Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
2151 results about "Enforcement" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Enforcement is the process of ensuring compliance with laws, regulations, rules, standards, and social norms. Governments attempt to effectuate successful implementation of policies by enforcing laws and regulations. Enactment refers to application of a law or regulation, or carrying out of an executive or judicial order.
System and method for policy management
InactiveUS20070180490A1Computer security arrangementsSpecial data processing applicationsStrategy makingComputer security
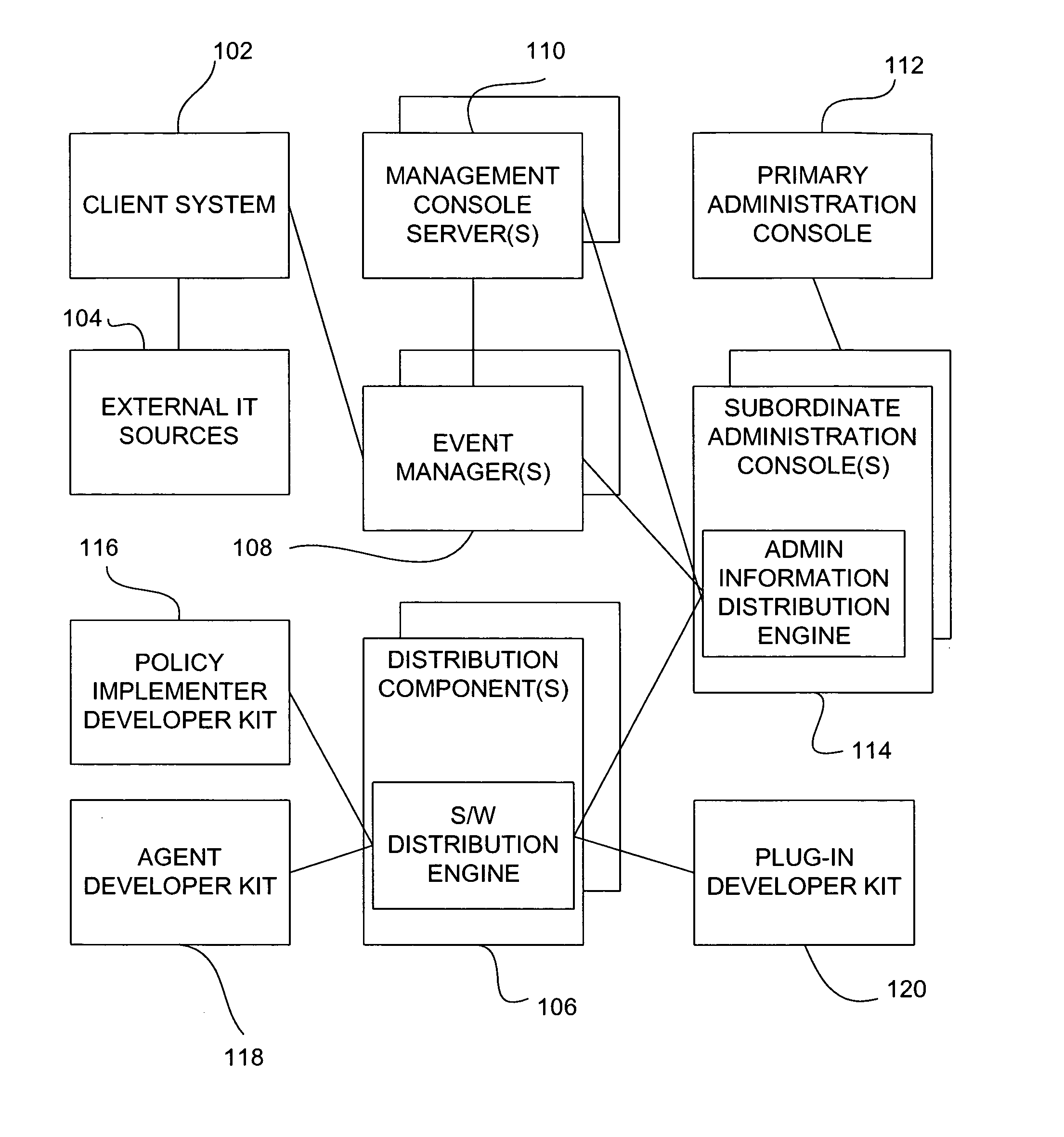
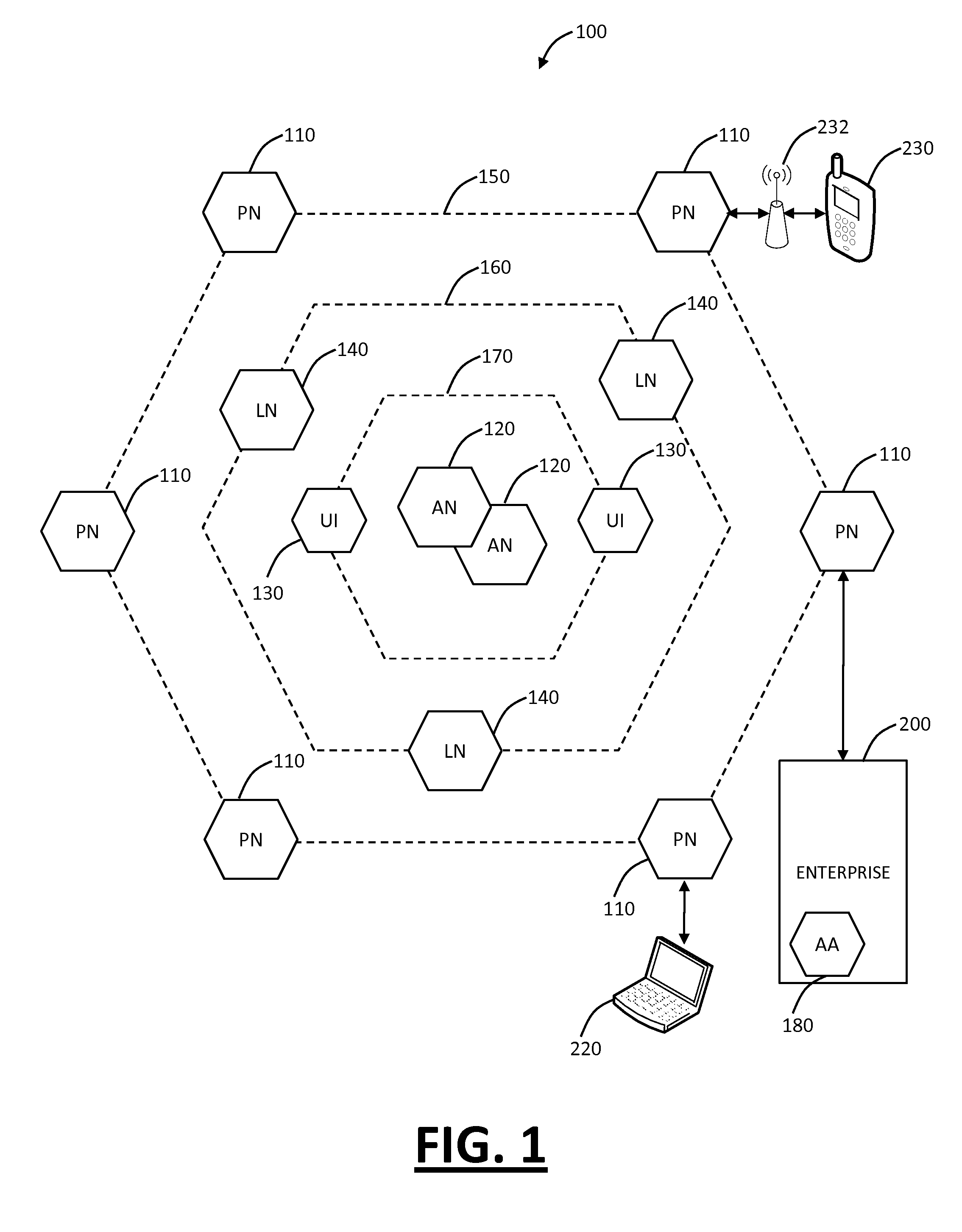
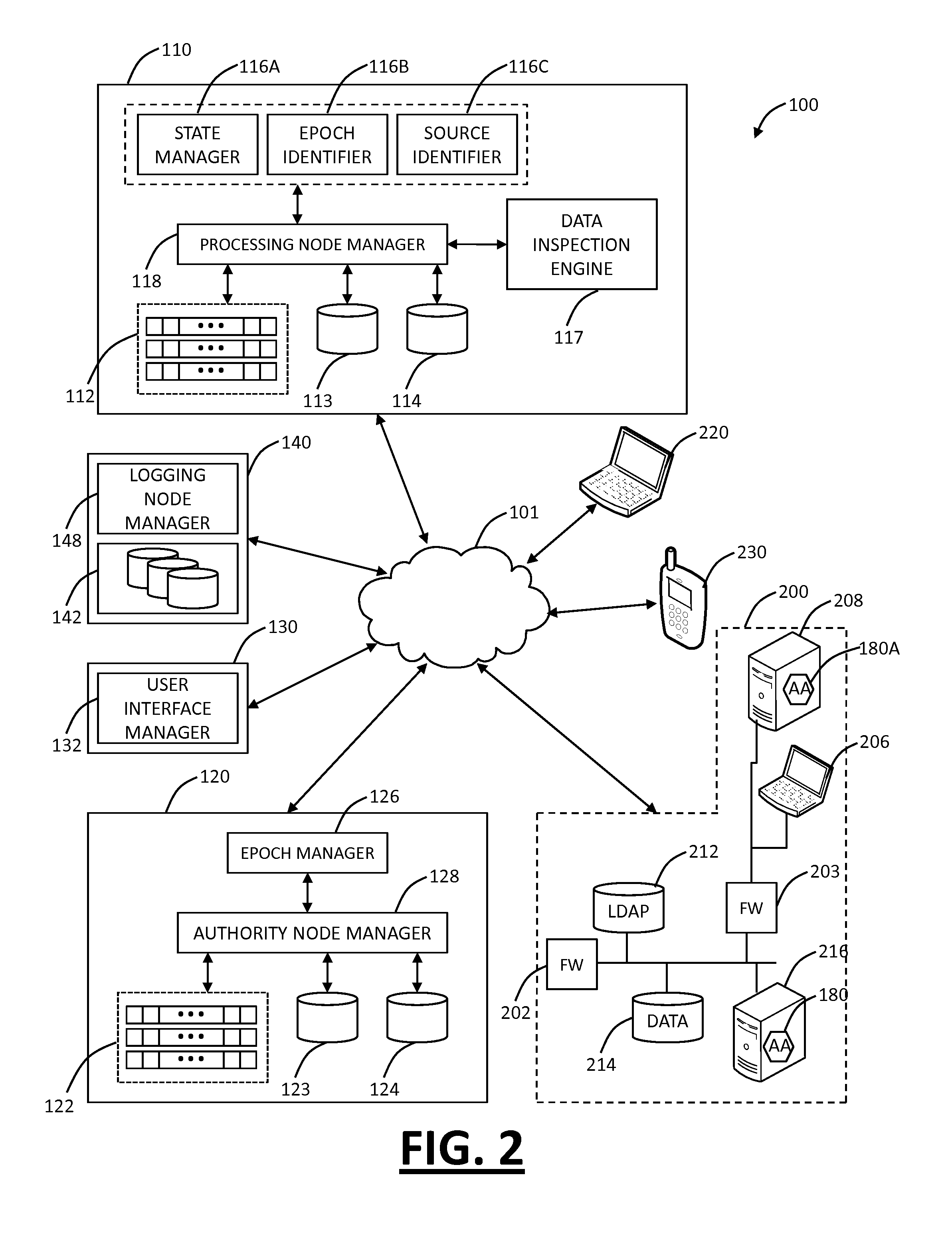
The invention provides a system and method for providing policy-based protection services. As a new threat is understood, one or more protection techniques are considered for protecting the asset, the organization assigns responsibilities to carry out or protect the asset, and a policy is constructed. After the policy is developed a plan is put into action to protect the asset, and a policy implementer is developed and / or purchased, distributed, configured, and managed. Finally, the policy, its enforcement, and its effectiveness, are reviewed to determine any changes needed, and new requirements are discovered, closing the lifecycle.
Owner:ALLEGENT TECH GROUP
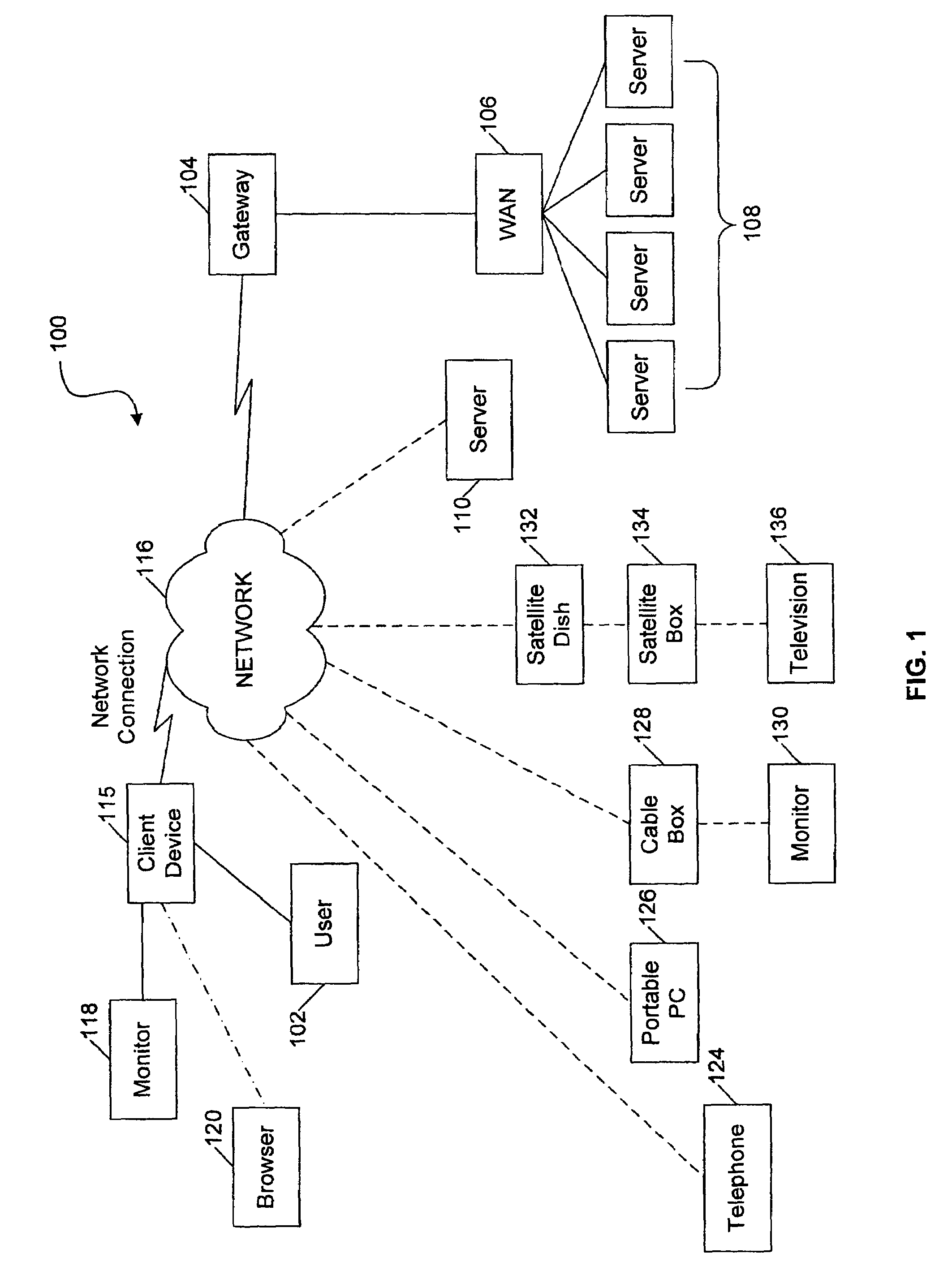
Administration of protection of data accessible by a mobile device
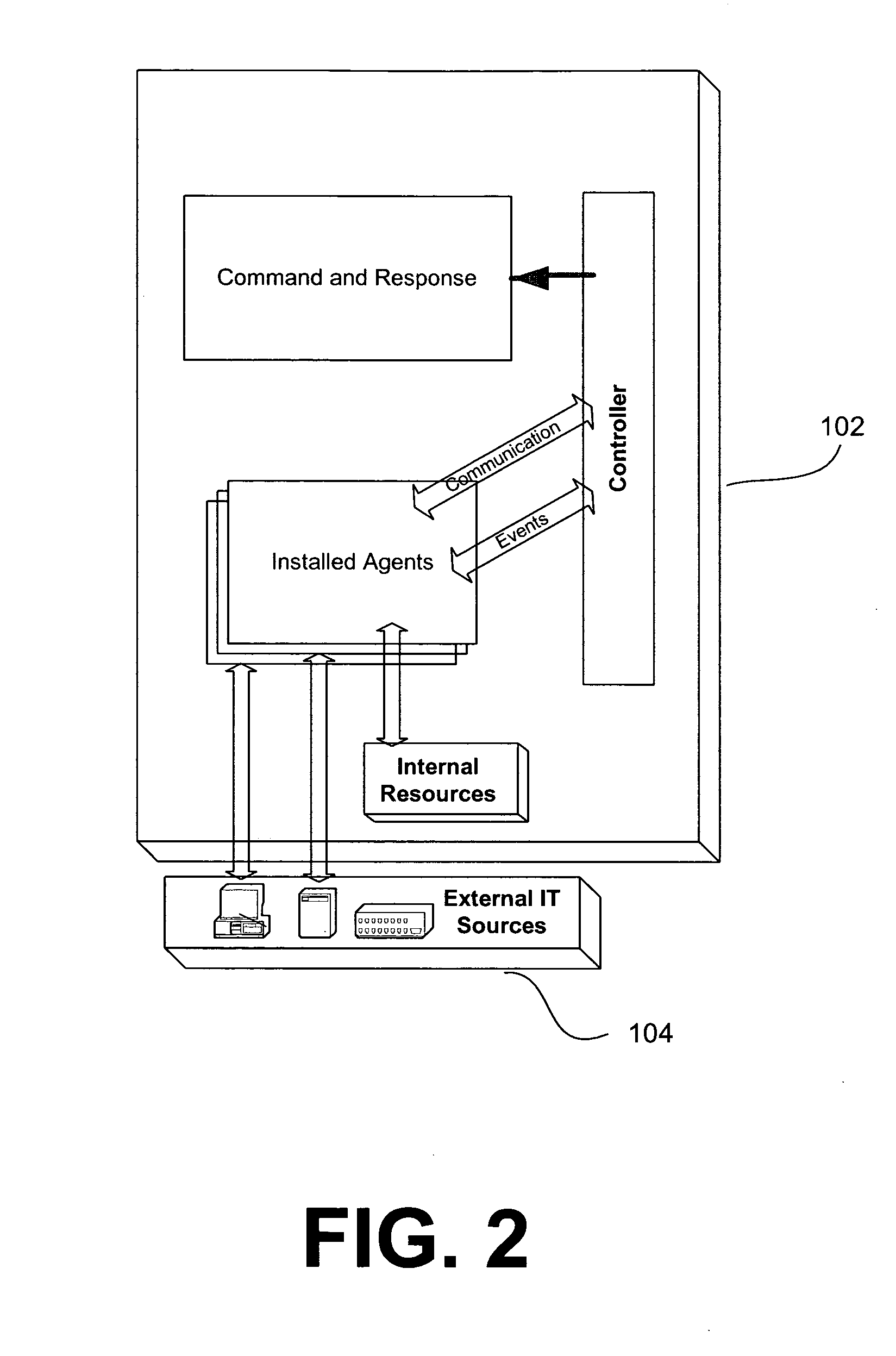
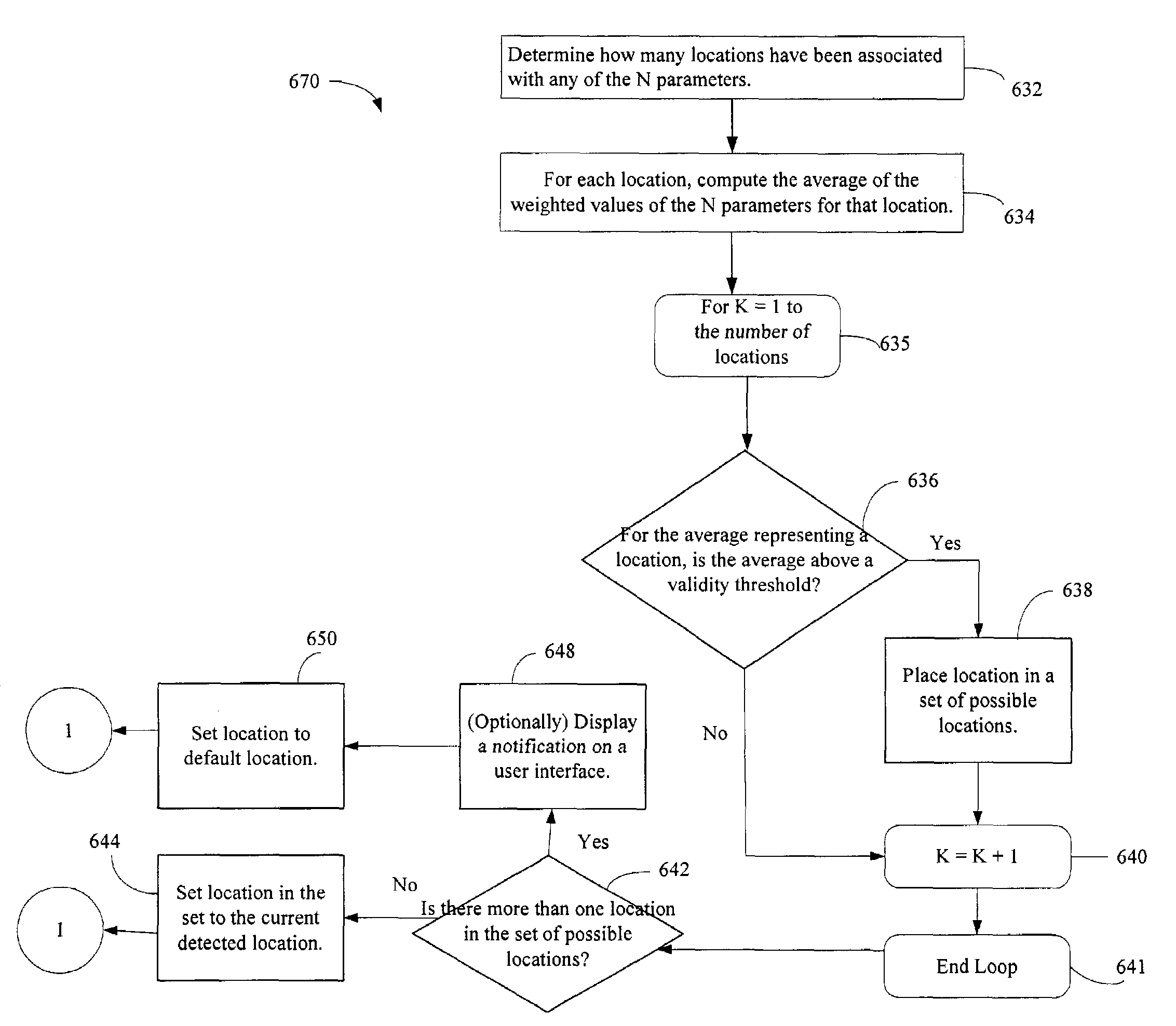
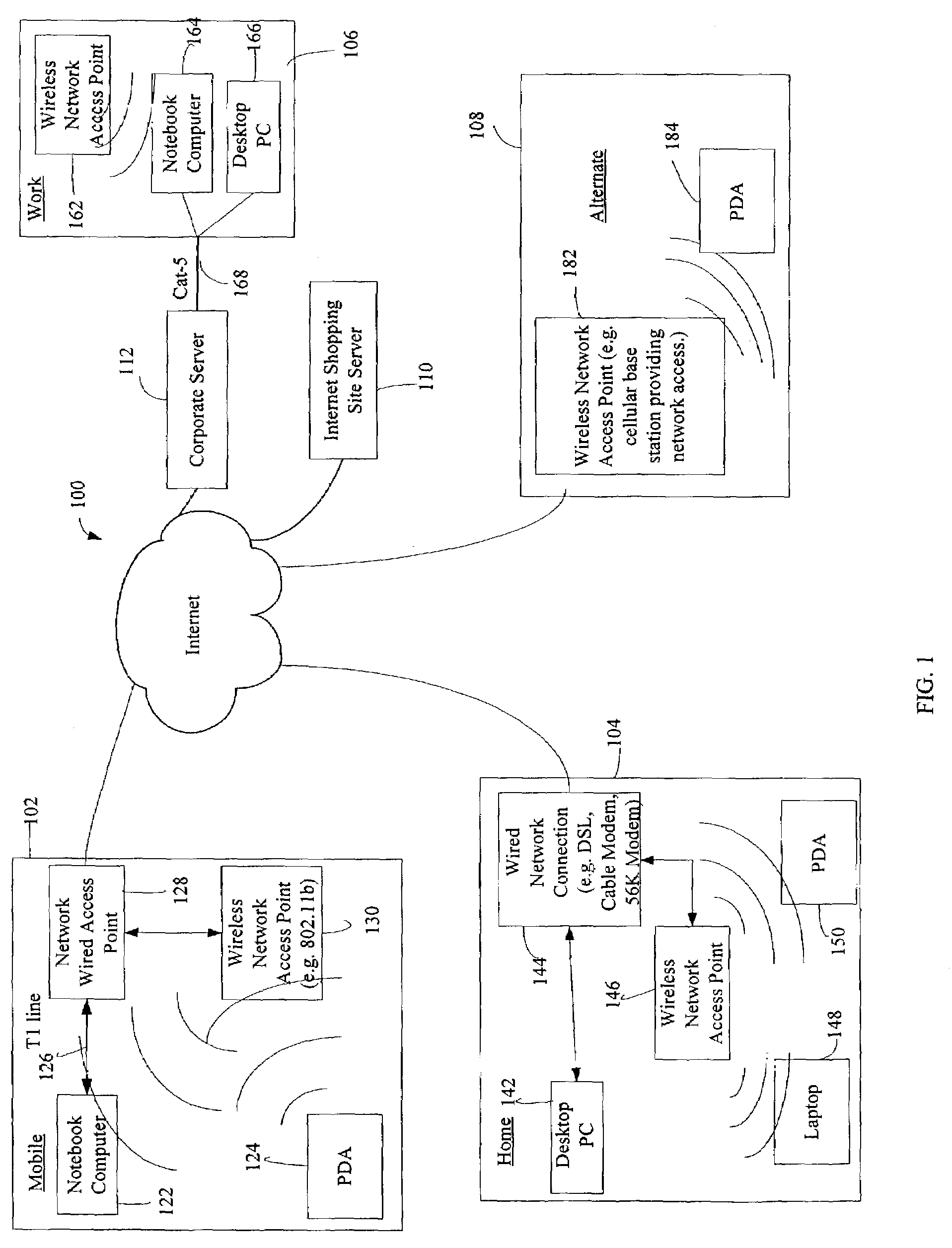
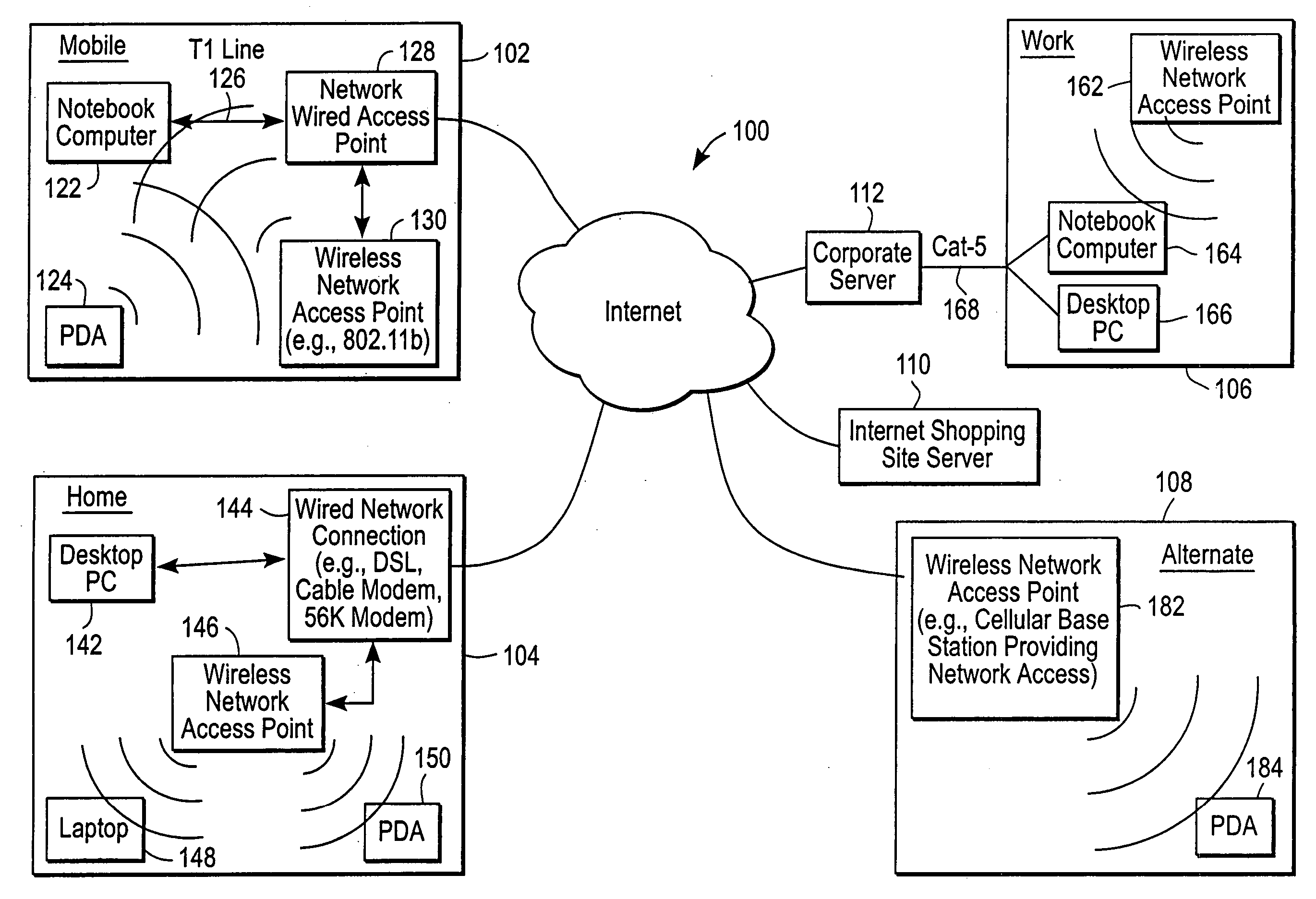
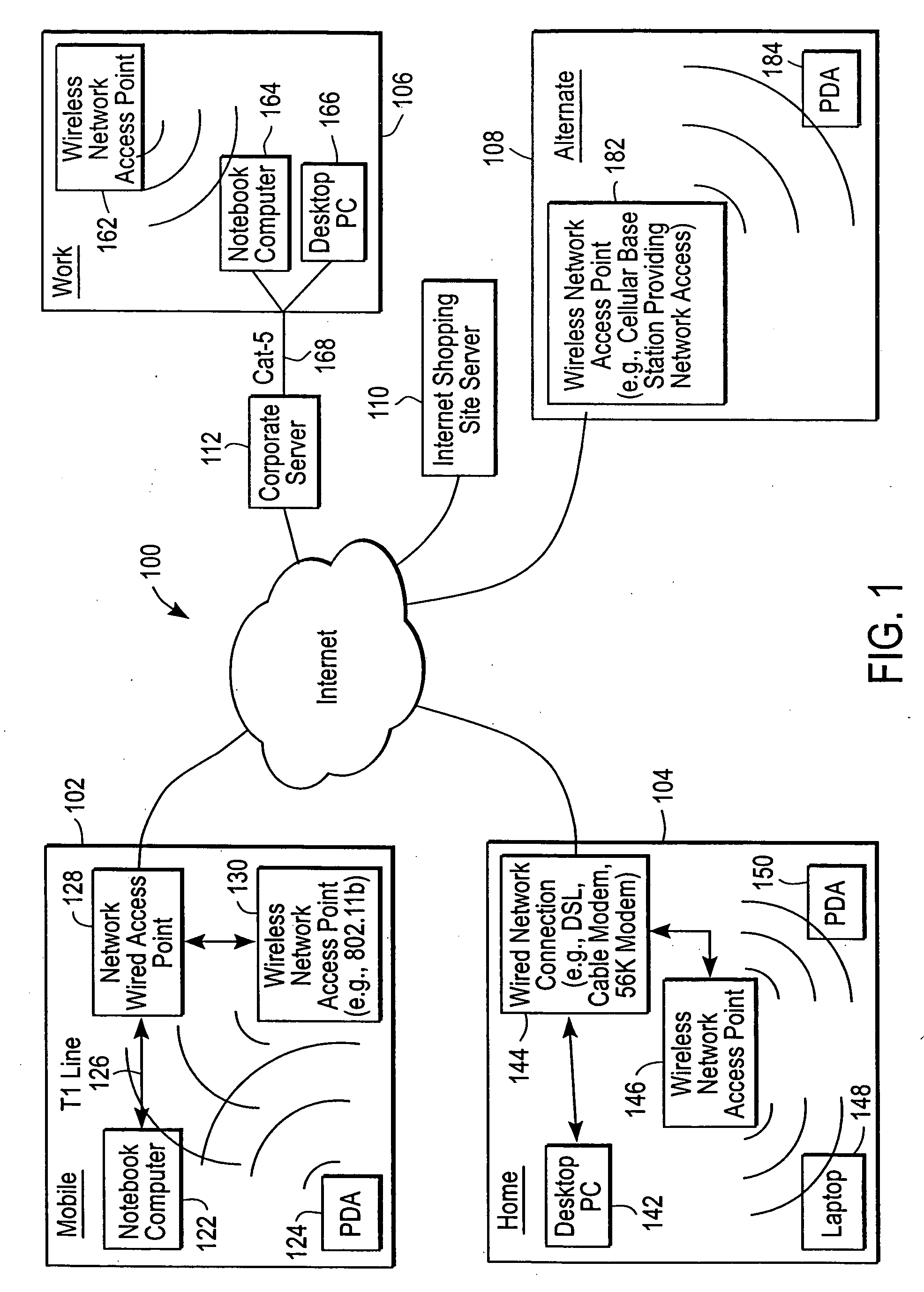
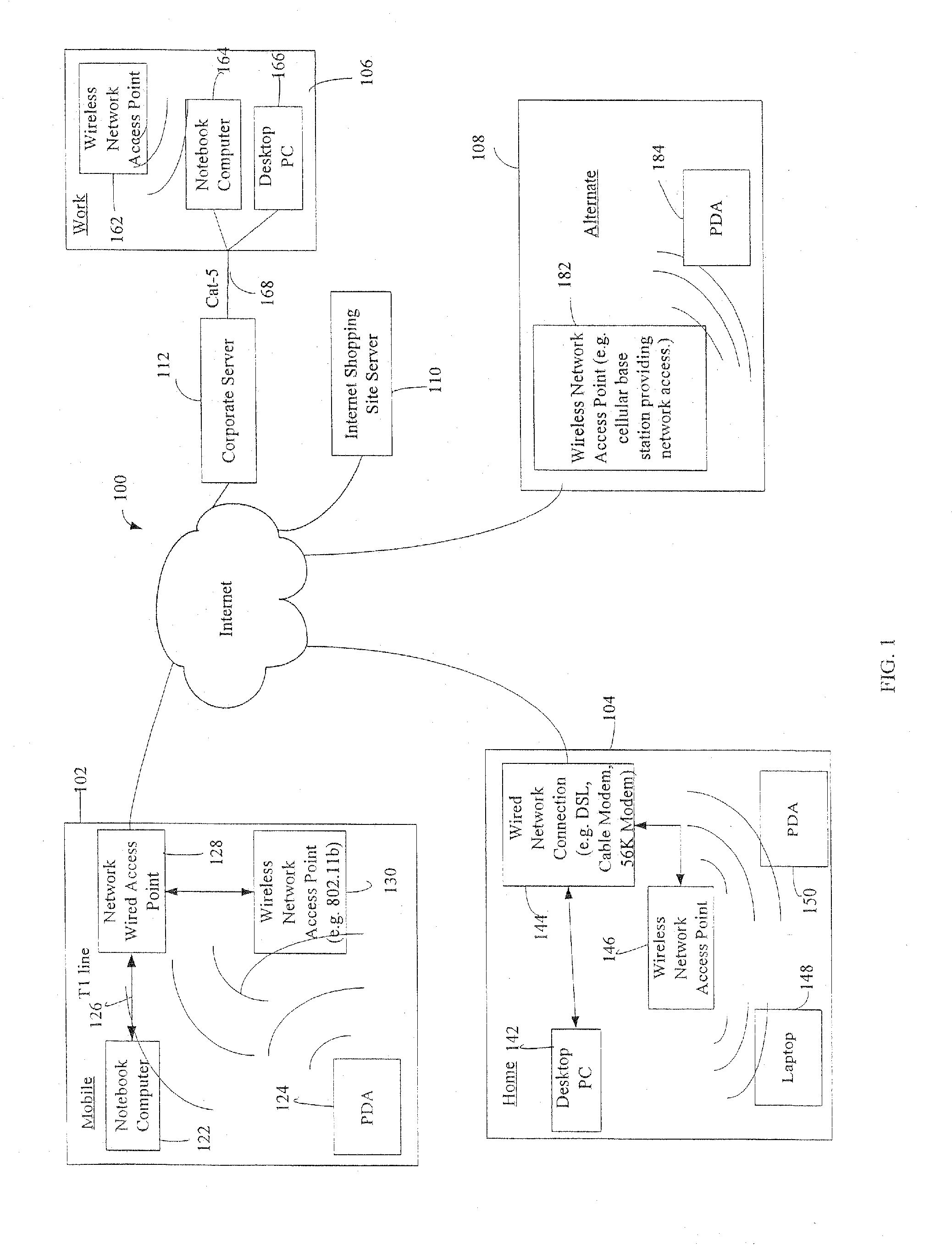
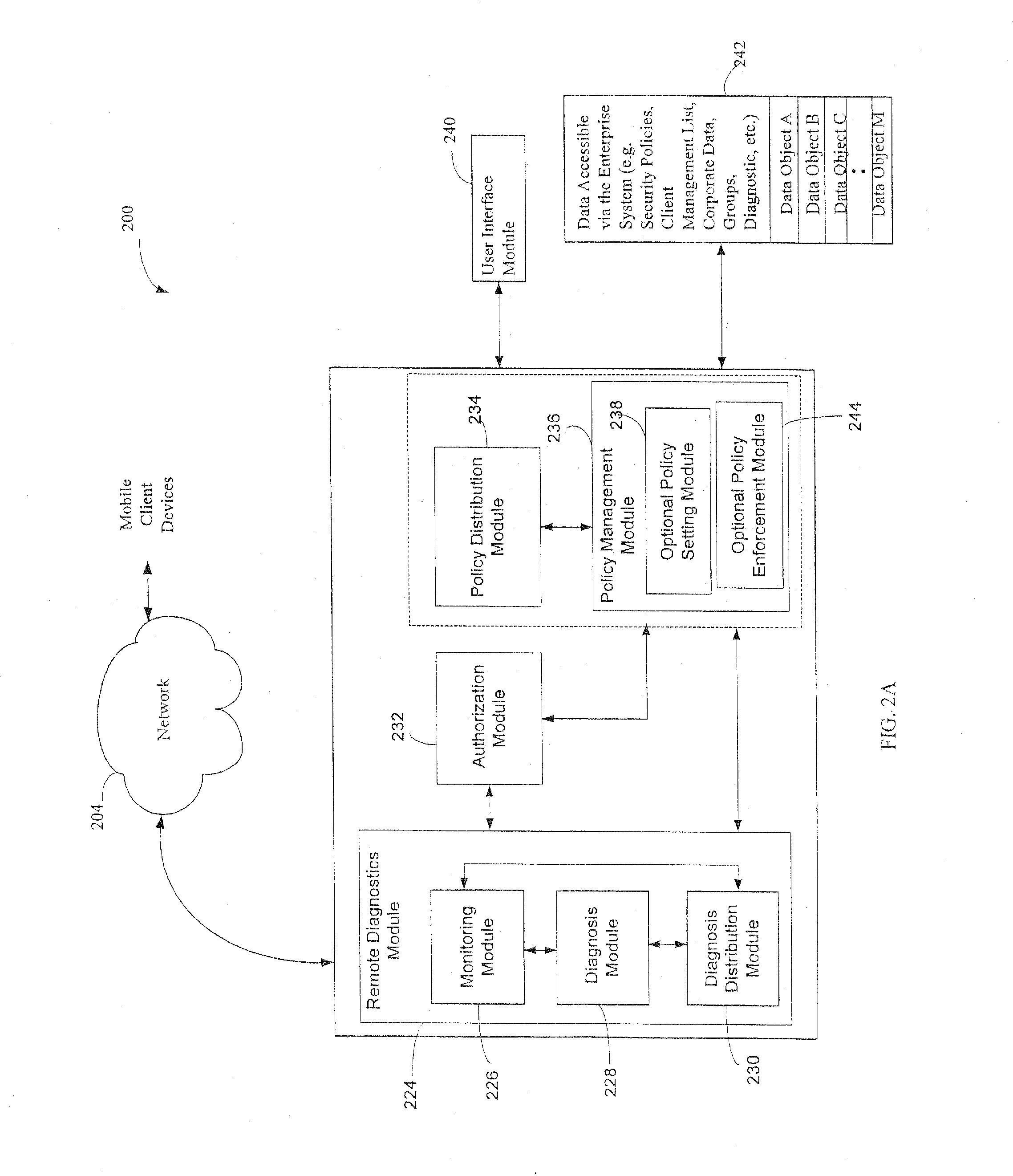
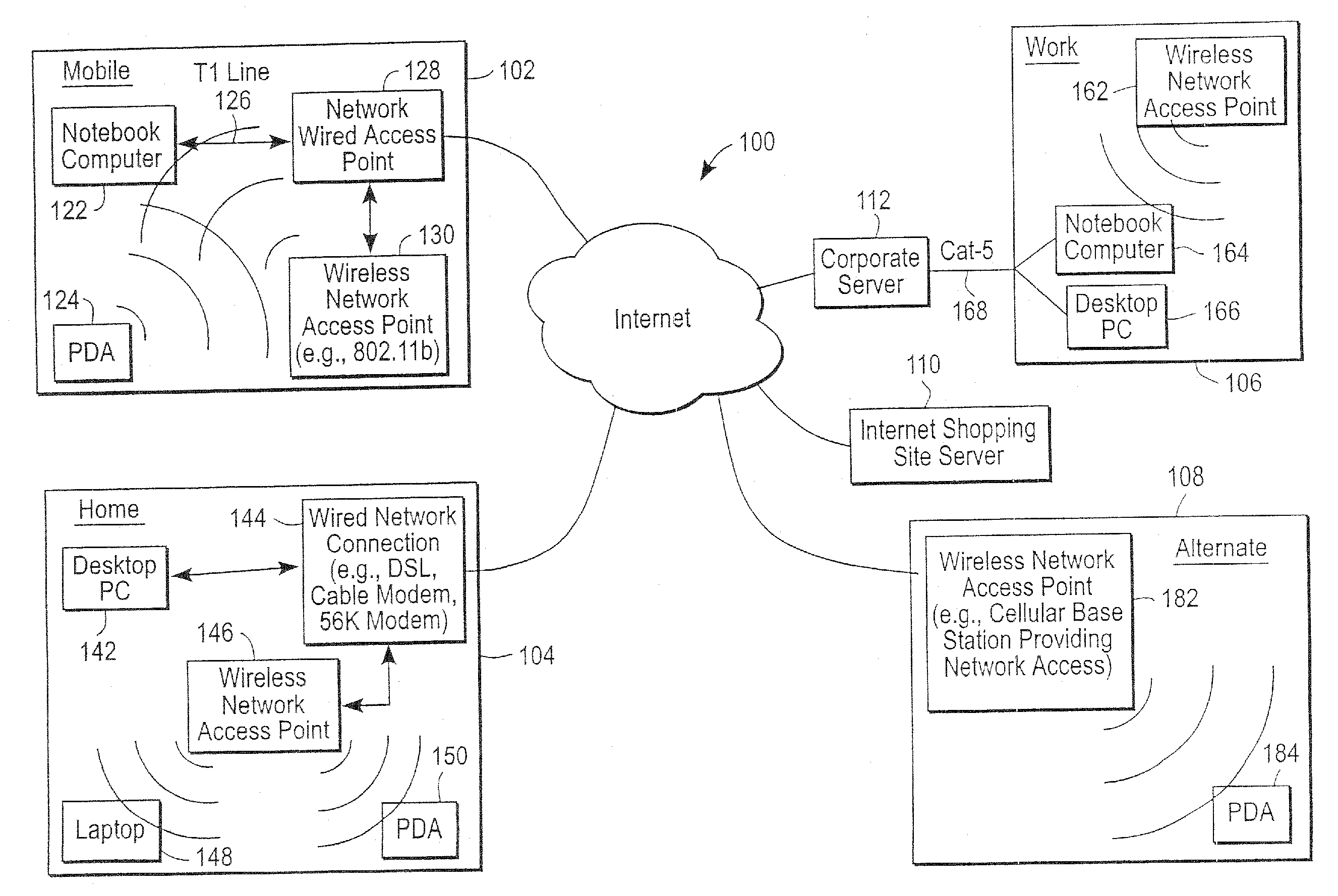
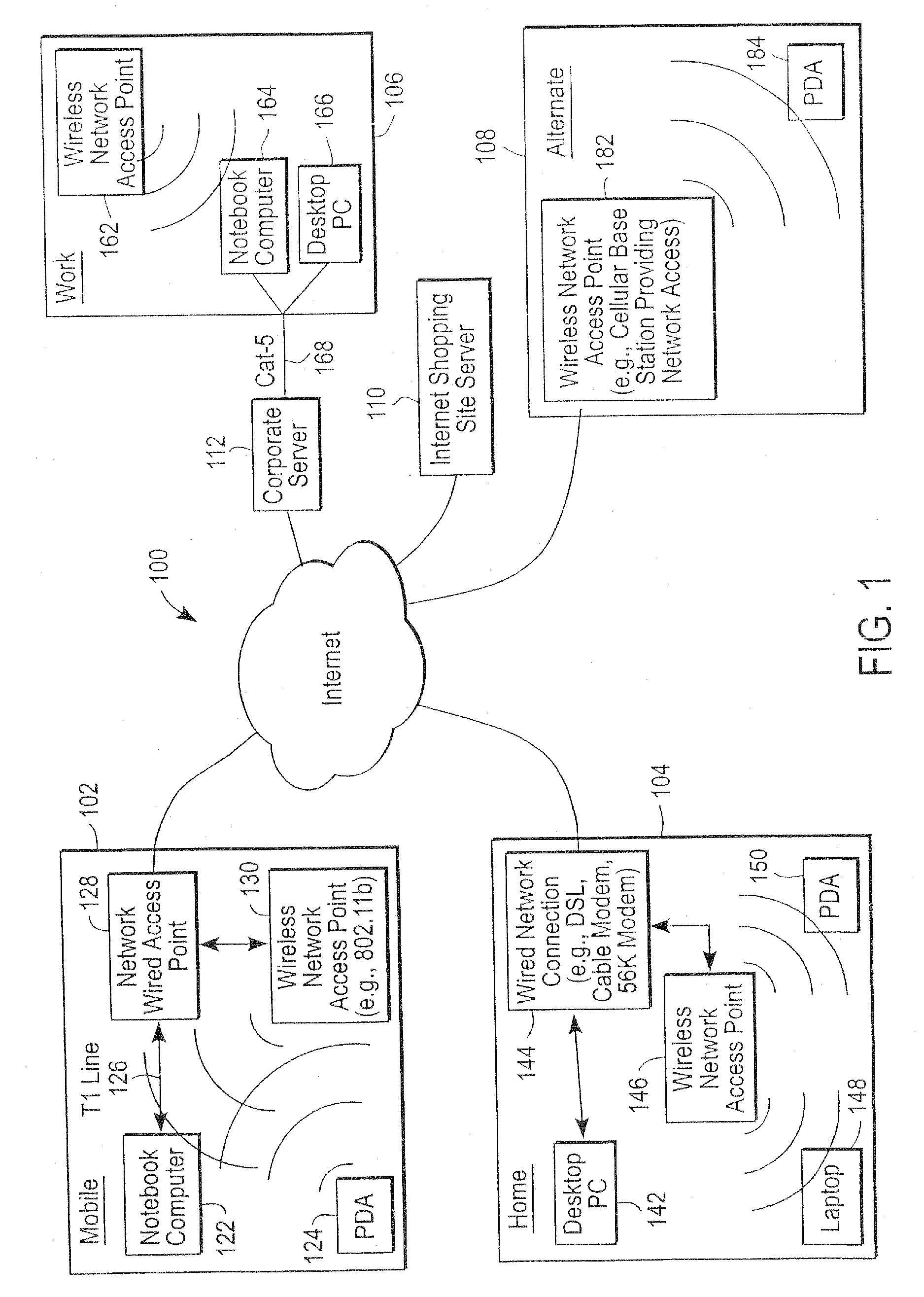
The administration of protection of data on a client mobile computing device by a server computer system such as within an enterprise network or on a separate mobile computing device is described. Security tools are described that provide different security policies to be enforced based on a location associated with a network environment in which a mobile device is operating. Methods for detecting the location of the mobile device are described. Additionally, the security tools may also provide for enforcing different policies based on security features. Examples of security features include the type of connection, wired or wireless, over which data is being transferred, the operation of anti-virus software, or the type of network adapter card. The different security policies provide enforcement mechanisms that may be tailored based upon the detected location and / or active security features associated with the mobile device. Examples of enforcement mechanisms are adaptive port blocking, file hiding and file encryption.
