Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
291 results about "Digital rights management system" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
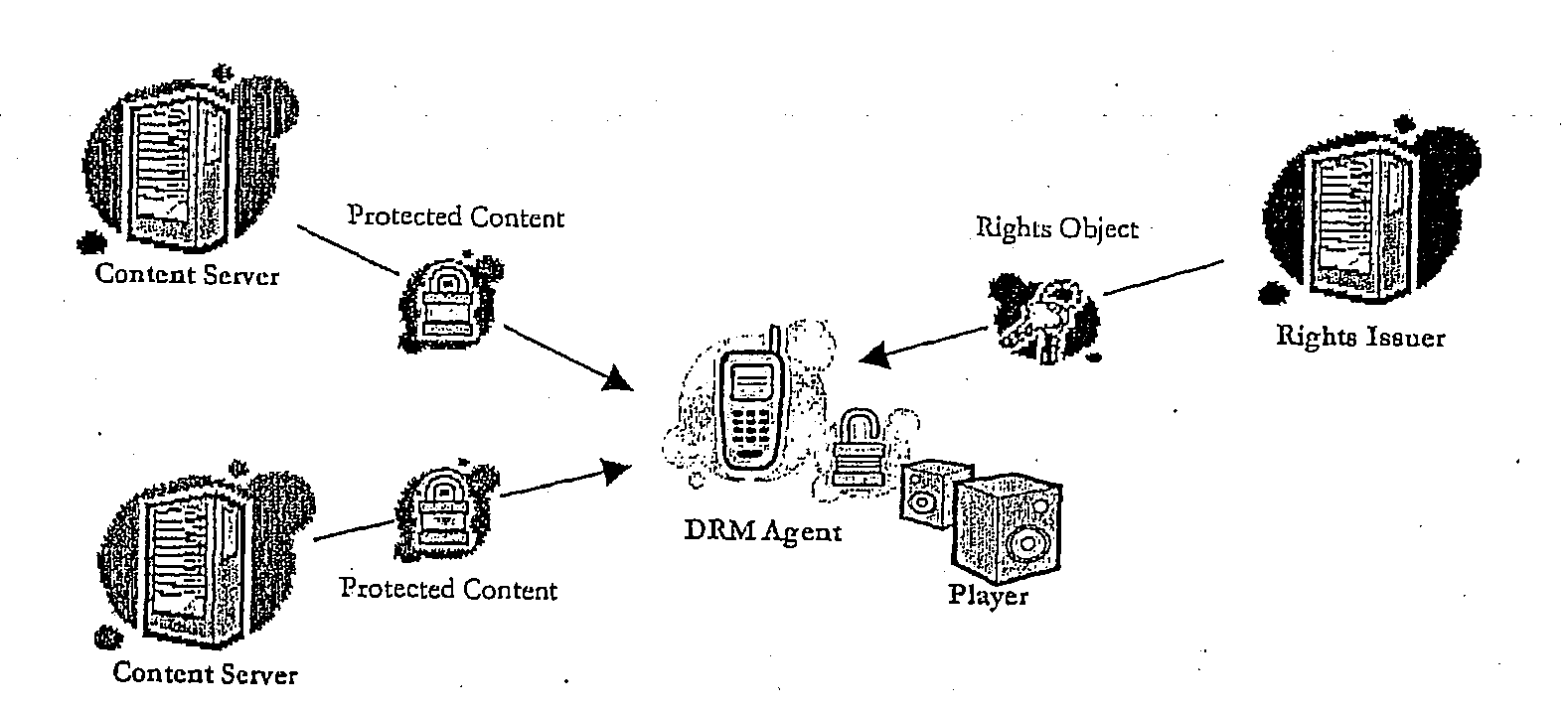
Digital rights management (DRM) is a systematic approach to copyright protection for digital media. The purpose of DRM is to prevent unauthorized redistribution of digital media and restrict the ways consumers can copy content they've purchased.
Method of Providing Digital Rights Management for Music Content by Means of a Flat-Rate Subscription
ActiveUS20100031366A1Reliable and goodEasy to manageMetering/charging/biilling arrangementsDigital data processing detailsOperational systemComputer network
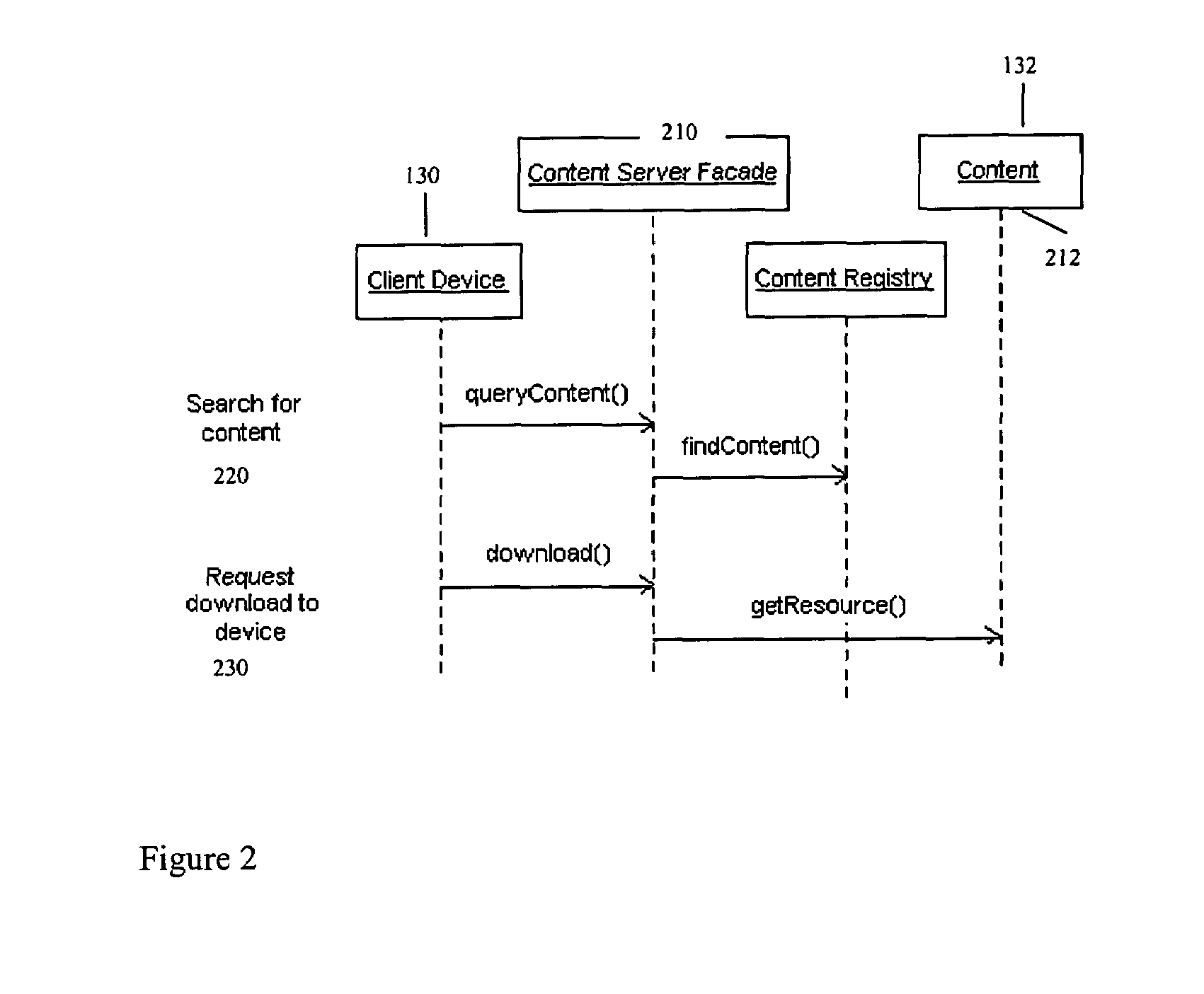
The invention enables digital music content to be downloaded to and used on a portable wireless computing device. An application running on the wireless device has been automatically adapted to parameters associated with the wireless device without end-user input (e.g. the application has been configured in dependence on the device OS and firmware, related bugs, screen size, pixel number, security models, connection handling, memory etc. This application enables an end-user to browse and search music content on a remote server using a wireless network; to download music content from that remote server using the wireless network and to playback and manage that downloaded music content. The application also includes a digital rights management system that enables unlimited legal downloads of different music tracks to the device and also enables any of those tracks stored on the device to be played so long as a subscription service has not terminated.
Owner:TIKTOK PTE LTD
Method and system for binding enhanced software features to a persona
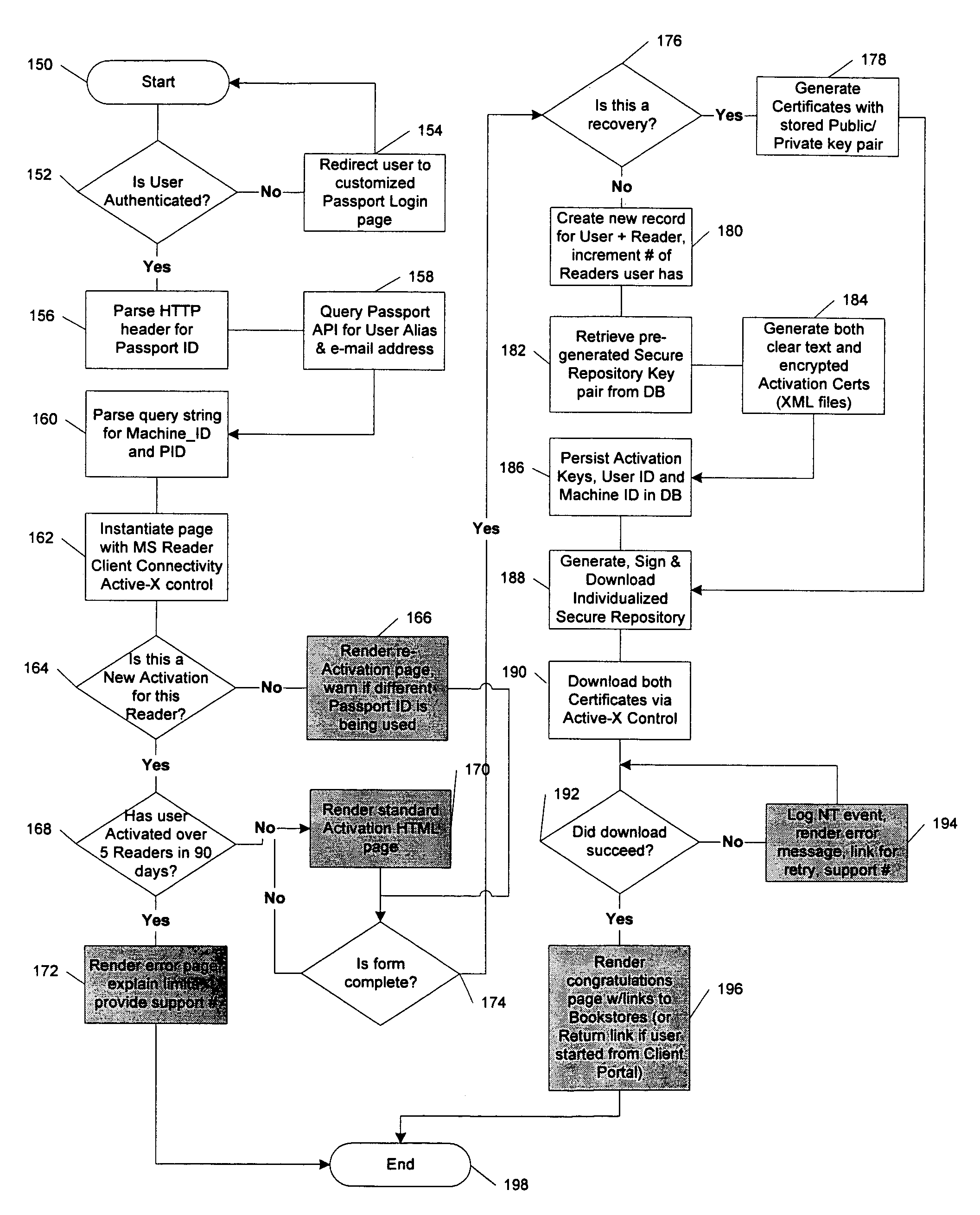
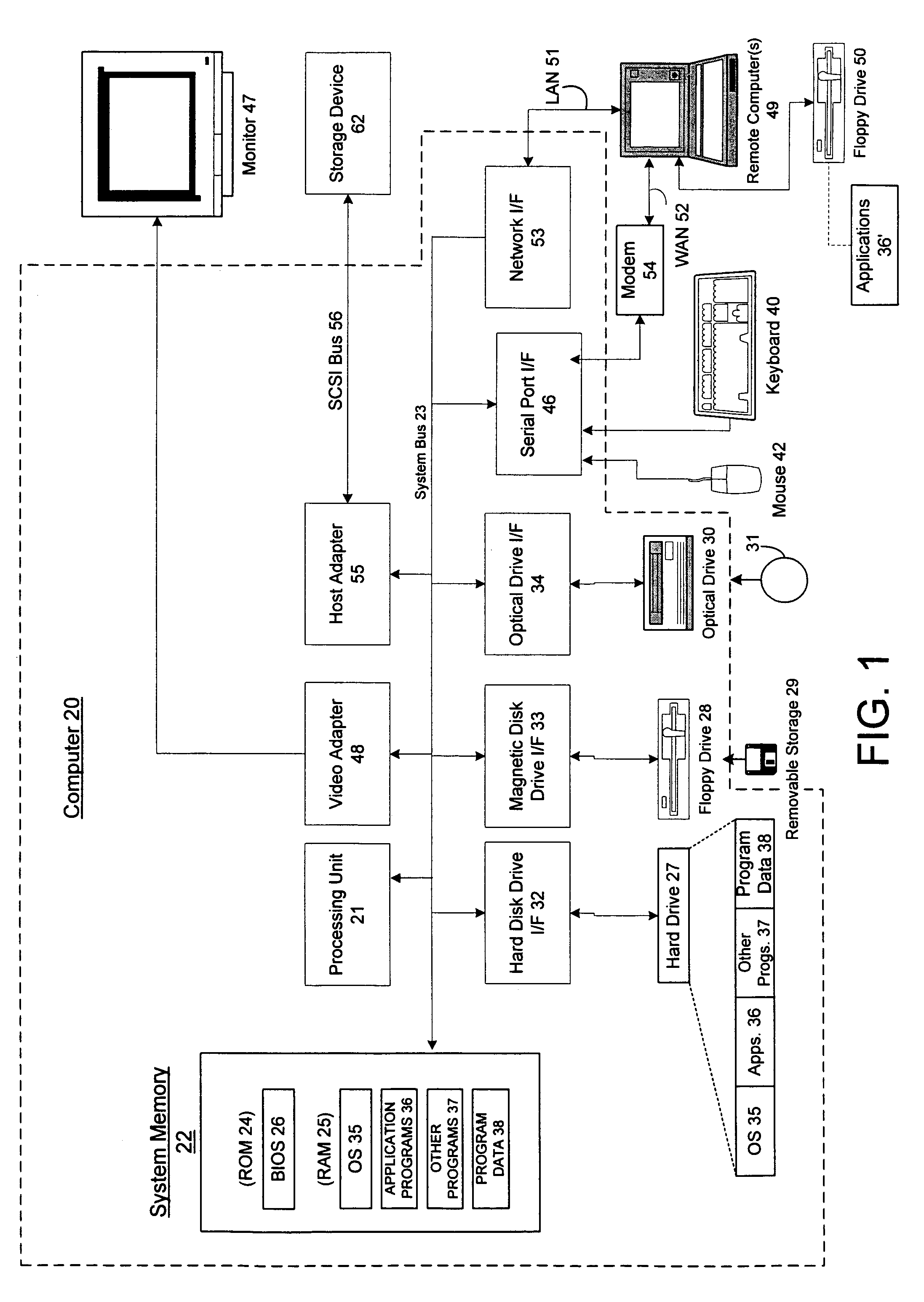
InactiveUS6891953B1Preventing unchecked proliferationKey distribution for secure communicationDigital data processing detailsBiological activationUniform resource locator
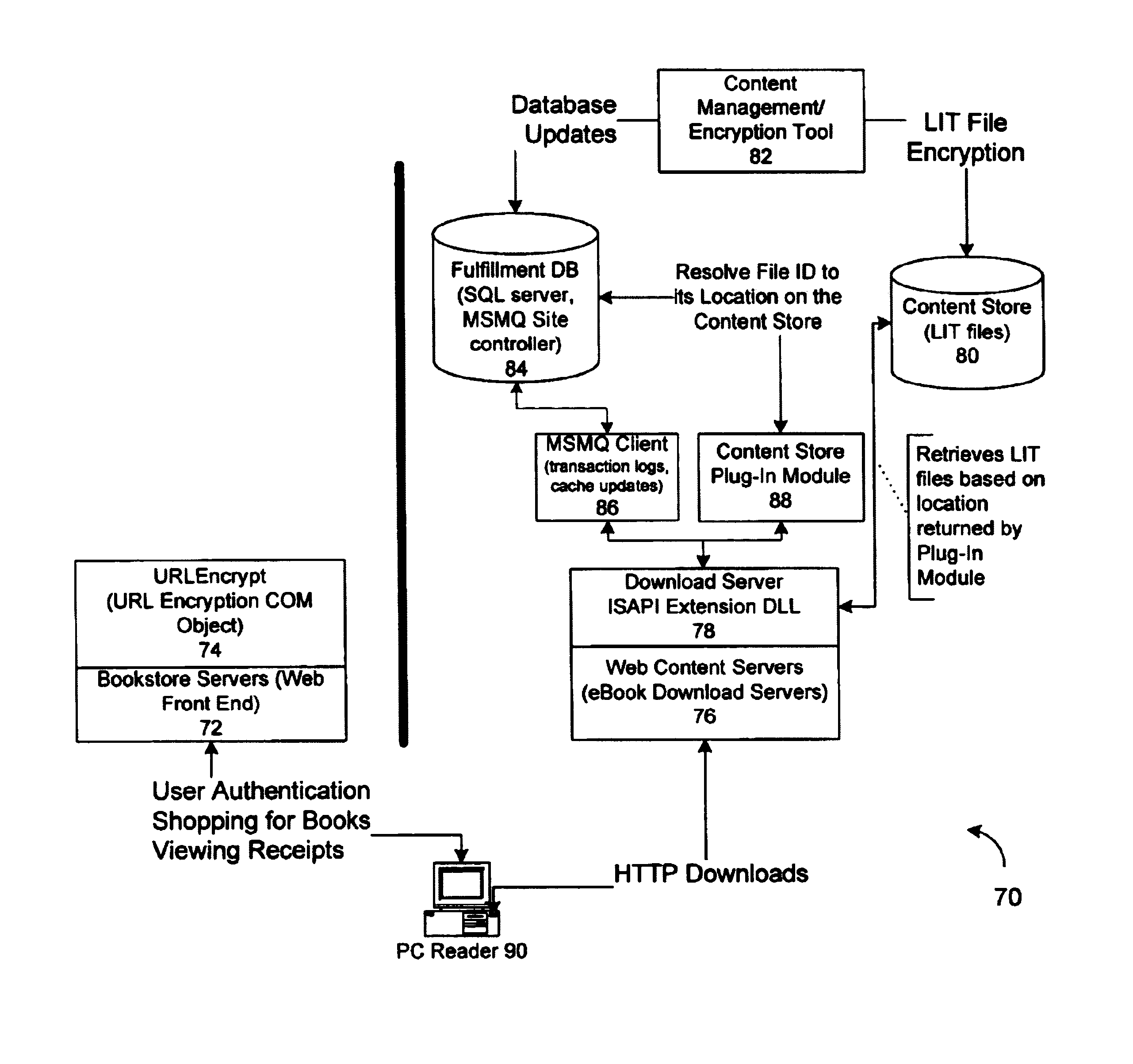
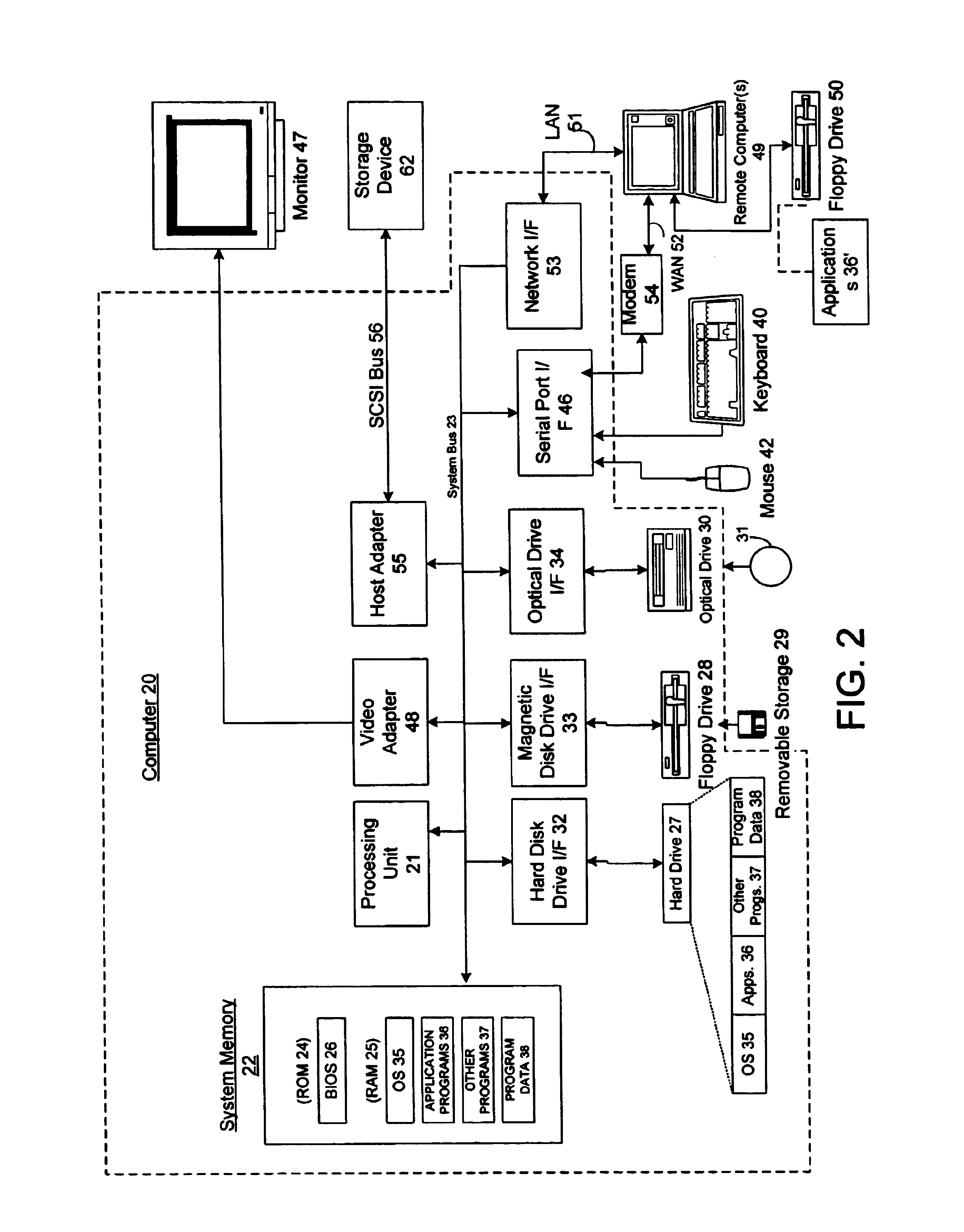
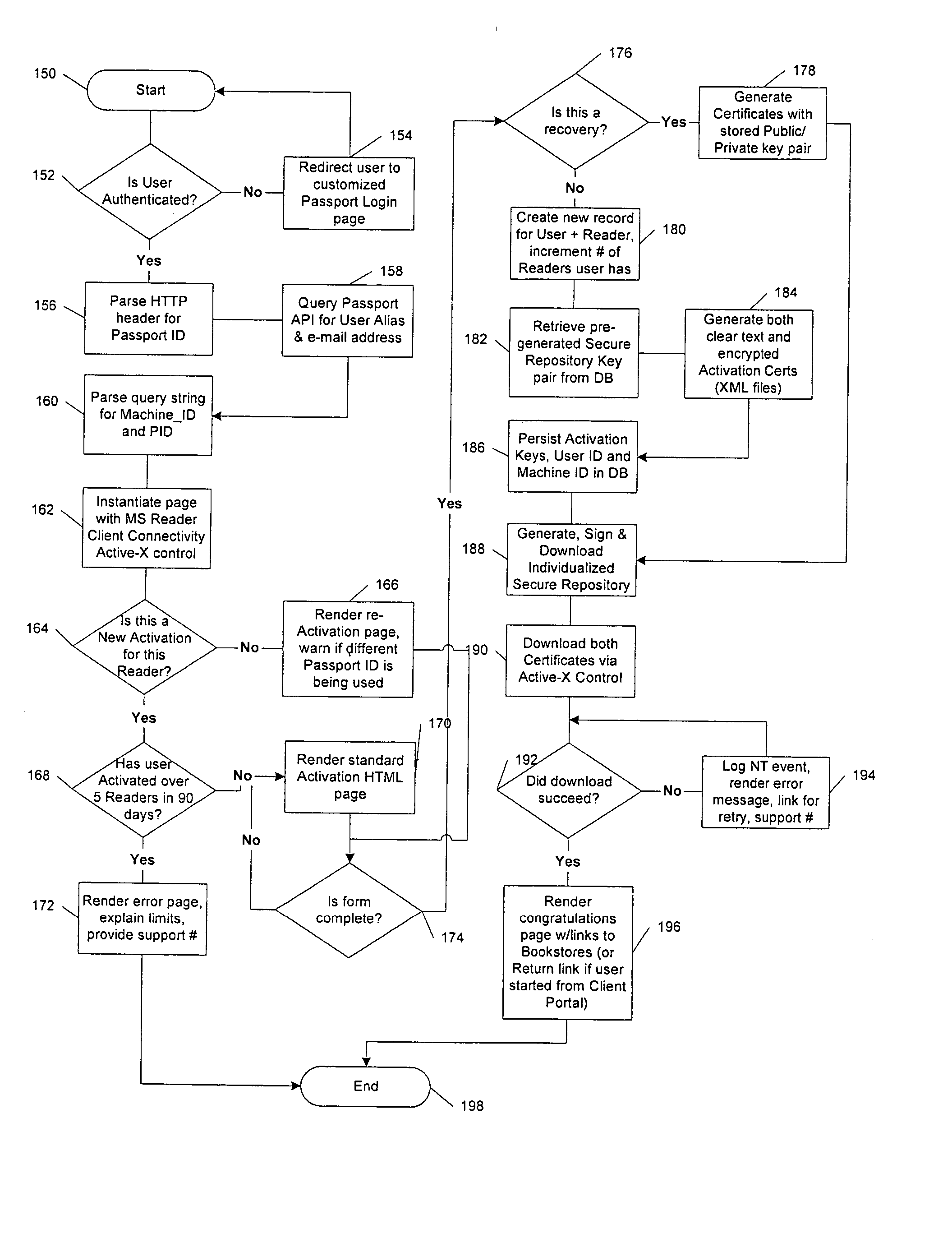
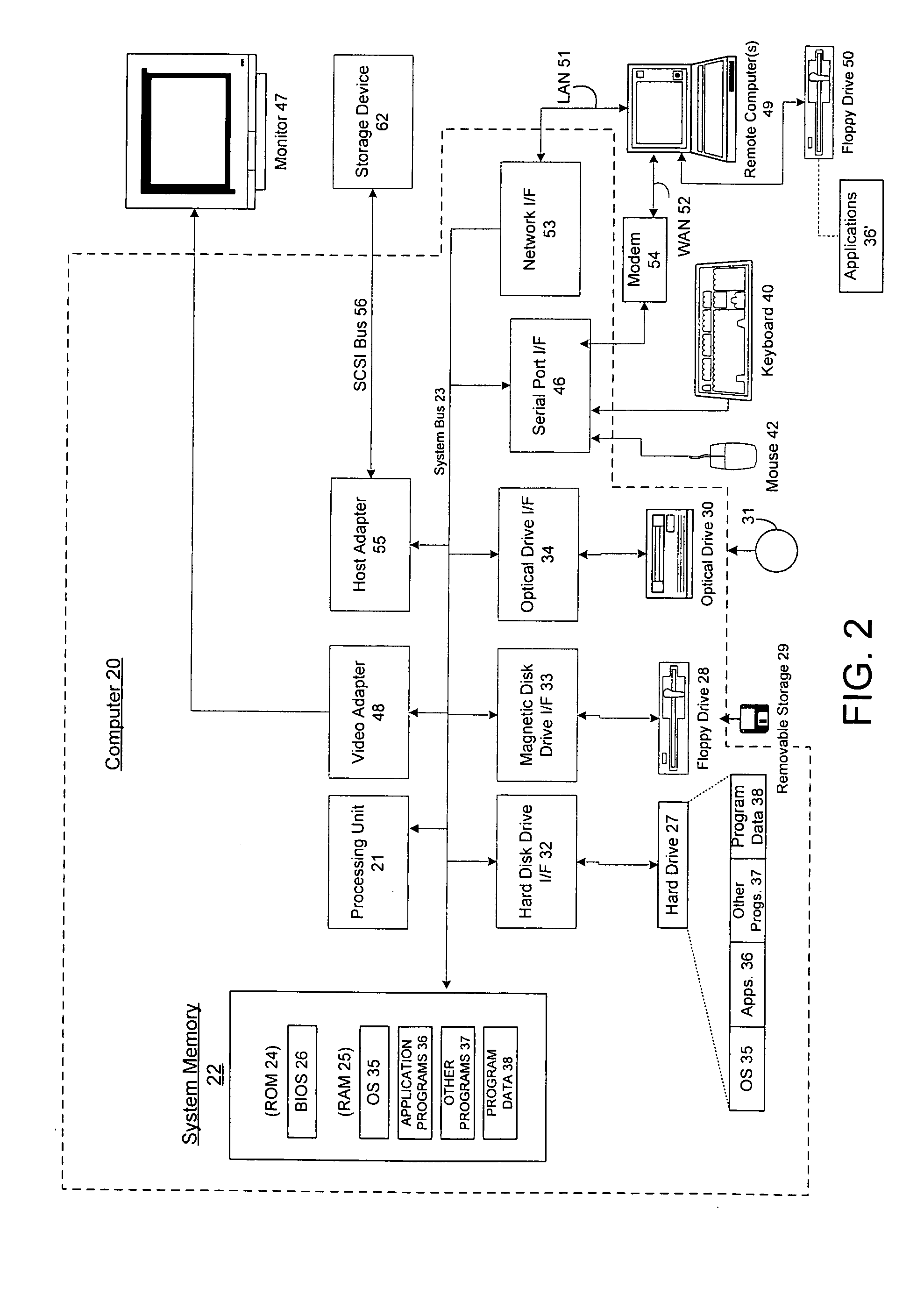
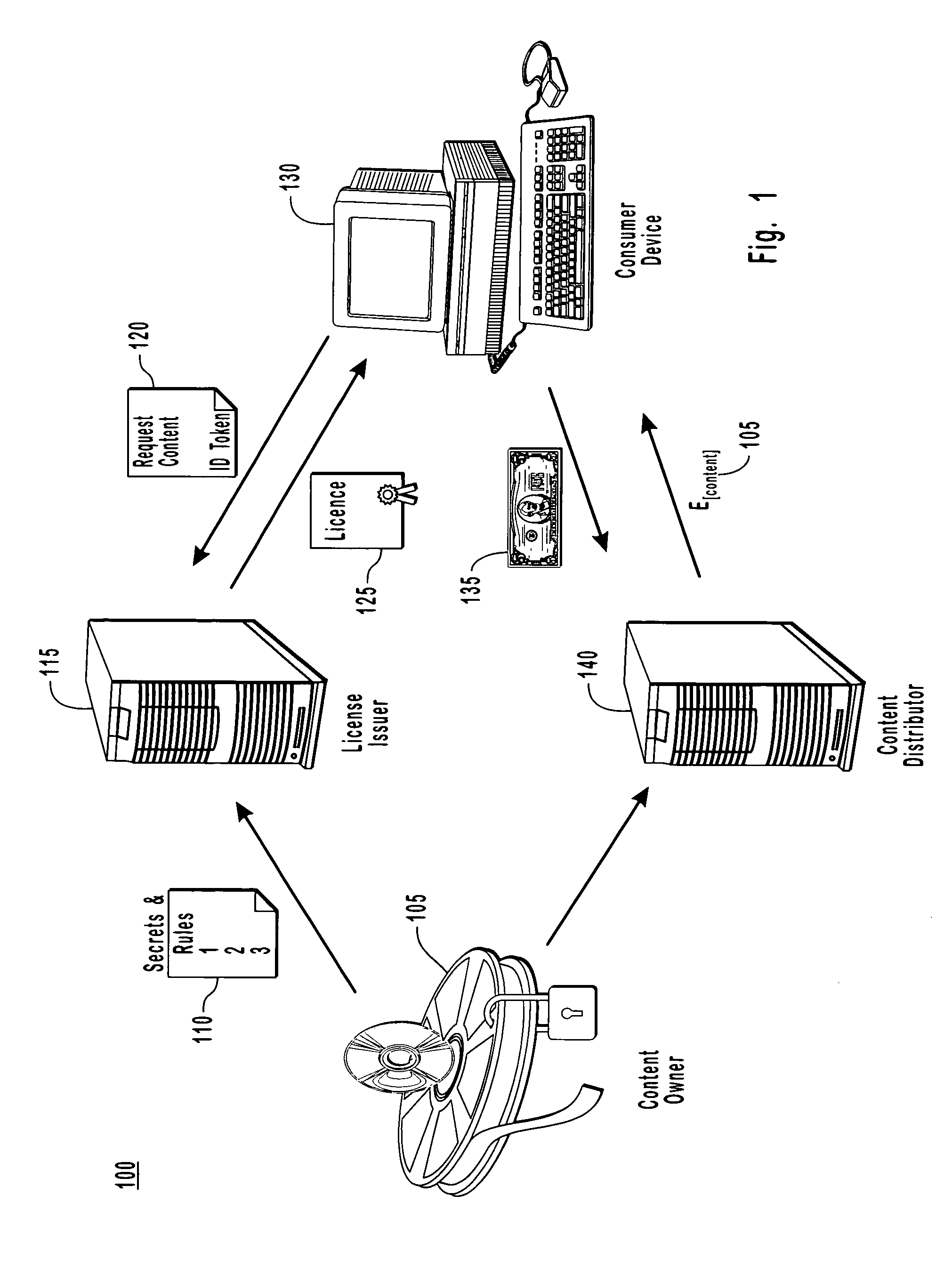
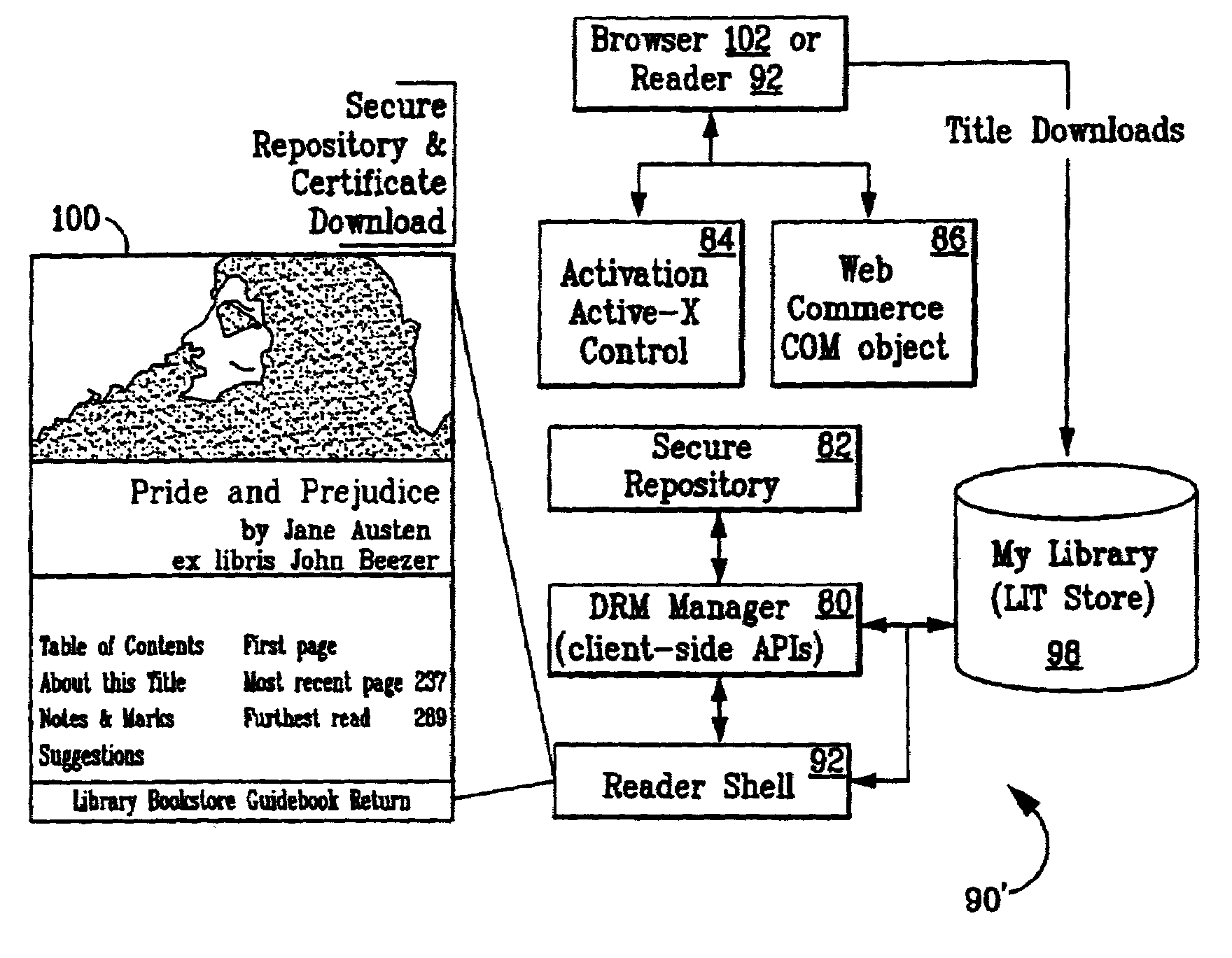
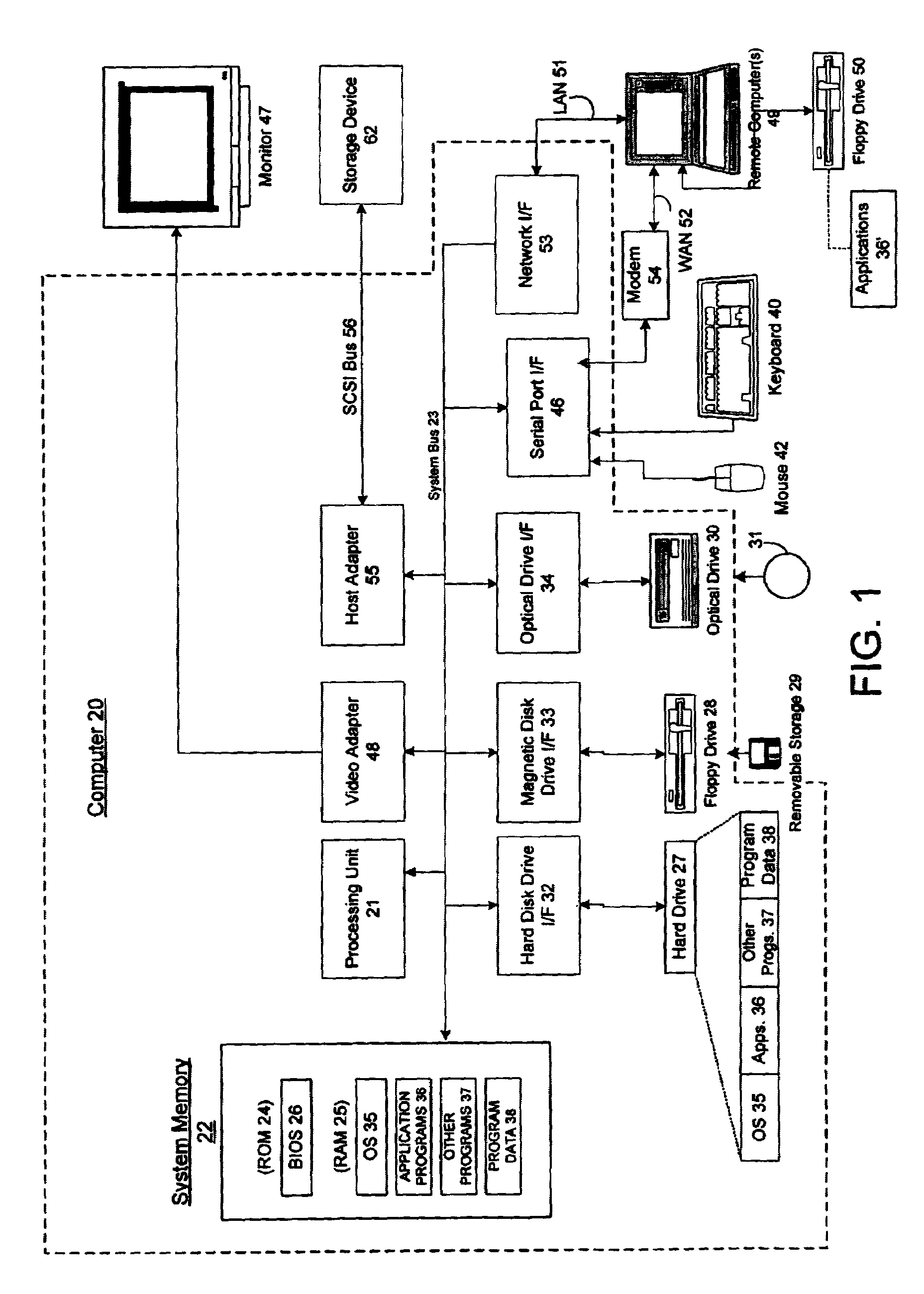
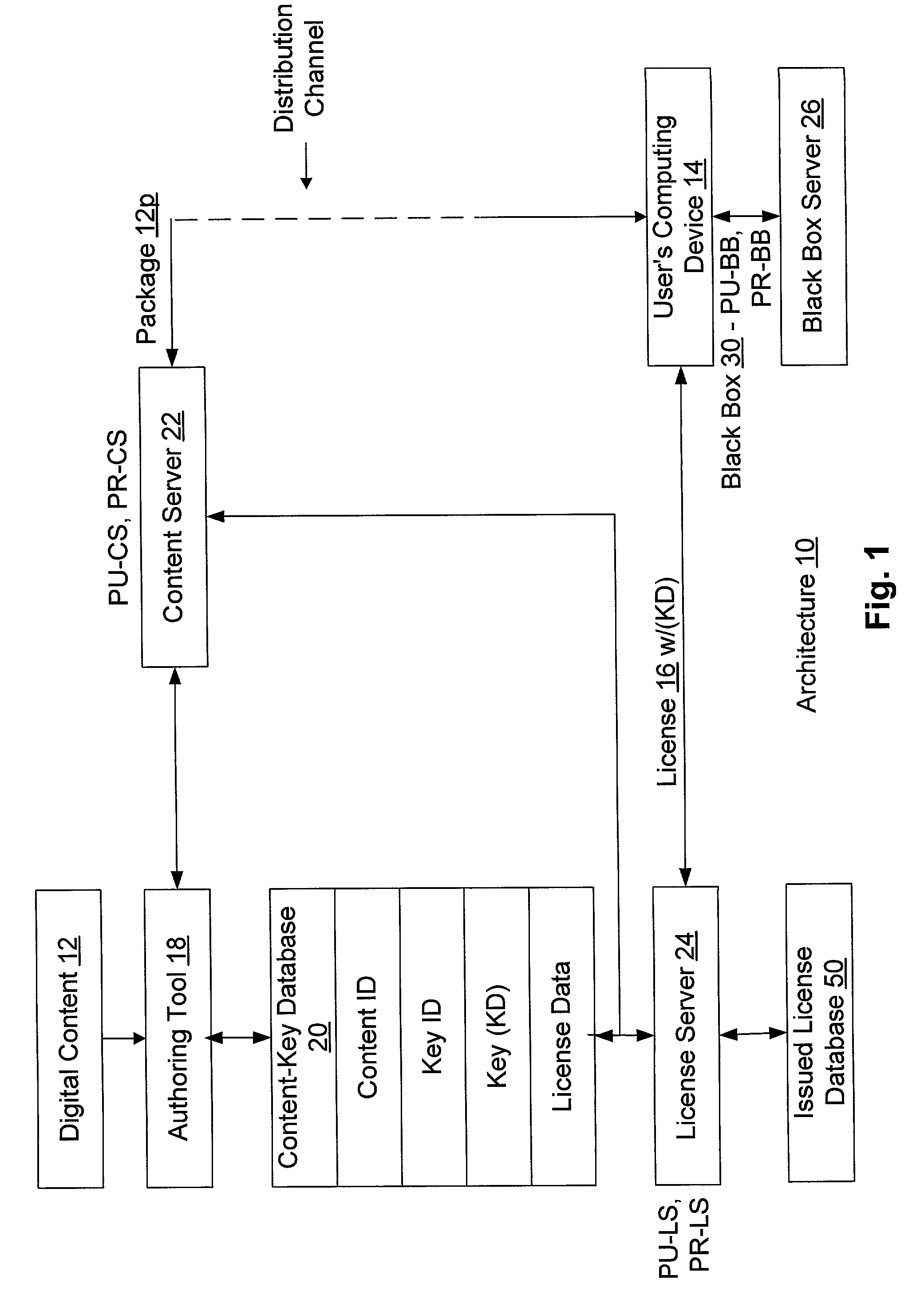
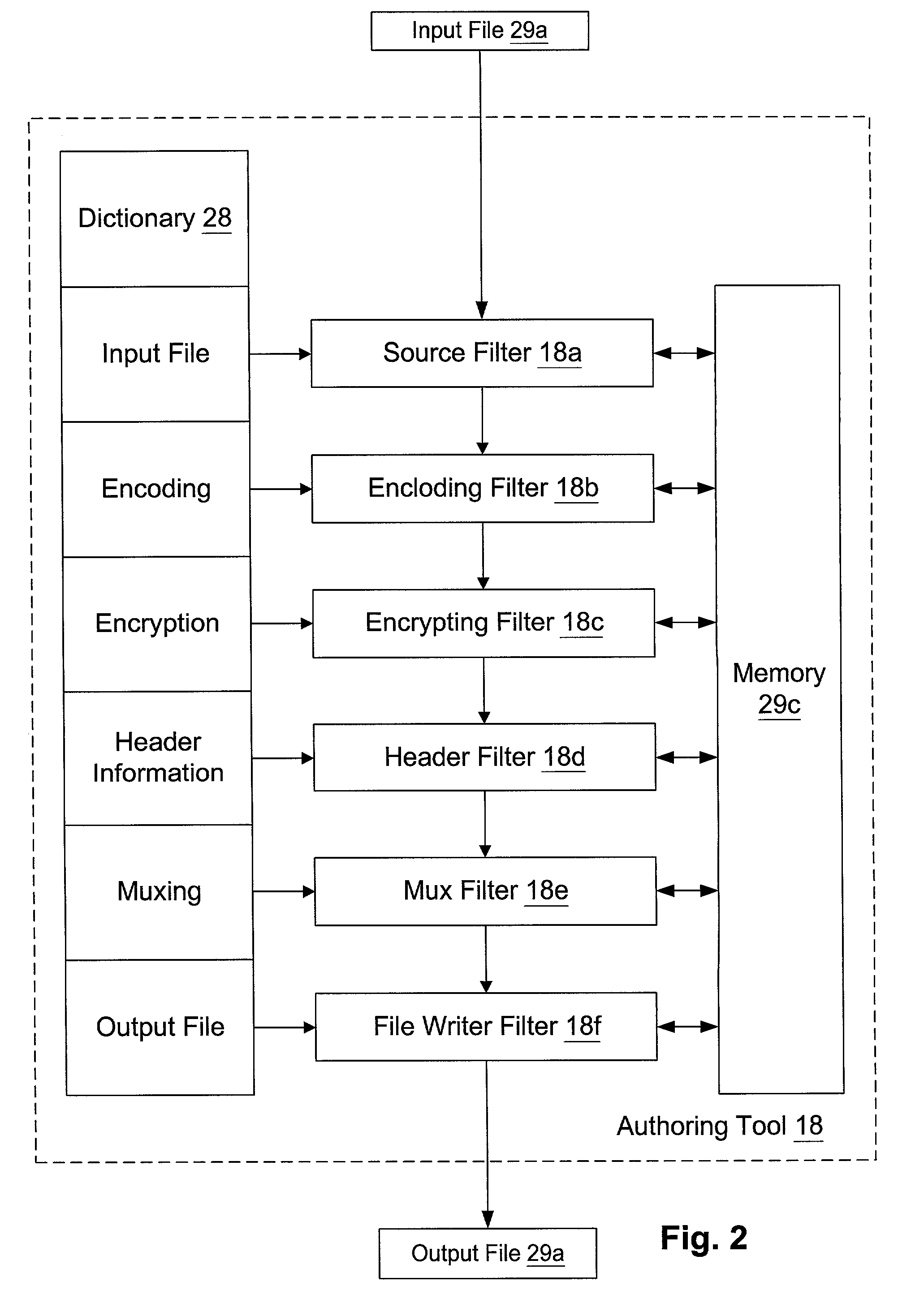
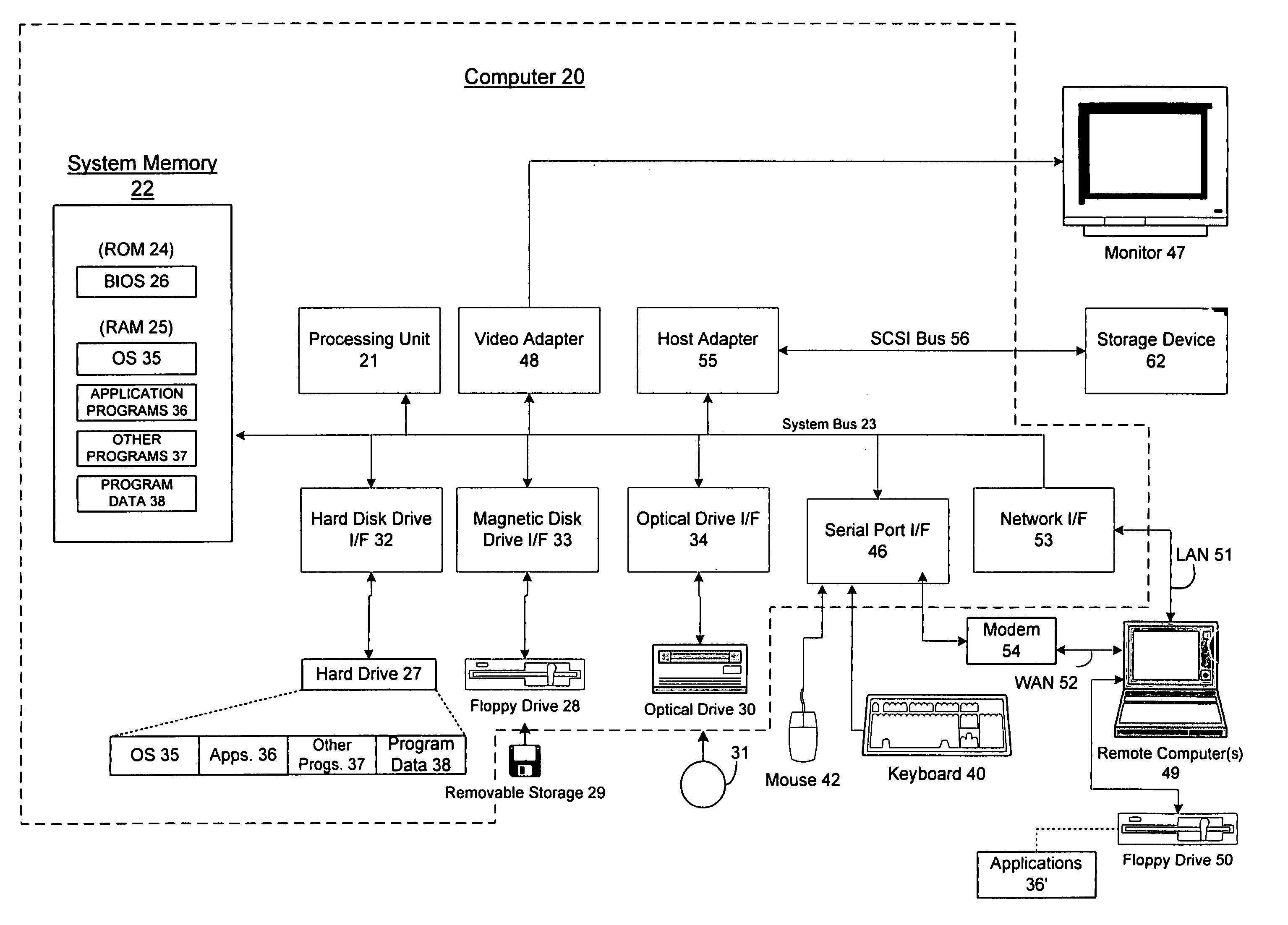
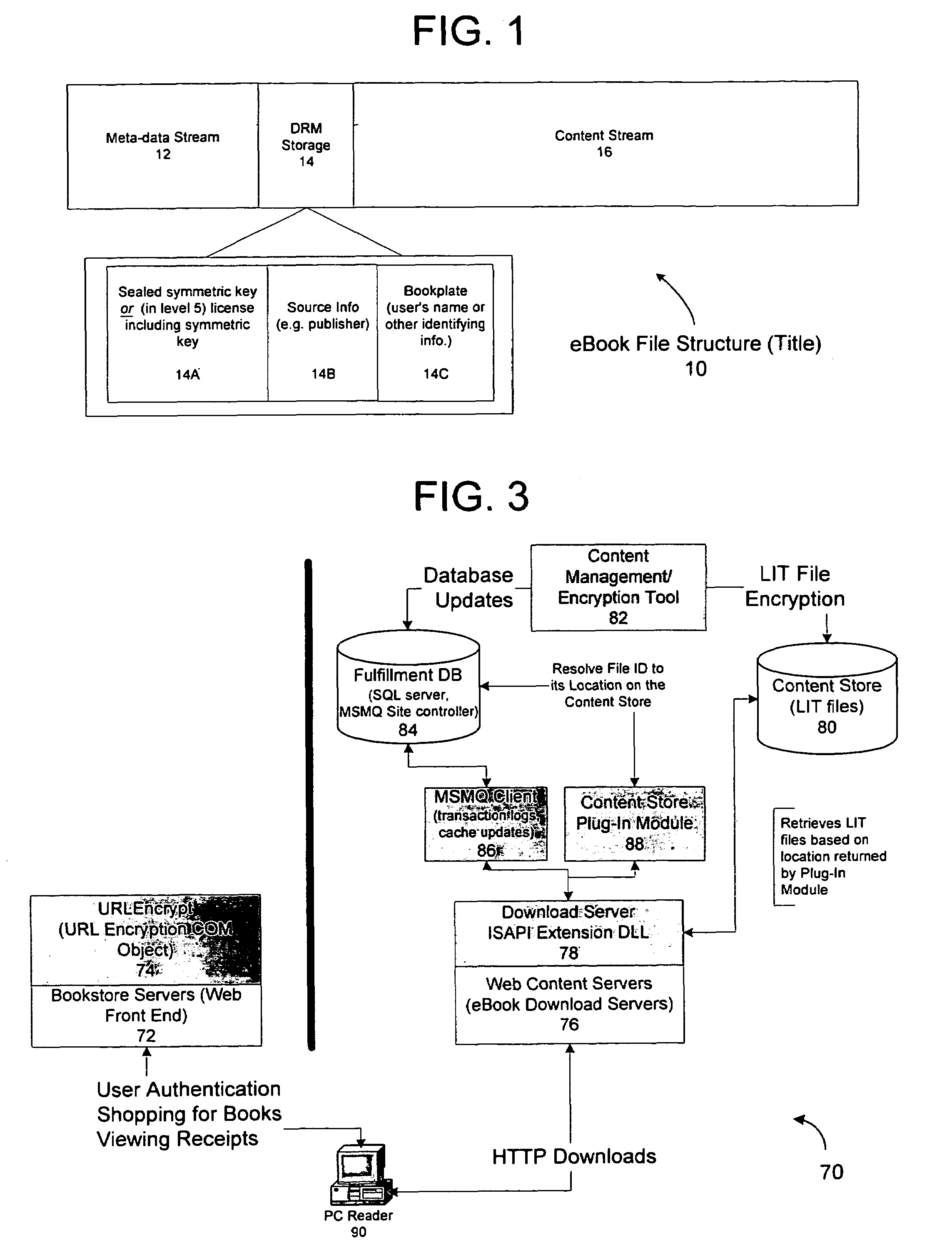
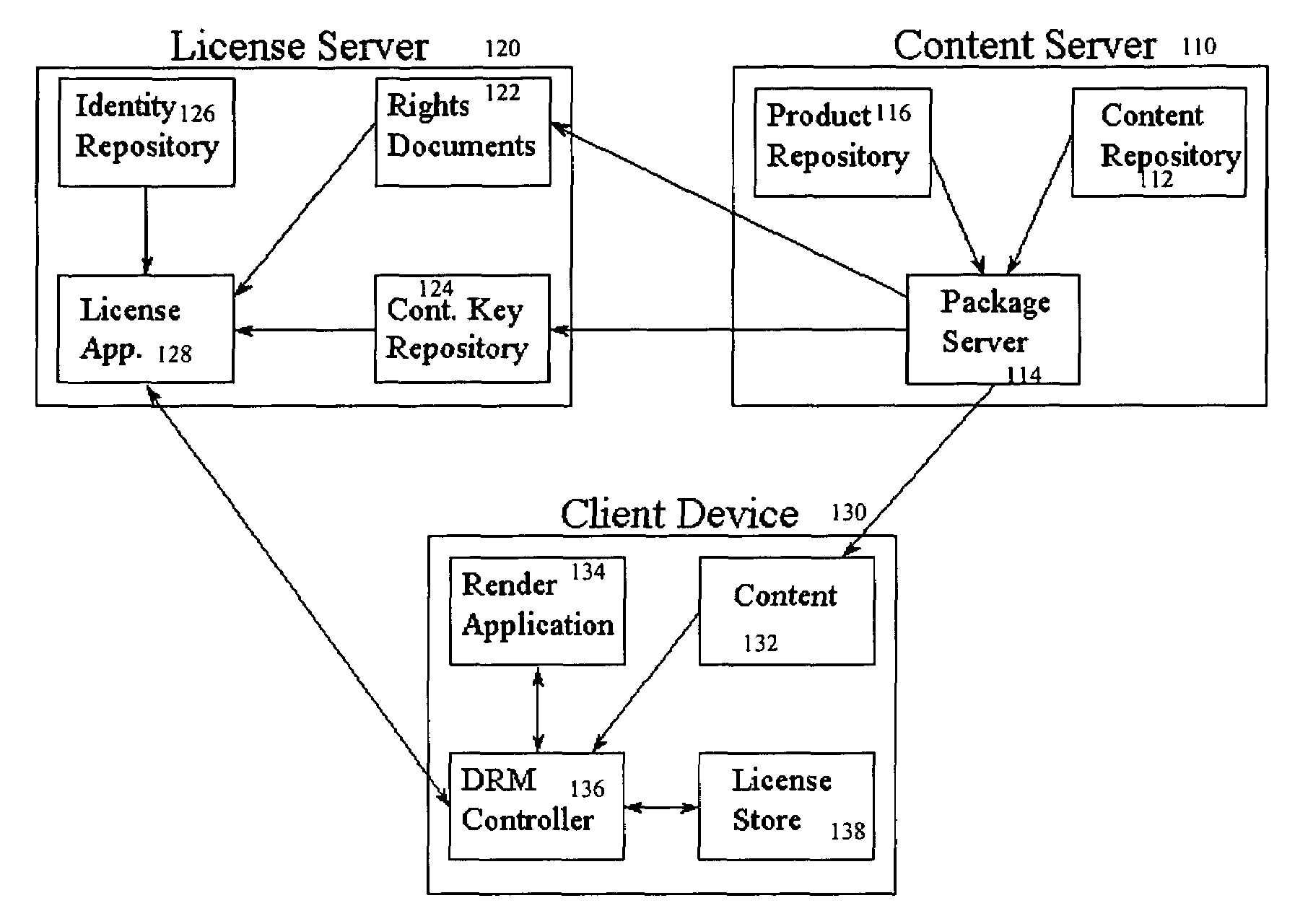
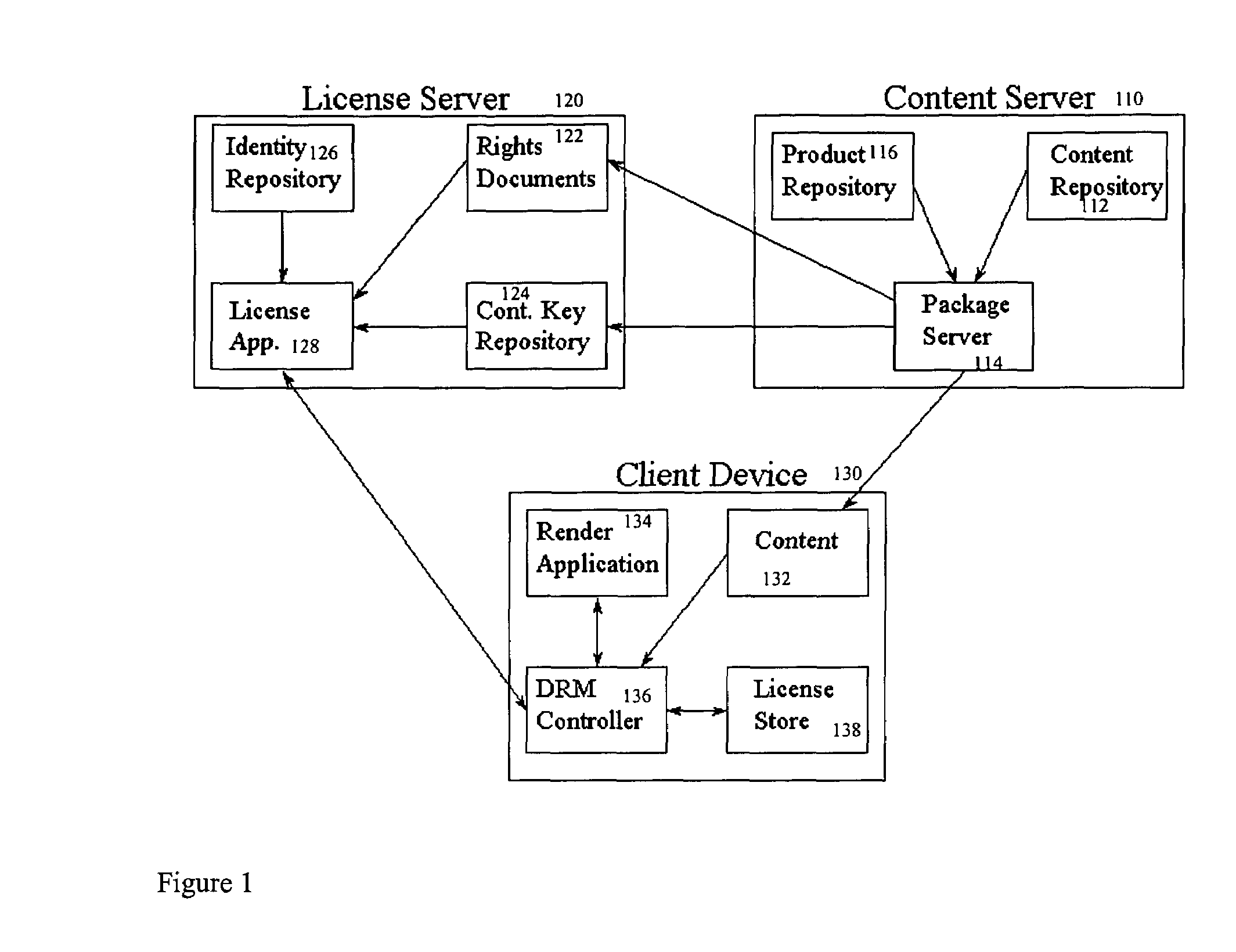
A server architecture for a digital rights management system that distributes and protects rights in content. The server architecture includes a retail site which sells content items to consumers, a fulfillment site which provides to consumers the content items sold by the retail site, and an activation site which enables consumer reading devices to use content items having an enhanced level of copy protection. Each retail site is equipped with a URL encryption object, which encrypts, according to a secret symmetric key shared between the retail site and the fulfillment site, information that is needed by the fulfillment site to process an order for content sold by the retail site. Upon selling a content item, the retail site transmits to the purchaser a web page having a link to a URL comprising the address of the fulfillment site and a parameter having the encrypted information. Upon following the link, the fulfillment site downloads the ordered content to the consumer, preparing the content if necessary in accordance with the type of security to be carried with the content. The fulfillment site includes an asynchronous fulfillment pipeline which logs information about processed transactions using a store-and-forward messaging service. The fulfillment site may be implemented as several server devices, each having a cache which stores frequently downloaded content items, in which case the asynchronous fulfillment pipeline may also be used to invalidate the cache if a change is made at one server that affects the cached content items. An activation site provides an activation certificate and a secure repository executable to consumer content-rendering devices which enables those content rendering devices to render content having an enhanced level of copy-resistance. The activation site “activates” client-reading devices in a way that binds them to a persona, and limits the number of devices that may be activated for a particular persona, or the rate at which such devices may be activated for a particular persona.
Owner:MICROSOFT TECH LICENSING LLC
