Patents
Literature
Hiro is an intelligent assistant for R&D personnel, combined with Patent DNA, to facilitate innovative research.
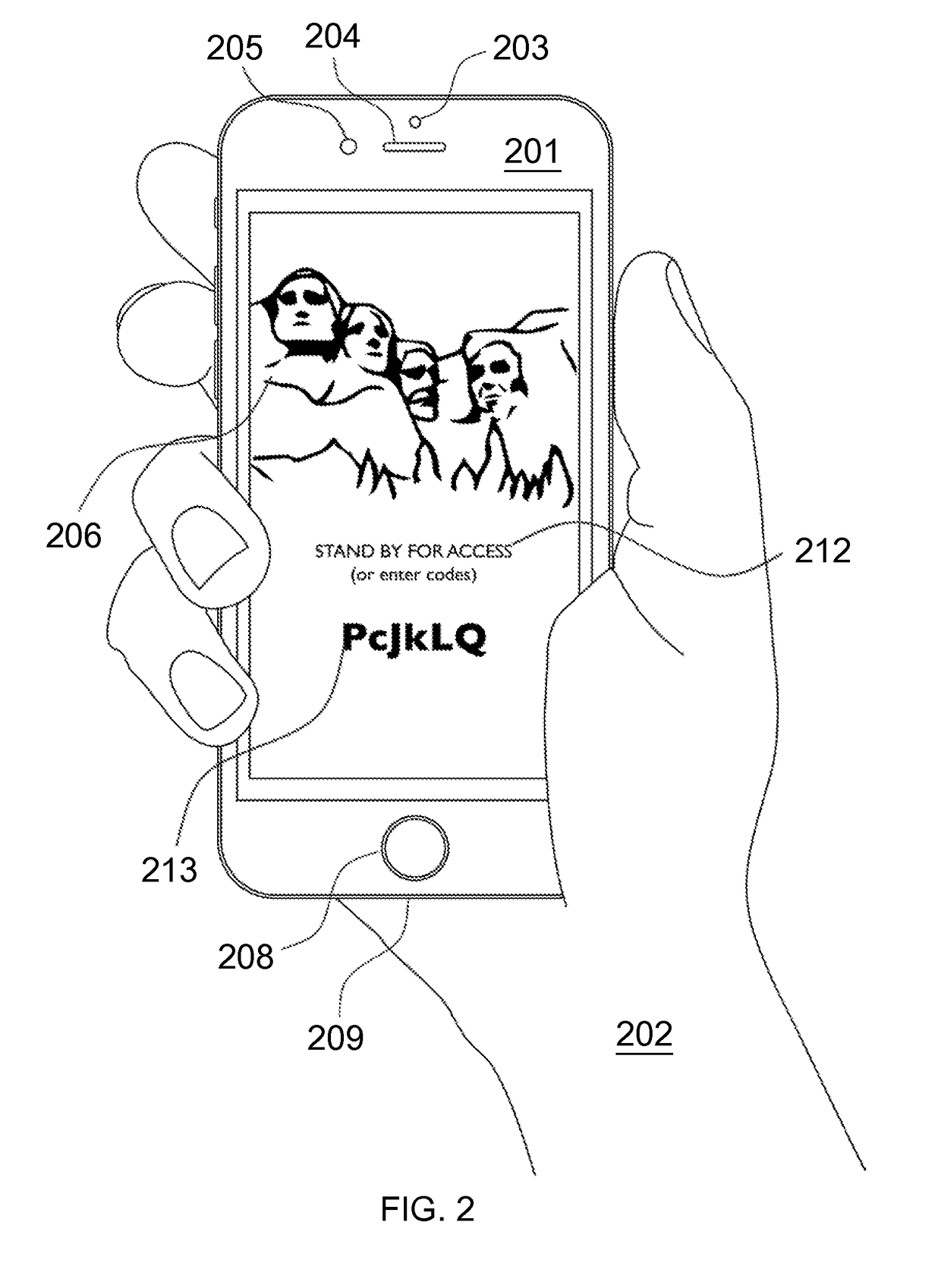
445 results about "Landing page" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
In online marketing, a landing page, sometimes known as a "lead capture page", "static page", or a "destination page", is a single web page that appears in response to clicking on a search engine optimized search result, marketing promotion, marketing email, or an online advertisement. The landing page will usually display directed sales copy that is a logical extension of the advertisement, search result or link. Landing pages are used for lead generation. The actions that a visitor takes on a landing page is what determines an advertiser's conversion rate.
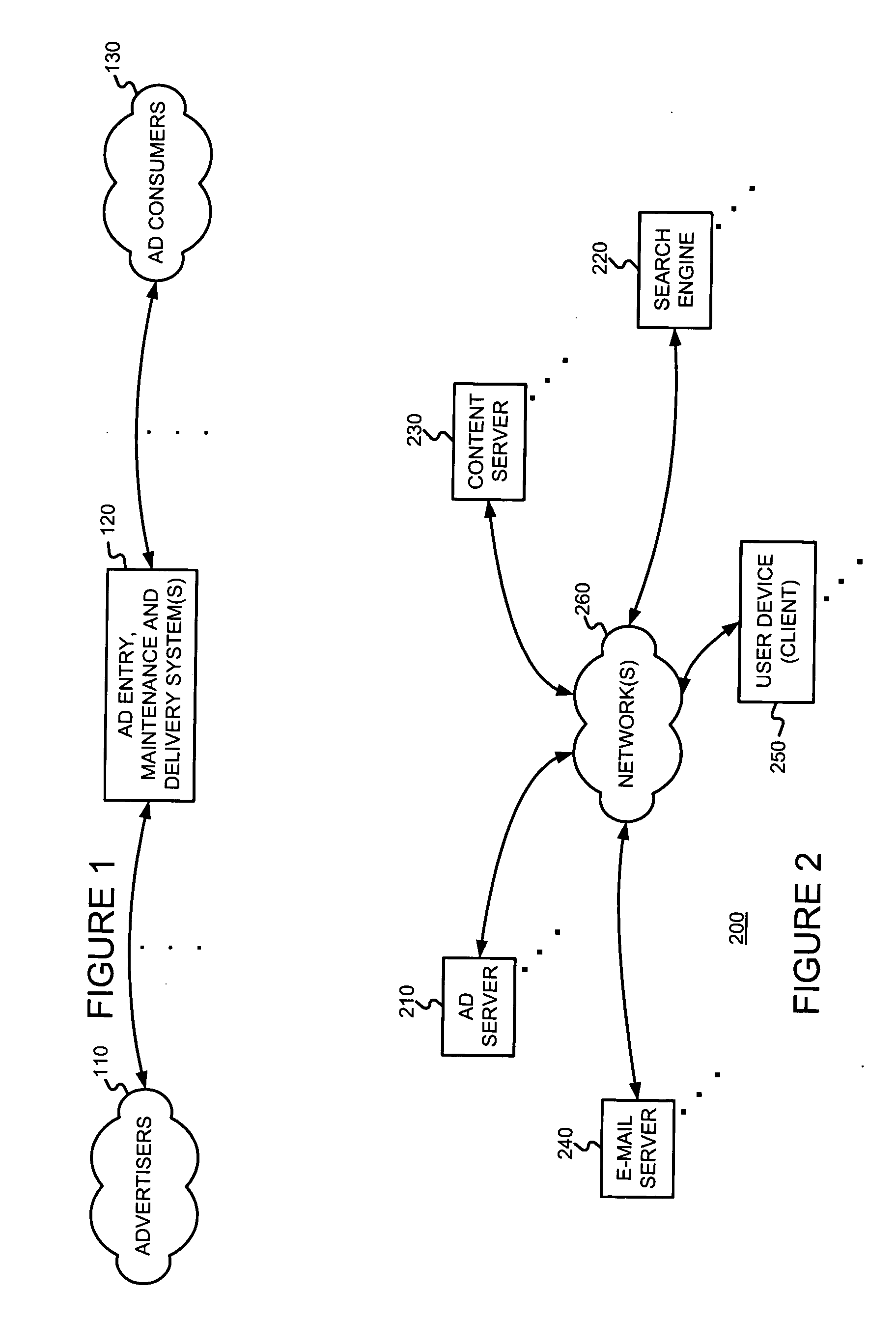
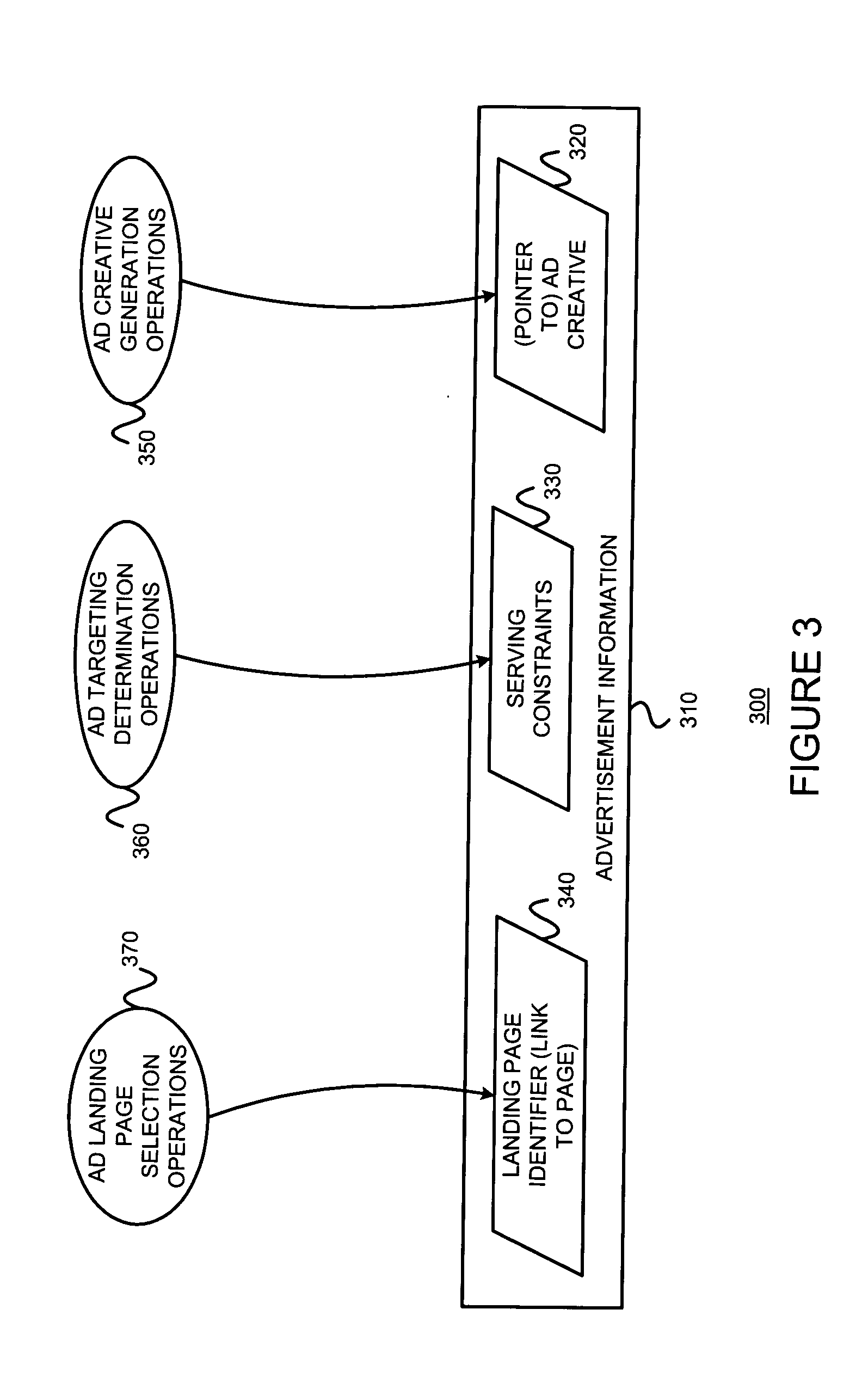
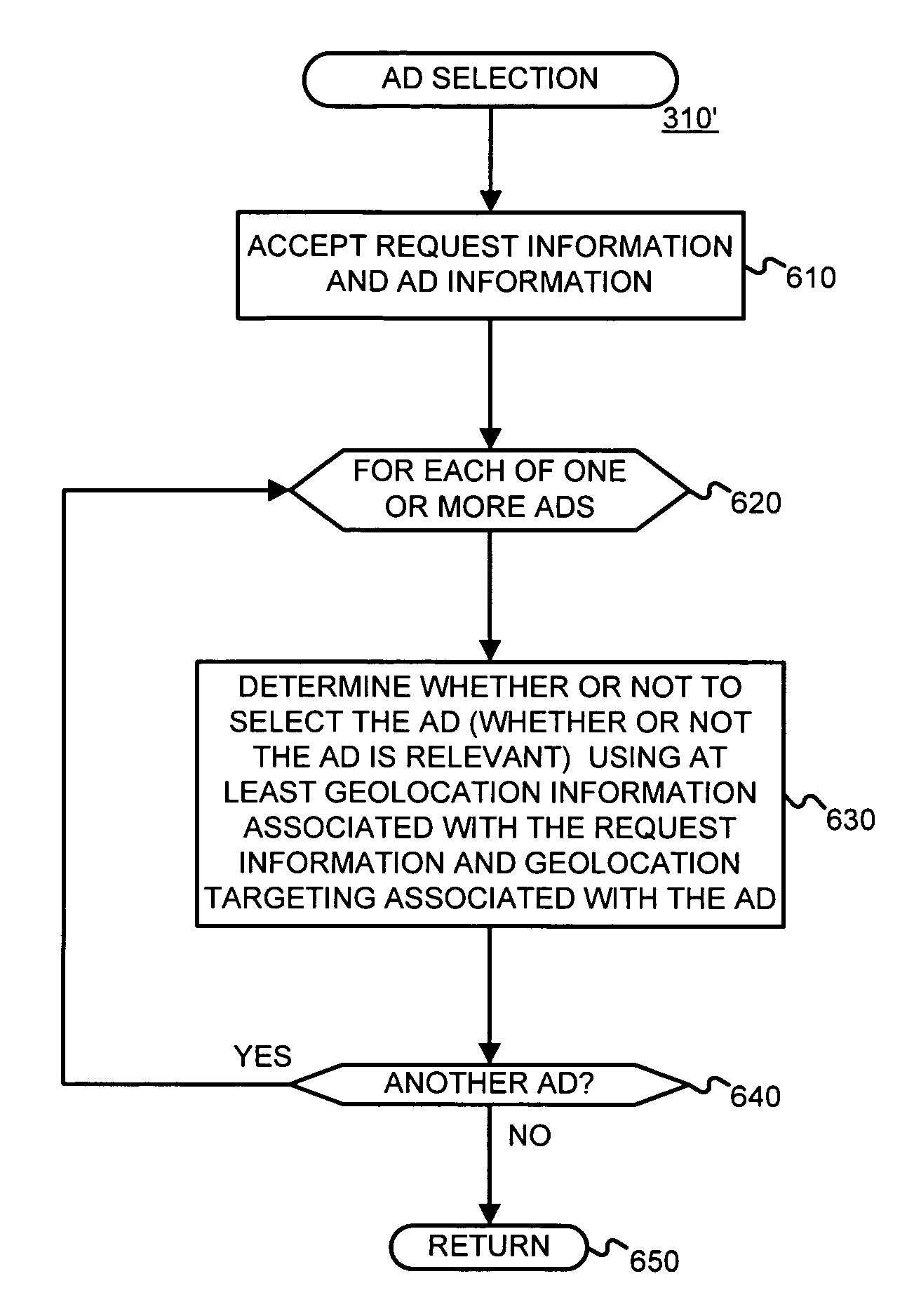
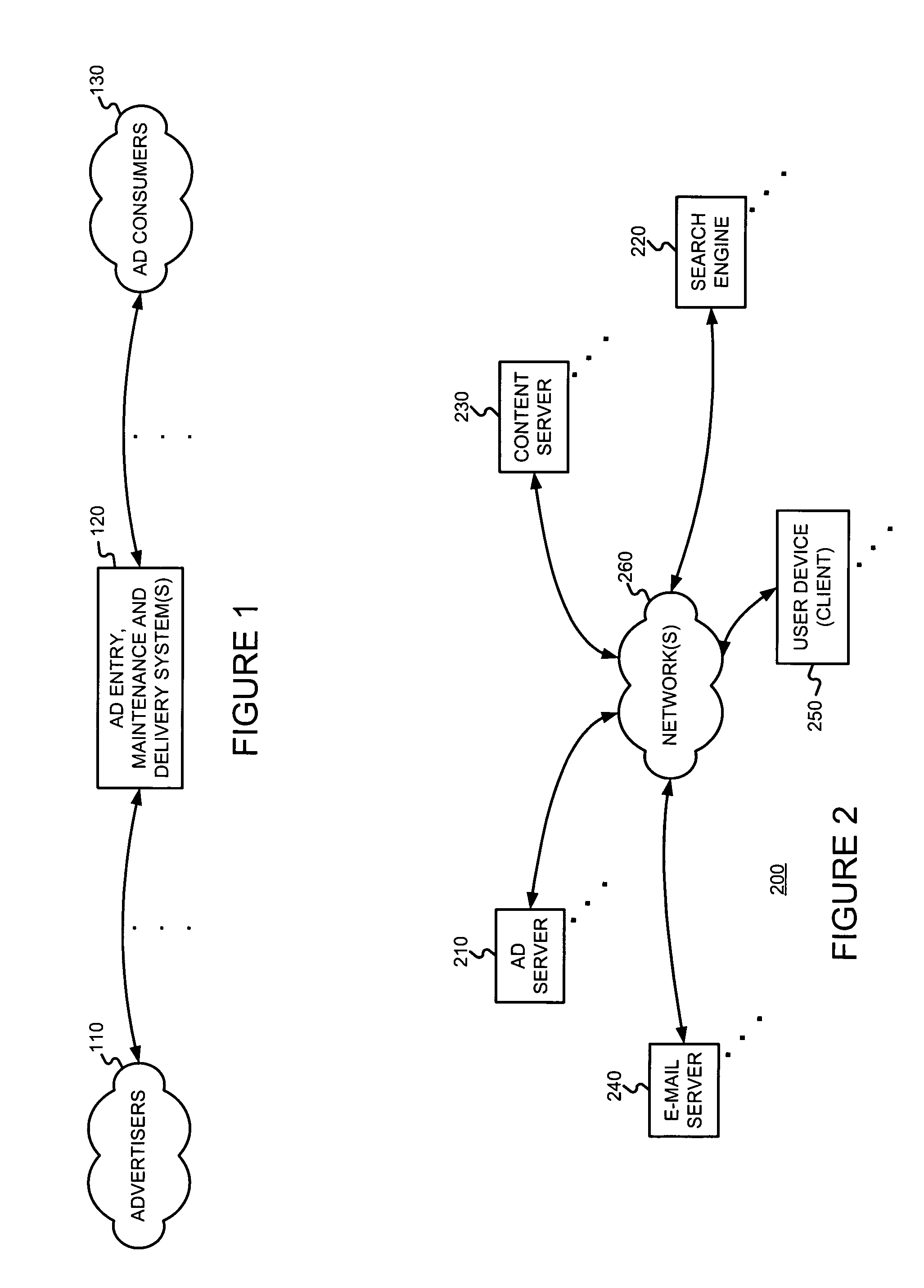
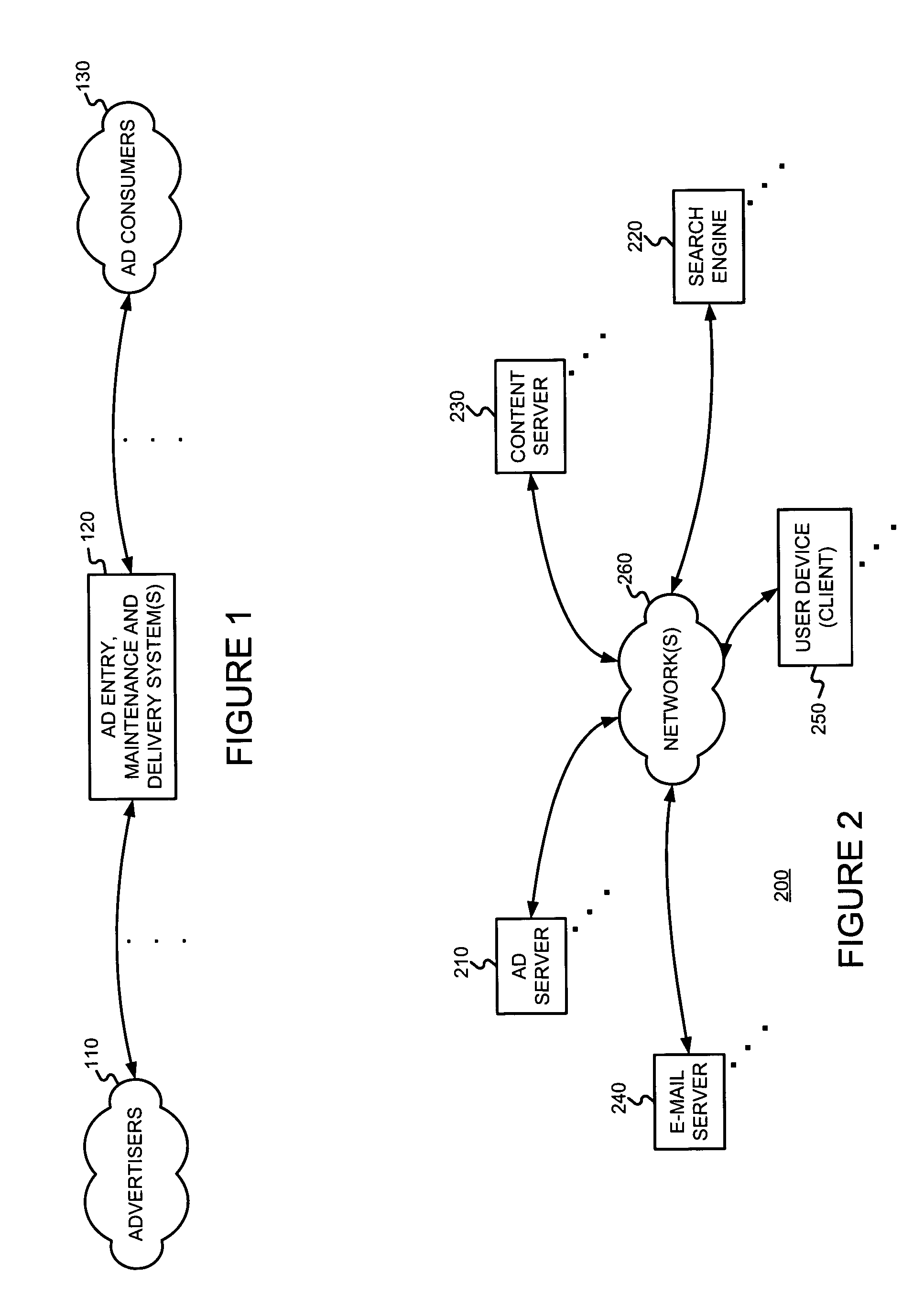
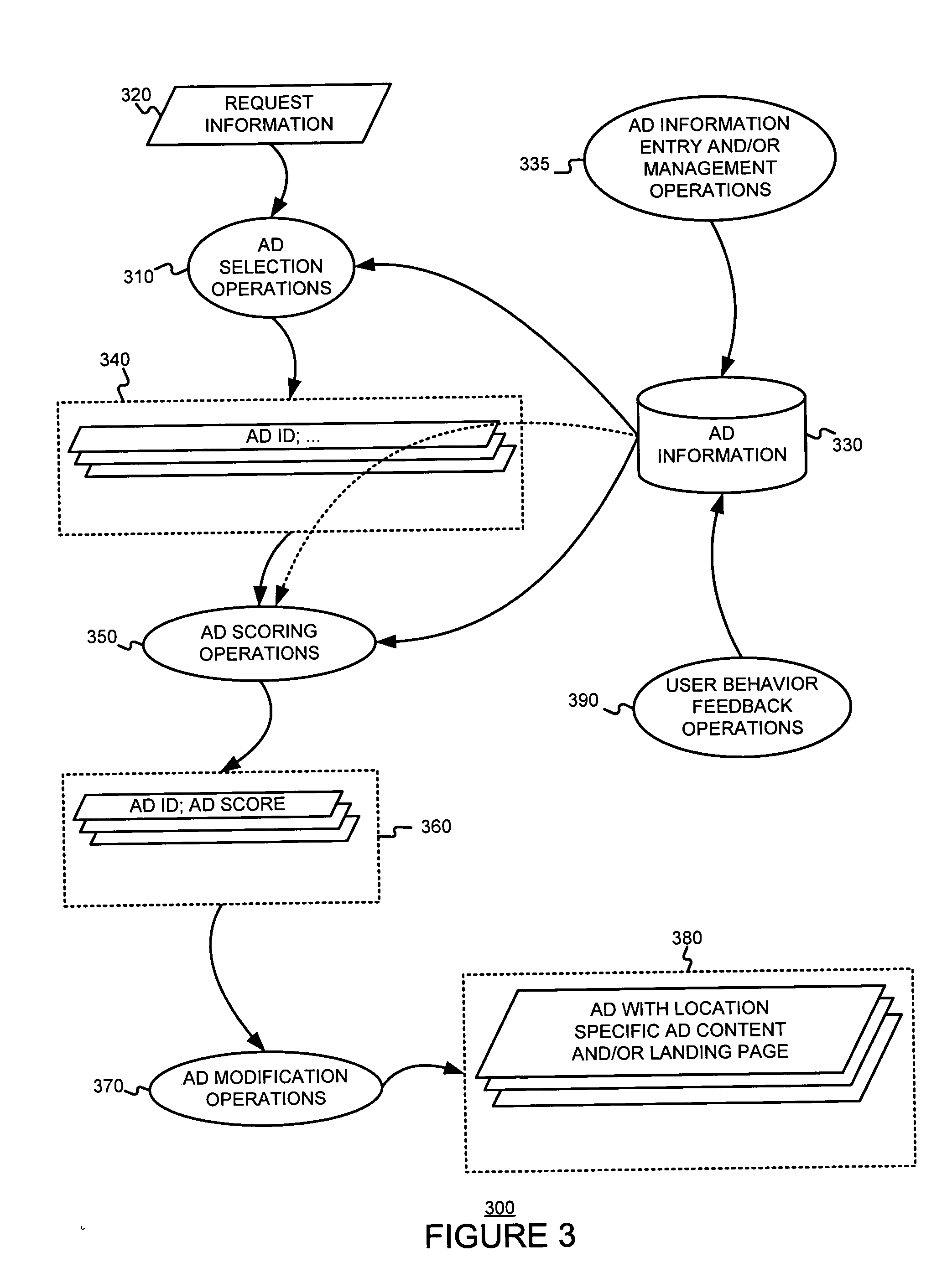
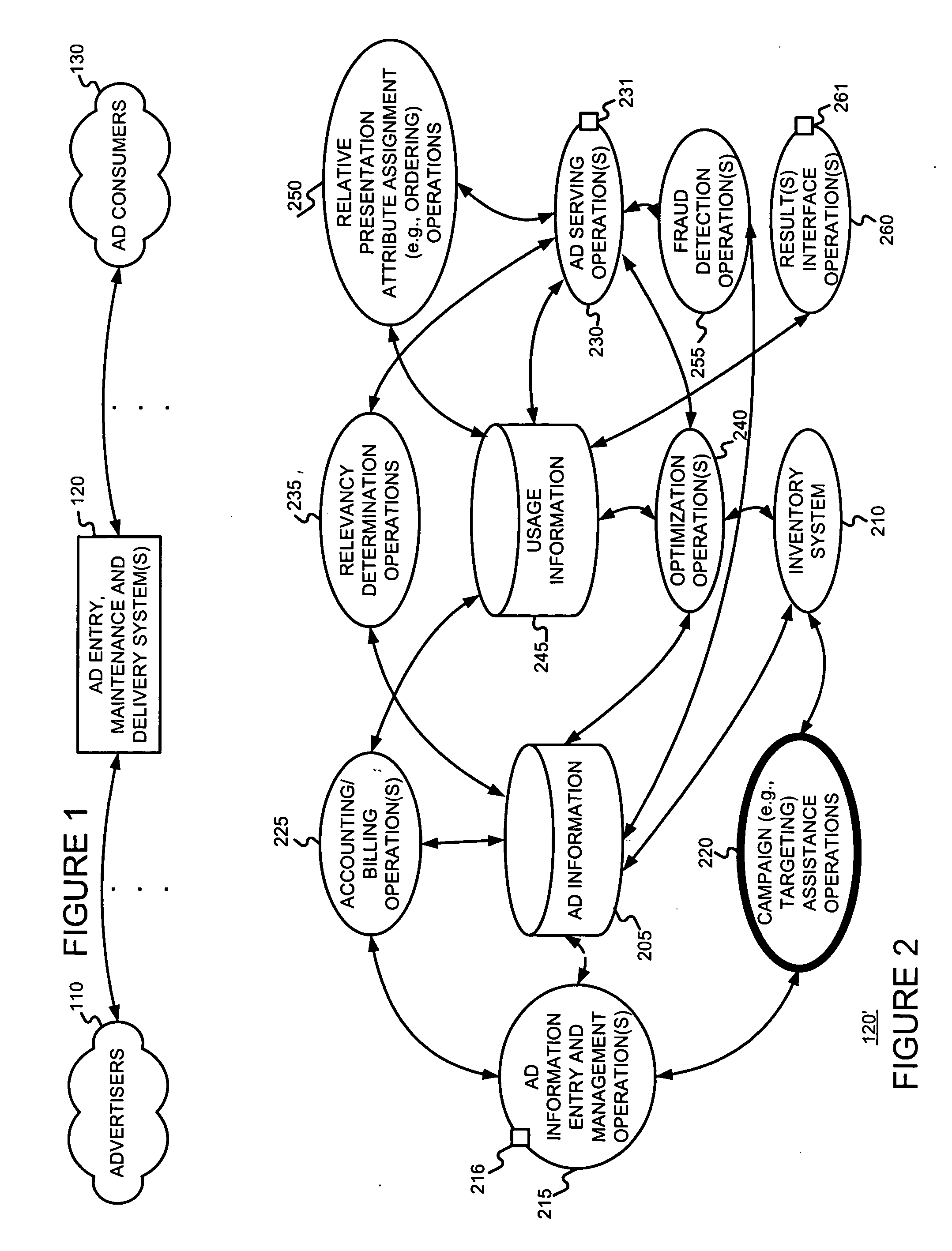
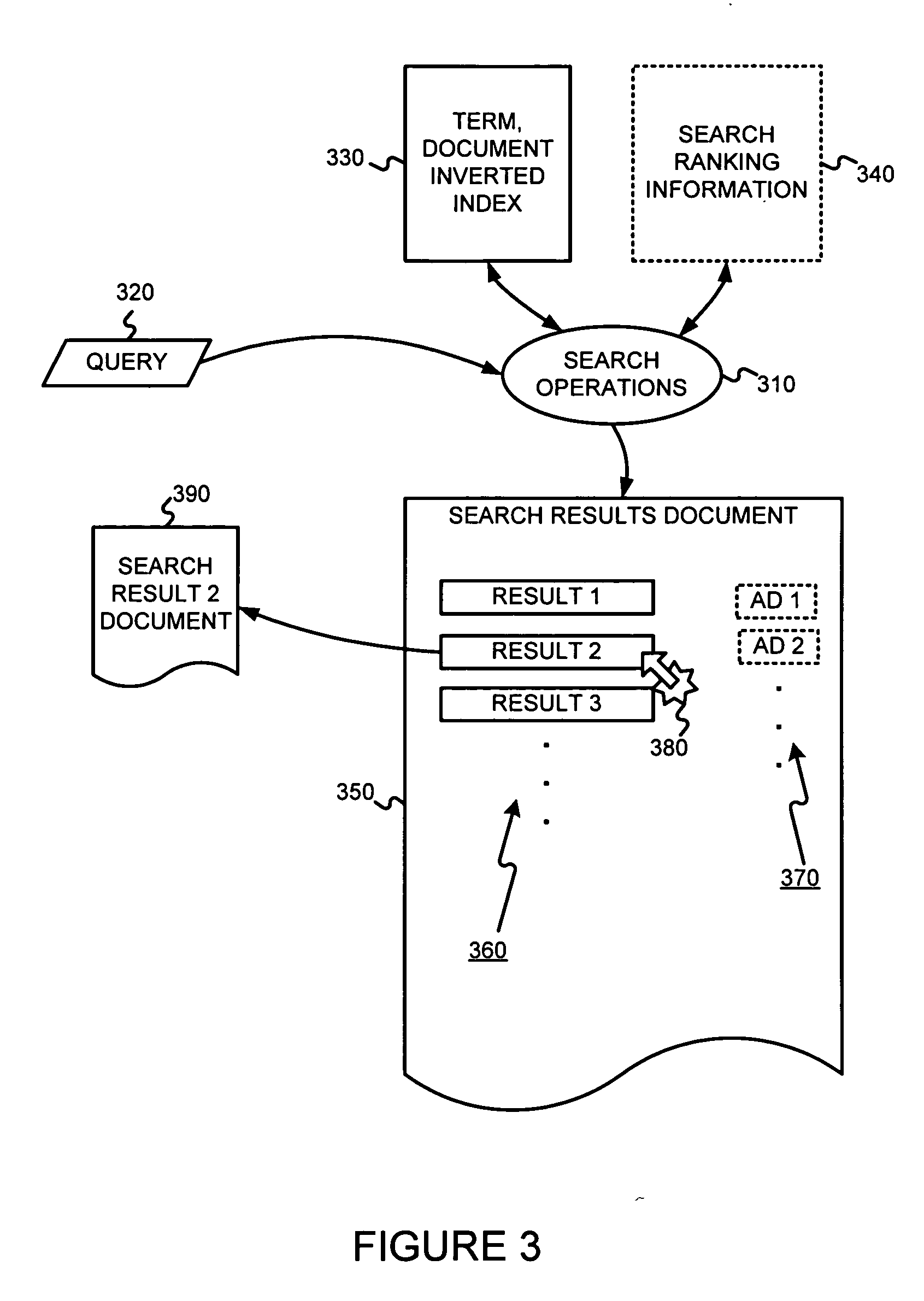
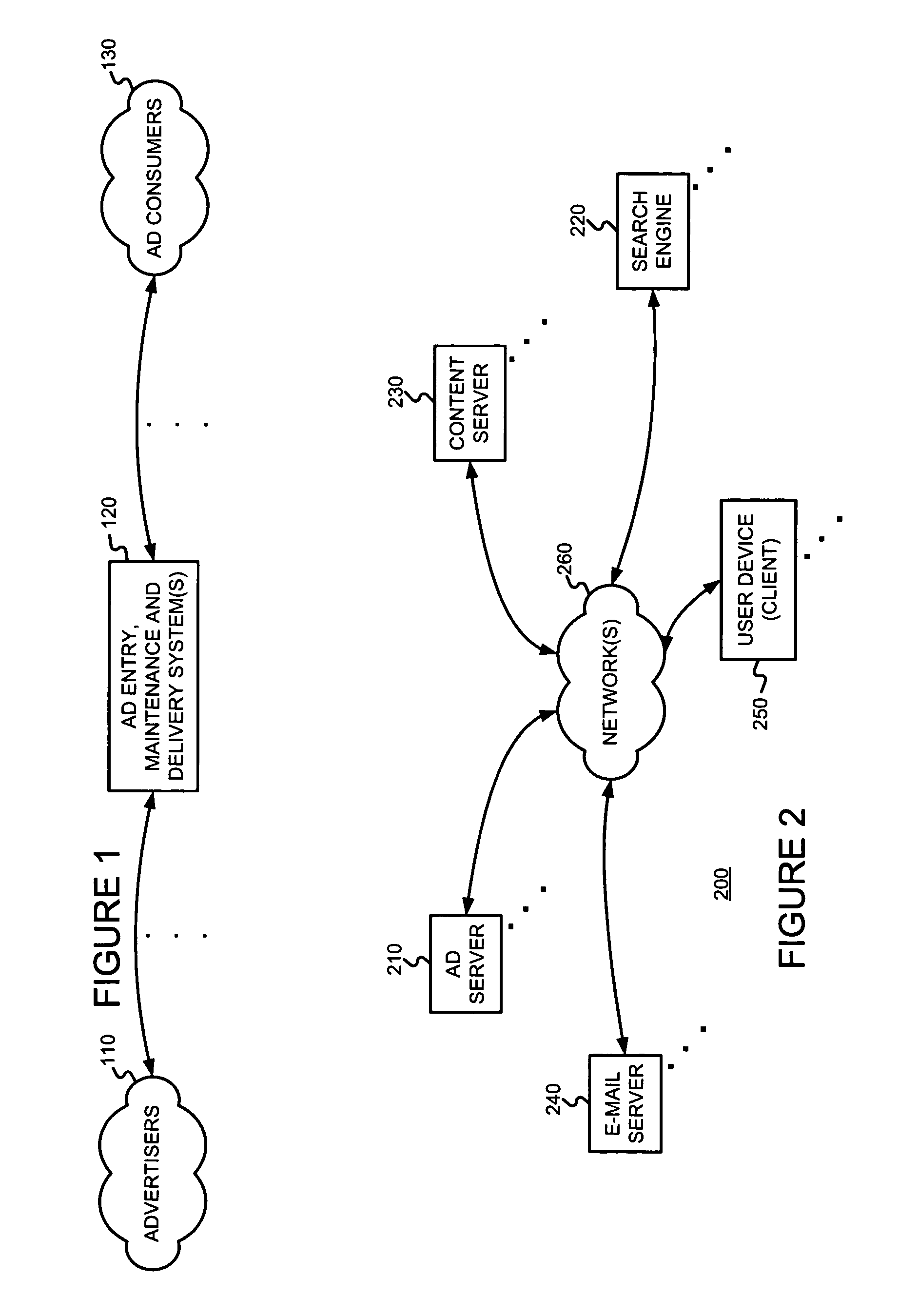
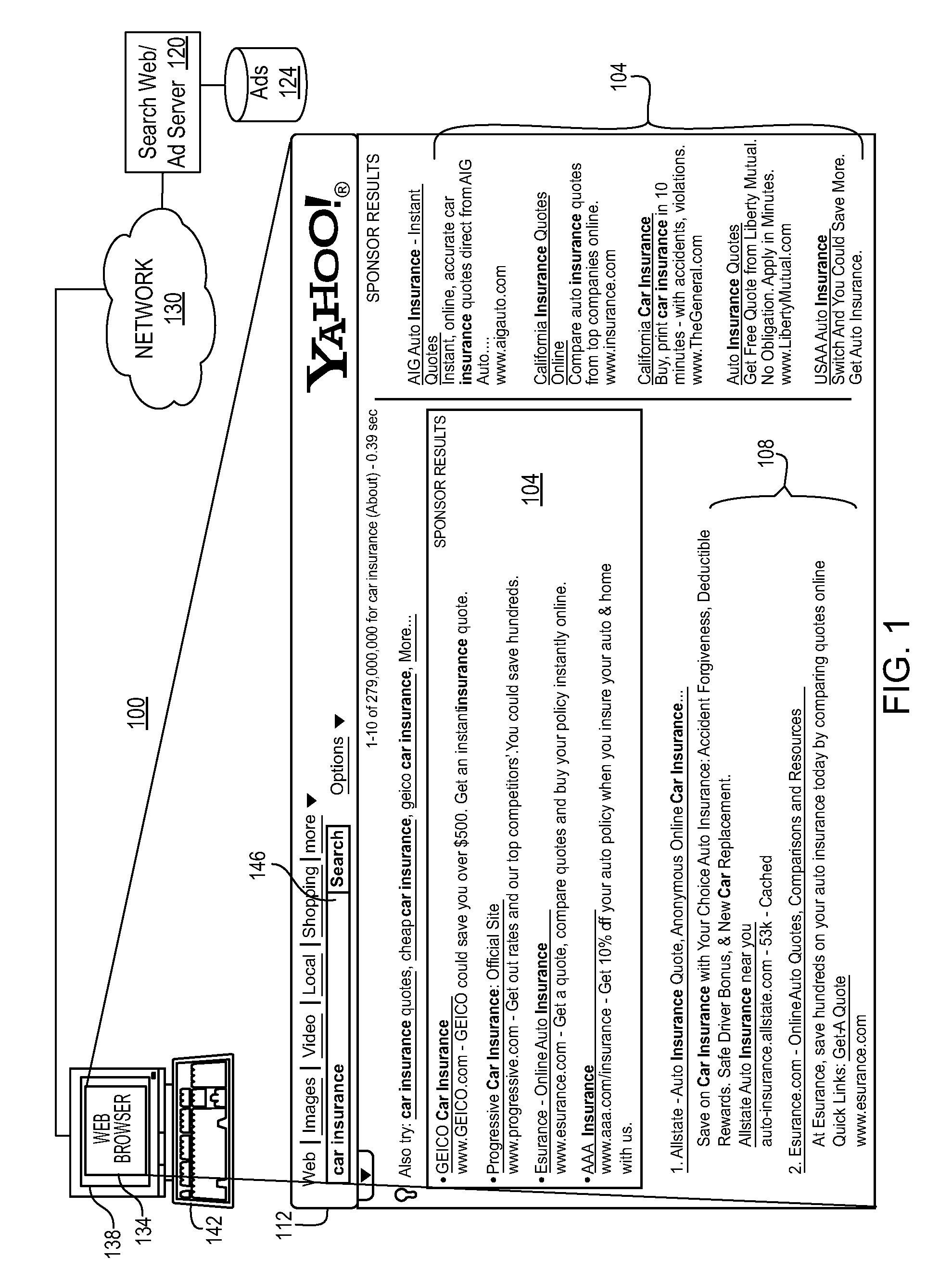
Determining and/or using location information in an ad system
ActiveUS20050050027A1Improve performanceImprove the usefulnessDigital data information retrievalDigital data processing detailsEllipseLongitude
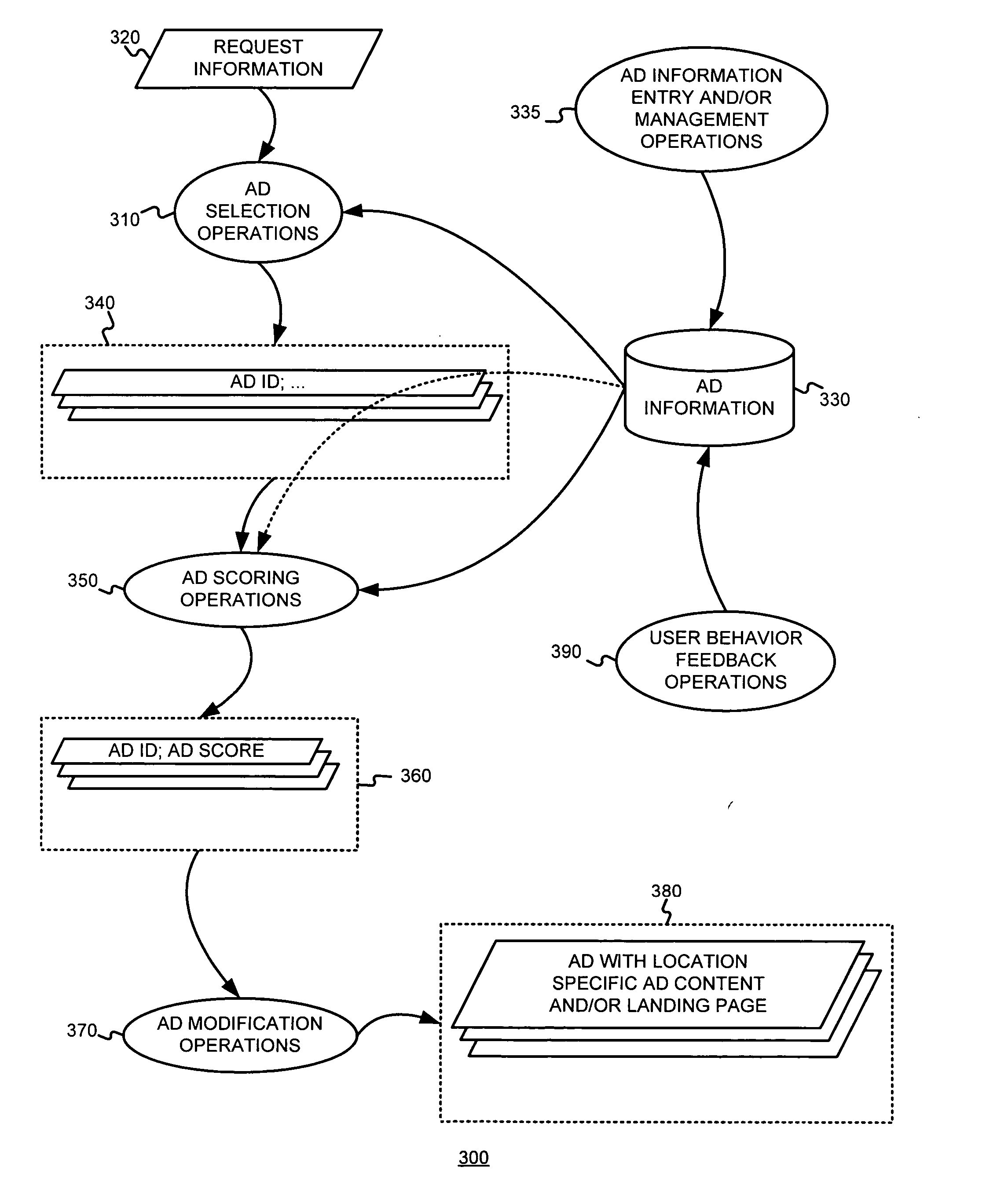
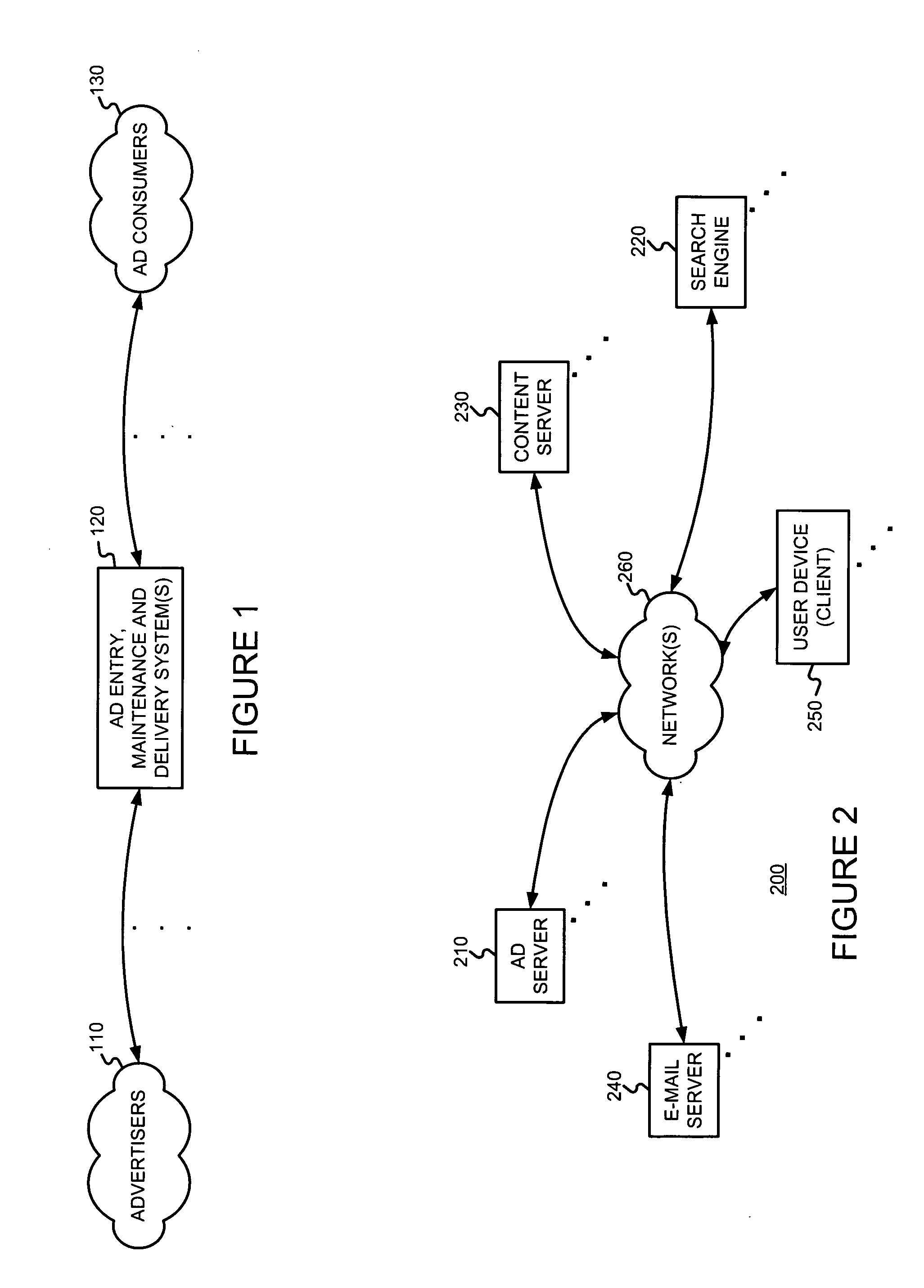
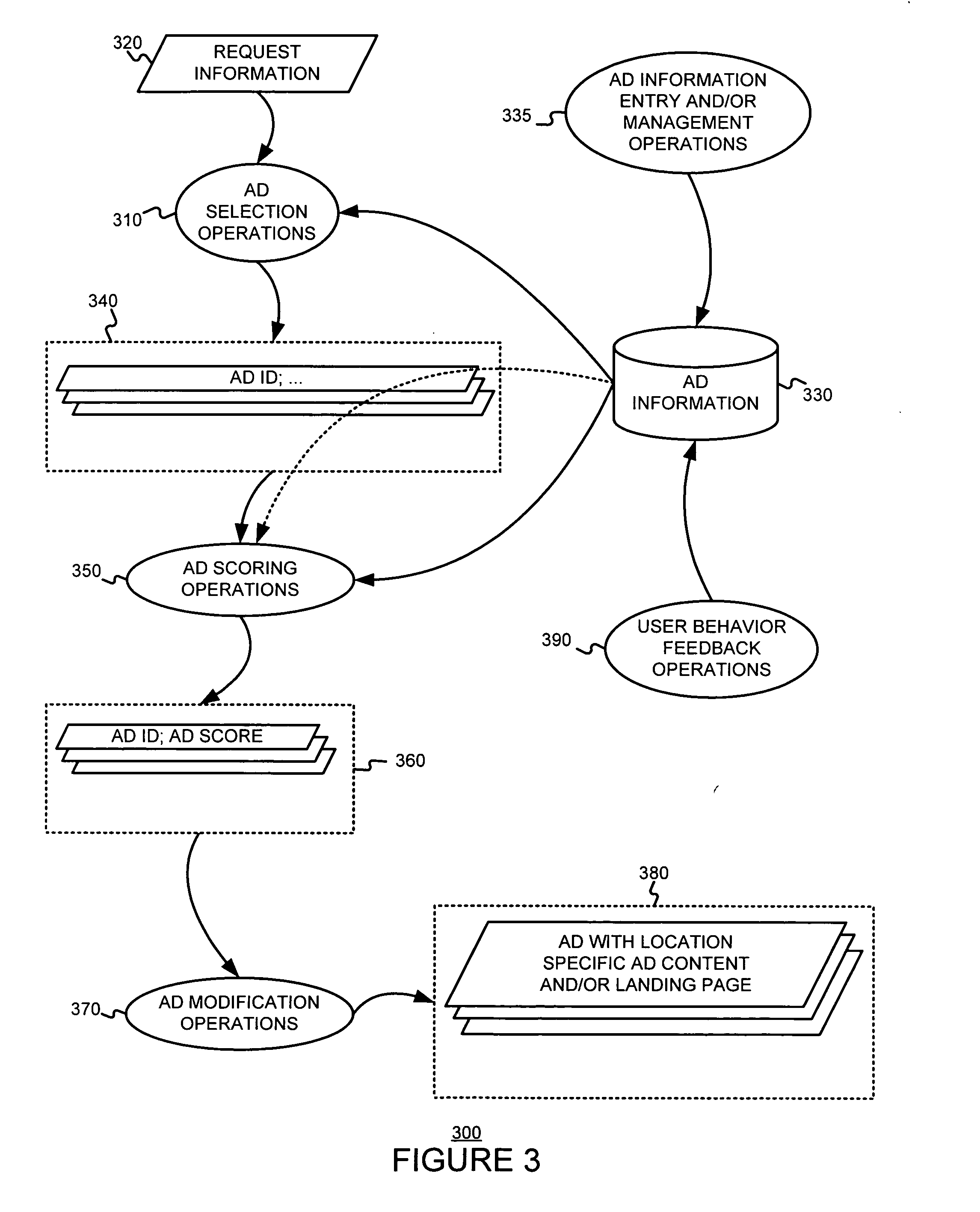
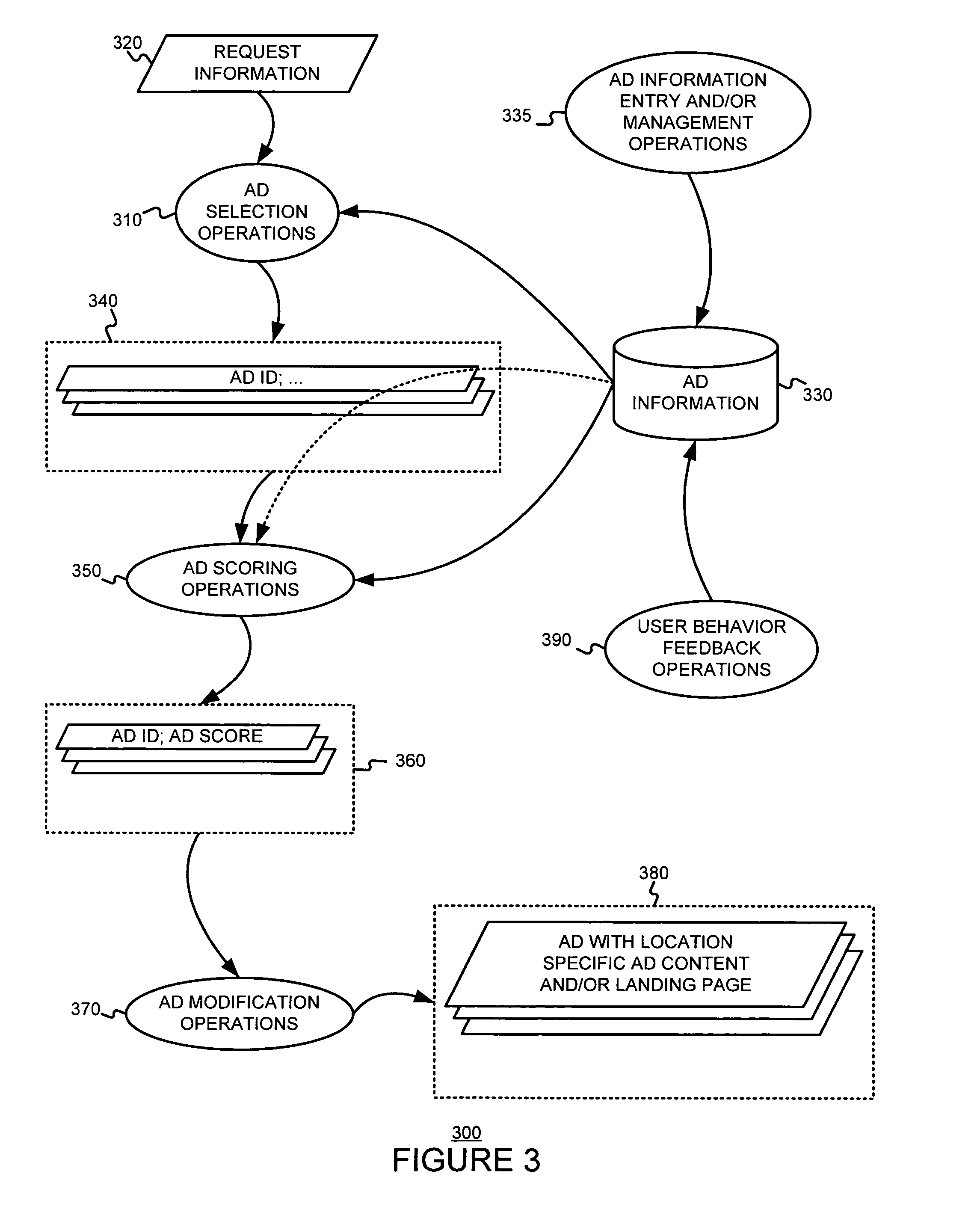
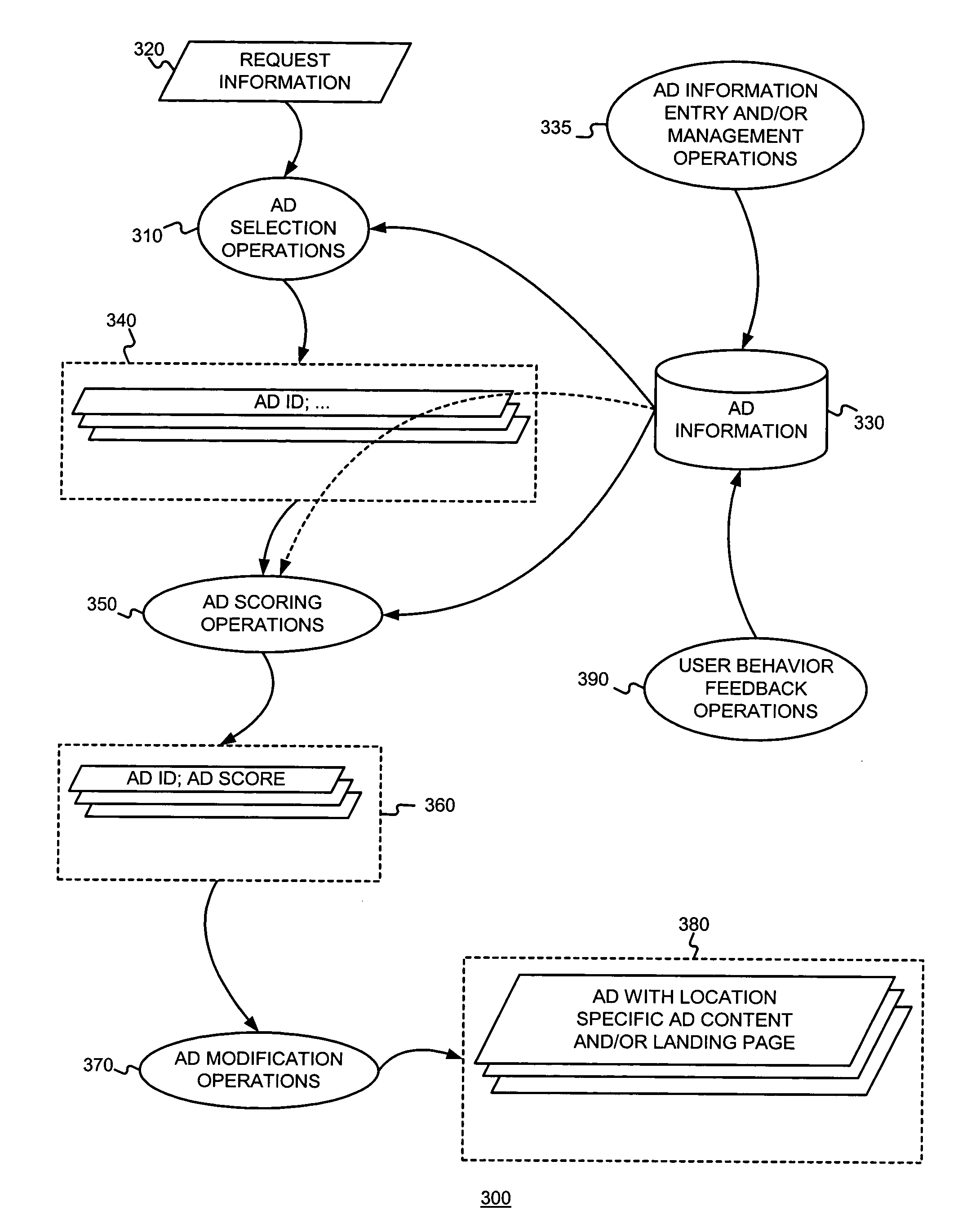
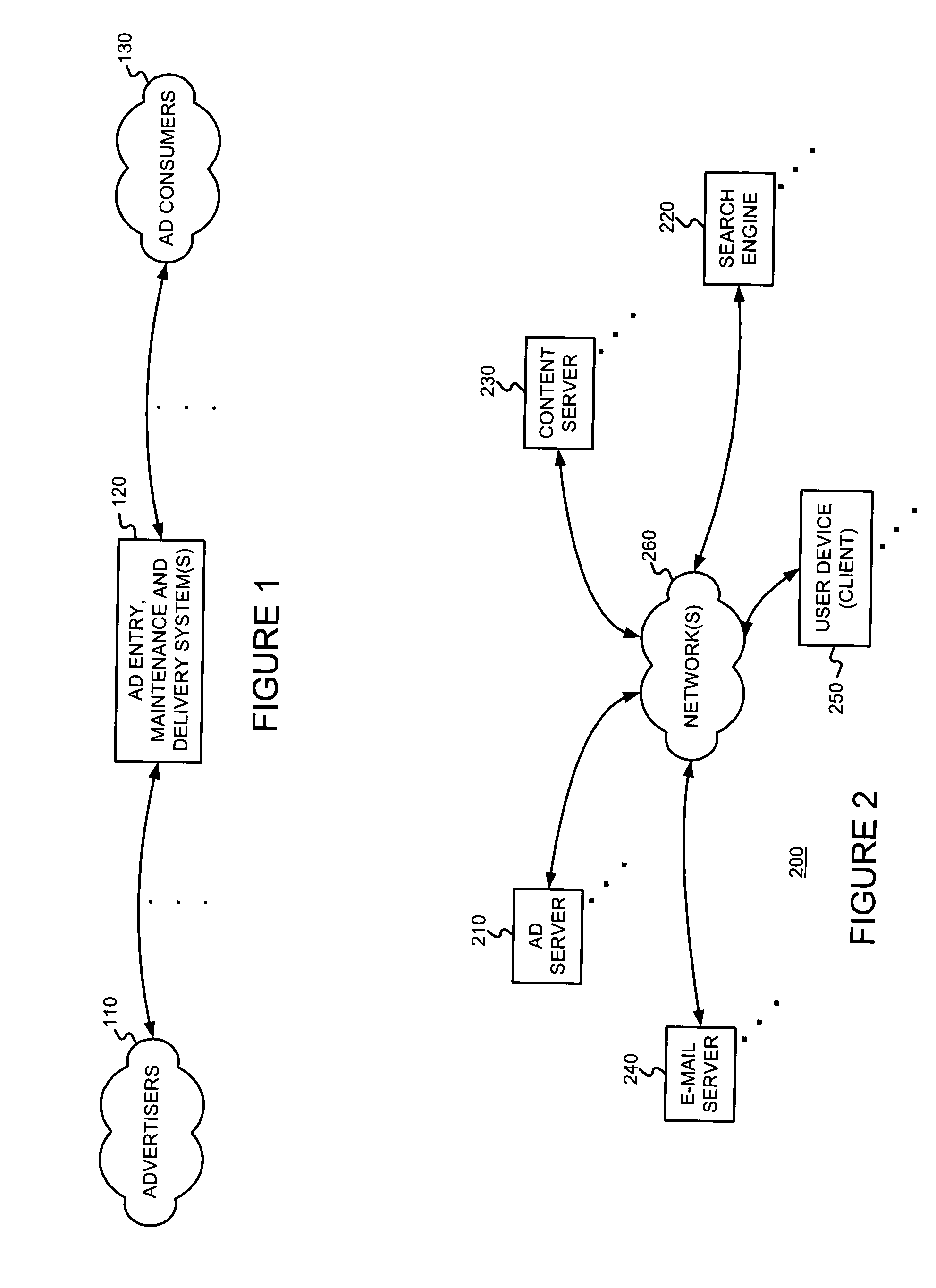
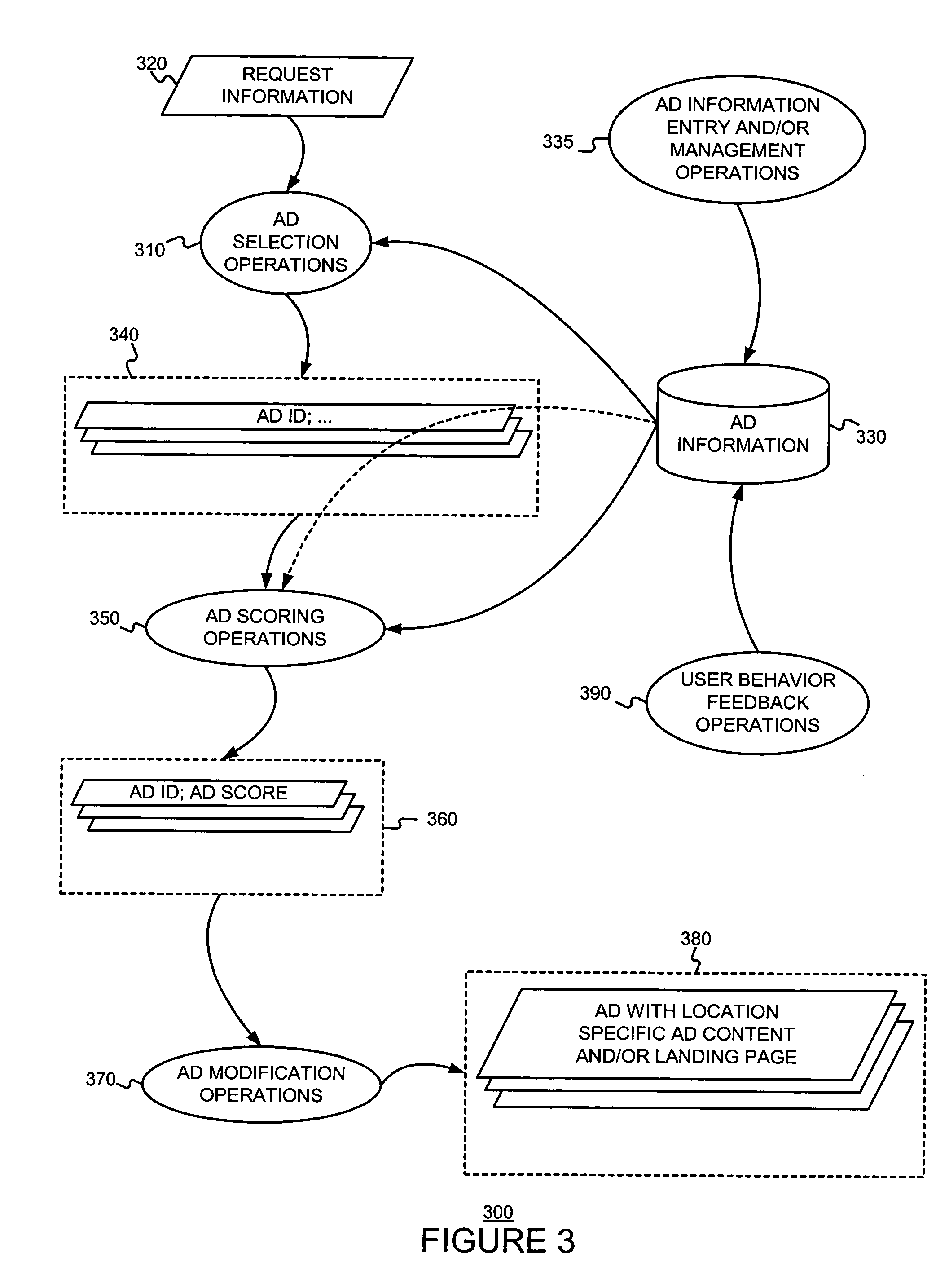
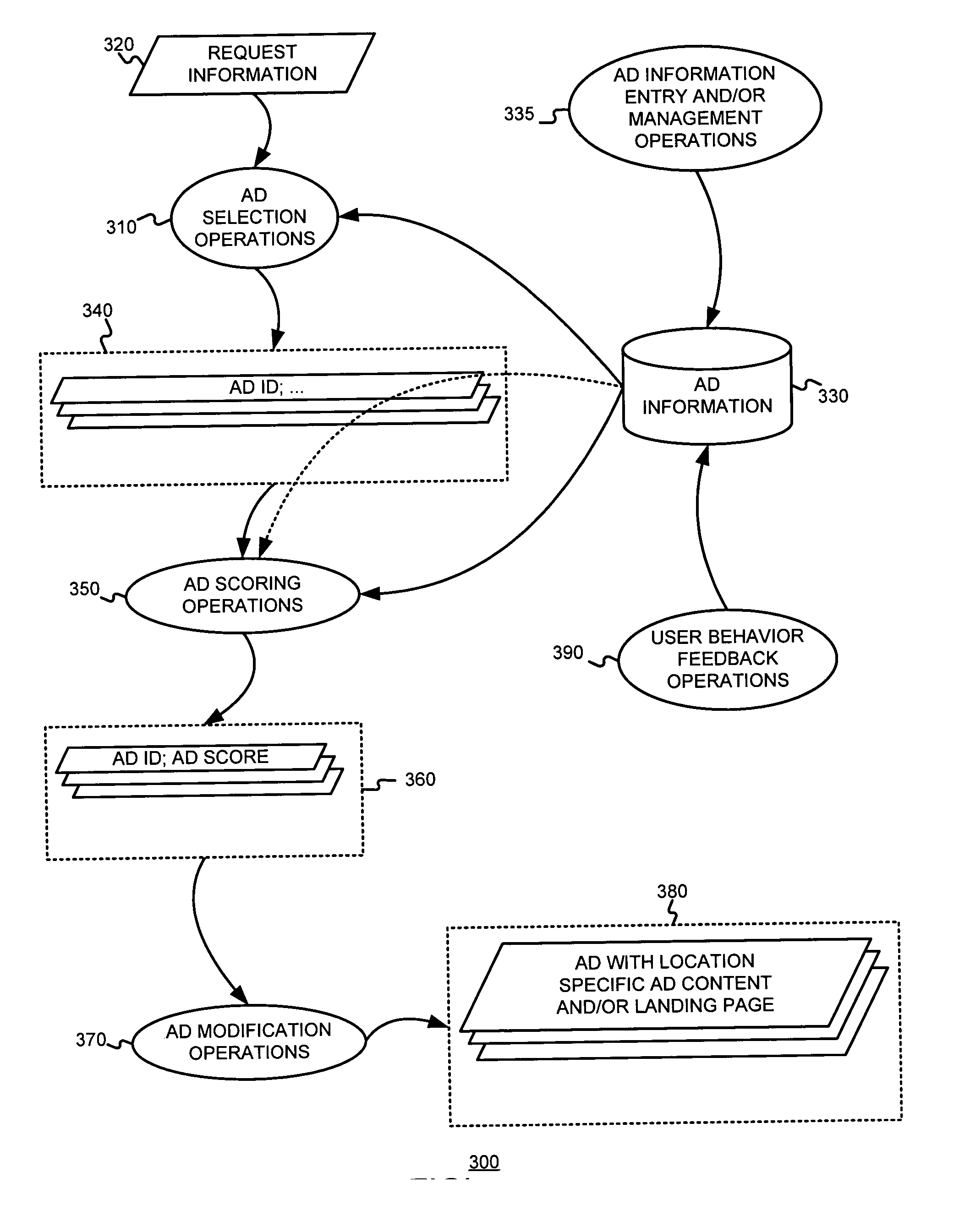
The usefulness, and consequently the performance, of advertisements are improved by allowing businesses to better target their ads to a responsive audience. Location information is determined (or simply accepted) and used. For example, location information may be used in a relevancy determination of an ad. As another example, location information may be used in an attribute (e.g., position) arbitration. Such location information may be associated with price information, such as a maximum price bid. Such location information may be associated with ad performance information. Ad performance information may be tracked on the basis of location information. The content of an ad creative, and / or of a landing page may be selected and / or modified using location information. Finally, tools, such as user interfaces, may be provided to allow a business to enter and / or modify location information, such as location information used for targeting and location-dependent price information. The location information used to target and / or score ads may be, include, or define an area. The area may be defined by at least one geographic reference point (e.g., defined by latitude and longitude coordinates) and perhaps additional information. Thus, the area may be a circle defined by a geographic reference point and a radius, an ellipse defined by two geographic reference points and a distance sum, or a polygon defined by three or more geographic reference points, for example.
Owner:GOOGLE LLC
Generating information for online advertisements from Internet data and traditional media data
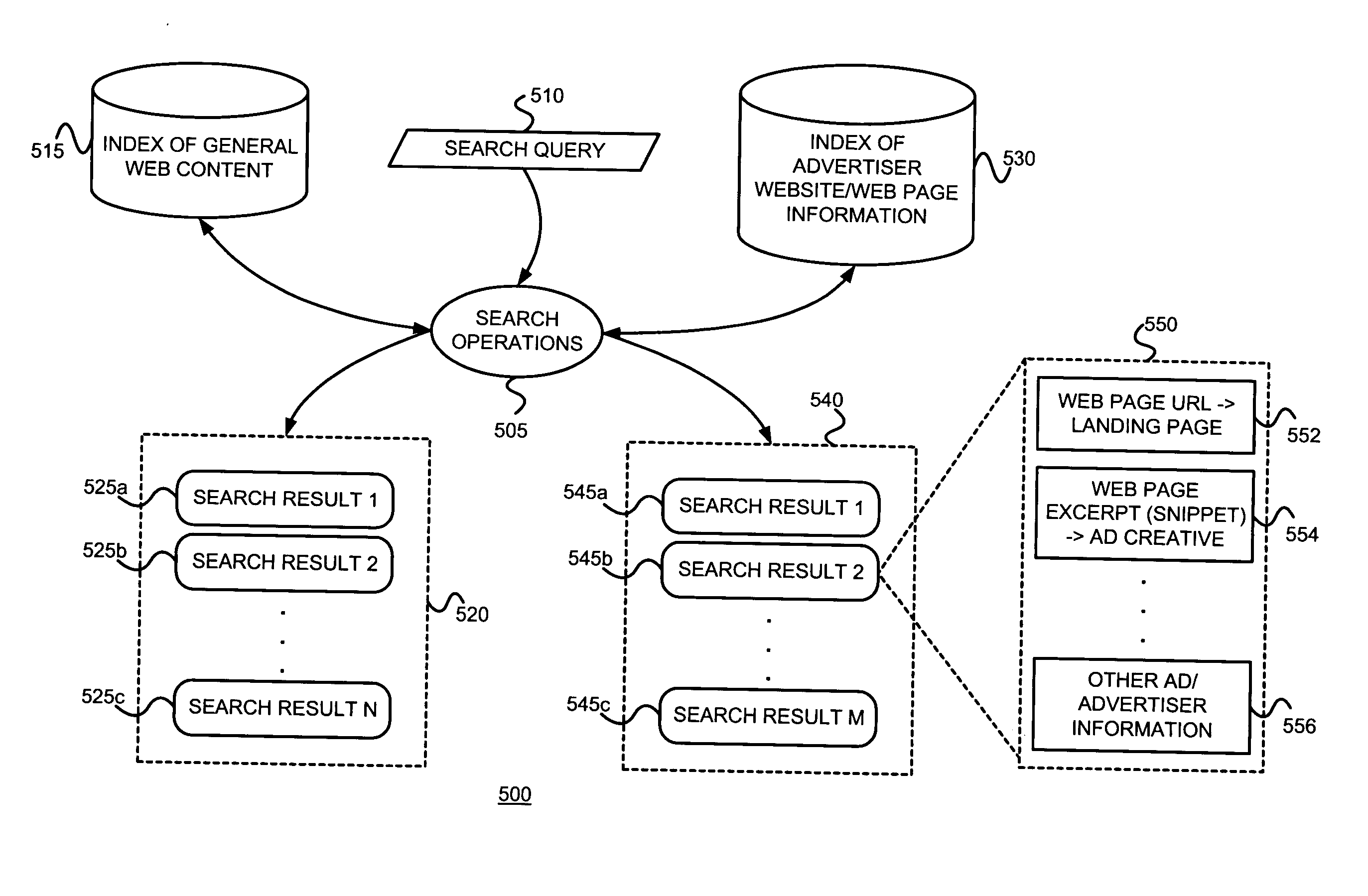
