Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
70 results about "Tangible object" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Tangible objects are things, such as a machine or a building, on which you can perform a physical service task. A tangible service object can also be an inventory item that you create in the Released product details form. Depending on the inventory dimension group that you attach to the item, you can create a service object...
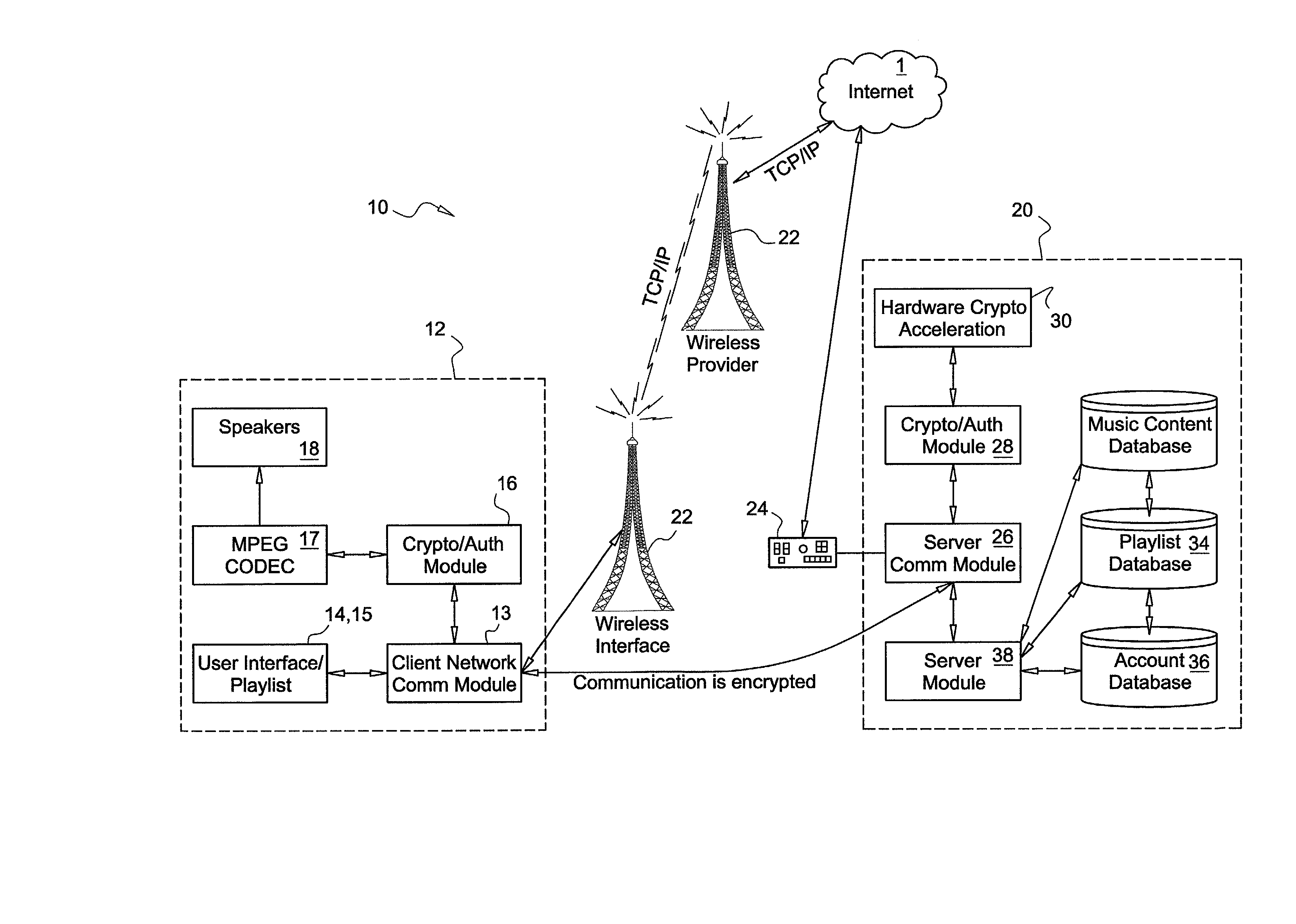
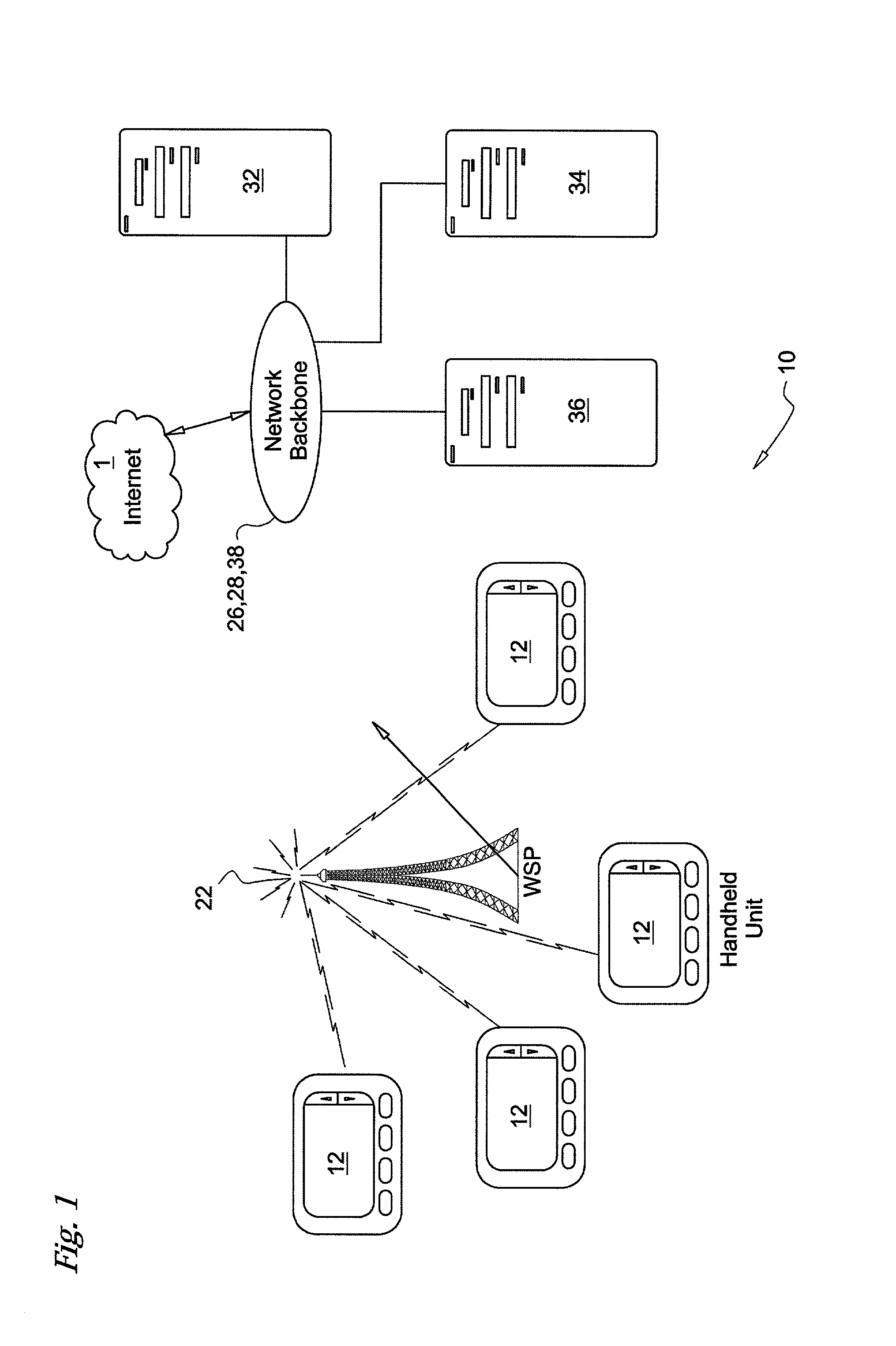
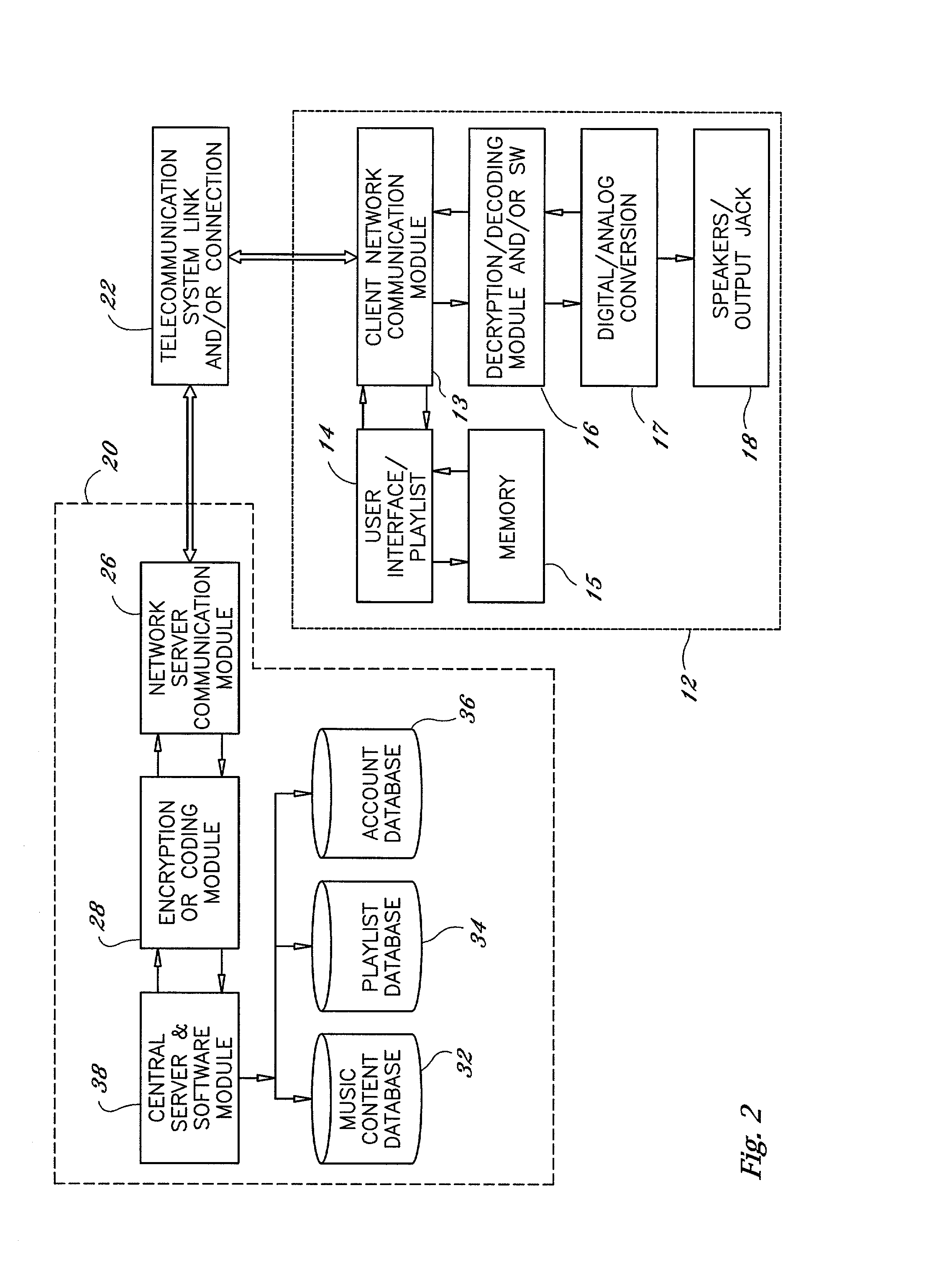
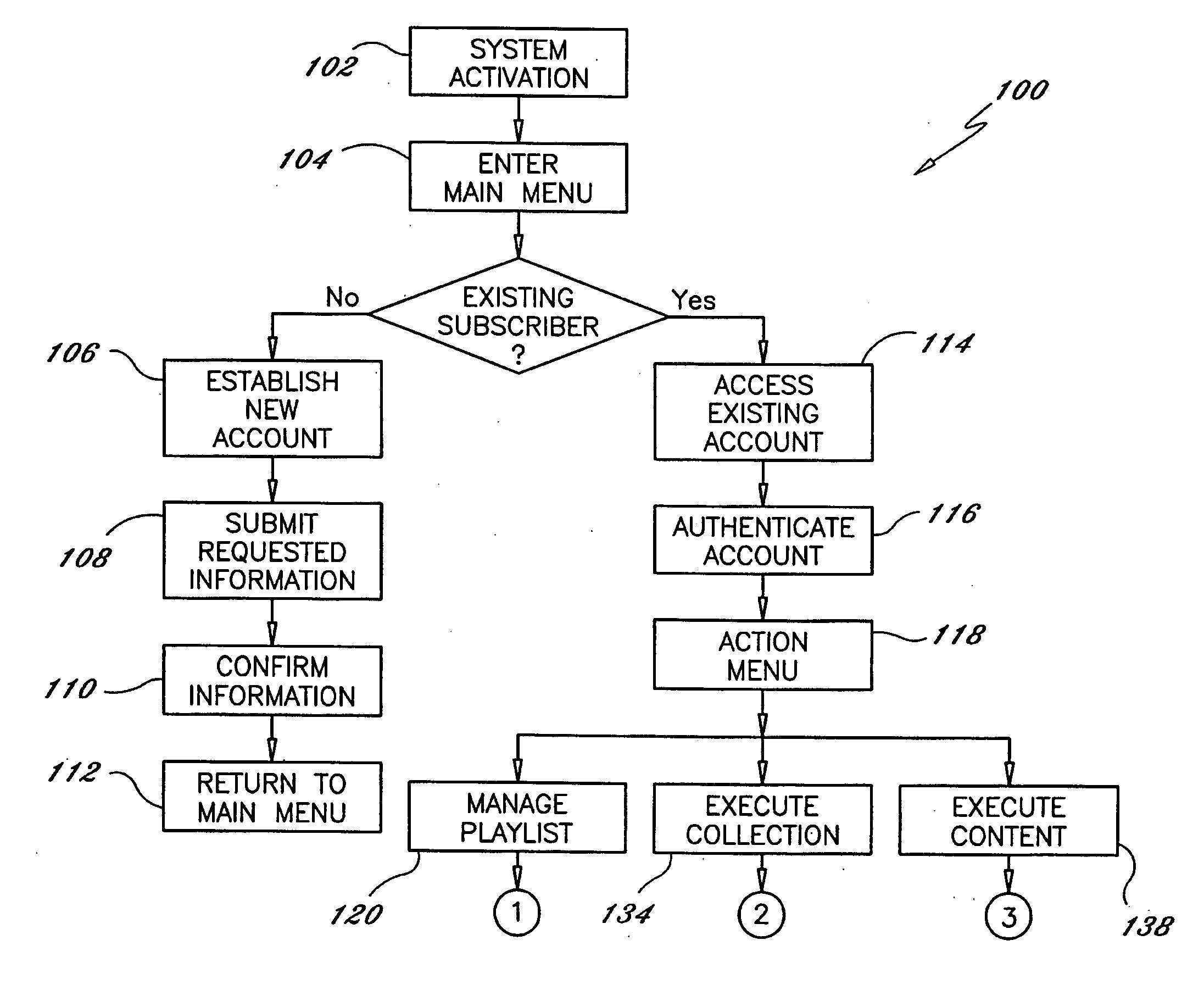
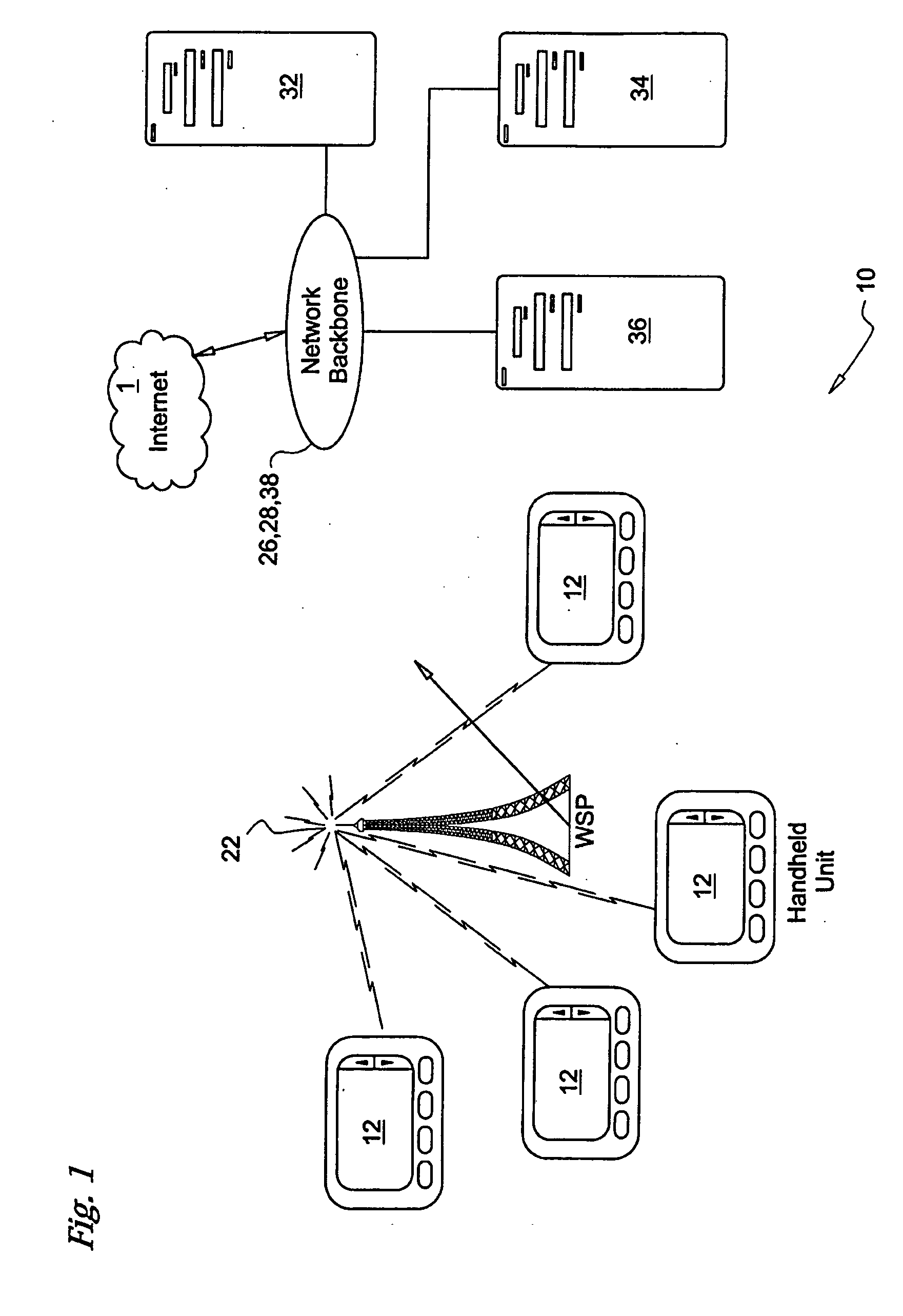
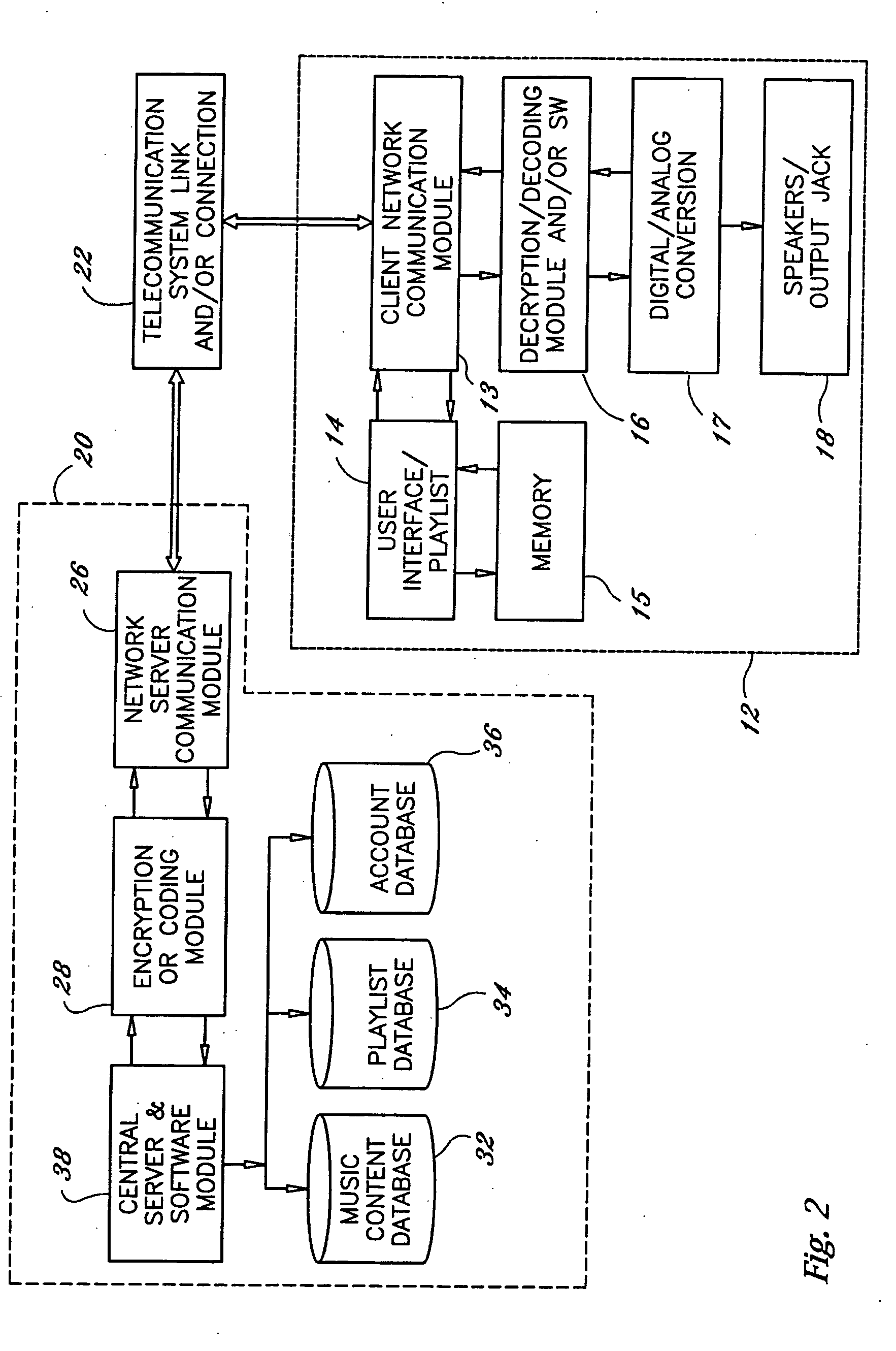
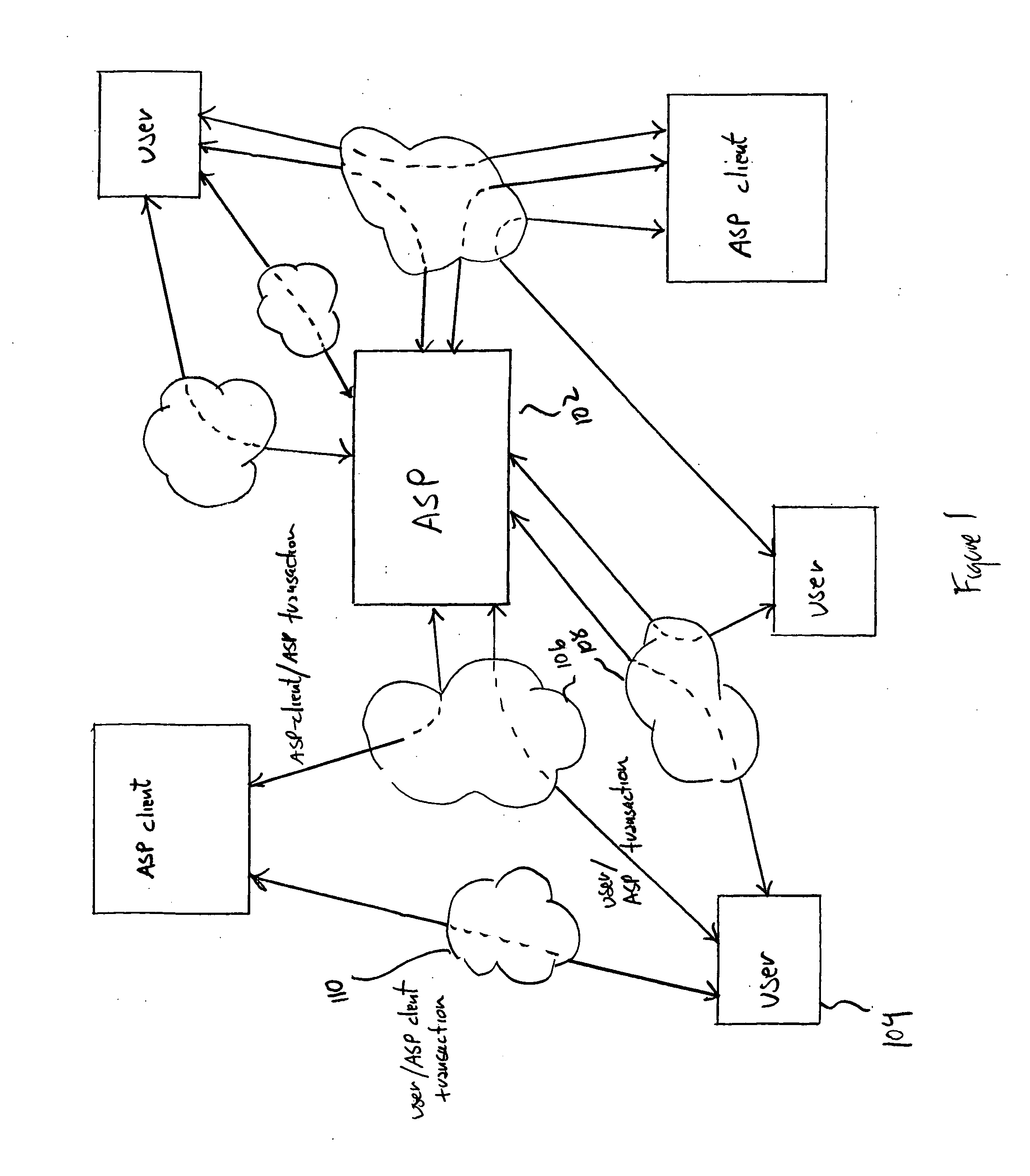
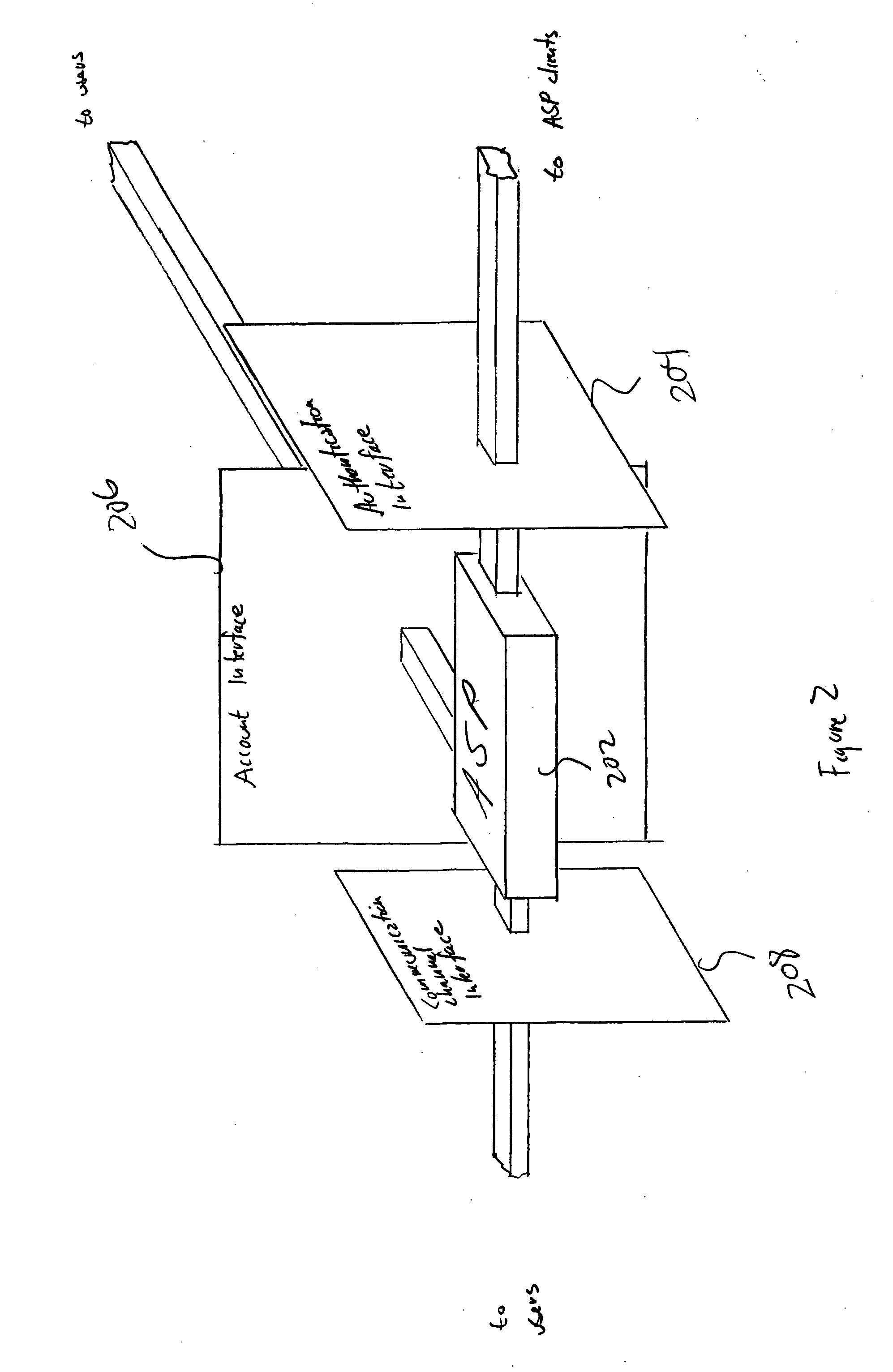
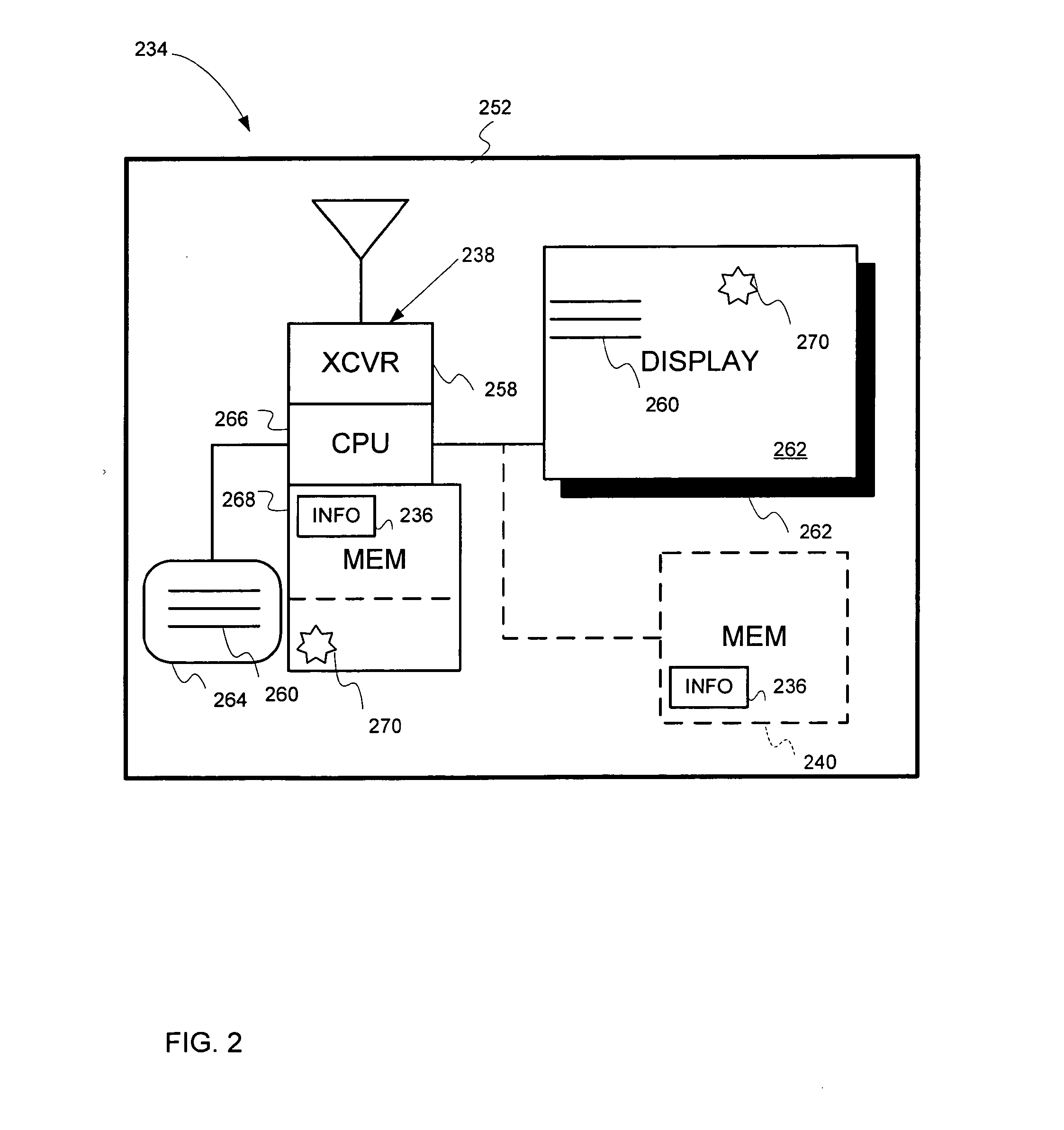
System, device and method for remotely providing, accessing and using personal entertainment media
InactiveUS20020091848A1Analogue secracy/subscription systemsComputer security arrangementsTangible objectComputer terminal
Systems and methods for permitting consumers to securely purchase, access, download and / or stream entertainment content such as musical and audio visual works, including a remote terminal or terminals. Consumers subscribe to the system and obtain a terminal or terminals. The terminals permit the subscribers to access the system to obtain content, either by downloading same to the terminal or by directly perceiving the content while streaming the content to the terminal. The invention prevents unauthorized copying, distribution and / or performance of protected works while at the same time eliminating the need for consumers to possess the tangible objects, e.g. CDS and DVDs, upon which detectable works normally reside. The software associated with the system regulates the transmission of content from the database(s) upon which it is stored, through a central server associated with the system, to the subscriber terminals for storage or immediate, i.e., "streaming", playback.
Owner:AGRESTA ROBERT +2
System, device and method for remotely providing, accessing and using personal entertainment media
InactiveUS20060031551A1Easy accessAnalogue secracy/subscription systemsMultiple digital computer combinationsTangible objectMediaFLO
Systems and methods for permitting consumers to securely purchase, access, download and / or stream entertainment content such as musical and audio visual works, including a remote terminal or terminals. Consumers subscribe to the system and obtain a terminal or terminals. The terminals permit the subscribers to access the system to obtain content, either by downloading same to the terminal or by directly perceiving the content while streaming the content to the terminal. The invention prevents unauthorized copying, distribution and / or performance of protected works while at the same time eliminating the need for consumers to possess the tangible objects, e.g. CDS and DVDs, upon which detectable works normally reside. The software associated with the system regulates the transmission of content from the database(s) upon which it is stored, through a central server associated with the system, to the subscriber terminals for storage or immediate, i.e., “streaming”, playback.