Server for an electronic distribution system and method of operating same
ActiveUS7047411B1Preventing unchecked proliferationKey distribution for secure communicationUser identity/authority verificationStore and forwardDigital rights management system
A server architecture for a digital rights management system that distributes and protects rights in content. The server architecture includes a retail site which sells content items to consumers, a fulfillment site which provides to consumers the content items sold by the retail site, and an activation site which enables consumer reading devices to use content items having an enhanced level of copy protection. Each retail site is equipped with a URL encryption object, which encrypts, according to a secret symmetric key shared between the retail site and the fulfillment site, information that is needed by the fulfillment site to process an order for content sold by the retail site. Upon selling a content items, the retail site transmits to the purchase a web page having a link to a URL comprising the address of the fulfillment site and a parameter having the encrypted information. Upon the following the link, the fulfillment site downloads the ordered content to the consumer preparing the content if necessary in accordance with the type of security to be carried with the content. The fulfillment site includes an asynchronous fulfillment pipeline which logs information about processed transactions using a store-and-forward messaging service. The fulfillment site may be implemented as several server devices, each having a cache which stores frequently downloaded content items, in which case the asynchronous fulfillment pipeline may also be used to invalidate the cache if a change is made at one server that affects the cached content items. An activation site provides an activation certificate and a secure repository executable to consumer content-rendering devices which enable those content rendering devices to render content having an enhanced level of copy-resistance. The activation site “activates” client-reading devices in a way that binds them to a persona, and limits the number of devices that may be activated for a particular persona, or the rate at which such devices may be activated for a particular persona.
Owner:MICROSOFT TECH LICENSING LLC
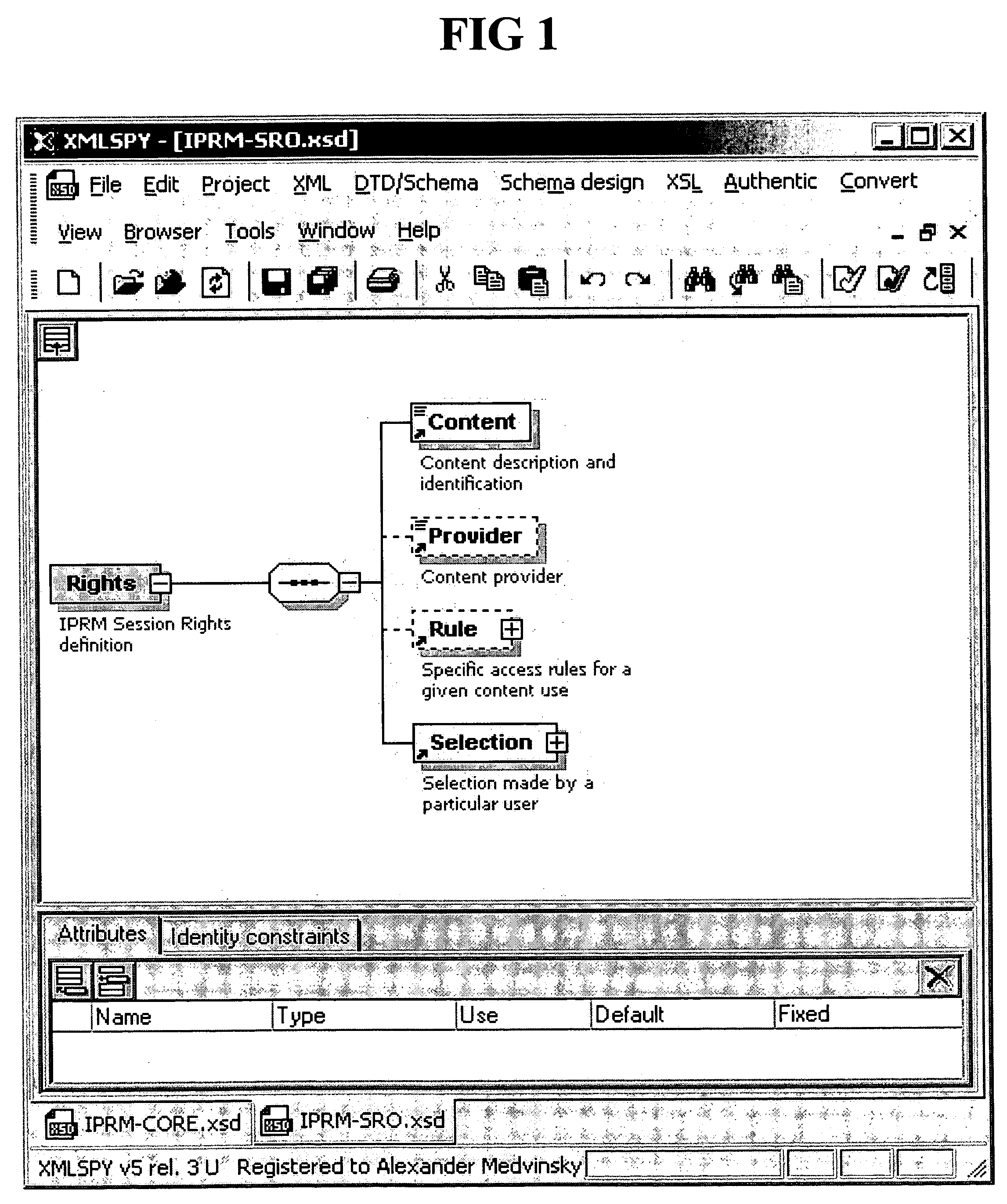
Method and system for limiting the use of user-specific software features
InactiveUS20050060266A1Preventing unchecked proliferationDigital data processing detailsUser identity/authority verificationSchema for Object-Oriented XMLUniform resource locator
A server architecture for a digital rights management system that distributes and protects rights in content. The server architecture includes a retail site which sells content items to consumers, a fulfillment site which provides to consumers the content items sold by the retail site, and an activation site which enables consumer reading devices to use content items having an enhanced level of copy protection. Each retail site is equipped with a URL encryption object, which encrypts, according to a secret symmetric key shared between the retail site and the fulfillment site, information that is needed by the fulfillment site to process an order for content sold by the retail site. Upon selling a content item, the retail site transmits to the purchaser a web page having a link to a URL comprising the address of the fulfillment site and a parameter having the encrypted information. Upon following the link, the fulfillment site downloads the ordered content to the consumer, preparing the content if necessary in accordance with the type of security to be carried with the content. The fulfillment site includes an asynchronous fulfillment pipeline which logs information about processed transactions using a store-and-forward messaging service. The fulfillment site may be implemented as several server devices, each having a cache which stores frequently downloaded content items, in which case the asynchronous fulfillment pipeline may also be used to invalidate the cache if a change is made at one server that affects the cached content items. An activation site provides an activation certificate and a secure repository executable to consumer content-rendering devices which enables those content rendering devices to render content having an enhanced level of copy-resistance. The activation site “activates” client-reading devices in a way that binds them to a persona, and limits the number of devices that may be activated for a particular persona, or the rate at which such devices may be activated for a particular persona.