Online information (such as advertiser Web pages in conjunction with products lists, Web content, existing online ads, etc.), or an electronic version of offline advertisement information, is used to generate online advertising information, such as a landing page, targeting information, and / or ad creative information.
Owner:GOOGLE LLC
Determining and/or using location information in an ad system
ActiveUS7668832B2Improve performanceImprove the usefulnessDigital data information retrievalDigital data processing detailsEllipseLongitude
The usefulness, and consequently the performance, of advertisements are improved by allowing businesses to better target their ads to a responsive audience. Location information is determined (or simply accepted) and used. For example, location information may be used in a relevancy determination of an ad. As another example, location information may be used in an attribute (e.g., position) arbitration. Such location information may be associated with price information, such as a maximum price bid. Such location information may be associated with ad performance information. Ad performance information may be tracked on the basis of location information. The content of an ad creative, and / or of a landing page may be selected and / or modified using location information. Finally, tools, such as user interfaces, may be provided to allow a business to enter and / or modify location information, such as location information used for targeting and location-dependent price information. The location information used to target and / or score ads may be, include, or define an area. The area may be defined by at least one geographic reference point (e.g., defined by latitude and longitude coordinates) and perhaps additional information. Thus, the area may be a circle defined by a geographic reference point and a radius, an ellipse defined by two geographic reference points and a distance sum, or a polygon defined by three or more geographic reference points, for example.
Owner:GOOGLE LLC
Mutual authentication security system with detection and mitigation of active man-in-the-middle browser attacks, phishing, and malware and other security improvements.
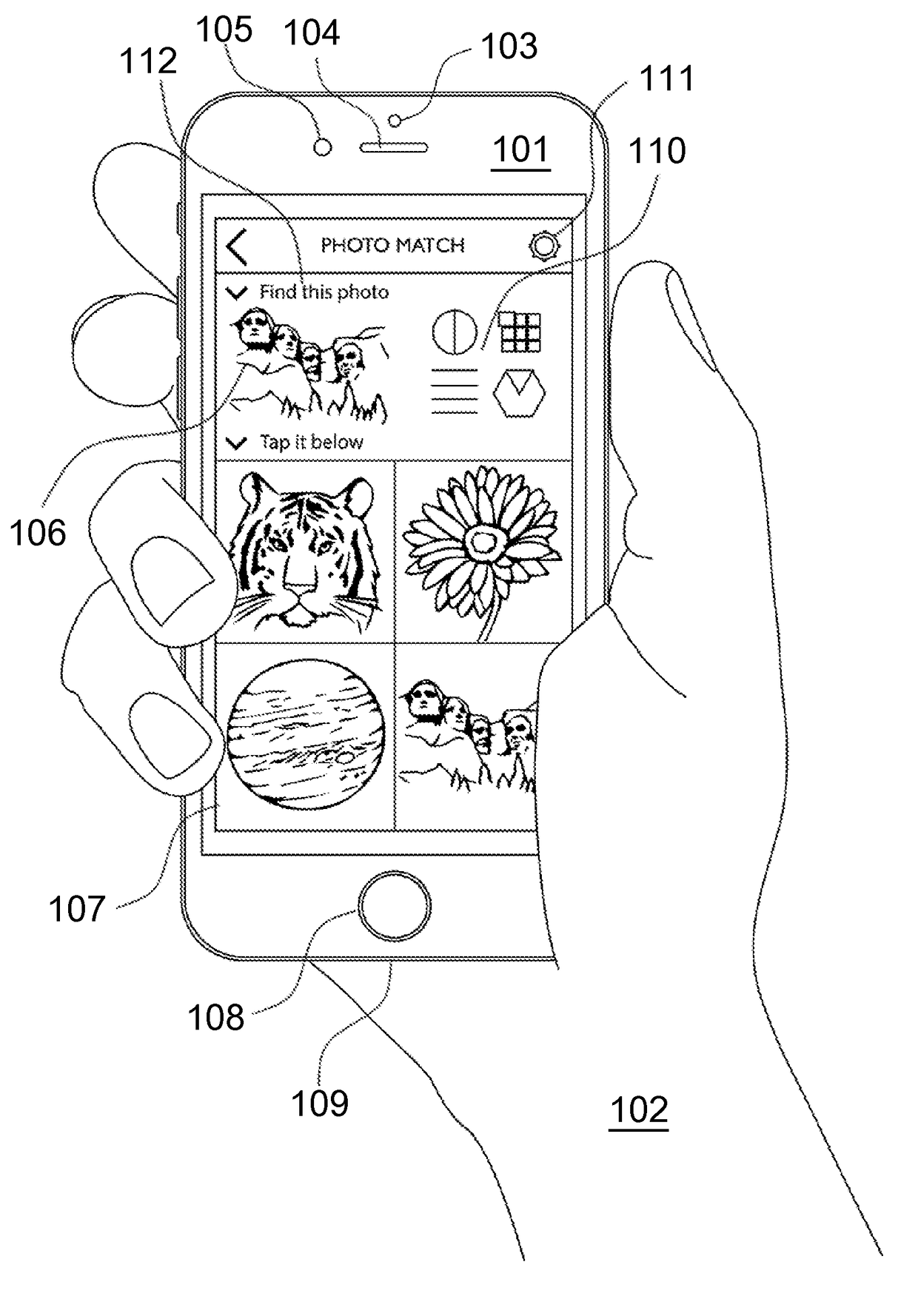
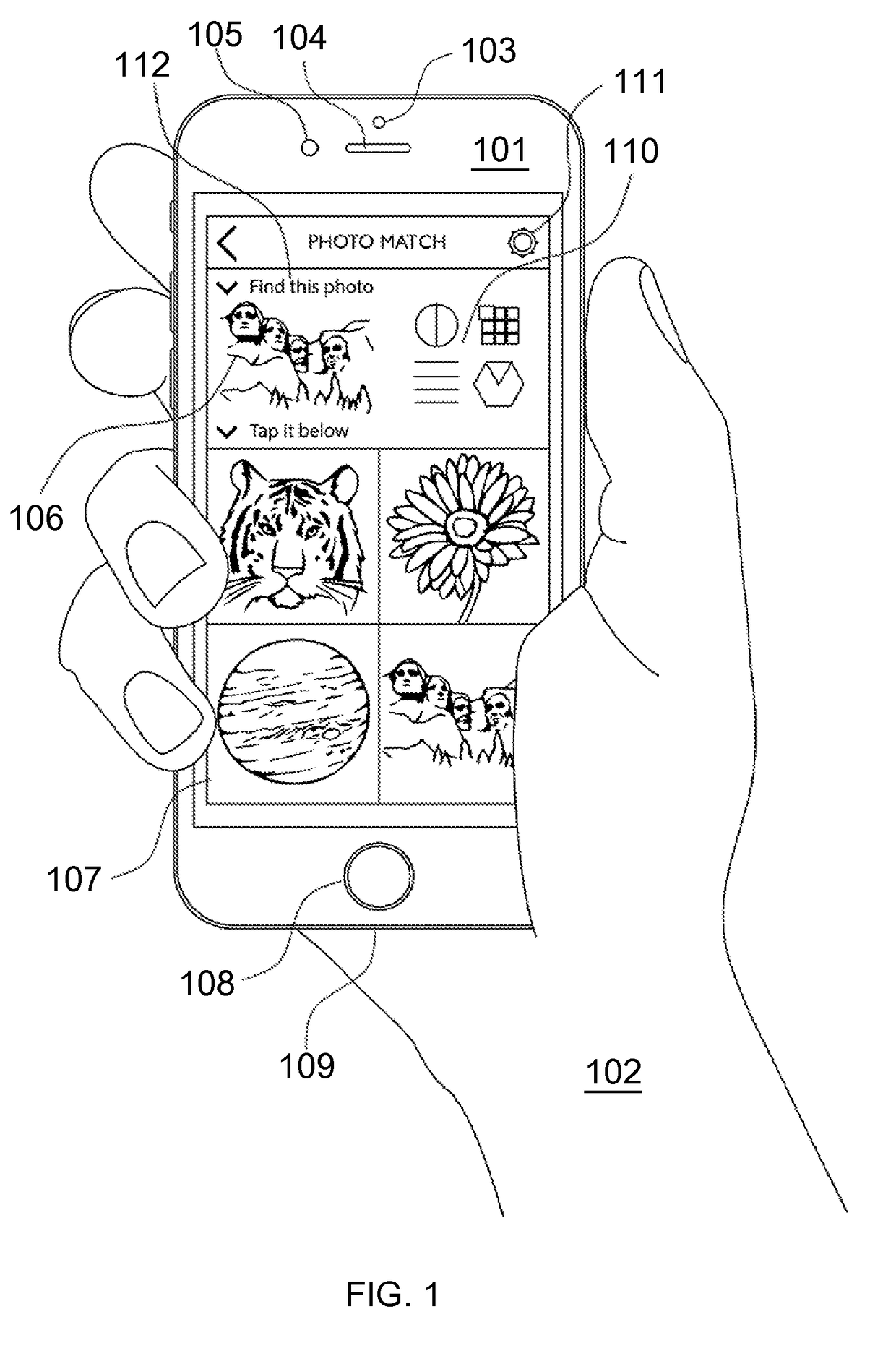
ActiveUS20170346851A1Multiple keys/algorithms usagePublic key for secure communicationWeb sitePhishing
A strong, unified and comprehensive new computer security and authentication solution is disclosed. It is ideal for everyday users, and invents faster and easier enrollments, faster usage, easier usage, numerous aspects of stronger security including token based rapid mutual-authentication with protection against phishing, MitM, malware and user carelessness, secure resilience against token loss or theft, continuing protection in harsh situations, non-repudiation benefits, biometric encryption, code self-defenses, improved deployment, lower costs, new revenue opportunities, and more. One aspect's flow, visually-enforced mutual-authentication is: customer visits protected web site's login page, gets identified via Cookies, site displays one random photograph on said page, triggers customer's smartphone to automatically show a grid of random photos, one of which matches the login page photo, and customer taps it to login. Disclosed techniques teach how to block fraudulent sites and activity by preventing these producing any matching photo the customer can tap.