Owner:AGRESTA ROBERT +2
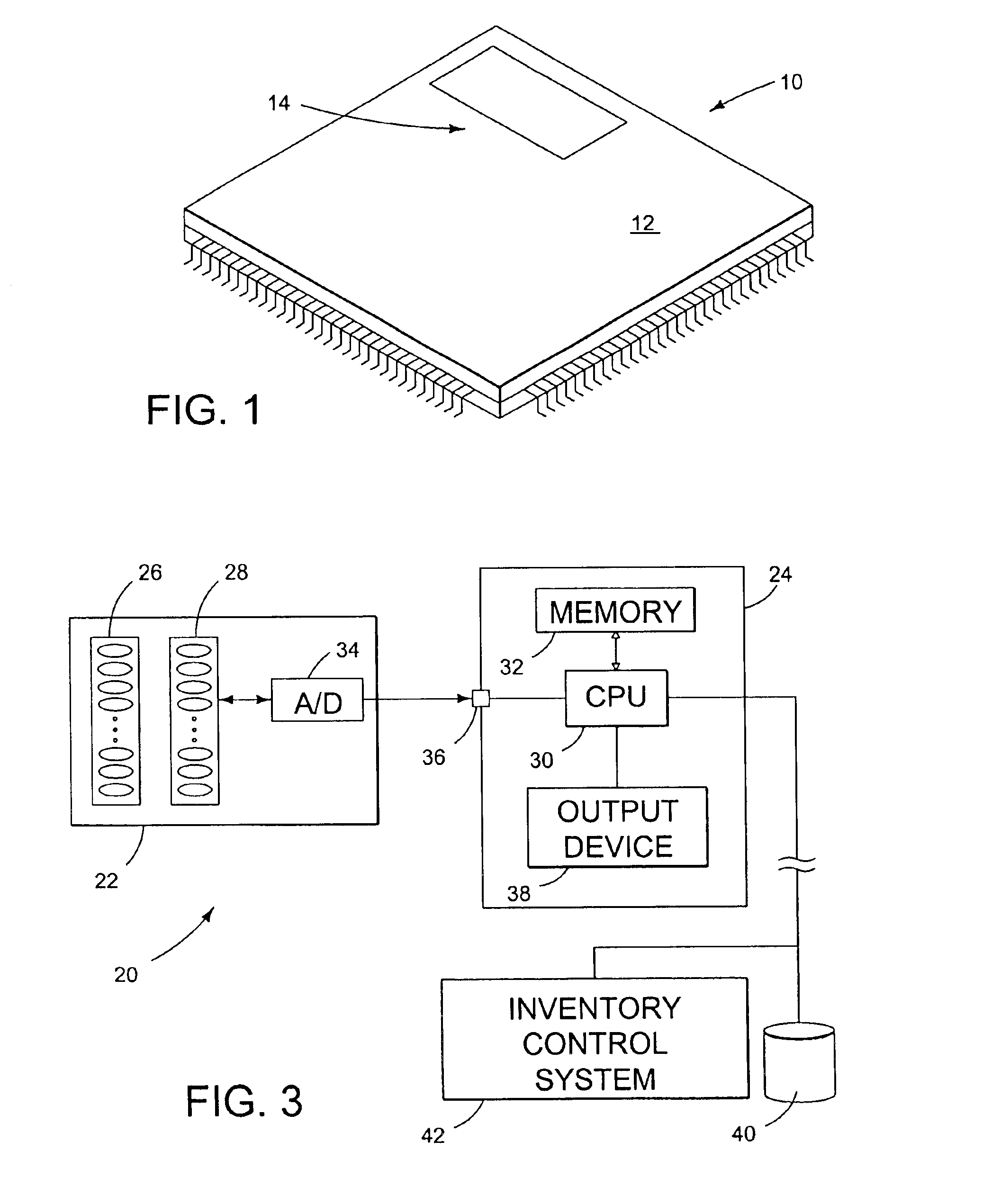
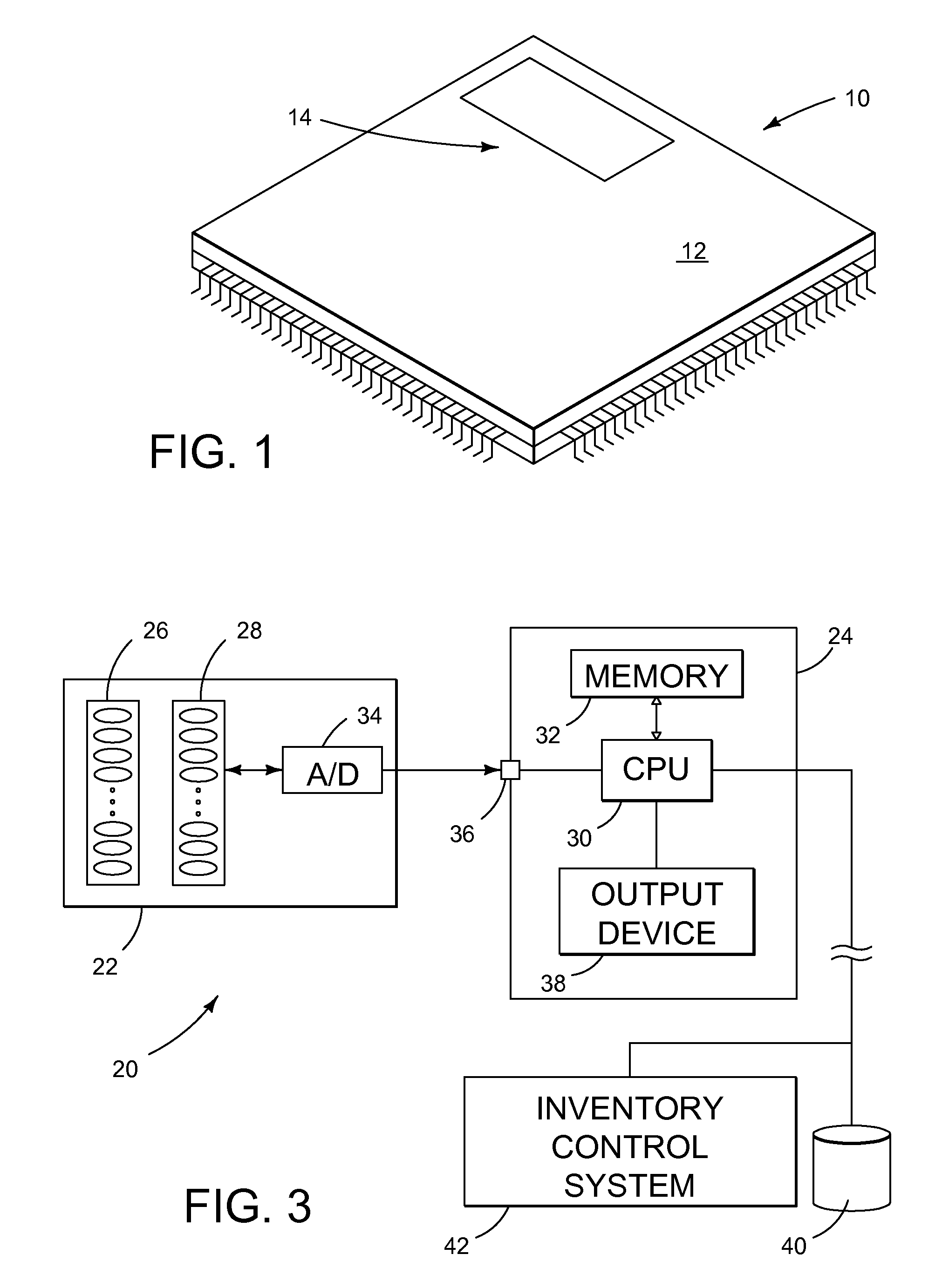
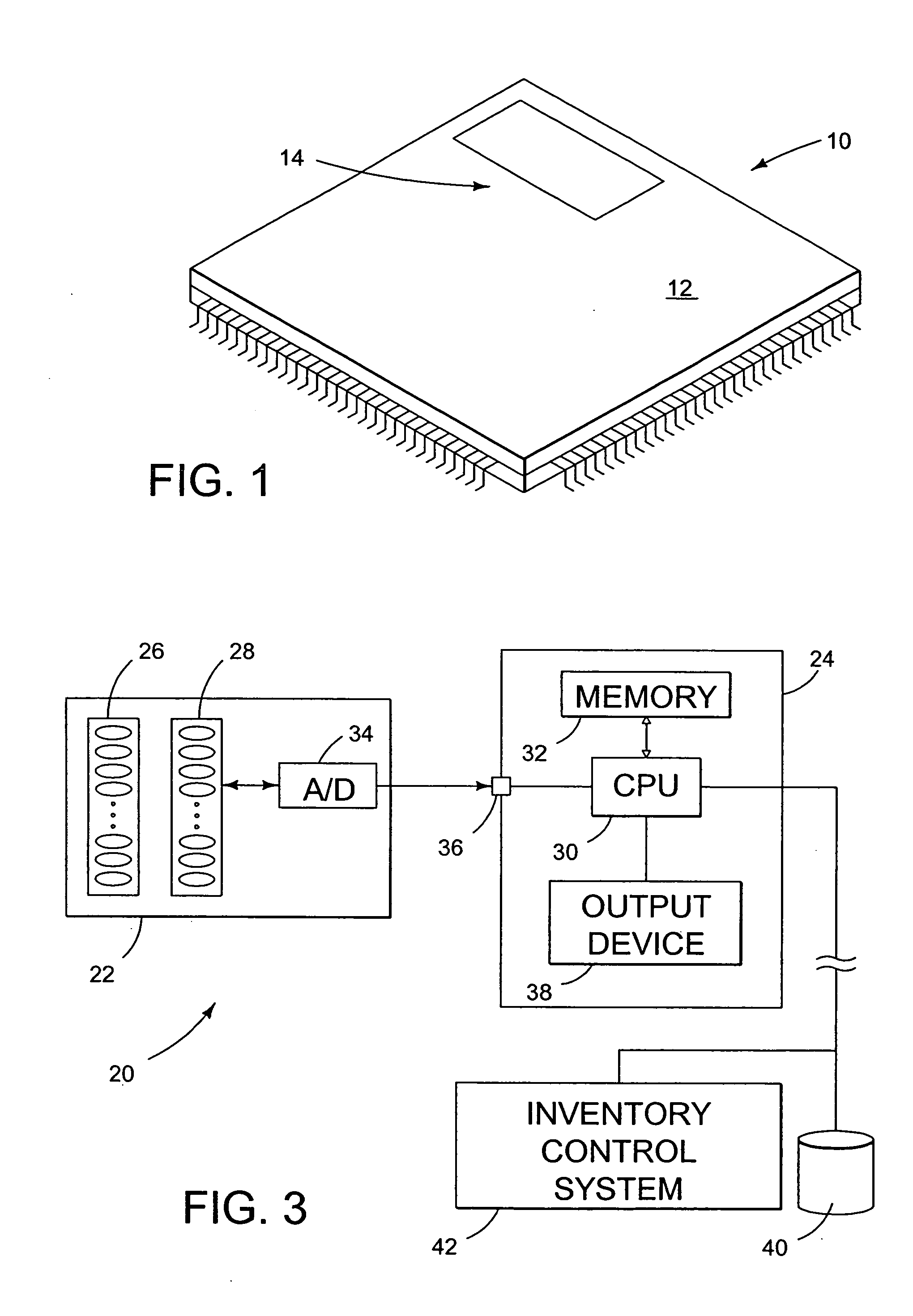
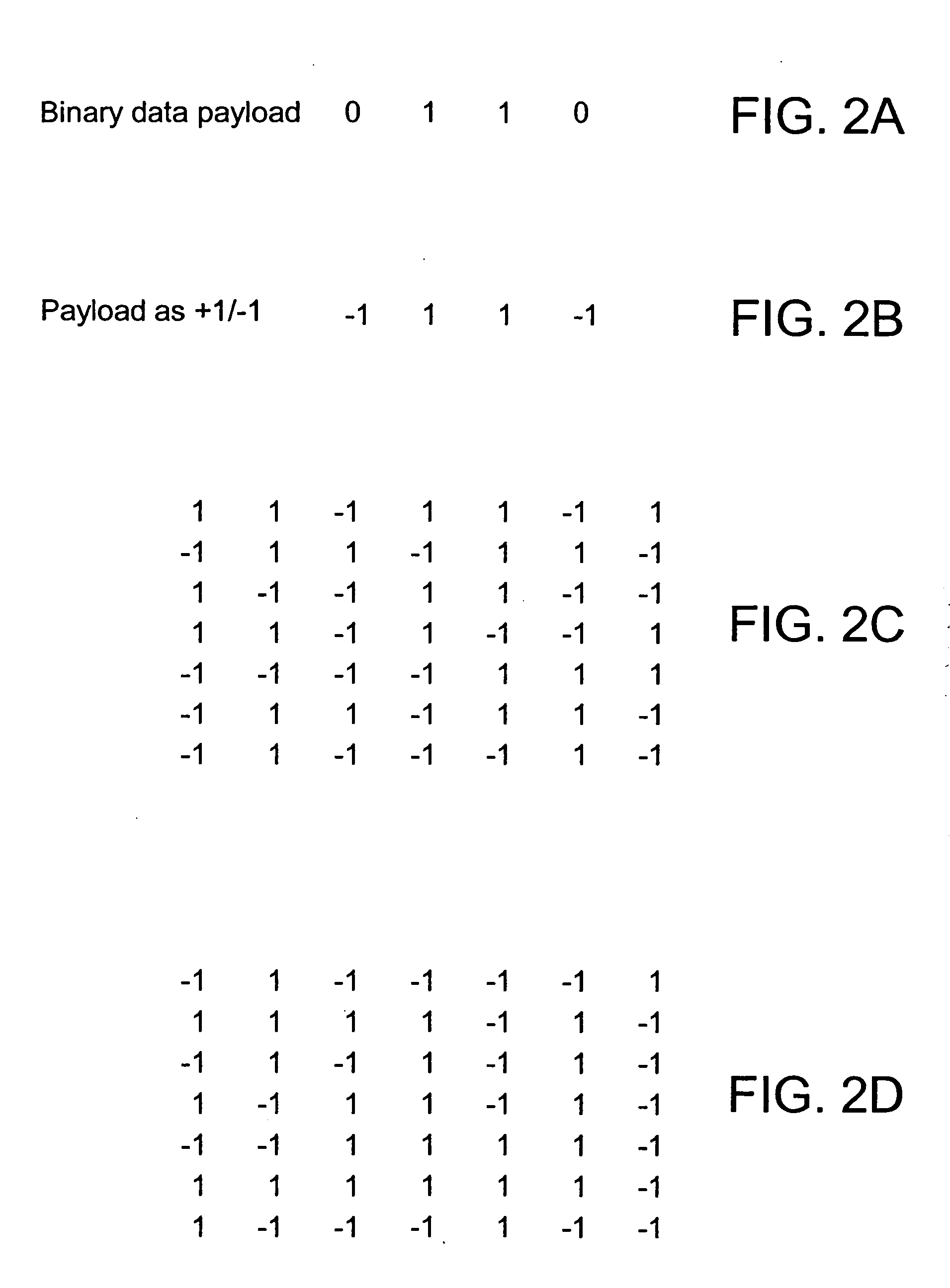
Methods and tangible objects employing textured machine readable data
InactiveUS6882738B2Overcomes drawbackAddressing slow performanceTelevision system detailsSemiconductor/solid-state device detailsCompact discTangible object
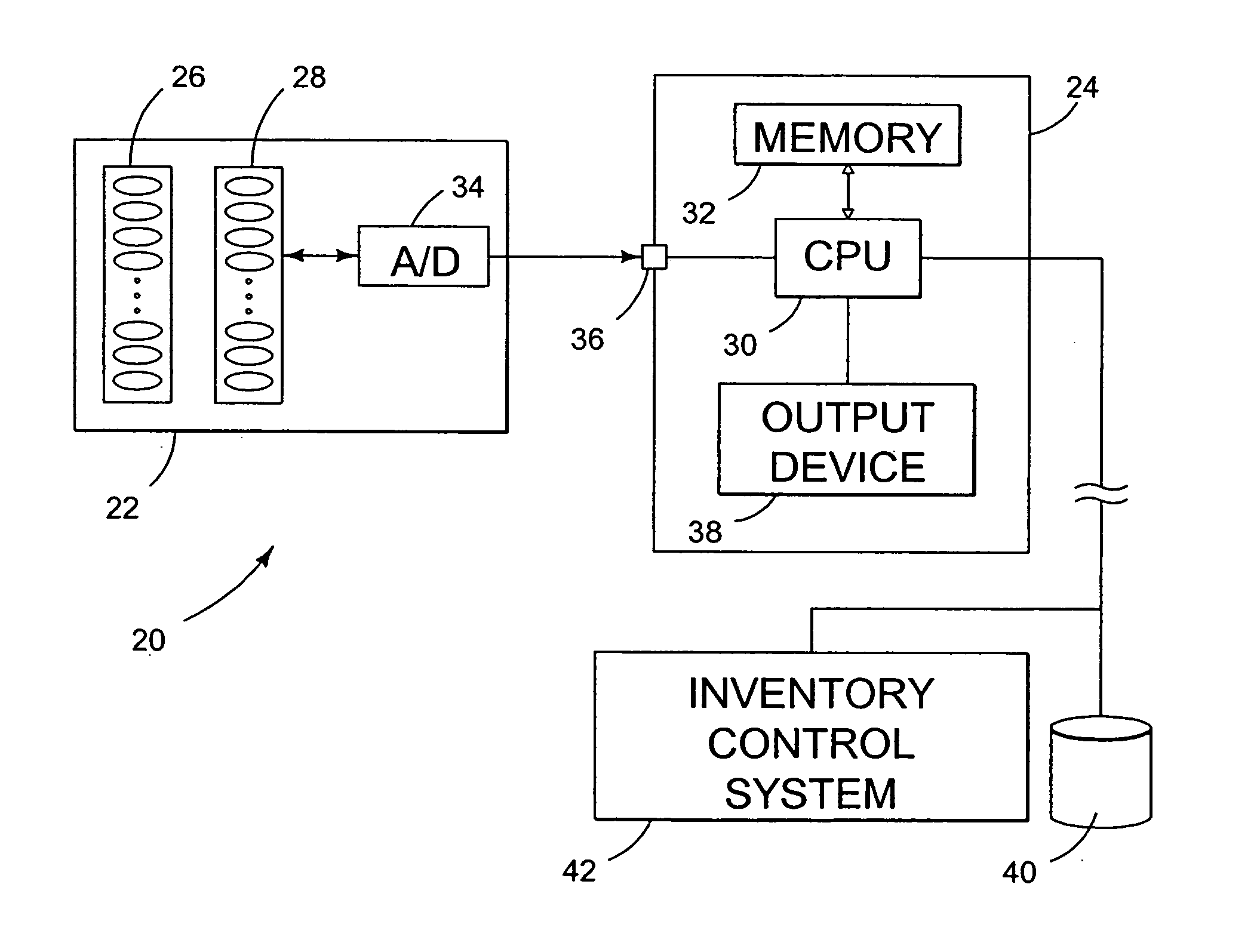
A tangible object (such as a microprocessor, wristwatch, pharmaceutical, compact disc, vehicle part, etc) is surface-textured to encode a plural-bit code thereon. In one arrangement, this encoding conveys date information. In use, the object can be imaged by a scanner apparatus, and the resulting scan data analyzed to discern the plural-bit code. The decoded date information can be used in a determination relating to the object. For example, at a port of entry, date information encoded on a Rolex wristwatch can be used to determine whether importation of the wristwatch should be permitted. The texture-encoded data can also convey other information, such as a vehicle identifier for an automotive part, a place of fabrication, a specification with which the part complies, etc.
Owner:DIGIMARC CORP
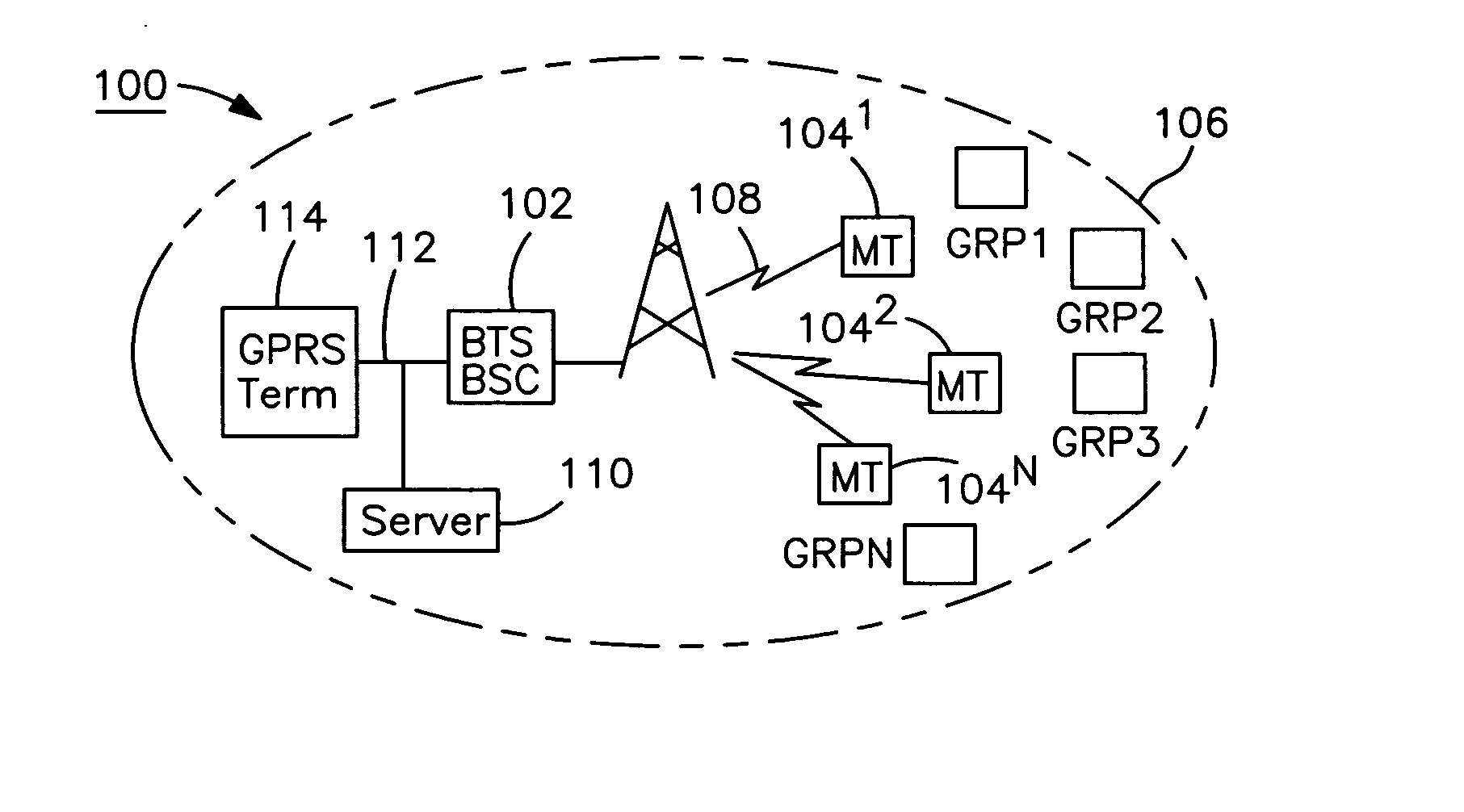
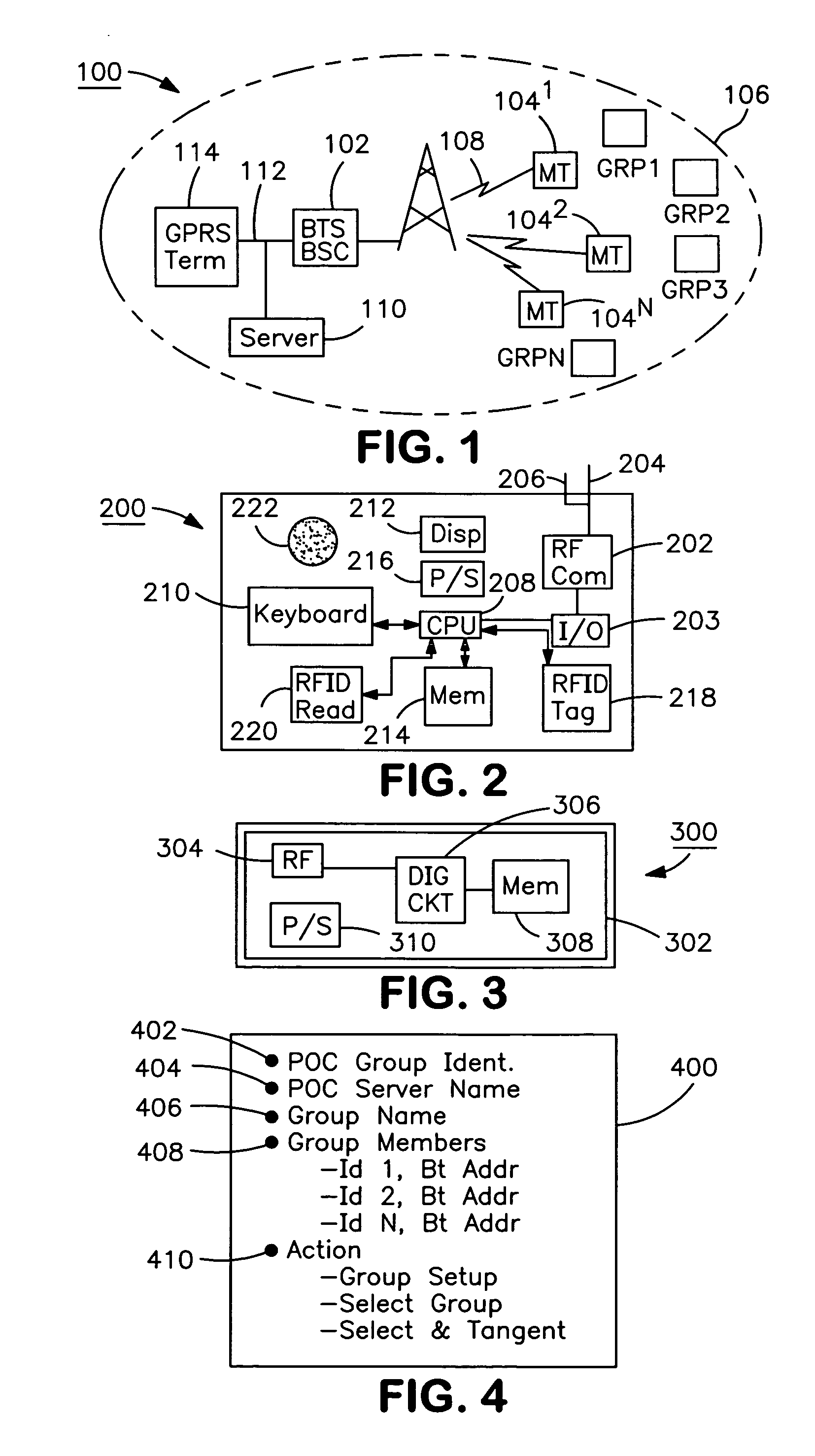
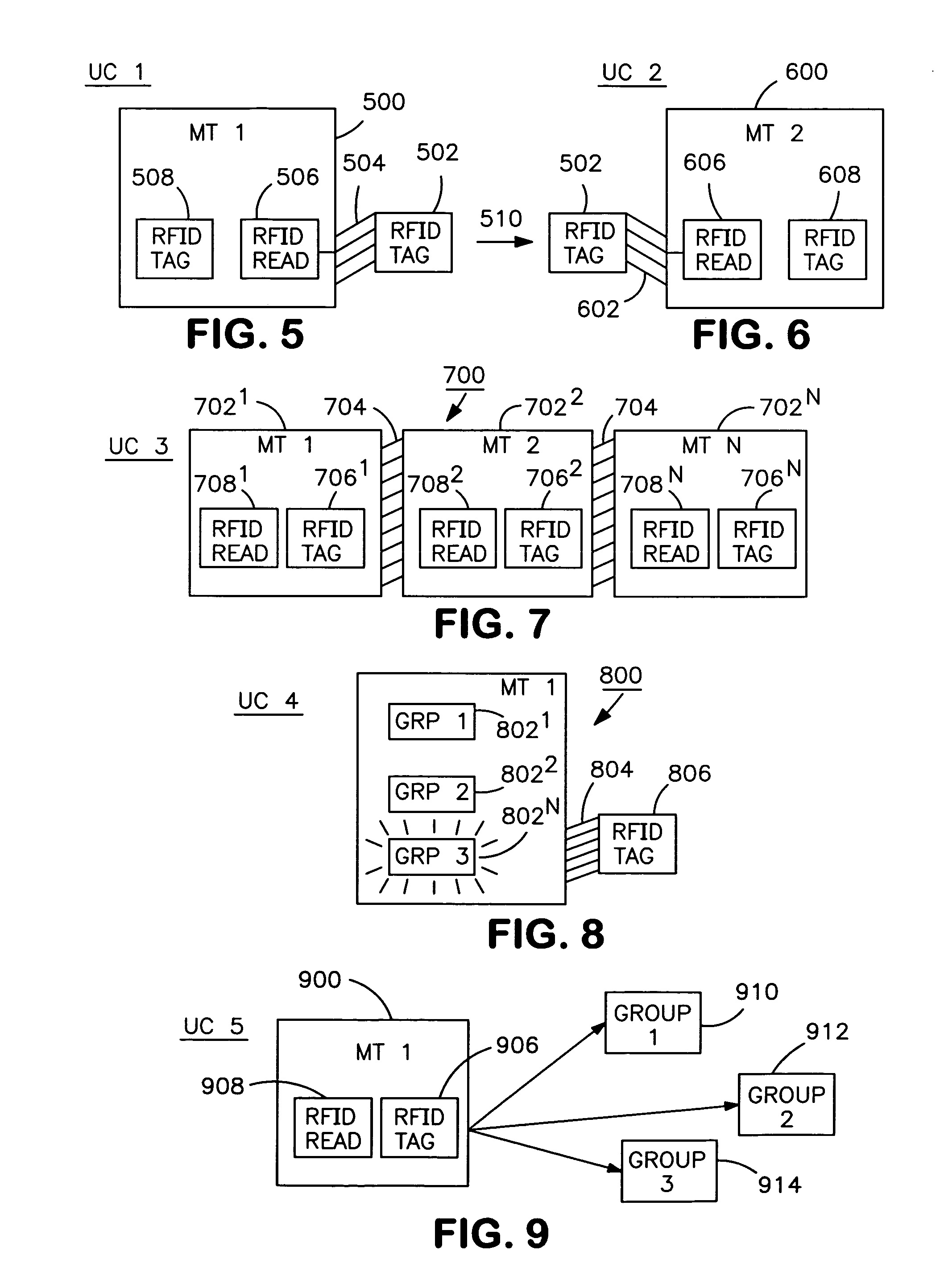
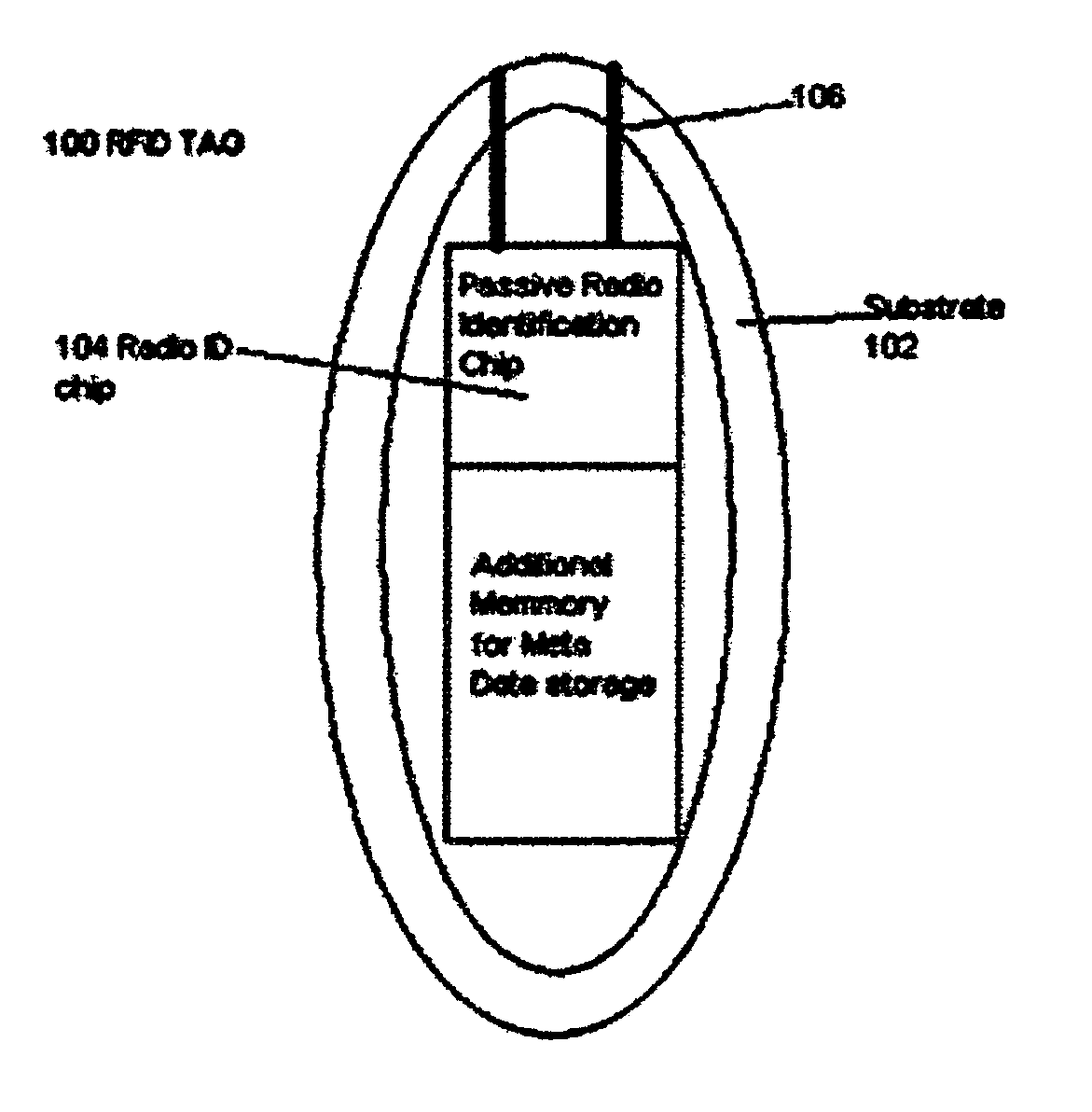
Push-to-talk over cellular group set-up and handling using near field communication (NFC)
InactiveUS20070263560A1Firmly connectedConnection managementData switching by path configurationSemi activeTangible object
A system, apparatus and method for creating and managing group services in a cellular network for easy, fast and reliable connection of a subscriber(s) to one or more group services. A first terminal device stores service descriptions records for a first group of services in a cellular network. The first terminal is equipped with a communication module including a first RFID / NFC interface. A tangible object, typically a passive or semi-active tag with a RFID / NFC tag / transponder stores service description records for a first group of services. The first terminal is capable of initiating a new group of services group in the cellular network by way of communicating with the tangible object by touching the first RFID / NFC interface. A second communication module is capable of joining to the group of services group by way of reading the information from the tangible object over the second RFID / NFC interface upon touching the tangible object.
Owner:NOKIA CORP
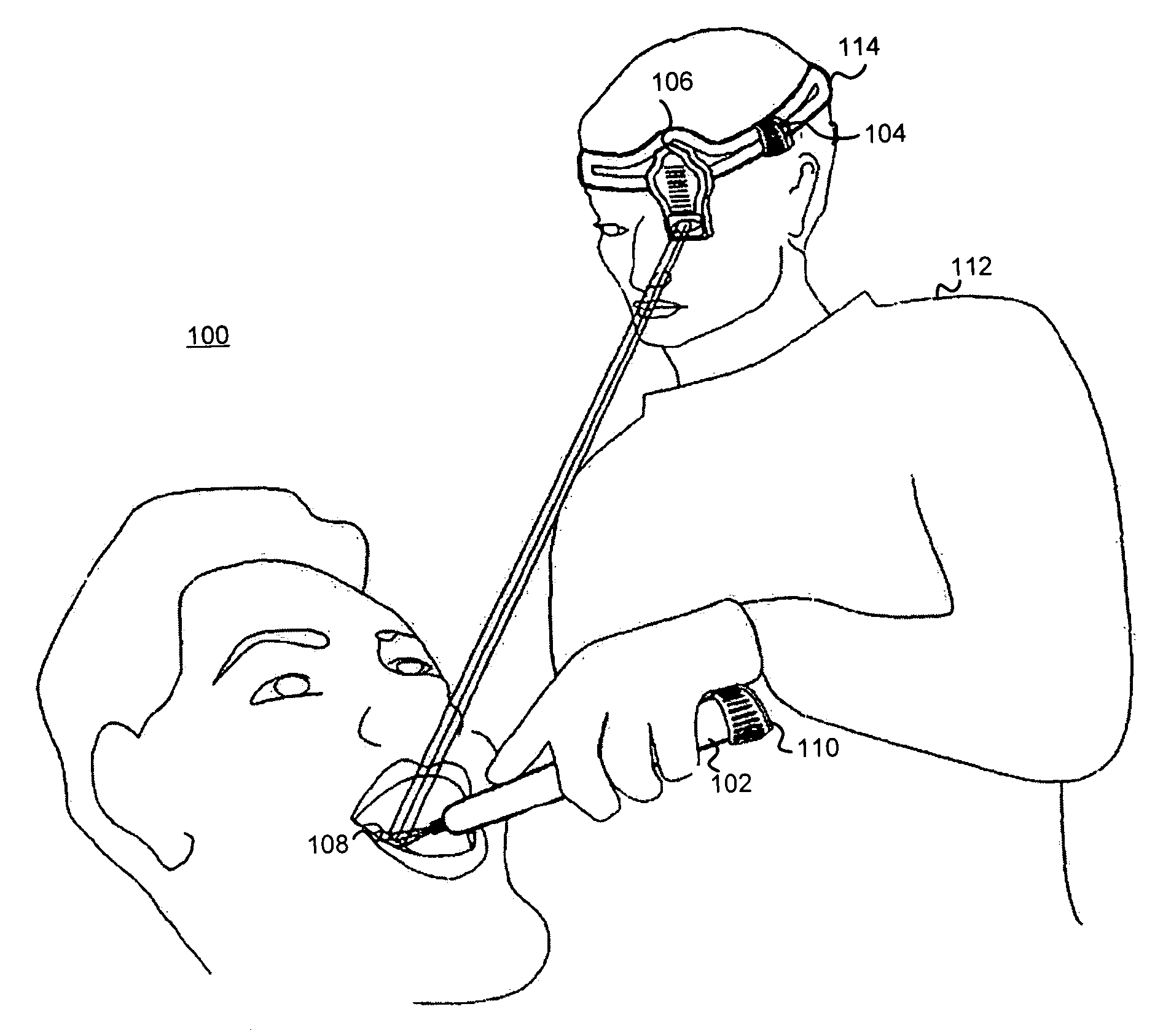
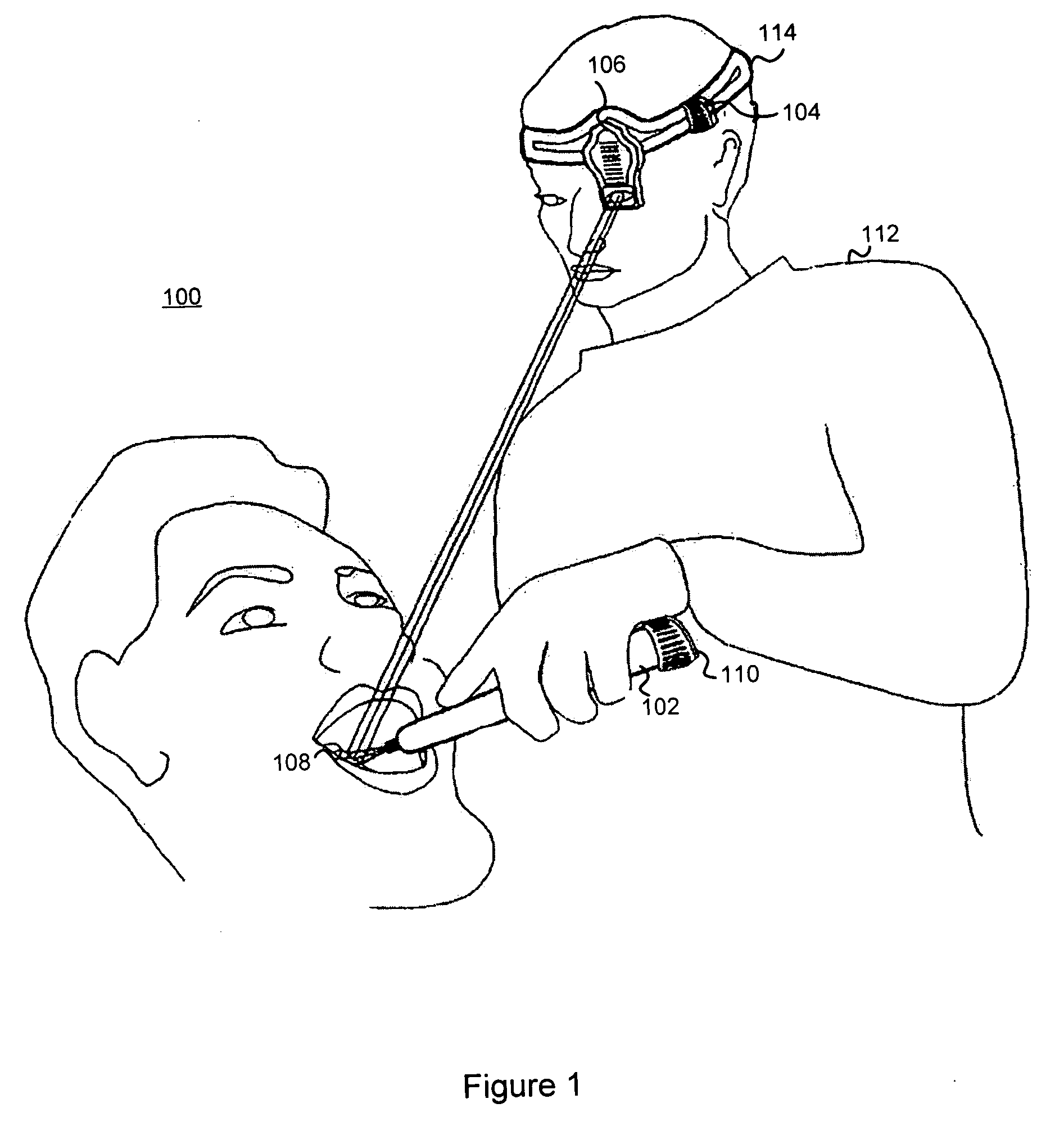
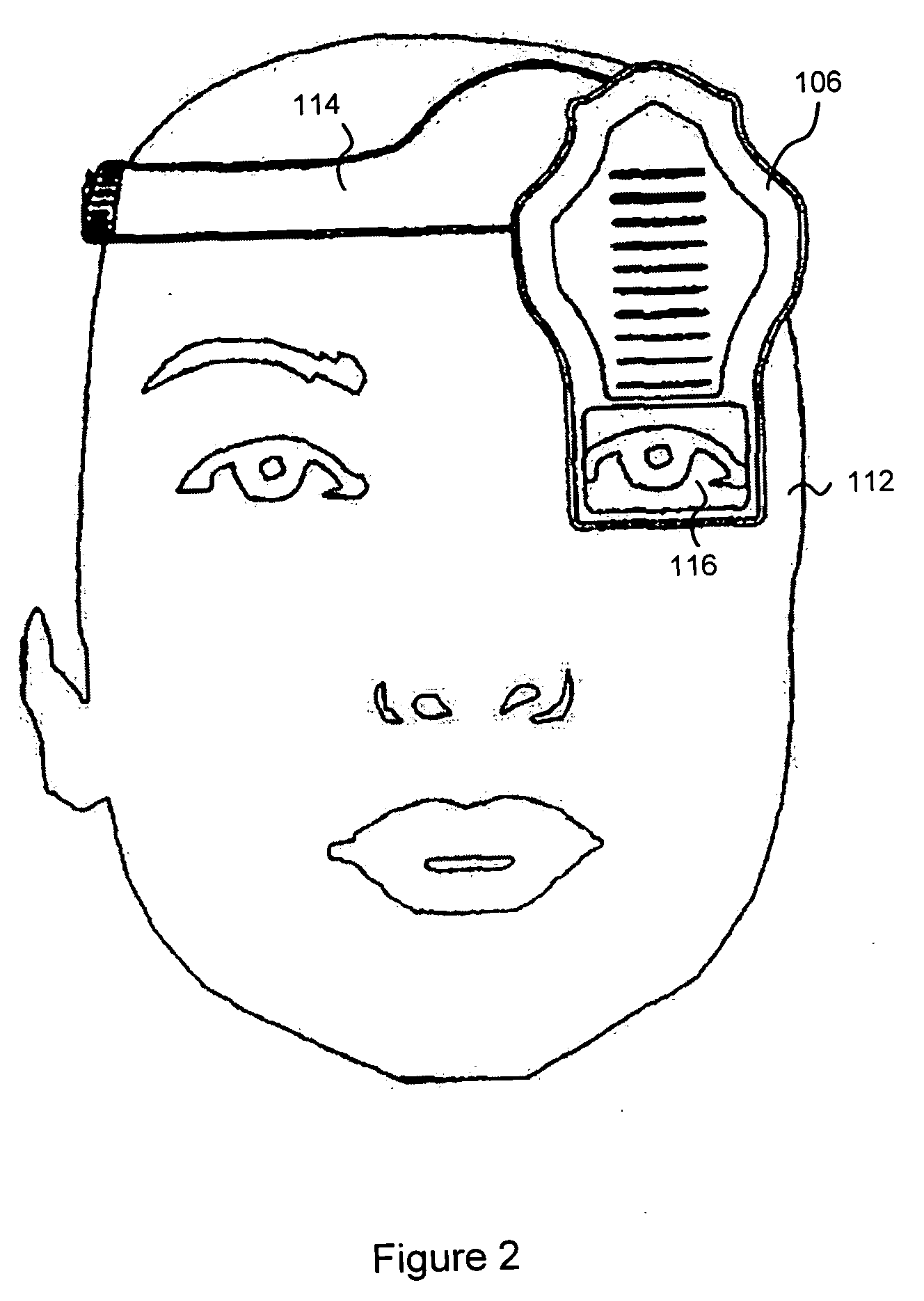
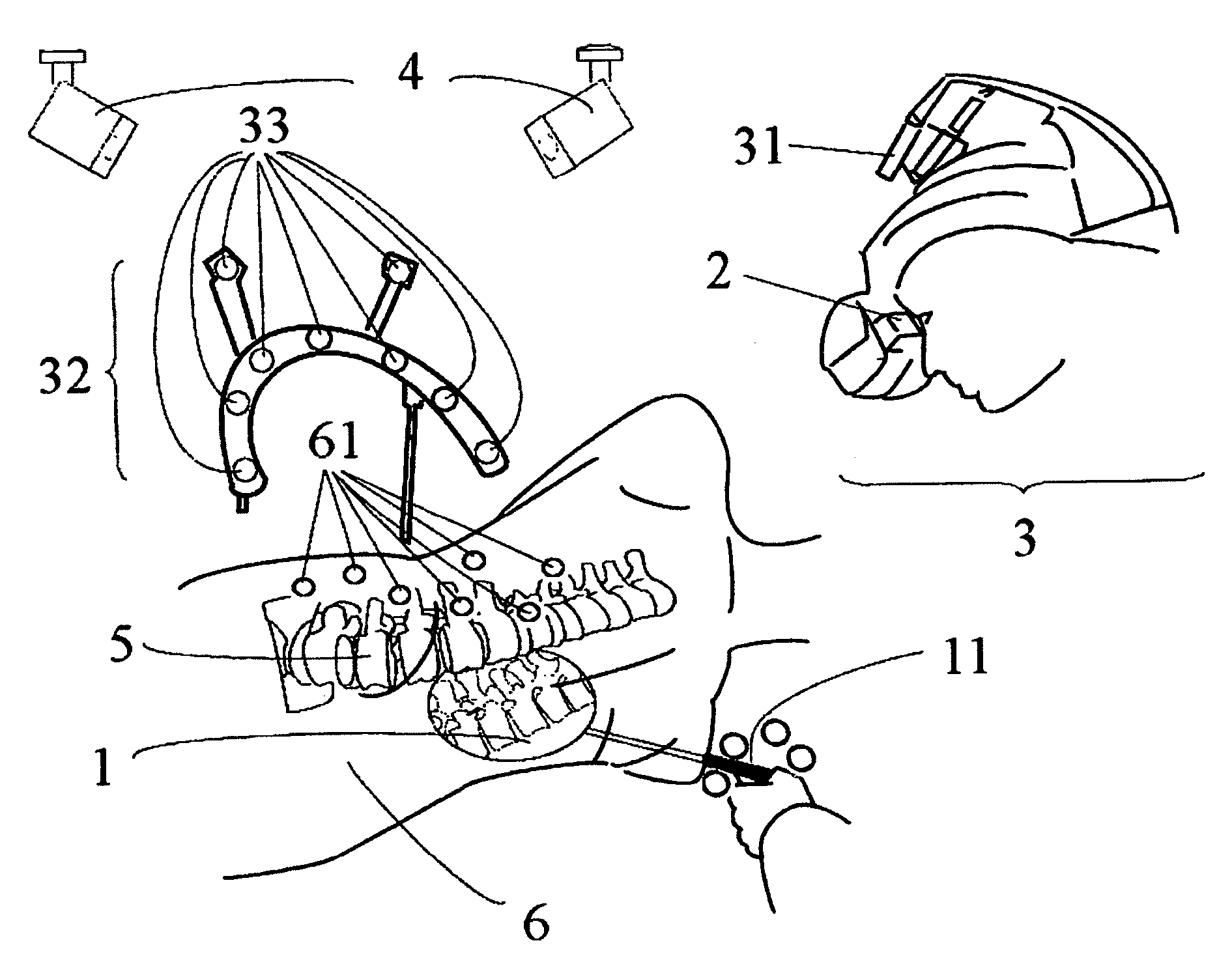
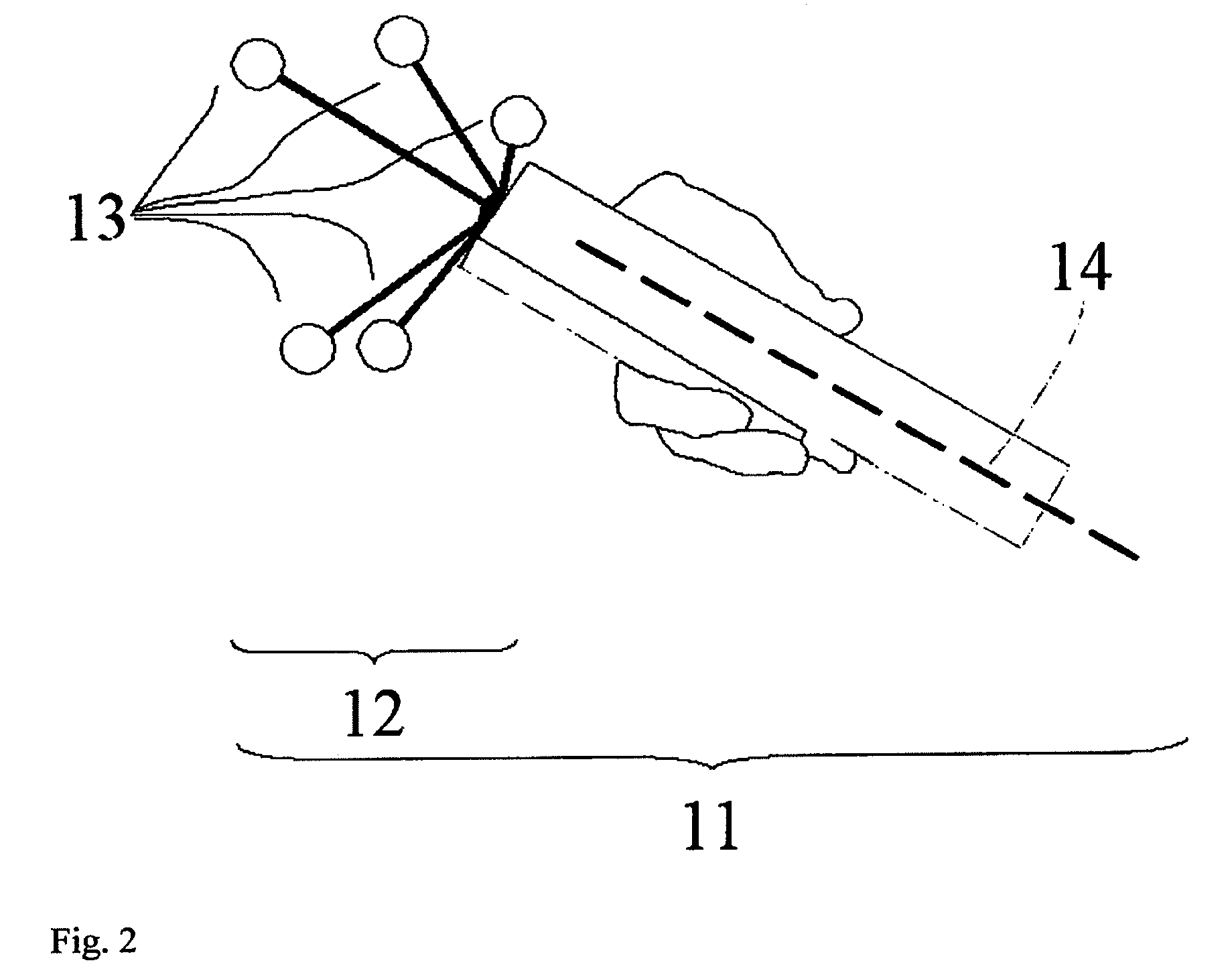
Intra-oral imaging system
InactiveUS20050020910A1Reduce and eliminate effectEndoscopesSomatoscopeTangible objectMulti dimensional
A digitized image of a tangible object is displayed in an operator's field of view of the object almost simultaneously as the digitized image is being captured. The image is projected onto a screen in an orientation, position and scale corresponding to an orientation and position of the object within the field of view of the operator so as to be perceived as an overlay to the object. The image may be a one-, two, three, or other multi-dimensional representation of the object and may be captured by an imaging system, such as an intra-oral imaging device.