Owner:MICROSOFT TECH LICENSING LLC
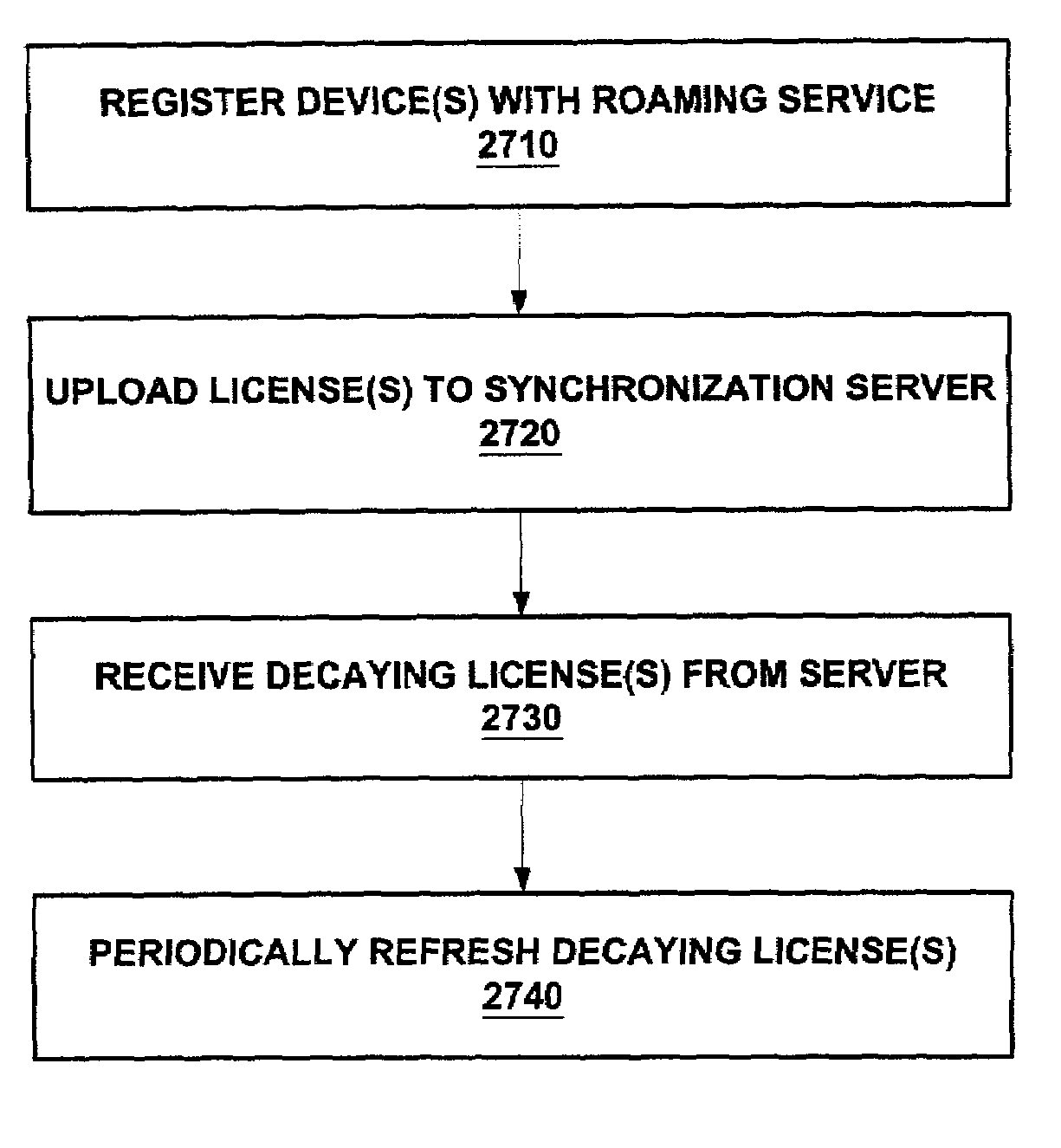
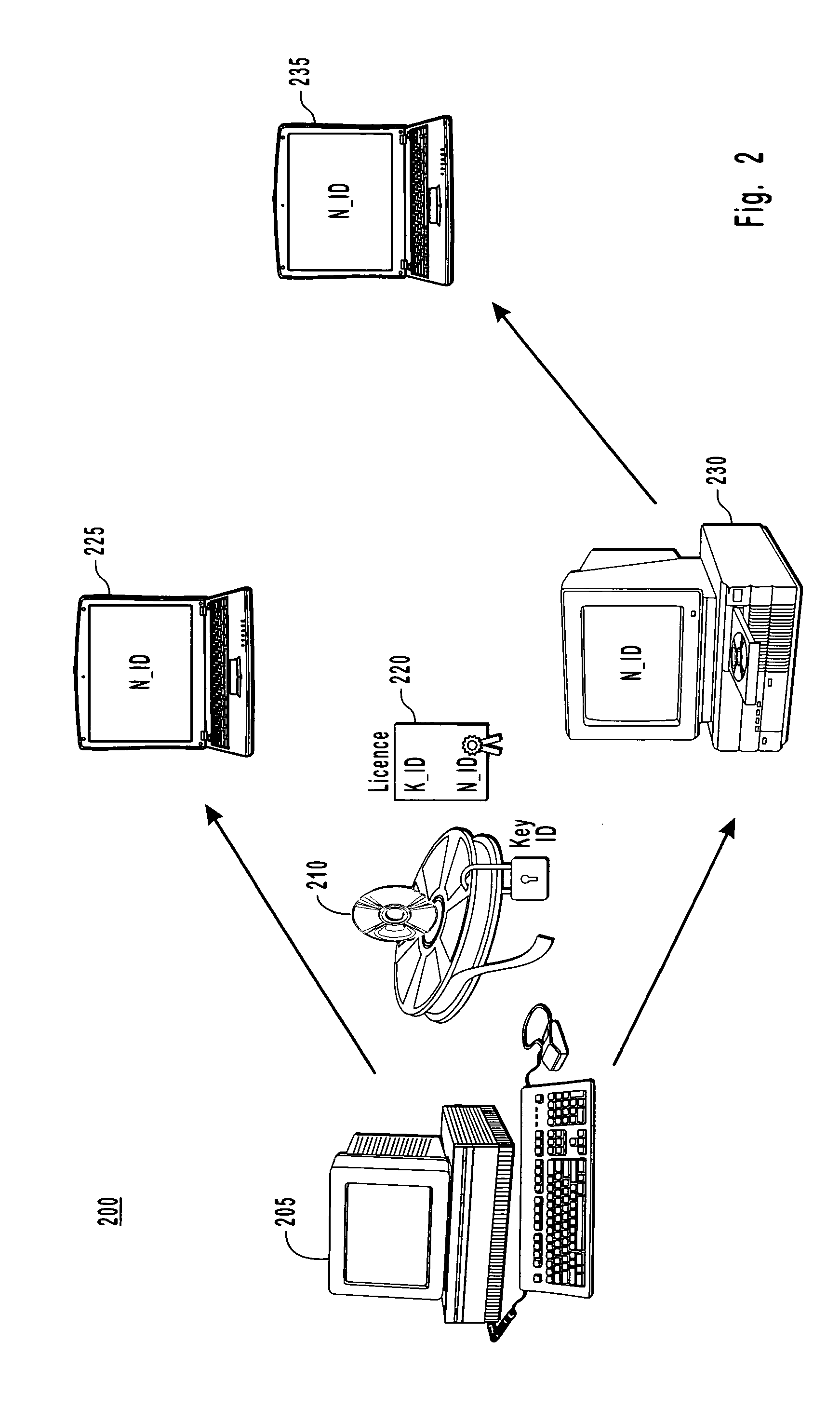
Enforcement architecture and method for digital rights management system for roaming a license to a plurality of user devices
InactiveUS7203966B2Prevent long-term misusePrevent long-term misuse of the systemDigital data processing detailsUnauthorized memory use protectionUser deviceDevice register
An enforcement architecture and method for implementing roaming digital rights management are disclosed. A license distributed from a license server to a computing device of a user may be uploaded to a license synchronization server, and rebound to other devices registered with the service, thereby enabling access to the licensed content from other computing devices. A second digital license of a second computing device is set to expire prior to a first digital license of a first computing device. Reactivating a decayed first digital license, that is deactivated during transmission of the second digital license, to the second device to access content of the first computing device.
Owner:MICROSOFT TECH LICENSING LLC
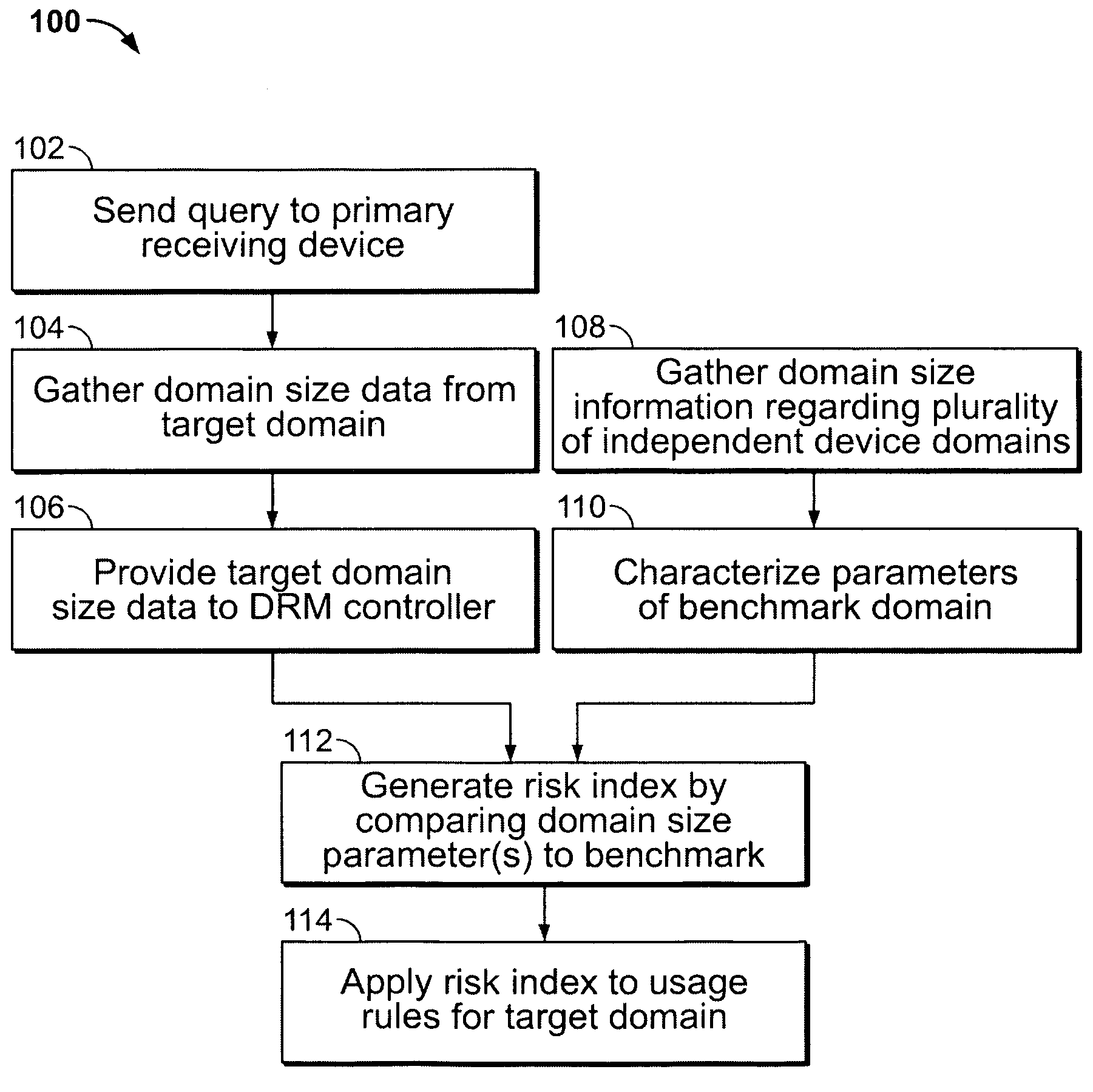
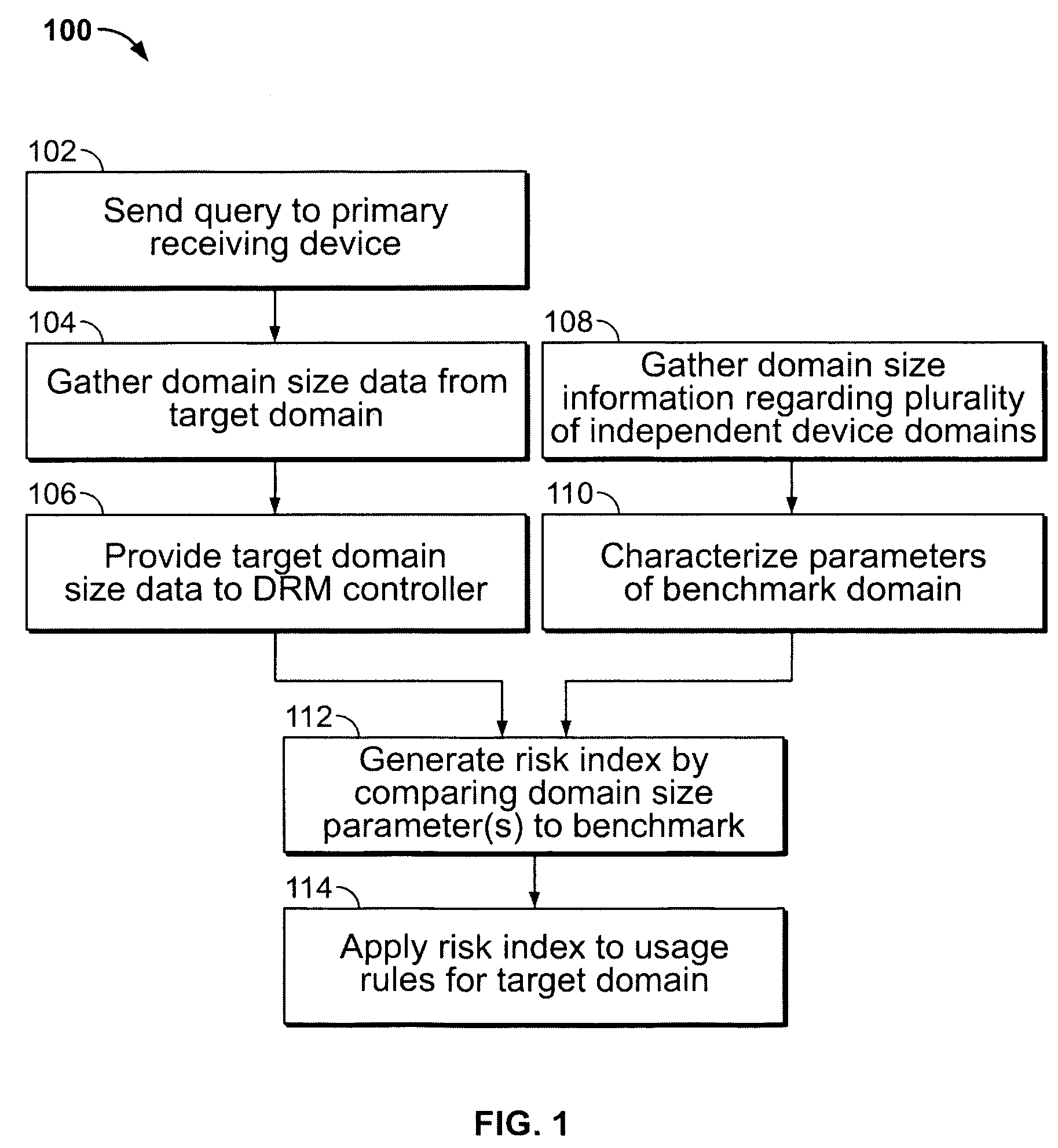
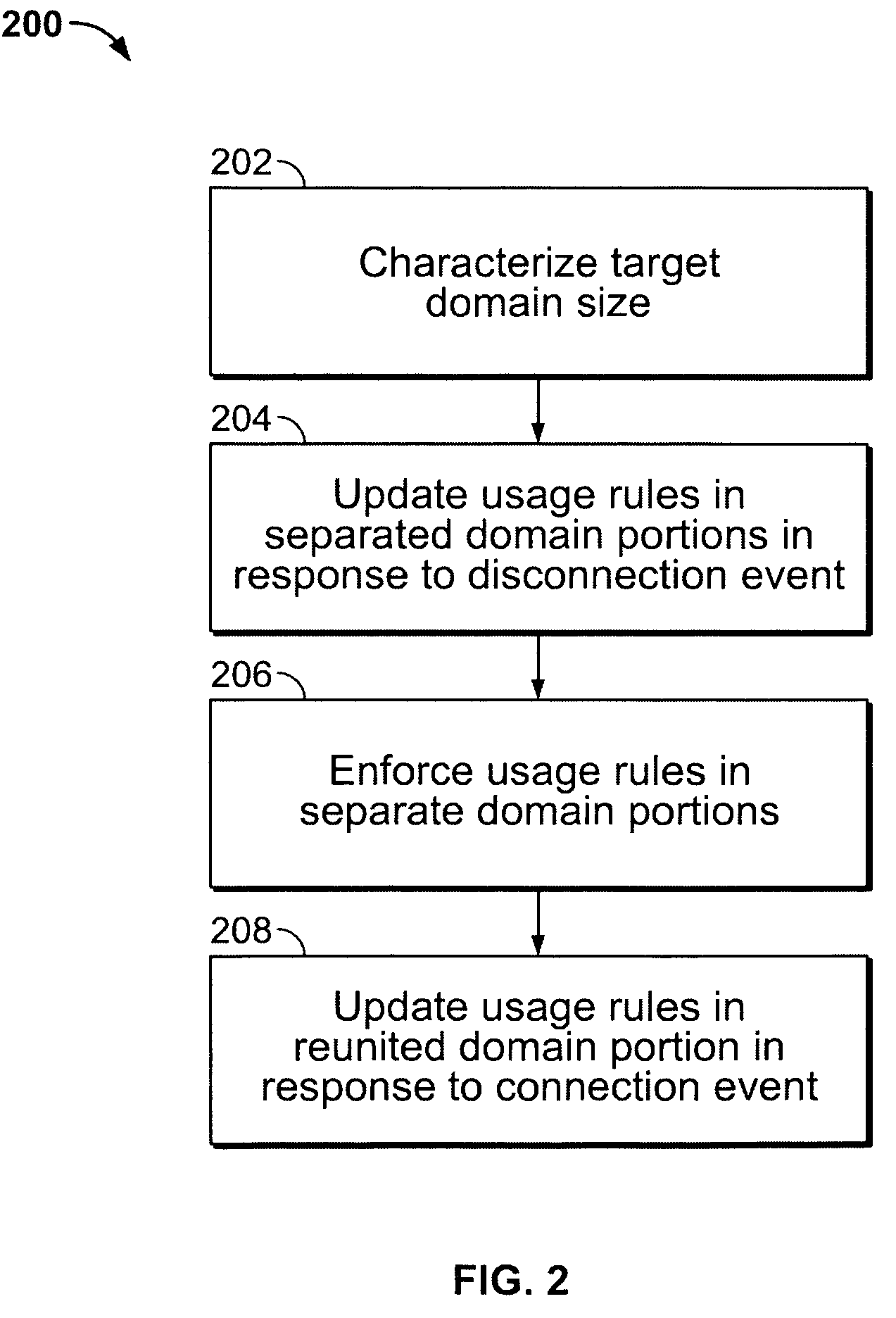
Adaptive digital rights management system for plural device domains
InactiveUS7512987B2Digital data processing detailsUser identity/authority verificationInternet privacyDigital rights management system
A system and methods of digital rights management for plural device domains that adapts in response to external use data. Domain size parameters of a target domain that includes multiple receiving devices are determined. The domain parameters are compared to a domain benchmark developed from external data. A risk index for the target domain is then generated and used to create content usage rights for controlling access and usage of digital content by the collection of devices within that domain. The system may include a plurality of information-gathering tools for collecting the domain parameters from a plurality of independent domains as well as from the target domain.
Owner:MOTION PICTURE ASSOC OF AMERICA
System and method for accessing protected content in a rights-management architecture
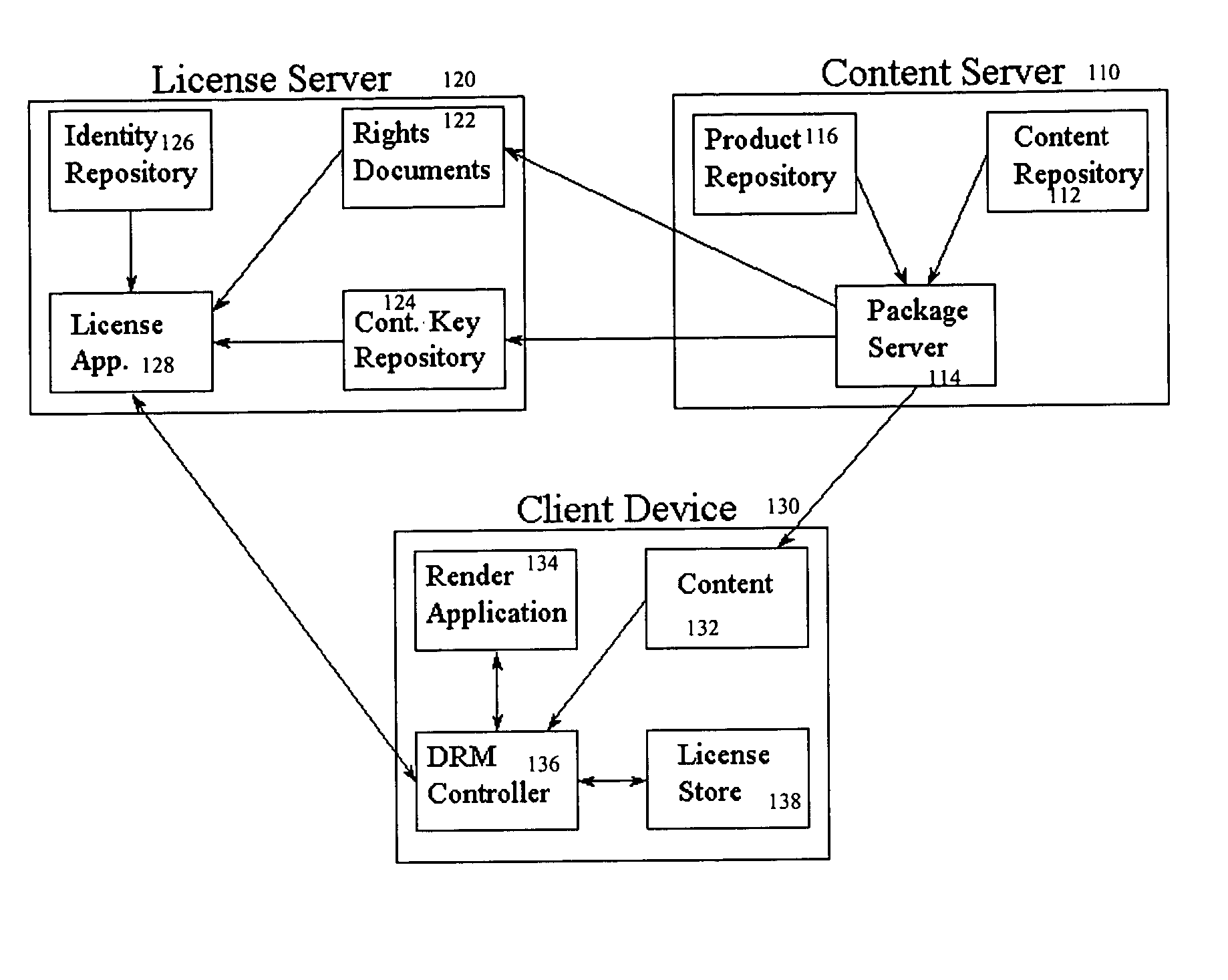
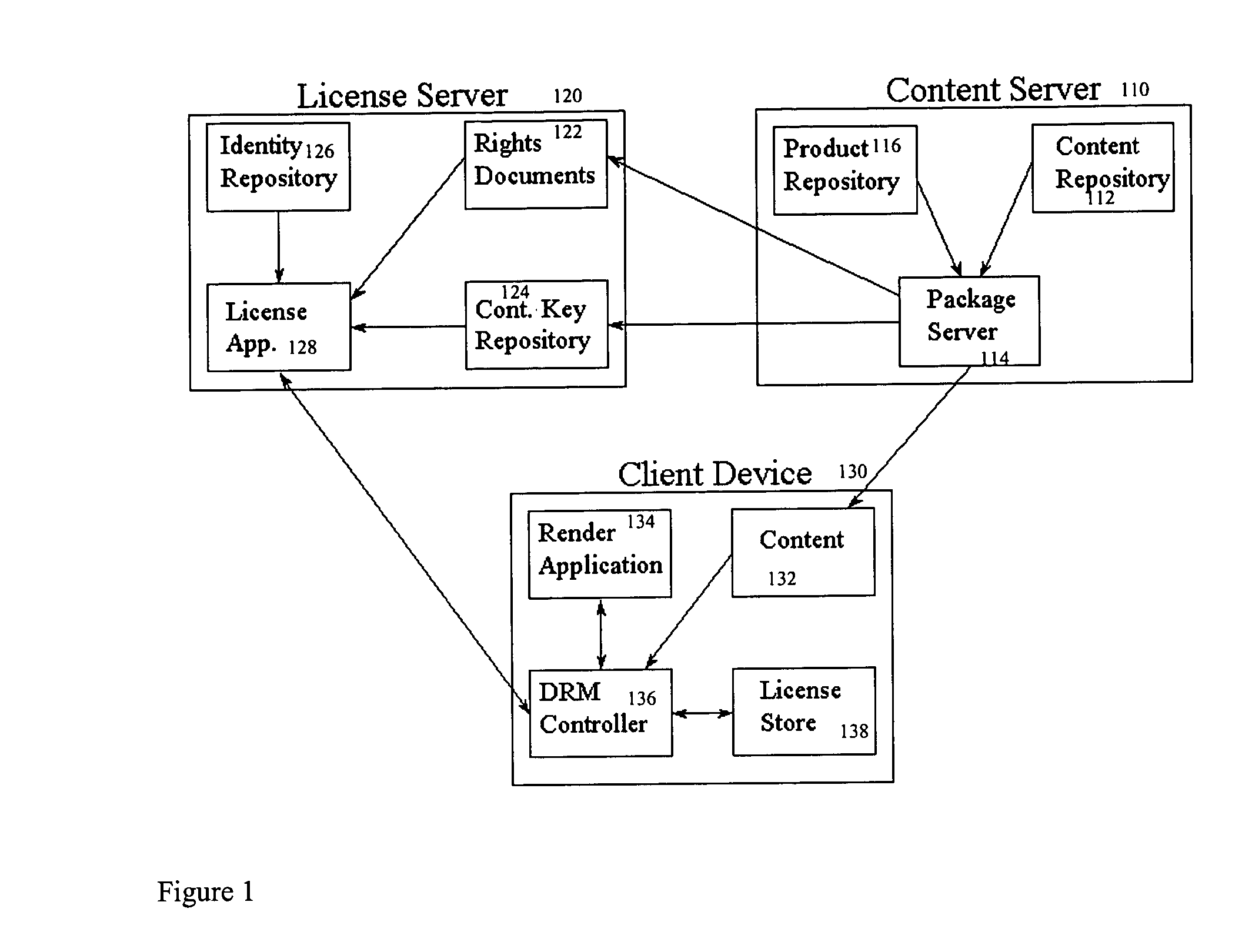
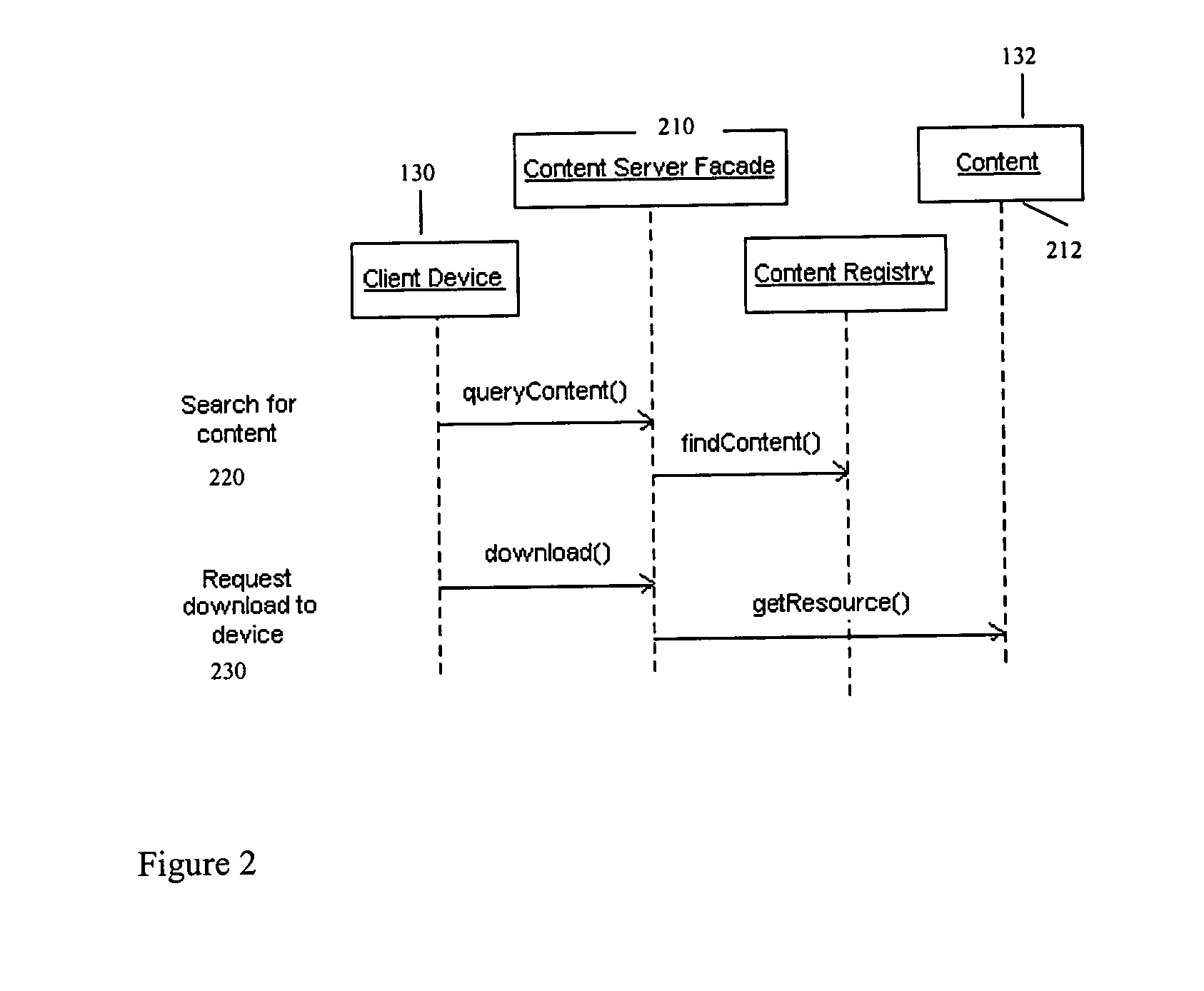
InactiveUS6996720B1Digital data processing detailsUnauthorized memory use protectionPersonalizationDigital rights management system
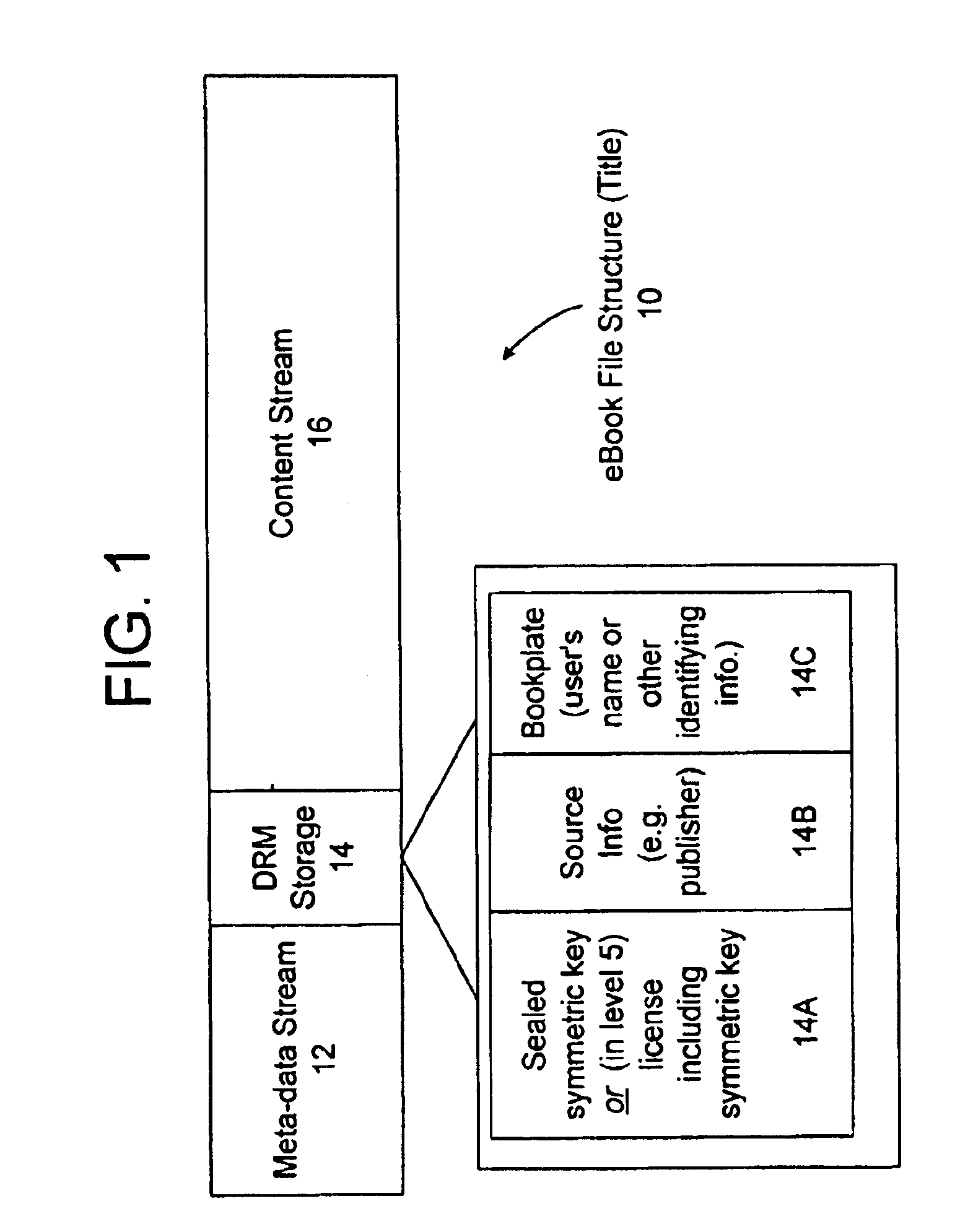
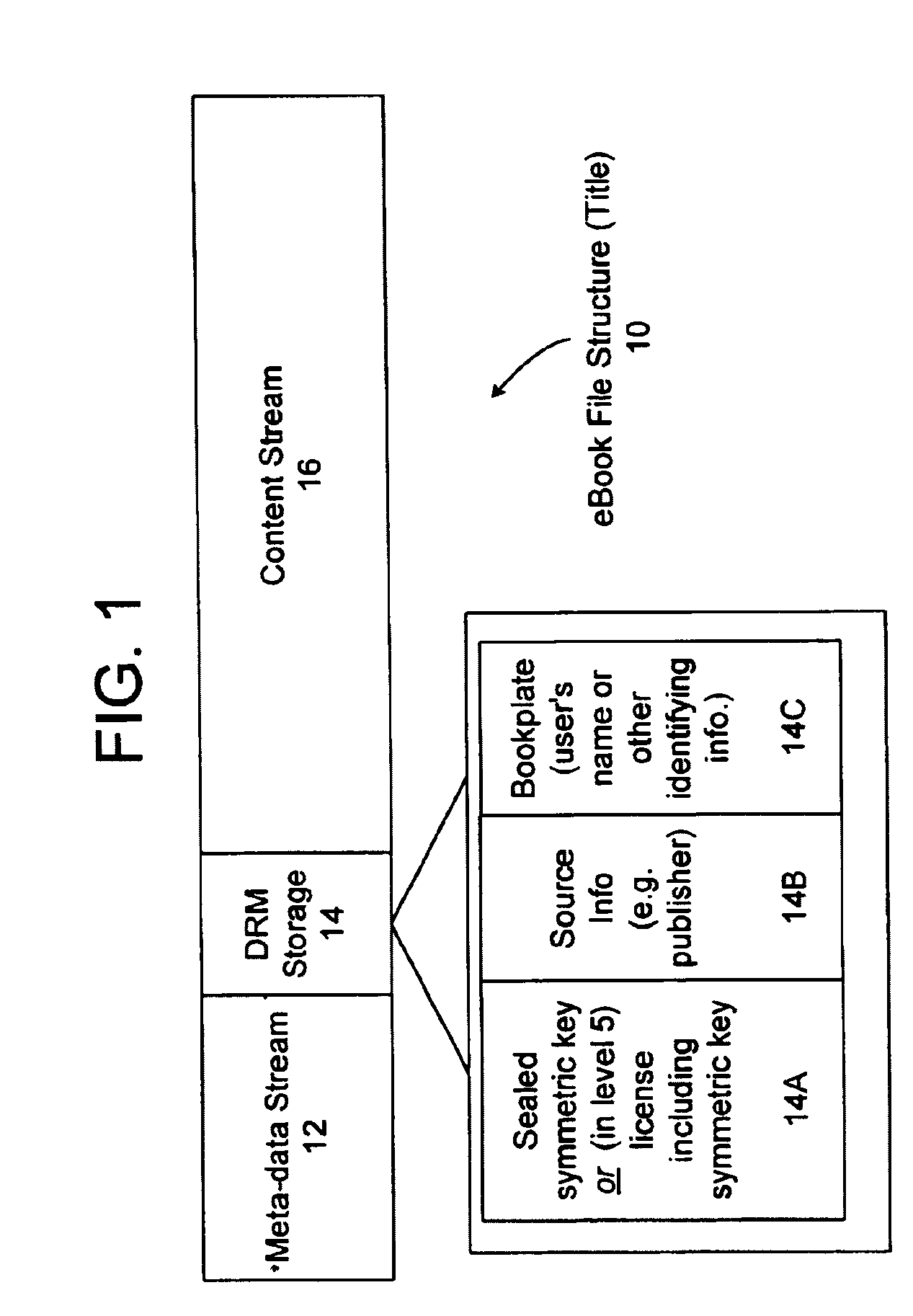
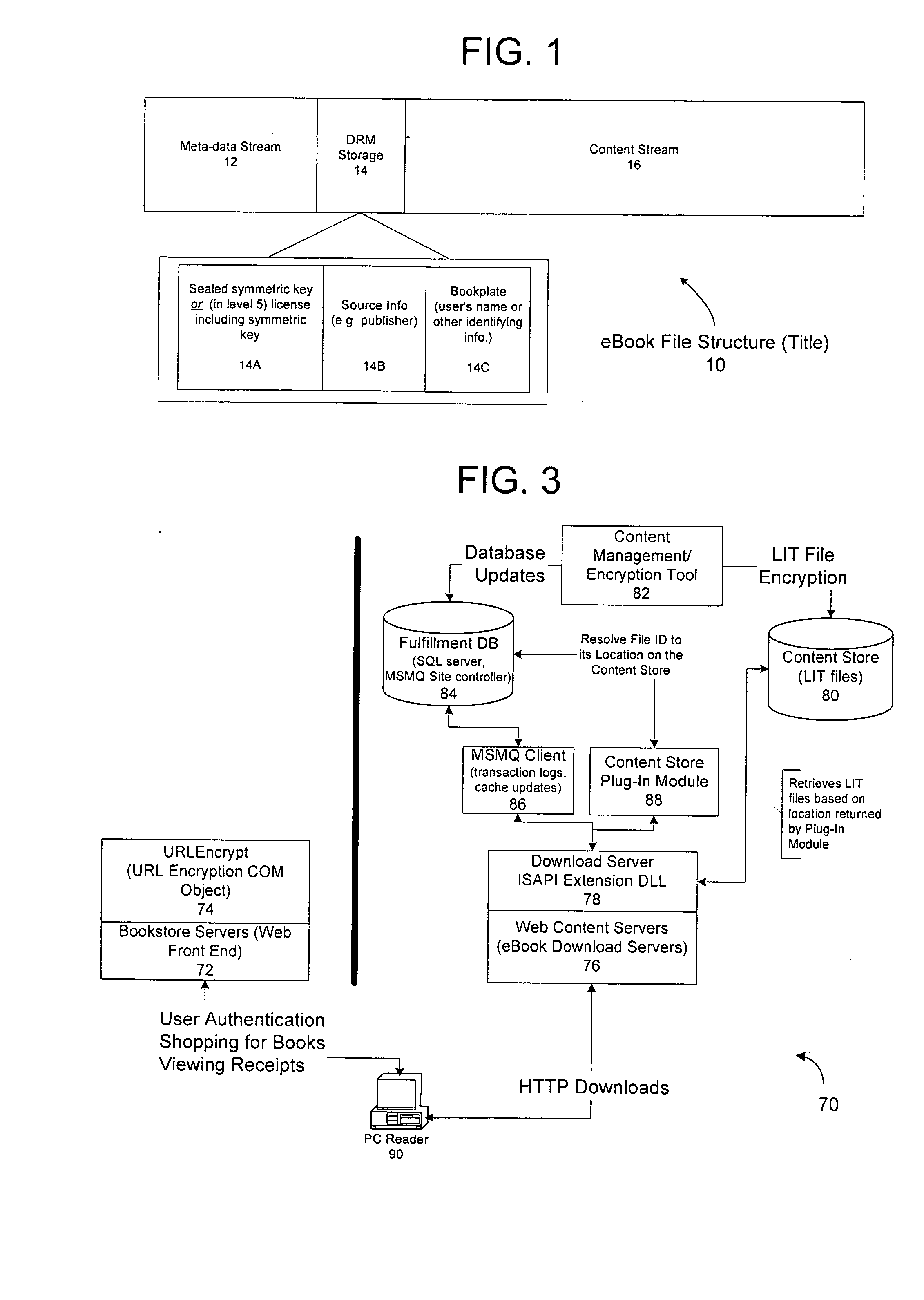
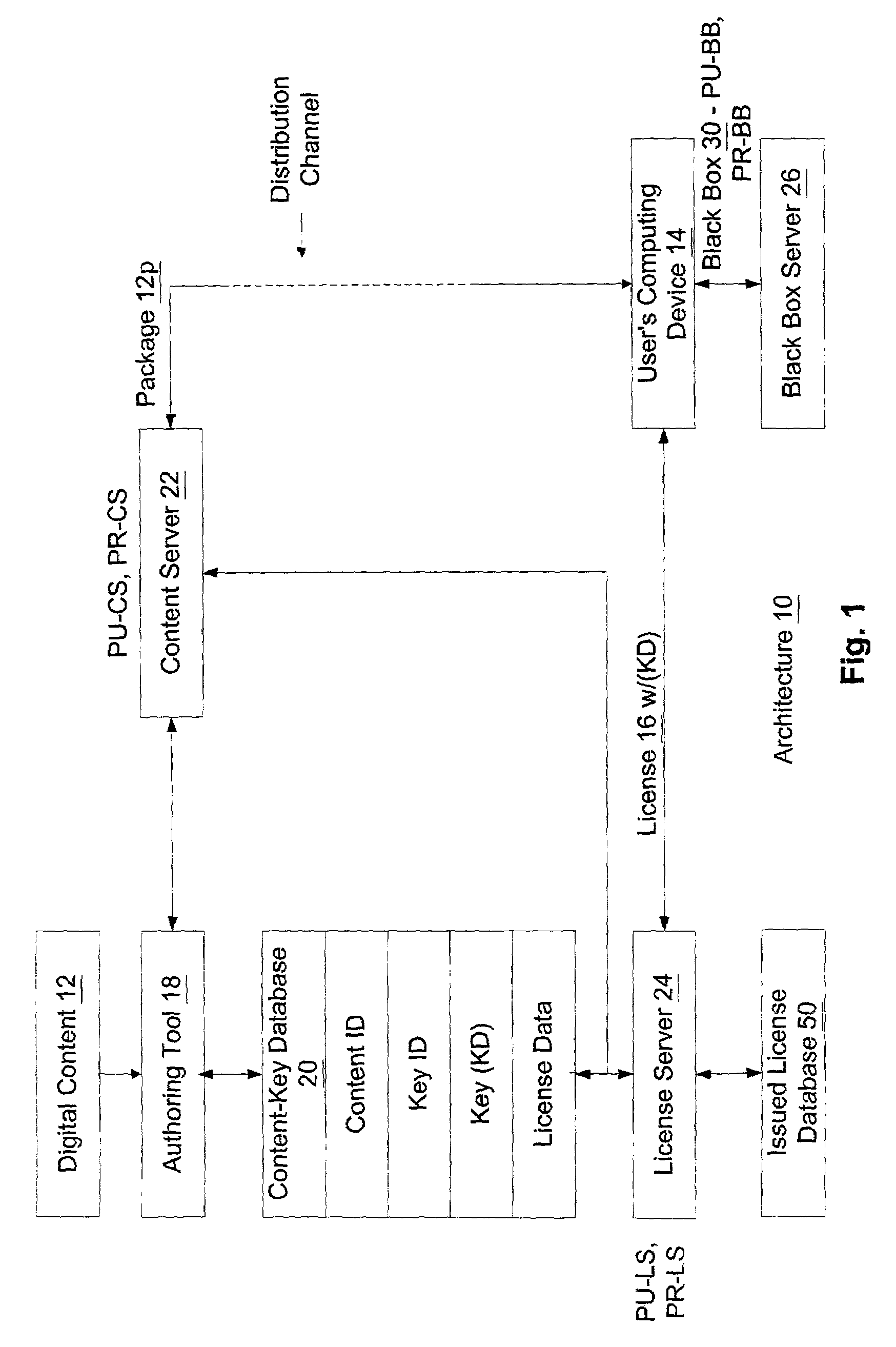
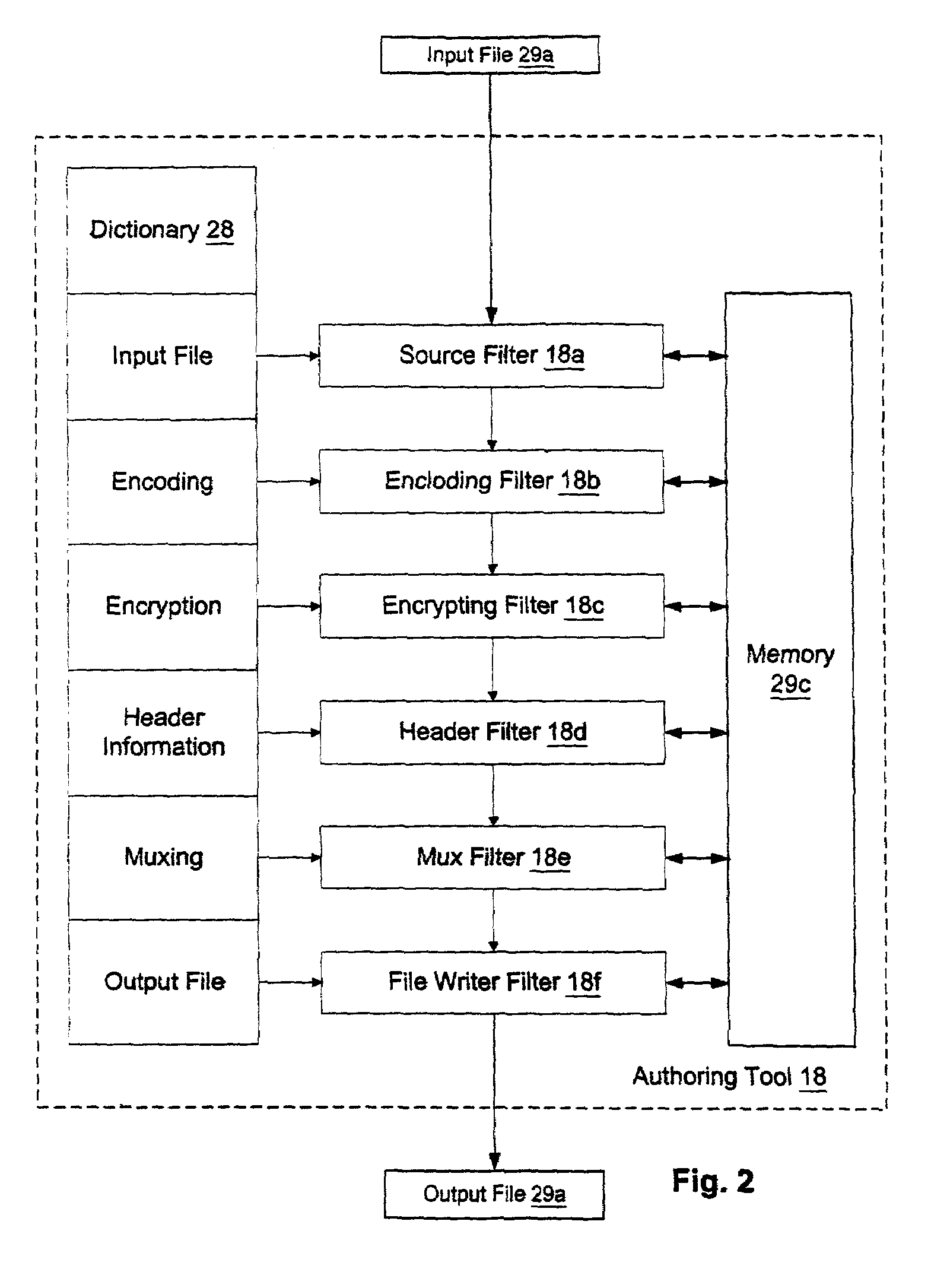
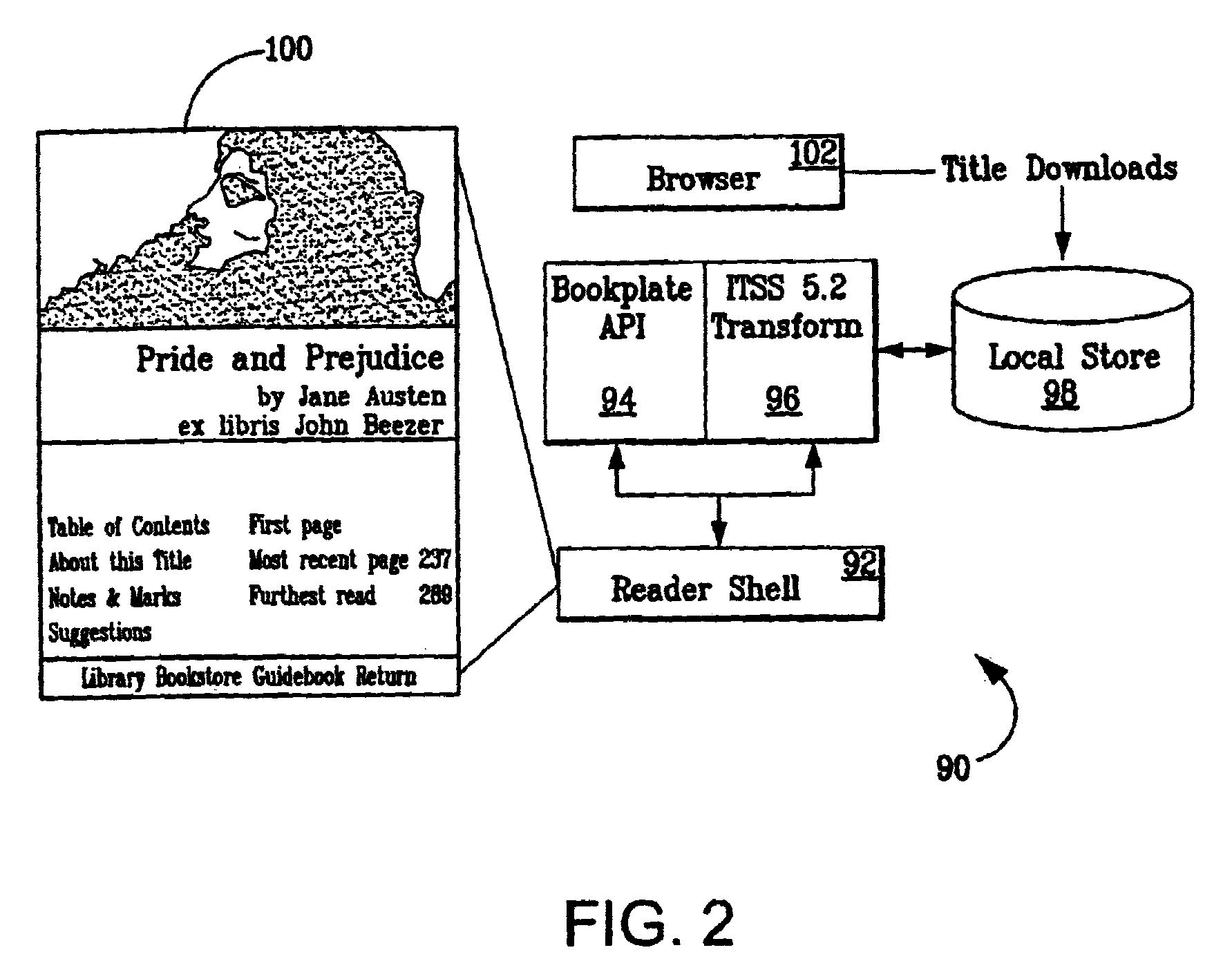
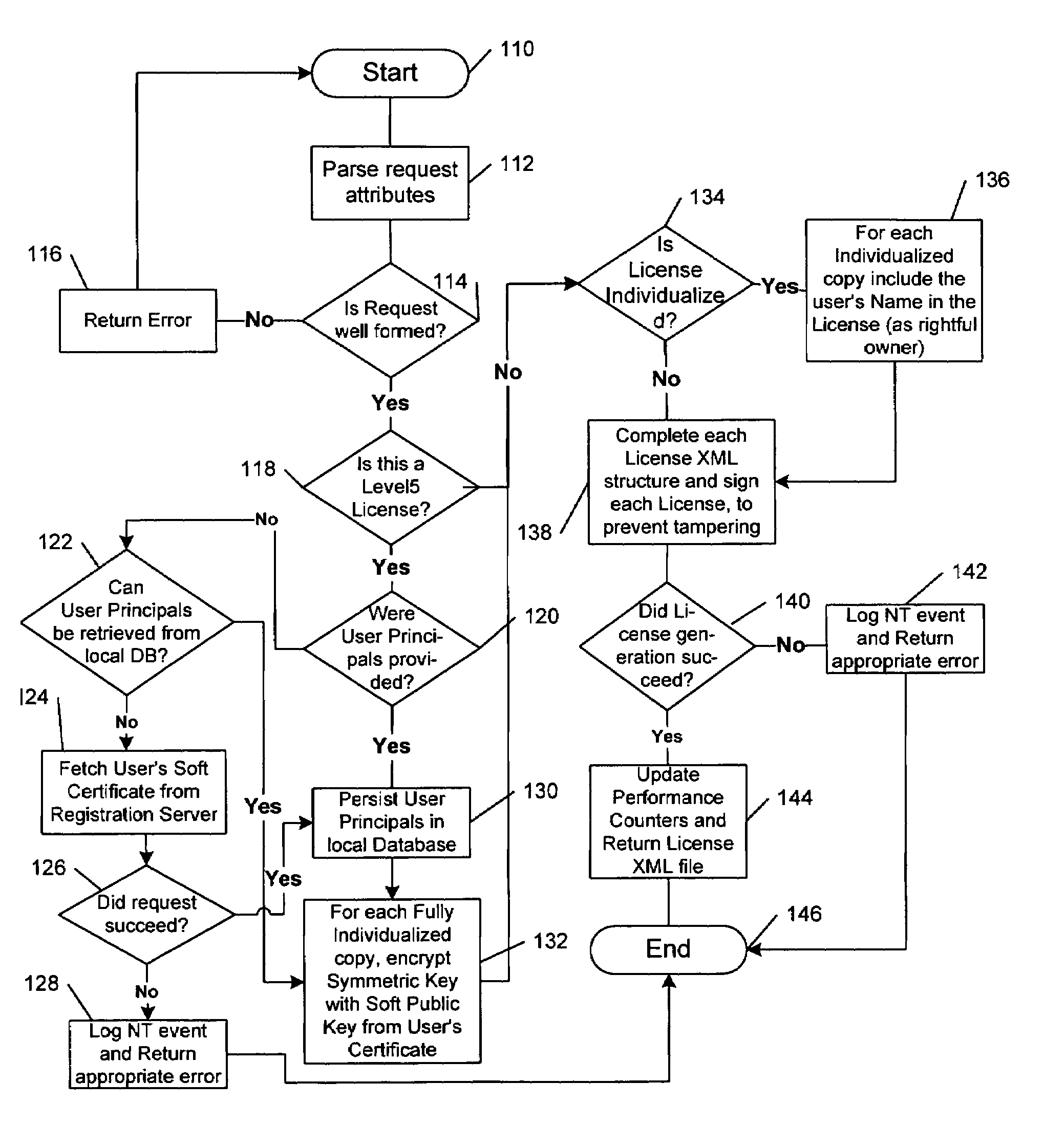
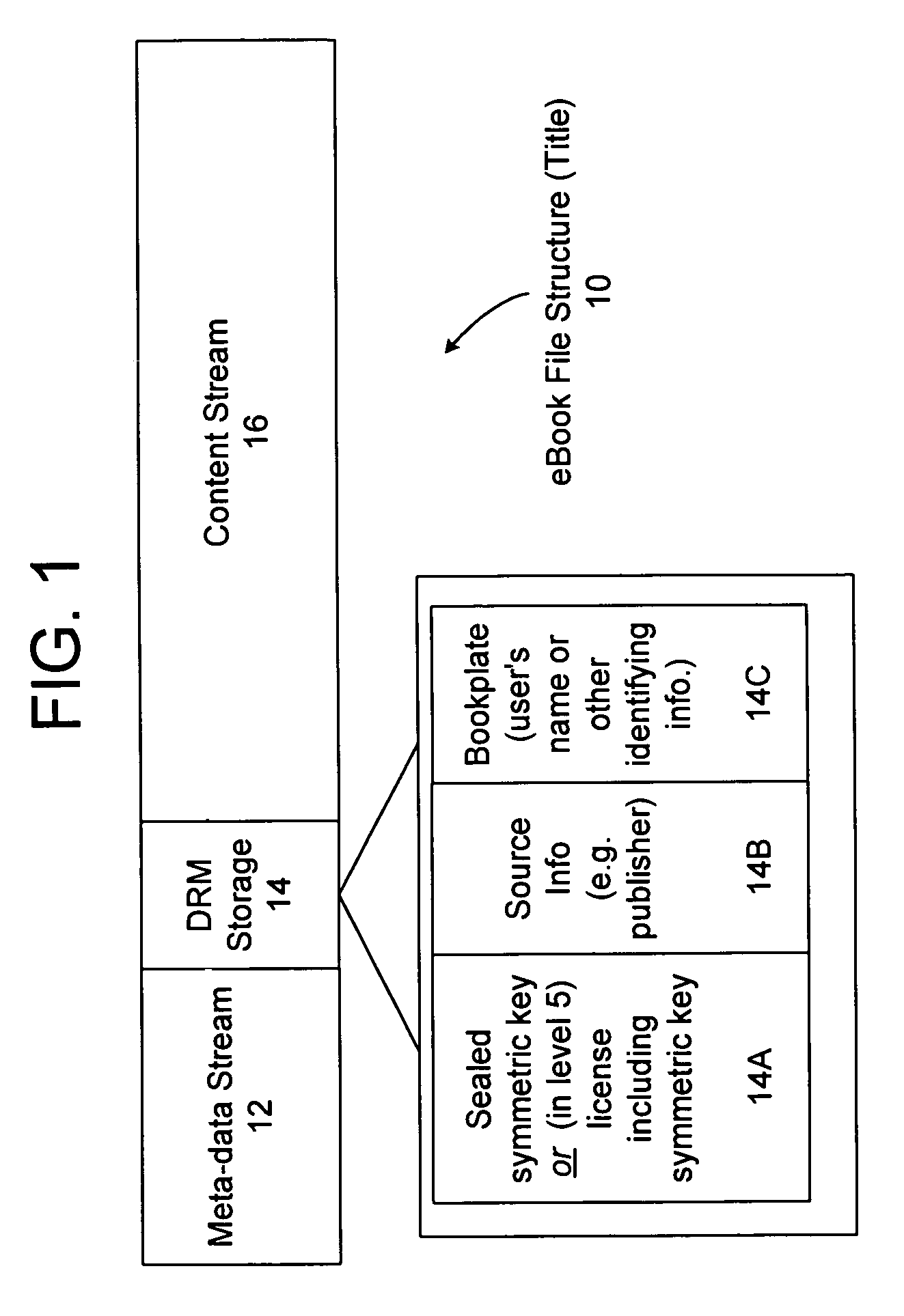
A digital rights management system for the distribution, protection and use of electronic content. The system includes a client architecture which receives content, where the content is preferably protected by encryption and may include a license and individualization features. Content is protected at several levels, including: no protection; source-sealed; individually-sealed (or “inscribed”); source-signed; and fully-individualized (or “owner exclusive”). The client also includes and / or receives components which permit the access and protection of the encrypted content, as well as components that allow content to be provided to the client in a form that is individualized for the client. In some cases, access to the content will be governed by a rights construct defined in the license bound to the content. The client components include an object which accesses encrypted content, an object that parses the license and enforces the rights in the license, an object which obtains protection software and data that is individualized for the client and / or the persona operating the client, and a script of instructions that provides individualization information to a distributor of content so that the content may be individualized for the client and / or its operating persona. Content is generally protected by encrypting it with a key and then sealing the key into the content in a way that binds it to the meta-data associated with the content. In some instances, the key may also be encrypted in such a way as to be accessible only by the use of individualized protection software installed on the client, thereby binding use of the content to a particular client or set of clients.
Owner:MICROSOFT TECH LICENSING LLC
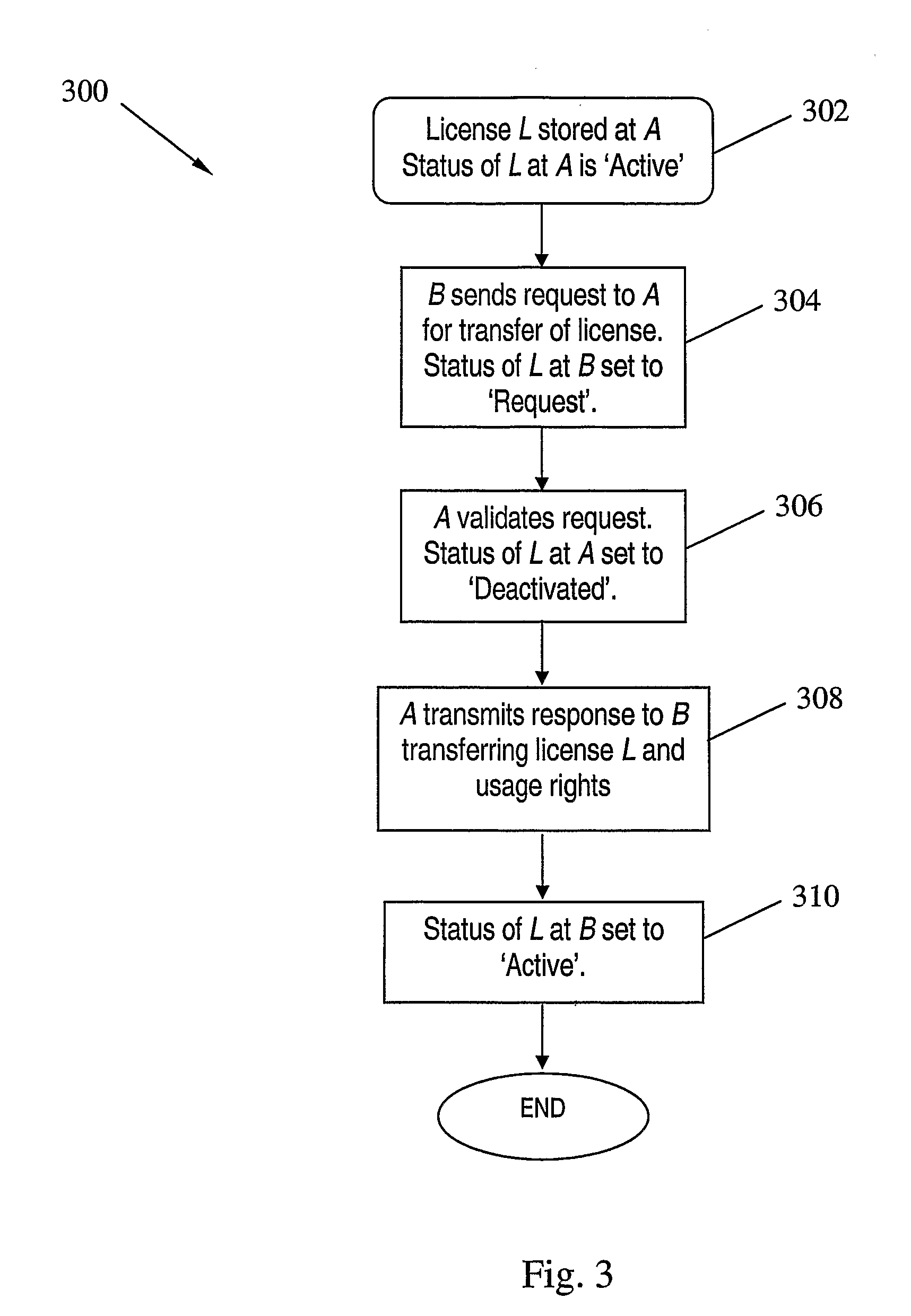
Digital License Sharing System and Method
