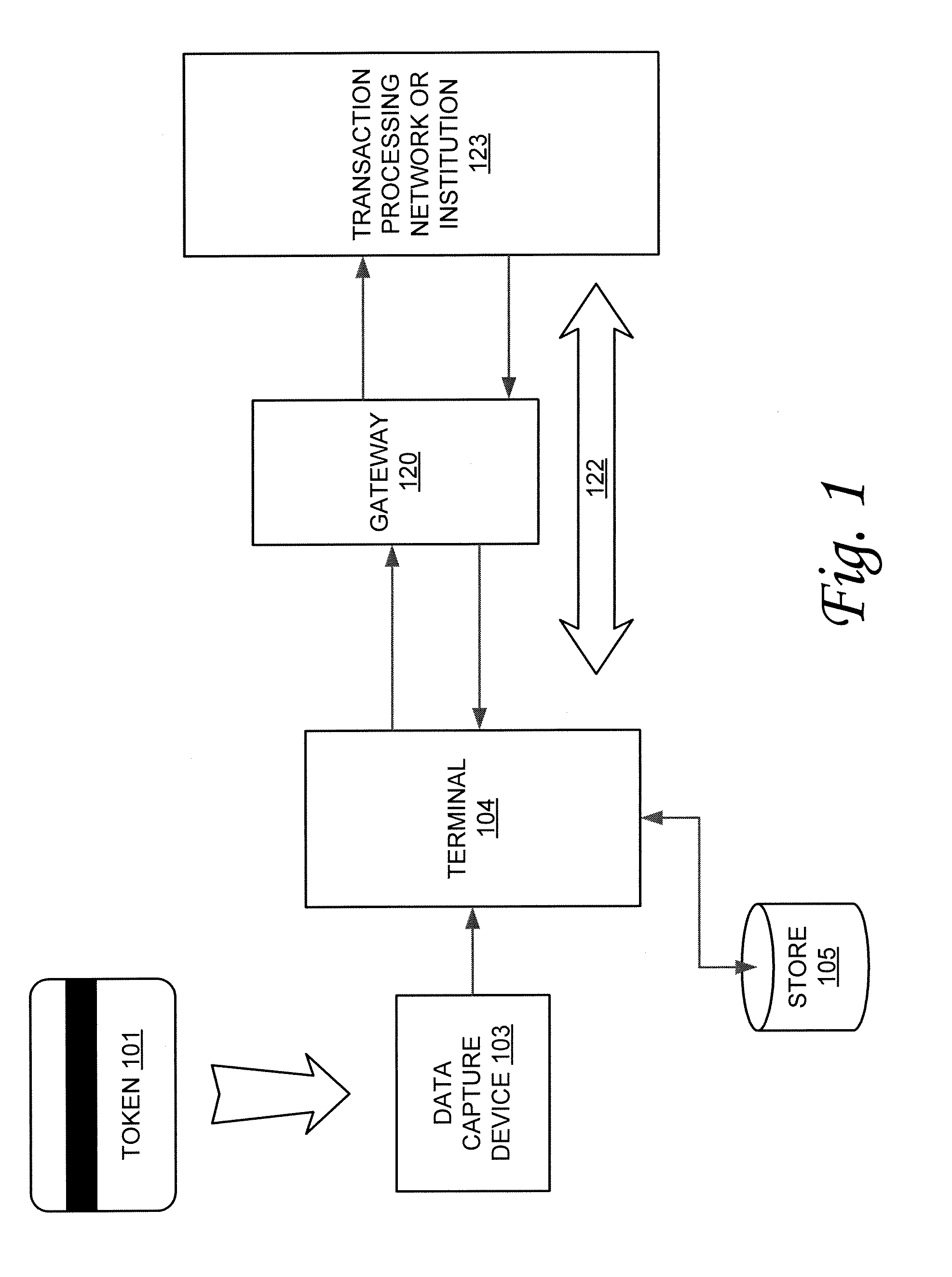
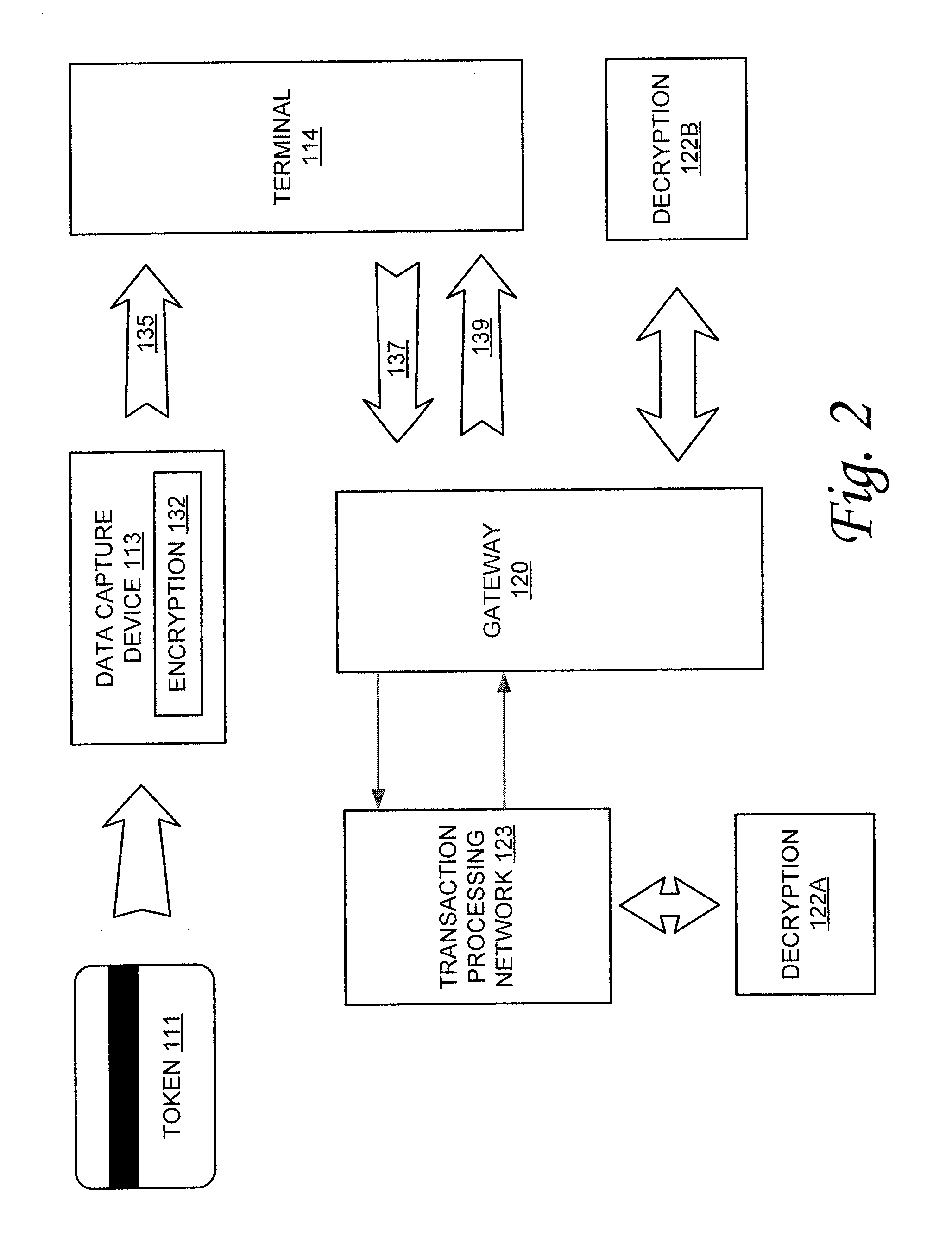
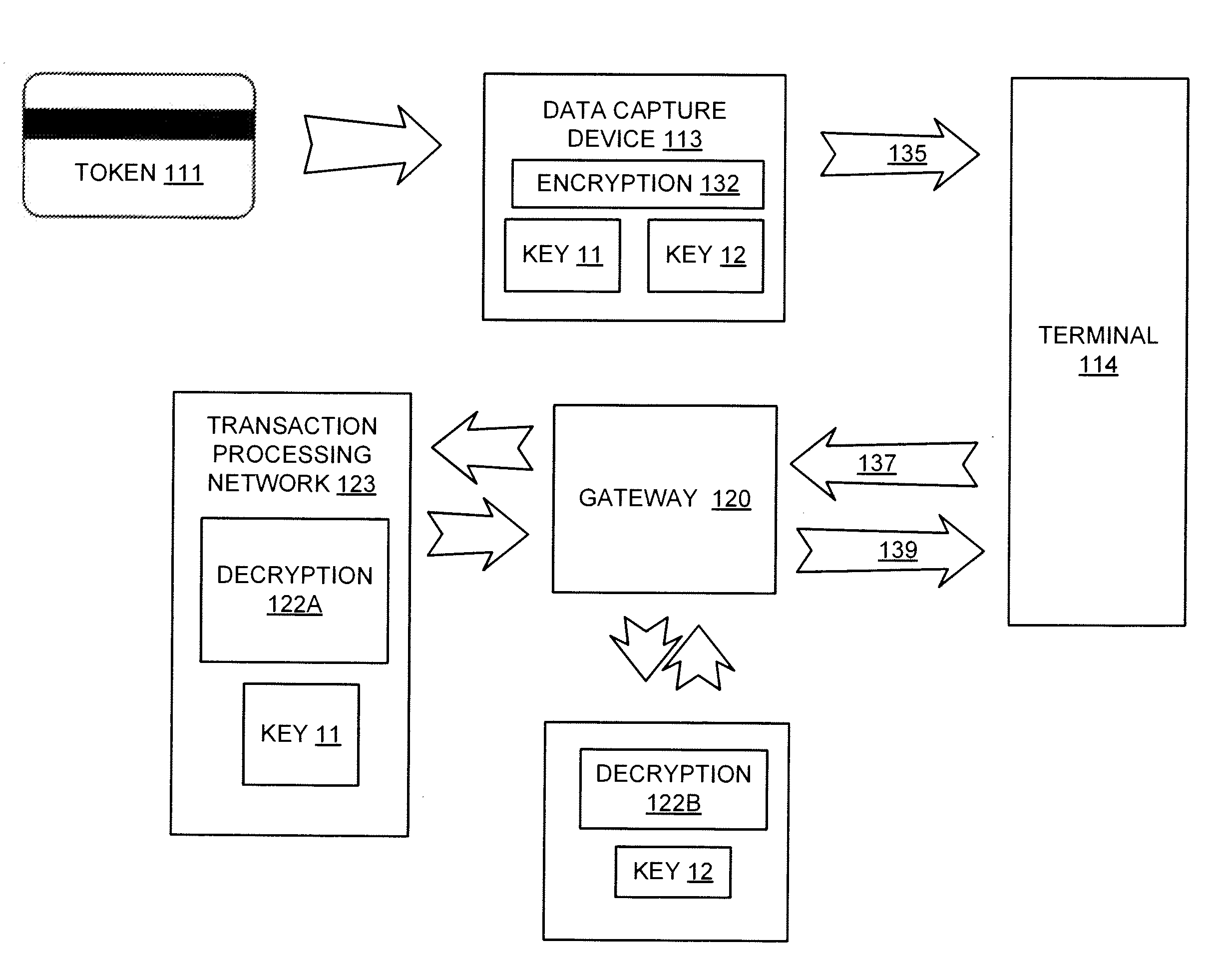
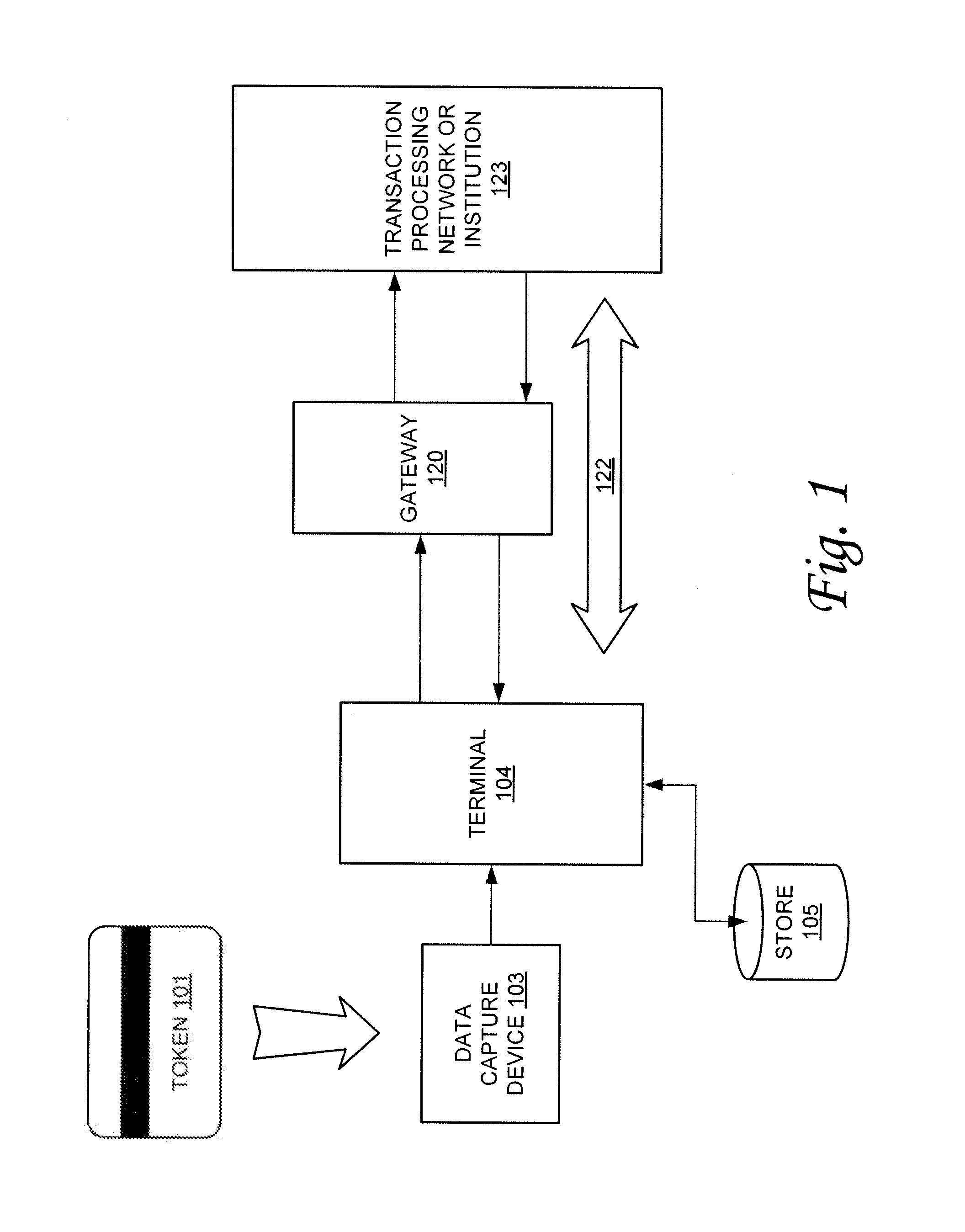
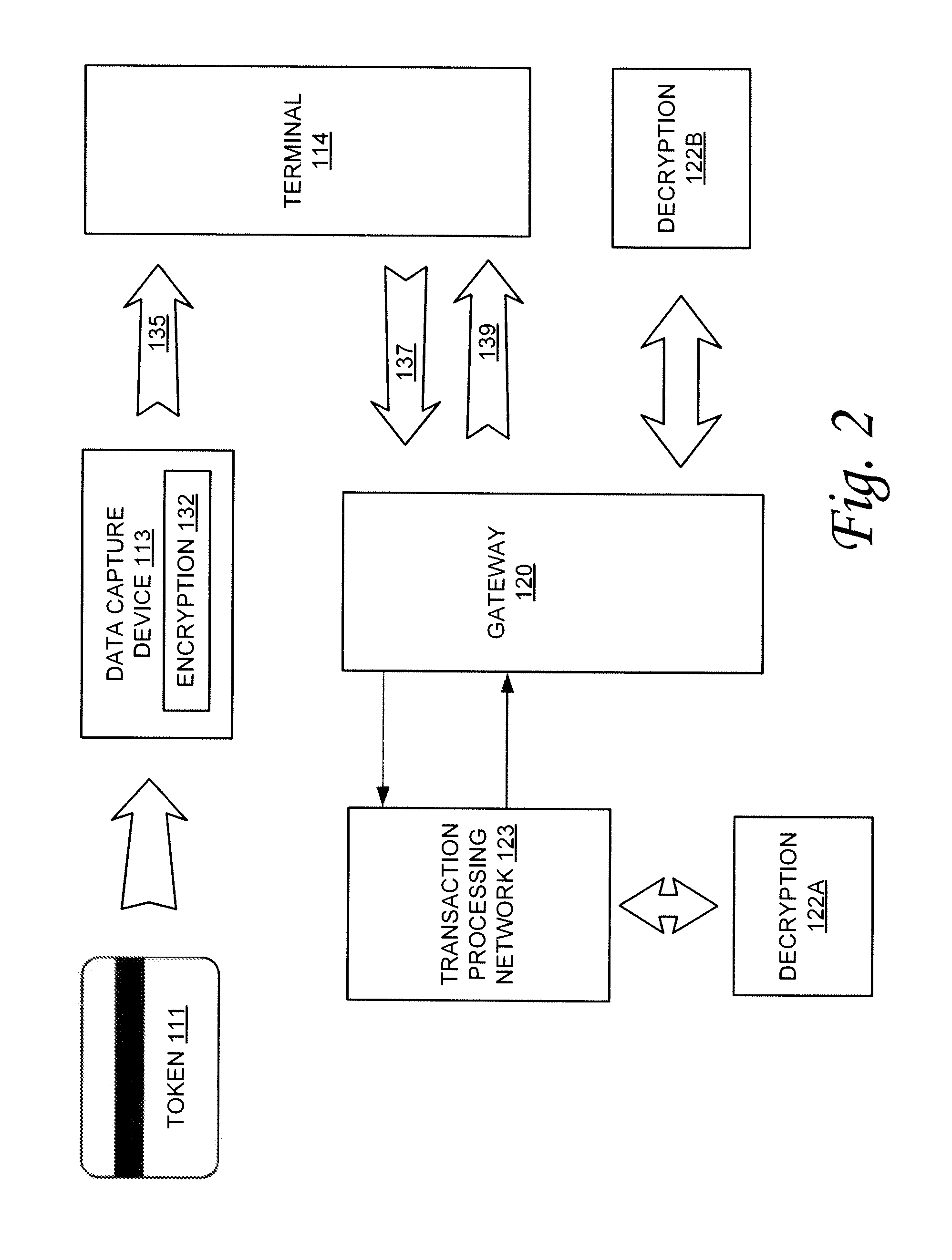
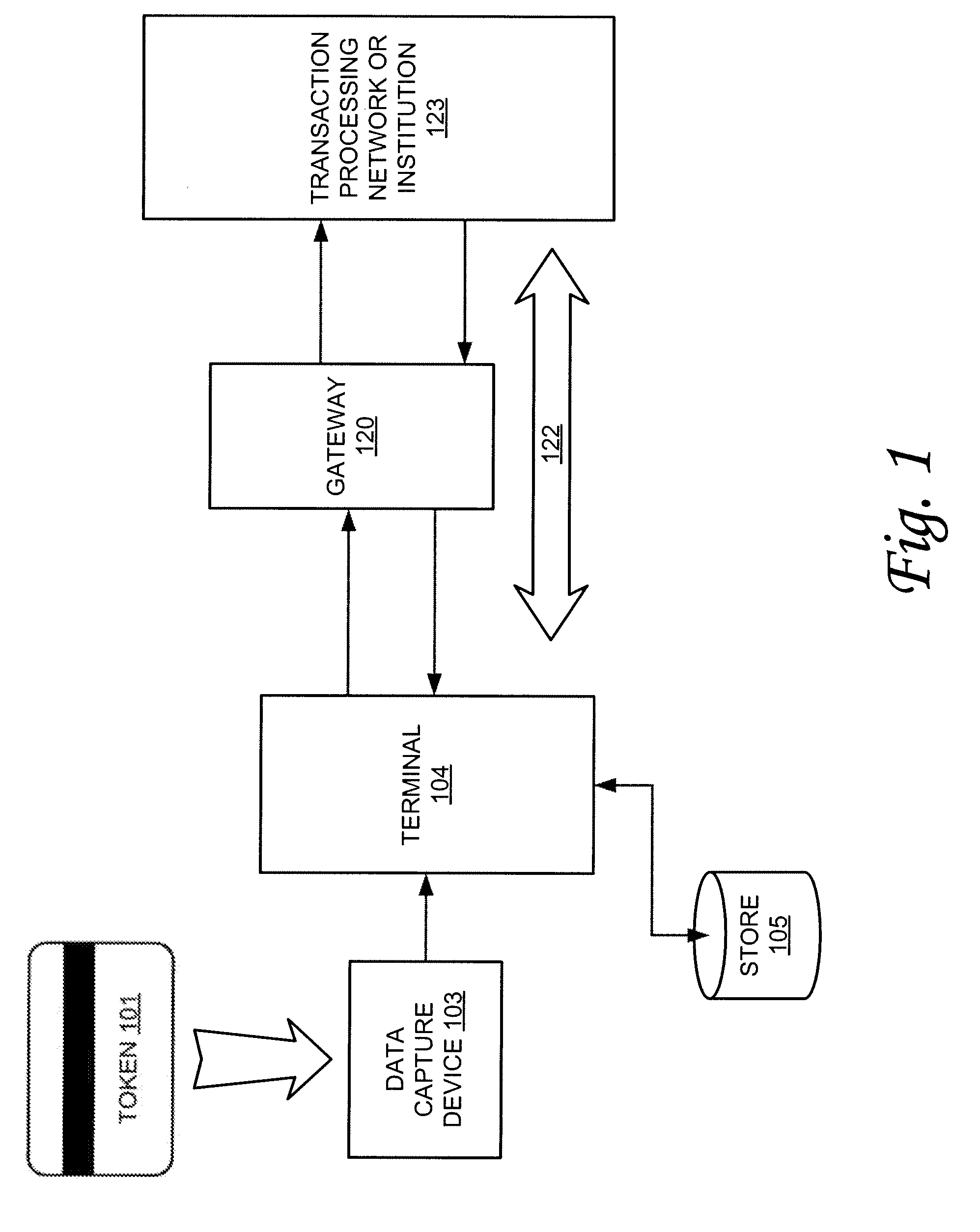
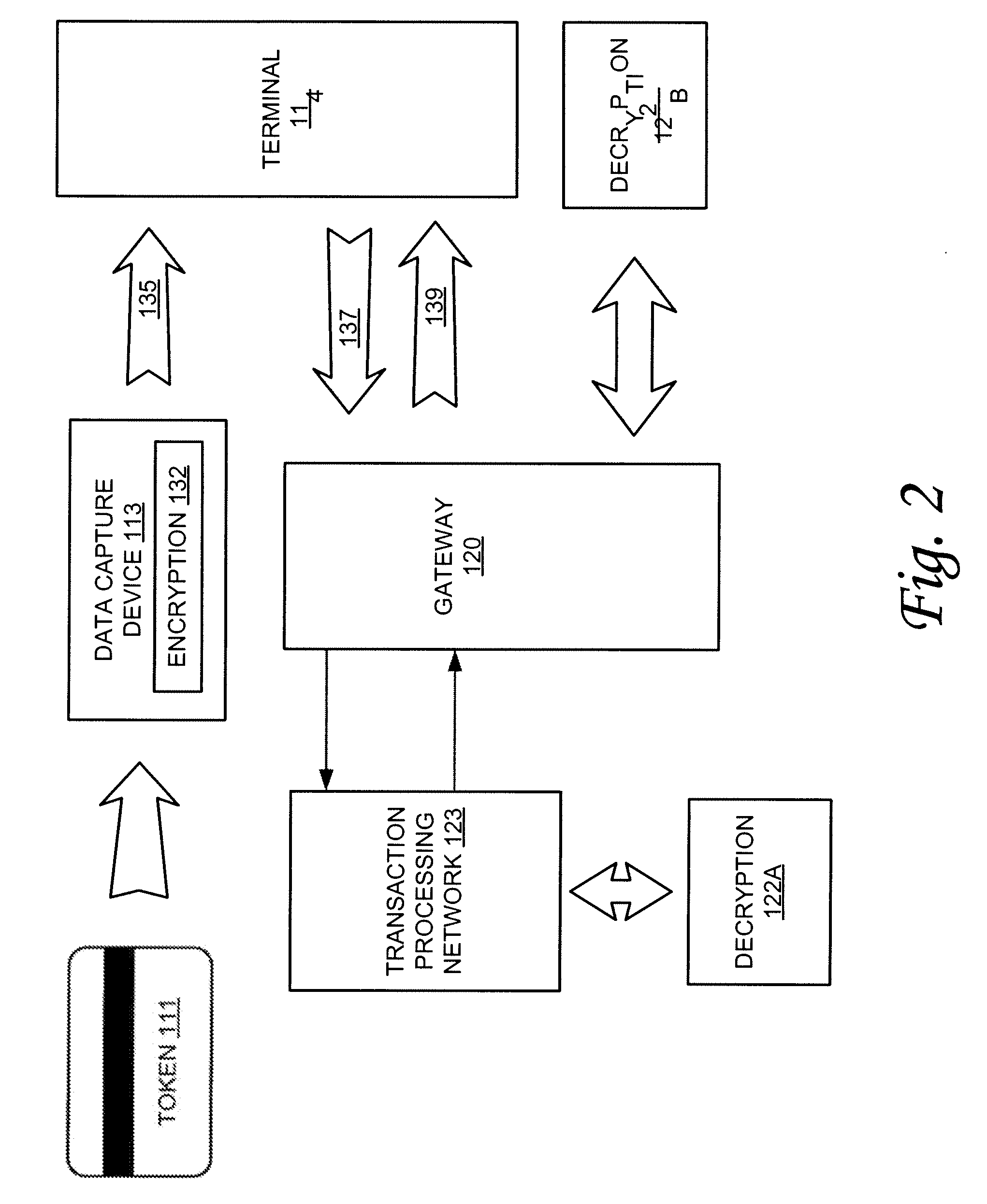
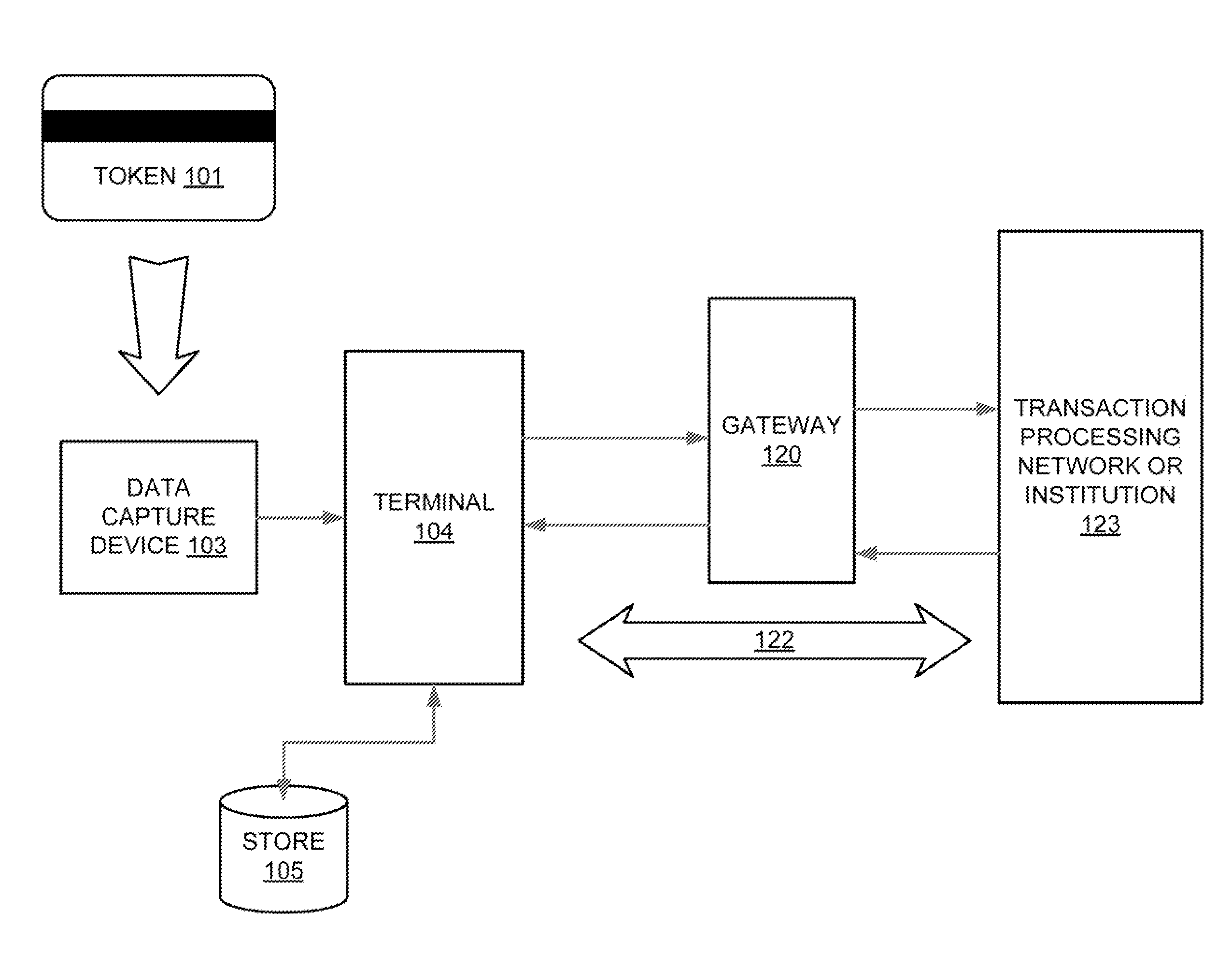
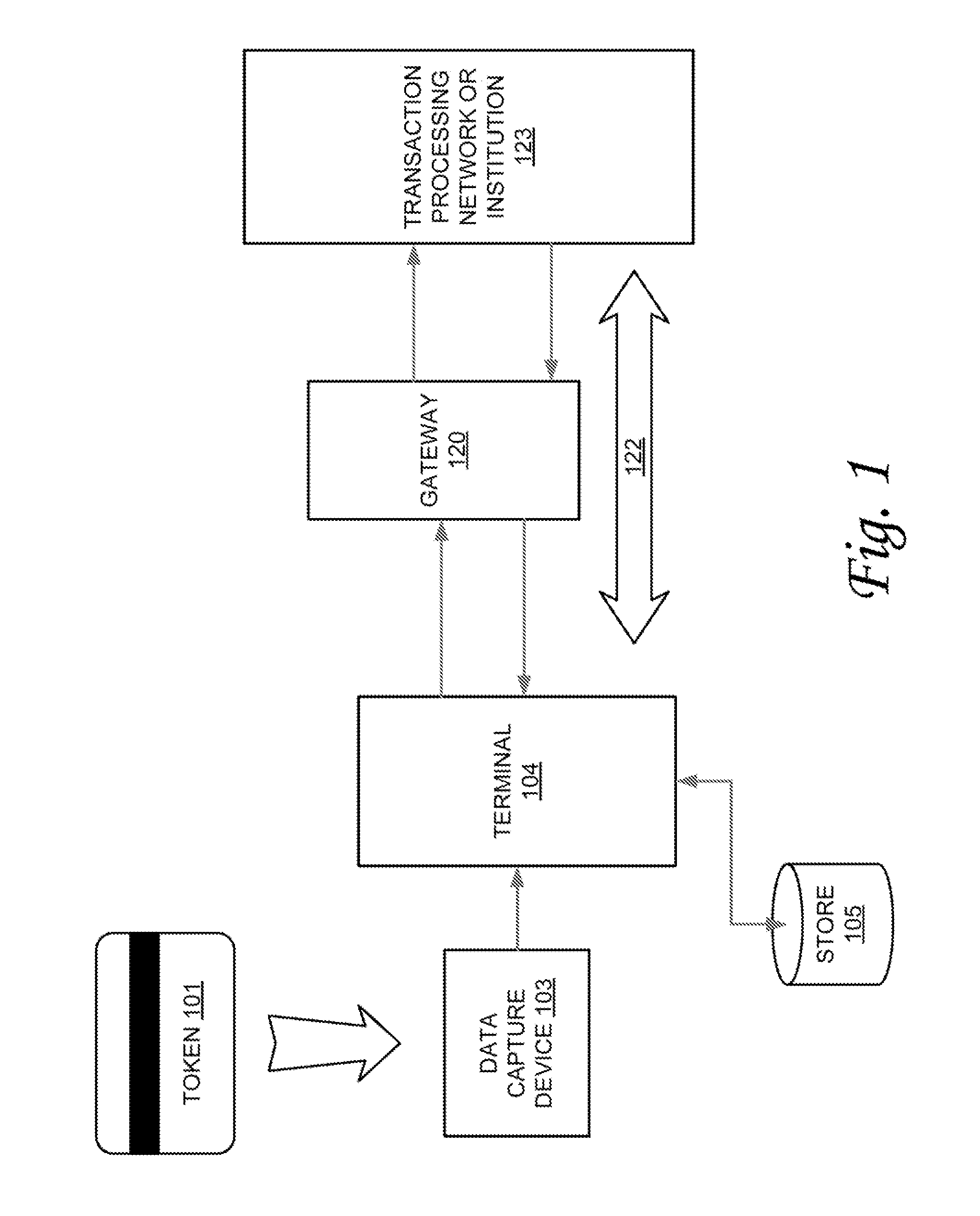
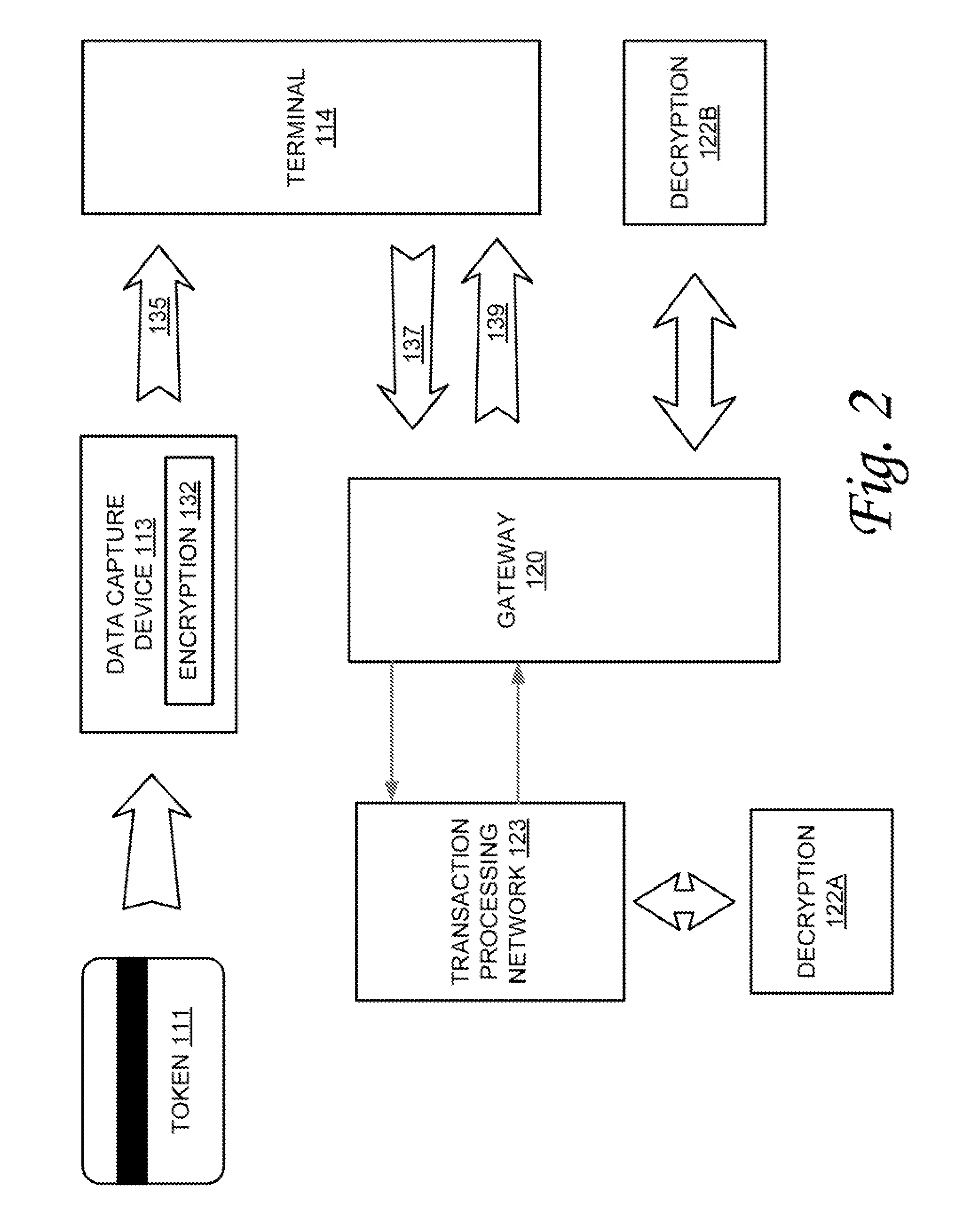
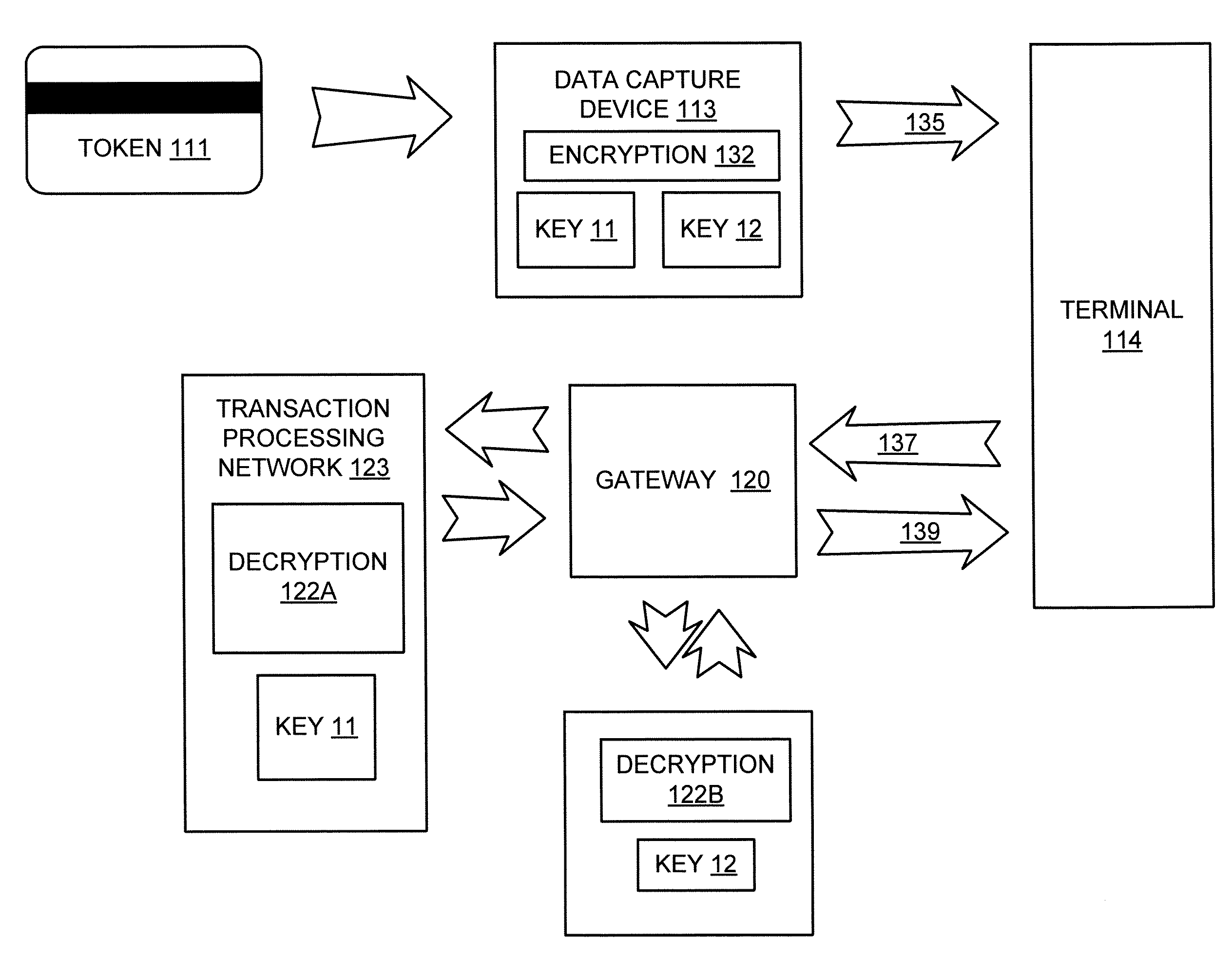
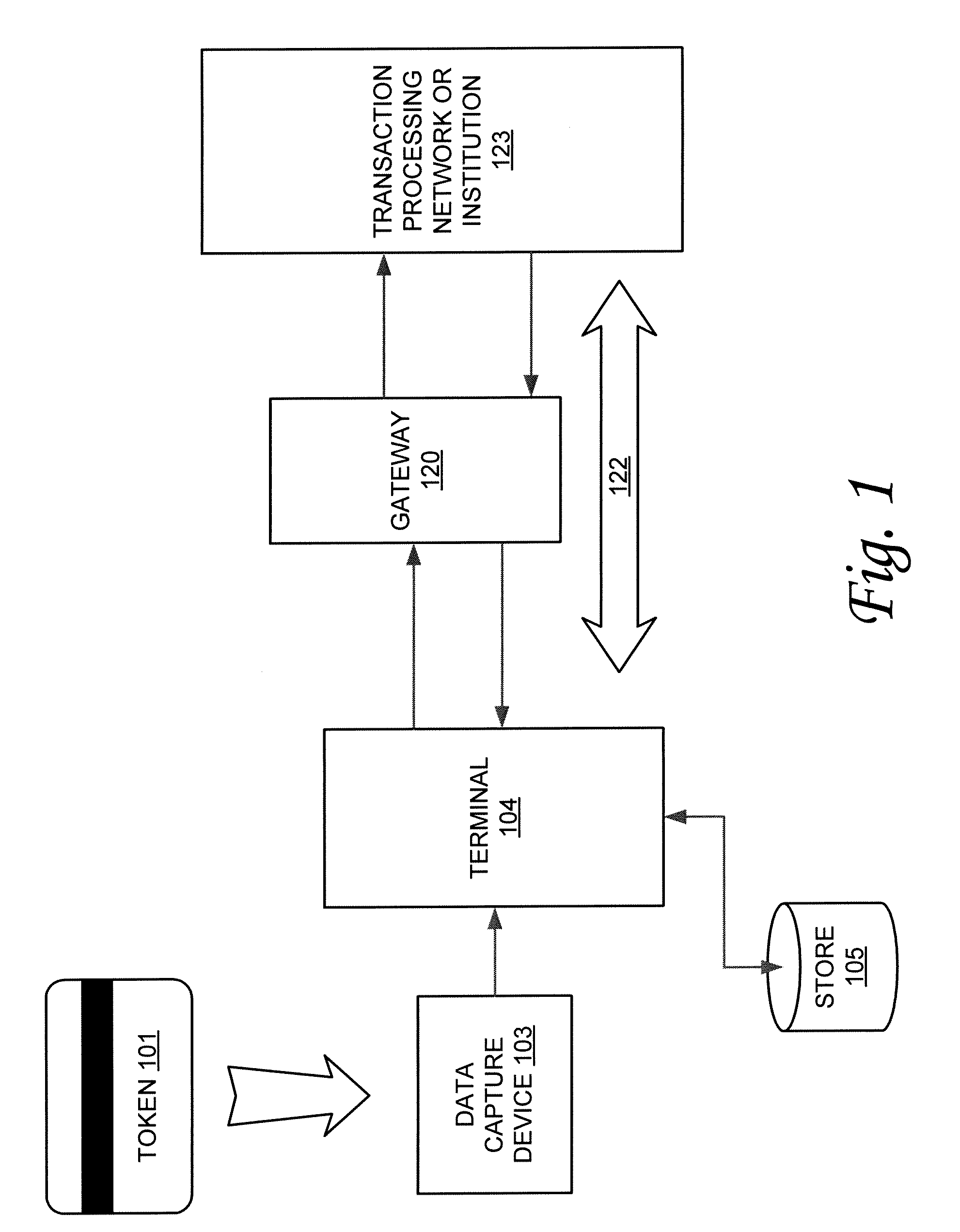
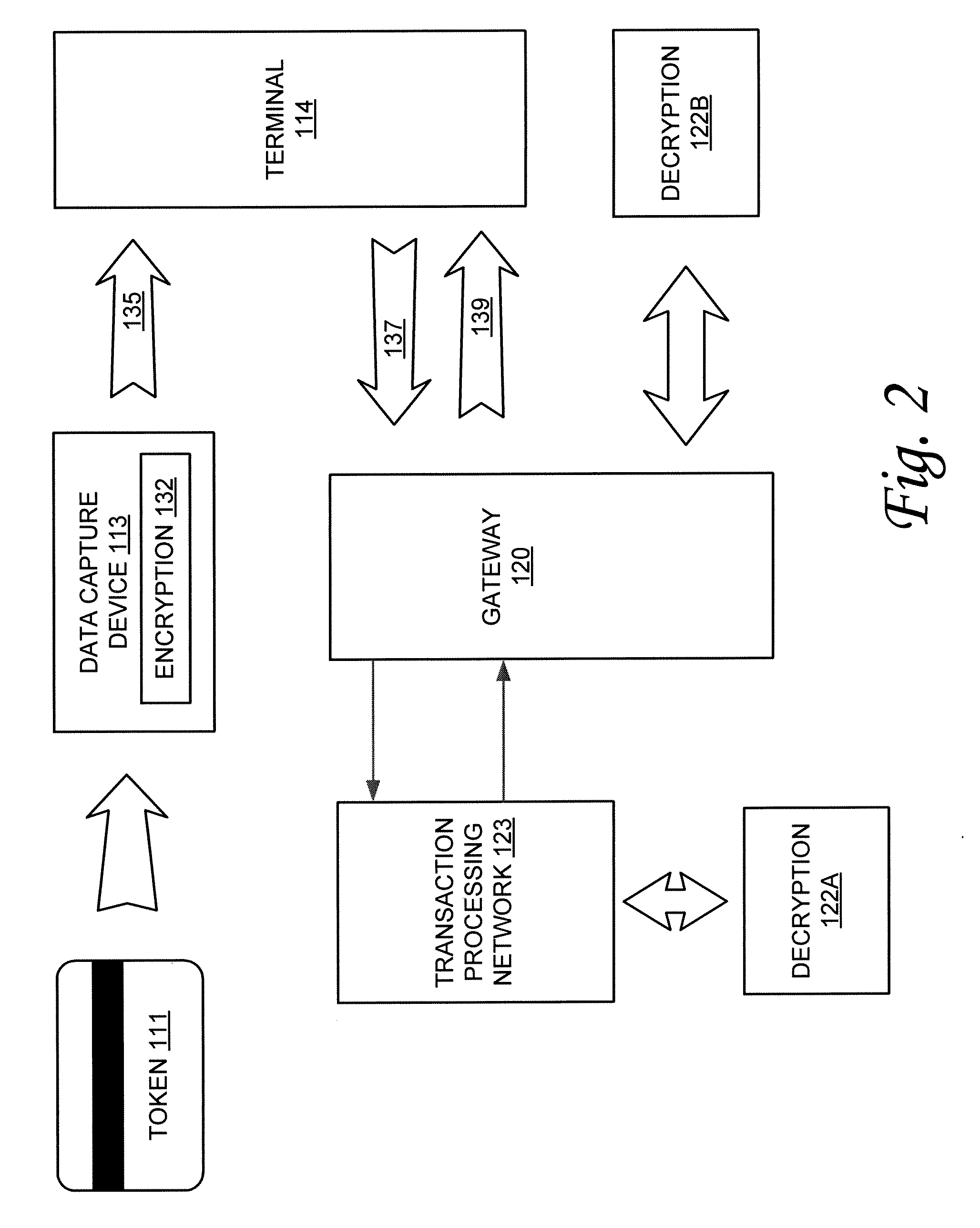
Method and system for secured transactions
InactiveUS20070276765A1Improve securityEasy to upgradeAcutation objectsFinancePlaintextBatch processing
Owner:SEMTEK INNOVATIVE SOLUTIONS
Data security system and method associated with data mining
ActiveUS7322047B2Ease overhead performanceHigh overhead performancePeptide/protein ingredientsMultiple keys/algorithms usagePlaintextInternet privacy
The data security method, system and associated data mining enables multiple users, each having a respective security clearance level to access security sensitive words, data objects, characters or icons. The method extracts security sensitive words, data objects, characters or icons from plaintext or other source documents to obtain (a) subsets of extracted data and (b) remainder data. The extracted data is, in one embodiment, stored in a multilevel security system (MLS) which separates extract data of different security levels with MLS guards. Some or all of the original data is reconstructed via one or more of the subsets of extracted data and remainder data only in the presence of a predetermined security level. In this manner, an inquiring party, with the proper security clearance, can data mine the data in the MLS secured storage.
Owner:DIGITAL DOORS
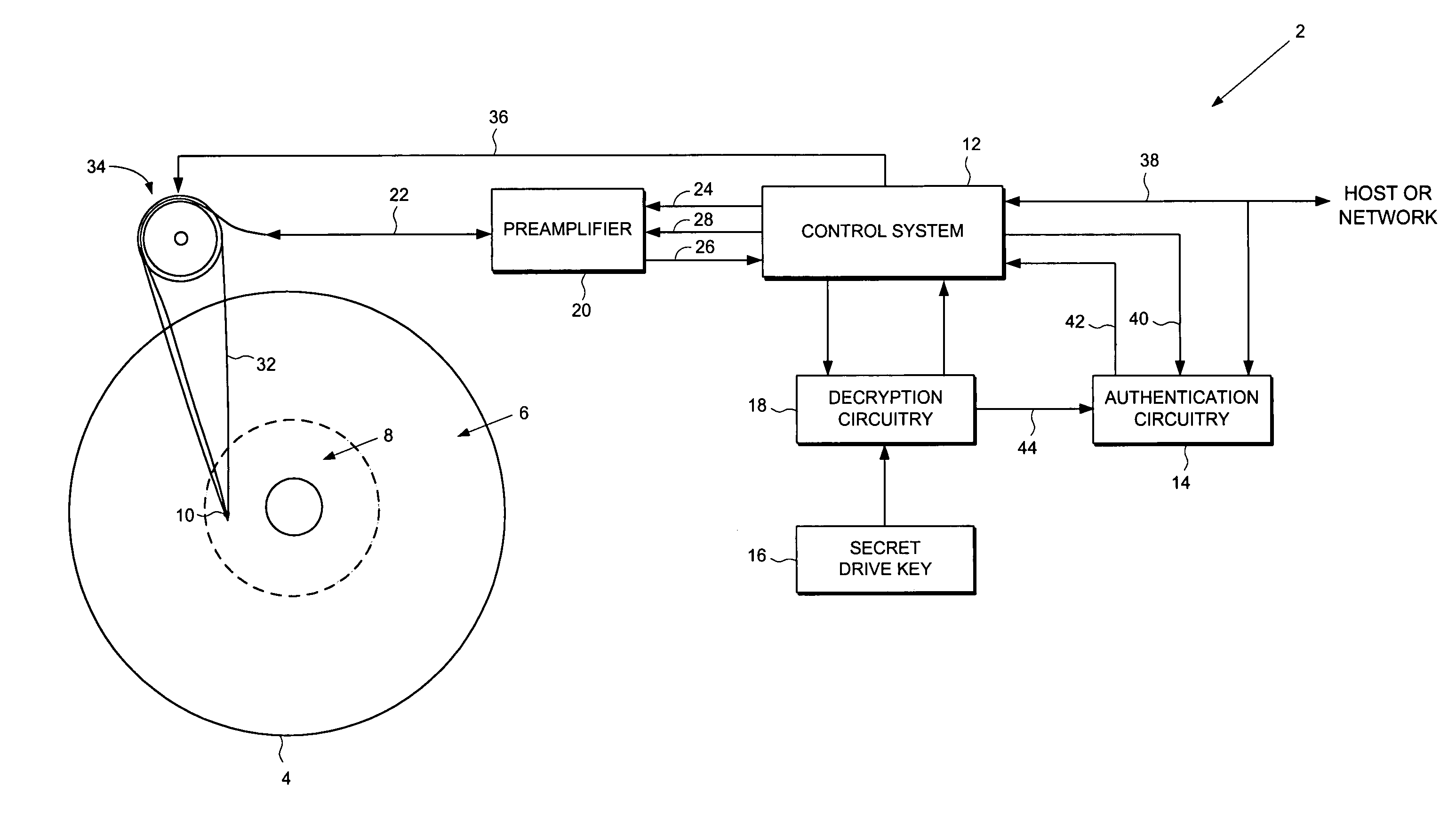
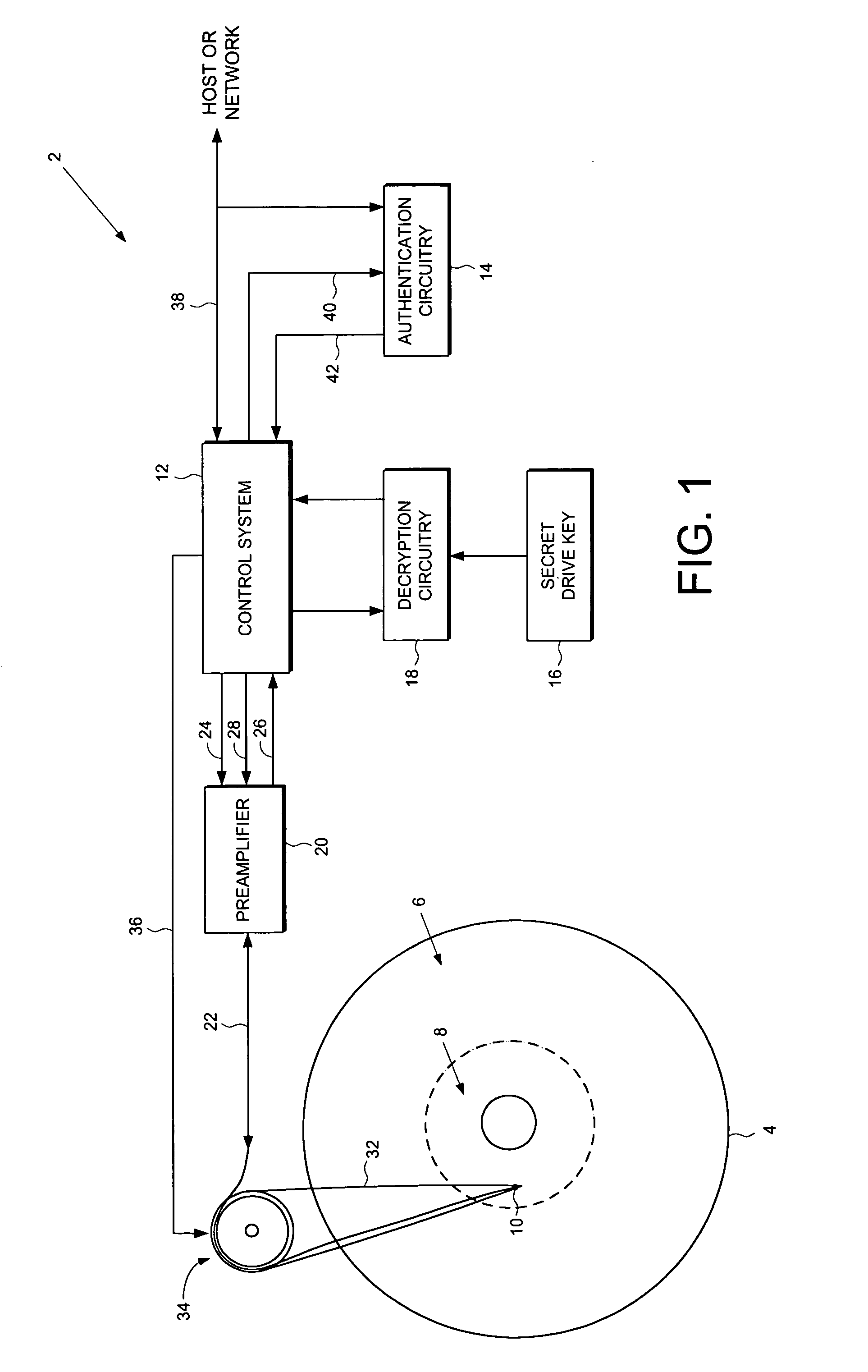
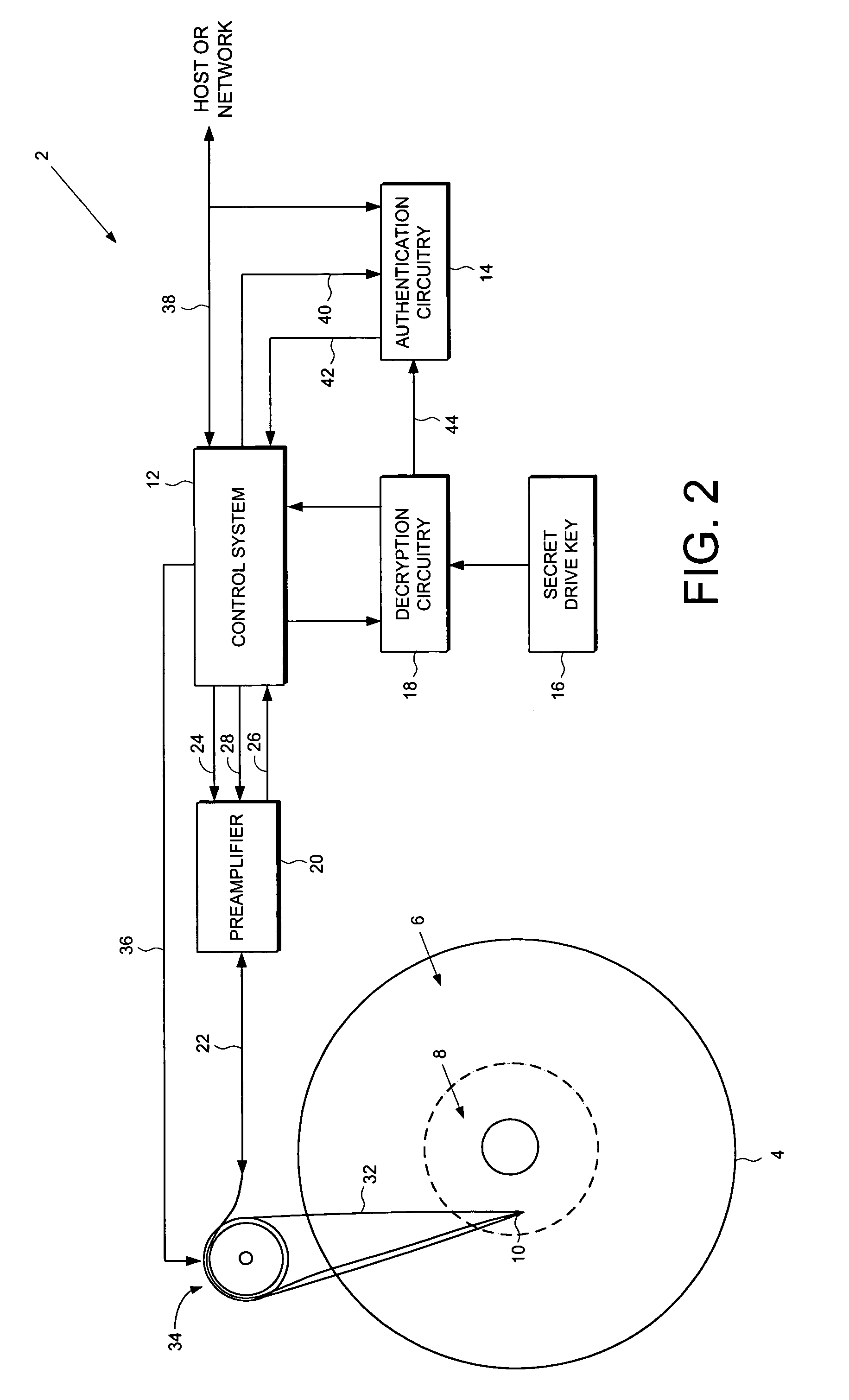
Disk drive employing a disk with a pristine area for storing encrypted data accessible only by trusted devices or clients to facilitate secure network communications