Owner:DRAKE CHRISTOPHER NATHAN TYRWHITT
Determining and/or using location information in an ad system
ActiveUS20050050097A1Improve performanceImprove the usefulnessDigital data information retrievalDigital data processing detailsPosition dependentComputer science
The usefulness, and consequently the performance, of advertisements are improved by allowing businesses to better target their ads to a responsive audience. Location information, such as country, region, metro area, city or town, postal zip code, telephone area code, etc. is determined (or simply accepted) and used. For example, location information may be used in a relevancy determination of an ad. As another example, location information may be used in an attribute (e.g., position) arbitration. Such location information may be associated with price information, such as a maximum price bid. Such location information may be associated with ad performance information. Ad performance information may be tracked on the basis of location information. The content of an ad creative, and / or of a landing page may be selected and / or modified using location information. Finally, tools, such as user interfaces, may be provided to allow a business to enter and / or modify location information, such as location information used for targeting and location-dependent price information.
Owner:GOOGLE LLC
Determining and/or using end user local time information in an ad system
ActiveUS20050076014A1Improve performanceImprove the usefulnessDigital data processing detailsMarketingTime informationBusiness enterprise
The usefulness, and consequently the performance, of advertisements are improved by allowing advertisers to better target their ads to a responsive audience. End user local time information, such as at least one of (a) a local time-of-day, (b) a local time-of-day range, (c) a local date, (d) a local day-of-week, (e) a local date range, (f) a local day-of-week range, and (g) a local season, is determined (or simply accepted) and used. For example, end user local time information may be used in a relevancy determination of an ad. As another example, end user local time information may be used in an attribute (e.g., position) arbitration. Such end user local time information may be associated with price information, such as a maximum price bid. Such end user local time information may be associated with ad performance information. Ad performance information may be tracked on the basis of end user local time information. The content of an ad creative, and / or of a landing page may be selected and / or modified using end user local time information. Finally, tools, such as user interfaces, may be provided to allow a business to enter and / or modify end user local time information, such as end user local time information used for targeting and end user local time-dependent price information.
Owner:GOOGLE LLC
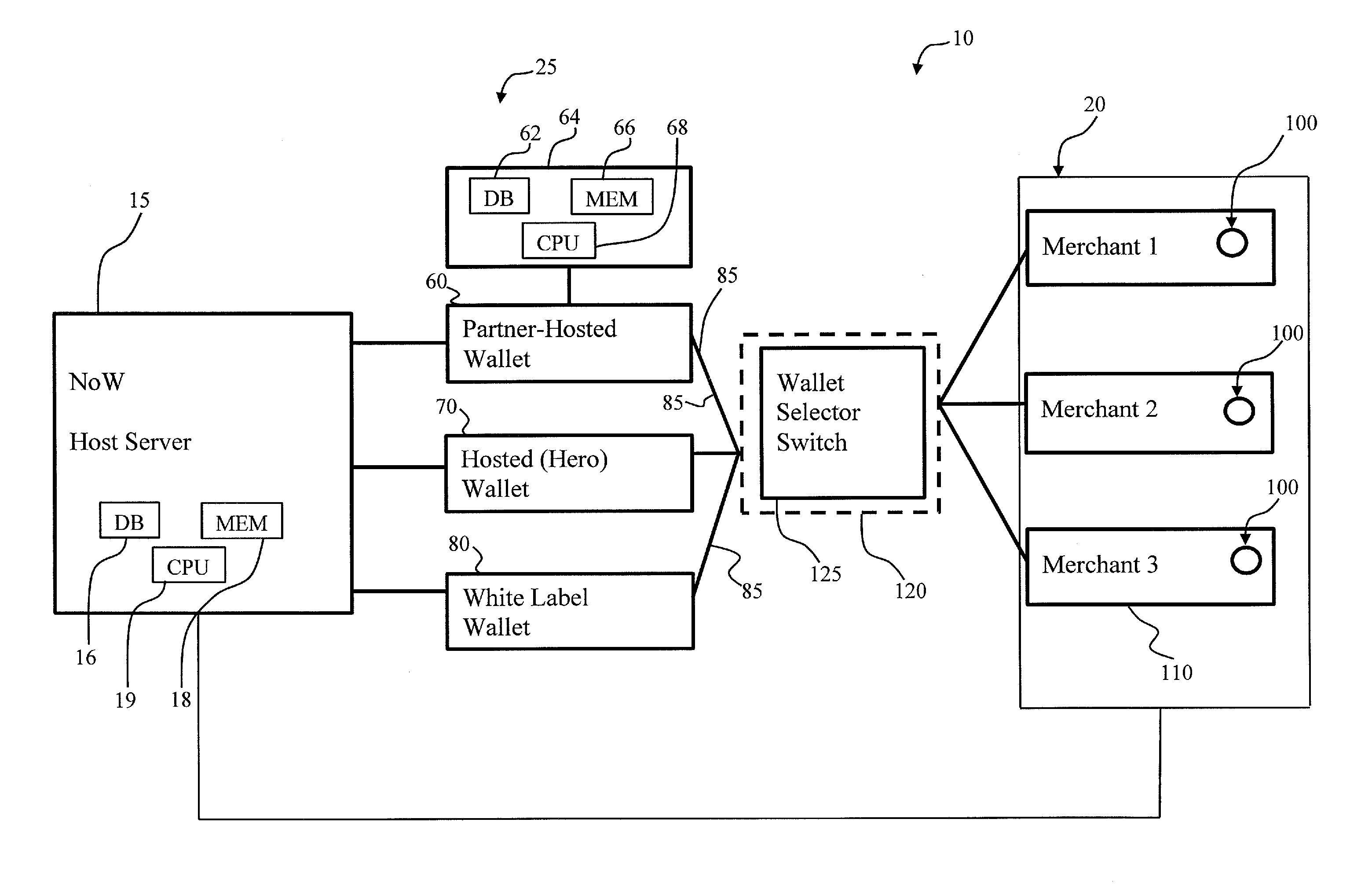
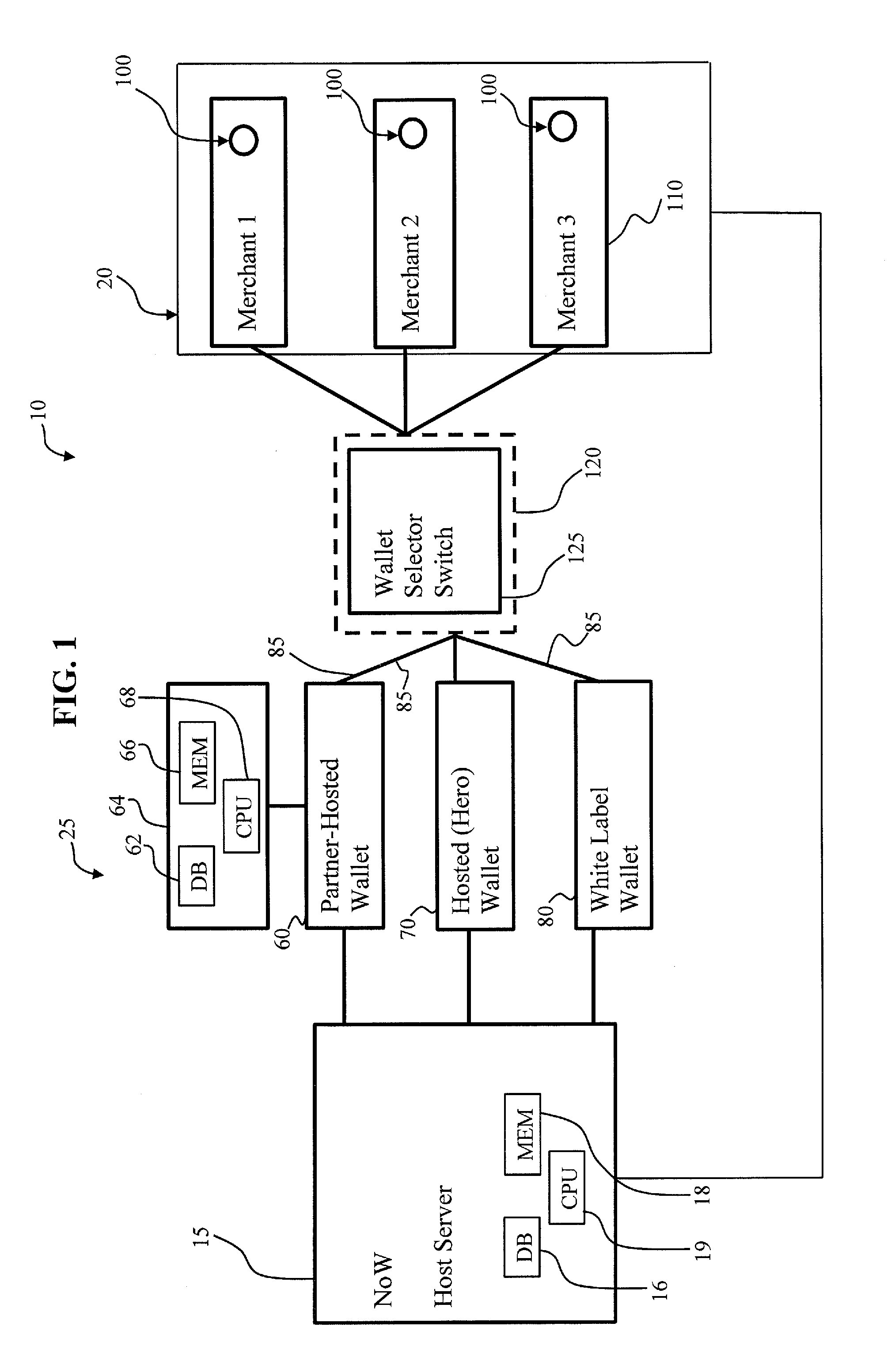
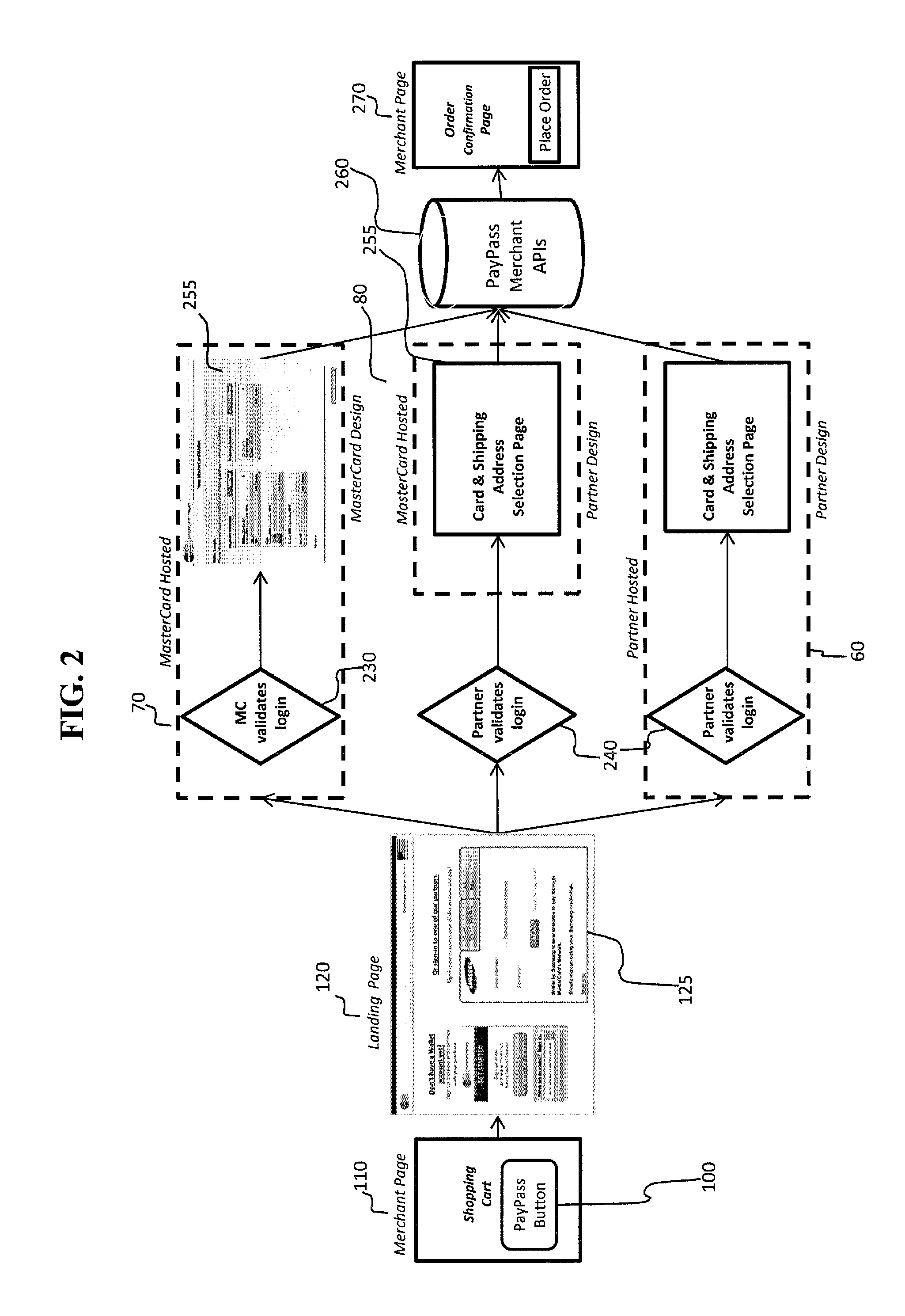
System and method to enable a network of digital wallets
A method for authorizing a digital wallet transaction initiated by a consumer from a merchant web site or app includes providing an acceptance mark on a merchant landing page associated with the merchant web site or app for initiating the digital wallet transaction, the acceptance mark comprising a link to a host server accessing an acceptance network for authorizing payment, the acceptance network comprising a plurality of digital wallets. A wallet selector switch allows selection of a wallet, the transaction is routed to the selected wallet, a payment card and shipping address are selected and the transaction is redirected back to the merchant with purchase details for authorizing and completing the digital wallet transaction. The wallets can include federated and non-federated cobranded wallets and partner-hosted wallets. Direct provisioning with partner credentials and automatic update of consumer details is provided in a federated cobranded wallet.
Owner:MASTERCARD INT INC
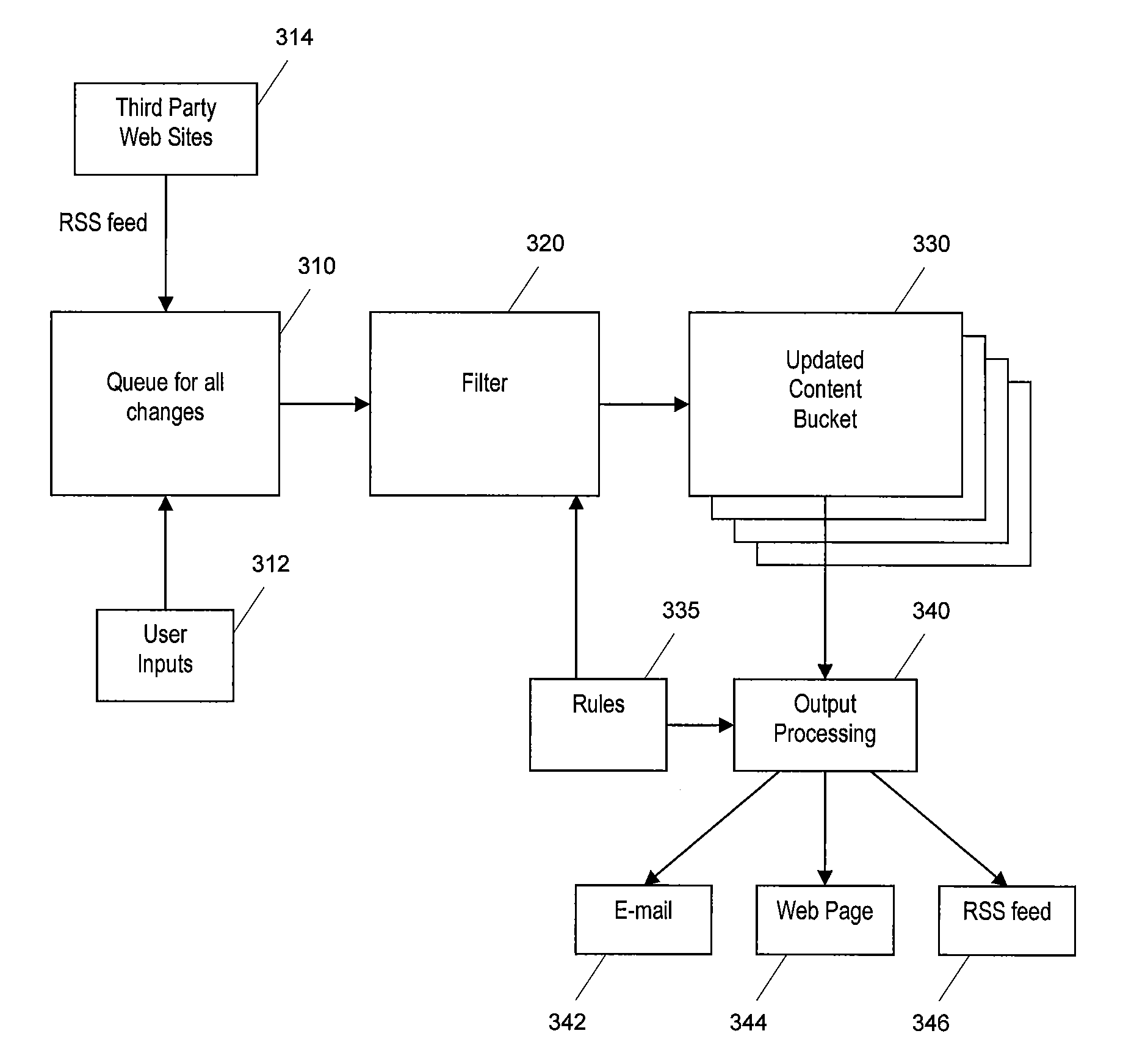
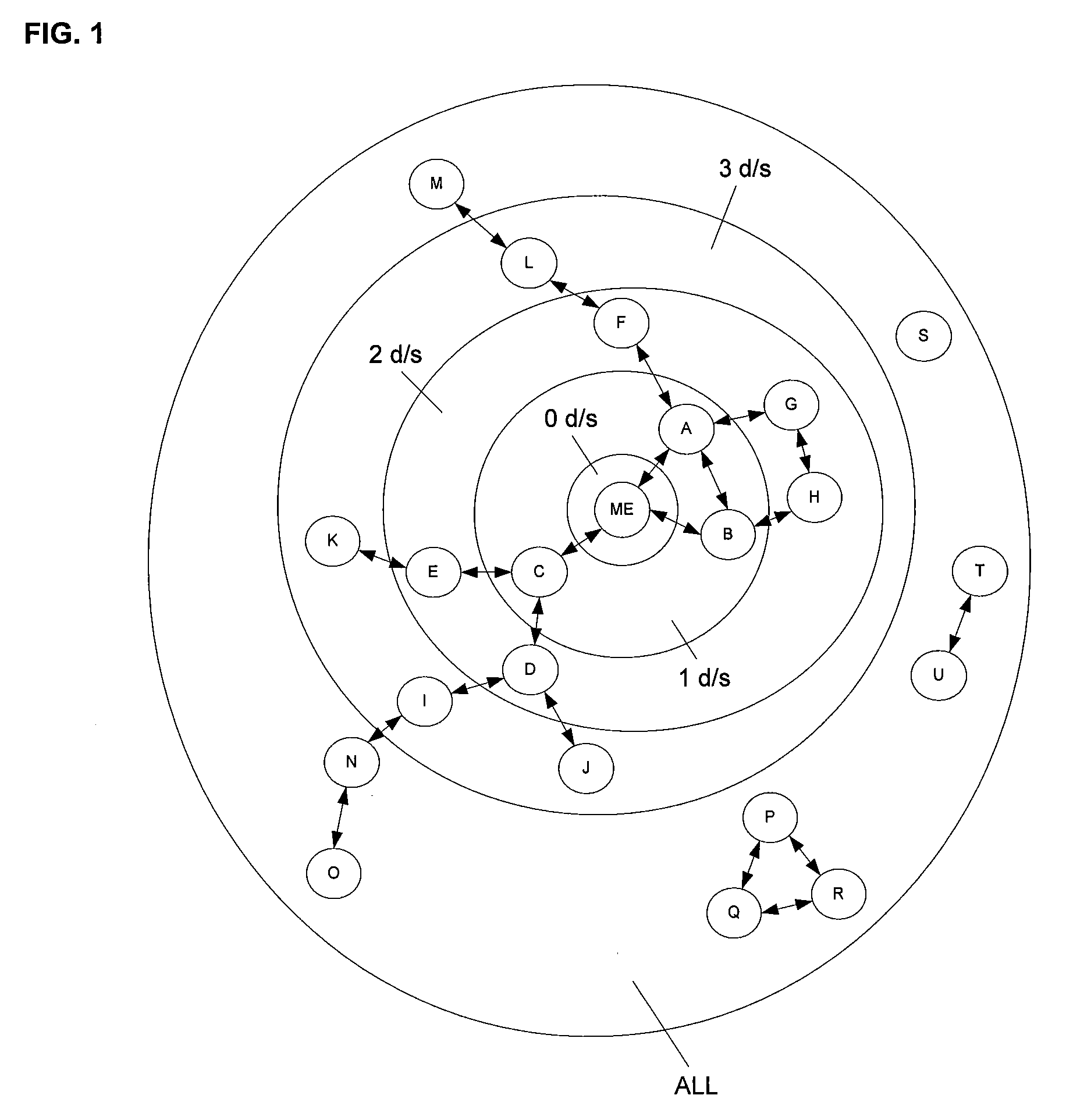
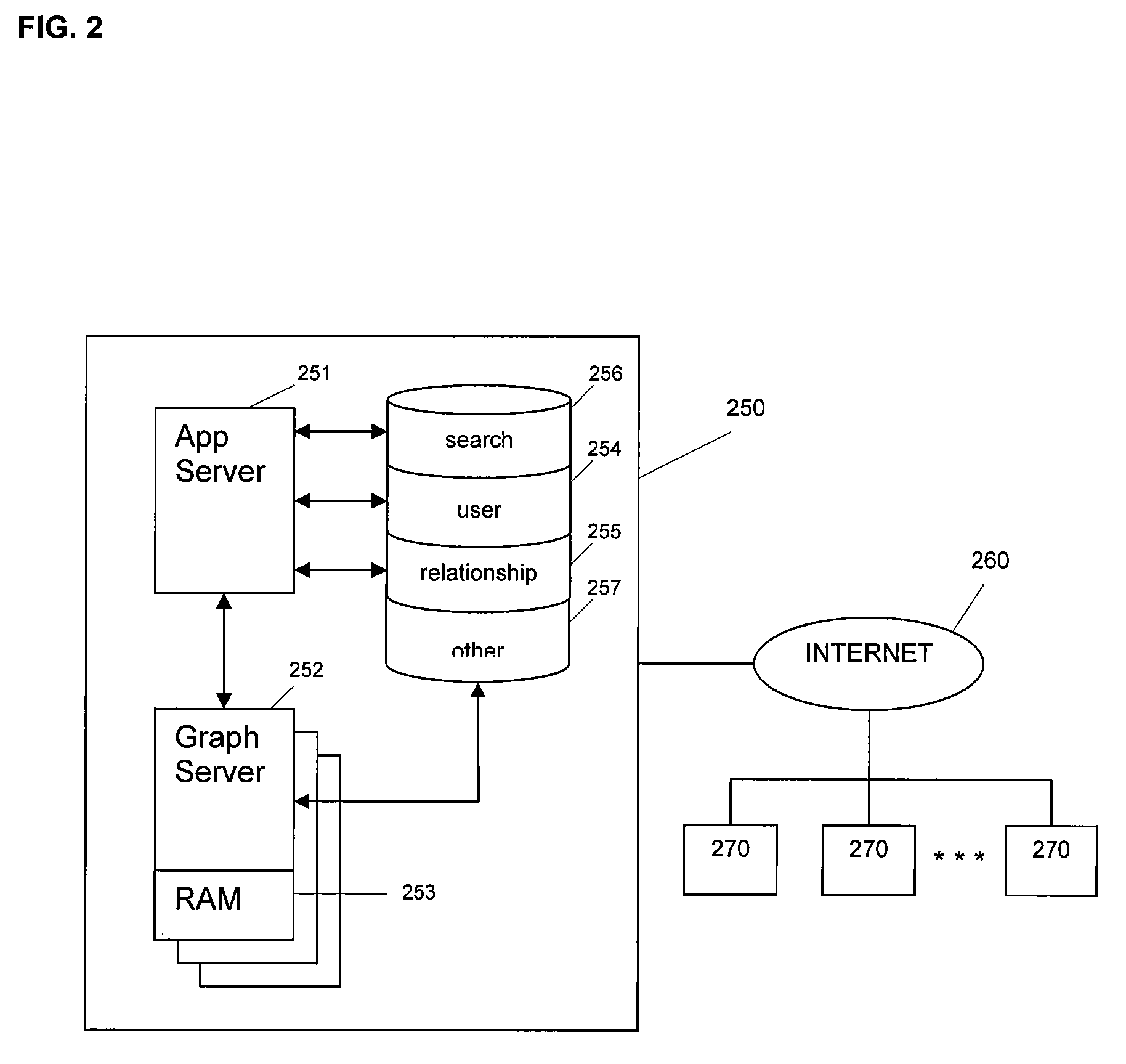
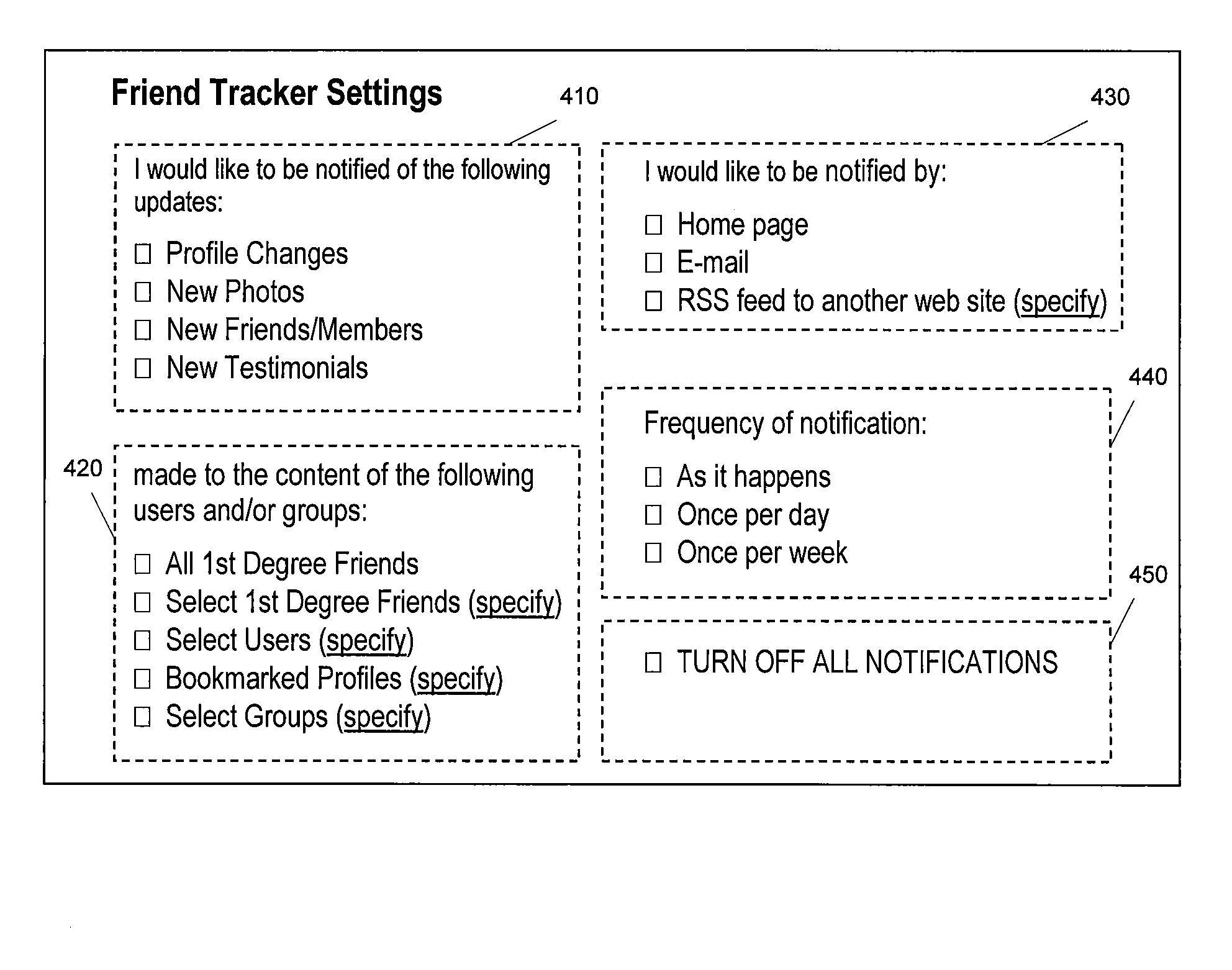
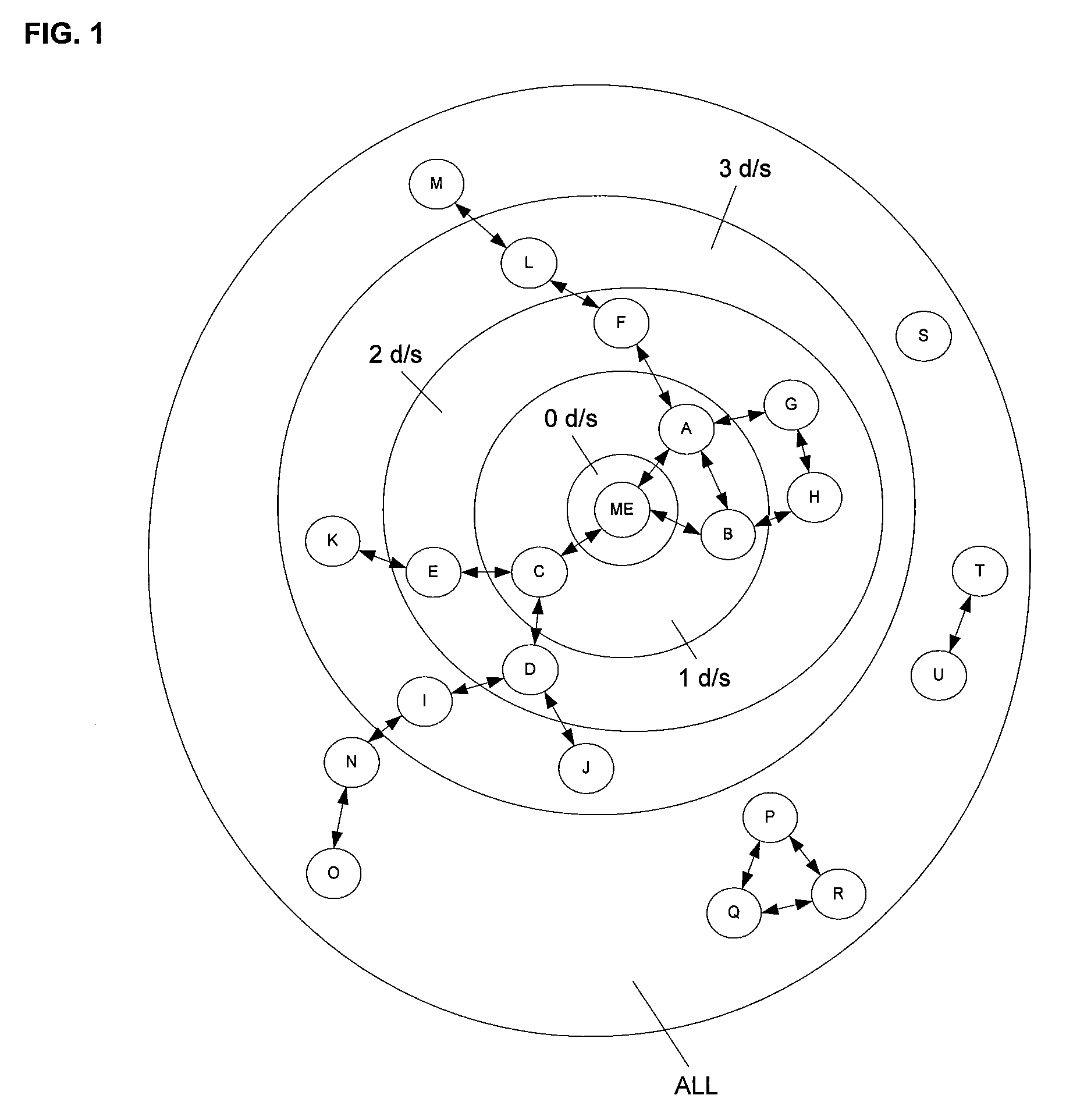
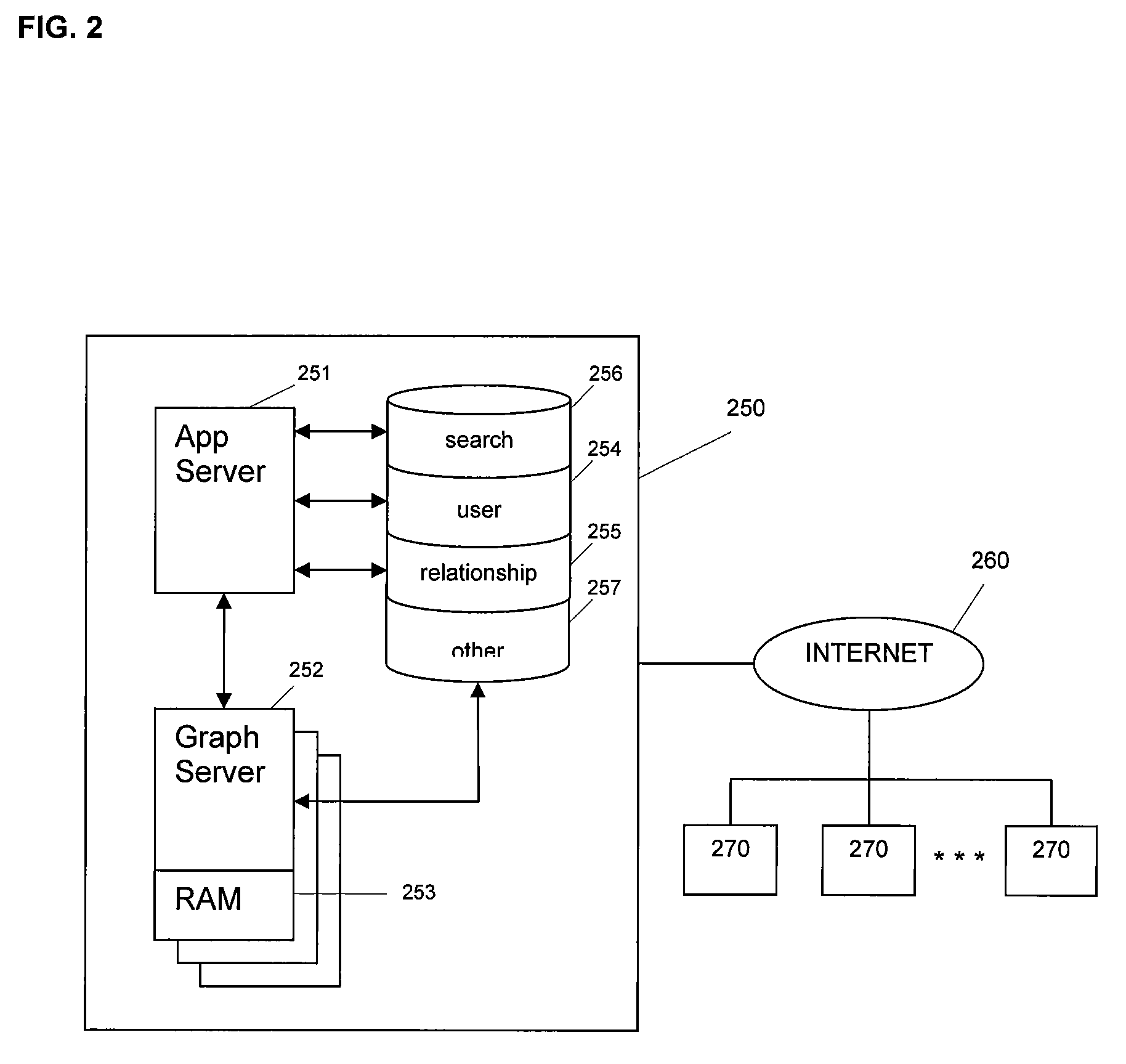
Feeding updates to landing pages of users of an online social network from external sources
ActiveUS20080065604A1More contentEfficiency of muchData processing applicationsDigital data processing detailsSocial webLanding page
Updates to landing pages of users in an online social network are fed from external sources so that content maintained by any one user can be consolidated in a single location regardless of where the changes are made to the content. When an update event occurs, users of the online social network are notified according to various criteria that they have set. With this feature, users can browse through content of other users efficiently.
