Flow table rapid searching method and system under high-concurrency network environment
A network environment and flow table technology, applied in the field of network security, can solve problems such as system missed detection, and achieve the effect of reducing overhead, improving access efficiency, and high efficiency and flexibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The present invention will be further described below through specific embodiments and accompanying drawings.
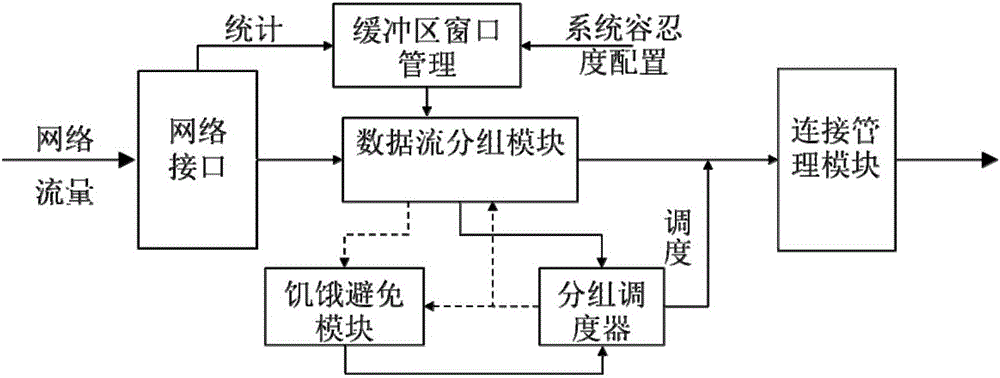
[0027] The general framework of the present invention is as figure 1 As shown, it consists of six parts: network interface, buffer window management module, data stream grouping module, starvation avoidance module, packet scheduler, and connection management module. The operation steps are as follows:
[0028] 1) When the traffic enters the network interface, the traffic situation is counted, and the traffic statistics are sent to the buffer window management module; the buffer window management module selects one from the preset window sizes according to the current traffic situation;
[0029] 2) According to the set window size, the data stream grouping module performs a grouping operation on the arriving data packets, and when the scheduling opportunity arrives, triggers the grouping scheduler;
[0030] 3) After receiving the trigger instruction, the packe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com