A disk drive is disclosed comprising a disk for storing data, the disk comprising a public area for storing plaintext data and a pristine area for storing encrypted data. The disk drive comprises a head for reading the encrypted data from the pristine area of the disk, and a control system for controlling access to the pristine area of the disk. Authentication circuitry within the disk drive is provided for authenticating a request received from an external entity to access the pristine area of the disk and for enabling the control system if the request is authenticated. The disk drive further comprises a secret drive key, and decryption circuitry responsive to the secret drive key, for decrypting the encrypted data stored in the pristine area of the disk.
Owner:WESTERN DIGITAL VENTURES
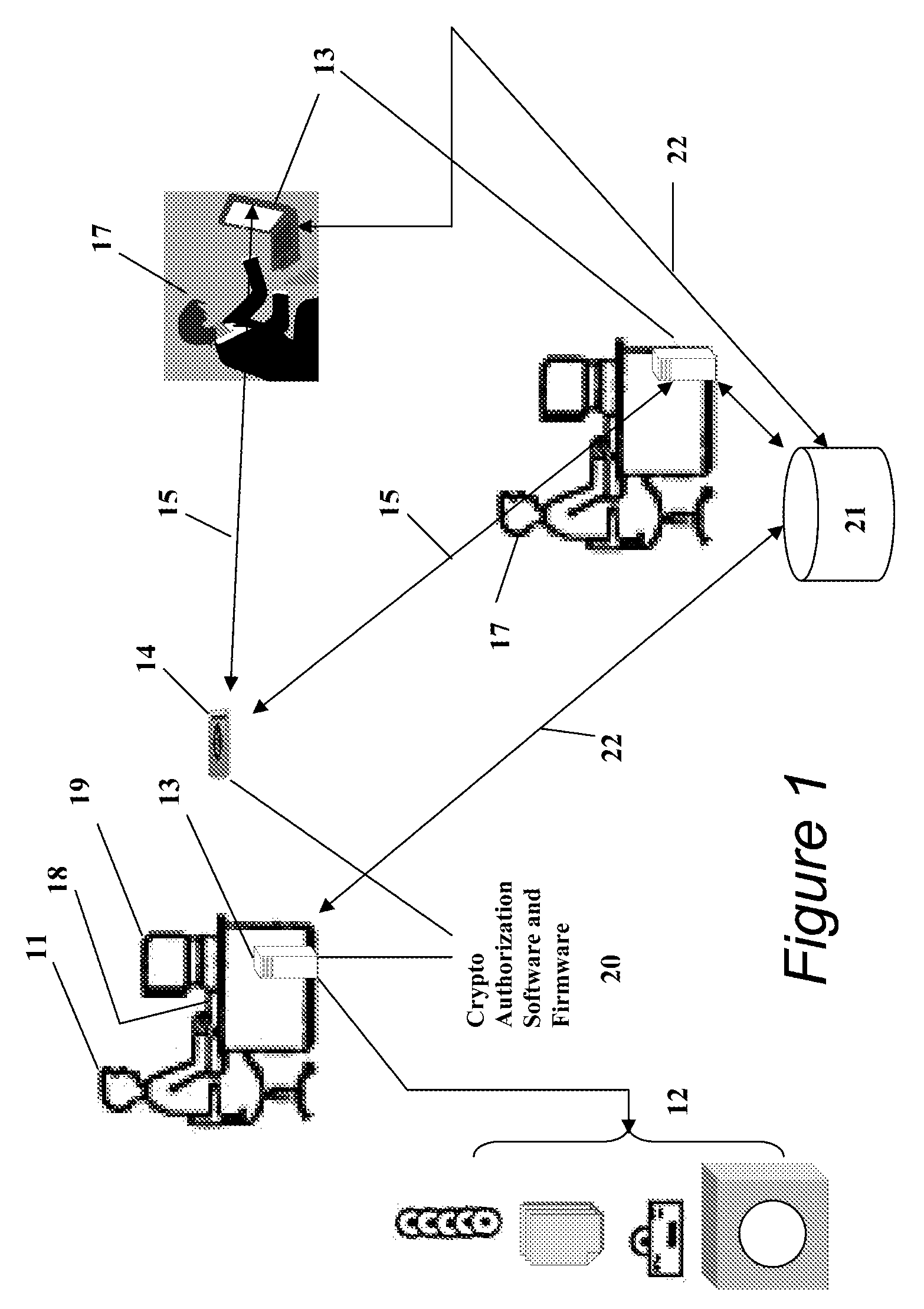
Portable data encryption device with configurable security functionality and method for file encryption
ActiveUS9049010B2Mitigates and eliminates vulnerabilityKey distribution for secure communicationUser identity/authority verificationPlaintextComputer hardware
A portable encryption device with logon access controlled by an encryption key, with an on board cryptographic processor for reconstituting the encryption key from a plurality of secrets generated by a secret sharing algorithm, optionally shrouded with external secrets using an invertible transform resistant to quantum computing attacks. Another embodiment provides file decryption controlled by a file encryption key, with the on board cryptographic processor reconstituting the file encryption key from a version of the file encryption key which has been shrouded with a network authorization code. A method for encryption of a plaintext file by hashing, compressing, and encrypting the plaintext file, hashing the ciphertext, hashing the plaintext hash and the ciphertext hash, and sealing the ciphertext together with the resulting hash. A portable encryption device for performing the method is also disclosed.
