Computer information security system
An information security system and computer technology, which is applied in the field of computer information security systems, can solve problems such as poor smoothing effect, insufficient definition of image details, and large time-consuming
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
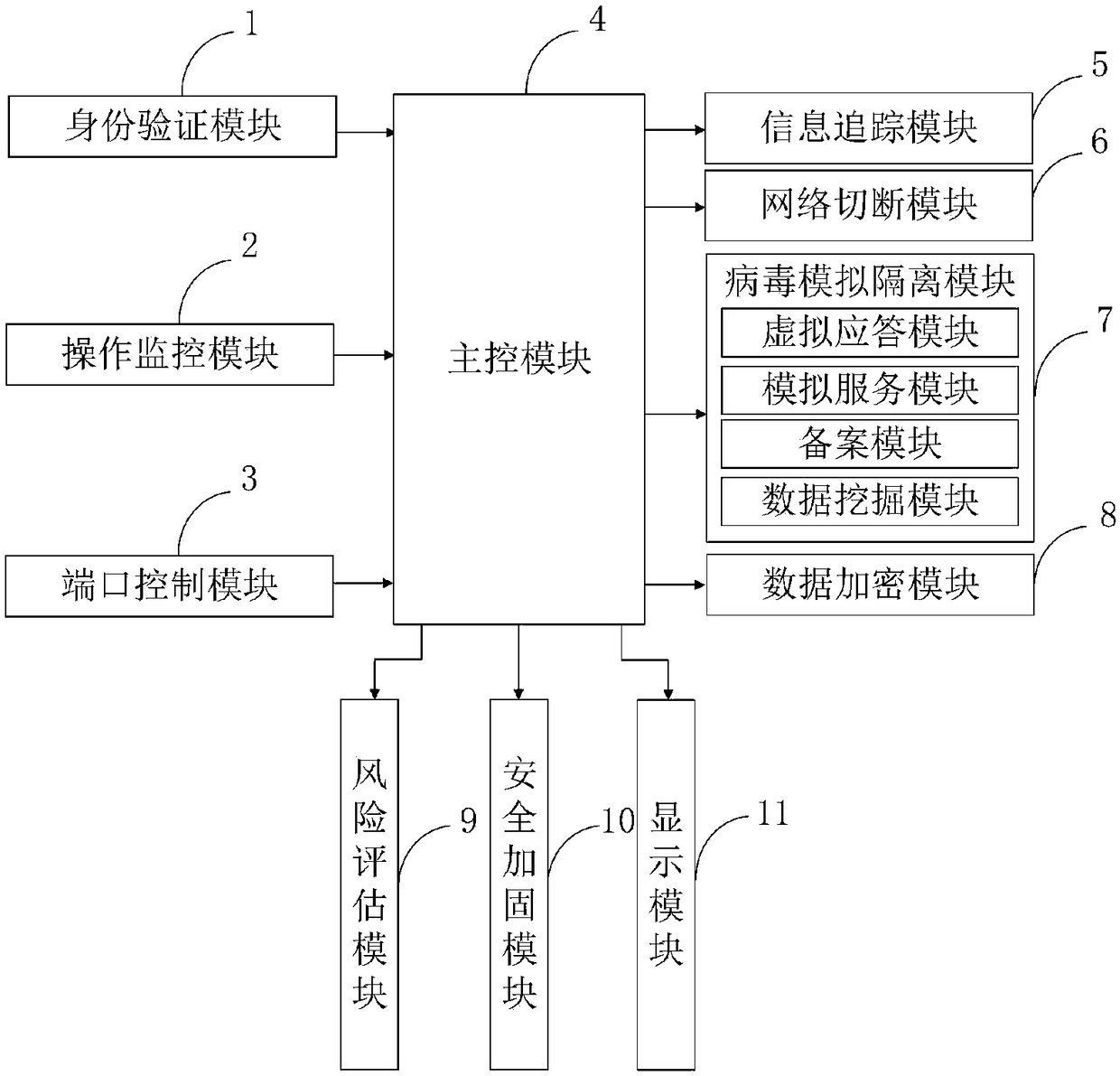
[0100] In order to further understand the content, features and effects of the present invention, the following examples are given, and detailed descriptions are given below with reference to the accompanying drawings.
[0101] The structure of the present invention will be described in detail below in conjunction with the accompanying drawings.
[0102] Such as figure 1As shown, the computer information security system provided by the present invention includes: identity verification module 1, operation monitoring module 2, port control module 3, main control module 4, information tracking module 5, network cut-off module 6, virus simulation isolation module 7, data An encryption module 8 , a risk assessment module 9 , a security hardening module 10 , and a display module 11 .
[0103] The identity verification module 1 is connected with the main control module 4, and is used to verify the legitimacy of the login information through the identity verification program;
[010...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com