Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
126results about How to "Reduced risk of tampering" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
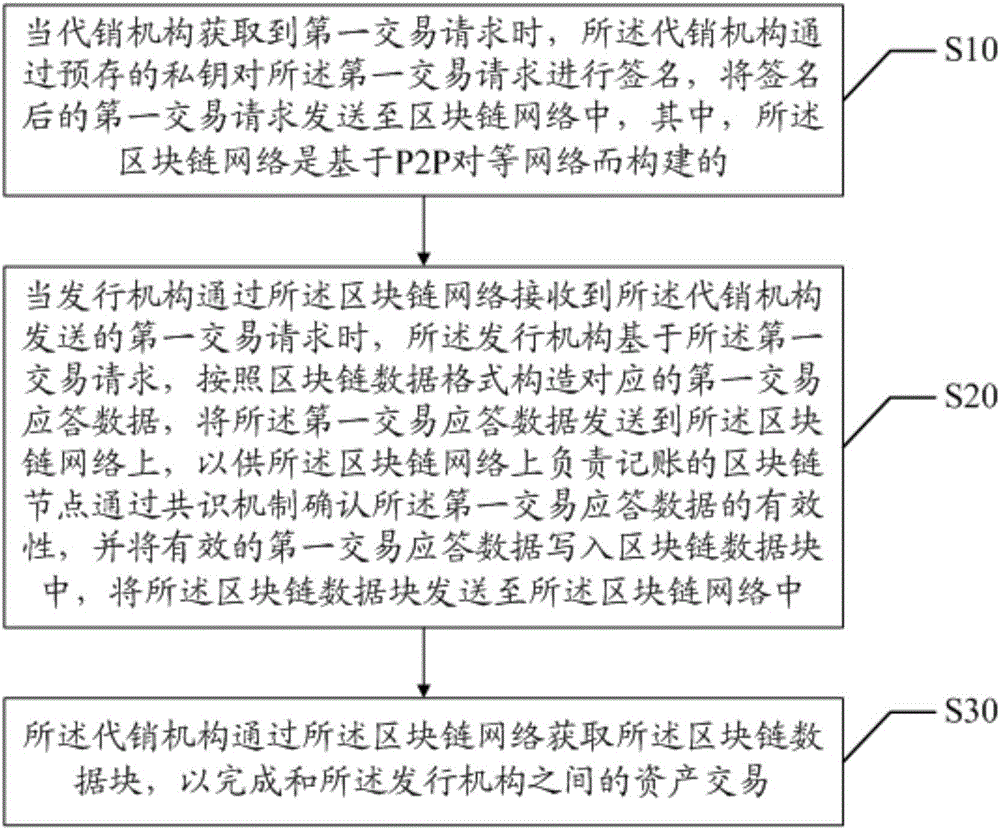
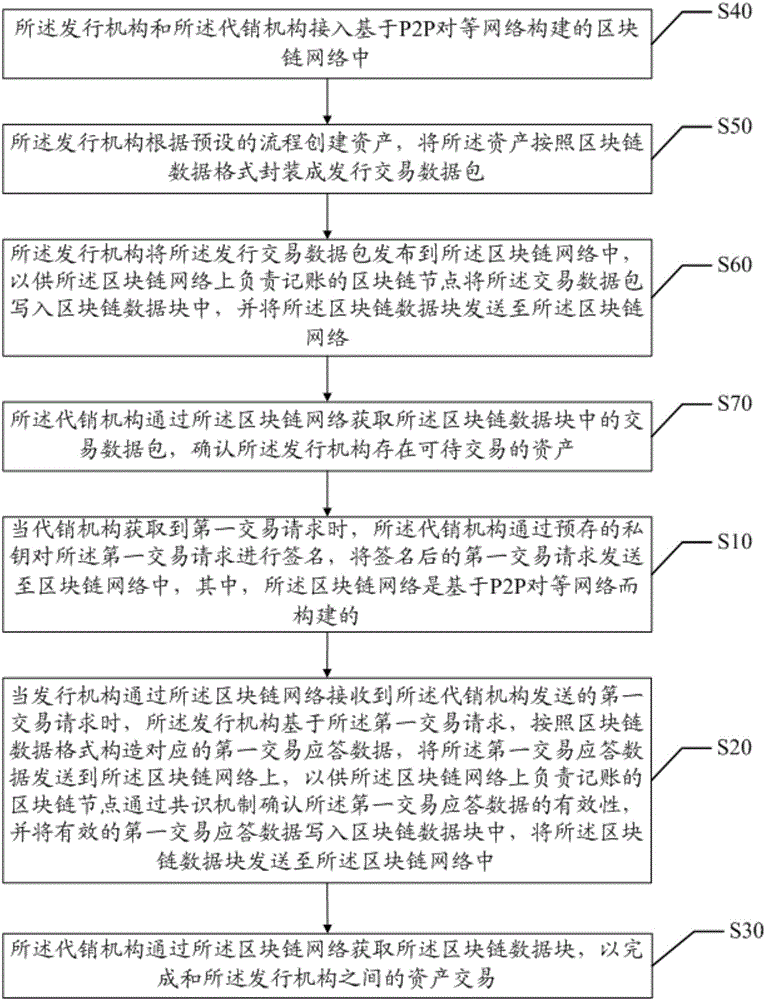
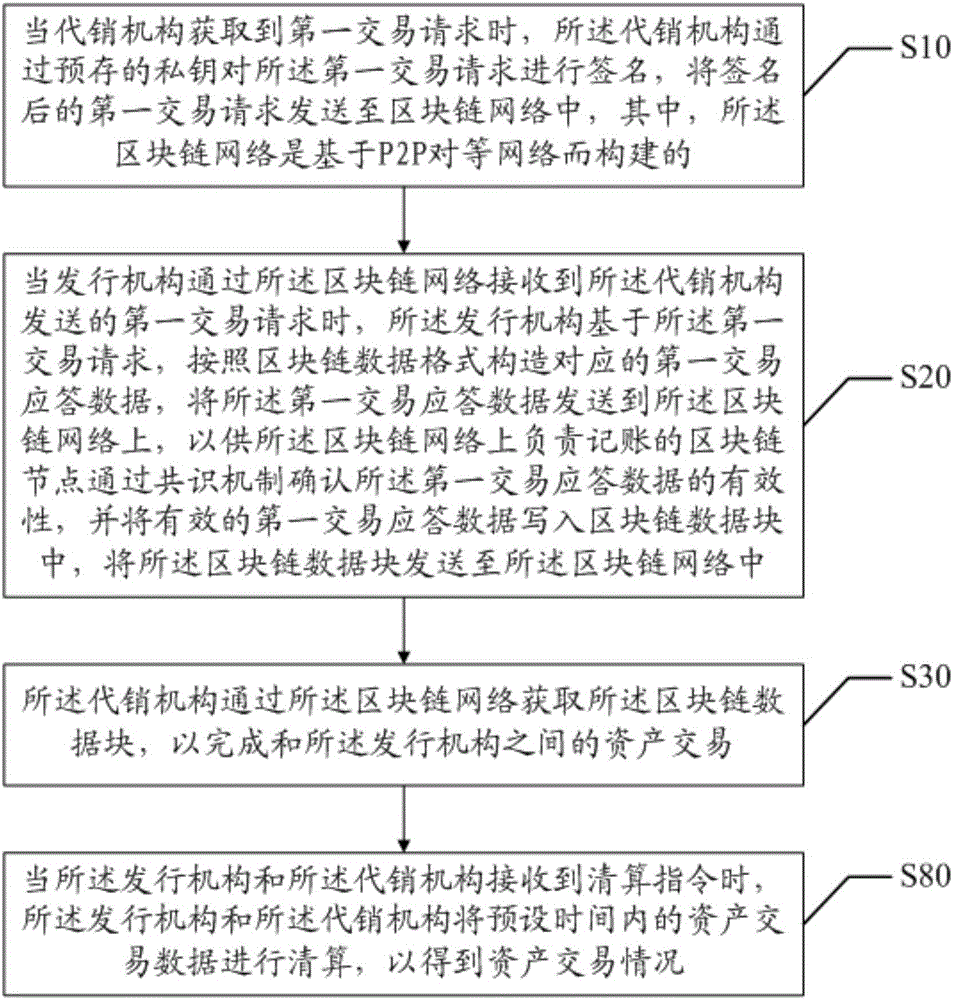
Asset transaction method and device
ActiveCN105976232AReduce operation and maintenance costsReduce transaction flowUser identity/authority verificationBuying/selling/leasing transactionsFinancial transactionChain network
The invention discloses an asset transaction method and a system. The method comprises steps that an acquired first transaction request is signed by a consignment agency, the first transaction request after signature is sent to the block chain network established on the basis of the P2P network, the first transaction response data is constructed by an issuing mechanism on the basis of the first transaction request acquired from the block chain network, the first transaction response data is sent to the block chain network so that validity of the first transaction response data can be confirmed by a block chain node on the block chain network responsible for accounting, the first effective transaction response data is written in a block chain data block, the block chain data block is acquired by the consignment agency through the block chain network, and asset transaction with the issuing mechanism and the consignment agency is accomplished. Through the method, transaction steps between the issuing mechanism and the consignment agency can be reduced in a transaction process, risks of being tampered of the data can be reduced, asset transaction confirmation cost is reduced, and operation cost of the block chain network is further reduced.
Owner:WEBANK (CHINA)
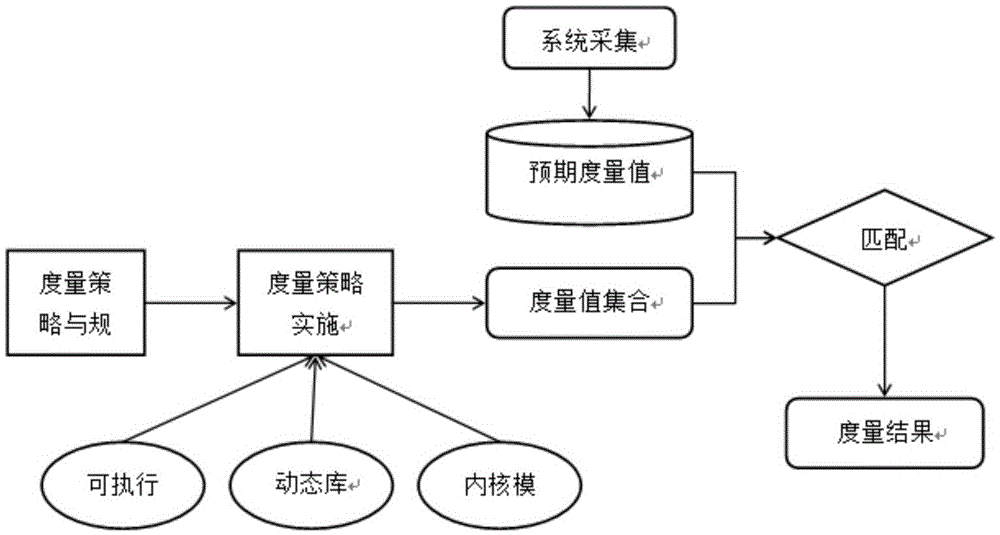
Trusted computing cryptogram platform suitable for general computation platform of electric system
ActiveCN105468978AEnsure credibleGuaranteed recognition effectPlatform integrity maintainanceOperational systemSoftware system
The invention provides a trusted computing cryptogram platform suitable for a general computation platform of an electric system. The cryptogram platform comprises a trusted computing cryptogram module and a trusted software system, wherein the trusted computing cryptogram module comprises a trusted measurement root, a trusted storage root and a trusted report root and is a transferring starting point of a platform trust chain; and the trusted software system comprises a trusted computing cryptogram driving module, a measurement module and an auditing module and provides an interface which uses the trusted computing cryptogram platform for an operating system and application software. The trusted computing cryptogram module is the trusted root which provides trusted environment for the operation of the trusted computing cryptogram platform, and the trusted software system is a core for realizing the functions and the service of the trusted computing cryptogram platform and provides guarantee for the management of the trusted computing cryptogram platform. The trusted computing cryptogram platform can provide functions including static measurement, dynamic measurement, white lists, access control and the like for a business system, and manages the sources and the operation of the system software to guarantee that the software is trusted, recognizable and controllable.