Owner:SPYRUS
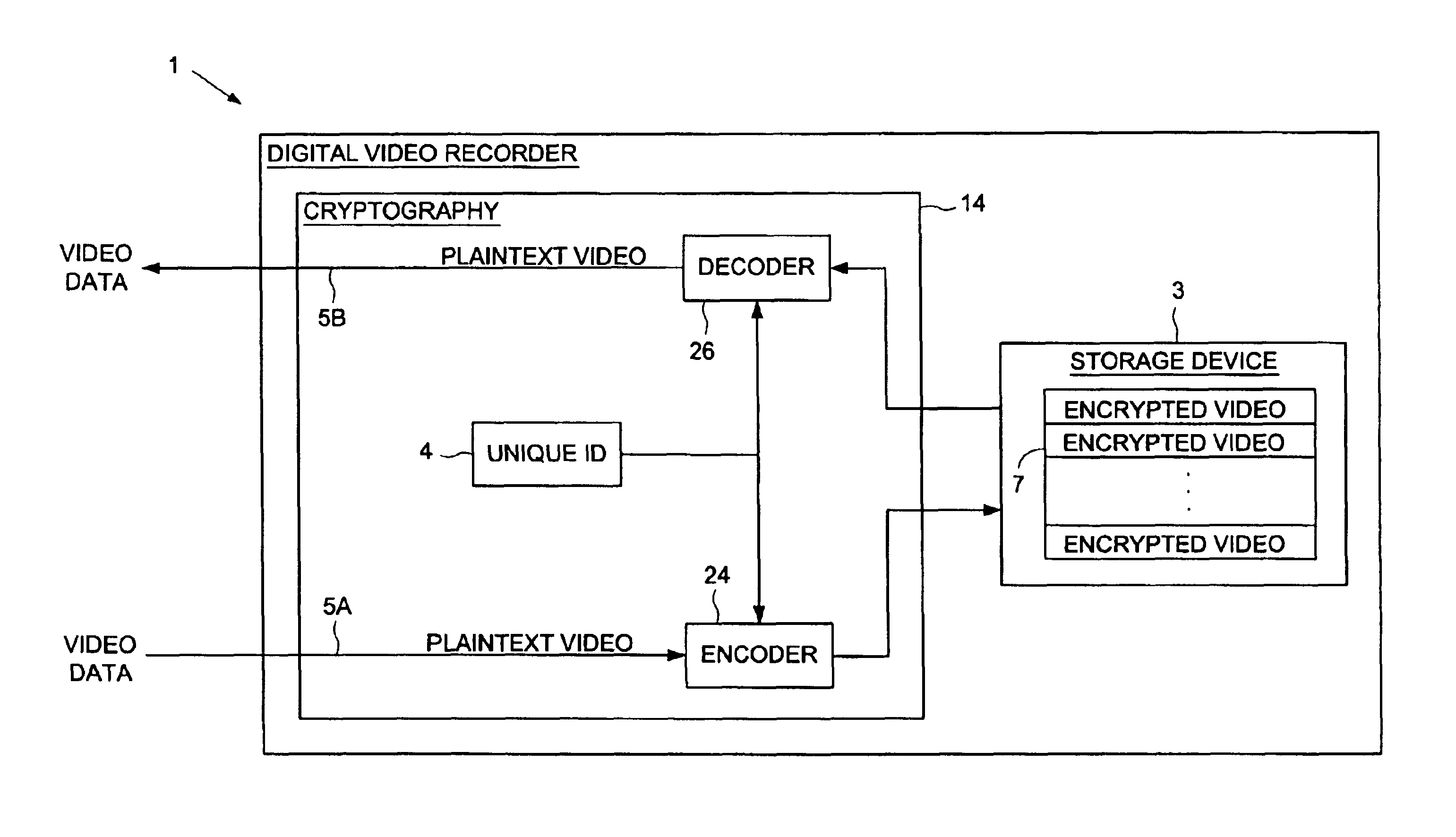
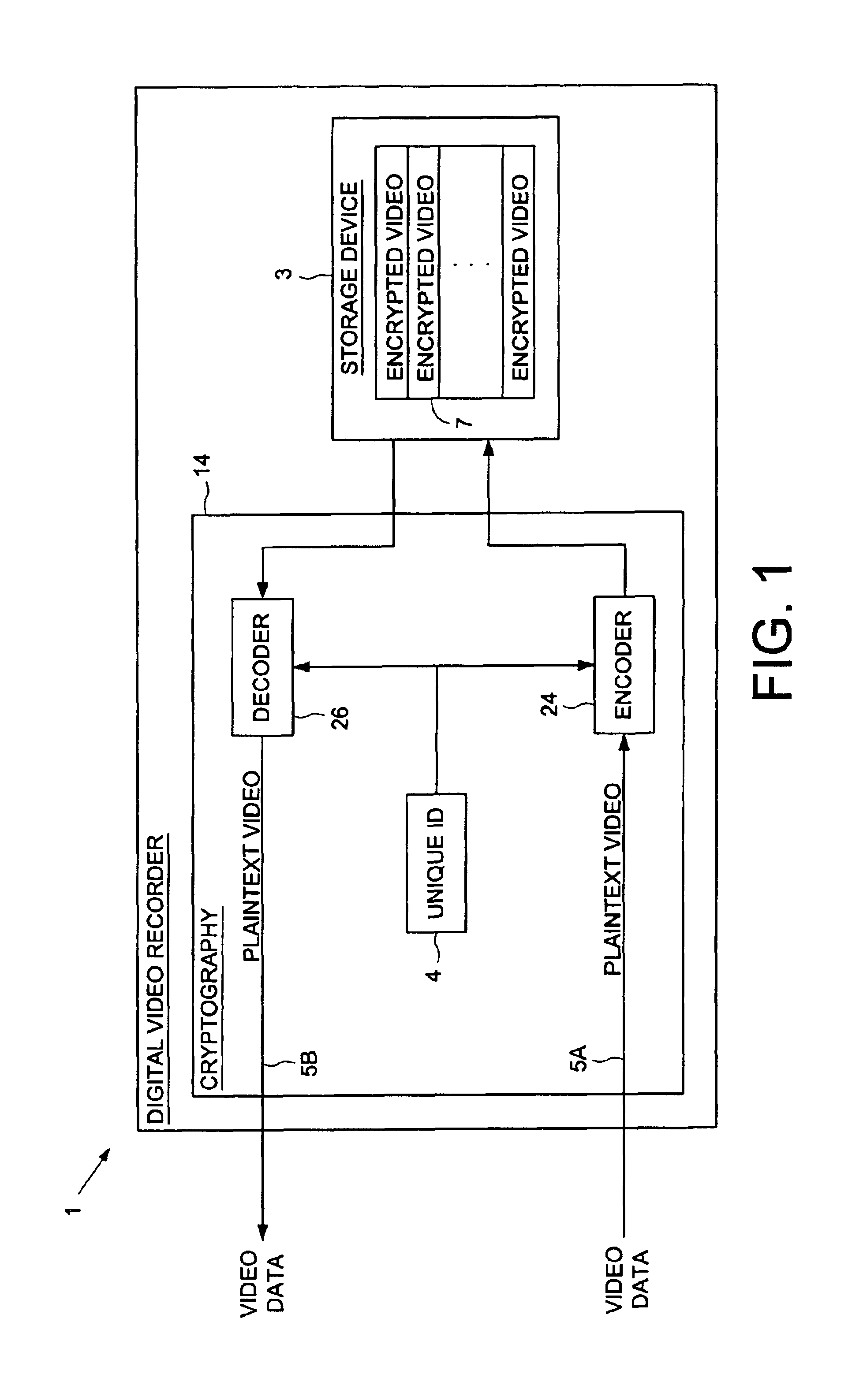
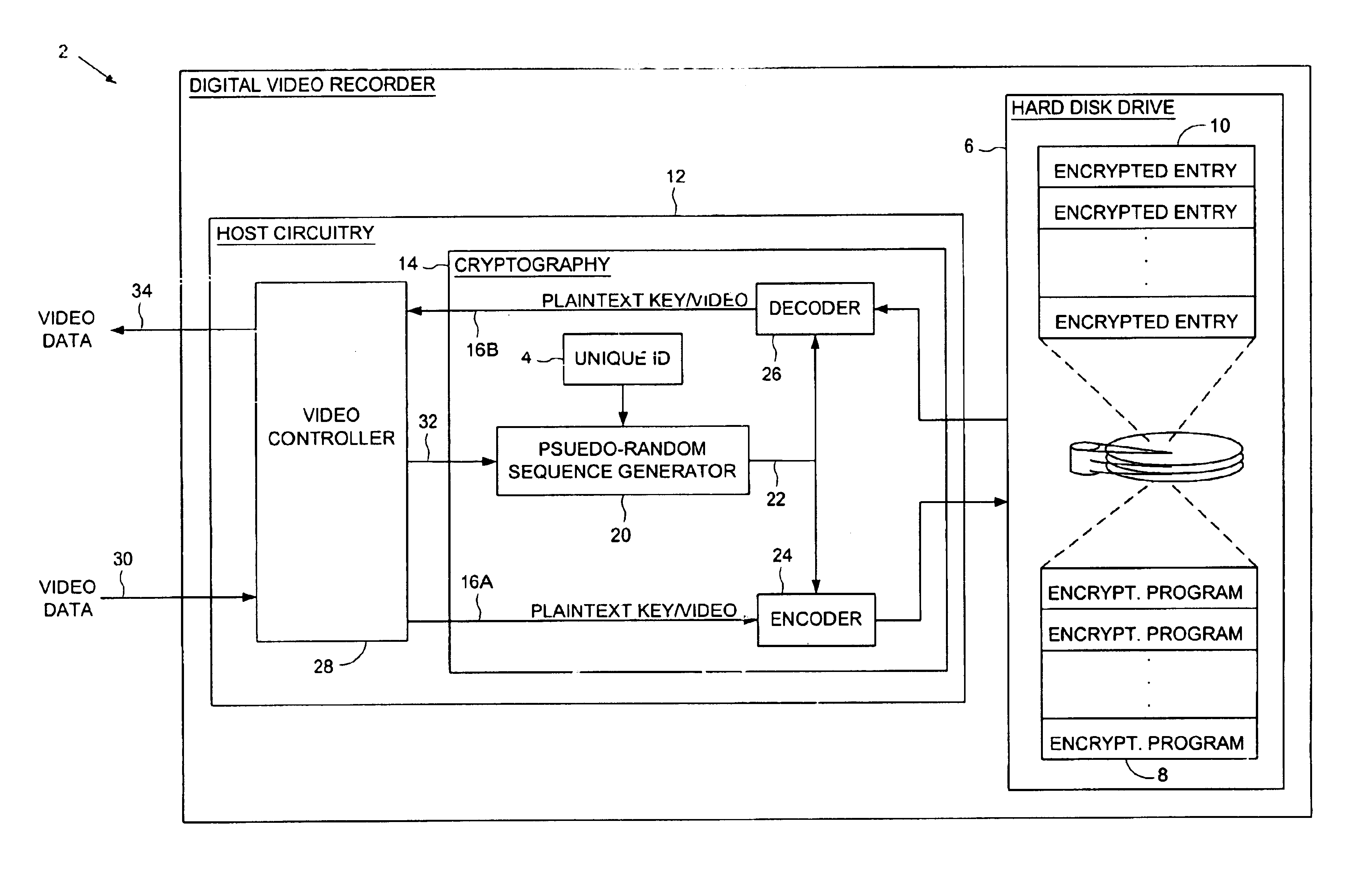
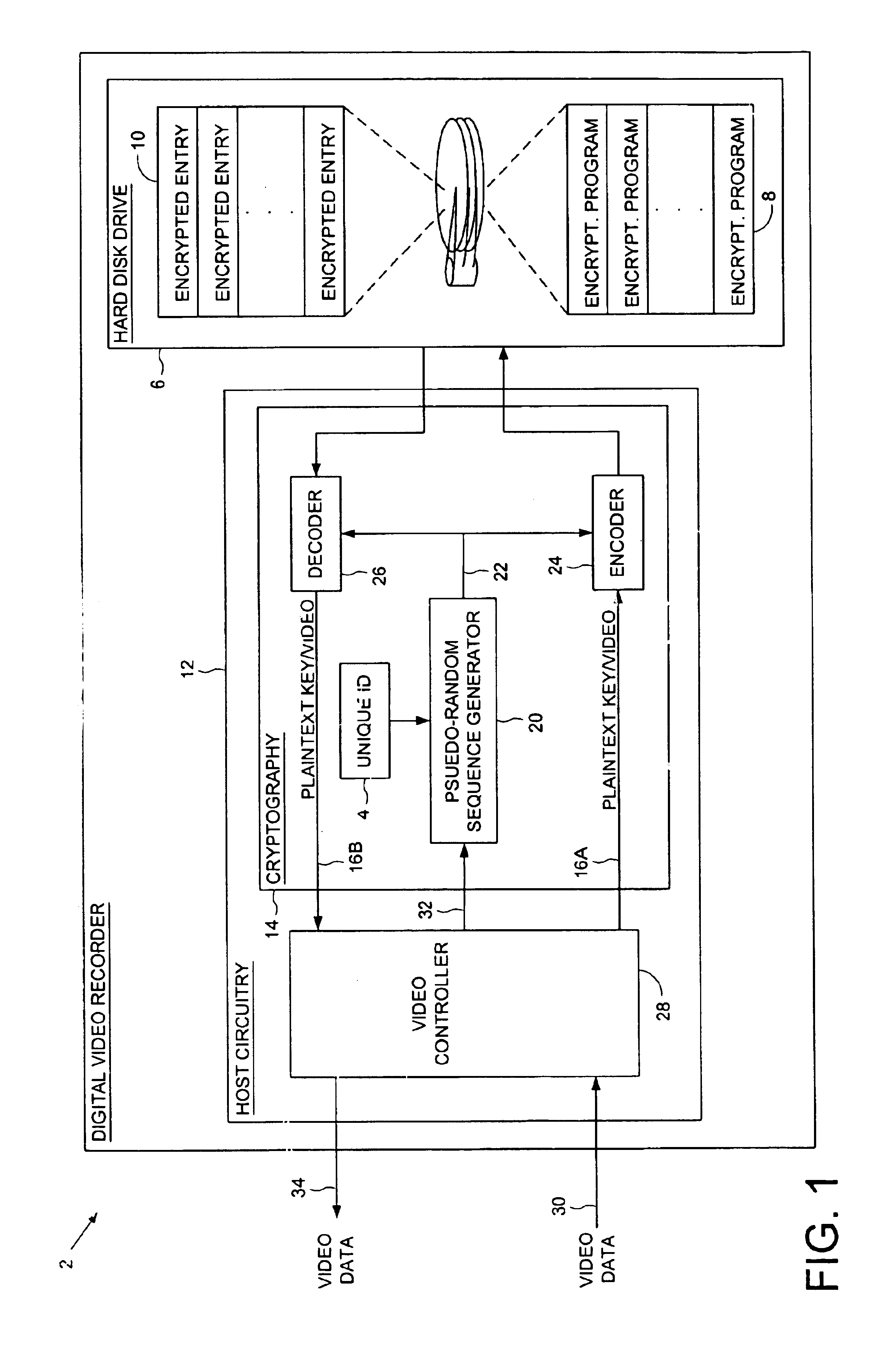
Digital video recorder employing a unique ID to interlock with encrypted video programs stored on a storage device
The present invention may be regarded as a digital video recorder (DVR) comprising a storage device for storing an encrypted video program, a unique ID for interlocking the encrypted video program with the digital video recorder, and a cryptography facility. The cryptography facility comprises an encoder, responsive to the unique ID, for encrypting a plaintext video program into the encrypted video program stored on the storage device, and a decoder, responsive to the unique ID, for decrypting the encrypted video program stored on the storage device into the plaintext video program during playback.
Owner:KEEN PERSONAL MEDIA +1
System and method for secure transaction
ActiveUS20090070583A1Improve securityEasy to upgradeFinanceCryptography processingPlaintextAuthentication
Systems and methods for performing a secure transaction provided. In one embodiment, the method includes: reading data on a command token, reading data on a token; encrypting the token data with a key; encrypting an authentication data with a clear text token data; and transmitting the encrypted authentication data with the encrypted token data to a remote device.
Owner:VERIFONE INC
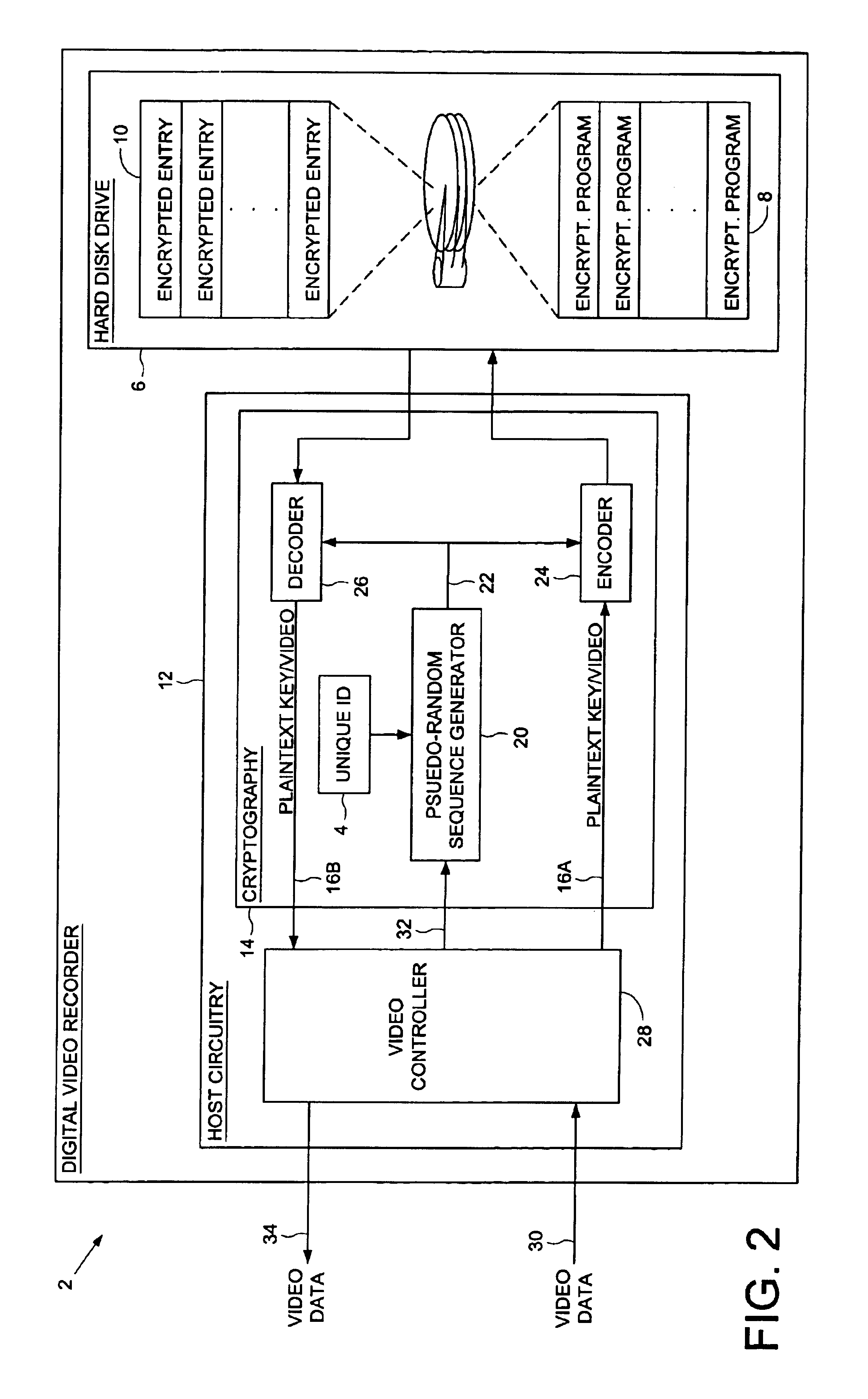
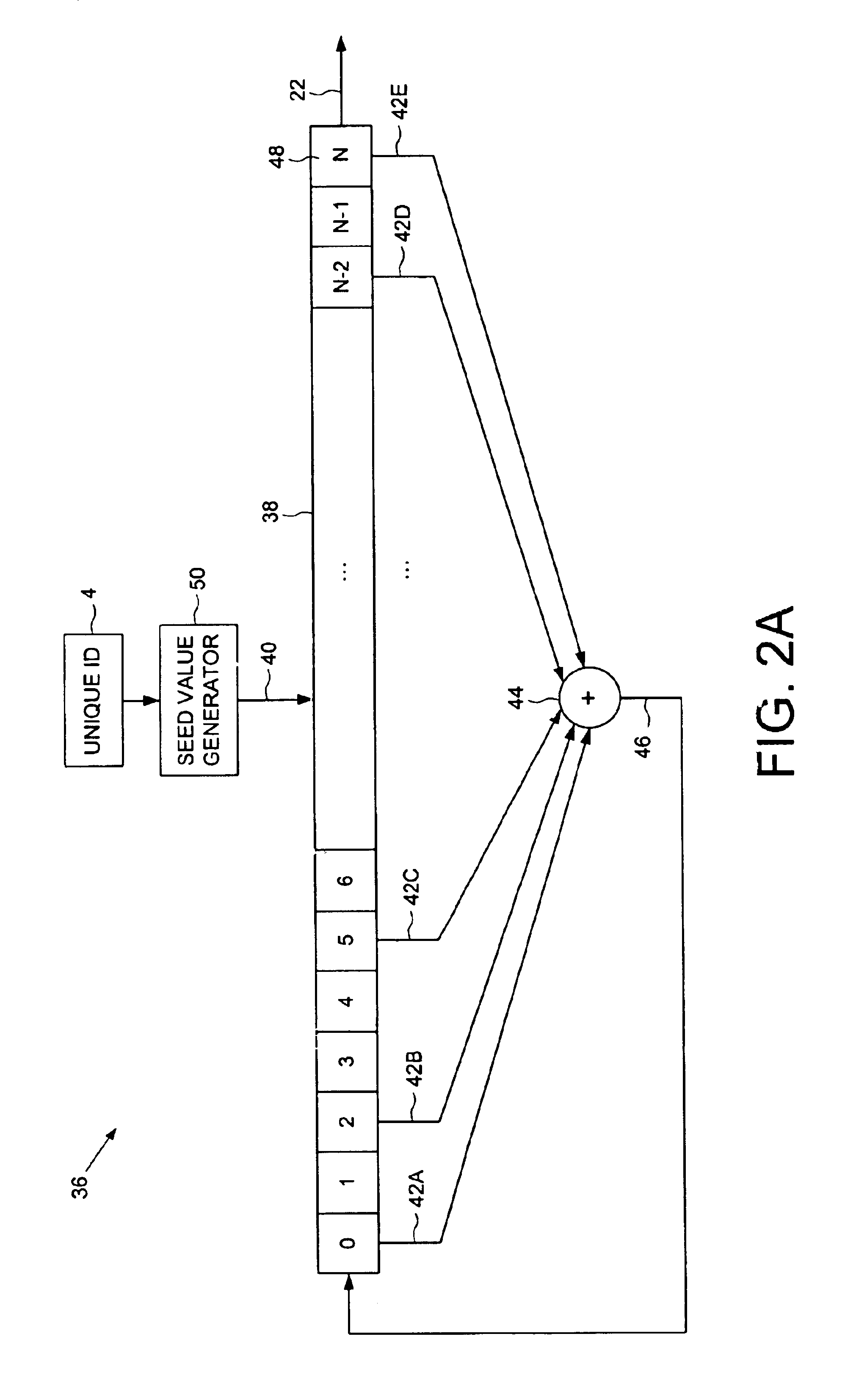
Digital video recorder employing a file system encrypted using a pseudo-random sequence generated from a unique ID
A digital video recorder (DVR) is disclosed comprising a unique ID, a hard disk drive (HDD) for storing a plurality of encrypted video programs and an encrypted file system, the encrypted file system comprising a plurality of encrypted file system entries for decrypting the plurality of video programs. The DVR further comprises host circuitry for interfacing with the HDD, the host circuitry comprising a cryptography facility for encrypting plaintext file system entries into the encrypted file system entries stored on the HDD, and for decrypting the encrypted file system entries read from the HDD into plaintext file system entries. The cryptography facility comprises a pseudo-random sequence generator, responsive to the unique ID, for generating a pseudo-random sequence. The cryptography facility further comprises an encoder for combining the pseudo-random sequence with the plaintext file system entries to generate the encrypted file system entries stored on the HDD, and a decoder for combining the pseudo-random sequence with the encrypted file system entries read from the HDD to generate the plaintext file system entries.
Owner:KEEN PERSONAL MEDIA +1
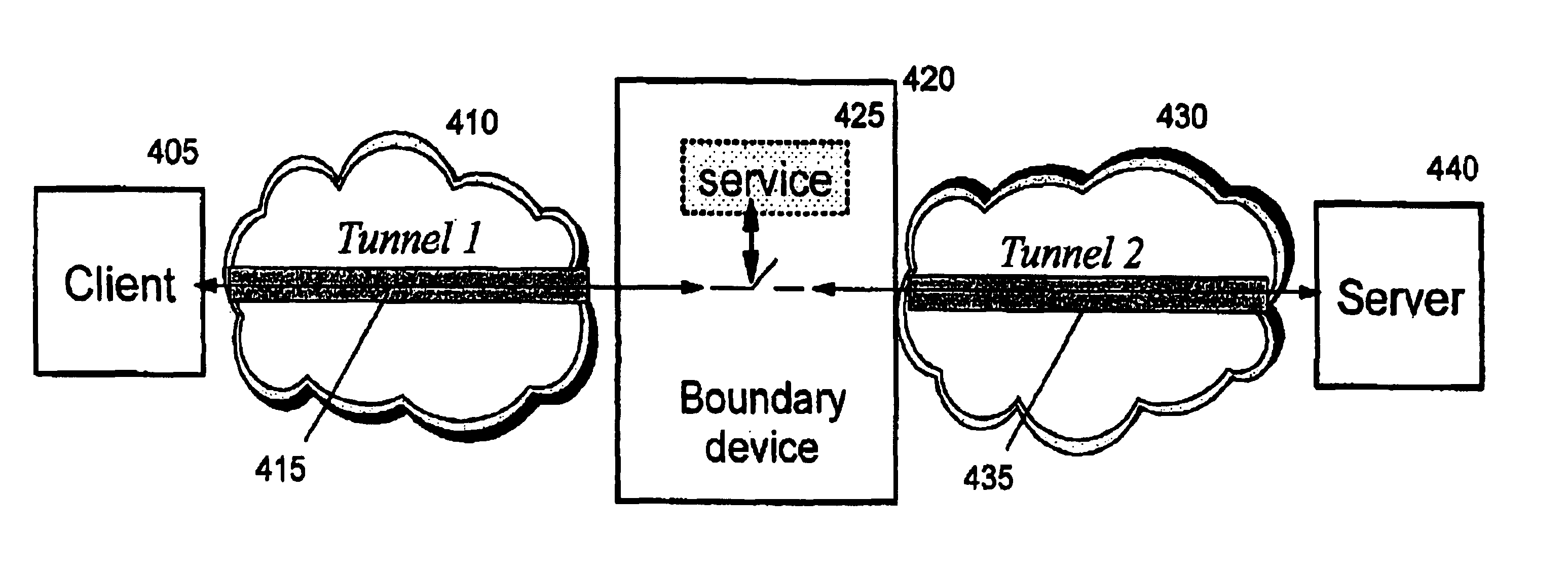
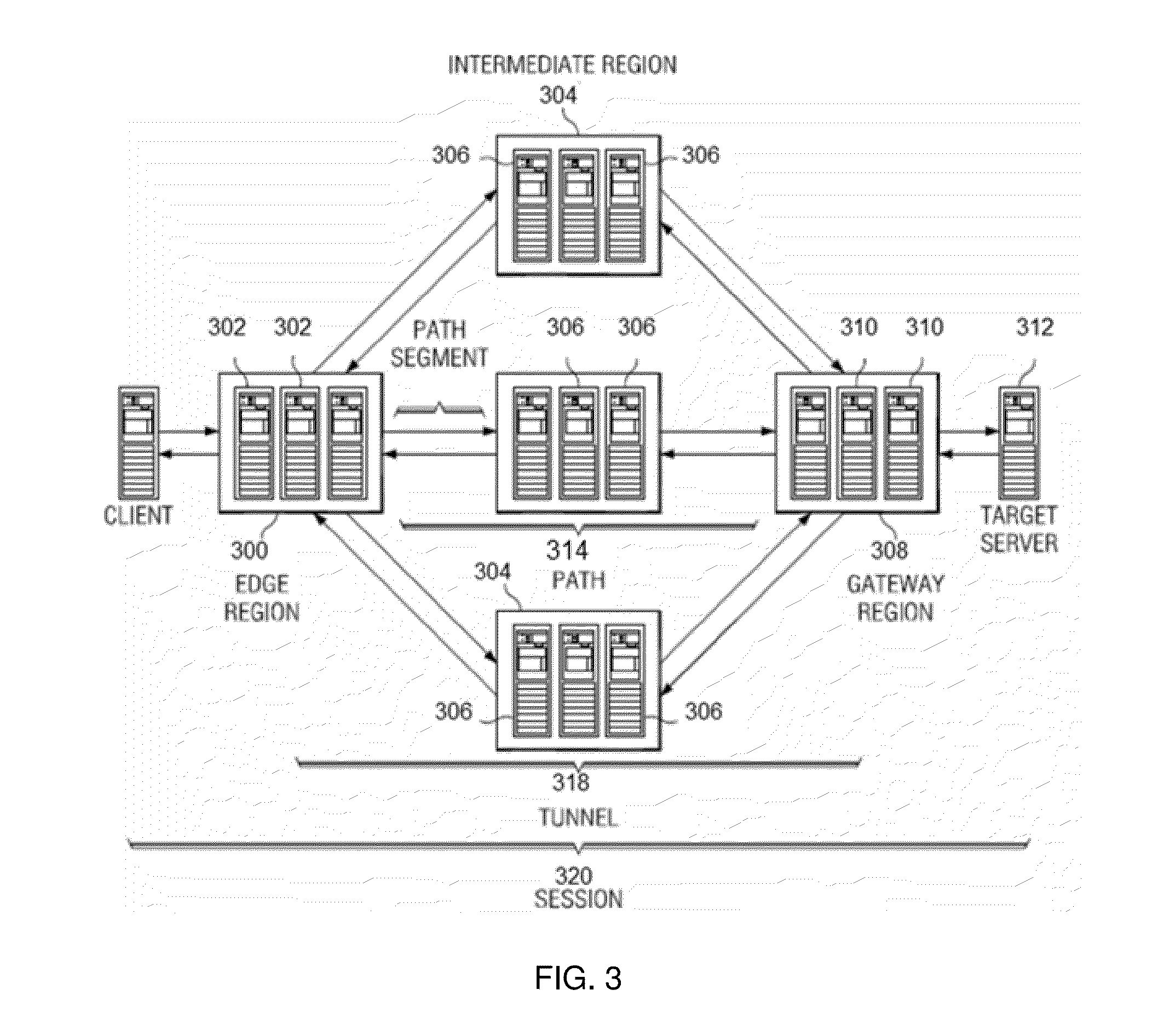
Establishing consistent, end-to-end protection for a user datagram
A method, system, and computer program product for providing consistent, end-to-end protection within a computer network for user datagrams (i.e. packets) traveling through the network. The network may comprise network segments that are conventionally assumed to be secure (such as those found in a corporate intranet) as well as network segments in non-secure networks (such as the public Internet or corporate extranets). Because security breaches may in fact happen in any network segment when datagrams are unprotected, the present invention discloses a technique for protecting datagrams throughout the entire network path by establishing cascaded tunnels. The datagrams may be exposed in cleartext at the endpoints of each tunnel, thereby enabling security gateways to perform services that require content inspection (such as network address translation, access control and authorization, and so forth). The preferred embodiment is used with the “IPSec” (Internet Protocol Security Protocol) and “IKE” (Internet Key Exchange) protocols, thus providing a standards-based solution.
Owner:IBM CORP
Pin block replacement
ActiveUS20080189214A1Improve securityEasy to upgradeAcutation objectsPoint-of-sale network systemsPlaintextPassword
Systems and methods for performing token transactions are provided. In one embodiment, the invention provides for processing token transactions, including receiving an encrypted password for a debit card transaction, wherein the password was secured using encrypted debit-card information, decrypting the password using encrypted debit-card information for the debit card, recreating the password using actual debit-card information for the debit card, and forwarding the recreated password for subsequent transaction processing. The invention is suitable for implementation with other types of tokens in addition to debit-card tokens as well. The invention can be implemented in a scenario where the password includes a PIN block that is created by combining a clear or encrypted PIN for the token with token information.