Owner:D4D TECH LP
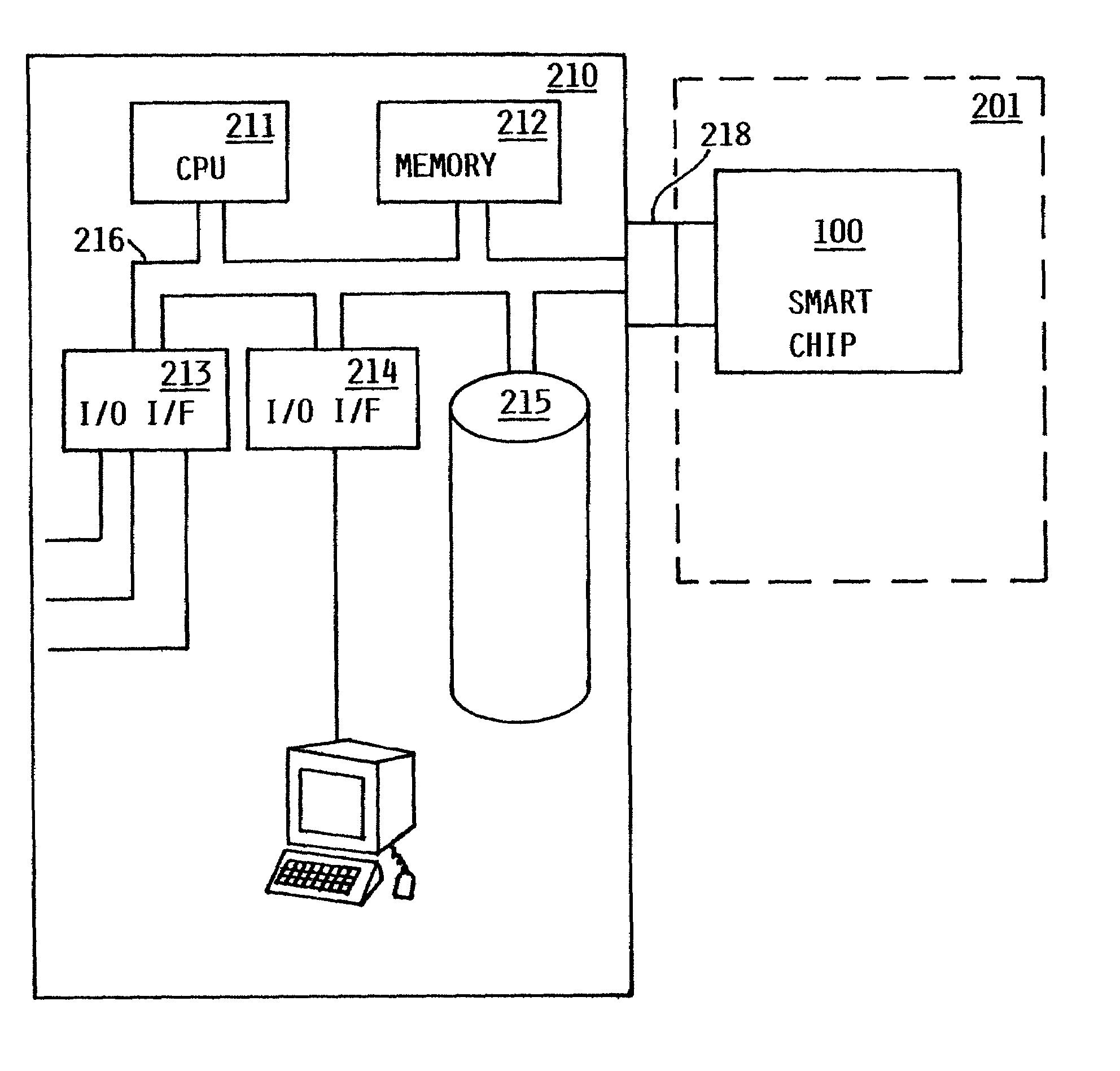
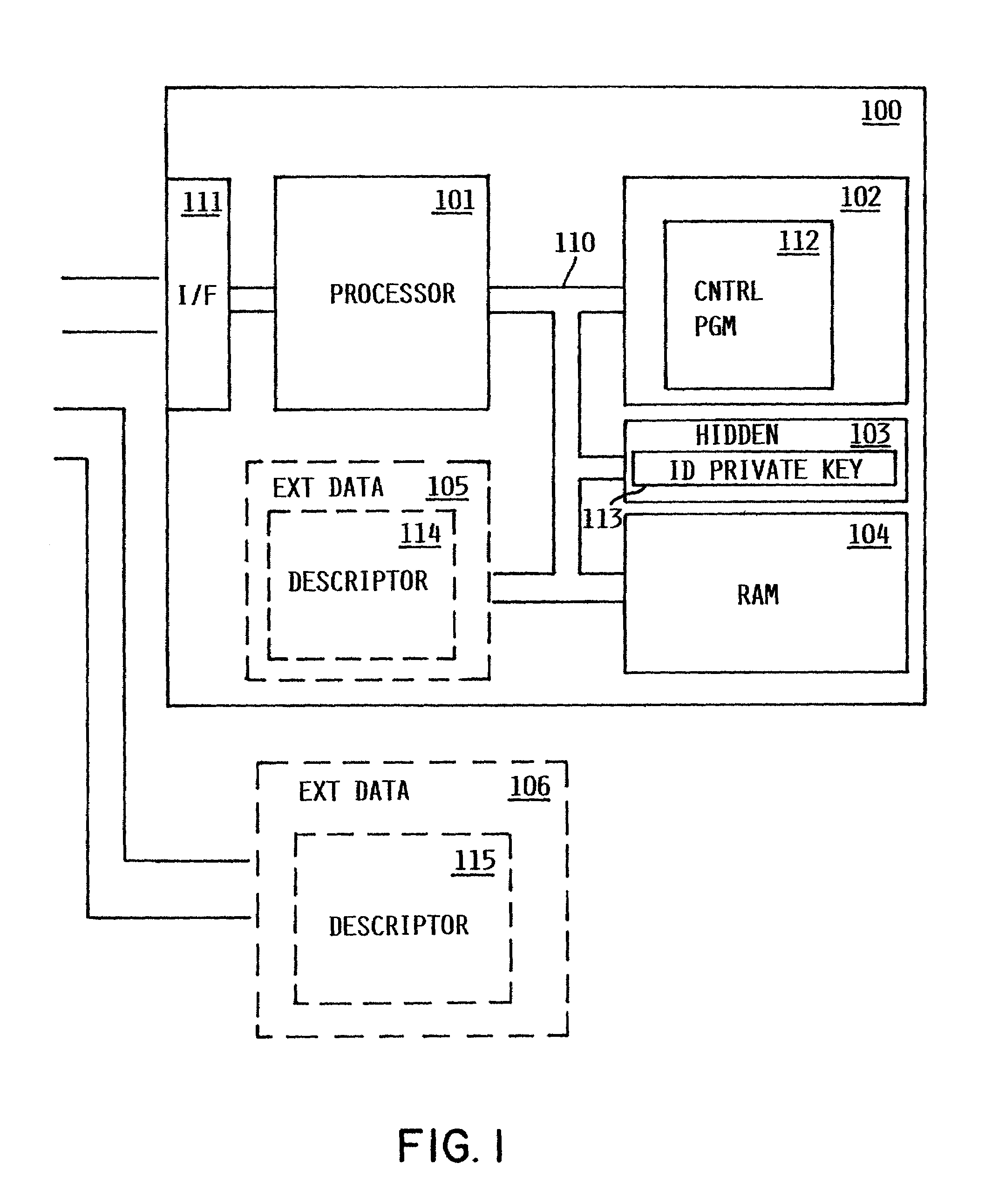
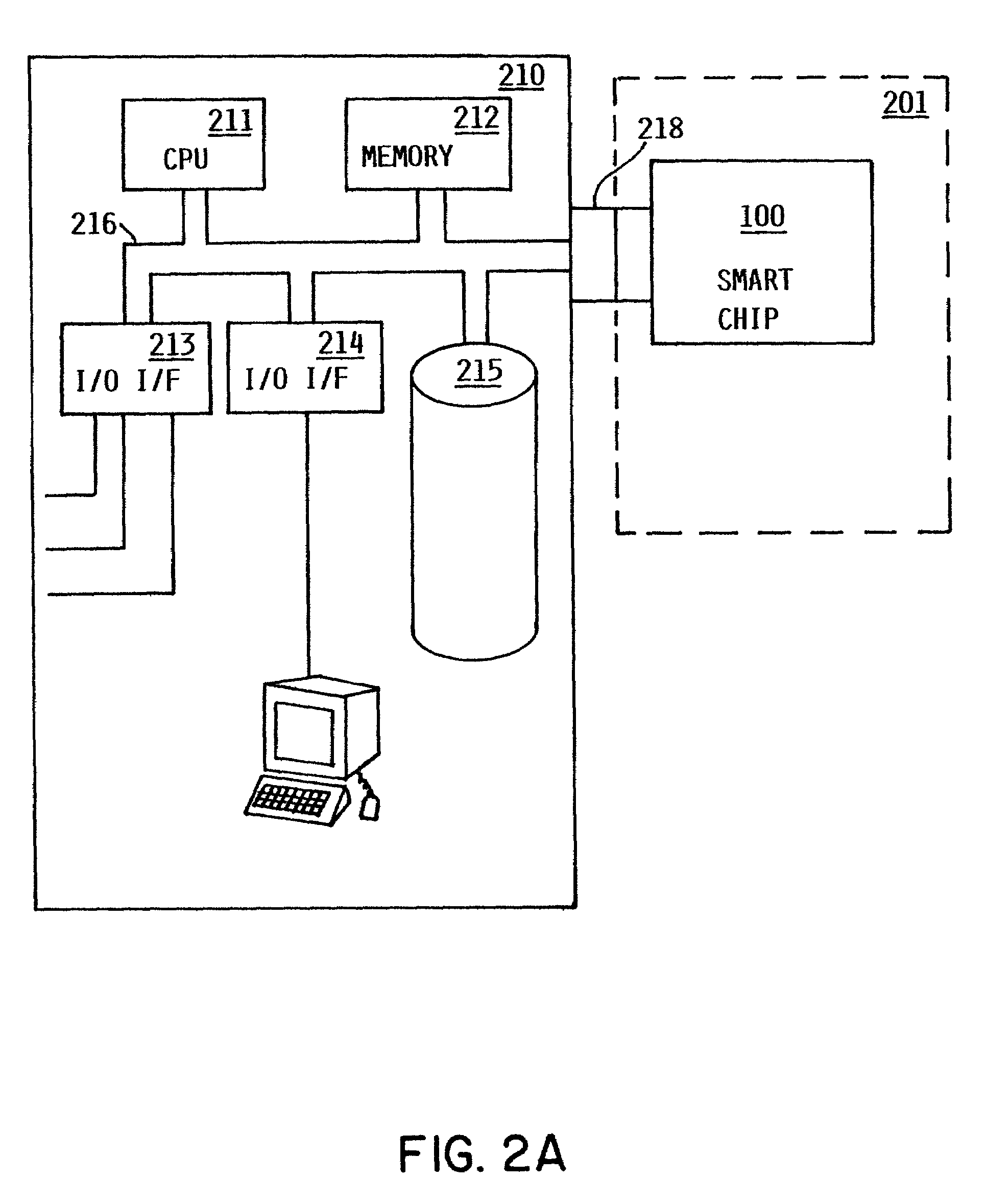
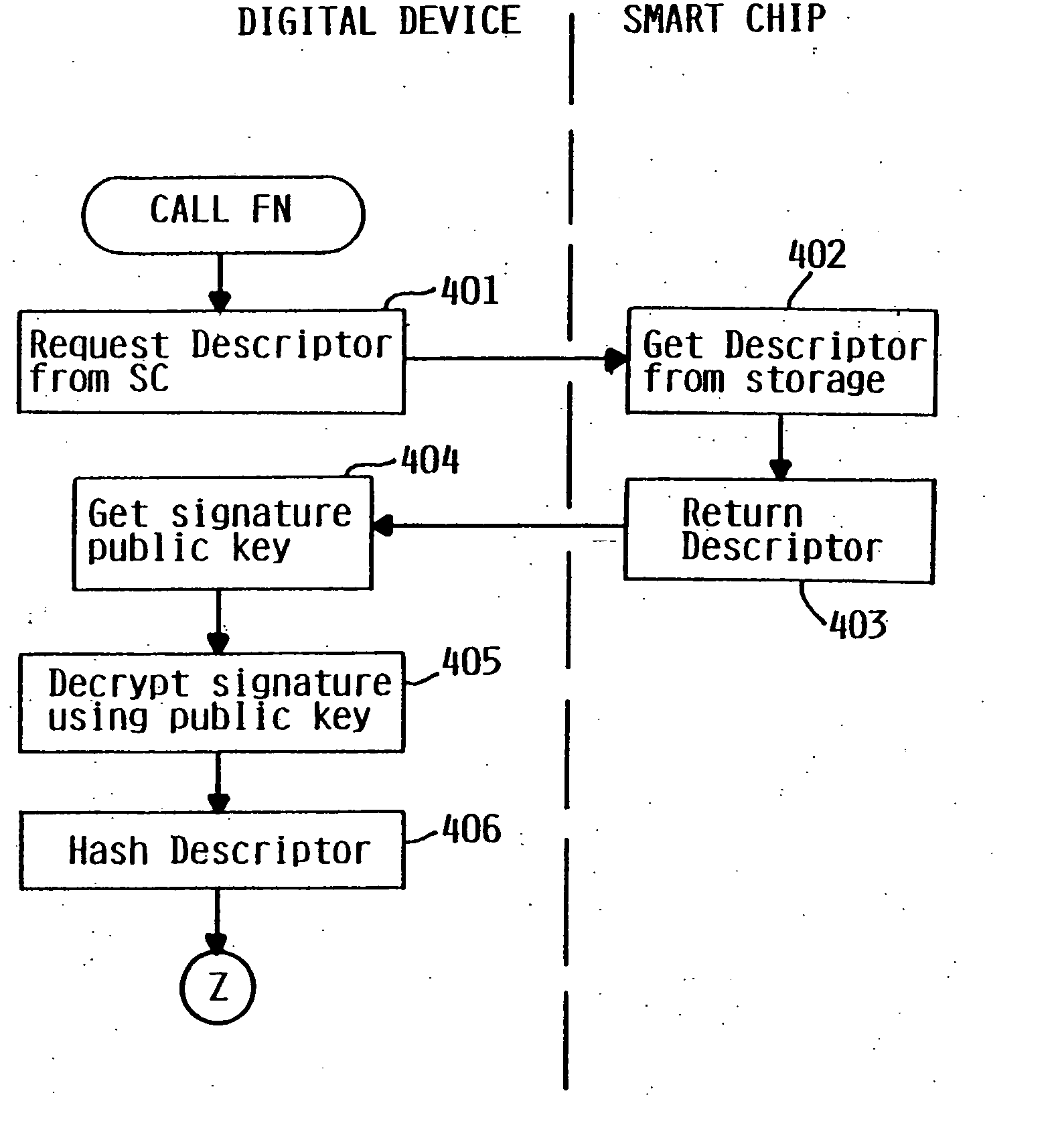
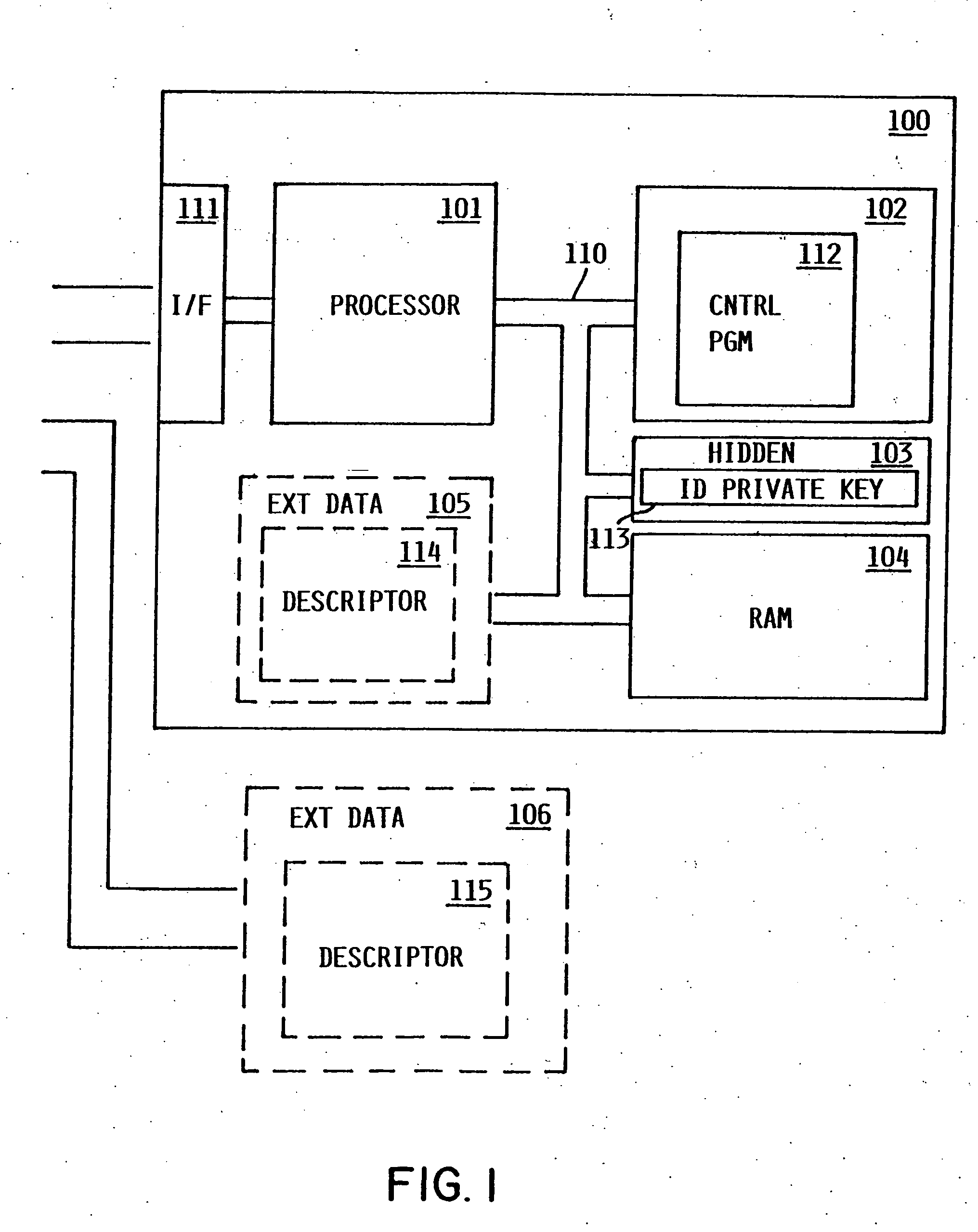
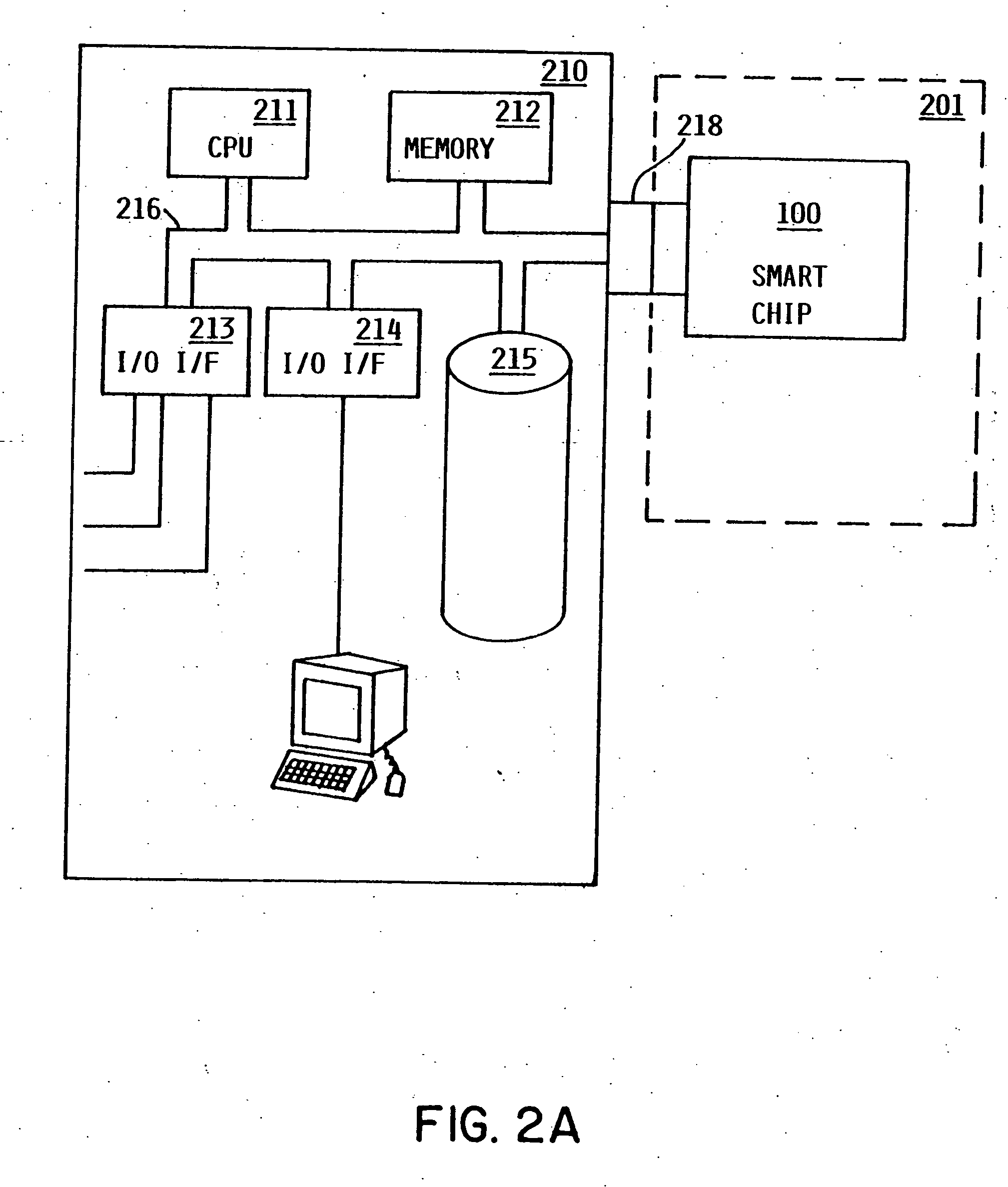
Method and apparatus for uniquely and authoritatively identifying tangible objects
InactiveUS7000115B2Alteration can be preventedEasy to readDigital data processing detailsUser identity/authority verificationDigital signatureTangible object
A smart chip protection system contains a unique public / private identity key pair and uses a separate public / private signature key pair. The identity private key is stored in permanent, secure storage such that it can not be read outside the chip. An issuing entity generates a descriptor containing the identity public key, attribute data, and a digital signature. The digital signature is generated by enciphering a derivation of the identity public key and the attribute data with the signature private key known only to the issuer. The authenticity of the descriptor data is verified by decrypting the signature with the signature public key using a known algorithm, and comparing the result to the derivation of the descriptor data. The identity of the object can be verified requesting the smart chip ro perform an encryption / decryption operation using its identity private key, and performing the complement using the public key.
Owner:IBM CORP
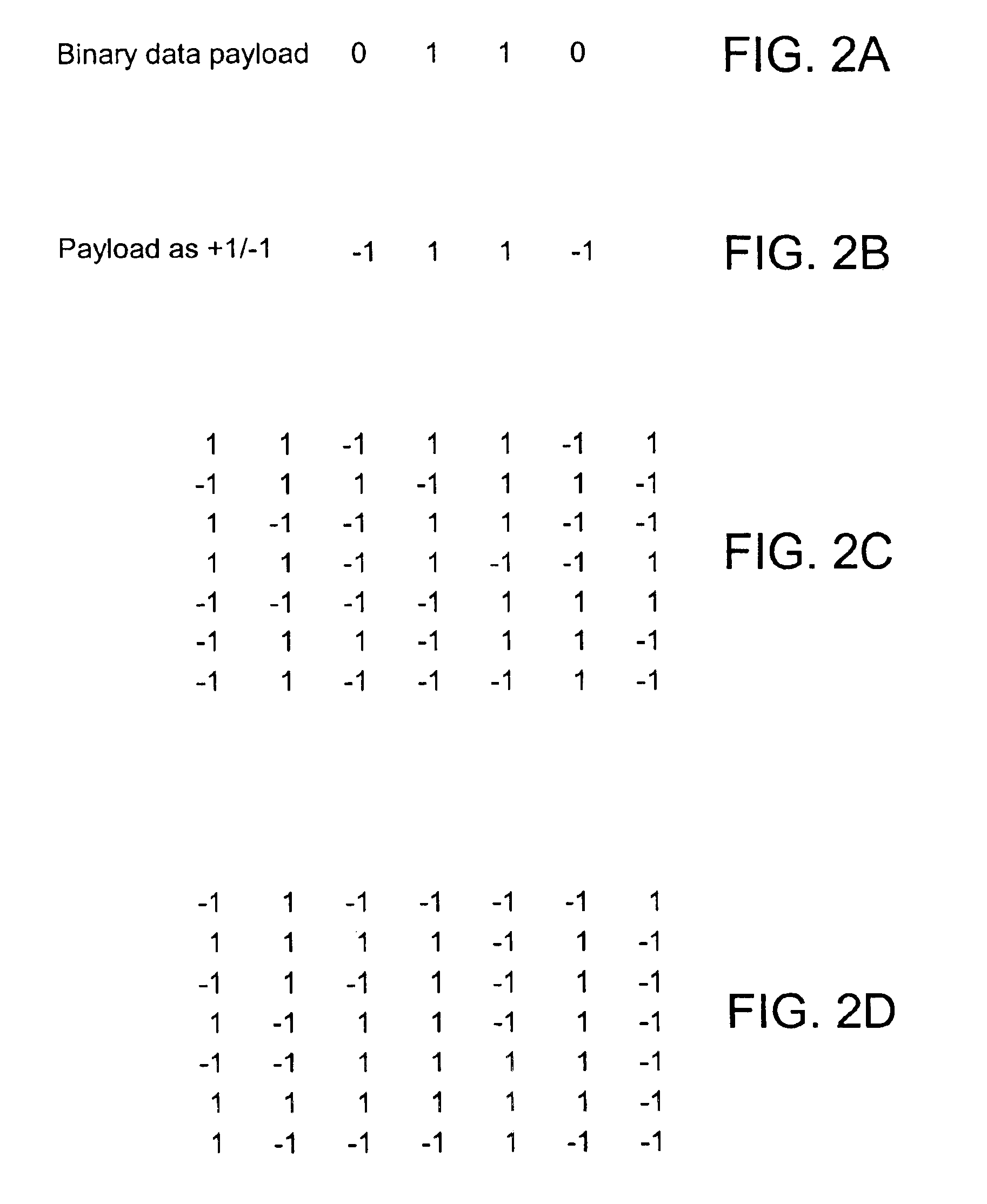
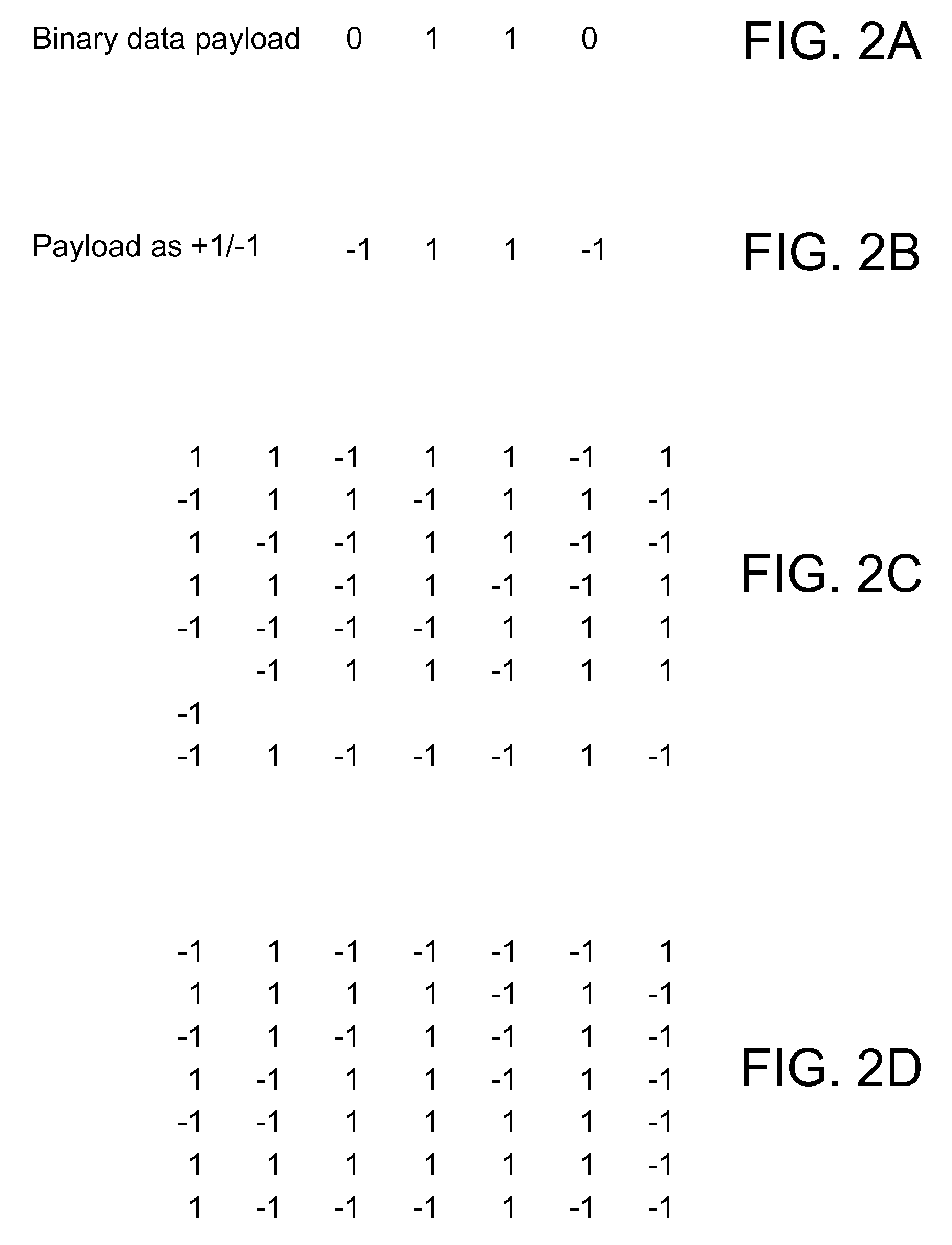
Methods and tangible objects employing machine readable data in photo-reactive materials
InactiveUS7313253B2Television system detailsSemiconductor/solid-state device detailsTangible objectMachine-readable data
The present invention relates generally to steganography and data hiding. In one implementation we provide a method including: obtaining auxiliary data; providing a mask for a photo-reactive material, the mask corresponding at least in part to the auxiliary data; and exposing the material through the mask to steganographically impart the auxiliary data in the photo-reactive material. The auxiliary data is machine-readable from the exposed material. In another implementation the material is exposed through photolithographic illumination. Of course, other implementations are described and claimed as well.
Owner:DIGIMARC CORP
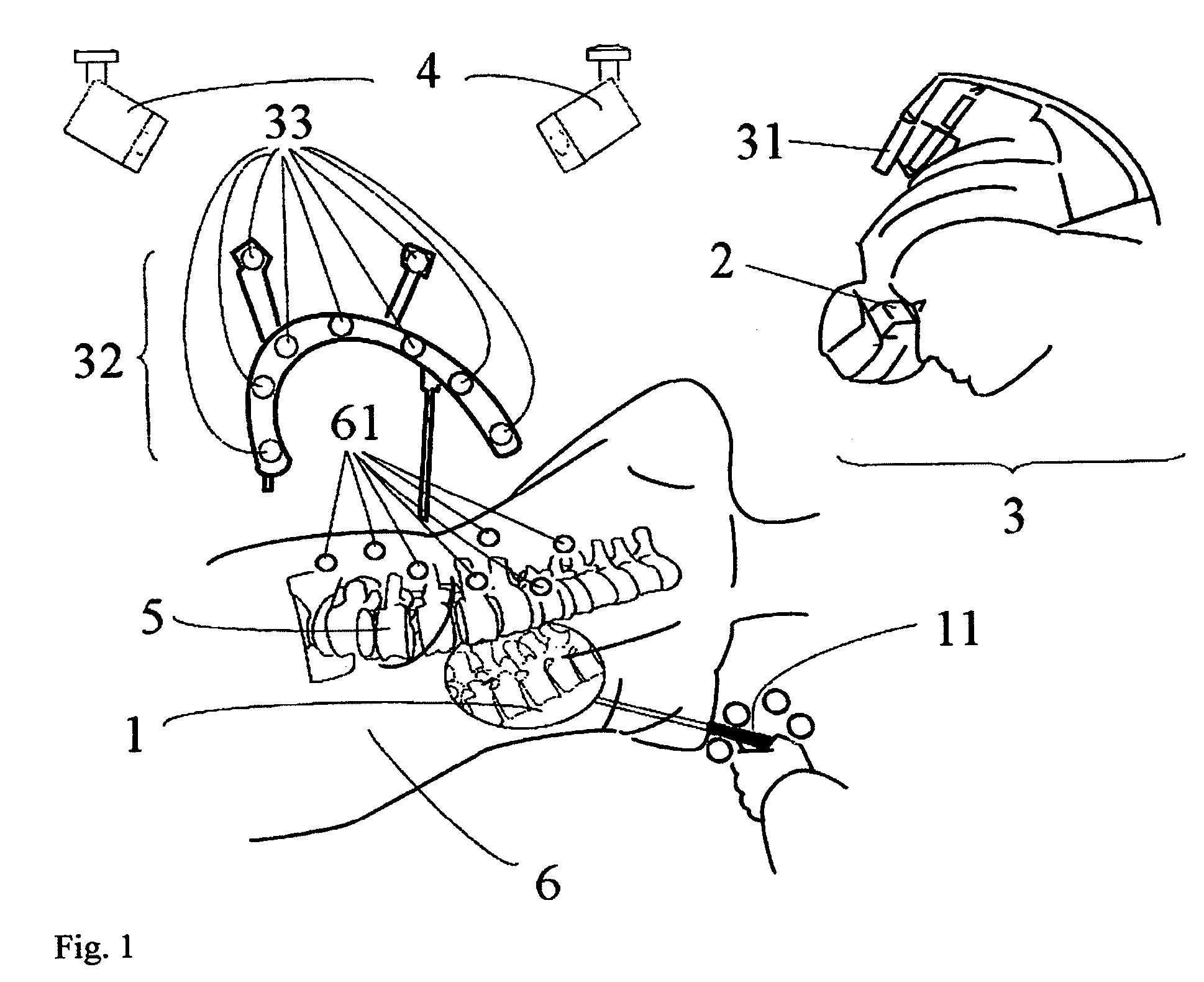
Virtual penetrating mirror device for visualizing of virtual objects within an augmented reality environment
InactiveUS8314815B2Improve abilitiesReduce riskSurgical navigation systemsCathode-ray tube indicatorsTangible objectDisplay device
A virtual penetrating mirror device for visualizing at least one virtual object within an augmented reality environment includes a tracking system tracking a plurality of markers attached to a tangible object, and a displaying device associated with at least one additional marker, characterized in that the displaying device displays a first view of the tangible object and at least one virtual penetrating mirror virtually reflecting a second view of the tangible object according to a localized position of the displaying device relative to the markers attached to the tangible object, wherein the virtual penetrating mirror is virtually disposed within the first view of the tangible object.
