Cloud computing network server inner core safe access method
A cloud computing server and cloud computing network technology, applied in electrical components, transmission systems, etc., can solve the problems of insufficient credit level access control capabilities of server core reinforcement technology, and achieve the effect of ensuring communication security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] In order to make the object, technical solution and advantages of the present invention clearer, the implementation manner of the present invention will be further described in detail below in conjunction with the accompanying drawings.
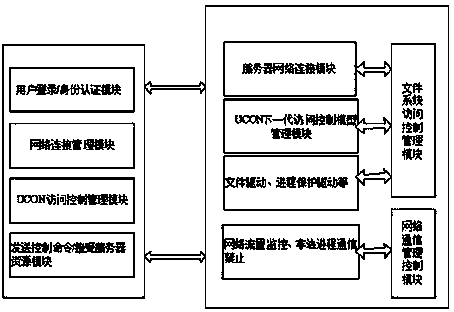
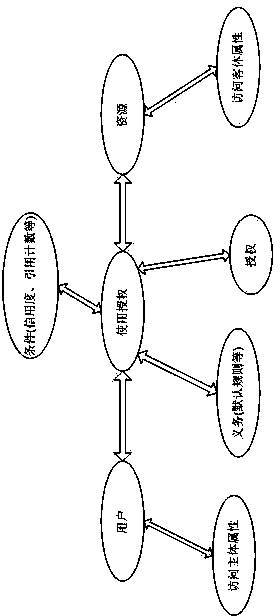
[0035] This embodiment is applied in a cloud computing server, and access control is performed on resources at the driver kernel layer. Referring to the trusted operation grading standard of the secure operating system, UCON (usage control) access control technology is adopted. The basic elements of UCON include: subject, object authority and elements related to authorization: conditions (authorization rules) and obligations, conditions have trust, Resource reference counting, etc. When the system accesses cloud computing resources, it authorizes the accessed objects according to the user's trust degree, reference technology and mandatory access control rules, and performs operations such as read-only and disable.
[0036] In terms of...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com