Owner:VERIFONE INC
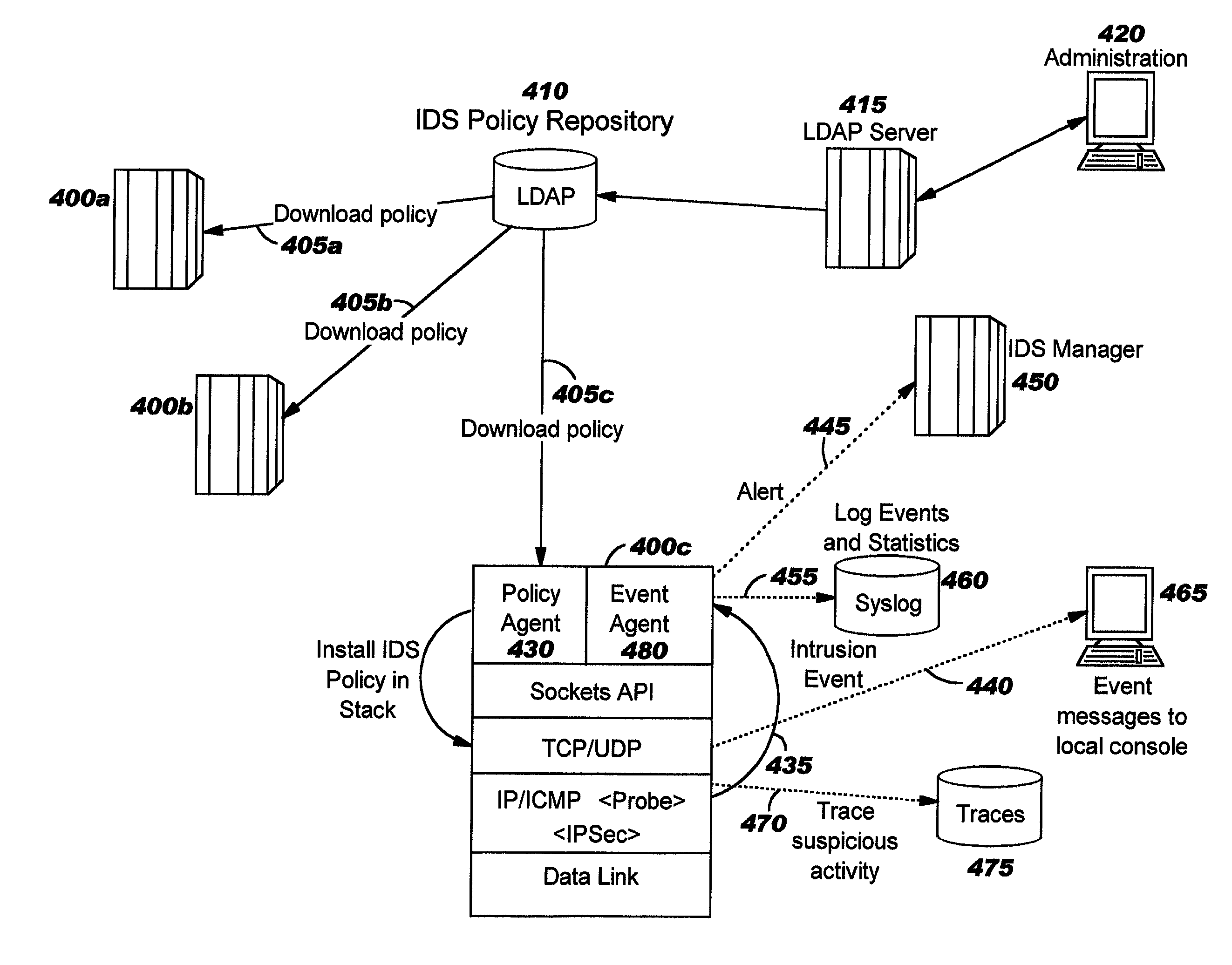
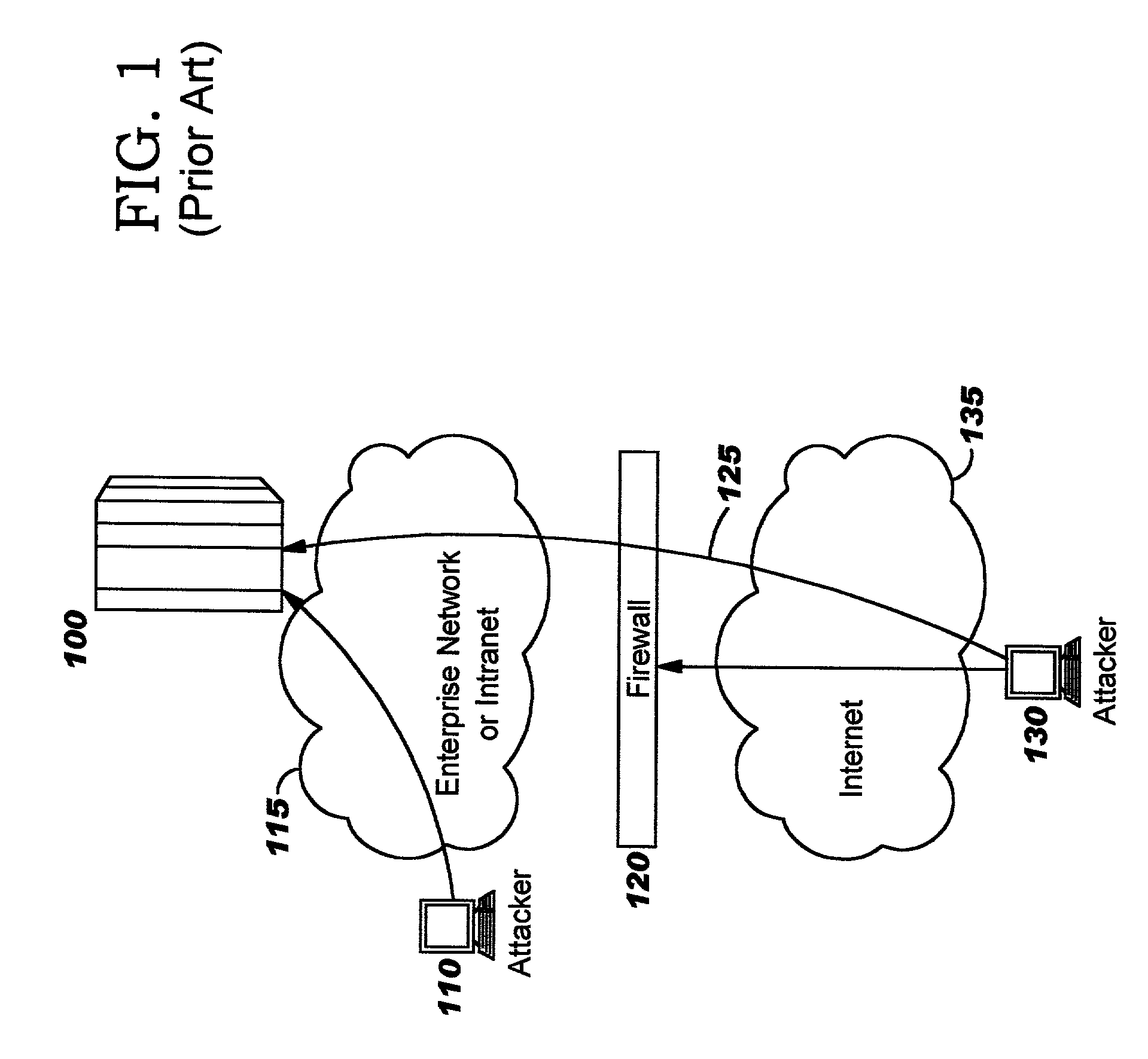
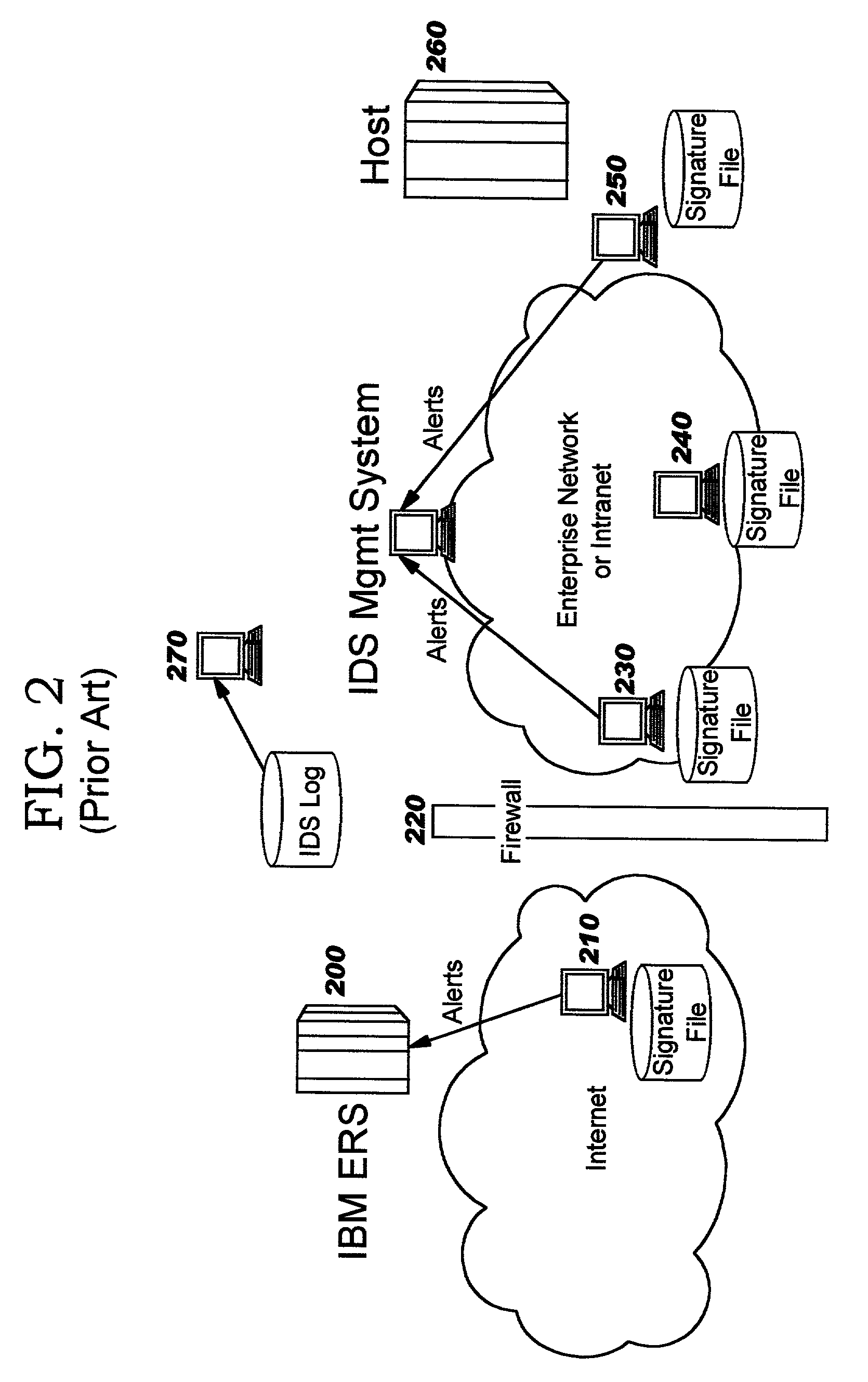
Integrated intrusion detection services
ActiveUS7076803B2Improve securityEasy to detectMemory loss protectionError detection/correctionTraffic capacityPlaintext
Improvements in intrusion detection are disclosed by providing integrated intrusion detection services. Preferably, these services are integrated into a system or server that is the potential target of attack. Stack-based security processing is leveraged for access to cleartext data within the layers of the protocol stack. Layer-specific attacks may therefore be processed efficiently. Evaluation of incoming traffic for an intrusion is preferably performed only after an error condition of some type has been detected. This approach reduces the overhead of intrusion detection by reducing the number of packets to be inspected, and at the same time allows more efficient packet inspection through use of context-specific information that may be used to direct the inspection to particular candidate attacks. Generic attack class capability is also disclosed. Intrusion detection policy information may be used to direct the actions to be taken upon detecting an attack.
Owner:TREND MICRO INC
System and method for variable length encryption
InactiveUS20120039469A1Ensure data securityImprove securityCryptography processingPayment architecturePlaintextVariable length
Systems and methods for performing a secure transaction provided. In one embodiment, the method includes: reading data on a command token, reading data on a token; encrypting the token data with a key; encrypting an authentication data with a clear text token data; and transmitting the encrypted authentication data with the encrypted token data to a remote device.
Owner:VERIFONE INC
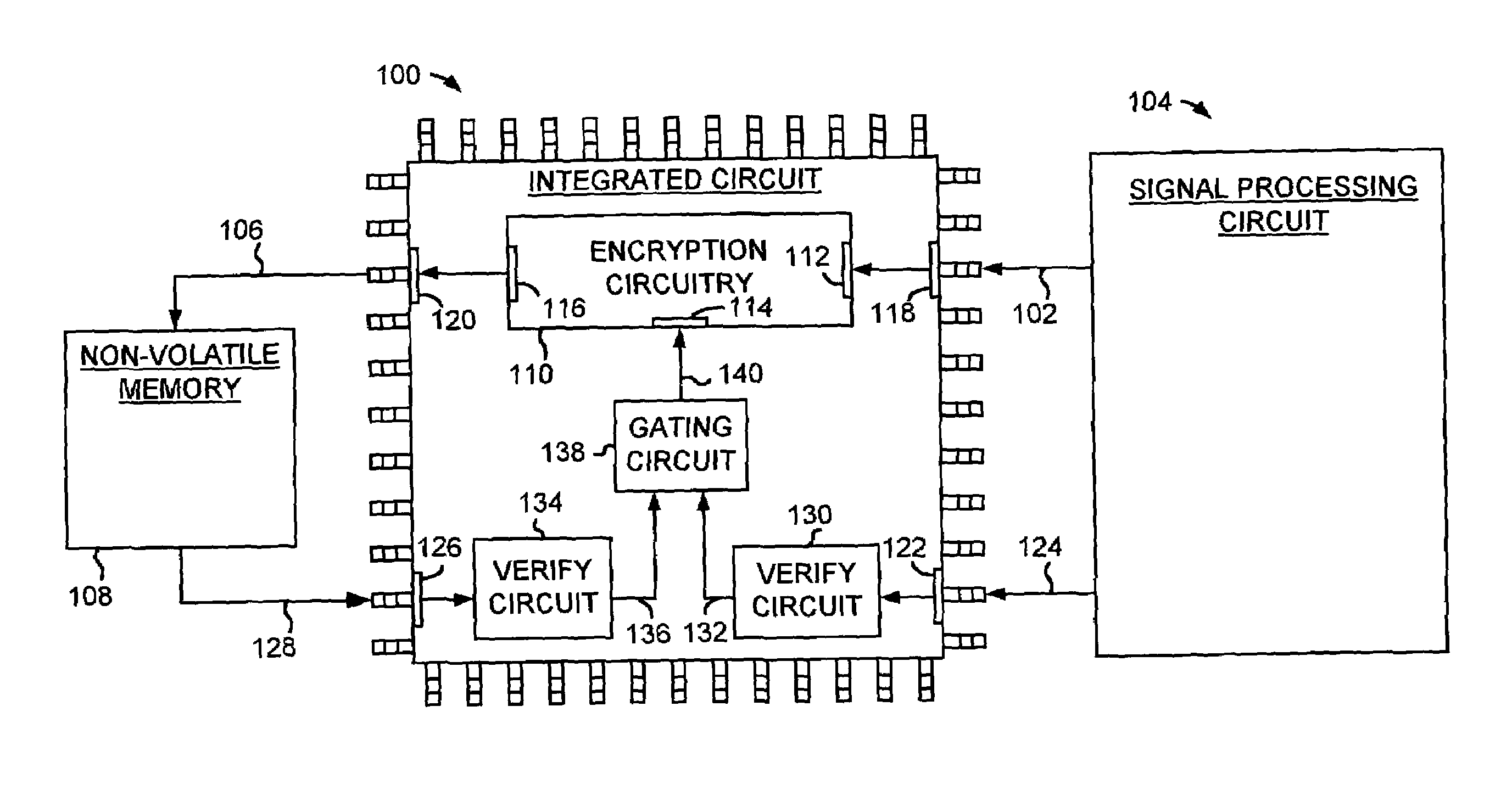
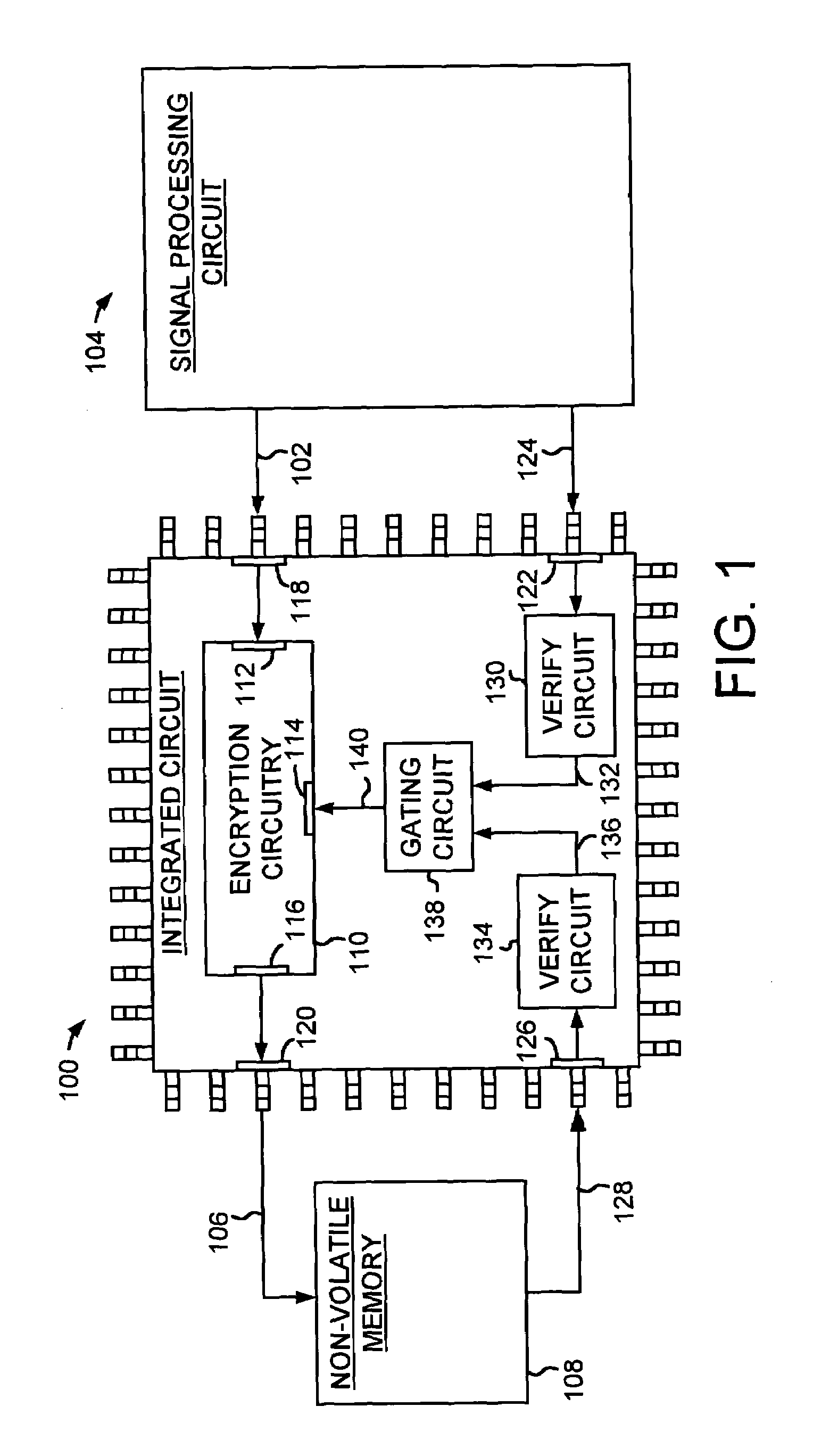
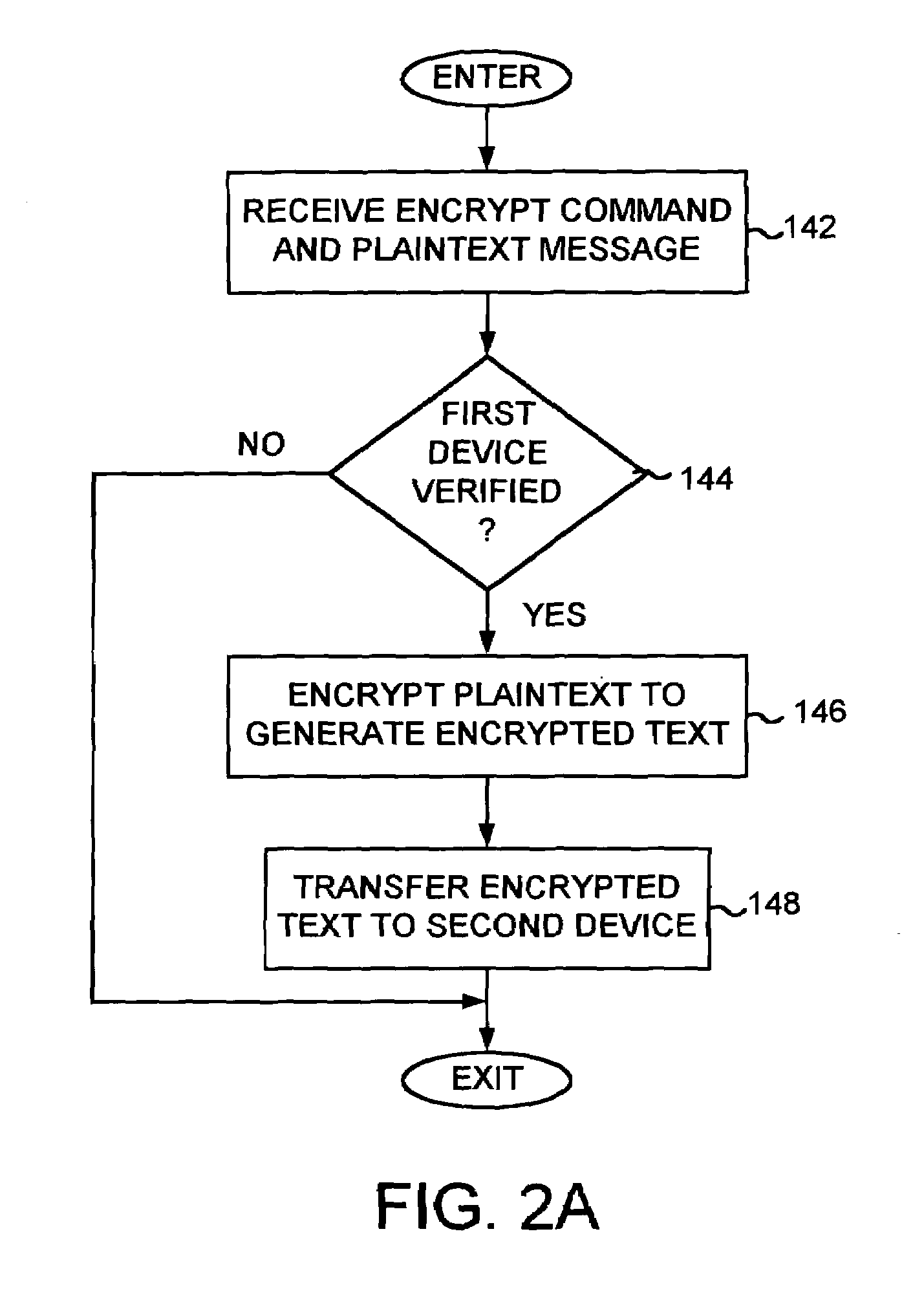
Integrated circuit comprising encryption circuitry selectively enabled by verifying a device
InactiveUS6973570B1Digital data processing detailsUser identity/authority verificationPlaintextIntegrated circuit
An integrated circuit is disclosed for selectively encrypting plaintext data received from a first device to produce encrypted data to send to a second device. The integrated circuit comprises controllable encryption circuitry comprising a data input, an enable input, and a data output. The integrated circuit further comprises a plaintext input for providing the plaintext data to the data input, an encrypted text output for providing the encrypted data from the data output, and a first control input for receiving a first device authentication signal for authenticating the first device. The integrated circuit further comprises a verification circuit responsive to the first device authentication signal for producing a first verification signal for use in controlling the enable input of the encryption circuitry to enable the encryption circuitry to provide the encrypted data via the encrypted text output.
Owner:WESTERN DIGITAL VENTURES
Batch settlement transactions system and method
InactiveUS20080091944A1Ensure data securityImprove securityCryptography processingUser identity/authority verificationPlaintextBatch processing
Systems and methods for performing settlement of token access transactions are provided. In one embodiment, the invention provides for batch processing bank card transactions, including receiving transaction records for a plurality of bank card transactions, wherein at least some of the transaction records include encrypted token information; determining whether the transaction records contain encrypted token information; decrypting the encrypted token information for a transaction record that is determined to have encrypted token information; and providing clear text token information obtained by decrypting the encrypted token information for a transaction record for transaction settlement.
Owner:VERIFONE INC
Accessing protected data on network storage from multiple devices
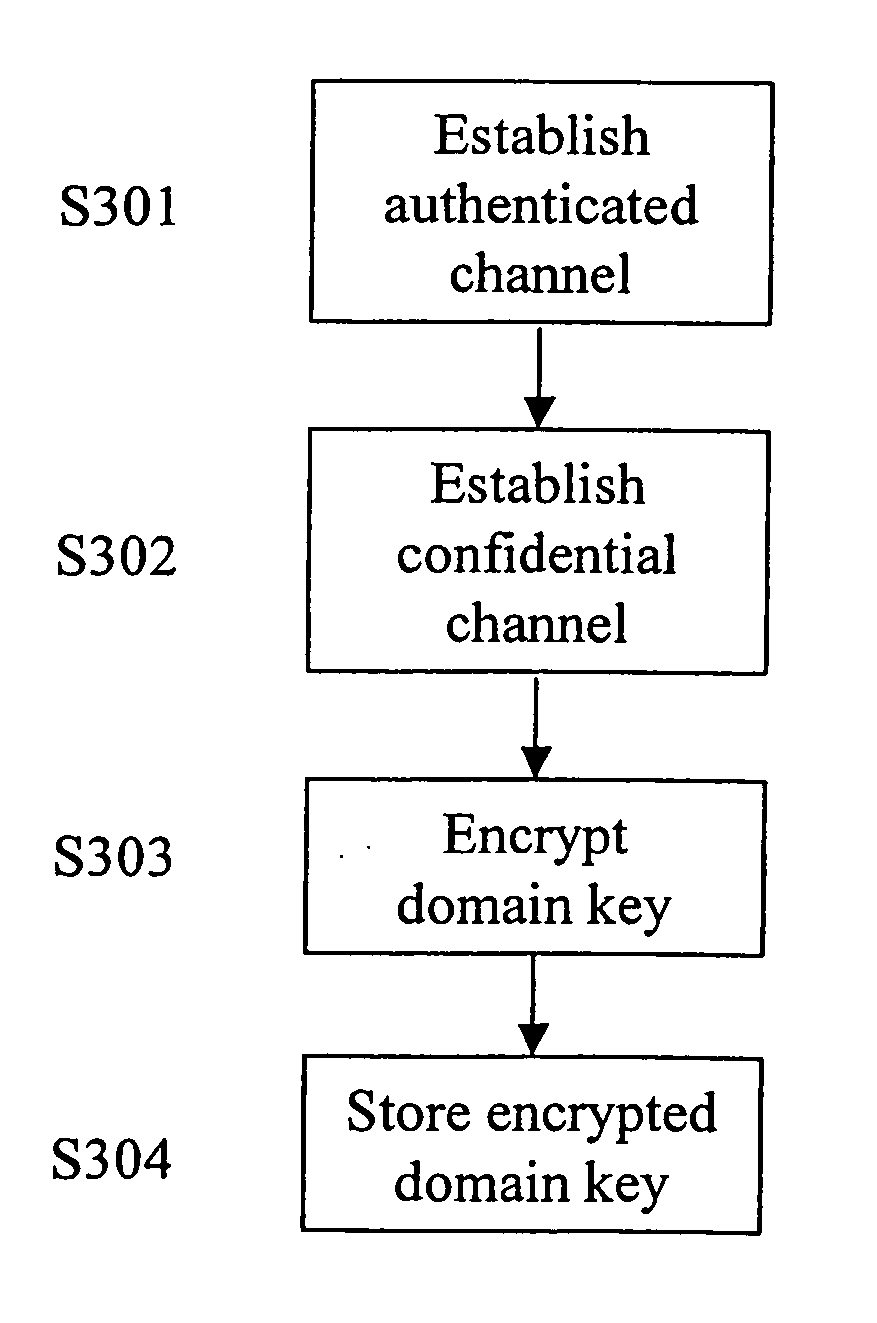
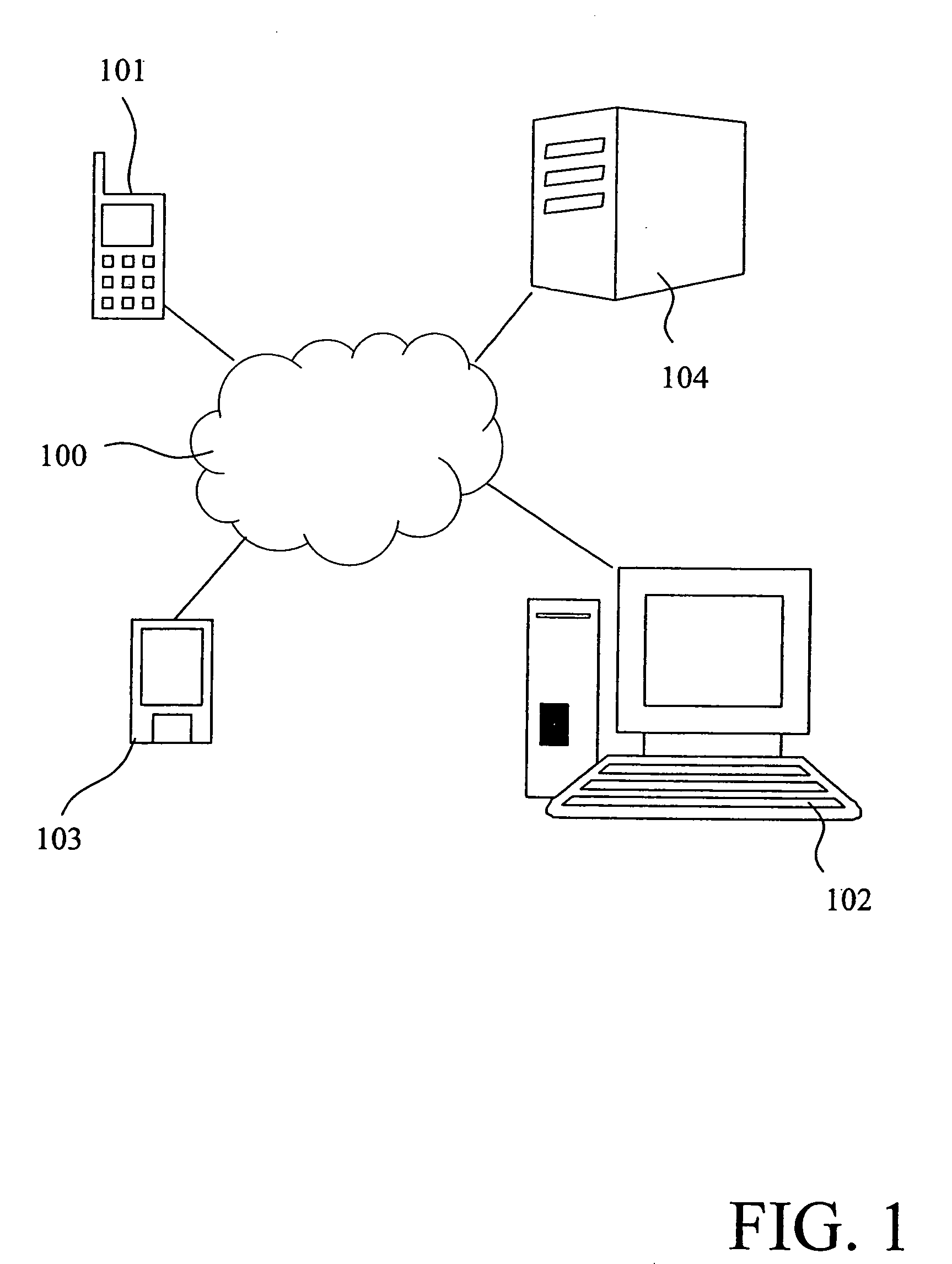
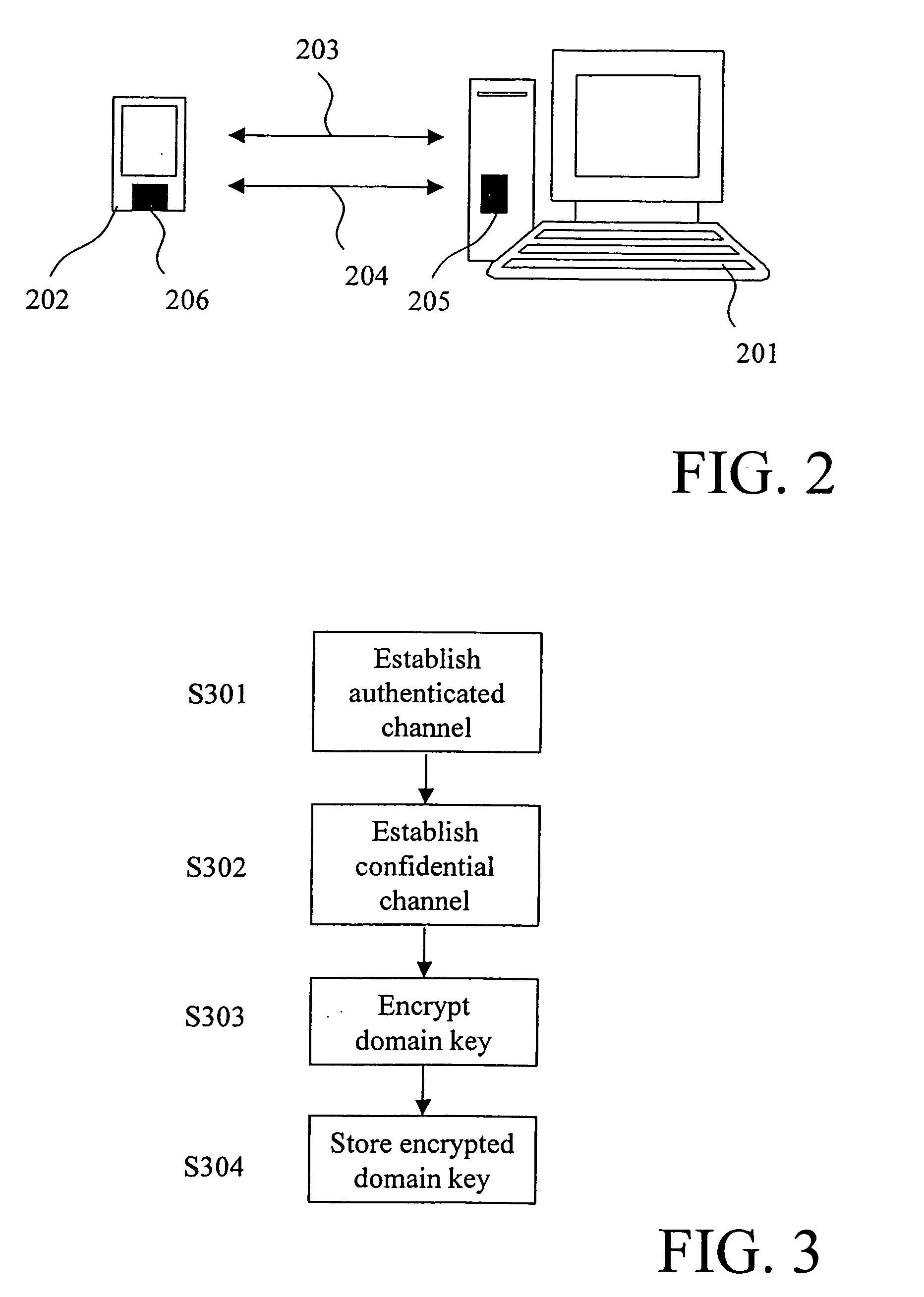
ActiveUS20050193199A1Easy to manageKey distribution for secure communicationData taking preventionPlaintextAuthorized domain
The present invention relates to a method and a system of securely storing data on a network (100) for access by an authorized domain (101, 102, 103), which authorized domain includes at least two devices that share a confidential domain key (K), and an authorized domain management system for securely storing data on a network for access by an authorized domain. The present invention enables any member device to store protected data on the network such that any other member device can access the data in plaintext without having to communicate with the device that actually stored the data.
