A privacy protection method for cross-domain dating based on mobile social network agent re-encryption
A mobile social network, proxy re-encryption technology, applied to an encryption device with a shift register/memory, key distribution, can solve threats to the data privacy security of dating users, violent guessing, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0056] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
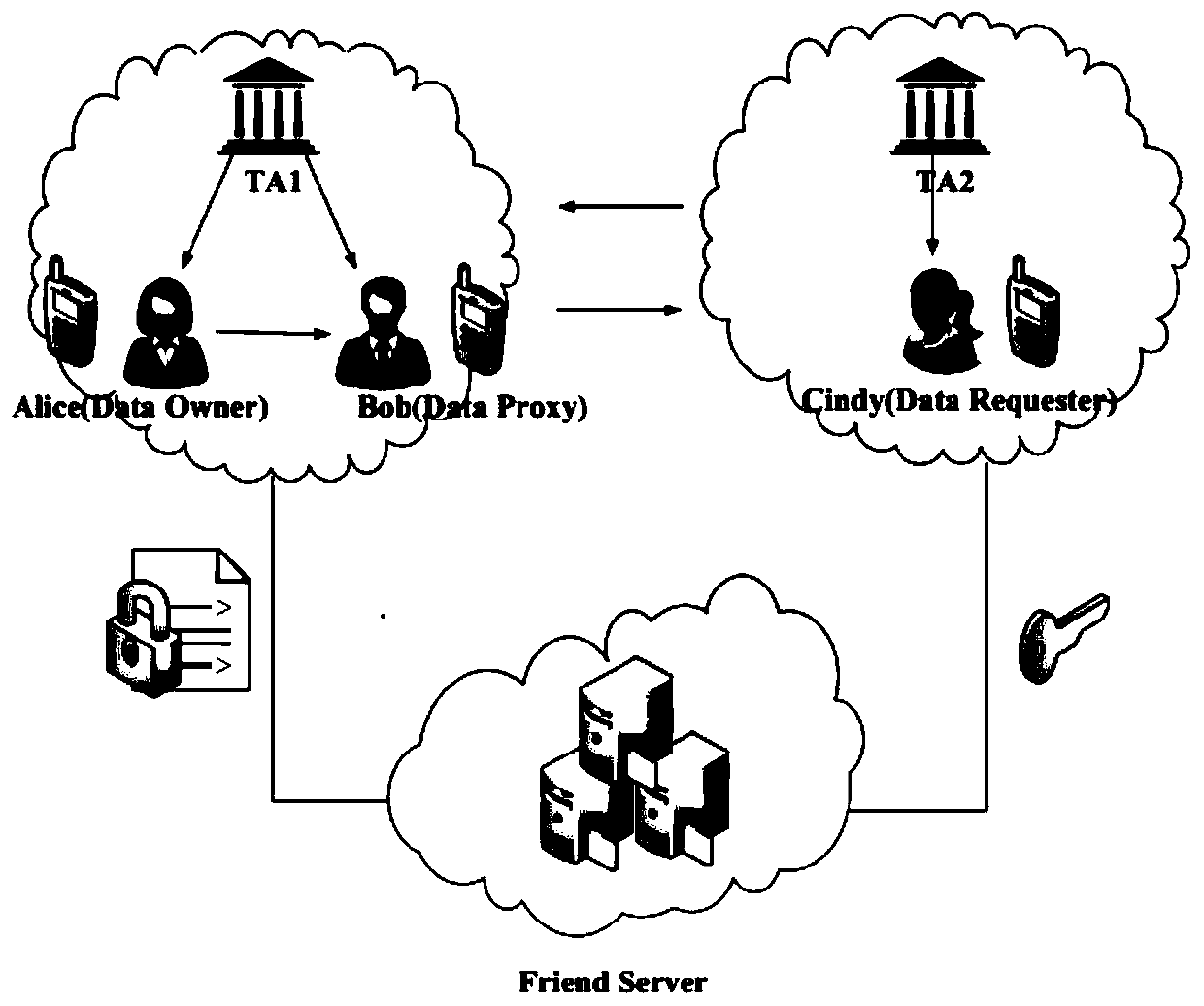
[0057] The schematic diagram of the overall architecture of the method of the present invention is as follows figure 1 shown.
[0058] FS: Responsible for storing ciphertexts of users' sensitive information about making friends, including personal photos, hobbies, contact information, identity information, personal videos and other information.
[0059] TA: Responsible for system initialization and attribute key generation, key distribution, and fine-grained access control policies for this area.
[0060] DO: Responsible for creating, modifying, deleting, encrypting, and specifying access control policies for files. Only the access control policies of the information owner who meet the attributes of the user who makes the friend request can correctly decrypt the file, so as to conduct further communication and communication. This article assumes that ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com