Owner:GLOBAL ENERGY INTERCONNECTION RES INST CO LTD +5
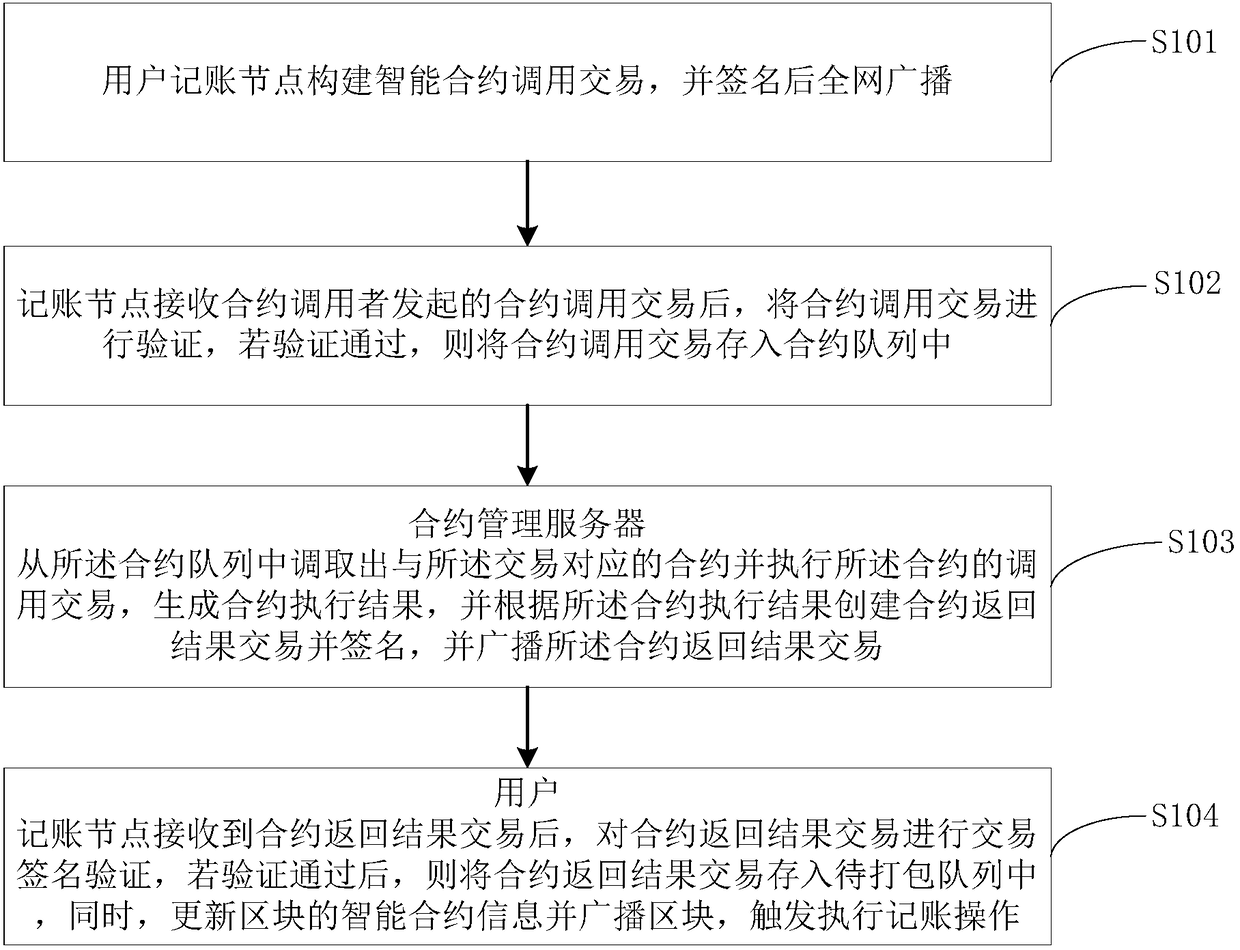
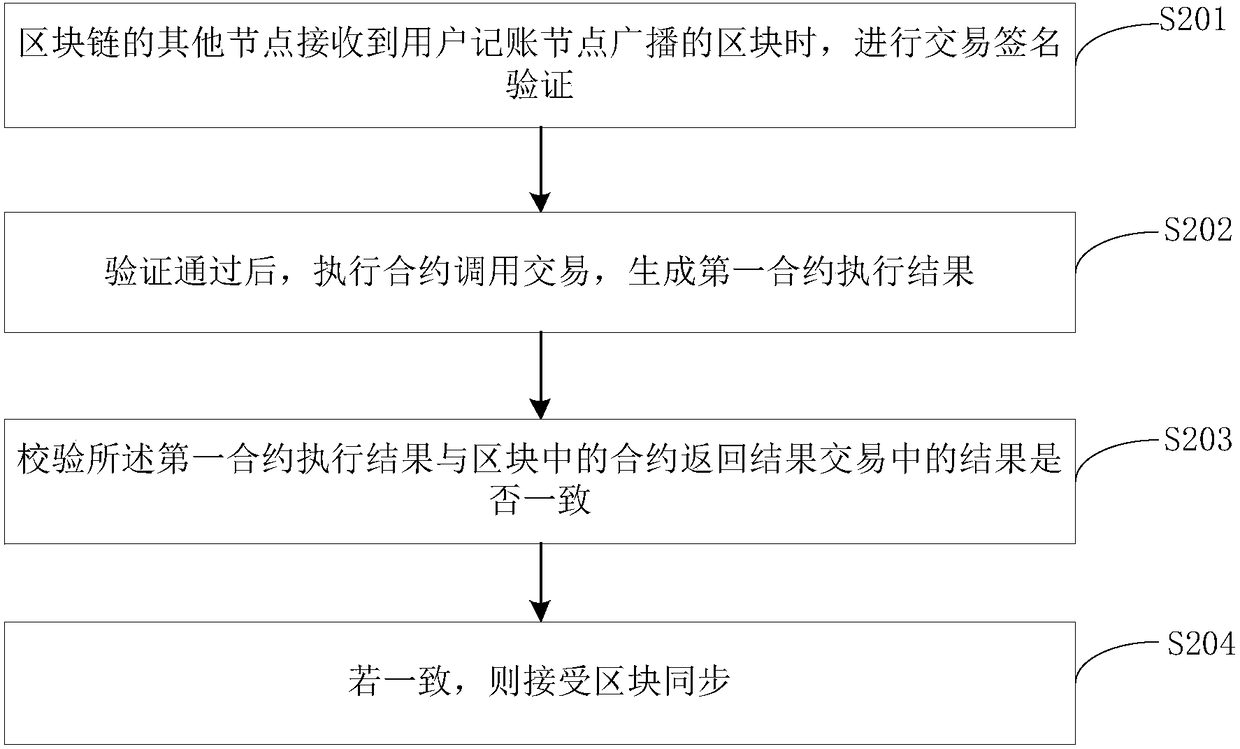
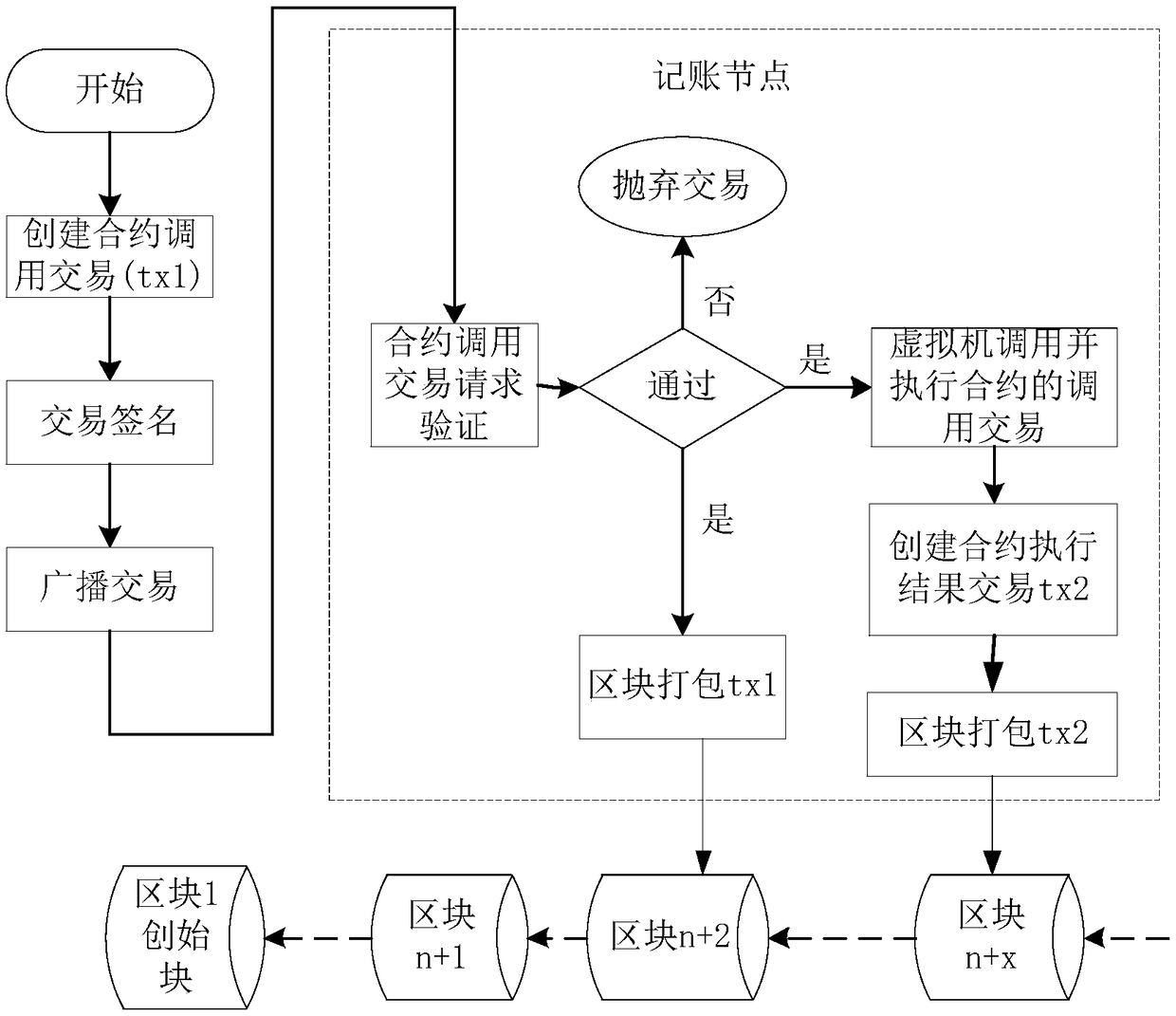
Intelligent contract bookkeeping method, computer device and readable storage medium
ActiveCN109064334AEnsure legalityEnsure effectivenessFinancePayment protocolsService efficiencySmart contract
The invention is applicable to the field of computer technology, and provides an intelligent contract bookkeeping method, a computer device and a readable storage medium. The method comprises the following steps: a user bookkeeping node constructs an intelligent contract calling transaction, and broadcasts the transaction throughout the network after signing; The bookkeeping node verifies the contract call transaction after receiving the contract call transaction, and stores the contract call transaction into the contract queue after the verification is passed; At the same time, the contract management server transfers out the contract corresponding to the transaction from the contract queue and executes the contract, generates the contract execution result, and creates the contract returnresult transaction according to the contract execution result and broadcasts after signing; The bookkeeping node performs transaction signature verification after receiving the contract return resulttransaction, stores the contract return result transaction into the queue to be packed after verification, updates the intelligent contract information of the block and broadcasts the block, triggersthe bookkeeping operation. The bookkeeping operation safety of the invention is good, and the intelligent contract can be more focused on the service of the service data, thereby improving the service efficiency.