InactiveUS20070219917A1Fail can be robustAvoid trackingUser identity/authority verificationComputer security arrangementsInternet privacyDigital rights management system
A digital license sharing method, system and apparatus is provided for use in a digital rights management system. Usage rights in respect of digital content are transferred between content player devices or applications by associating with each player a status indication. Transfer is carried out by transmitting a request to obtain the usage rights from a player requiring usage rights to a player currently holding the rights. The transferring player sets a first status indication to indicate that it is no longer entitled to exercise the rights, and transmits a response to the requesting player to transfer the usage rights. The requesting player then sets a second status indication to indicate that it is henceforth entitled to exercise the rights. Methods and apparatus for creating transferable licenses are also provided that employ a sharable license format including a validated portion and an unvalidated portion. The validated portion, which may be, for example, digitally signed by a license issuing authority, includes characteristic information of a digital content decryption key required to access the digital content controlled by the license. The unvalidated portion includes the digital content key itself, encrypted using an encryption key associated with a player entitled to use the license.
Owner:SMART INTERNET TECH CRC
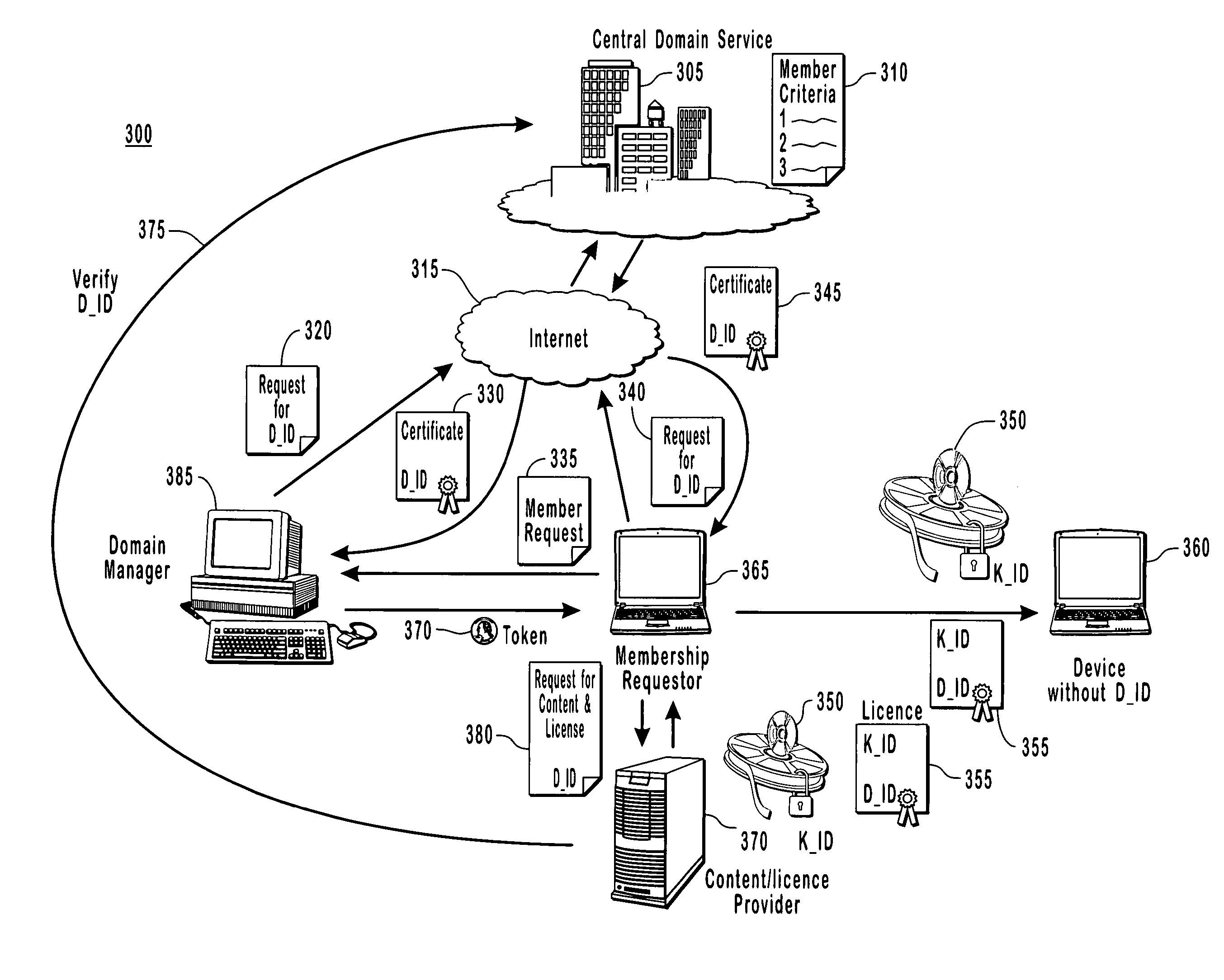
Binding content to a domain
The present invention provides for a digital rights management system with a centralized domain service capable of creating and managing membership criteria for joining a domain in accordance with business rules defined by ac content owner. A domain identification is created that allows a content provider to uniquely bind content licenses to a domain. The content licenses include usage rights that define how content associated with the licenses may be consumed by one or more members of the domain. The centralized domain service can enforce digital rights by validating membership criteria including at least one of a domain proximity check for validating that a requestor is in close proximity to the domain, a total number of requestors, or the frequency that the requests have been made by various requesters to join the domain and unjoin from the domain.
Owner:ZHIGU HLDG
System and method for activating a rendering device in a multi-level rights-management architecture
InactiveUS7017189B1Digital data processing detailsUser identity/authority verificationPersonalizationDigital rights management system
Owner:MICROSOFT TECH LICENSING LLC
Supervised license acquisition in a digital rights management system on a computing device
InactiveUS7065507B2Satisfies needPayment protocolsBuying/selling/leasing transactionsDigital contentDigital rights management system
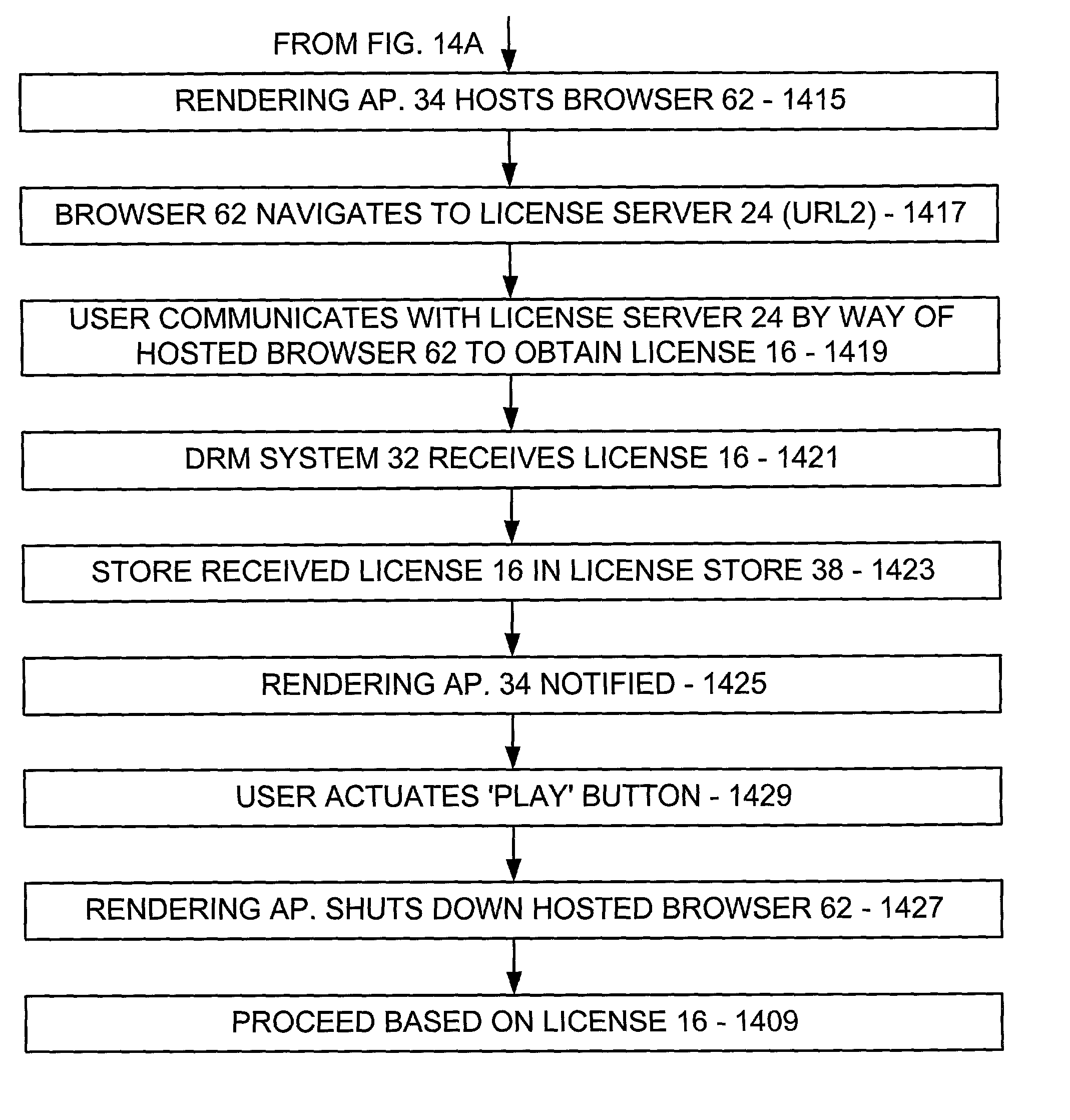
A rendering application on a computing device requests a digital rights management (DRM) system on the computing device to authorize digital content rendering based on a corresponding digital license. If unavailable, the DRM system attempts to silently acquire the license from a license server without the intervention of a user. In the course thereof, the rendering application receives status information from the DRM system relating to the attempted license acquisition thereby and displays the received status information in a rendering application status display portion. If silent acquisition fails, the rendering application hosts a browser, causes the browser to navigate to a license server, allows a user to communicate with the license server by way of the hosted browser to acquire the license, and shuts down the hosted browser upon reception of the license from the license server.
Owner:MICROSOFT TECH LICENSING LLC
Conditional access to digital rights management conversion
ActiveUS20050182931A1Drying solid materials with heatUser identity/authority verificationSecurity kernelDigital rights management system
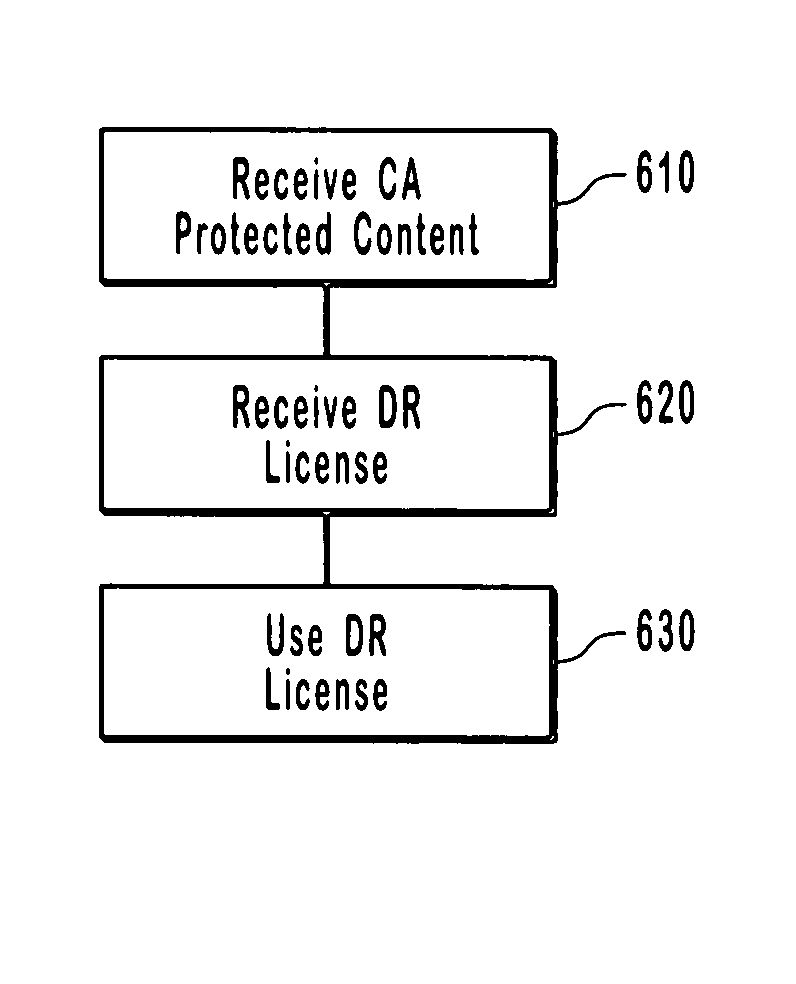
The present invention provides for an interface between two seemingly incompatible and different content protection systems. Accordingly, protected content may be transferred between the respective security kernels of a conditional access (CA) and digital rights management (DRM) systems, while maintaining security of the content and any associated protection information. The transfer and consumption of protected content and the associated content protection information may be achieved by temporarily or permanently binding the respective security kernels of the CA and DRM systems, transcribing content protection information, and potentially transcribing the content.