Owner:APPLE INC
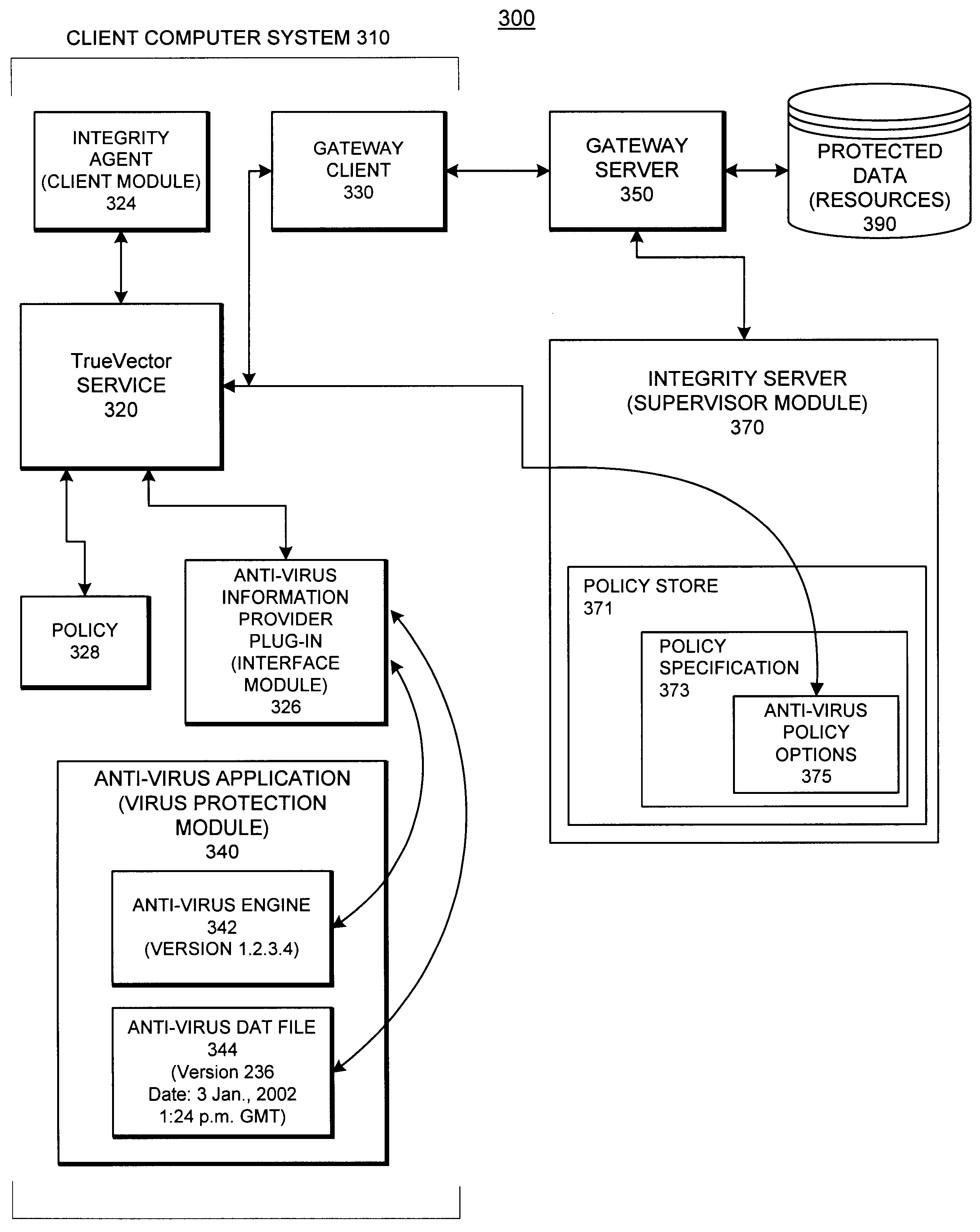
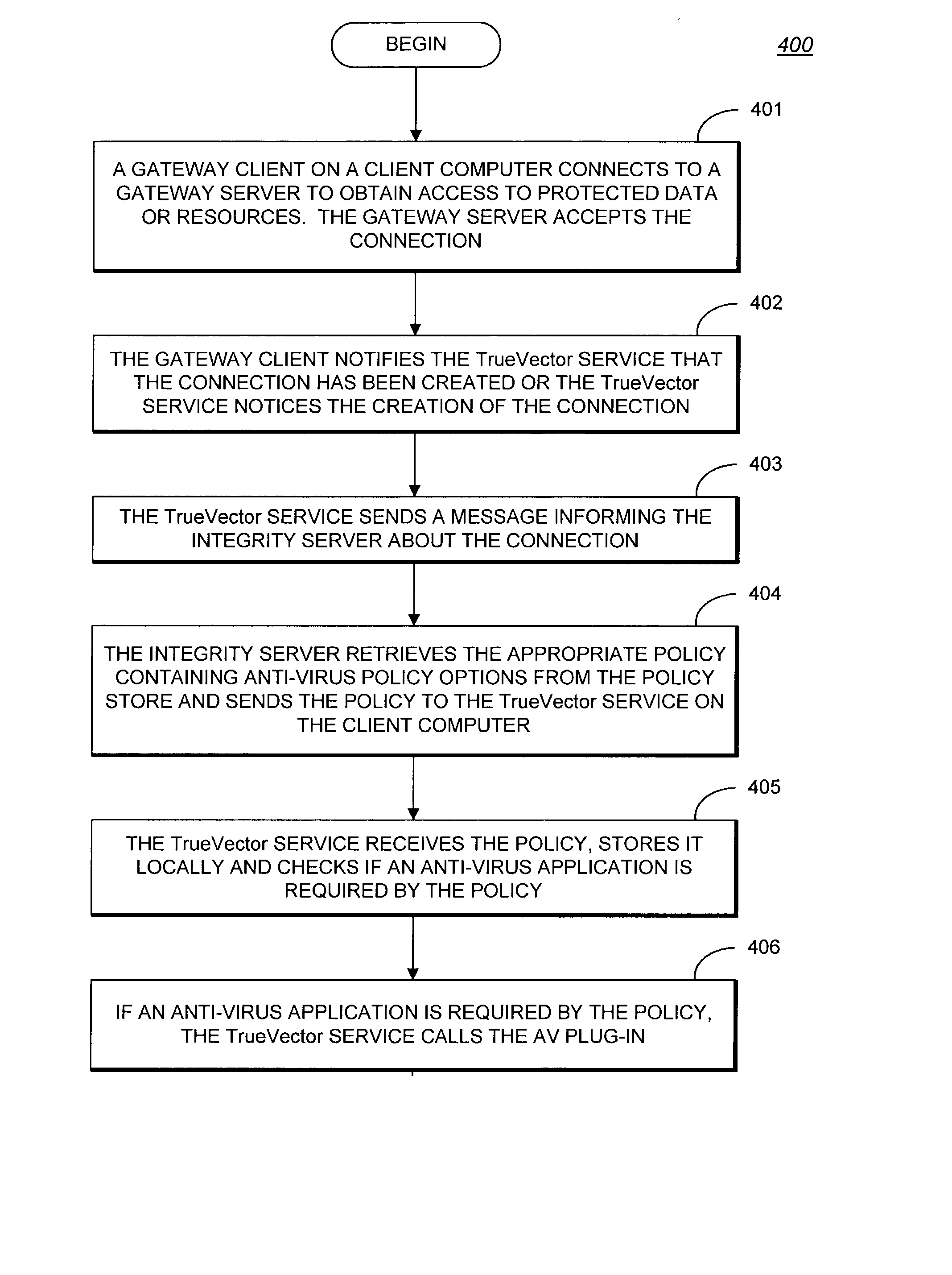
System and methods providing anti-virus cooperative enforcement
InactiveUS6873988B2Data processing applicationsMultiple digital computer combinationsAnti virusComputer network
A system providing methods for anti-virus cooperative enforcement is described. In response to a request from a device for access to protected resources, such as a network or protected data, a determination is made as to whether an anti-virus policy applies to the request for access made by the device. If an anti-virus policy is applicable, information pertaining to virus protection available on the device is collected. The virus protection information that is collected is evaluated to determine whether the device is in compliance with the anti-virus policy. If the device is determined to be in compliance with the anti-virus policy, the device is allowed to access the protected resources.
Owner:CHECK POINT SOFTWARE TECH INC
Administration of protection of data accessible by a mobile device
ActiveUS20050055578A1Digital data processing detailsMultiple digital computer combinationsAnti virusEnterprise networking
The protection of data on a client mobile computing device by a server computer system such as within an enterprise network or on a separate mobile computing device is described. Security tools are described that provide different security policies to be enforced based on a location associated with a network environment in which a mobile device is operating. Methods for detecting the location of the mobile device are described. Additionally, the security tools may also provide for enforcing different policies based on security features. Examples of security features include the type of connection, wired or wireless, over which data is being transferred, the operation of anti-virus software, or the type of network adapter card. The different security policies provide enforcement mechanisms that may be tailored based upon the detected location and / or active security features associated with the mobile device. Examples of enforcement mechanisms are adaptive port blocking, file hiding and file encryption.
Owner:APPLE INC
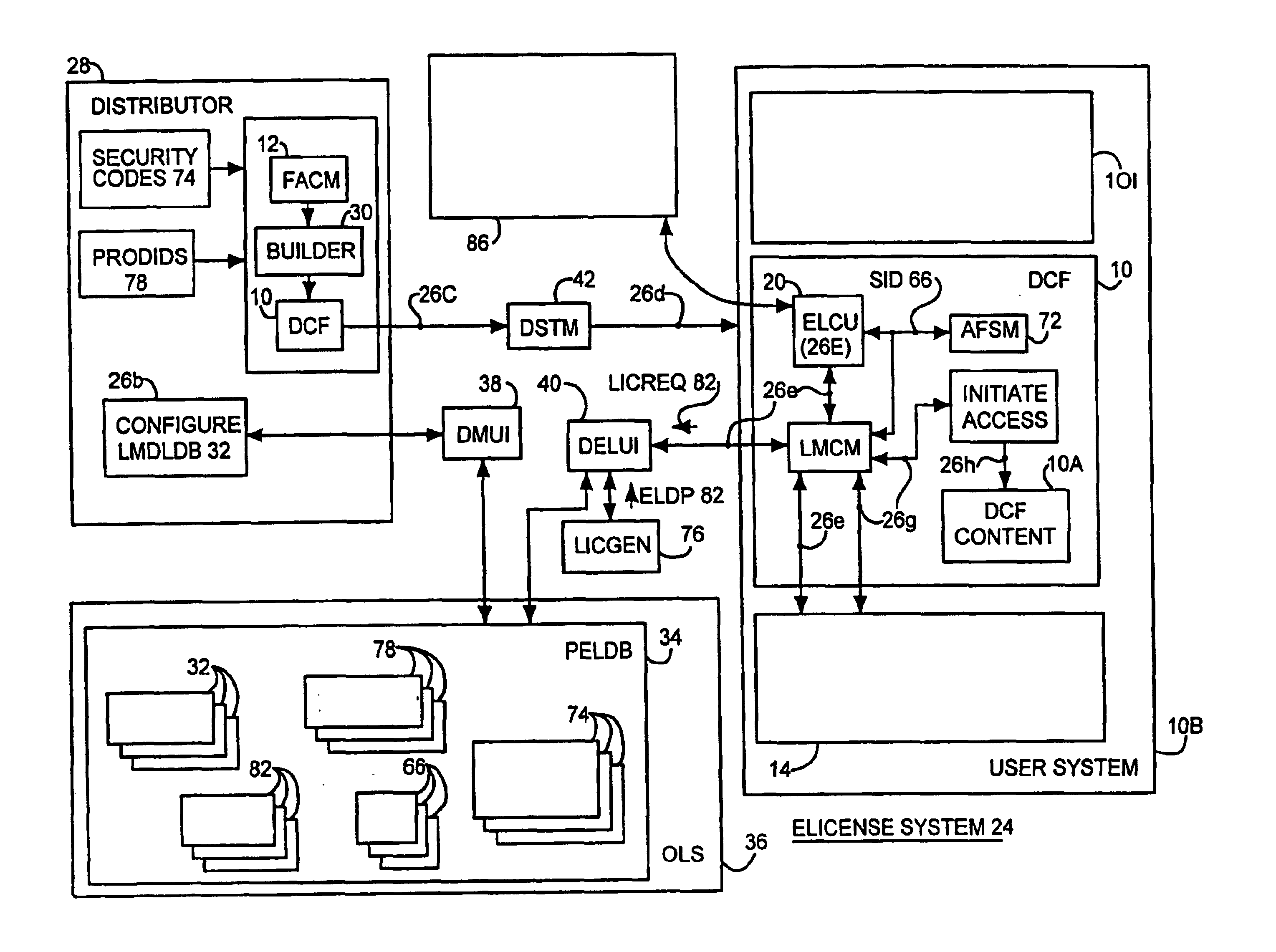
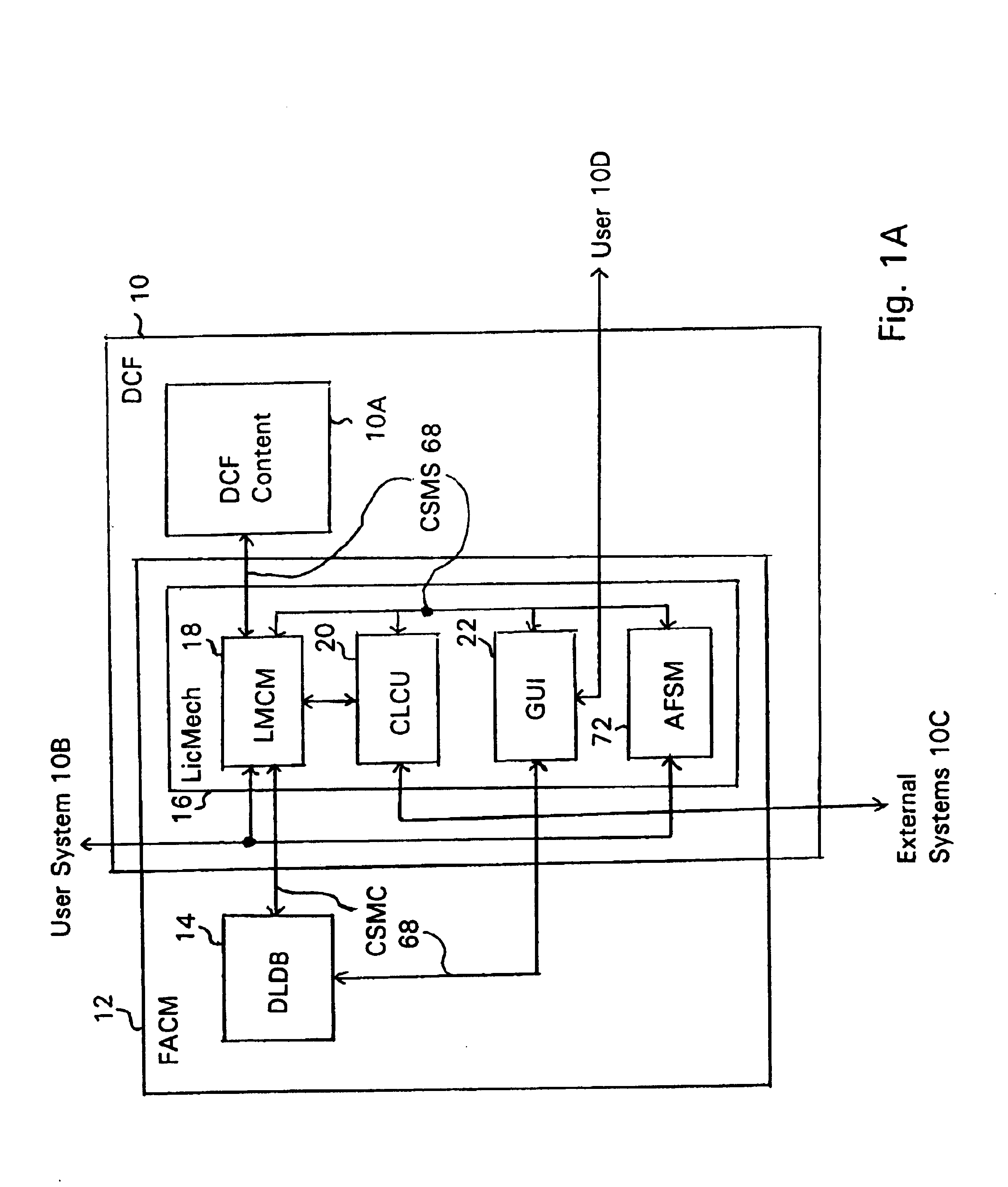
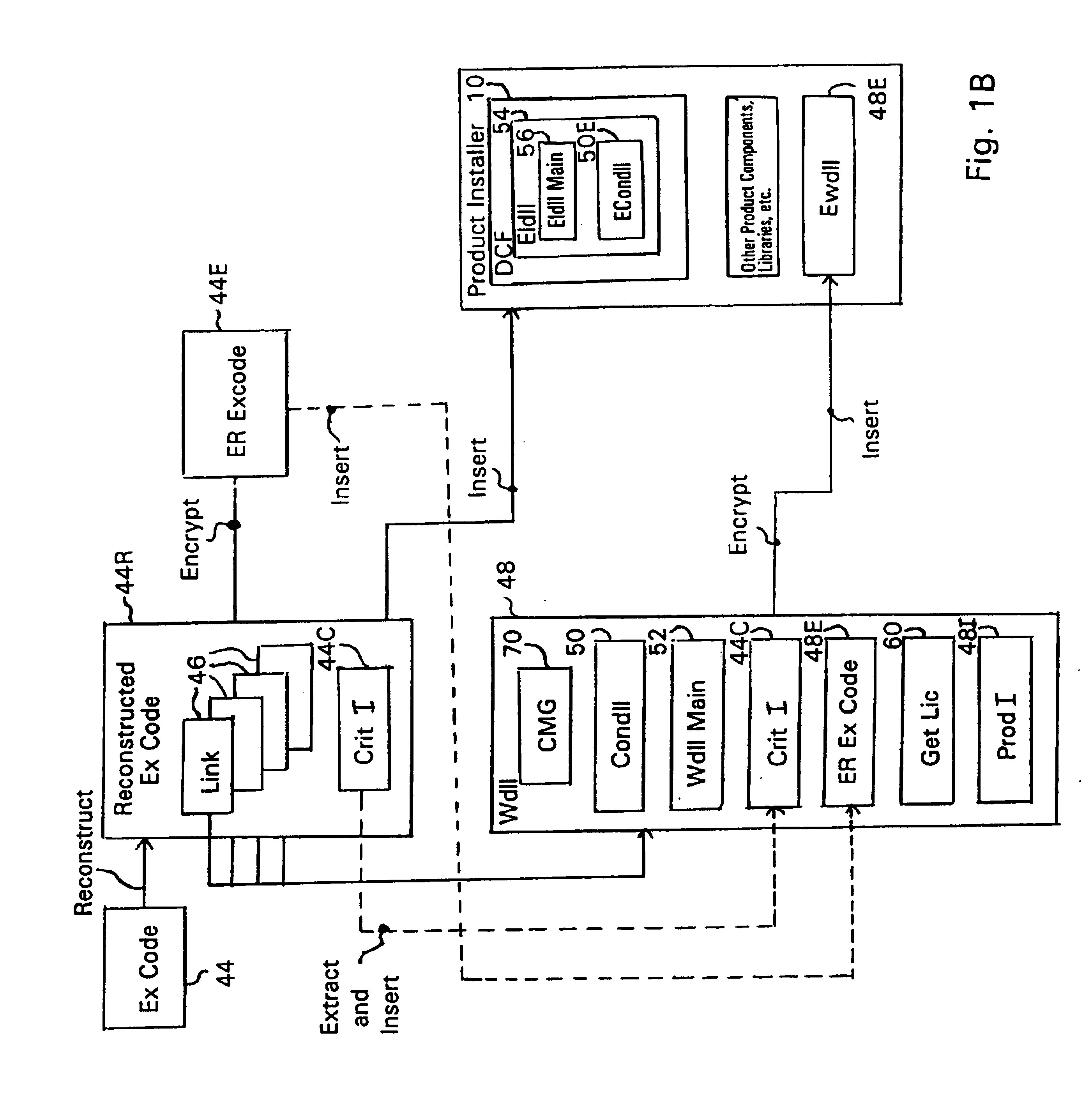
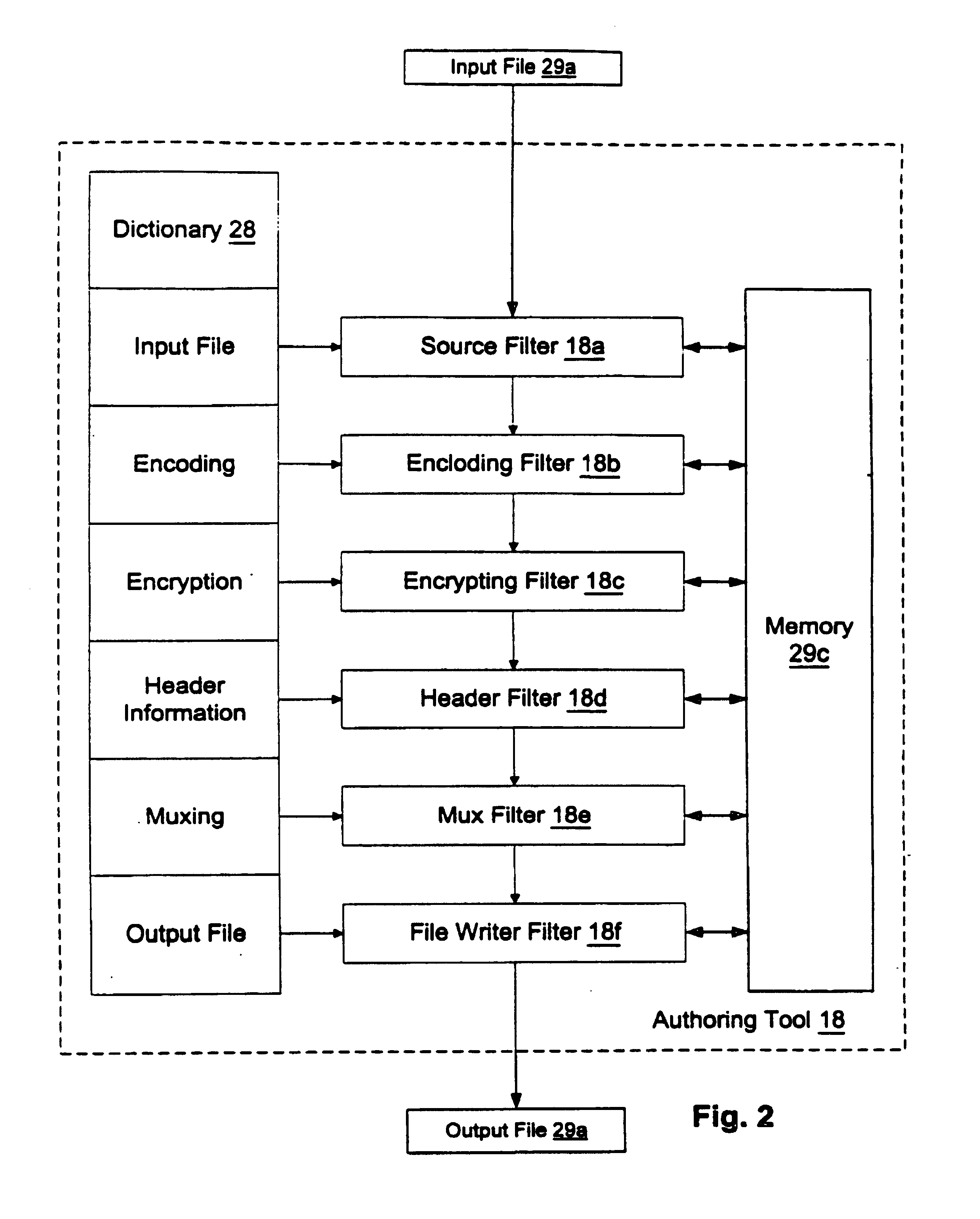
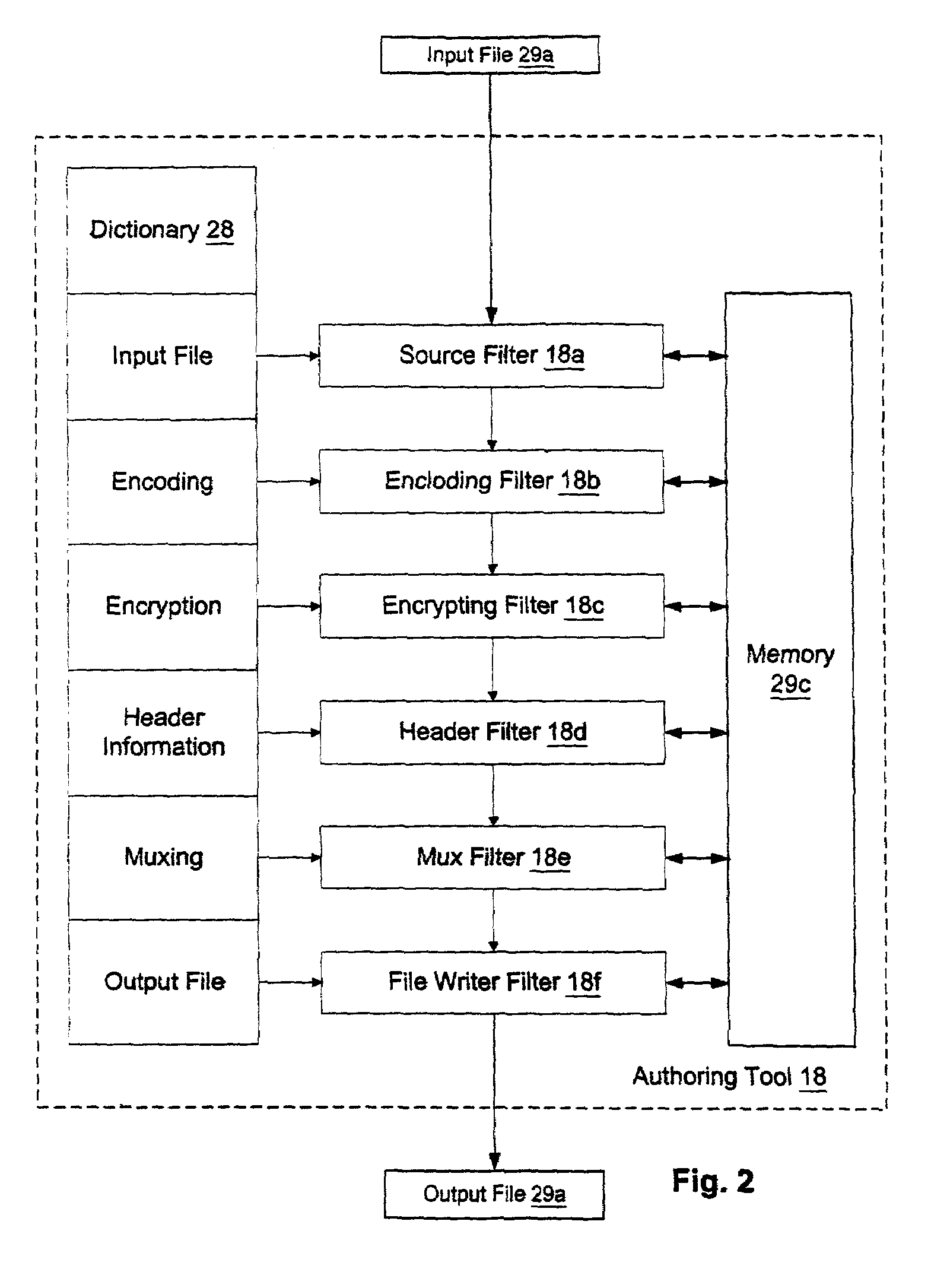
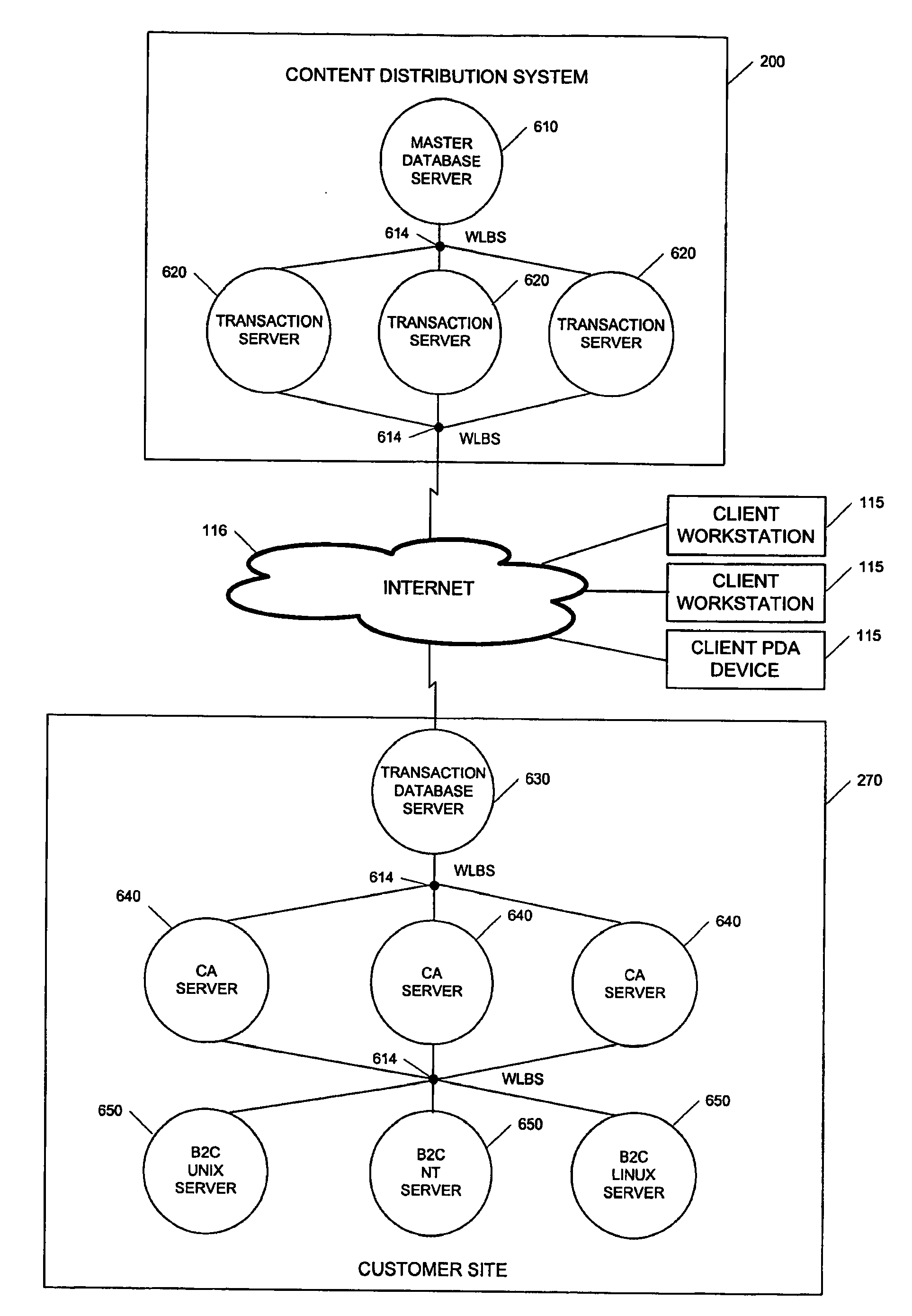
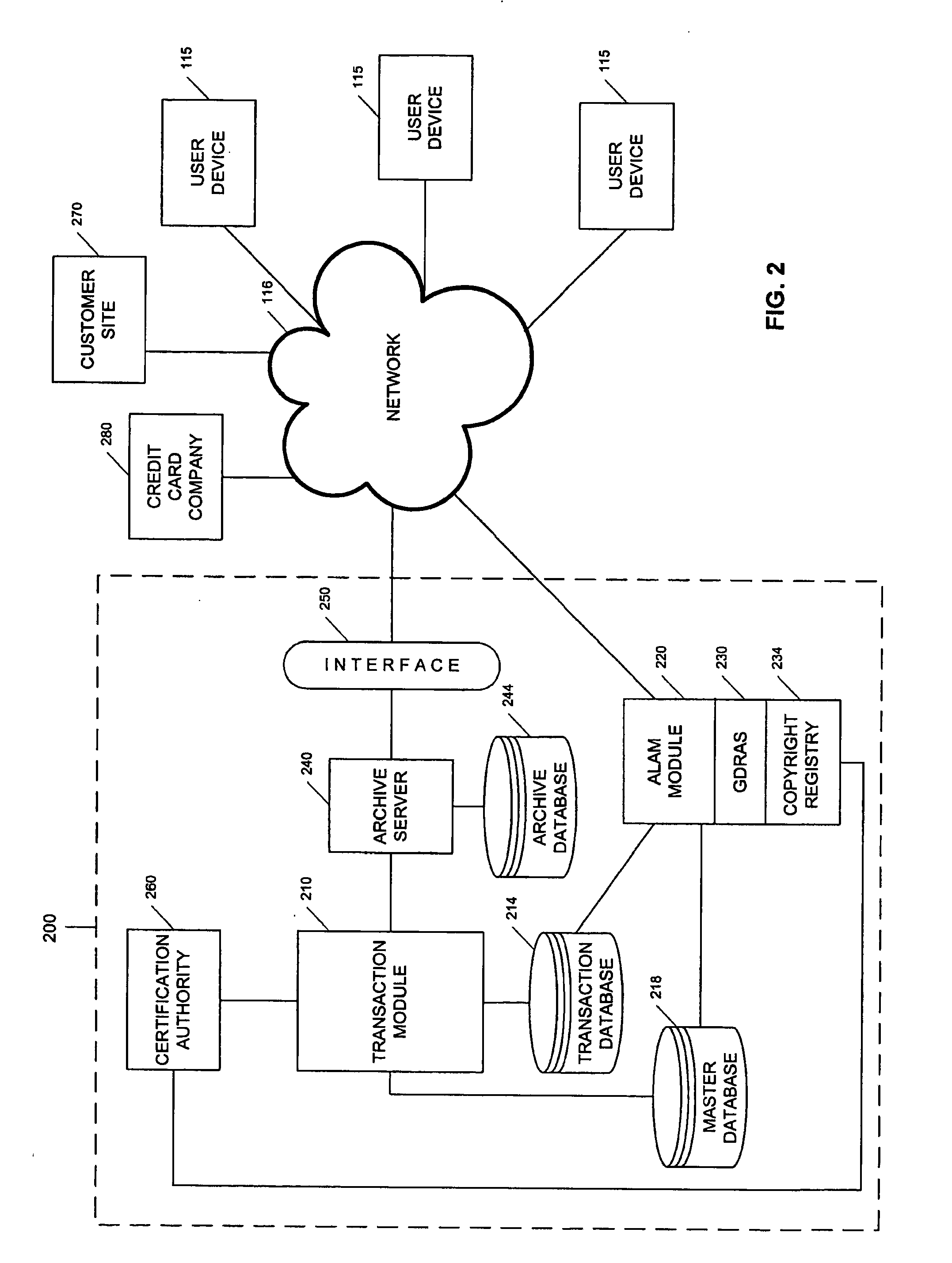
System and embedded license control mechanism for the creation and distribution of digital content files and enforcement of licensed use of the digital content files
A digital content file including a license control mechanism controlling the licensed use of digital content and a system and method for distributing licensable digital content files and licenses. A digital content file includes a digital content, which may be executable code or data, an embedded file access control mechanism and a dynamic license database associated with the file access mechanism for storing license information used by the file access control mechanism in controlling use of the digital content. The file access control mechanism includes a license monitor and control mechanism communicating with the dynamic license database and controlling use of the digital content and a license control utility providing communications between a user system and an external system to communicate license definition information and includes a graphical user interface. License information may be stored initially in the dynamic license database or provided from an external system. The system allows the distribution of digital content files and the acquisition of licenses with seamless transaction processing through an order processing system generating an order identification and authorization for a license and a product configuration and order database containing license management databases associated with the digital content files and containing license information to be transmitted to a user system upon receipt of an order identifier. The product configuration and order database also generates a license record for each transaction.