Owner:WEALEDGER NETWORK TECH CO LTD
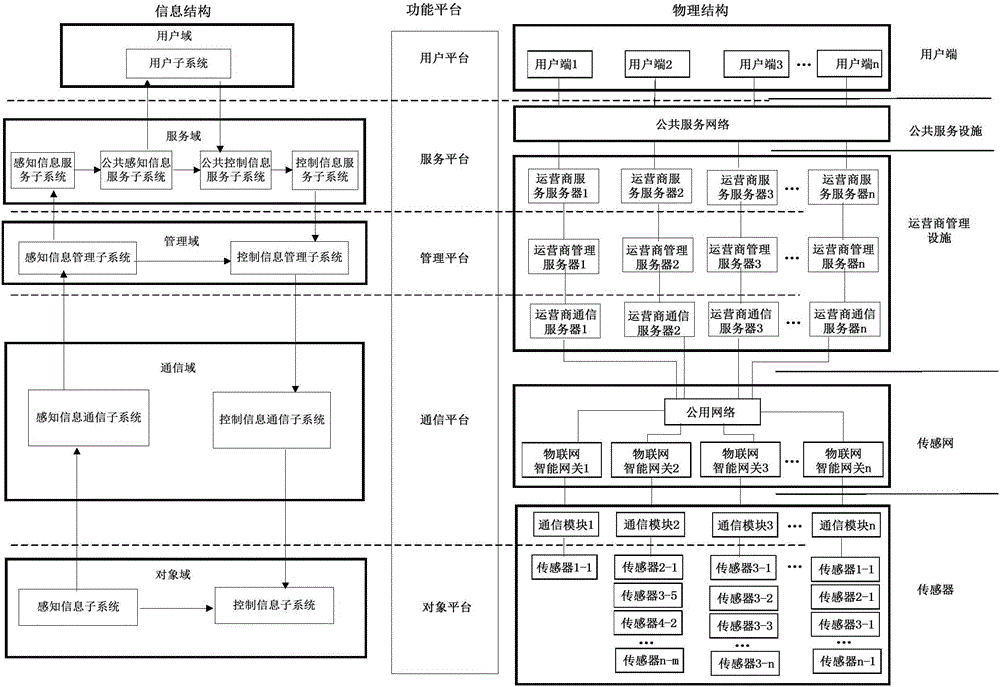
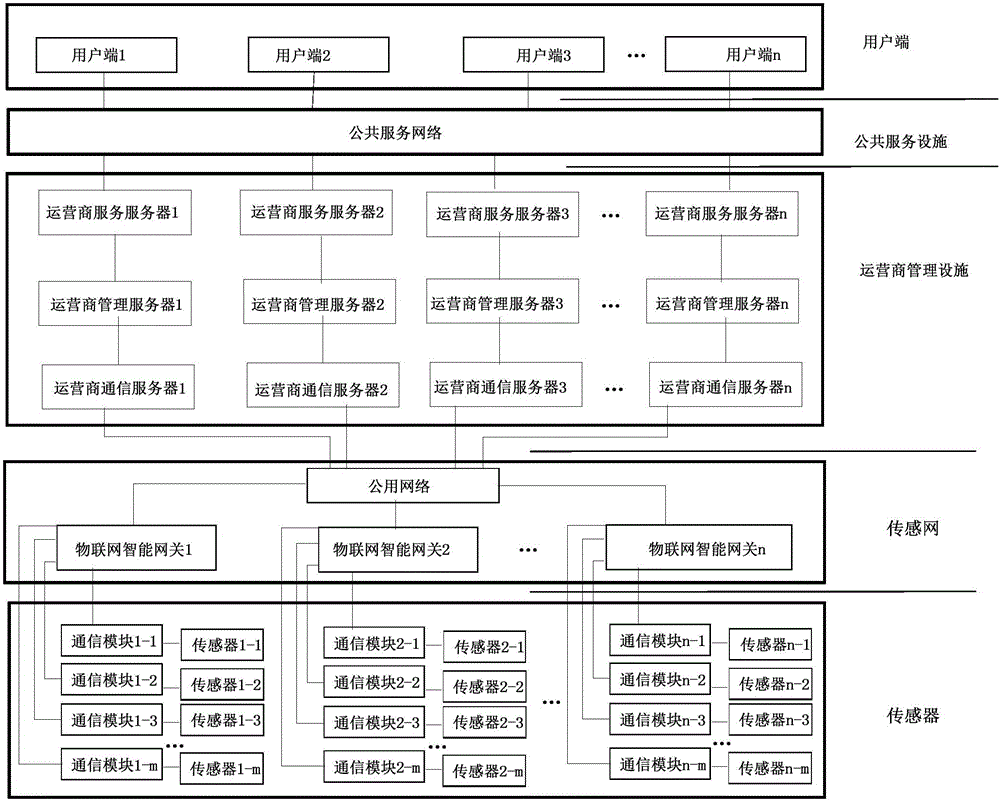
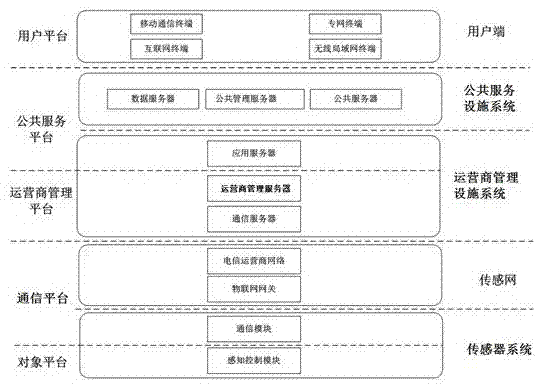
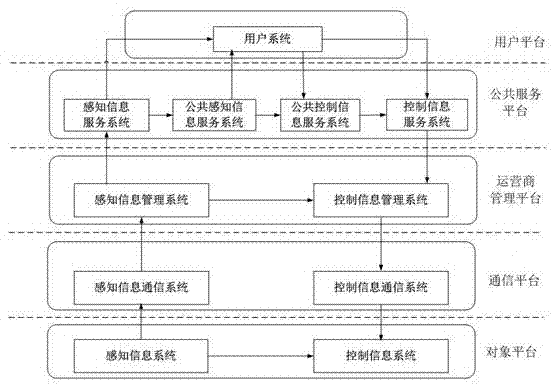
Smart city system
The invention discloses a smart city system, and belongs to an Internet of things system. The system comprises a smart city information system, a smart city physical system and a smart city function system. The smart city information system comprises an object domain, a communication domain, a management domain, a service domain and a user domain; the smart city physical system comprises multiple Internet of things units, wherein each Internet of things unit comprises a sensor, an Internet of things intelligent gateway, a service provider management server and a user end; and the smart city function system comprises an object platform, a communication platform, a management platform, a service platform and a user platform. The integral smart city system provided by the invention is simple in structure and diversified in transmission modes, has great reference significance for arrangement of various modes in construction of a smart city, can be used as a system with different functions in a smart city design system, and is wide in application scope.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
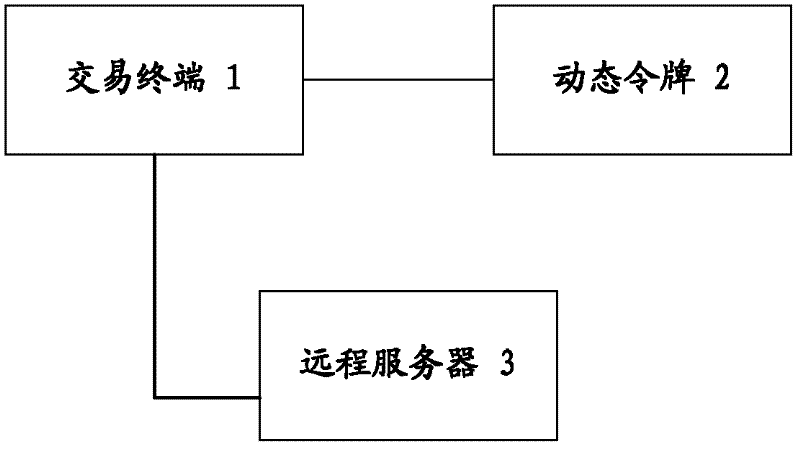
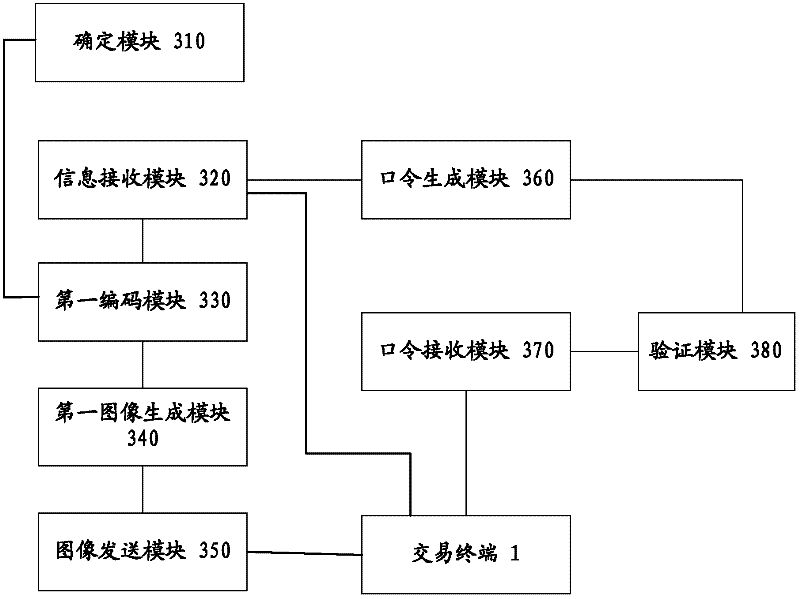
Trading system, method and device
ActiveCN102509037AReduce stepsImprove experienceDigital data authenticationTransmissionPasswordComputer terminal
The invention provides a trading system, a method and a device. The trading system comprises a trading terminal, a dynamic token and a remote server, wherein the trading terminal is used for receiving the trade content of a user, sending the trade content to the remote server and displaying a dynamic image; the dynamic token is used for receiving an optical signal sent by the dynamic image, obtaining the trade content according to the optical signal and generating a second dynamic password according to the trade content; the remote server is used for receiving the trade content, generating a first dynamic password according to the trade content, receiving the second dynamic password and verifying whether the first dynamic password and the second dynamic password are matched to judge whether to trade; the remote server stores a service strategy; and the service strategy determines the trading terminal or remote server to generate a dynamic image. According to the invention, the trade content can be quickly input into the dynamic token, the operation steps of the user are reduced, and the operation difficulty is reduced. Moreover, the risk of tampering the user trade is reduced.
Owner:北京宏基恒信科技有限责任公司
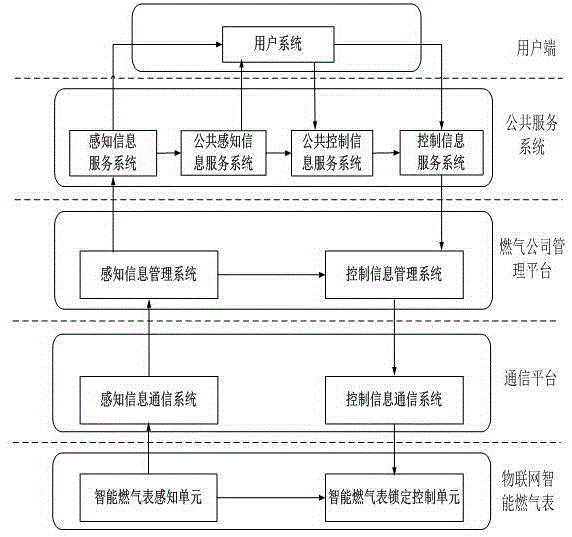
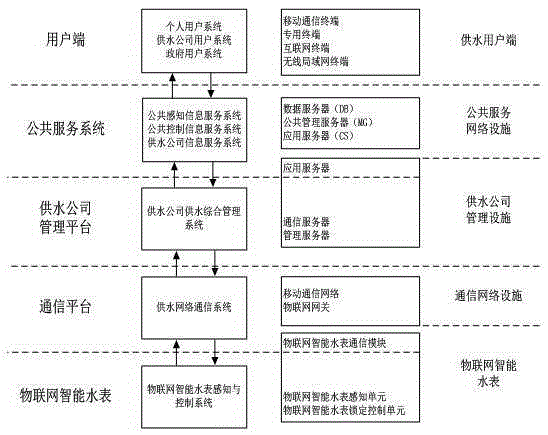
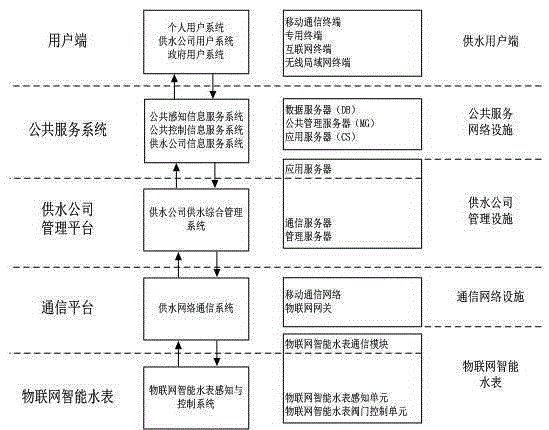
Internet of things information system structure
ActiveCN105450745AThe transfer process is clearReduced risk of tamperingTransmissionService providerSystem structure
The invention discloses an Internet of things information system structure and relates to the Internet of things transmission technology field. The structure comprises a sensor system, a sensing network, a service provider equipment system, a common service facility system and a user terminal. The sensor system establishes a communication protocol with a service provider management facility system through the sensing network. The service provider management facility system establishes the communication protocol with the common service facility system. The common service facility system establishes the communication protocol with the user terminal. By using the Internet of things information system structure provided in the invention, the structure is simple, a transmission process is diversified, the structure is suitable for various kinds of Internet of things application systems and an application scope is wide.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
Asset certification authorization check method, system, electronic device and computer readable storage medium
ActiveCN107832632AFully automatedReduced risk of tamperingDigital data protectionComputer moduleData transmission
Theinvention provides an asset certification authorization check method, system, an electronic device and computer readable storage medium. The asset certification authorization check method and system comprises a first asset certification production module, a first authorization certification production module, a first sending module, a first receiving module, a first verification module, a firstasset certification calculation module and a first asset certification module. Data transmission automation can be realized; and data manipulation risks can be reduced.
Owner:VTEAM FINANCIAL TECH SERVICE
Blockchain-based DNS root data distribution method and system
ActiveCN109672760AImprove securityAchieve rapidityTransmissionDistribution methodDistribution networks
The invention discloses a blockchain-based DNS root data distribution method and system. The root data of a root node are obtained through a pre-established miner node in a root data distribution network, then the freshness of the obtained root data is compared with that of the root data of the latest block on a local blockchain, the root data are verified based on the blockchain technology, basedon the characteristics of the blockchain technology, if a large number of links need to be hijacked, it is necessary to tamper more than half of the miner node data, so that the difficulty is large,and a DNS root data distribution network is formed via various miner node networks in the blockchain technology to reduce the tampering risk of the data. Furthermore, zone data of the root node are verified by the blockchain technology to improve the security of the obtained root data, and the network fastness of root data distribution is achieved through a blockchain network.
Owner:CHINA INTERNET NETWORK INFORMATION CENTER
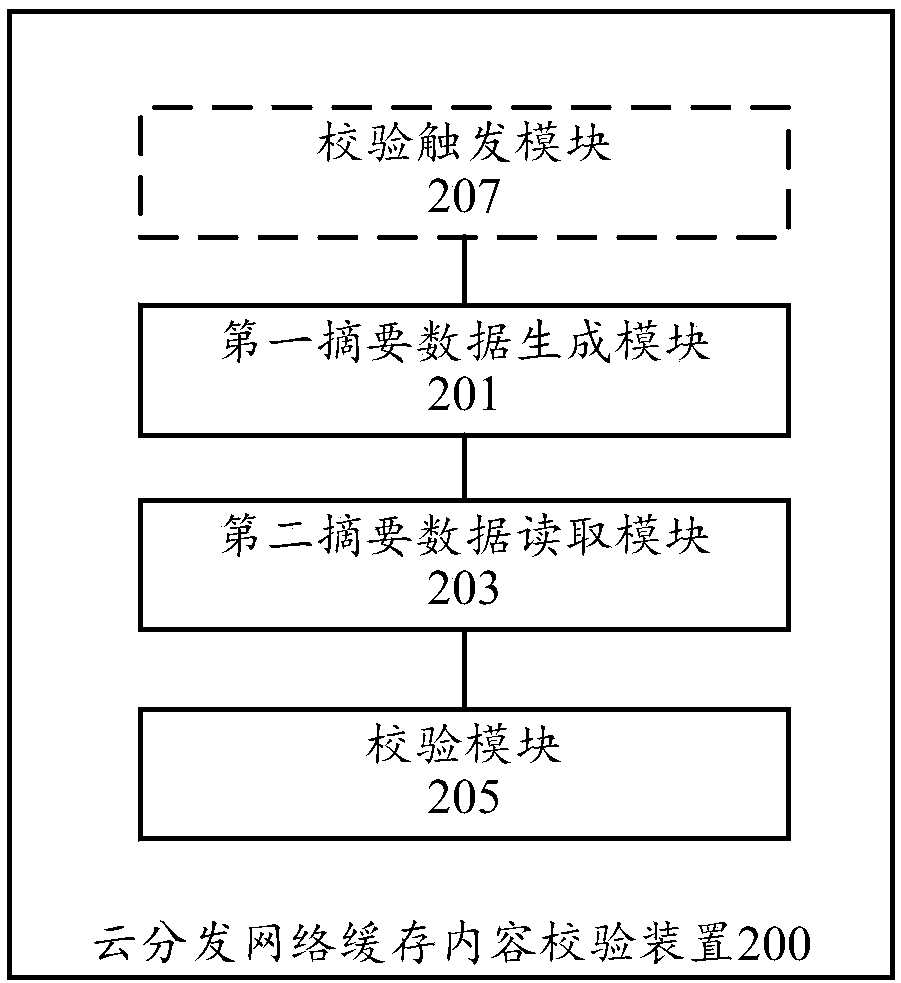
Cloud distribution network cache content verification method and device, network, storage medium and computing device
The invention discloses a cloud distribution network cache content verification method and device, network, a storage medium and a computing device. The disclosed cloud distribution network cache content verification method comprises the following steps of generating first summary data on the basis of a cache content corresponding to a source station content; acquiring second summary data from a block chain; and verifying the consistency between the cache content and the source station content on the basis of the consistency between the first summary data and the second summary data, wherein the second summary data is generated based on the source station content. According to the technical scheme, the risk that data is tampered after a single centralized database is attacked is reduced.
