Novel authentication mechanism for encrypting vector
An encryption authentication, vector technology, applied in the basic field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
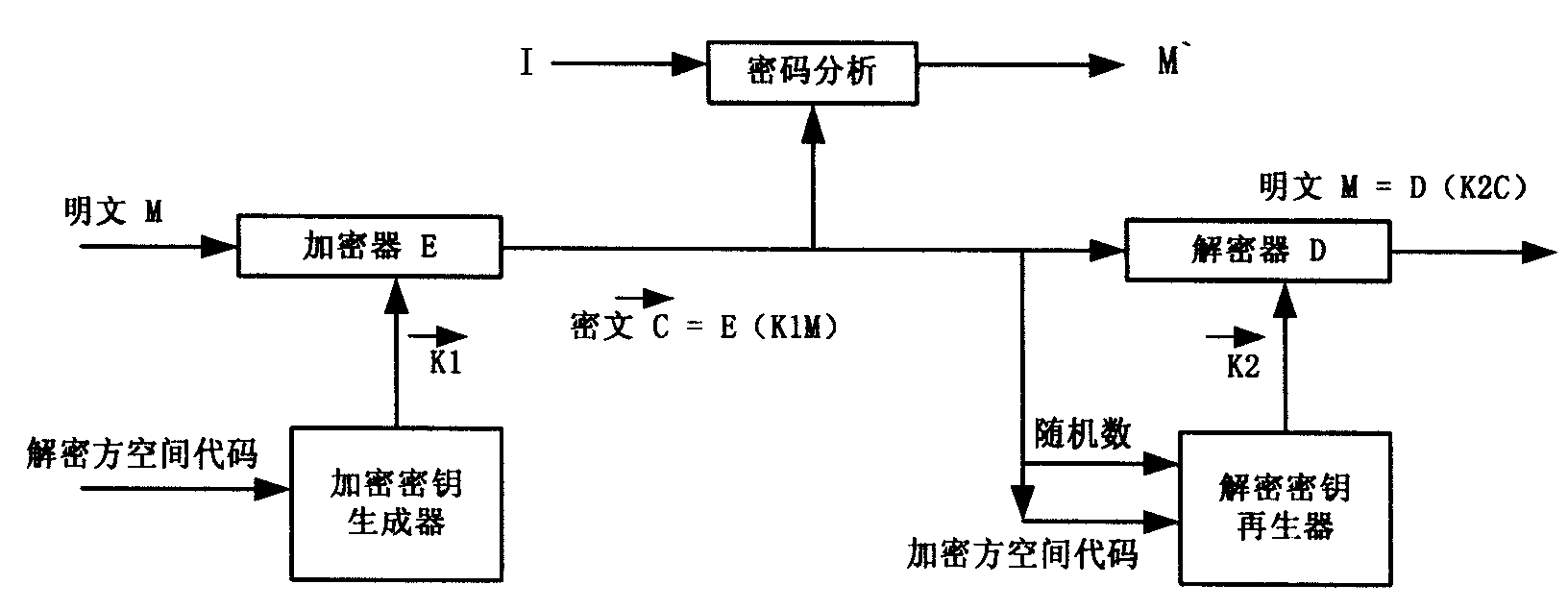
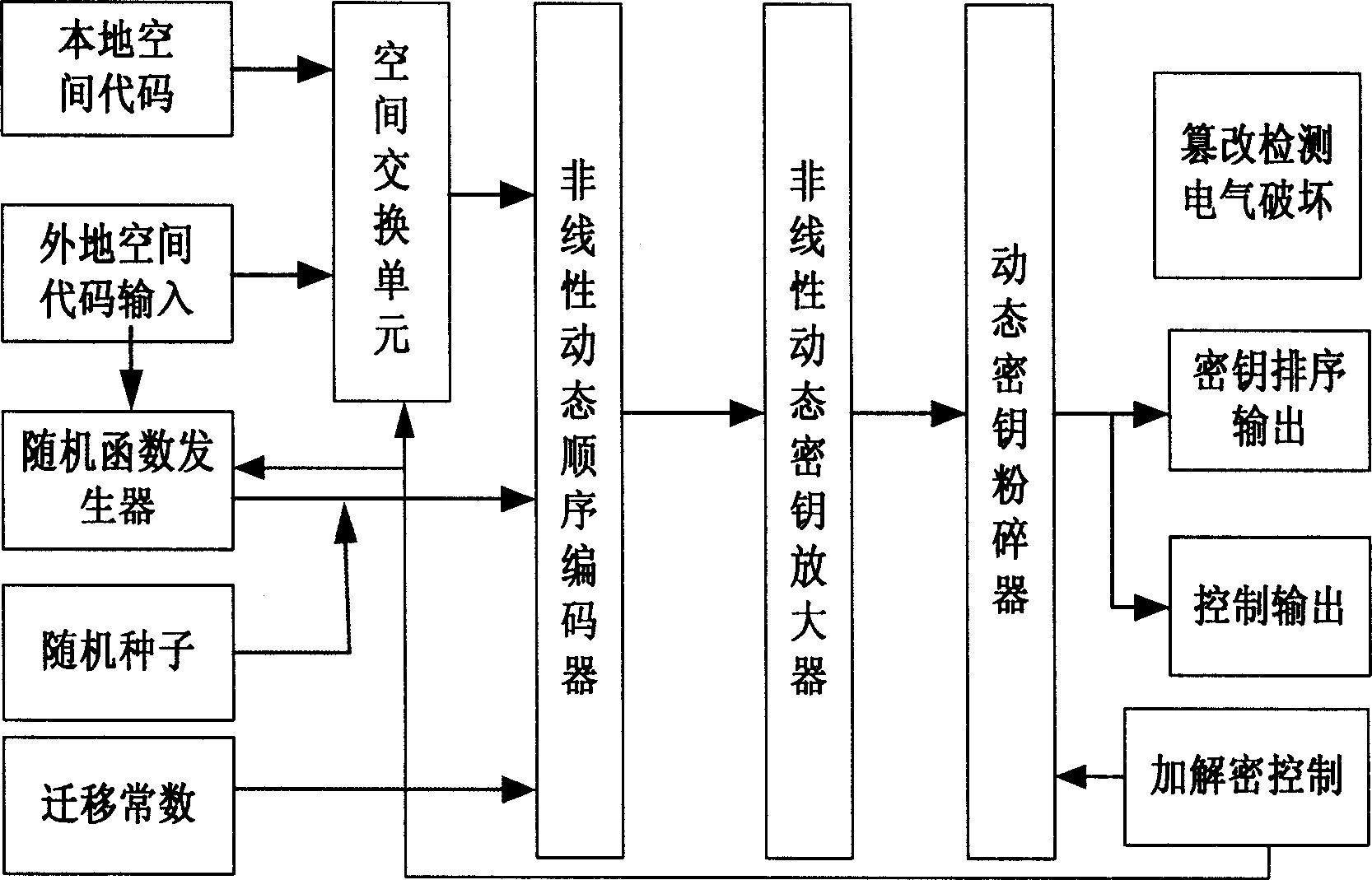
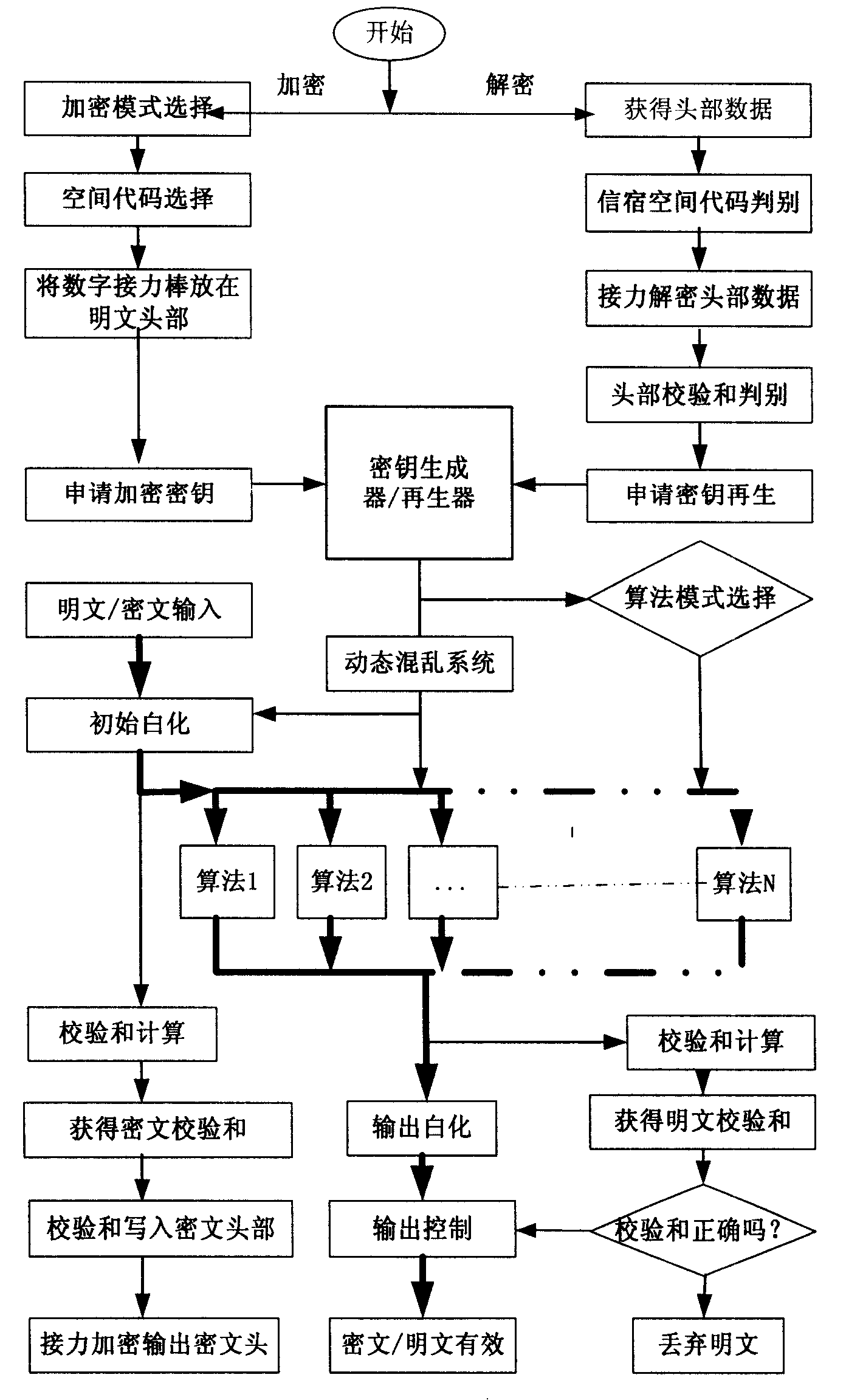
[0162]After the legal decryptor receives the ciphertext information, start the software module and choose to decrypt, and then tell the system the location of the ciphertext. The software first takes out the space code of the legal destination in the head and compares it with the space code of the machine. If they are the same, then The sink is authenticated, and then uses the encryptor's space code to retrieve the last digital relay key from the communication database to decrypt the ciphertext header. If the header checksum is correct, use the subsequent header data to apply to the hardware key regenerator. To solve the key regeneration, the key regenerator first starts the space exchange unit to exchange the position of the internal / external space code, and then sends the internal / external space code, key material and migration constant to the nonlinear sequence encoder to generate the seed key, and then passes The key is amplified and crushed, and the qualified decryption ke...
Embodiment 2
[0172] After the terminal PTM module of user B receives the ciphertext information, it takes out the space code of the legal destination and compares it with itself, so as to confirm that the legal destination is itself, obtains the verification data from the decryption of the ciphertext header, and judges that the data is valid according to the header checksum Then, send the follow-up source space code, random key material and encryption mode to the key regenerator to regenerate the decryption vector key, decrypt the ciphertext information, obtain the digital baton, plaintext and checksum, and based on the calibration Whether the checksum is correct or not disposes of the plaintext.
[0173] If the checksum is wrong, it means that the obtained ciphertext information has been tampered with, then discard the plaintext; if the checksum is correct, then judge whether the obtained plaintext information is a replay of past information according to the digital baton, and discard the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com