Privacy encryption method, electronic equipment, storage medium and chip
An encryption method and privacy technology, applied in the field of communications, can solve problems affecting the authenticity of information, non-repudiation of integrity, interception or even tampering of plaintext M, and reduction of information security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
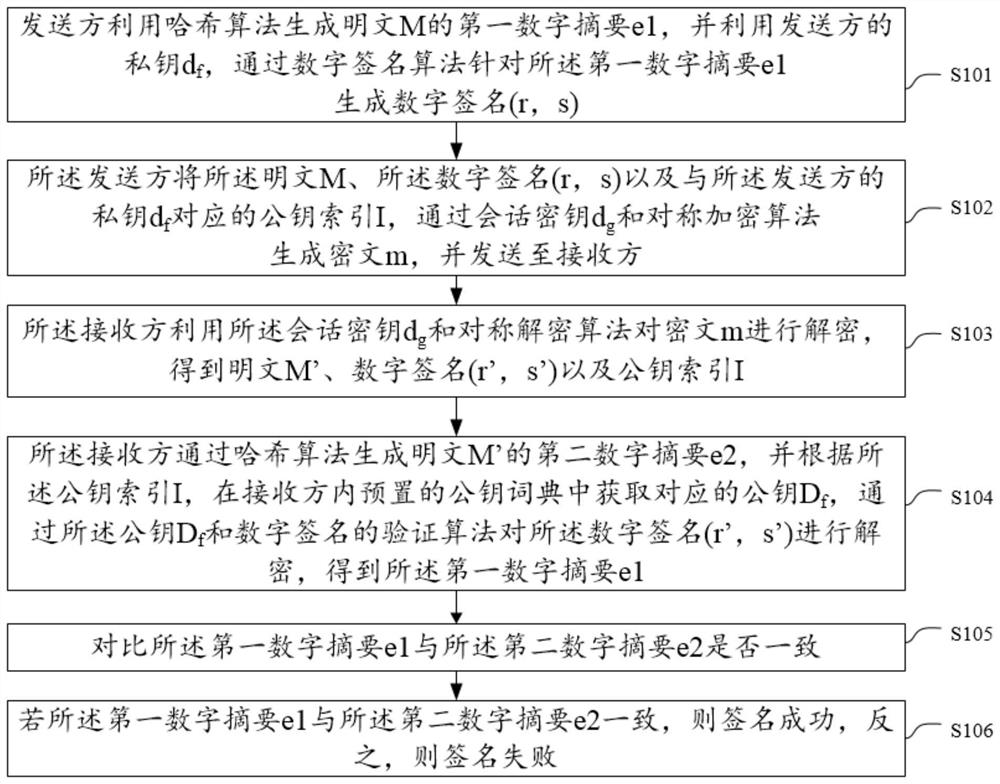
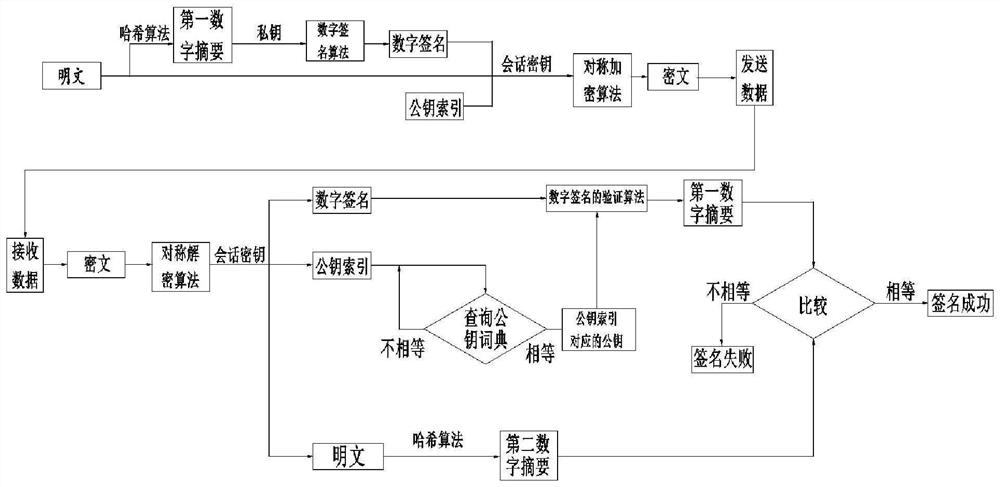
[0032] The technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the drawings in the embodiments of the present application. Apparently, the described embodiments are some of the embodiments of the present application, but not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of this application.
[0033] A digital signature is a digital string that can only be generated by the sender of the message and cannot be forged by others. This digital string is also an effective proof of the authenticity of the message sent by the sender of the message. It is a sign for electronic messages. In this method, digital signatures can be obtained based on both public key cryptosystem and private key cryptosystem.
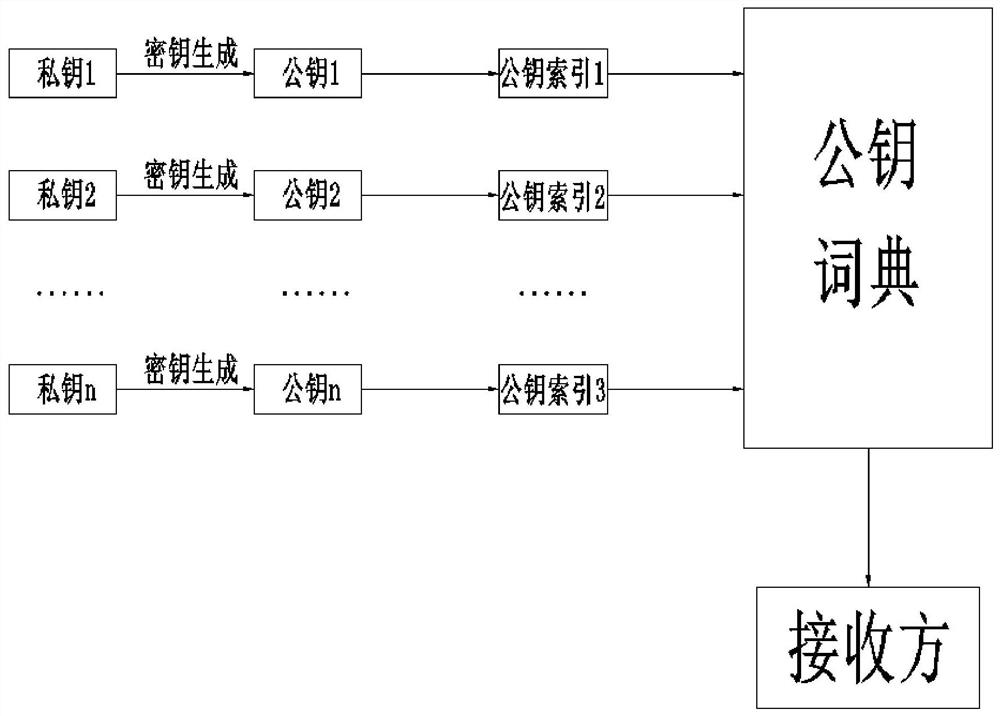
[0034] The public key and the private key are a key pair obtai...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com