Owner:BEIJING BAISHANCLOUD TECH CO LTD
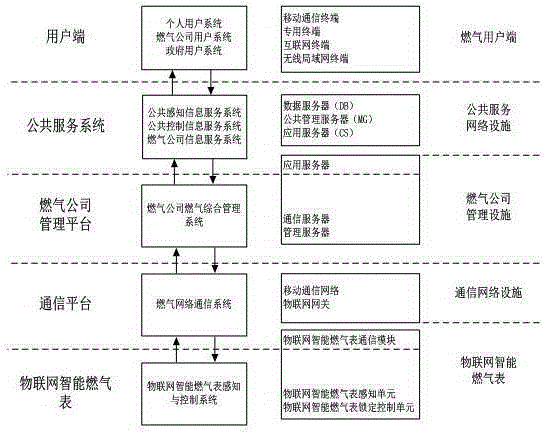
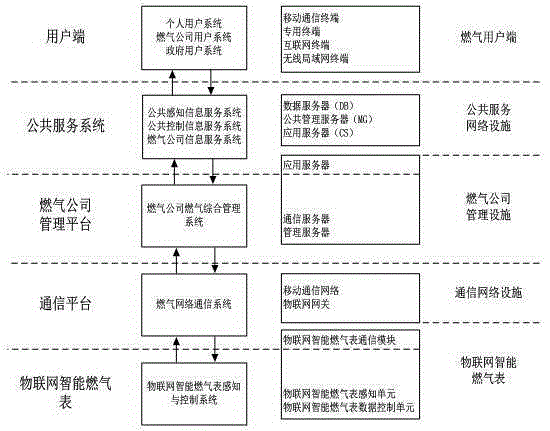
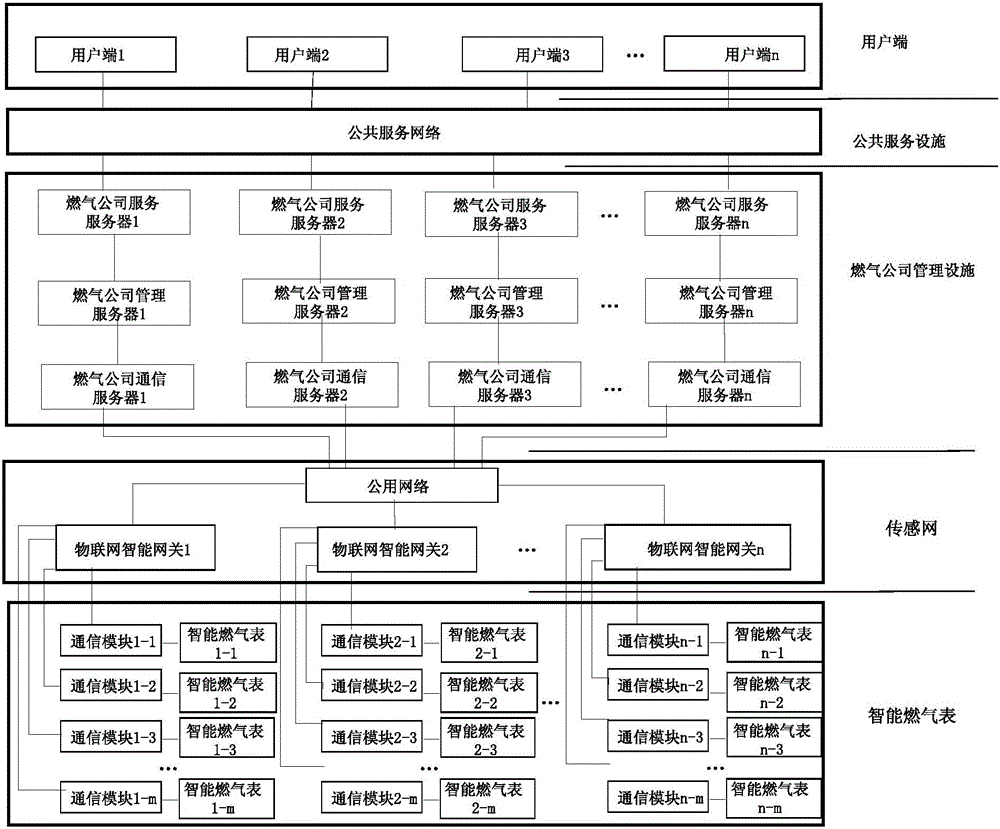
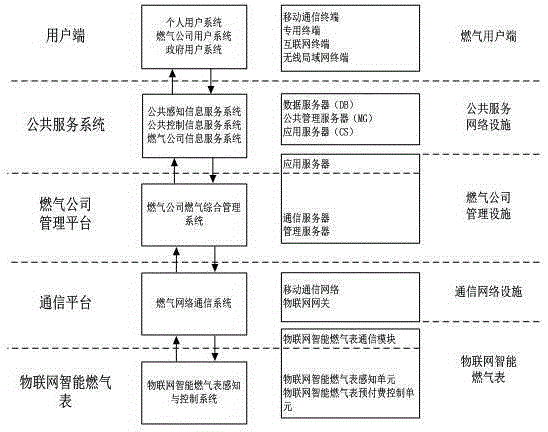
Intelligent gas meter system with remote locking function
ActiveCN105279936AWith remote locking functionThe transfer process is clearTransmission systemsTransmissionCommunications systemInformation transmission
The invention discloses an intelligent gas meter system with the remote locking function and relates to the technical field of Internet of things intelligent gas meters. The intelligent gas meter system comprises an intelligent gas meter sensing unit, an intelligent gas meter locking control unit, a sensing information communication system, a control information communication system and a gas company gas comprehensive management system. The intelligent gas meter sensing unit and the intelligent gas meter locking control unit are in communication with the gas company gas comprehensive management system through the sensing information communication system and the control information communication system respectively, and locking control over an intelligent gas meter is achieved. The intelligent gas meter system is simple in structure, the transmission process is diversified, information transmission is safer and more reliable, and responses to the locking function of the intelligent gas meter and control over the locking function of the intelligent gas meter can be effectively achieved.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
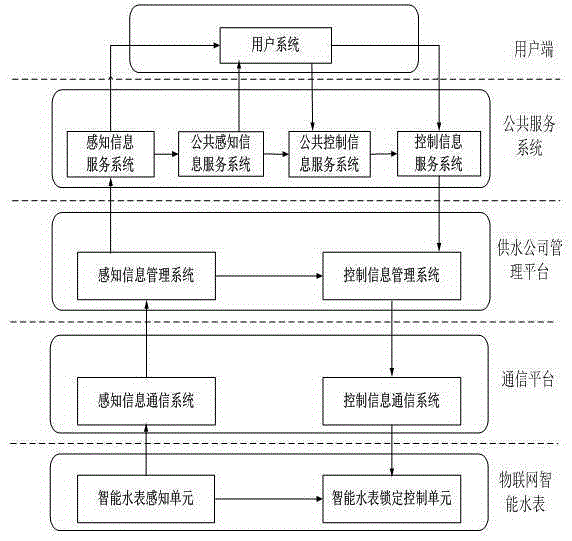
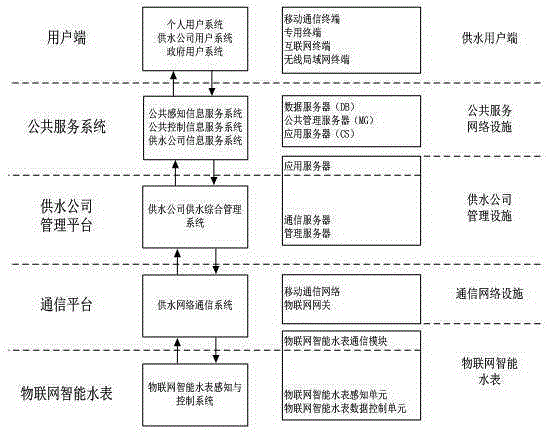
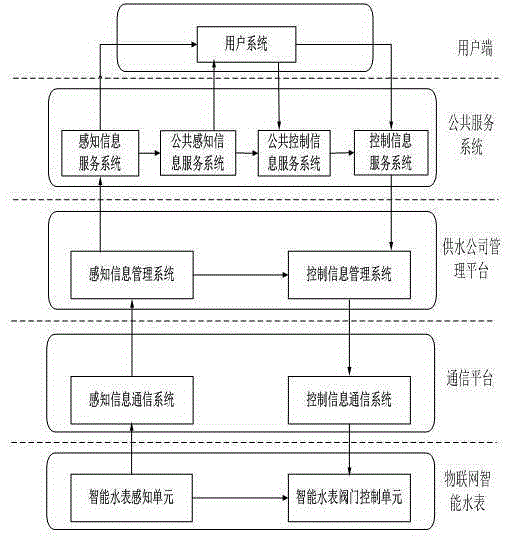
Intelligent water meter system with remote locking function
ActiveCN105306590AWith remote locking functionThe transfer process is clearTransmissionCommunications systemEngineering
The invention discloses an intelligent water meter system with remote locking function, and relates to the technical field of Internet of Things intelligent water meter. The intelligent water meter system with remote locking function comprises an intelligent water meter sensing unit, an intelligent water meter locking control unit, a sensing information communication system, a control information communication system and a water supply integrated management system of water supply company. The intelligent water meter sensing unit and the intelligent water meter locking control unit respectively build communication connection with the water supply integrated management system of water supply company through the sensing information communication system and the control information communication system; and locking control for the intelligent water meter is realized. The intelligent water meter system with remote locking function is simple in structure, has diversified transmission process, transmits information more safely and reliably, and can effectively realize response and control to the locking function of the intelligent water meter.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
Intelligent gas meter system with timed data reporting function
ActiveCN105279935ARealize the timing reporting functionSimple structureTransmission systemsVolume indication and recording devicesData controlInformation transmission
The invention discloses an intelligent gas meter system with the timed data reporting function and relates to the technical field of Internet of things intelligent gas meters. The intelligent gas meter system comprises an intelligent gas meter sensing unit, an intelligent gas meter data control unit, a sensing information communication system, a control information communication system and a gas company gas comprehensive management system. The intelligent gas meter sensing unit and the intelligent gas meter data control unit are in communication with the gas company gas comprehensive management system through the sensing information communication system and the control information communication system respectively, and data control over an intelligent gas meter is achieved. The intelligent gas meter system is simple in structure, the transmission process is diversified, information transmission is safer and more reliable, and responses to the timed data reporting function of the intelligent gas meter and control over the timed data reporting function of the intelligent gas meter can be effectively achieved.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
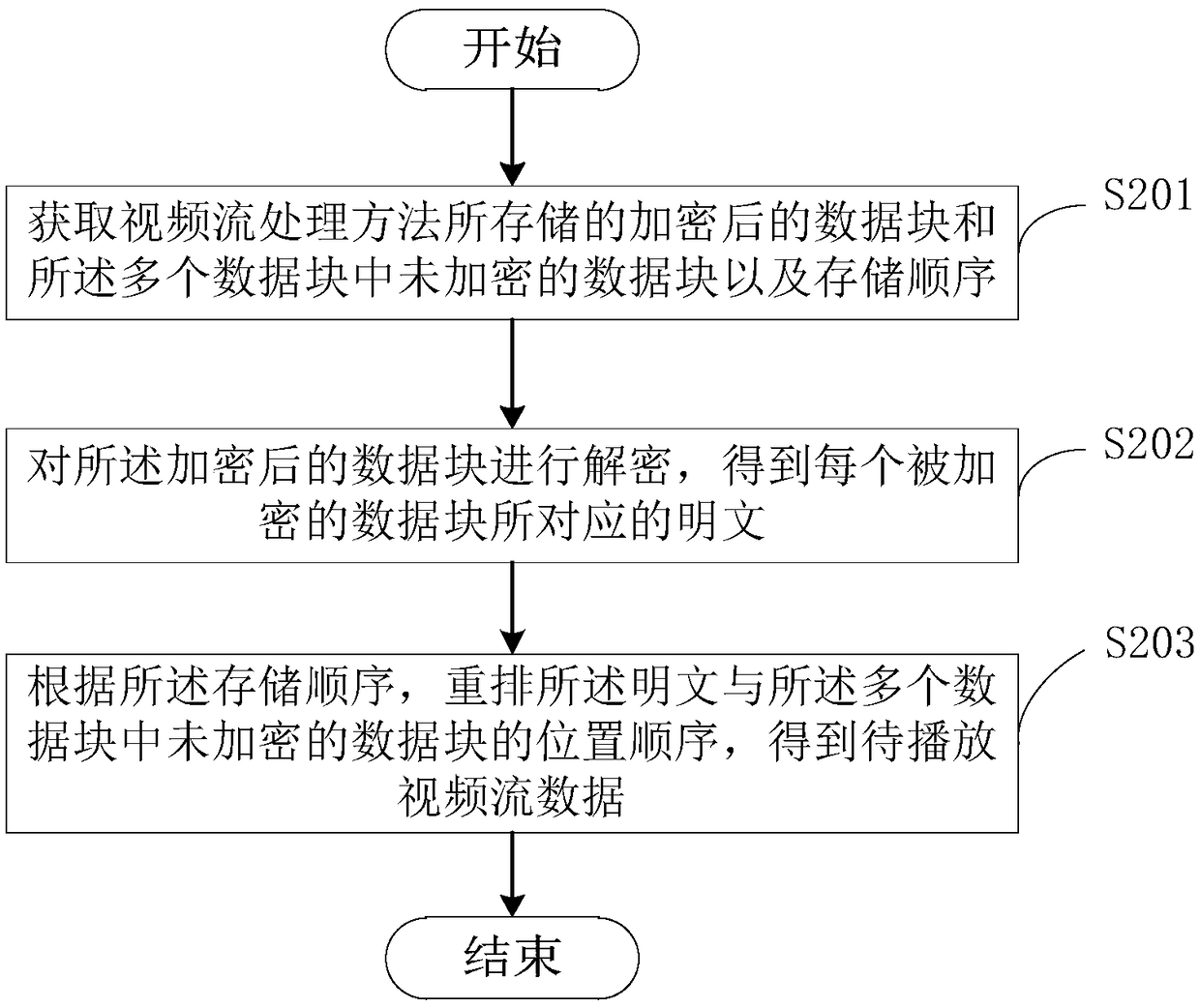
Video stream processing method, device and equipment for broadcast and TV cloud platform, and medium
InactiveCN108777803ASolve technical problems with high risk of tamperingReduced risk of tamperingEncryption apparatus with shift registers/memoriesSelective content distributionStreaming dataVideo processing
The invention provides a video stream processing method, device and equipment for a broadcast and TV cloud platform, and a medium, and belongs to the technical field of video processing. The method comprises the steps: dividing to-be-processed video stream data into a plurality of data blocks; selecting a part of the plurality of data blocks as to-be-encrypted data blocks according to a preset rule; encrypting each to-be-encrypted data block; performing distributed cloud storage of the encrypted data block and the unencrypted data blocks in the plurality of data blocks, wherein the storage sequence of the encrypted data blocks and unencrypted data blocks is different from a position sequence in the to-be-processed video stream data, so that in the open broadcast and TV cloud platform, thecriminals can read all the video stream data blocks stored on the cloud server, but cannot know which data blocks belong to the same file and in what order the data blocks are arranged to form file, thereby reducing the risk that a new media news video of the broadcast and TV cloud platform will be tampered.