Owner:META PLATFORMS INC
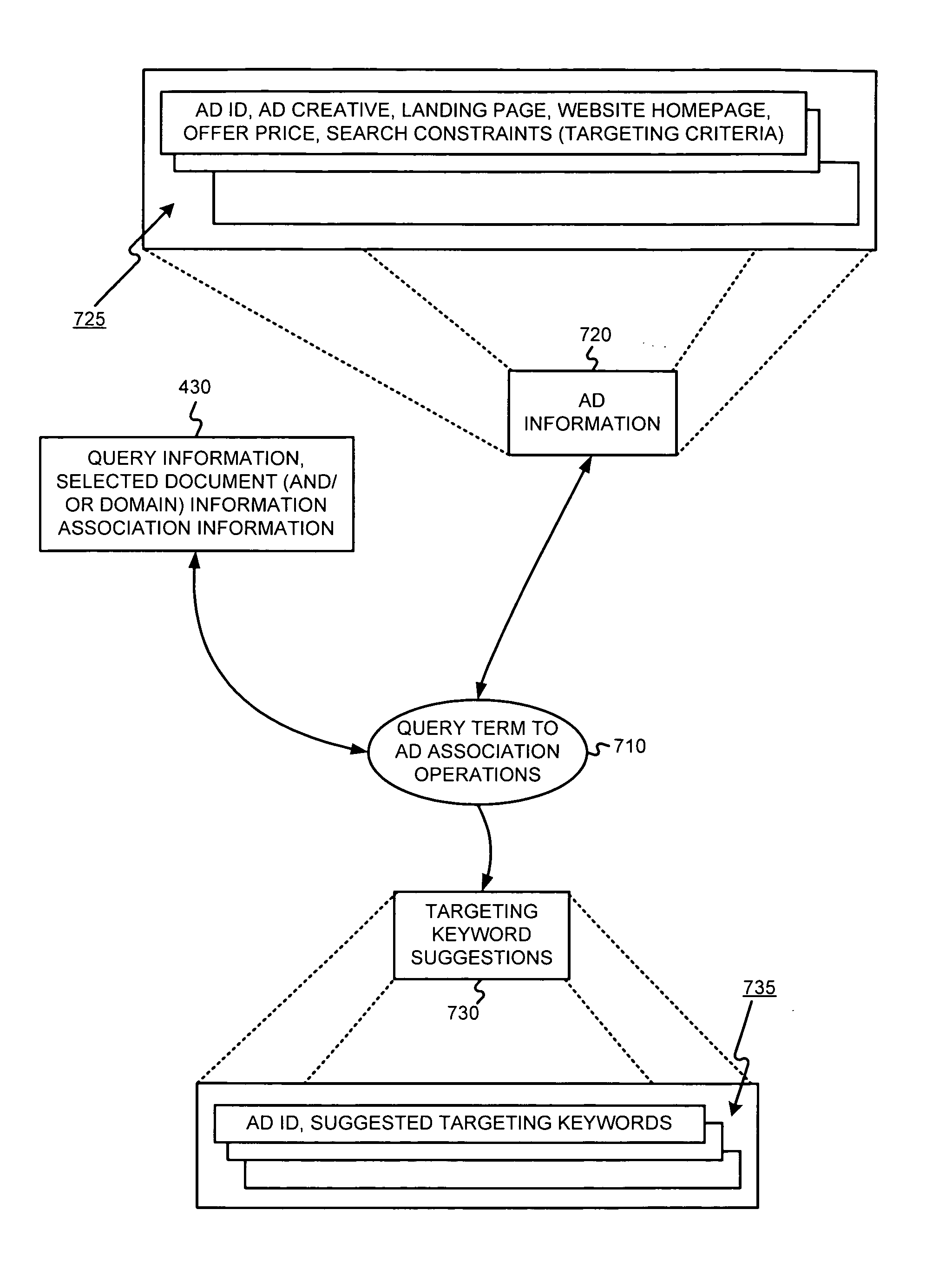
Determining ad targeting information and/or ad creative information using past search queries
InactiveUS20050222901A1Web data indexingUnstructured textual data retrievalDomain levelPaper document
Ad information, such as ad targeting keywords and / or ad creative content for example, may be determined using aggregated selected document-to-query information associations. For example, popular terms and / or phrases also associated with a selected document may be used as ad targeting keywords and / or ad creative content for an ad having the document as a landing page. Query information may be tracked on a per document level, a per domain level, etc. The determined ad information may be used to automatically populate an ad record, or may be provided to an advertiser as suggested or recommended ad information.
Owner:GOOGLE LLC
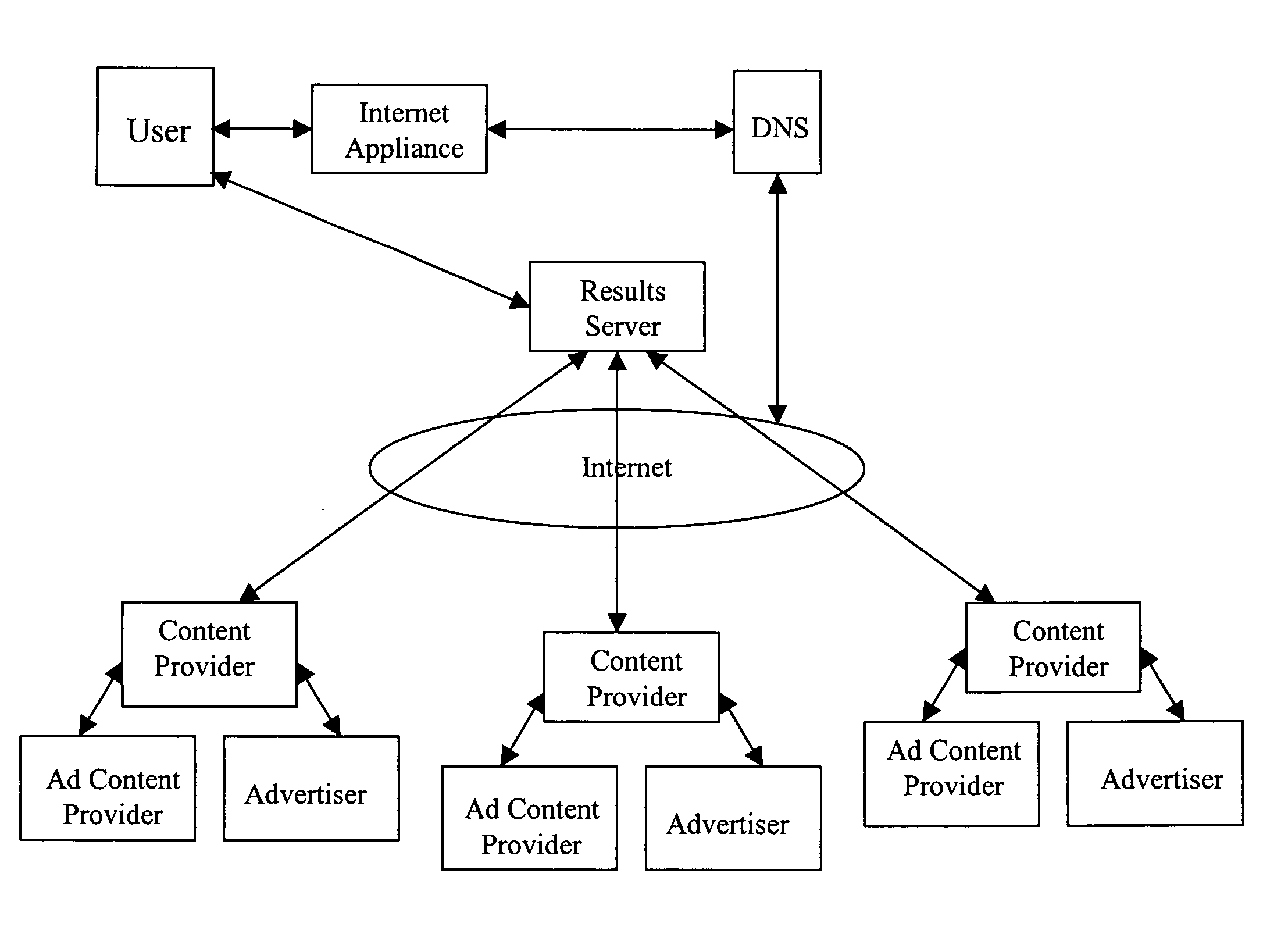
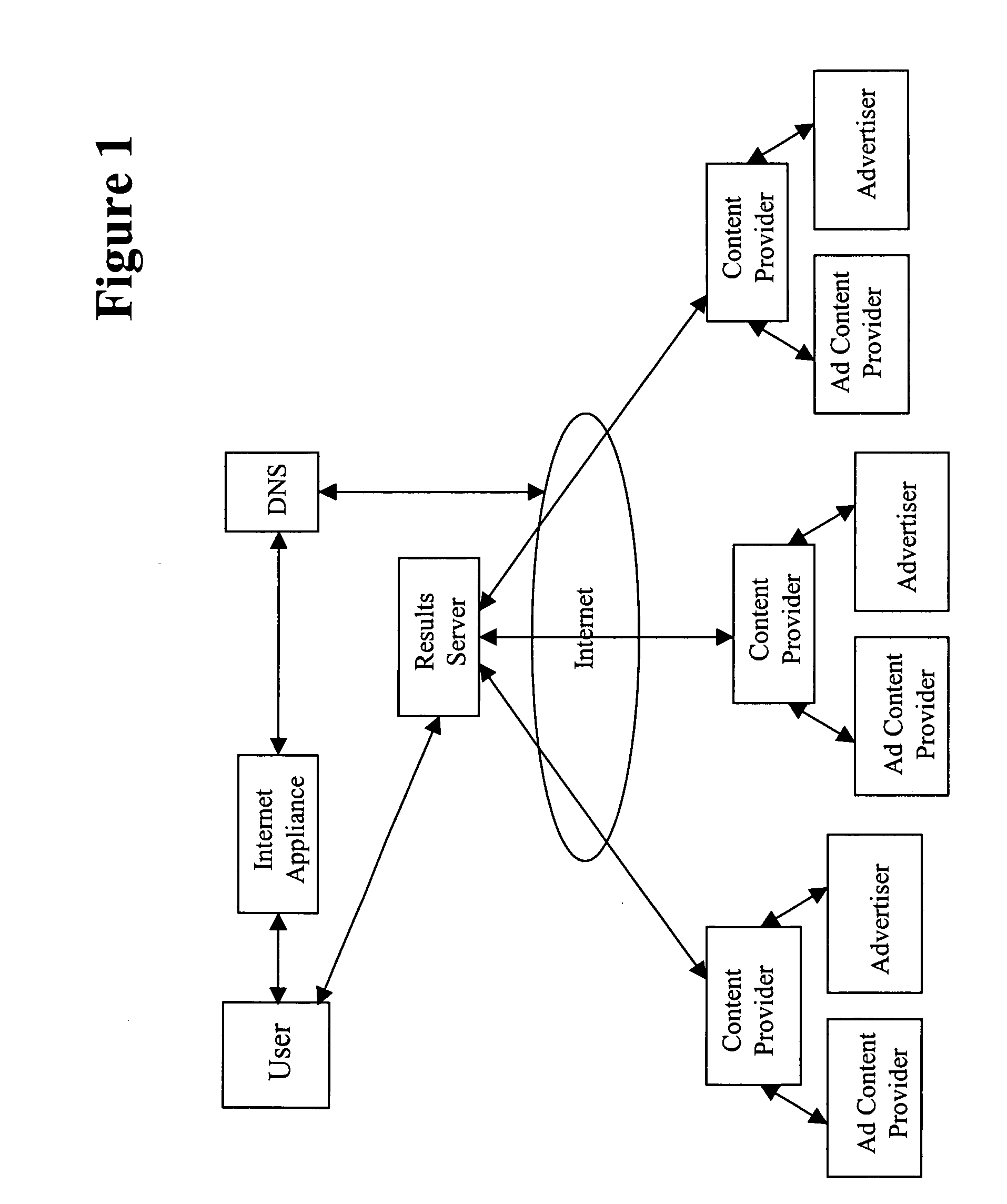
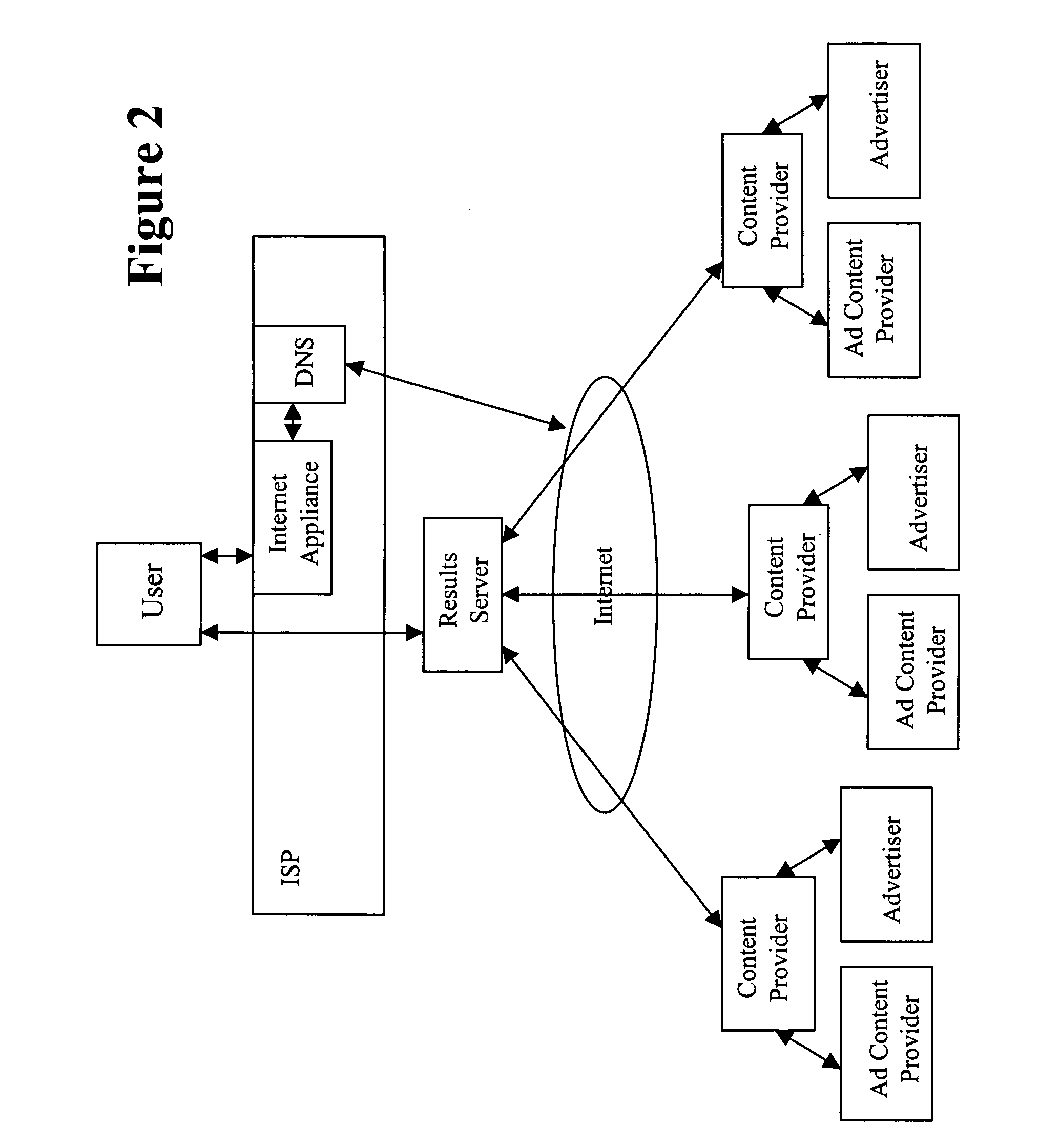
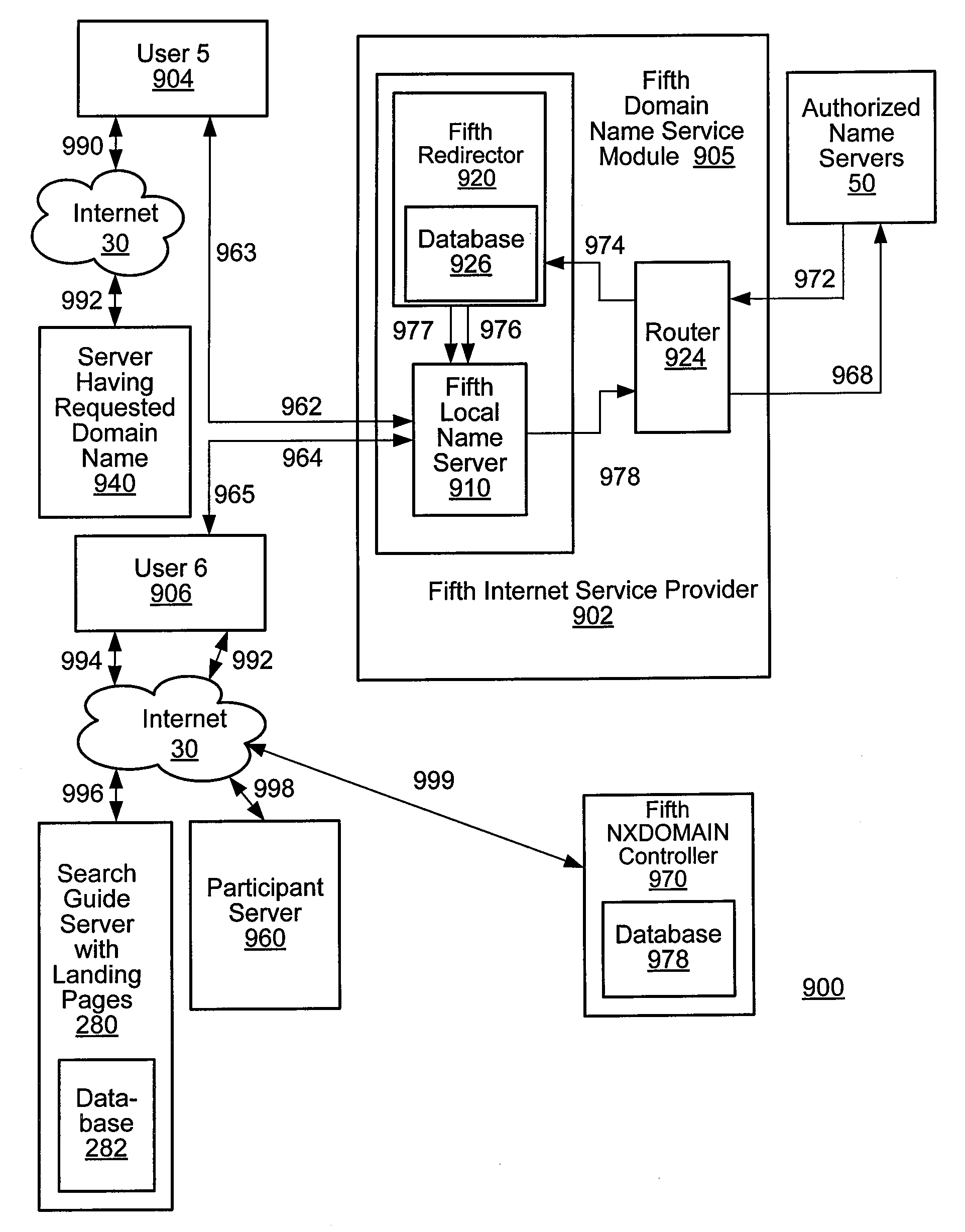
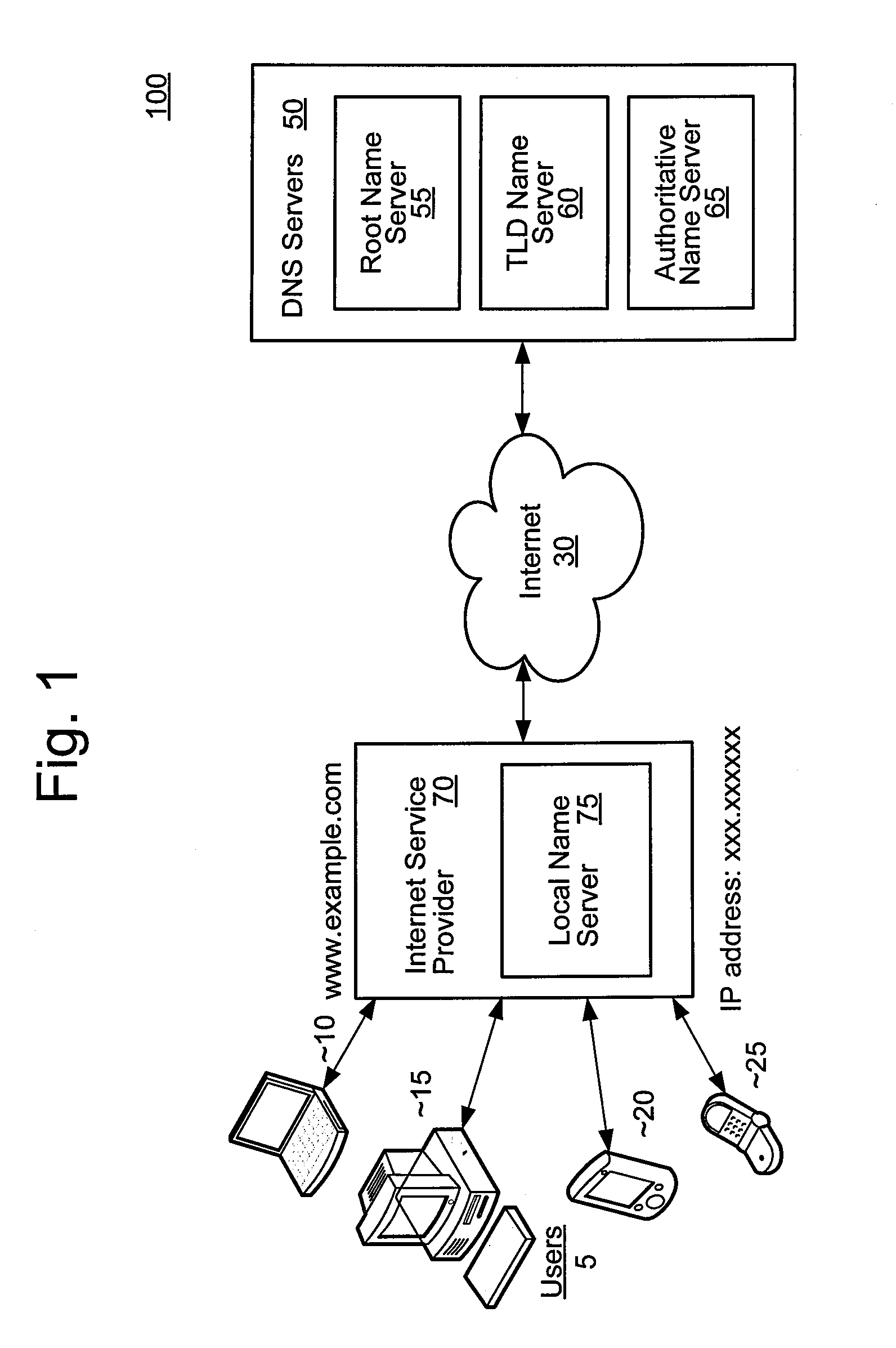
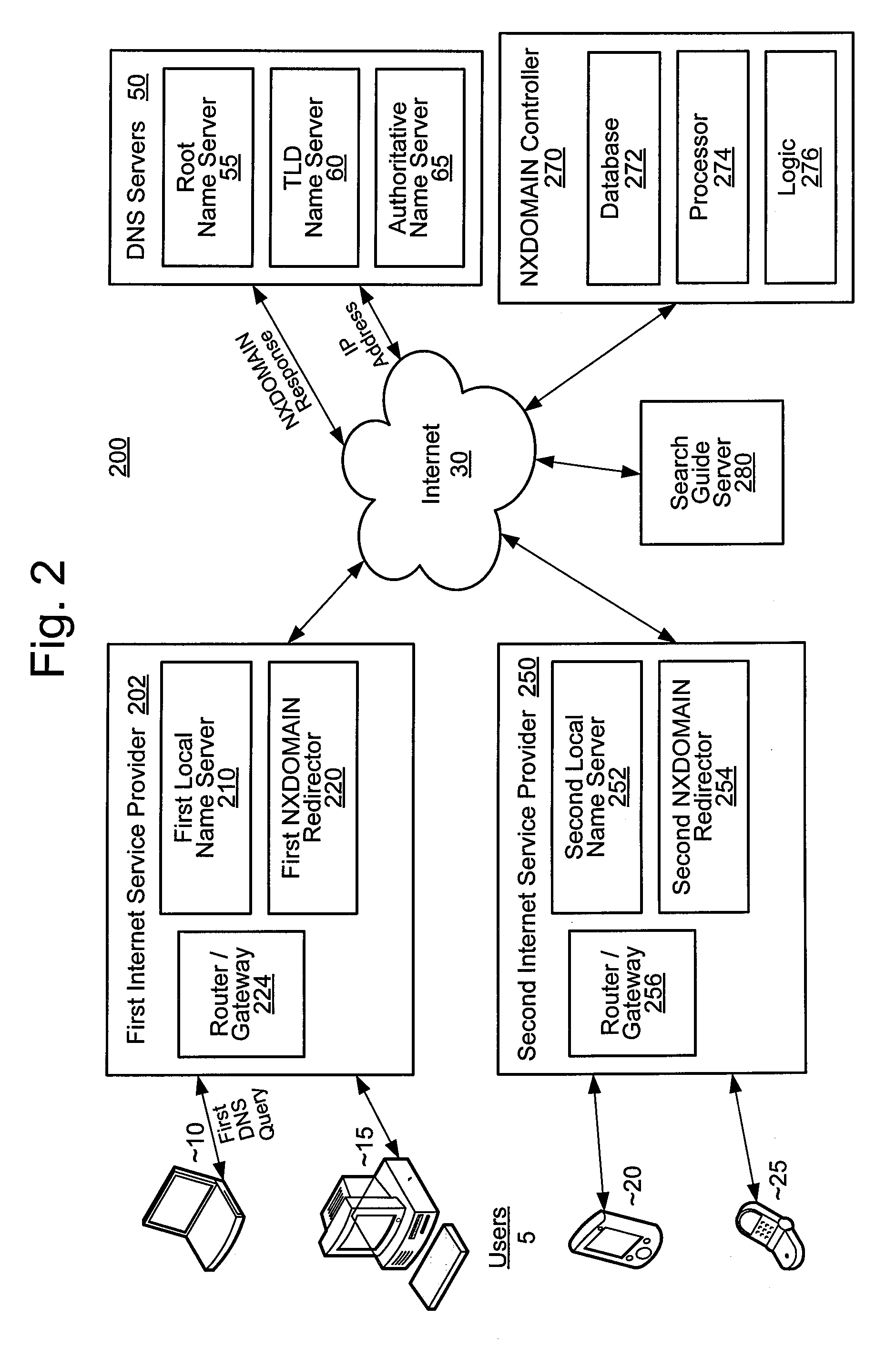
Systems and methods for providing information and conducting business using the internet
InactiveUS20070162331A1High trafficIncrease salesAdvertisementsDigital computer detailsInternet communicationLanding page
The present invention provides systems and methods of doing business that provide revenue streams to ISP based on advertising revenue for advertisements displayed to ISP customers as a result of Internet communication sessions. In certain configurations, the invention provides redirect services based on pre-defined criteria, and displays advertising on redirection landing pages.
Owner:PAXFIRE
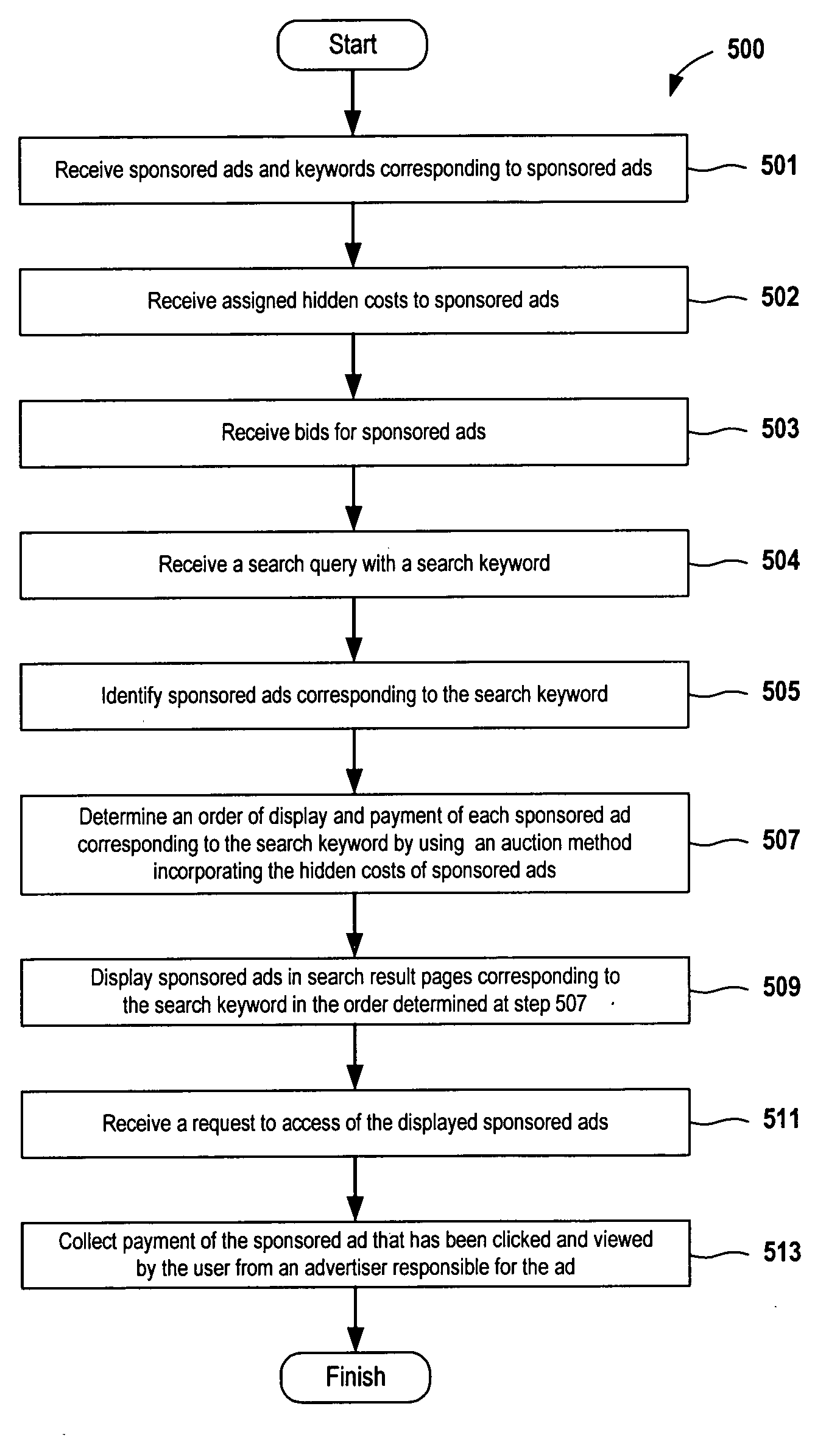
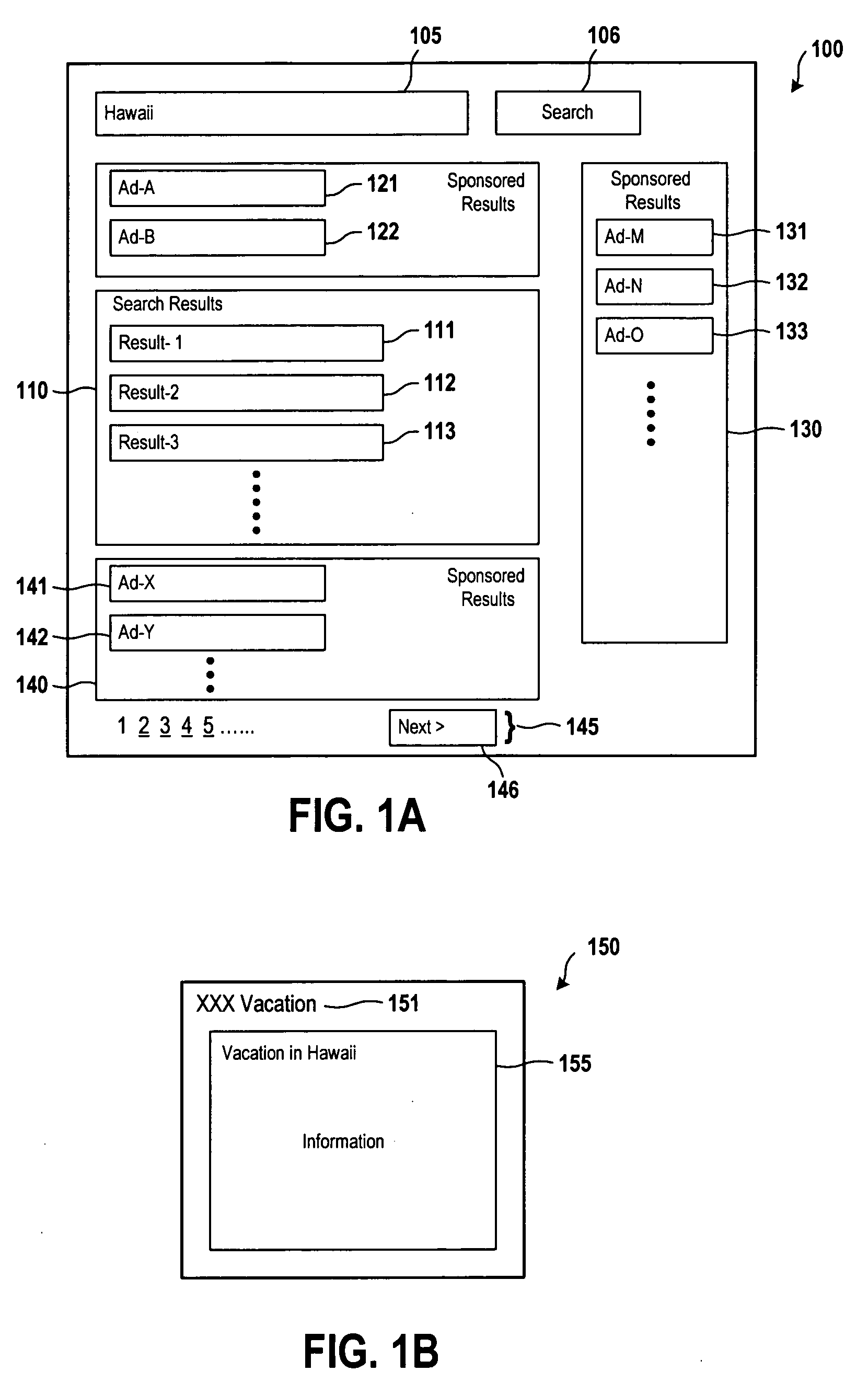
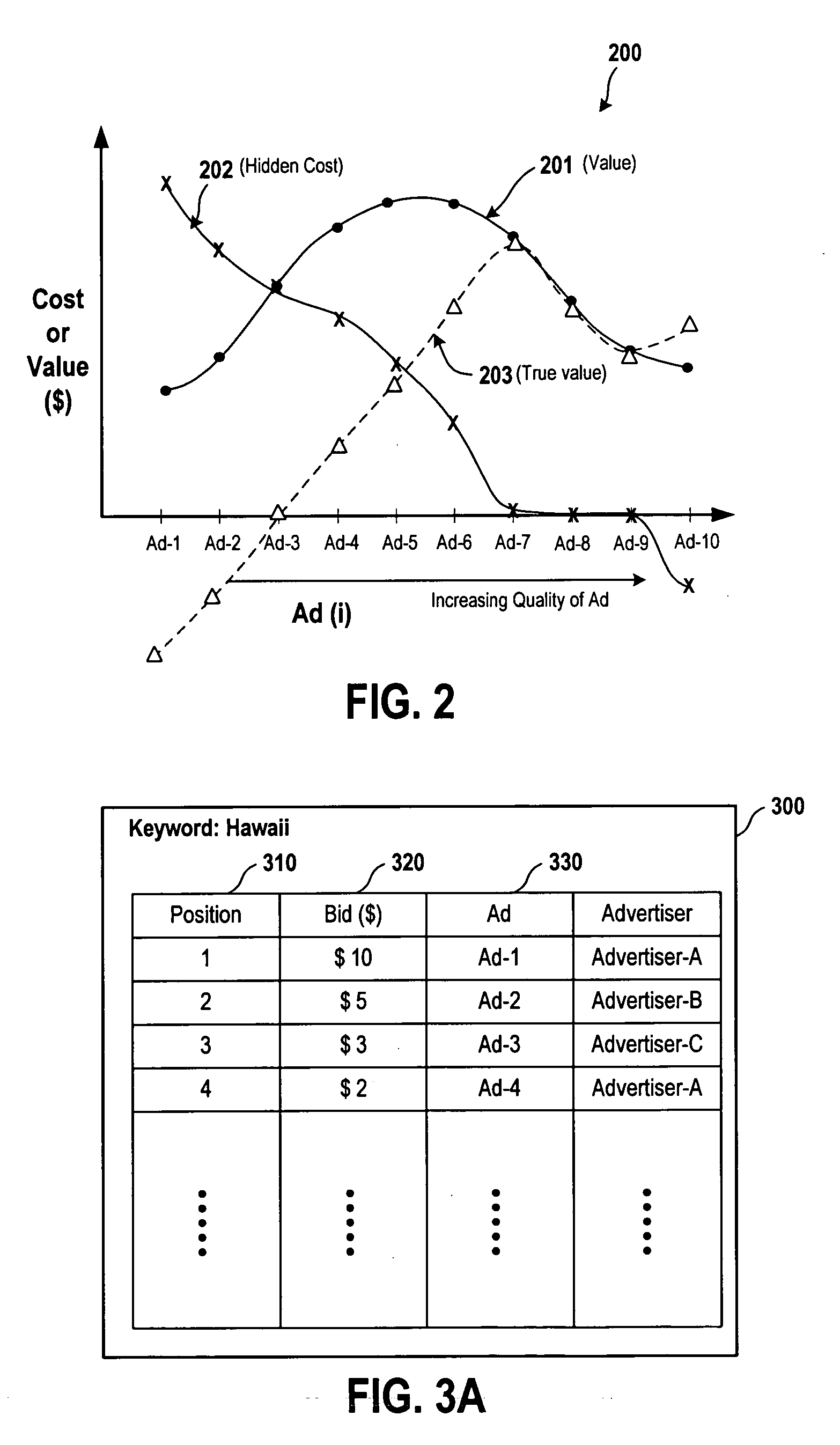
Method and system for managing advertisement quality of sponsored advertisements
InactiveUS20090254414A1Quality improvementNegative externalityAdvertisementsSpecial data processing applicationsWeb pagePoor quality
Various embodiments of systems and methods for auctioning sponsored ads are provided. The auctioning systems and methods take hidden costs of sponsored ads into account. A user's future propensity to click on ads is influenced by his / her experience with past clicks. An ad with disappointing quality of landing page imposes a negative externality on the search engine and the future stream of revenue from a user is reduced. The externality may also be positive. A good experience with an ad may train users to pay more attention to other ads. The externality of an advertisement (ad) can be considered as a “hidden cost.” Including hidden costs of sponsored ads in the auctioning process promote (or encourage) ads with good quality and discourage (or penalize) ads with poor quality. By doing so, advertisers are likely to improve the quality of ads being placed in the bidding pool, which will result in improvement in the overall quality of sponsored ads. Users benefit from the higher quality ads. The advertisers also benefit from the higher quality ads by paying less or no hidden costs for ads and by getting more satisfied customers. The search engine (site) can also benefit from having higher quality sponsored ads to gain more ad revenue.
Owner:YAHOO INC
System and method for controlling non-existing domain traffic
A system and method for controlling internet traffic controls internet traffic directed to a non-existing domain in a centralized manner. Instead of a non-existing domain response, the user may receive alternative responses such as a landing page including useful information and resourceful suggestions under the control of a global controller. The centralized control over the user's request may be implemented by redirecting a DNS query to the global controller or an optimal search guide server at an individual internet service provider level. Redirection of the DNS query may involve a record modification of a domain name resolution response indicating the non-existing domain.
