Method and apparatus for securely transmitting data through Bluetooth technology
A technology for data transmission and technical security, applied in security devices, wireless communications, transmission systems, etc., can solve problems such as inability to communicate with terminal equipment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
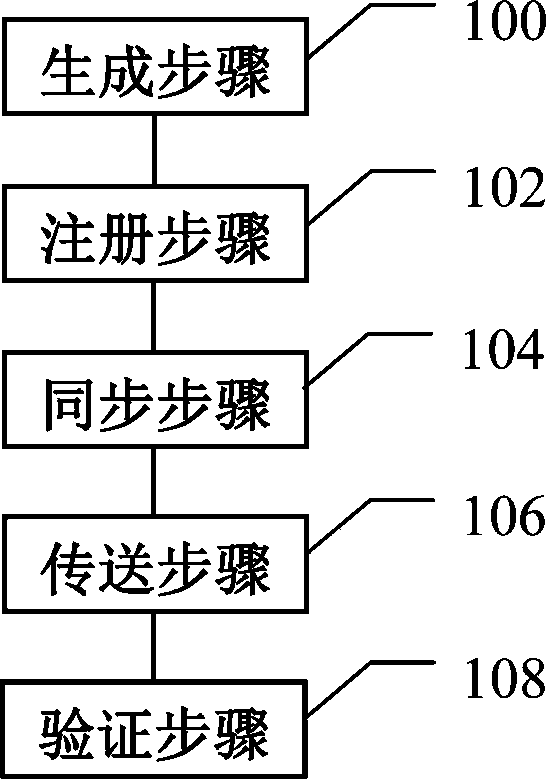
[0029] like figure 1 Shown is a schematic flowchart of a method for securely transmitting data through Bluetooth technology according to an embodiment of the present invention, including a registration step 102 and a transmission step 106 . In other embodiments, a generating step 100 , a synchronizing step 104 , and / or a verifying step 108 are also optionally included. Each of them will be described in detail below.