Owner:NOKIA TECHNOLOGLES OY
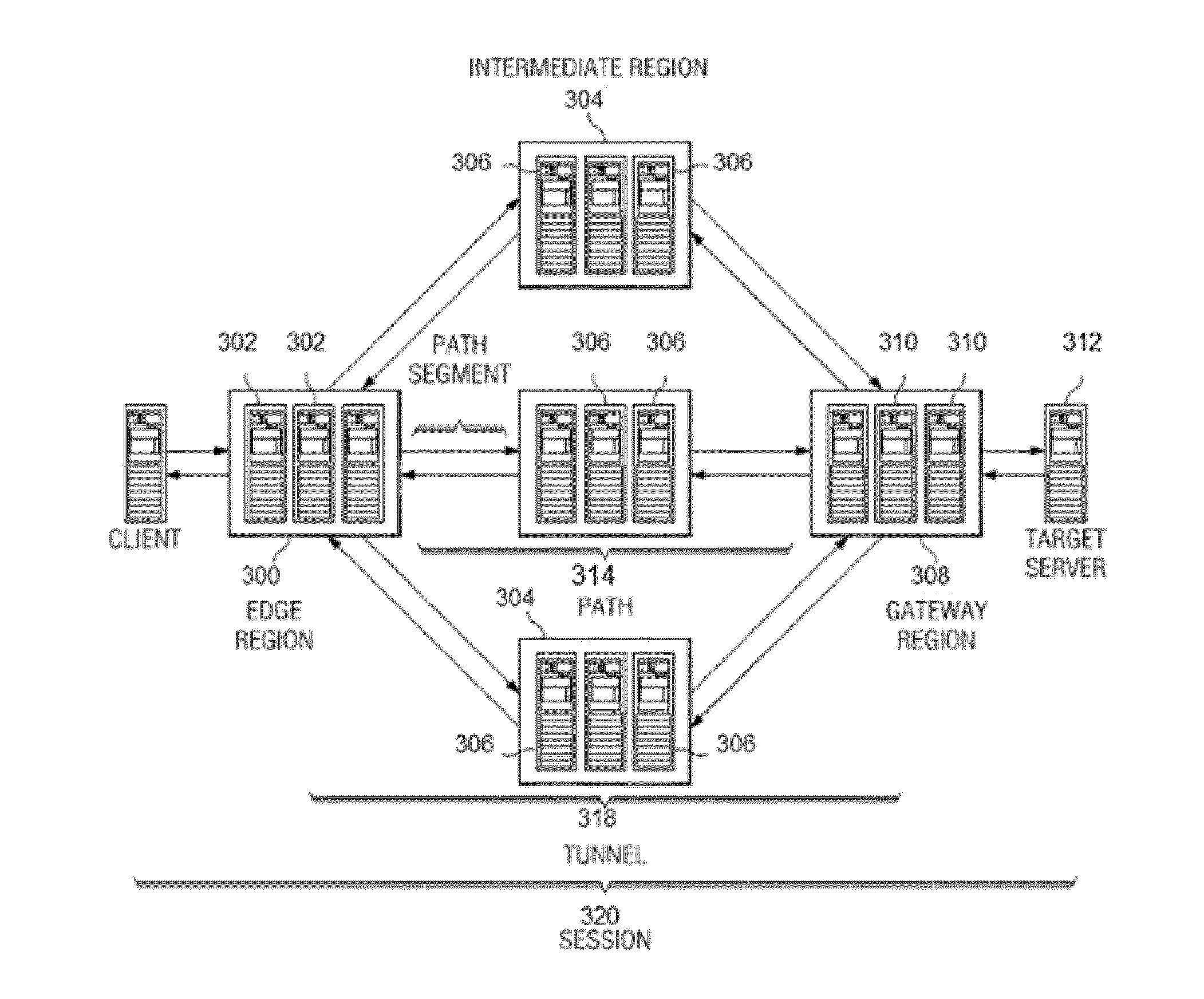
Virtual private network (VPN)-as-a-service with load-balanced tunnel endpoints
ActiveUS20150188823A1Facilitate (VPN)-as-a-serviceEfficient use ofError preventionFrequency-division multiplex detailsPlaintextData stream
A mechanism to facilitate a private network (VPN)-as-a-service, preferably within the context of an overlay IP routing mechanism implemented within an overlay network. The overlay provides delivery of packets end-to-end between overlay network appliances positioned at the endpoints. During such delivery, the appliances are configured such that the data portion of each packet has a distinct encryption context from the encryption context of the TCP / IP portion of the packet. By establishing and maintaining these distinct encryption contexts, the overlay network can decrypt and access the TCP / IP flow. This enables the overlay network provider to apply one or more TCP optimizations. At the same time, the separate encryption contexts ensure the data portion of each packet is never available in the clear at any point during transport. According to another feature, data flows within the overlay directed to a particular edge region may be load-balanced while still preserving IPsec replay protection.
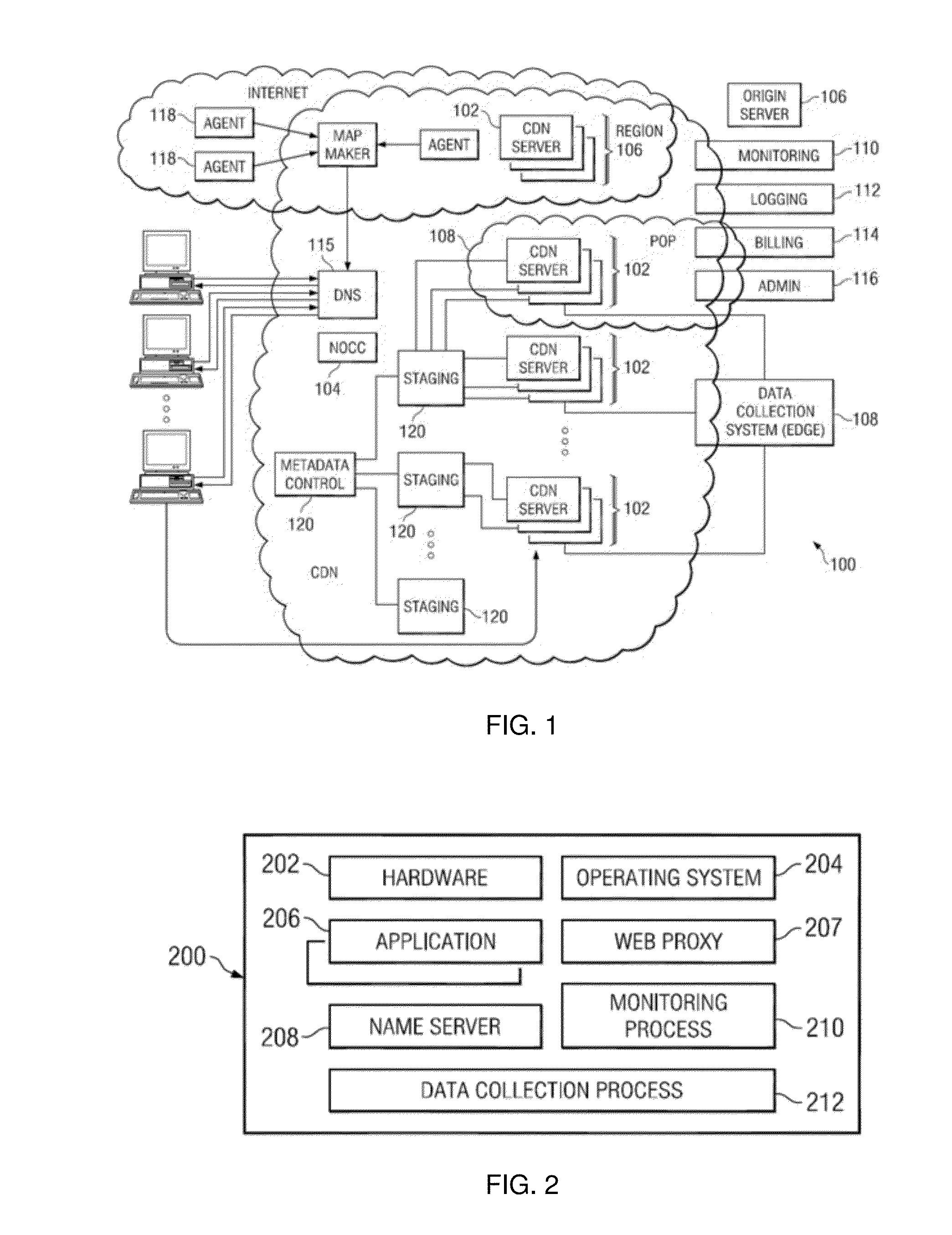
Owner:AKAMAI TECH INC
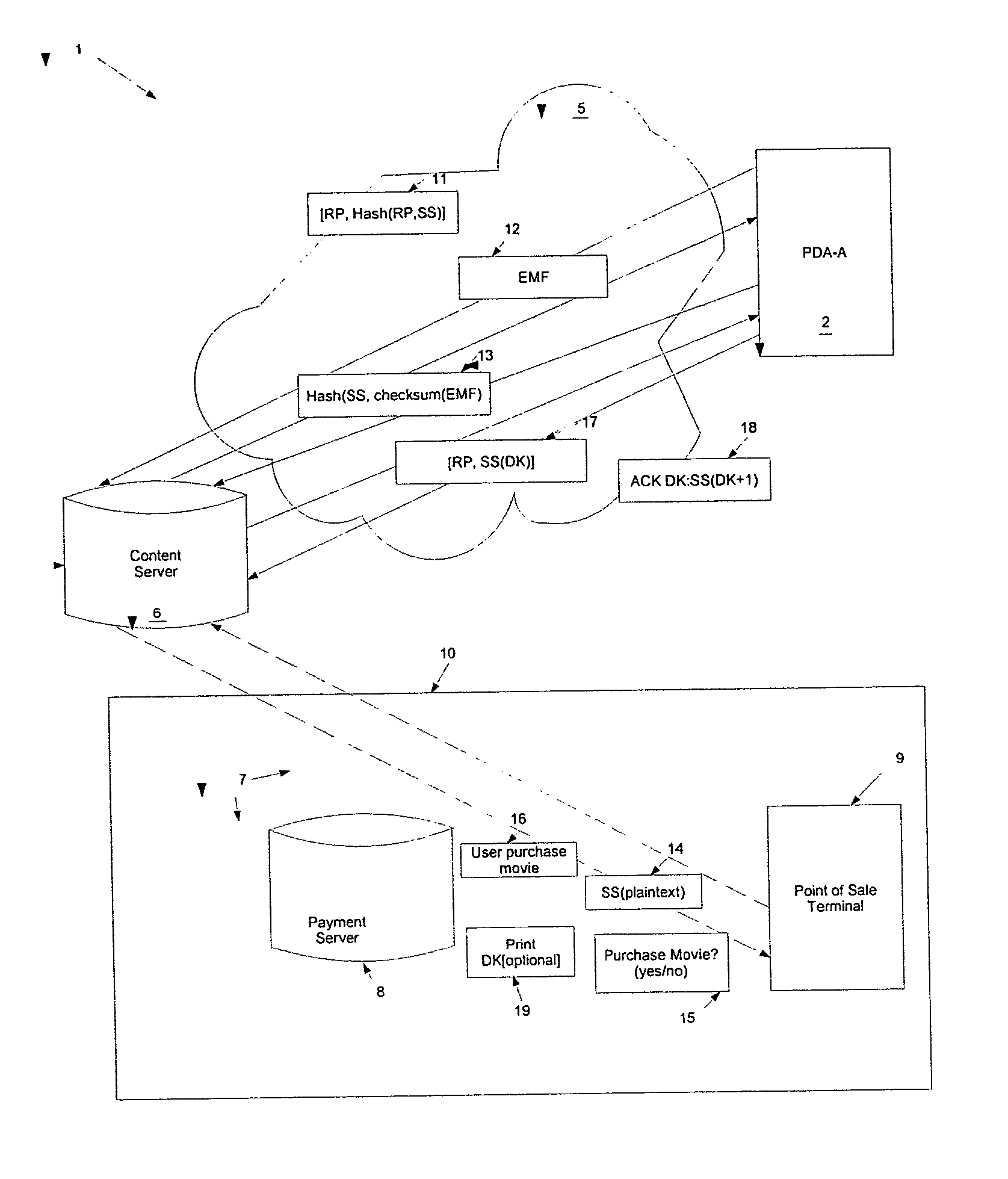
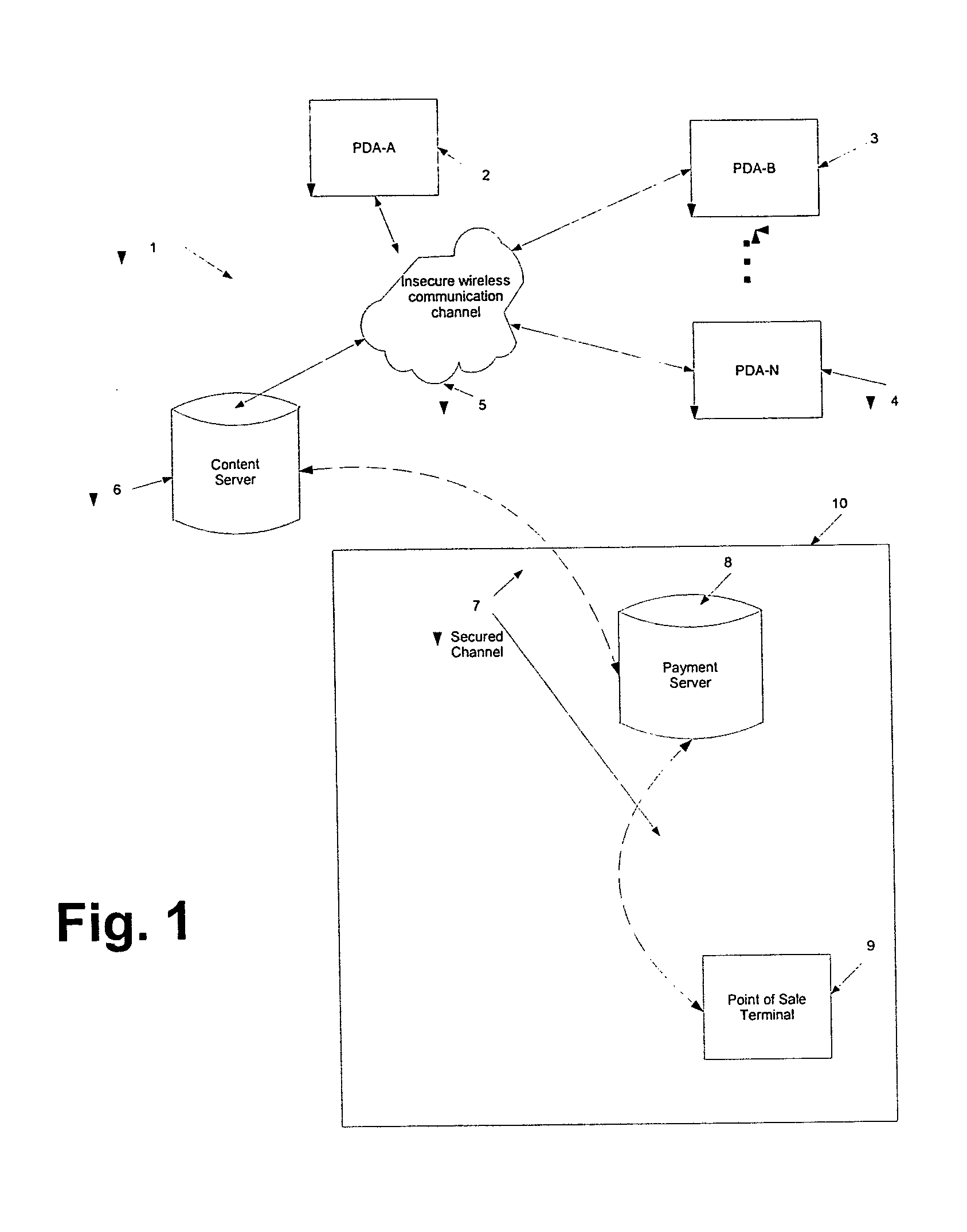
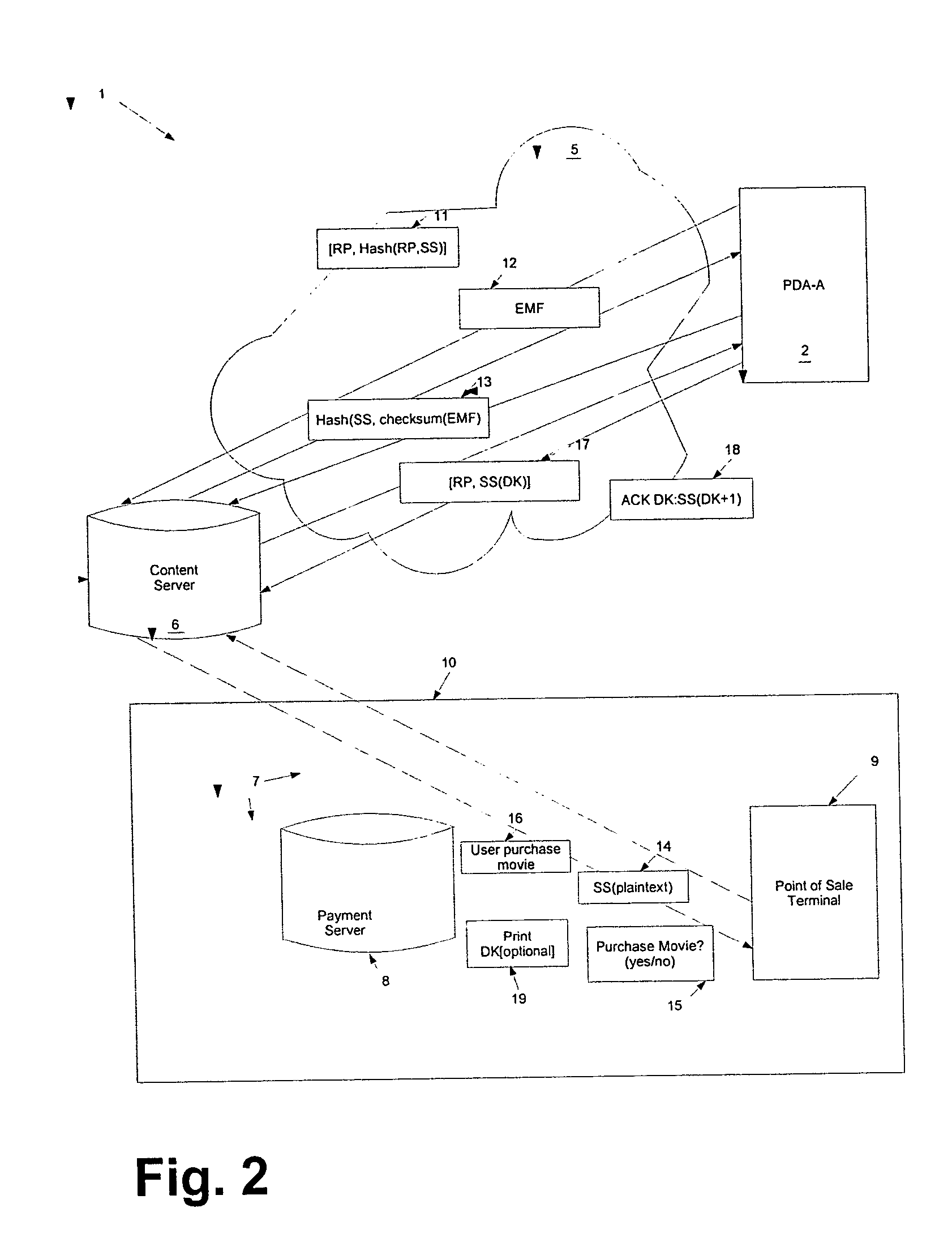
Method and system for content downloads via an insecure communications channel to devices
ActiveUS20050076210A1Easy to downloadKey distribution for secure communicationDigital data processing detailsPlaintextSecure communication
The present teachings provide for a method and system for facilitating content download to one or more remote devices via an insecure communication channel. The method comprises the steps of receiving at least one shared secret from a device via an insecure communications channel, each shared secret encoded and functioning as an identifier for the device, transmitting an encrypted file, from a file server, to the device associated with the encoded shared secret, receiving the shared secret in a plaintext form a via a secure communications channel, receiving a confirmation authorizing the release of a decryption key, and sending a decryption key corresponding to the transmitted file, for which the authorization for the release of the decryption key has been received. The decryption key is encrypted using the shared secret if transmission is via the insecure channel.
Owner:MARQETA
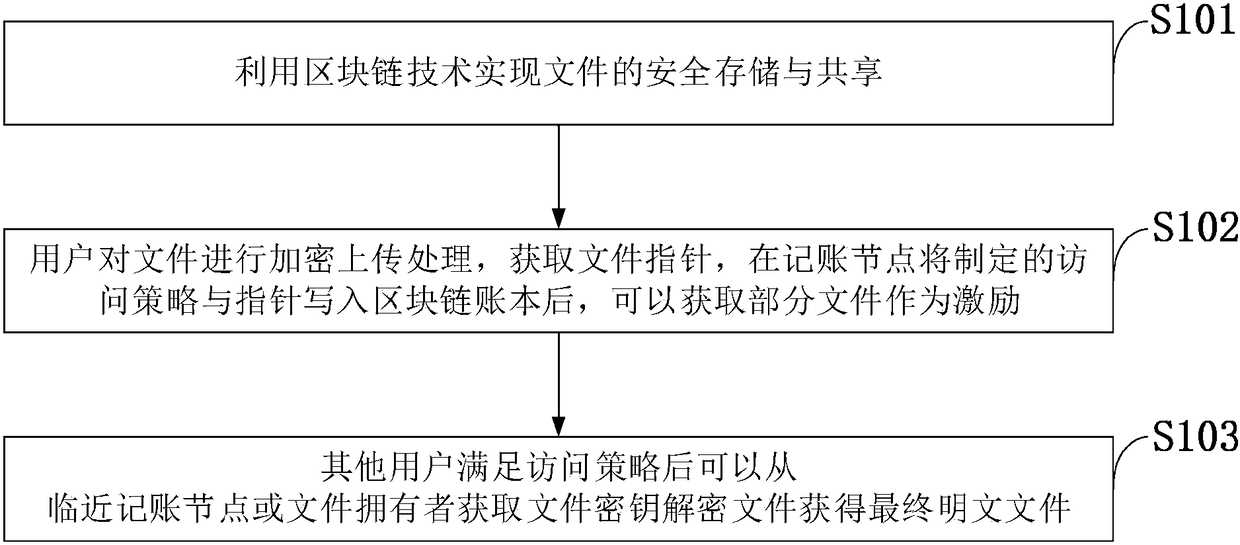
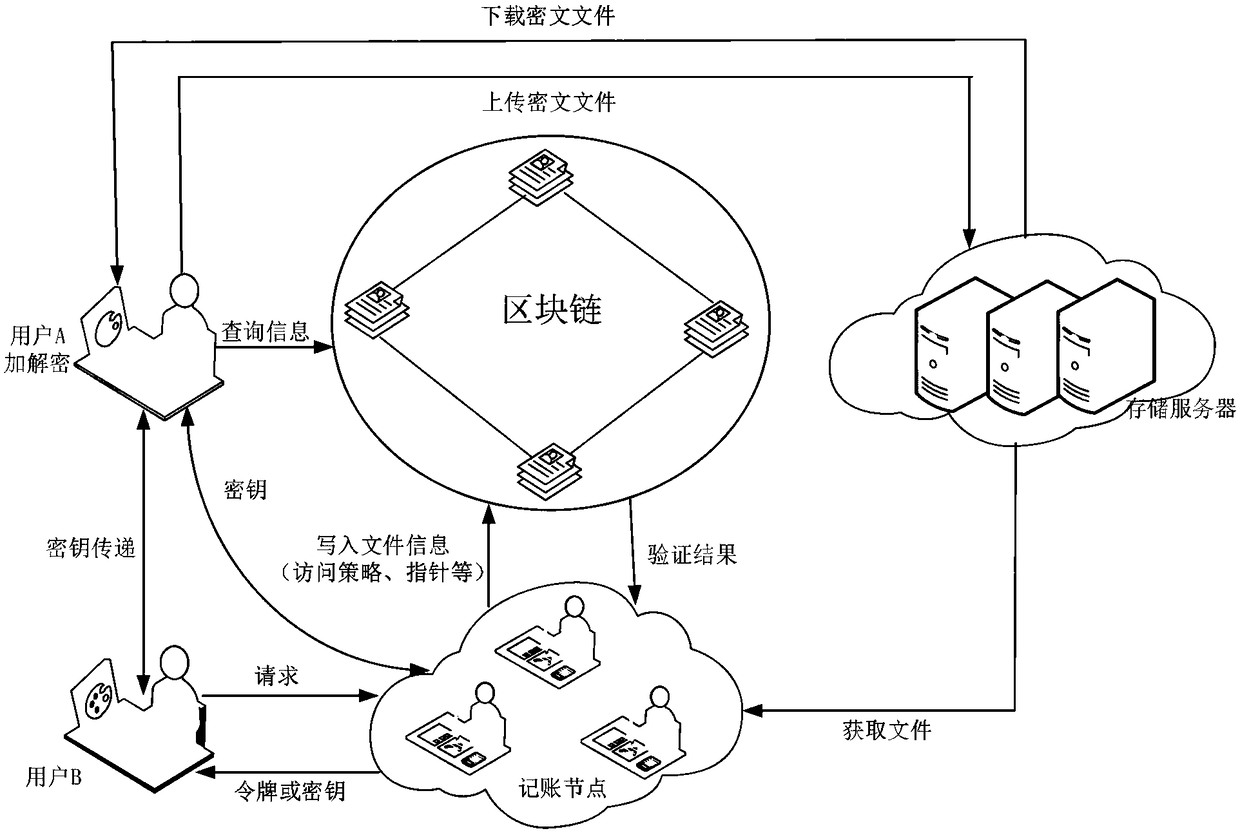
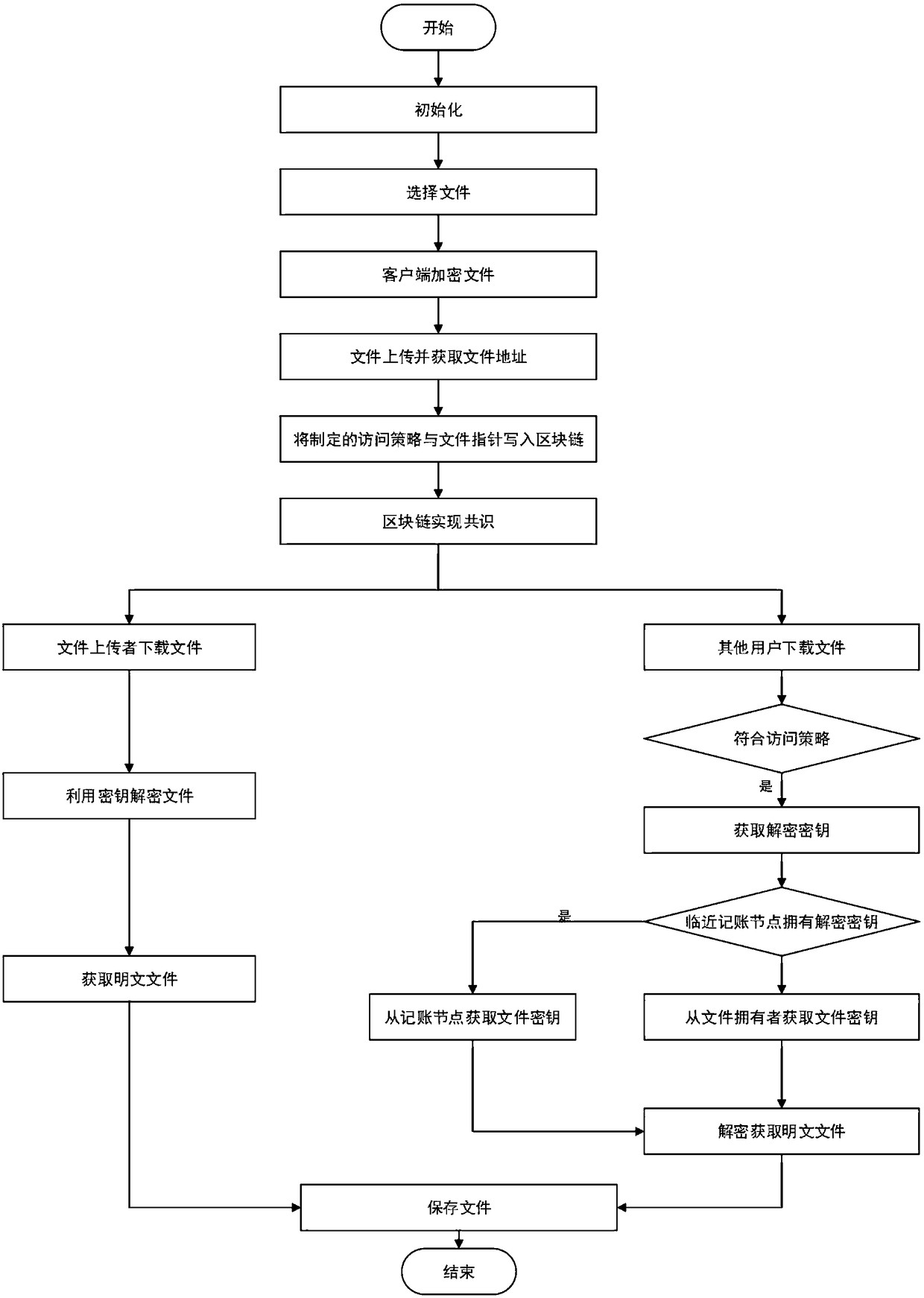
Method for storing and sharing secure files based on blockchain
ActiveCN108462568AGuaranteed not to be tampered withIntegrity guaranteedKey distribution for secure communicationEncryption apparatus with shift registers/memoriesPlaintextData library
The invention belongs to the technical field of information retrieval and database structure, discloses a method for storing and sharing secure files based on a blockchain, and uses the blockchain technology to realize secure storage and sharing of files. A user encrypts and uploads the files to obtain a file pointer, and acquires the partial file as the excitation after the accounting node writesthe information such as the formulated access policy and the pointer into a blockchain account. And the other users may acquire a file key from the adjacent accounting node or the file owner after satisfying the access policy to decrypt the files so as to finally obtain a plaintext file. The invention ensures the security of the user data, and is simple and convenient for the user to use, and thepublic key cryptography technology makes the file more secure at the same time. The unchangeable modification progress of the blockchain account further ensures the complete availability of the files, enables the user to formulate different access strategies for different files, and enables full control of the files while sharing the same.
Owner:XIDIAN UNIV
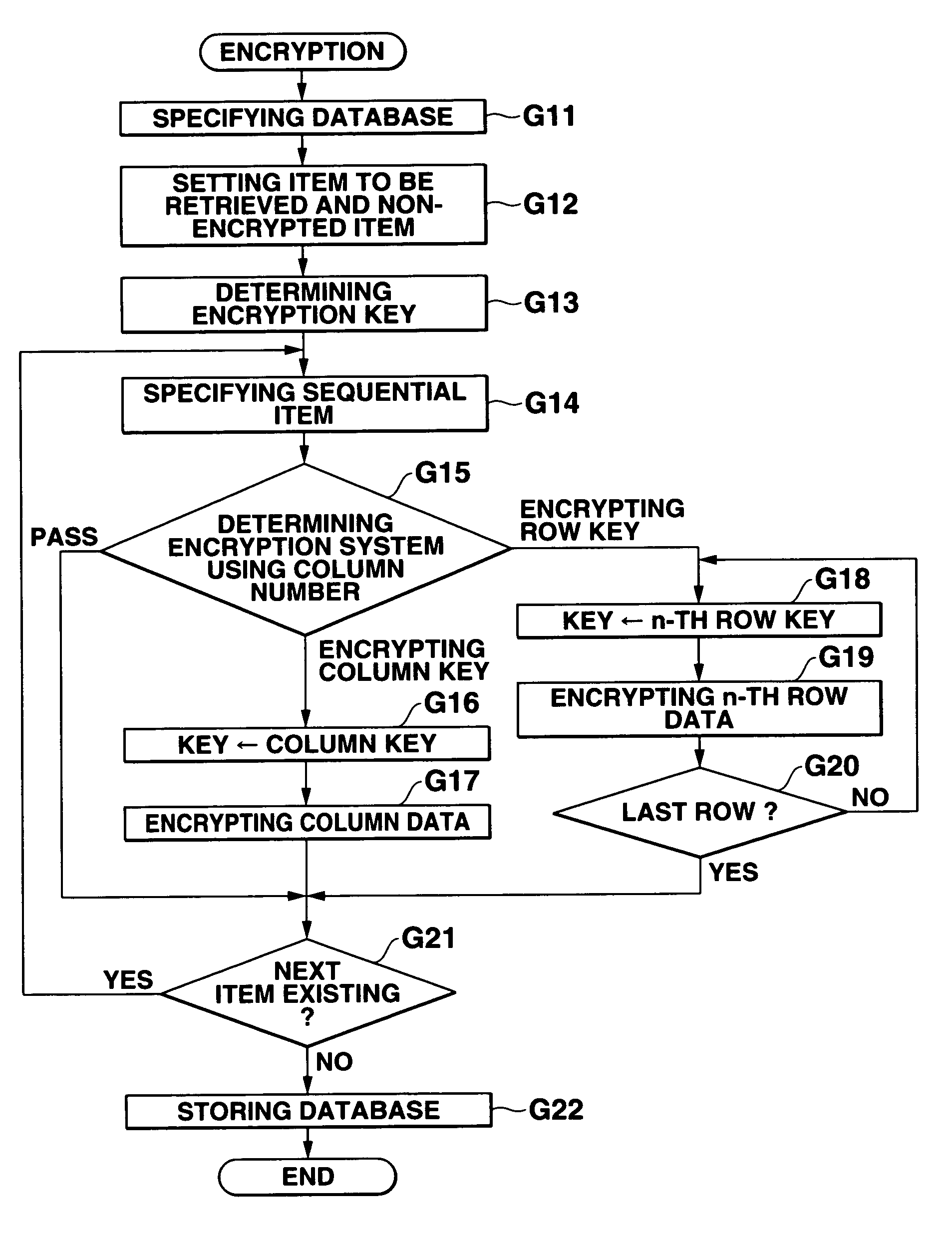
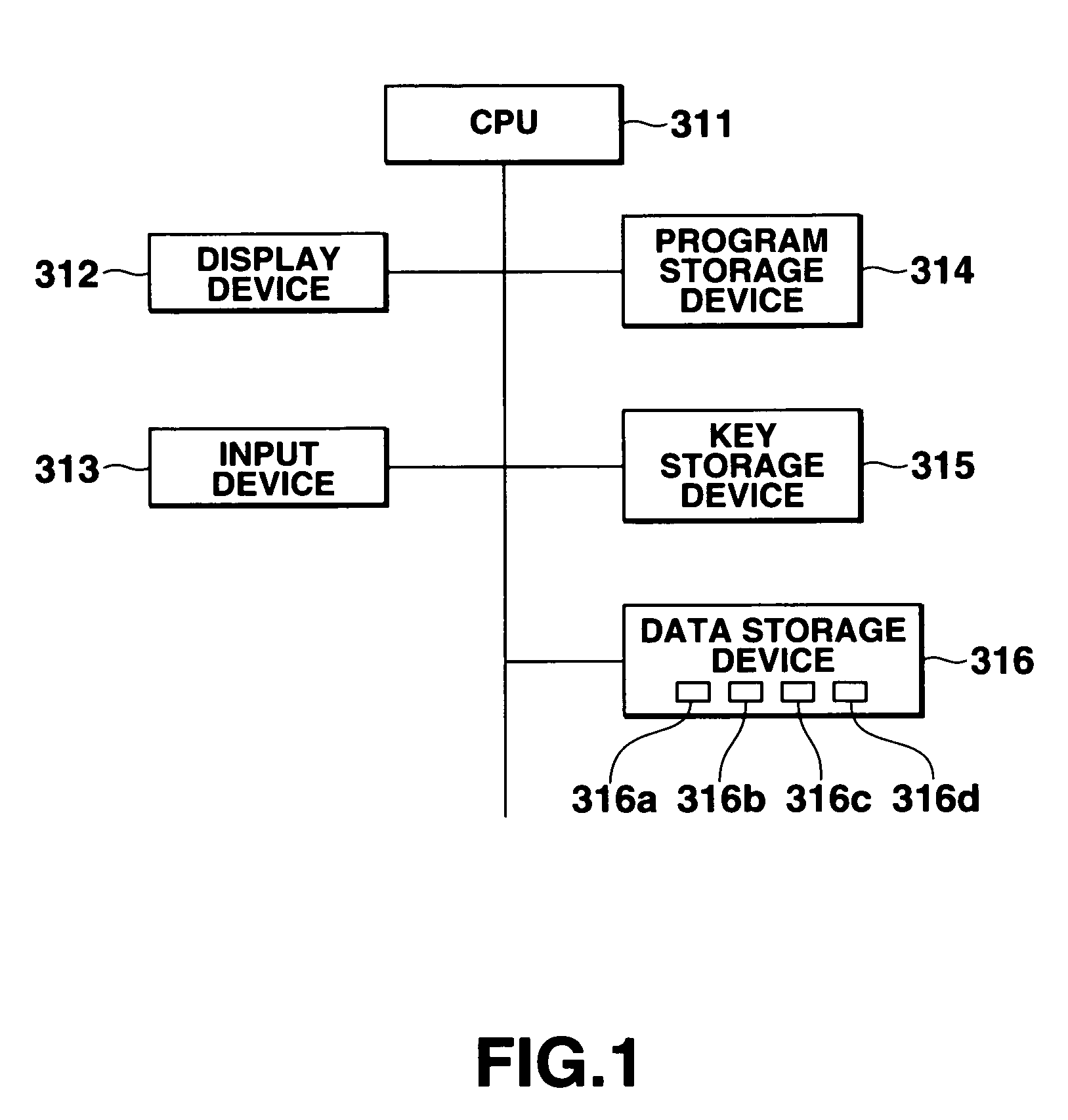
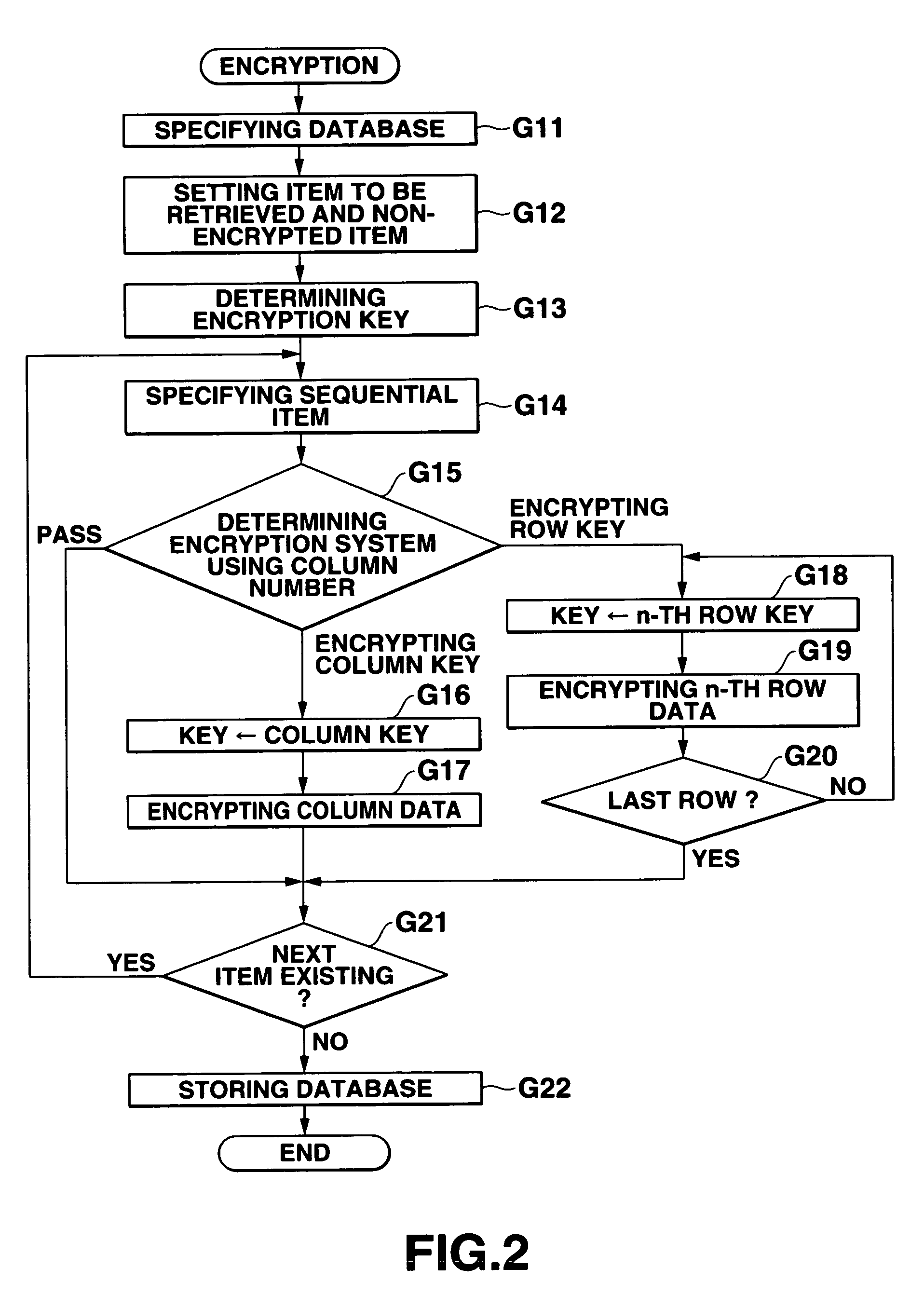
Database management apparatus and encrypting/decrypting system
InactiveUS7093137B1Easy to addEasy to changeData processing applicationsUnauthorized memory use protectionPlaintextTheoretical computer science
In a database, a frequently retrieved column is encrypted using a common key, and other columns are encrypted using a specific row key. Thus, a retrieving process can be performed at a high speed, and the security can be improved. Then, the row and column of the database are encrypted by assuming the plaintext to be encrypted as a bit string, and performing a binary operation with a random bit string. A random bit string is obtained by sequentially generating multidimensional vectors using a nonlinear function by defining a predetermined bit length as 1 word and a plurality of words as components of the multidimensional vector.