Owner:HOSTWAY CORP
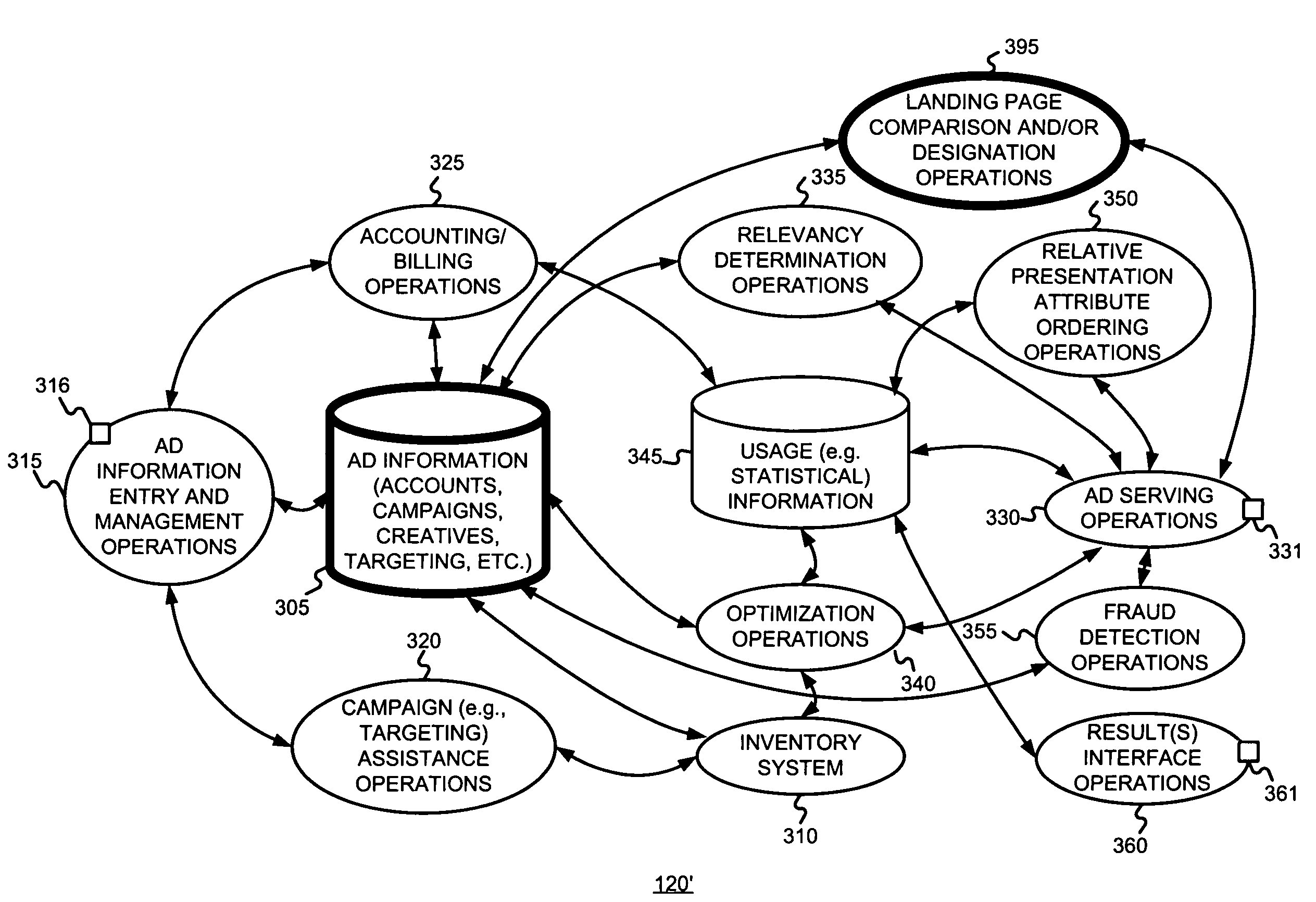
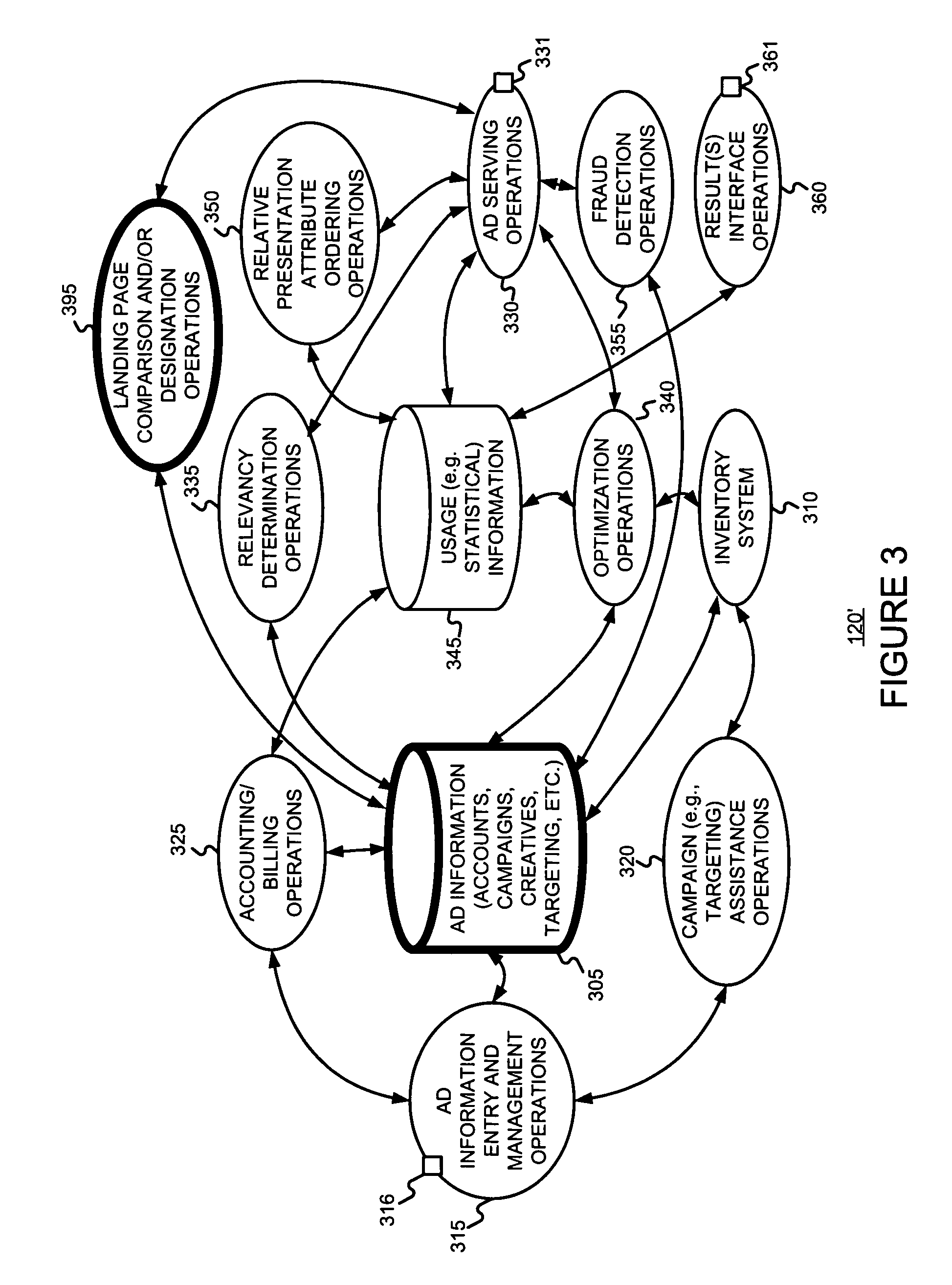
Determining and/or designating better ad information such as ad landing pages
ActiveUS7523087B1Improve performanceEasy to combineSpecial data processing applicationsMarket data gatheringApplication softwareWeb page
The performance (e.g., in terms of selection rates, conversion rates, revenues, profits, etc.) of different ad landing pages may be evaluated and compared by (i) for a given ad or collection of ads, serving the ad with the different ad landing pages (e.g., by rotating through the ad landing pages), and (ii) collecting per ad landing page performance information. An authorized user may be provided with such per ad landing page performance information and may designated one of the ad landing pages to be used in future serves of the ad. An authorized application program may be provided with such ad landing pages performance information and may designate one of the ad landing pages to be used in further serves of the ad using such information.
Owner:GOOGLE LLC
Systems and methods for performing or creating simulated phishing attacks and phishing attack campaigns
ActiveUS20170251009A1Risk minimizationMalicious action is preventedTransmissionElectronic mailData library
A method for establishing a campaign for a simulated phishing attack includes receiving, via a campaign manager, specification of a plurality of parameters for a campaign including at least an identifier of a campaign and identification of users to which to send the campaign, establishing, via the campaign manager, a type of exploit for the campaign and one or more types of data to collect via the type of exploit, storing, by the campaign manager, the campaign comprising the plurality of parameters, and identifying, by a simulation server, the campaign stored in the database to create a simulated phishing email, to be sent to email accounts of the users, using the plurality of parameters of the campaign, wherein the simulated phishing email is to be created to have a link to a landing page comprising the type of exploit and configured to collect the one or more types of data.
Owner:KNOWBE4 INC
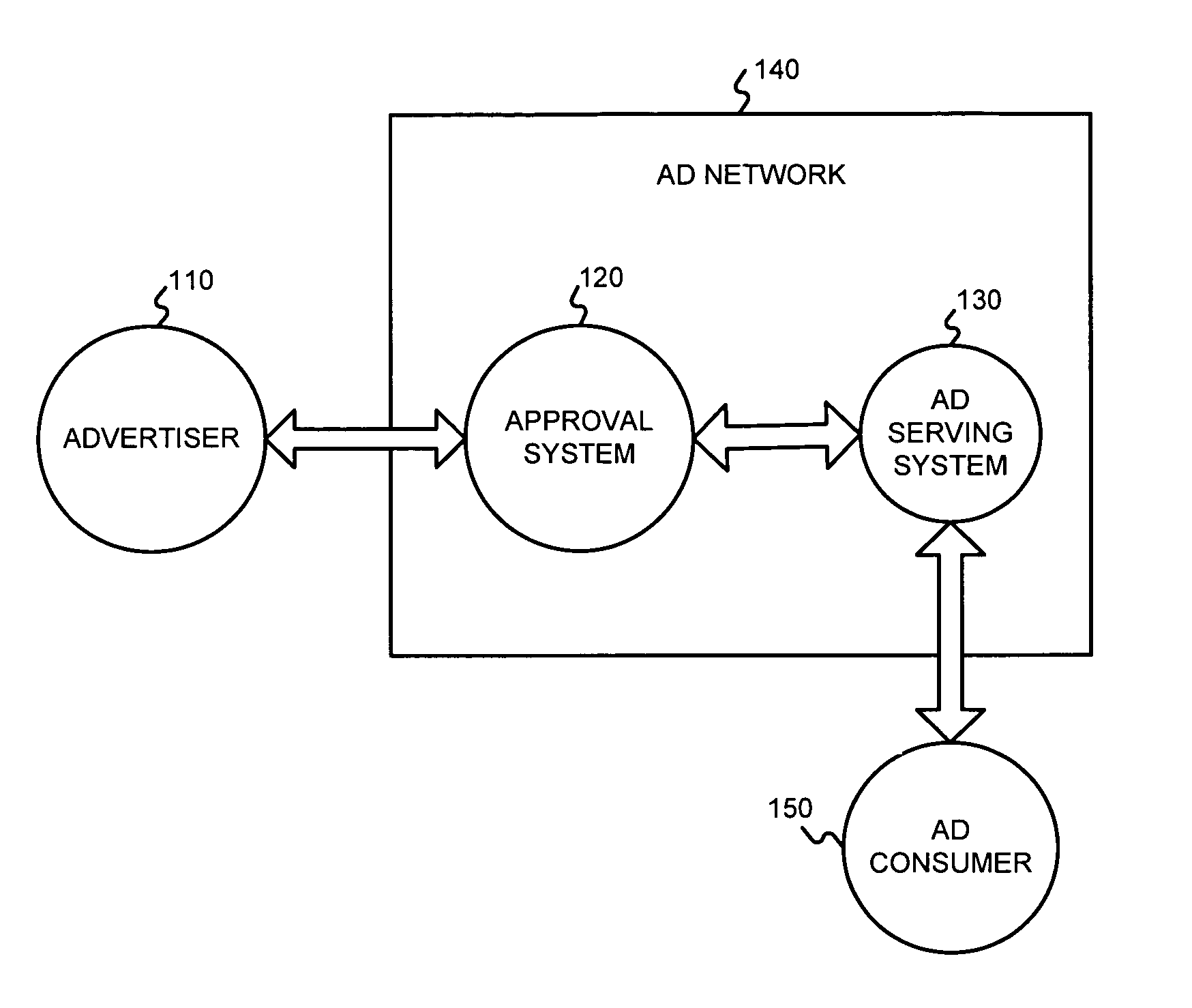
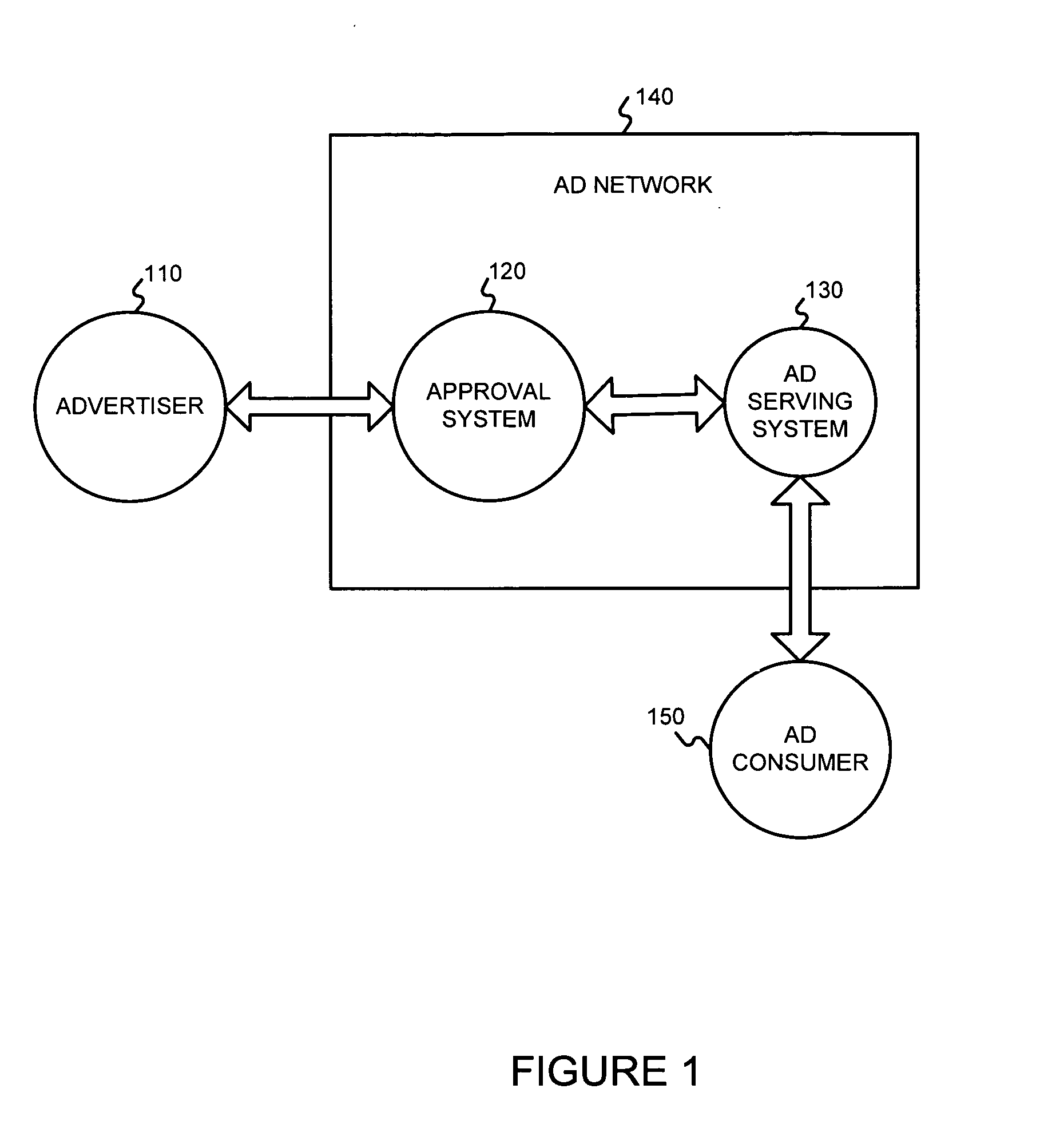
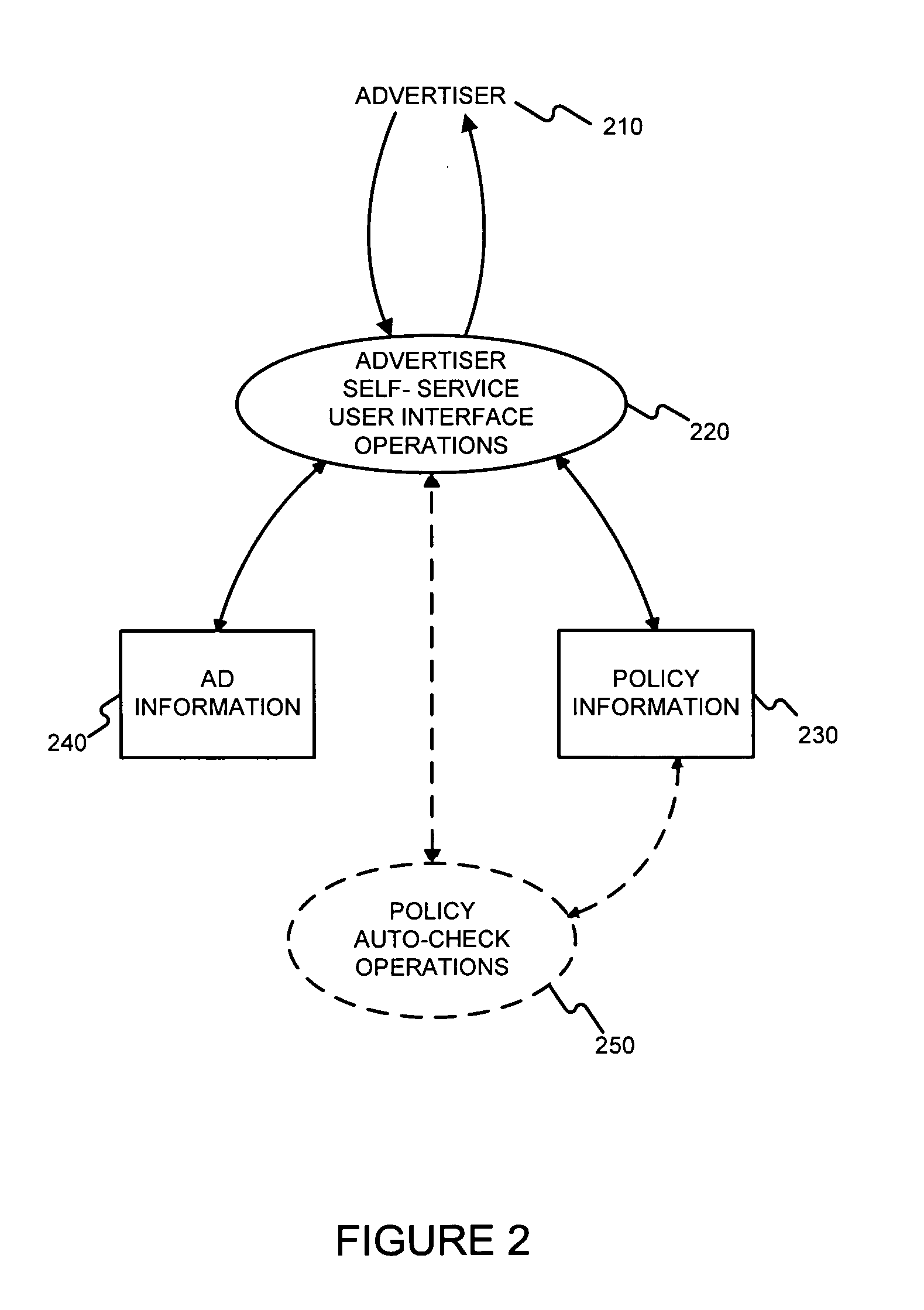
Advertisement approval
An advertisement for use with an online ad serving system may be automatically checked for compliance with one or more policies of the online ad serving system. If the advertisement is approved, then it is allowed by be served by the ad serving system. Follow up checks of the advertisement may be scheduled. One follow up check may be to test a landing page of the advertisement for compliance with policies. If the advertisement is not approved, hints for making the ad comply with one or more violated policies may be provided to an advertiser associated with the ad, and / or an ad serving system customer service representative. Determining whether or not to approve the advertisement may include determining violations of one or more policies by the advertisement, and, for each of the violations, determining whether or not to exempt the violation.
Owner:GOOGLE LLC
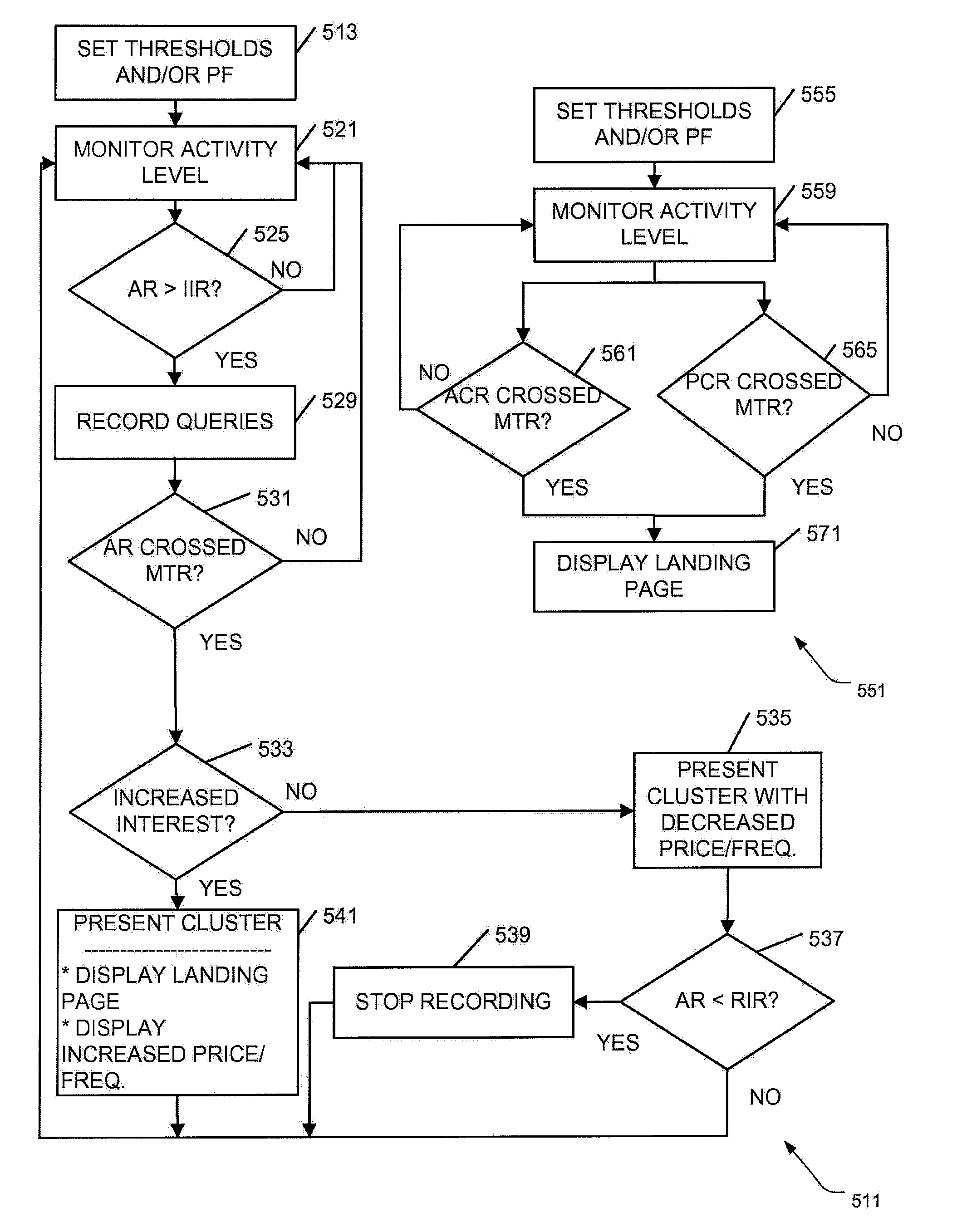
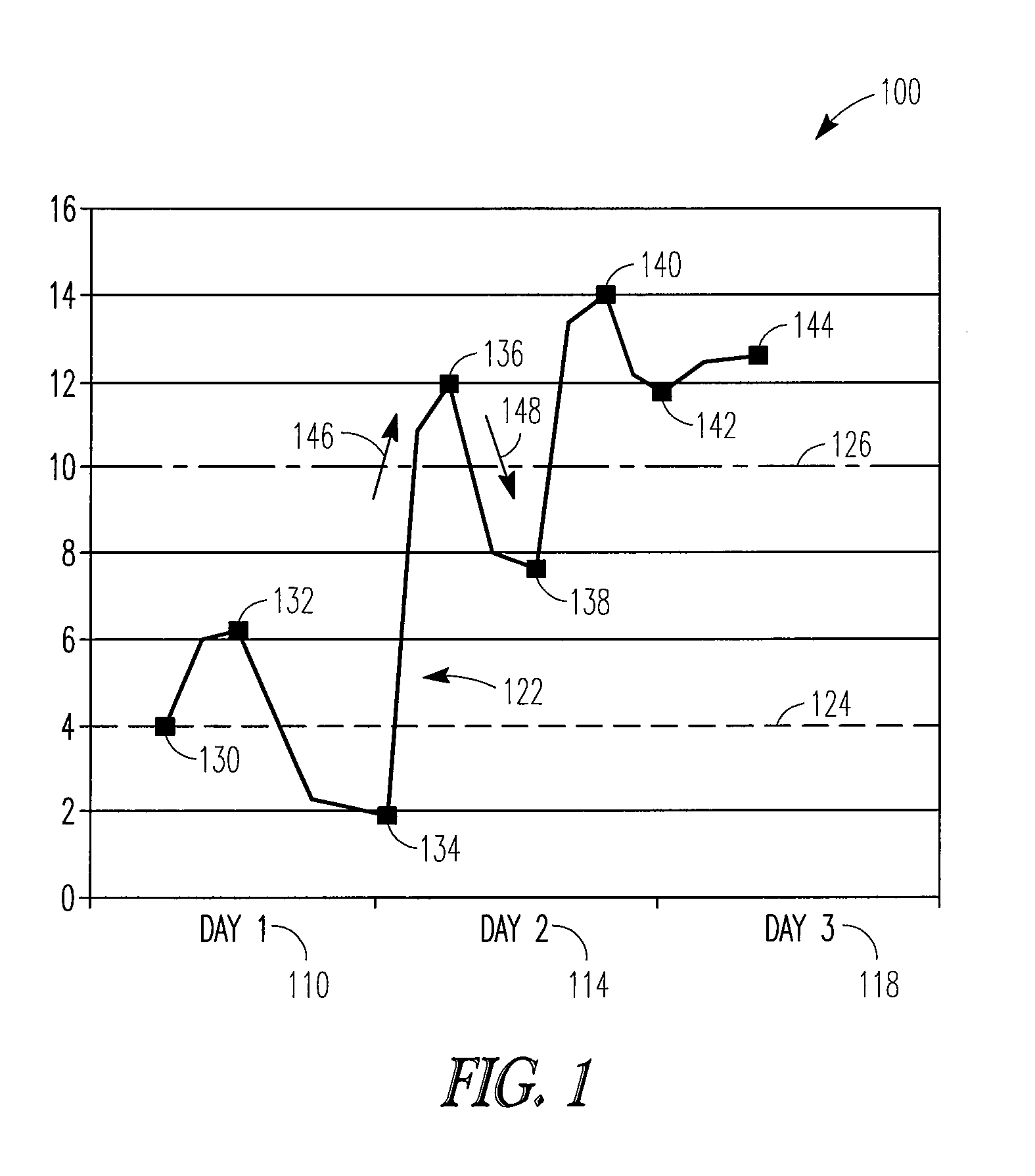
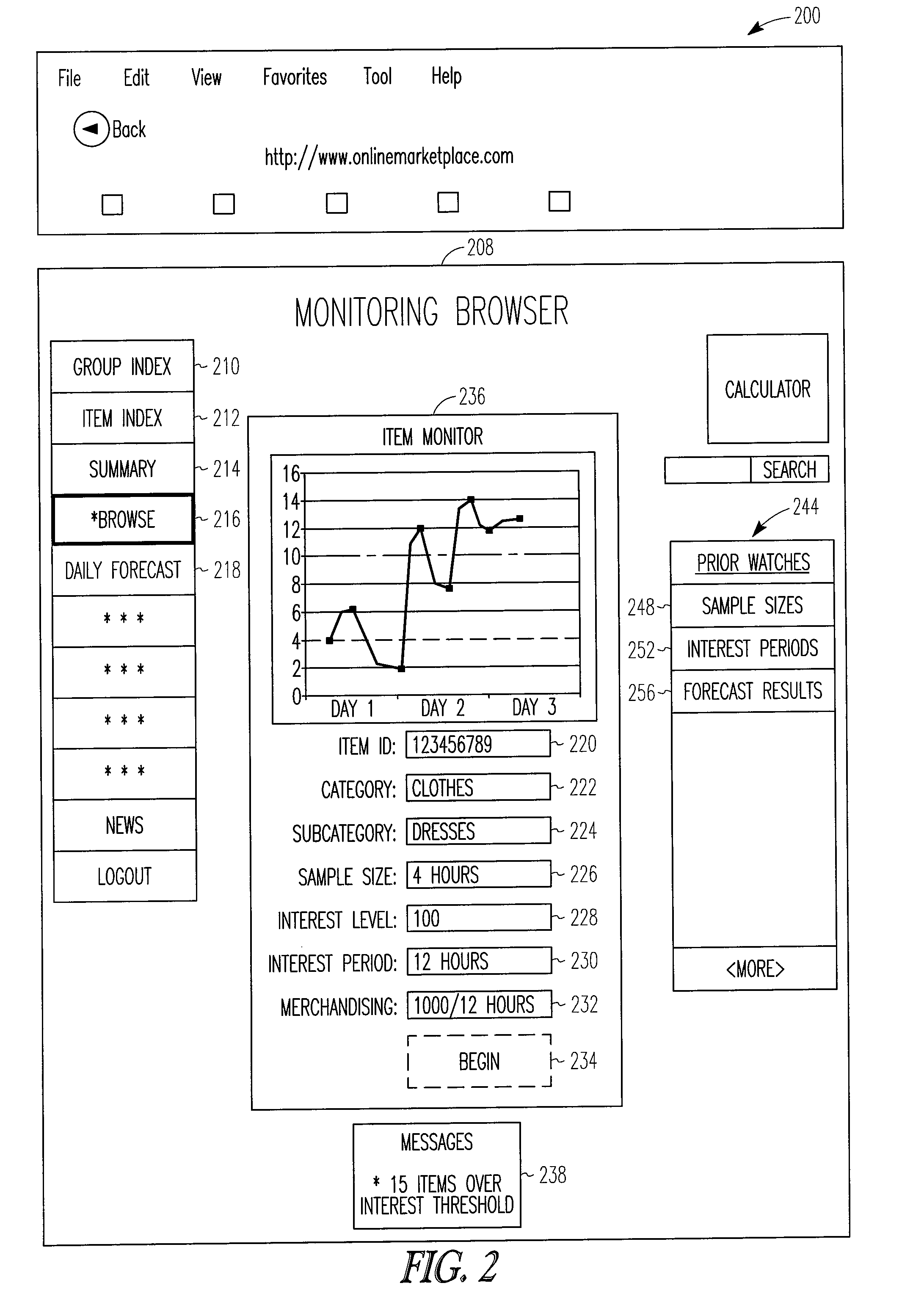
Interest level detection and processing
Apparatus, systems, and methods may operate to monitor an activity level associated with queries made in an online marketplace over a monitoring time period to provide an activity rate, and to determine that the activity rate has crossed a merchandising threshold rate. In response, a cluster of items or item groups associated with the queries may be presented on a display, perhaps in conjunction with a landing page merchandising promotion. Additional apparatus, system, and methods are disclosed.
Owner:EBAY INC
Systems and methods for performing or creating simulated phishing attacks and phishing attack campaigns
ActiveUS9894092B2Expose a lack of vigilance and/or know-howRisk minimizationTransmissionElectronic mailData library
A method for establishing a campaign for a simulated phishing attack includes receiving, via a campaign manager, specification of a plurality of parameters for a campaign including at least an identifier of a campaign and identification of users to which to send the campaign, establishing, via the campaign manager, a type of exploit for the campaign and one or more types of data to collect via the type of exploit, storing, by the campaign manager, the campaign comprising the plurality of parameters, and identifying, by a simulation server, the campaign stored in the database to create a simulated phishing email, to be sent to email accounts of the users, using the plurality of parameters of the campaign, wherein the simulated phishing email is to be created to have a link to a landing page comprising the type of exploit and configured to collect the one or more types of data.