Owner:VIATECH TECH
System and methods providing anti-virus cooperative enforcement
InactiveUS20030055994A1Data processing applicationsMultiple digital computer combinationsAnti virusComputer network
A system providing methods for anti-virus cooperative enforcement is described. In response to a request from a device for access to protected resources, such as a network or protected data, a determination is made as to whether an anti-virus policy applies to the request for access made by the device. If an anti-virus policy is applicable, information pertaining to virus protection available on the device is collected. The virus protection information that is collected is evaluated to determine whether the device is in compliance with the anti-virus policy. If the device is determined to be in compliance with the anti-virus policy, the device is allowed to access the protected resources.
Owner:CHECK POINT SOFTWARE TECH INC
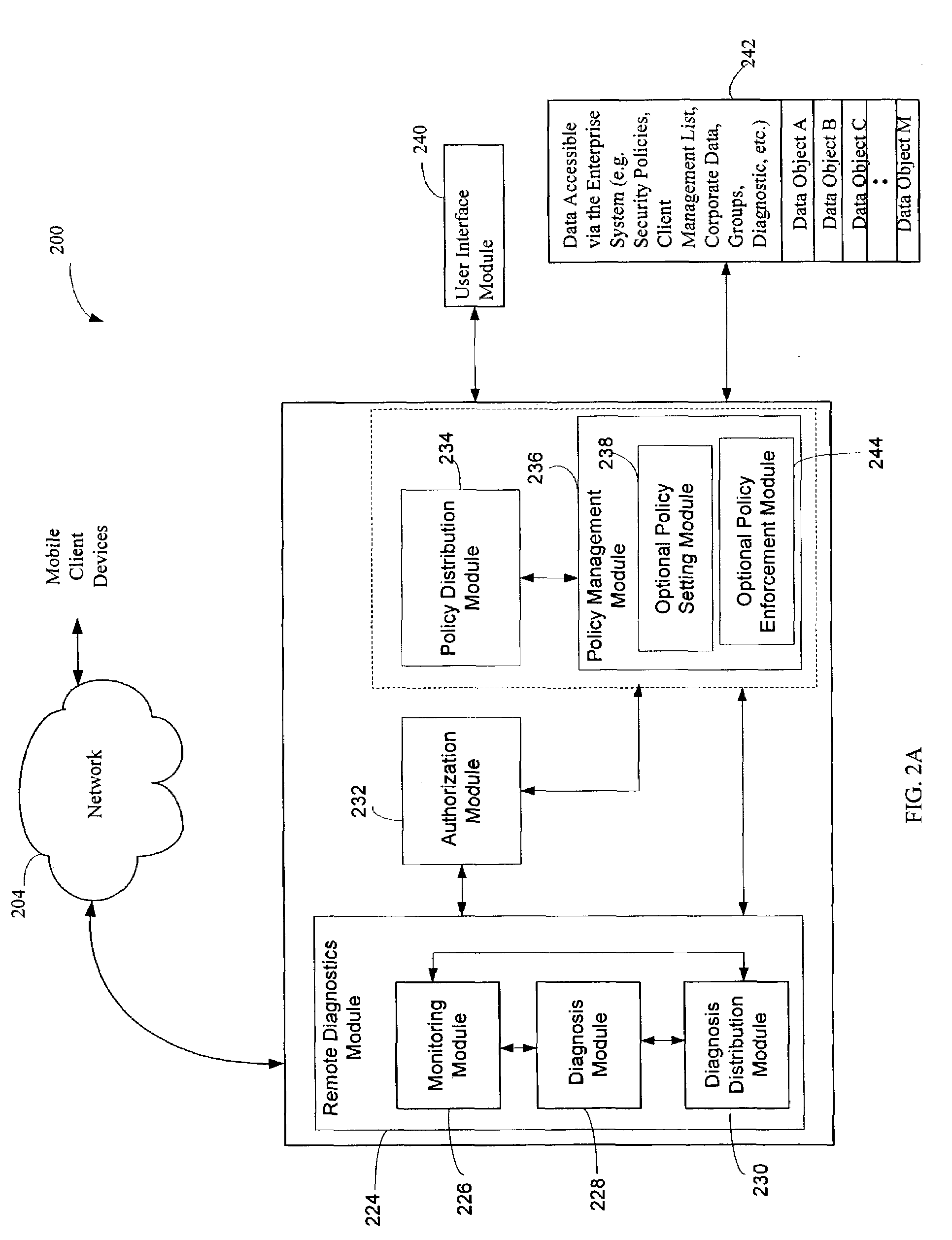
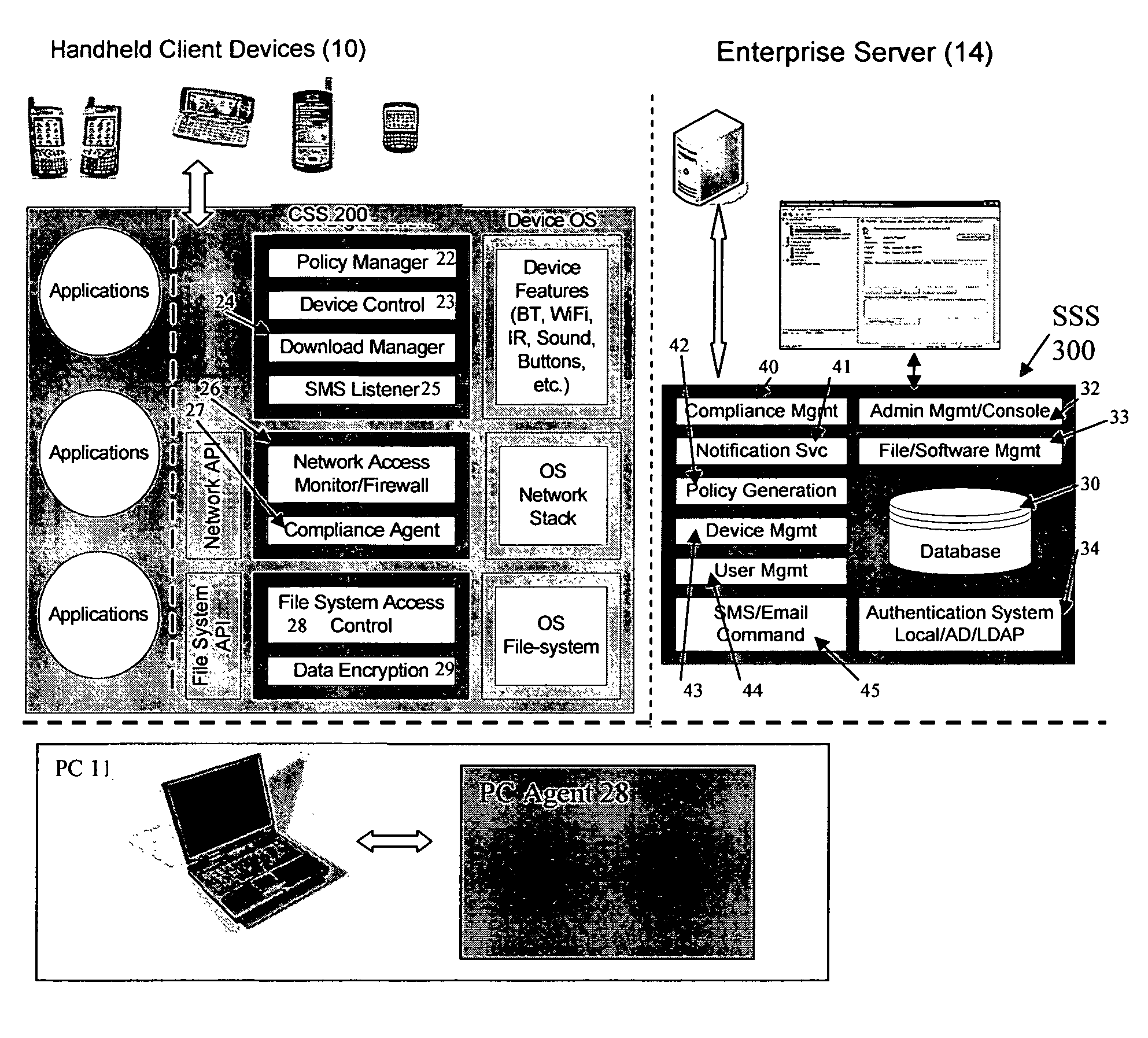
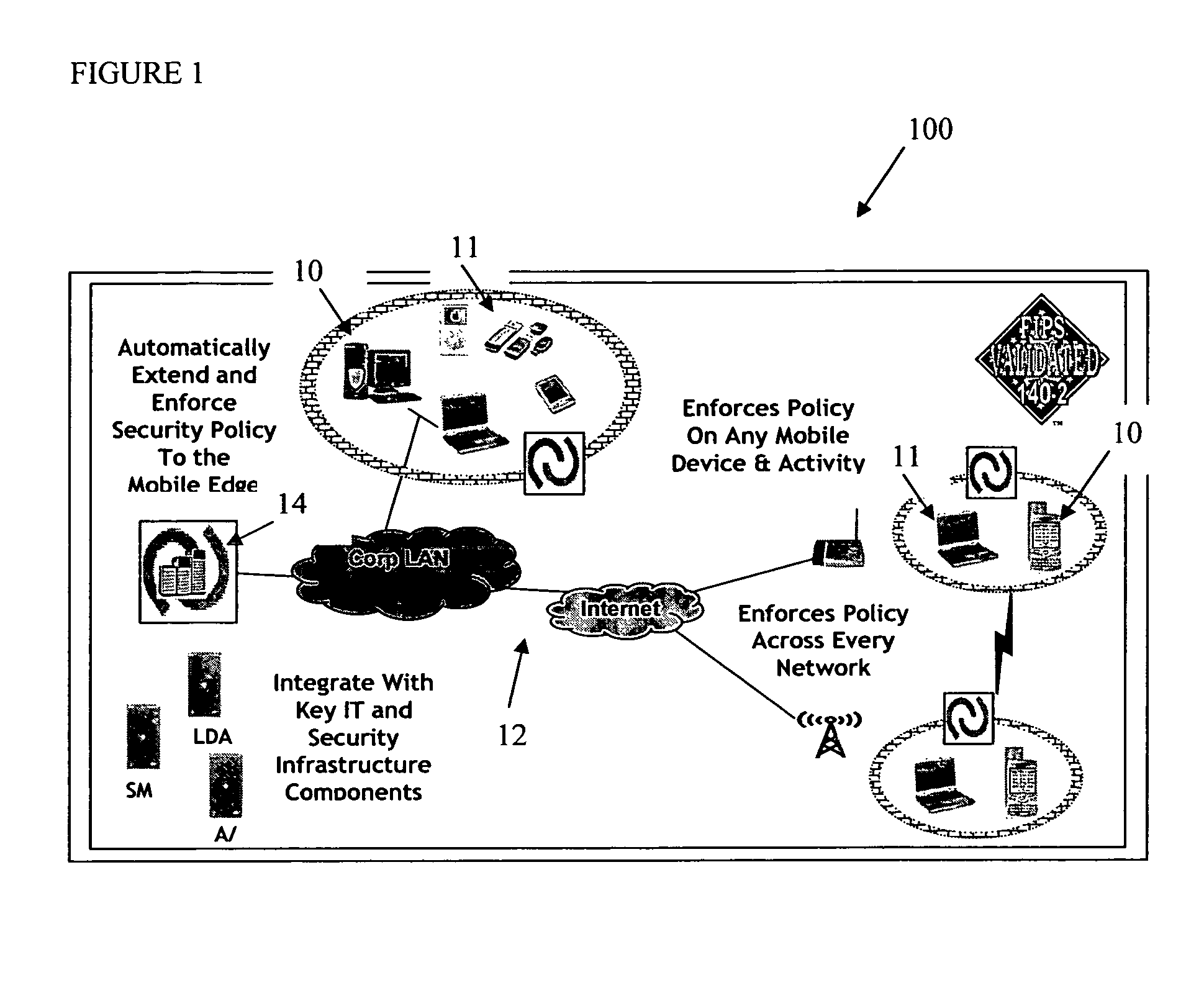
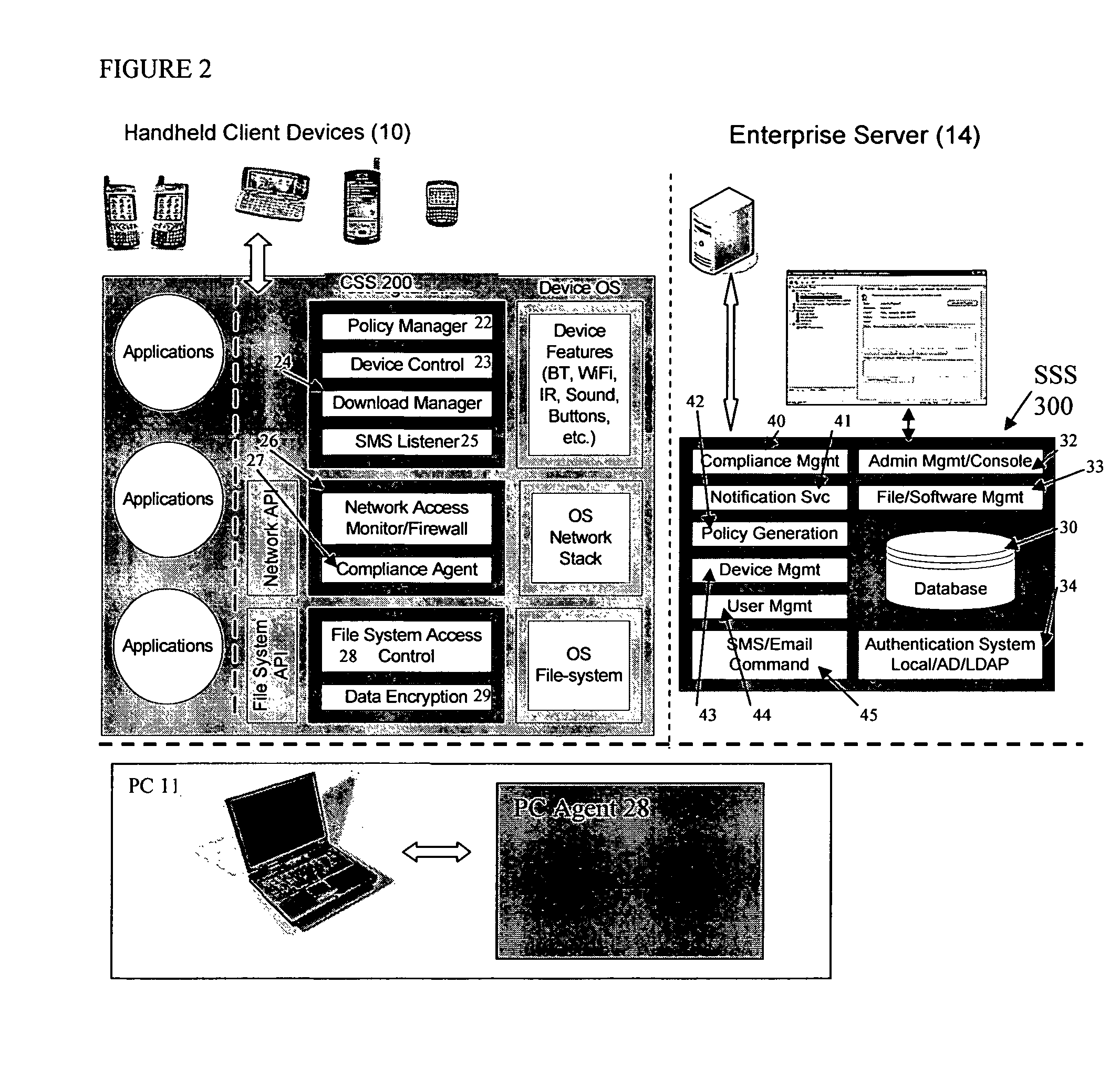
Mobile data security system and methods
ActiveUS20060224742A1Transparent applicationUnauthorised/fraudulent call preventionEavesdropping prevention circuitsMobile securitySecurity system
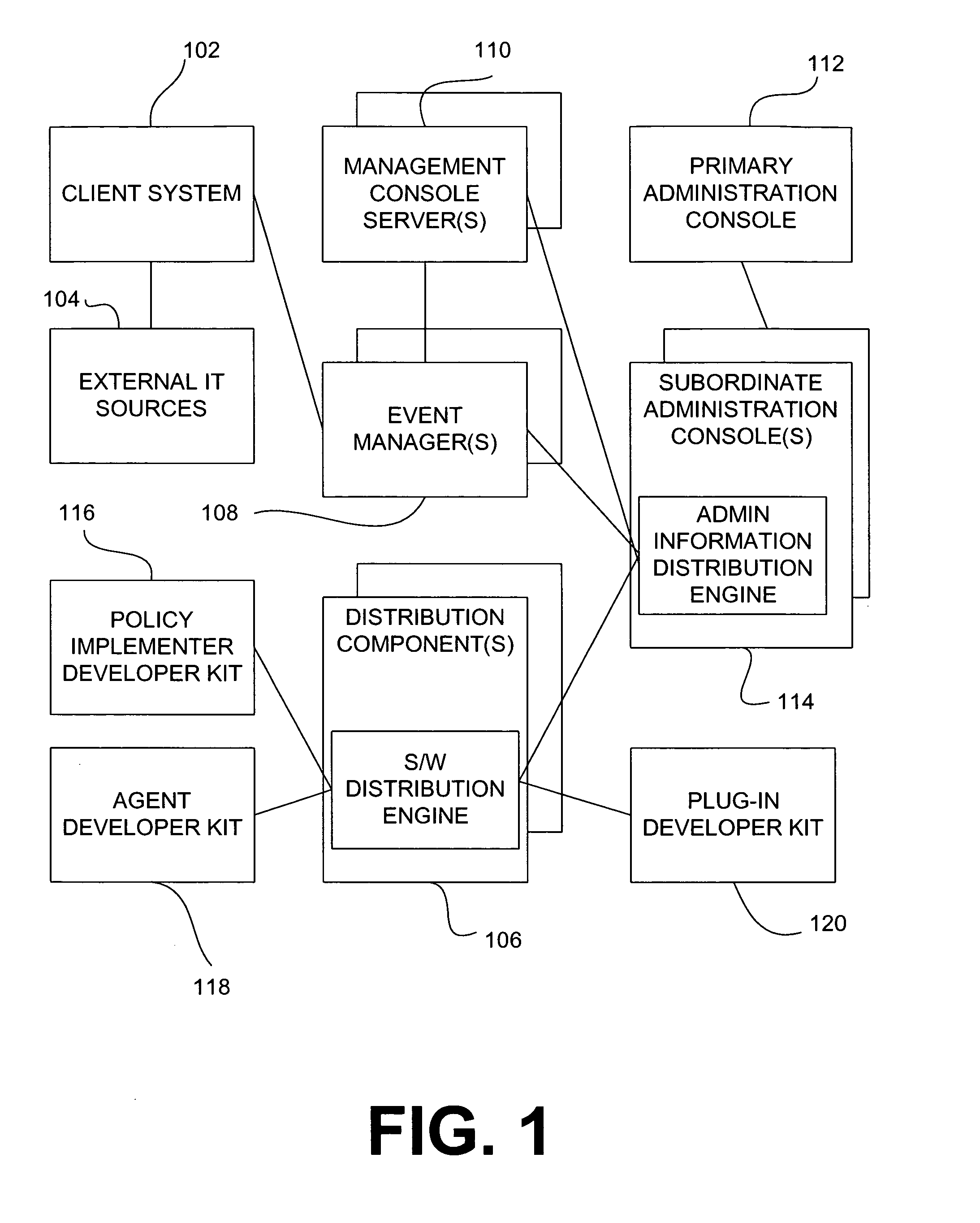
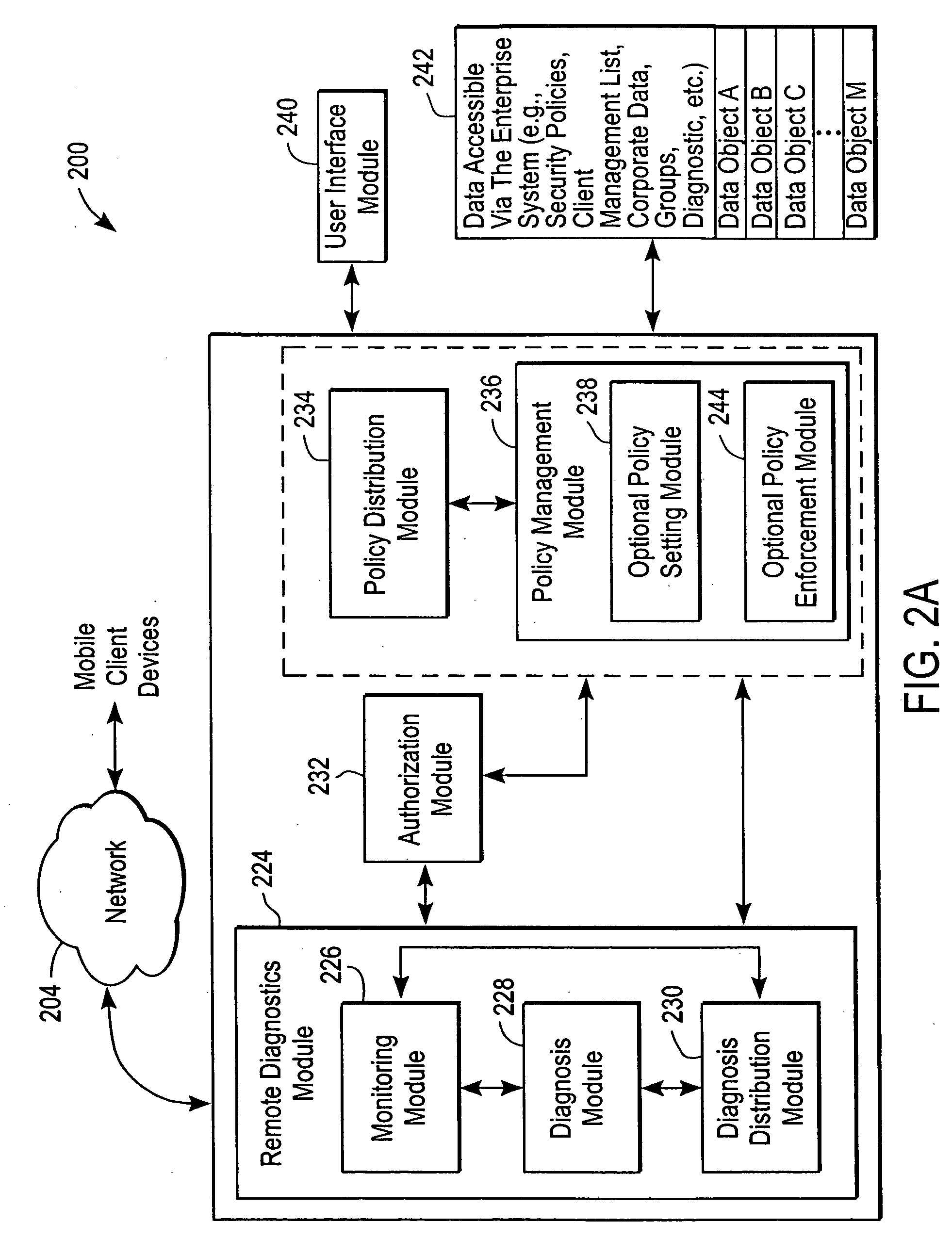
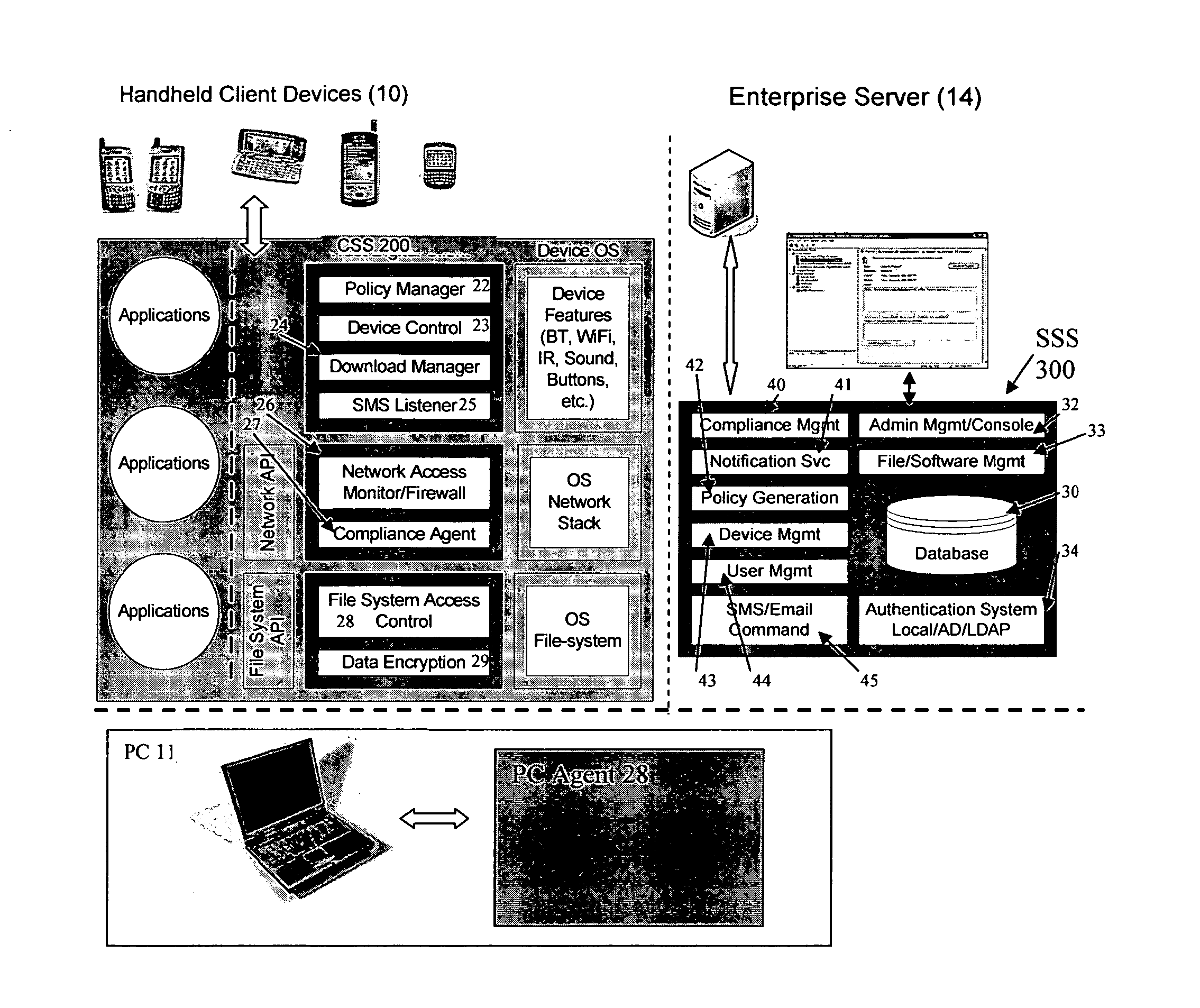
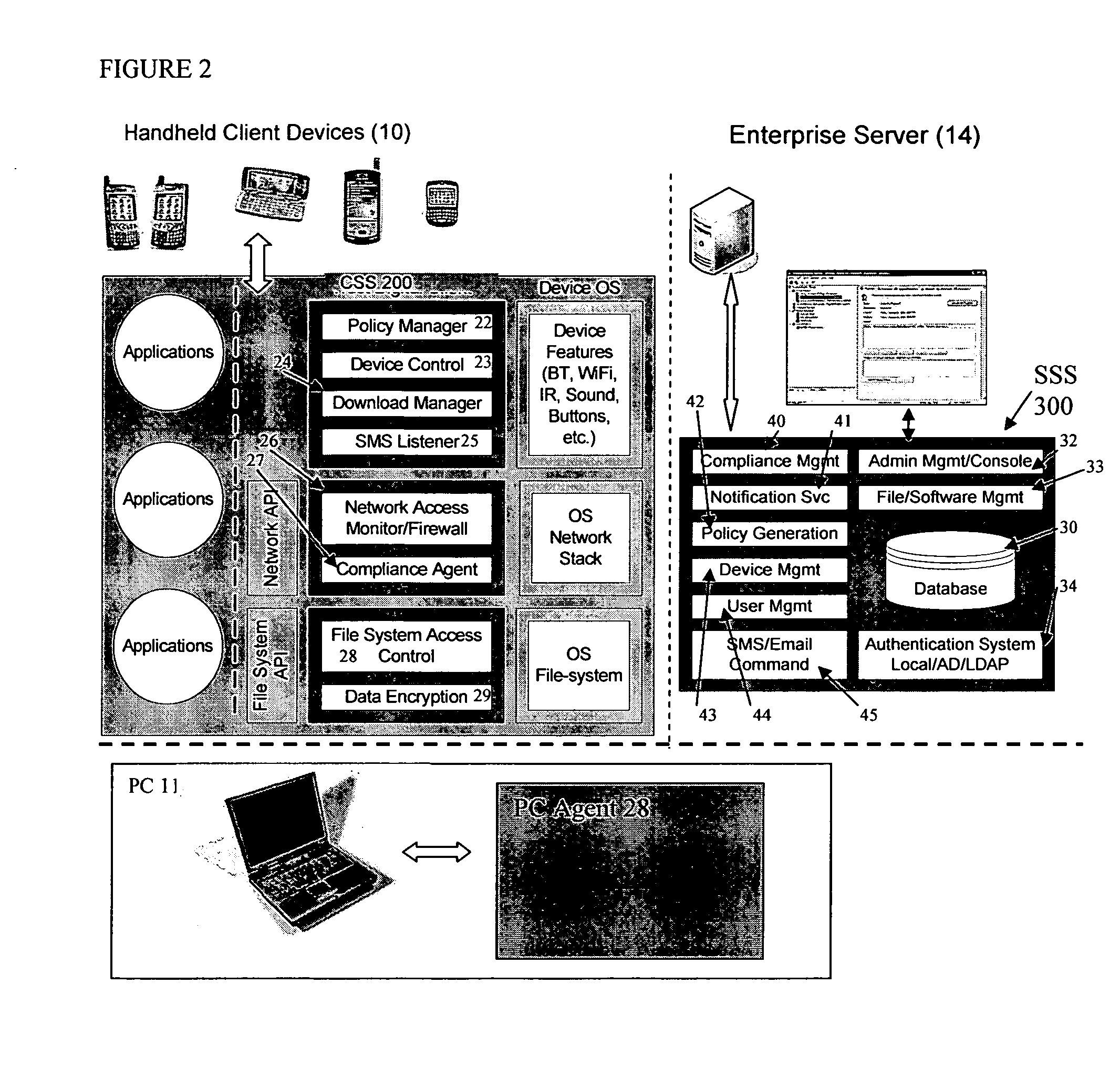
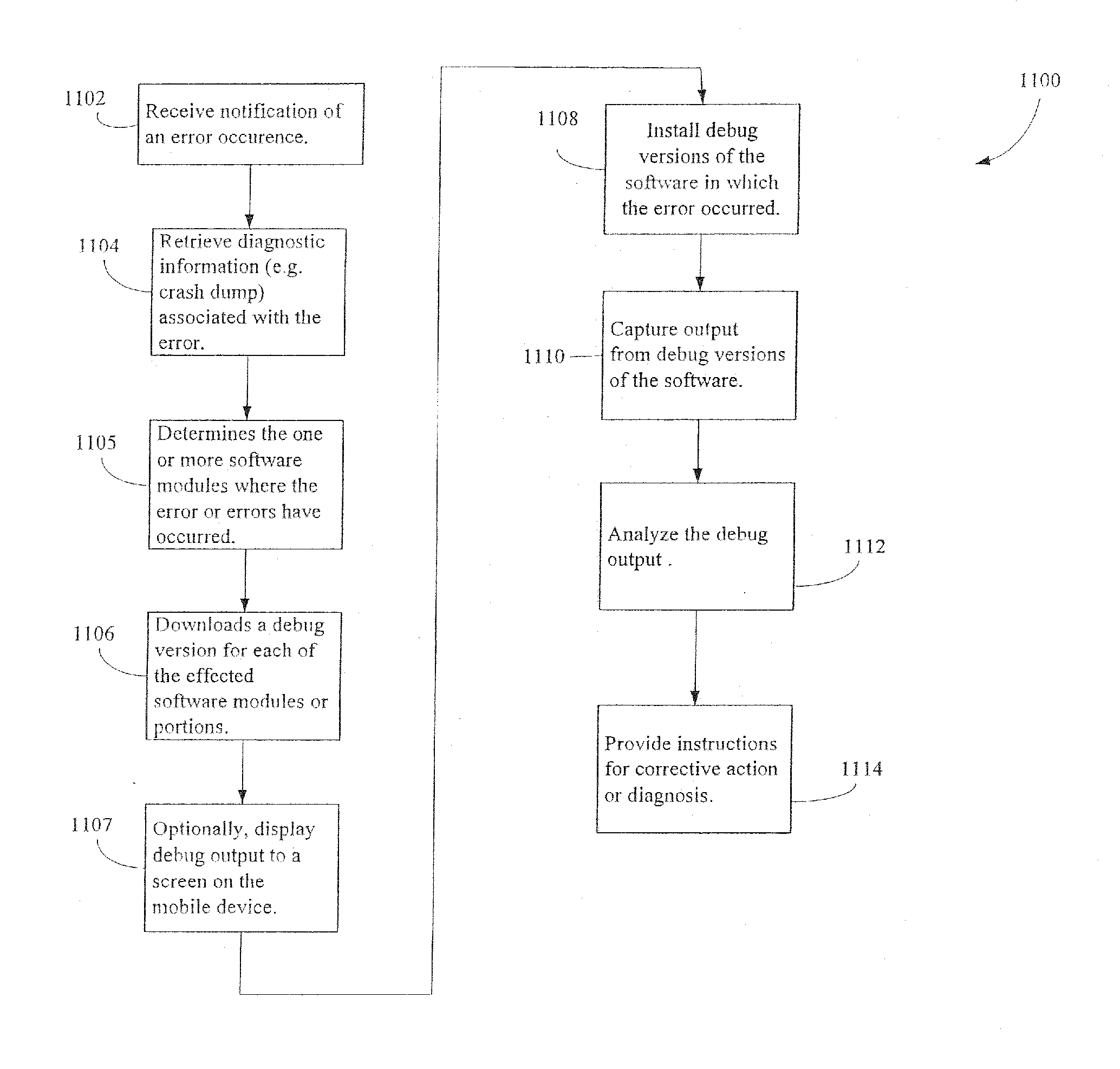
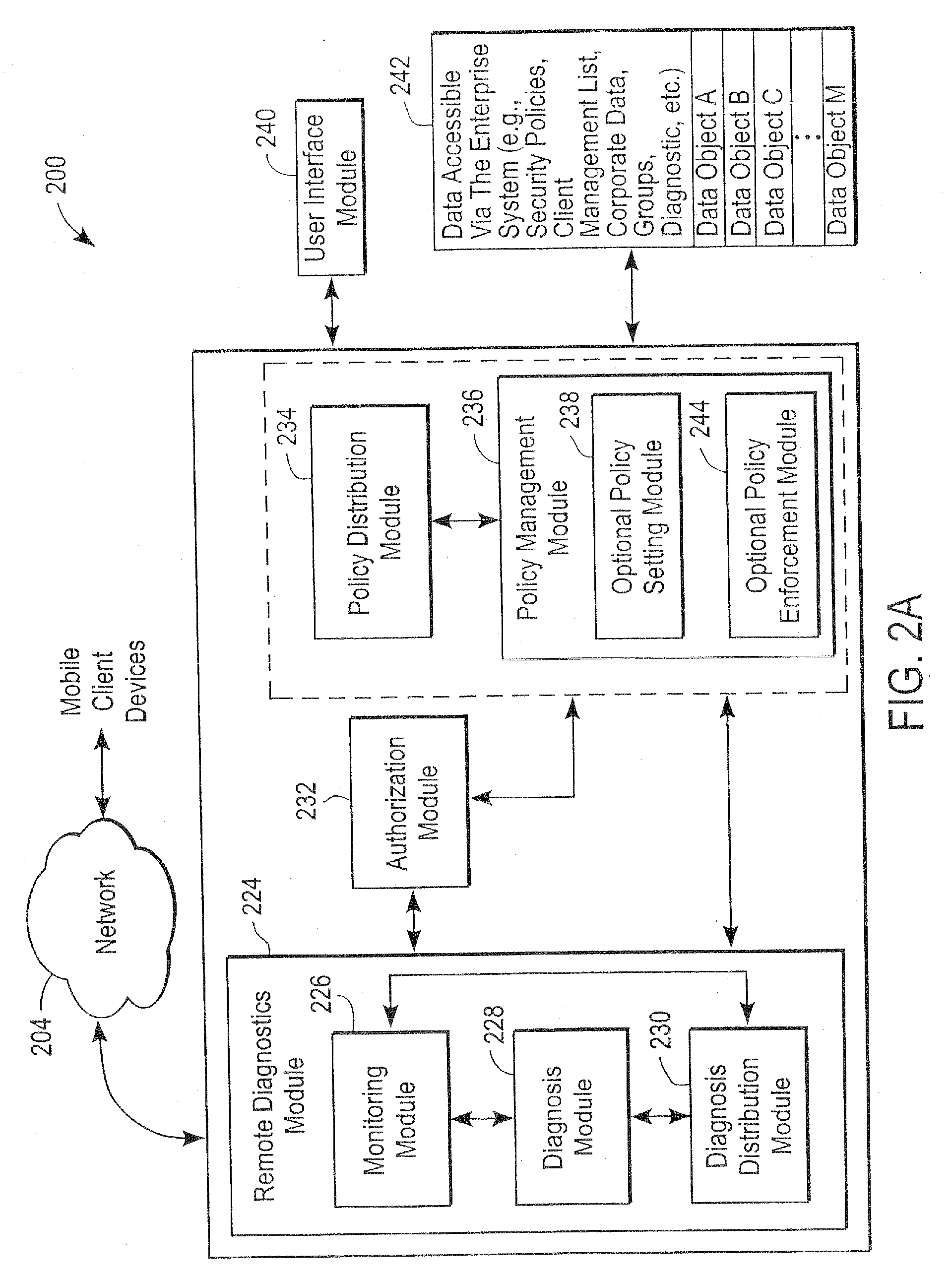
The present invention is directed to security systems and methods for mobile network-based data environments. The present invention provides an integration of security, mobile computing, wireless and IT infrastructure management technology, to create a new level of automation and enforcement to enable the transparent application of mobile security across an enterprise, while embracing end user “transparency” and “ease of use” and empowering IT administration.