[0030] In the generating step 100, the generation of the key can have the following three schemes:
[0031] In one embodiment, a Media Access Control (MAC) address or a random number of the detection device is directly extracted as the key.
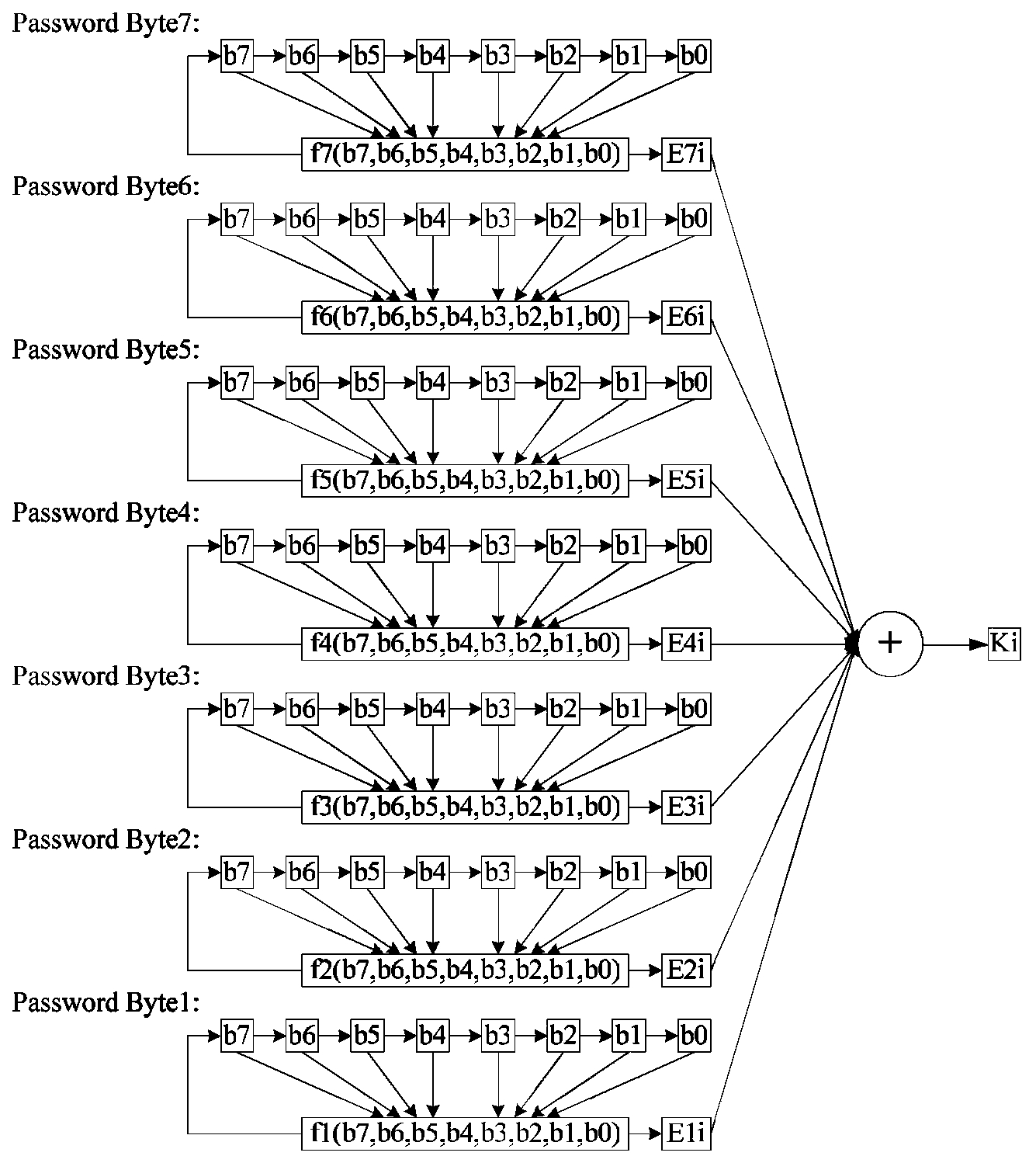
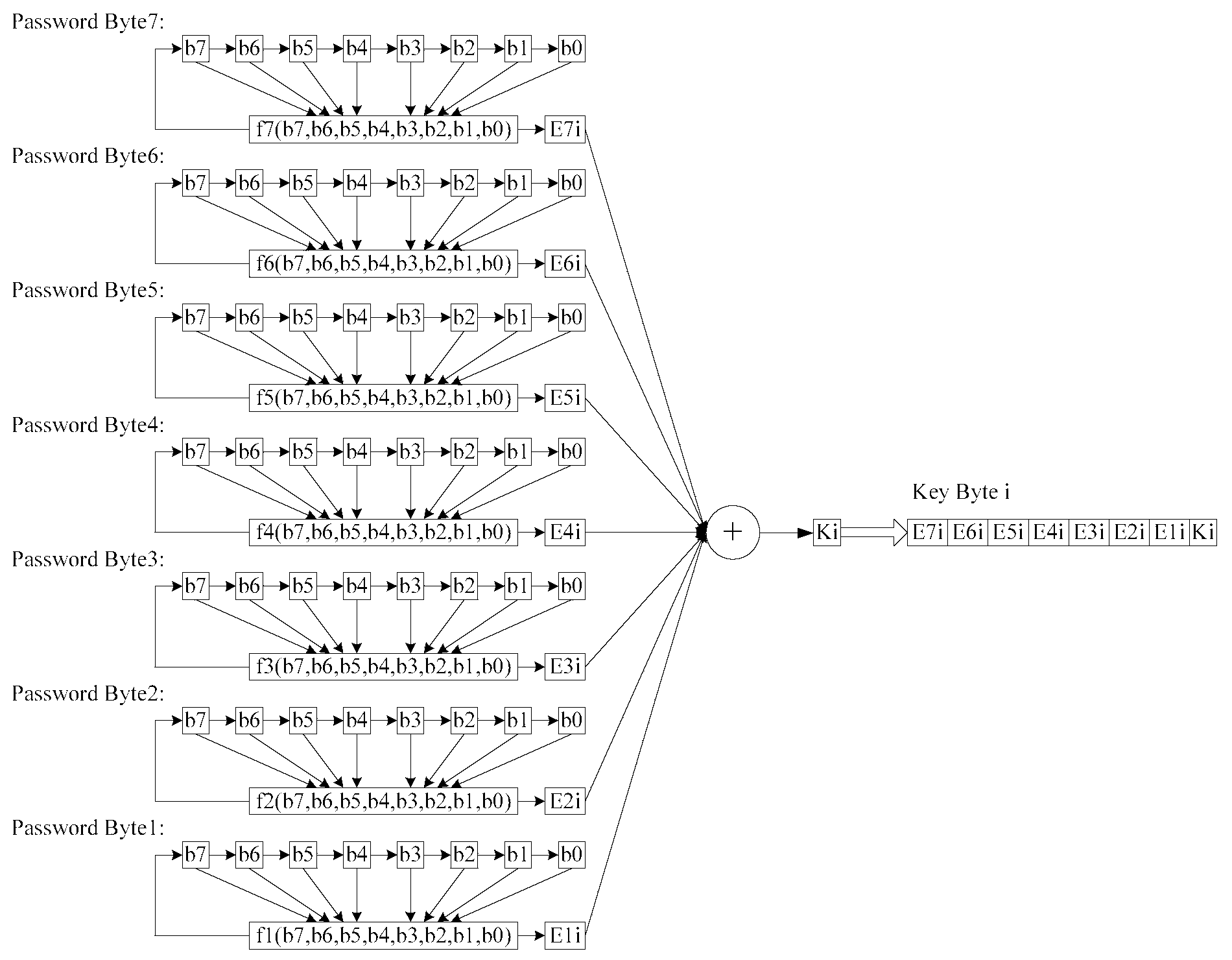
[0032] In another embodiment, a keystream is employed. For example, if the linear feedback shift register (LFSR) method is used, taking the 7-byte (6-byte fixed and 1-byte composed of the Checksum in each sent detection data packet) password as an example, the key stream is generated as follows: Figure 2 to Figure 5 As ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com