Login behavior detection method and device, storage equipment and electronic equipment
A technology of behavior and detection results, applied in secure communication devices, electrical components, digital transmission systems, etc., can solve problems such as poor versatility, and achieve the effect of reliable attack data and secure login requirements.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
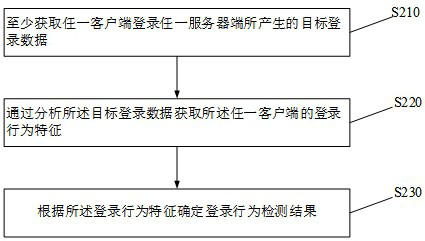
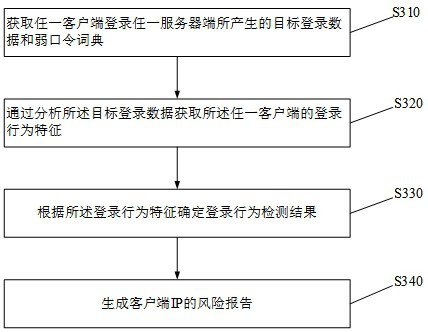
[0042] The technical solutions in some embodiments of the present application will be described below with reference to the accompanying drawings in some embodiments of the present application.
[0043] It should be noted that like numerals and letters refer to like items in the following figures, so once an item is defined in one figure, it does not require further definition and explanation in subsequent figures. Meanwhile, in the description of the present application, the terms "first", "second", etc. are only used to distinguish the description, and cannot be understood as indicating or implying relative importance.
[0044] In the related art, the data packet detection technology based on network traffic is a very critical link in the detection of security threats. The current Network Intrusion Detection System (NIDS) and Network Detection and Response (NDR) systems first collect network traffic data, and then use NIDS or NDR to analyze the network traffic data. Threat ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com