Owner:MICROSOFT TECH LICENSING LLC
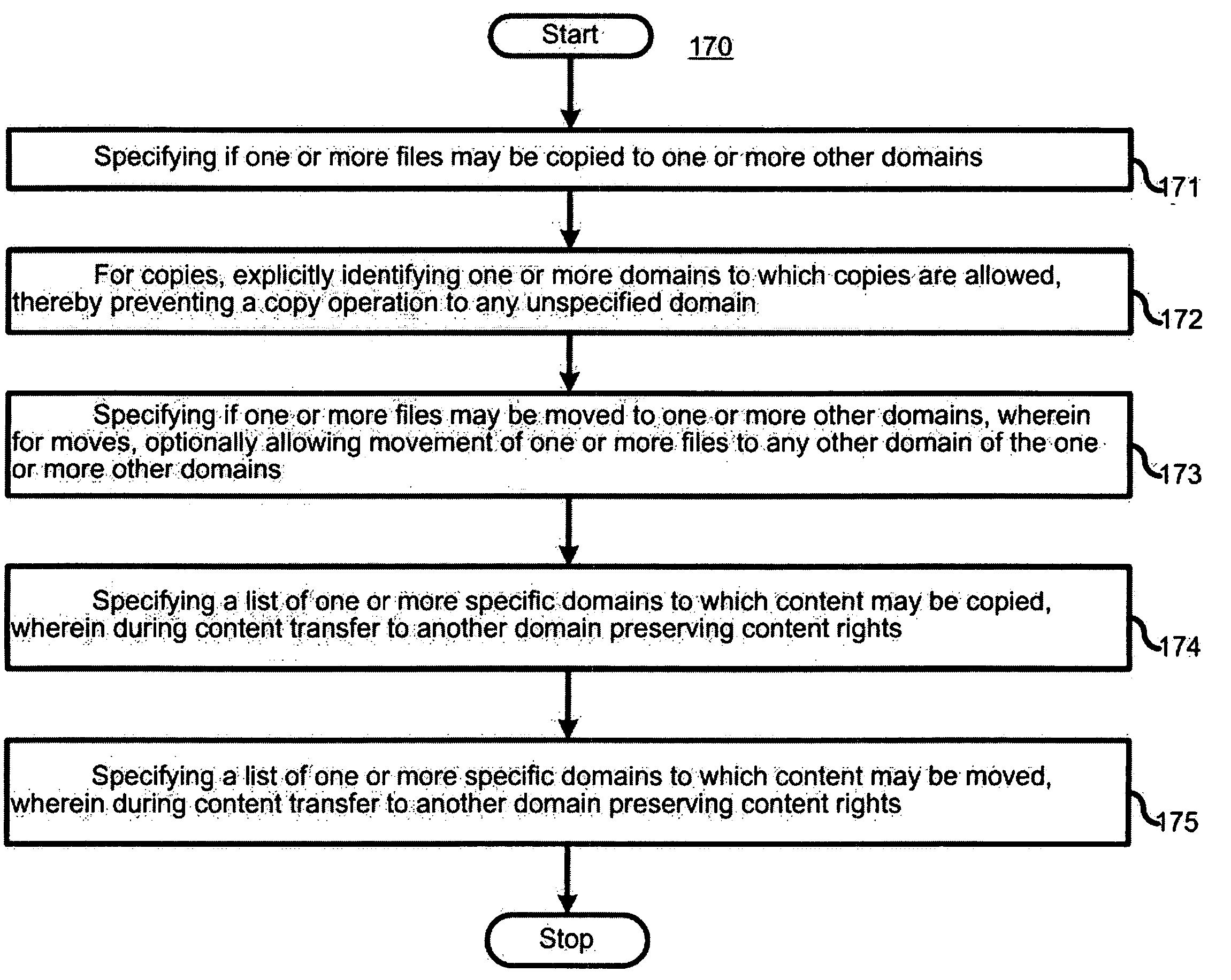
Separation of copy protection rules
InactiveUS20050071669A1Digital data processing detailsAnalogue secracy/subscription systemsDigital rights management systemCopy protection
A copyright protection method (150) and apparatus (190) employs (151) a first protection scheme (160) within a single authorized domain (195), in which all interfaces (194a-c) are protected with digital rights management system and employs (152) a second protection scheme (170) for use in inter-domain file transfers. The method (150) and apparatus (190) may employ (153) a third protection scheme (180) for external outputs (197a-c) not protected by a digital rights management system. The first protection scheme (160) includes specifying (161) whether a copy of files is allowed to be stored anywhere within the single authorized domain; specifying (162) whether files may be stored only on specific devices within the single authorized domain; or specifying (163) how many simultaneous rendering devices are permitted when rendering files. The second protection scheme (170) may include: specifying (171) if the files may be copied to other domains; and explicitly identifying (172) domains to which copies are allowed; specifying (173) if files may be moved to other domains, and optionally allowing movement of files to any other domain; specifying (174) a list of specific domains to which content may be copied, and preserving content rights during content transfer to another domain; or specifying (175) specific domains to which content may be moved, and preserving content rights during content transfer. The third protection scheme (180) may include: specifying (181) copy protection information separately for analog, digital uncompressed and digital compressed outputs; specifying (182) a CGMS Copy protection state; specifying (183) MACROVISION parameters for analog outputs; specifying (184) if a particular type of output is allowed at all; or disabling (185) the particular type of output if the particular output type is not allowed.
Owner:GOOGLE TECH HLDG LLC
System and method for securing digital content
ActiveUS20050044016A1Simplify the purchasing processIntuitive experienceComplete banking machinesFinanceDigital contentDigital rights management system
Owner:NETCRACKER TECH SOLUTIONS
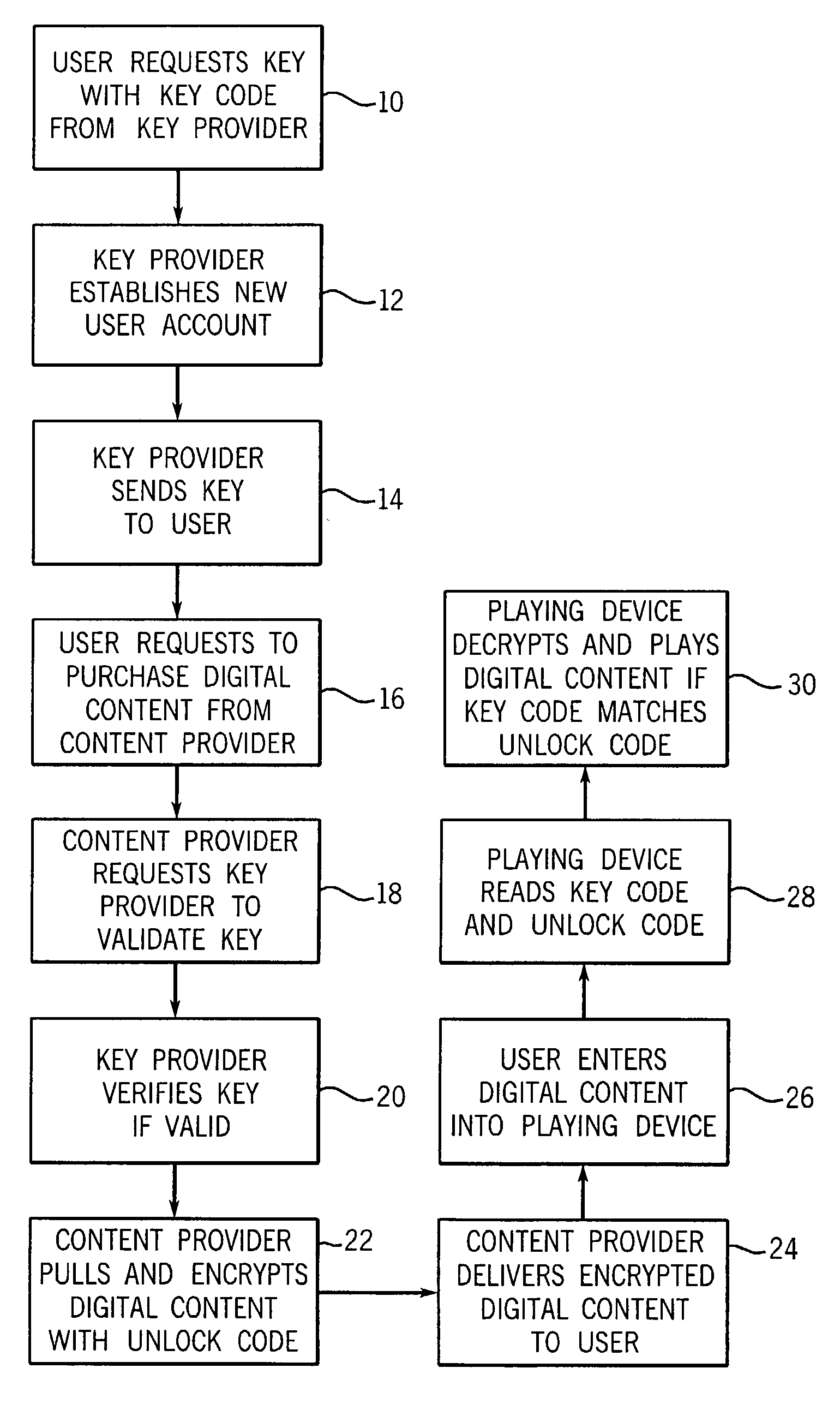
Digital rights management
InactiveUS7472280B2Unprecedented convenienceUnprecedented freedomDigital data processing detailsAnalogue secracy/subscription systemsComputer hardwareDigital rights management system
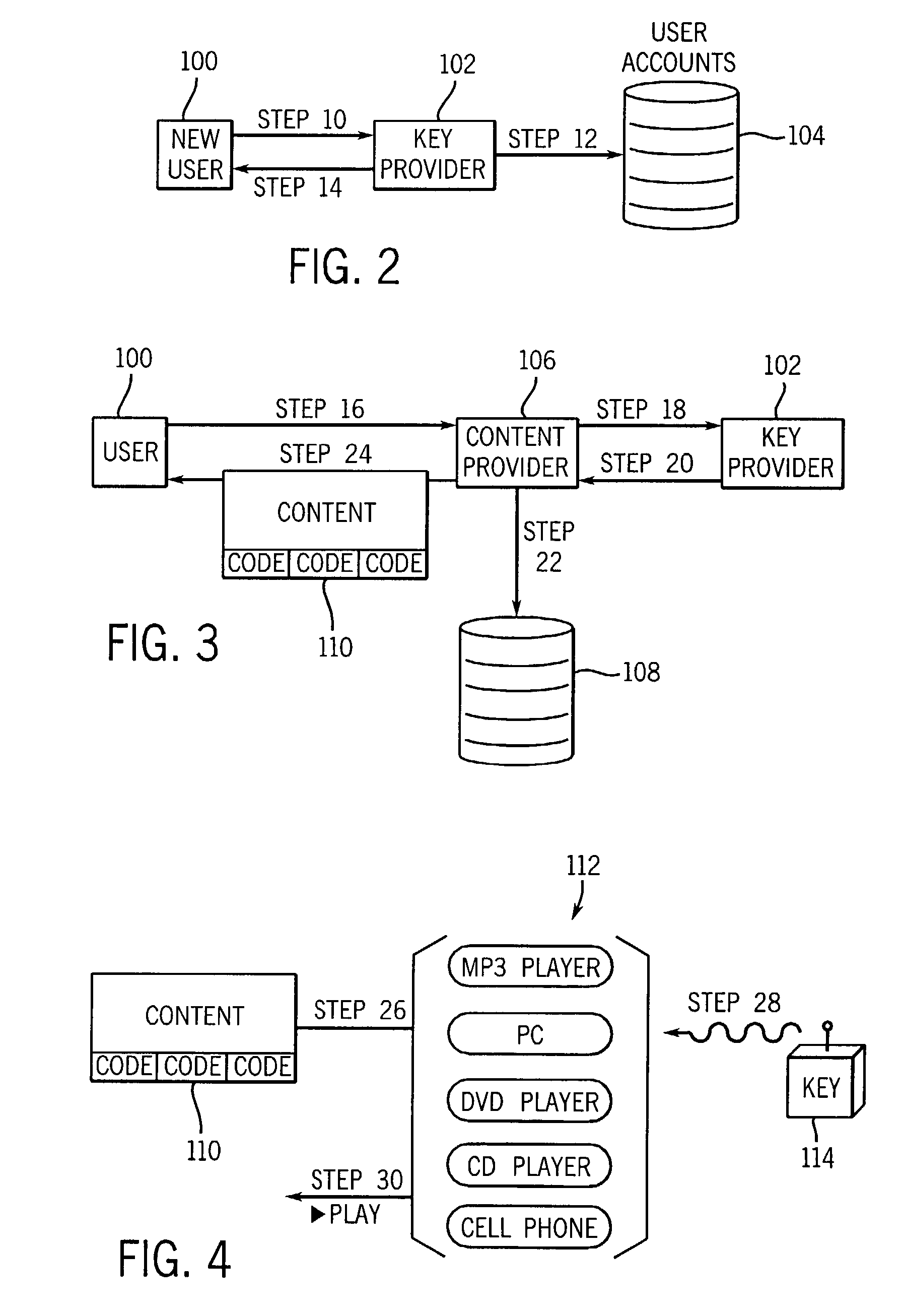
A method of managing digital rights comprises the following steps. First, a physical electronic key containing a first activation code is provided to a requesting user. Second, locked digital content is provided to the requesting user. The digital content is encoded with a second activation code associated with the first activation code. Third, the locked digital content is received in a playing device that reads the first activation code and determines whether the first activation code is associated with the second activation code. Fourth, the playing device is enabled to unlock and play the digital content if the first activation code is associated with the second activation code. A digital right management system for implementing the foregoing method is also disclosed.
Owner:PROXENSE
Digital rights management system and method
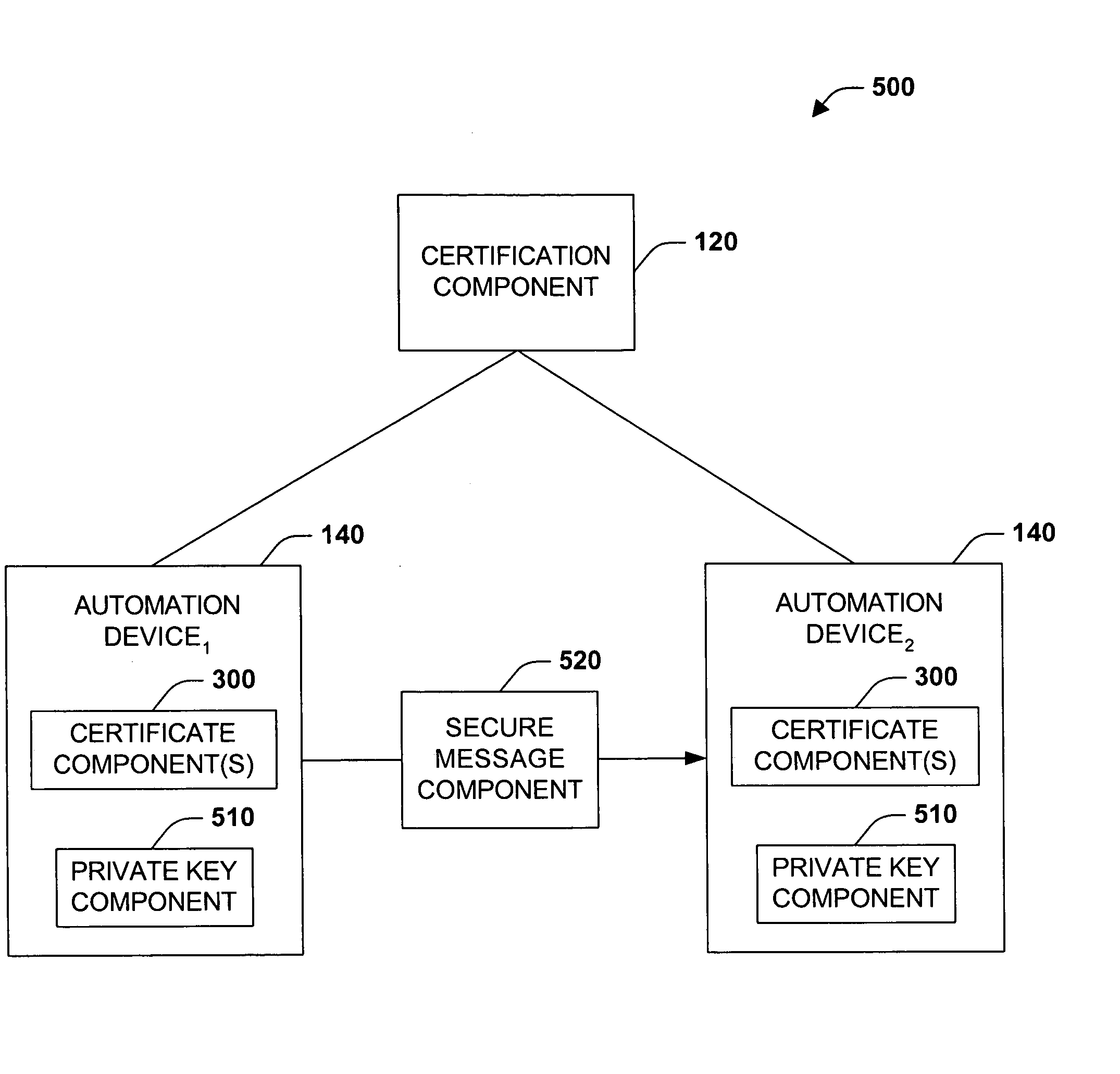
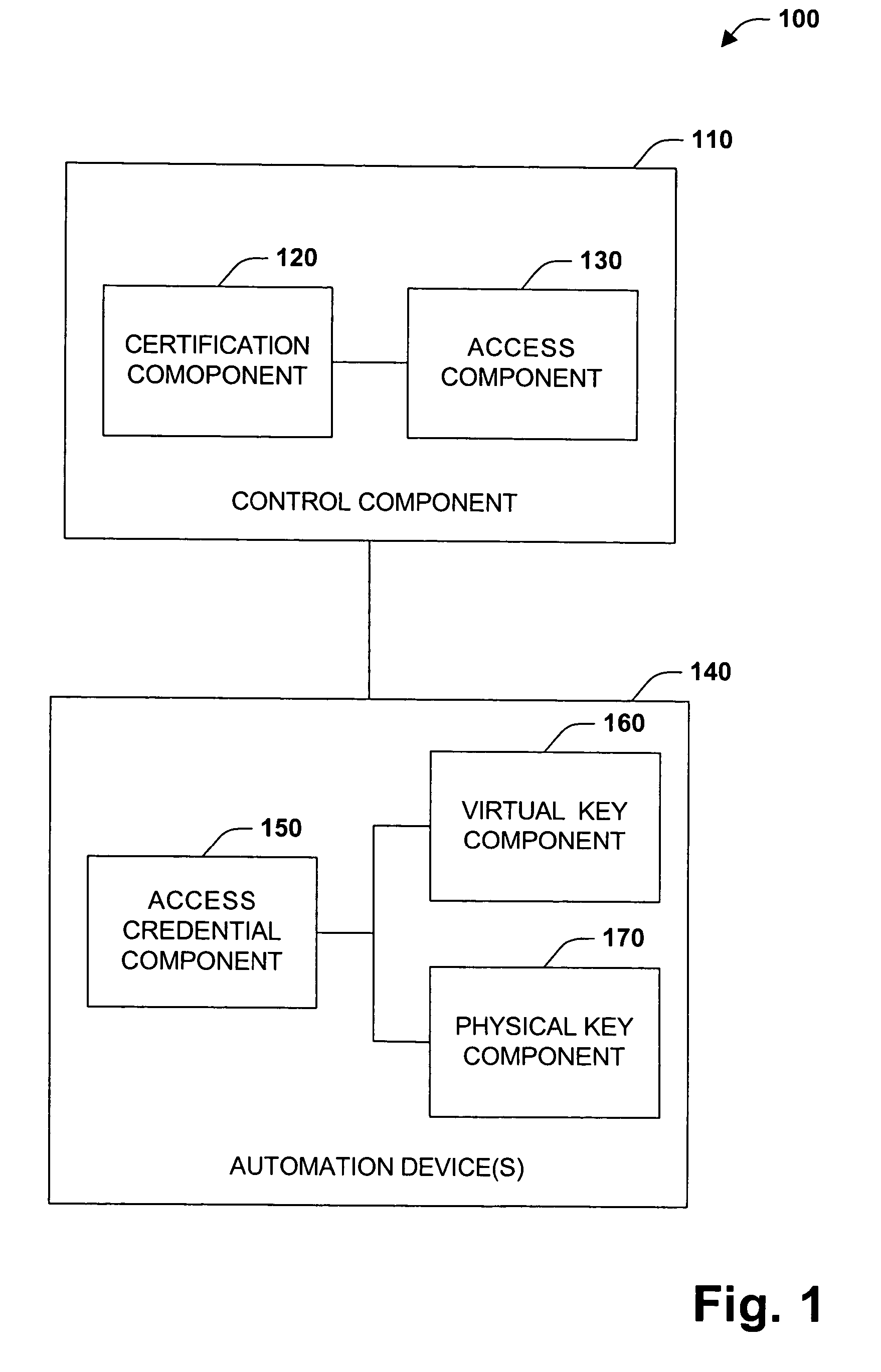
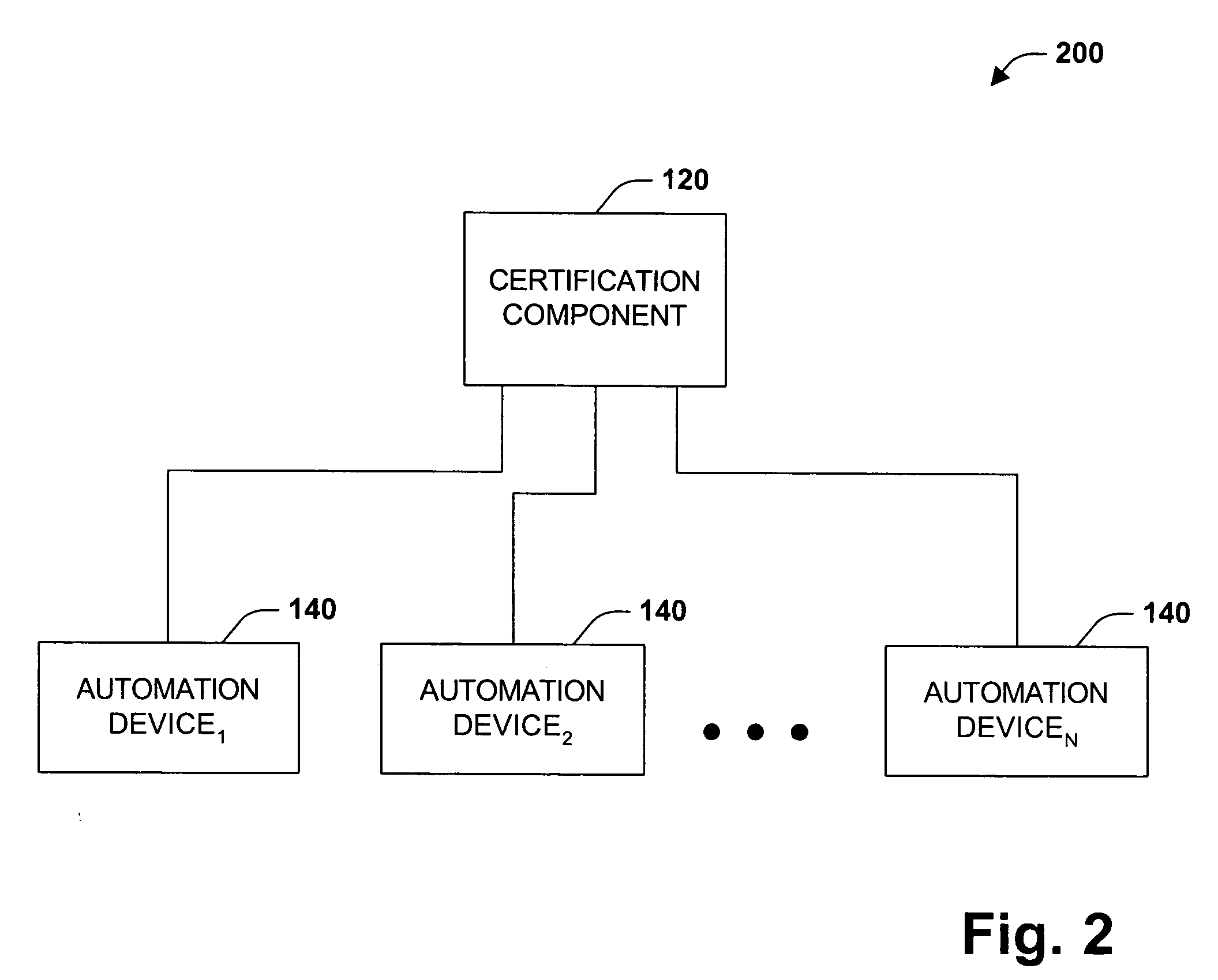
InactiveUS20050229004A1Improve securityCommunication securityProgramme controlComputer controlUser PrivilegeSecure transmission
The present invention concerns application of digital rights management to industrial automation devices including programmable logic controllers (PLCs), I / O devices, and communication adapters. Digital rights management involves a set of technologies for controlling and managing access to device objects and / or programs such as ladder logic programs. Access to automation device objects and / or programs can be managed by downloading rules of use that define user privileges with respect to automation devices and utilizing digital certificates, among other things, to verify the identity of a user desiring to interact with device programs, for example. Furthermore, the present invention provides for secure transmission of messages to and amongst automation devices utilizing public key cryptography associated with digital certificates.
Owner:ROCKWELL AUTOMATION TECH
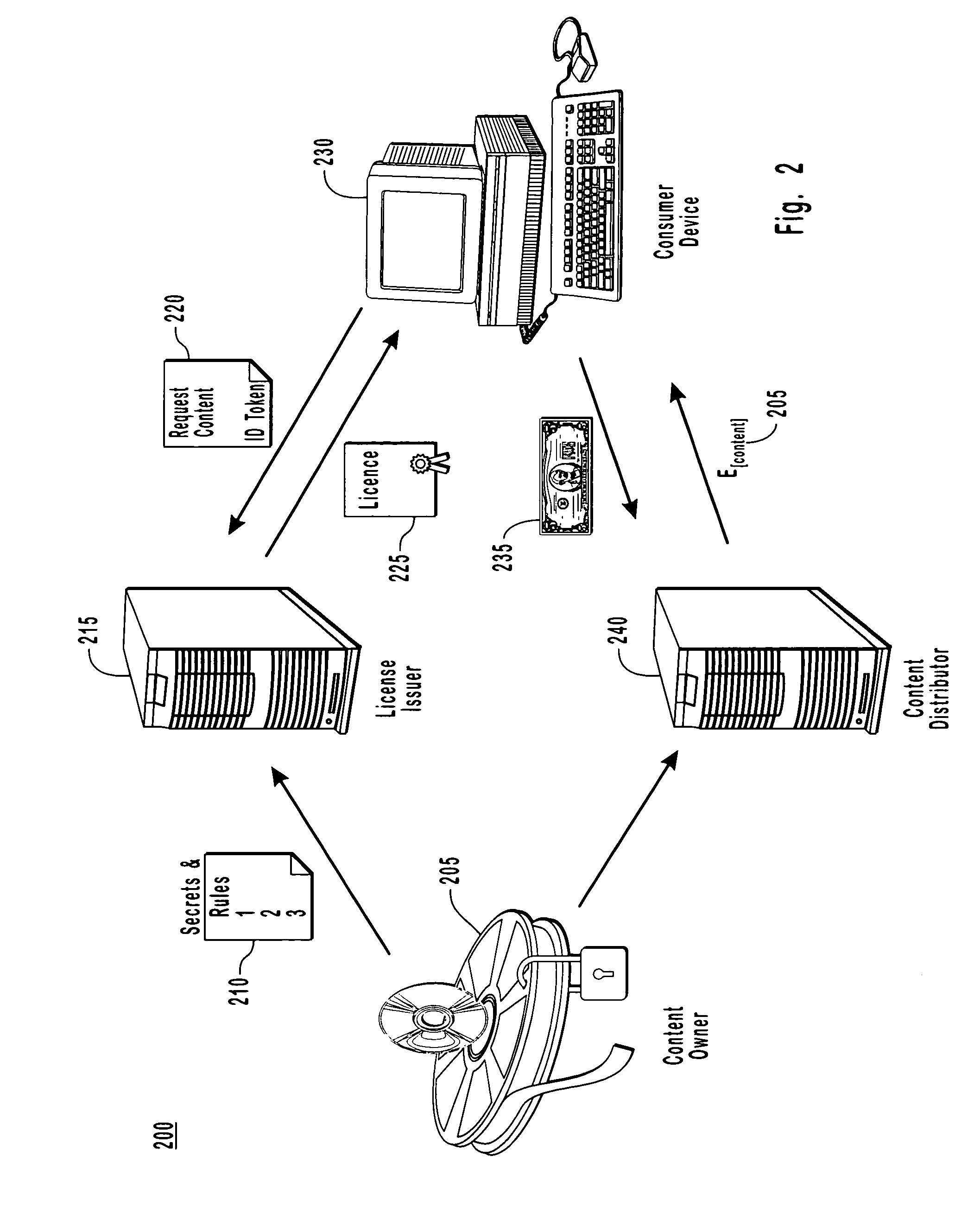
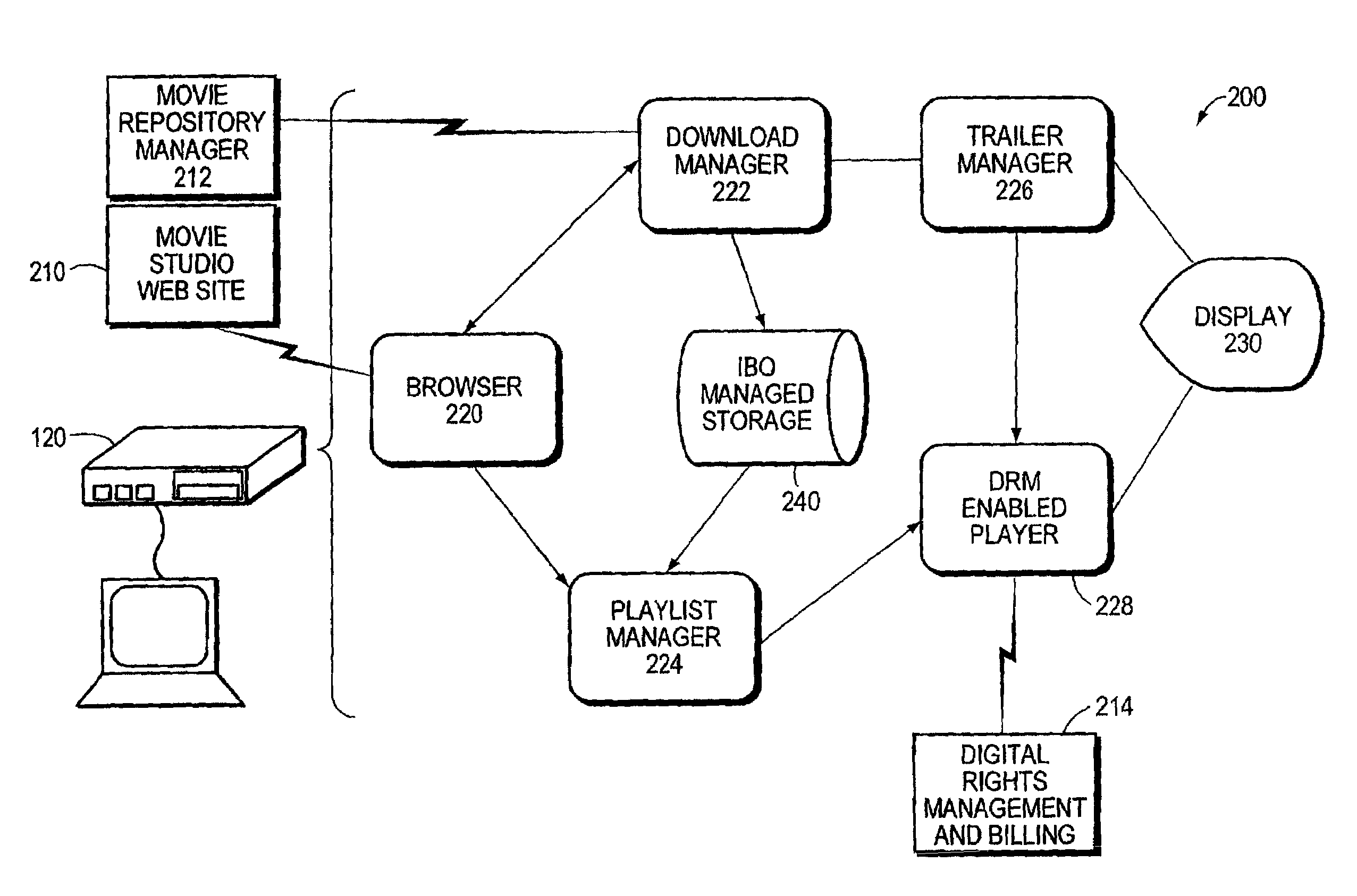
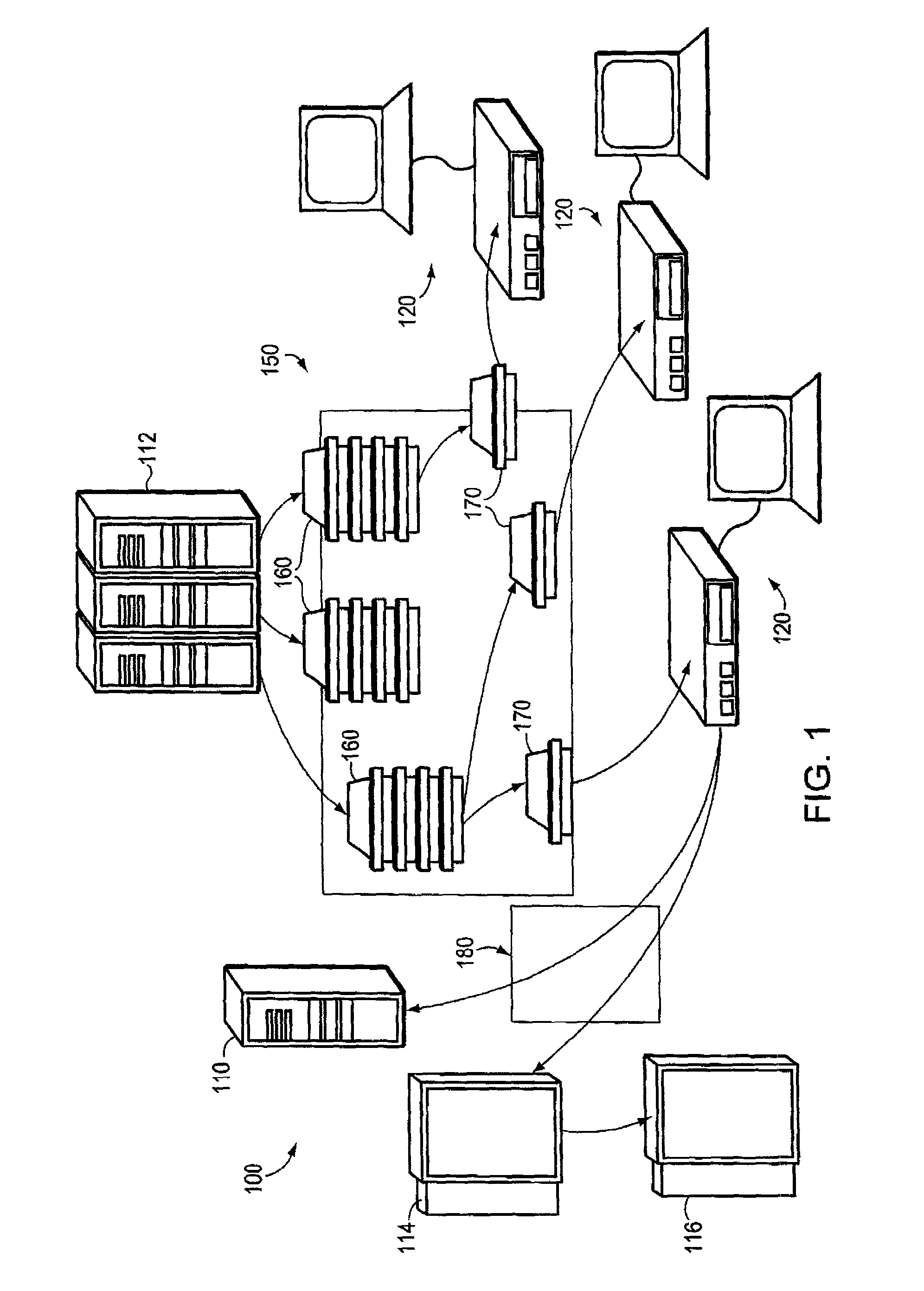
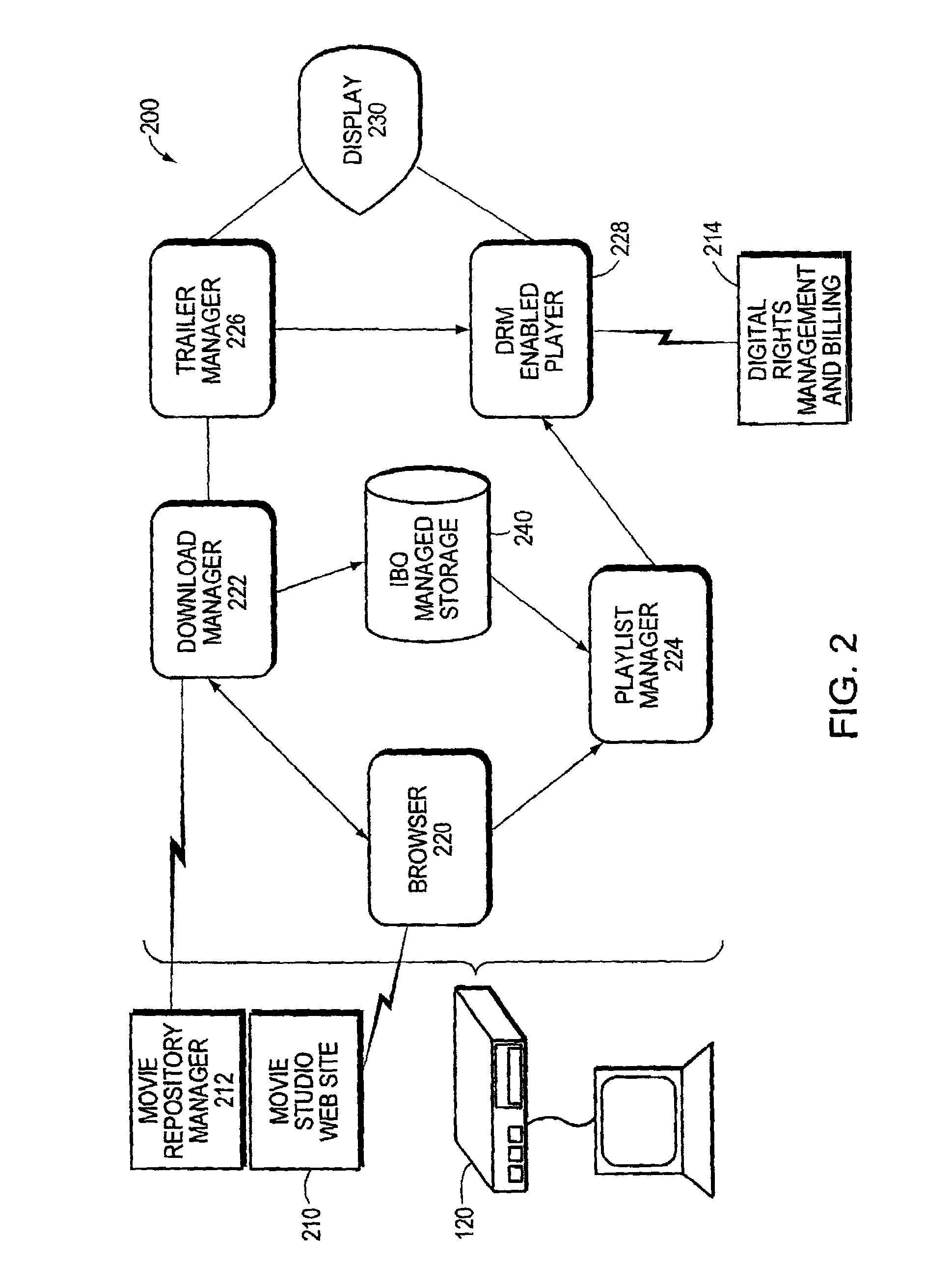
Method and mechanism for vending digital content
InactiveUS6993508B1Easy accessRetain controlAnalogue secracy/subscription systemsPayment architectureDigital rights management systemIntellectual property
An Internet Box Office (IBO) system and technique vends digital content via a computer network, such as the Internet. The IBO system comprises a viewing system that cooperates with a Digital Rights Management system and various deployment enhancements within the Internet to provide an infrastructure that facilitates access to digital content in a manner that comports with copyright law and the control of intellectual property by the copyright owner. The IBO system enables a content copyright owner to retain control of its intellectual property while allowing a consumer to have transparent access to the copyright-protected content via the network. To that end, the IBO system operates to download and stage the copyrighted digital content on the viewing system of a consumer.