Owner:KNOWBE4 INC
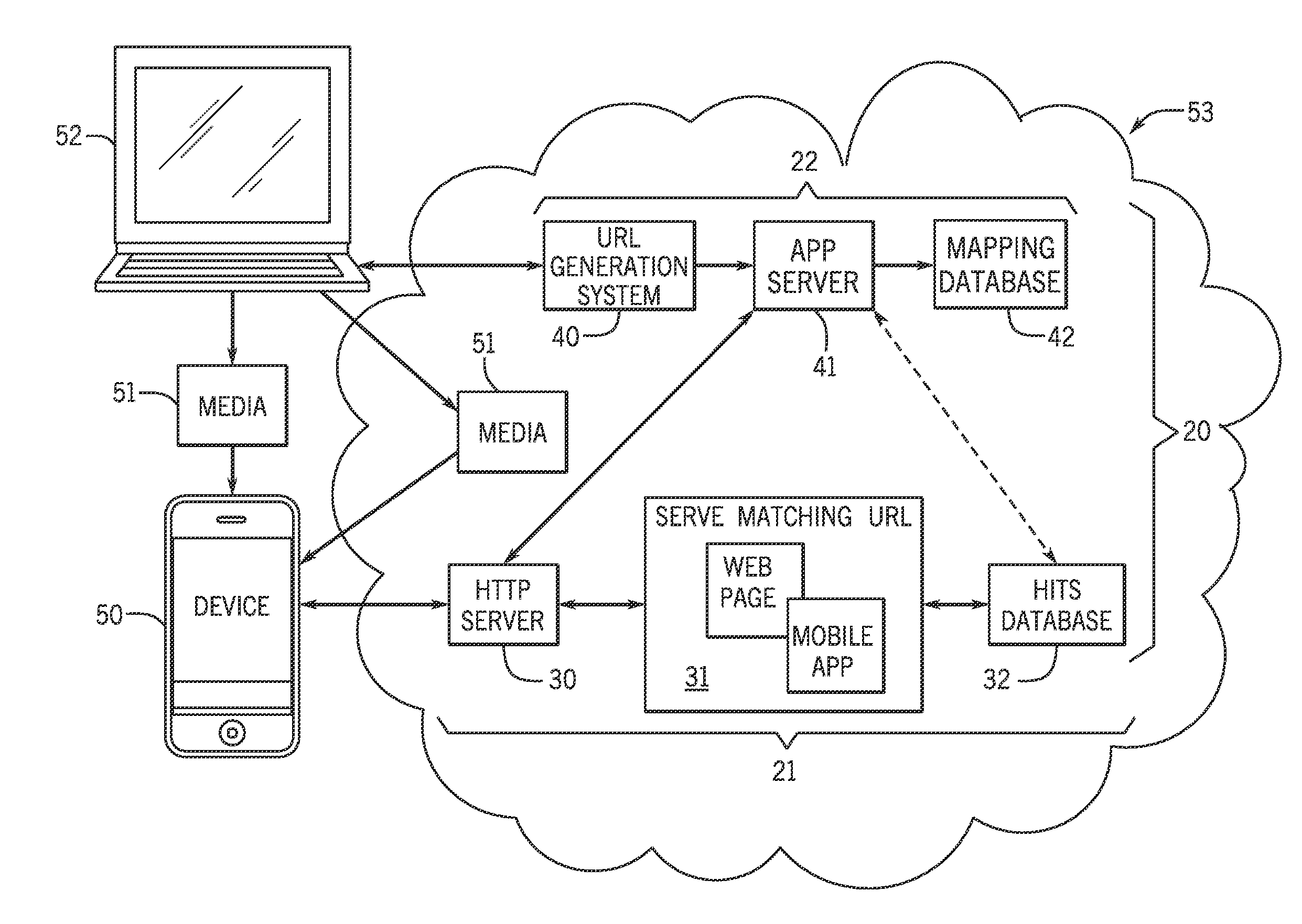
Uniform resource locator mapping and routing system and method
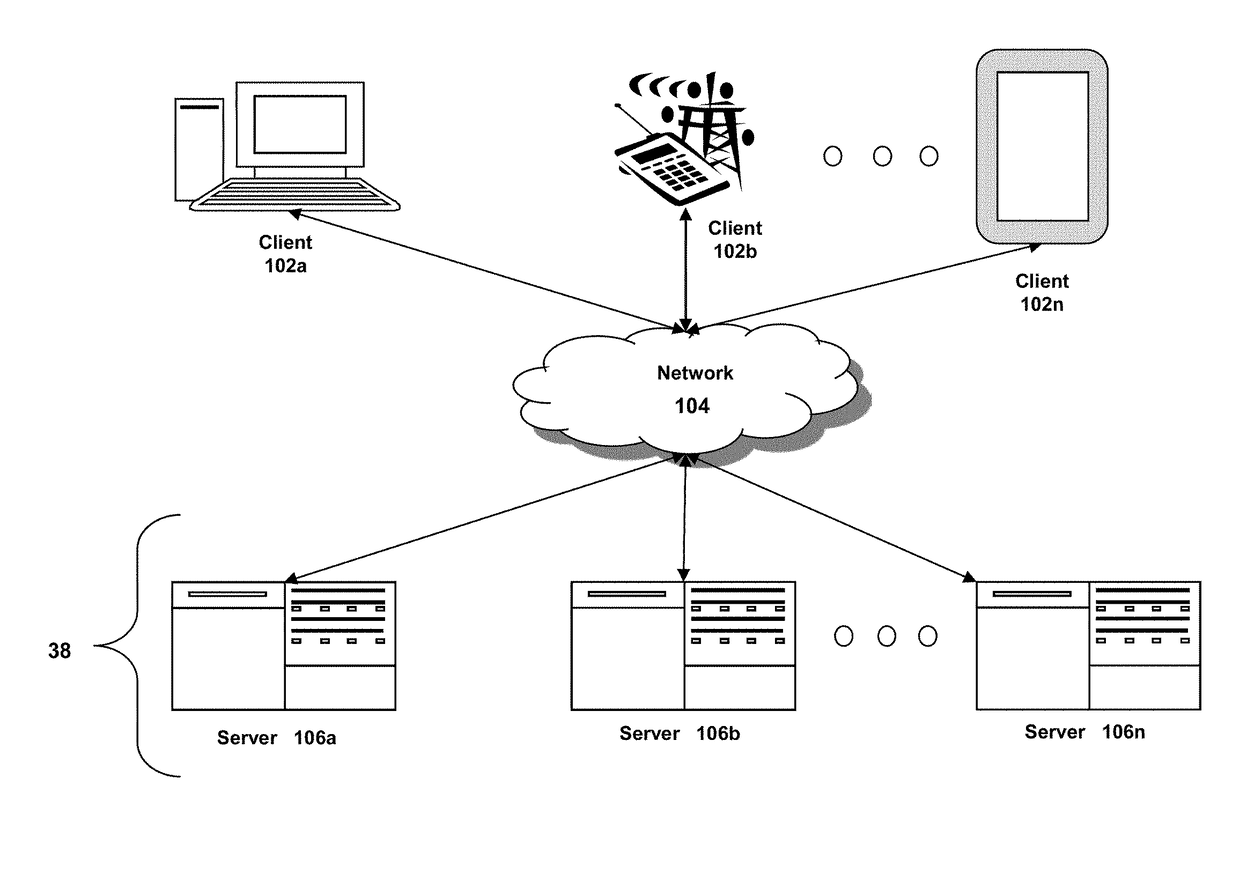
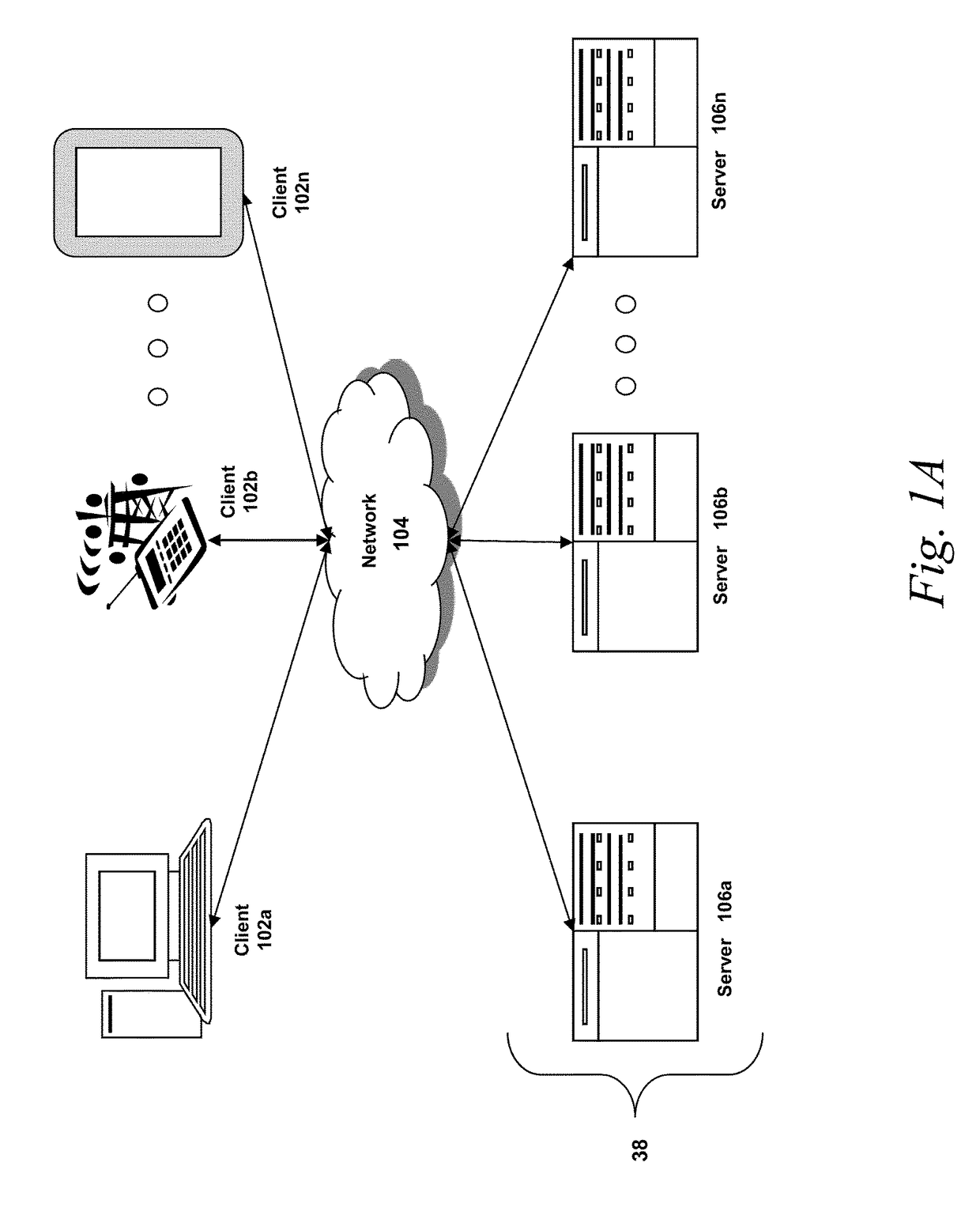
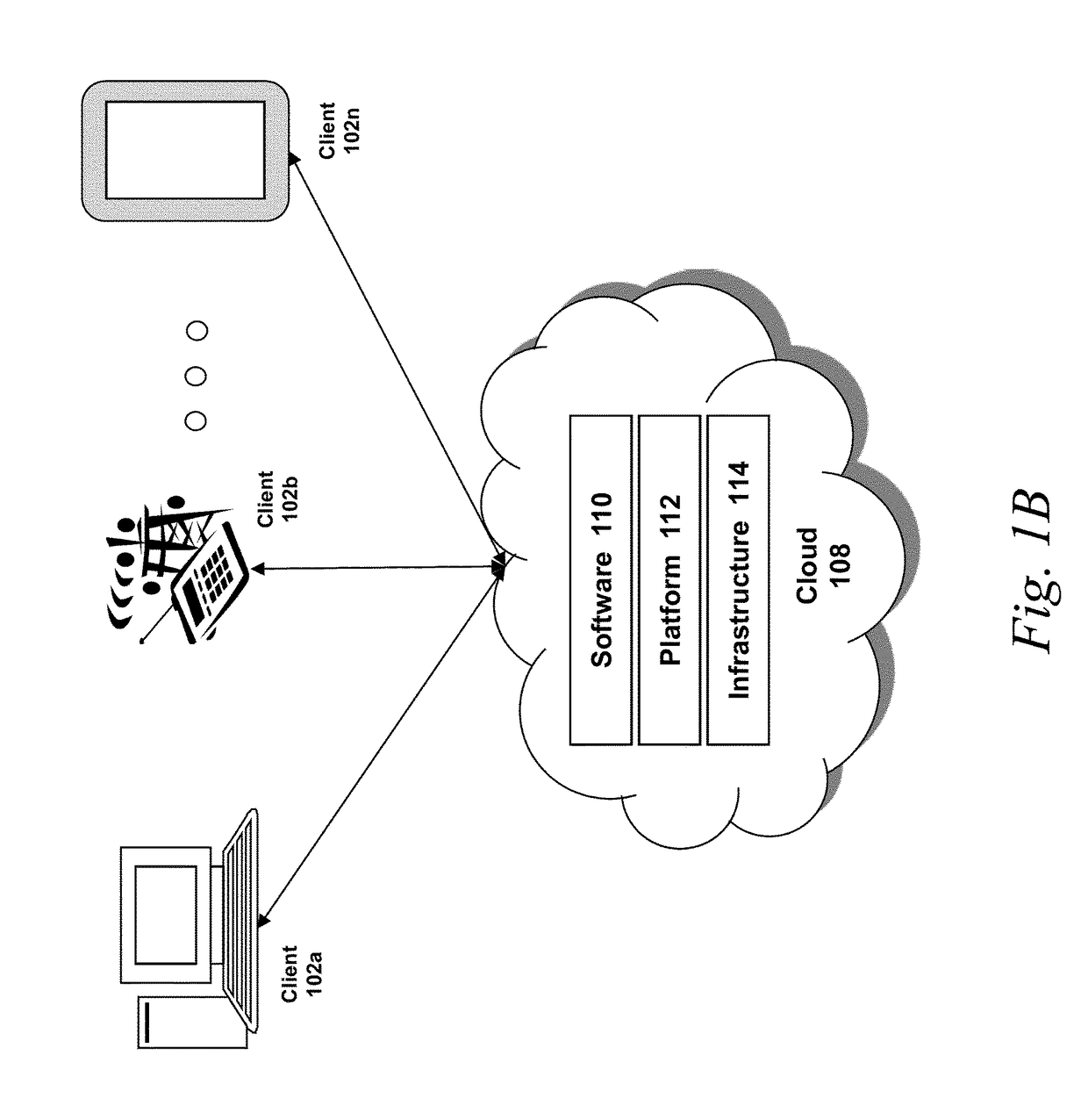
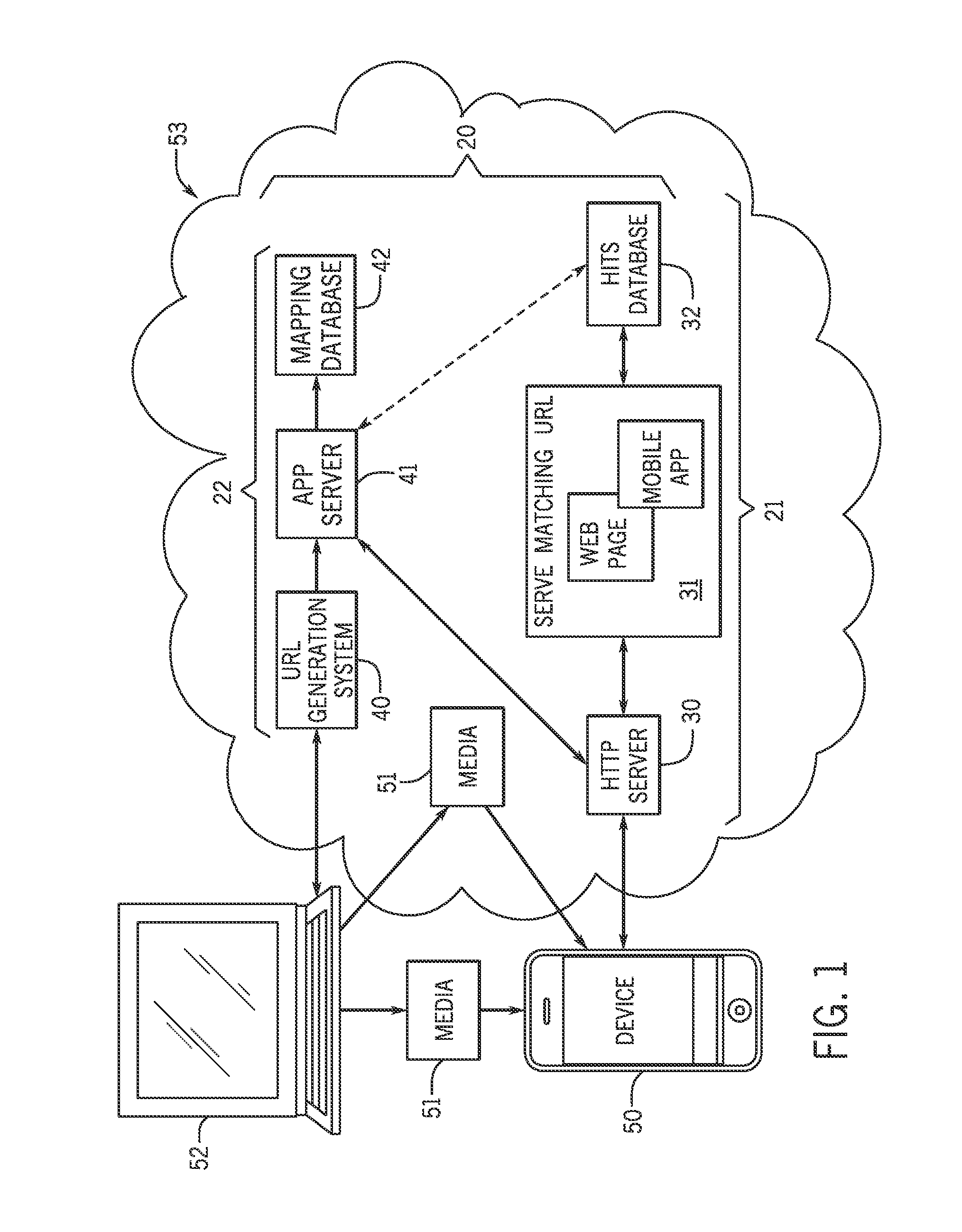
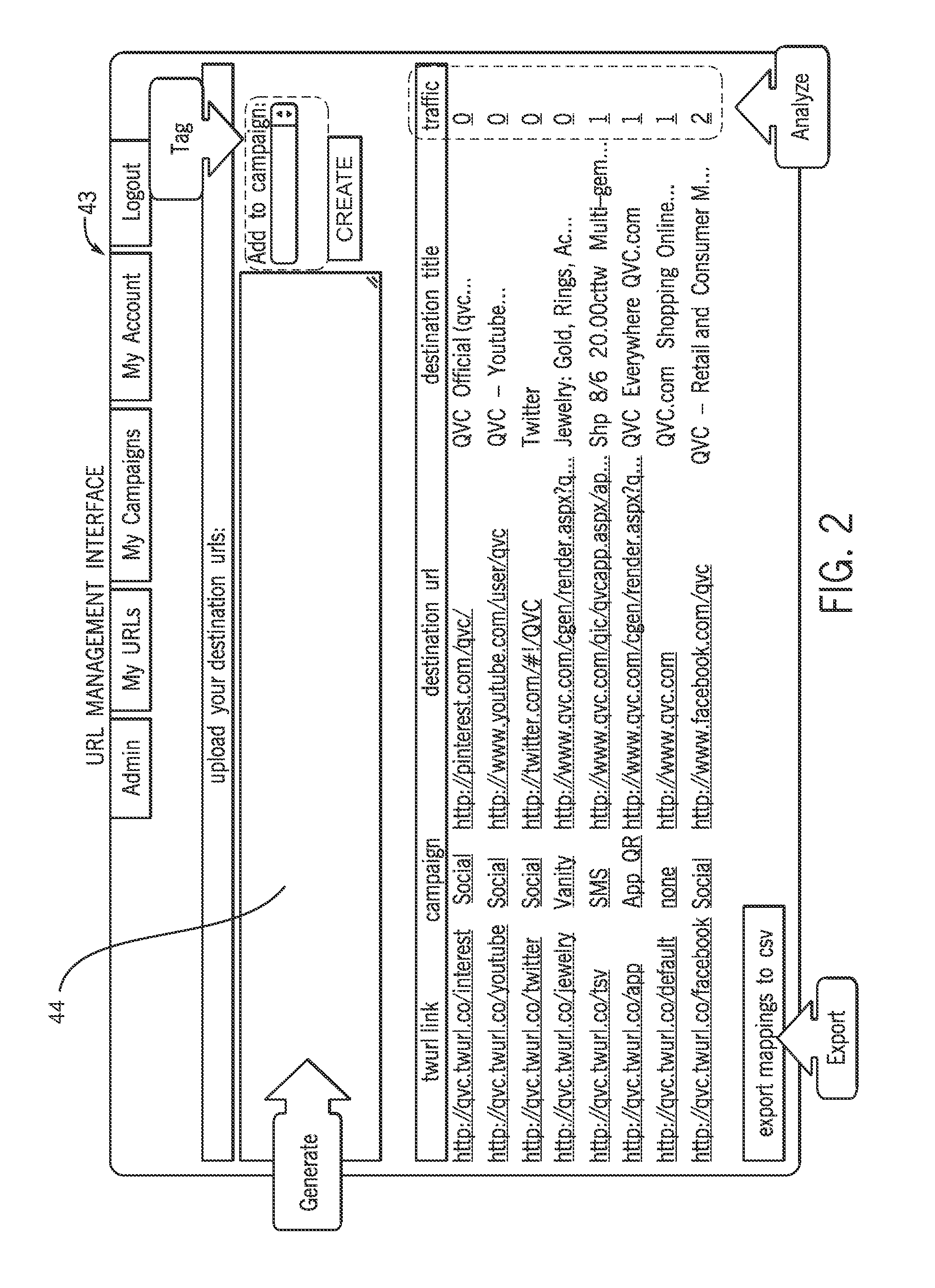
ActiveUS20140129733A1Digital computer detailsData switching networksInternet usersUniform resource locator
A uniform resource locator (URL) mapping and routing system and method for generating, routing, and managing URLs is used to route internet users to application landing pages or websites based on a URL mapping scheme. Routing instructions for the URL may route a user accessing a URL to a destination landing page or an alternate landing page depending on routing instructions in the URL mapping scheme.
Owner:PURE OXYGEN LABS
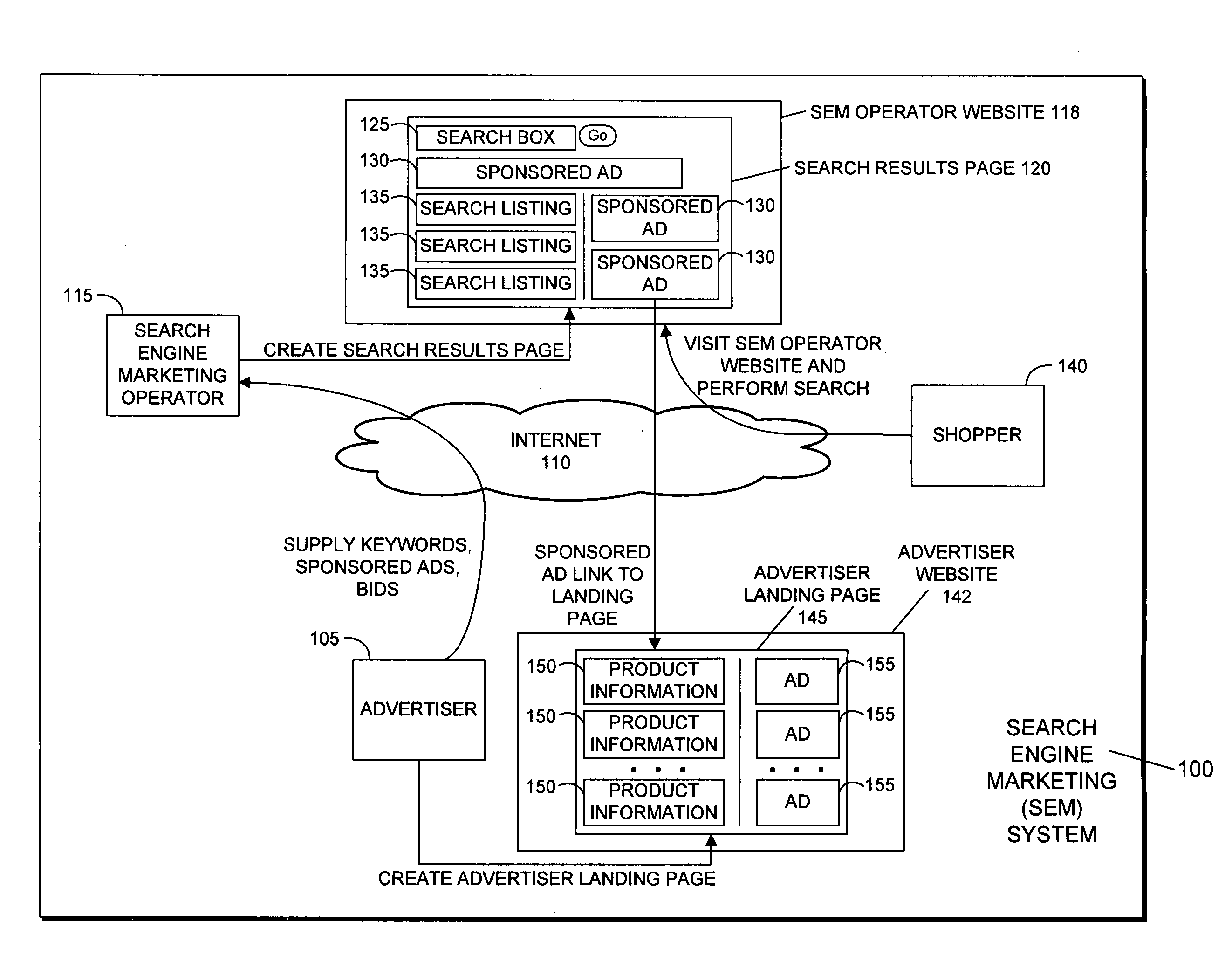
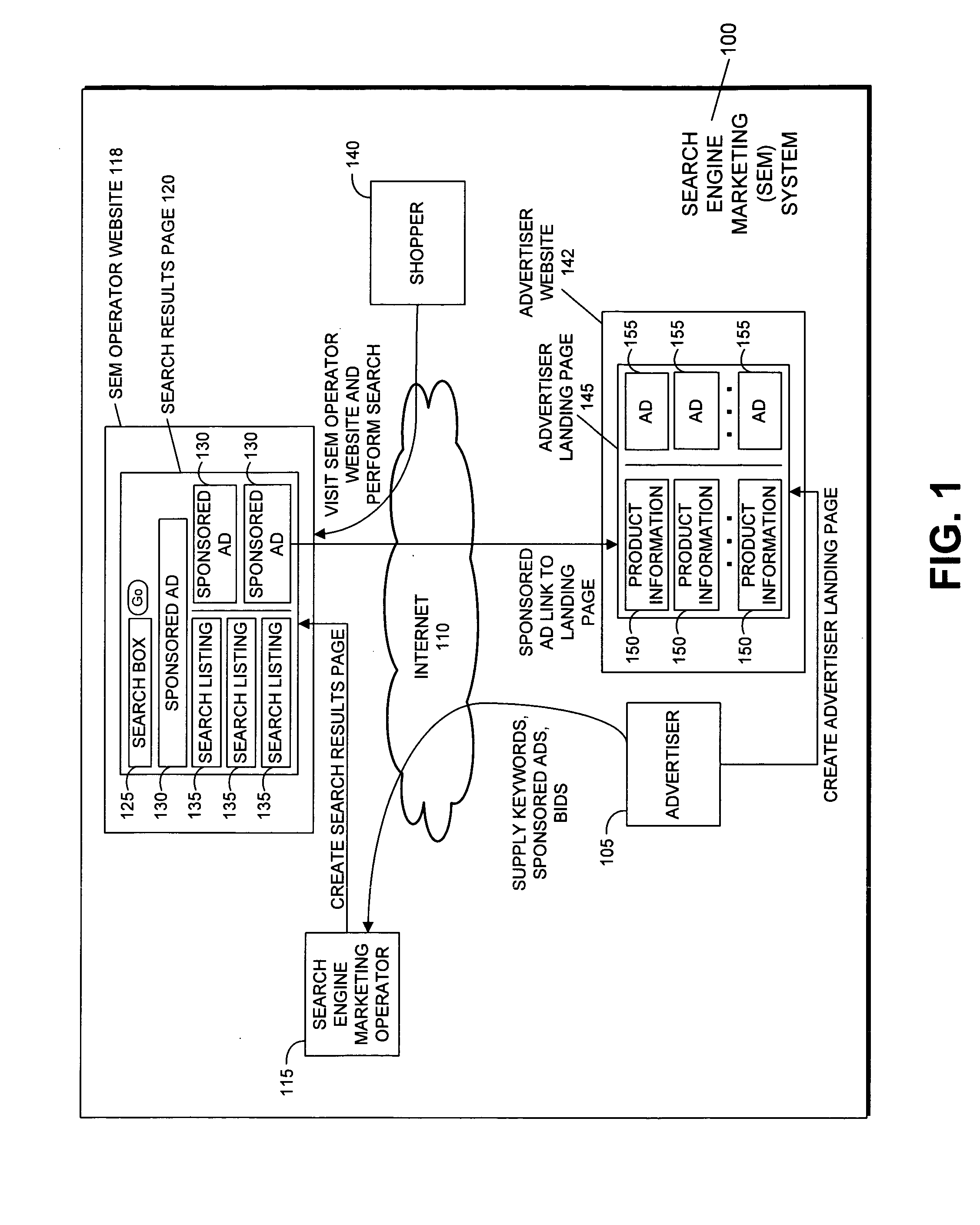
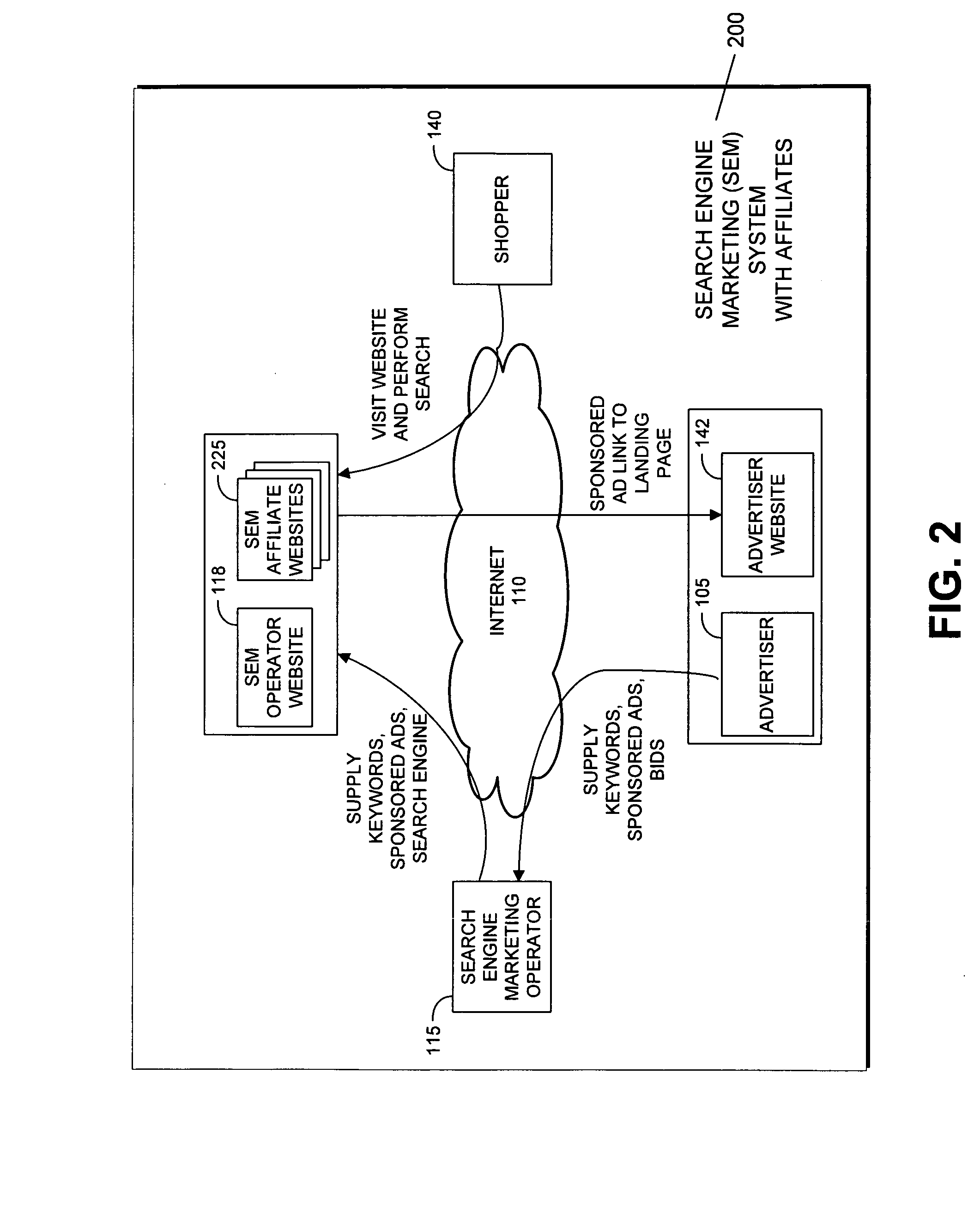
Bidding system for search engine marketing
A method for search engine keyword bidding, including providing a search engine that is used by shoppers to search for products and services, maintaining by an advertiser a keyword database used by the search engine, collecting by the advertiser statistics for revenue generated during each Internet session on the advertiser's website that begins when a shopper visits the advertiser's landing page in response to the shopper clicking on an advertiser's sponsored ad, maintaining by the advertiser a tracking database comprising records of Internet sessions for a plurality of shoppers, and periodically revising by the advertiser a bid amount for a keyword in the keyword database, based on total revenue in the tracking database corresponding to the keyword over a given time period.
Owner:MARKET AMERICA
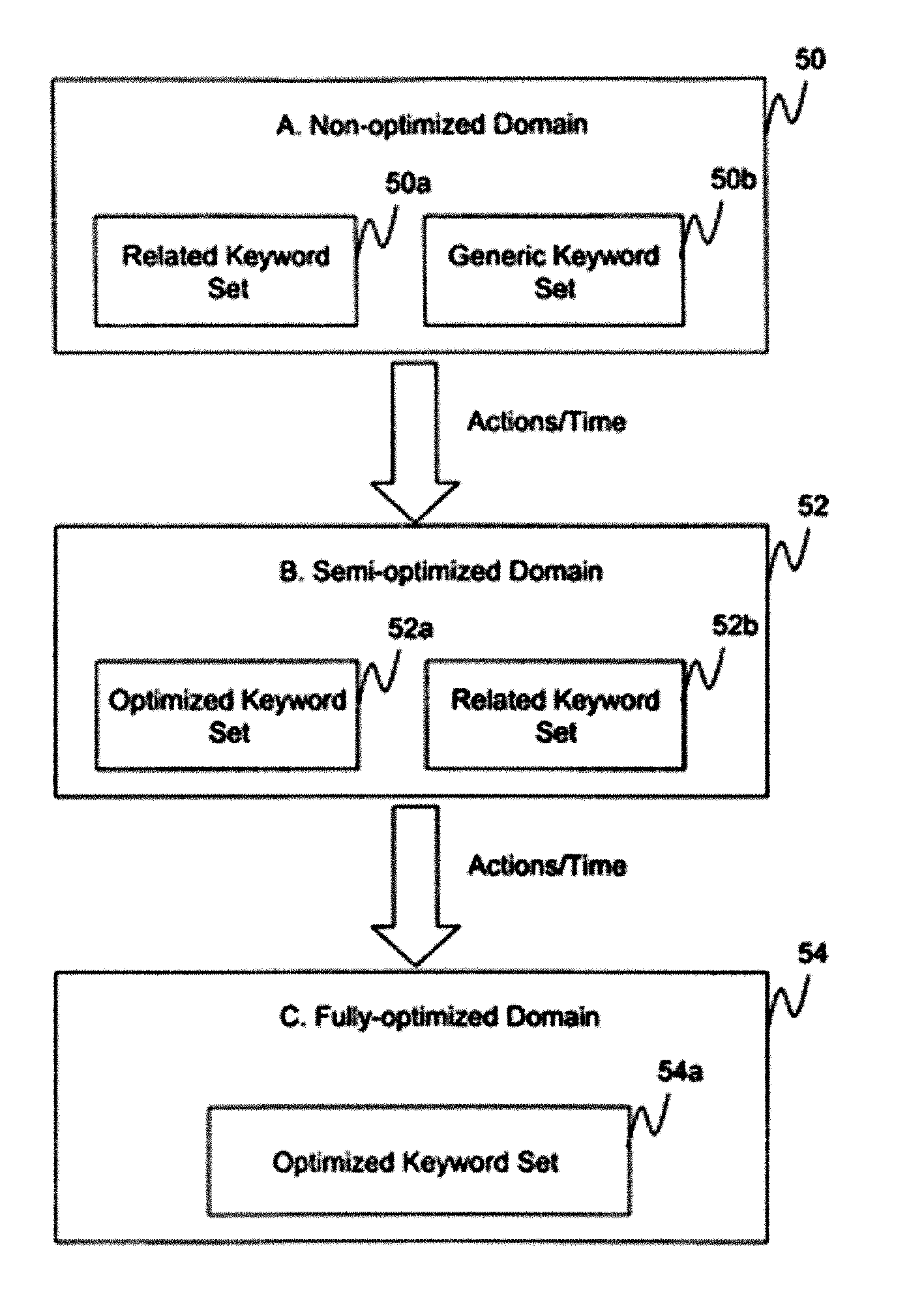
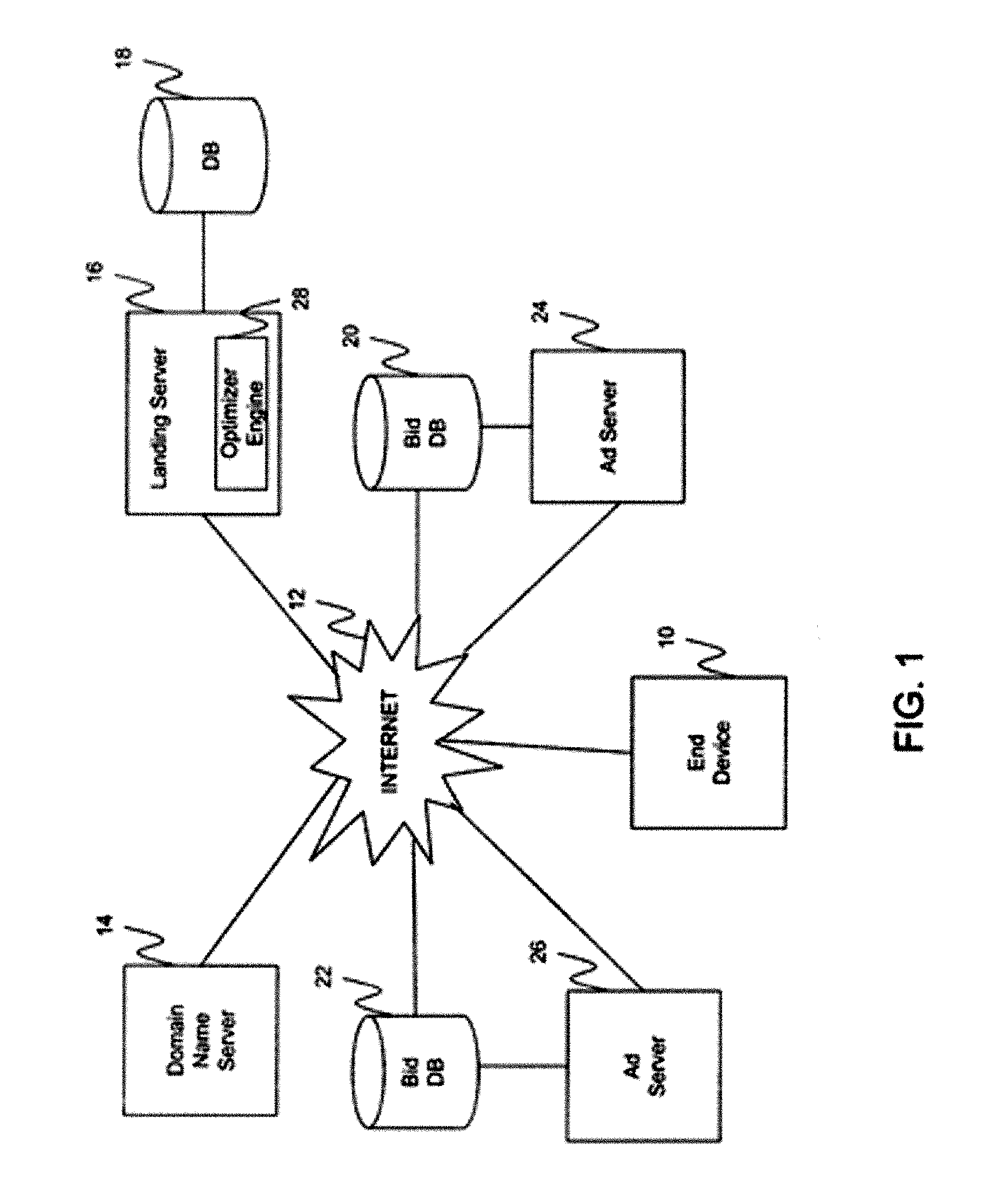
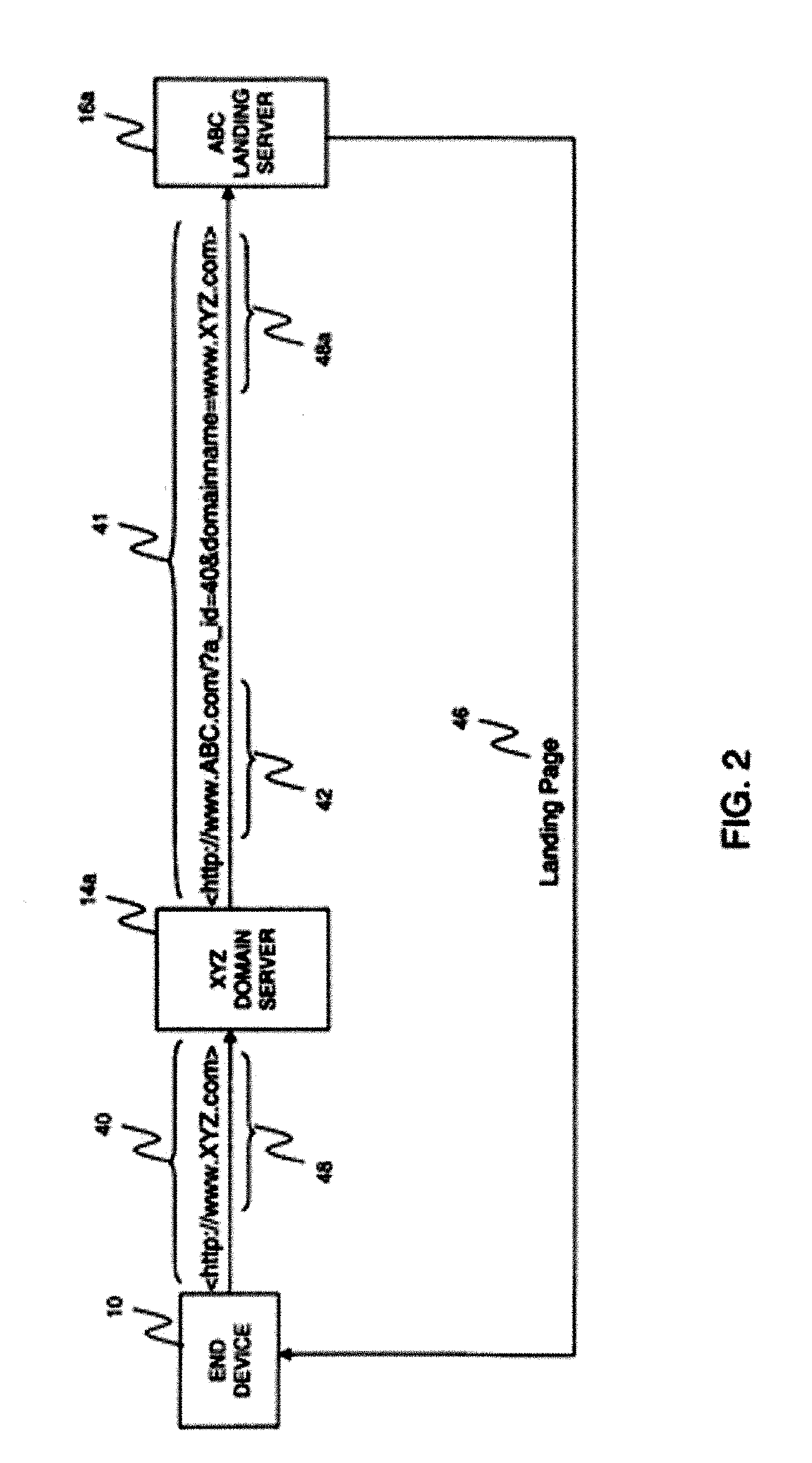
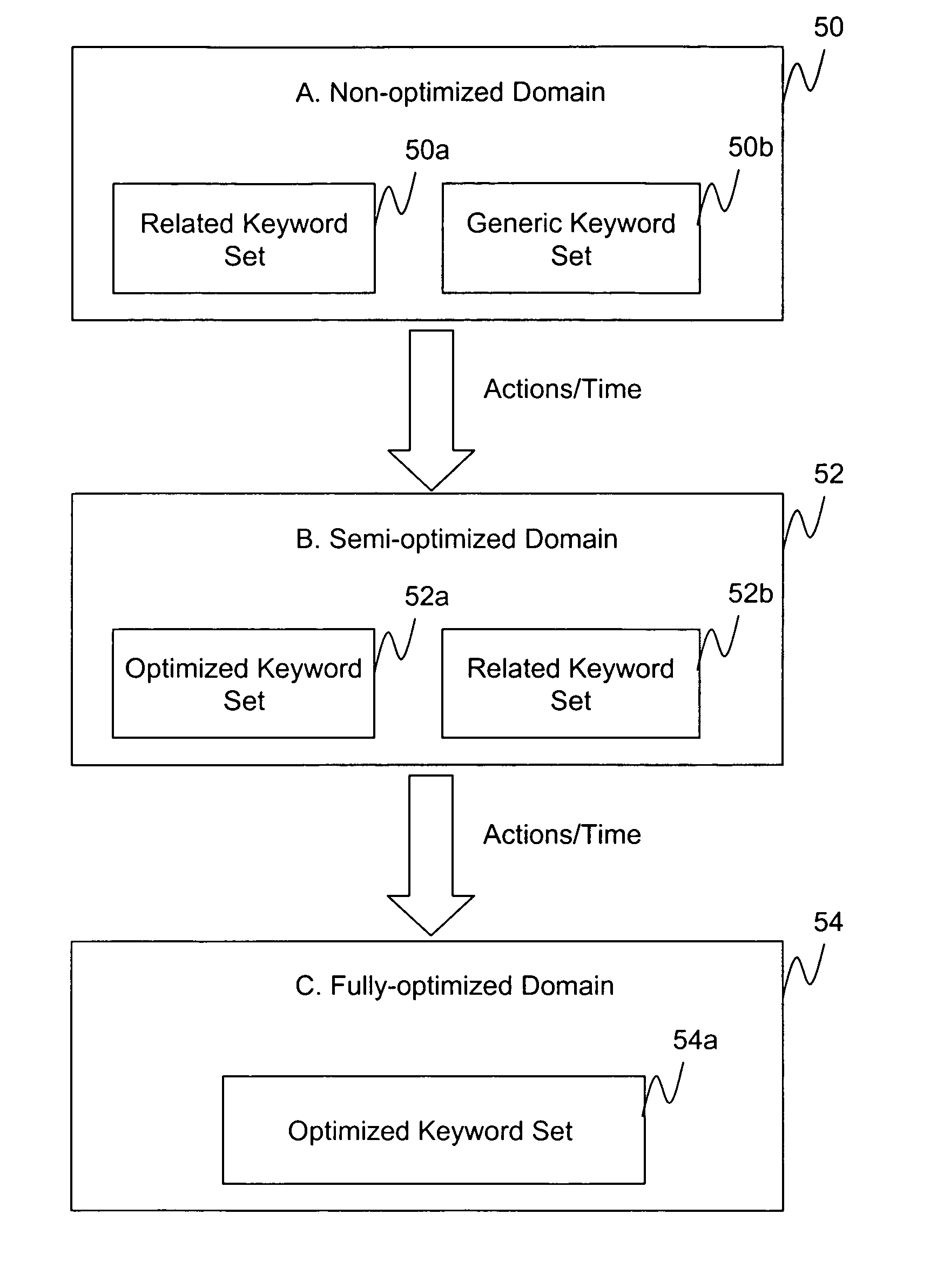
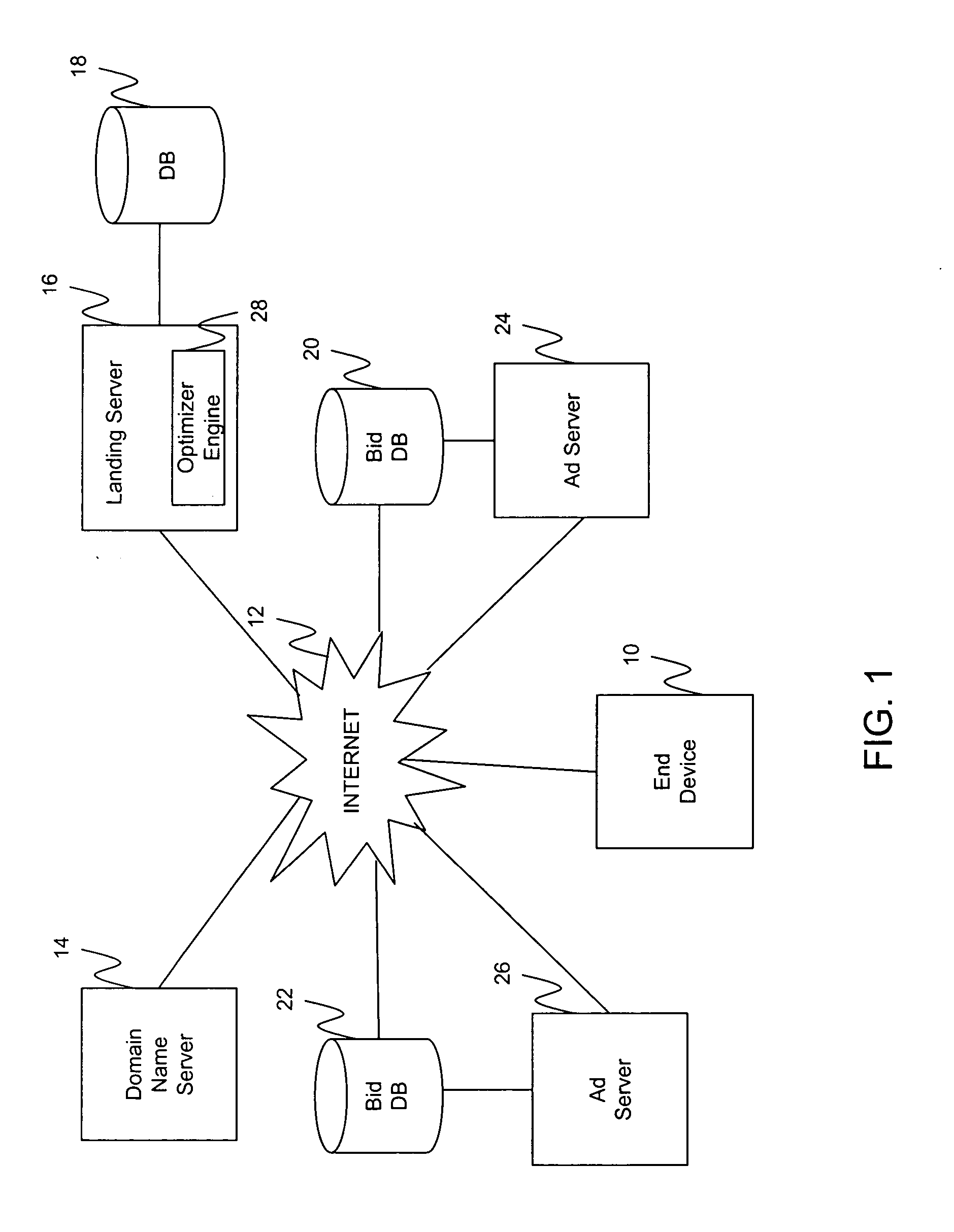
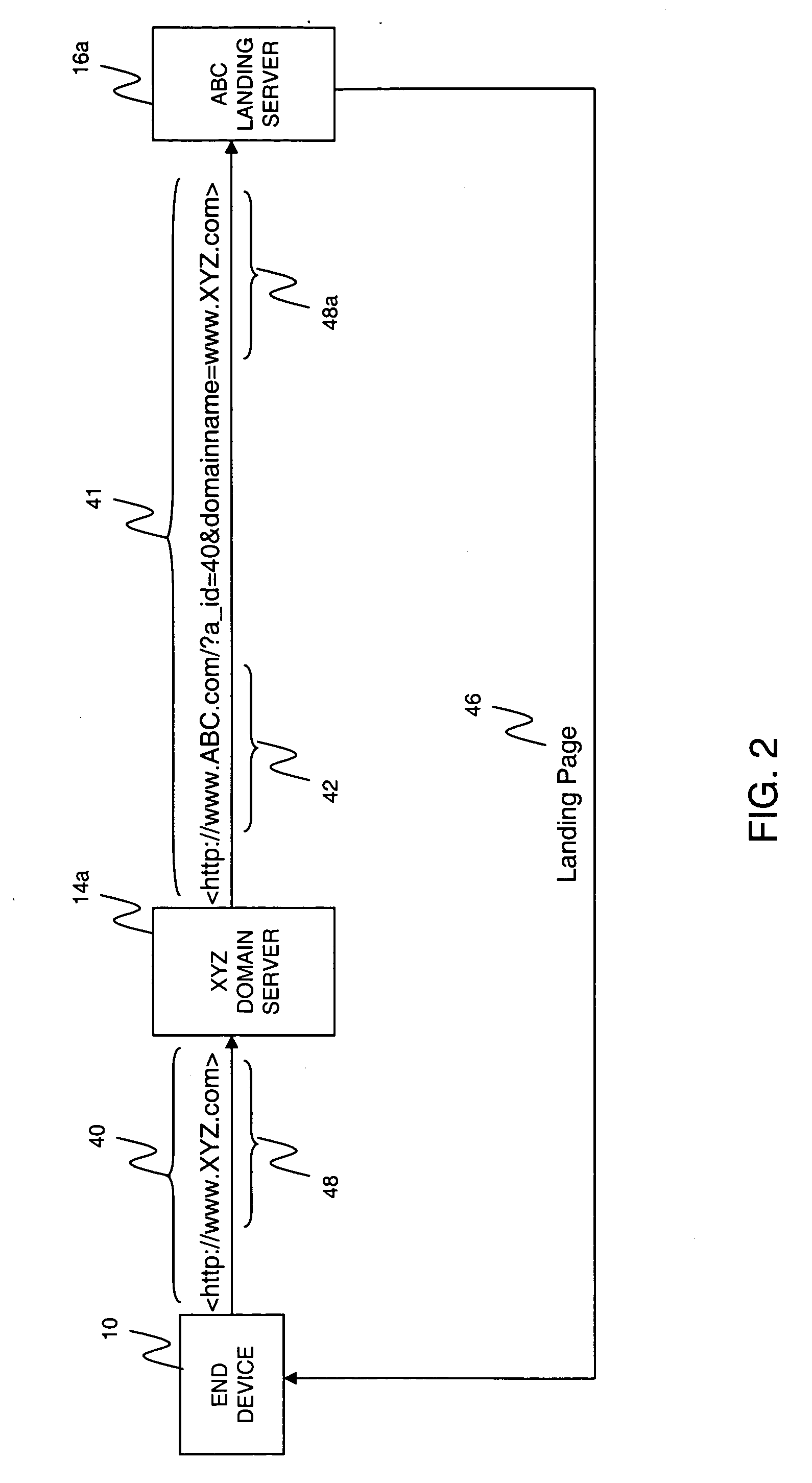
Internet Domain Keyword Optimization
ActiveUS20060069784A2Increase incomeWeb data indexingMultiple digital computer combinationsDomain nameData set
Abstract of the DisclosureA computerized system and method for optimizing contents of a domain landing page for increased revenues for the domain name owner. A landing server tracks user interactions with the domain landing page and generates an optimized keyword data set for the domain name. The keyword data set is used for selecting the information to be displayed on the domain name page. According to one embodiment, the keywords are associated with advertiser payment values. When a link to an advertiser bidding on a particular keyword is selected, revenue generated due to the click is shared with the domain name owner. Selection of links on pop-under pages displayed with a landing page are also shared with the domain name owner. Semantic analysis of keywords and domain names allows the generation of a related keyword data set when there is insufficient number of relevant user interactions for generating the optimized keyword data set.