Owner:NAVAB NASSIR +2
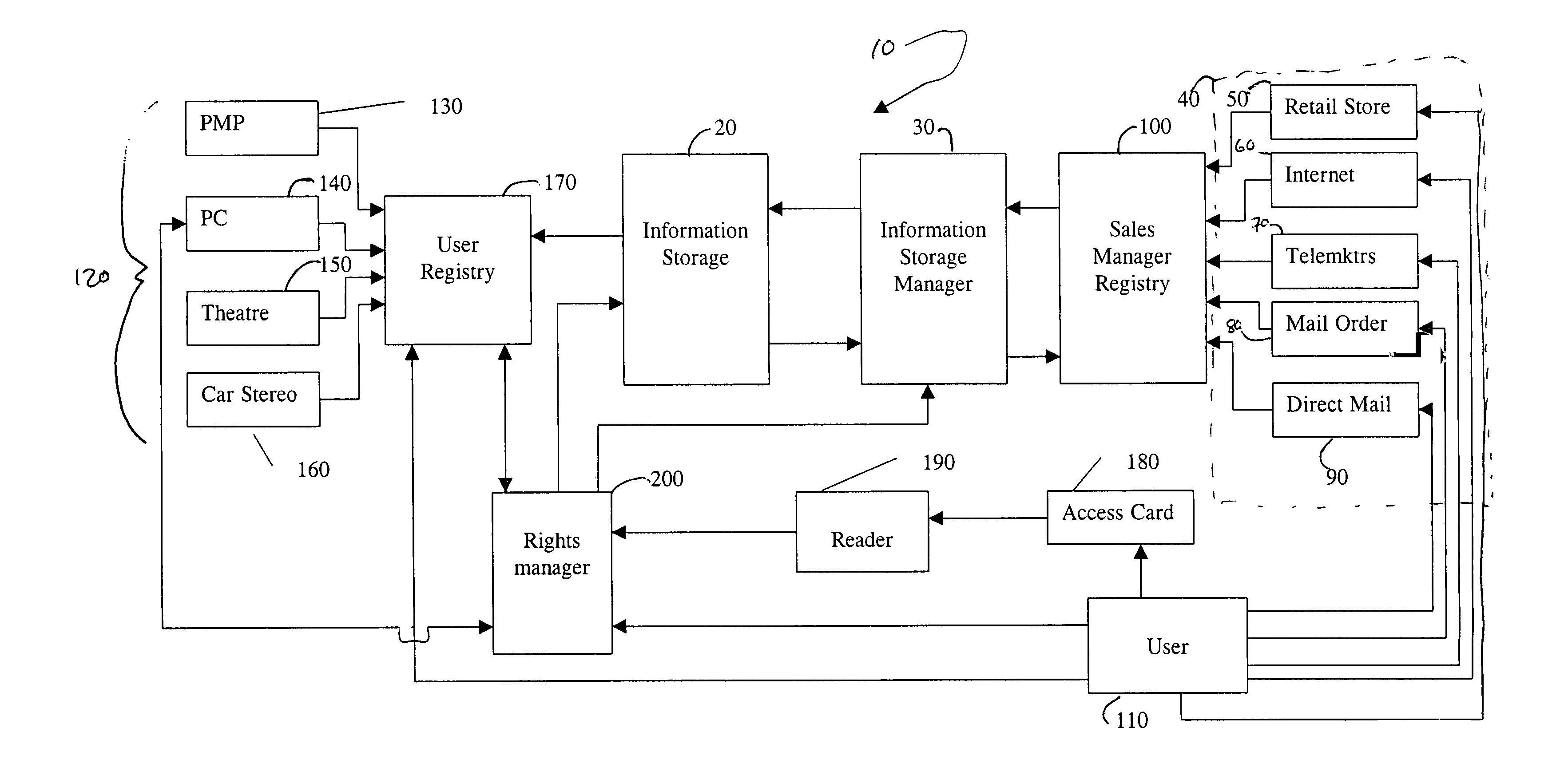
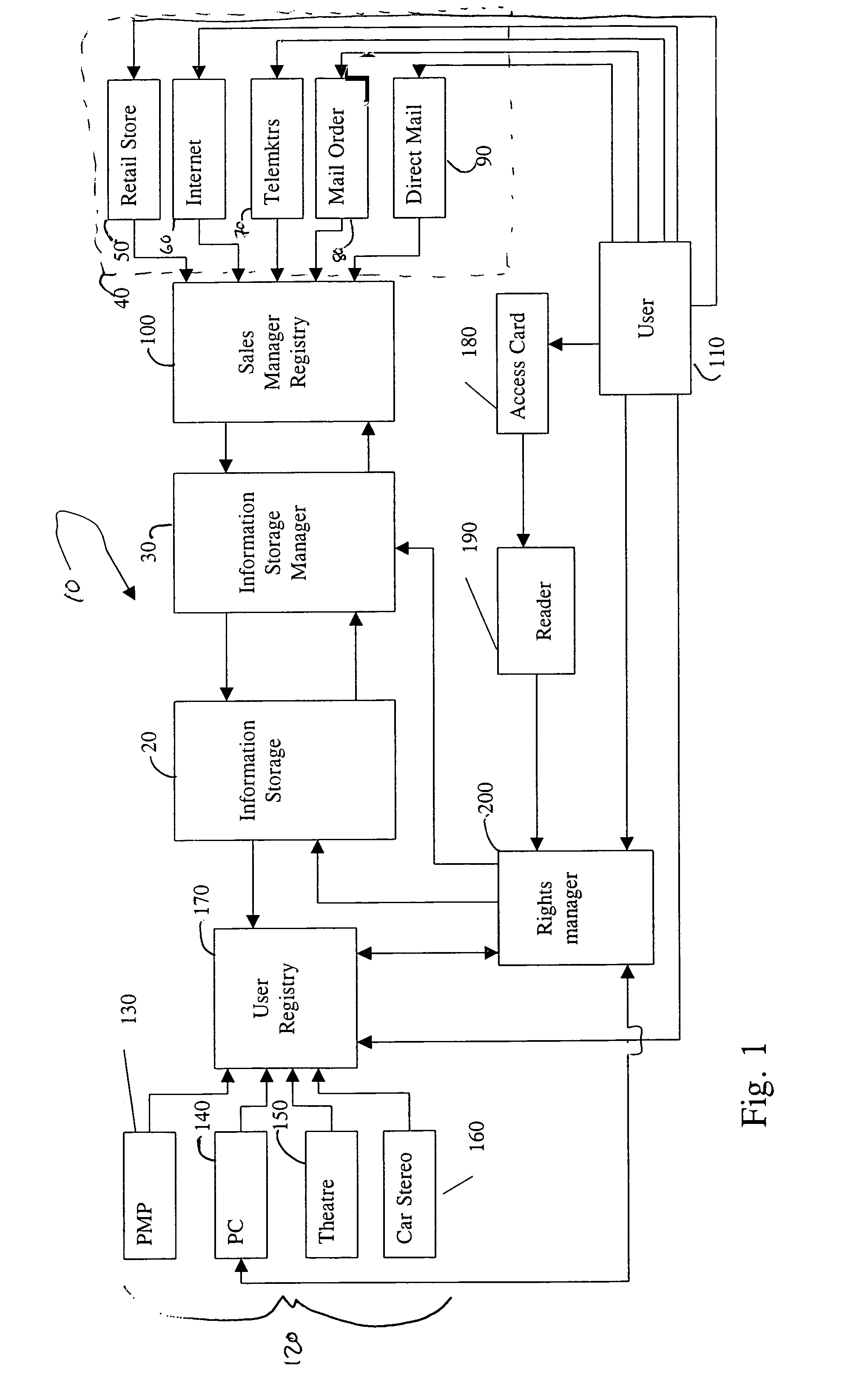
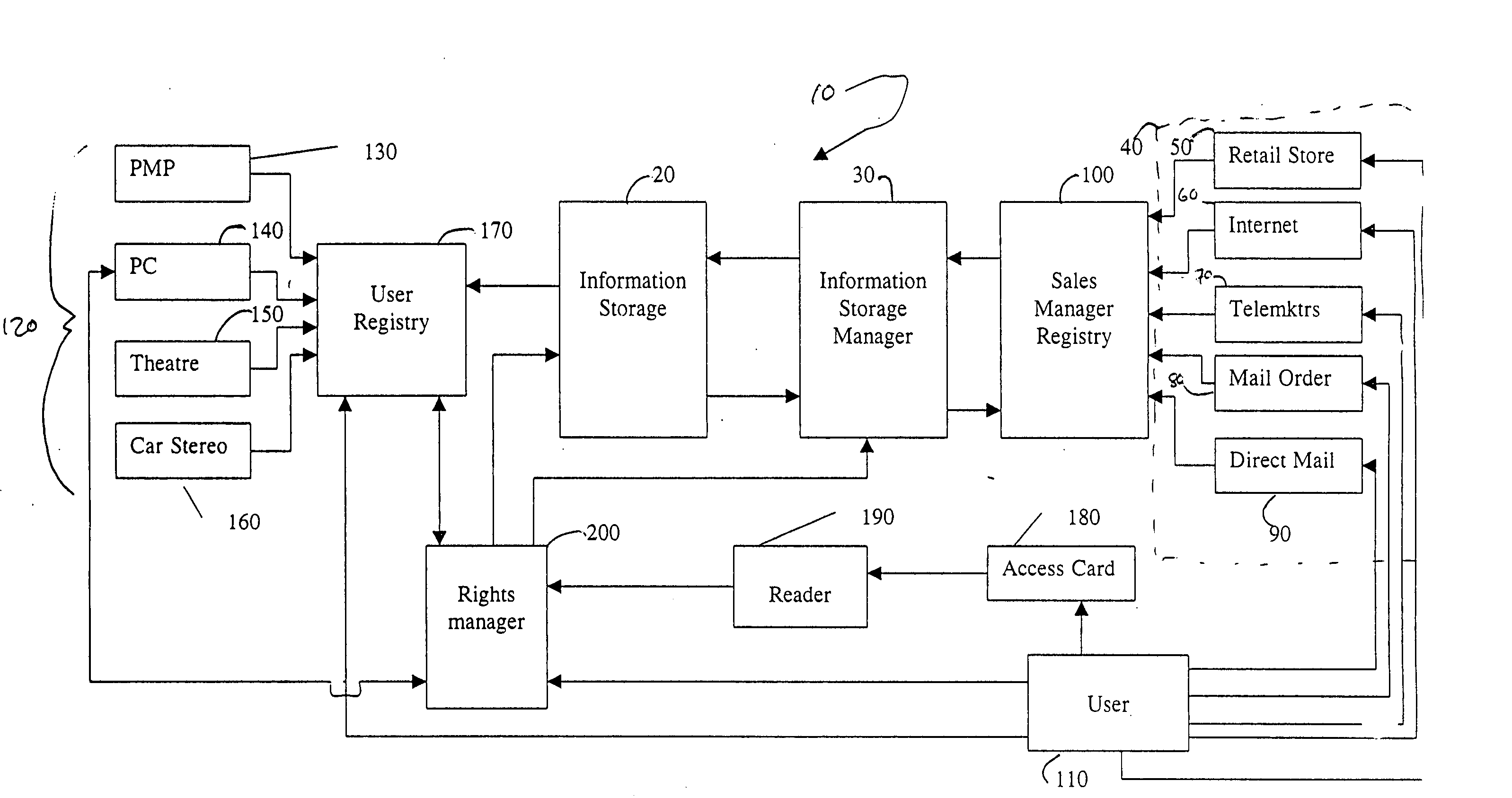
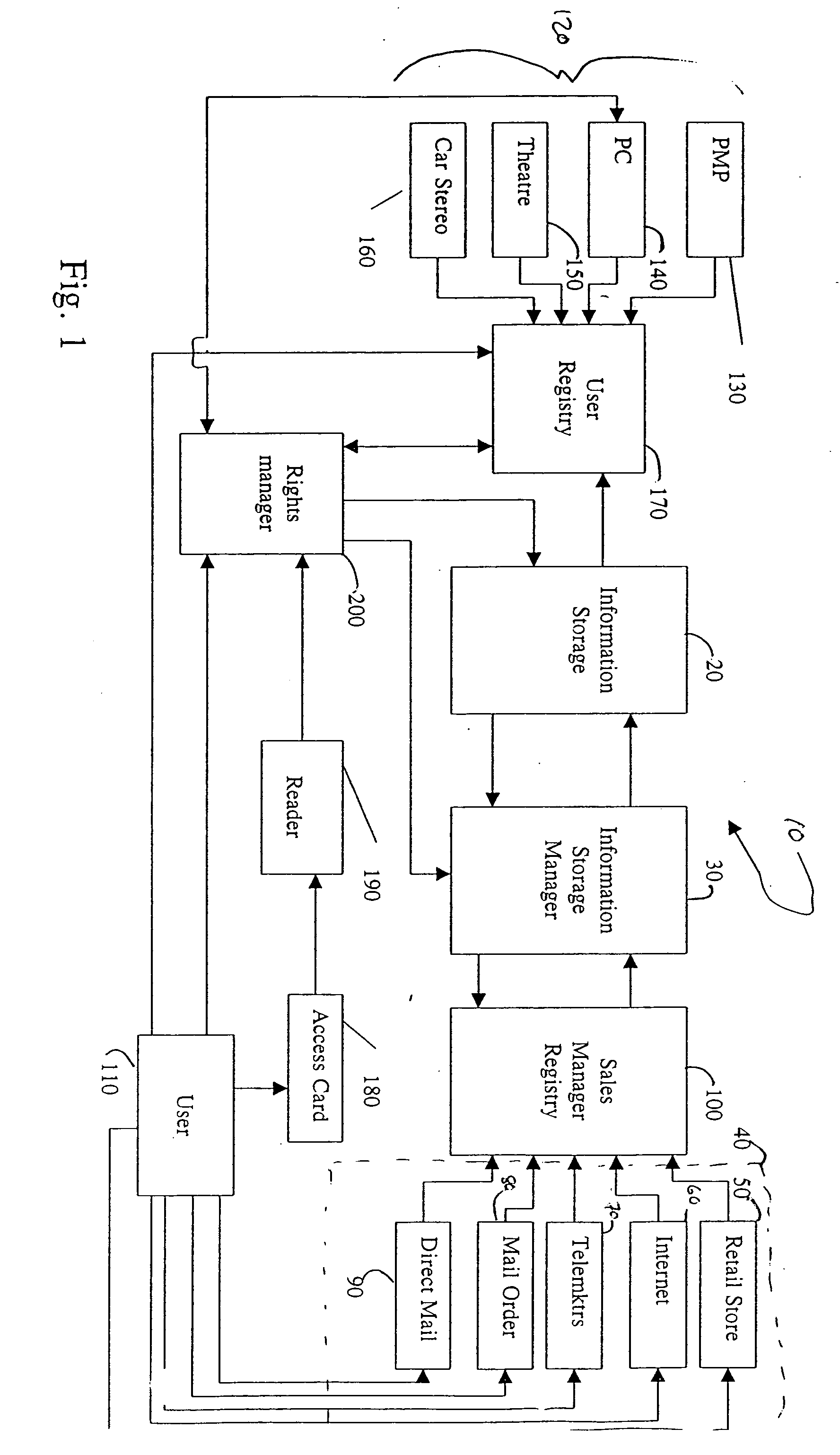
Method and system for managing rights in digital information over a network
InactiveUS6993131B1Less expensiveLow costDigital data processing detailsUnauthorized memory use protectionInformation accessTangible object
A method and system for distributing digital information is disclosed. Preferably, a user acquires a tangible object which contain a code authorizing access to the digital information. The user reads the tangible object through a reader, which sends the code to a server on which the digital information is stored. The server then authorizes access to the digital information to one or more access devices listed in registries belonging to the user. The user may use the digital information on the terms he agrees to, and, while in use by the user, access to the digital information to other users or other playback devices is disabled. Once the user no longer is using the digital information, the access device erases the digital information, and signals the server that the digital information is no longer in use, thereby re-enabling access to the digital information by the other playback devices listed in the registry.
Owner:NOKIA TECHNOLOGLES OY
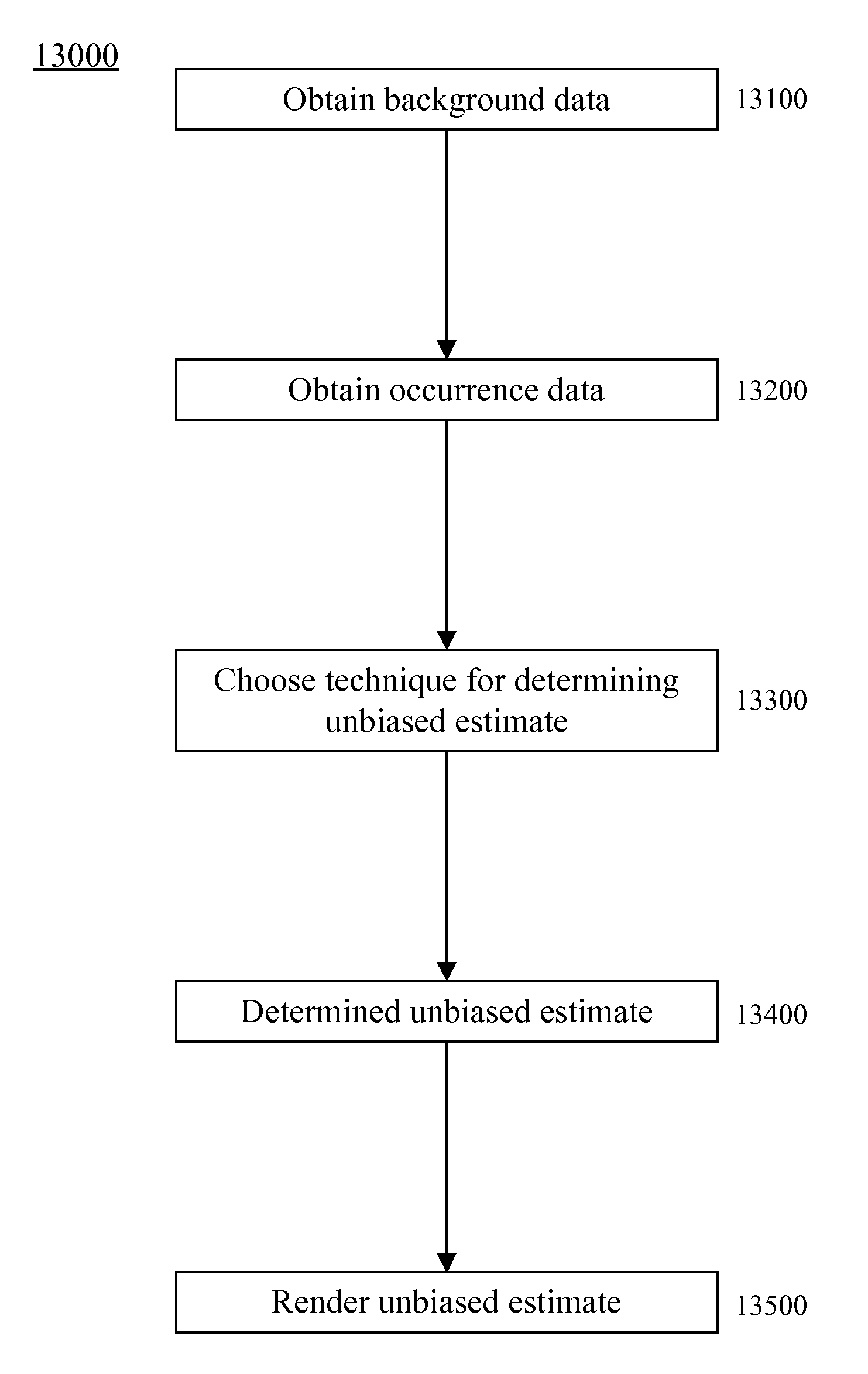
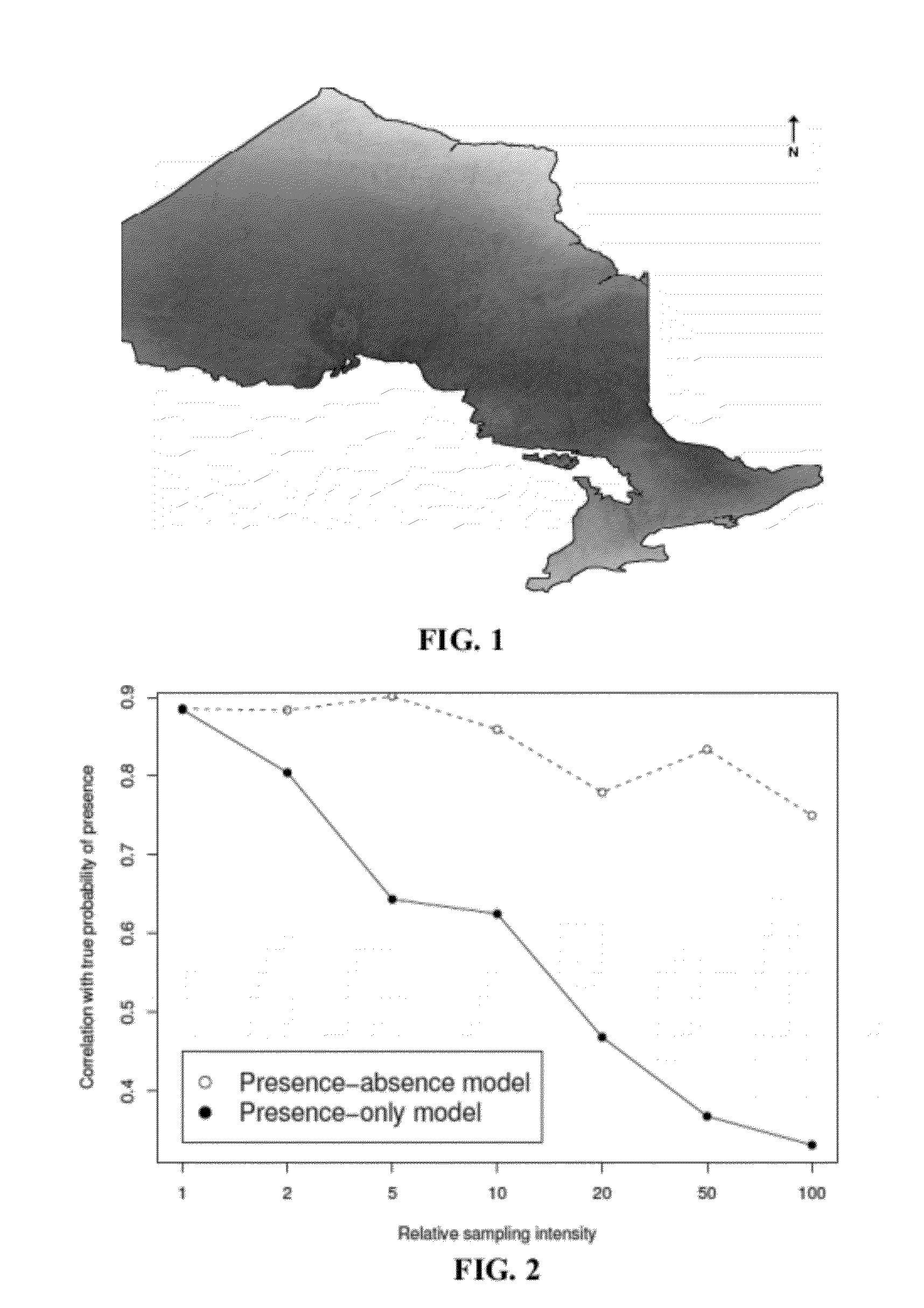
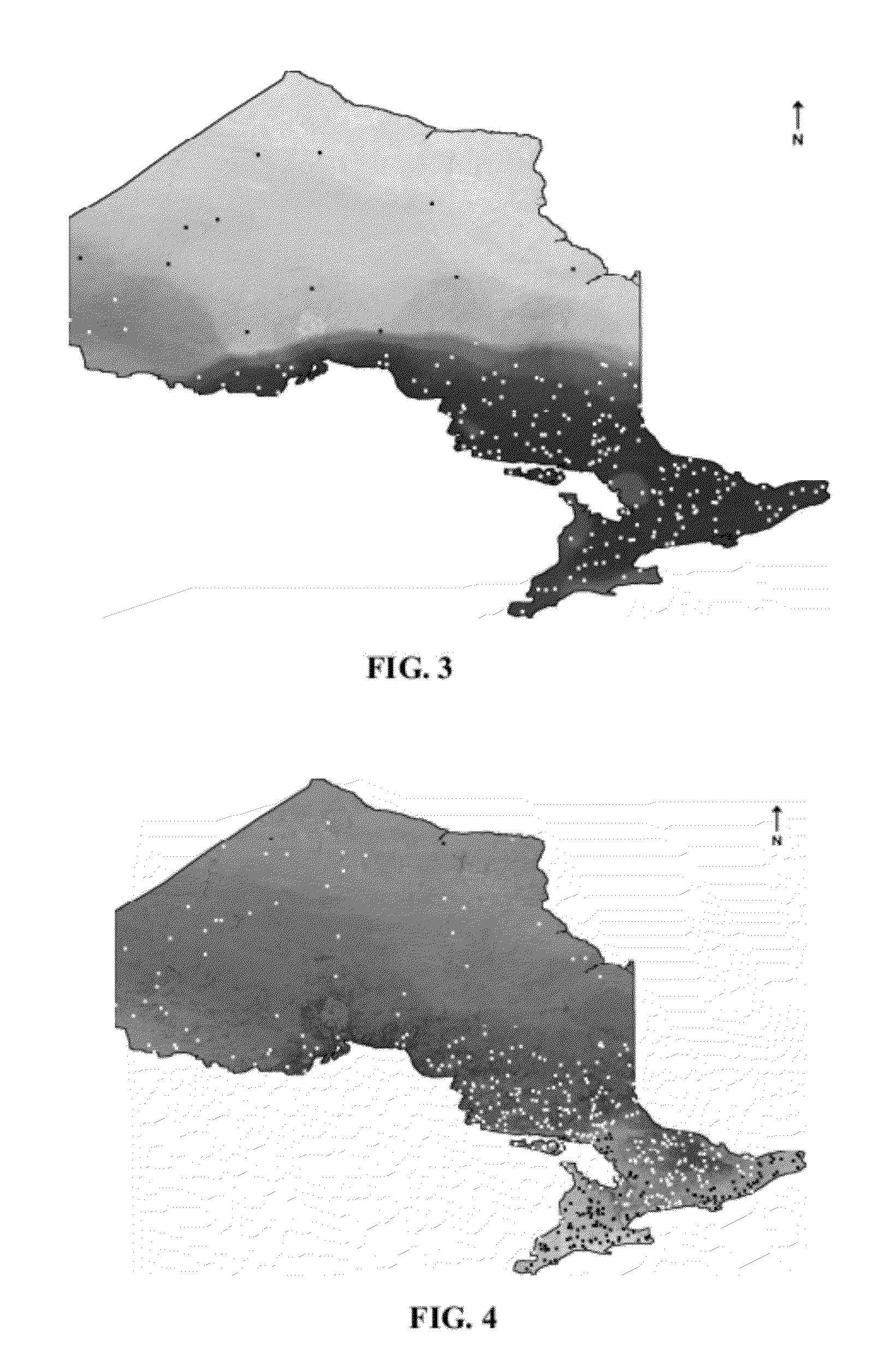
Systems, devices, and/or methods for managing sample selection bias
ActiveUS8291069B1Digital computer detailsAmplitude-modulated carrier systemsSelection biasOccurrence data
A method for managing sample selection bias is disclosed. Embodiments of the method can include automatically determining an unbiased estimate of a distribution from occurrence data via a special purpose processor. The occurrence data that is utilized in determining the estimate may have an occurrence data sample selection bias that is substantially equivalent to a background data sample selection bias associated with background data. Additionally, the occurrence data may be related to the background data, and the background data may be chosen with the background data sample selection bias. Furthermore, the occurrence data may represent a physically-measurable variable associated with one or more physical and tangible objects or substances.
Owner:NUANCE COMM INC
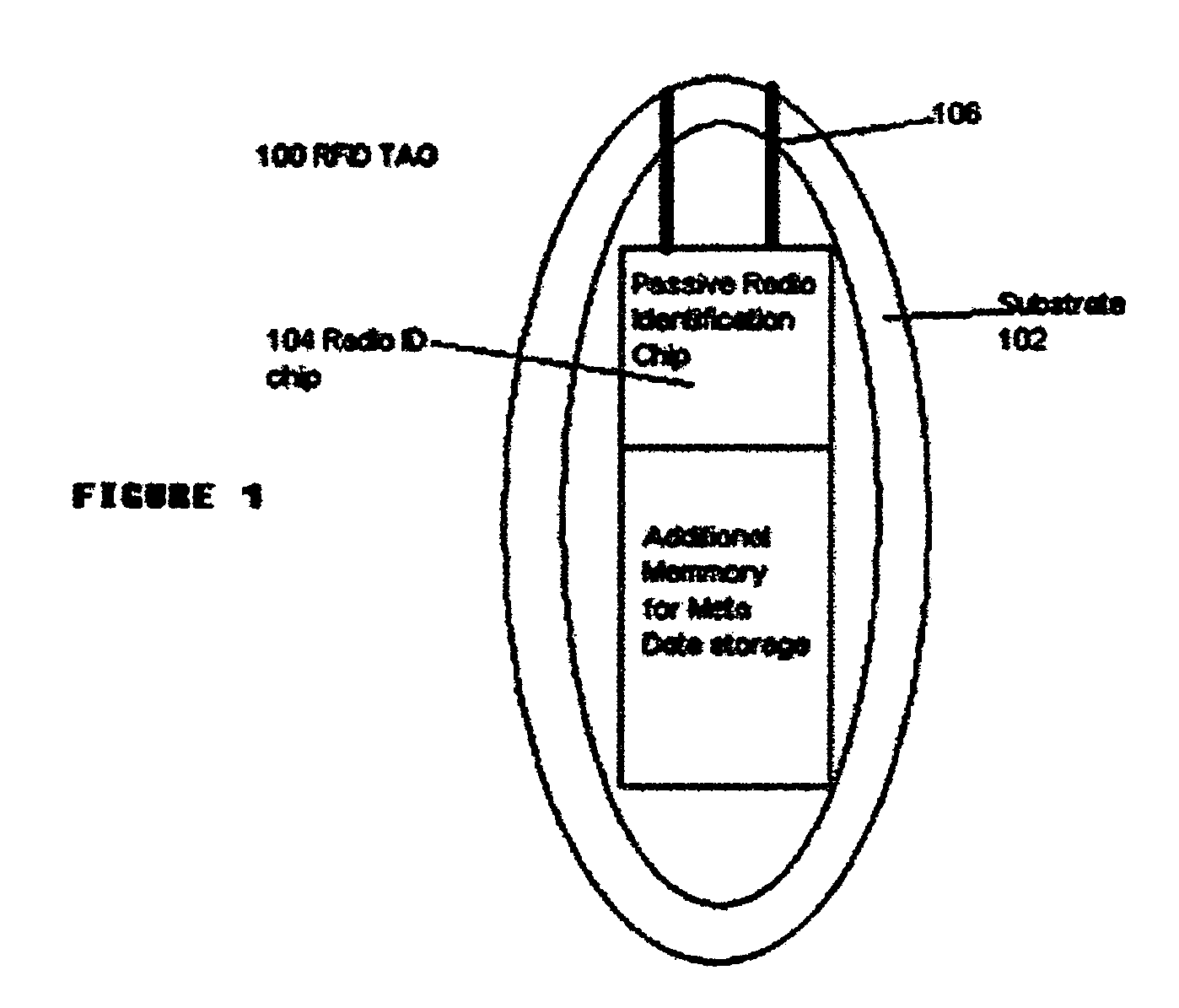
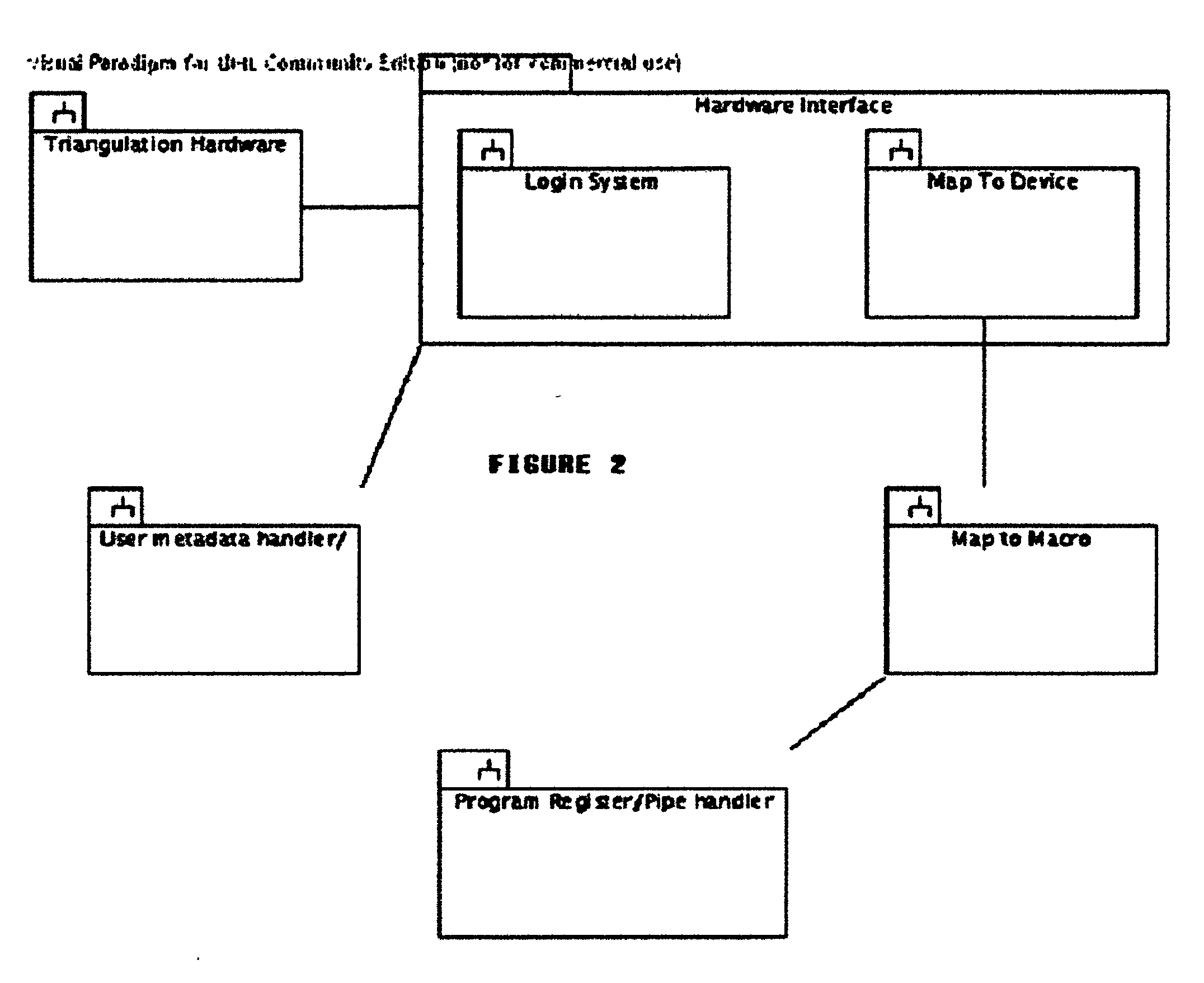
Methods and apparatus for RFID interface control
Methods and apparatus for interacting with a computer system using hand gestures, tangible objects that contain a tracking RFID tag, tangible objects that contain no RFID tag, and holographic or virtually displayed objects. This invention allows any real or virtually displayed object to be used as a tool for interaction with a computer system. The system provides an entirely user configurable interface for a computer and allows user metadata to be easily carried by the user from one computer to the next.