Owner:CASIO COMPUTER CO LTD
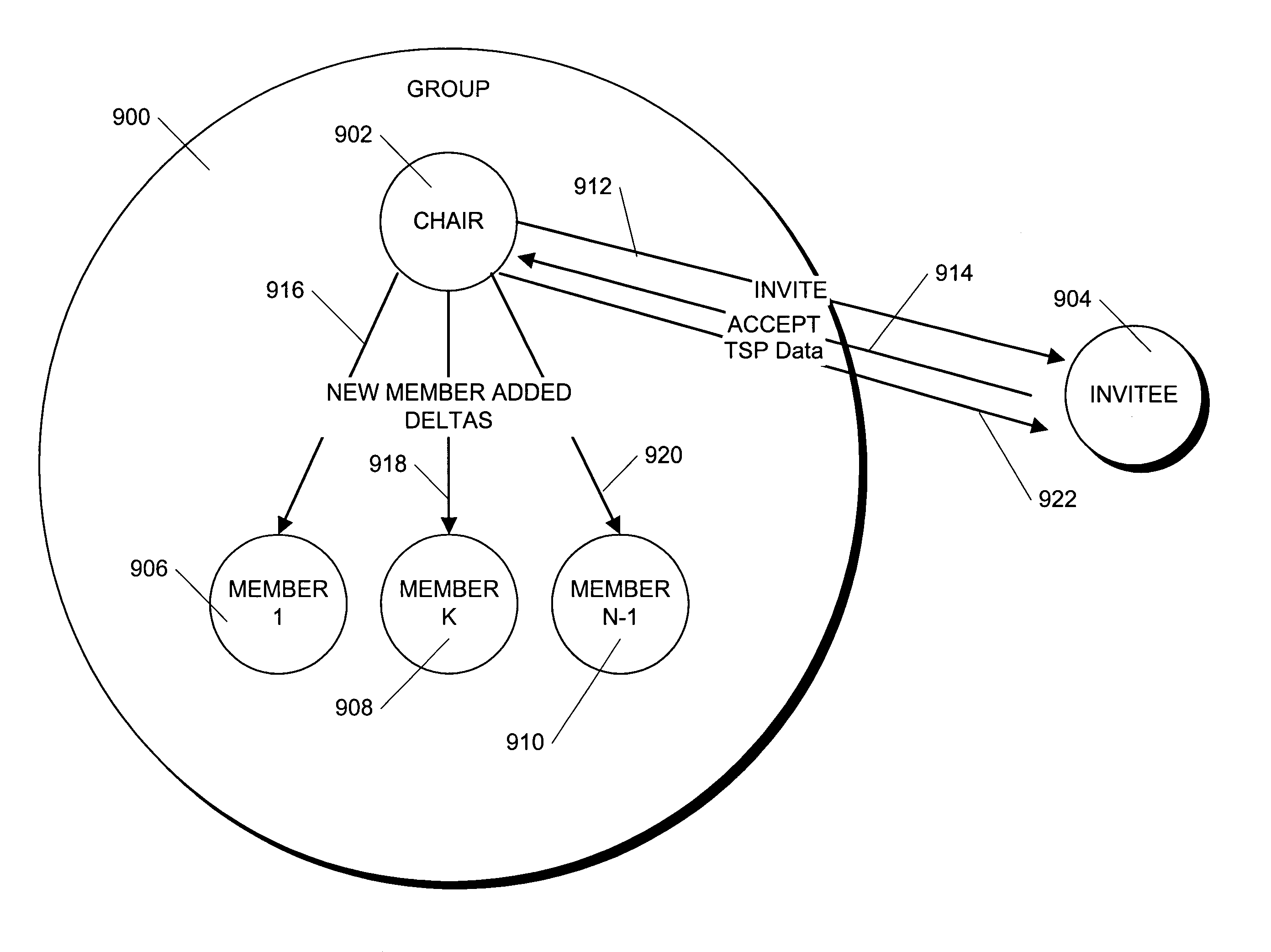
Method and apparatus for managing secure collaborative transactions
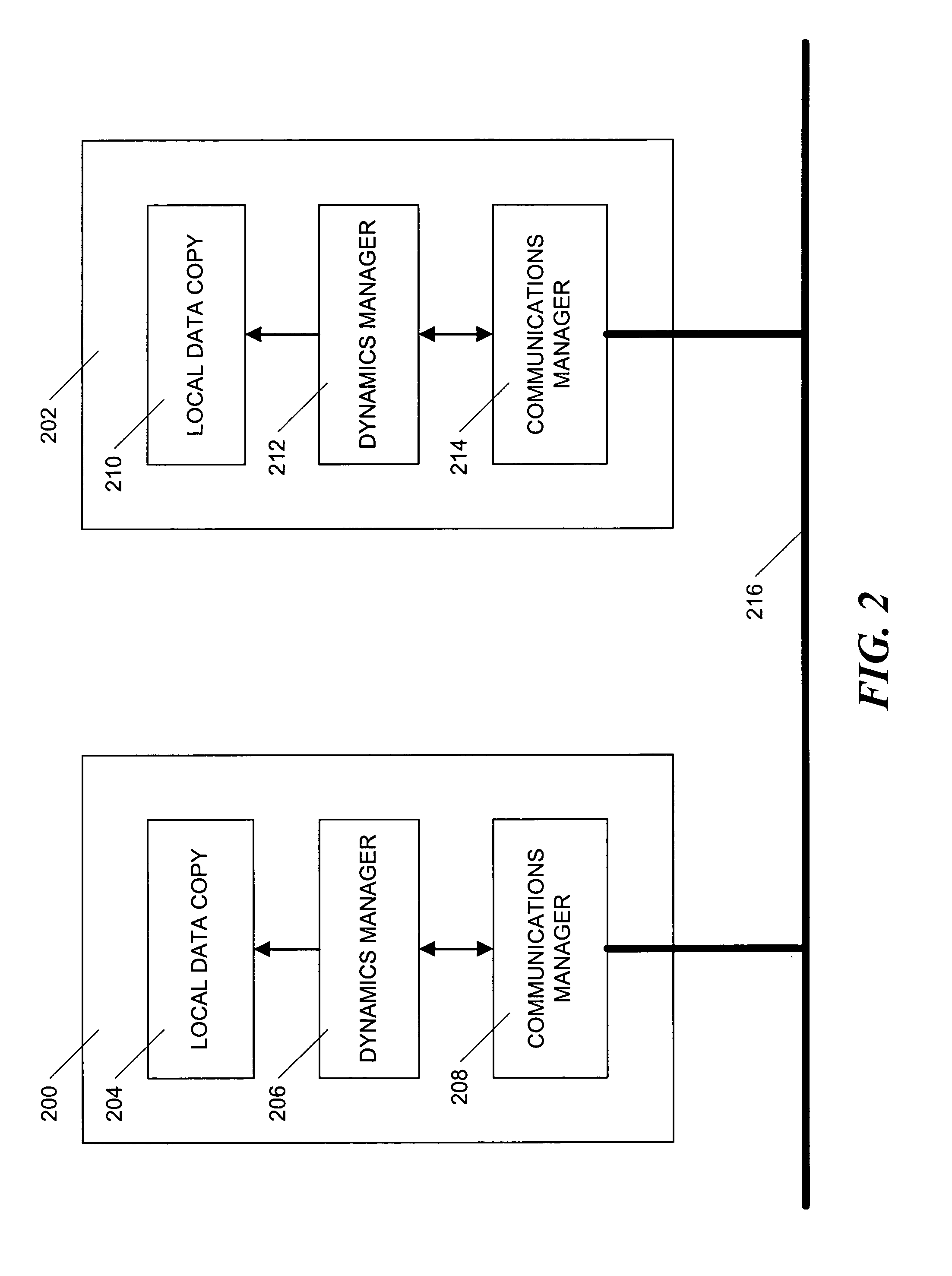
InactiveUS6986046B1Reduce key management overheadReduce administrative overheadKey distribution for secure communicationUser identity/authority verificationPlaintextSecurity level
Different levels of security are provided in a security system so that users can decide the security level of their own communications. Users can choose a low level of security and maintain the security overhead as low as possible. Alternatively, they can choose higher levels of security with attendant increases in security overhead. The different levels of security are created by the use of one or more of two keys: an encryption key is used to encrypt plaintext data in a delta and a message authentication key is used to authenticate and insure integrity of the data. Two keys are used to avoid re-encrypting the encrypted data for each member of the telespace. In one embodiment, the security level is determined when a telespace is created and remains fixed through out the life of the telespace. For a telespace, the security level may range from no security at all to security between the members of the telespace and outsiders to security between pairs of members of the telespace. In another embodiment, subgroups called “tribes” can be formed within a telespace and each tribe adopts the security level of the telespace in which it resides.
Owner:MICROSOFT TECH LICENSING LLC
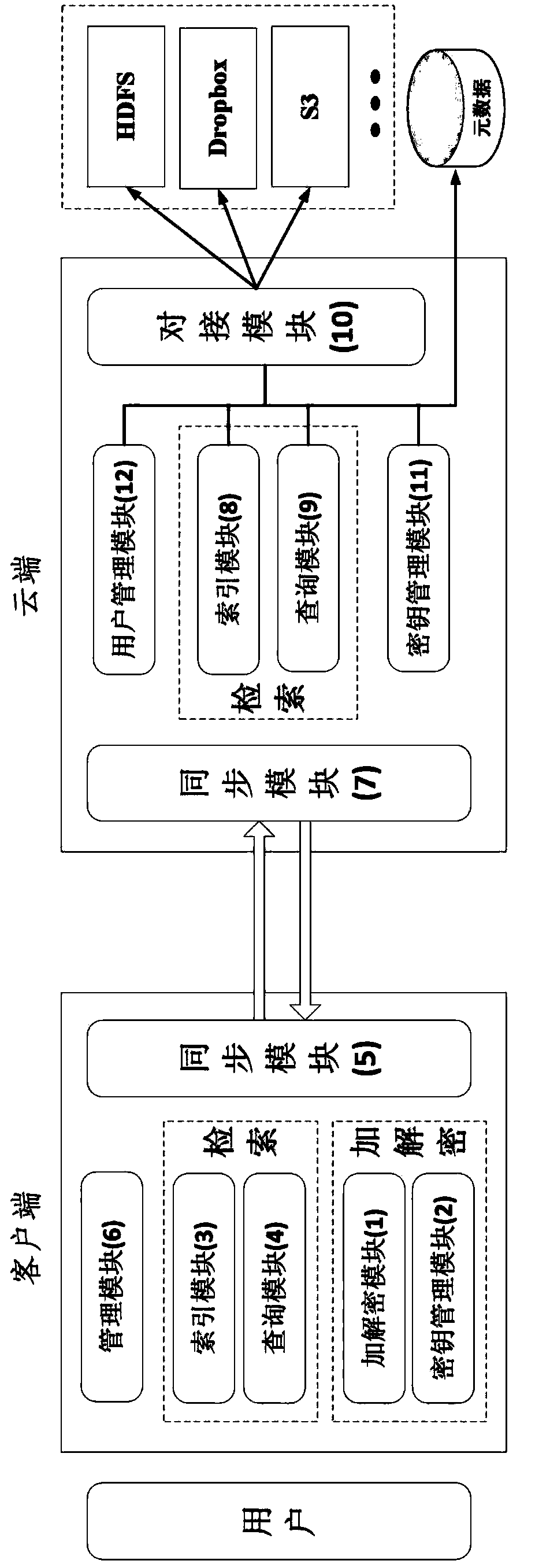
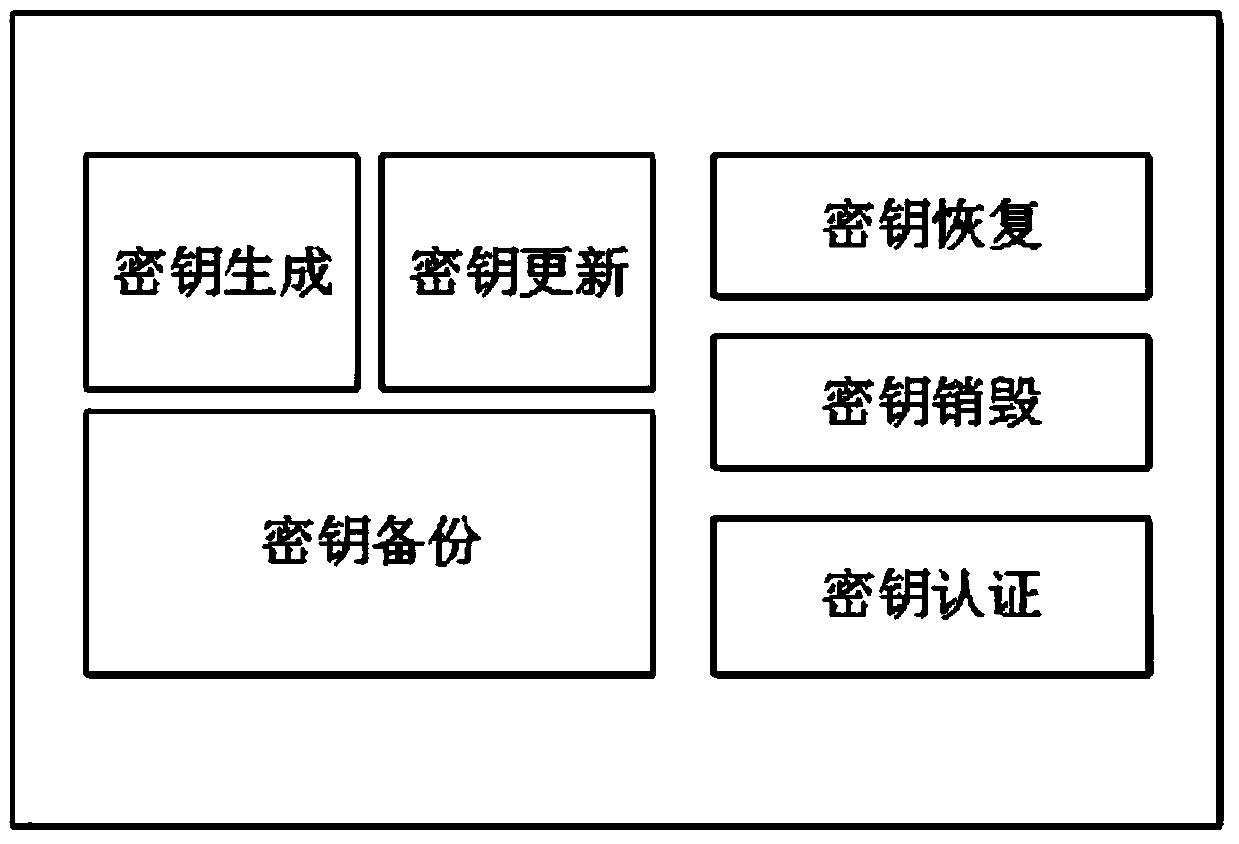
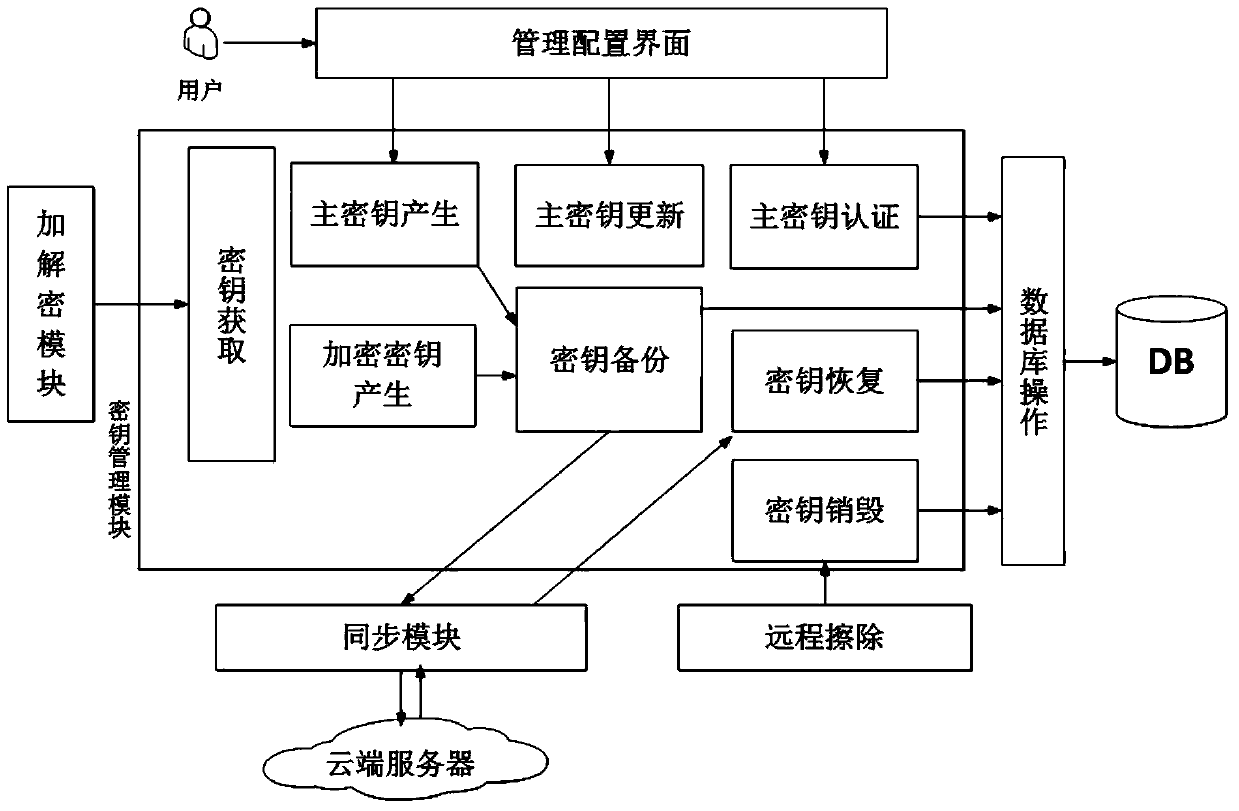
Ciphertext cloud storage method and system
InactiveCN103595730AWon't leakDoes not affect survivalTransmissionComputer hardwareData synchronization
The invention relates to a ciphertext cloud storage method and system. In the ciphertext cloud storage method system composed of at least one client terminal and a cloud terminal server, the ciphertext cloud storage method comprises the steps that (1) a user adopts a ciphertext and / or a plaintext to conduct data synchronism on the client terminal in the process of data storage and selects an encryption algorithm for the ciphertext; (2) authentication parameters provided based on the identity of the user is used for generating a master key, synchronous data of the ciphertext are encrypted on the client terminal through two-level keys comprising the master key and an encryption and decryption key, and the master key is backed up; (3) the ciphertext and a ciphertext index are synchronized on the client terminal and a cloud terminal, or a plaintext index is established after synchronous data of the plaintext are synchronized on the cloud terminal and the client terminal; (4) the plaintext and / or ciphertext is / are stored in a local private cloud storage server or in a storage server of a cloud storage provider according to a mount point requested by the user. By the adoption of the ciphertext cloud storage method and system, the data cannot be lost when the terminal is lost, if protection is inappropriate, only the ciphertext form of a file is damaged, and the ciphertext cloud storage system can dock with multiple cloud server providers.
Owner:INST OF INFORMATION ENG CHINESE ACAD OF SCI
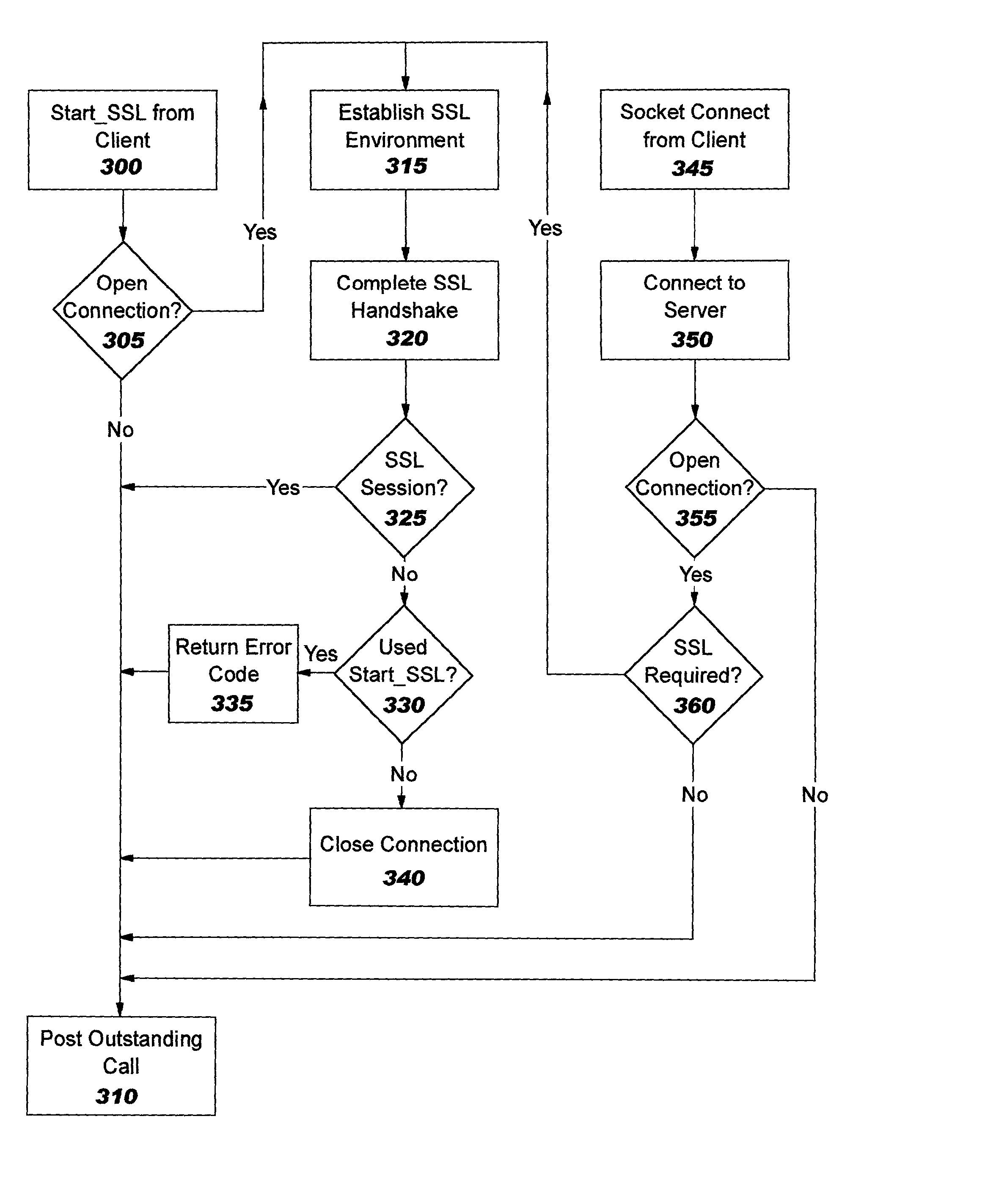
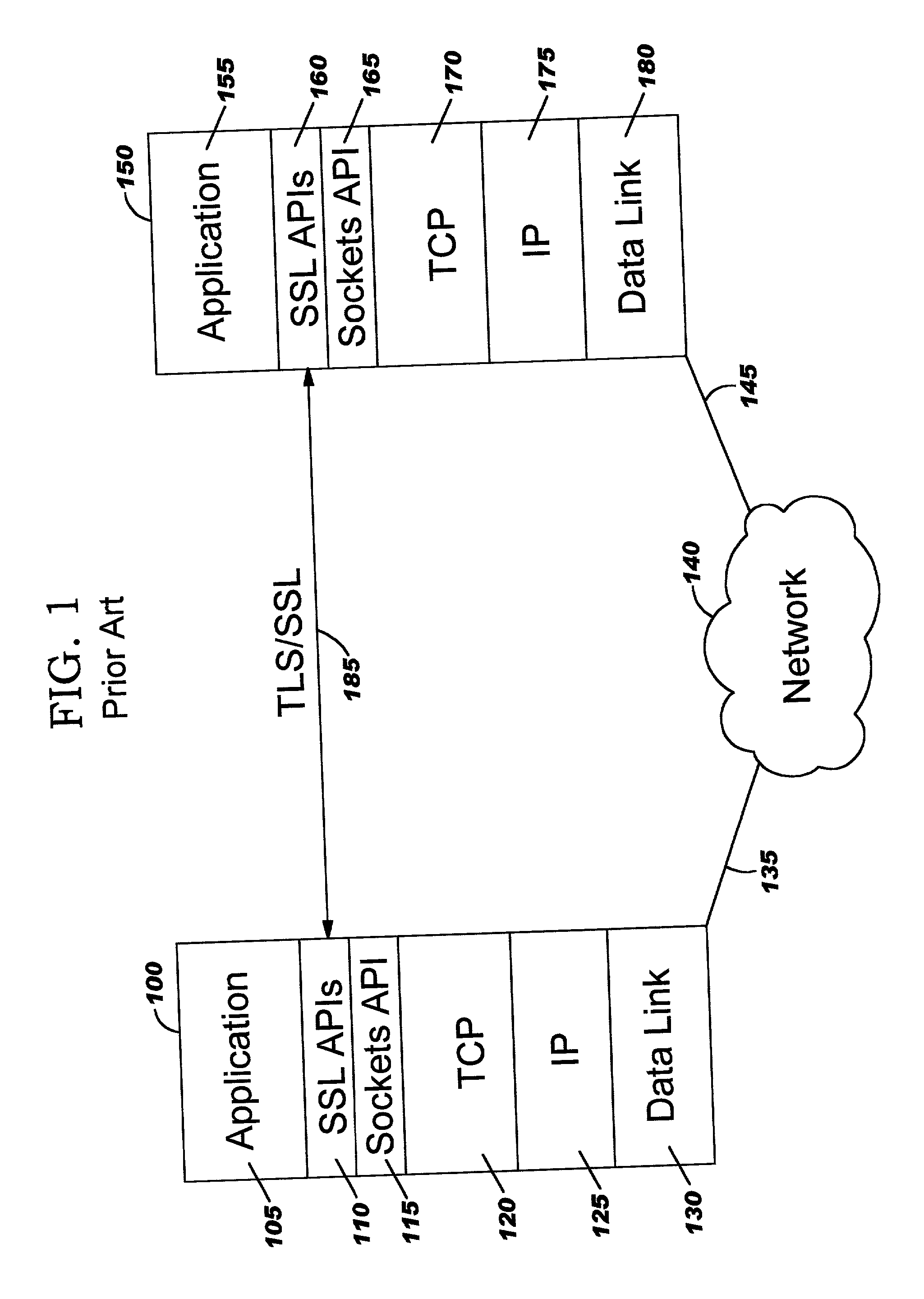
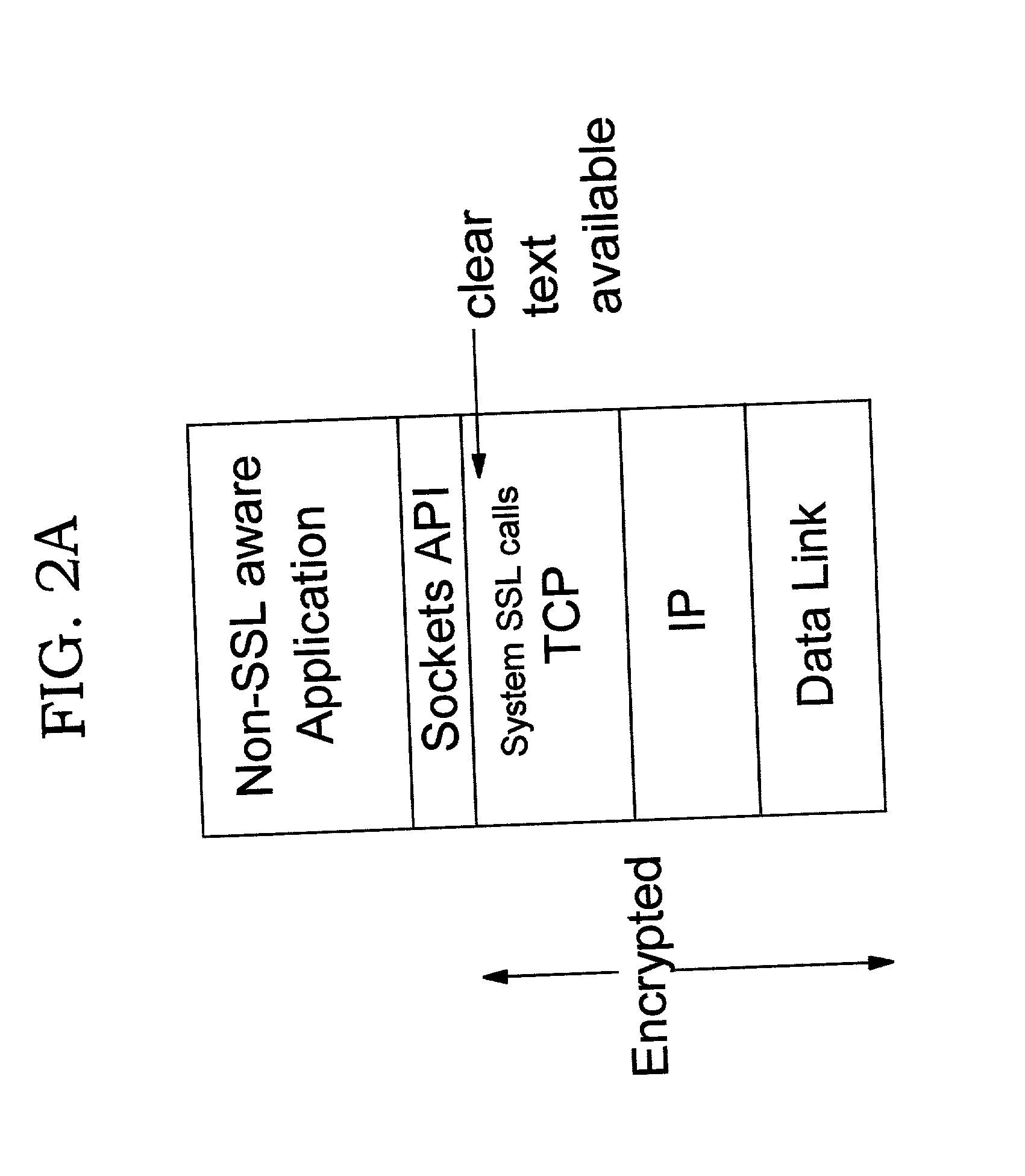
Offload processing for secure data transfer
InactiveUS20030105977A1Safe handlingMultiple digital computer combinationsProgram controlPlaintextSafe handling
Improvements in security processing are disclosed which enable security processing to be transparent to the application. Security processing (such as Secure Sockets Layer, or "SSL", or Transport Layer Security, or "TLS") is performed in (or controlled by) the stack. A decision to enable security processing on a connection can be based on configuration data or security policy, and can also be controlled using explicit enablement directives. Directives may also be provided for allowing applications to communicate with the security processing in the stack for other purposes. Functions within the protocol stack that need access to clear text can now be supported without loss of security processing capability. No modifications to application code, or in some cases only minor modifications (such as inclusion of code to invoke directives), are required to provide this security processing. Improved offloading of security processing is also disclosed, which provides processing efficiencies over prior art offloading techniques.