Owner:SOL INVICTUS COMITI LP
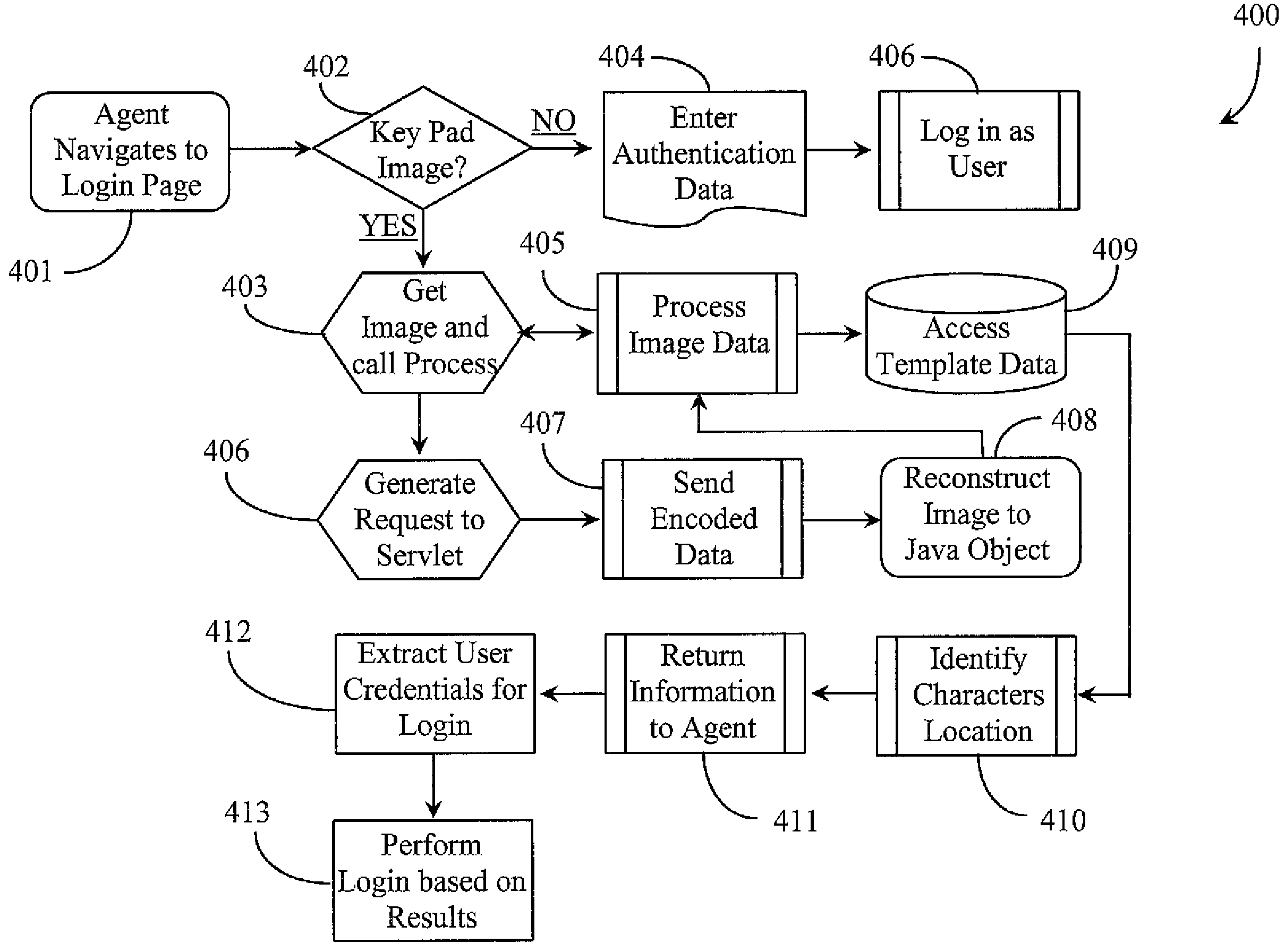
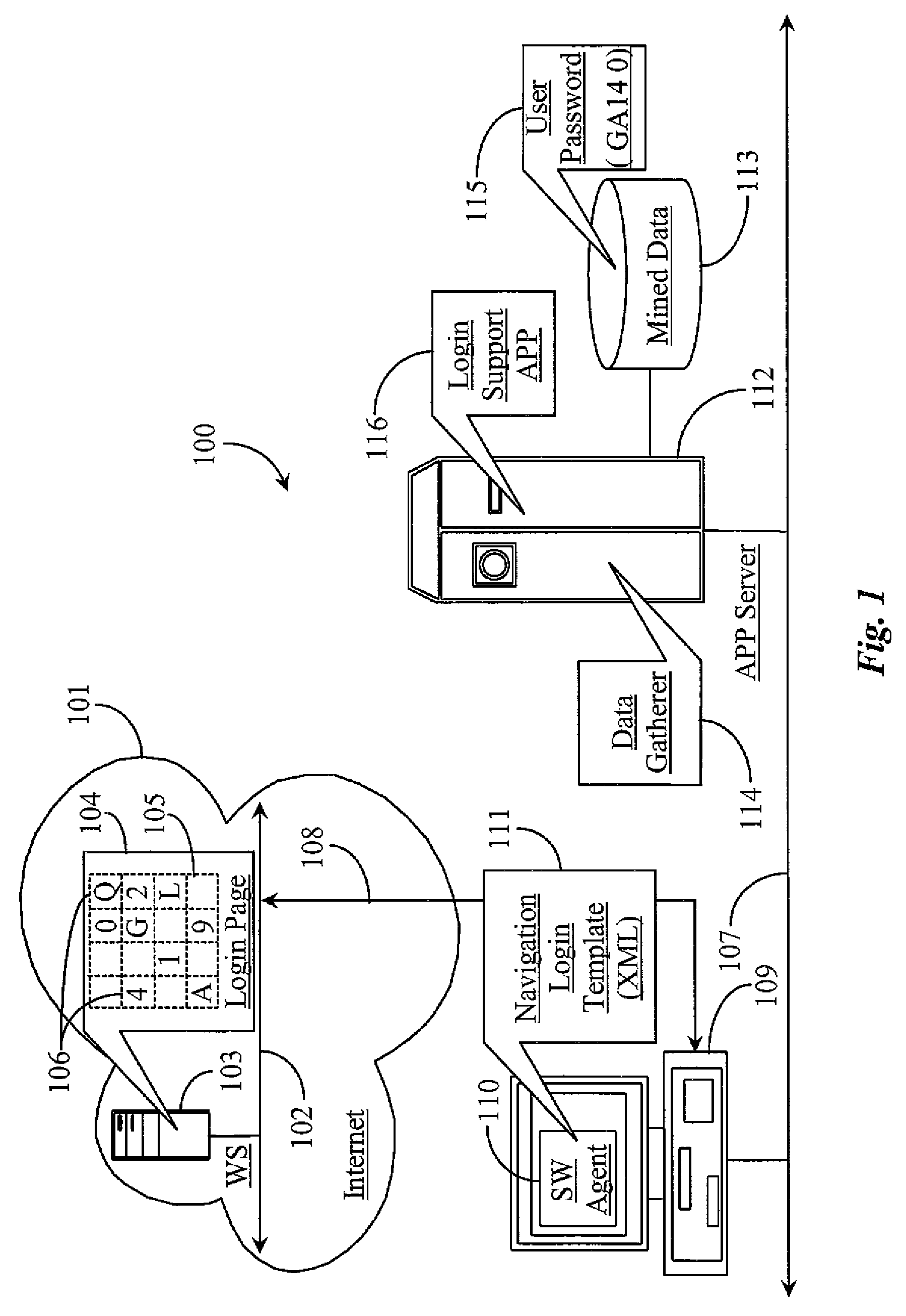
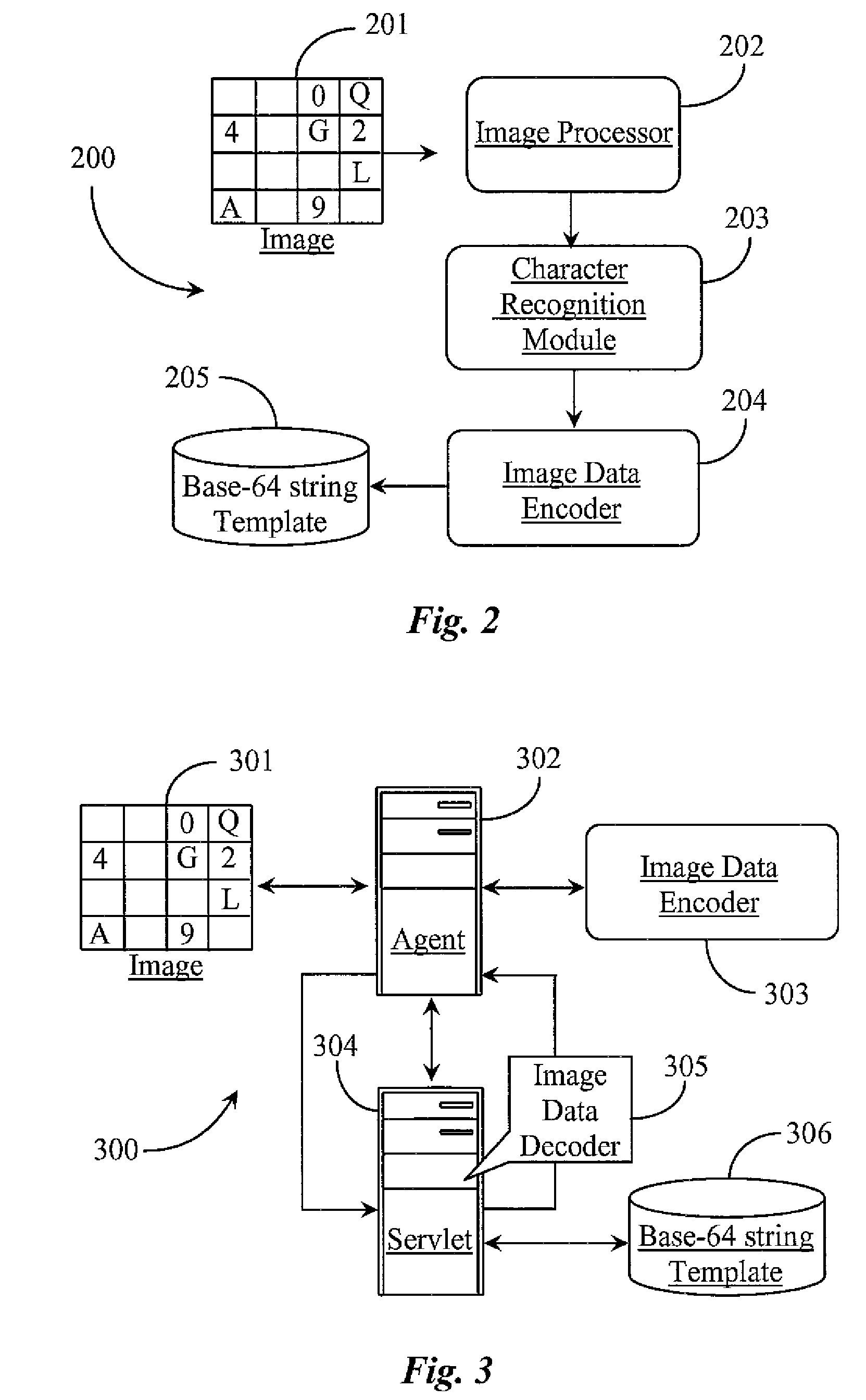
System and Methods for Automatically Accessing a Web Site on Behalf of a Client
ActiveUS20100215270A1Improve intelligenceWithout compromising site securityDigital data processing detailsUser identity/authority verificationWeb siteApplication software
A system for performing an automated network-based login procedure on an interactive keypad image includes a software agent executable from a digital medium connected to the network for navigating to a login page, accessing the keypad image, and performing an automated login, and an automated login support application executable from the same or a different digital medium connected to the network, the support application including at least an image processor, an optical character recognizer, and an image data encoder and decoder. The software agent performs a login at the virtual keypad image based on character image matching and location information acquisition for each character of a client's specific set of credential characters included in the image of the keypad.
Owner:YODLEE COM INC
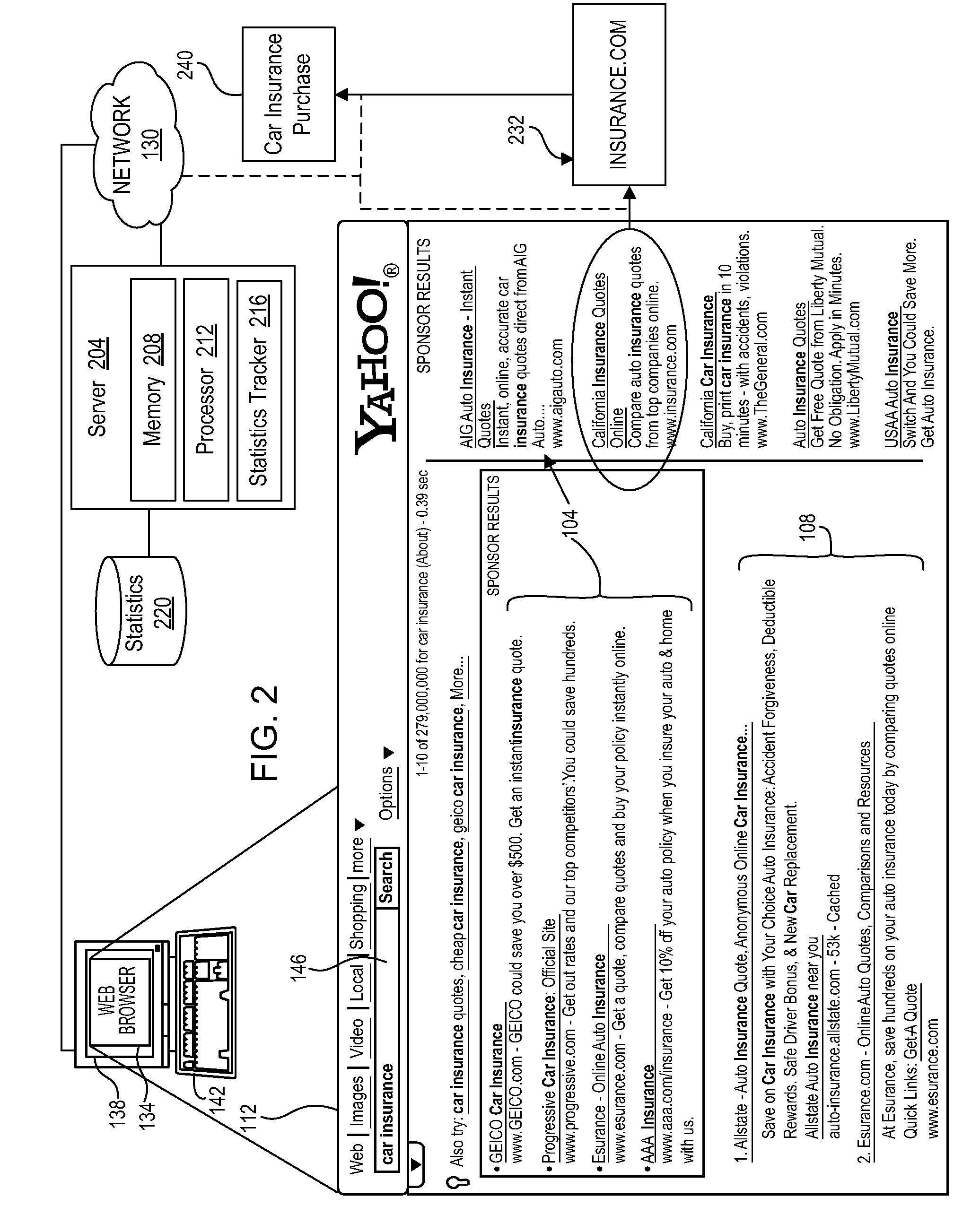
Context transfer in search advertising
A computer-implemented method is disclosed for determining a type of landing page to which to transfer web searchers that enter a particular query, the method comprising: classifying a landing page as one of a plurality of landing page classes with a trained classifier of a computer based on textual content of the landing page; determining, by the computer, characteristics of one or more query to be associated with the landing page; and choosing, with the computer, whether to retain or to change classification of the landing page to be associated with the one or more query based on relative average conversion rates of advertisements on a plurality of manually-classified landing pages when associated with the characteristics of the one or more query.
Owner:R2 SOLUTIONS
Feeding updates to landing pages of users of an online social network from external sources
ActiveUS8037093B2More contentEfficiency of muchData processing applicationsDigital data processing detailsSocial webLanding page
Updates to landing pages of users in an online social network are fed from external sources so that content maintained by any one user can be consolidated in a single location regardless of where the changes are made to the content. When an update event occurs, users of the online social network are notified according to various criteria that they have set. With this feature, users can browse through content of other users efficiently.
Owner:META PLATFORMS INC
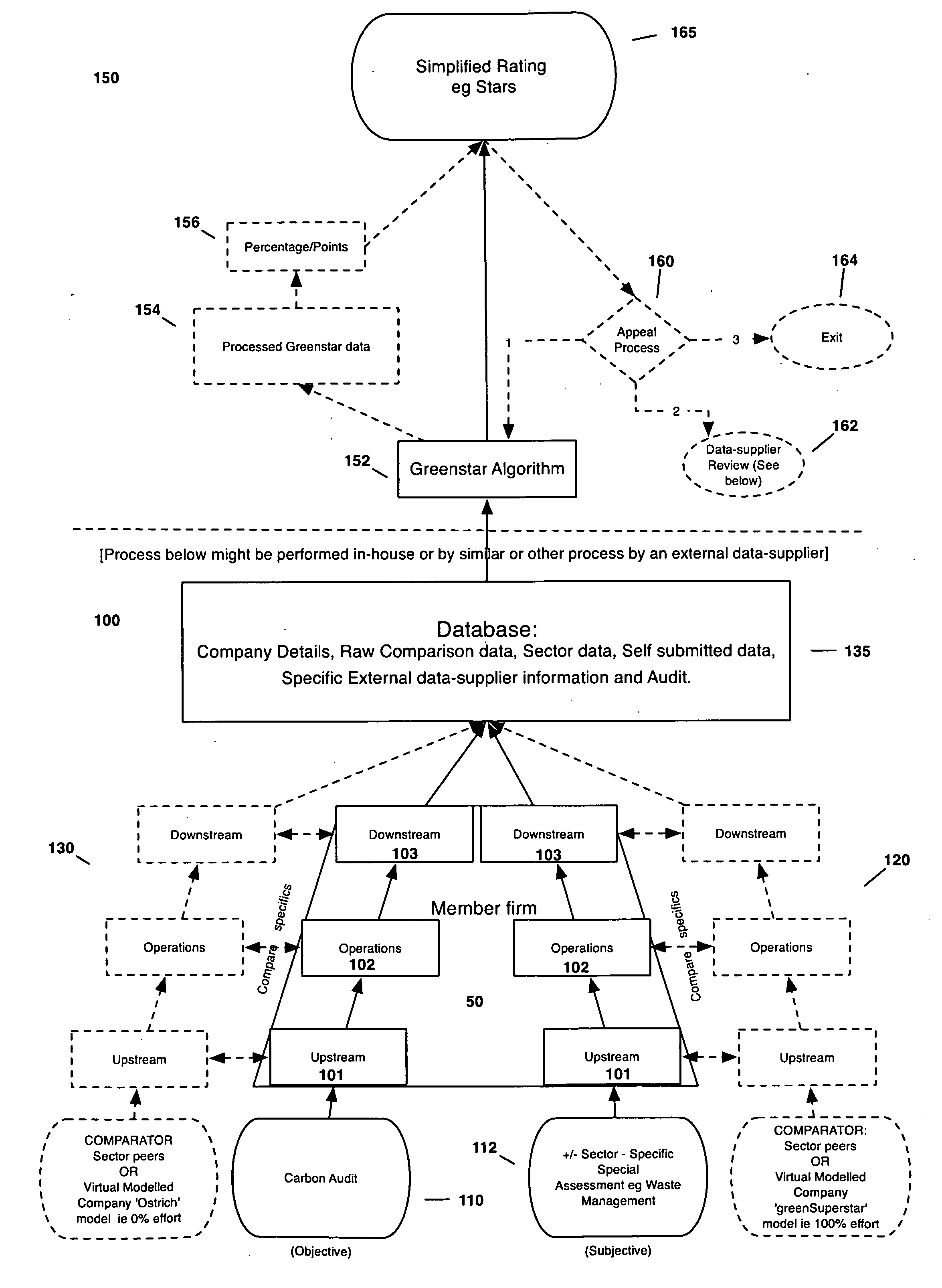
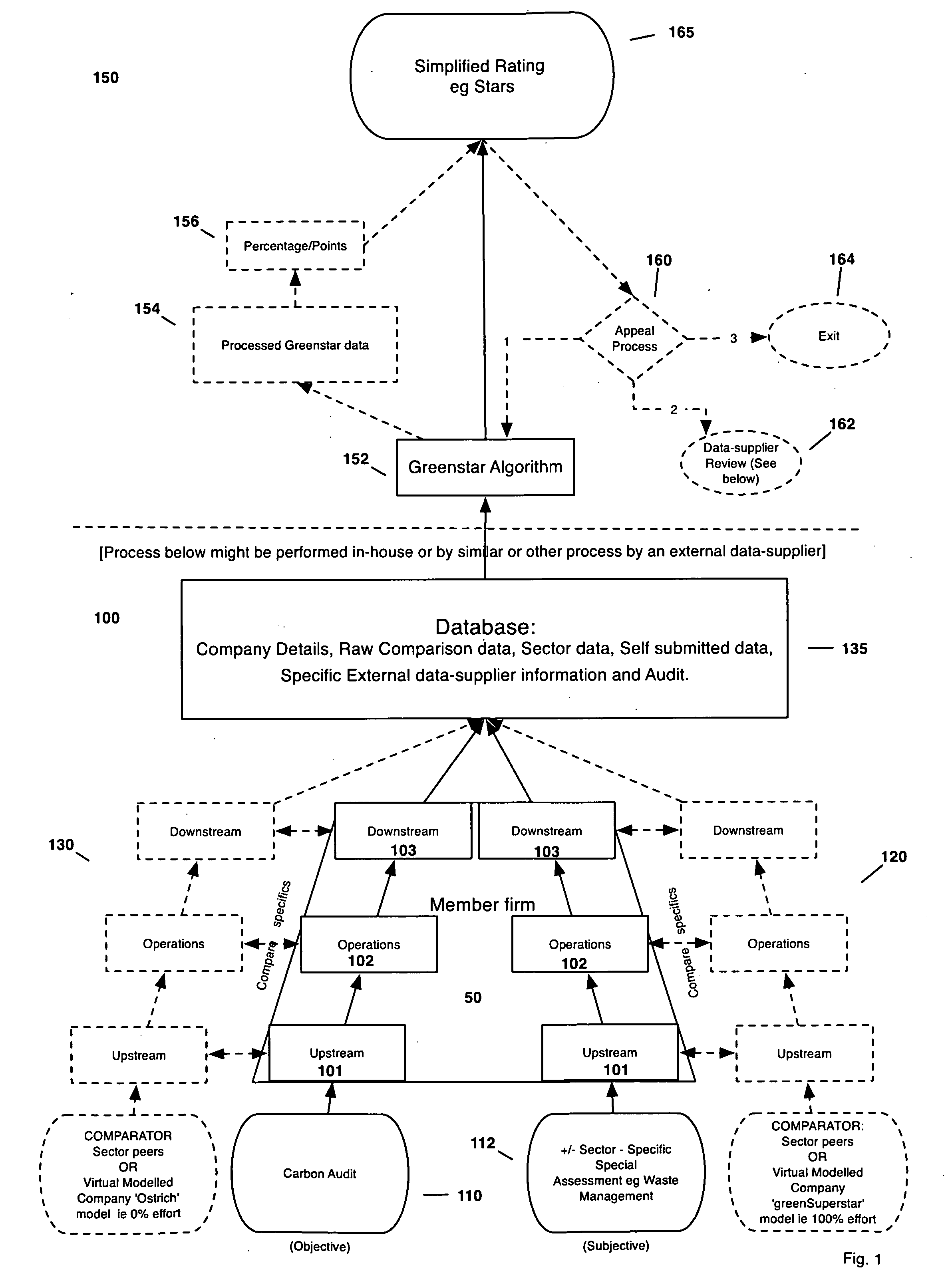
Green Rating System and Associated Marketing Methods
InactiveUS20090171722A1Entry barrier higherImprove performanceTechnology managementMarketingRating systemMicroblogging
A method and system for assigning a rating to an entity based on a plurality of metrics, for example, assigning a rating to an entity which reflects that entity's level of environmental performance, and then assigning an indicia to the entity which reflects the rating relative to other like entities. The system includes ways to generate revenue based on the entity's use of the indicia, such as integrating the display of the indicia with search engines such that the indicia is displayed when the entity's link appears on a search results list and charging a per impression and / or a per click through microfee. The invention also comprises a filtered search facility which only features rated member entities on its search results list. A website is also provided which contains landing pages for each rated entity which may be accessed by clicking on the displayed indicia in the search results list.
Owner:ROBERTS CHARLES E S
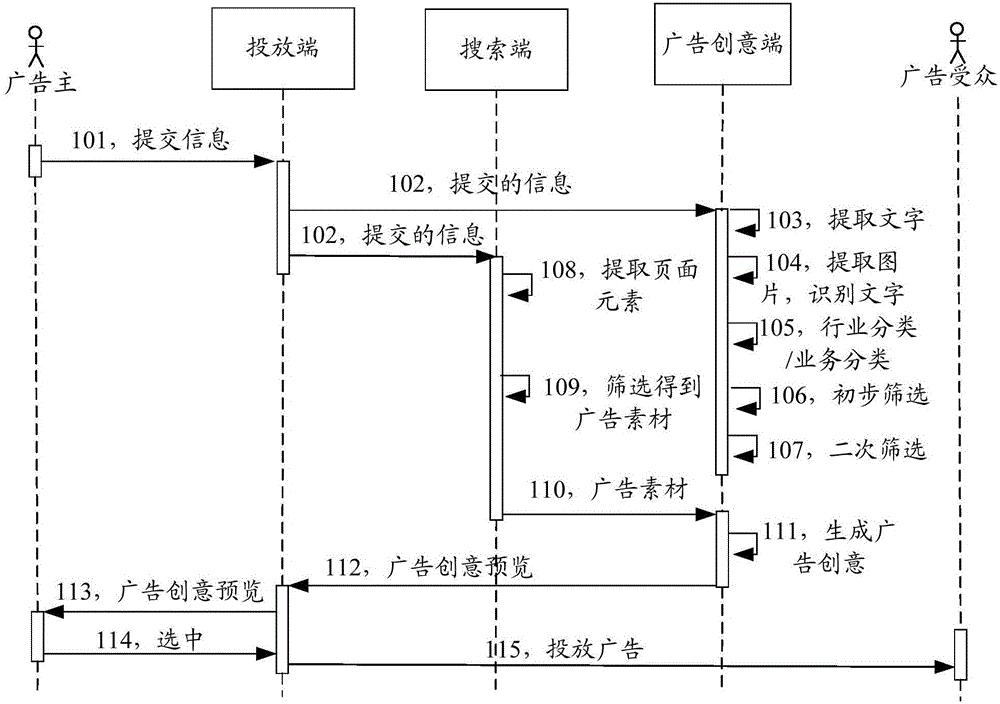
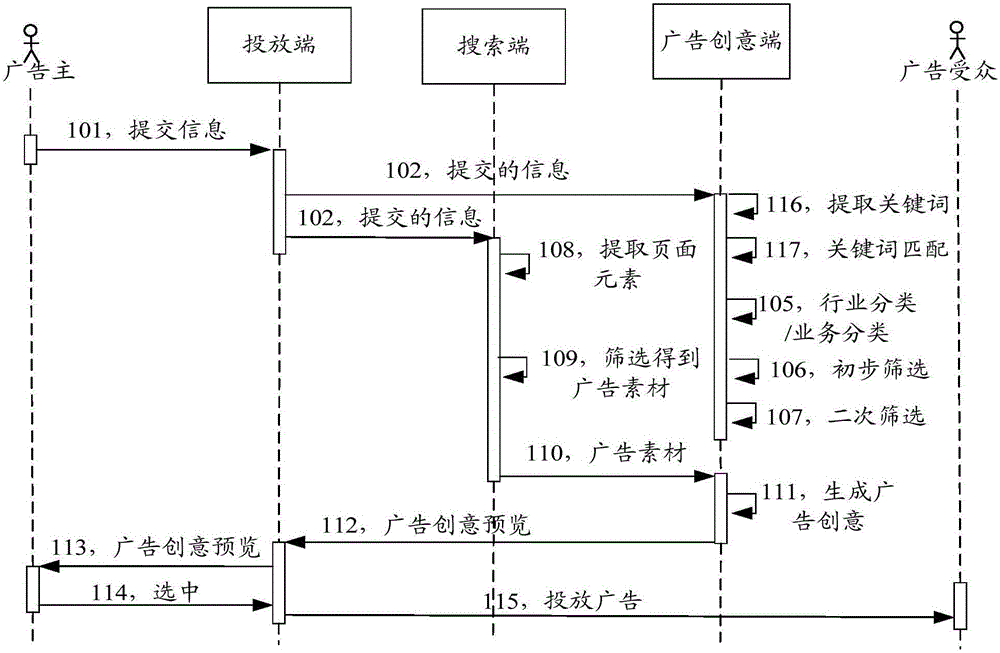
Advertisement creativity processing method and advertisement creativity processing apparatus
ActiveCN106096995AImprove production efficiencyAvoid problems with modifying ad creativeAdvertisementsPersonalizationTemplate match
The invention discloses an advertisement creativity processing method and an advertisement creativity processing apparatus. The method comprises the steps of obtaining advertisement creativity specifications, an advertisement landing page address and advertiser industry information; screening out advertisement creativity templates matched with the advertiser industry information from advertisement creativities meeting the advertisement creativity specifications; performing priority sorting on the screened-out advertisement creativity templates, and screening out advertisement creativity templates meeting priority conditions; extracting page elements from an advertisement landing page, and screening the extracted page elements to obtain advertisement materials; filling the advertisement creativity templates meeting the priority conditions with the advertisement materials to obtain the advertisement creativities; and returning the advertisement creativities to an advertiser based on priority sorting of corresponding advertisement creativity templates. By implementing the method and the apparatus, the advertiser can be supported to quickly obtain the advertisement creativities meeting the specifications and personalized demands to perform advertisement release as soon as possible, so that the utilization rate of advertisement positions of an advertisement system is increased.
