Network threat intelligence automatic extraction method based on deep learning
A deep learning and automatic extraction technology, applied in the field of network security, can solve the problems of low intelligence recognition accuracy and intelligence entity disorder, and achieve the effect of improving accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
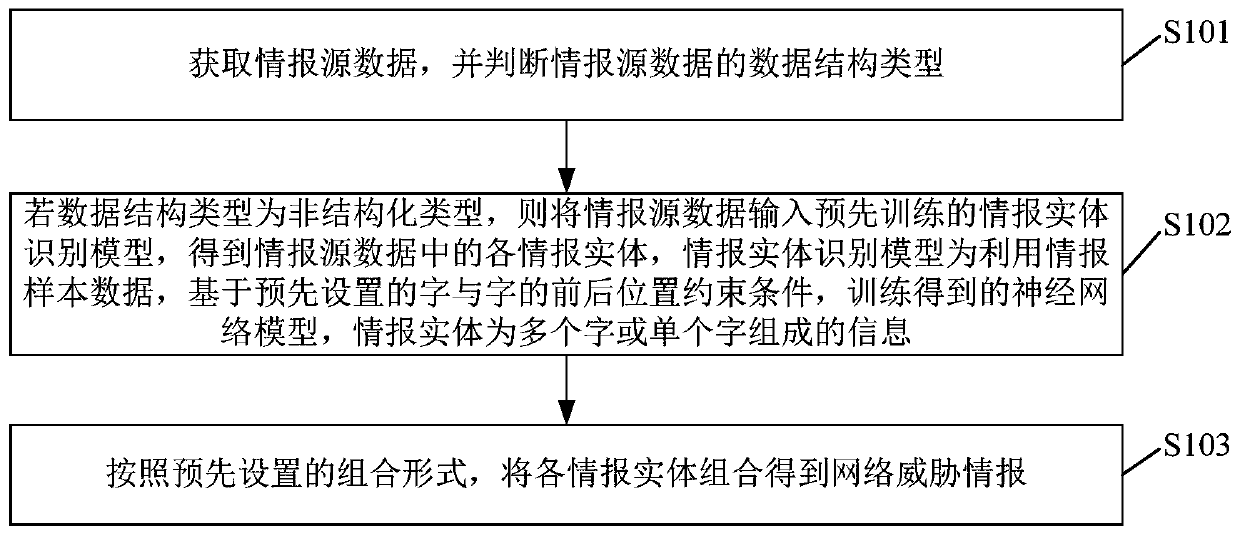
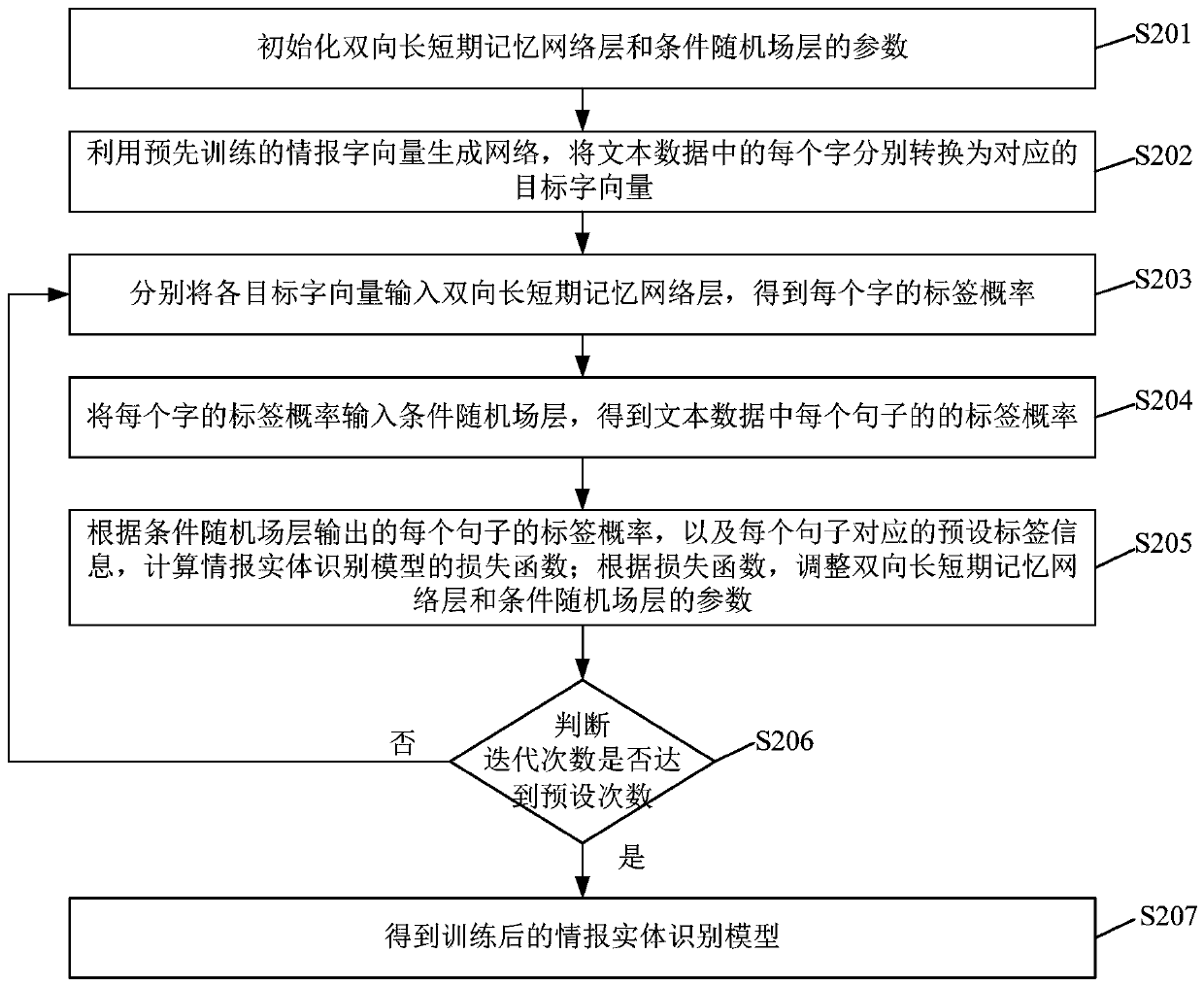
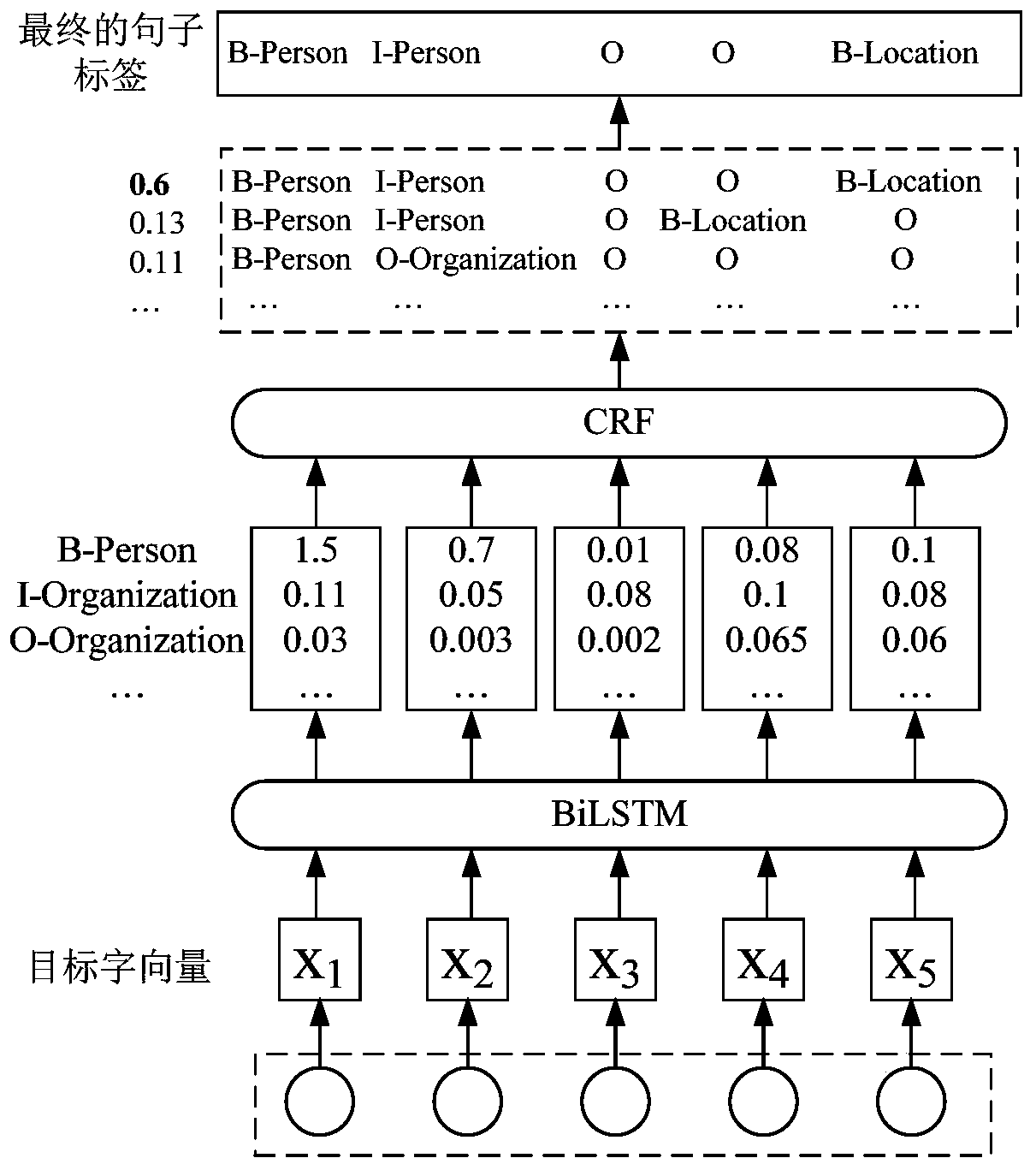
Method used
Image
Examples
Embodiment Construction
[0027] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only a part of the embodiments of the present invention, rather than all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative work shall fall within the protection scope of the present invention.
[0028] TI (Threat Intelligence) defines knowledge based on evidence, including scenarios, mechanisms, indicators, meanings, and actionable recommendations. Among the network security defense methods, the use of known CTI (Cyber Threat Intelligence) to defend against attacks from unknown threats is an active defense method that uses detection and analysis as a means. Compared with traditional passive defense, active defense has excellen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com