Owner:THOMAS NICHOLAS
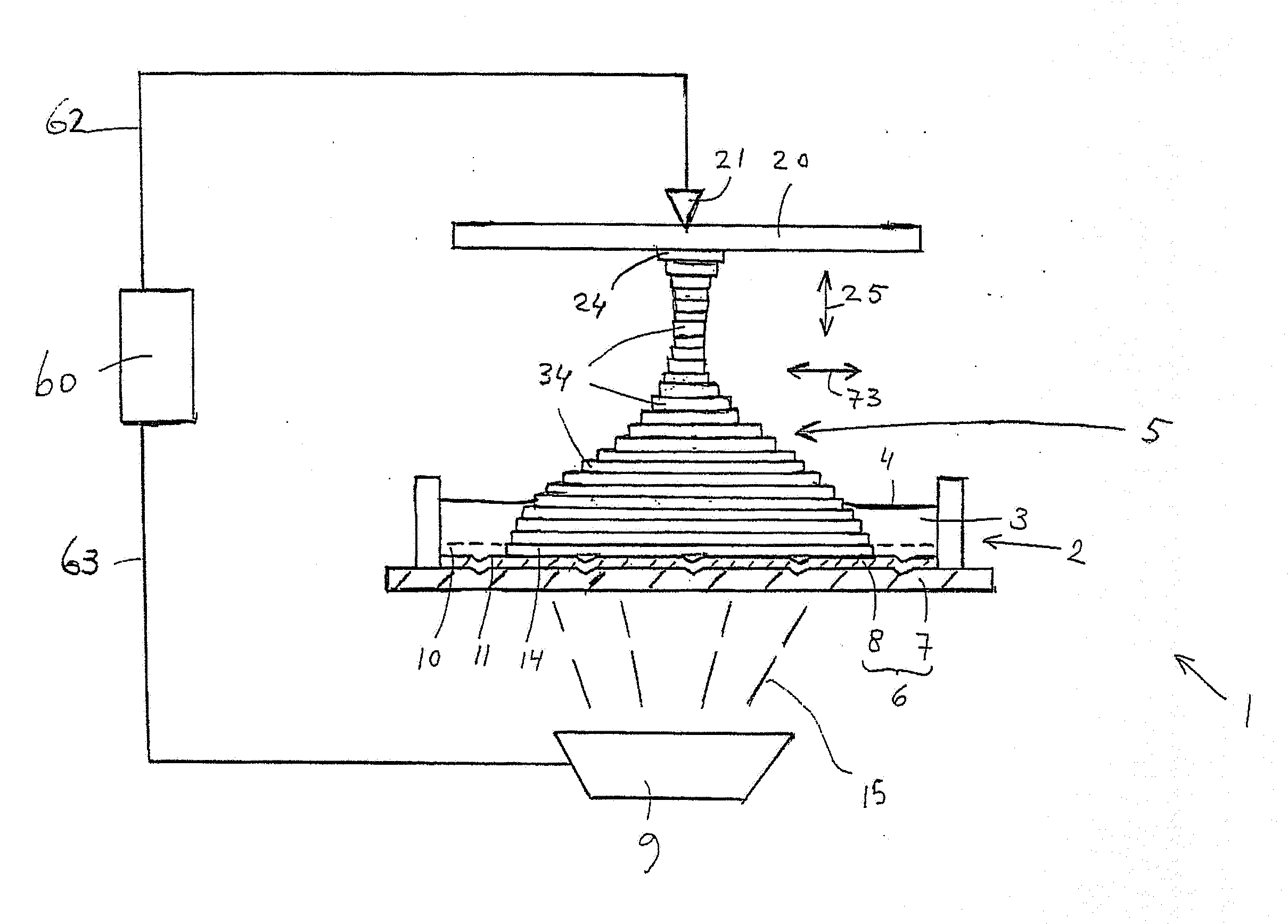
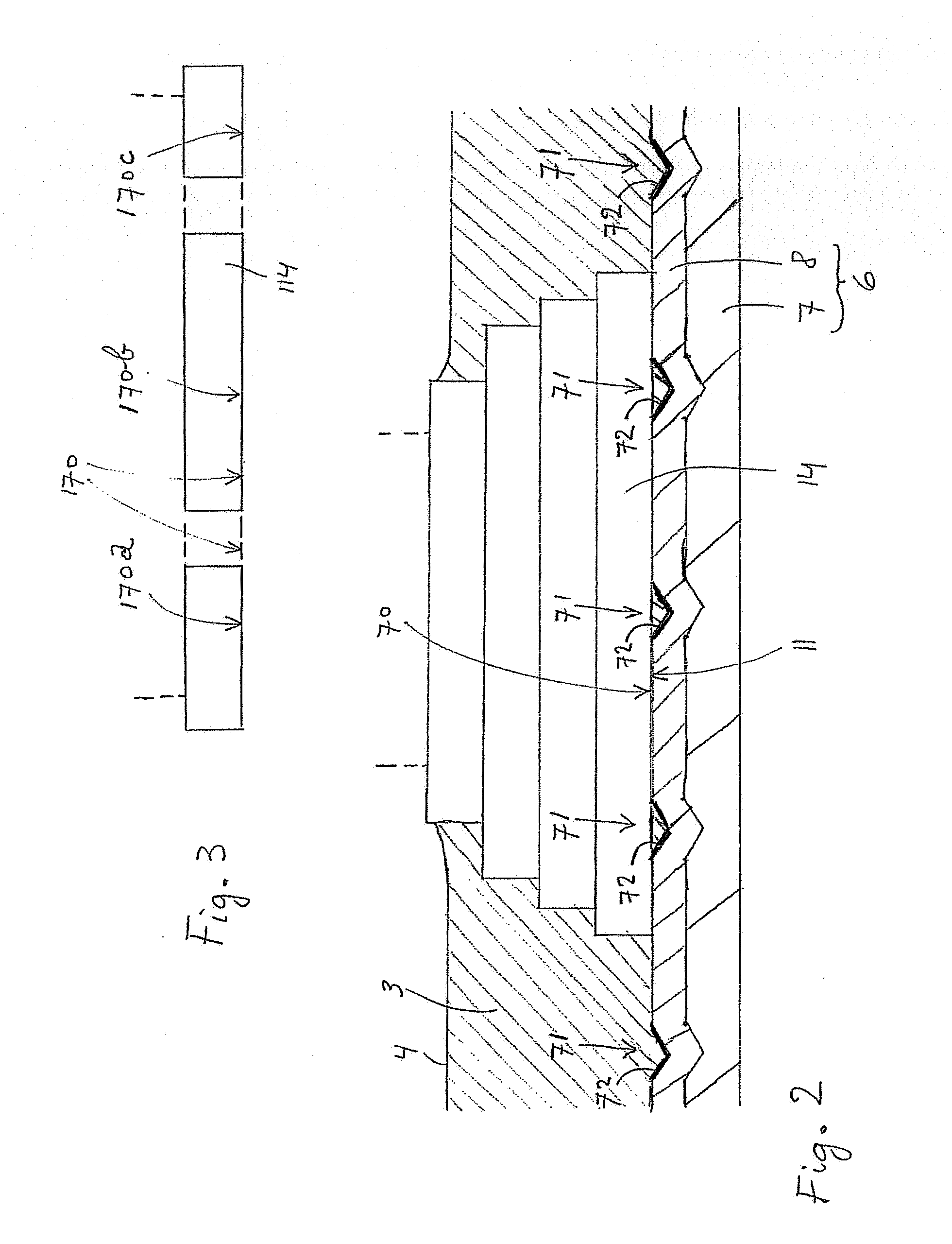
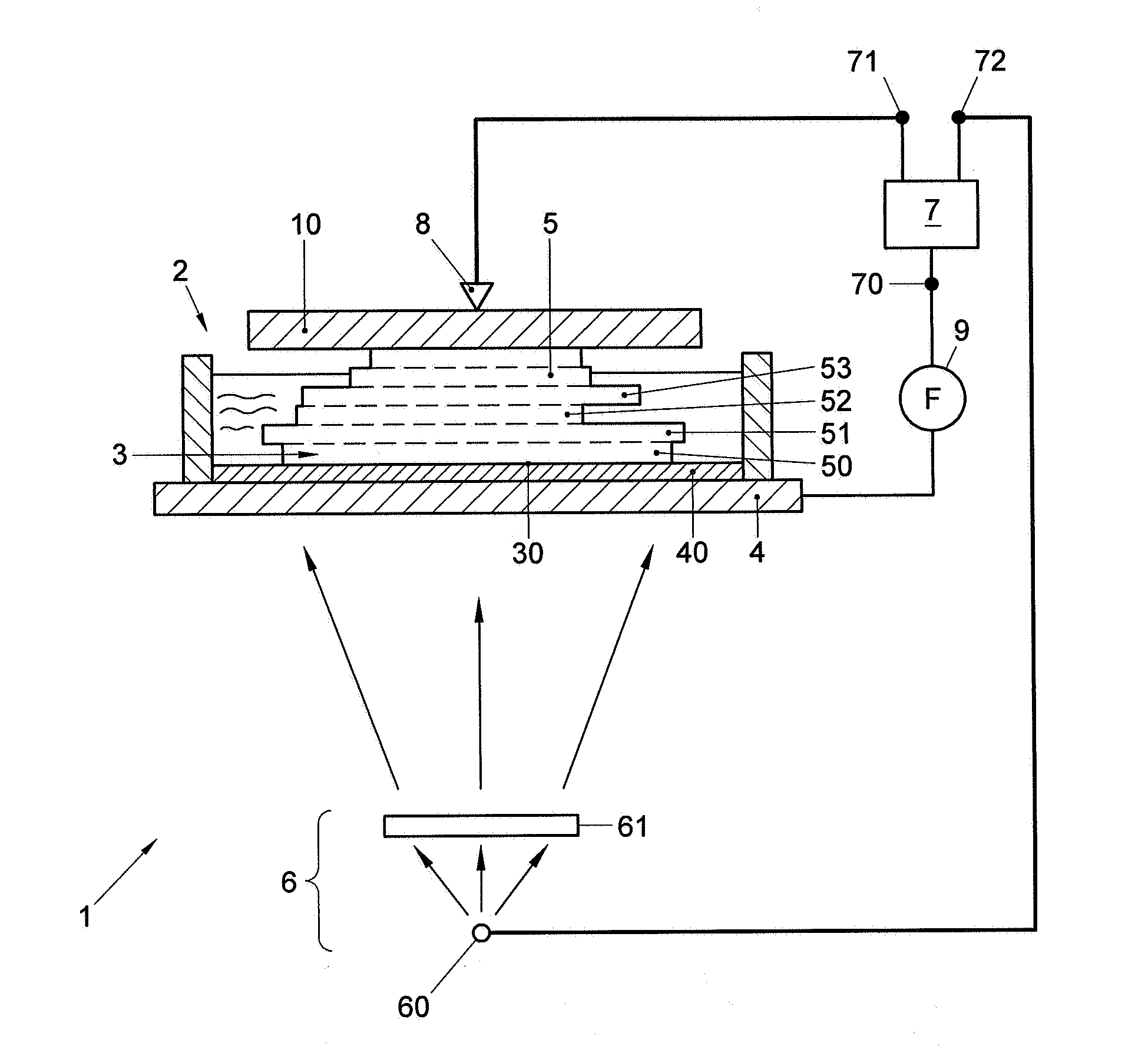
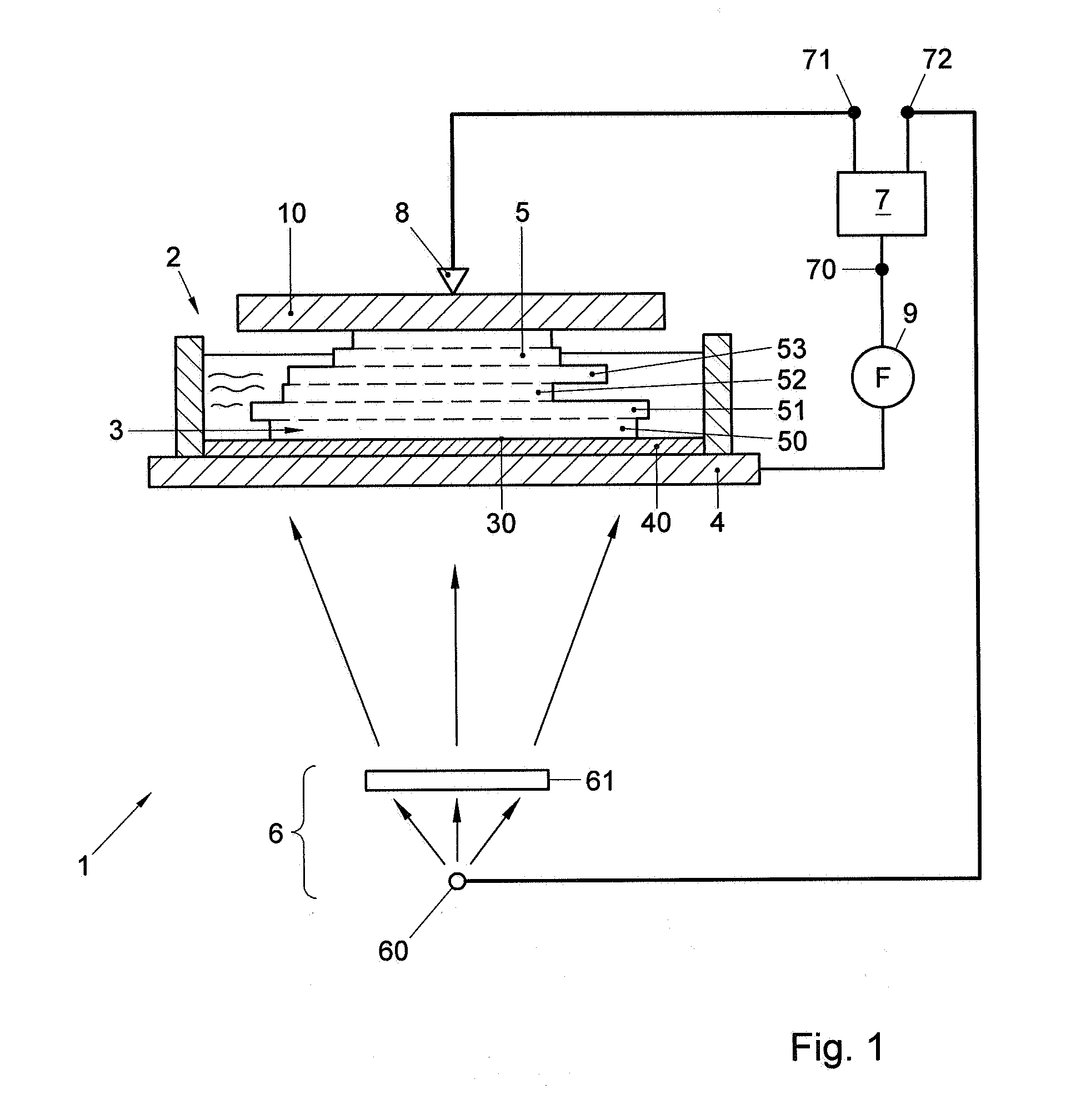
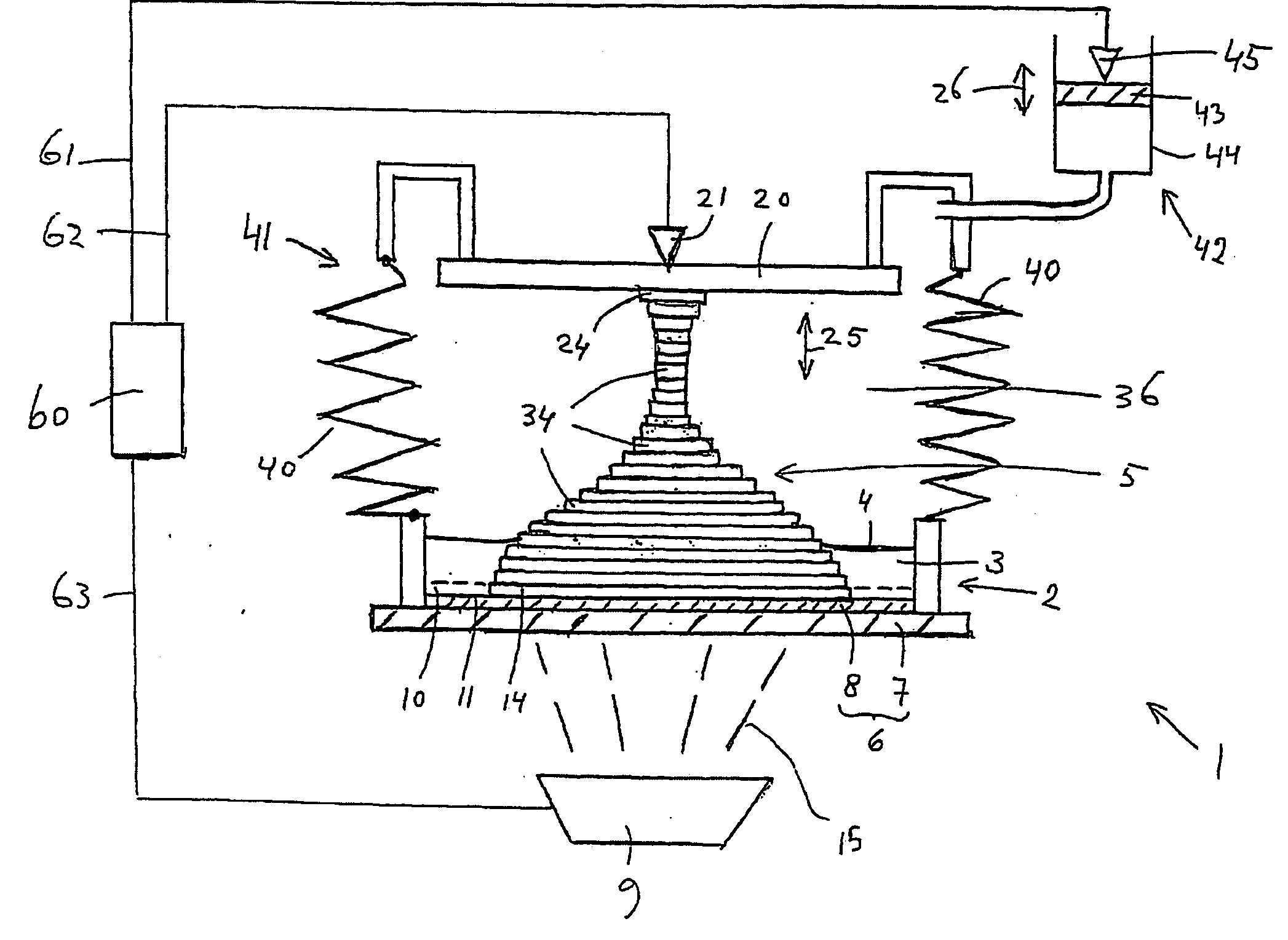
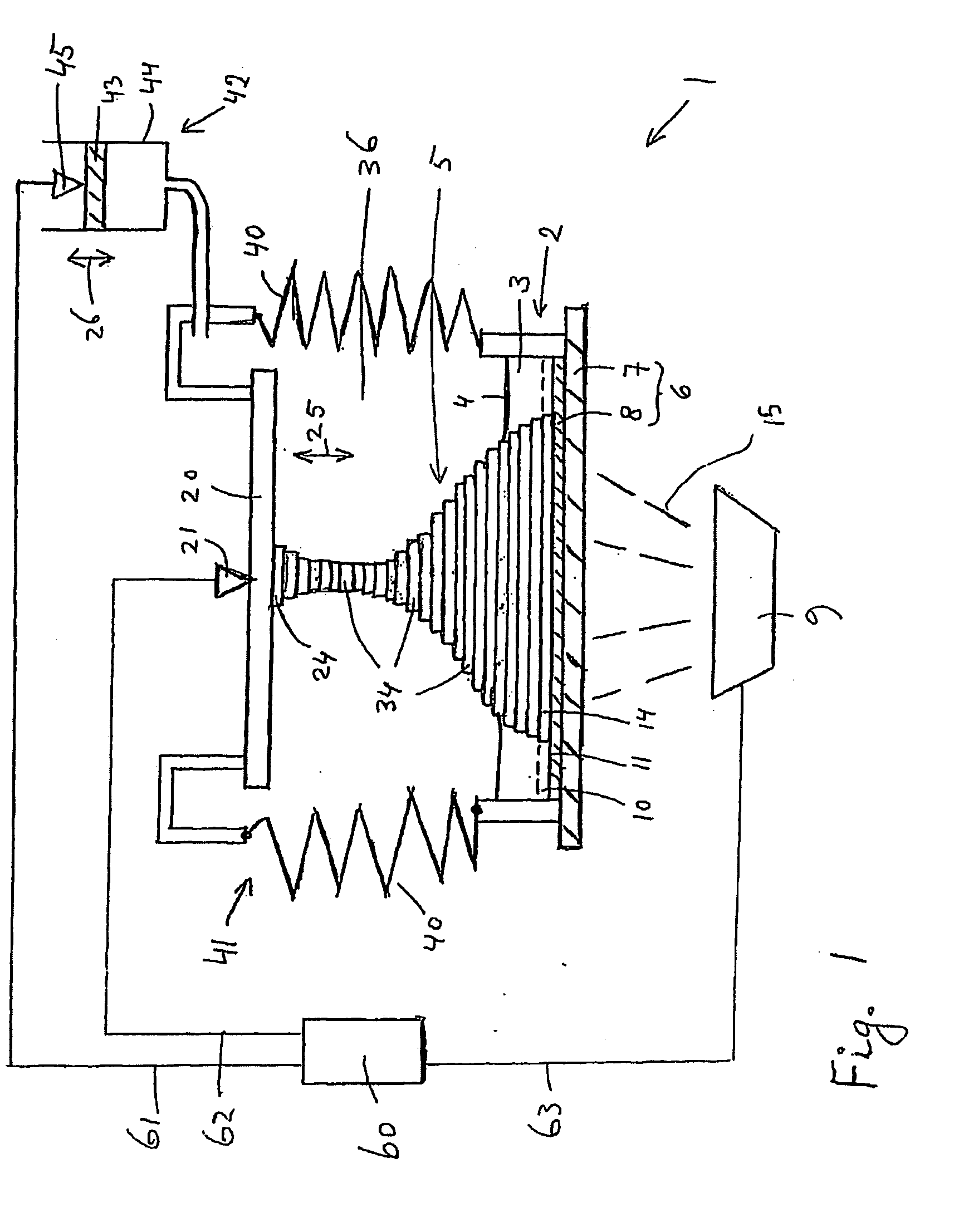
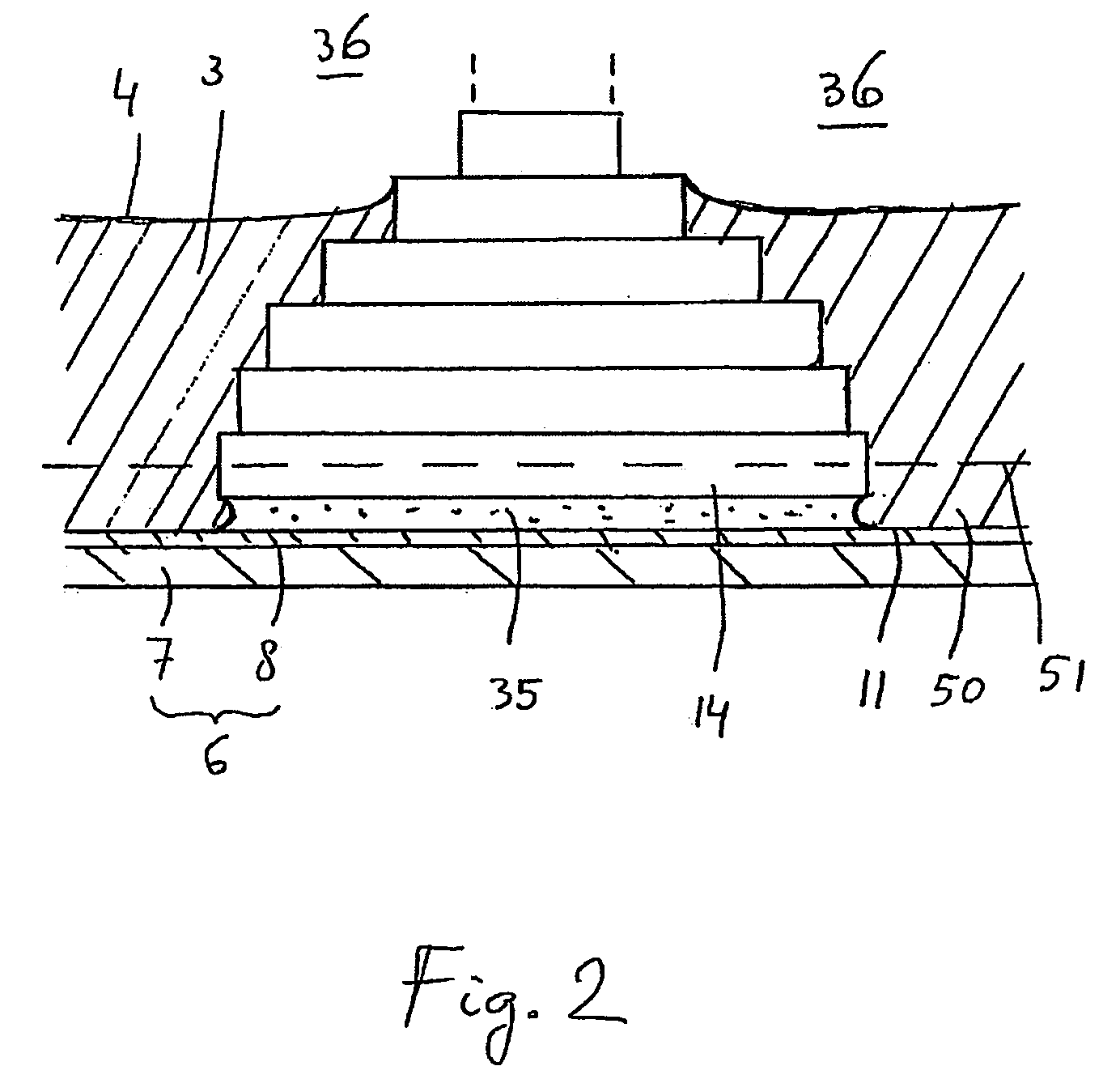
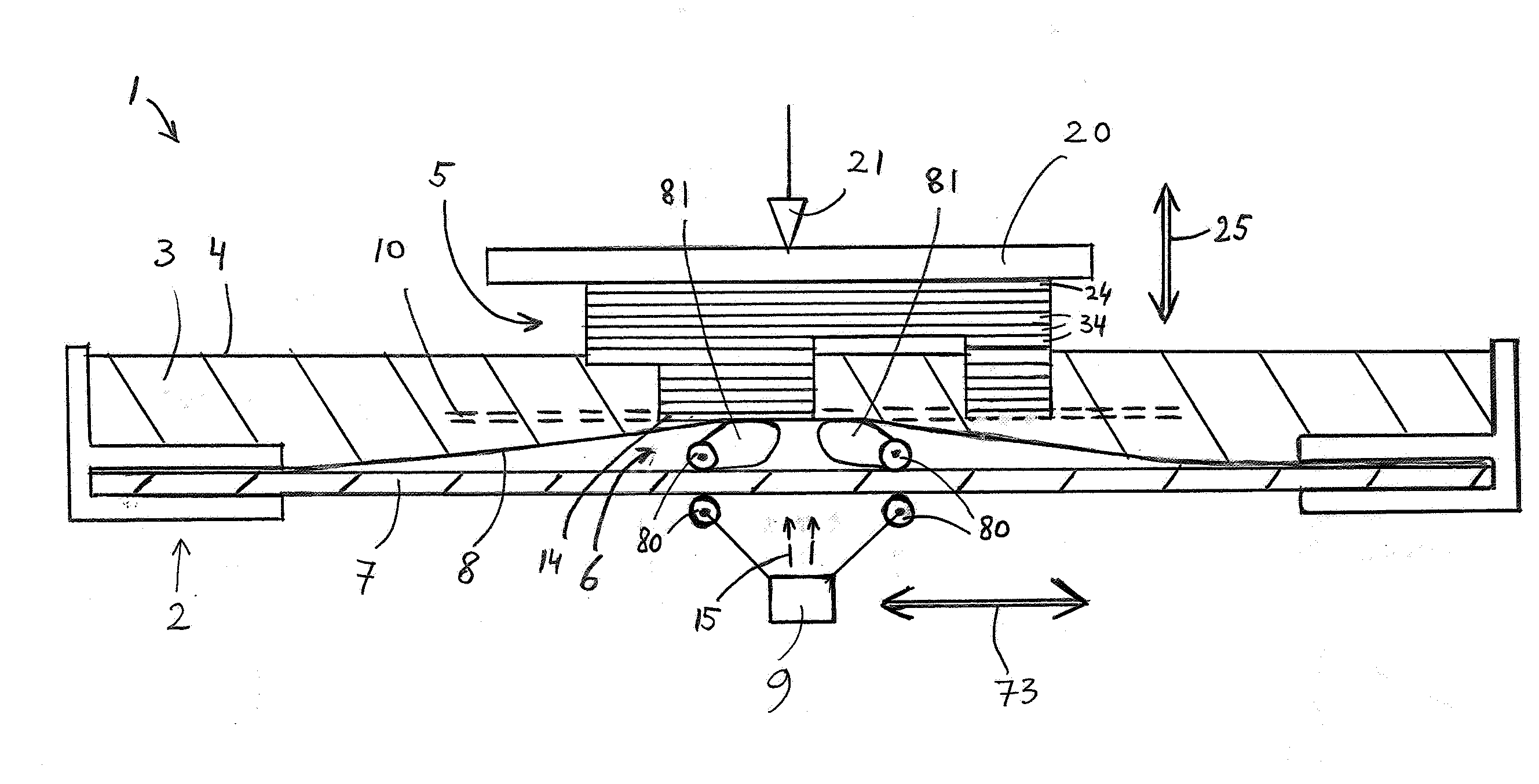
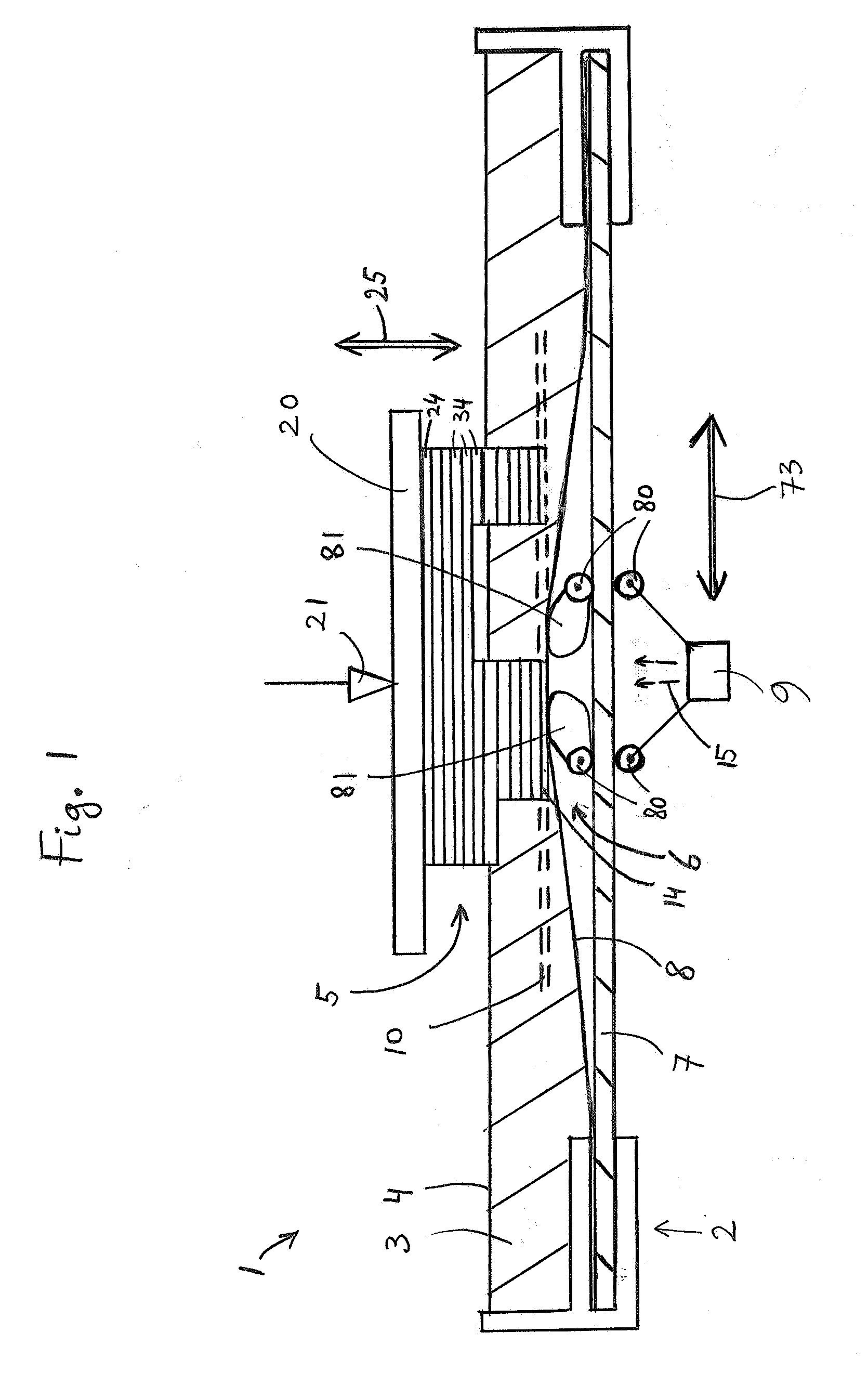
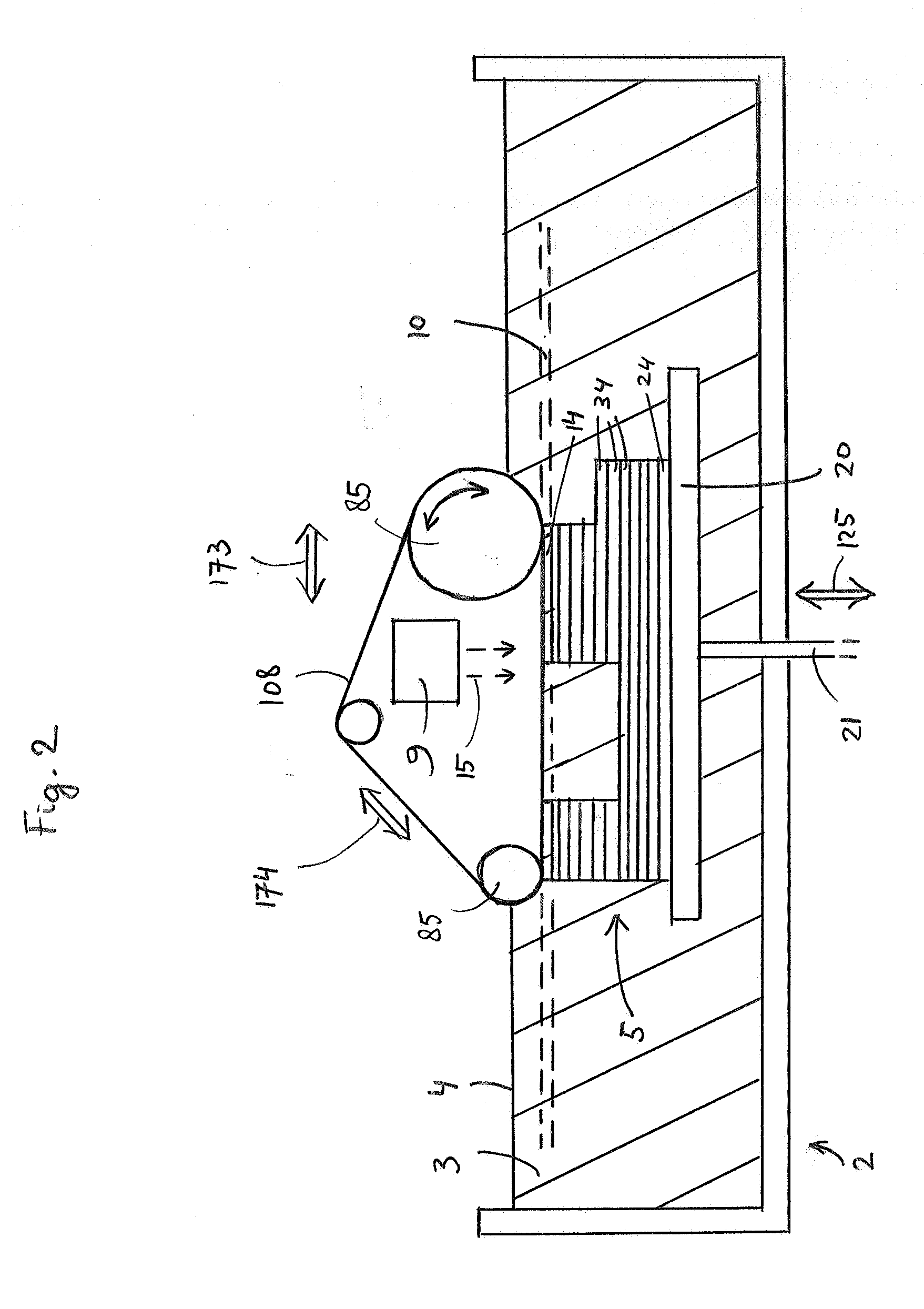
Method and system for layerwise production of a tangible object
ActiveUS20090309267A1Reduce differential pressureEasy to separateAdditive manufacturing apparatusTailstocks/centresTangible objectMechanical engineering
A method cycle of a method for layerwise production of a tangible object (5) comprises the successive steps of: solidifying predetermined parts of a liquid so as to obtain a solid layer (14) having a predetermined shape; separating said solid layer from a construction shape (6); and moving, relative to one another, the separated solid layer and the construction shape to a predetermined position relative to one another. Solidifying is carried out such that the solid layer and the construction shape have nonmatching shapes in the sense that all surface portions of a solid layer side (70) that are or have been in contact with a liquid contacting side (11) of the construction shape can not simultaneously be brought in full contacting engagement with the liquid contacting side.
Owner:NEDERLANDSE ORG VOOR TOEGEPAST-NATUURWETENSCHAPPELIJK ONDERZOEK (TNO)
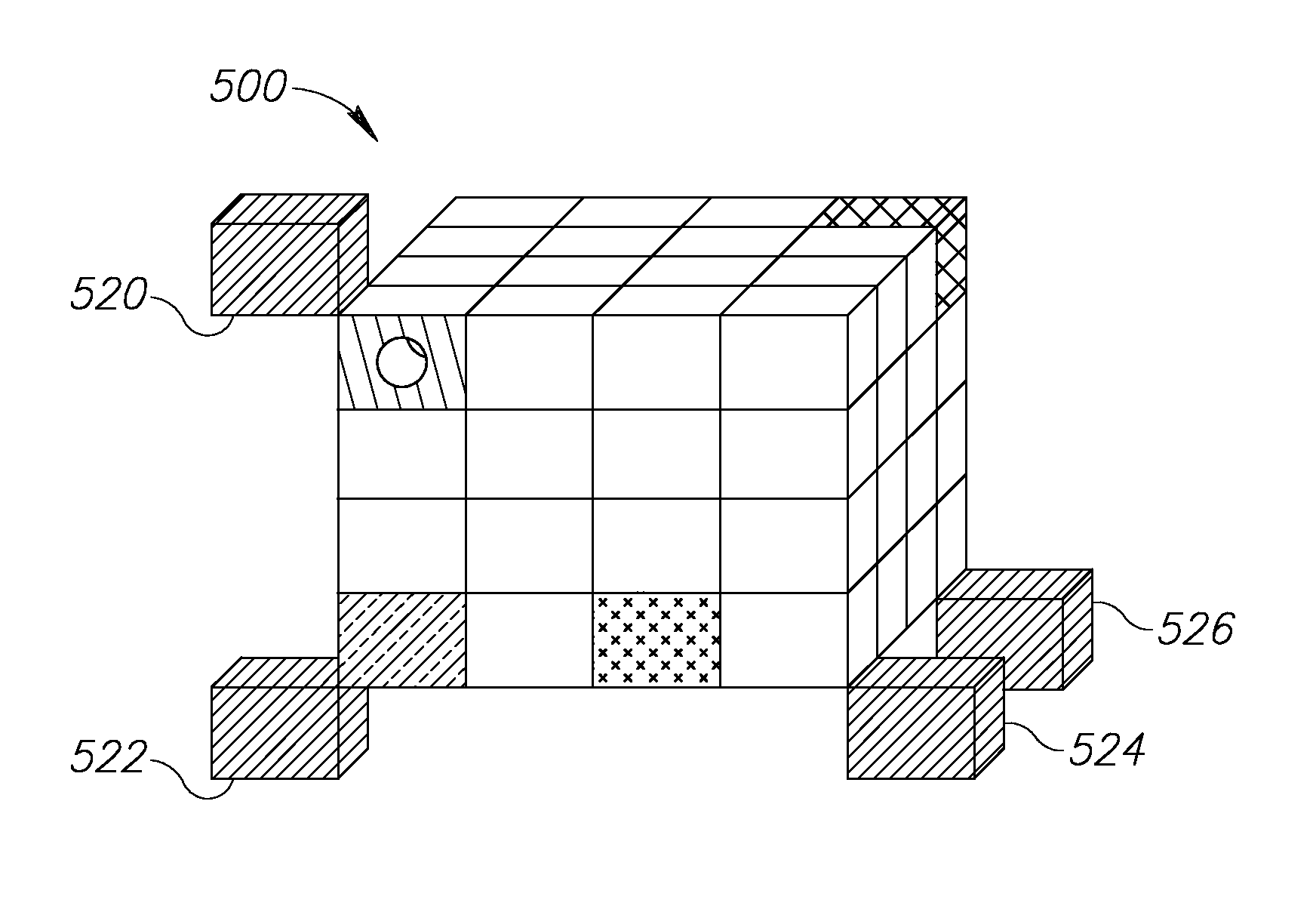
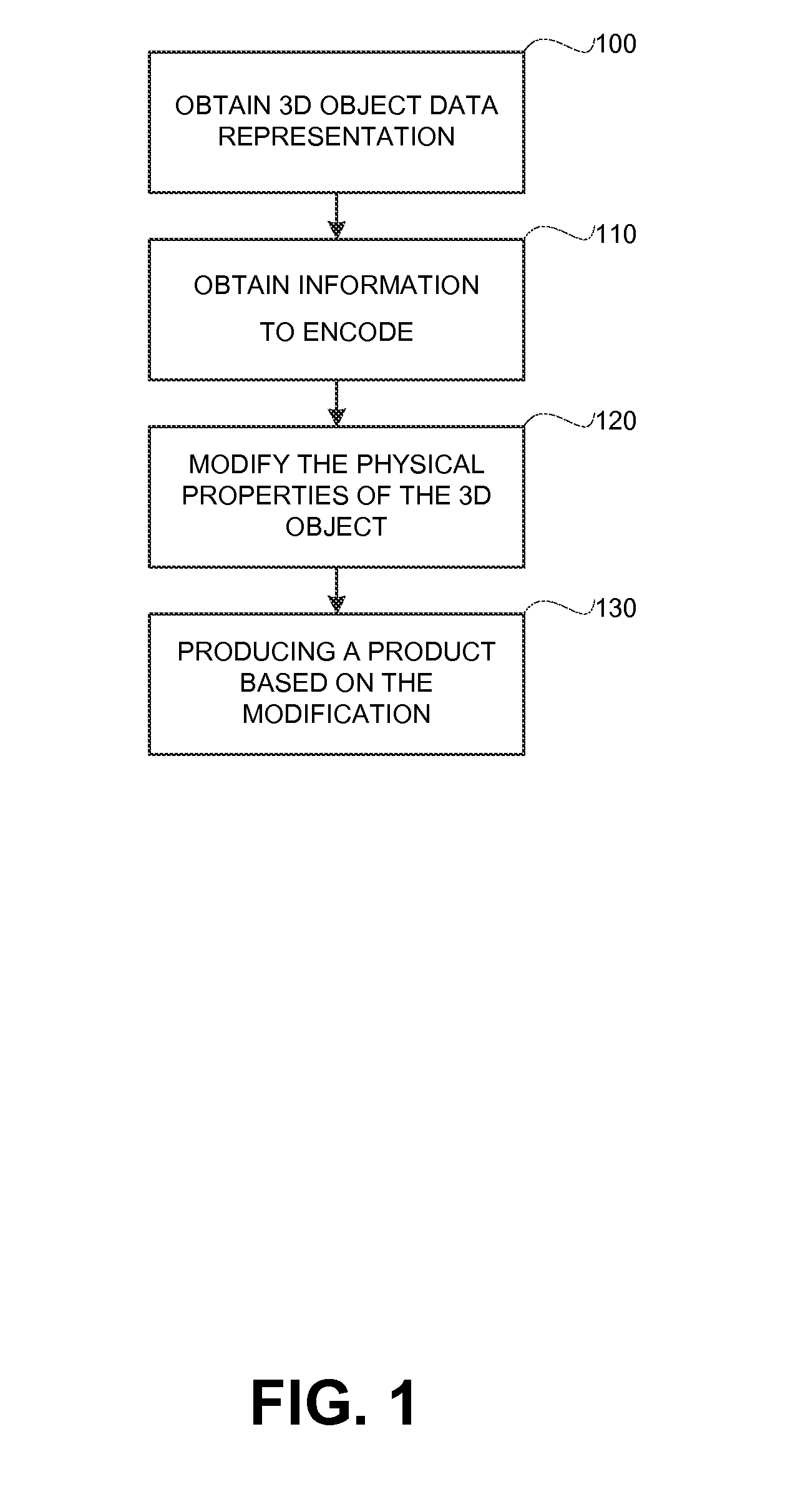
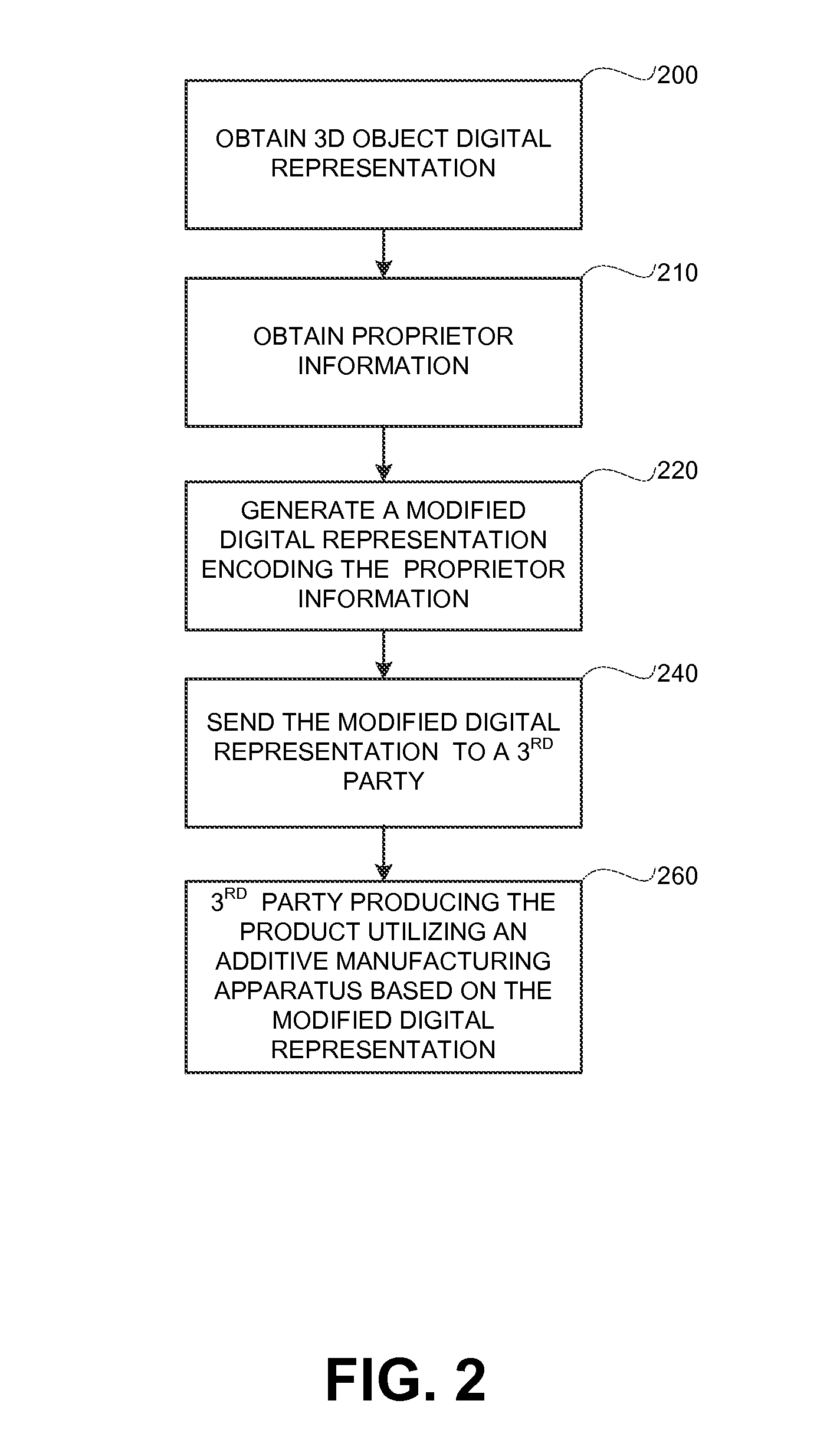
Encoding information in physical properties of an object
ActiveUS20150242737A1Programme controlAdditive manufacturing apparatusTangible objectComputer science
A method, system for encoding or decoding information in physical properties of an object. A tangible product comprises a three dimensional tangible object having modified physical properties; and wherein the modified physical properties are a modification of physical properties, wherein the modification encodes information. A method comprising: obtaining a representation of a three dimensional object having physical properties; obtaining information to encode; determining modified physical properties by modifying the physical properties to encode within the modified physical properties the information; and producing a tangible product, wherein the tangible product is the three dimensional object having the modified physical properties.