Owner:IBM CORP
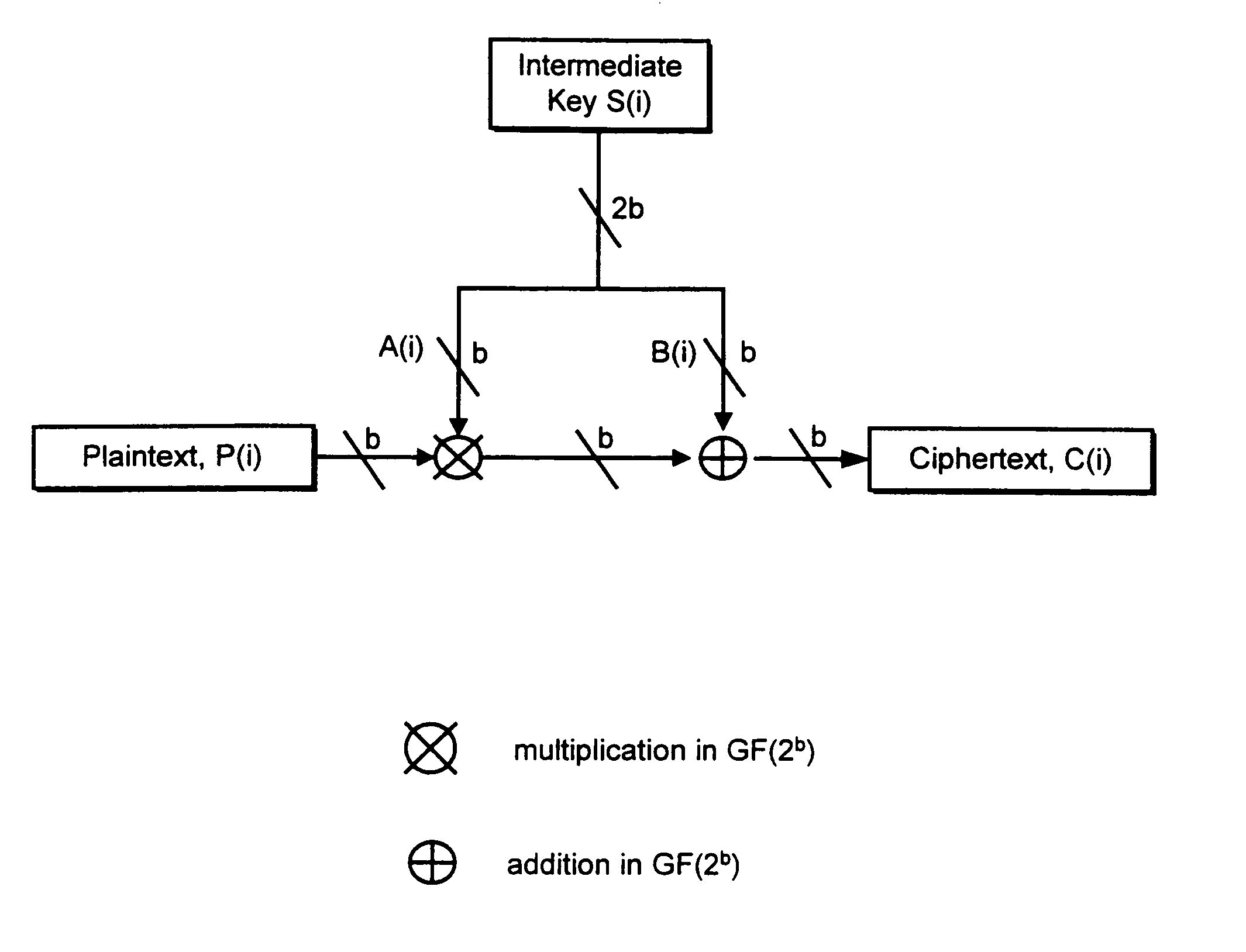
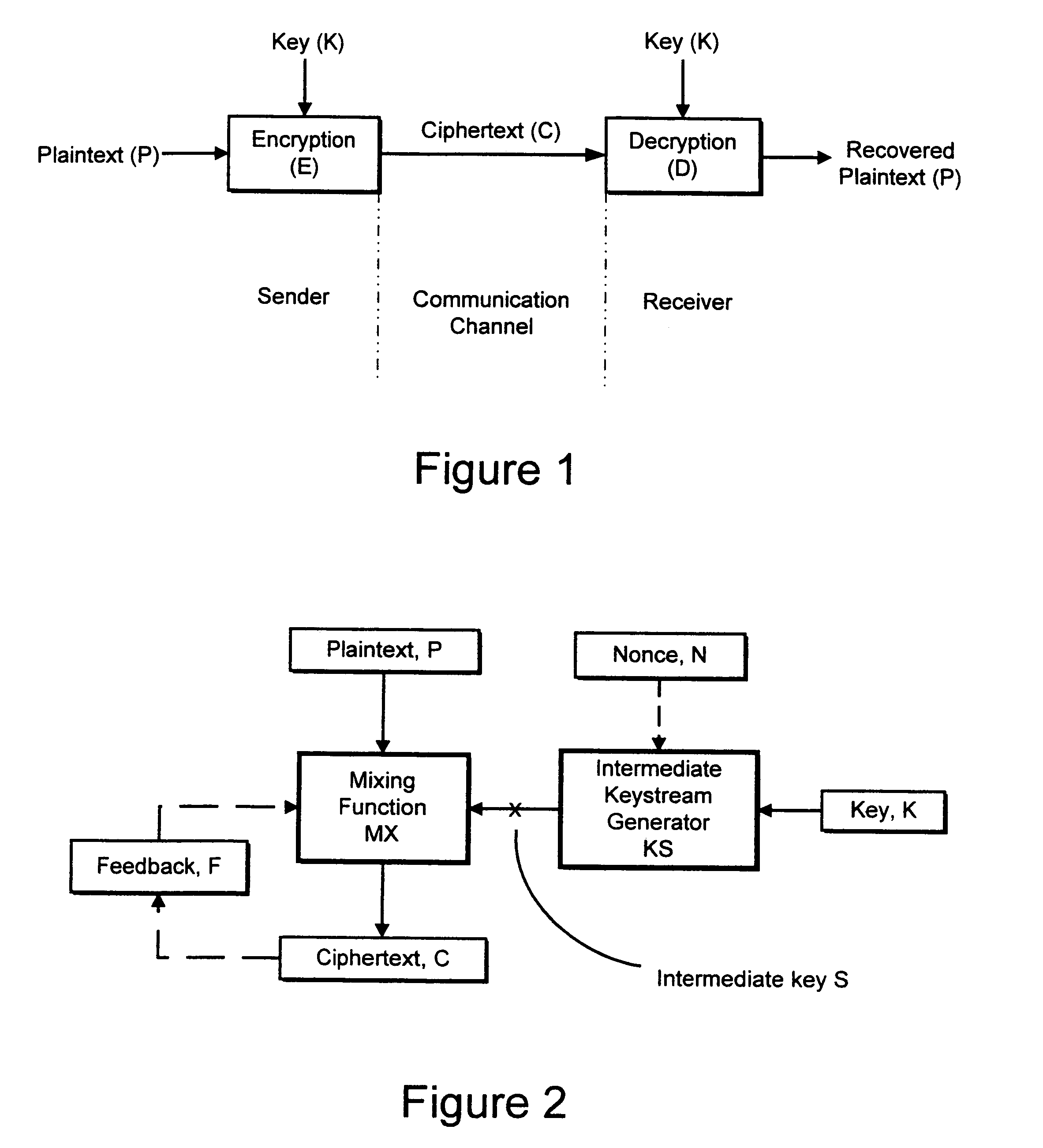
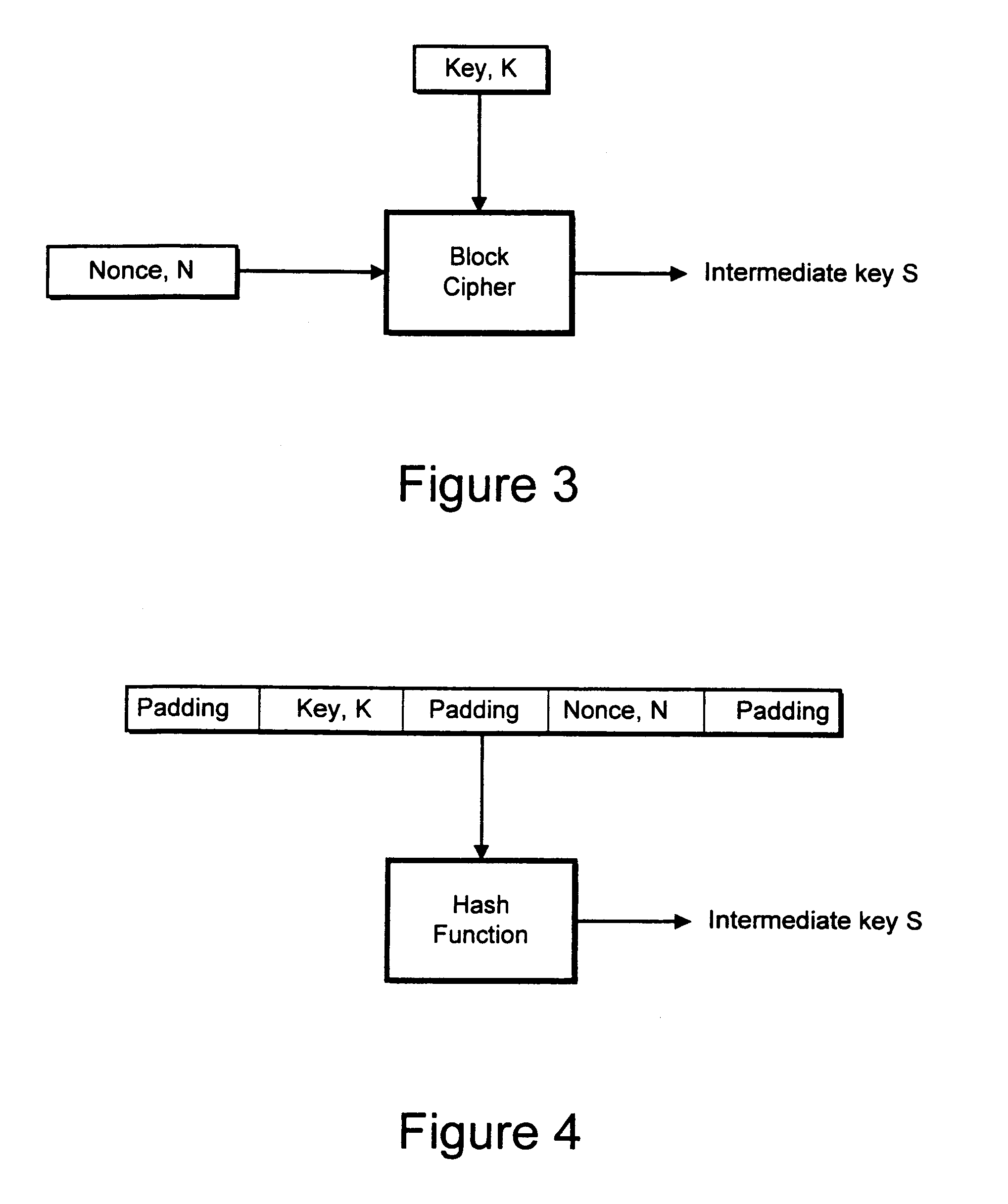
Cryptographic apparatus and method
InactiveUS7177424B1Quick implementationEasy to operateEncryption apparatus with shift registers/memoriesUnauthorized memory use protectionPlaintextComputer hardware
An encryption system comprises a pseudo-random number generator (KS) for generating a long pseudo-random sequence (S) from a shorter encryption key (K) and, if necessary, a nonce value (N), and a mixing function (MX) for combining the sequence with a plaintext message (P) on a block-by-block basis, where successive blocks (S(i)) of 128 bits of the sequence are combined with successive 64-bit blocks of plaintext (P(i)) to produce successive 64-bit blocks of ciphertext. The blockwise use of a long pseudo-random sequence preserves the advantages of a block cipher in terms of data confidentiality and data integrity, as well as benefiting from the speed advantages of a stream cipher.
Owner:HITACHI LTD
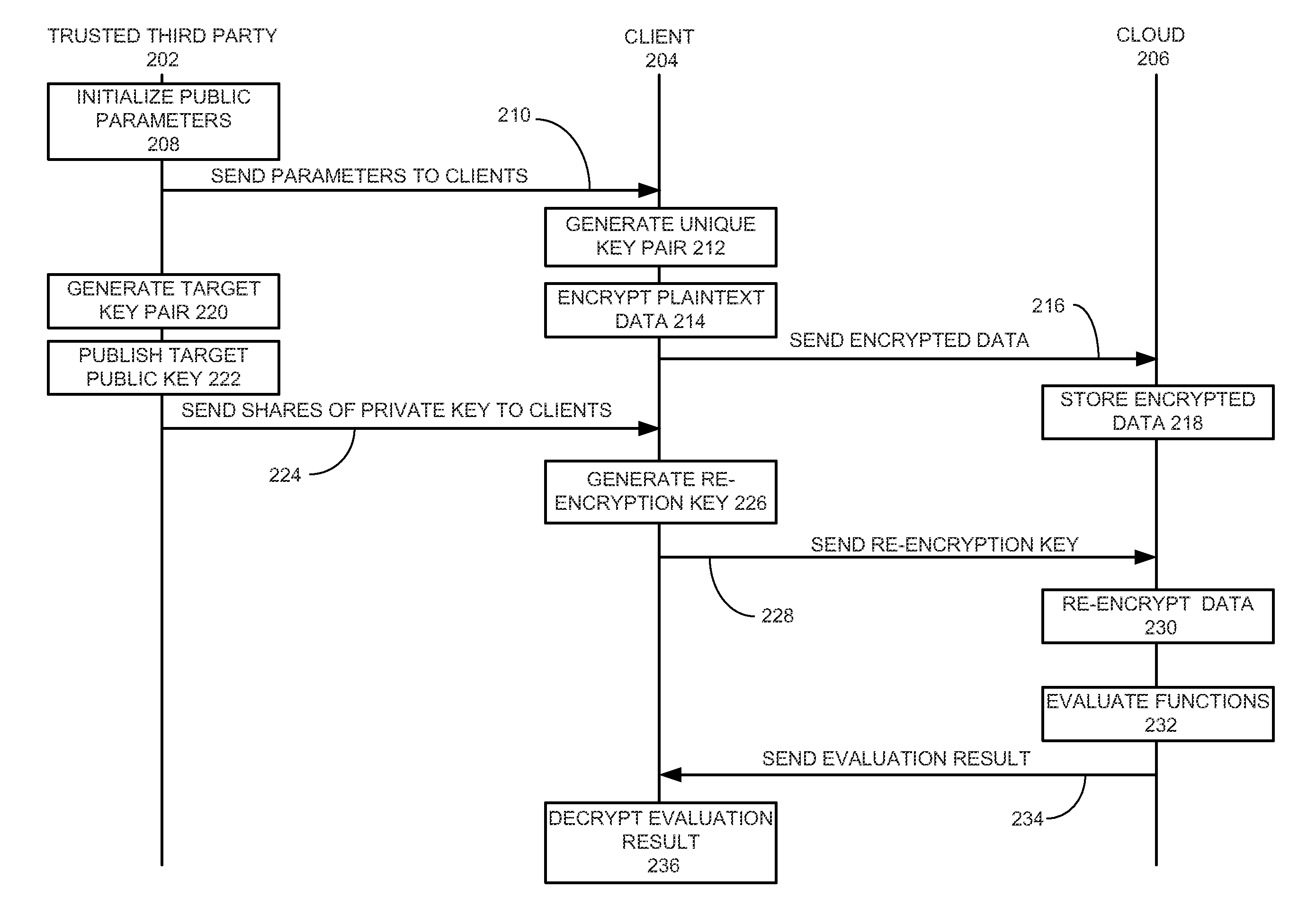
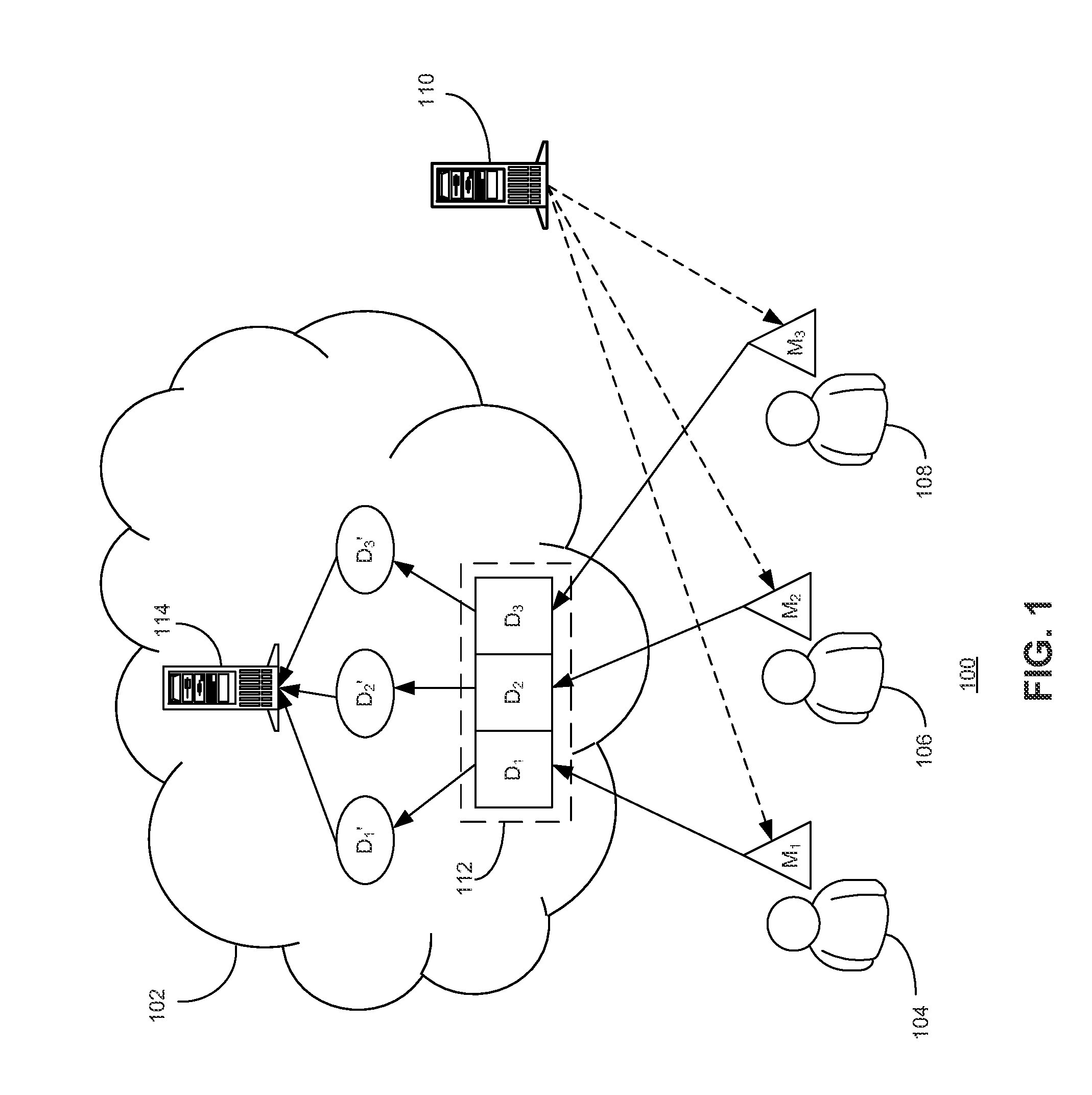
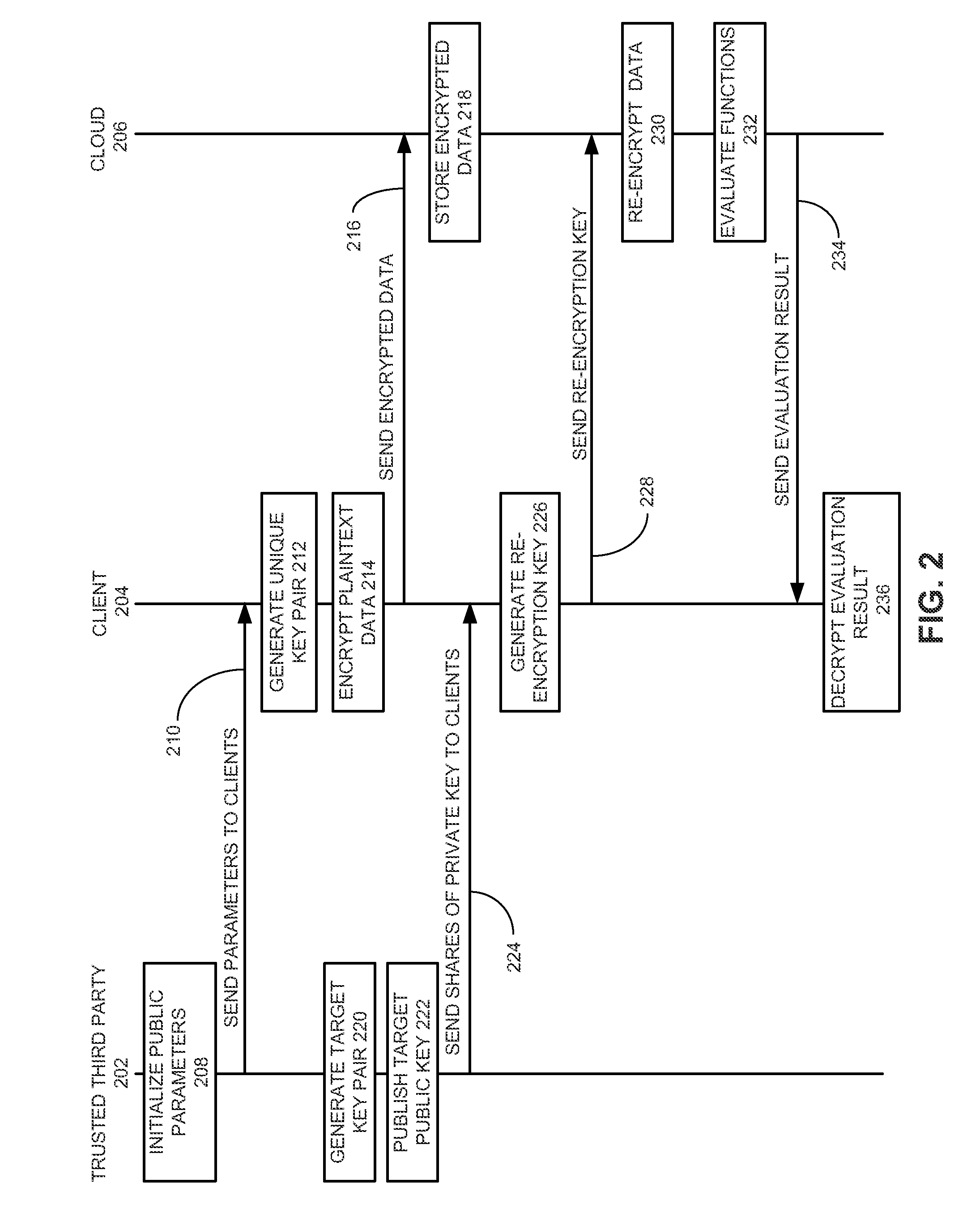
Method and system for secure multiparty cloud computation
One embodiment of the present invention provides a system for performing secure multiparty cloud computation. During operation, the system receives multiple encrypted datasets from multiple clients. An encrypted dataset associated with a client is encrypted from a corresponding plaintext dataset using a unique, client-specific encryption key. The system re-encrypts the multiple encrypted datasets to a target format, evaluates a function based on the re-encrypted multiple datasets to produce an evaluation outcome, and sends the evaluation outcome to the multiple clients, which are configured to cooperatively decrypt the evaluation outcome to obtain a plaintext evaluation outcome.
Owner:FUTUREWEI TECH INC
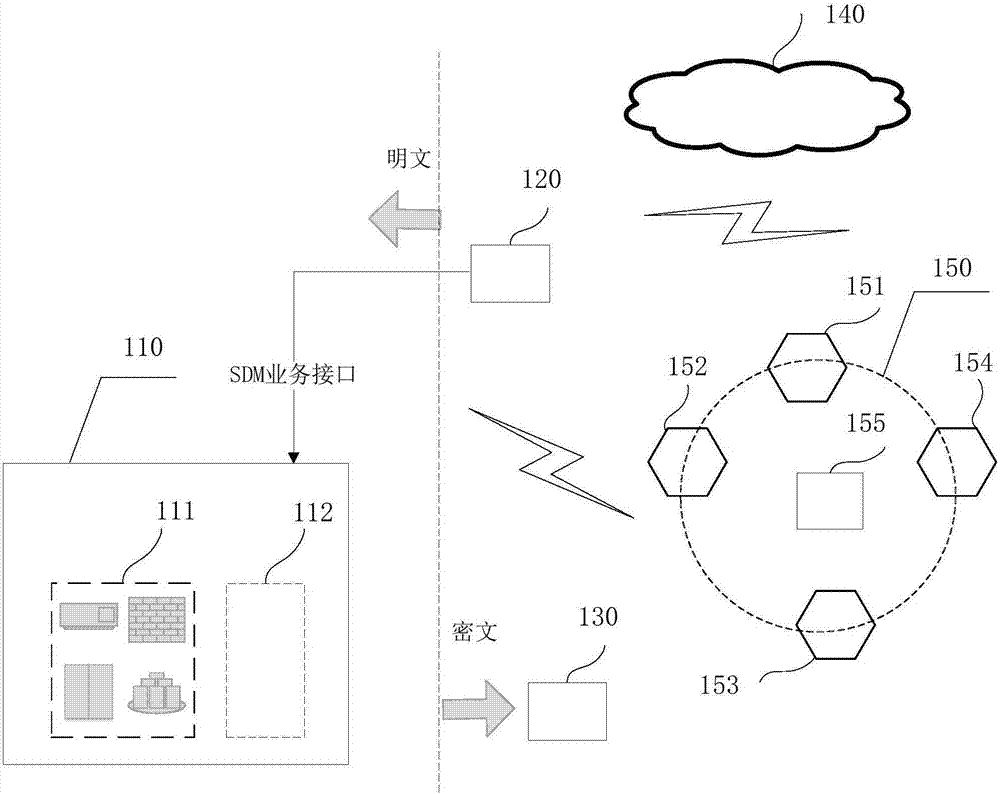
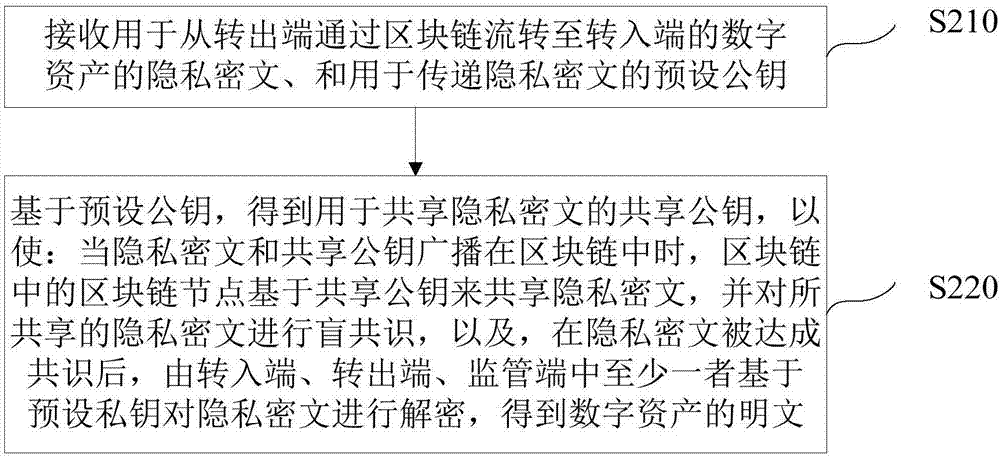
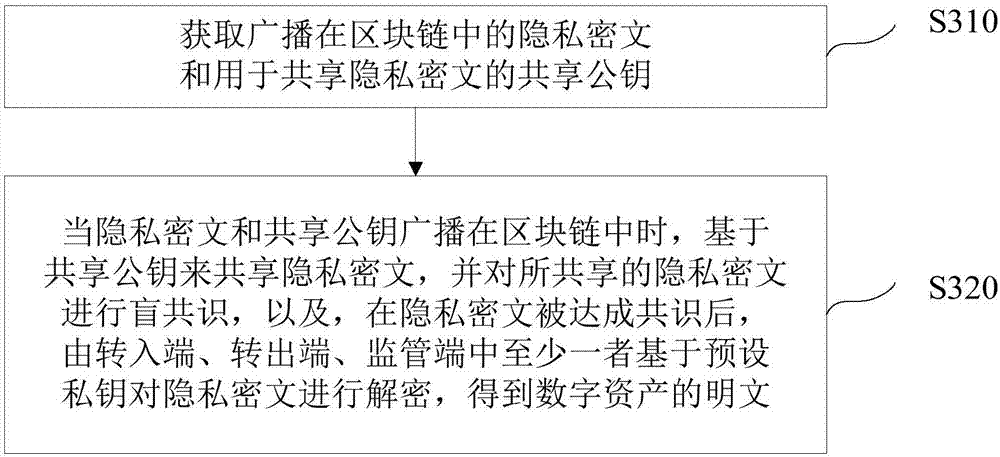
Blockchain-based digital asset processing method and device
ActiveCN106982205AProtection of privacySmooth circulationKey distribution for secure communicationDigital data protectionPlaintextCiphertext
The invention discloses a blockchain-based digital asset processing method and device. The method comprises the following steps: receiving private ciphertext for a digital asset circulated from a sending end to a receiving end through a blockchain, and a preset public key; and obtaining a sharing public key for sharing the private ciphertext based on the preset public key, so that when the private ciphertext and the sharing public key are broadcast in the blockchain, blockchain nodes on the blockchain can share the private ciphertext based on the sharing public key and reach a blind consensus on the shared private ciphertext, and after the consensus on the private ciphertext is reached, the private ciphertext can be decrypted by at least one of three parties, i.e., the sending end, the receiving end and a monitoring end, based on a preset private key to obtain plaintext of the digital asset. The method and device provided by the embodiment of the invention has the advantages that the privacy right of a user is protected; under the premise of privacy protection, the single general digital asset can be smoothly circulated within one blockchain or among multiple blockchains, and a total currency amount remains unchanged; and a monitoring party other than the transaction parties can monitor transaction information at any time.