Owner:TENCENT TECH (SHENZHEN) CO LTD
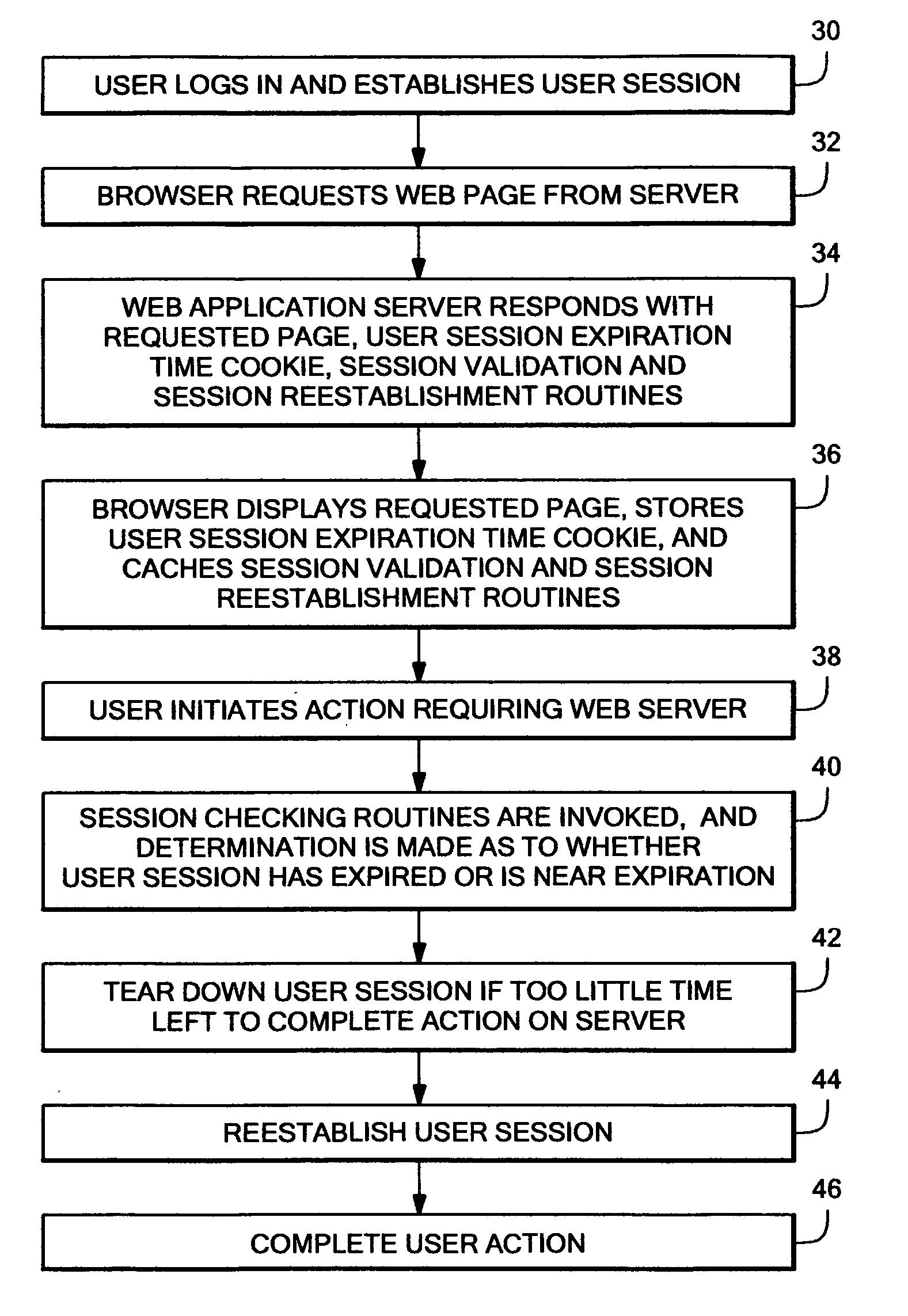
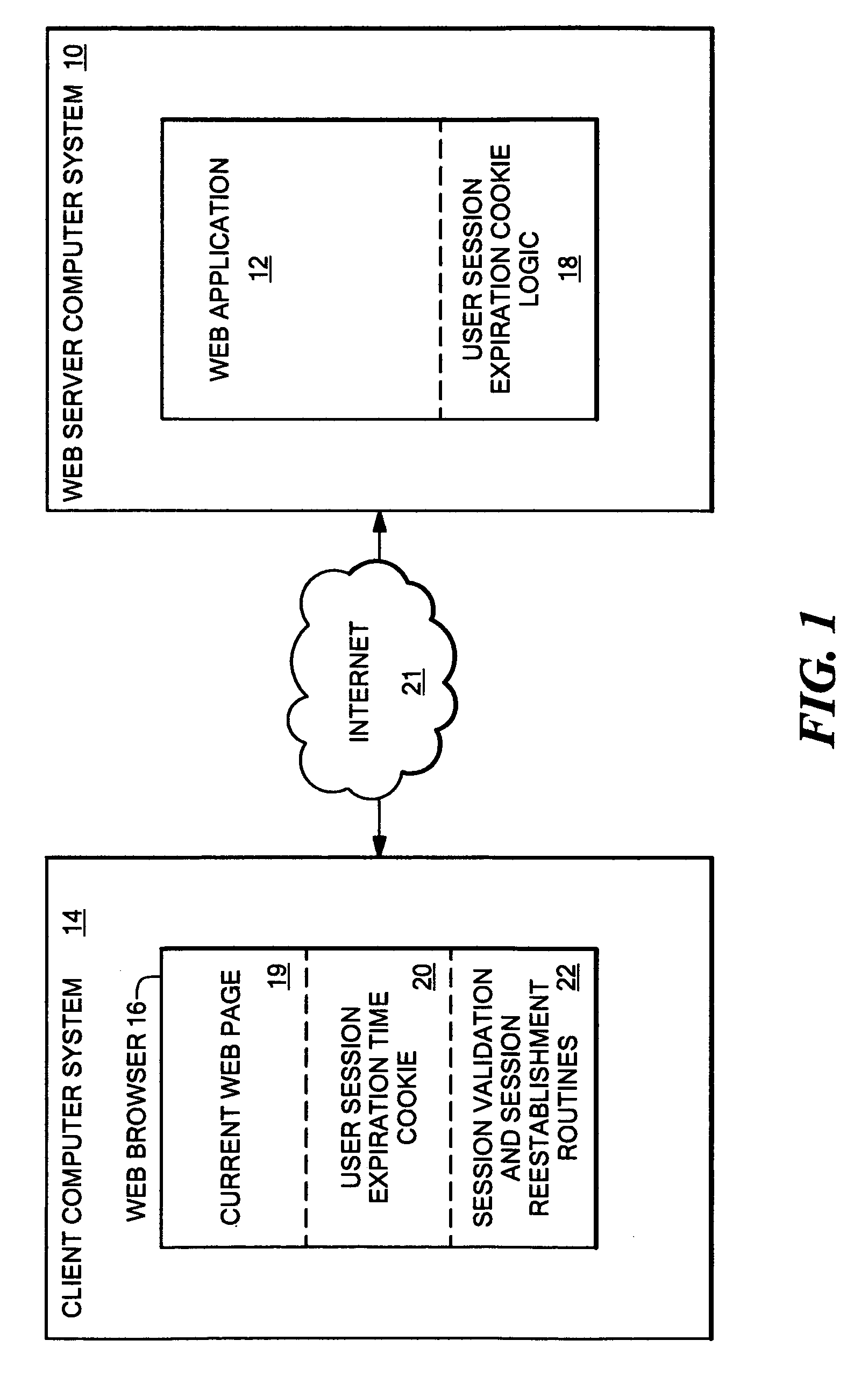
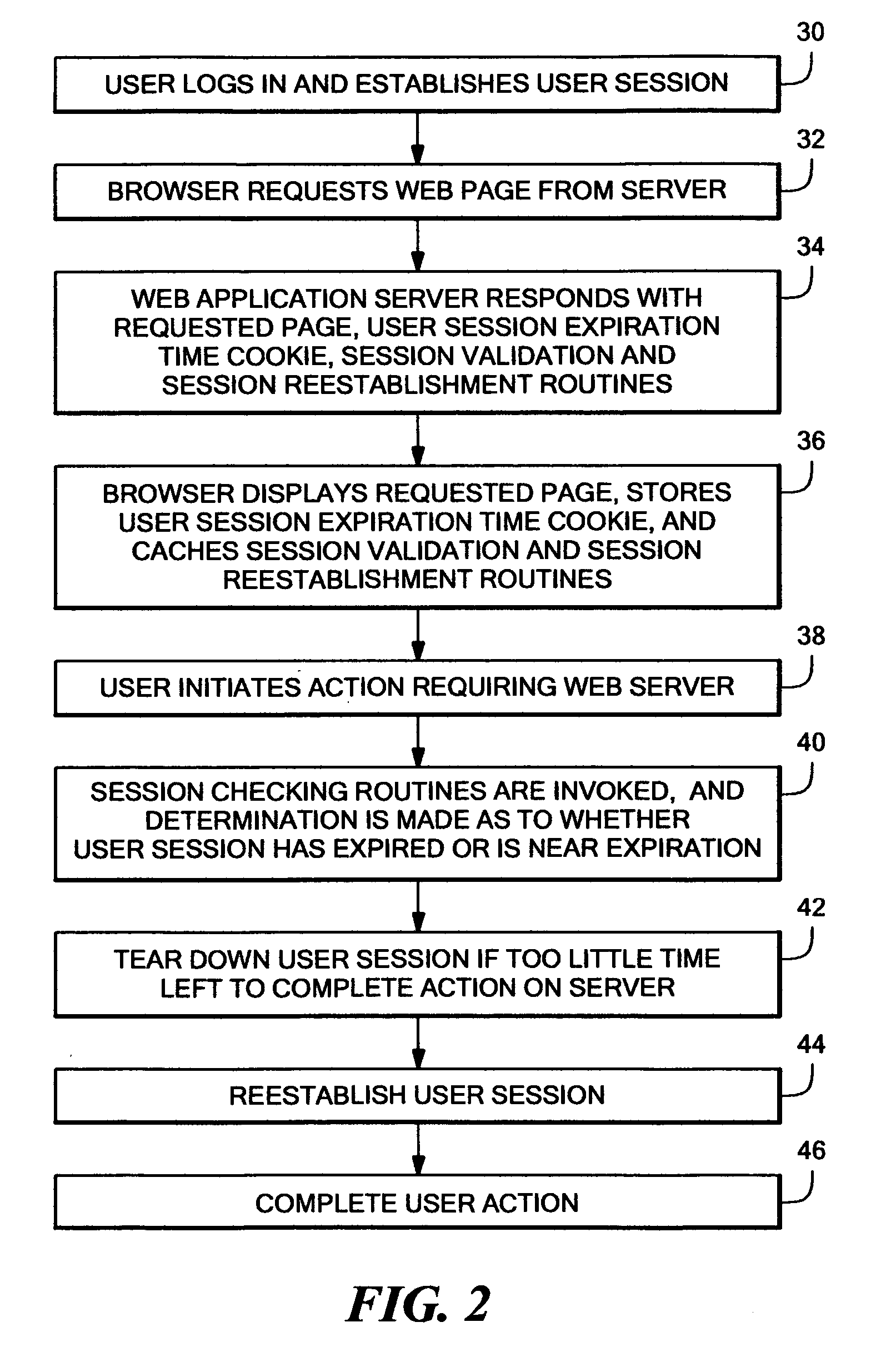
System and method for gracefully reestablishing an expired browser session
InactiveUS20060075110A1Easy to compareDigital data processing detailsMultiple digital computer combinationsExpiration TimeWindow detection
A new system for gracefully re-establishing an expired user session in which a separate session expiration time cookie is provided to communicate the session expiration time from the Web server to the browser. The Web server further provides the browser with session validation and re-establishment routines that include logic for checking whether a current user session has expired, or is near expiration. These routines are cached by the browser. When a browser user performs an action requiring server action, a determination is made as to whether the current user session has expired, or is near expiration. If either of these cases are true, the user action just invoked is stored, and a separate browser window is opened. A protected page is loaded which closes the browser window. In order to display the protected page, the user first encounters the login page and enters the proper credentials to log-in to the server. As part of displaying the protected page, the server updates the user session expiration time cookie to the new session expiration time. At this point, the original window detects the new session expiration time and at this time the prior invoked action can be re-attempted. Since the session is not expired, or at risk of immediate expiration, the action can be completed properly.
Owner:IBM CORP
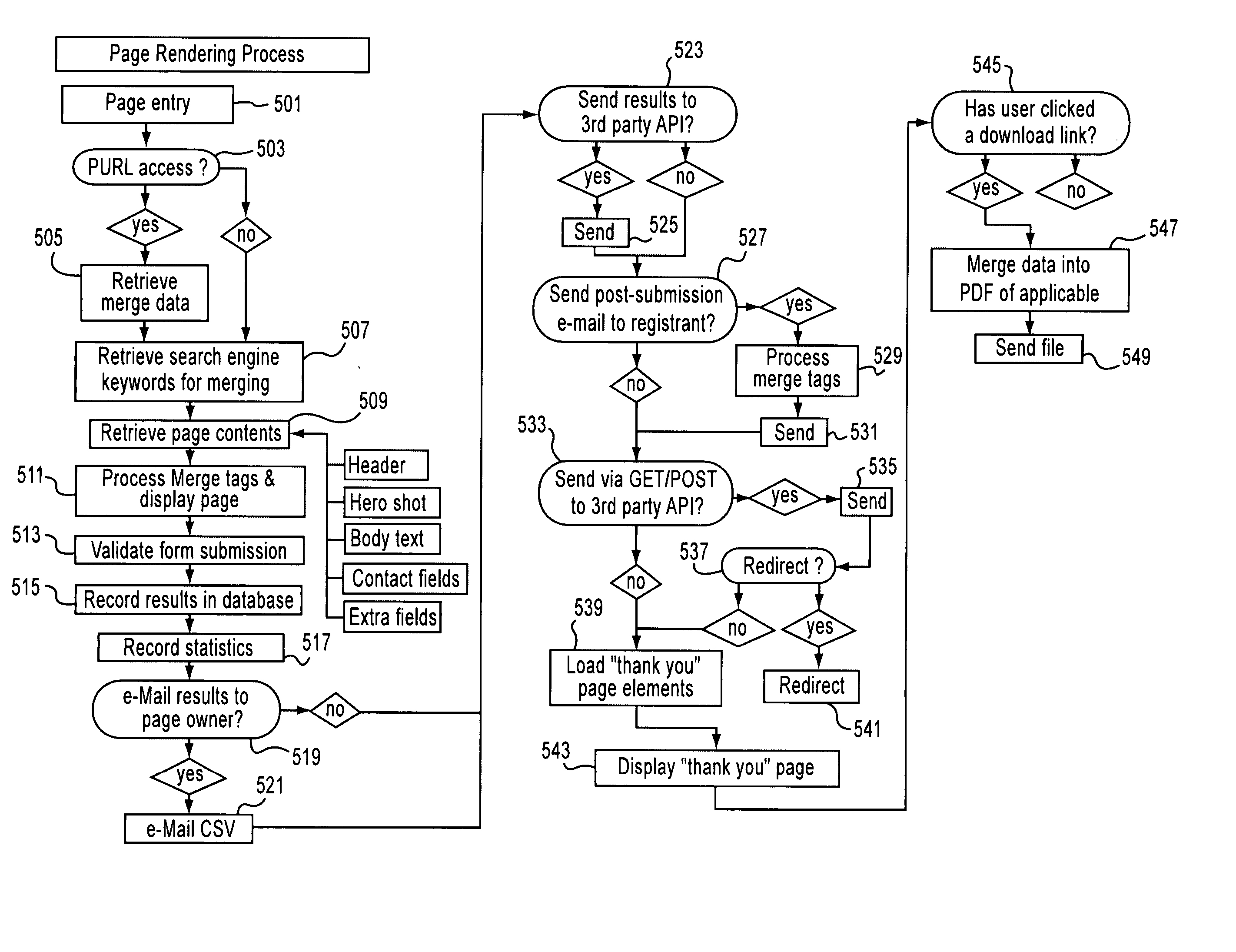
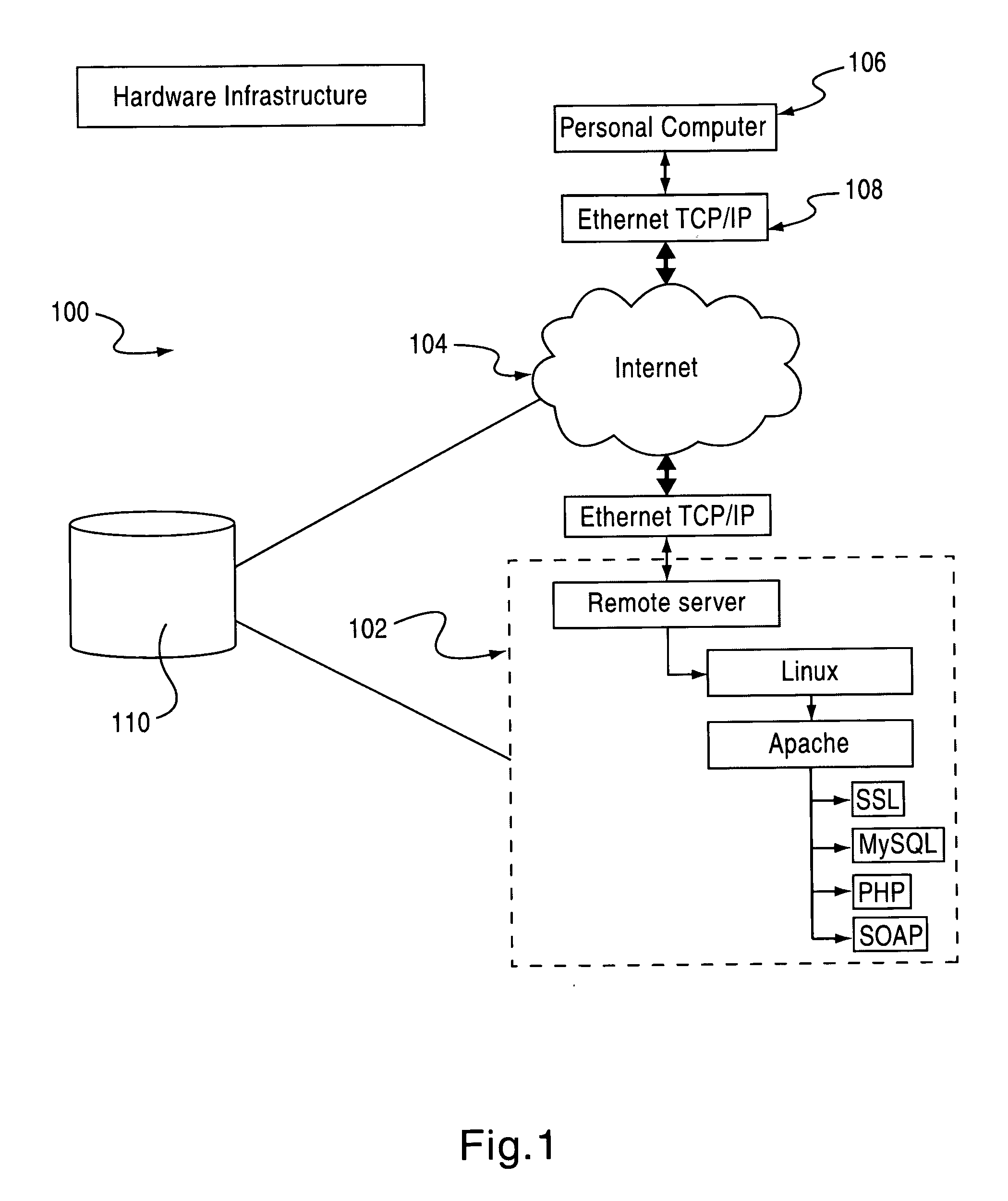
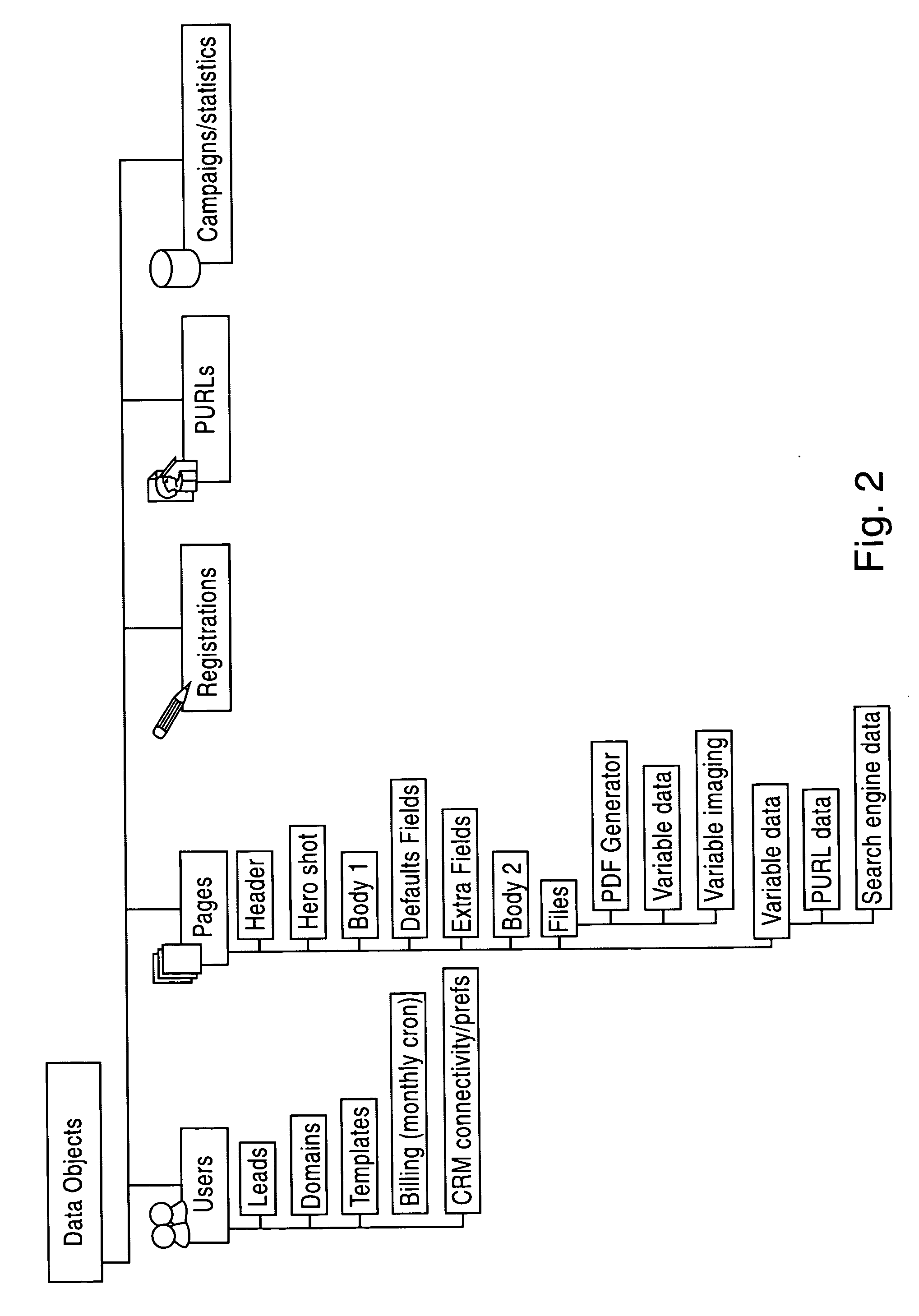
System and method for generating, maintaining, and rendering landing and web pages
InactiveUS20070136255A1Overcome disadvantagesEasy to createWebsite content managementSpecial data processing applicationsComputer graphics (images)Template based
A system and method are provided for generating, maintaining and rendering landing pages. The system may include a user interface configured to allow input of an identification of a plurality of fields and rendering criteria. A template defines a look and feel of a web page. A landing page generating facility is configured to receive an identification of a plurality of fields and rendering criteria from the user interface and to generate a landing page based on the template and the rendering criteria. The landing page includes the plurality of fields.
Owner:INEO MARKETING
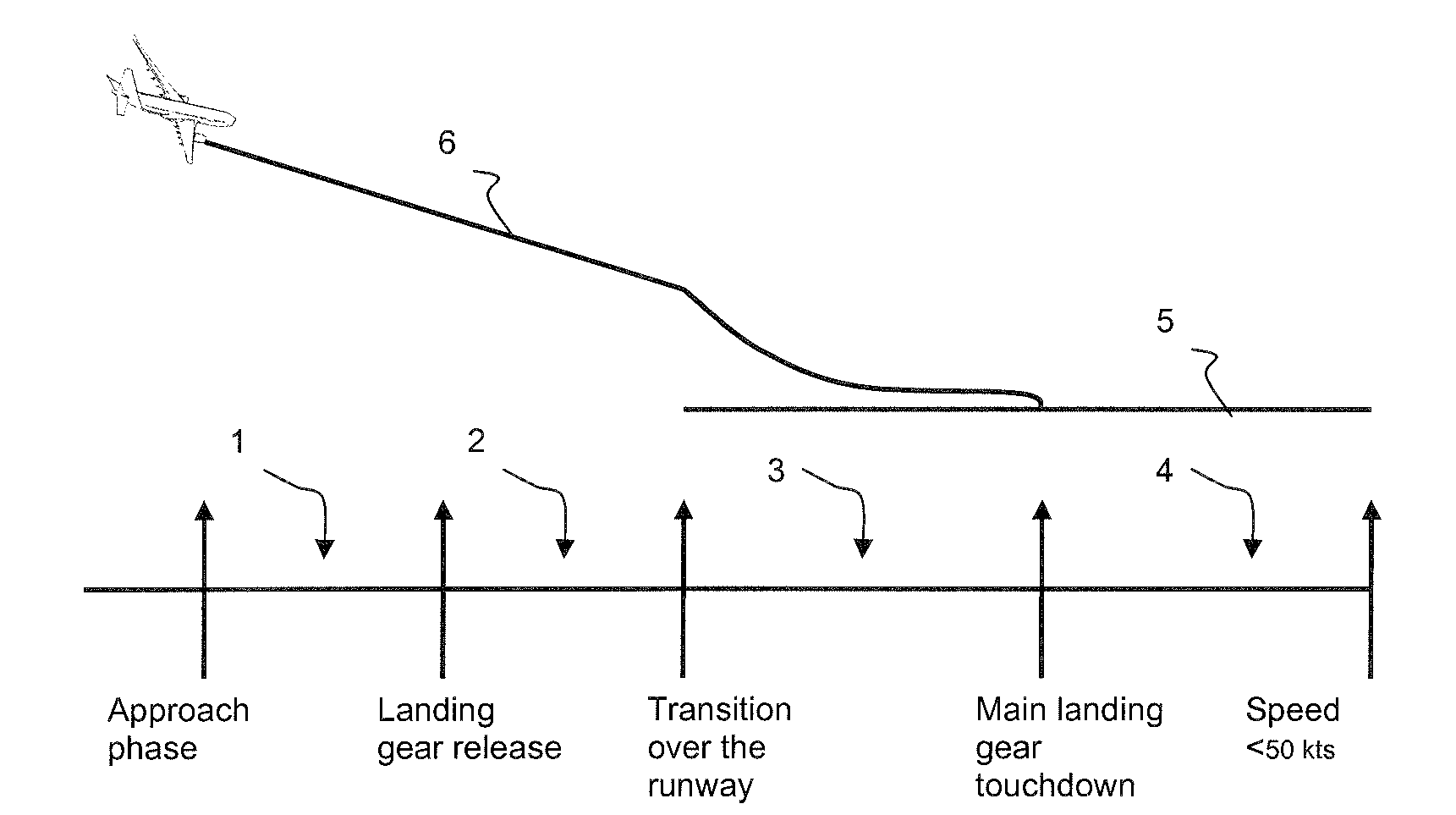
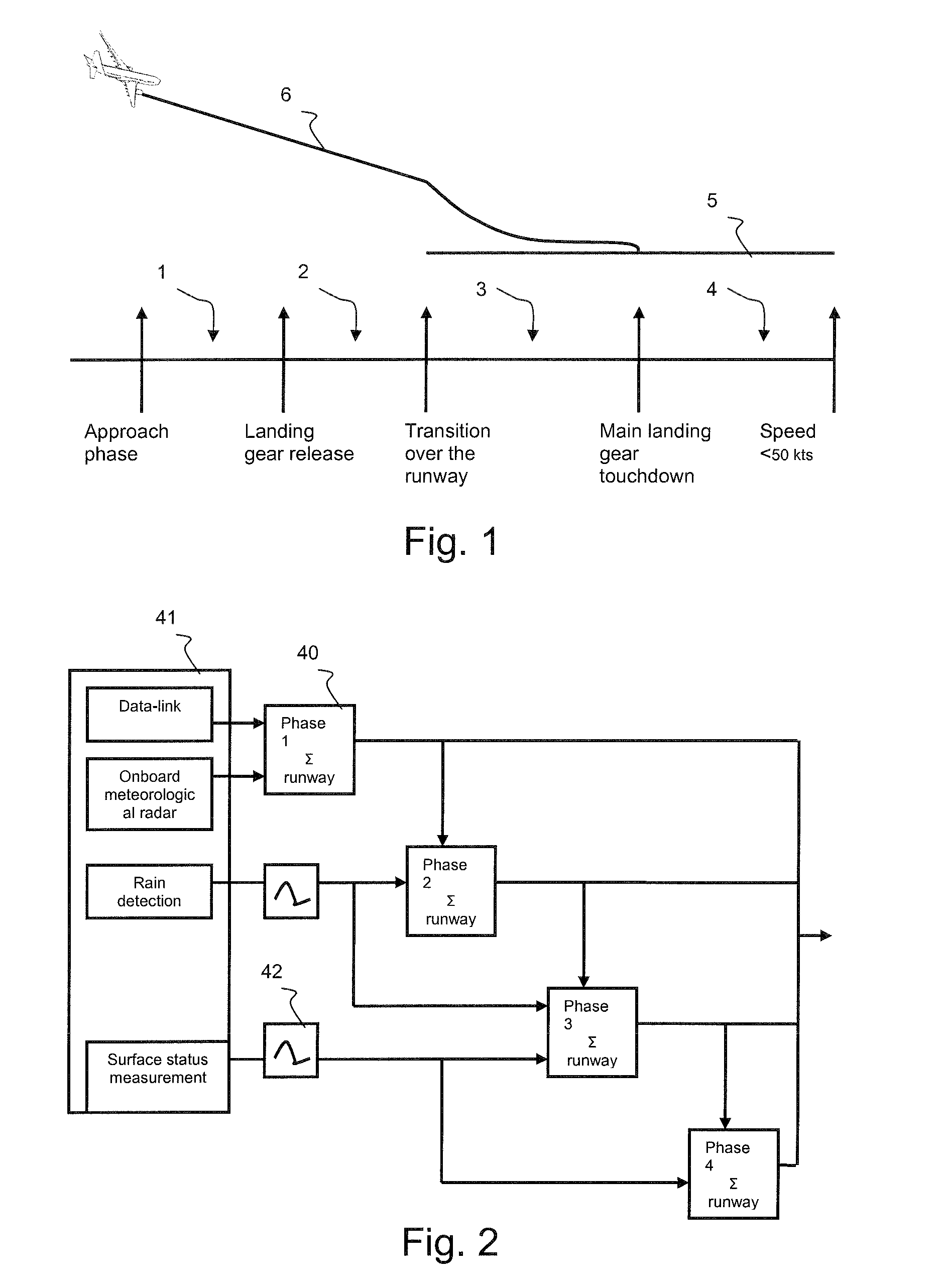
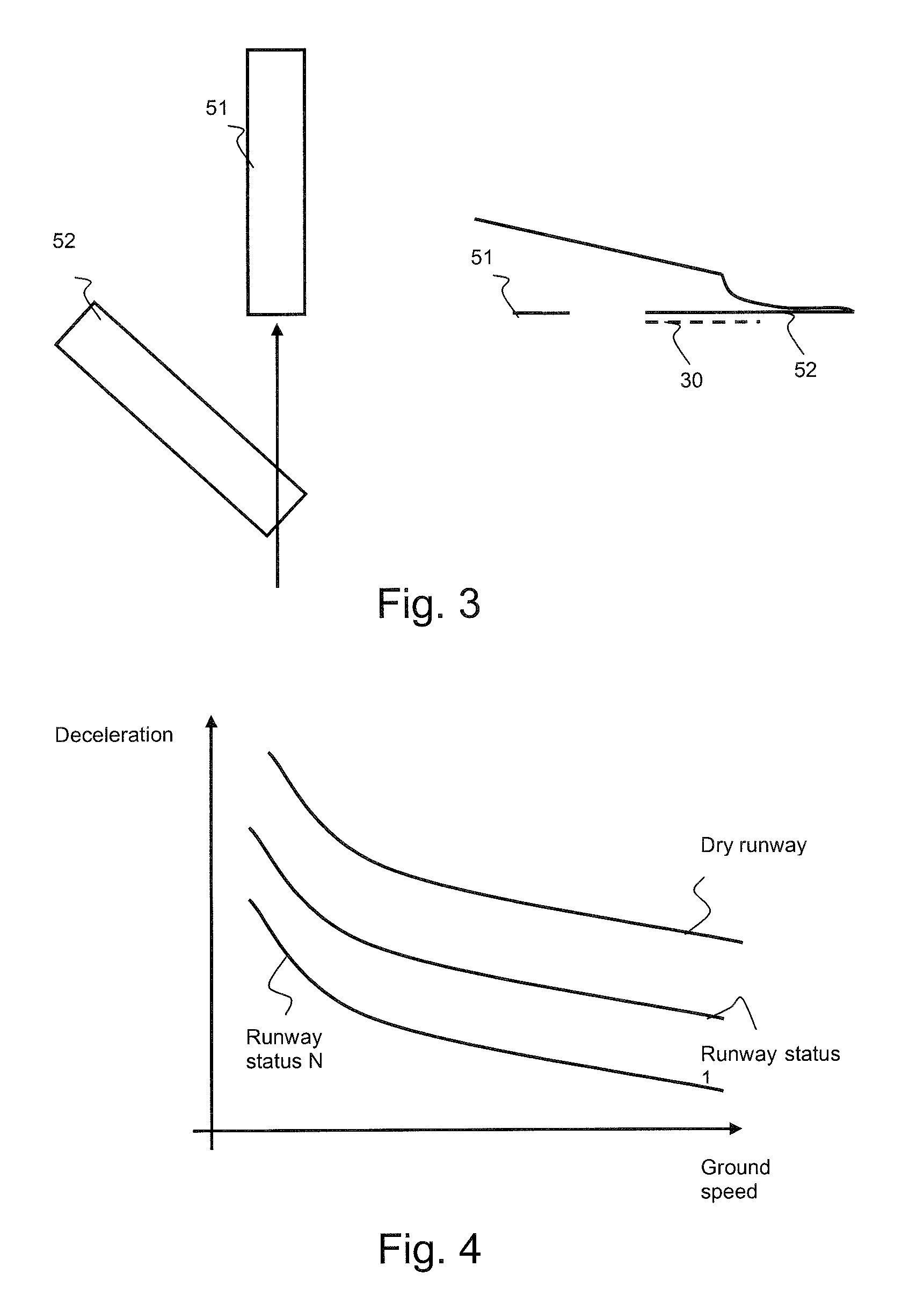
Method of Monitoring the Landing Phase of an Aircraft
ActiveUS20100079308A1Improve securityAnalogue computers for vehiclesLanding aidsFlight vehicleVisual perception
The invention relates to the field of monitoring the landing phase of an aircraft.The invention is a method making it possible to calculate and monitor the provisional landing distance and the configuration of the aircraft and flight parameters during the changes in the landing phase manoeuvre. The method consists in determining the landing runway then in analyzing the configuration and the dynamic parameters of the aeroplane, the meteorological and airport data in order to assess, from a performance database, whether the planned braking is suitable and will stop the aeroplane before the end of the runway.The result of the analysis gives rise, if the situation demands it, to appropriate visual and oral alarms.
Owner:THALES SA
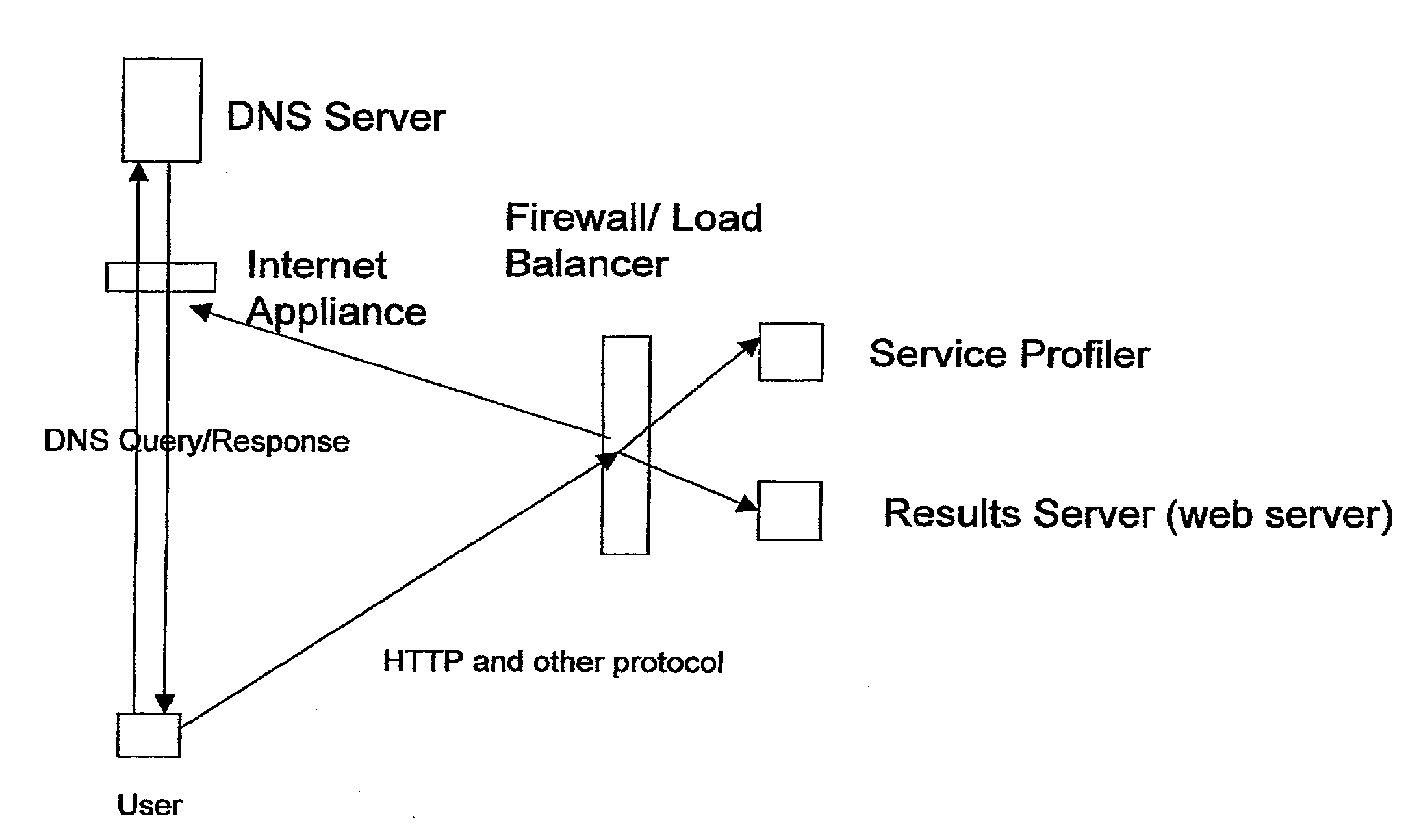
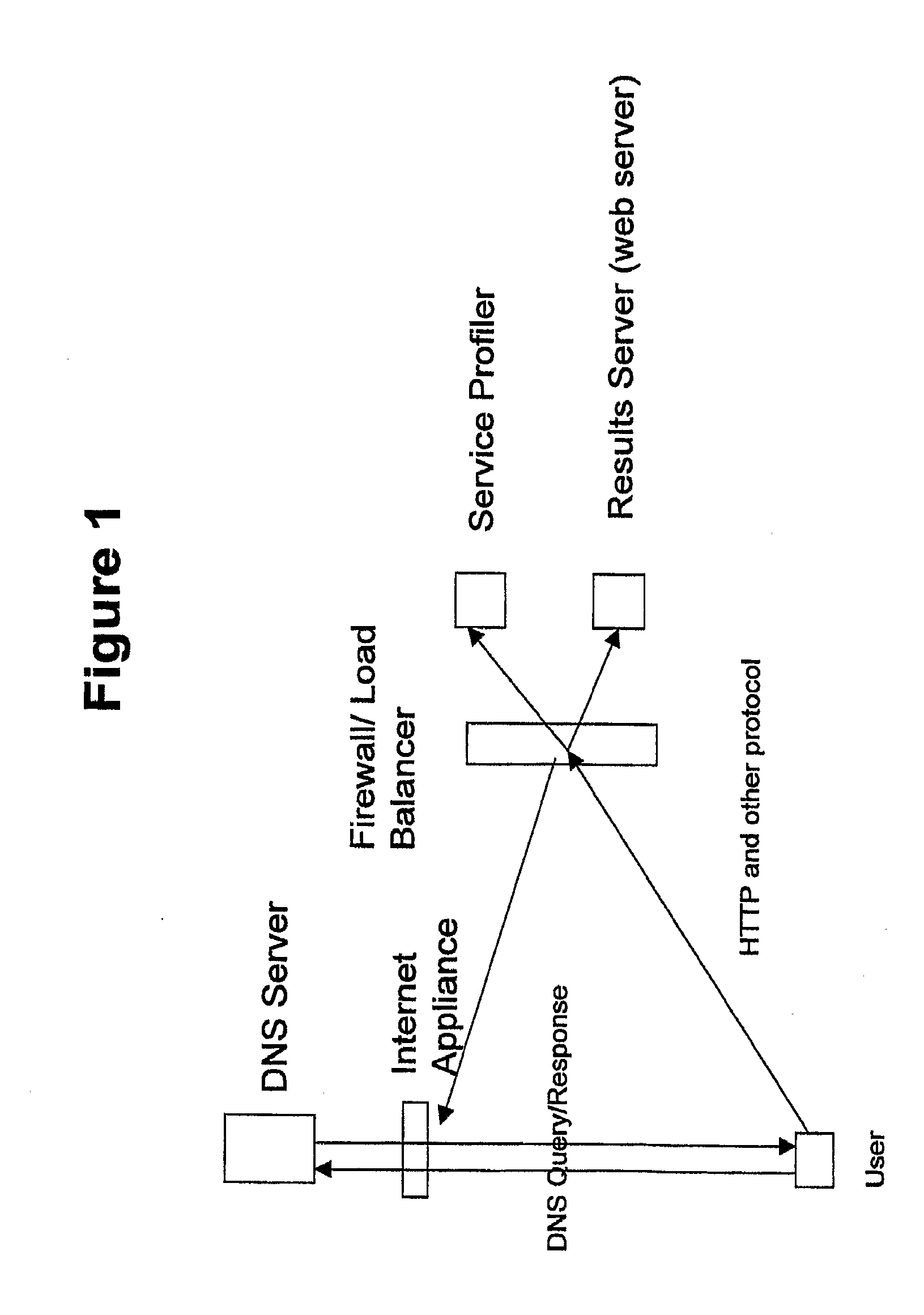
Systems and Methods for Discerning and Controlling Communication Traffic
InactiveUS20090013089A1Efficient and effective traffic controlMultiple digital computer combinationsTransmissionTraffic capacityControl communications
Communication traffic redirection systems and methods are disclosed that allow for redirection of communication traffic over the Internet based, at least in part, on the type of higher-level communication protocol intended to be used. The systems and methods permit redirection of only certain types of communication traffic of interest for example HTTP traffic, while permitting other types of communication, for example SMTP traffic, to pass without redirection. The systems and method can employ a training and dynamic feedback procedure to ensure only traffic of interest is redirected. The systems and methods provide efficient redirection of specific types of traffic to redirect landing pages, and allow for efficient methods of generating revenue through advertising.
Owner:BUSHNELL HAWTHORNE
Internet domain keyword optimization
ActiveUS20050038894A1Increase incomeWeb data indexingMultiple digital computer combinationsPaymentDomain name
A computerized system and method for optimizing contents of a domain landing page for increased revenues for the domain name owner. A landing server tracks user interactions with the domain landing page and generates an optimized keyword data set for the domain name. The keyword data set is used for selecting the information to be displayed on the domain name page. According to one embodiment, the keywords are associated with advertiser payment values. When a link to an advertiser bidding on a particular keyword is selected, revenue generated due to the click is shared with the domain name owner. Selection of links on pop-under pages displayed with a landing page are also shared with the domain name owner. Semantic analysis of keywords and domain names allows the generation of a related keyword data set when there is insufficient number of relevant user interactions for generating the optimized keyword data set.
Owner:SOL INVICTUS COMITI LP
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com