Data safety transmission method
A data security and data technology, applied in the security field to ensure reliability, reduce the chance of leaks, and improve security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
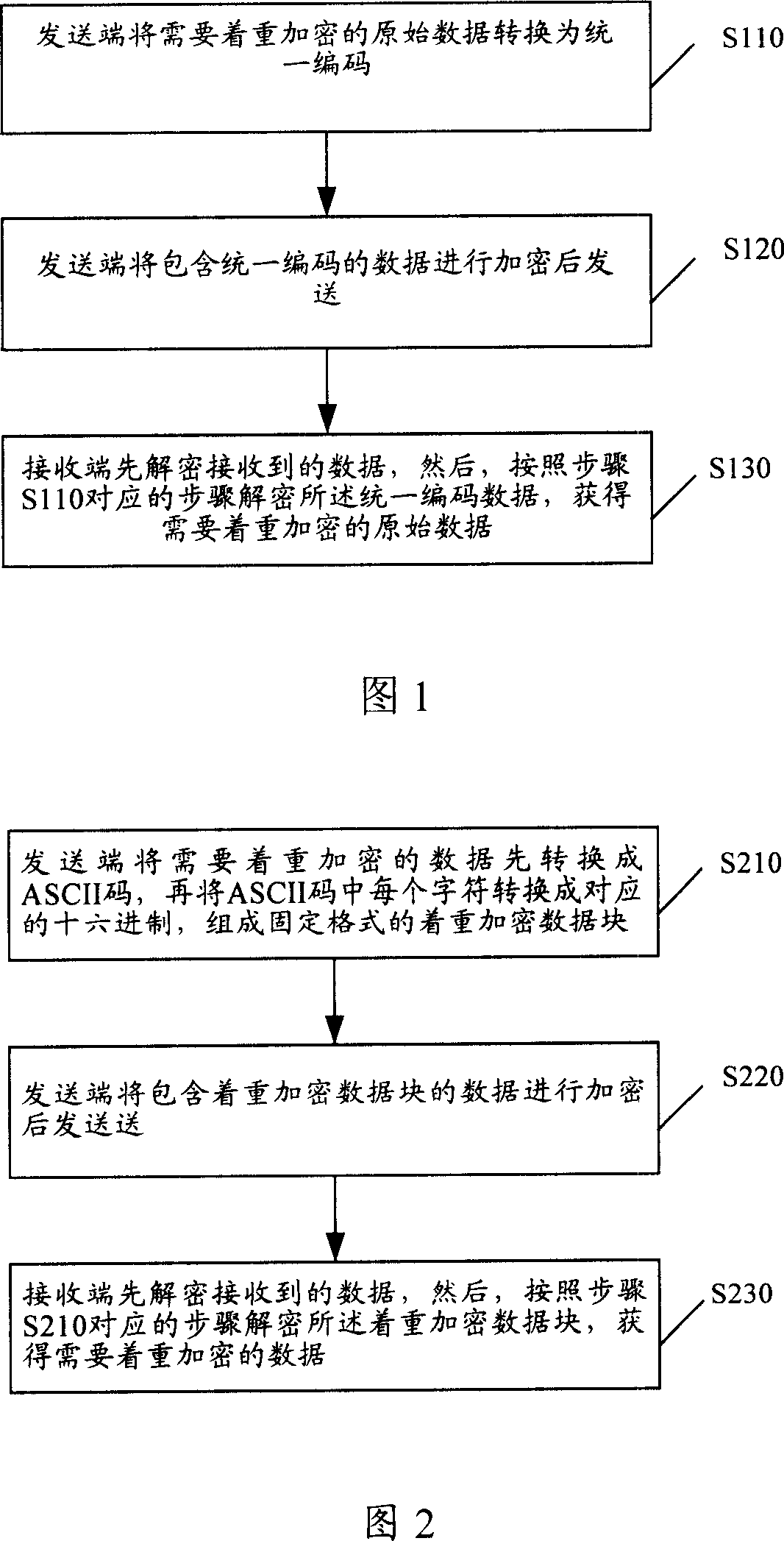
[0018] The present invention will be described in detail below in conjunction with the accompanying drawings.
[0019] Considering that the receiver correctly parses the received data, in many cases it is necessary to display all fields in the file with visible characters, even encrypted content must be displayed with visible characters. Therefore, the core of the present invention is that the sending end uniformly encodes the important data into other visible characters, and then encrypts the data that needs to be sent including the visible characters before sending it. Similarly, the receiving end first decrypts the received data , and then use the corresponding decryption method to convert these visible characters into important data. When the sending end is a local area network, when the original important data is obtained, it is immediately uniformly encoded into other visible characters for display, and the data transmitted inside the local area network is encoded visibl...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com