Owner:中钞信用卡产业发展有限公司杭州区块链技术研究院 +1
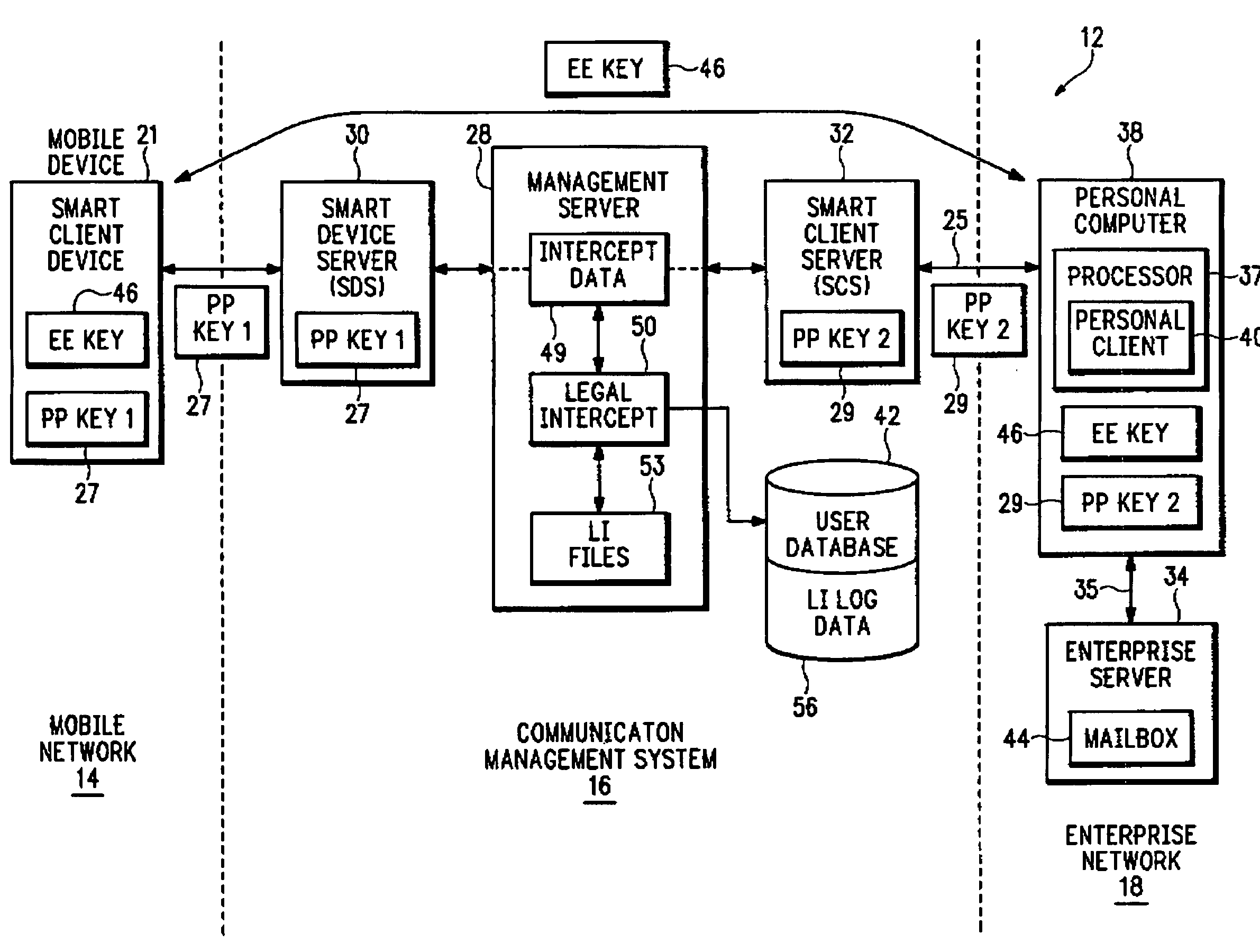
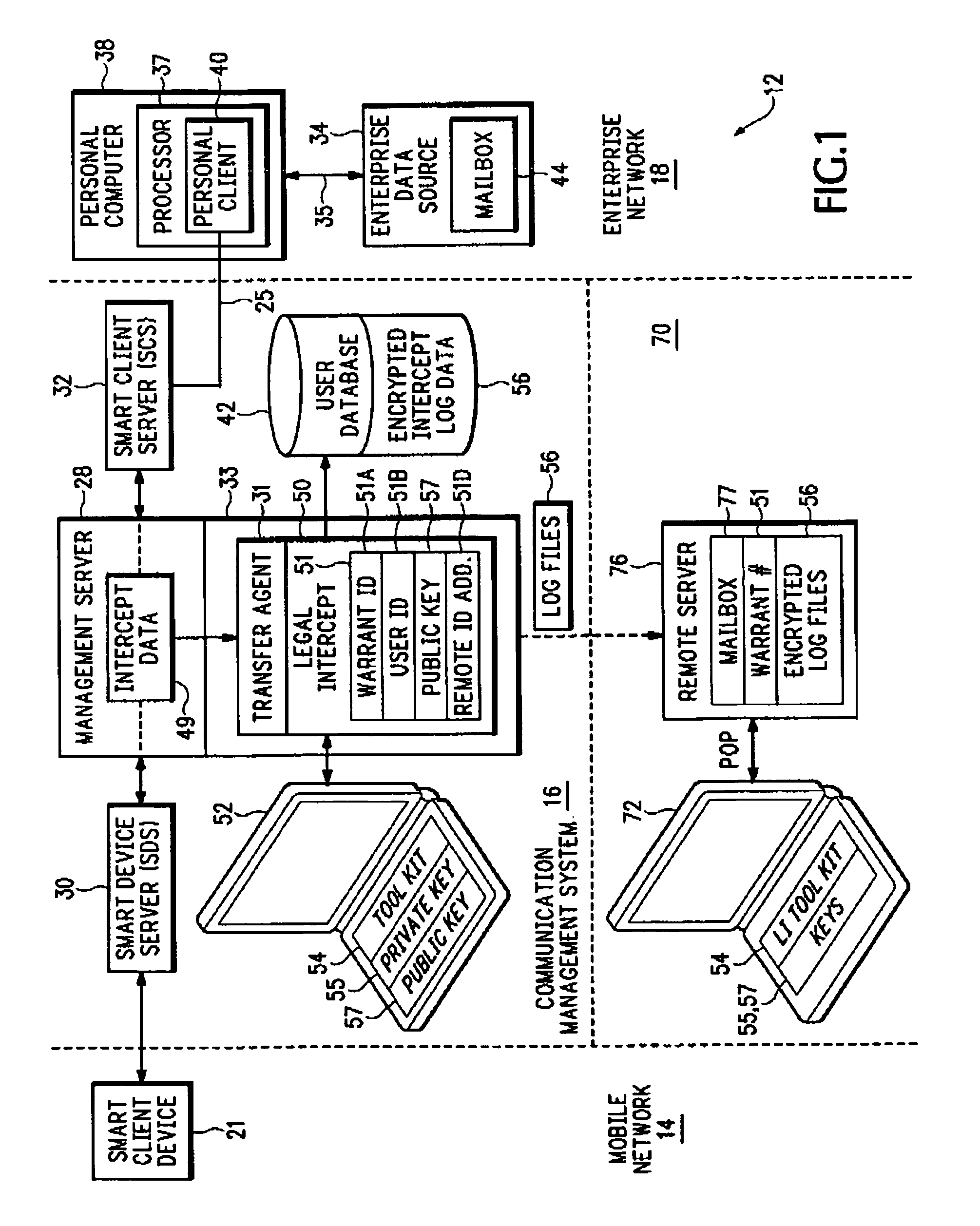
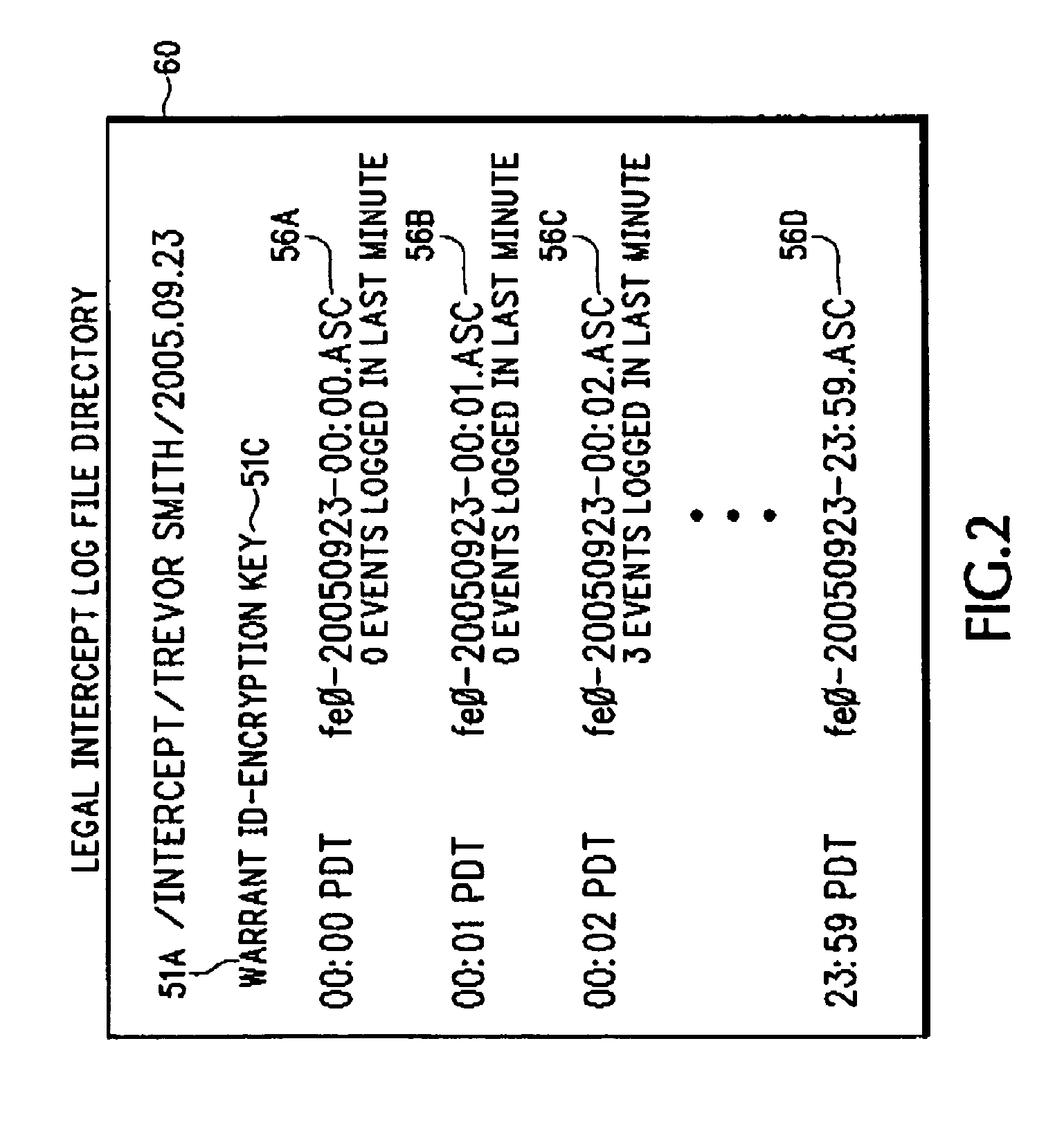
Method and apparatus for intercepting events in a communication system
InactiveUS7441271B2Effective and efficient complianceMemory loss protectionError detection/correctionPlaintextCommunications system
An intercept system provides more effective and more efficient compliance with legal intercept warrants. The intercept system can provide any combination of operations that include near-real-time intercept, capture of intercepted data in structured authenticated form, clear text intercept for communications where there is access to encryption keys, cipher text intercept for communications where there is no access to encryption keys, provision of transactional logs to the authorized agency, interception without altering the operation of the target services, and encryption of stored intercepted information.
Owner:SEVEN NETWORKS INC
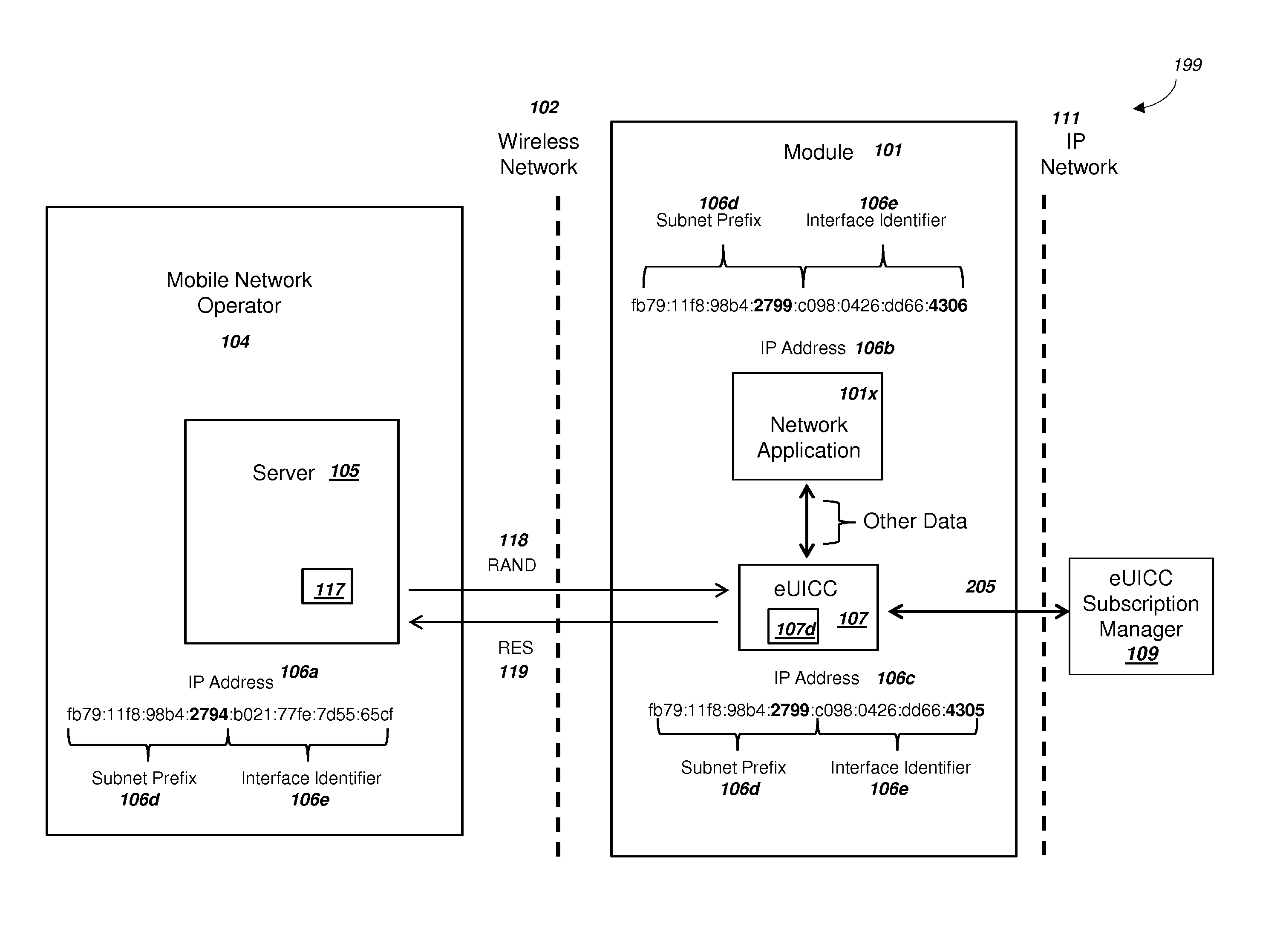
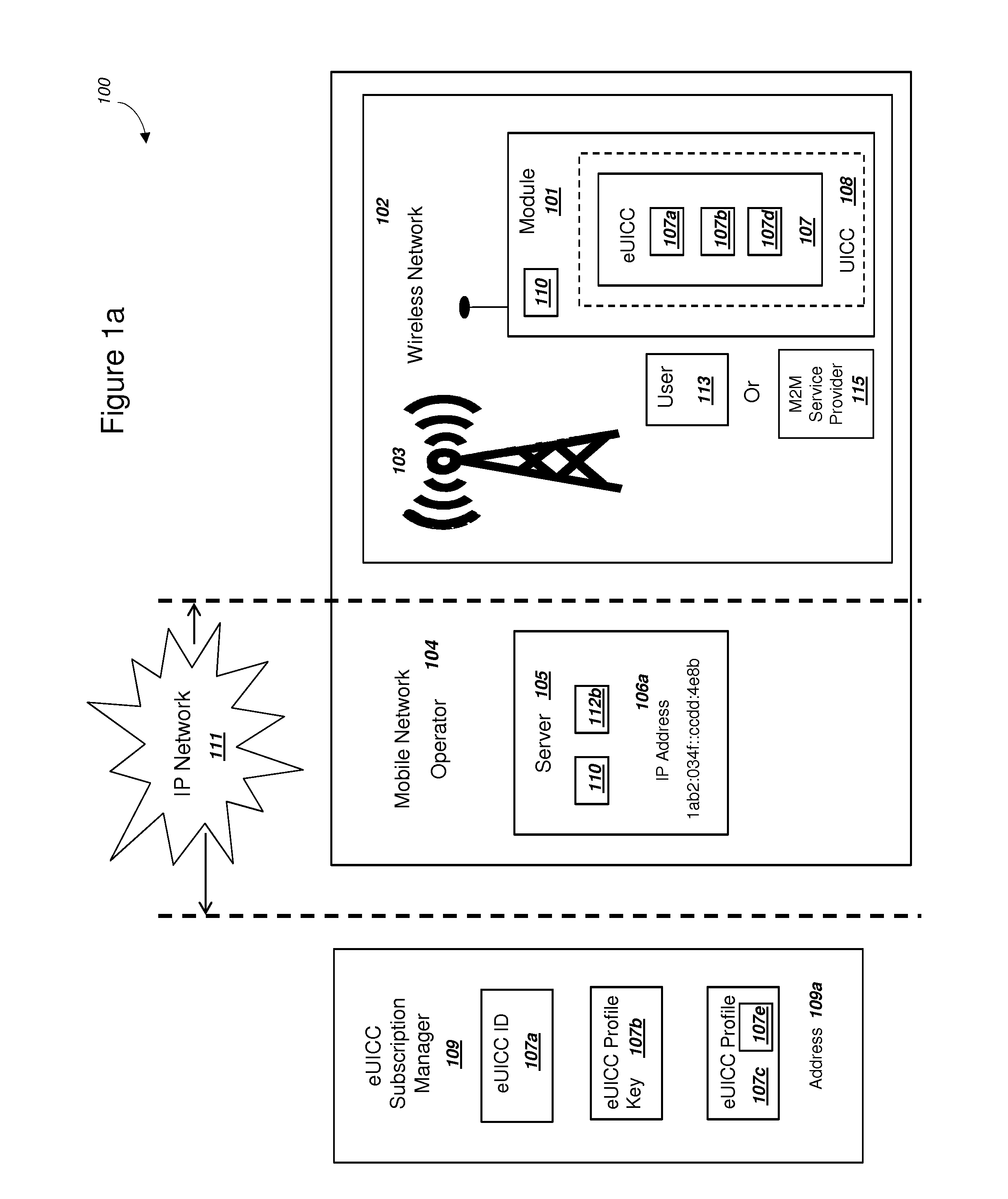
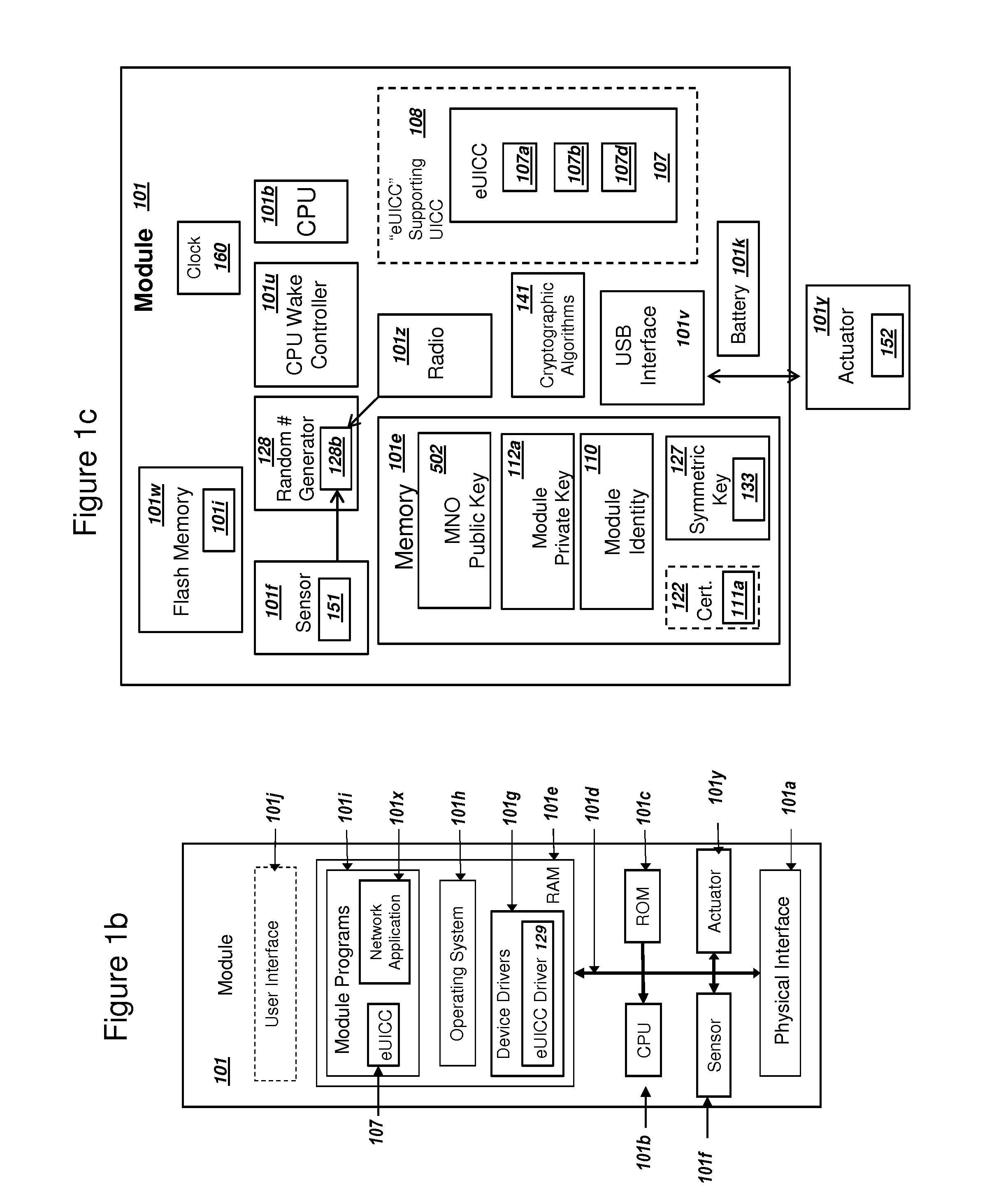
Embedded Universal Integrated Circuit Card Supporting Two-Factor Authentication
ActiveUS20150163056A1Increase flexibilityLow costKey distribution for secure communicationSecurity arrangementPlaintextComputer hardware
A module with an embedded universal integrated circuit card (eUICC) can include a profile for the eUICC. The profile can include a first and second shared secret key K for authenticating with a wireless network. The first shared secret key K can be encrypted with a first key, and the second shared secret key K can be encrypted with a second key. The module can (i) receive the first key, (ii) decrypt the first shared secret key K with the first key, and (iii) subsequently authenticate with the wireless network using the plaintext first shared secret key K. The wireless network can authenticate the user of the module using a second factor. The module can then (i) receive the second key, (ii) decrypt the second shared secret key K, and (iii) authenticate with the wireless network using the second shared secret key K. The module can comprise a mobile phone.
Owner:NIX JOHN A +1
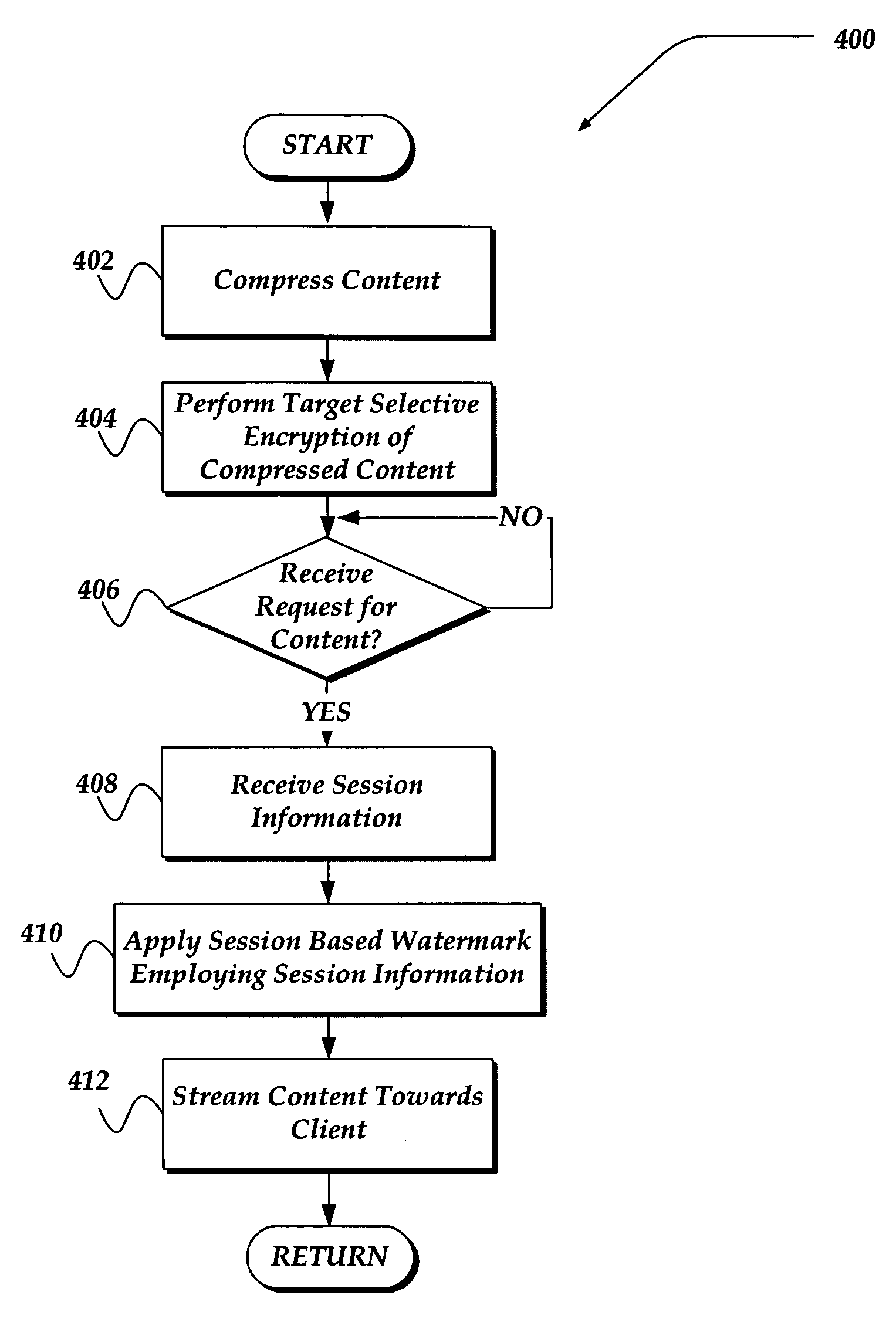
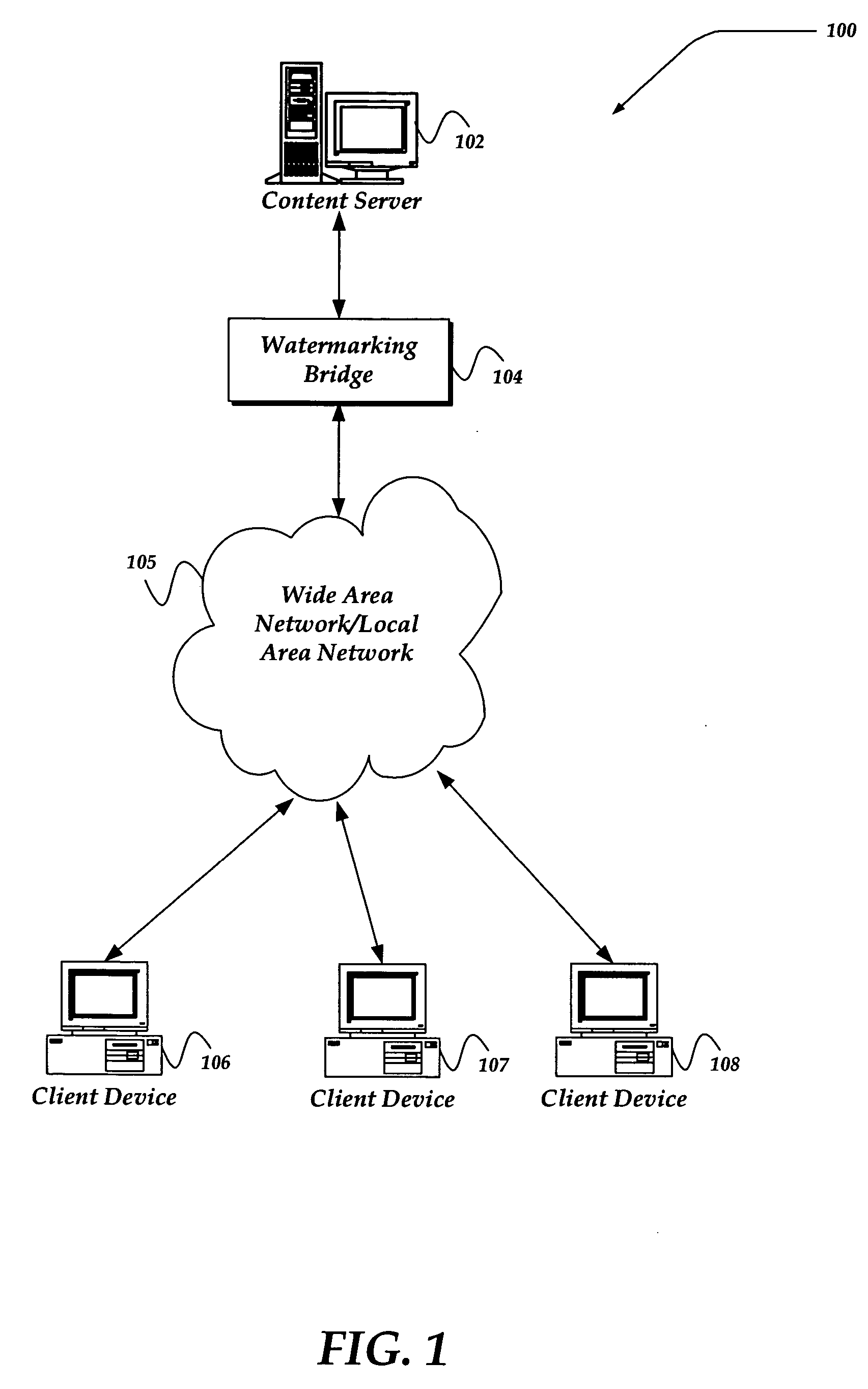
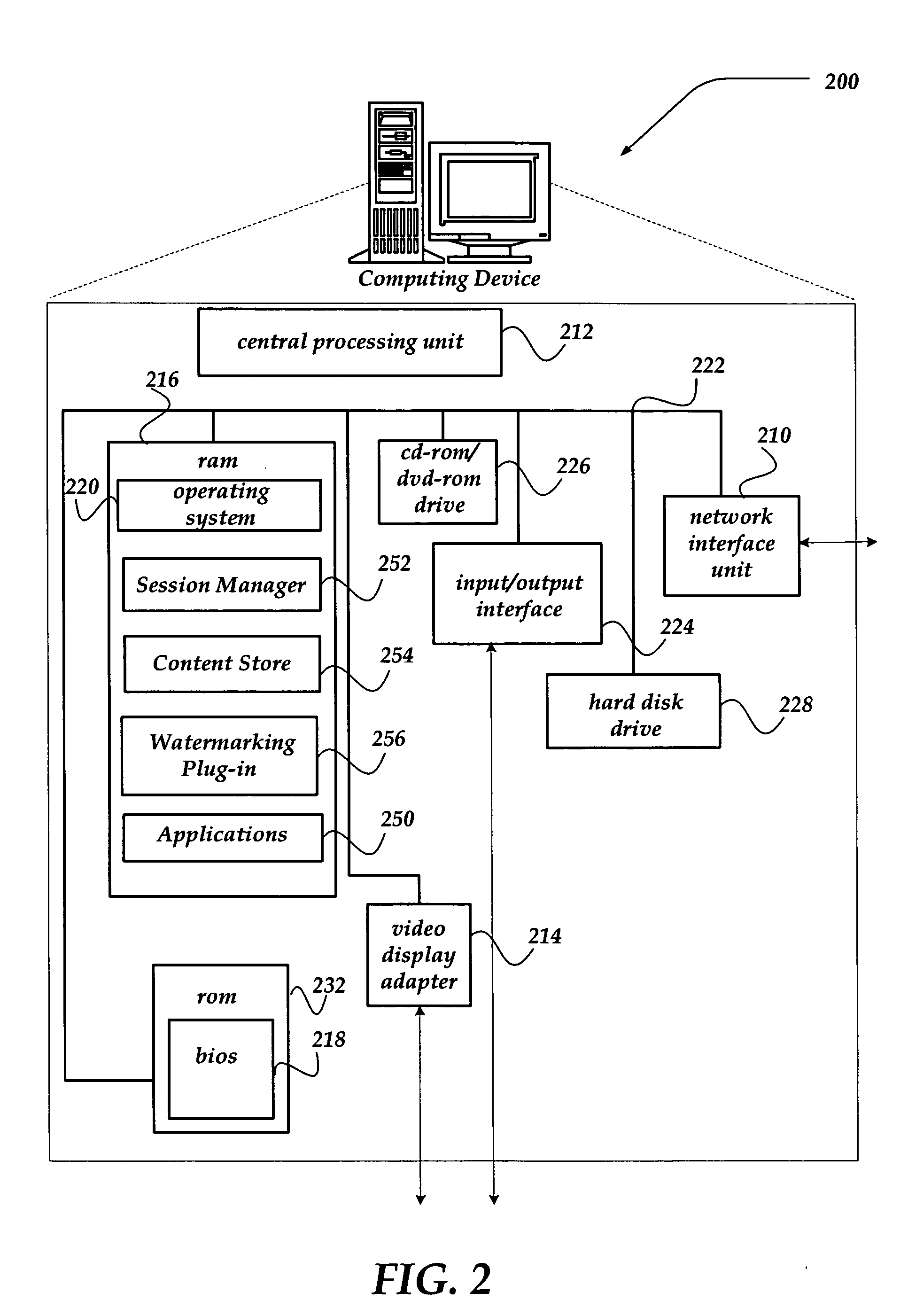
Method and system for session based watermarking of encrypted content
InactiveUS20050193205A1Digital data processing detailsUser identity/authority verificationPlaintextDigital signature
A method and apparatus applies a variety of session based watermarks in real-time to content that is streamed from a server towards a client. The invention employs content where differing targeted portions are selectively encrypted, such that other portions remain in the clear (unencrypted). Session information, such as an intended client, end-user, operator of a content server, content owner, and the like, may be used to generate the various watermarks. The watermarks may also be digitally signed and / or encrypted. The watermarks may be applied to the portions of the clear content as the content is streamed towards the client. In one embodiment, a bridge server is configured to modify packets of streaming media data files with the variety of watermarks. In another embodiment, the content server for the streaming media data includes a plug-in component that dynamically modifies the packets of streaming media data files with the variety of watermarks.
Owner:GOOGLE LLC
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com