Owner:TRUST DIGITAL
Administration of protection of data accessible by a mobile device
The administration of protection of data on a client mobile computing device by a server computer system such as within an enterprise network or on a separate mobile computing device is described. Security tools are described that provide different security policies to be enforced based on a location associated with a network environment in which a mobile device is operating. Methods for detecting the location of the mobile device are described. Additionally, the security tools may also provide for enforcing different policies based on security features. Examples of security features include the type of connection, wired or wireless, over which data is being transferred, the operation of anti-virus software, or the type of network adapter card. The different security policies provide enforcement mechanisms that may be tailored based upon the detected location and / or active security features associated with the mobile device. Examples of enforcement mechanisms are adaptive port blocking, file hiding and file encryption.
Owner:APPLE INC
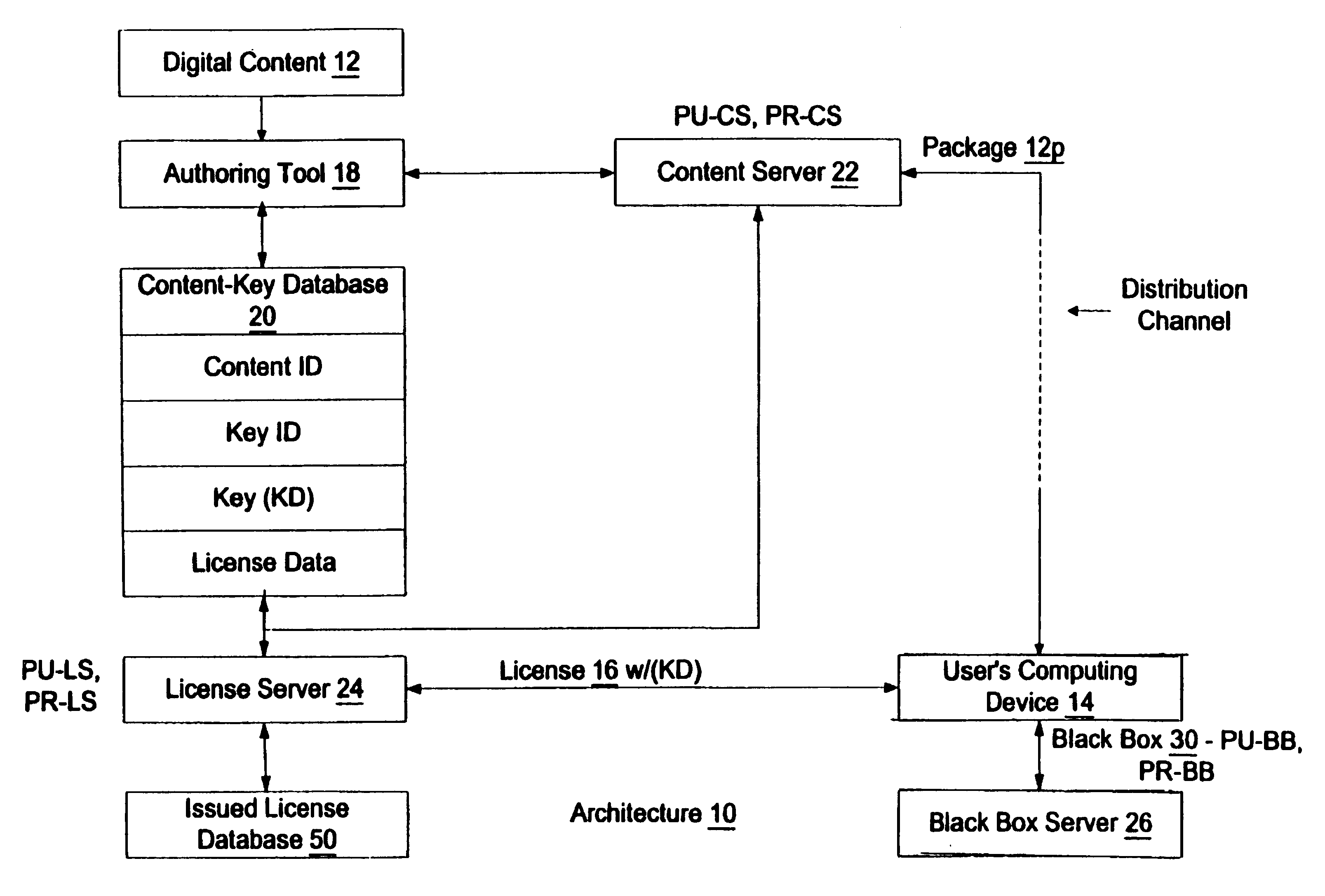
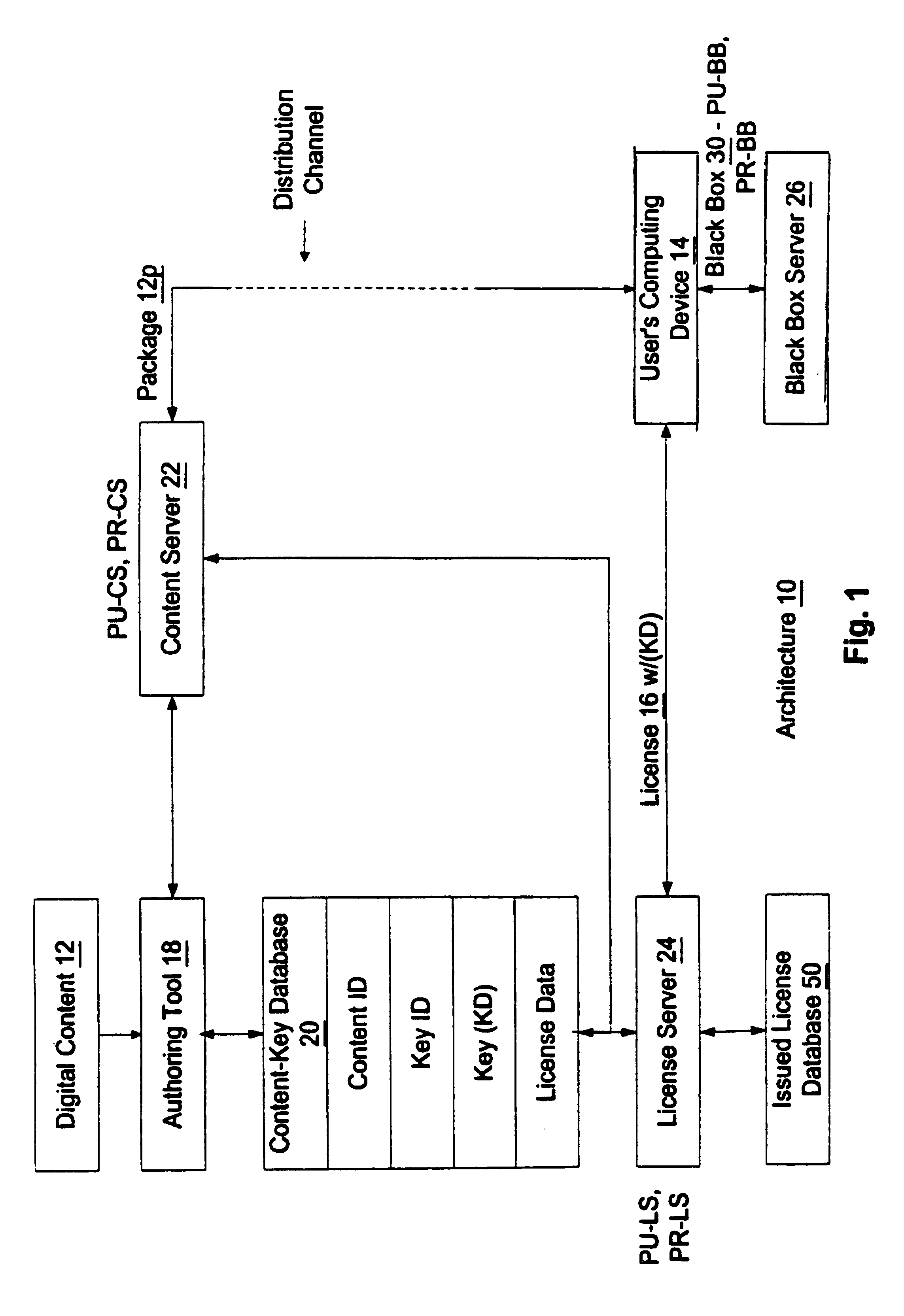
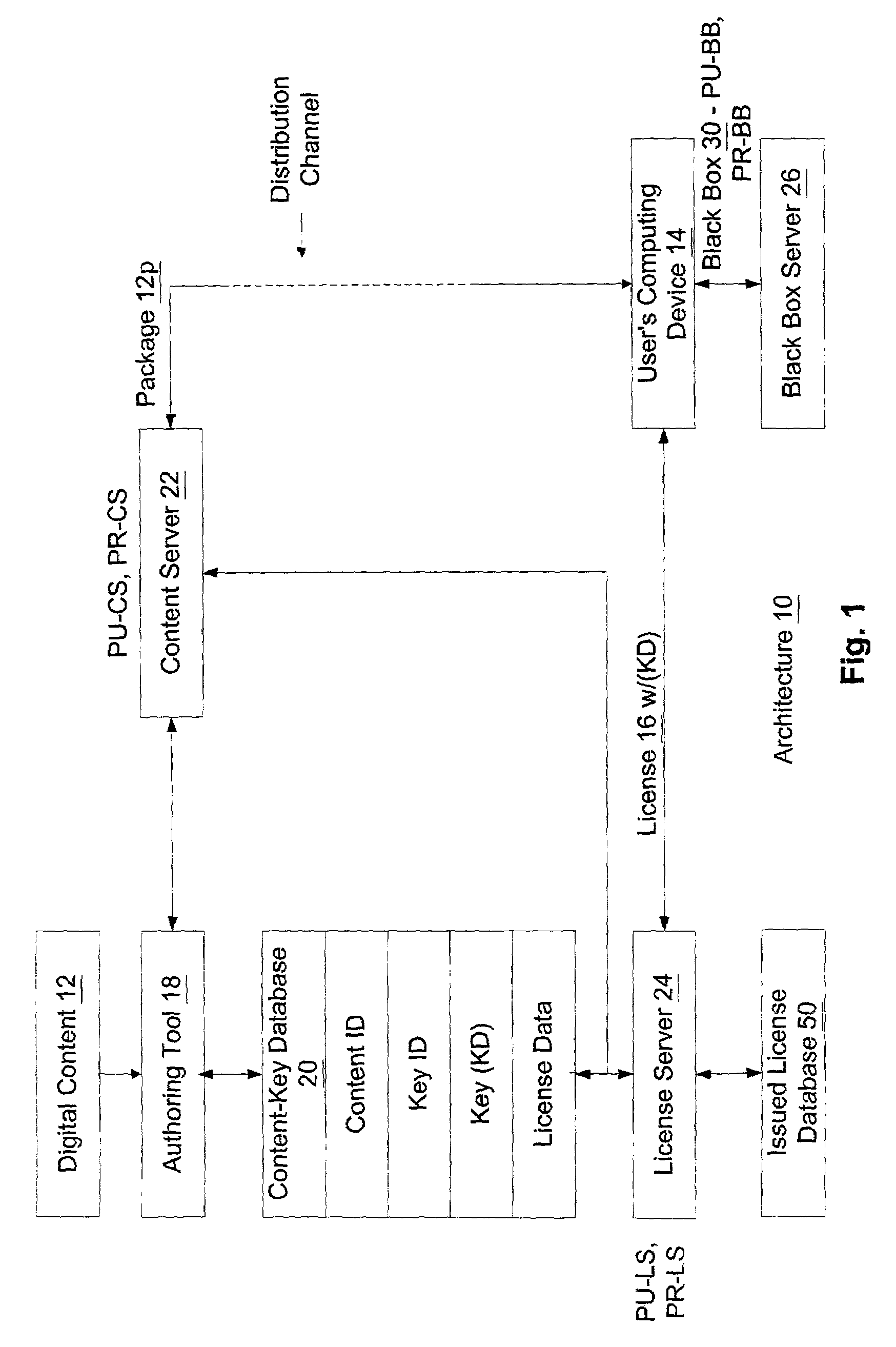
Enforcement architecture and method for digital rights management
InactiveUS7103574B1Satisfies needKey distribution for secure communicationDigital data processing detailsDigital contentNumber content
An enforcement architecture and method for implementing digital rights management are disclosed. Digital content is distributed from a content server to a computing device of a user and received, and an attempt is made to render the digital content by way of a rendering application. The rendering application invokes a Digital Rights Management (DRM) system, and such DRM system determines whether a right to render the digital content in the manner sought exists based on any digital license stored in the computing device and corresponding to the digital content. If the right does not exist, a digital license that provides such right and that corresponds to the digital content is requested from a license server, and the license server issues the digital license to the DRM system. The computing device receives the issued digital license and stores the received digital license thereon.
Owner:MICROSOFT TECH LICENSING LLC
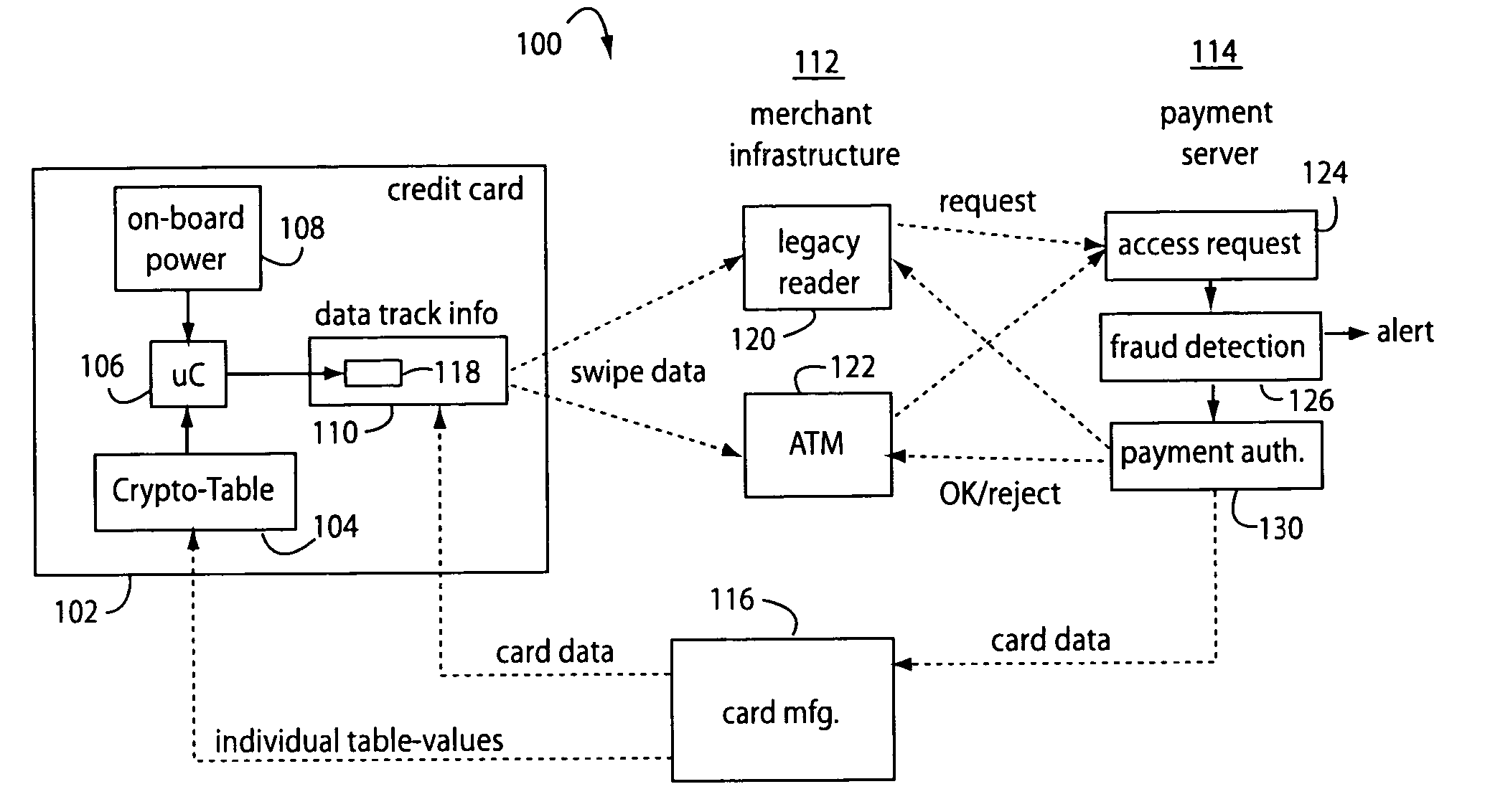
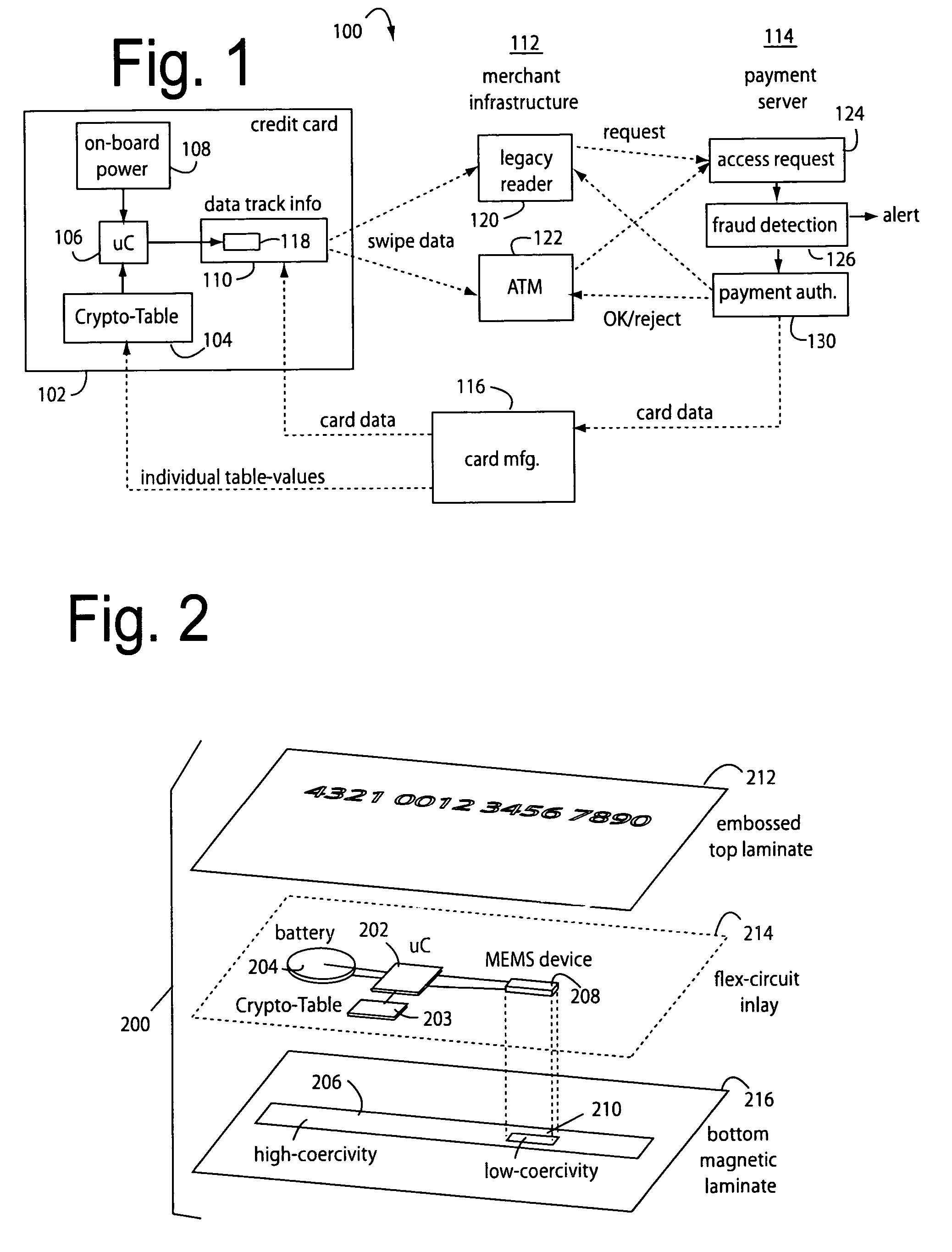
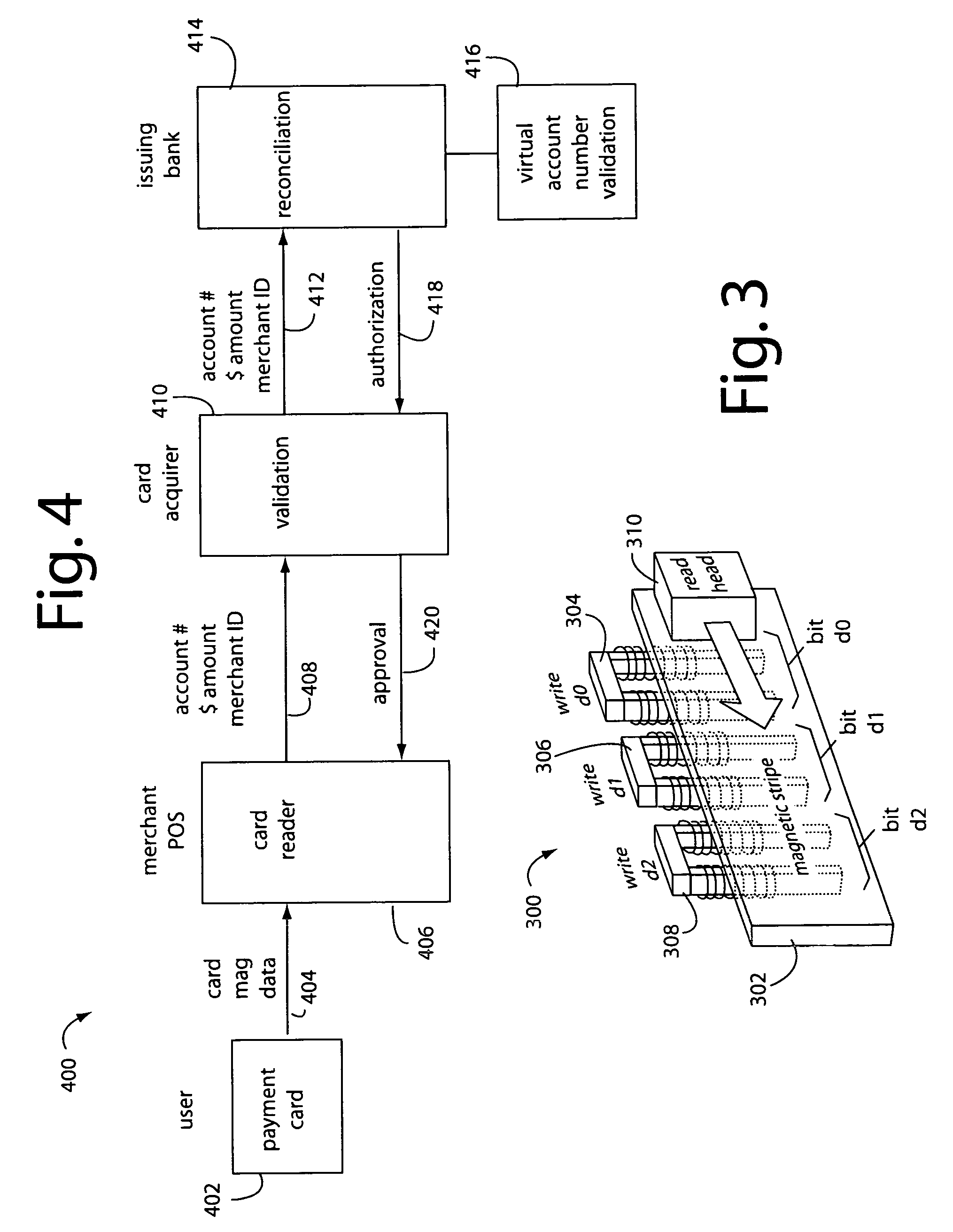
Automated payment card fraud detection and location
A payment card fraud detection business model comprises an internal virtual account number generator and a user display for Card-Not-Present transactions. Card-Present transactions with merchant card readers are enabled by a magnetic array internally associated with the card's magnetic stripe. The internal virtual account number generator is able to reprogram some of the magnetic bits encoded in the magnetic stripe to reflect the latest virtual account number. The internal virtual account number generator produces a sequence of virtual numbers that can be predicted and approved by the issuing bank. Once a number is used, such is discarded and put on an exclusion list or reserved for a specific merchant until the expiration date. A server for the issuing bank logs the merchant locations associated with each use or attempted use, and provides real-time detection of fraudulent attempts to use a virtual account number on the exclusion list. Law enforcement efforts can then be directed in a timely and useful way not only where the fraud occurs but also at its origination.
Owner:FITBIT INC
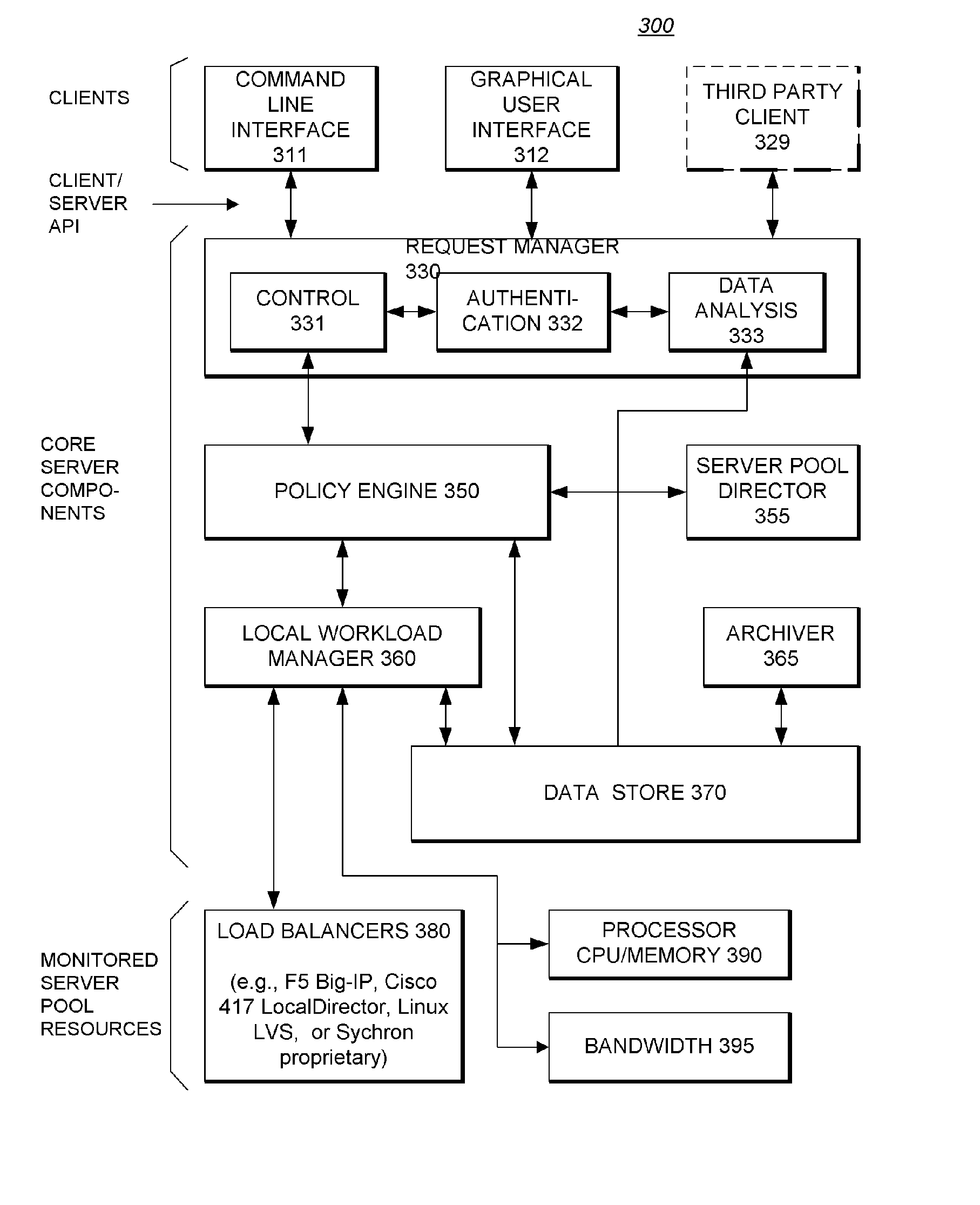
System Providing Methodology for Policy-Based Resource Allocation
A system providing methodology for policy-based resource allocation is described. In one embodiment, for example, a system for allocating computer resources amongst a plurality of applications based on a policy is described that comprises: a plurality of computers connected to one another through a network; a policy engine for specifying a policy for allocation of resources of the plurality of computers amongst a plurality of applications having access to the resources; a monitoring module at each computer for detecting demands for the resources and exchanging information regarding demands for the resources at the plurality of computers; and an enforcement module at each computer for allocating the resources amongst the plurality of applications based on the policy and information regarding demands for the resources.
Owner:CAVALIER NEWCO +1
Administration of protection of data accessible by a mobile device
The protection of data on a client mobile computing device by a server computer system such as within an enterprise network or on a separate mobile computing device is described. Security tools are described that provide different security policies to be enforced based on a location associated with a network environment in which a mobile device is operating. Methods for detecting the location of the mobile device are described. Additionally, the security tools may also provide for enforcing different policies based on security features. Examples of security features include the type of connection, wired or wireless, over which data is being transferred, the operation of anti-virus software, or the type of network adapter card. The different security policies provide enforcement mechanisms that may be tailored based upon the detected location and / or active security features associated with the mobile device. Examples of enforcement mechanisms are adaptive port blocking, file hiding and file encryption.
Owner:APPLE INC
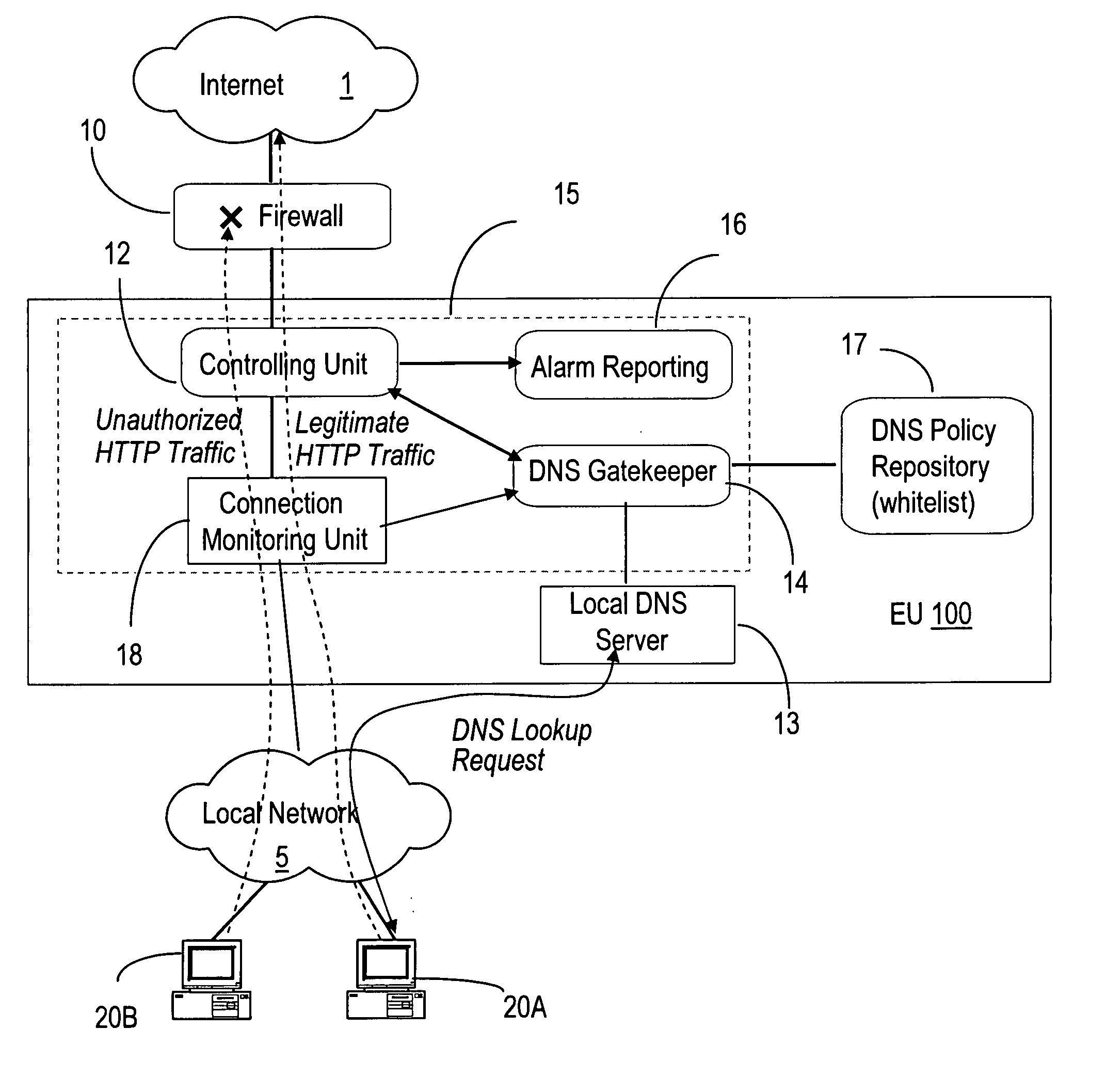
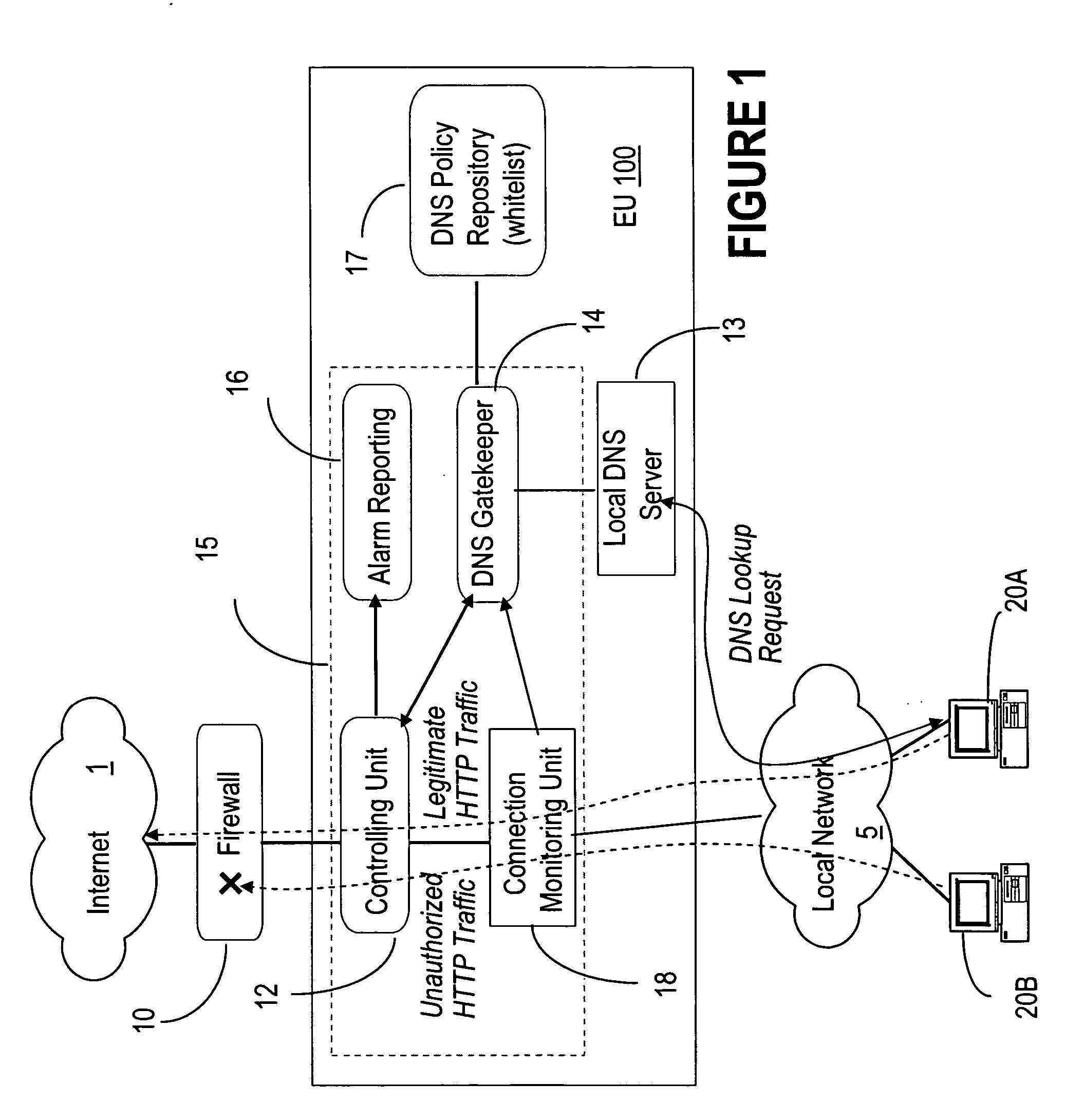
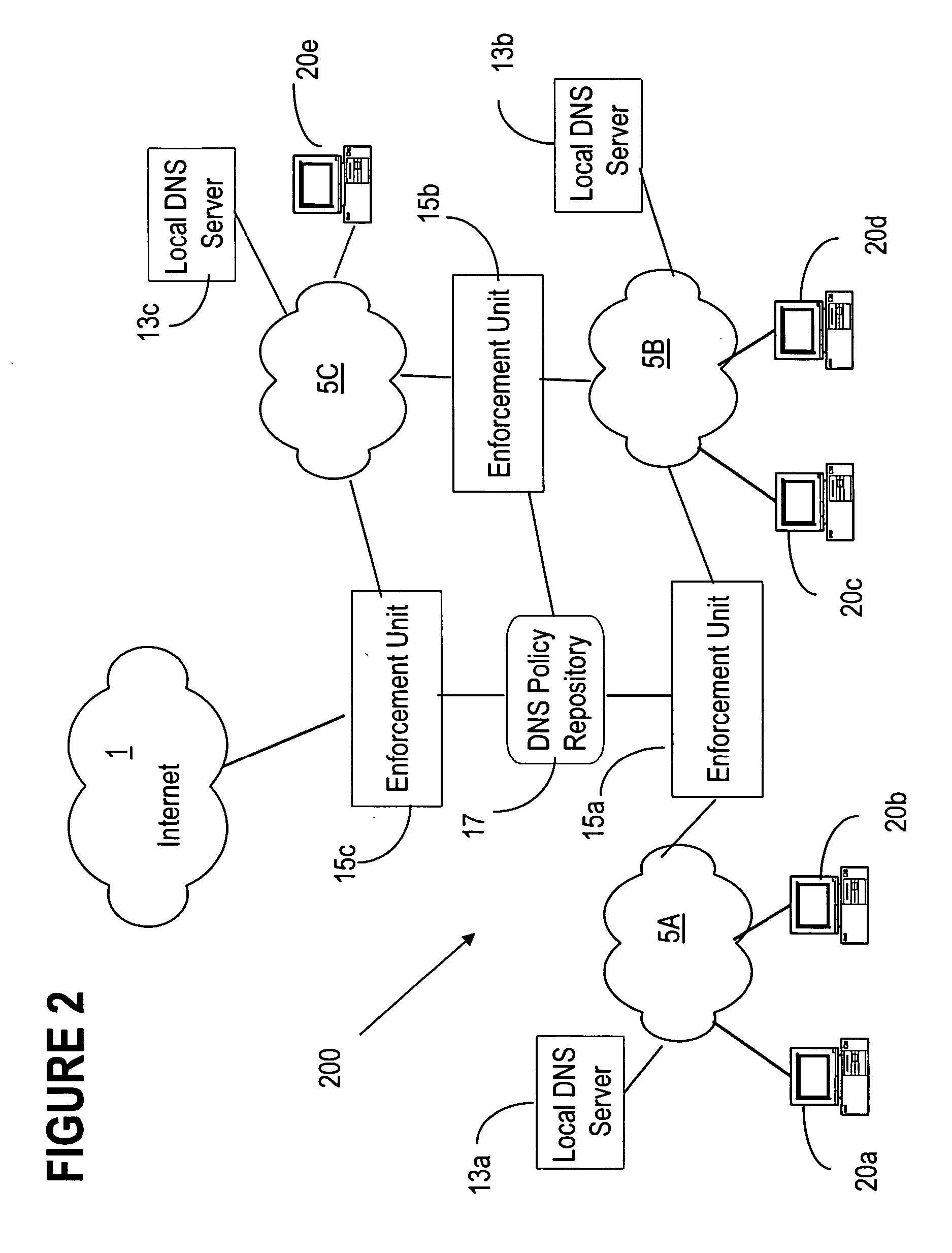
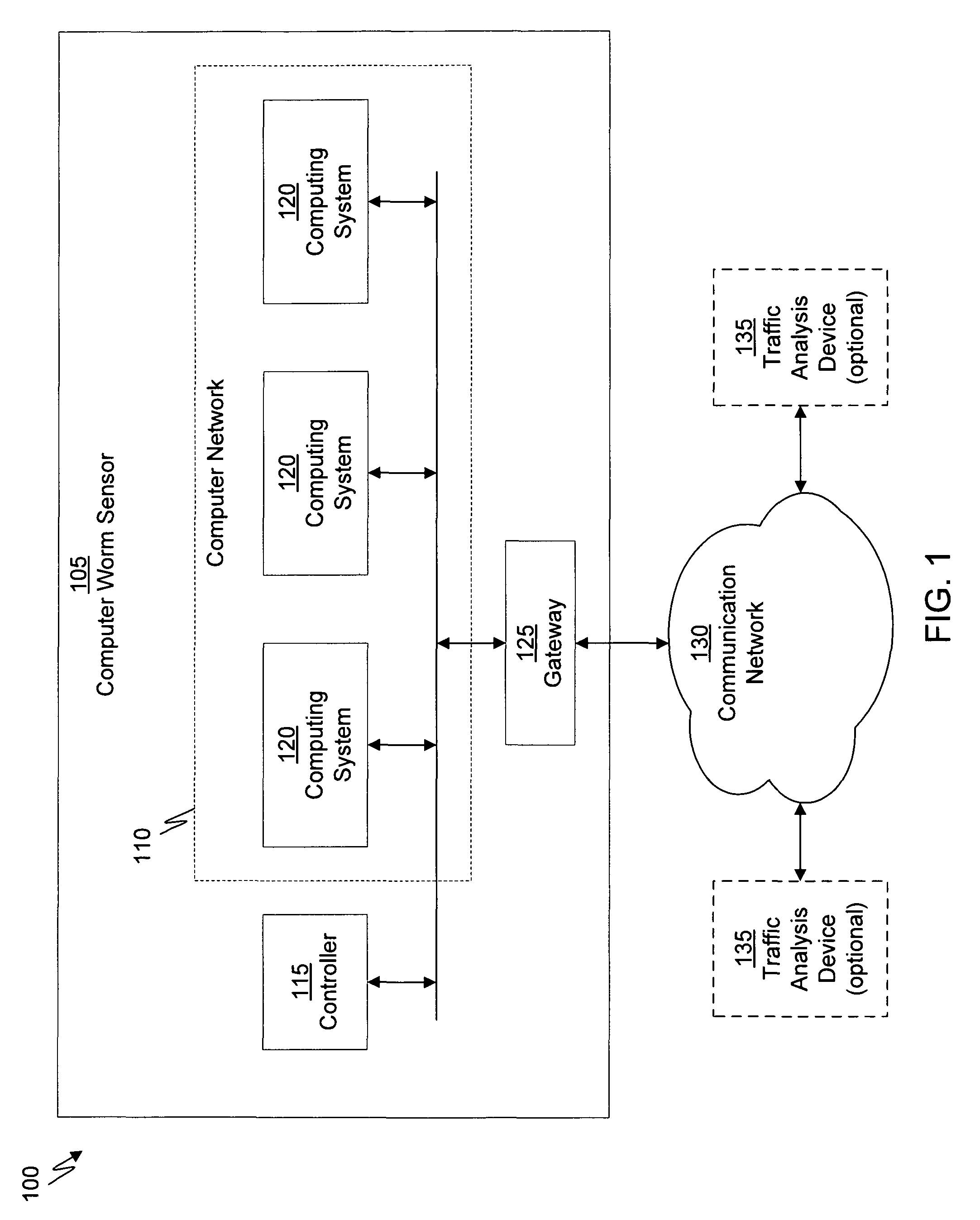
DNS based enforcement for confinement and detection of network malicious activities
InactiveUS20070033645A1Avoid detectionAvoid spreadingDigital data processing detailsUnauthorized memory use protectionDomain nameNetwork activity
Malicious network activities do not make use of the Domain Name System (DNS) protocol to reach remote targets outside a local network. This DNS-based enforcement system for confinement and detection of network malicious activities requires that every connection toward a resource located outside the local network is blocked by default by the local enforcement box, e.g. a firewall or a proxy. Outbound connections are allowed to leave the local network only when authorized directly by an entity called the DNS Gatekeeper.
