Internet of things access control method with privacy protection based on blockchain
An access control and privacy protection technology, applied in the field of the Internet of Things, can solve the problems of access control method privacy leakage and other issues, and achieve the effect of protecting the privacy of access records and data privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in combination with specific examples and with reference to the accompanying drawings.
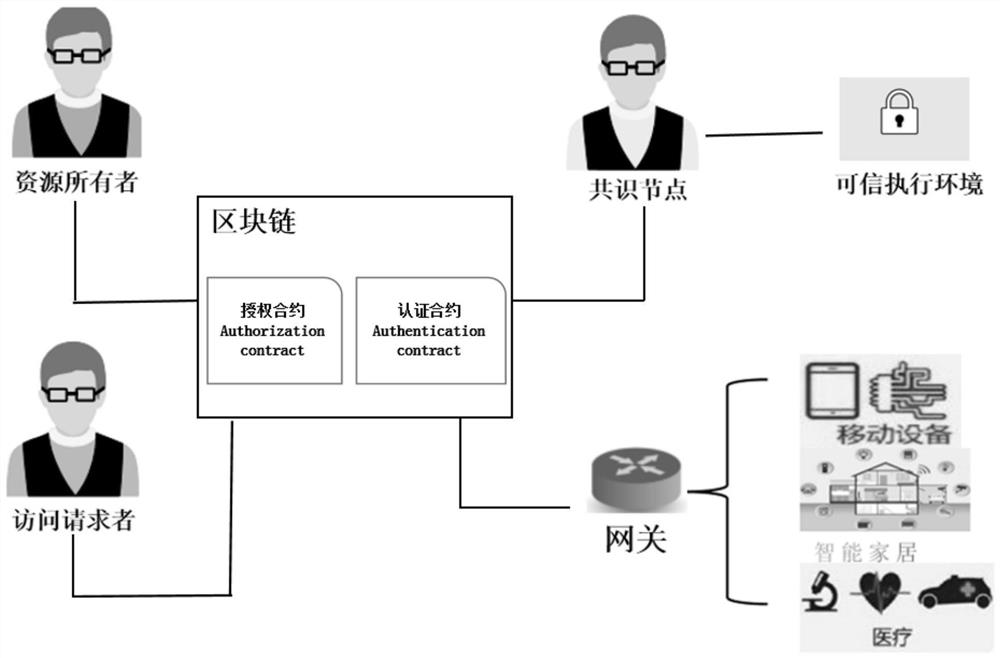
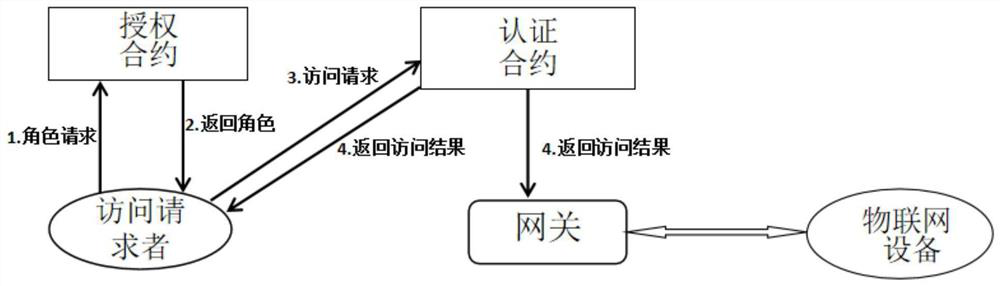
[0038] see figure 1 and 2 , a privacy-protected Internet of Things access control method based on blockchain, which specifically includes the following steps:
[0039] Step 1: The resource owner creates an authorization contract (Authorization Contract), and writes the authorization contract through an offline compiler to realize functions such as granting roles, adding roles, and deleting roles in the authorization contract.
[0040] The resource owner is the owner of the IoT device.
[0041] The authorization contract is used to grant roles and corresponding permissions to access requesters. For internal members, resource owners can directly add and delete role information through transactions. For external members, th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com