Owner:SICHUAN NORMAL UNIVERSITY +1
Intelligent water meter system with regular data reporting function
ActiveCN105306589ARealize the timing reporting functionThe transfer process is clearTransmissionData controlCommunications system
The invention discloses an intelligent water meter system with regular data reporting function, and relates to the technical field of Internet of Things intelligent water meter. The intelligent water meter system with regular data reporting function comprises an intelligent water meter sensing unit, an intelligent water meter data control unit, a sensing information communication system, a control information communication system and a water supply integrated management system of water supply company. The intelligent water meter sensing unit and the intelligent water meter data control unit respectively build communication connection with the water supply integrated management system of water supply company through the sensing information communication system and the control information communication system; and data control for the intelligent water meter is realized. The intelligent water meter system with regular data reporting function is simple in structure, has diversified transmission process, transmits information more safely and reliably, and can effectively realize response and control to the regular reporting function of the intelligent water meter.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
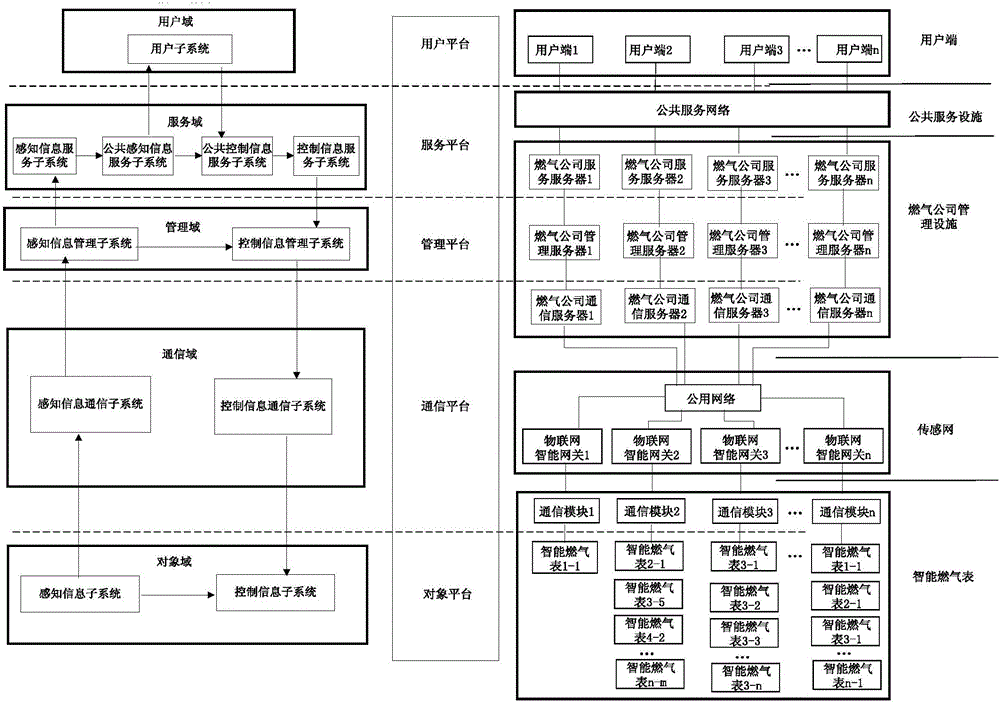
Internet of Things intelligent gas meter system based on smart city system
InactiveCN105678997AMeet different needsThe transfer process is clearData processing applicationsTransmission systemsThe InternetSmart city
The invention belongs to an Internet of Things system and discloses an Internet of Things intelligent gas meter system based on a smart city system. The Internet of Things intelligent gas meter system comprises an object platform, a communication platform, a management platform, a service platform and a user platform. The object platform at least comprises an intelligent gas meter which is connected into an Internet of Things intelligent gateway; the communication platform is respectively connected with the object platform and the management platform through networks; the management platform is respectively connected with the communication platform and the service platform and at least comprises a gas company server; the service platform is respectively connected with the management platform and the user platform and at least comprises a gas company server; the user platform is connected into the service platform or the management platform and at least comprises a user terminal. In the Internet of Things system, the servers, the Internet of Things intelligent gateways, users and the intelligent gas meters can be in one-to-one, many-to-one or many-to-many connection for transmission of sensing information and control information to meet different requirements in use of the Internet of Things in the smart city system.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
Update method, update system and security authentication device
InactiveCN105812136APrevent leakageReduced risk of tamperingUser identity/authority verificationSecurity authenticationKey generation
The invention provides an update method, an update system and a security authentication device. After the security authentication device receives an update command, the device generates a certificate request by using a certificate renewal key preset in the security authentication device. After that, the device applies a certificate to a security authentication server by using the certificate request. Since the certificate request is generated based on the certificate renewal key preset in the security authentication device, the certificate request is encrypted in the security authentication device. Meanwhile, the security authentication device itself is capable of resisting attacks and avoiding the key leakage, so that the certificate request grenade by the security authentication device is higher in security. Therefore, the risk that the certificate request is tampered is lowered. As a result, the security of the update process is improved.
Owner:WATCHDATA SYST
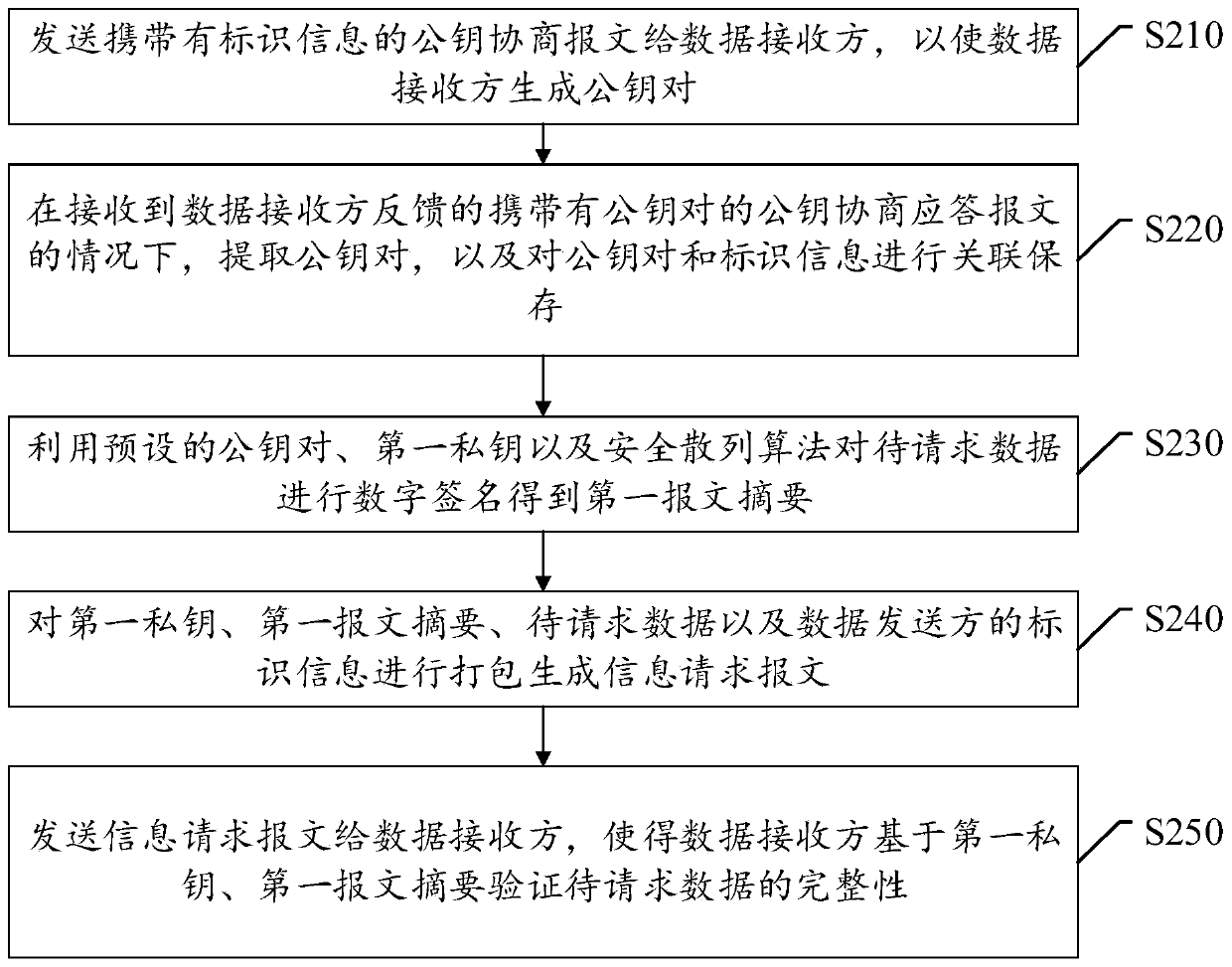
Data transmission method and device and electronic equipment
PendingCN111431724AReduce the risk of tamperingEnsure original integrityUser identity/authority verificationData transmissionCommon key
The invention discloses a data transmission method and device, and electronic equipment, and relates to the technical field of network security. The data transmission method comprises steps of based on a public key pair determined by a data receiver and a data sender through message negotiation, performing digital signature on the to-be-requested data in combination with a first private key and asecurity hash algorithm to obtain a first message abstract; packaging the first private key, the first message abstract, the to-be-requested data and the identification information of the data senderto generate an information request message; and sending the information request message to a data receiver, so that the data receiver verifies the integrity of the to-be-requested data based on the first private key and the first message abstract to ensure the original integrity in the data transmission process.