Owner:RPX CORP
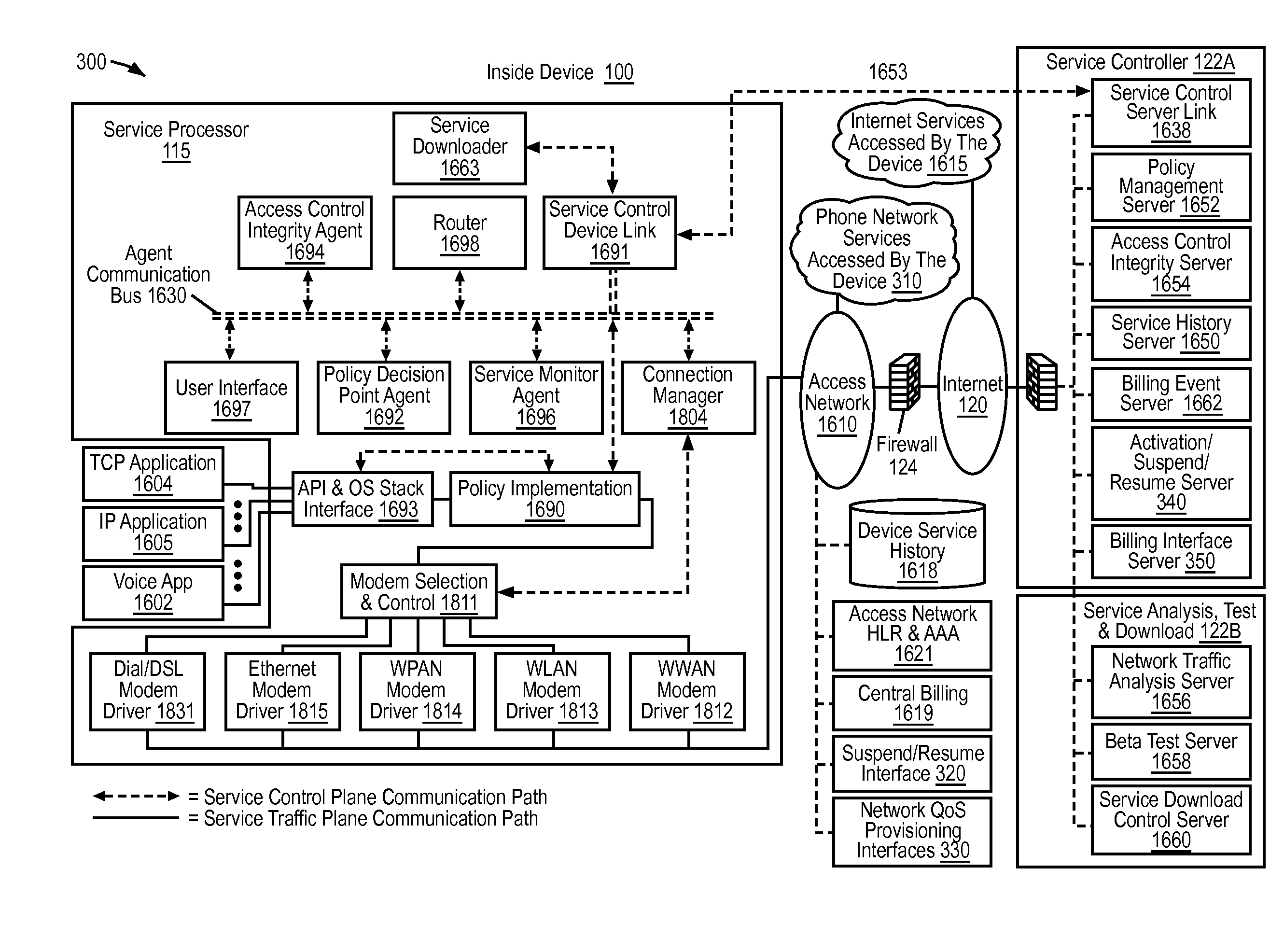
End user device that secures an association of application to service policy with an application certificate check
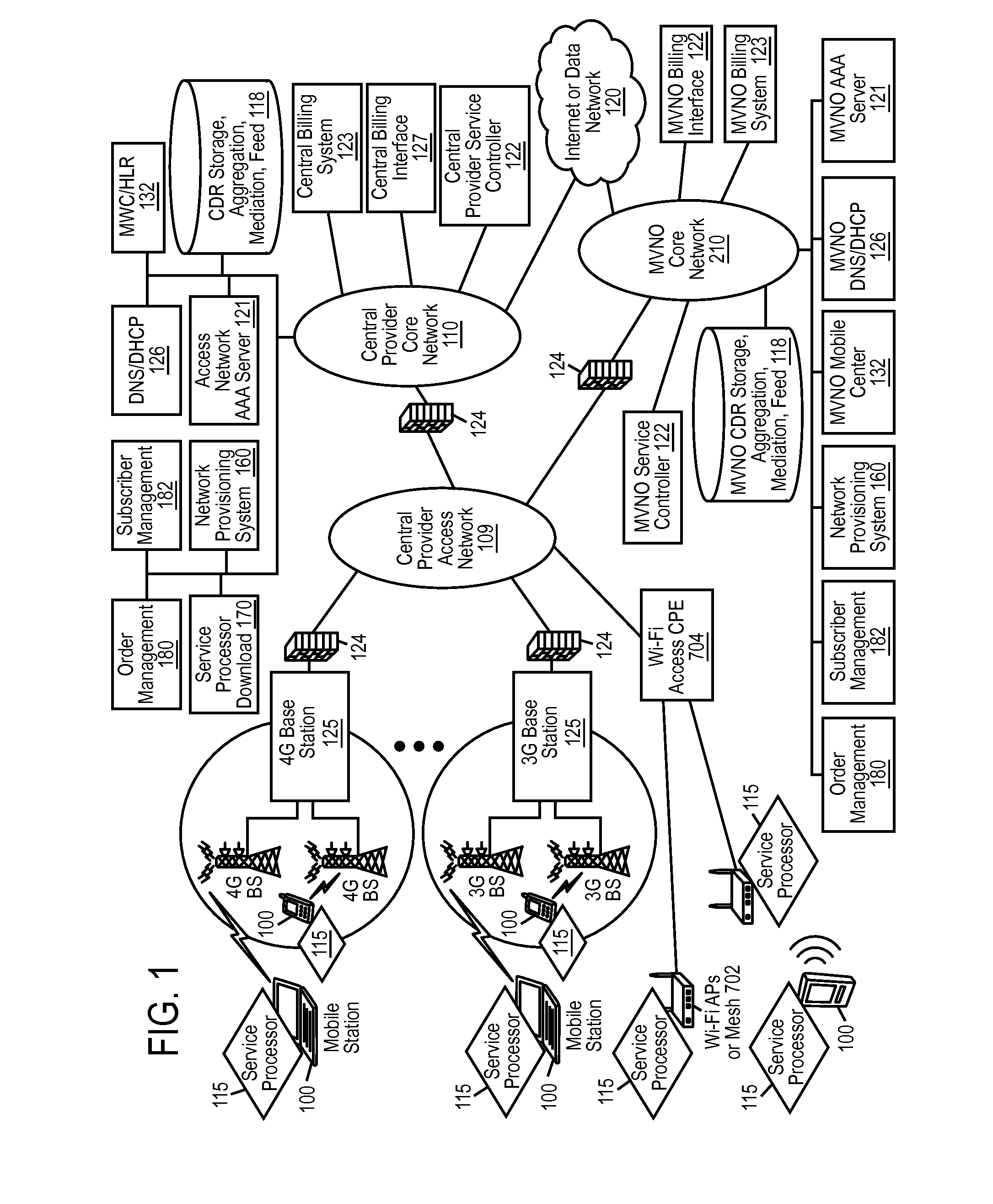
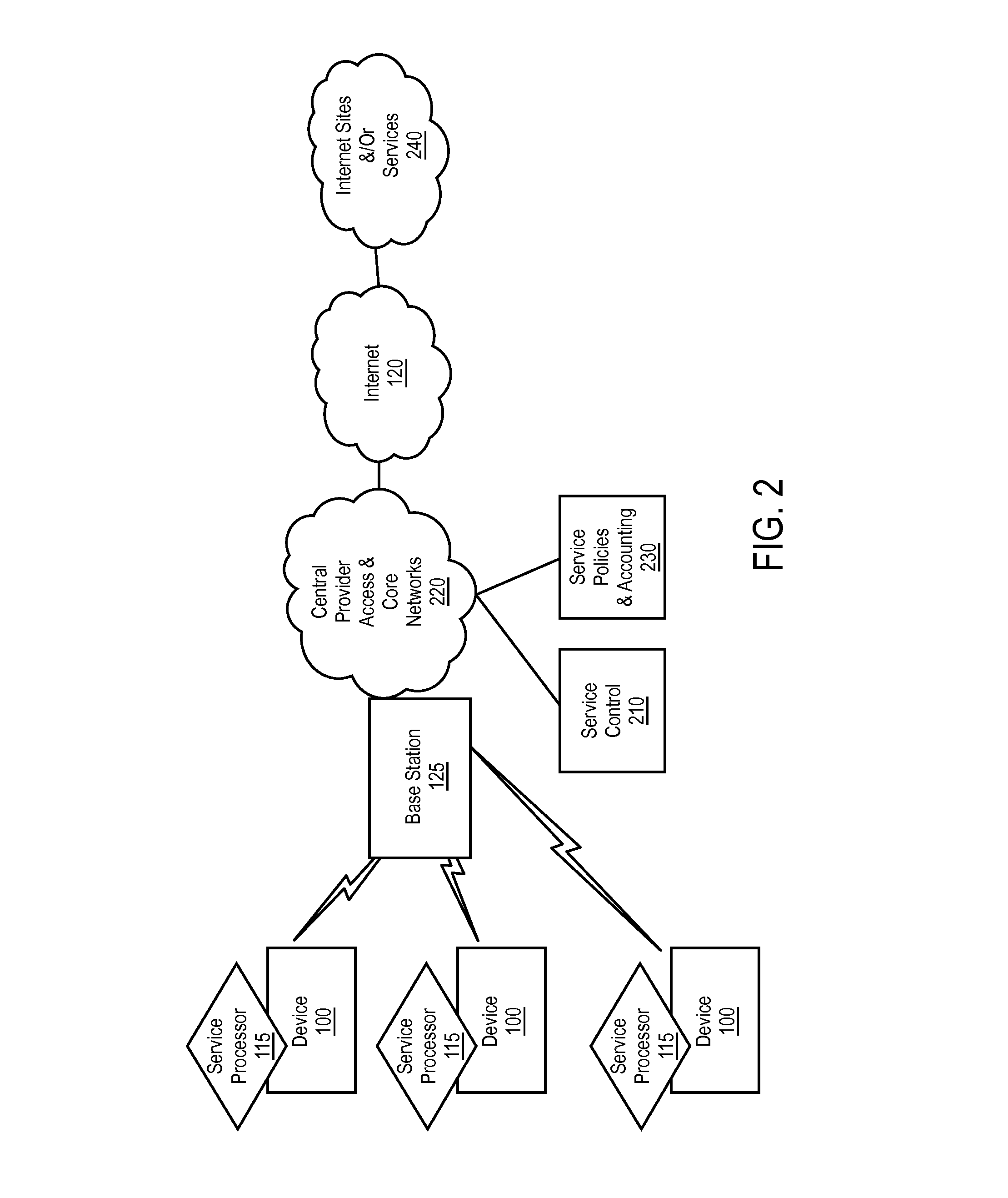
ActiveUS20120221955A1Input/output for user-computer interactionAccounting/billing servicesTraffic capacityApplication software
Network service provisioning is described. Network service provisioning to a device includes a mechanism for ensuring that network services are available based upon one or more of appropriate traffic control, billing, and notification policies. Ensuring that the policies are properly enforced on a device is a focus of this paper. The enforcement policies can be on the device or in the network.
Owner:HEADWATER RES LLC
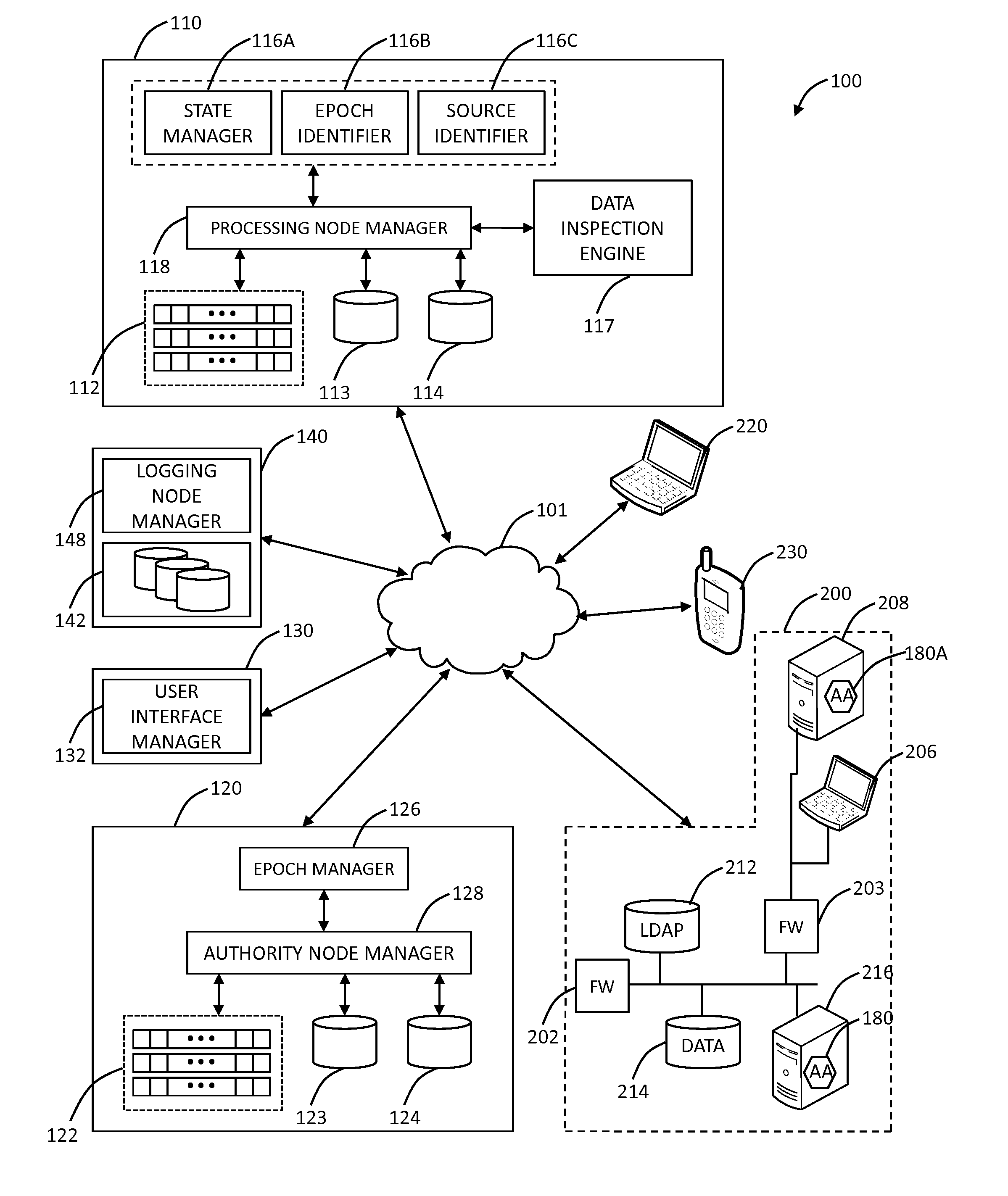
Systems and methods for mobile application security classification and enforcement
ActiveUS20110167474A1Avoid forwardingMemory loss protectionError detection/correctionUser deviceThe Internet
The present disclosure provides systems and methods for mobile application security classification and enforcement. In particular, the present invention includes a method, a mobile device, and a distributed security system (e.g., a “cloud”) that is utilized to enforce security on mobile devices communicatively coupled to external networks (i.e., the Internet). Advantageously, the present invention is platform independent allowing it to operate with any current or emerging mobile device. Specifically, preventing malicious applications from running on an end user's mobile device is challenging with potentially millions of applications and billions of user devices; the only effective way to enforce application security is through the network that applications use to communicate.
Owner:ZSCALER INC
Mobile data security system and methods
ActiveUS8495700B2Transparent applicationUnauthorised/fraudulent call preventionEavesdropping prevention circuitsMobile securityMobile Web
The present invention is directed to security systems and methods for mobile network-based data environments. The present invention provides an integration of security, mobile computing, wireless and IT infrastructure management technology, to create a new level of automation and enforcement to enable the transparent application of mobile security across an enterprise, while embracing end user “transparency” and “ease of use” and empowering IT administration.
Owner:TRUST DIGITAL
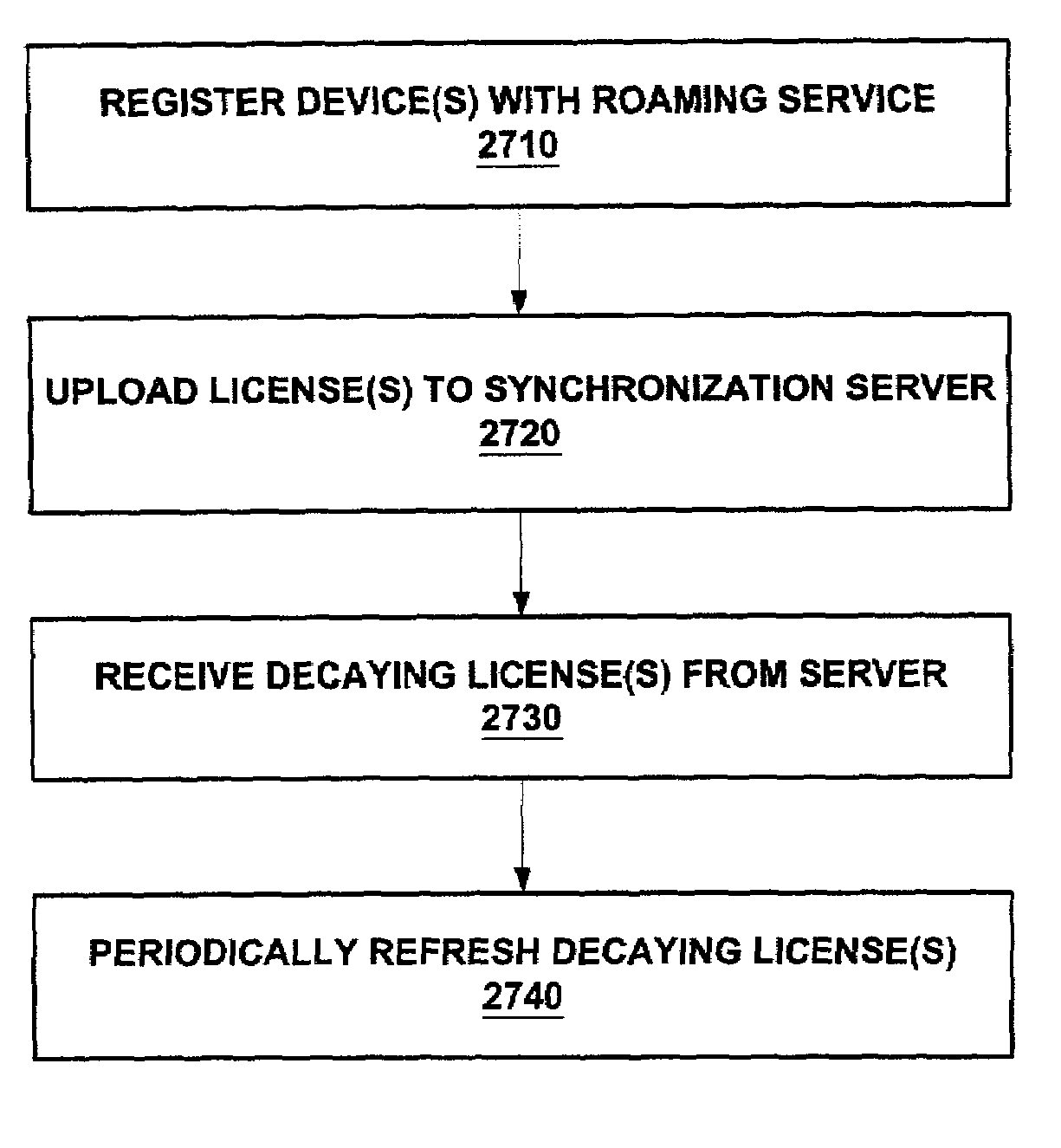
Enforcement architecture and method for digital rights management system for roaming a license to a plurality of user devices
InactiveUS7203966B2Prevent long-term misusePrevent long-term misuse of the systemDigital data processing detailsUnauthorized memory use protectionUser deviceDevice register
An enforcement architecture and method for implementing roaming digital rights management are disclosed. A license distributed from a license server to a computing device of a user may be uploaded to a license synchronization server, and rebound to other devices registered with the service, thereby enabling access to the licensed content from other computing devices. A second digital license of a second computing device is set to expire prior to a first digital license of a first computing device. Reactivating a decayed first digital license, that is deactivated during transmission of the second digital license, to the second device to access content of the first computing device.
Owner:MICROSOFT TECH LICENSING LLC
Systems and methods for mobile application security classification and enforcement
The present disclosure provides systems and methods for mobile application security classification and enforcement. In particular, the present invention includes a method, a mobile device, and a distributed security system (e.g., a “cloud”) that is utilized to enforce security on mobile devices communicatively coupled to external networks (i.e., the Internet). Advantageously, the present invention is platform independent allowing it to operate with any current or emerging mobile device. Specifically, preventing malicious applications from running on an end user's mobile device is challenging with potentially millions of applications and billions of user devices; the only effective way to enforce application security is through the network that applications use to communicate.
Owner:ZSCALER INC
Dynamic signature creation and enforcement
Owner:FIREEYE SECURITY HLDG US LLC
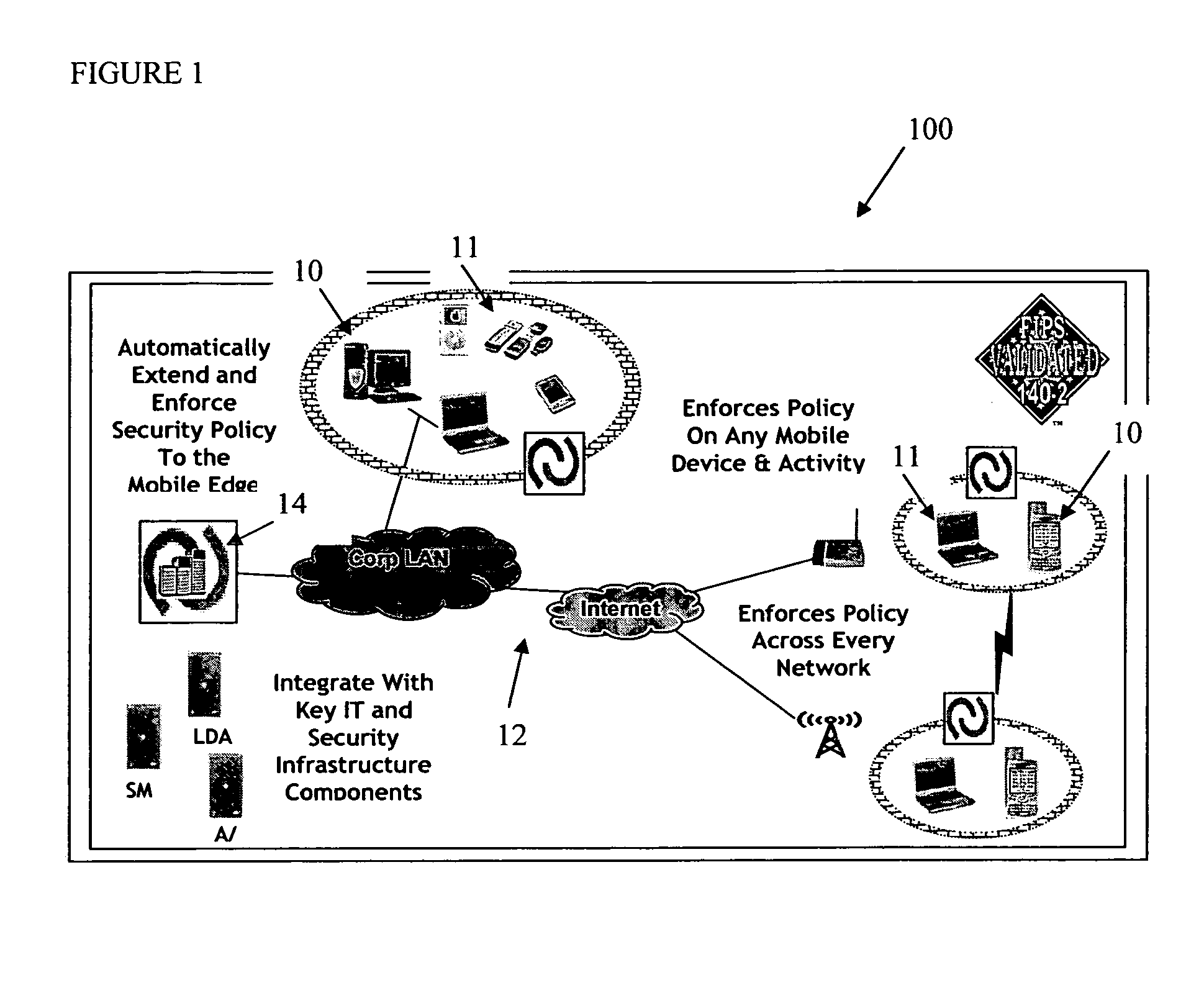
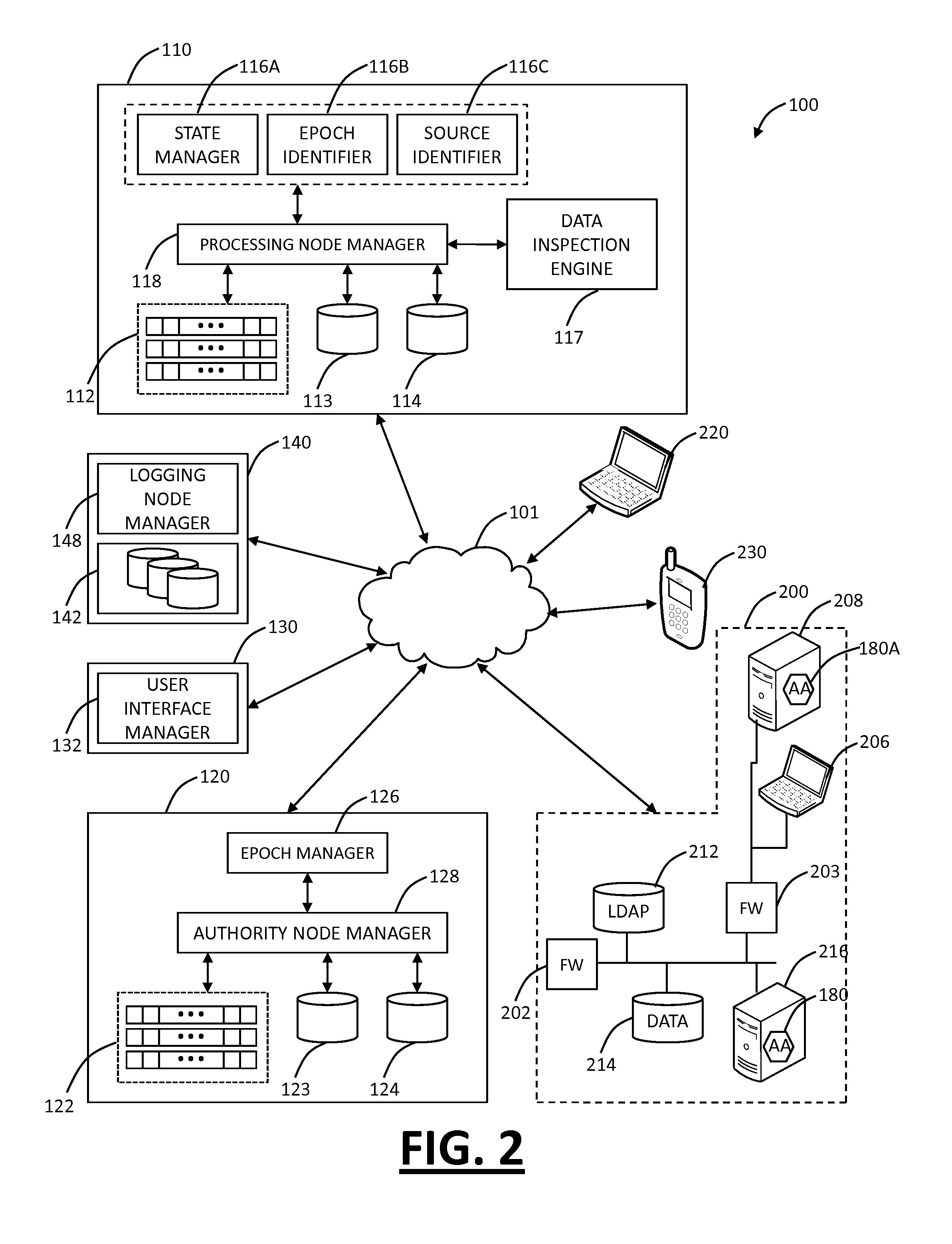
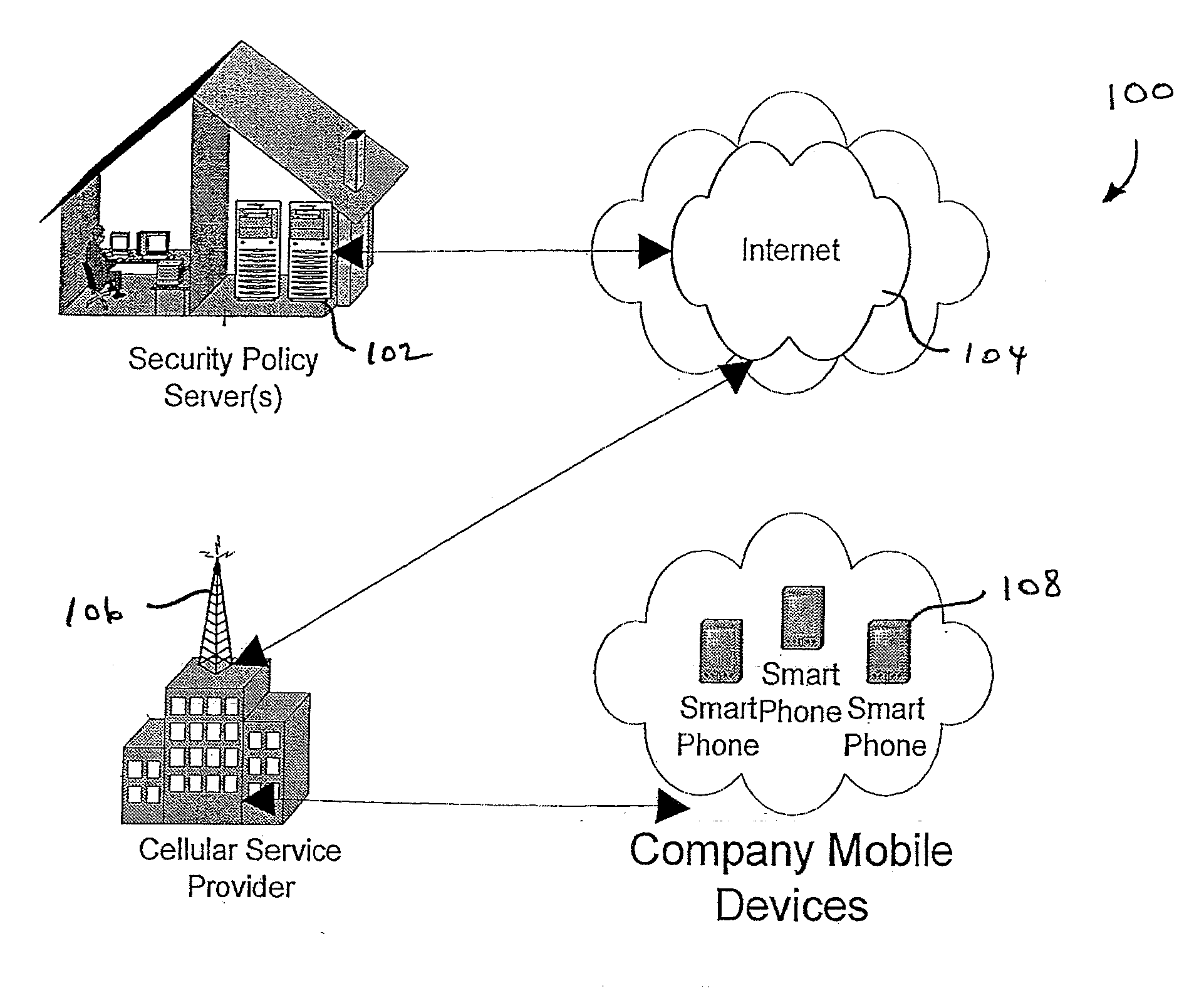
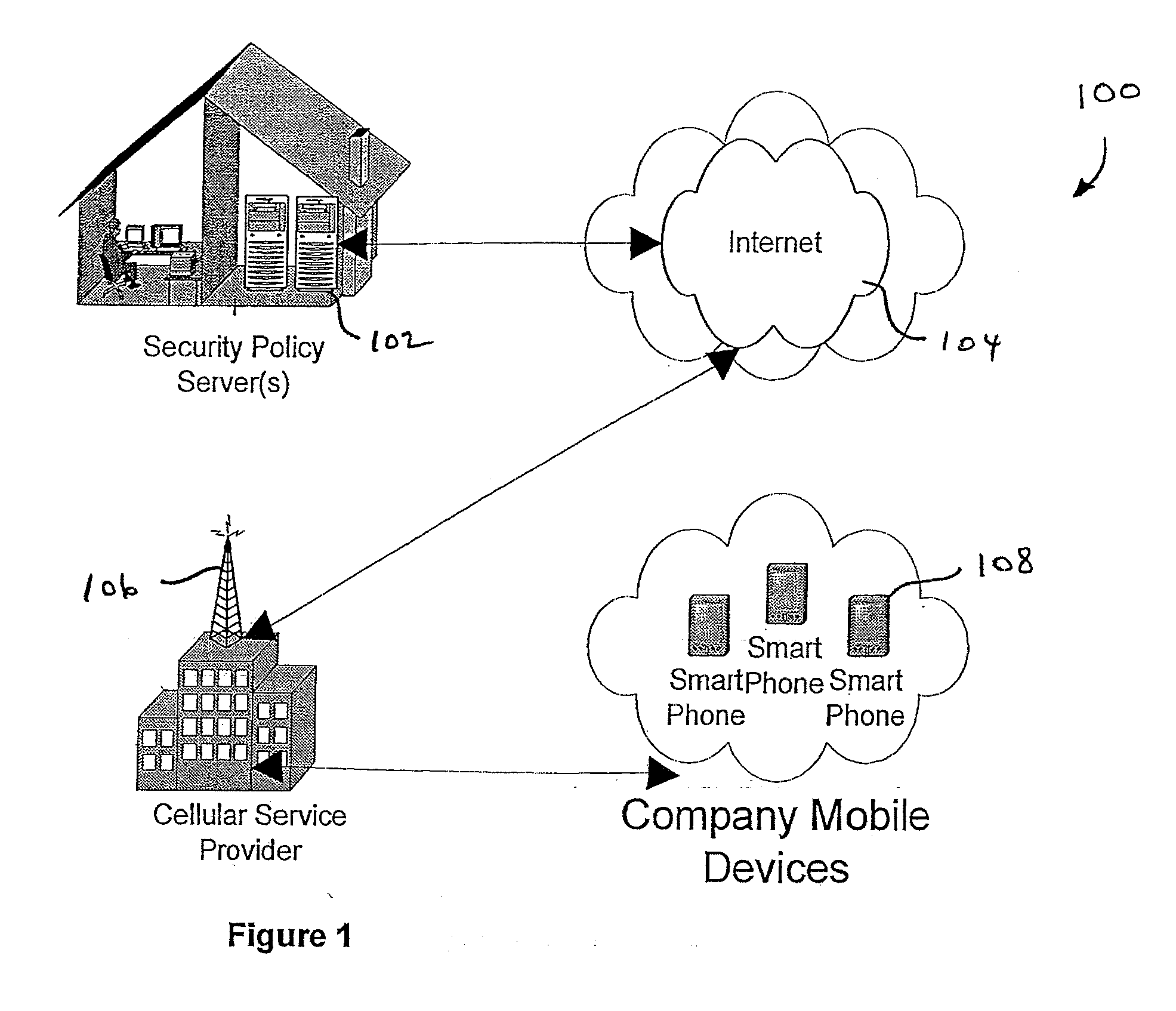
Centralized Dynamic Security Control for a Mobile Device Network
InactiveUS20070266422A1Well formedSecurity arrangementSpecial data processing applicationsTimerSecurity system
An security system for an enterprise network and data automates the revision, deployment, enforcement, auditing and control of security policies on mobile devices connected to said enterprise network, through automated communication between a security policy server and the mobile device. Control of the security system is centralized through administrative control of security policies stored on the security policy server. Automation of deployment of security policies to mobile devices occurs through transparent background communication and transfer of updated policies either triggered by a change in a security policy within the central repository of security policies or upon the expiration of a certain time period during which no policies were downloaded to the mobile device. When the mobile device is not in compliance with a security policy, a software security agent operating thereon limits access to said enterprise network and enterprise data. To aid in preventing the overwhelming of the enterprise network and the security policy server as a result of to many synchronization communications coming from too many mobile devices, a randomized timer is set by the software security agent upon receipt by the mobile device of a synchronization command from the security policy server.
