Dual verification method for trusted equipment access application
A device access and double verification technology, applied in the field of application security verification, can solve problems such as dictionary attacks, password errors, password leakage, etc., to achieve the effect of enhancing security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] In order to make the technical problems, technical solutions and beneficial effects solved by the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
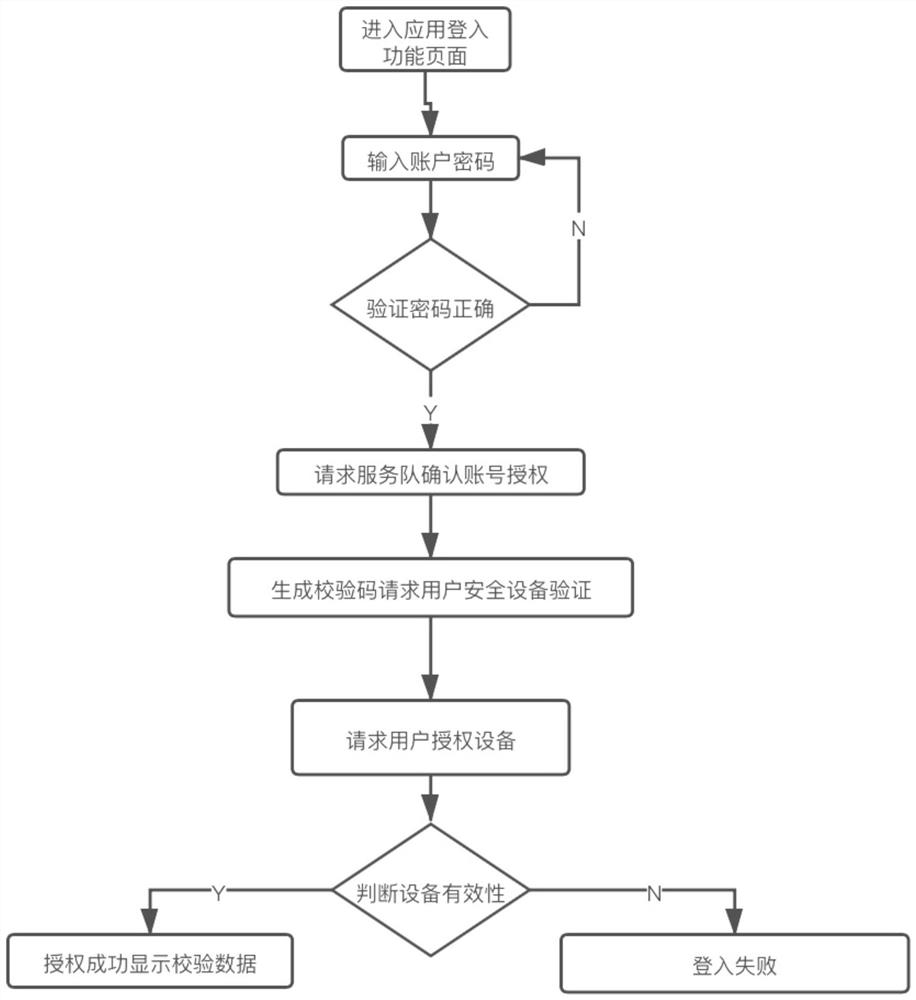
[0038]The present invention provides a double verification method for a trusted device to access an application. The double verification method is the safest and most convenient way in terms of security and deployment compared to other non-ID / PW mode solutions.
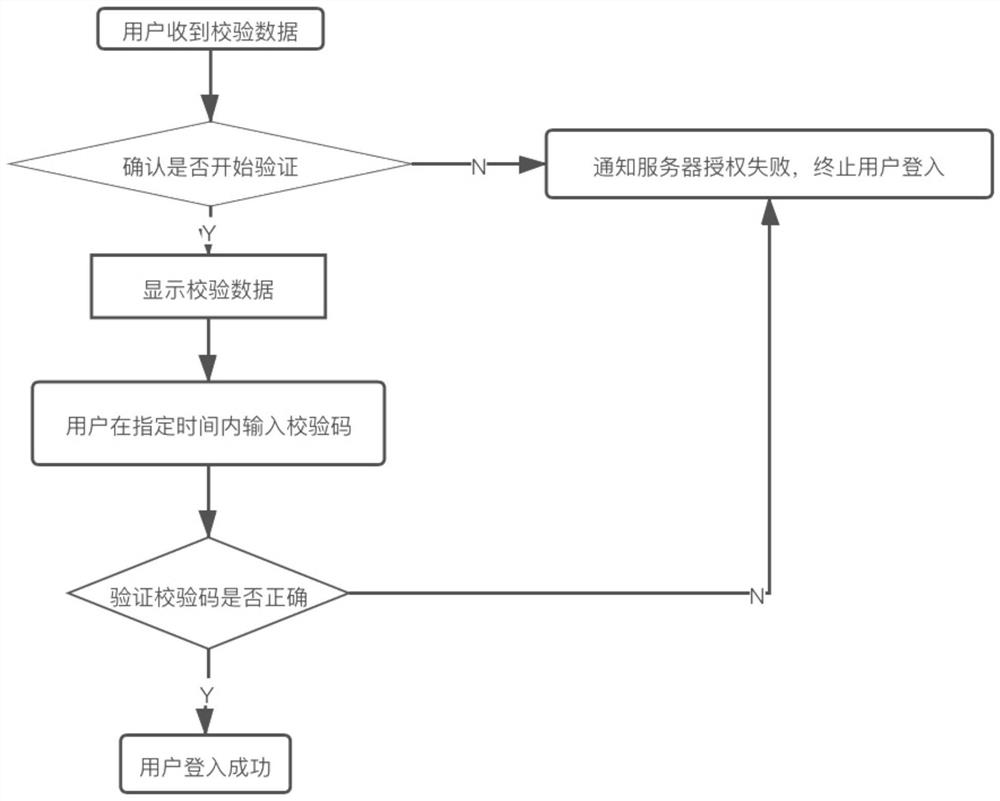
[0039] After enabling two-factor authentication, users can only access the application software corresponding to their account on authorized devices (that is, trusted devices or web pages). When logging in to a new device (unauthorized device) for the first time and accessing the application software correspondi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com