Identity-based encryption method supporting ciphertext equivalence test function
A test function and base encryption technology, applied in the field of information security, can solve problems such as low efficiency and impracticality, achieve the effects of short key and ciphertext size, reduce communication overhead, and improve computing efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
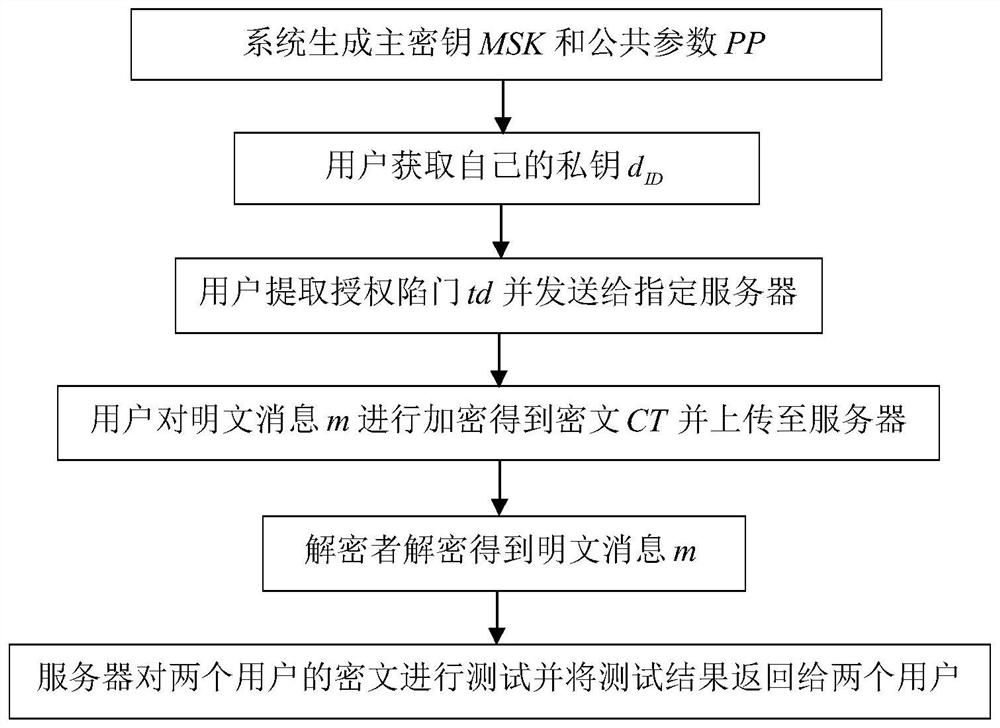
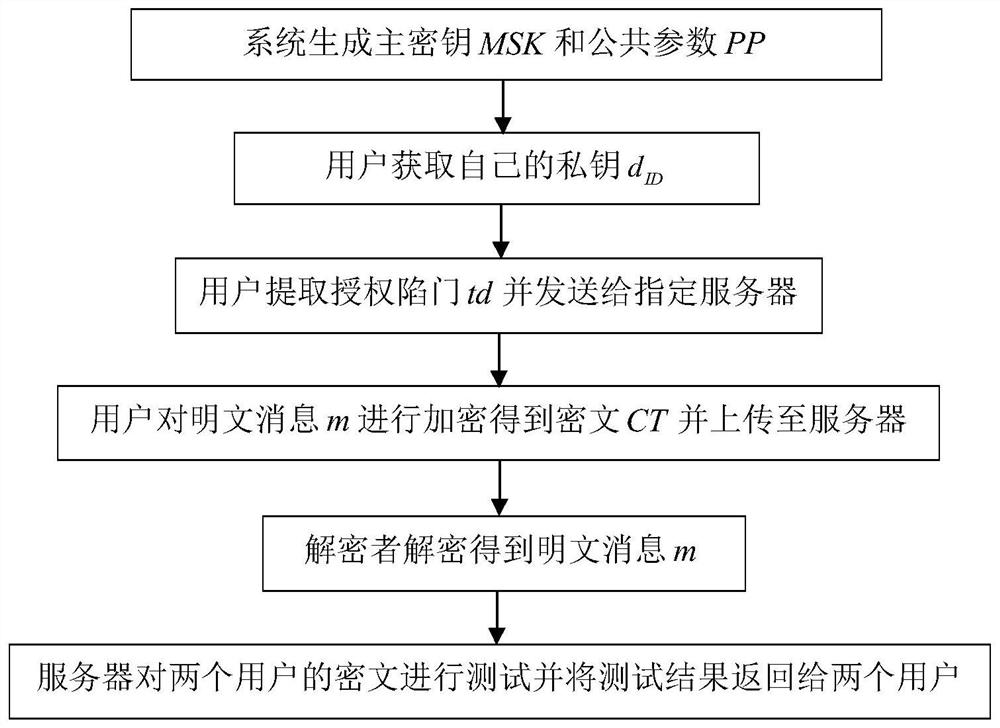
[0039] Embodiments of the present invention are further described in detail below in conjunction with the accompanying drawings:
[0040] refer to figure 1 , this example supports the identity-based encryption method of the ciphertext equivalence test function, and the implementation steps are as follows:
[0041] Step 1, system initialization.
[0042] (1.1) Input security parameter λ, given a bilinear map e: Let g be A generator of , let e(g,g) be A generator of , where, is the multiplicative cyclic group of order p, is a multiplicative cyclic group of order p;
[0043] (1.2) The key generation center KGC selects two cryptographic hash functions H 1 : H: and in Randomly select 5 different master key generation stage parameters α, β 1 ,β 2 ,β 3 ,β 4 , where {0,1} * represents an arbitrarily long bit string, Represents the set {0,1,...,p-1};
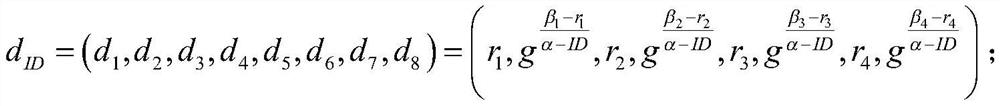
[0044] (1.3) The key generation center calculates and outputs the system master key MSK and the system public p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com