Owner:GLAZBERG APPLEBAUM
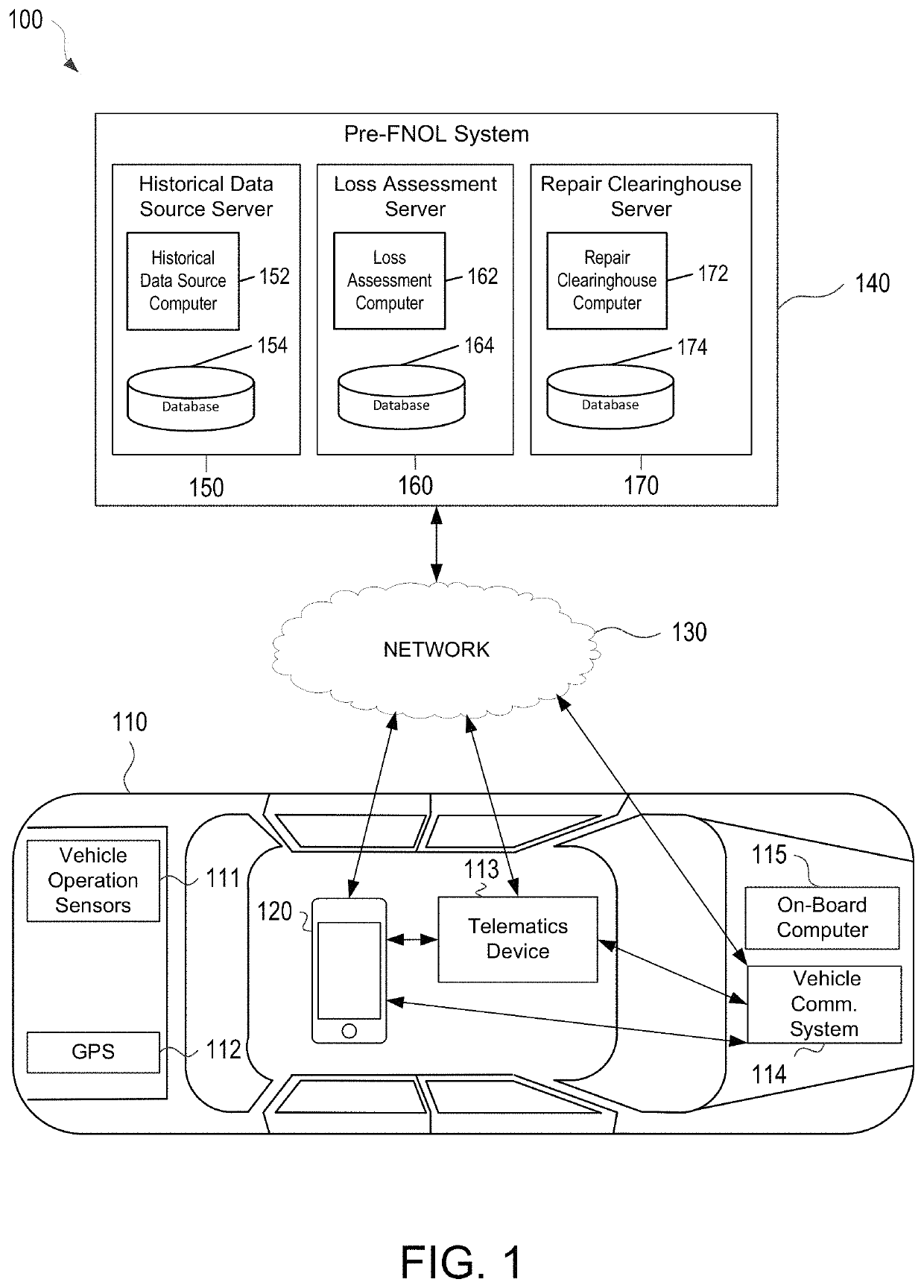
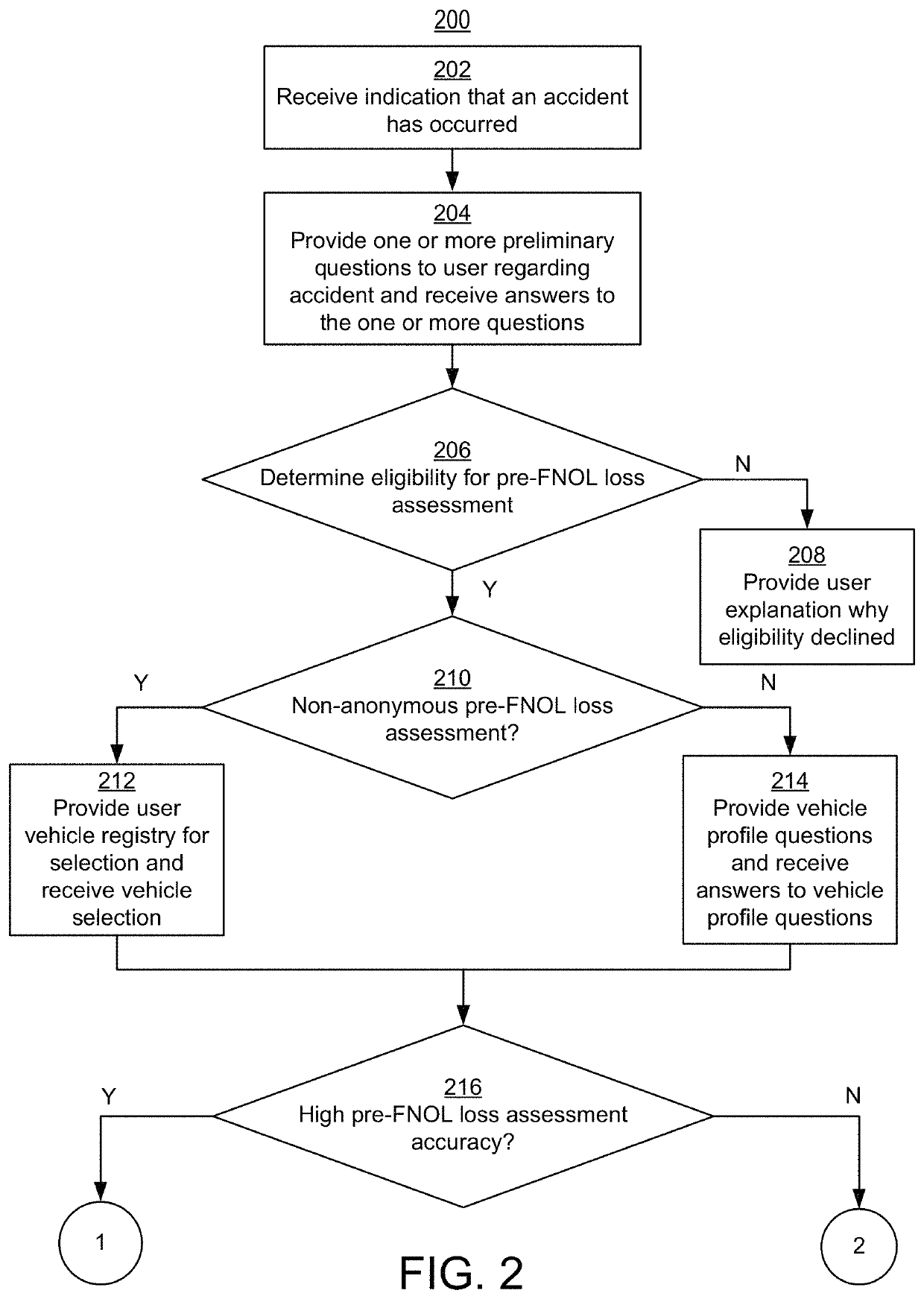
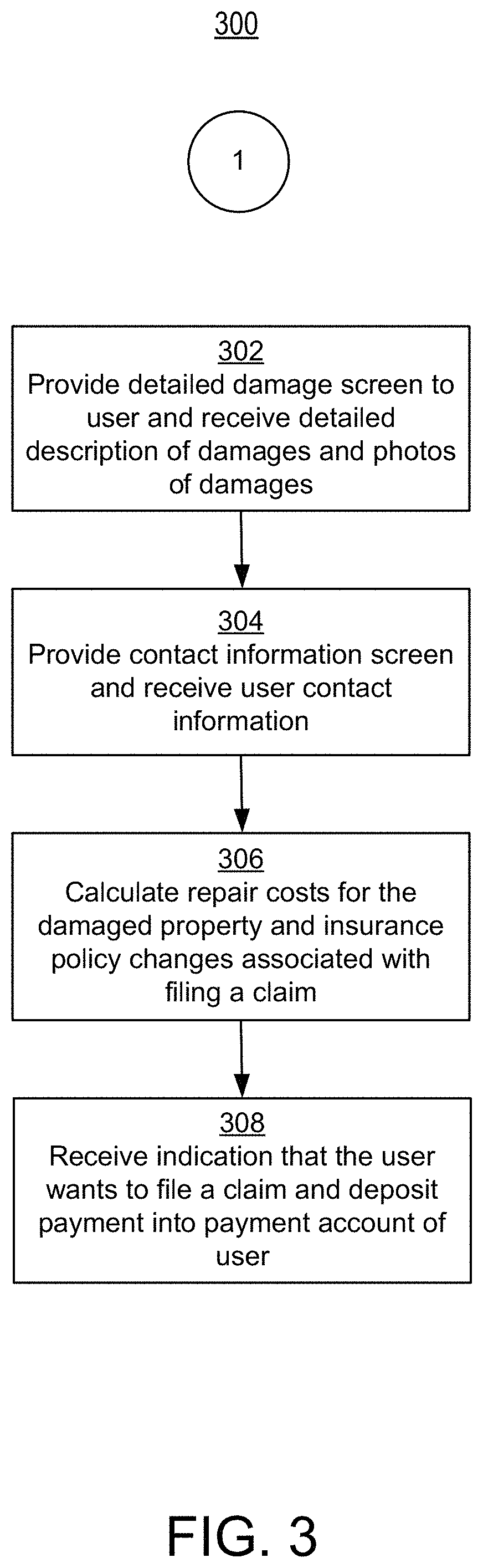
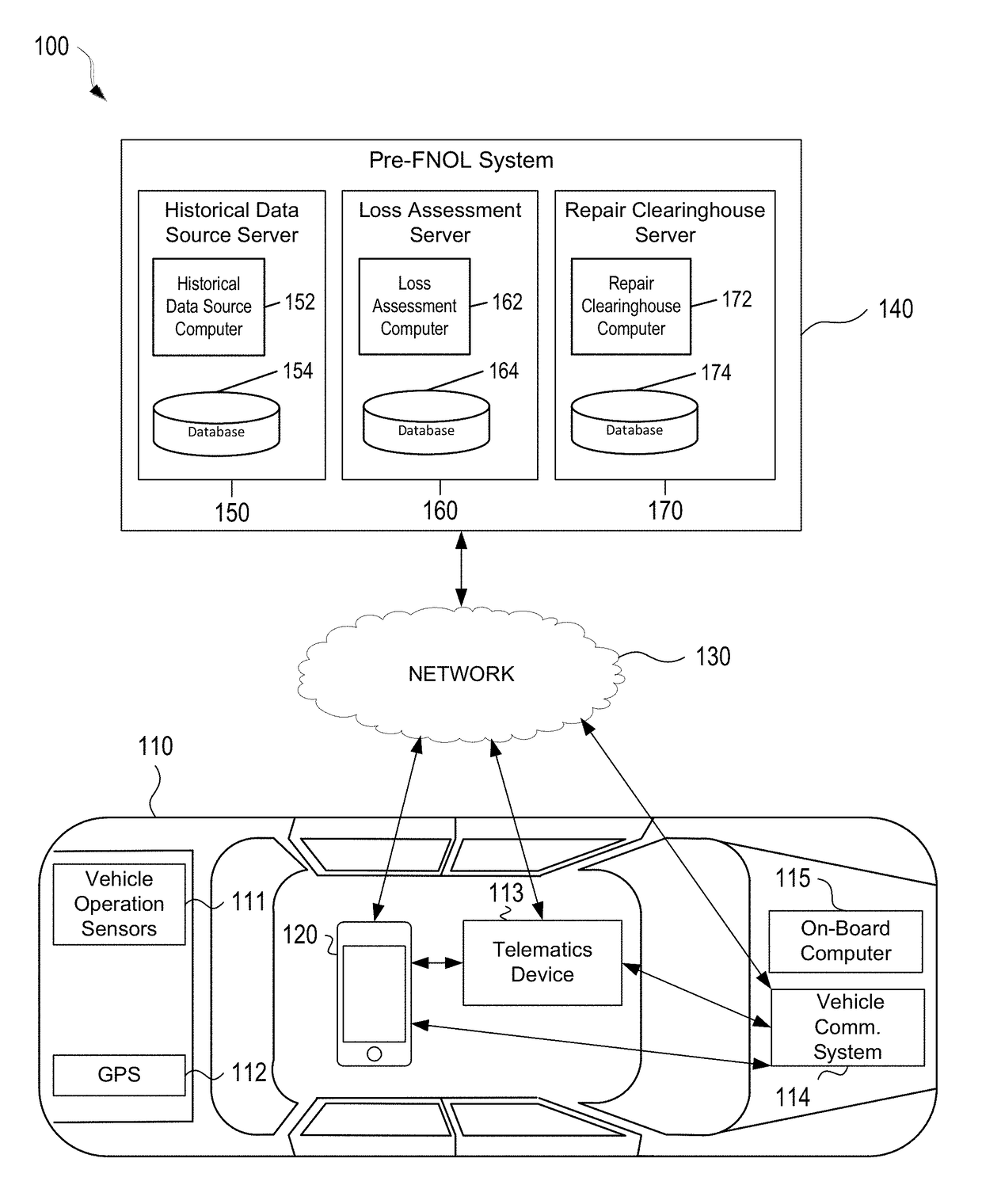
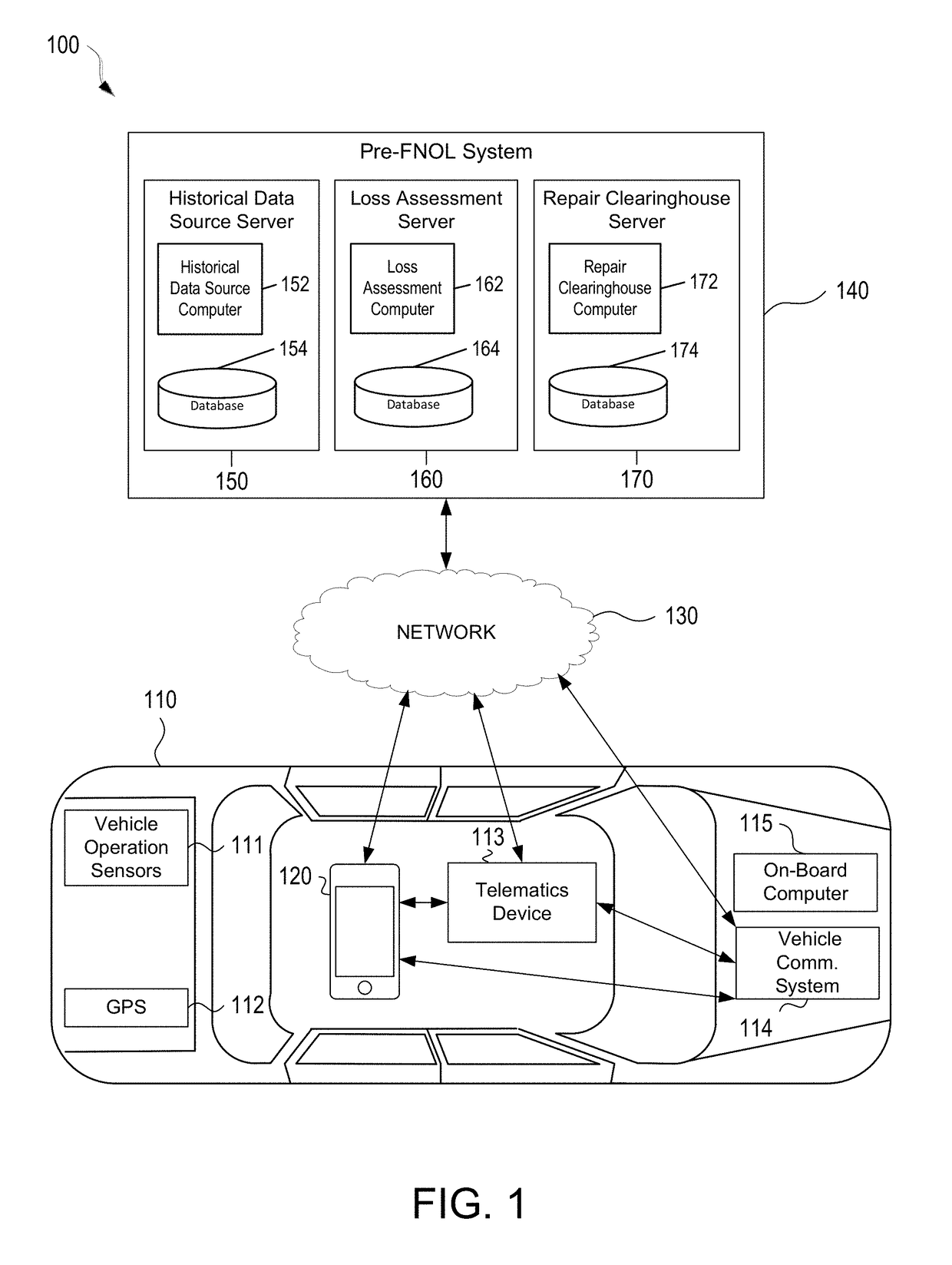
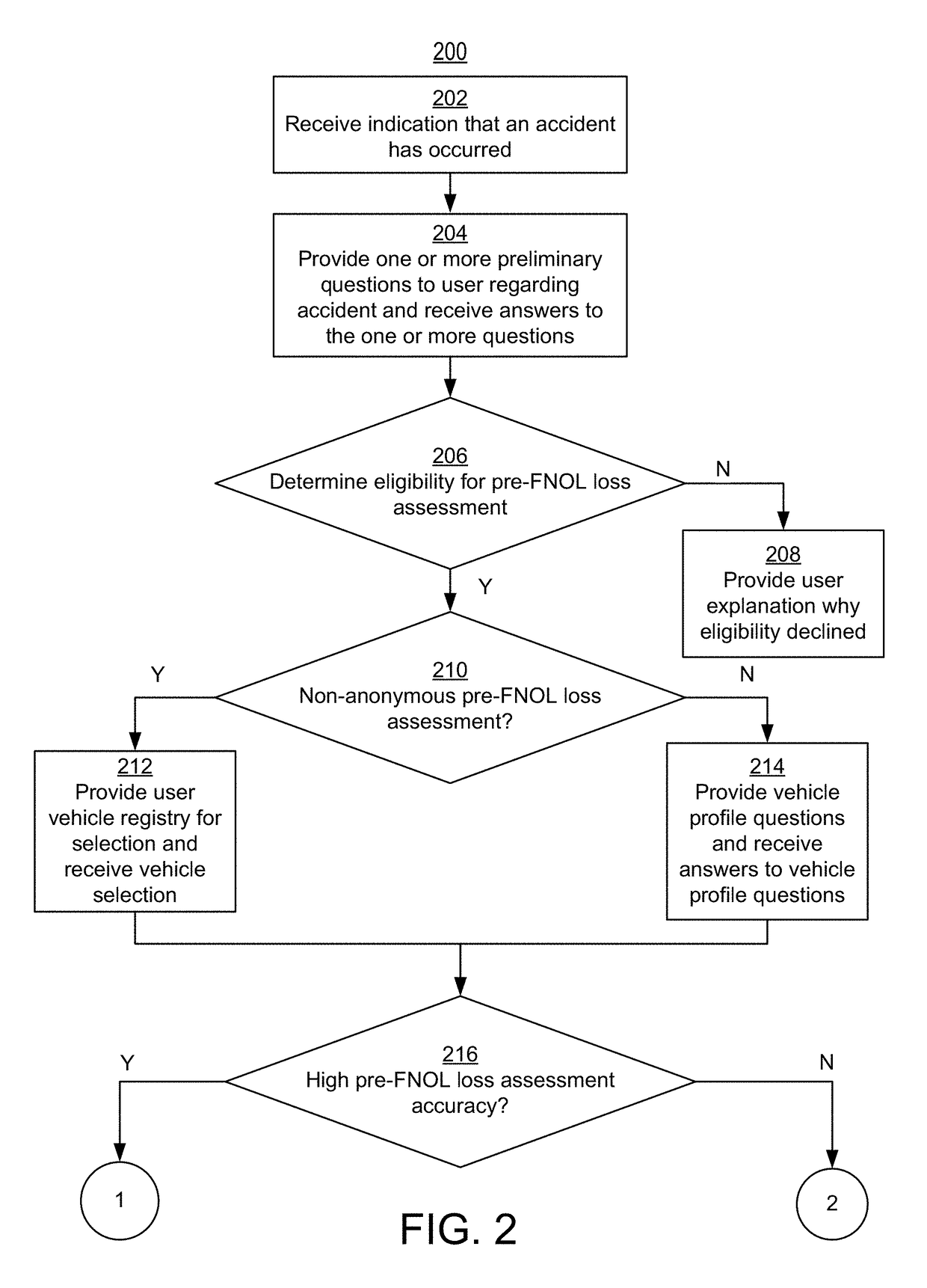
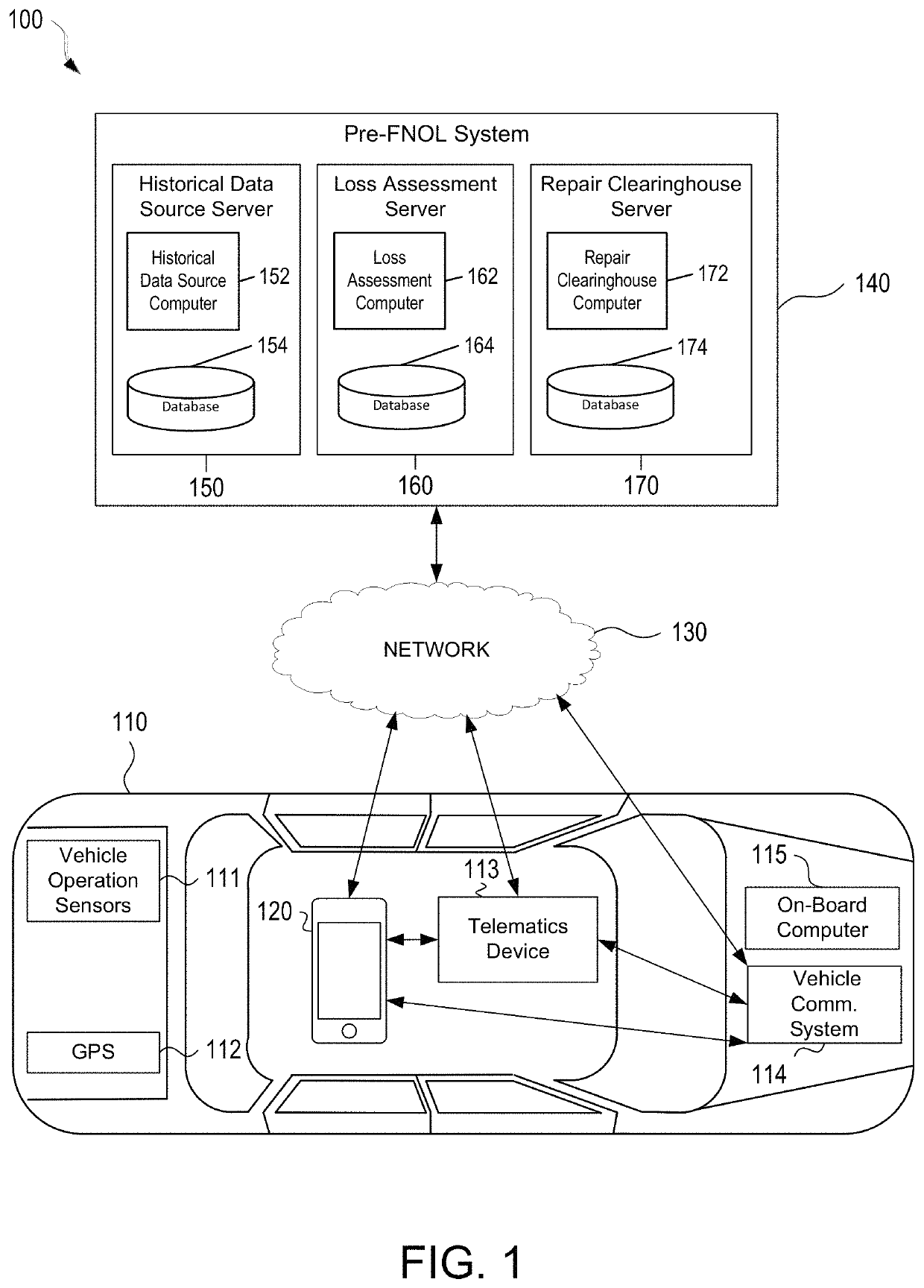
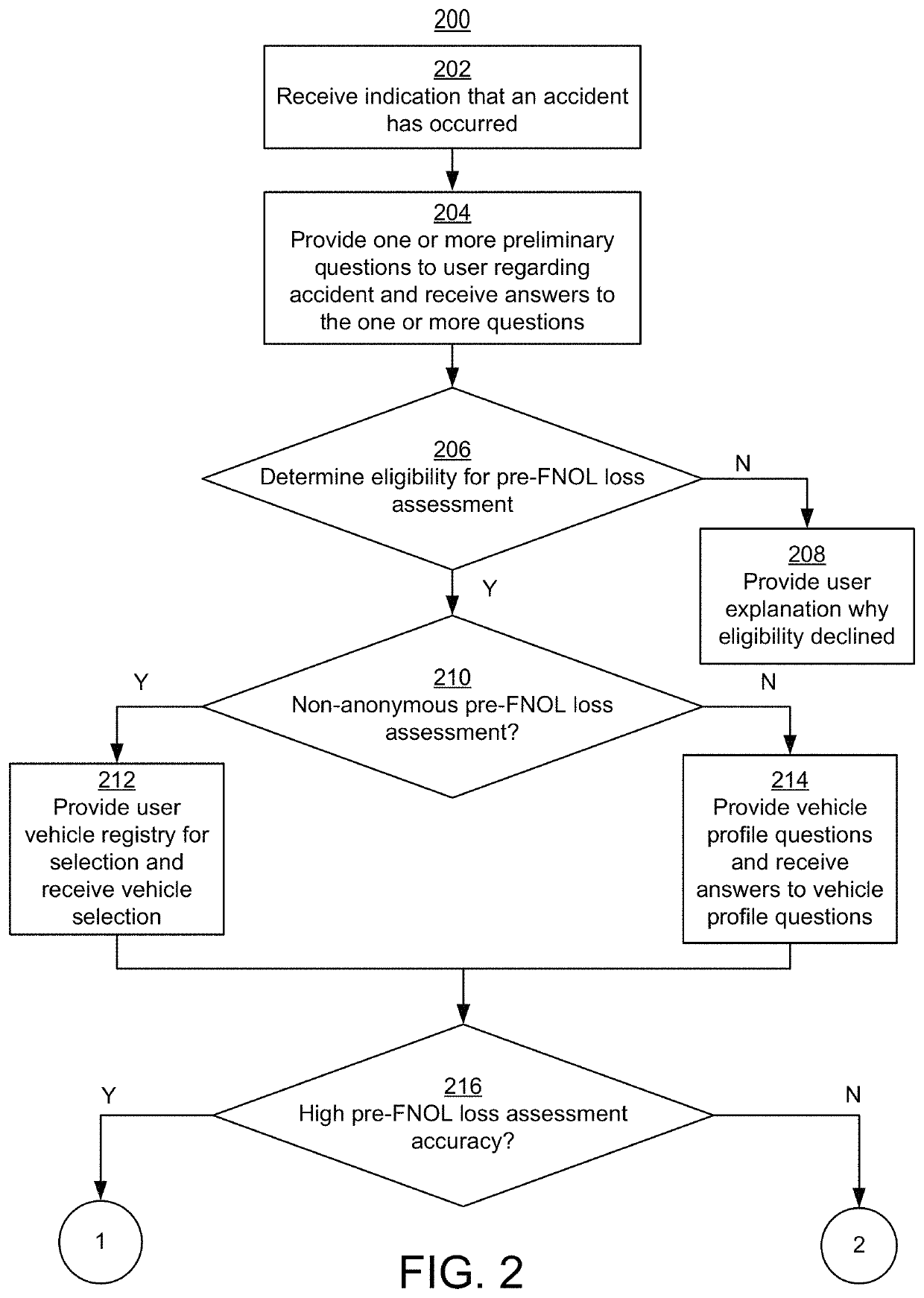
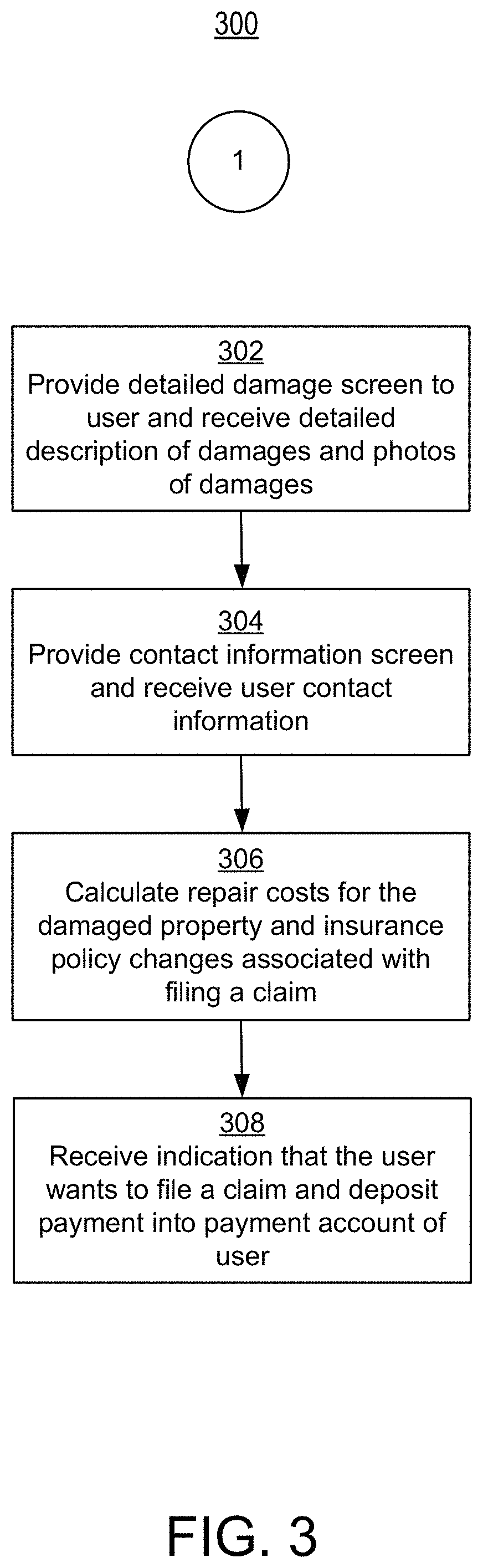
Enhanced Image Capture and Analysis of Damaged Tangible Objects
ActiveUS20180082379A1Facilitate repair agreementFinanceStatic indicating devicesTangible objectComputer science
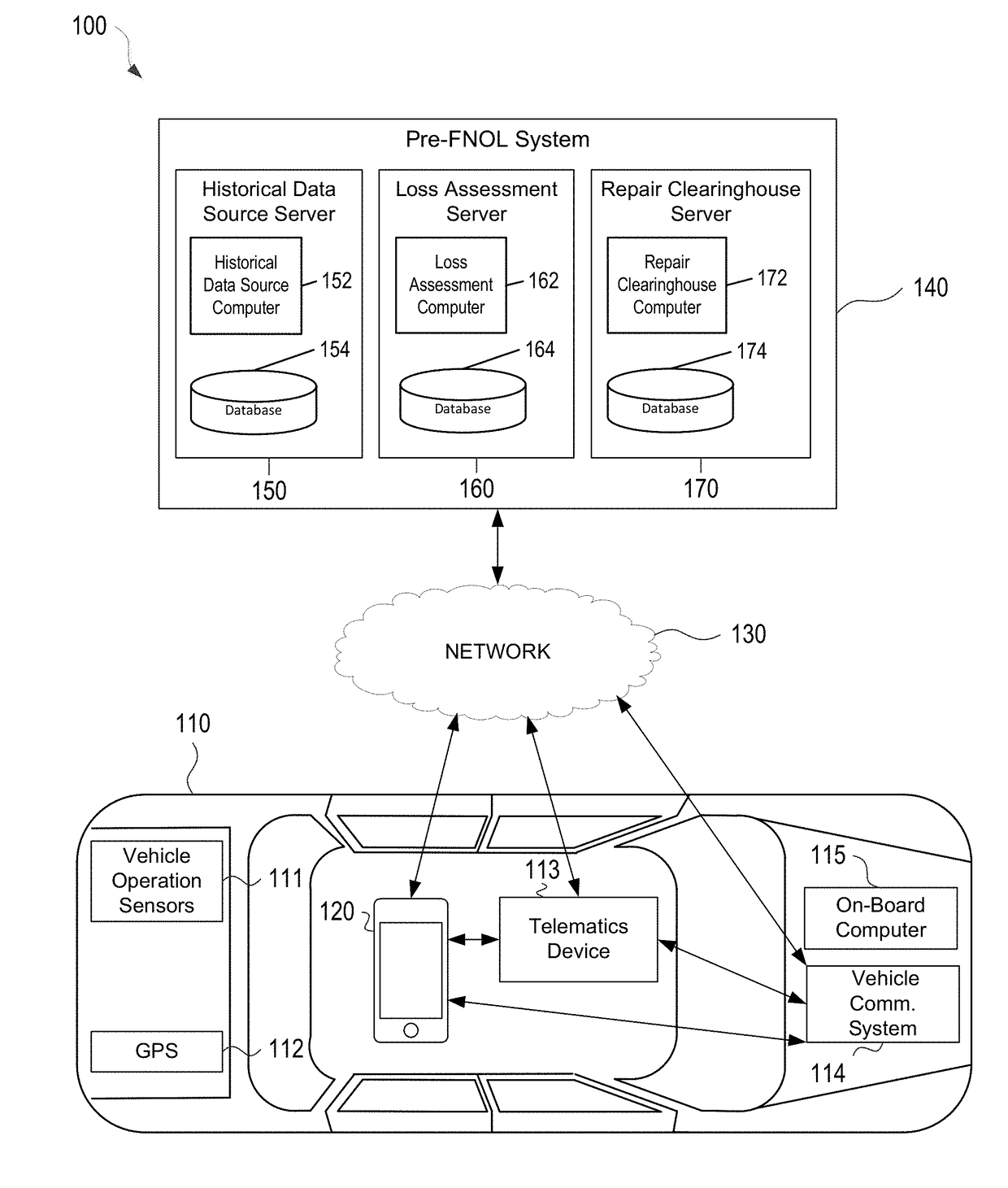
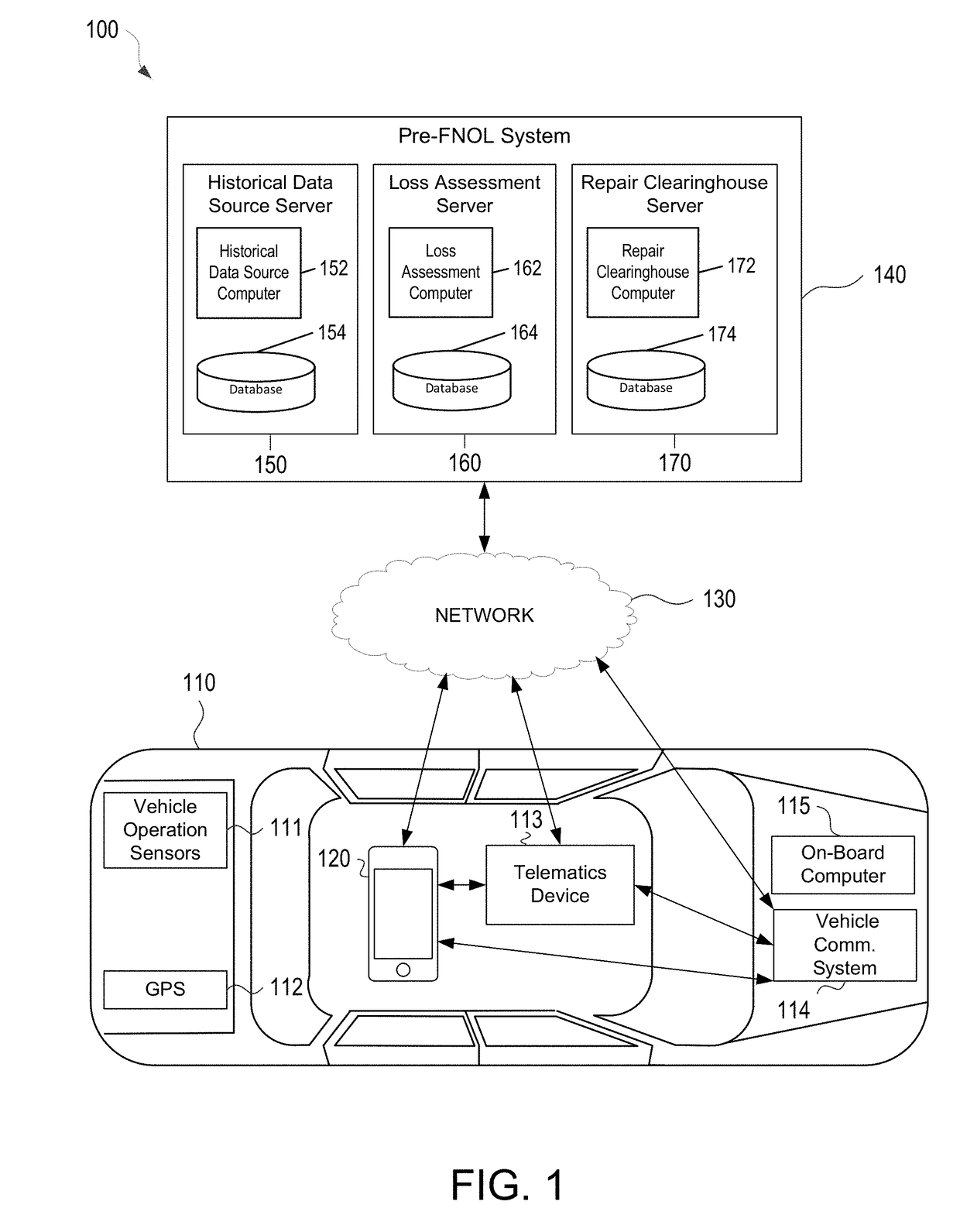
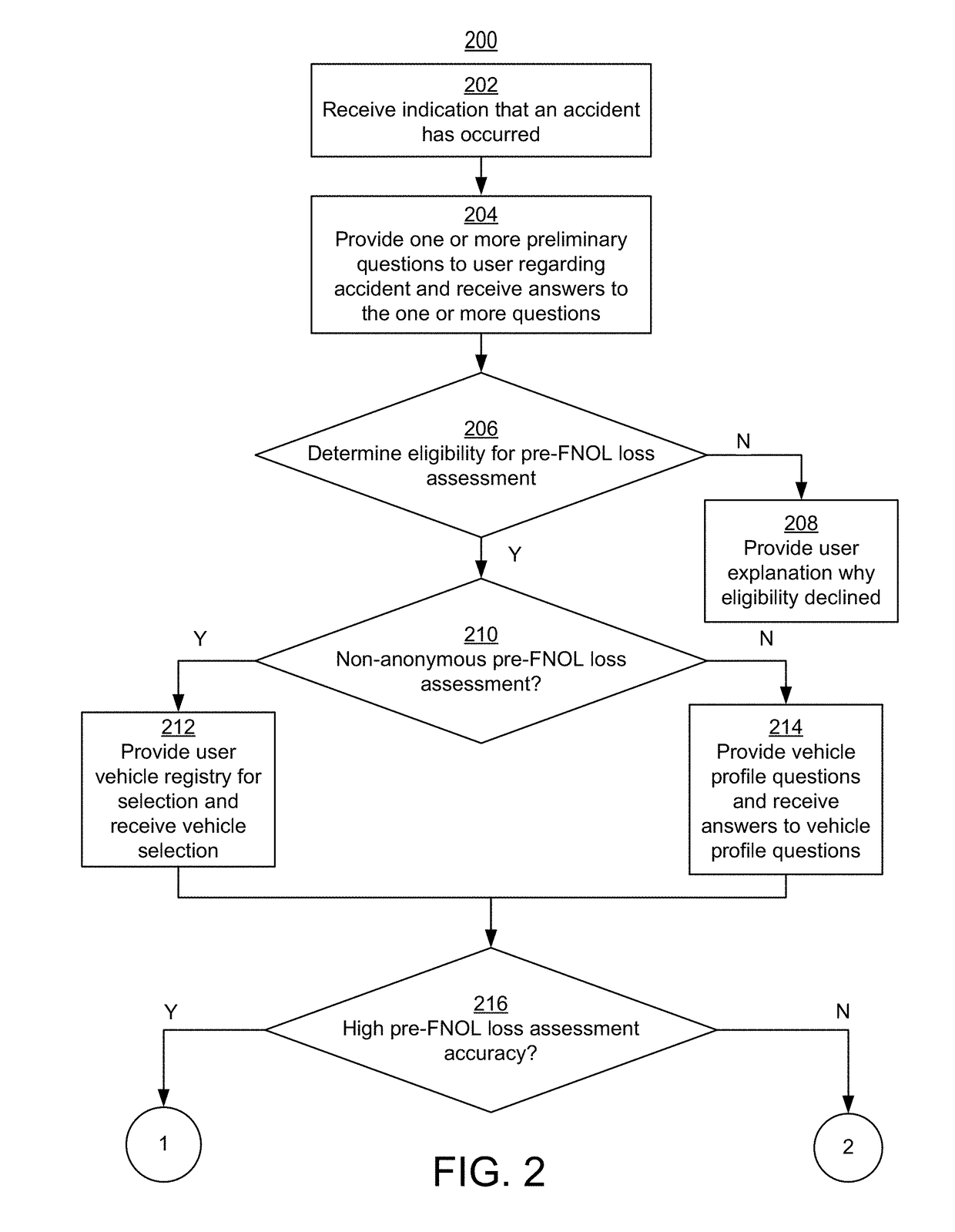
Apparatuses, systems, and methods are provided for the usage of enhanced pictures (e.g., photos) of tangible objects (e.g., property, cars, etc.) damaged in an accident and answers to questions about the accident to better assess the effect of the damage (e.g., repair expenses and accompanying changes to an insurance policy). A pre-FNOL system may receive responses to one or more questions regarding an accident and one or more enhanced pictures of the tangible property damaged in the accident. The pre-FNOL system may use the responses to the one or more questions and the one or more enhanced pictures to determine repair costs associated with the damaged property and accompanying changes to the insurance policy if an insurance claim were to be filed to cover the determined repairs costs.