Owner:MICRO DREAM TECHTRONIC NETWORK TECH CHINACO
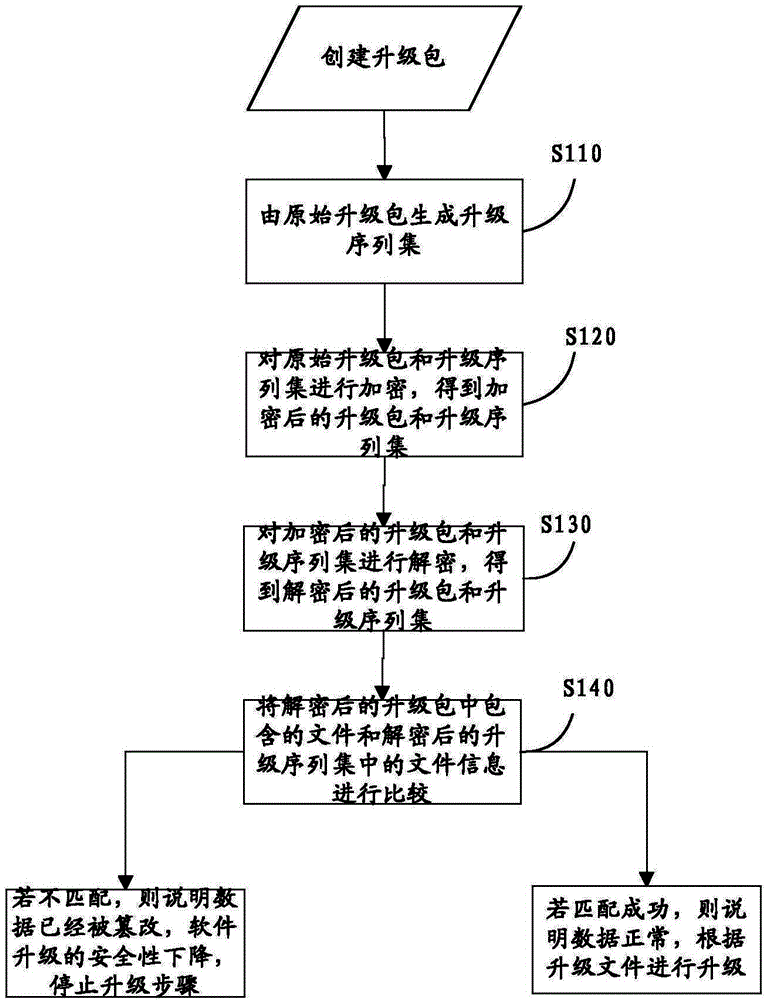
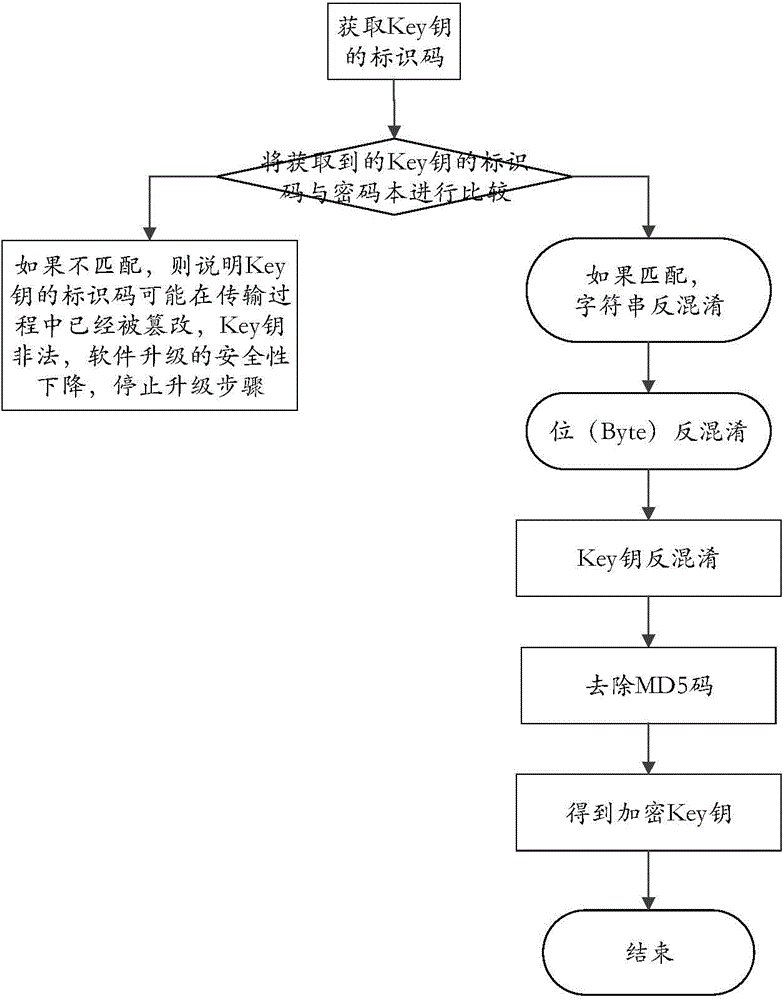
Method and device of upgrading Web software
ActiveCN104135531AReduce the risk of tamperingImprove securityEncryption apparatus with shift registers/memoriesProgram loading/initiatingUpgradeServer-side
The invention relates to the technical field of software upgrading and discloses a method and a device of upgrading Web software. The method comprises the following steps of: at an upgrade server side: generating an upgrade sequence set by an original upgrade package; encrypting the original upgrade package and the upgrade sequence set to obtain an encrypted upgrade package and an encrypted upgrade sequence set; at a local service side: decrypting the encrypted upgrade package and the encrypted upgrade sequence set to obtain a decrypted upgrade package and a decrypted upgrade sequence set; comparing a file included in the decrypted upgrade package and file information in the decrypted upgrade sequence set; if not matched, stopping upgrading; and if matched successfully, upgrading according to an upgrade file. According to the method and the device, when data are transmitted, the encryption processing is carried out on the data, so that the risk of tampering the data is reduced; in addition, accuracy of the obtained upgrade file is judged, so that security of software upgrading is improved.
Owner:武汉益模科技股份有限公司
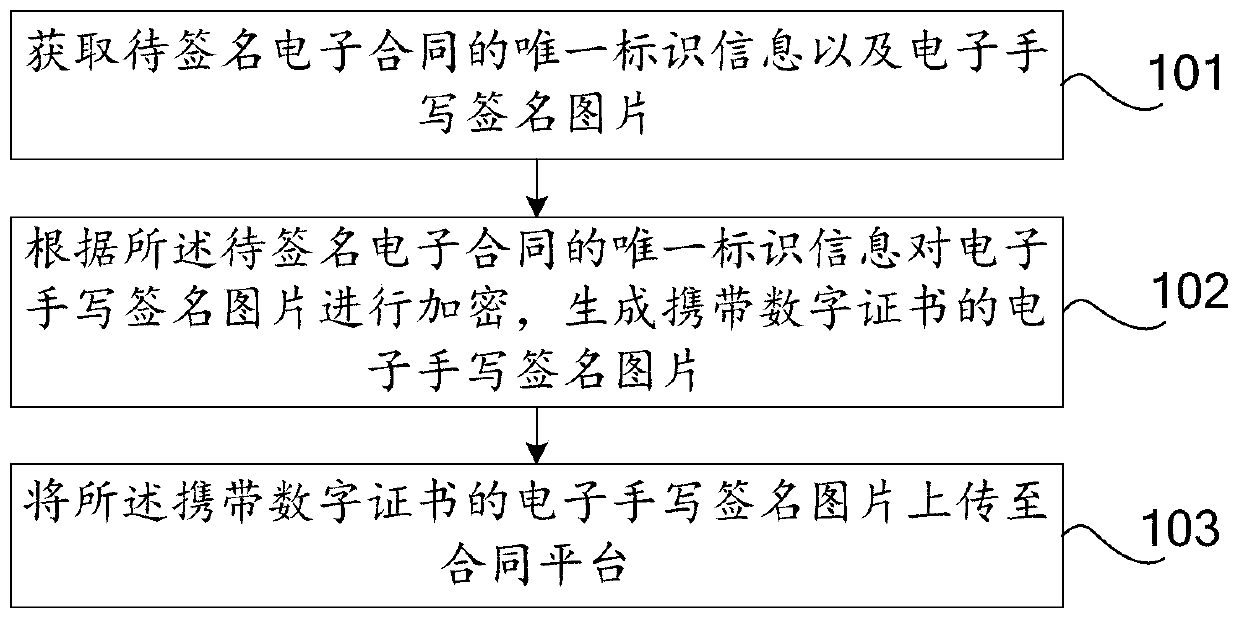
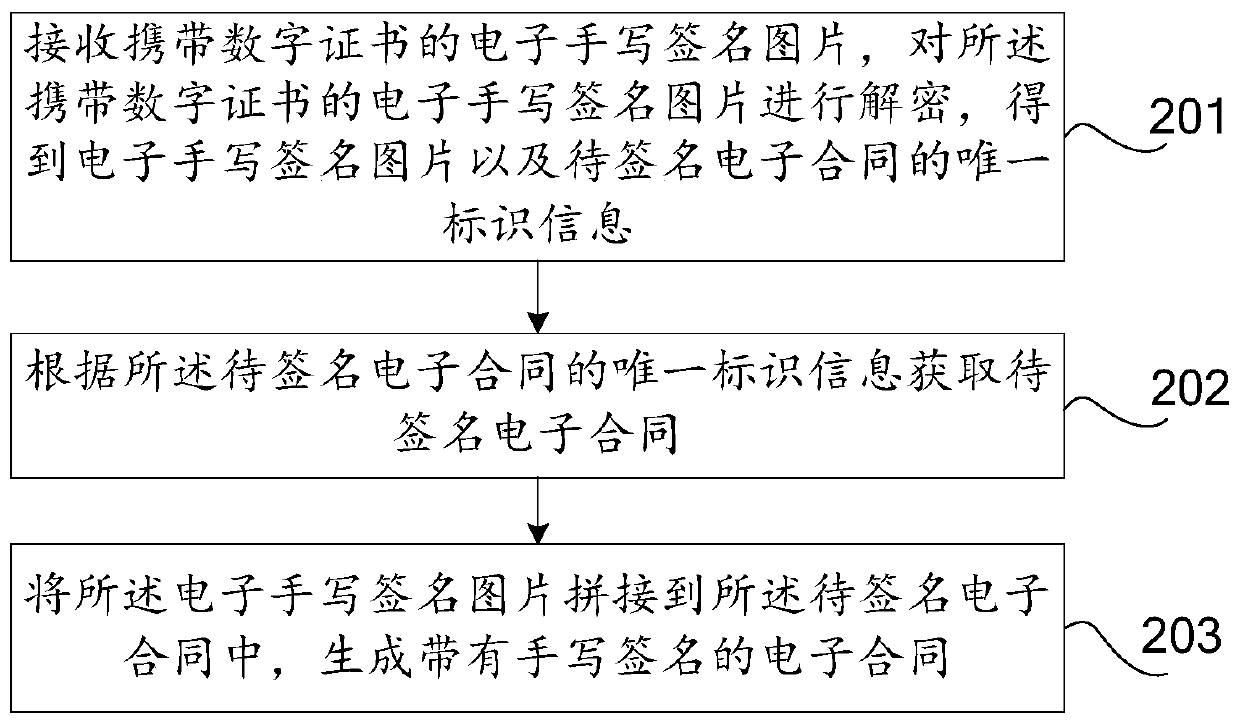
Method, device and system for generating electronic contract based on handwritten signature picture
PendingCN109829317AReduced risk of tamperingEnsure safetyDigital data protectionElectronic contractsComputer science
The invention discloses a method, device and system for generating an electronic contract based on a handwritten signature picture, relates to the technical field of electronic signatures, and can reduce the risk that the electronic contract is tampered. The method comprises the following steps: obtaining unique identification information of a to-be-signed electronic contract and an electronic handwritten signature picture; Encrypting the electronic handwritten signature picture according to the unique identification information of the to-be-signed electronic contract to generate an electronichandwritten signature picture carrying a digital certificate; Uploading the electronic handwritten signature picture carrying the digital certificate to a contract platform, so that the contract platform decrypts the electronic handwritten signature picture carrying the digital certificate to obtain the electronic handwritten signature picture and unique identification information of an electronic contract to be signed; Obtaining a to-be-signed electronic contract according to the unique identification information of the to-be-signed electronic contract; And splicing the electronic handwritten signature picture into the to-be-signed electronic contract to generate the electronic contract with the handwritten signature.
Owner:PING AN TECH (SHENZHEN) CO LTD
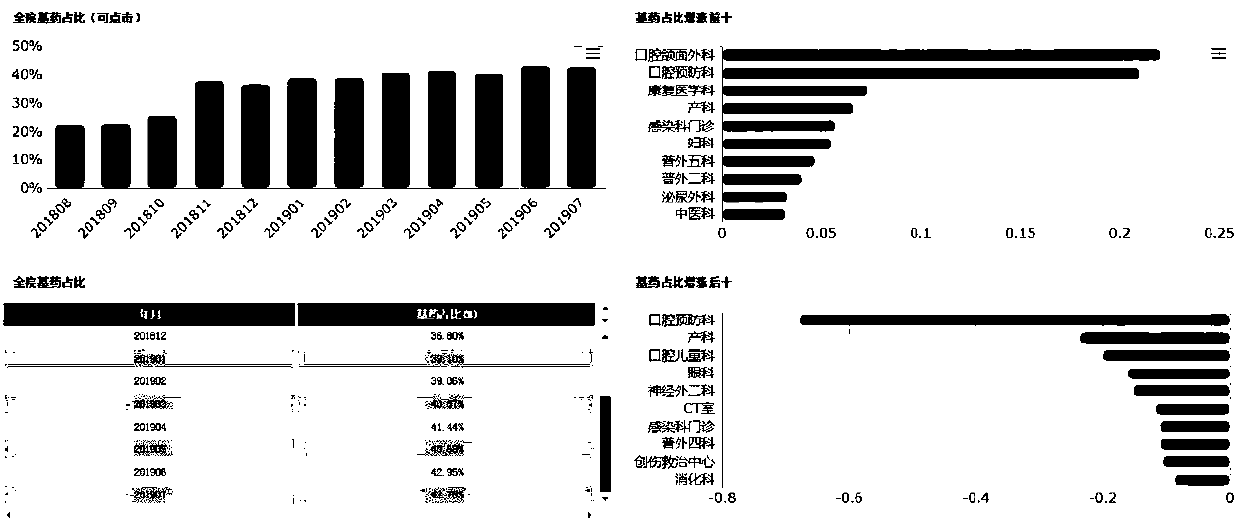
Hospital low-administration risk prevention and control system developed based on commercial intelligent system
InactiveCN110765116ARespond quicklyReduced risk of tamperingDatabase management systemsData miningData warehouseRisk indicator
The invention discloses a hospital low-administration risk prevention and control system developed based on a commercial intelligent system, and relates to the technical field of medical information.According to the system, all business information systems in a hospital are integrated together by using an existing business intelligent system; and the system performs the following steps: extracting information mainly monitored by hospital record inspection from data in an information island of an online running business system (HIS, RIS, LIS, HERP, PASS and the like) into a data warehouse through an ETL tool in a commercial intelligent system; carrying out data mining on the data in the data warehouse, defining the data into index items in a multi-dimensional manner, and then integrating the index items into data needing to be displayed; finally, data needing to be displayed is made into various charts through a sail soft report tool, and the charts are visually displayed through an information display platform. After the system is actually operated, the daily management workload of a hospital commemorator is greatly reduced, the risk that data is tampered is reduced, risk indexescan be monitored in real time, and adverse events and violation events are prevented from happening.