Owner:SQUARE 1 BANK
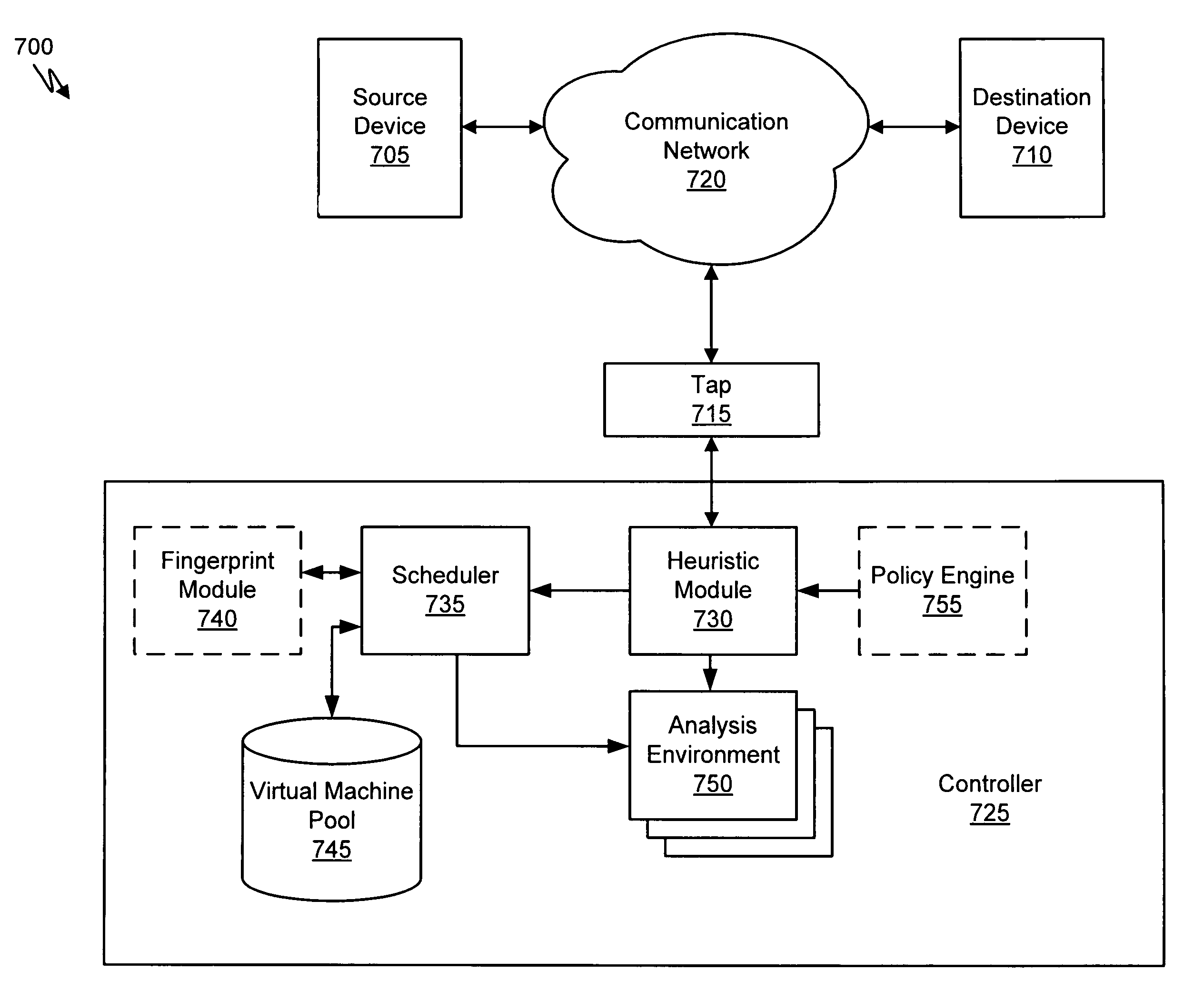
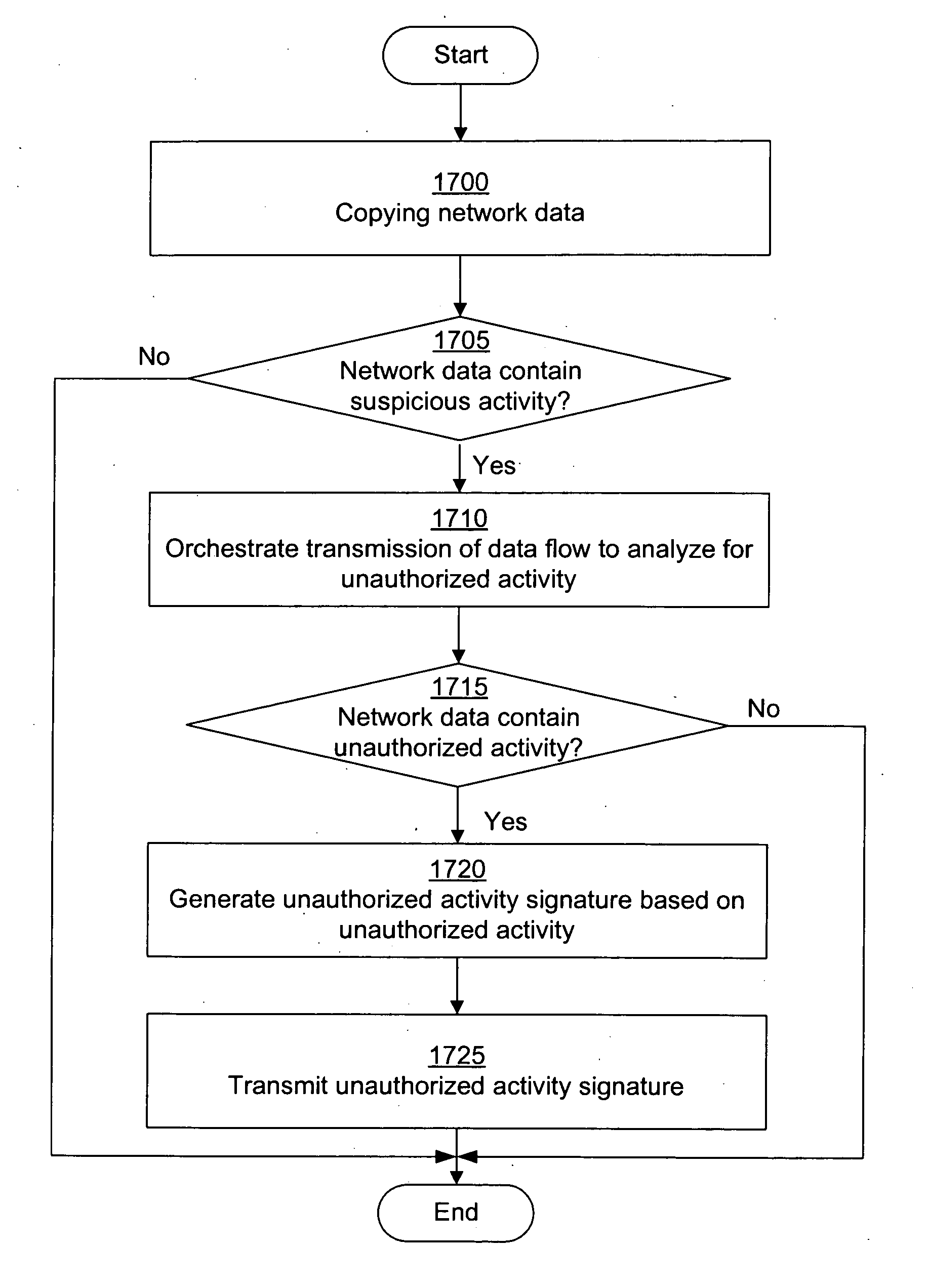
Dynamic signature creation and enforcement
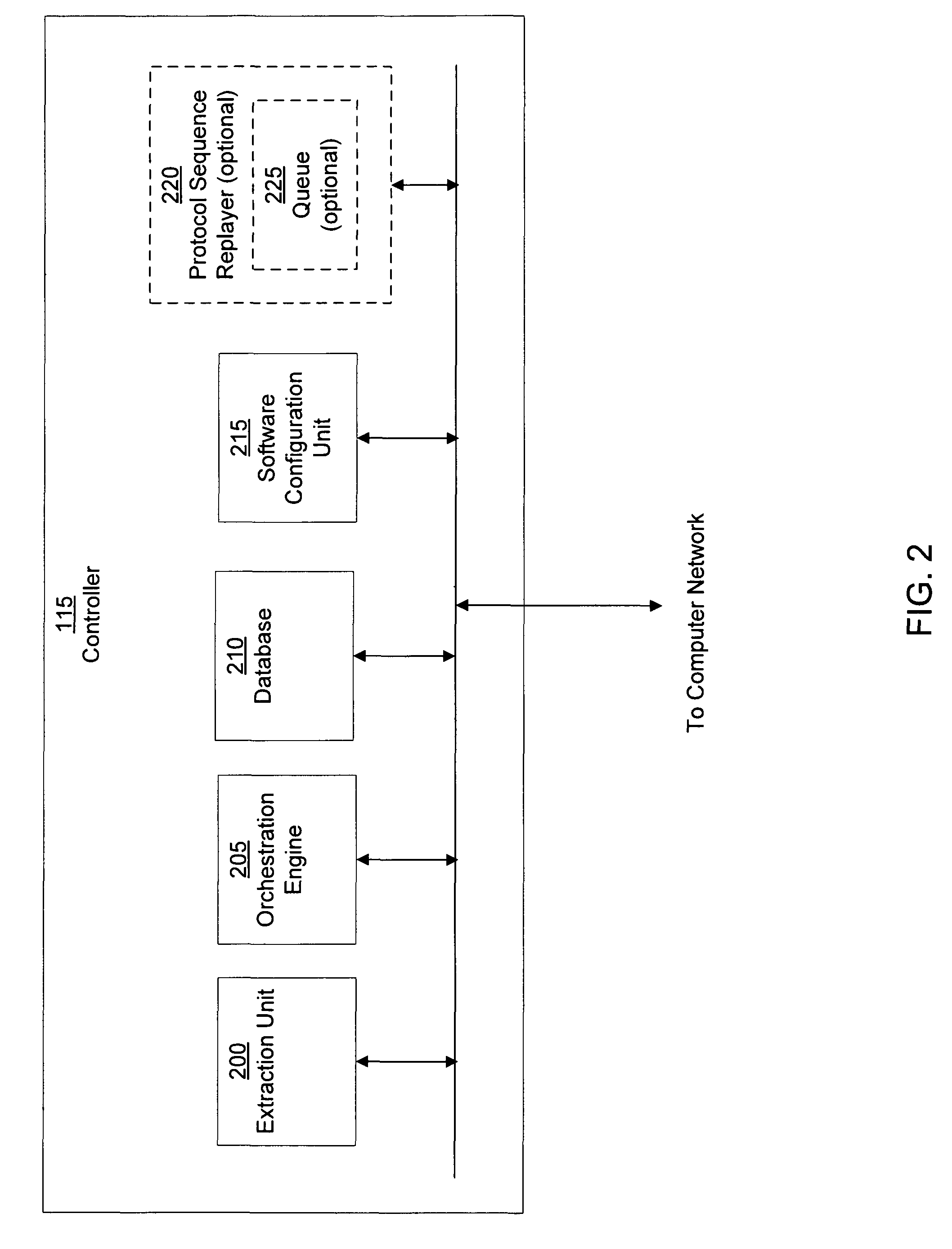
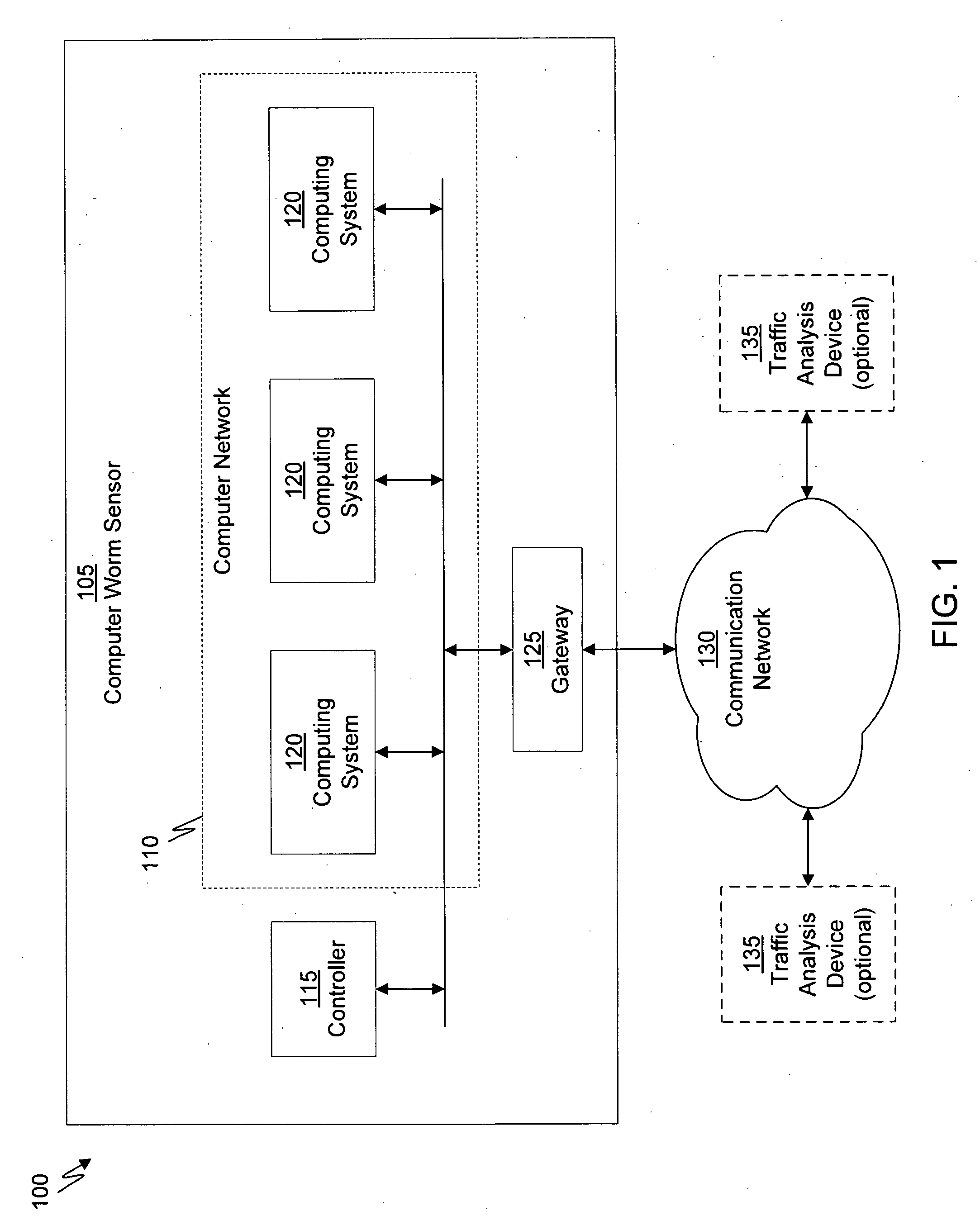
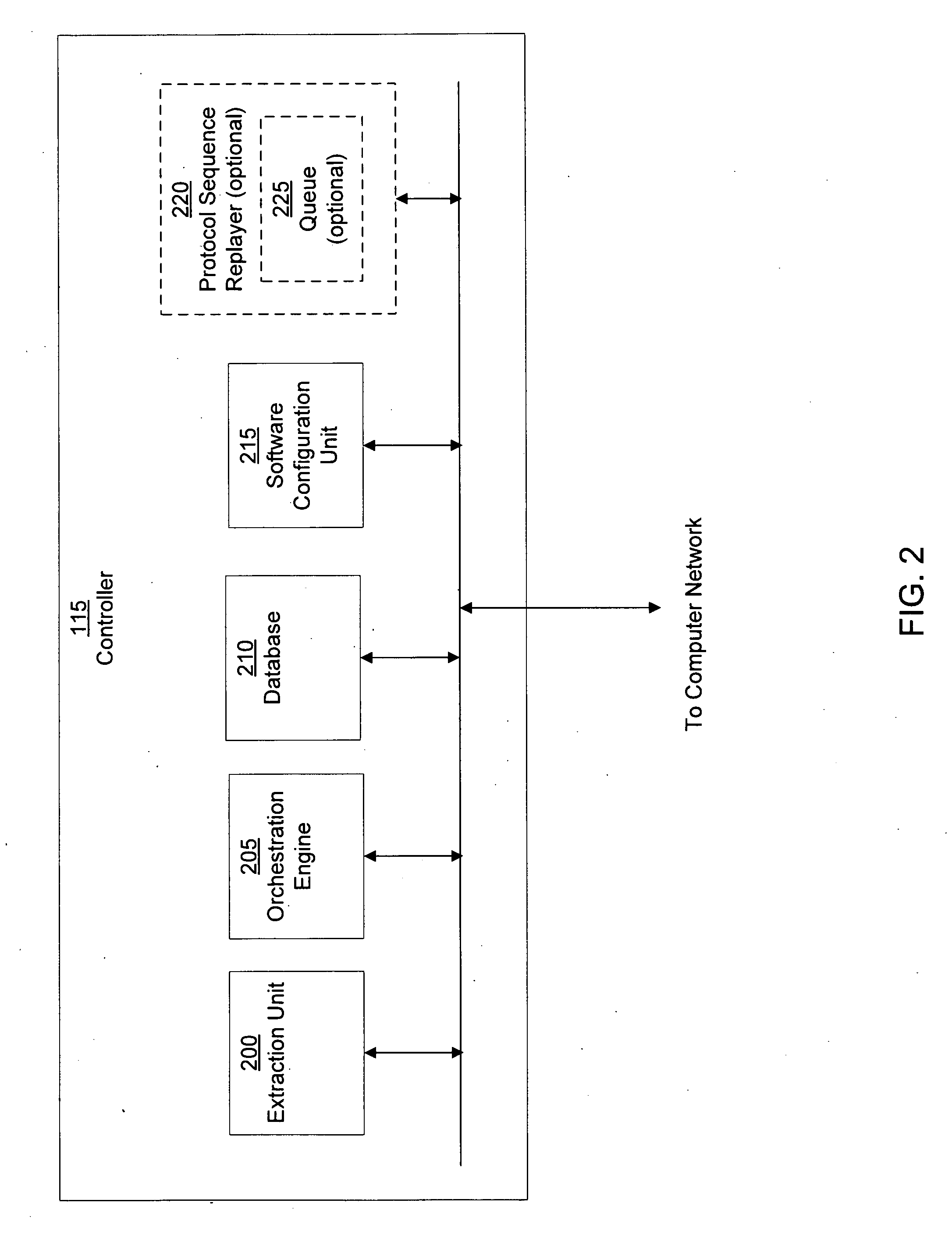
ActiveUS20120331553A1Memory loss protectionDigital data processing detailsNetwork dataDigital device
A dynamic signature creation and enforcement system can comprise a tap configured to copy network data from a communication network, and a controller coupled to the tap. The controller is configured to receive the copy of the network data from the tap, analyze the copy of the network data with a heuristic to determine if the network data is suspicious, flag the network data as suspicious based on the heuristic determination, simulate transmission of the network data to a destination device to identify unauthorized activity, generate an unauthorized activity signature based on the identification, and transmit the unauthorized activity signature to a digital device configured to enforce the unauthorized activity signature.
Owner:FIREEYE SECURITY HLDG US LLC
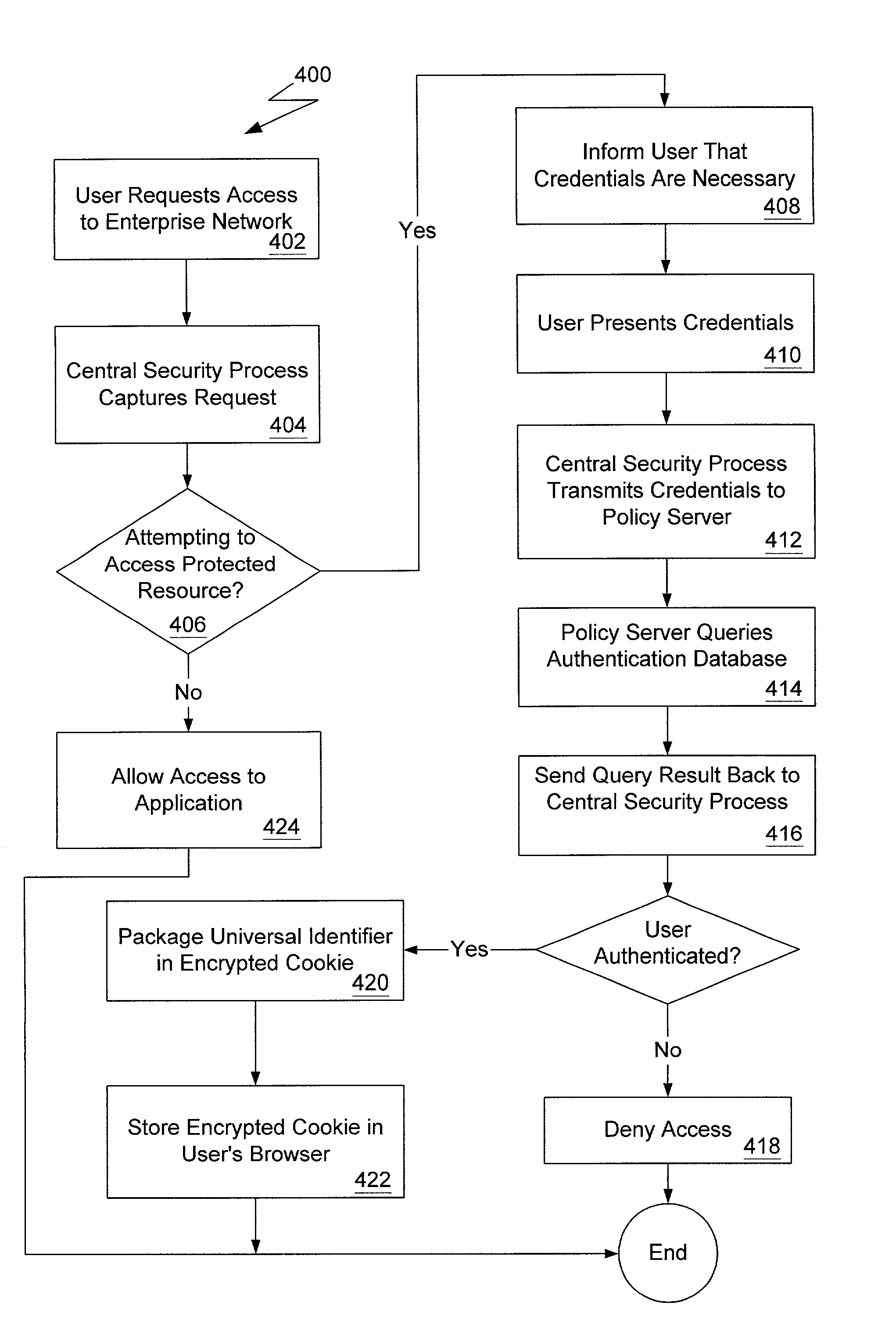
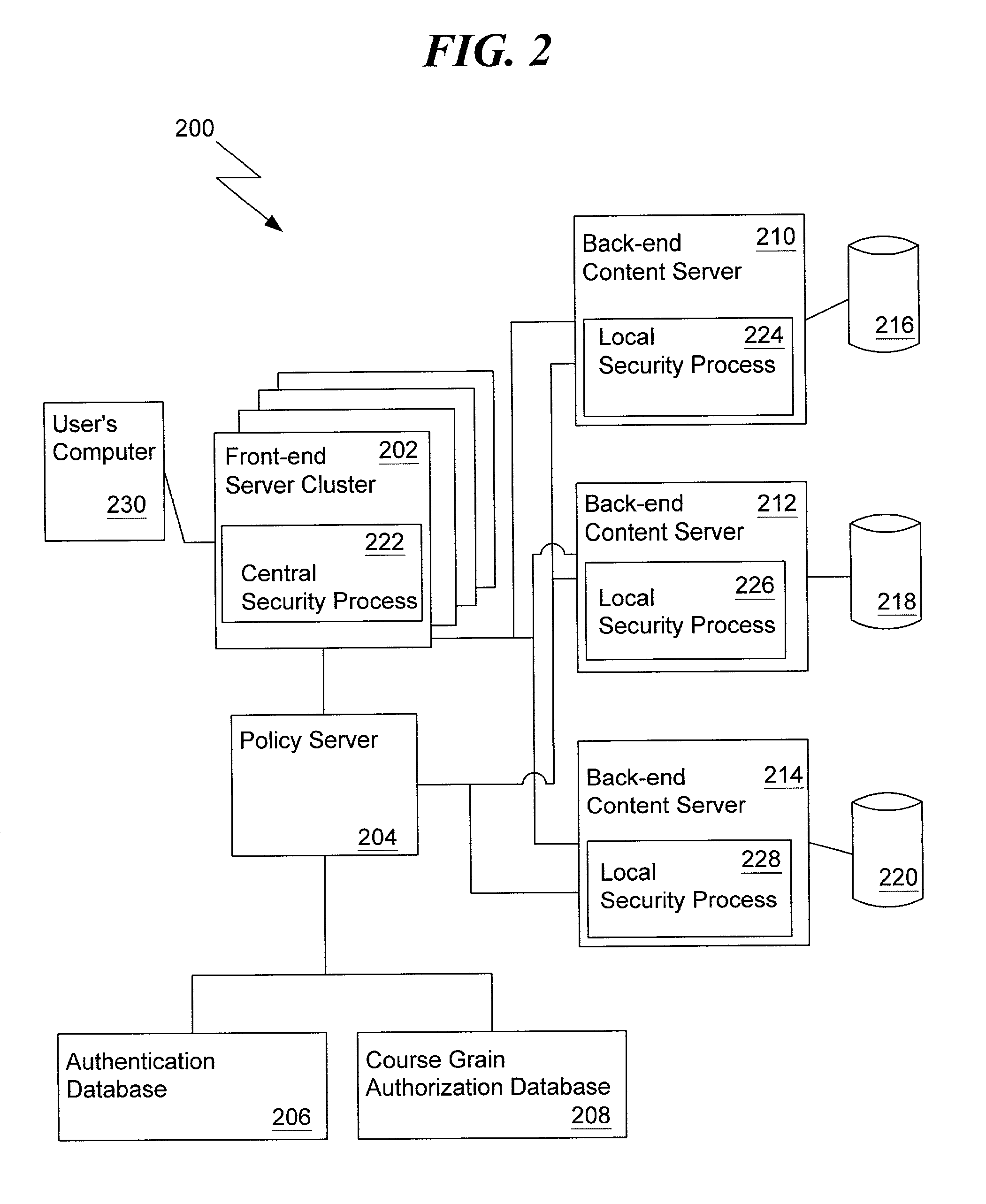
Authentication and authorization mapping for a computer network
ActiveUS7350229B1User identity/authority verificationComputer security arrangementsApplication softwareAuthorization
A method and apparatus for a network-wide authentication and authorization mapping system for a network is provided. The global authentication and authorization mapping system enables a seamless transition from one web-based application in the network configuration to another web-based application in the network configuration, including a single sign-on capability for users. There are no localized security enforcement processes required to further authenticate a user.
Owner:COMP ASSOC THINK INC
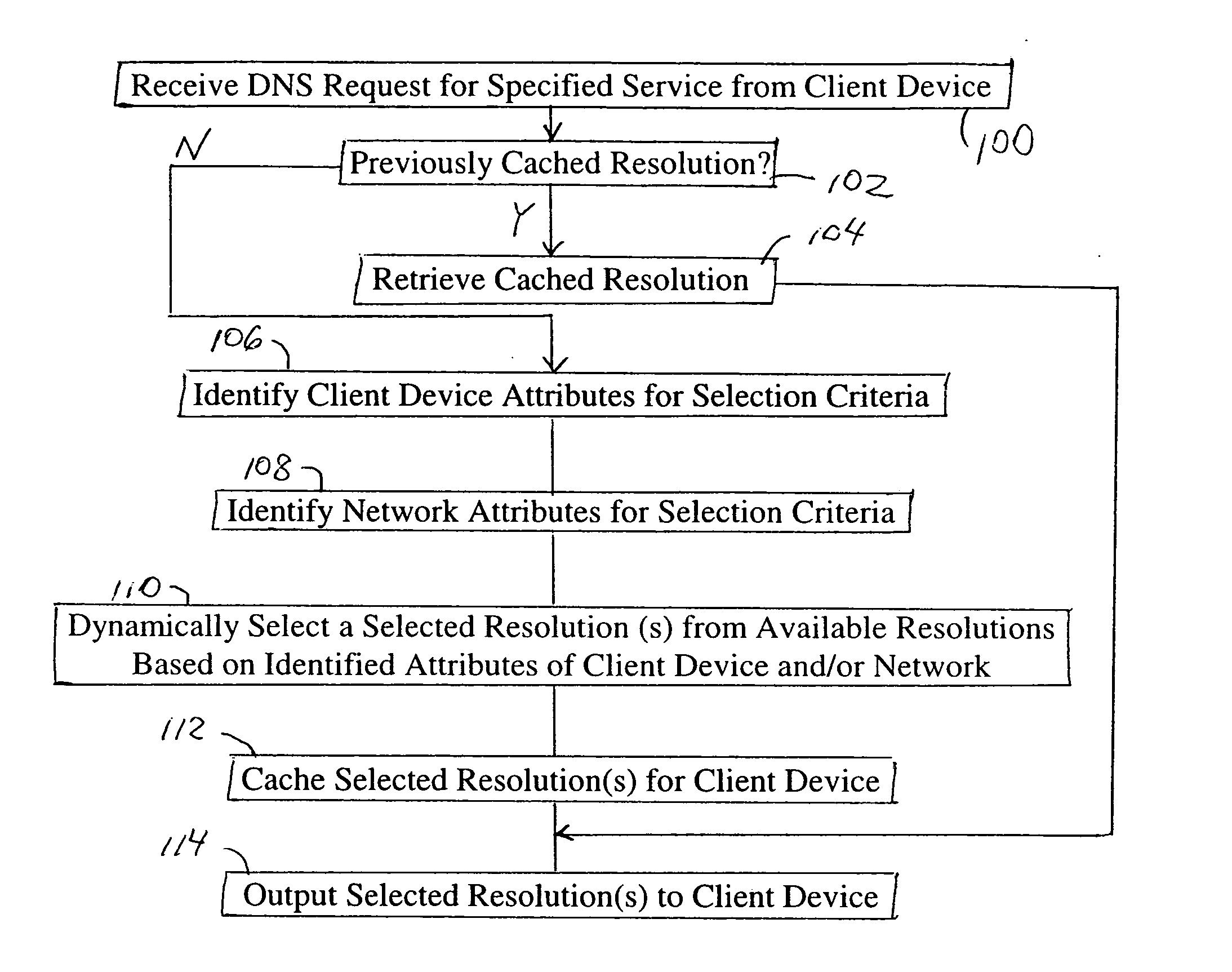
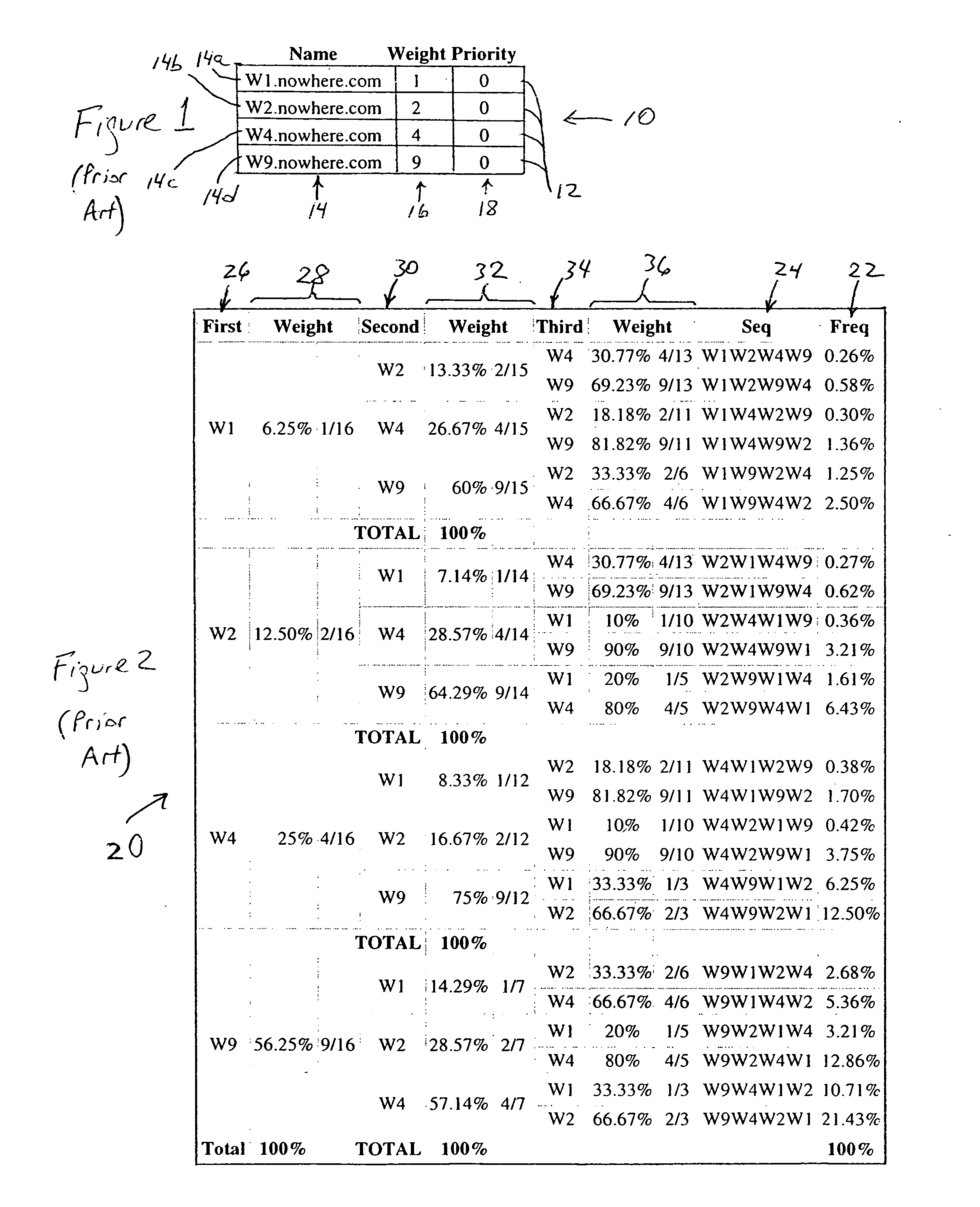
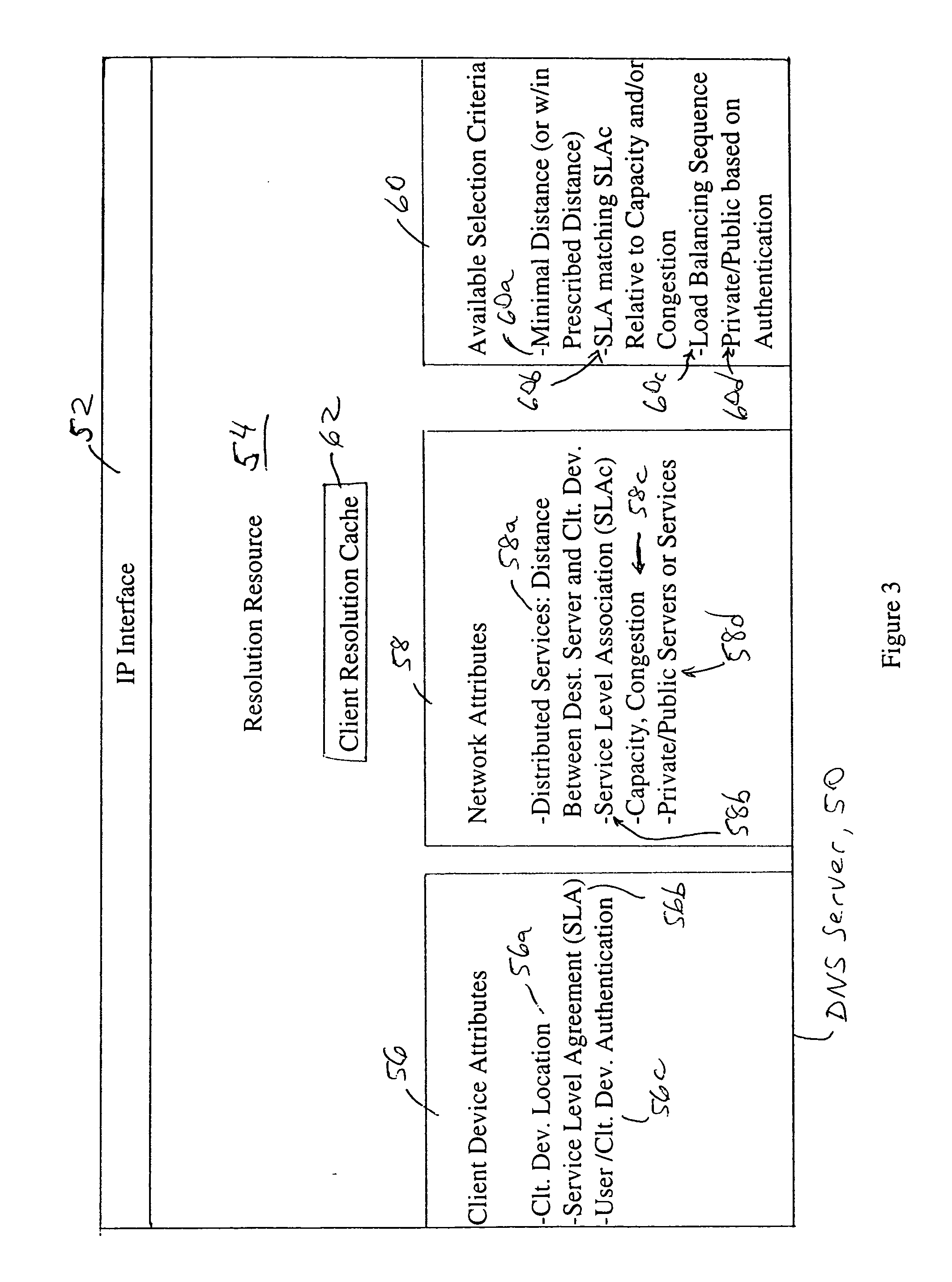
Arrangement in a server for providing dynamic domain name system services for each received request
ActiveUS20060129665A1Multiprogramming arrangementsMultiple digital computer combinationsService-level agreementLoad Shedding
A Domain Name System (DNS) server is configured for dynamically selecting, for a client device, a selected resolution from available resolutions, the selected resolution identifying at least one destination for the specified service. The dynamic selection of the selected resolution is based on an attribute of the client device and / or a determined attribute of the network. Hence, the selected resolution directs the client device to a specific server based on prescribed selection criteria, for example service level agreements, the location of the client device, network performance or detected congestion conditions, authentication of the user of the client device, etc. The selected resolution also can be for enforcement of load balancing policies.
