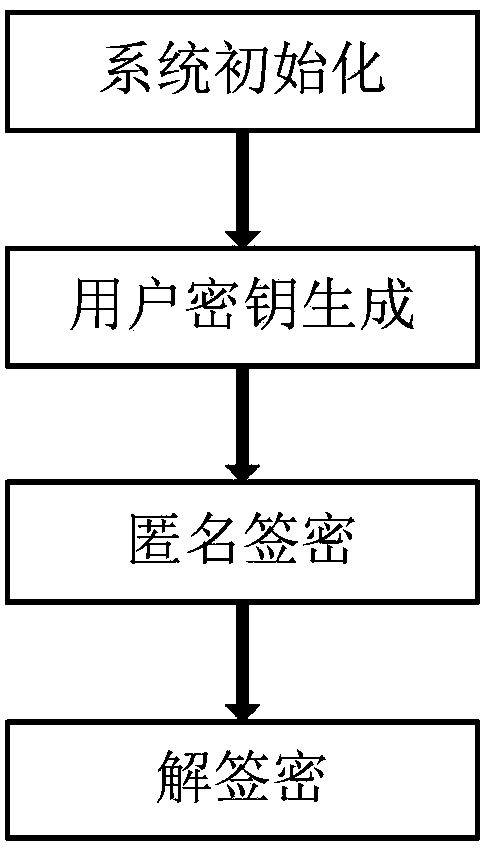
Anonymous signcryption method from identity public key system to certificate public key system
A technology of identity public key and certificate public key, applied in the direction of user identity/authority verification, etc., can solve the problems of inability to realize the anonymity of message delivery, leakage of user privacy, and not wanting any third party to know the message
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] One, the mathematical theory used in the present invention and technical term description:
[0043] 1. Bilinear pairing
[0044] In the present invention, bilinear pairing is a mapping that satisfies bilinearity, non-degenerateness, and computability, and it maps two elements in the prime order group G to the prime order group G T an element in . For example, the Weil pair and Tate pair defined on supersingular elliptic curves are bilinear pairs that satisfy the condition.
[0045] 2. Hash function
[0046] A hash function is a one-way function that transforms an input of any length into a fixed-length output, which is called the hash value of the input. A secure hash function should meet the following conditions: ①The output length is fixed, generally at least 128 bits, to resist birthday attacks; ②For each given input, its hash value can be easily calculated ; ③Given a description of a hash function and a hash value, it is computationally infeasible to find the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com