Owner:杨志刚
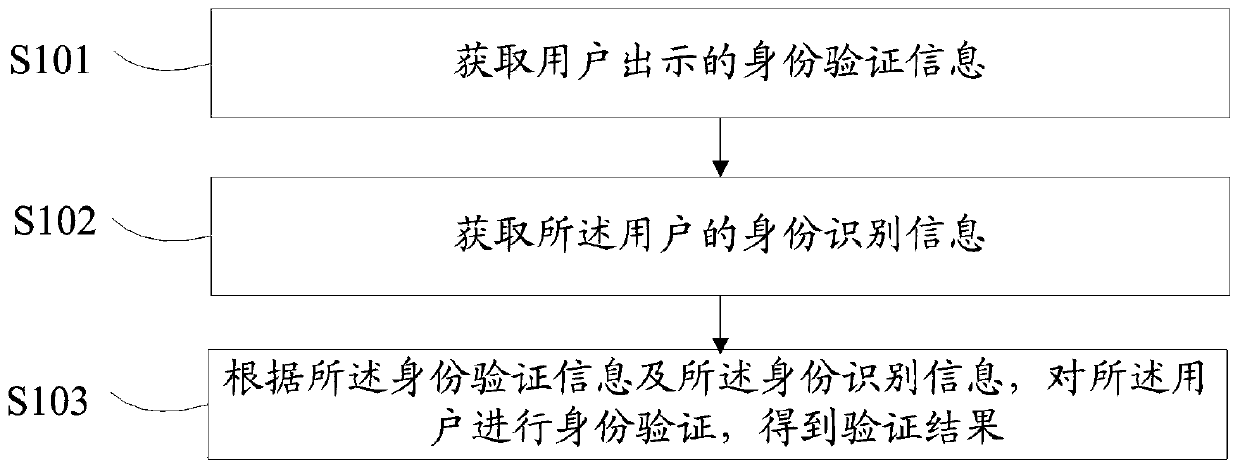
Identity verification method, device and equipment
PendingCN110378091AReduced risk of tamperingImprove safety and efficacyDigital data authenticationThird partyInternet privacy
The embodiment of the invention discloses an identity verification method, device and equipment. According to the scheme, the method comprises the steps that identity verification information shown bya user is acquired, the identity verification information is generated according to information fed back by a third-party server in response to an identity identifier generation request carrying a user identity certificate, and identity recognition information of the user is acquired; and performing identity verification on the user according to the identity verification information and the identity recognition information to obtain a verification result.
Owner:ADVANCED NEW TECH CO LTD
Coupon data processing method, device and system and storage medium
ActiveCN109191194AReduced risk of tamperingImprove securityDiscounts/incentivesFinanceComputer networkBlockchain
The embodiment of the invention discloses a coupon data processing method, device and system and a storage medium, wherein, the method comprises the following steps: a user terminal obtains coupon data corresponding to a service event in a first block chain node; the coupon data is service data selected in a user account based on the service event; the user terminal obtains the coupon data corresponding to the service event in the first block chain node; the user terminal sends the service event and the coupon data to the service terminal based on the service server; the service terminal receives the service event and the coupon data sent by the user terminal; the service terminal obtains the data transfer information corresponding to the coupon data in the second block chain node, and obtains the attribute information corresponding to the coupon data based on the service server; the service terminal verifies the coupon data based on the data transfer information and attribute information, and executes the service event after the verification is passed. By adopting the invention, the risk that the coupon data and the attribute information are tampered with can be effectively reduced, and the security of the coupon data and the attribute information can be improved.
Owner:TENCENT TECH (SHENZHEN) CO LTD
Display result generation method, system and device, readable storage medium and equipment
ActiveCN111814083AGuaranteed accuracyConfidenceDatabase distribution/replicationDigital data protectionComputer hardwareData set
The invention provides a display result generation method, a display result generation system, a display result generation device, a computer readable storage medium and electronic equipment, and relates to the technical field of computers. The method comprises the steps of obtaining a first-class interaction data set corresponding to a display object; receiving a second-class interaction data setwhich is sent by the participant equipment and aims at the display object, and obtaining second-class evidence storage data corresponding to the display object from the blockchain network; performingcorrectness verification on the second-class interaction data set according to the second-class evidence storage data; and if the second-class interaction data set is correct, generating a display result corresponding to the display object according to the first-class interaction data set and the second-class interaction data set. It can be seen that the risk that the data is tampered can be reduced and the accuracy of the display result is ensured by implementing the technical scheme of the invention.
Owner:TENCENT TECH (SHENZHEN) CO LTD
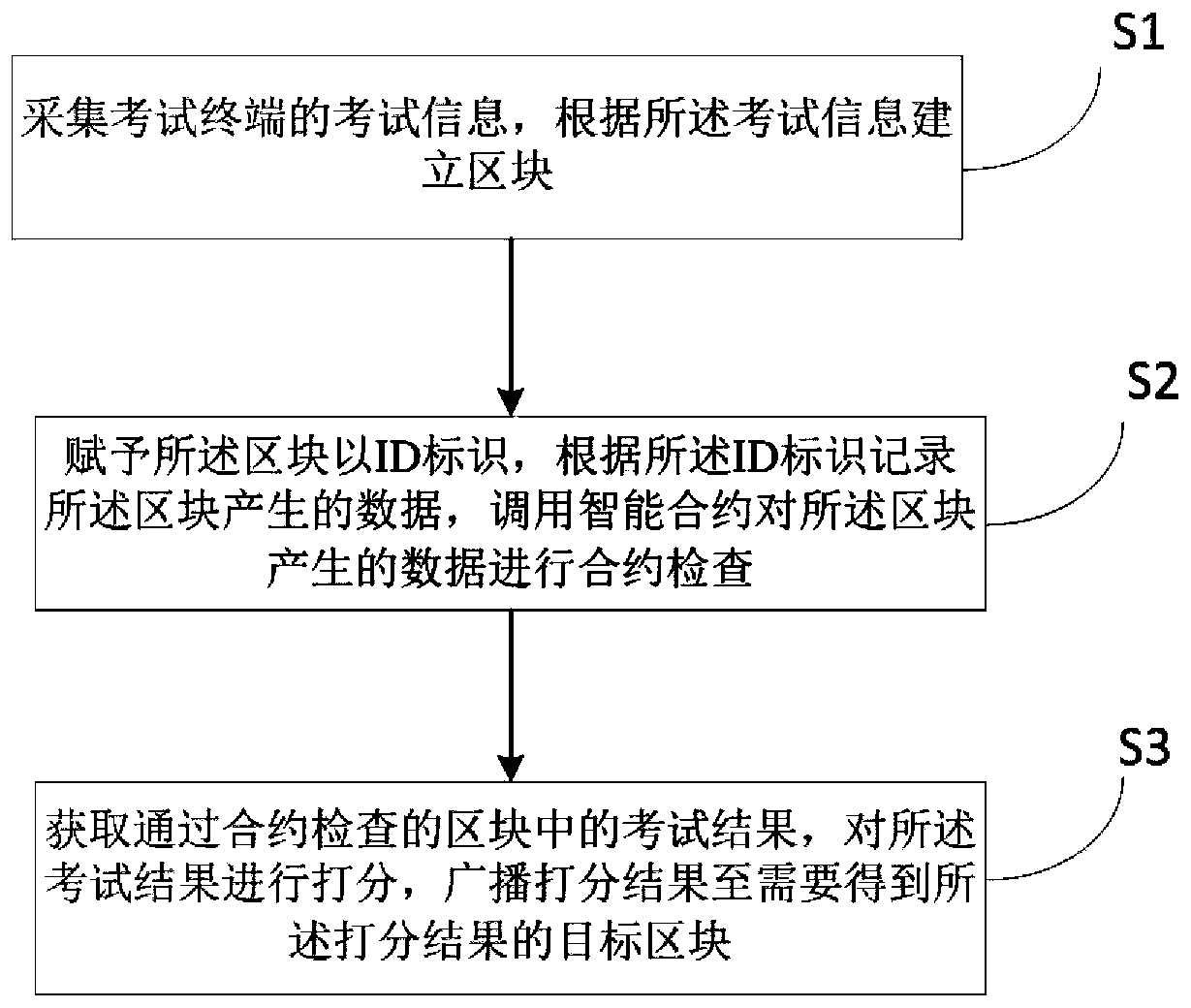
Examination information evaluation method and device based on block chain, equipment and storage medium
ActiveCN109951441AReduced risk of tamperingReduce the risk of counterfeitingData processing applicationsDigital data protectionBroadcastingComputer science
The invention relates to the technical field of block chains, in particular to an examination information evaluation method and device based on a block chain, equipment and a storage medium. The method comprises: collecting examination information of an examination terminal, and establishing a block according to the examination information; assigning an ID identifier to the block, recording data generated by the block according to the ID identifier, and calling an intelligent contract to carry out contract check on the data generated by the block; and obtaining an examination result in the block which passes contract examination, scoring the examination result, and broadcasting the scoring result to a target block which needs to obtain the scoring result. Through the block chain technology, the risk that the examination performance is tampered is reduced, the counterfeiting risk is reduced for workplace workers, education training and the like, and the social activity efficiency is improved.
Owner:ONE CONNECT SMART TECH CO LTD SHENZHEN
Intelligent water meter system with remote valve control function
ActiveCN105388867AThe transfer process is clearSimple structureVolume meteringTransmissionWater utilityCommunications system
The invention discloses an intelligent water meter system with a remote valve control function, and relates to the technical field of Internet-of-things intelligent water meters. The intelligent water meter system comprises an intelligent water meter sensing unit, an intelligent water meter valve control unit, a sensing information communication system, a control information communication system, and a water supply company water supply integrated management system. The intelligent water meter sensing unit and the intelligent water meter valve control unit are respectively in communication connection with the water supply company water supply integrated management system through the sensing information communication system and the control information communication system. Valve control of the intelligent water meter is realized. The intelligent water meter system has a simple structure. The transmission process is diverse. Information transmission is safer and more reliable. The intelligent water meter remote valve control function can be effectively responded to and controlled.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
Intelligent gas meter system with prepayment function
ActiveCN105336142ASimple structureFacilitate transmissionTransmission systemsTransmissionCommunications systemInformation transmission
The invention discloses an intelligent gas meter system with a prepayment function and relates to the technical field of IOT (Internet of things) intelligent gas meters. The intelligent gas meter system comprises an intelligent gas meter sensing unit, an intelligent gas meter prepayment control unit, a sensing information communication system, a control information communication system and a gas-company gas integrated management system, wherein the intelligent gas meter sensing unit and the intelligent gas meter prepayment control unit establish communication connection with the gas-company gas integrated management system through the sensing information communication system and the control information communication system respectively; prepayment control of the intelligent gas meter is realized. The intelligent gas meter system is simple in structure, the transmission process is diversified, the information transmission is safer and more reliable, and response and control for the prepayment function of the intelligent gas meter can be effectively realized.
Owner:CHENGDU QINCHUAN IOT TECH CO LTD
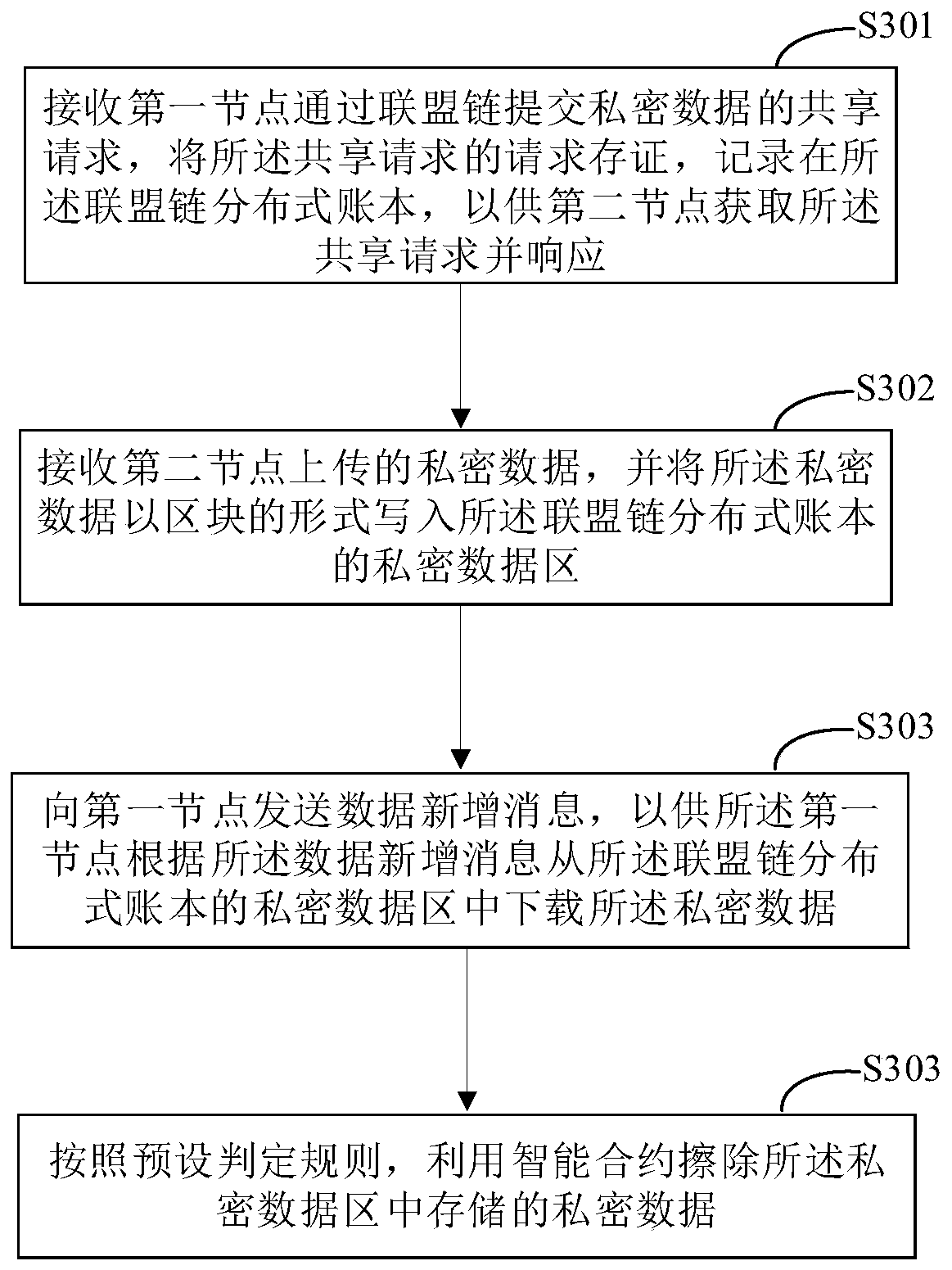
Data sharing method and device, electronic equipment and readable storage medium
PendingCN111368327AReduced risk of tamperingImprove securityDigital data protectionComputer networkEngineering
According to the data sharing method and device, the electronic equipment and the readable storage medium provided by the invention, the sharing request of the private data submitted by the first nodethrough the alliance chain is received, and the request of the sharing request is stored and recorded in the alliance chain distributed account book, so that the second node obtains the sharing request and responds to the sharing request; receiving private data uploaded by a second node, and writing the private data into a private data area of the alliance chain distributed account book in a block form; sending a data addition message to a first node, so that the first node downloads the private data from a private data area of the alliance chain distributed account book according to the dataaddition message; according to the embodiment of the invention, the sharing request and the private data are stored on the alliance chain distributed account book, so that the risk of being tamperedis reduced, the security is improved, the whole process is automated, and the efficiency is improved.