Owner:RPX CORP
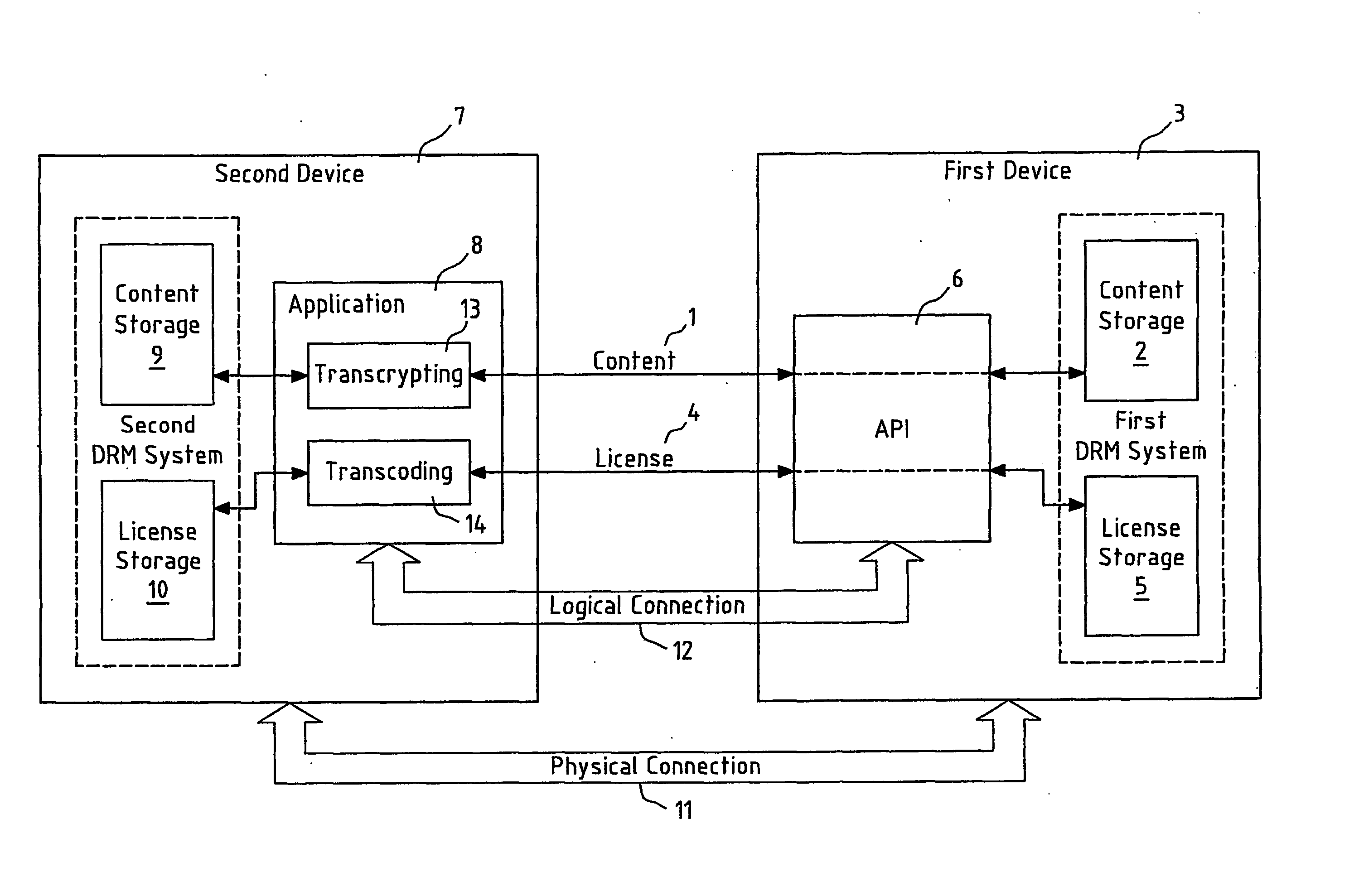
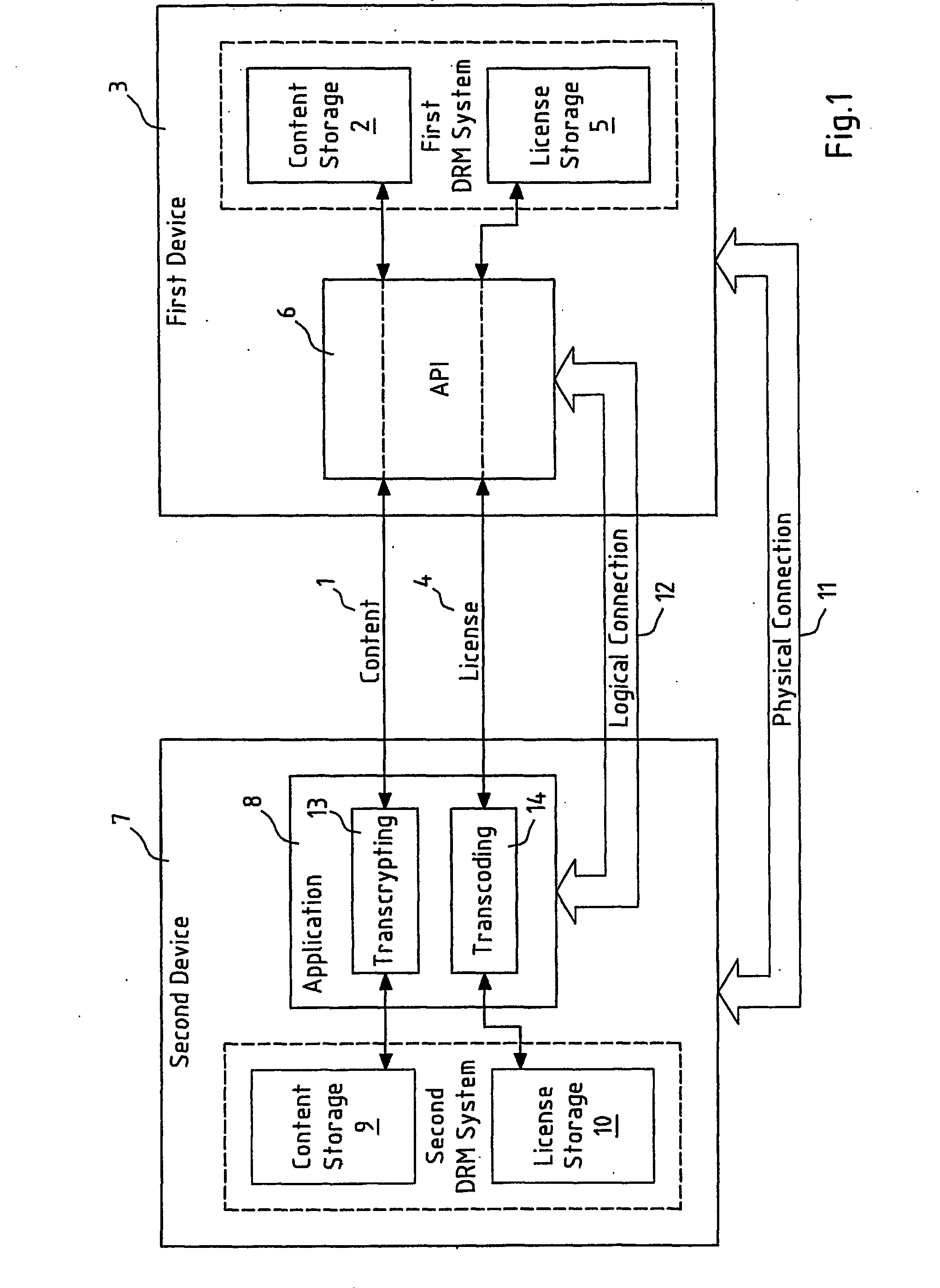
Transferring content between digital rights management systems
InactiveUS20070027814A1Reduce usageData processing applicationsProgram/content distribution protectionContent formatDigital rights management system
A method, system and computer program product are shown for transferring encrypted content (1) and a corresponding license (4) that are contained in a first device (3) that uses a first Digital Rights Management (DRM) system of a first or second type to a second device (7) that uses a second DRM system of a first or second type, wherein the encrypted content (1) obeys a content format of the first DRM system; wherein the corresponding license (4) obeys the Rights Expression Language of the first DRM system; wherein one of the devices (3) provides an Application Programming Interface (API) (6) for importing and / or exporting the encrypted content (1) and the corresponding license (4); and wherein the other device (7) provides an application (8) for transferring (13, 14) the encrypted content (1) and the corresponding license (4).
Owner:NOKIA CORP
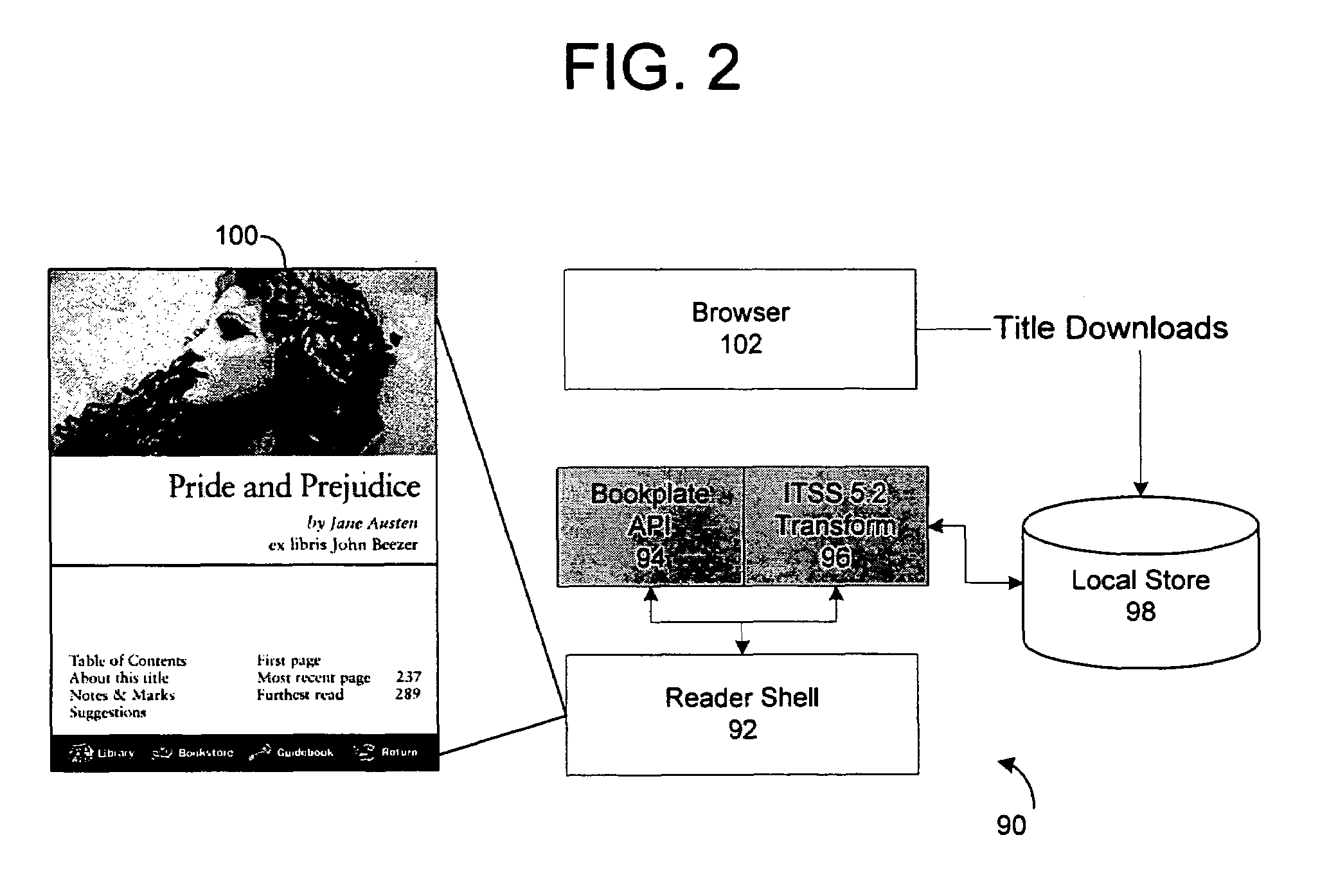
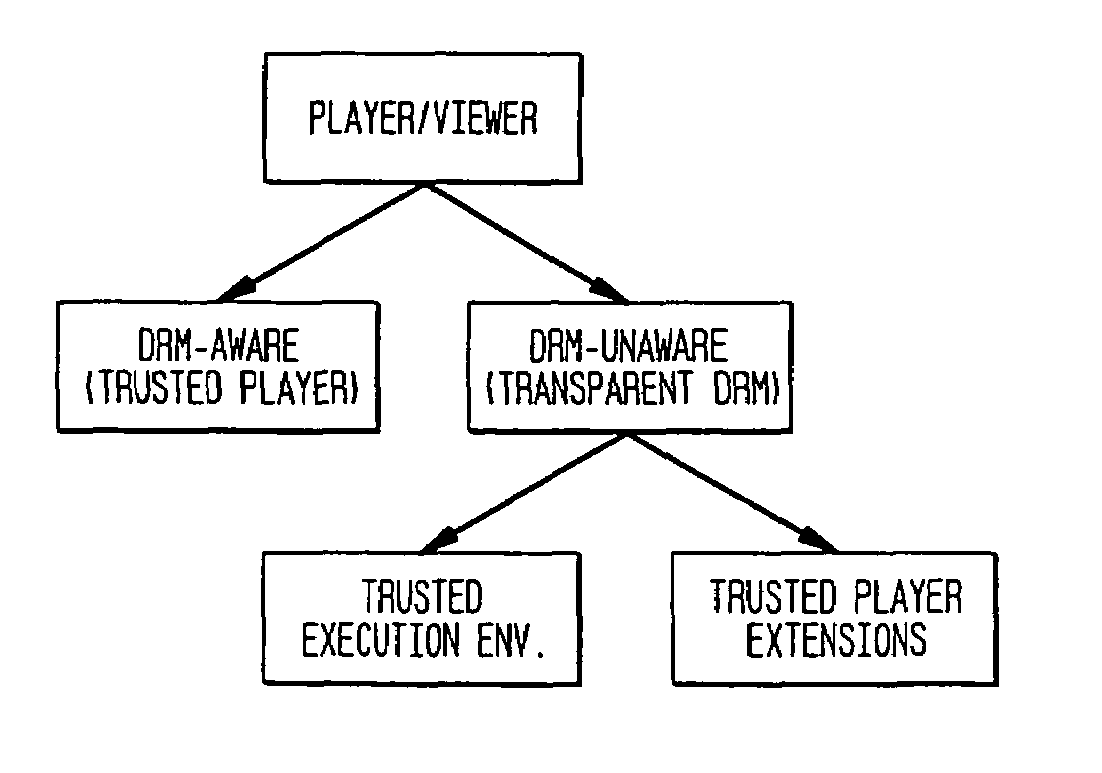
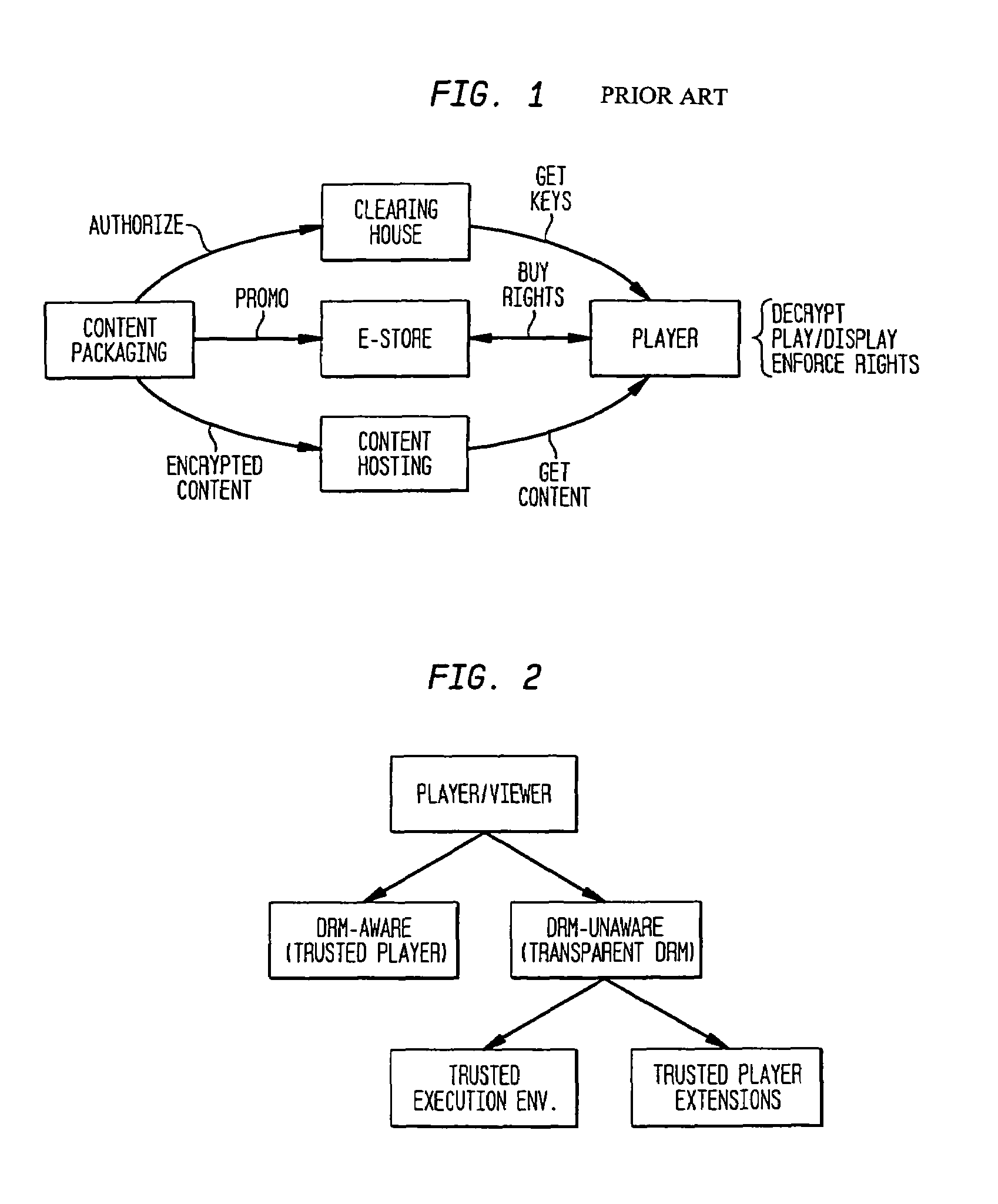
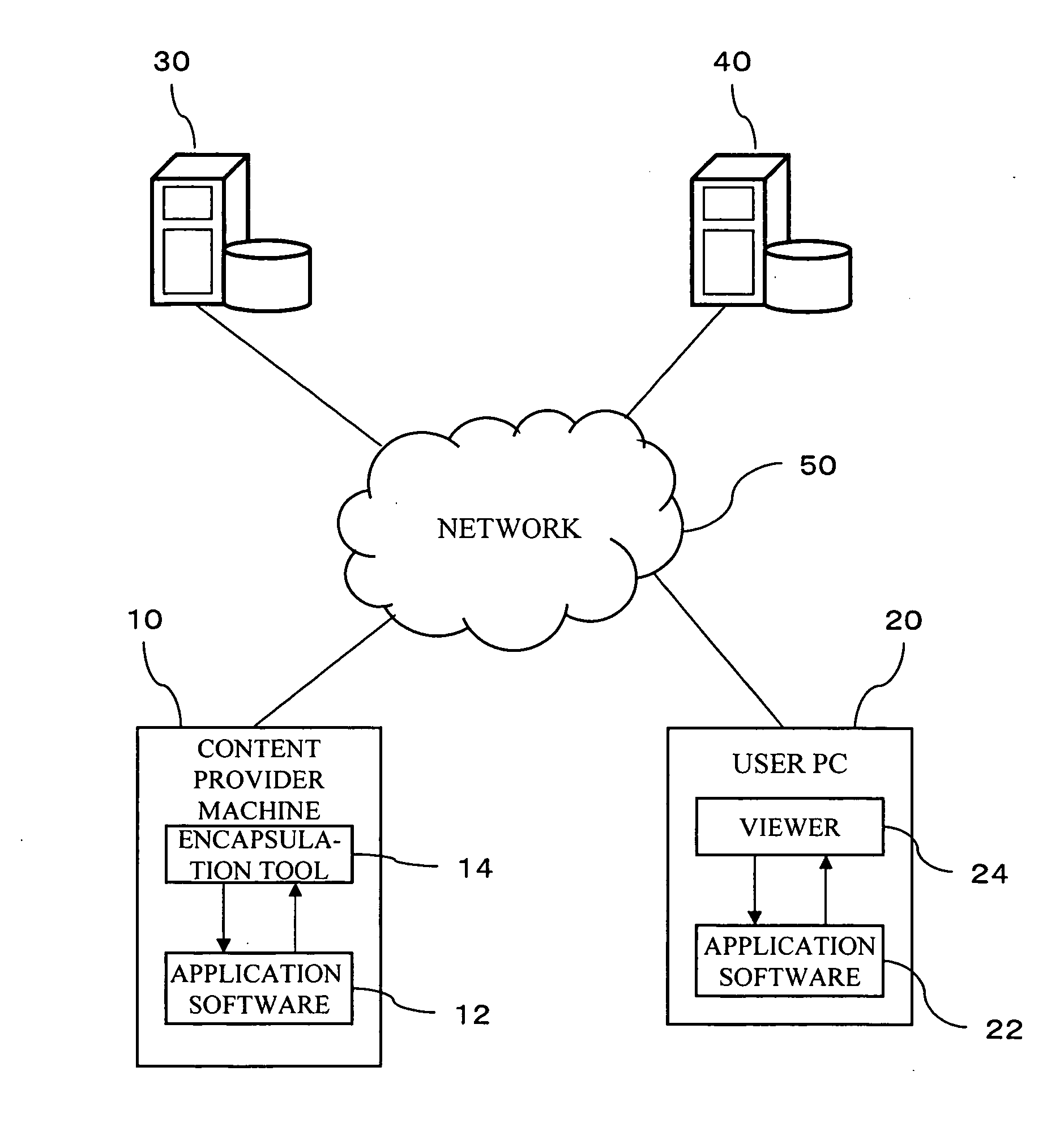
Transparent digital rights management for extendible content viewers
InactiveUS7171558B1Facilitate communicationDigital data processing detailsUser identity/authority verificationWeb browserDigital rights management system
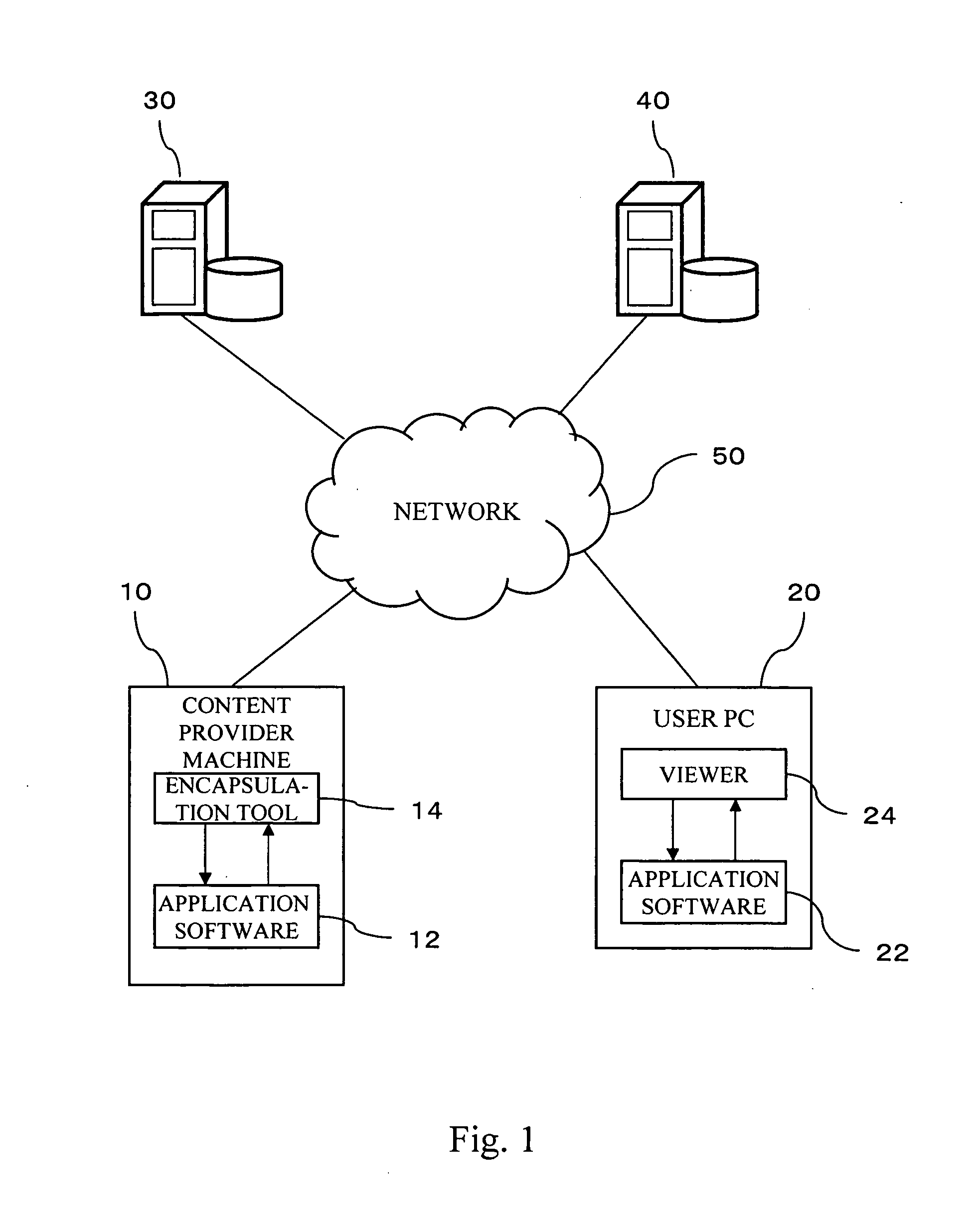
A digital rights management system for controlling the distribution of digital content to player applications. The system comprises a verification system, a trusted content handler, and a user interface control. The verification system is provided to validate the integrity of the player applications; and the trusted content handler is used to decrypt content and to transmit the decrypted content to the player applications, and to enforce usage rights associated with the content. The user interface control module is provided to ensure that users of the player applications are not exposed to actions that violate the usage rights. The preferred embodiment of the present invention provides a system that enables existing content viewers, such as Web browsers, document viewers, and Java Virtual Machines running content-viewing applications, with digital rights management capabilities, in a manner that is transparent to the viewer. Extending content viewers with such capabilities enables and facilitates the free exchange of digital content over open networks, such as the Internet, while protecting the rights of content owners, authors, and distributors. This protection is achieved by controlling access to the content and constraining it according to the rights and privileges granted to the user during the content acquisition phase.
Owner:IBM CORP
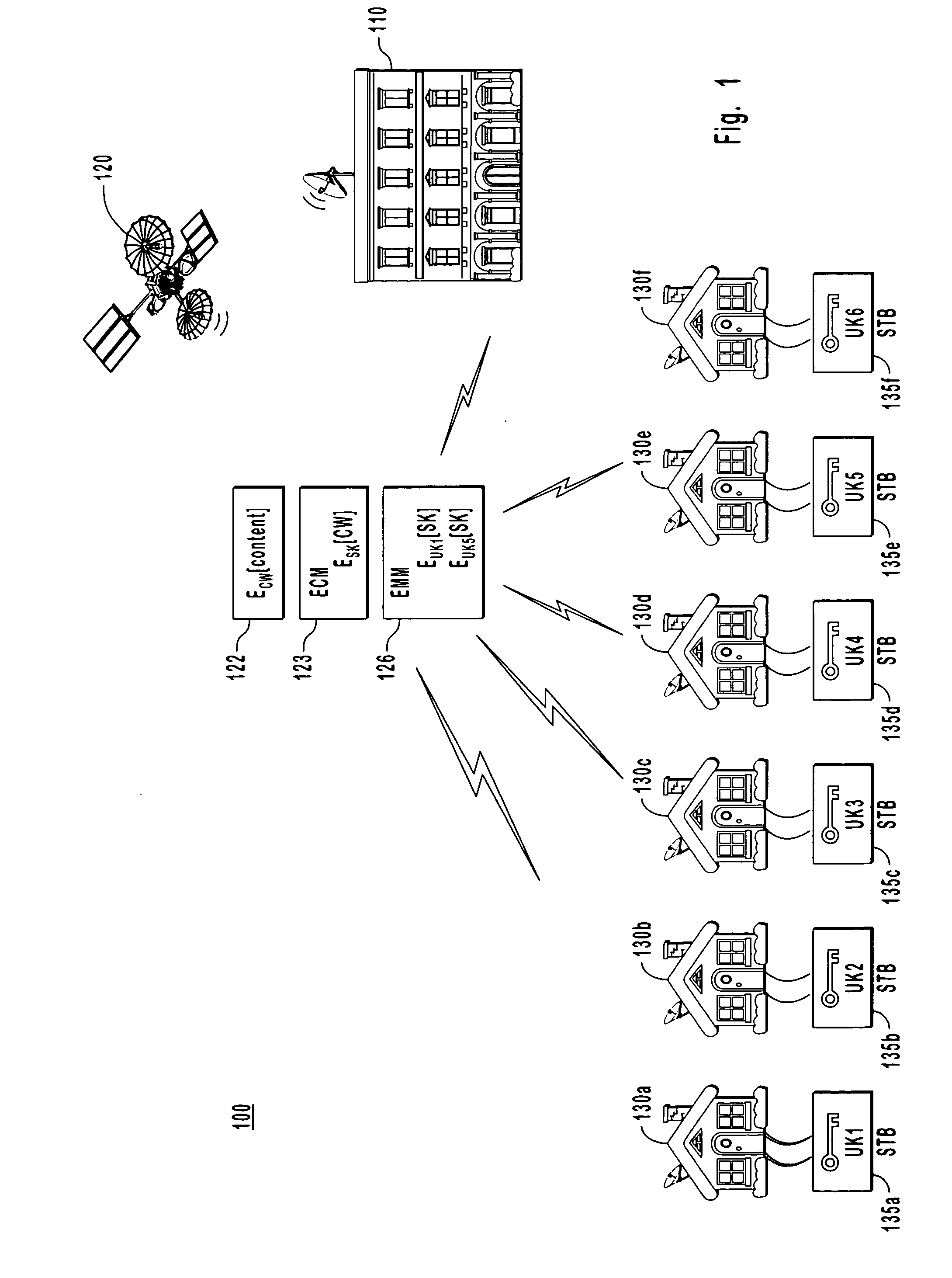
Systems and methods for conditional access and digital rights management
InactiveUS20070294170A1Simple deliverySecure and efficientTelevision system detailsProgram/content distribution protectionContent distributionDigital rights management system
Conditional access (CA) and digital rights management (DRM) in digital media delivery, processing, and storage systems. Methods and apparatuses are provided for managing digital rights under the protection of multiple CA and / or DRM systems. Some embodiments provide secure and robust methods for bridging multiple DRM systems in the digital media content distribution and playback systems. The present invention simplifies content delivery, conditional access, and digital rights management.
Owner:DIGITAL KEYSTONE
Device for protecting digital content, device for processing protected digital content, method for protecting digital content, method for processing protected digital content, storage medium storing program for protecting digital content, and storage medium storing program for processing protected digital content
InactiveUS20060288424A1Digital data processing detailsUser identity/authority verificationDigital contentDigital rights management system
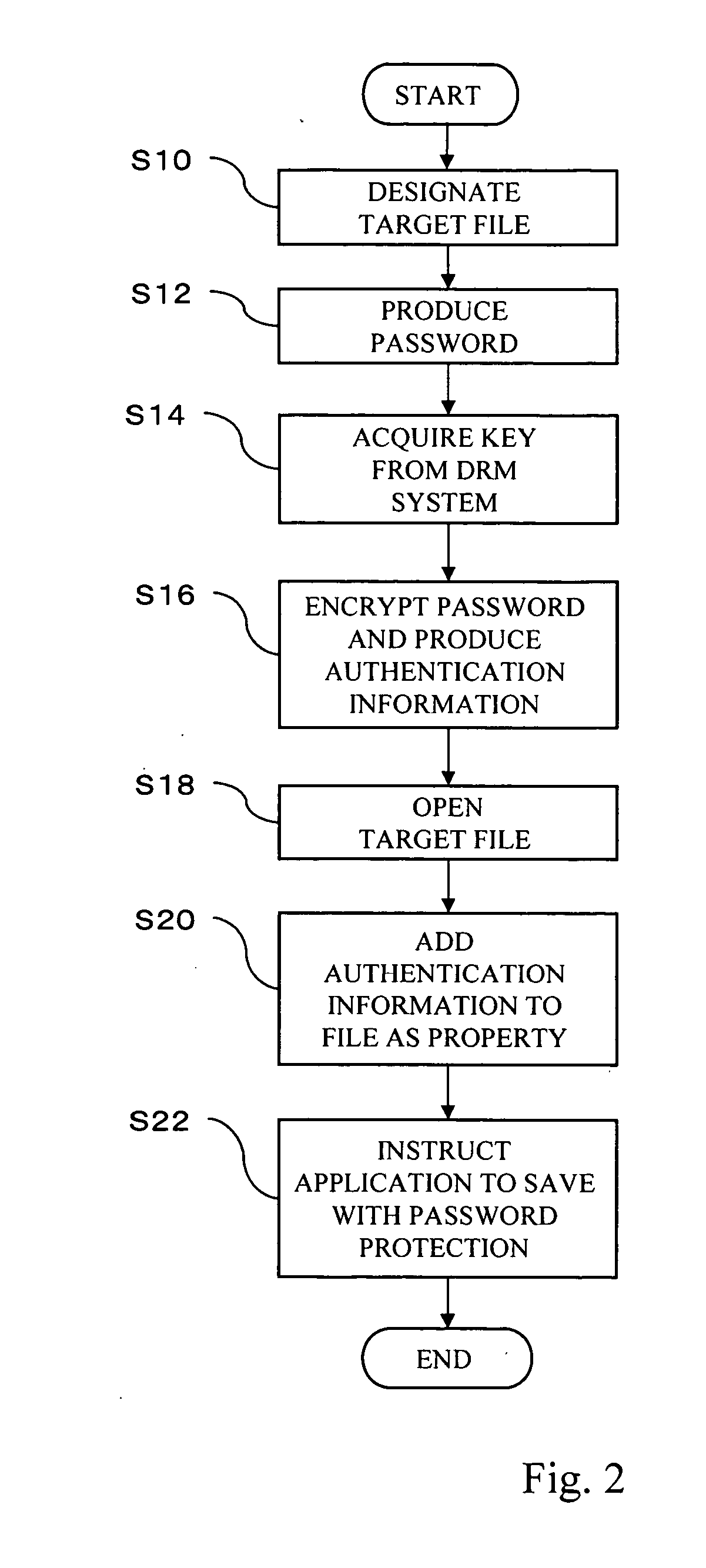
There is provided a device for protecting a digital content. The device includes a digital content processing section that causes a digital content to be protected using security information; and an encrypting section that encrypts the security information, using a key acquired from a Digital Right Management system of an electronic ticket system.