Owner:ALLSTATE INSURANCE
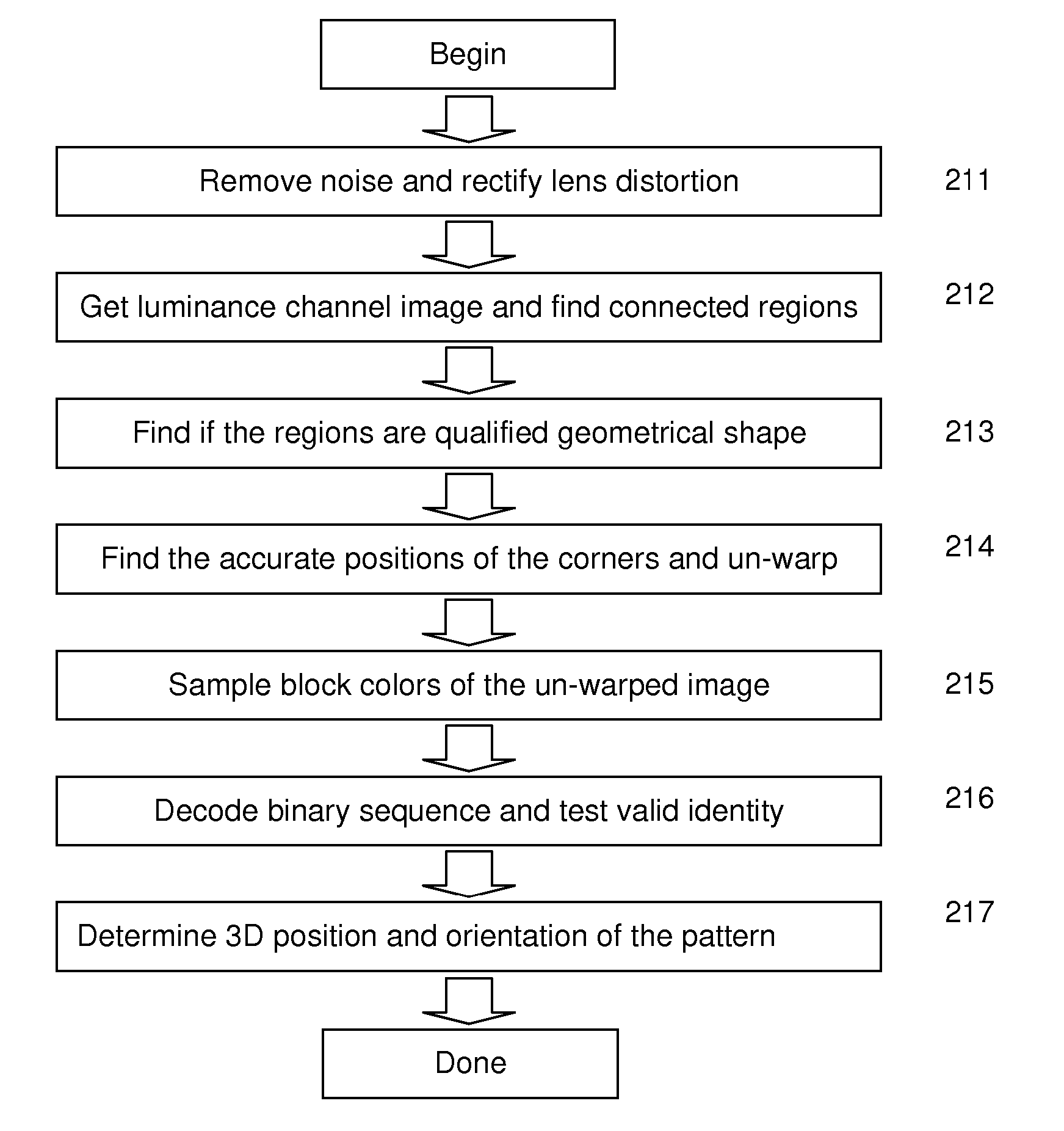
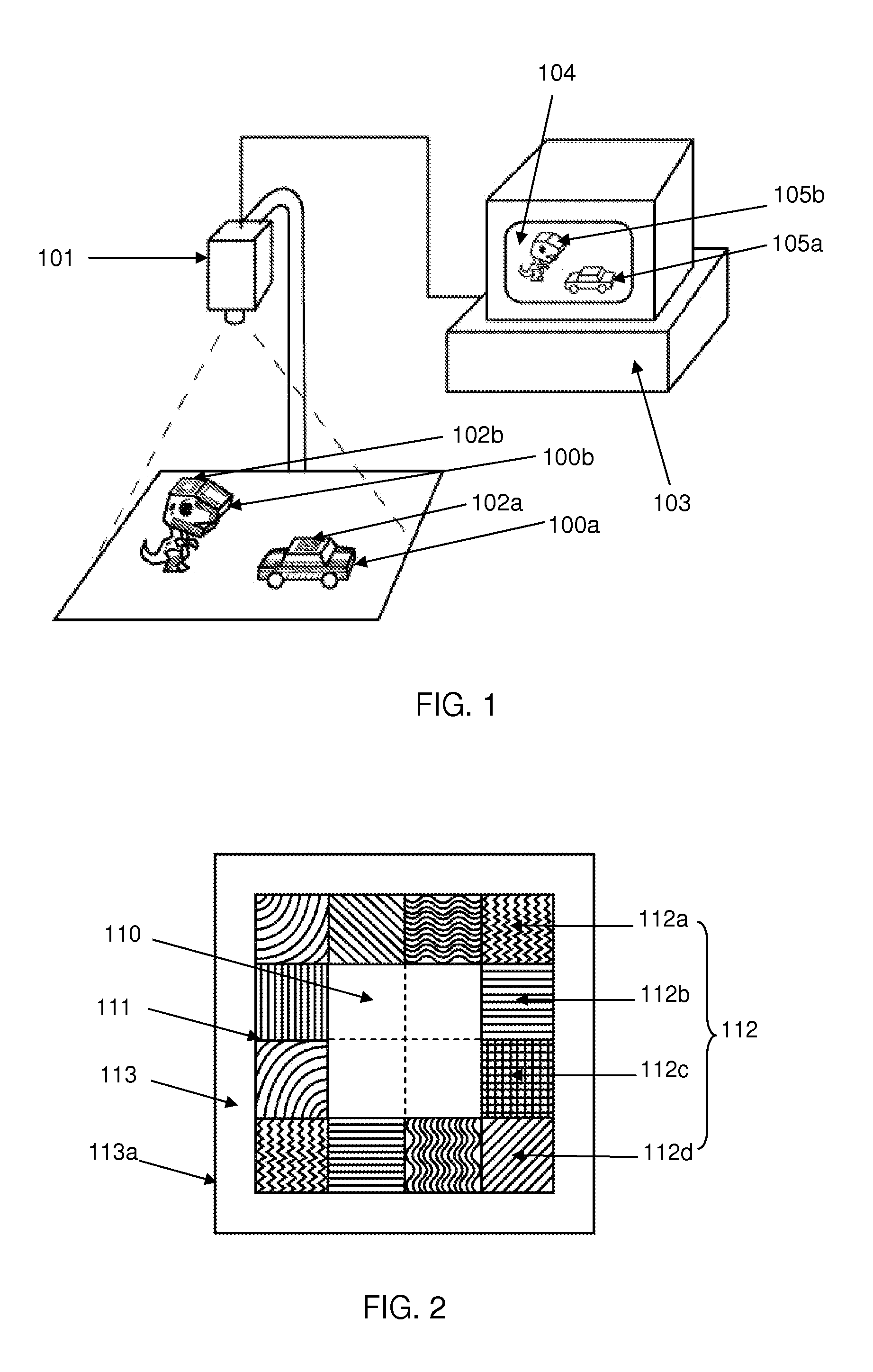
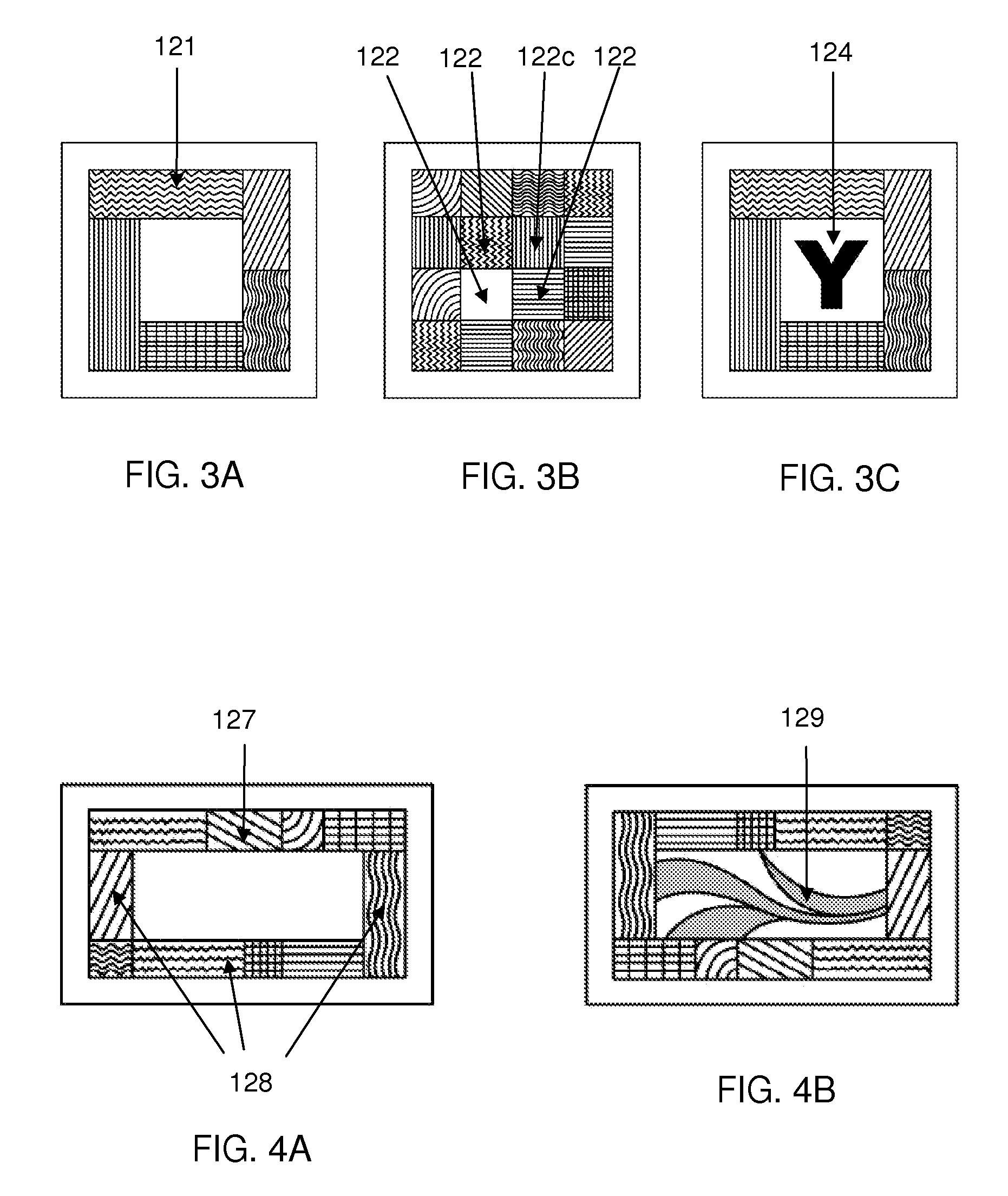
Video image based tracking system for identifying and tracking encoded color surface
InactiveUS20080101693A1Increases data bitIncrease the number ofCharacter and pattern recognitionTangible objectDegrees of freedom
A video image based tracking method and apparatus for identifying and tracking encoded color surface. Encoded color patterns are integrated with tangible objects such as tangible toys or tangible input objects so that they can be used as a tangible input device for a computing system to control virtual multimedia objects and trigger game interactions. The color pattern within the field of sight of a video image capturing device is identified and tracked and by a computing system. Method to configure the color pattern is included. A great number of encoded patterns can be created. Method to identify the encoded color pattern is included. Method to estimate the 6-DOF (degree-of-freedoms) orientation and coordinates information of the tangible object with encoded color pattern is included. Multiple encoded color patterns can be identified and tracked simultaneously. Tangible toys or tangible input objects configured with encoded color patterns can retain their color identity while capable of being identified and their 6-DOF orientation and coordinates tracked by the computing system.
Owner:INTELLIGENCE FRONTIER MEDIA LAB
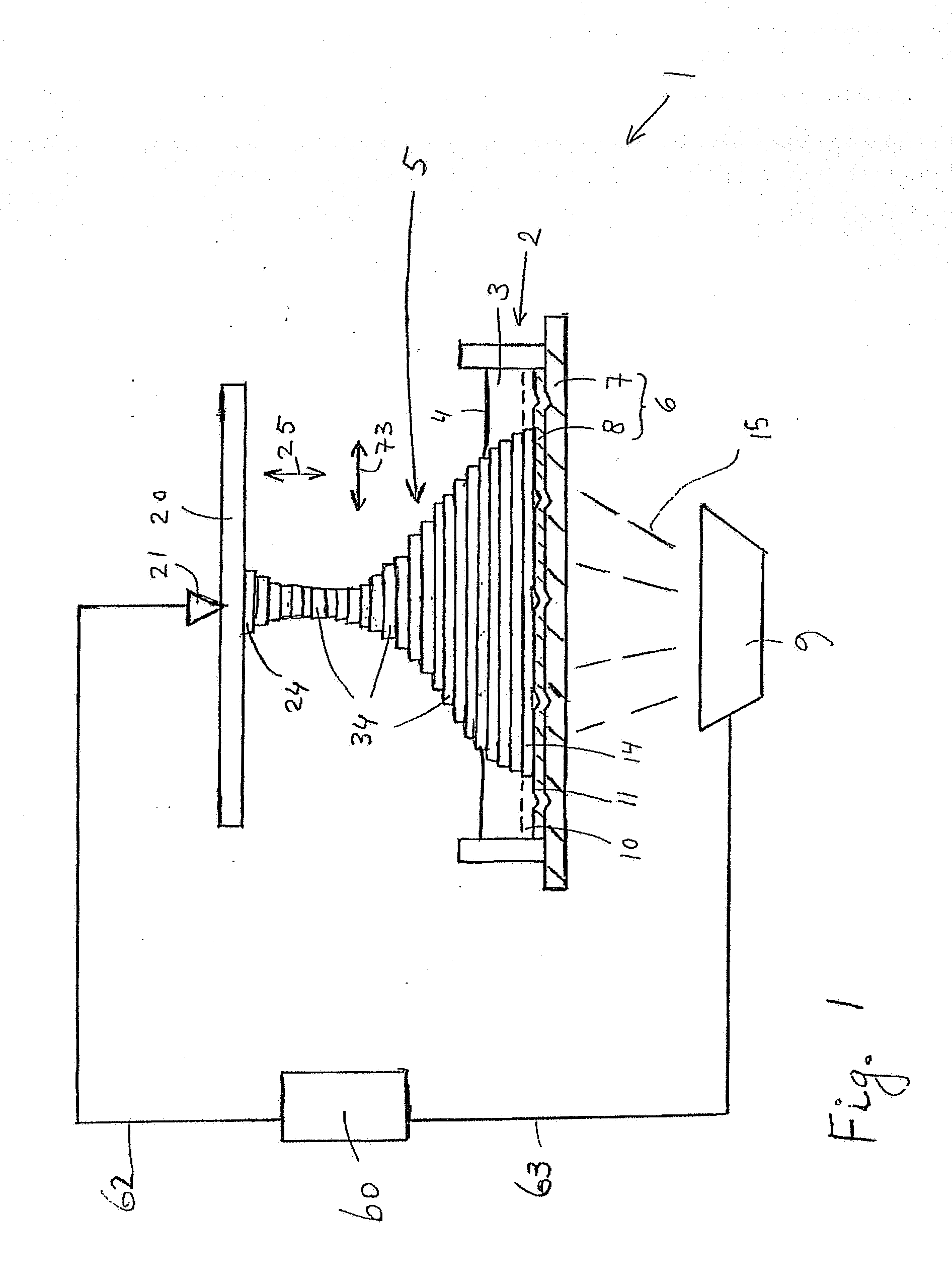
System and method for producing a tangible object
ActiveUS20090289384A1Rapid productionShorten the time periodMeasurement/indication equipmentsAuxillary shaping apparatusObject basedTransformer
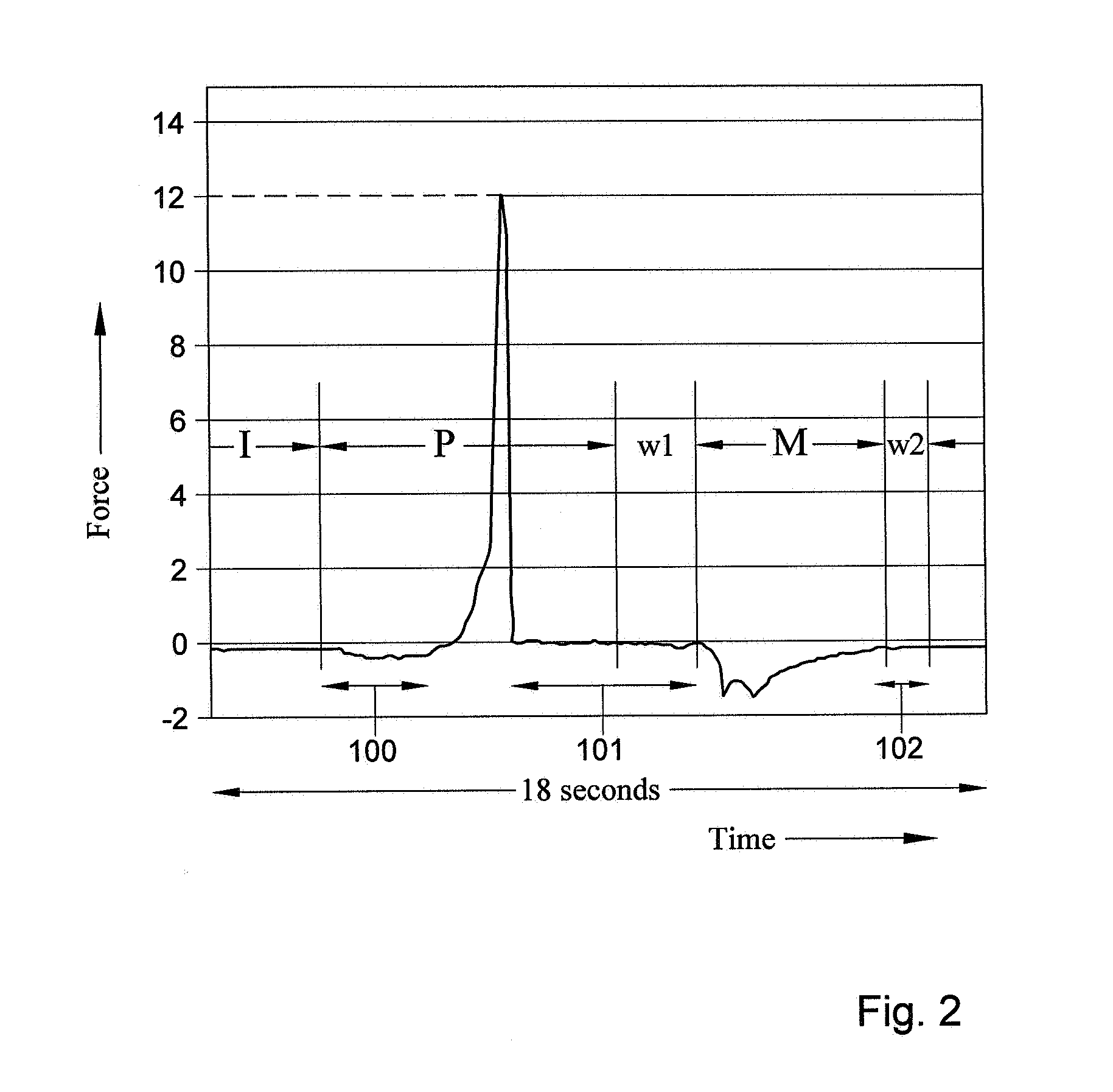
A system for producing a tangible object. The system has a space which can be filled with a fluid. A reference platform at least partially defines at least one side of the space. The system further has a phase-transformer which can form a layer of the object by selectively transforming the fluid into a solid in a predetermined area of the space. An actuator can separate the layer from the reference platform by moving the layer relative to the reference platform or vice versa. The system has a controller connected with an actuator control output to the actuator and / or with a transformer control output to the phase transformer. The controller can control the production of the object based on a determined value of the force exerted on the reference platform or the solid or of a parameter related to the force.
Owner:NEDERLANDSE ORG VOOR TOEGEPAST-NATUURWETENSCHAPPELIJK ONDERZOEK (TNO)
Method and apparatus for uniquely and authoritatively identifying tangible objects
InactiveUS20060107058A1Alteration can be preventedAvoid readingDigital data processing detailsUser identity/authority verificationDigital signatureTangible object
A smart chip protection system contains a unique public / private identity key pair and uses a separate public / private signature key pair. The identity private key is stored in permanent, secure storage such that it can not be read outside the chip. An issuing entity generates a descriptor containing the identity public key, attribute data, and a digital signature. The digital signature is generated by enciphering a derivation of the identity public key and the attribute data with the signature private key known only to the issuer. The authenticity of the descriptor data is verified by decrypting the signature with the signature public key using a known algorithm, and comparing the result to the derivation of the descriptor data. The identity of the object can be verified requesting the smart chip ro perform an encryption / decryption operation using its identity private key, and performing the complement using the public key.
Owner:IBM CORP
Enhanced image capture and analysis of damaged tangible objects
ActiveUS10902525B2Facilitate repair agreementFinanceStatic indicating devicesTangible objectEngineering
Owner:ALLSTATE INSURANCE
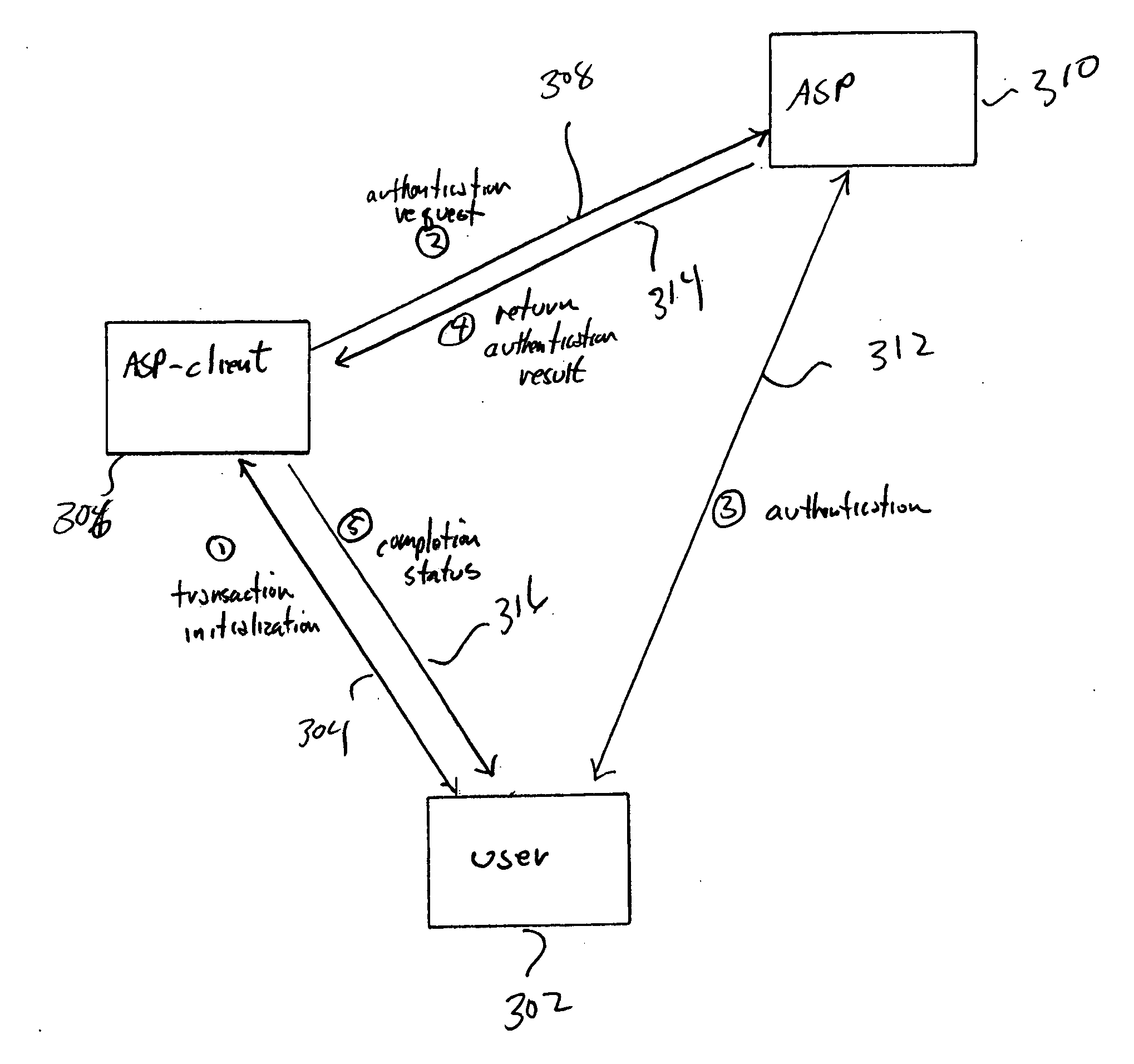
Method and system for user-controlled, strong third-party-mediated authentication
ActiveUS20070016527A1Strong authenticationFinanceUser identity/authority verificationThird partyTangible object
Various embodiments of the present invention provide strong authentication of users on behalf of commercial entities and other parties to electronic transactions. In these embodiments of the present invention, a user interacts with an authentication service provider to establish policies for subsequent authentication of the user. Thus, in these embodiments of the present invention, a user controls the level and complexity of authentication processes carried out by the authentication service provider on behalf of both the user and commercial entities and other entities seeking to authenticate the user in the course of conducting electronic transactions, electronic dialogues, and other interactions for which user authentication is needed. The policies specified by a user may include specification of variable-factor authentication, in which the user, during the course of an authentication, provides both secret information as well as evidence of control of a tangible object.
Owner:SMART AUTHENTICATION IP LLC
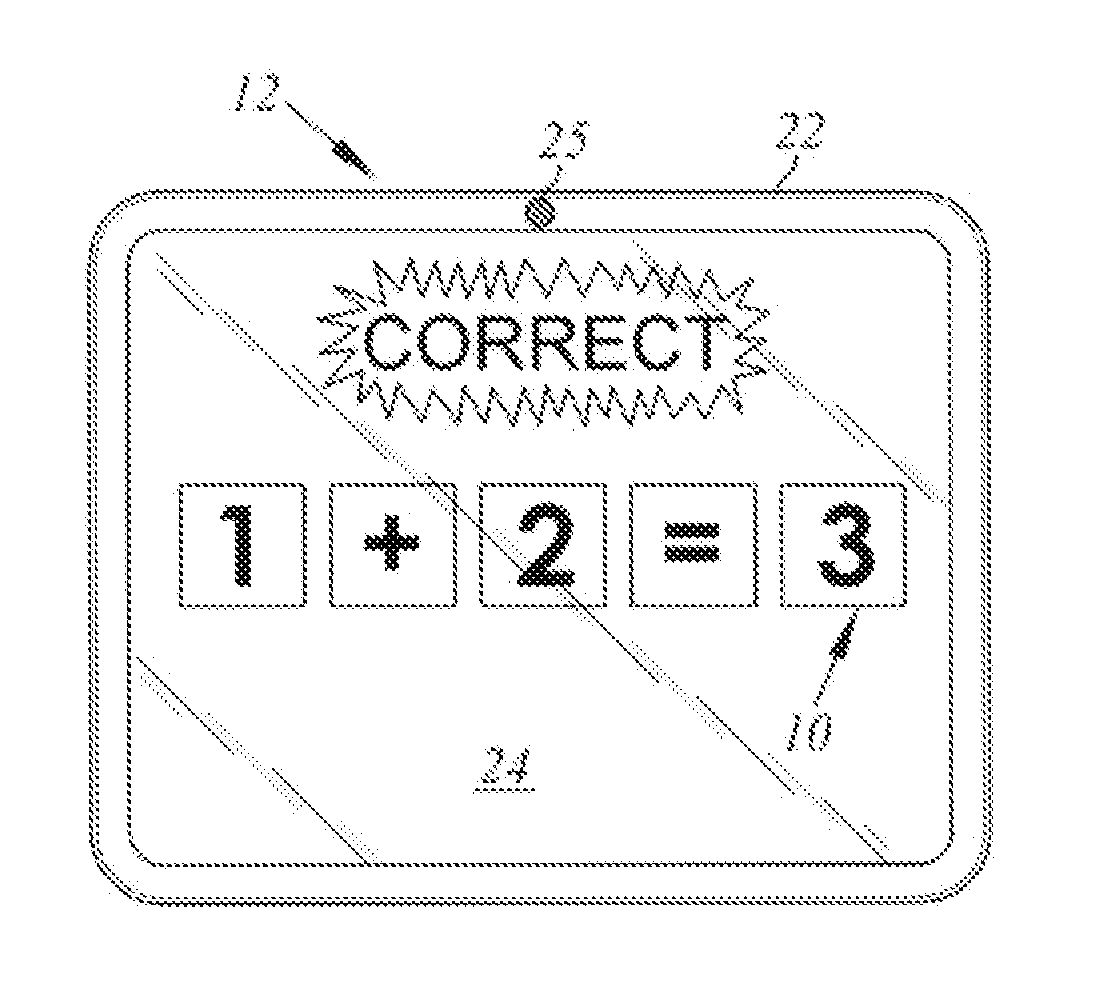
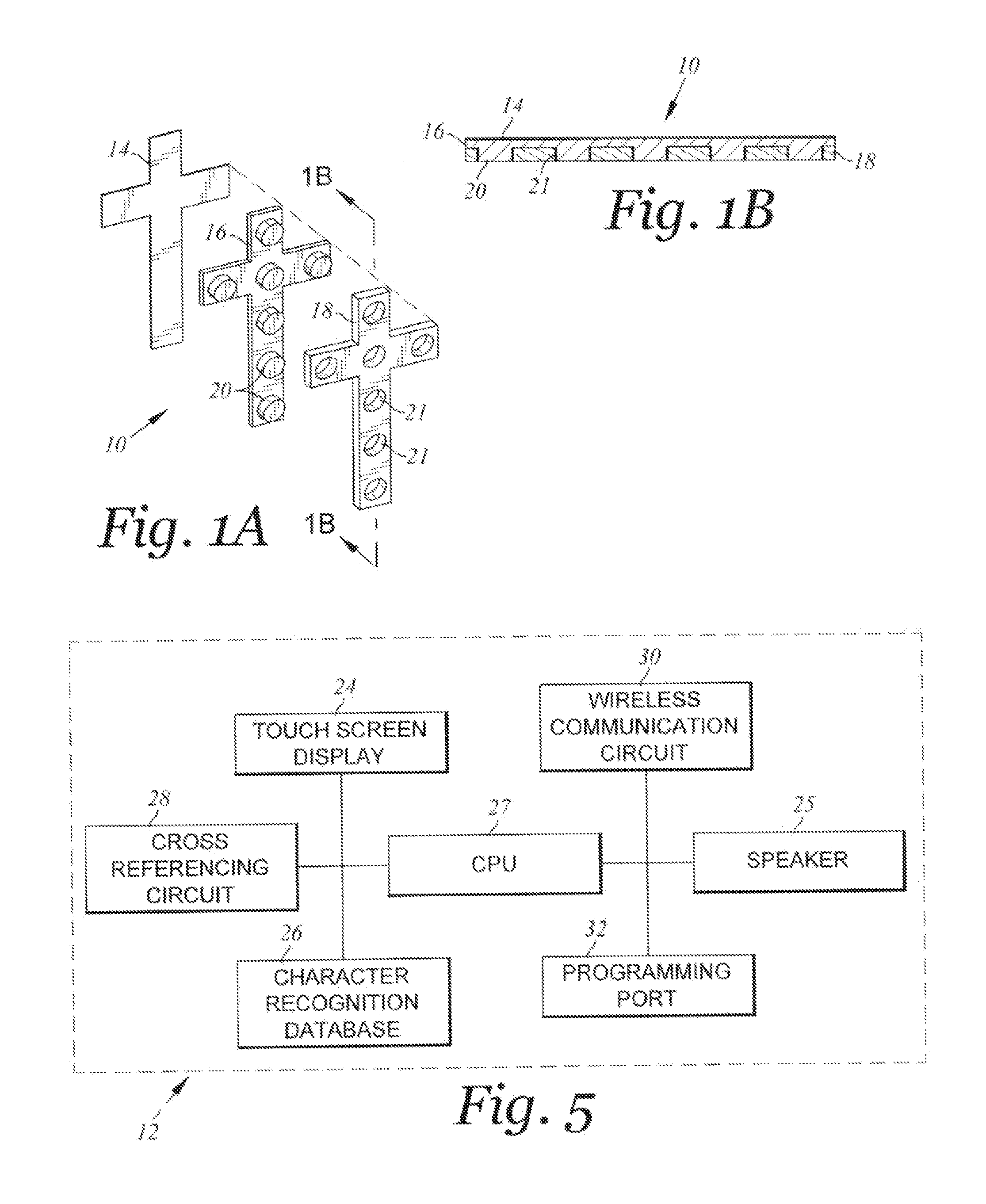
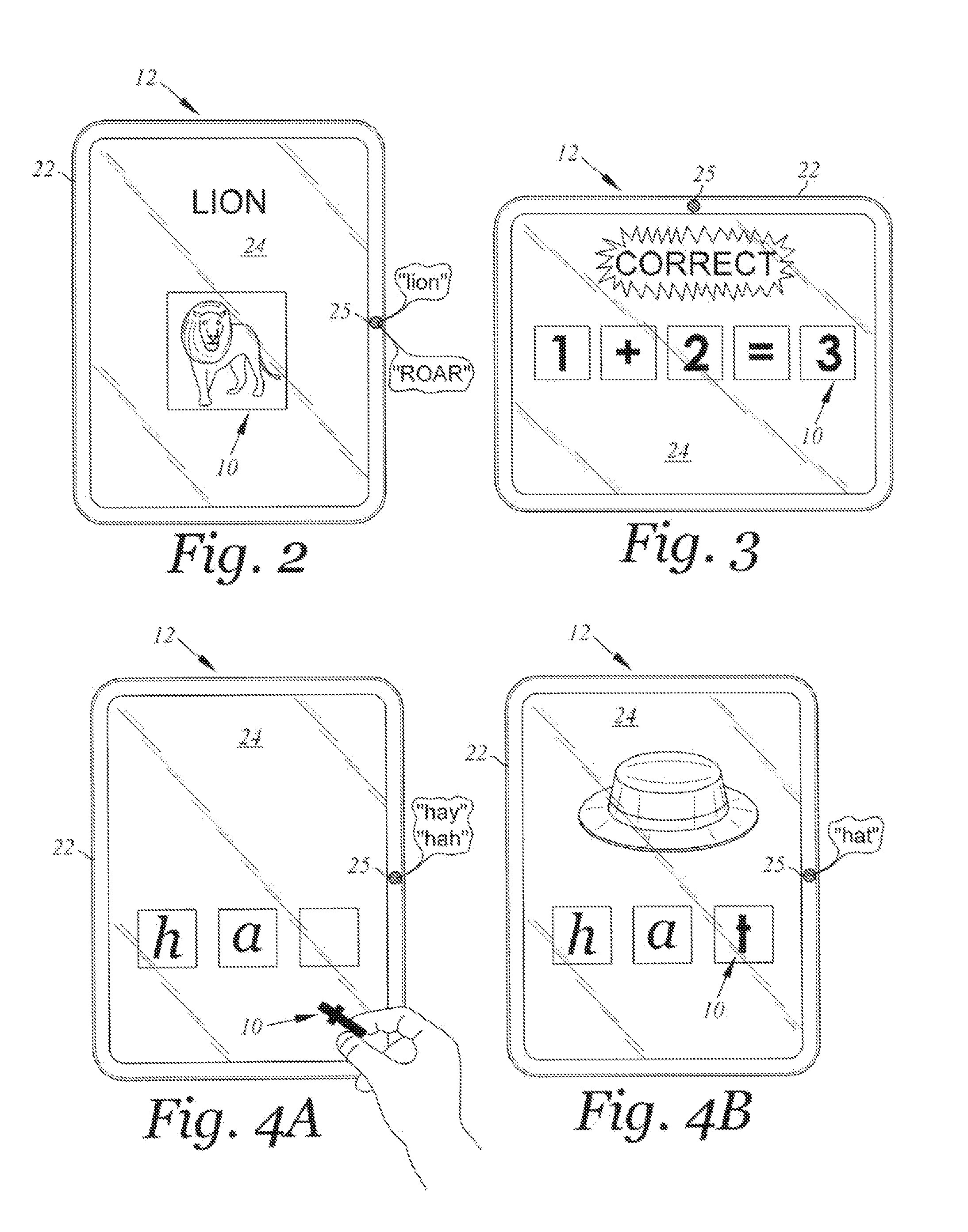
Tangible alphanumeric interaction on multi-touch digital display
InactiveUS20140168094A1Improve experienceInput/output for user-computer interactionGraph readingTangible objectDisplay device
A method and system of using a tangible object with a with screen display device to enhance a user's experience while operating the touch screen display device. The tangible object may be placed oaths touch screen display device by the user and the unique attributes may be detected by the touch screen display device's built-in detection / sensing capabilities and processed as an input to a program or app. running on the touch screen display device. In this regard, various aspects of the present invention are directed toward providing a tangible feature to touch screen display operation to provide a more interactive experience when using a touch screen display, especially for young children.