Owner:CHINA UNITED NETWORK COMM GRP CO LTD
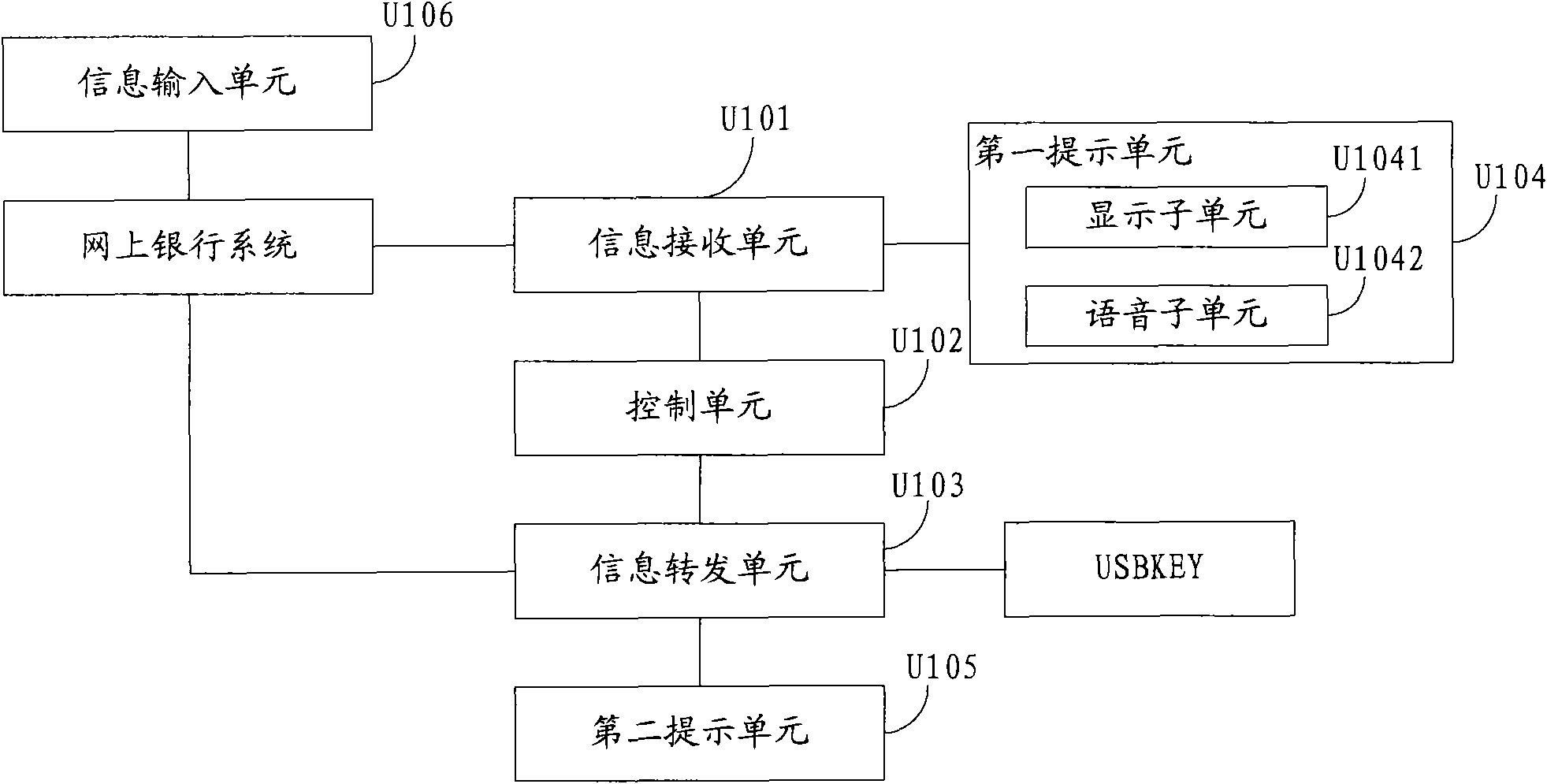
Device and method for assisting in realizing USB Key safety
The invention discloses a device for assisting in realizing USB Key safety. The device is connected between a device for operating an on-line bank system and a USB Key and comprises an information receiving unit, a control unit and an information transferring unit, wherein the information receiving unit is used for receiving transaction data information sent by the on-line bank system; the controlunit is used for sending the transaction data information to the USB Key when confirming information of users is received; and the information transferring unit is used for receiving the transactiondata information after the USB Key carries out digital signing and returning the transaction data information to the on-line bank system. By using the device, the common USB Key can have the same safety property with the USB Key with a confirm key. Simultaneously, if the control unit can not normally receive the confirming information, only the device is replaced without changing , therefore, thecost is saved.
Owner:CHINA CITIC BANK
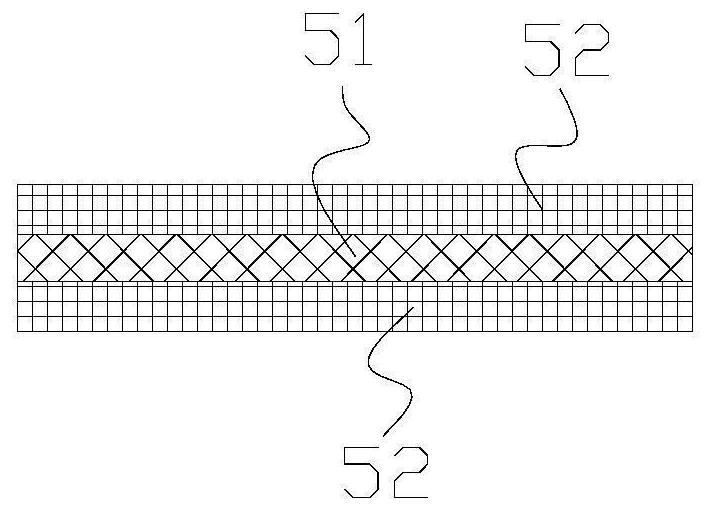
Lithium battery core and manufacturing method thereof
PendingCN113471546AReduced risk of tamperingReduced risk of short circuitsFinal product manufactureSecondary cellsStructural engineeringPositive current
The invention discloses a lithium battery core and a manufacturing method. The lithium battery core comprises at least one positive electrode sheet, at least one negative electrode sheet and at least one diaphragm, wherein the positive electrode sheet comprises a positive current collector and a positive electrode active material, the positive current collector comprises a plurality of first small sheets which are parallel at intervals, the adjacent first small sheets are connected by bent blank areas, the positive electrode active material is coated on the side surface of the first small sheet, the negative electrode sheet comprises a negative current collector and a negative electrode active material, the negative current collector comprises a plurality of second small sheets which are parallel at intervals, the adjacent second small sheets are connected by bent blank areas, the diaphragm is bent in an S shape, and the first small sheets and the second small sheets are sequentially and alternately connected to the space formed after the diaphragms are bent and between the adjacent diaphragms, and are connected with the diaphragms. The manufacturing method comprises the steps of inserting, folding and combining. According to the invention, the electrode sheets are fixed, the short-circuit risk of the battery core is reduced, the production efficiency is improved, the lamination qualification rate can be effectively improved, and the production process is effectively simplified.
Owner:HEFEI GUOXUAN HIGH TECH POWER ENERGY
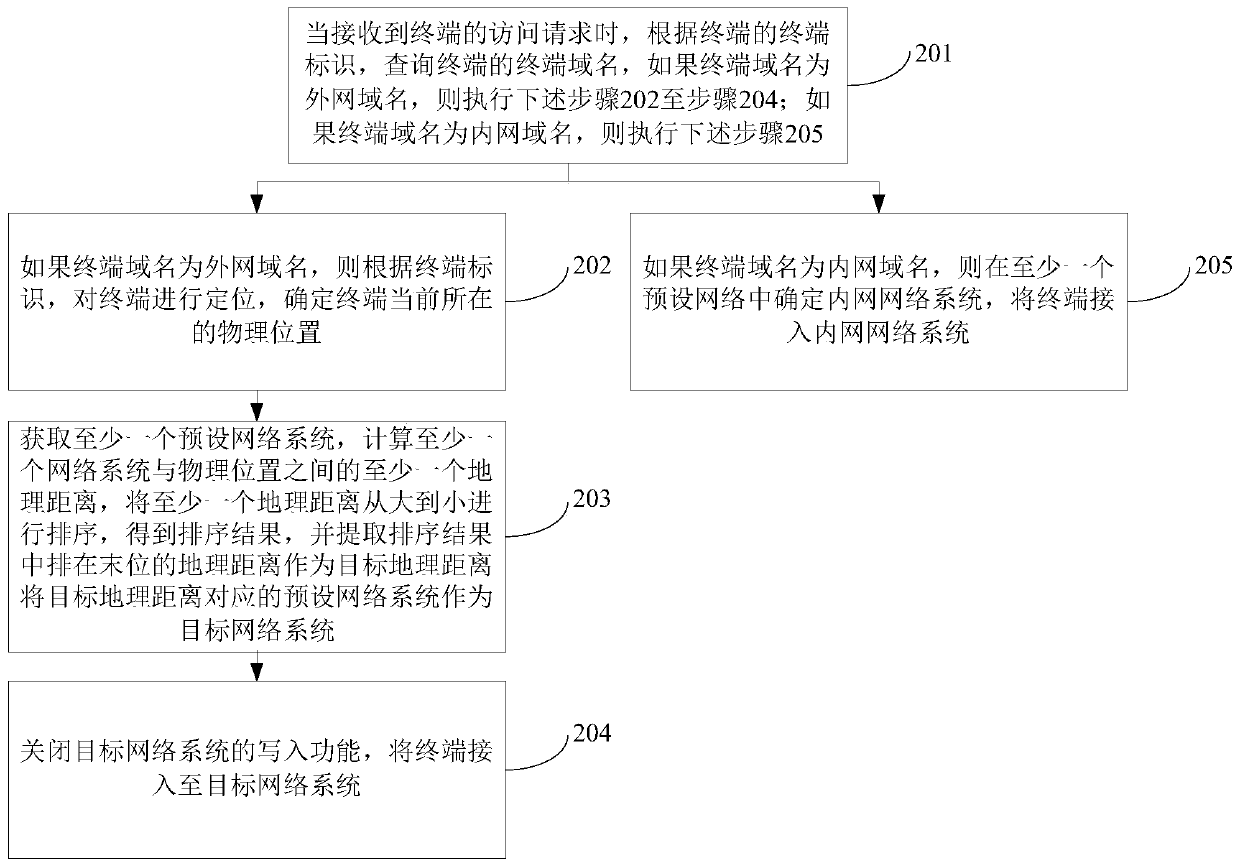
Network system access method and device, computer equipment and readable storage medium
The invention discloses a network system access method and device, computer equipment and a readable storage medium, relates to the technical field of Internet, and aims to determine whether to starta write-in function for a terminal or not according to a terminal domain name of the terminal, reduce the risk that data in a network system is tampered, and effectively ensure the safety and high availability of the network system. The method comprises the steps that when an access request of a terminal is received, inquiring a terminal domain name of the terminal according to a terminal identifier of the terminal, and the terminal domain name indicates the access permission of the terminal to a network system; if the terminal domain name is an external network domain name, determining the current physical position of the terminal, selecting a target network system from at least one preset network system according to the physical position, and enabling the target geographic distance between the target network system and the physical position to meet the distance requirement; and closing a write-in function of the target network system, and accessing the terminal to the target networksystem.
Owner:PING AN TECH (SHENZHEN) CO LTD
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com