Owner:FUJIFILM BUSINESS INNOVATION CORP
Inter-server communication using request with encrypted parameter
InactiveUS6970849B1Preventing unchecked proliferationDigital data processing detailsUser identity/authority verificationUniform resource locatorBiological activation
A server architecture for a digital rights management system that distributes and protects rights in content. The server architecture includes a retail site which sells content items to consumers, a fulfillment site which provides to consumers the content items sold by the retail site, and an activation site which enables consumer reading devices to use content items having an enhanced level of copy protection. Each retail site is equipped with a URL encryption object, which encrypts, according to a secret symmetric key shared between the retail site and the fulfillment site, information that is needed by the fulfillment site to process an order for content sold by the retail site. Upon selling a content item, the retail site transmits to the purchaser a web page having a link to a URL comprising the address of the fulfillment site and a parameter having the encrypted information. Upon following the link, the fulfillment site downloads the ordered content to the consumer, preparing the content if necessary in accordance with the type of security to be carried with the content. The fulfillment site includes an asynchronous fulfillment pipeline which logs information about processed transactions using a store-and-forward messaging service. The fulfillment site may be implemented as several server devices, each having a cache which stores frequently downloaded content items, in which case the asynchronous fulfillment pipeline may also be used to invalidate the cache if a change is made at one server that affects the cached content items. An activation site provides an activation certificate and a secure repository executable to consumer content-rendering devices which enables those content rendering devices to render content having an enhanced level of copy-resistance. The activation site “activates” client-reading devices in a way that binds them to a persona, and limits the number of devices that may be activated for a particular persona, or the rate at which such devices may be activated for a particular persona.
Owner:MICROSOFT TECH LICENSING LLC
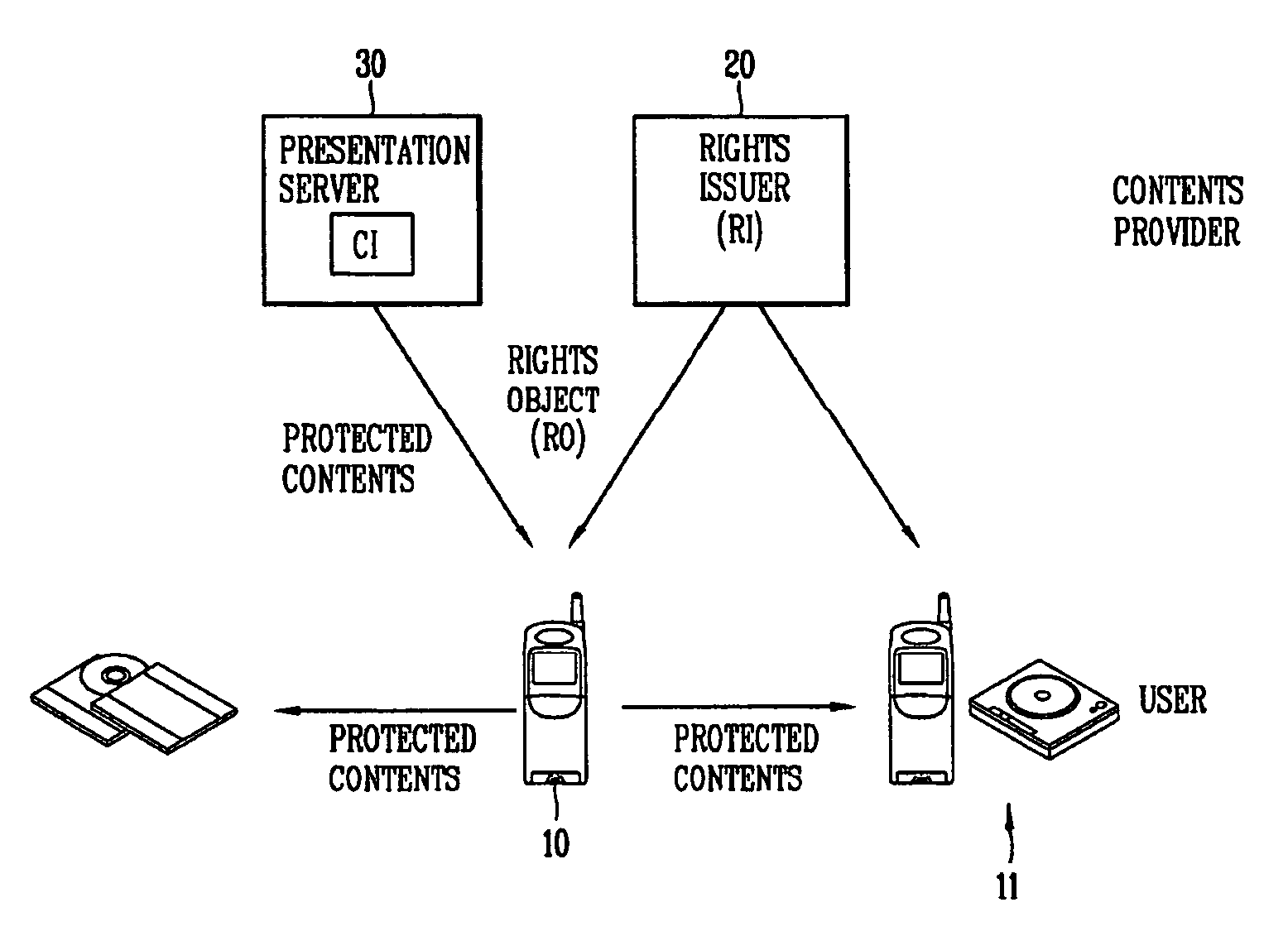
Method and apparatus for transferring protected content between digital rights management systems
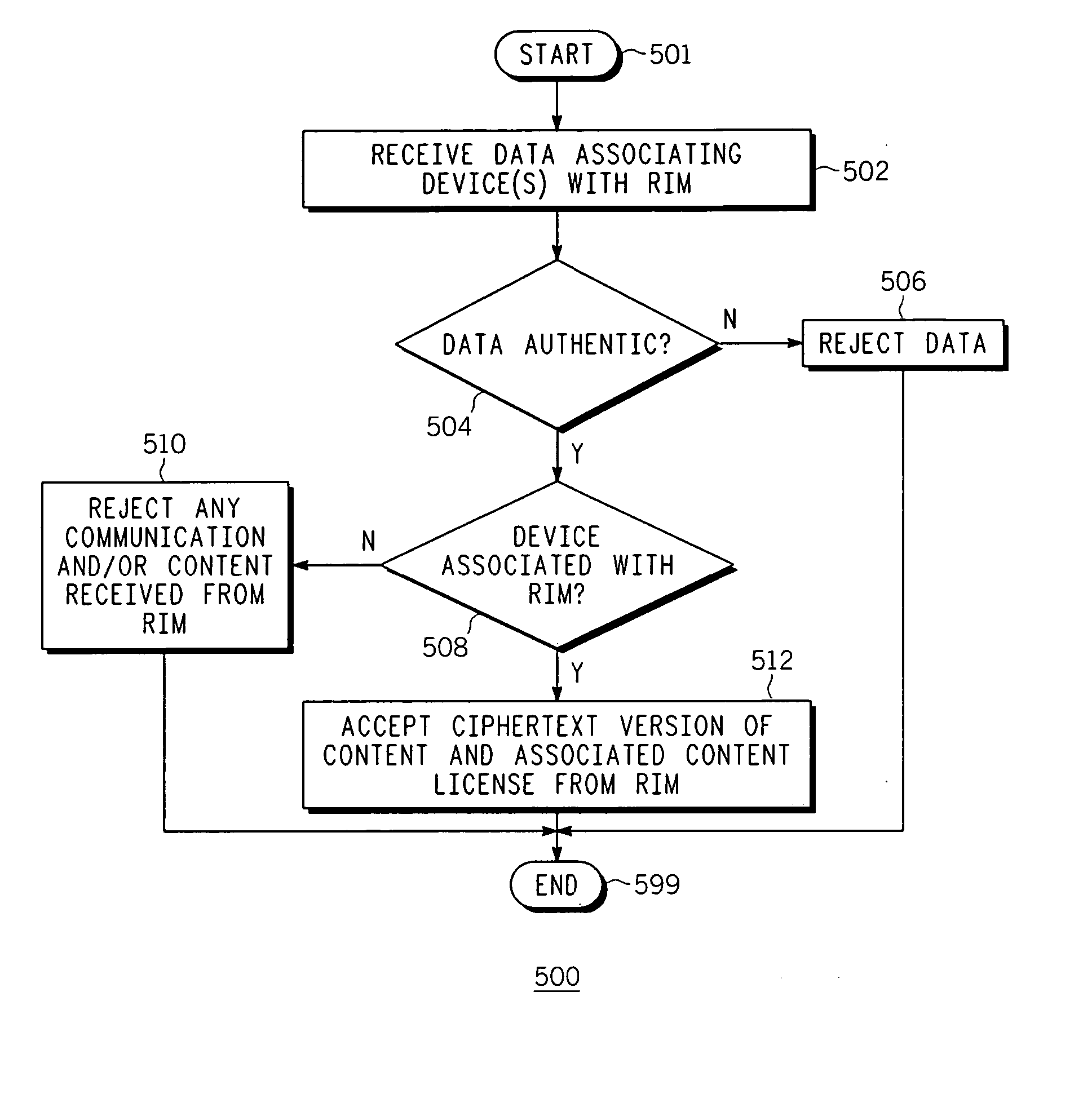
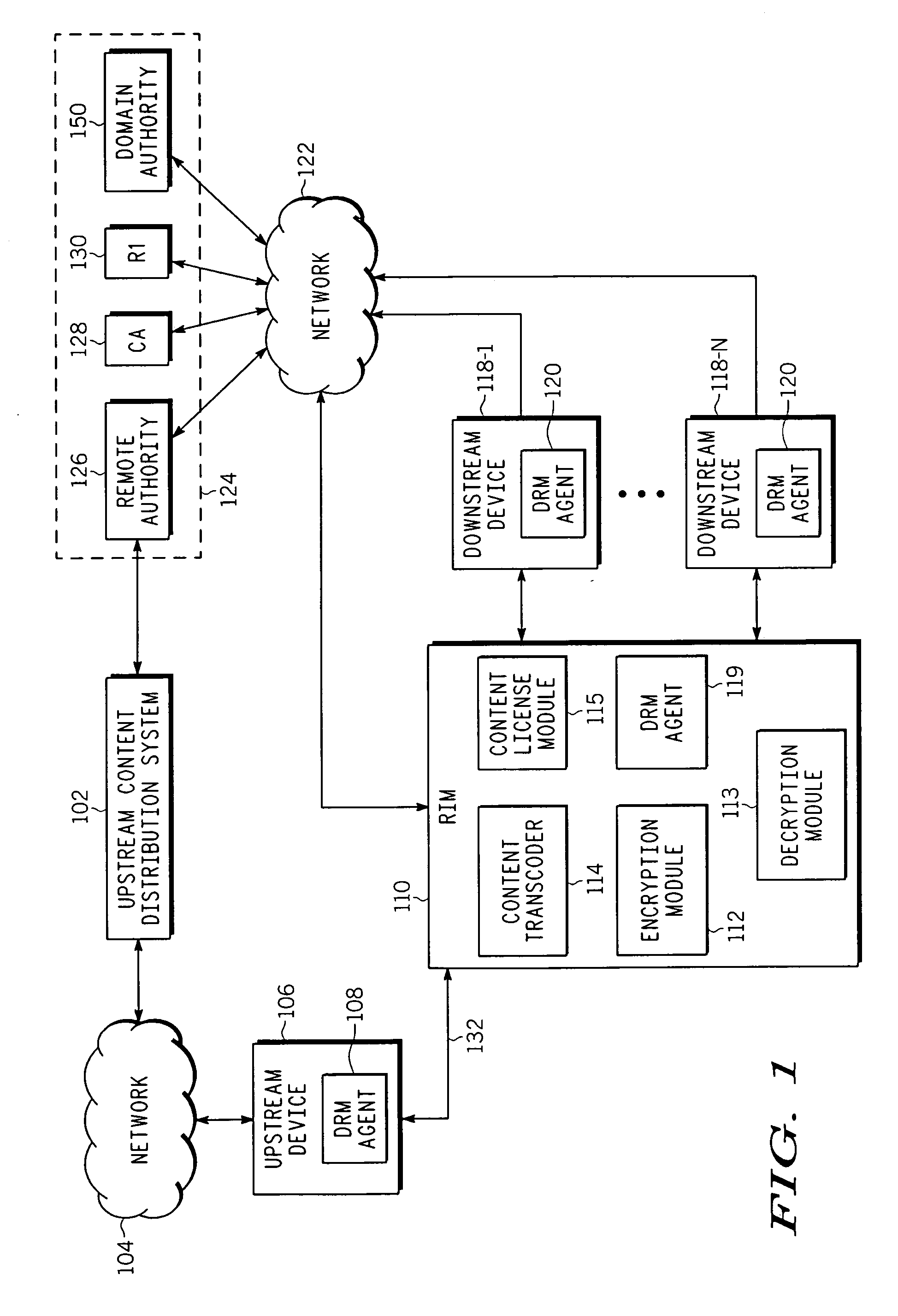
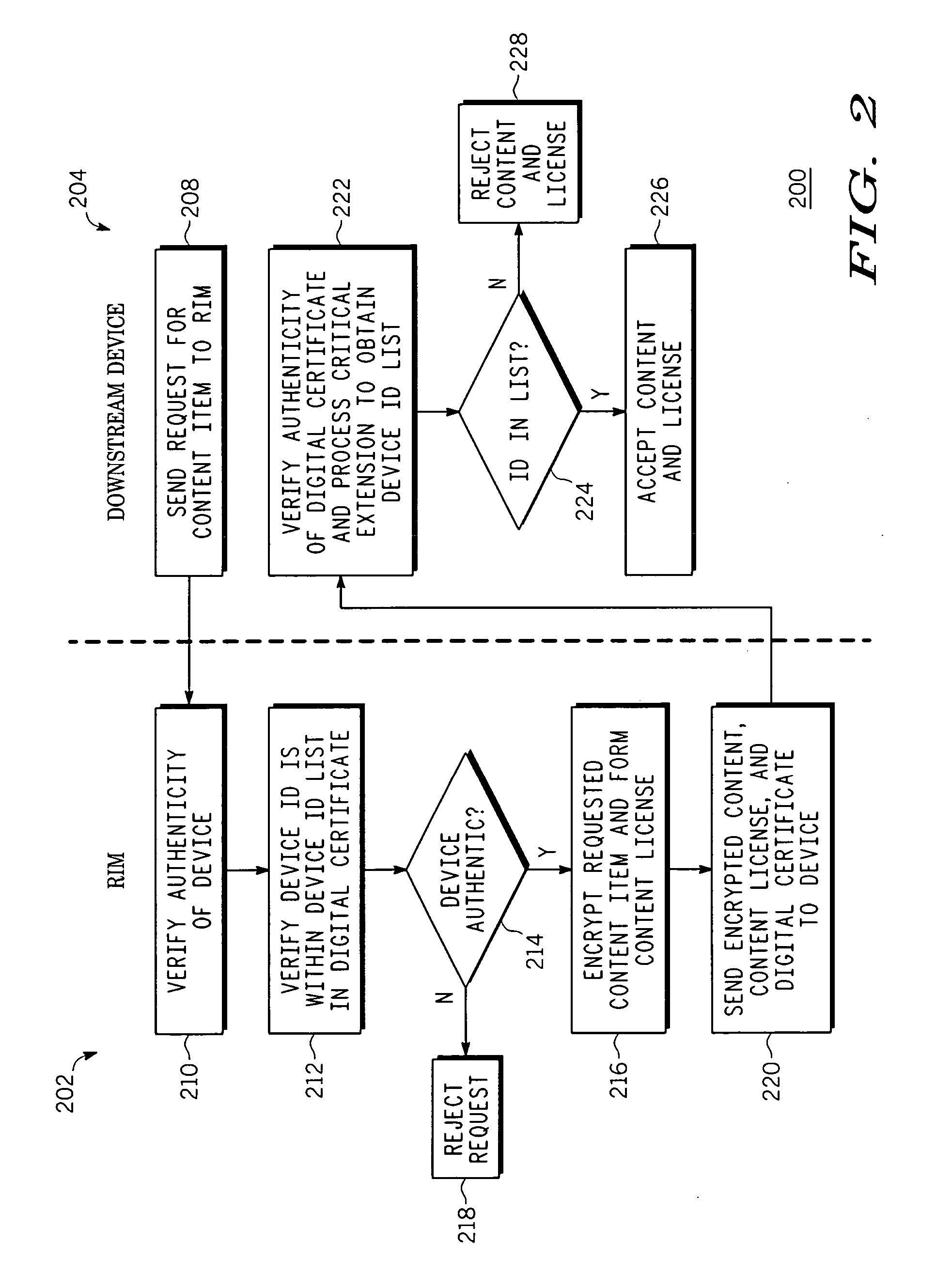
InactiveUS20060282391A1Program/content distribution protectionSelective content distributionCiphertextDigital rights management system
Method and apparatus for transferring protected content between digital rights management systems is described. One aspect of the invention relates to importing content from an upstream digital rights management (DRM) system into a device in a downstream DRM system. Data is received that associates at least one device in the downstream DRM system with a rights issuer module (RIM). Authenticity of the data is verified as originating from an entity in a trust hierarchy of the device. If the data is authentic and the device is one of the at least one device associated with the RIM, a ciphertext version of the content and a corresponding content license is accepted from the RIM.
Owner:GOOGLE TECH HLDG LLC
Key management method using hierarchical node topology, and method of registering and deregistering user using the same
InactiveUS20060177066A1Effectively and securely performingInstrument handpiecesTelevision systemsDigital rights management systemNetsniff-ng
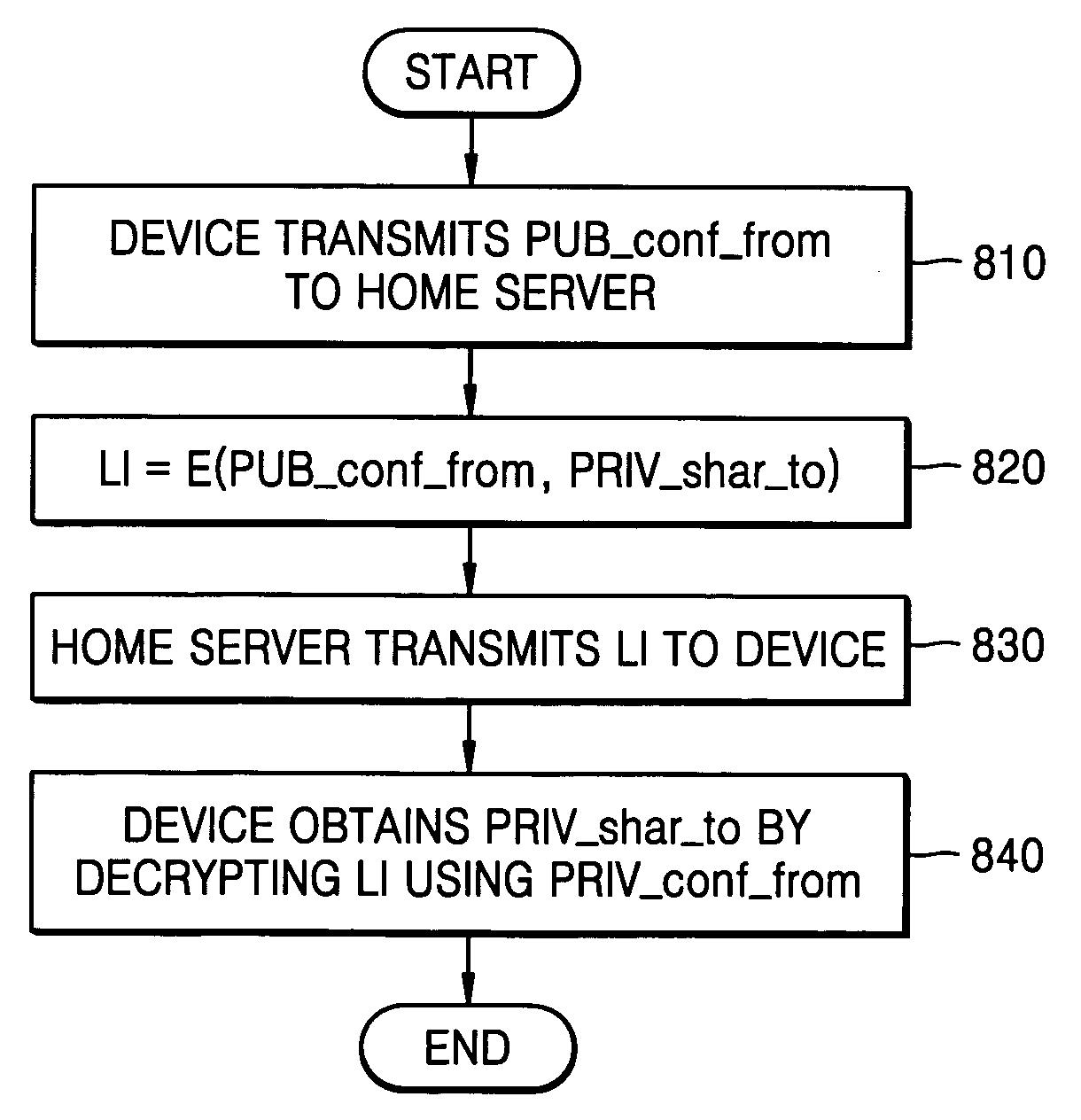
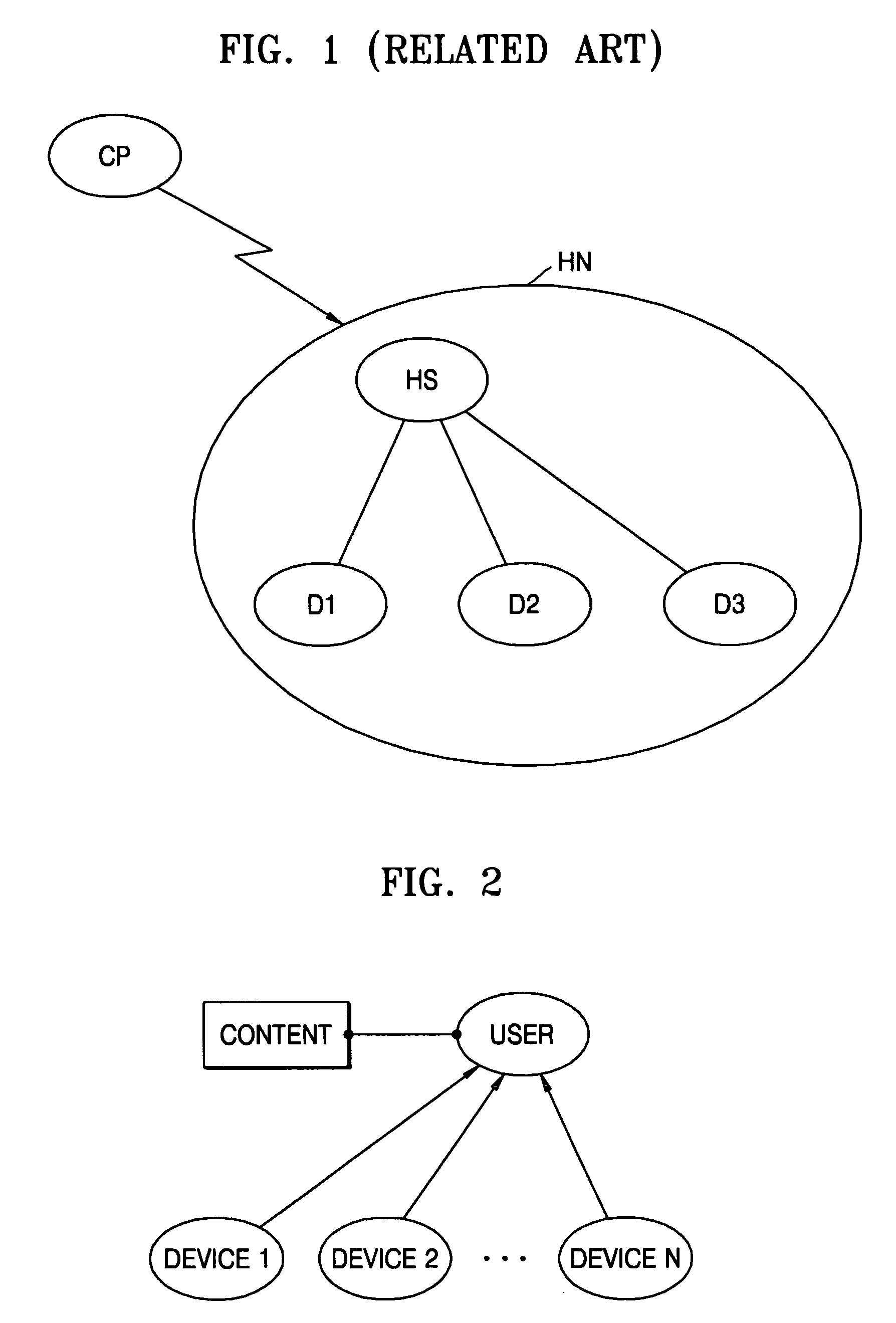
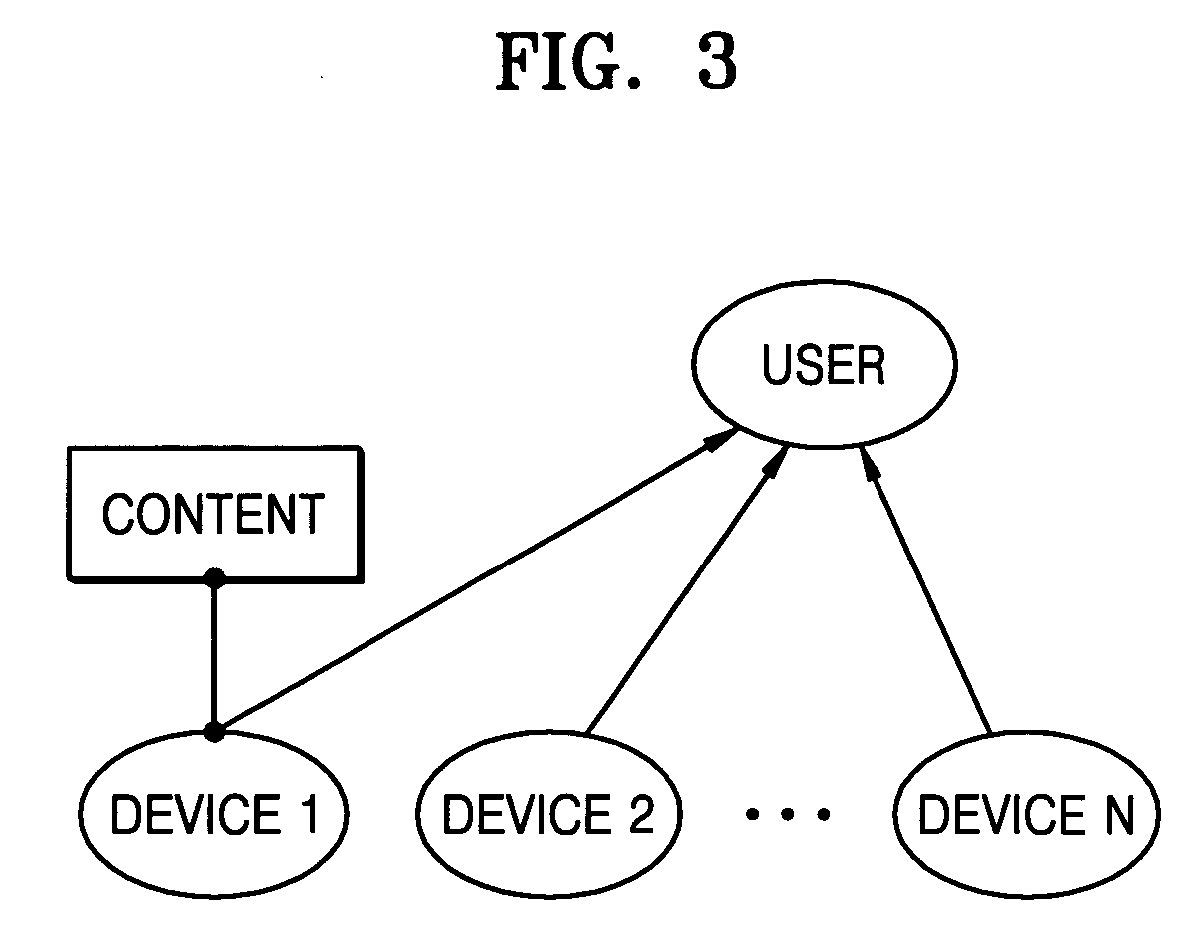
A key management, user registration and deregistration for a digital rights management (DRM) system in a home network, using a hierarchical node topology. In the key management, node information is generated by allocating a pair of keys (a public key and a private key) to each node. A node tree is made by generating link information using the pair of keys and a content key. The link information is delivered from an upper node to a lower node using the node tree. The link information is obtained by encrypting a private key of a ‘TO’ node using a public key of a ‘FROM’ node. Accordingly, it is possible to realize a DRM system that protects content and easily accomplishes a binding mechanism and a revocation mechanism.
Owner:SAMSUNG ELECTRONICS CO LTD
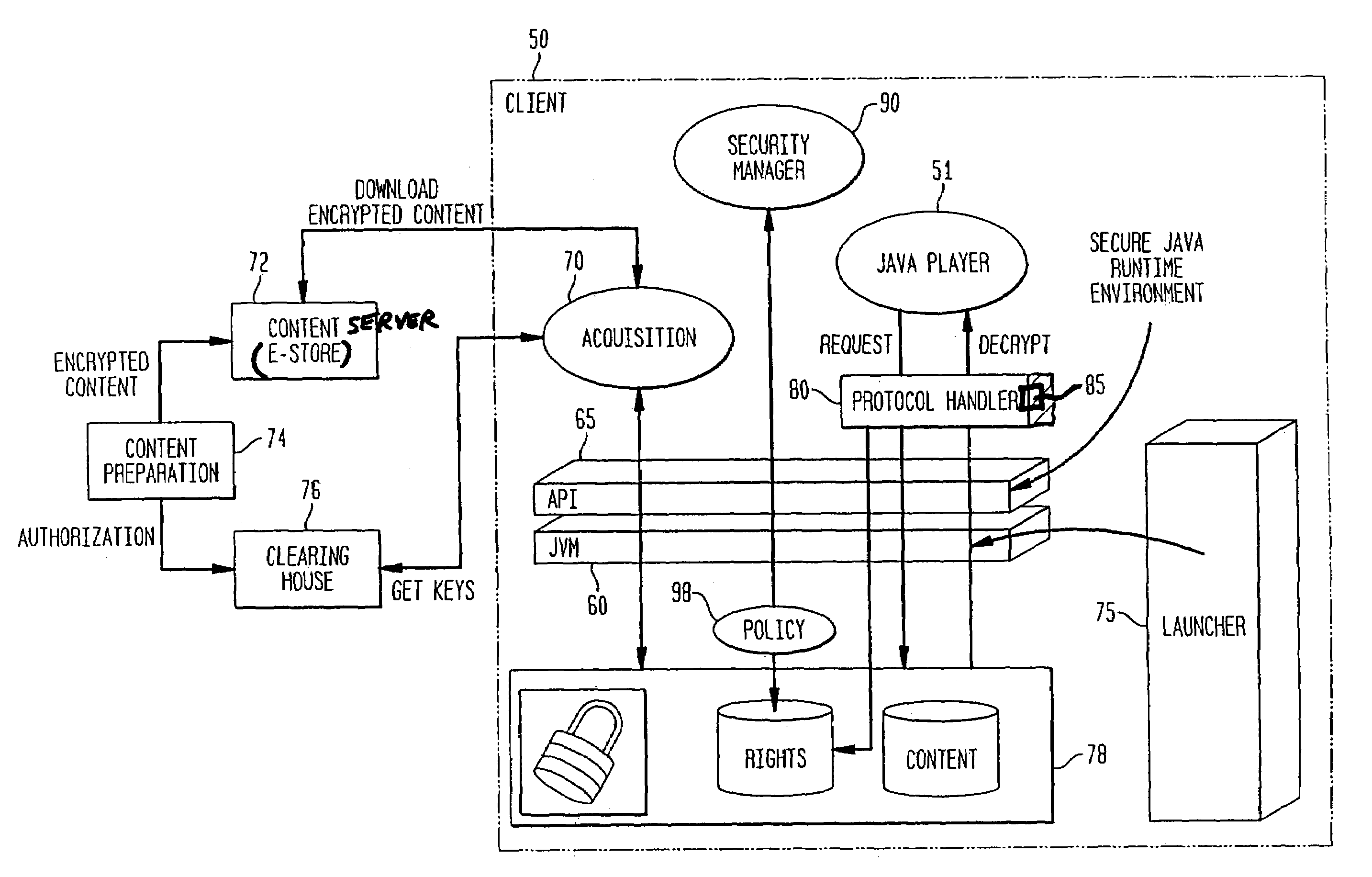
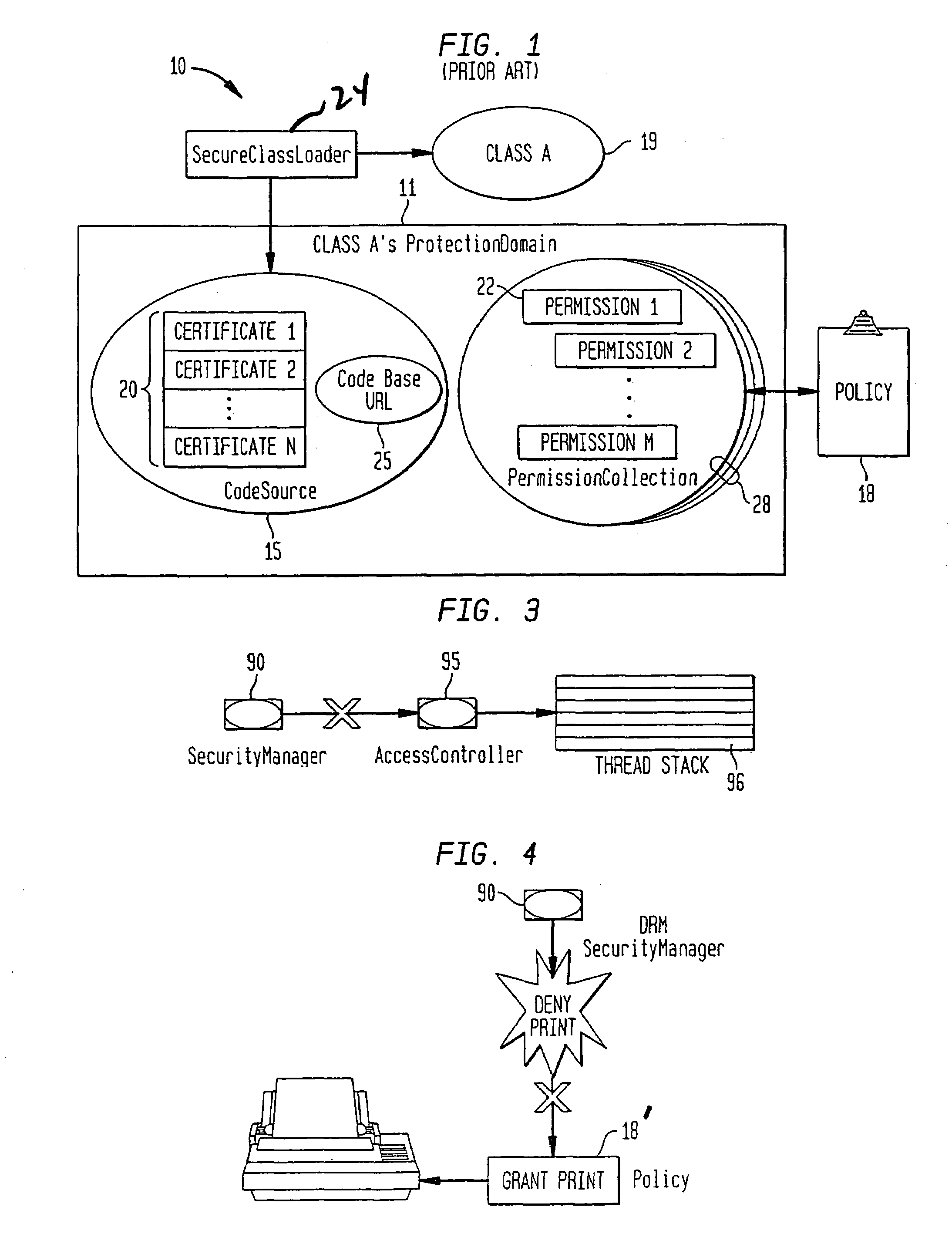
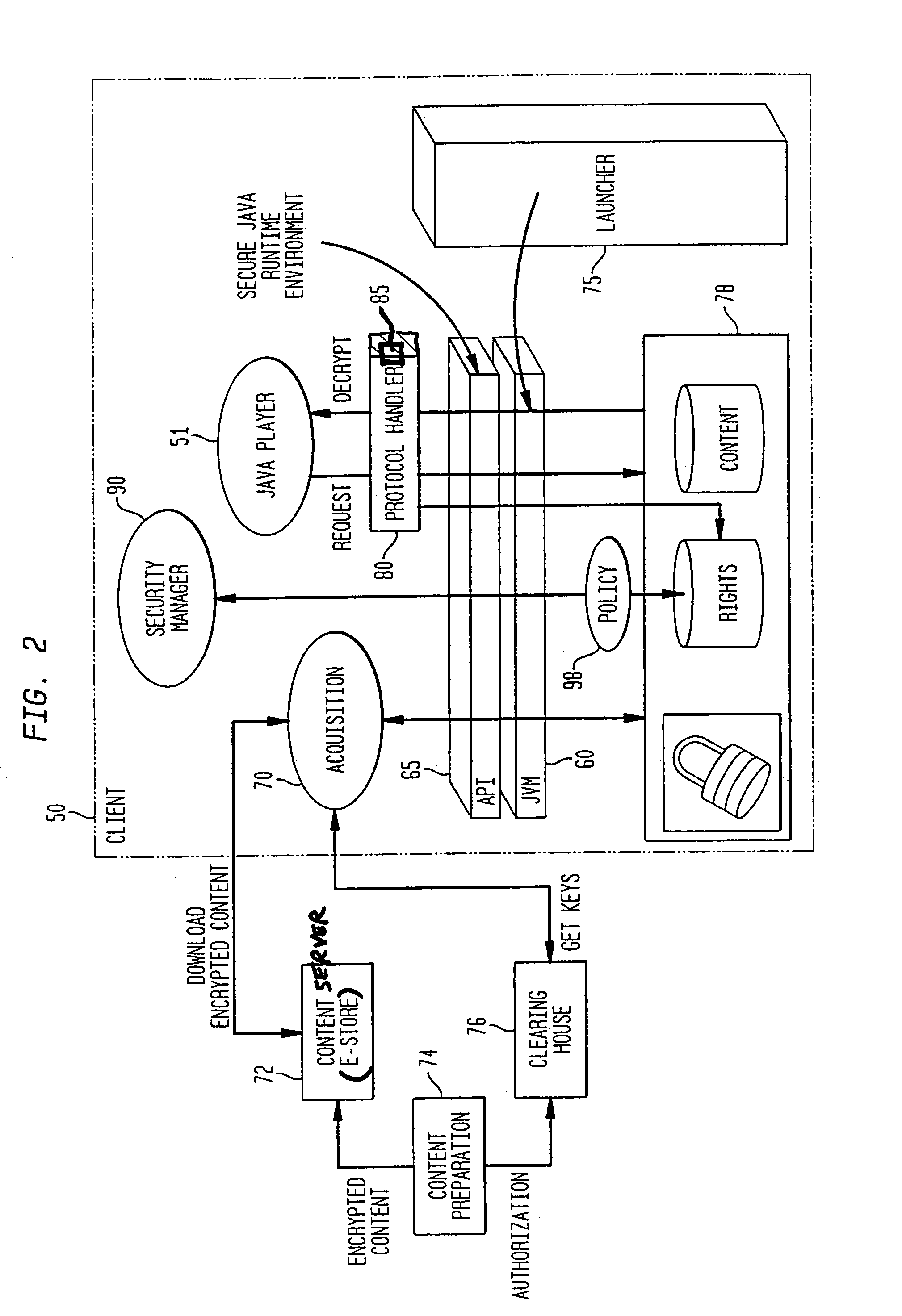
System and method for supporting digital rights management in an enhanced Java™ 2 runtime environment
InactiveUS7308717B2Provide protectionDigital data processing detailsAnalogue secracy/subscription systemsDigital rights management systemSoftware engineering
A digital rights management (DRM) system and methodology for a Java client implementing a Java Runtime Environment (JRE). The JRE comprises a Java Virtual Machine (JVM) and Java runtime libraries components and is capable of executing a player application for presenting content that can be presented through a Java program (e.g., a Java application, applet, servlet, bean, etc.) and downloaded from a content server to the client. The DRM system includes an acquisition component for receiving downloaded protected contents; and a dynamic rights management layer located between the JRE and player application for receiving requests to view or play downloaded protected contents from the player, and, in response to each request, determining the rights associated with protected content and enabling viewing or playing of the protected contents via the player application if permitted according to the rights. By providing a Ad DRM-enabled Java runtime, which does not affect the way non-DRM-related programs work, DRM content providers will not require the installation of customized players. By securing the runtime, every Java™ player automatically and transparently becomes a DRM-enabled player.
