High-efficiency and safe network communication method
A network communication and security technology, applied in secure communication devices and key distribution, to ensure the effect of ensuring no leakage, efficient and secure network communication, and guarding against illegal requests and repeated submissions
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] Such as figure 1 As shown, the present invention generates a string of certificates with time-to-live after the user logs in successfully. The client first encrypts the content to be transmitted, the certificate and the current timestamp, and then compresses the encrypted ciphertext, and finally compresses the compressed The ciphertext is URL-safe Base64 encoded, and then sent to the server; after the server receives it, it first performs URL-safe Base64 decoding, and then decompresses and decrypts it. After obtaining the certificate, it verifies the certificate. After the verification is successful, Then judge whether the timestamp has been requested. If there is no request, record the timestamp to the server to prevent repeated submission of requests. Specifically include the following steps:
[0035] Step 1: Client login authentication to obtain the certificate string;
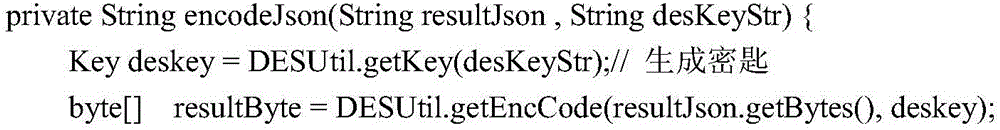
[0036] Step 2: Encrypt the information content, certificate and current timestamp with the priv...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com