Owner:CISCO TECH INC
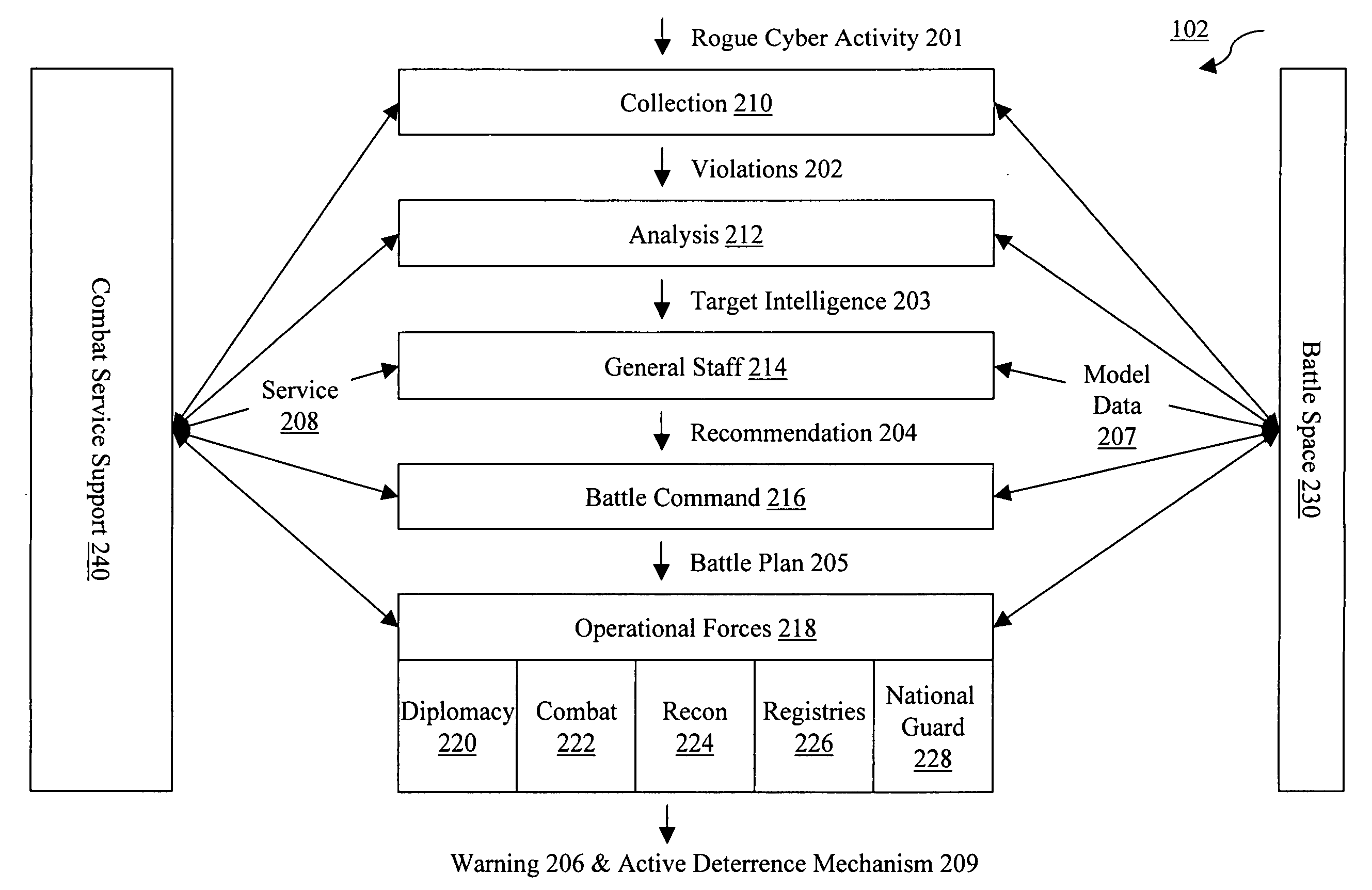
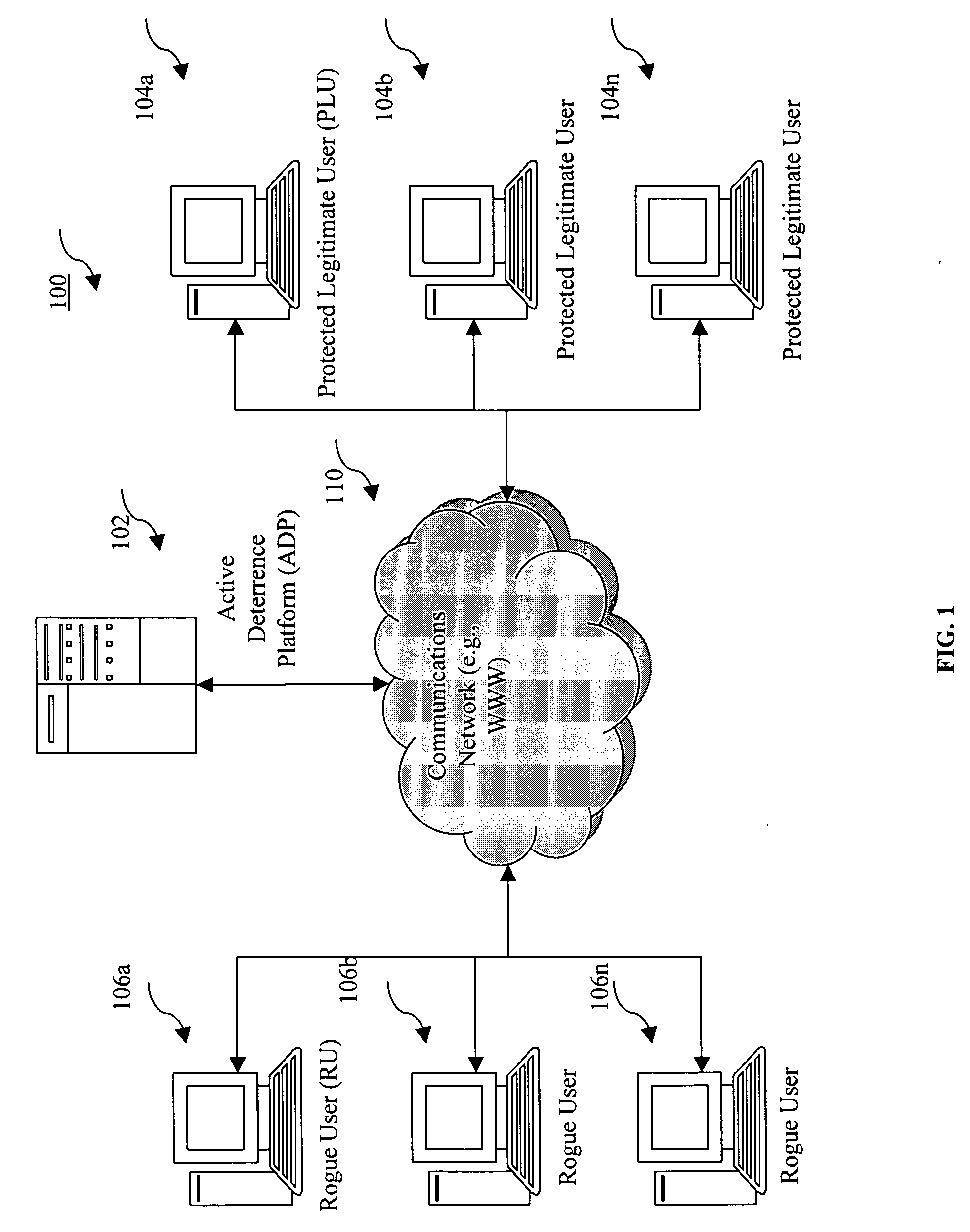
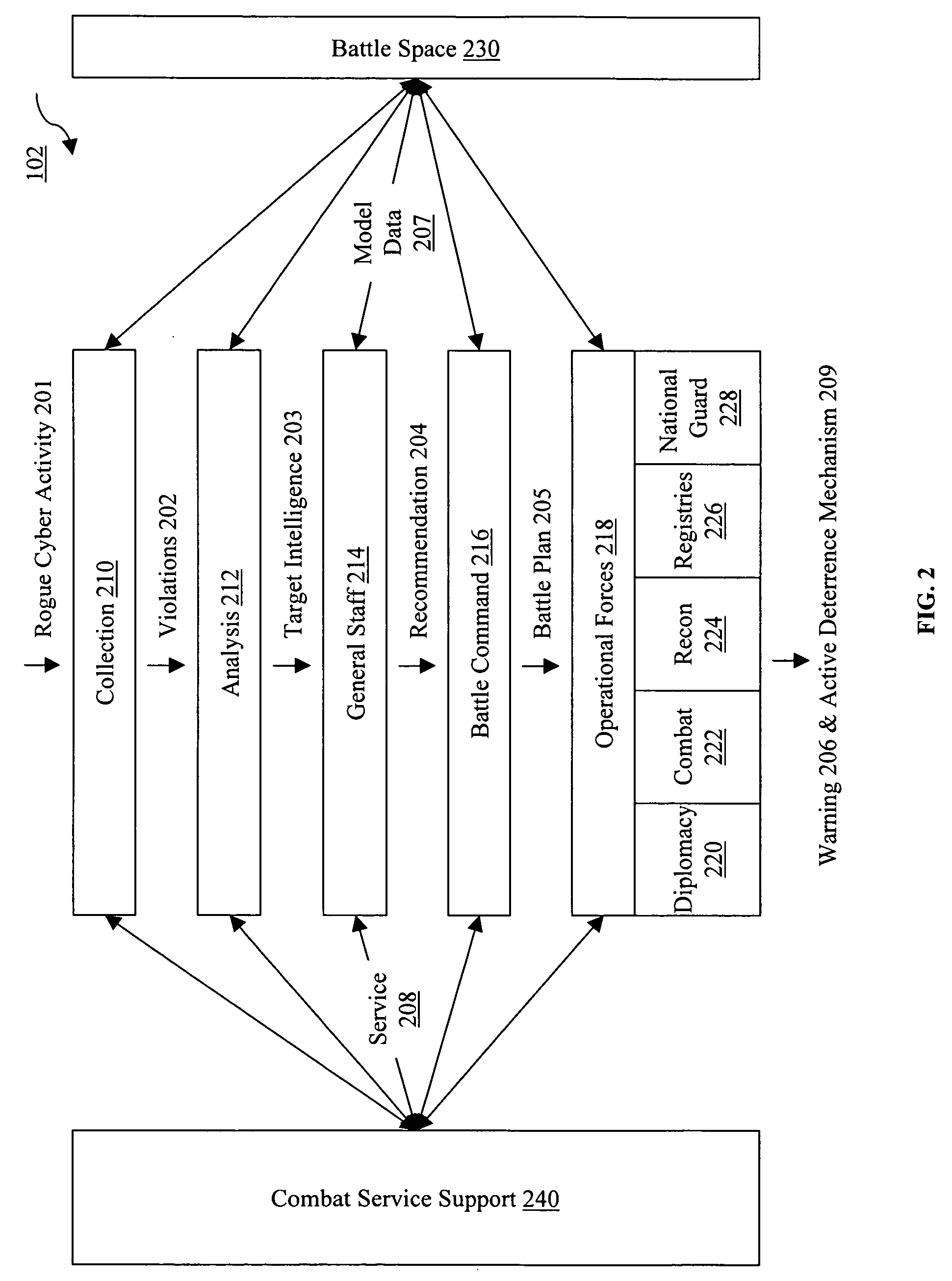
System and method for deterring rogue users from attacking protected legitimate users
InactiveUS20060161989A1Digital data processing detailsAnalogue secracy/subscription systemsMailing listInternet privacy
An active deterrence method and system deter rogue cyber activity targeting one or more protected legitimate users (PLUs). Methodologies and / or techniques are included to establish a PLU registry and / or enable a PLU to bear an identifying mark; detect rogue cyber activity; issue warnings to one or more rogue users (RUs) that target or attack PLUs with the detected rogue cyber activity; detect non-complying RUs that ignore or otherwise fail to comply with the warnings; and deploy one or more active deterrence mechanisms against the non-complying RUs. One active deterrence mechanism includes deploying a plurality of scripts to each PLU, and executing the scripts to issue complaints and request the non-complying RUs to clean their mailing lists of all PLUs. Other active deterrence mechanisms include alerting unaware business affiliates of the RUs, and notifying victims or law enforcement authorities of unlawful rogue cyber activity.
Owner:COLLACTIVE
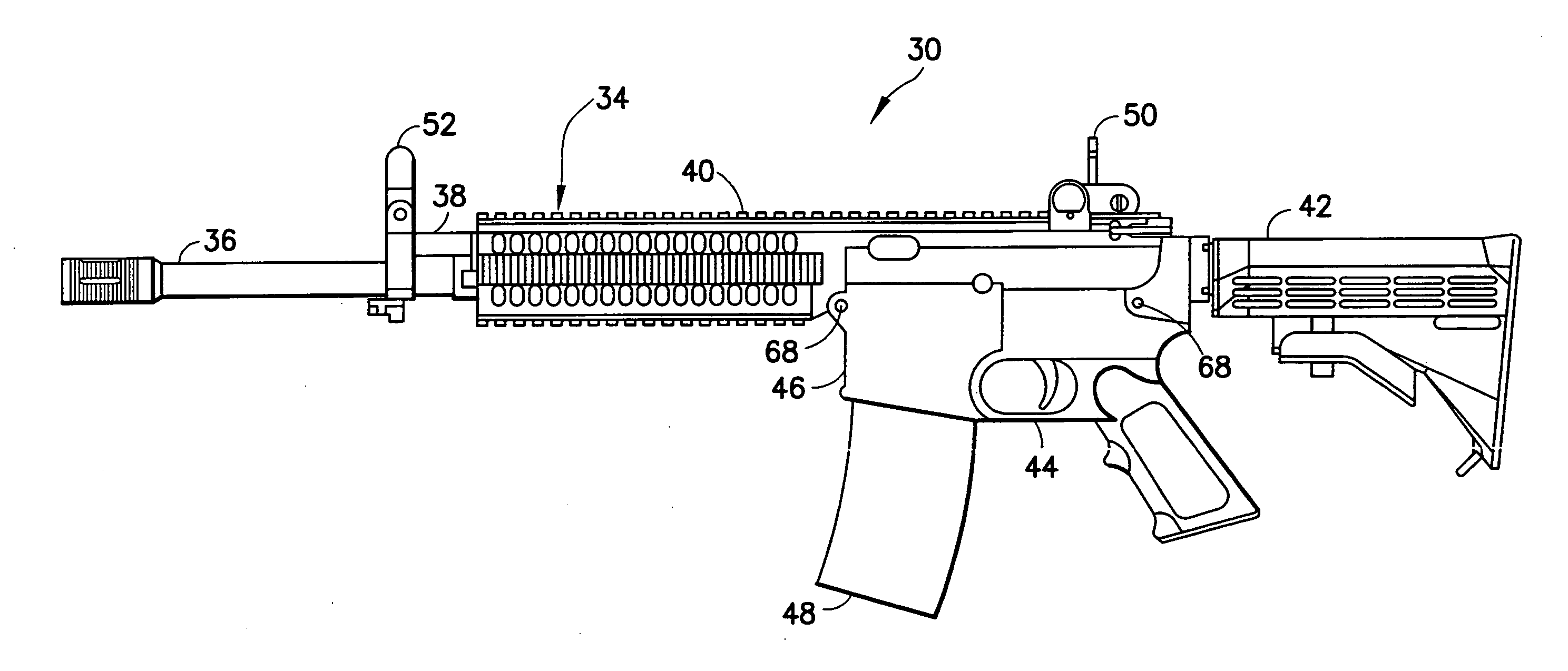
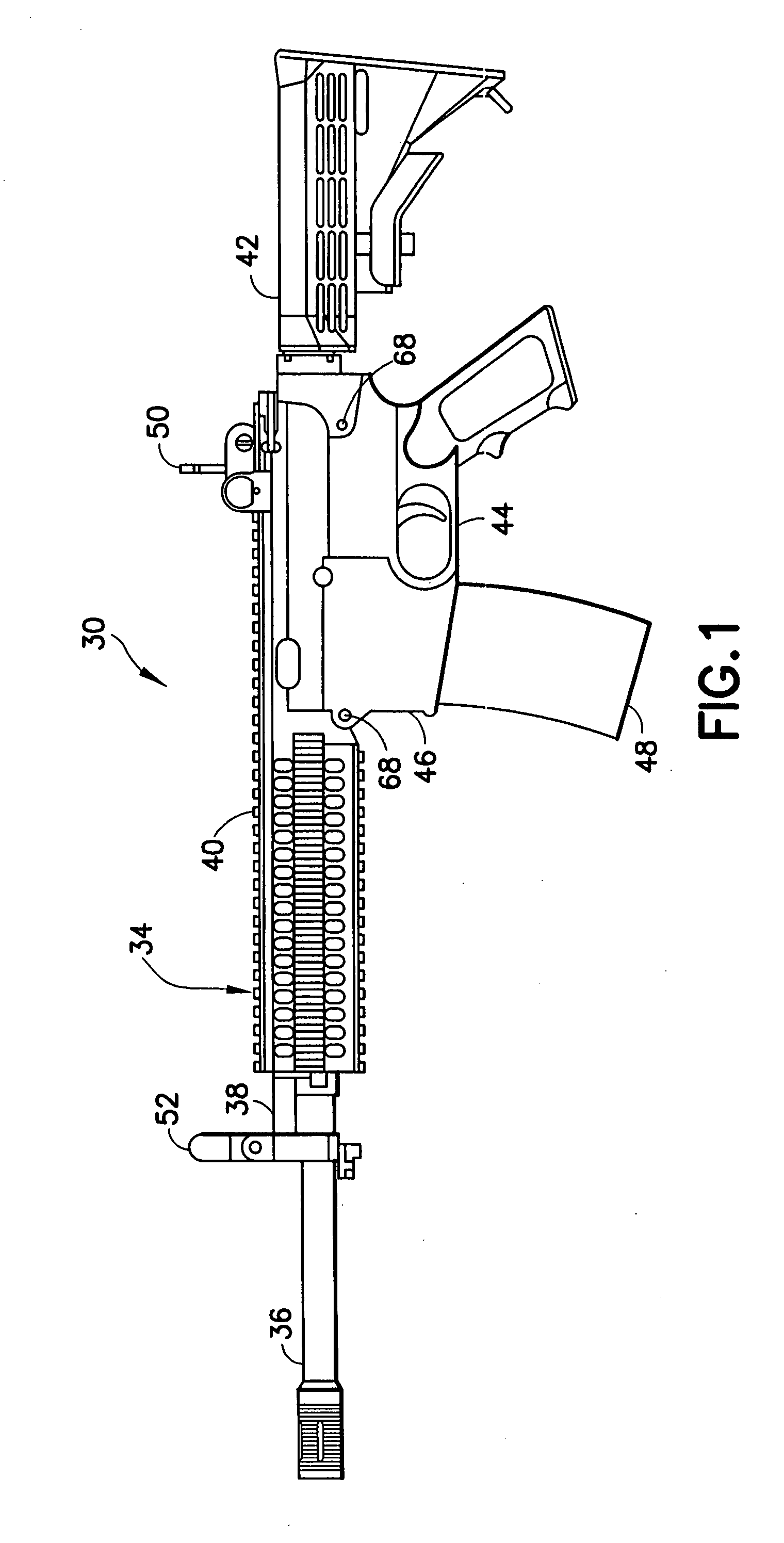
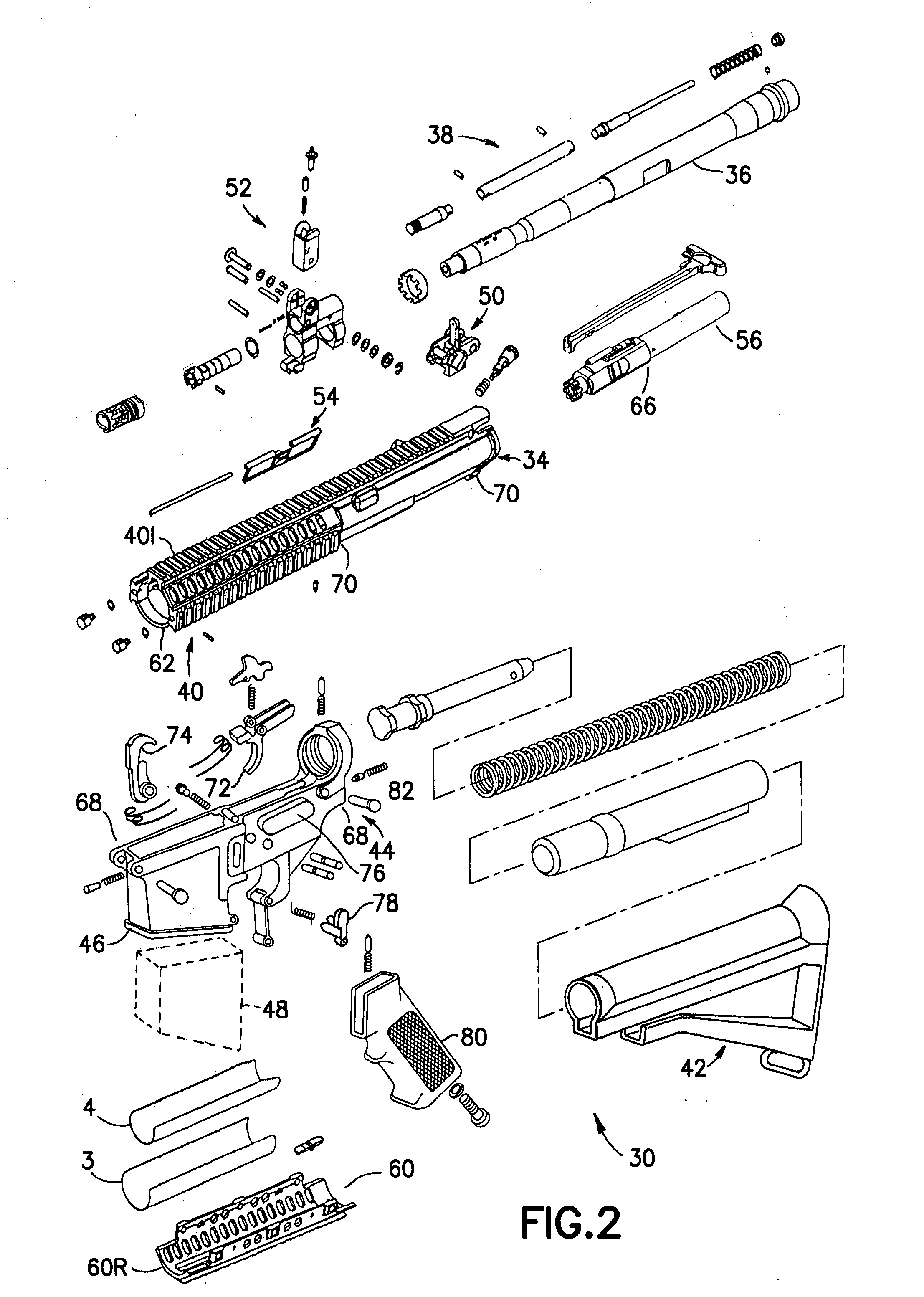
Law enforcement carbine with one piece receiver
An indirect gas operating system for an M4 type automatic or semi-automatic firearm. The indirect gas operating system has a gas block having a cylinder. The gas block is fitted to a barrel assembly having a bore with the cylinder in communication with the bore. A piston having a piston end and a striking end has the piston end fitted to the cylinder. A bolt assembly having a striking surface is provided. When a cartridge is fired, gas displaces the piston end and causes the striking end to strike the striking surface displacing the bolt assembly. The cylinder and the piston are together removable as an assembly from the firearm without removal of the gas block.
Owner:COLTS MFG IP HLDG COMPANY
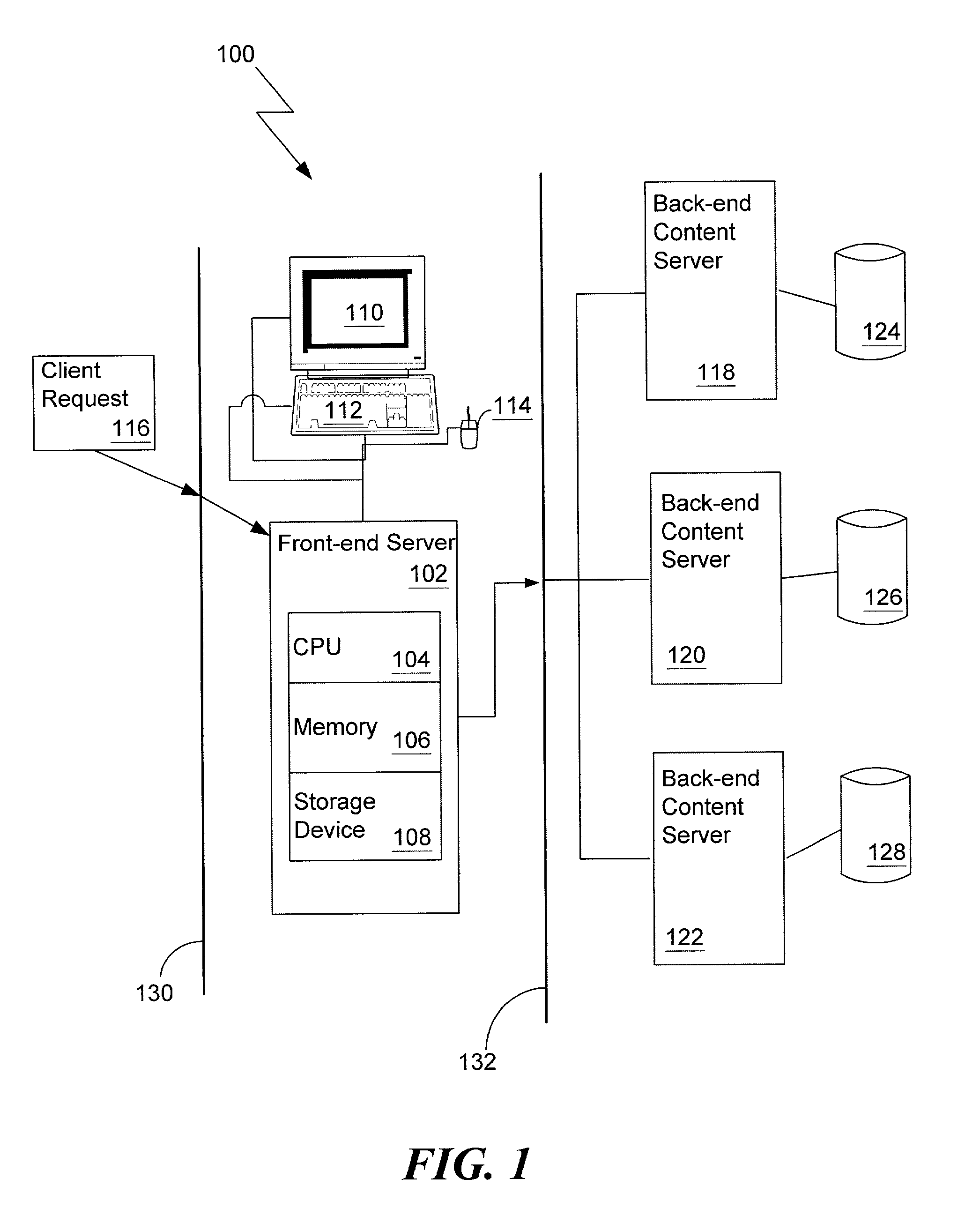
Network-based content distribution system
InactiveUS20090037388A1Maximize potential return-on-investmentMinimal burdenDigital data processing detailsUser identity/authority verificationContent distributionPublic network
Owner:VERIMATRIX INC
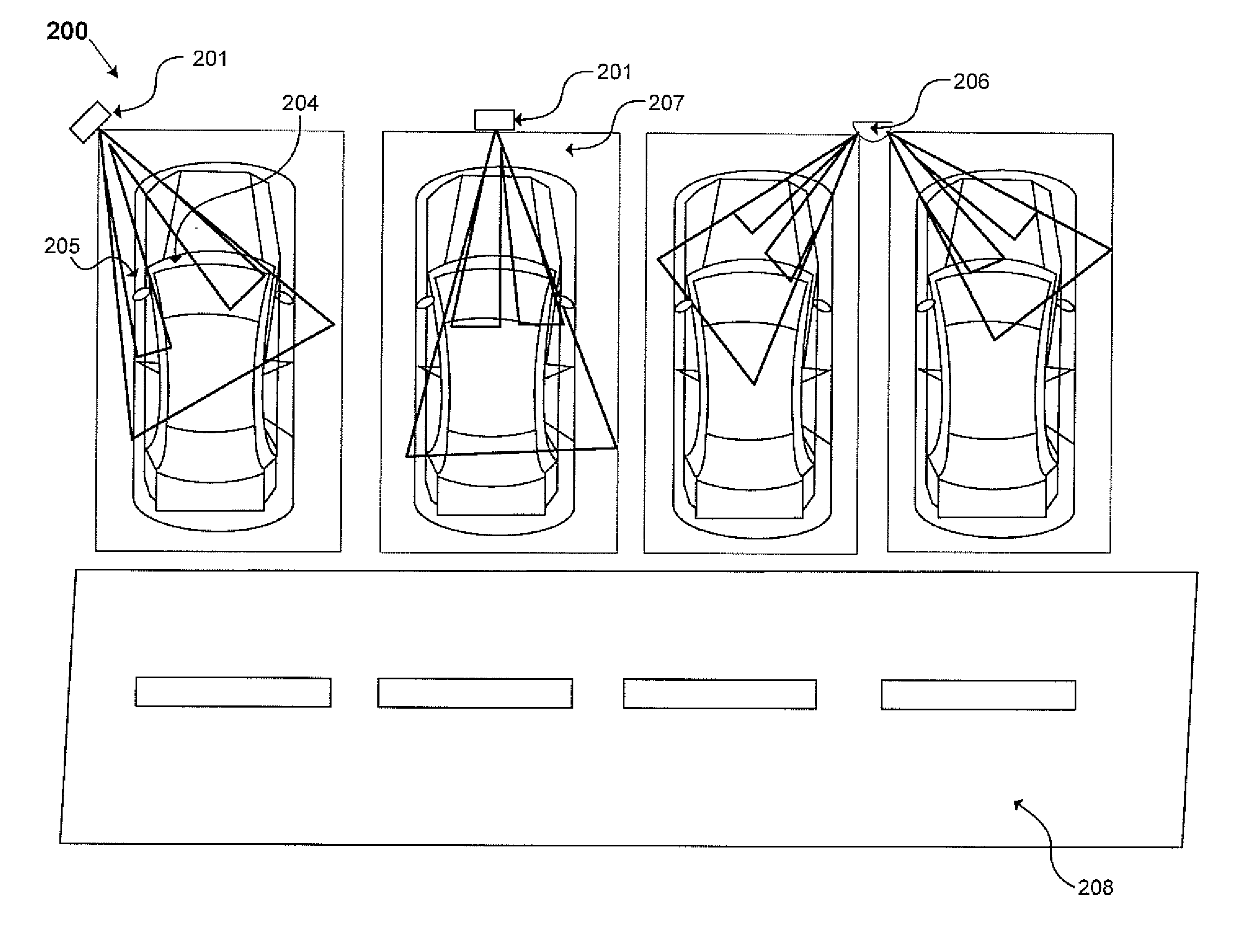
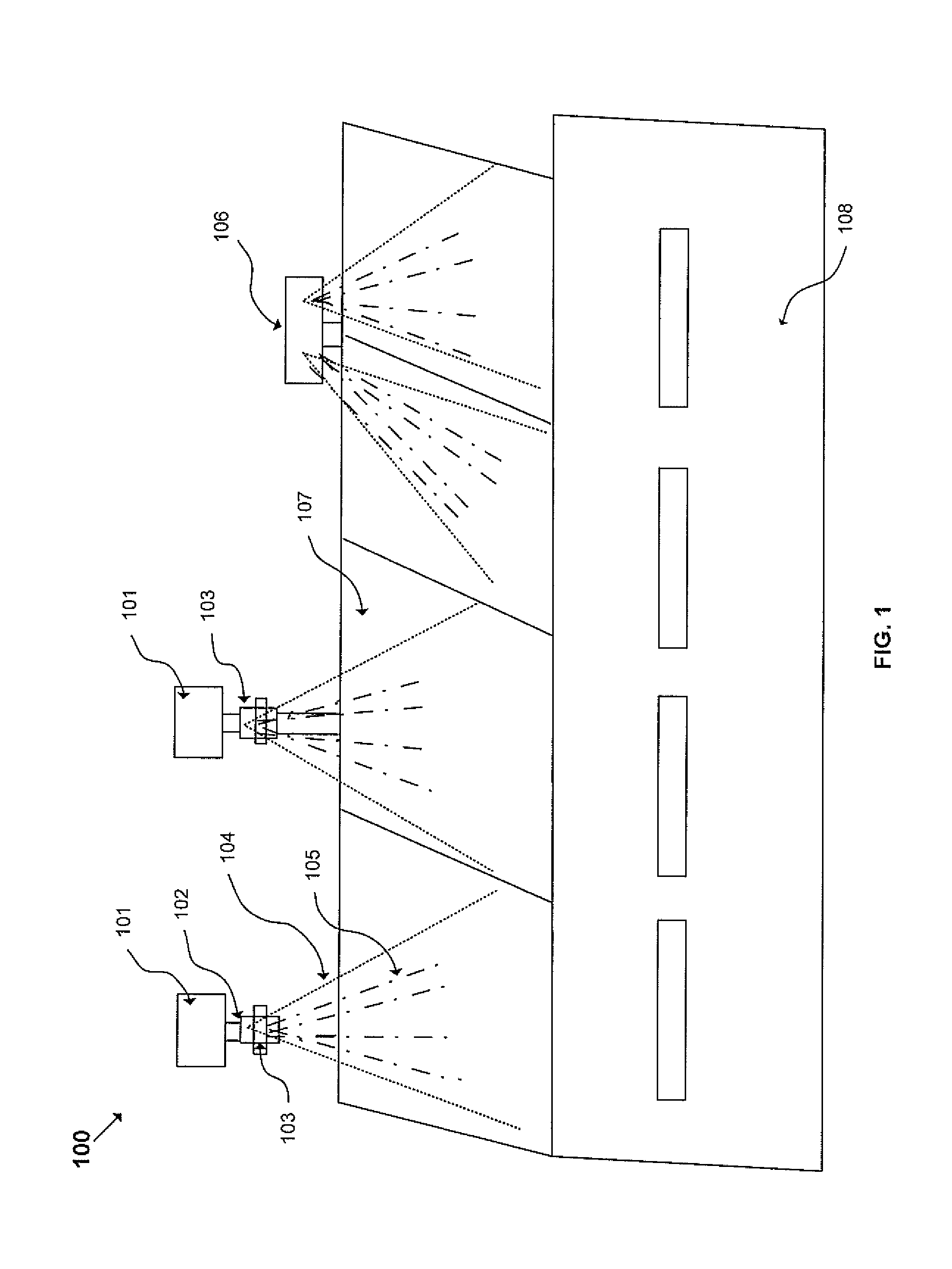
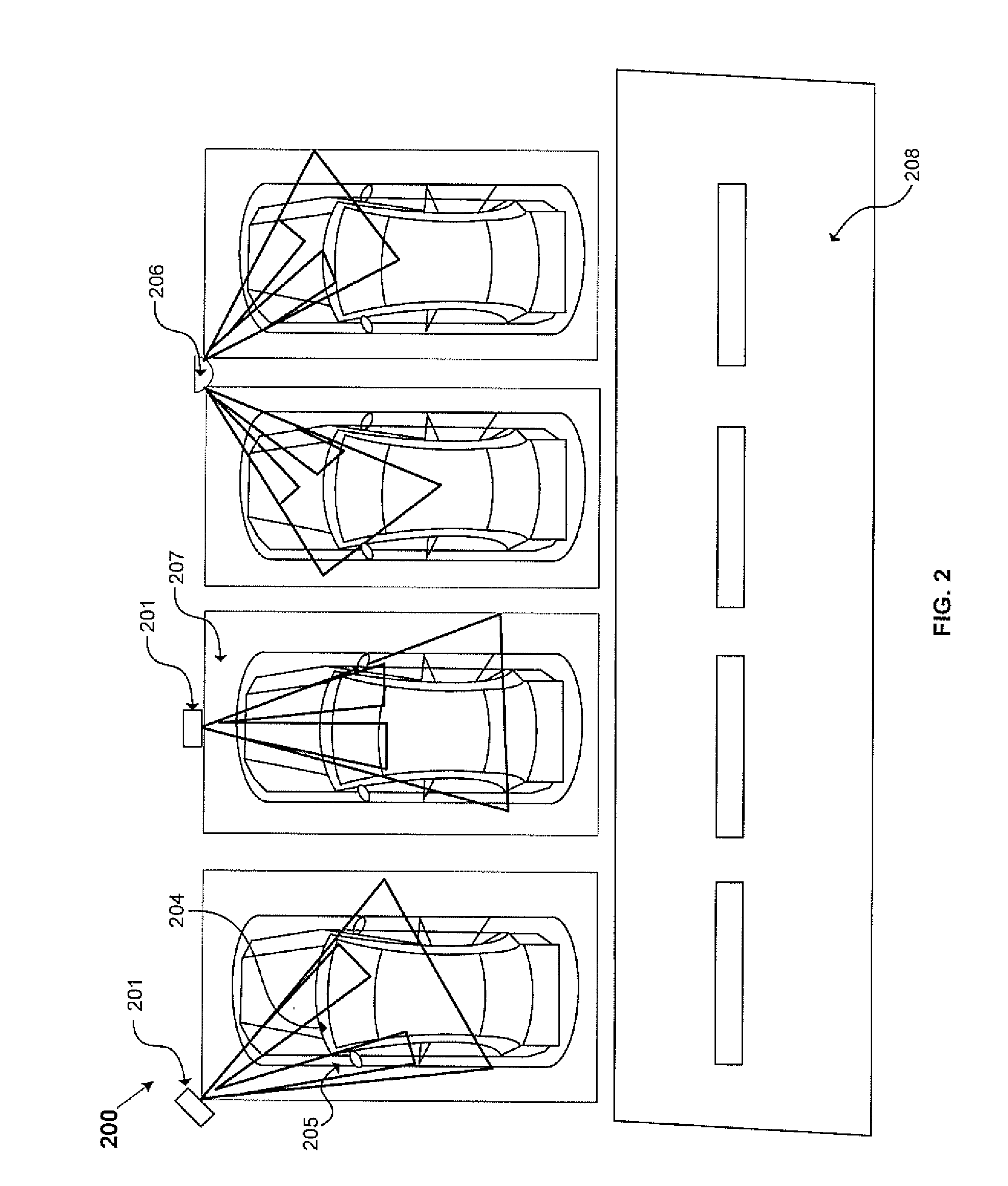
Advanced parking and intersection management system
A parking management system that facilitates motorist guidance, payment, violation detection, and enforcement using highly accurate space occupancy detection, unique vehicle identification and guidance displays is described. The system enables reduced time to find parking, congestion mitigation, accurate violation detection, and easier enforcement, and increased payment and enforcement revenues to cities. A system facilitating intersection management is also described having applicability to road intersections and railway crossings.