Owner:MILNE ROBIN DUNCAN +1
Method and system for managing rights in digital information over a network
InactiveUS20060078112A1Less expensiveLow costDigital data processing detailsTelevision systemsTangible objectNetwork management
Owner:NOKIA TECH OY
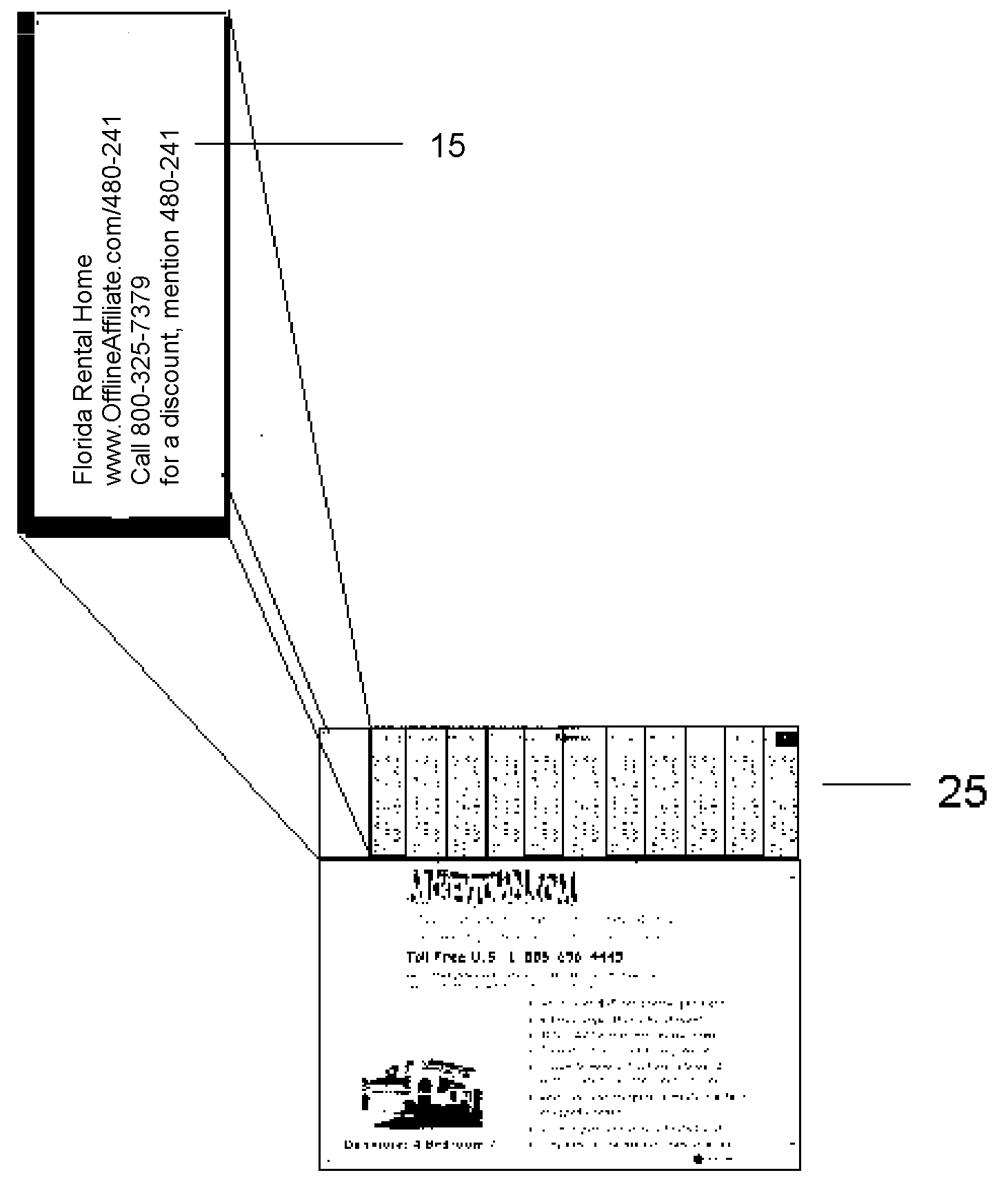
Interactively create uniquely Identified Tangible Print Advertising from Internet Web Pages
InactiveUS20050171837A1AdvertisementsSpecial data processing applicationsPrint versionTangible object
The current invention is a method for bridging the gap between the virtual multimedia-based Internet world and the physical world of tangible object media, such as print advertising. More particularly, a method for multimedia-based Internet Advertisers to expand the promotion of their products and web pages by encouraging Affiliates to post uniquely identified printed versions of the virtual advertising to be posted or otherwise physically distributed in the tangible world.
Owner:EGLINTON CHARLES
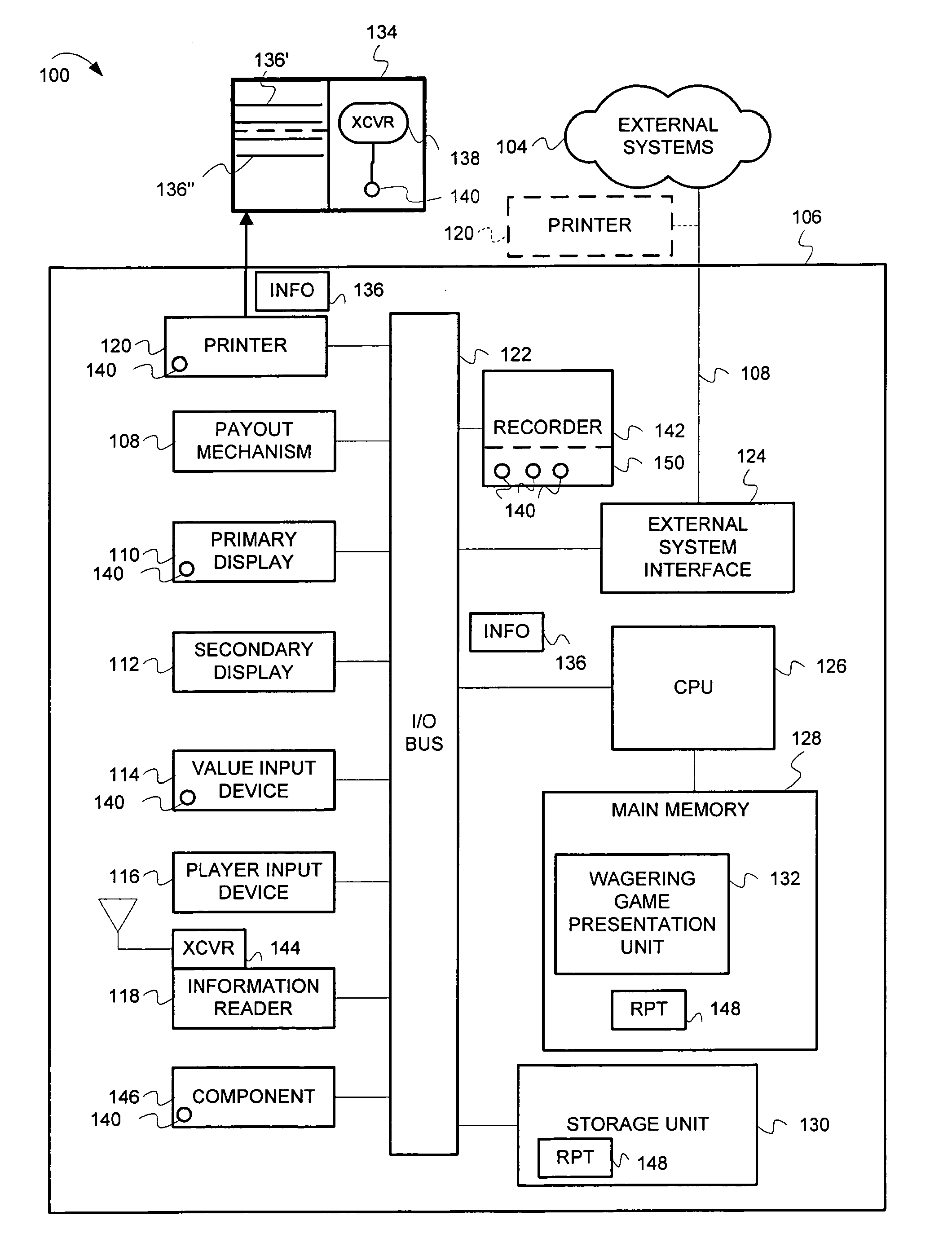
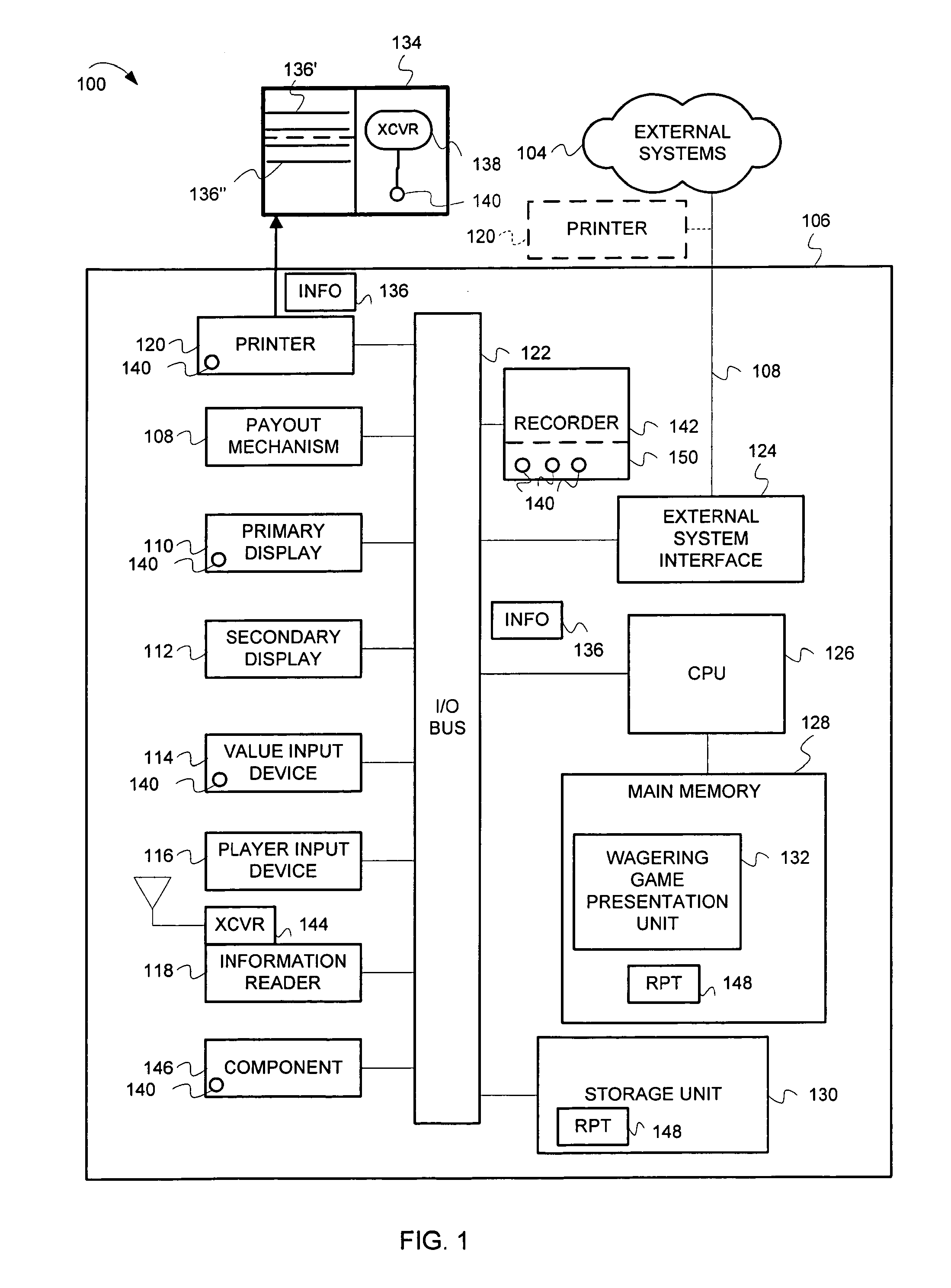
Wagering game machine information exchange
InactiveUS20100069145A1Apparatus for meter-controlled dispensingVideo gamesTangible objectMonetary value
Apparatus, systems, and methods may operate to receive information associated with a wagering game machine capable of engaging in the process of presenting a wagering game upon which monetary value may be wagered, print a first portion of the information in human perceivable form on a tangible object, such as a wagering game machine ticket, and record a second portion of the information in a wireless memory device to be attached to the wagering game machine ticket. Other apparatus, systems, and methods are disclosed.
Owner:BALLY GAMING INC
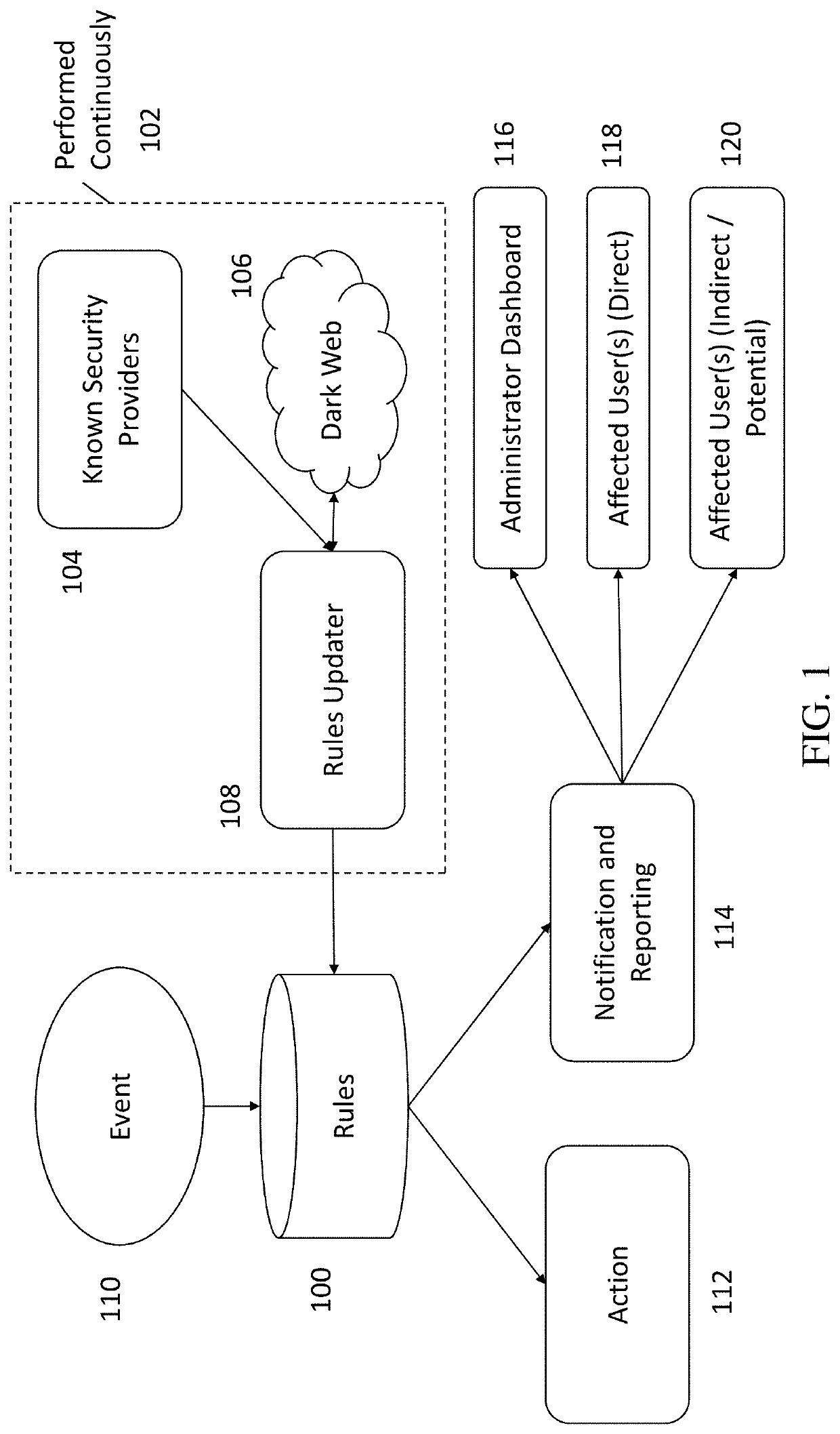
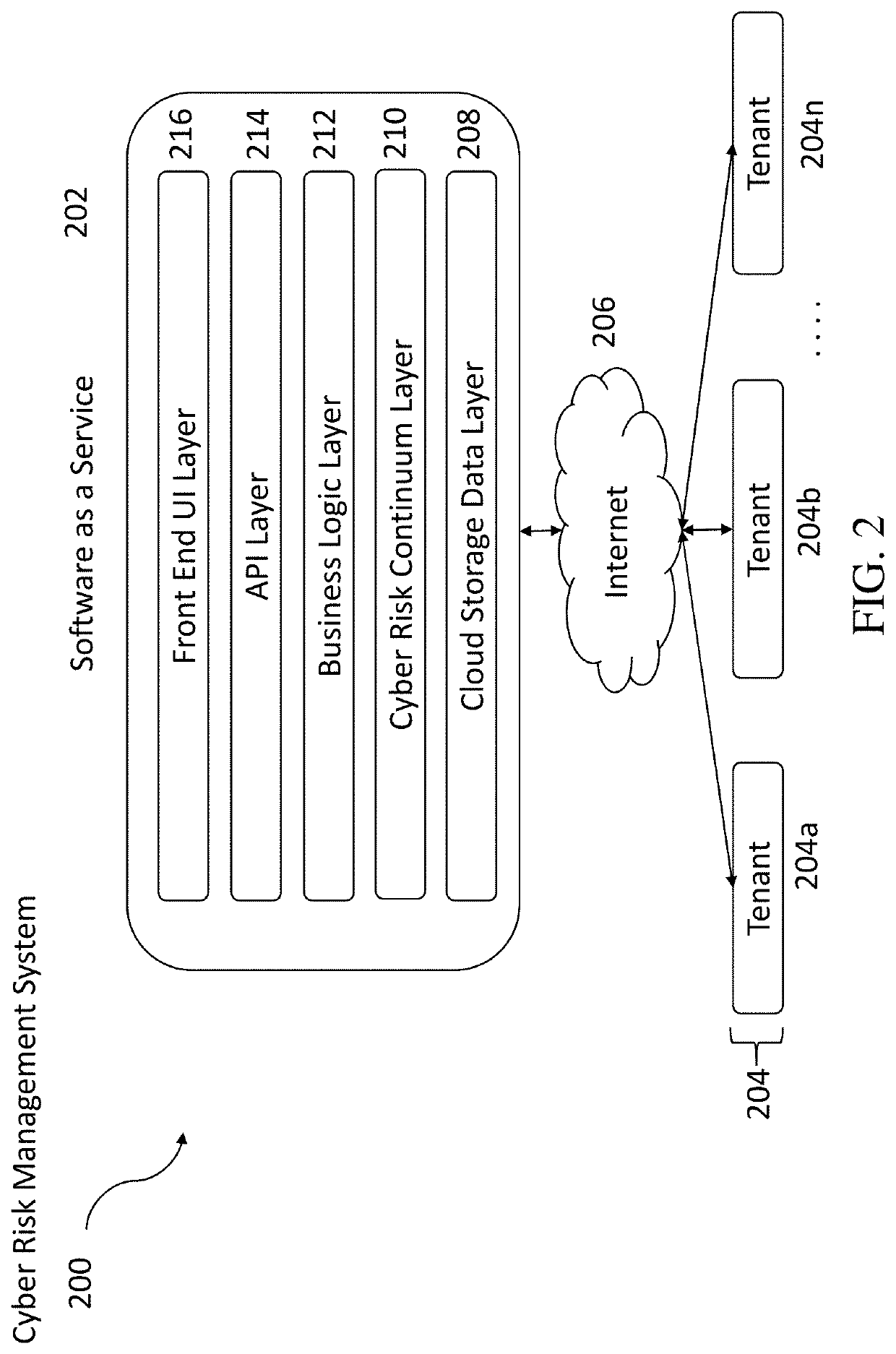
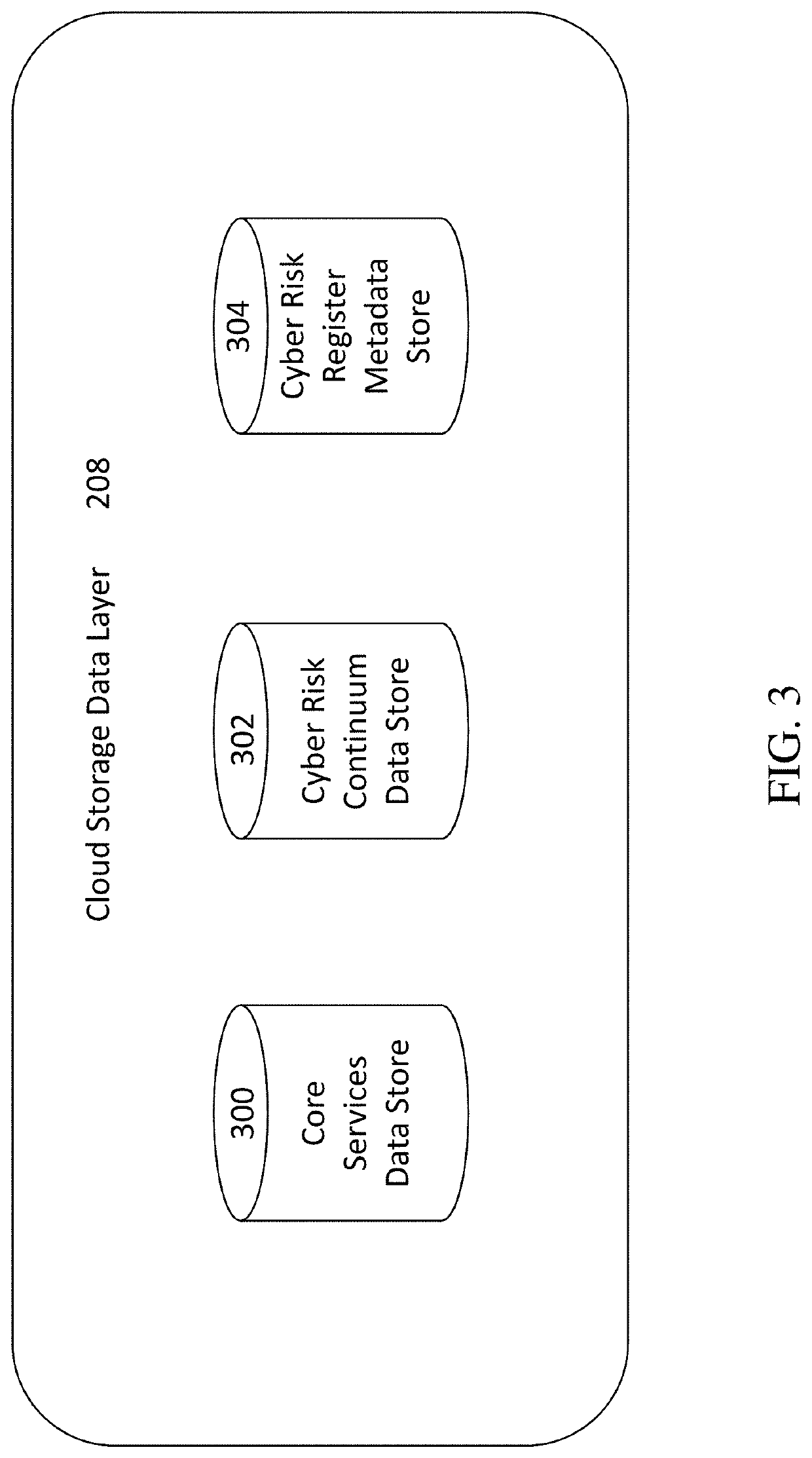
Methods, systems, and computer program products for continuous cyber risk monitoring
The subject matter described herein includes methods, systems, and computer program products for a software as a service (SaaS) system for continuous cyber risk management and monitoring. The method includes storing, maintaining, and updating one or more rules that associates a cyber risk, threat, or vulnerability with an action for one or more assets. The one or more assets includes at least one of: information systems, critical infrastructure, tangible objects, persons, data, and metadata. When an event is detected, it is determined whether a rule applies to the event by searching and matching information associated with the event with the one or more rules. If a rule applies, an action may be performed and various users notified. The action performed includes a corrective, remedial, or mitigating action as specified by the applicable rule. The method for continuous cyber risk management and monitoring described herein are performed automatically and continuously.
Owner:OLYMPUS INFOTECH LLC
Method and system for layerwise production of a tangible object
ActiveUS20090236778A1Reduce differential pressureEasy to separateMouldsConfectioneryLiquid layerTangible object
A method cycle of a method for layerwise production of a tangible object (5) comprises the successive steps of: solidifying a predetermined area of a layer (10) of a liquid (3), said liquid layer adjoining a construction shape (6), so as to obtain a solid layer (14) having a predetermined shape; separating said solid layer from said construction shape; and moving the separated solid layer and the construction shape to a predetermined position relative to one another for letting the liquid flow-in between the separated solid layer and the construction shape. Reduced pressure is applied to at least one fluid, such as the liquid (3).
Owner:NEDERLANDSE ORG VOOR TOEGEPAST-NATUURWETENSCHAPPELIJK ONDERZOEK (TNO)
Enhanced Image Capture and Analysis of Damaged Tangible Objects
ActiveUS20180082378A1Facilitate repair agreementTelevision system detailsEmergency connection handlingImage captureTangible object
Apparatuses, systems, and methods are provided for the usage of enhanced pictures (e.g., photos) of tangible objects (e.g., property, cars, etc.) damaged in an accident and answers to questions about the accident to better assess the effect of the damage (e.g., repair expenses and accompanying changes to an insurance policy). A pre-FNOL system may receive responses to one or more questions regarding an accident and one or more enhanced pictures of the tangible property damaged in the accident. The pre-FNOL system may use the responses to the one or more questions and the one or more enhanced pictures to determine repair costs associated with the damaged property and accompanying changes to the insurance policy if an insurance claim were to be filed to cover the determined repairs costs.
Owner:ALLSTATE INSURANCE
Enhanced image capture and analysis of damaged tangible objects
ActiveUS11361380B2Facilitate repair agreementTelevision system detailsFinanceTangible objectEngineering
Apparatuses, systems, and methods are provided for the usage of enhanced pictures (e.g., photos) of tangible objects (e.g., property, cars, etc.) damaged in an accident and answers to questions about the accident to better assess the effect of the damage (e.g., repair expenses and accompanying changes to an insurance policy). A pre-FNOL system may receive responses to one or more questions regarding an accident and one or more enhanced pictures of the tangible property damaged in the accident. The pre-FNOL system may use the responses to the one or more questions and the one or more enhanced pictures to determine repair costs associated with the damaged property and accompanying changes to the insurance policy if an insurance claim were to be filed to cover the determined repairs costs.
Owner:ALLSTATE INSURANCE
Method and system for layerwise production of a tangible object
InactiveUS20100227068A1Little and no downtimeIncrease production speedAdditive manufacturing apparatusPretreated surfacesLiquid layerTangible object
Owner:NEDERLANDSE ORG VOOR TOEGEPAST-NATUURWETENSCHAPPELIJK ONDERZOEK (TNO)
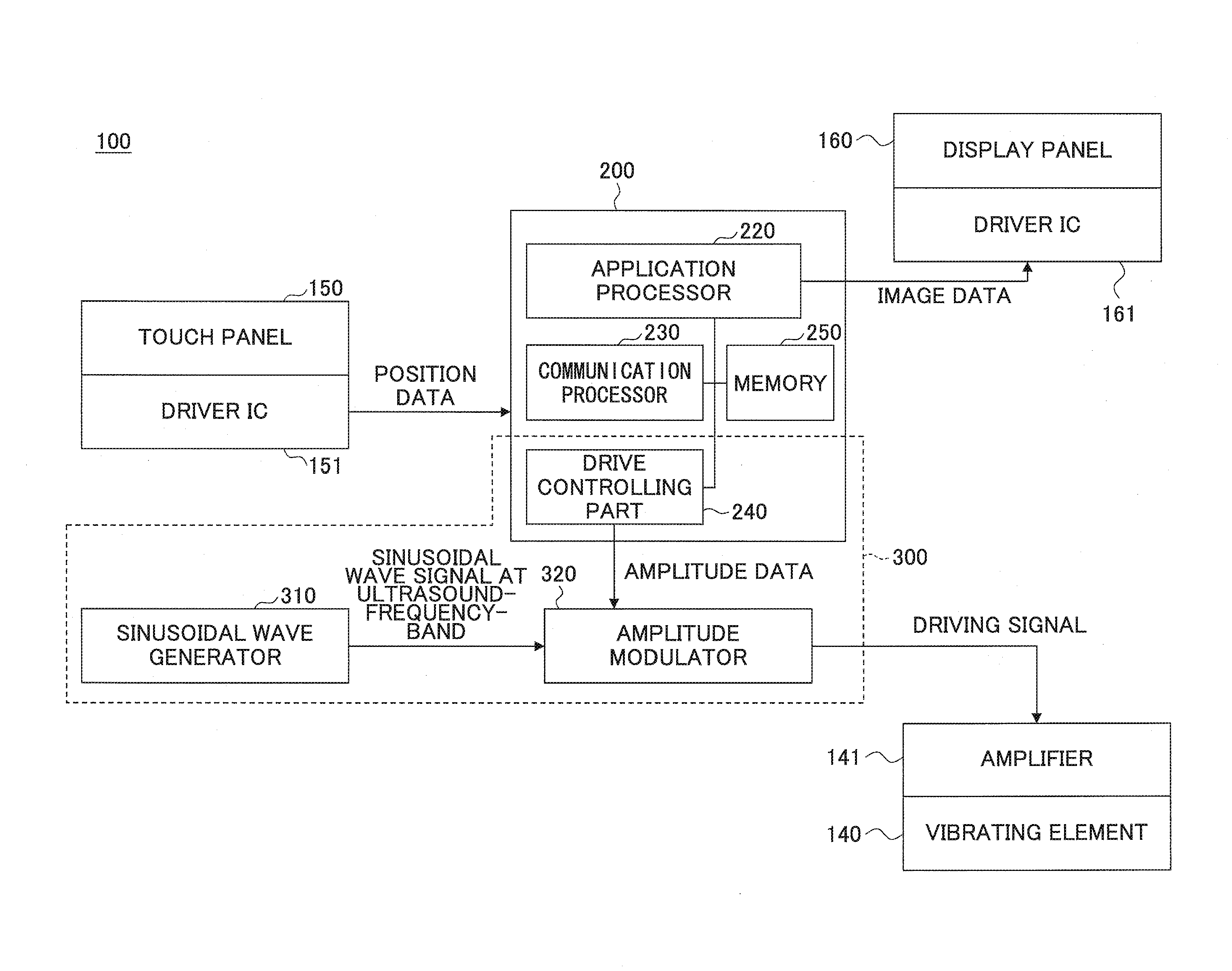
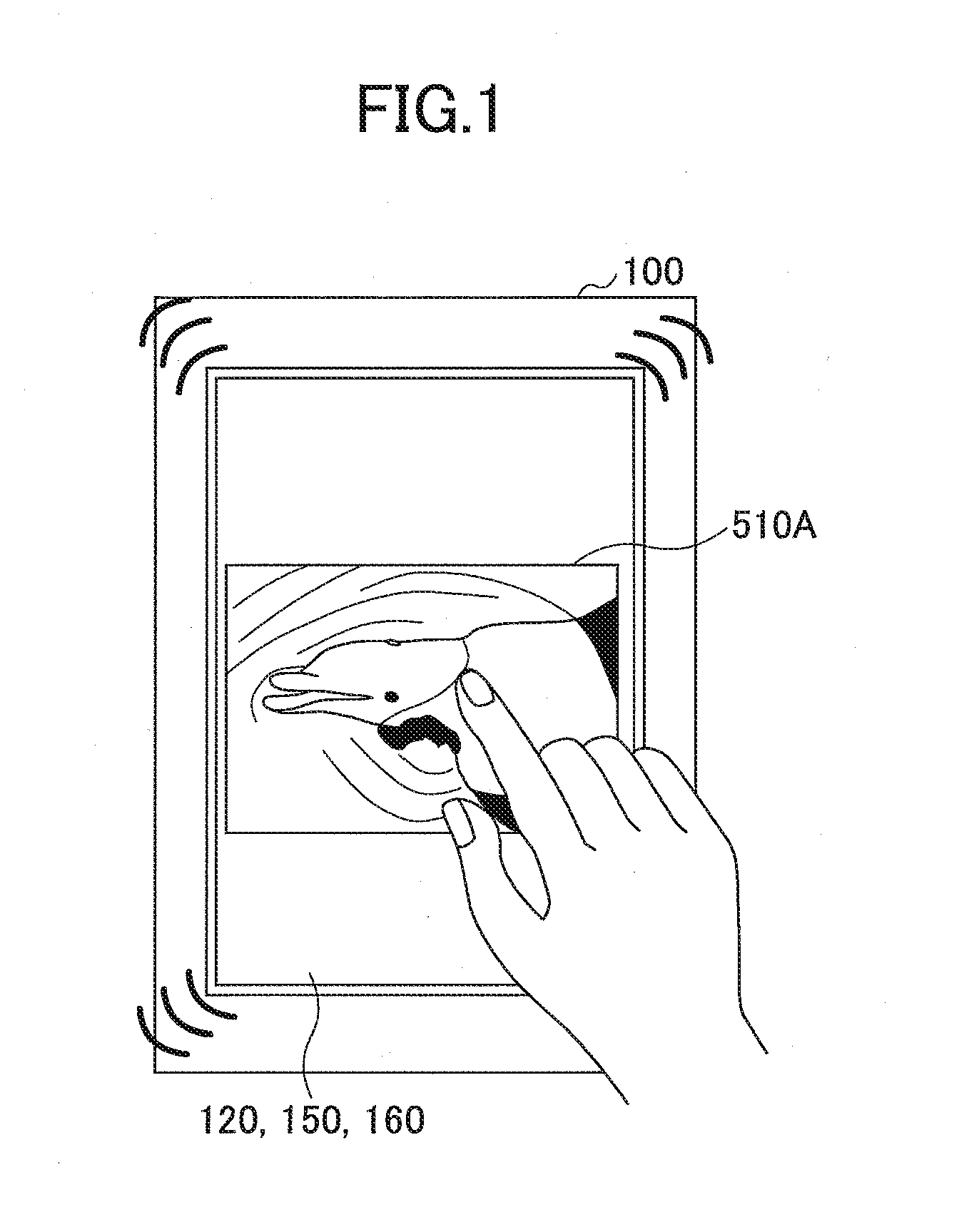
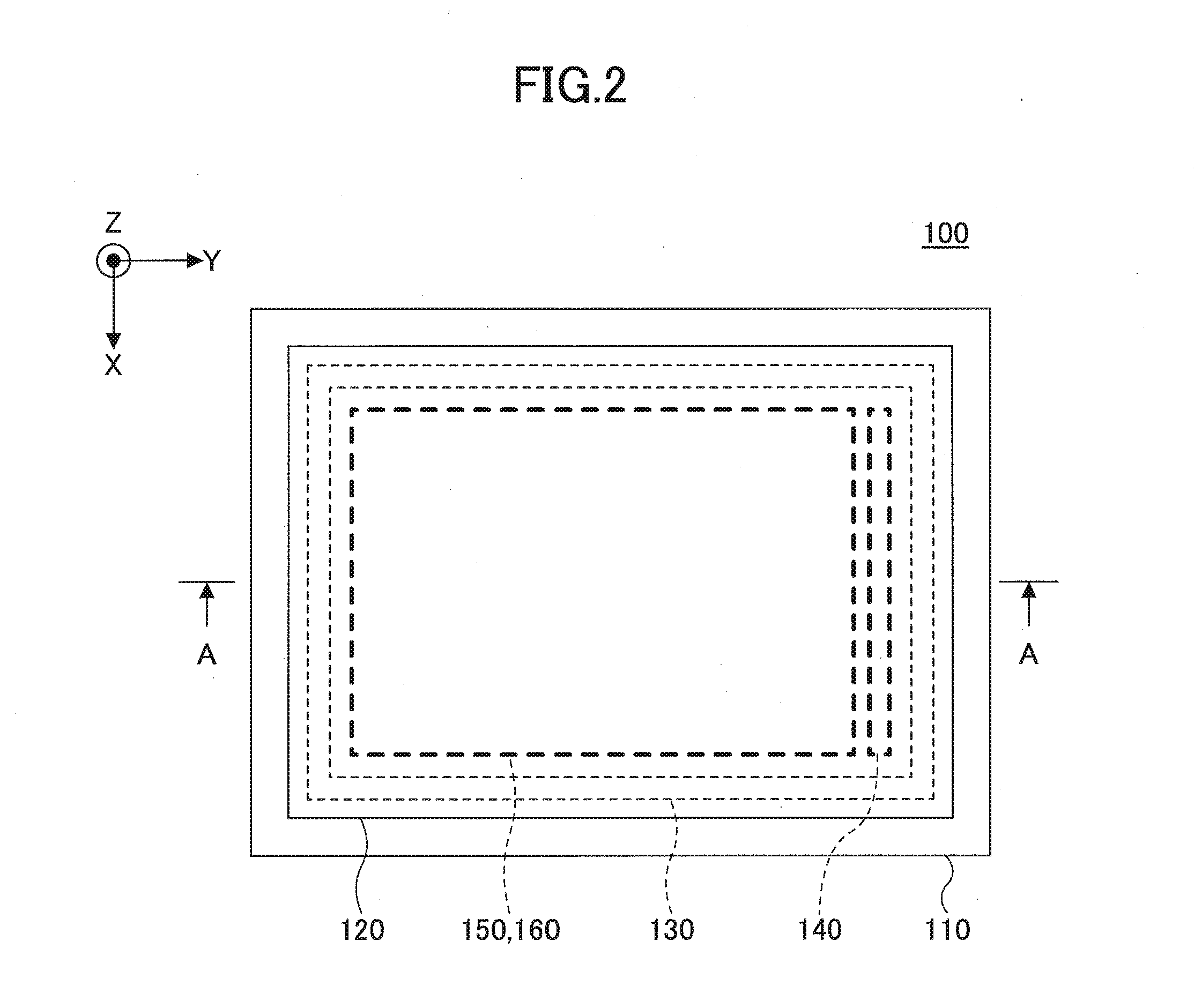
Tactile sensation providing apparatus and system
InactiveUS20160342269A1Input/output for user-computer interactionGraph readingTactile sensationTangible object
A tactile sensation providing apparatus includes a top panel having a manipulation input surface; a position detector configured to detect a position of a manipulation input; a first vibrating element; a memory configured to store tactile sensation data in which an image of a target tangible object is associated with positions in the image and amplitudes corresponding to tactile sensations of the target tangible object at the respective positions; and a drive controlling part configured to drive the first vibrating element by using a driving signal. The tactile sensation data, downloaded by a mobile terminal of a user from a server via a network, is input from the mobile terminal of the user. The drive controlling part adjusts an amplitude of the driving signal based on the position of the manipulation input and a position among the positions in the image included in the tactile sensation data.
Owner:FUJITSU LTD
Methods and tangible objects employing textured machine readable data
InactiveUS20050180599A1Increase in sizeImpacts yieldTelevision system detailsDigital data processing detailsCompact discTangible object
A tangible object (such as a microprocessor, wristwatch, pharmaceutical, compact disc, vehicle part, etc) is surface-textured to encode a plural-bit code thereon. In one arrangement, this encoding conveys date information. In use, the object can be imaged by a scanner apparatus, and the resulting scan data analyzed to discern the plural-bit code. The decoded date information can be used in a determination relating to the object. For example, at a port of entry, date information encoded on a Rolex wristwatch can be used to determine whether importation of the wristwatch should be permitted. The texture-encoded data can also convey other information, such as a vehicle identifier for an automotive part, a place of fabrication, a specification with which the part complies, etc.
Owner:DIGIMARC CORP
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com