Credible digital asset transaction method
A technology of digital assets and transaction methods, applied in digital data protection, electronic digital data processing, data processing applications, etc., can solve the problems of privacy leakage, poor transaction experience, bloated blockchain, etc., to prevent tampering and eliminate risks , Overcome the effect of insider trading
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0053] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
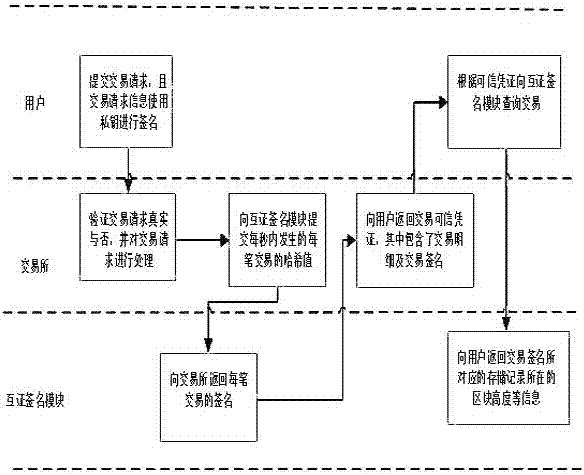
[0054] (1) Mutual authentication signature module
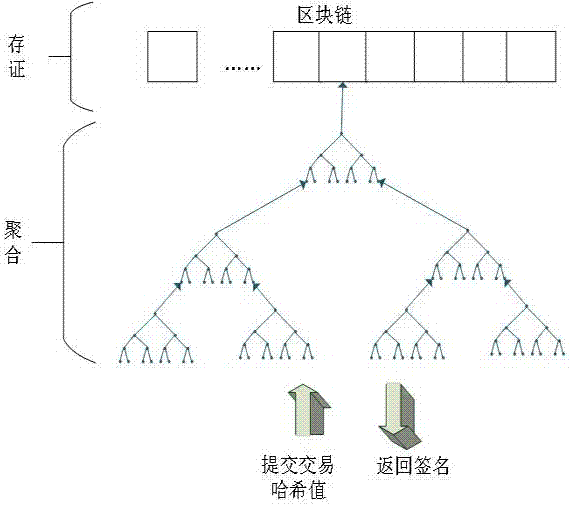
[0055] The mutual authentication signature module adopts hash tree (Merkle tree) aggregation technology, and any data submitted in the system can be "traceable to the source". Such as figure 1 As shown, the user sends a hash value of a transaction, assuming X1, all received requests are aggregated into a hash tree, and the signature returned to the user contains the complete path from the leaf node to the root node. To prove X 3 Integrity requires the use of X 4 、X 12 and x 58 Regenerate the root hash to prove that X3 participated in the generation of the root node.
[0056] Trusted Credentials
[0057] In this way, for the hash value of each transaction, there is a unique corres...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com