Outsourcing revocation method and system in attribute-based encryption system
An attribute-based encryption and system version technology, applied in the field of cryptography, can solve the problems of easy loss and theft, time-consuming, and a large amount of computing overhead, and achieve the effect of saving access overhead and overhead.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
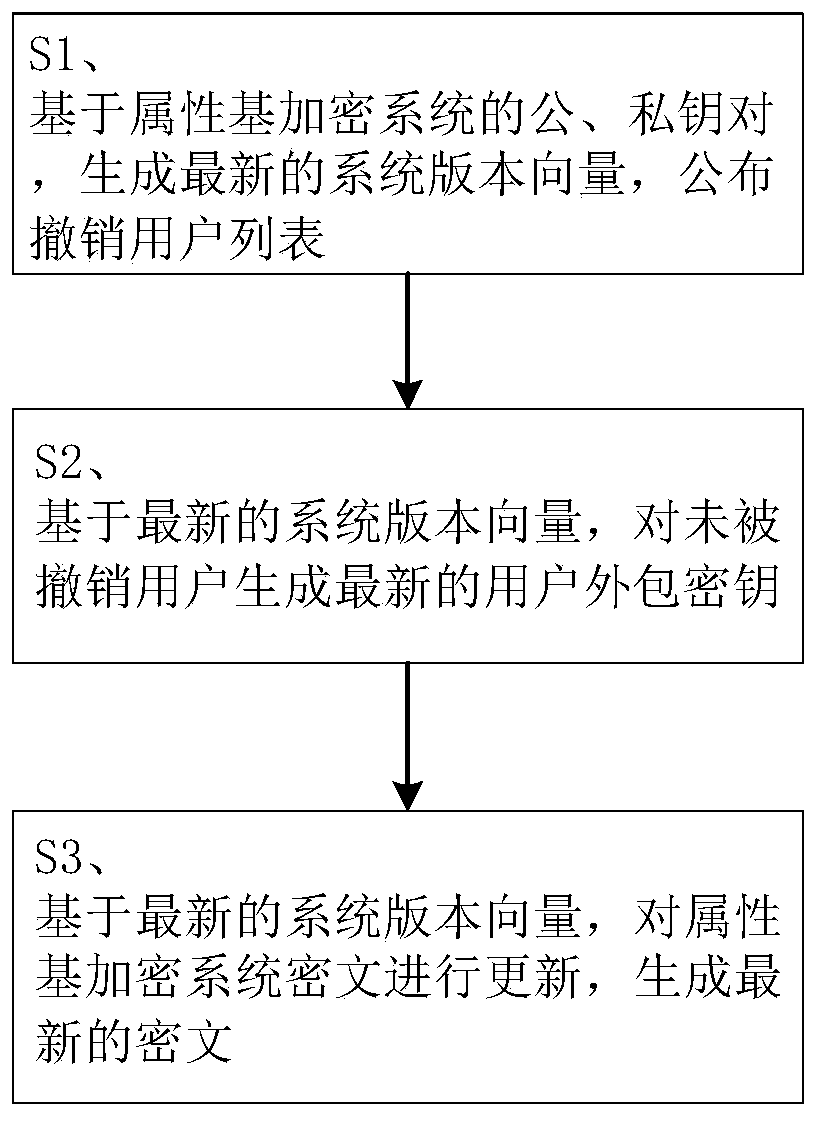
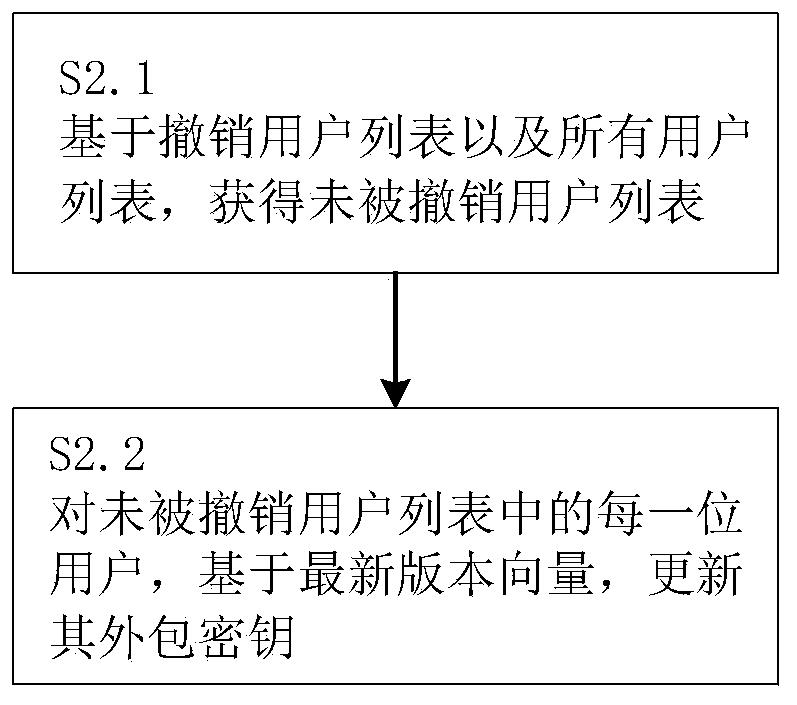
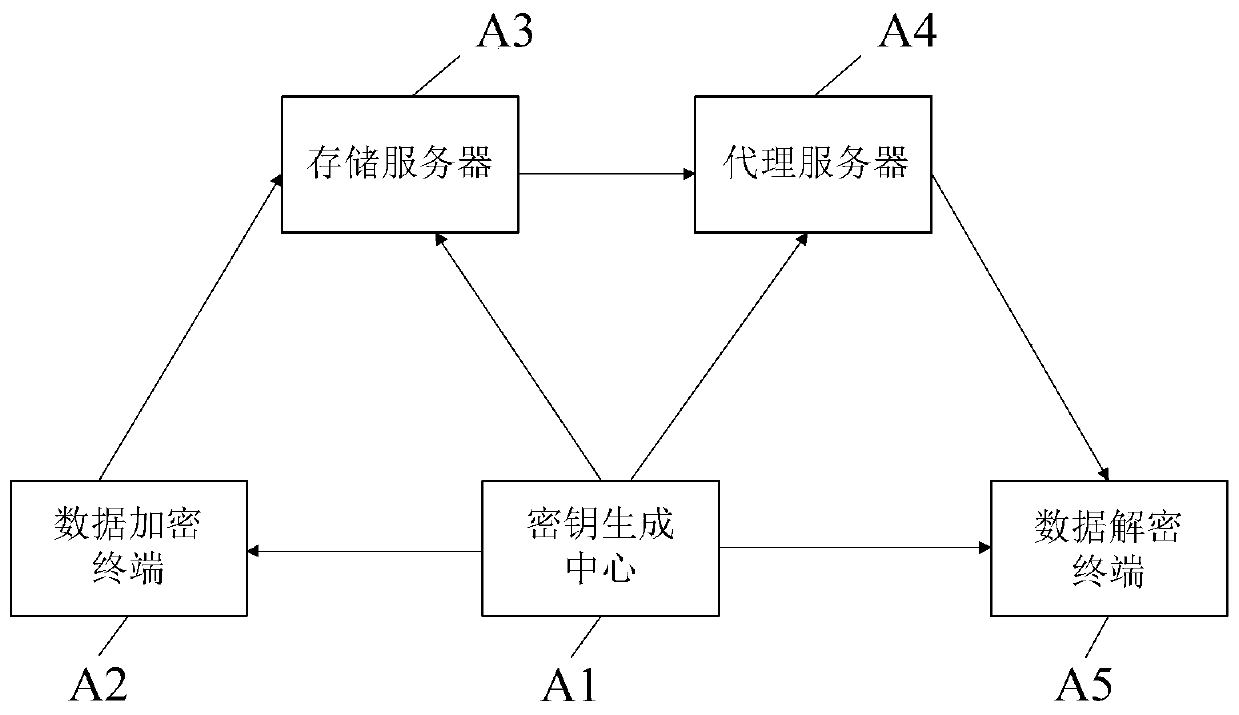
[0029] The specific embodiments of the present invention will be described in further detail below in conjunction with the drawings and embodiments. The following examples are used to illustrate the present invention, but not to limit the scope of the present invention.
[0030] The outsourcing revocation method and system in the attribute-based encryption system proposed by the present invention are mainly constructed based on the following existing mathematical and cryptographic knowledge.
[0031] (1) Bilinear pair
[0032] Define a function mapping e(.,.) to map elements in group G to group G T Go in, namely: e: G×G→G T ;
[0033] For a large prime number p, the properties satisfied by the bilinear pair are:
[0034] ①Bilinear characteristics: for g,h∈G, a,b∈Z p , There is e(g a ,h b )=e(g,h) ab Established, where Z p Represents the set {0,1,2,...,p-1};
[0035] ②Non-degeneration: there is at least one element g in the G group, so that the calculated e(g,g) is A generator of the g...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com