Encrypted data storage system based on key other-place storage and method
A storage system and technology for encrypting data, applied in the fields of information transmission and storage and information security, can solve the problems of safe separation of encryption keys and ciphertext data, and achieve unconditional security, low power consumption, and reduced data security protection costs. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
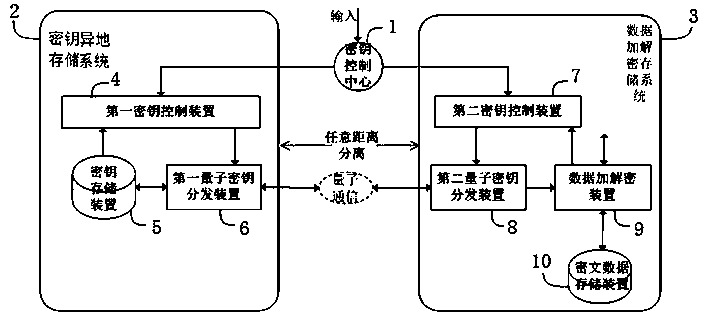
[0096] Example 1: see figure 2 , figure 2 It only shows the basic structure of key remote storage system 2 and data encryption and decryption storage system 3 in the application of database system, that is, it shows the basic security principles of establishing database encrypted storage and access, and database security backup, and completes the key-based remote storage The combination of the encrypted data storage system and various security control devices in the database system improves the security of the data. The specific structure is as follows.
[0097] The encrypted data storage system based on remote storage of keys is in the database application system. The database application system refers to the structured database application system, or the unstructured database application system, or the cloud storage application system. The entire system structure includes the control center, encryption key remote storage system 2, data encryption and decryption storage sy...
Embodiment 2
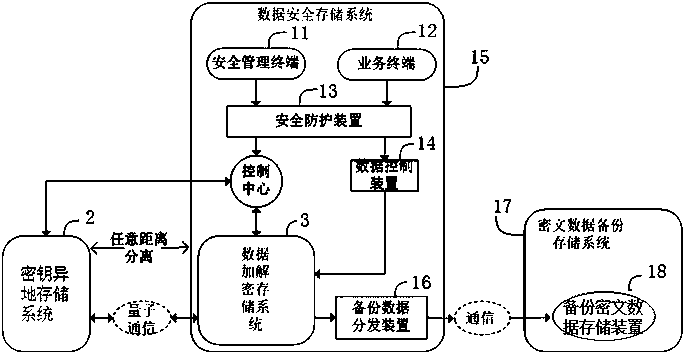
[0101] Example 2: see image 3 , image 3 It only shows the basic structure and principle of the encrypted data storage system based on remote key storage in database active-active application, and completes the combination of the encrypted data storage system based on remote key storage and the encryption device of the database active-active system, which greatly improves the database security. The security of the active-active system also improves the high reliability guarantee of the active-active database application. The specific structure is as follows.
[0102] The database active-active system of the encrypted data storage system based on the remote storage of keys, wherein the database application system can be a structured database application system, or an unstructured database application system, or an active-active or multi-active database system of a cloud storage application system , the system structure includes a control center, a remote storage system 2 for ...
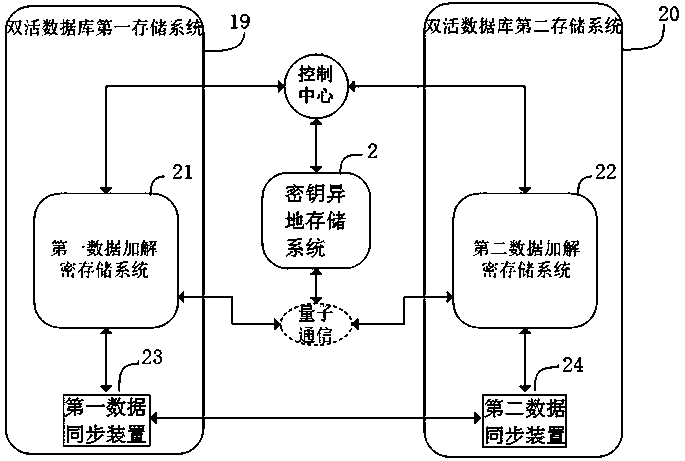
Embodiment 3
[0105] Embodiment 3: see Figure 4 , Figure 4 It only illustrates the basic structure and principle of the application of the dual-key remote storage system 2 based on the encrypted data storage system stored in different places, which realizes multiple remote storage of keys and improves the efficiency and security of key storage. The dual-key off-site storage system 2 includes a key control center 1, a data security storage system 15, a first key off-site storage system 25, and a second key off-site storage system 26; the data security storage system 15 includes a data encryption and decryption storage system 3;
[0106] The key control center 1 controls the data encryption and decryption storage system 3, the first key remote storage system 25 and the second key remote storage system 26 to work, and the specific encryption method and decryption method are the same as figure 1 The encryption method and decryption method in the structure are basically the same, the differe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com