Owner:IBM CORP
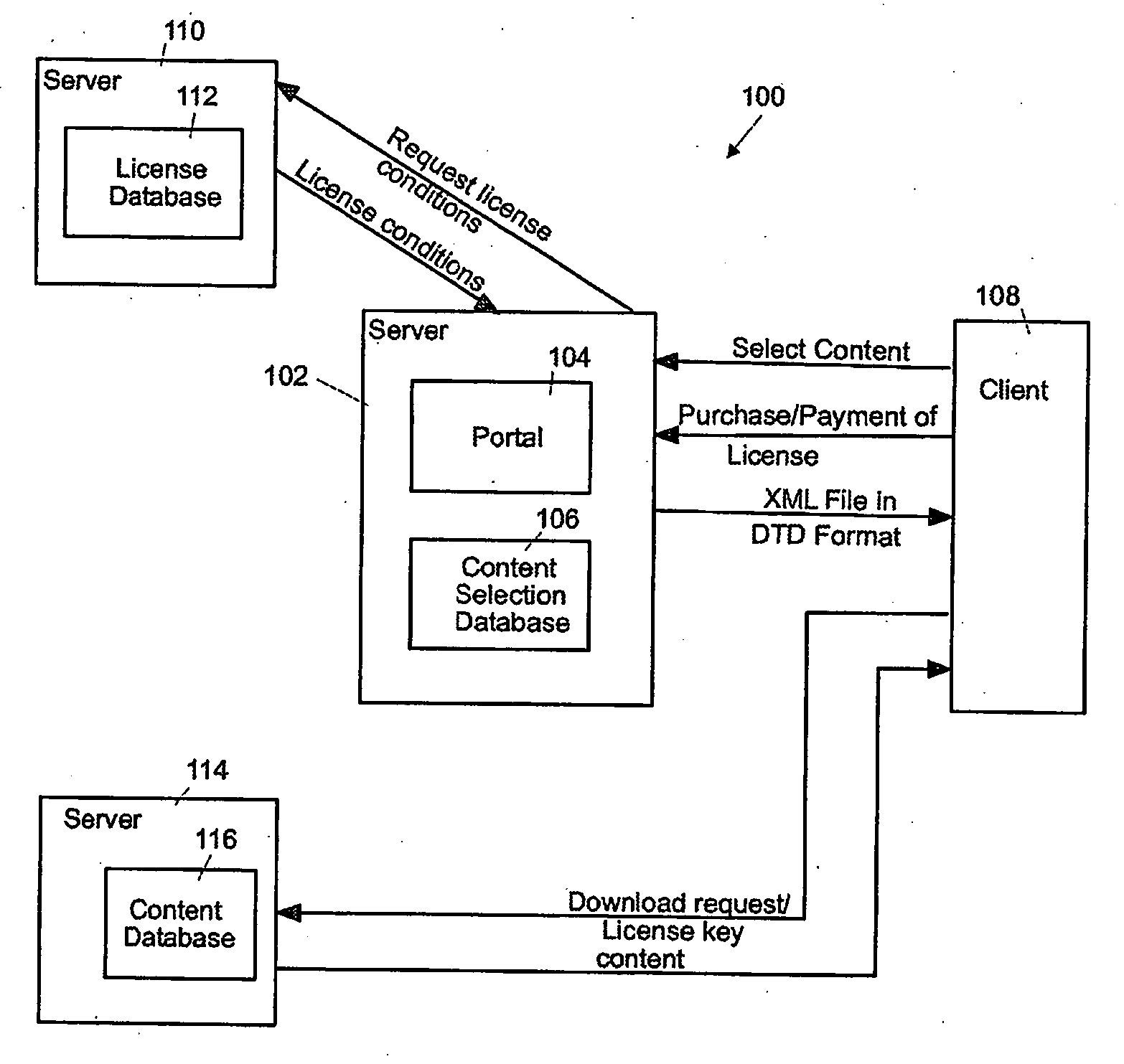
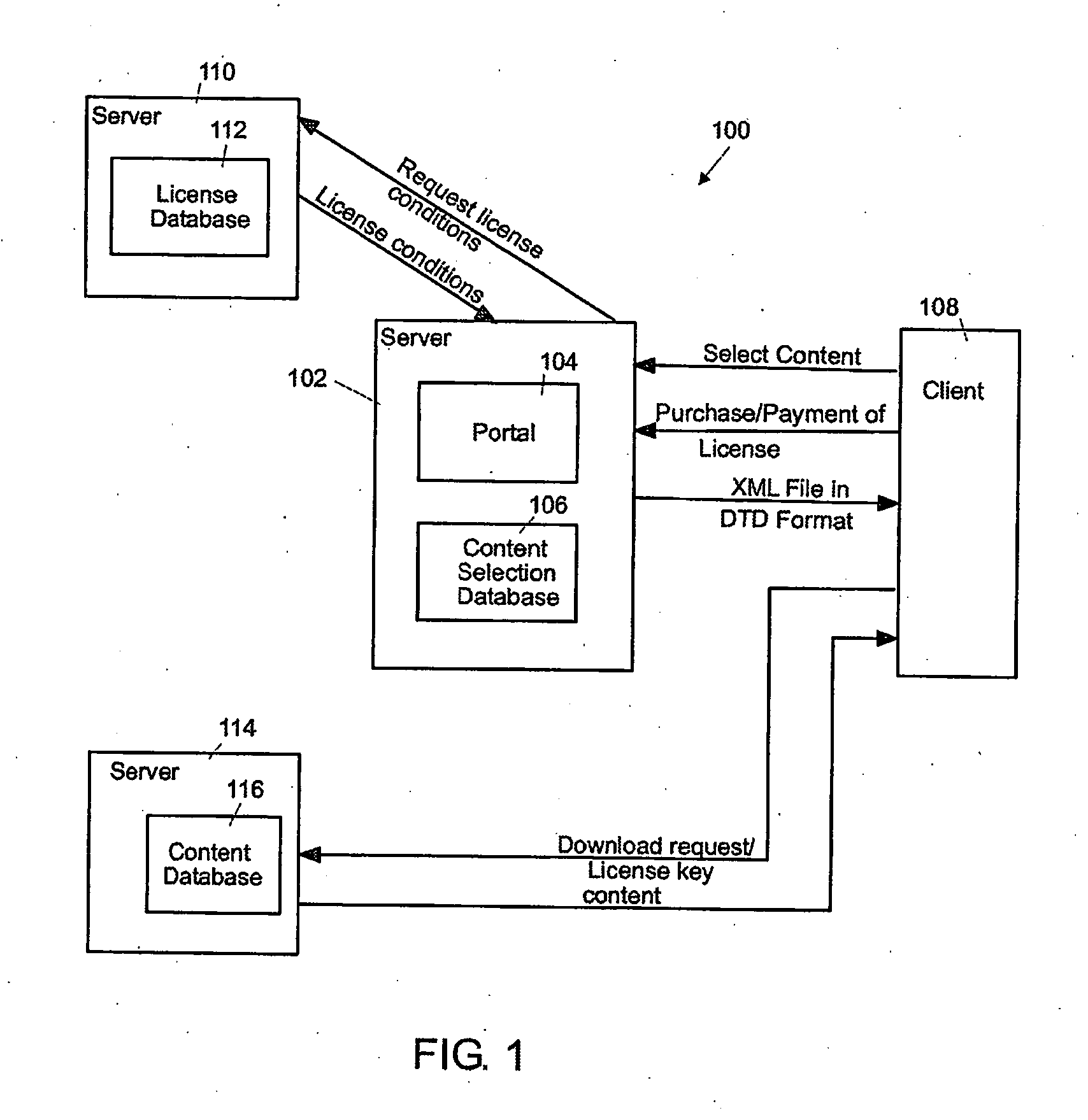
Method for providing of content data to a client
InactiveUS20060031222A1Digital data processing detailsPayment architectureData synchronizationDigital rights management system
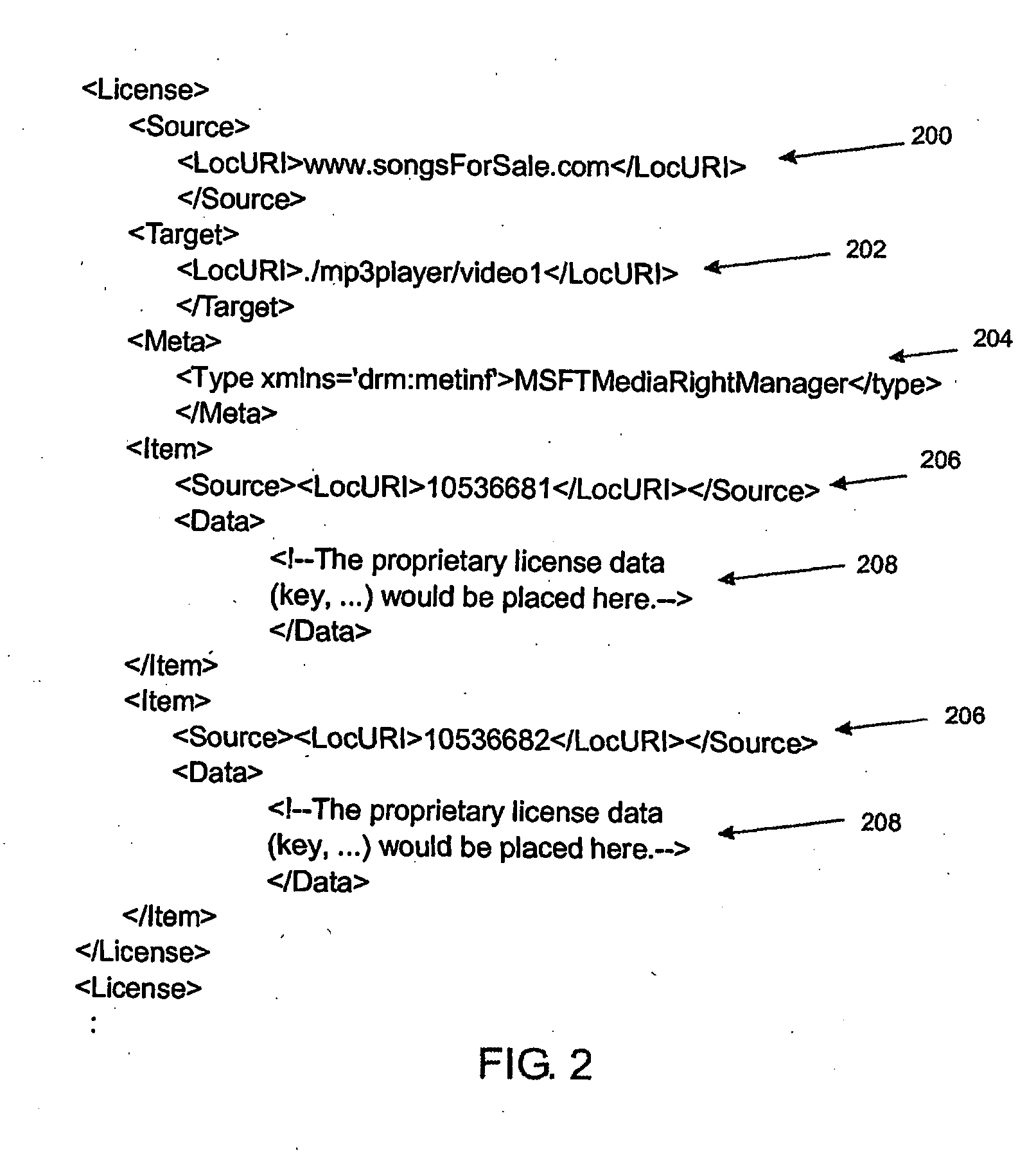
The present invention relates to a method for providing an interoperable digital rights management system for content data on a client based on synchronization technology, the method comprising the steps of:—receiving of a selection of content data from the, client,—generating of an XML file having a defined DTD format, the XML file comprising license information and a locator for the content data,—sending of the XML file to the client, synchronizing any license status relates data produced on the client back to the server.
Owner:IBM CORP
Asynchronous communication within a server arrangement
InactiveUS7171692B1Preventing unchecked proliferationDigital data processing detailsUser identity/authority verificationStore and forwardAsynchronous communication
A server architecture for a digital rights management system that distributes and protects rights in content. The server architecture includes a retail site which sells content items to consumers, a fulfillment site which provides to consumers the content items sold by the retail site. The fulfillment site includes an asynchronous fulfillment pipeline which logs information about processed transactions using a store-and-forward messaging service. The fulfillment site may be implemented as several server devices, each having a cache which stores frequently downloaded content items, in which case the asynchronous fulfillment pipeline may also be used to invalidate the cache if a change is made at one server that affects the cached content items.
Owner:MICROSOFT TECH LICENSING LLC
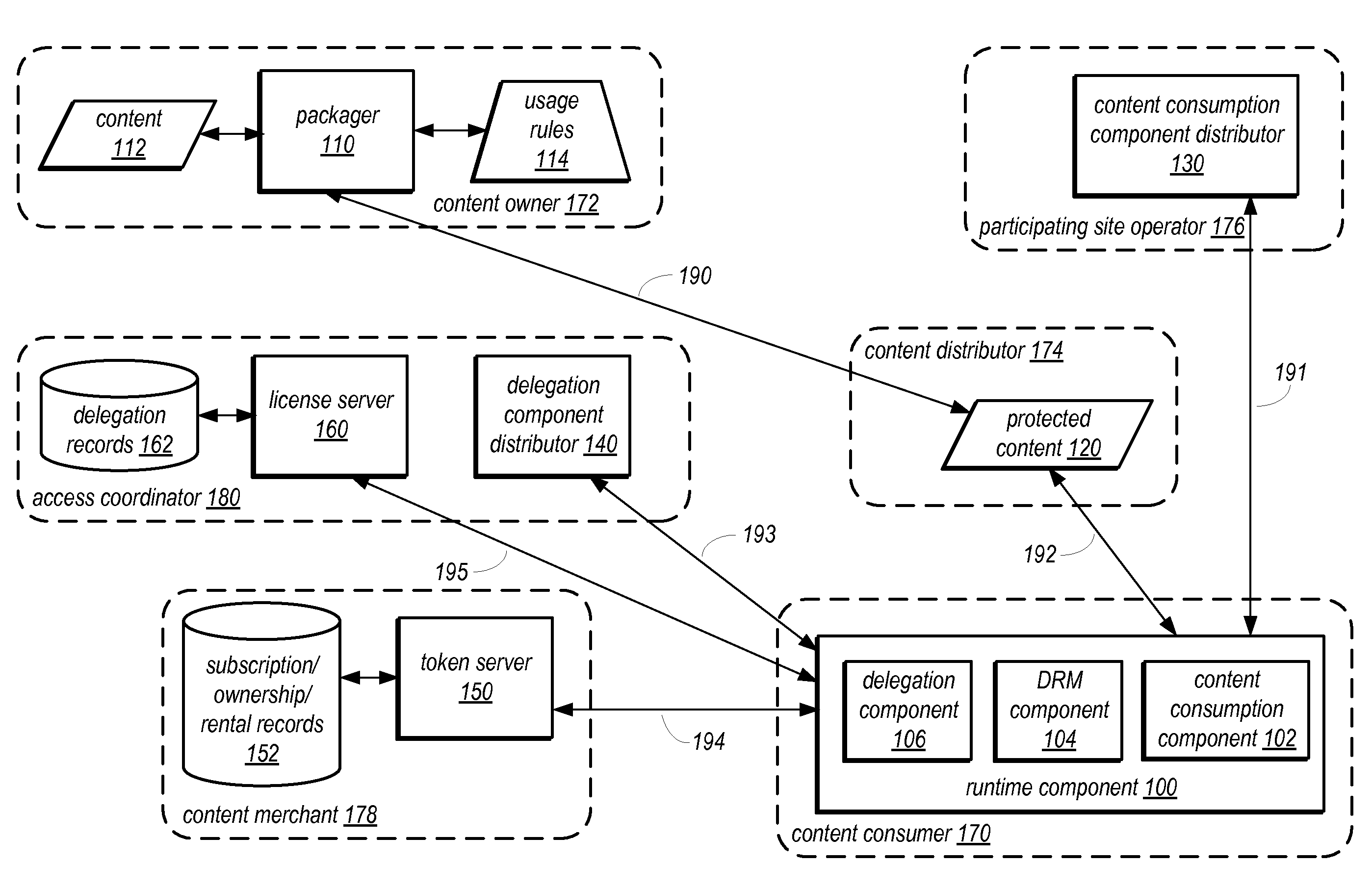
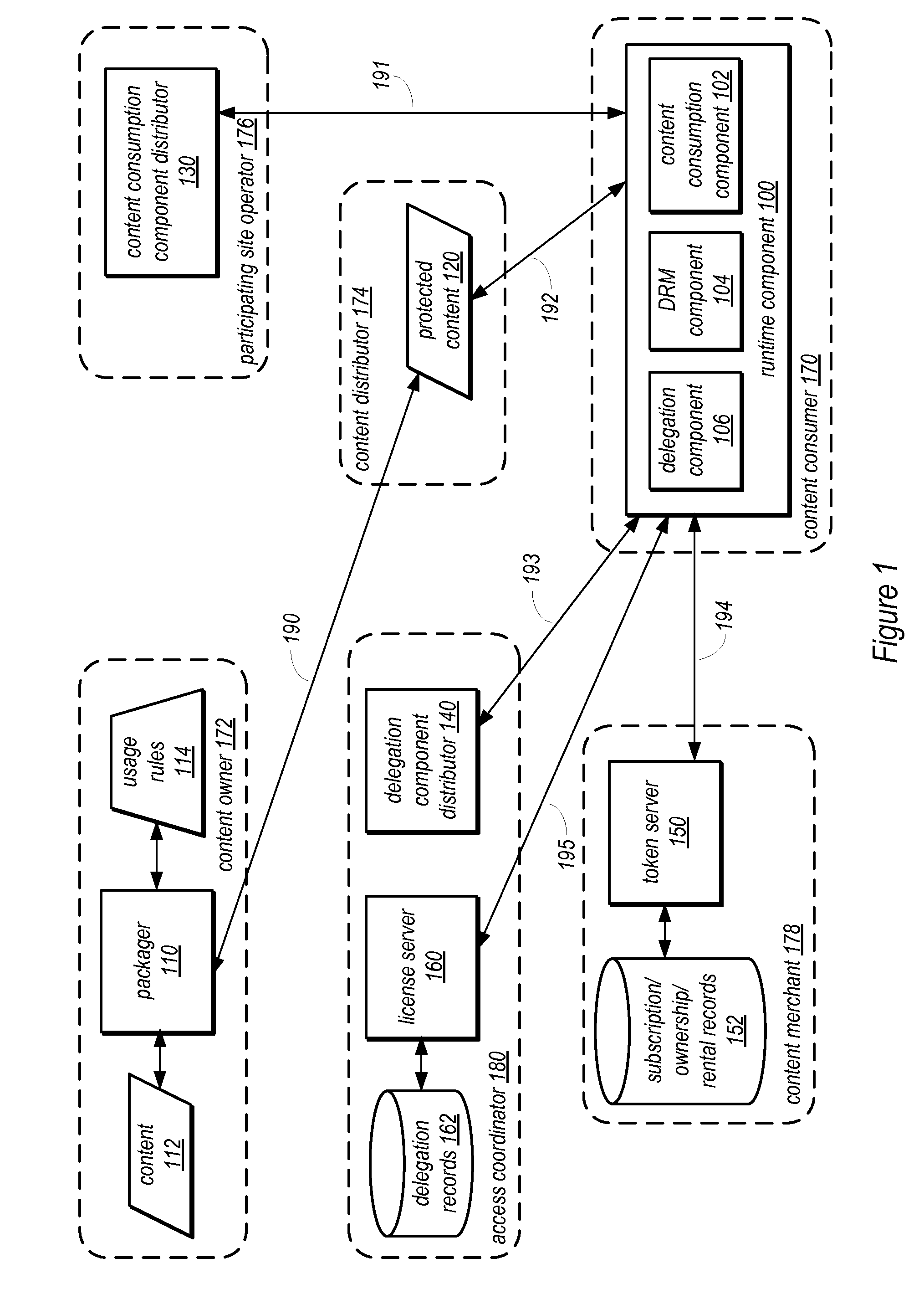
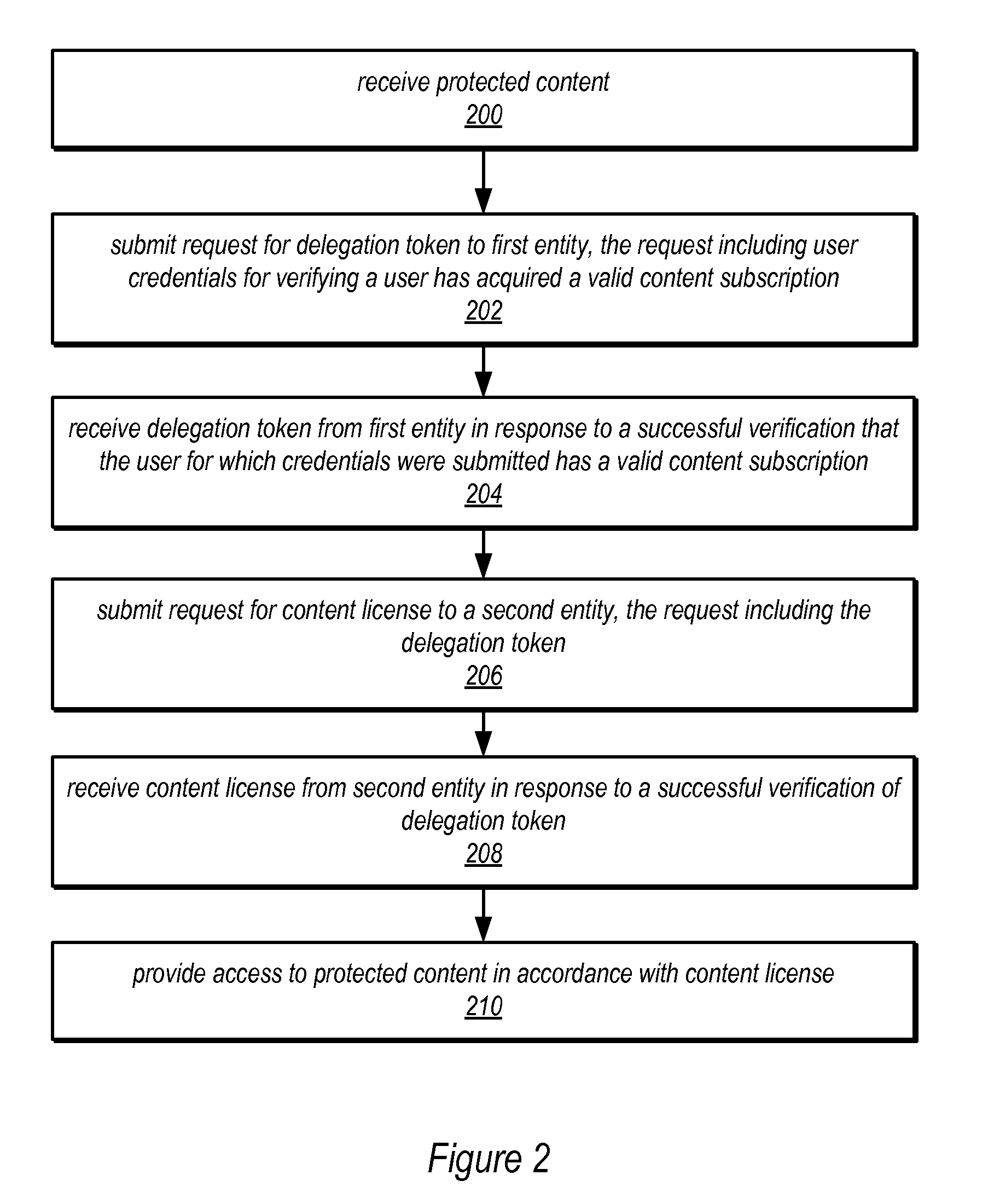
System And Method For Digital Rights Management With Delegated Authorization For Content Access
InactiveUS20130132232A1Digital data processing detailsAnalogue secracy/subscription systemsDigital rights management systemInternet privacy
Various embodiments of a system and method for digital rights management with delegated authorization for content access are described. Such embodiments may include a runtime component configured to receive protected content. The runtime component may be configured to submit a request for a delegation token to a first entity, such as a content merchant or some other entity. The runtime component may be configured to receive the delegation token from the first entity. The runtime component may also be configured to submit a request for a content license for the protected content to a second entity, such as an access coordinator or some other entity. The submitted request may include the received delegation token. The runtime component may be configured to receive the content license from the second entity. The runtime component may also be configured to provide access to the protected content in accordance with the received content license.
Owner:ADOBE INC
Method for processing rights object in digital rights management system and method and system for processing rights object using the same
InactiveUS20060031164A1User identity/authority verificationUnauthorized memory use protectionDigital rights management systemComputer science
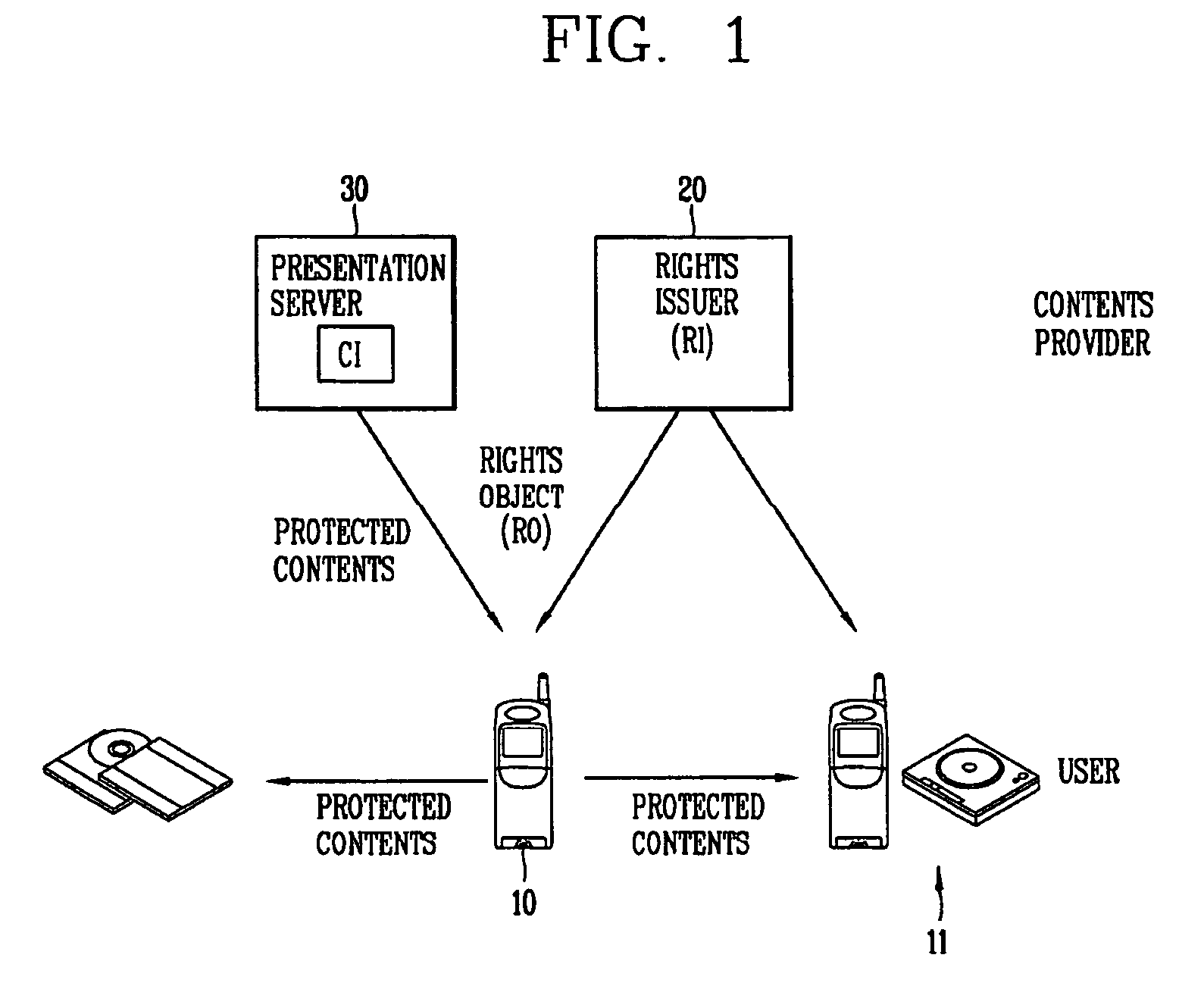
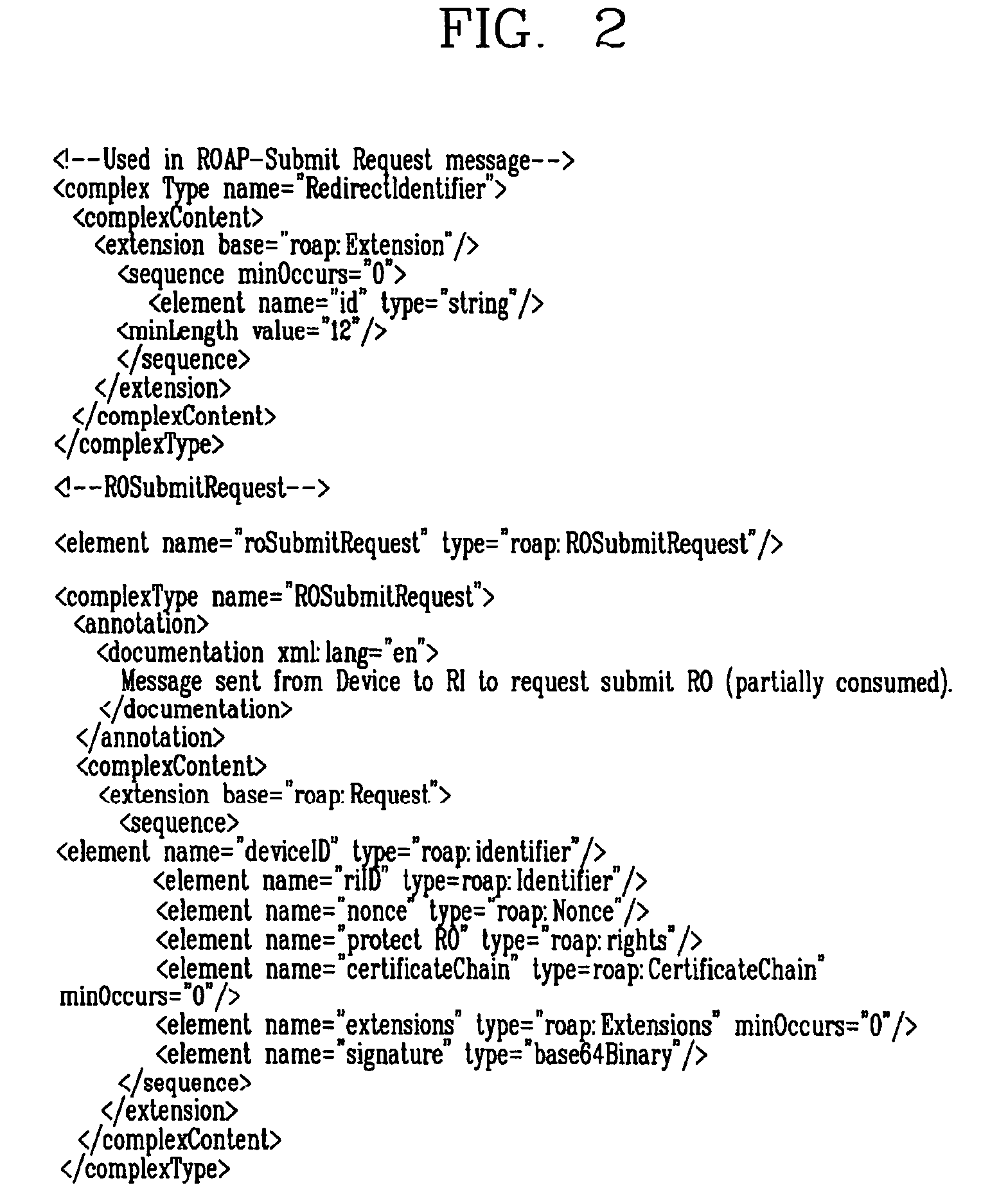
A message, method and system for processing rights object (RO) in a DRM system are disclosed. A message for requesting submission or return of an unused / partially consumed rights object (RO) is newly defined. When an authenticated device generates such a request message and transmits it to a right issuer (RI), the RI checks whether there exists an ID of a receiving device in the request message. If an ID of a receiving device exists in the request message, the RI performs a procedure for submitting the RO to the ID of the receiving device. If, however, the ID of the receiving device does not exist, the RI performs a procedure of returning of the RO or issuing of a different RO. Accordingly, the unused RO or partially consumed RO can be returned or submitted to a different device by using the request message.
Owner:LG ELECTRONICS INC
System and method for securing digital content
ActiveUS7496540B2Intuitive experienceSimplify the purchasing processComplete banking machinesFinanceDigital rights management systemDigital content
A system is disclosed for a digital rights management system which enforces license rights by incorporating a decryption key in a license rights package that further includes an account number associated with a primary consumer. The digital rights management system also includes a mechanism for renewing / updating the license by charging the account number associated with a primary consumer. This way, the consumer may transfer the license rights package along with the digital content to any personal devices he likes but he is discouraged from freely disseminating the license package as uses by other consumers will be debited against his package or, if renewed / extended, charged against his account.
Owner:NETCRACKER TECH SOLUTIONS
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com