Owner:SUBRAMANYA BALU
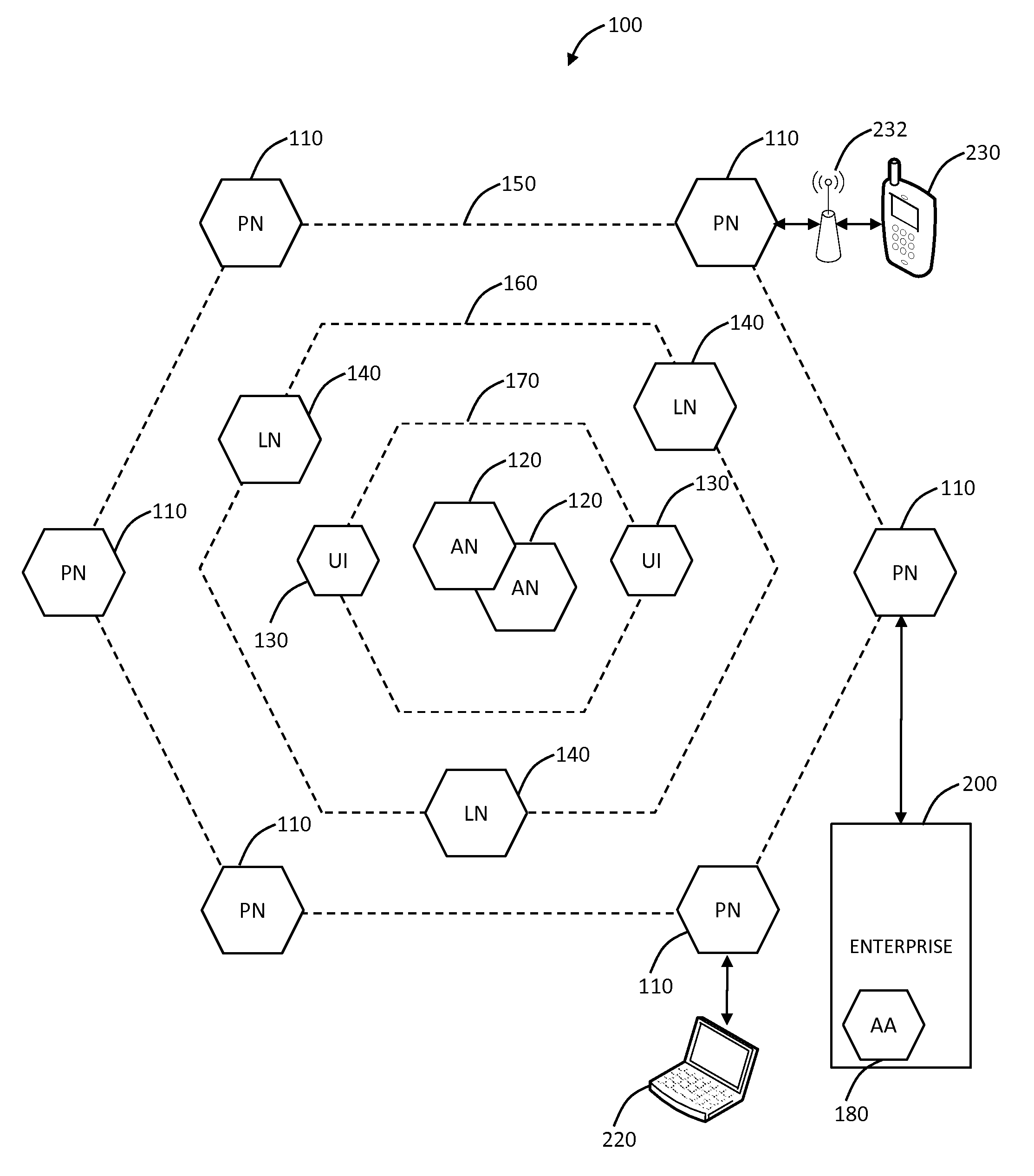
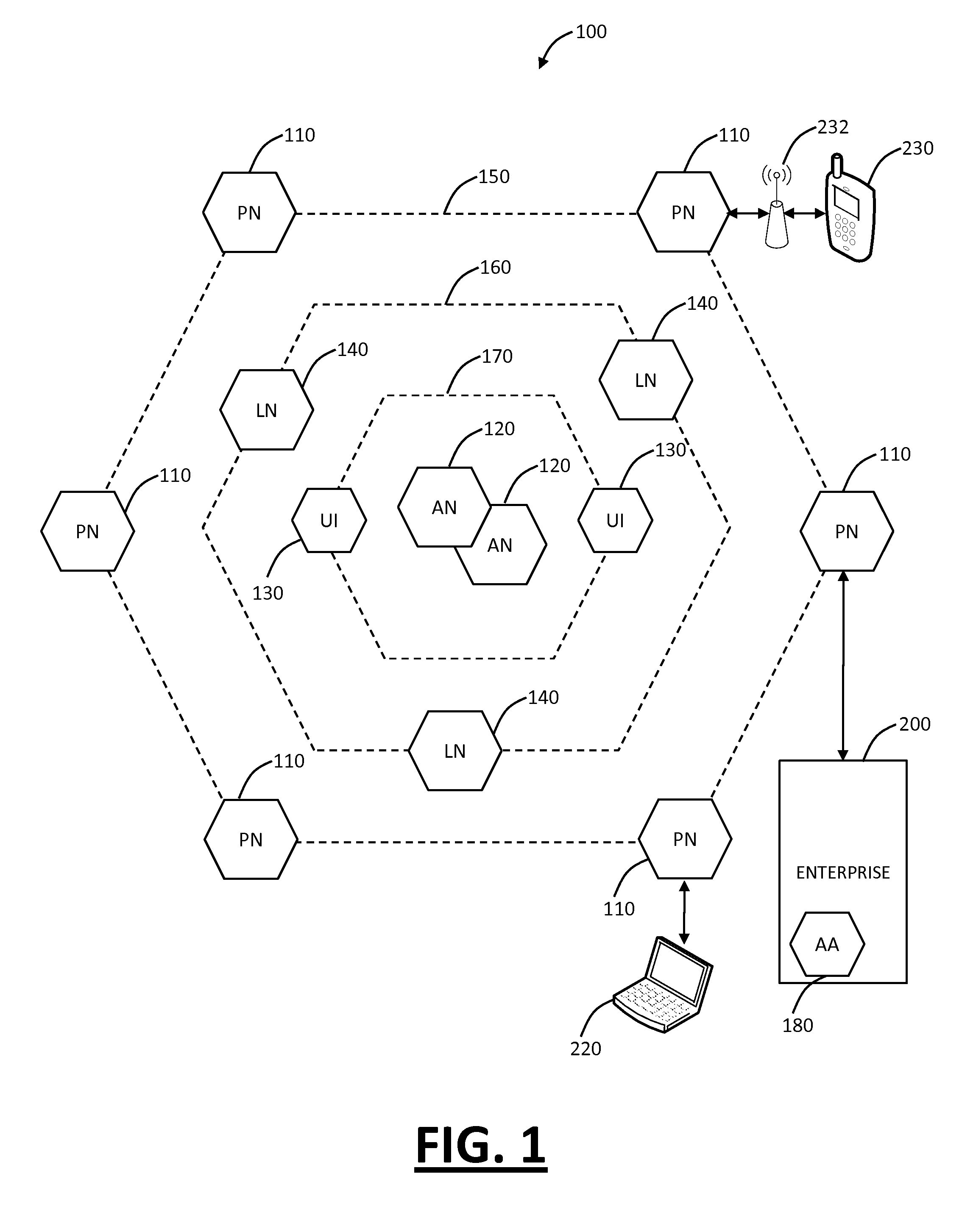
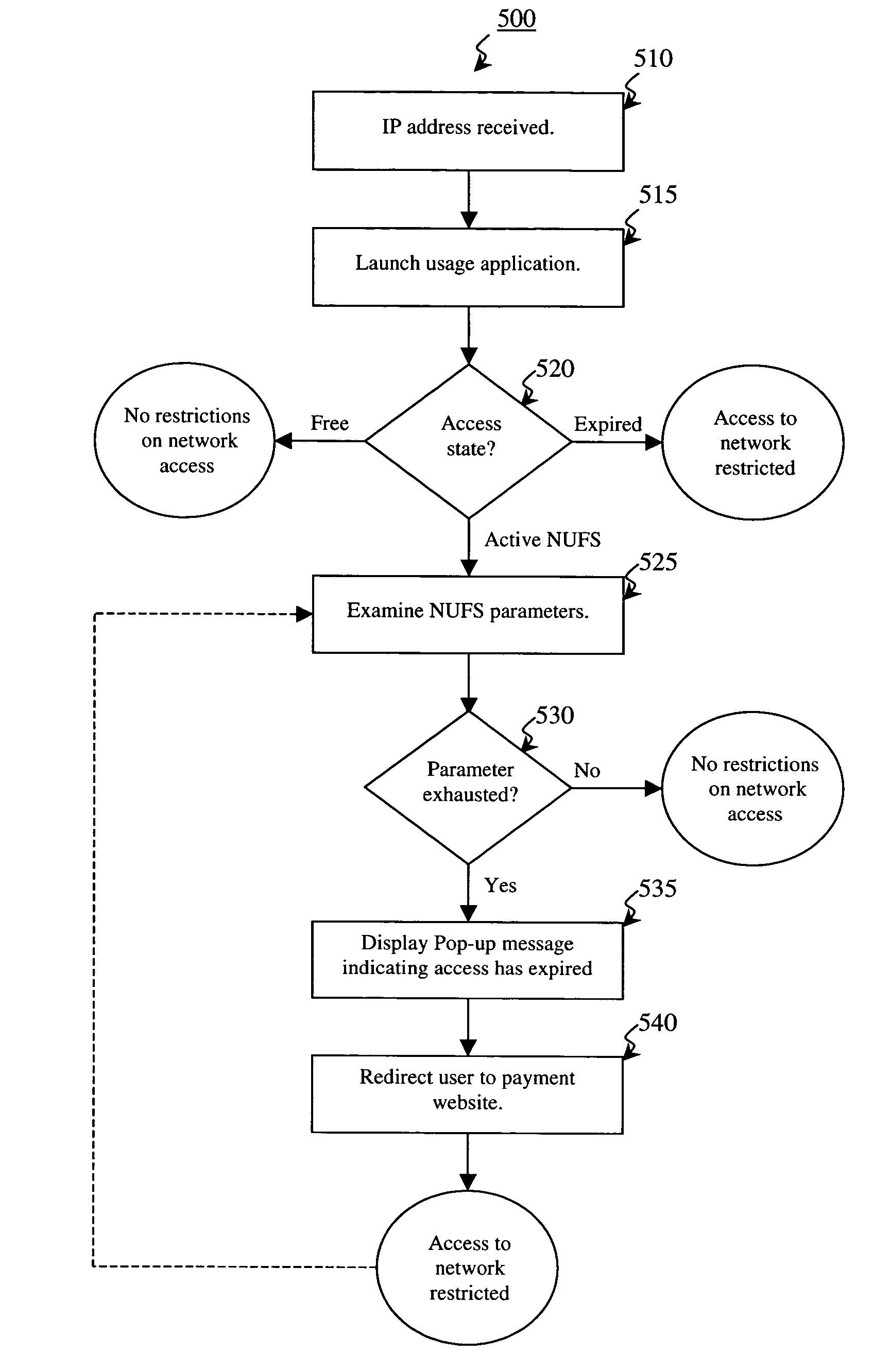
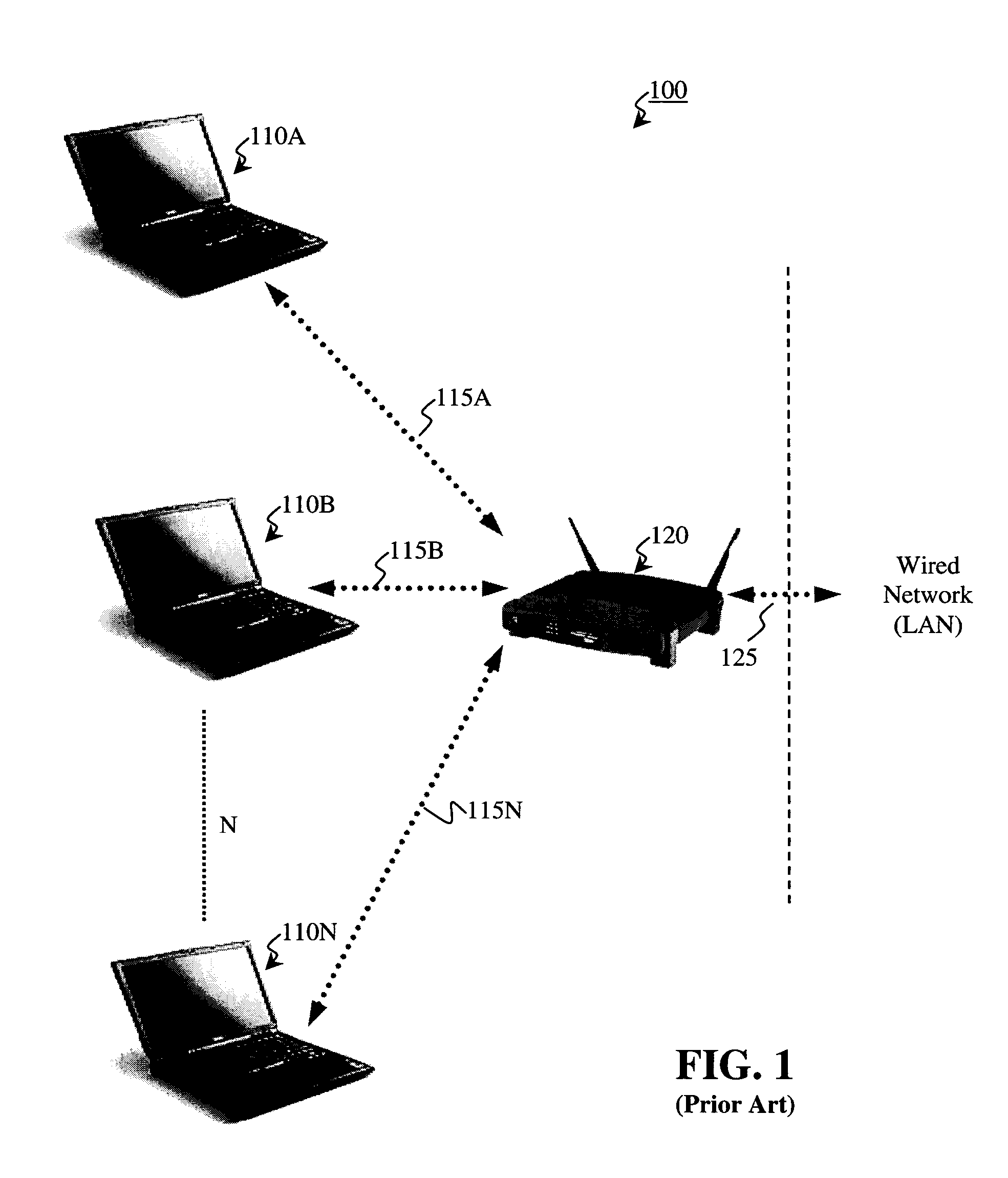
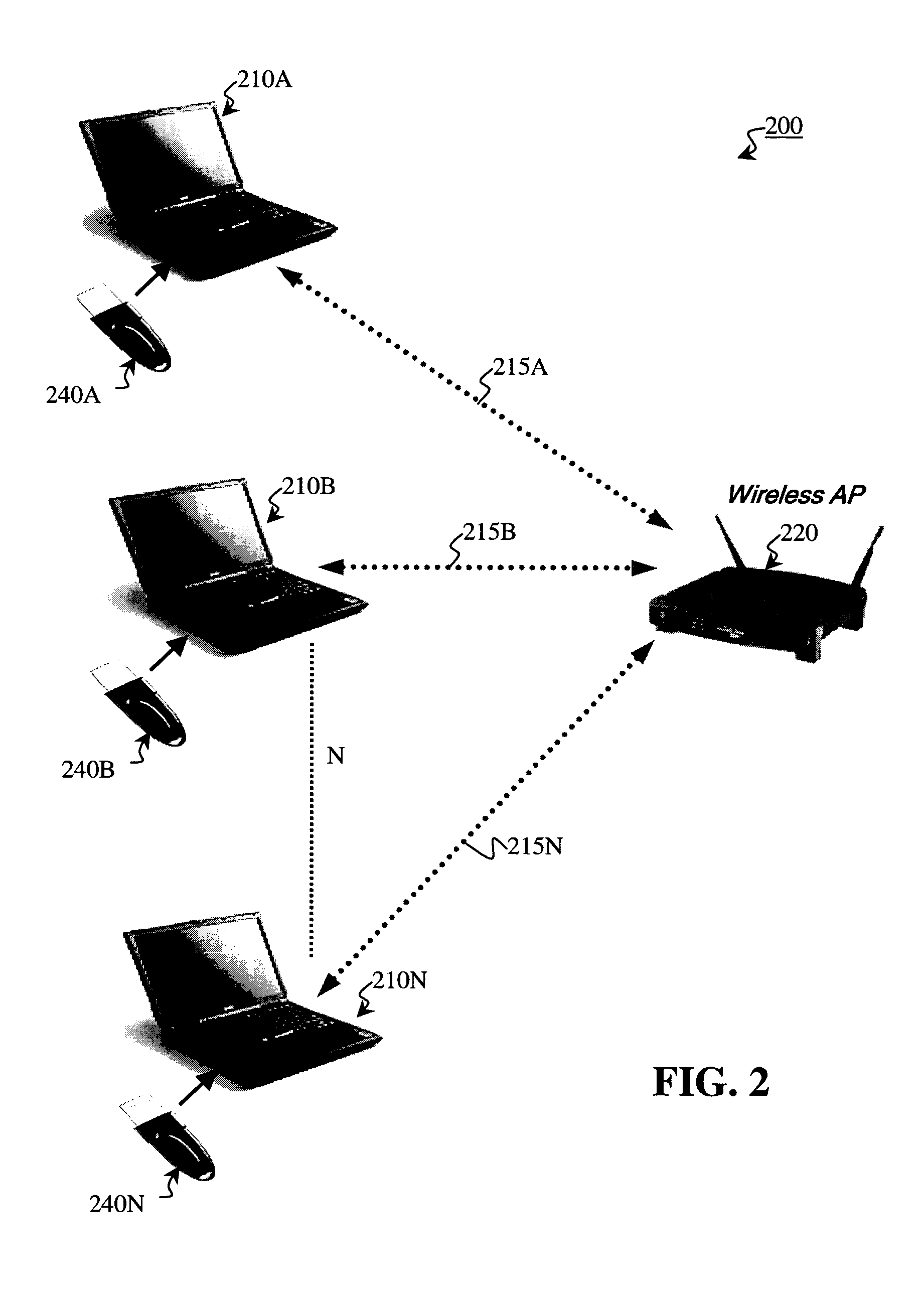
Self-managed network access using localized access management
ActiveUS7574731B2Provide usageAvoid modificationRandom number generatorsUser identity/authority verificationProgram planningBack end server
The invention provides a method and system for locally tracking network usage and enforcing usage plans at a client device. In an embodiment of the invention, a unique physical key, or token, is installed at a client device of one or more networks. The key comprises a usage application and one or more access parameters designated the conditions and / or limits of a particular network usage plan. Upon initial connection to the network, the usage application grants or denies access to the network based on an analysis of the current values of the access parameters. Therefore, network usage tracking and enforcement is made simple and automatic without requiring any back-end servers on the network while still providing ultimate flexibility in changing billing plans for any number of users at any time.
Owner:KOOLSPAN
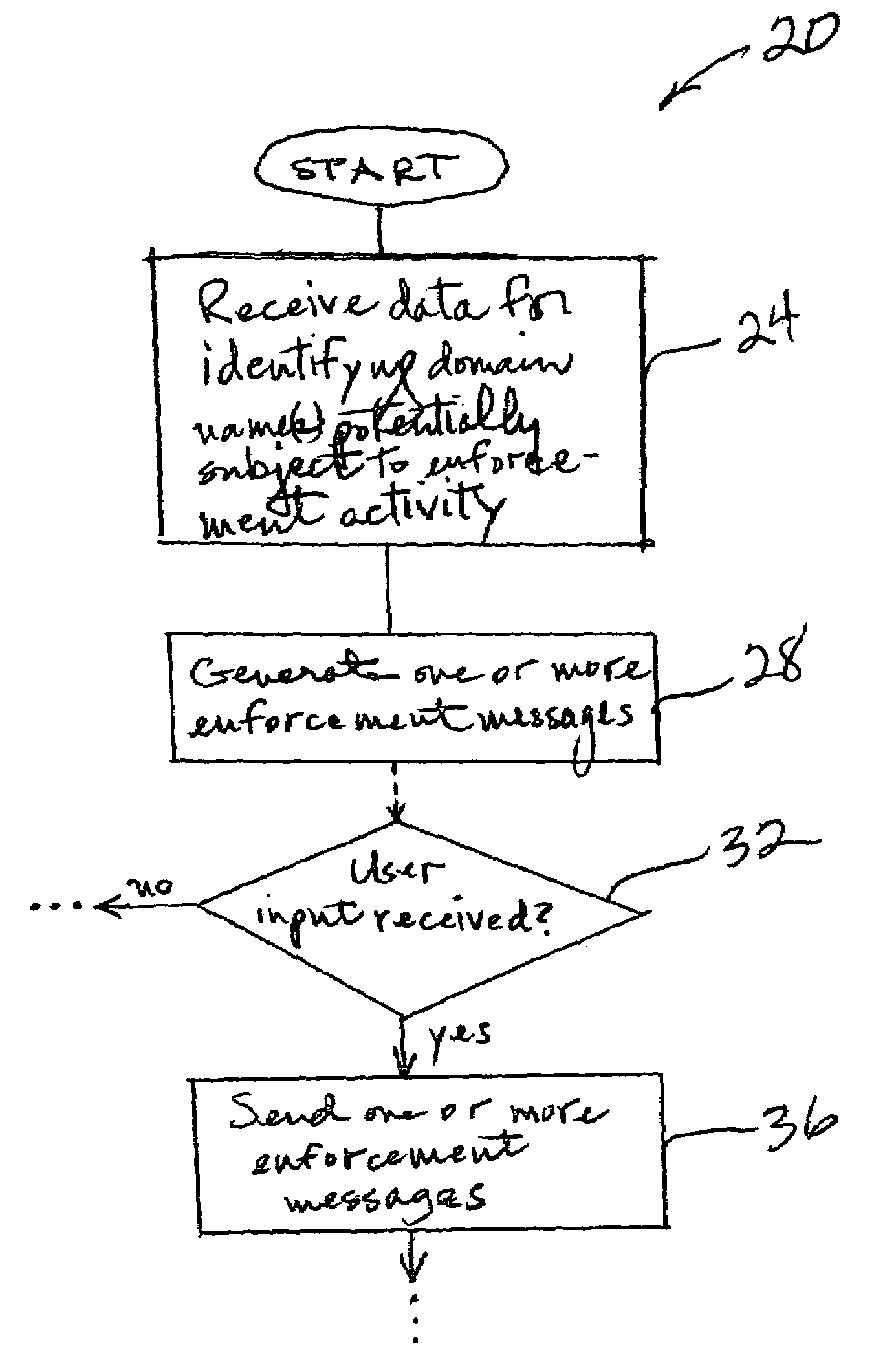
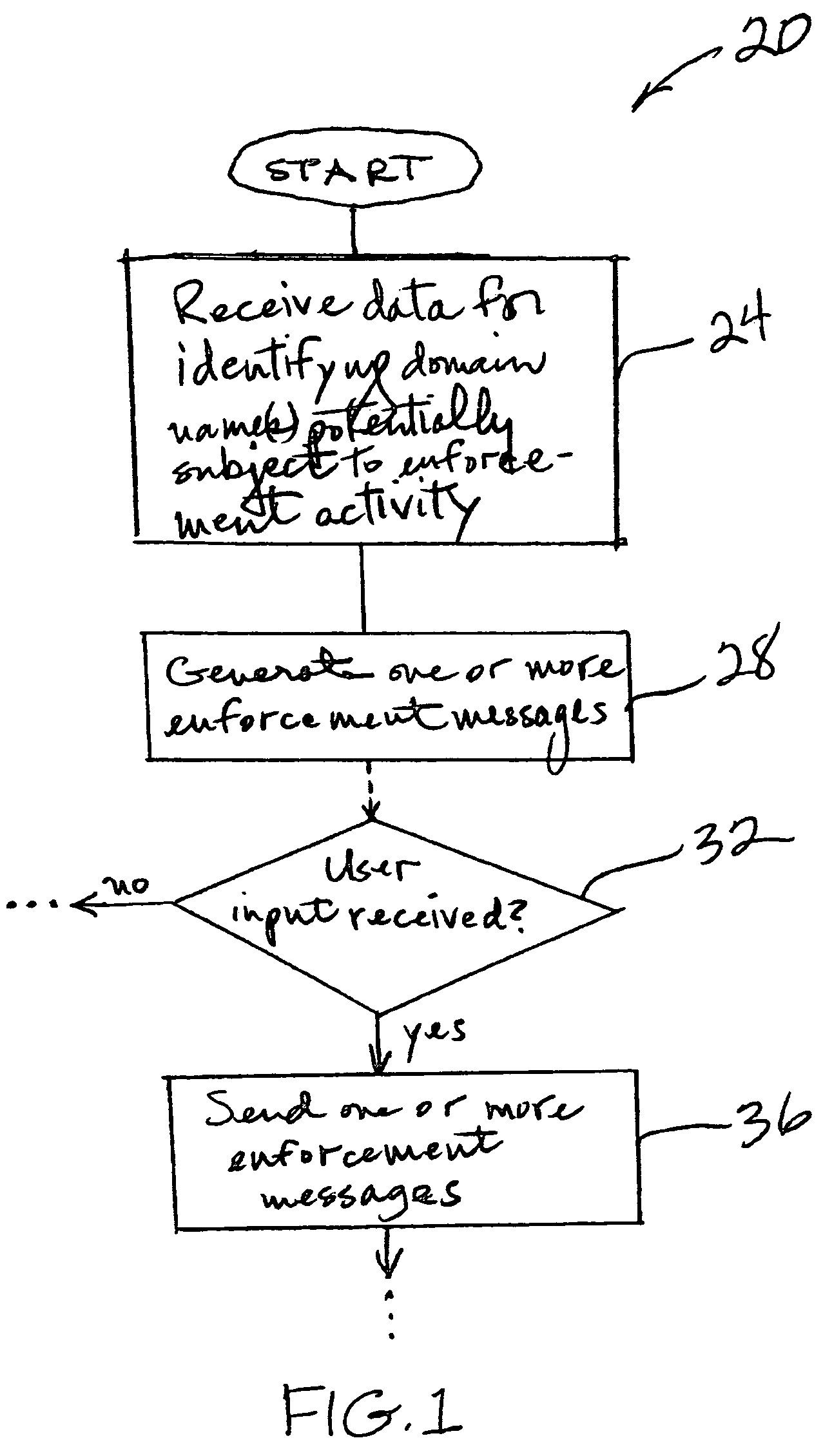
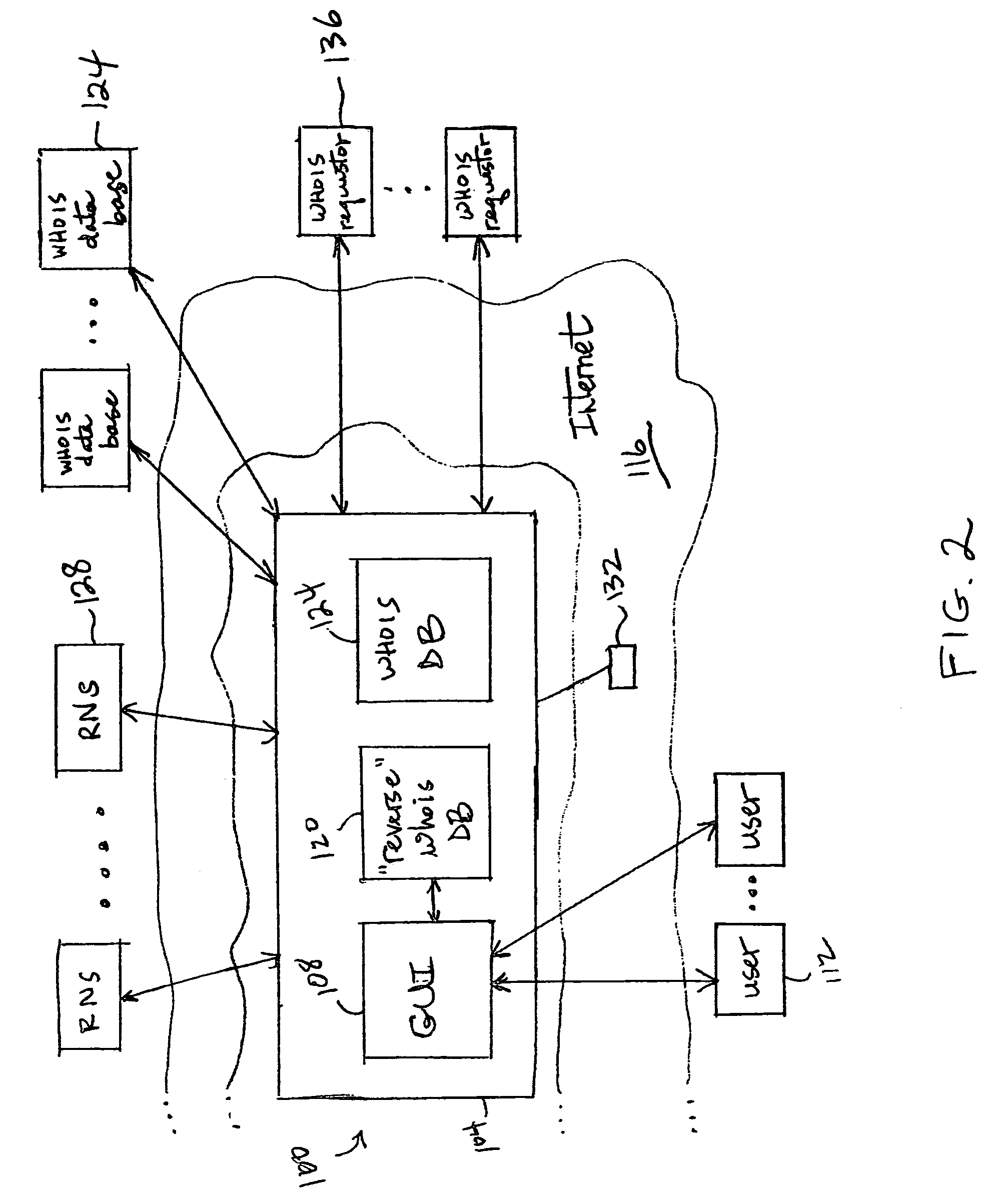
Policing internet domains
ActiveUS7548968B1Computer security arrangementsMultiple digital computer combinationsDomain nameSoftware
The present invention, in one set of embodiments, provides methods, systems and software that may be used to generate and manage enforcement actions against domains that are potentially and / or actually infringing rights of a user. Merely by way of example, some embodiments provide methods for identifying one or more domain names potentially subject to enforcement activity by a user. According to further embodiments, methods are provided for obtaining domain information regarding potential and / or actual infringing domains for a user. In certain embodiments, the present invention provides methods for analyzing domain information concerning potential and / or actual infringing domains and generating one or more enforcement messages for sending to one or more parties associated with the potentially and / or actually infringing domain names.
Owner:MARKMONITOR
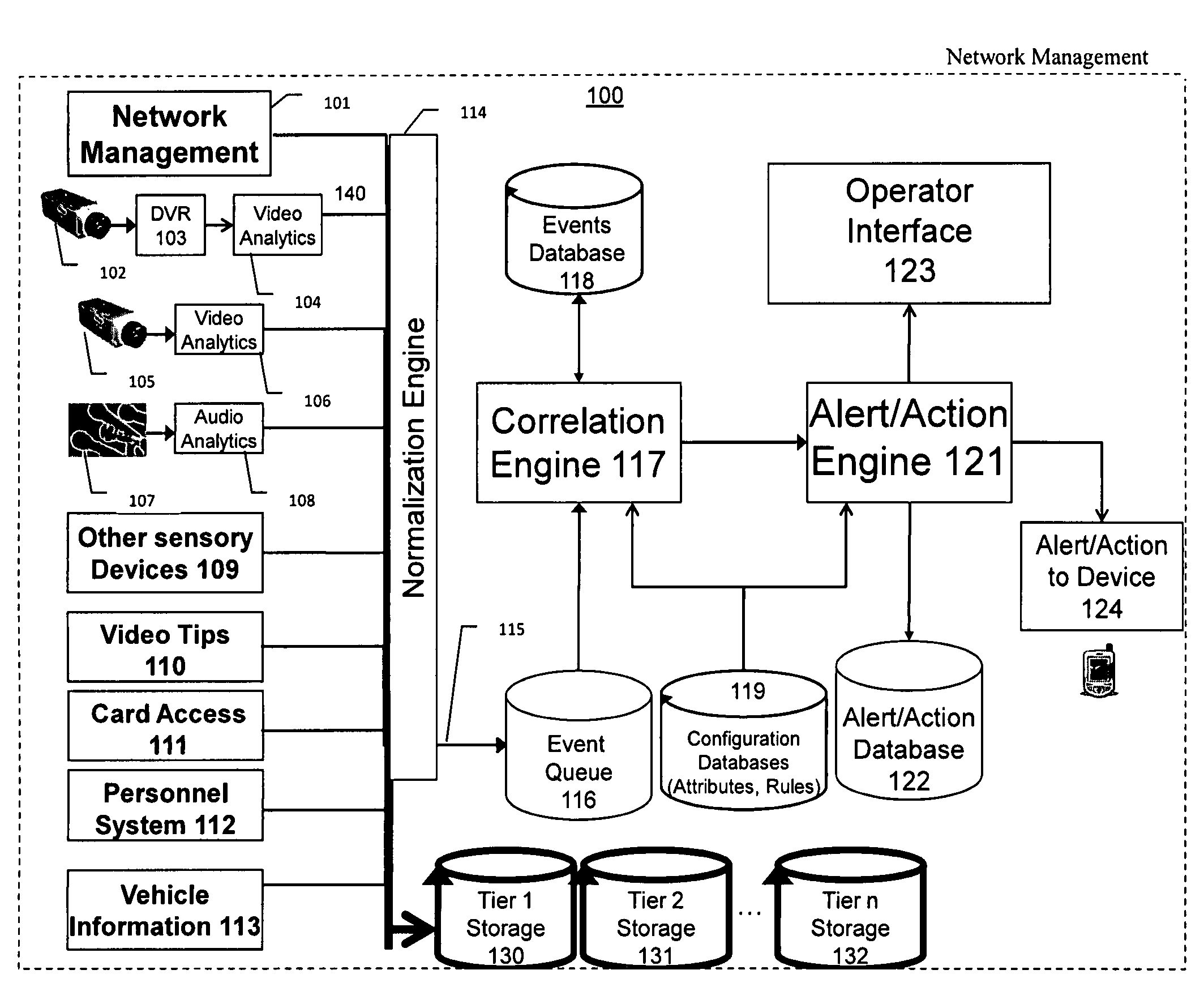
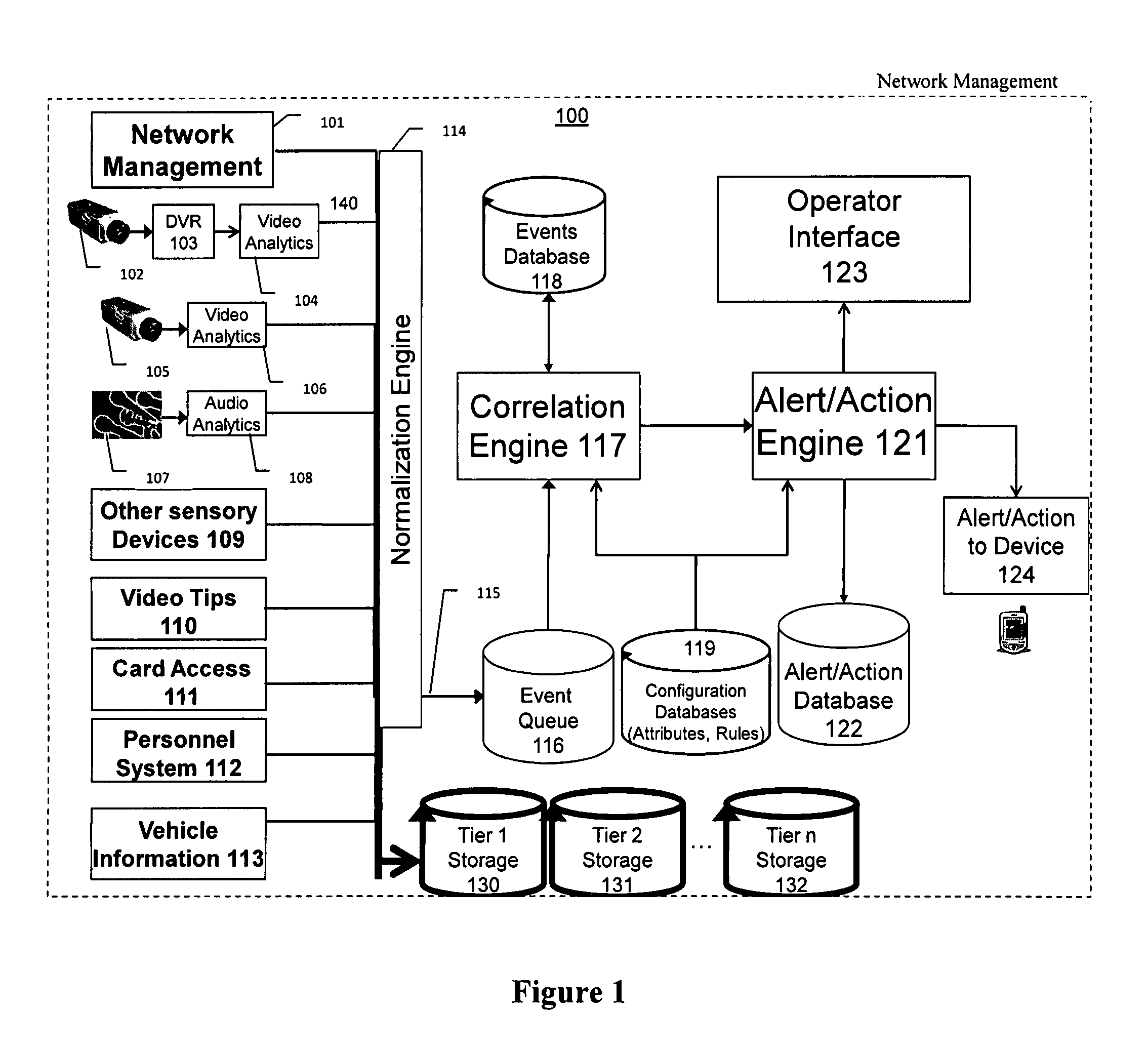
Video surveillance, storage, and alerting system having network management, hierarchical data storage, video tip processing, and vehicle plate analysis
ActiveUS7382244B1Television system detailsFrequency-division multiplex detailsVideo monitoringDriver/operator
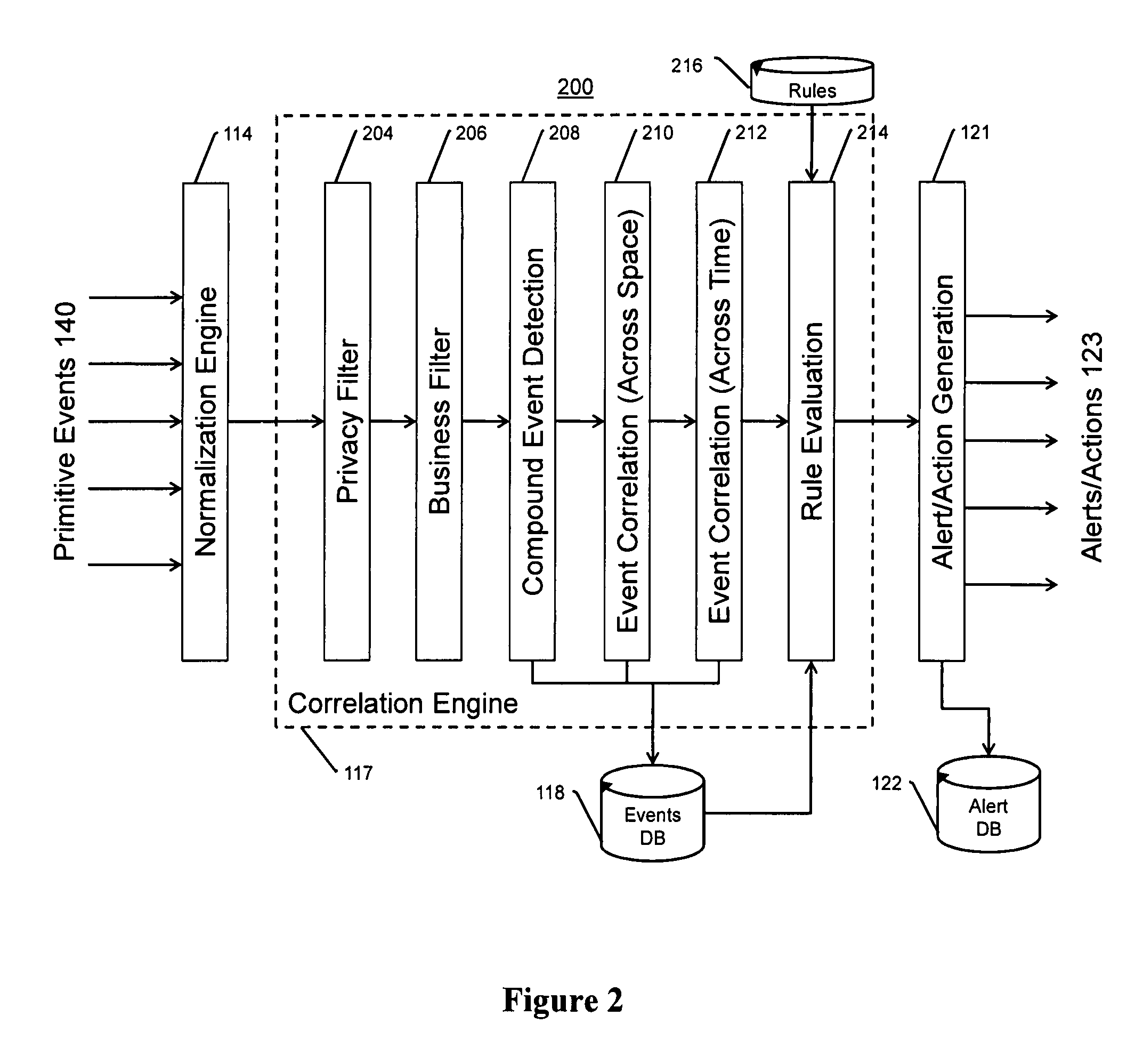
The present invention is a video surveillance, storage, and alerting system having surveillance cameras, video analytics devices, audio sensory devices, other sensory devices, and a plurality of data storage devices. A network management module monitors network status of all subsystems including cameras, servers, storage devices, etc. and shows actively monitored areas on a physical map. A vehicle information module retrieves information from a law enforcement database about vehicles detected in the video data based on the vehicle's license plate, including information about stolen vehicles, as well as warrant, wanted person, and mug shot information for registered drivers of the vehicles. Video tips are received and processed from anonymous and non-anonymous sources. A correlation engine correlates primitive events and compound events from each of the subsystems, weighted by attributes of the events, across both space and time, and an alerting engine generates alerts and performs actions based on the correlation. A hierarchical storage manager manages storage of the vast amounts of data, including video data, based on importance of the data calculated from attributes of the data. A privacy filter ensures no private data is detected, correlated, or stored.
Owner:SECURENET SOLUTIONS GRP
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com