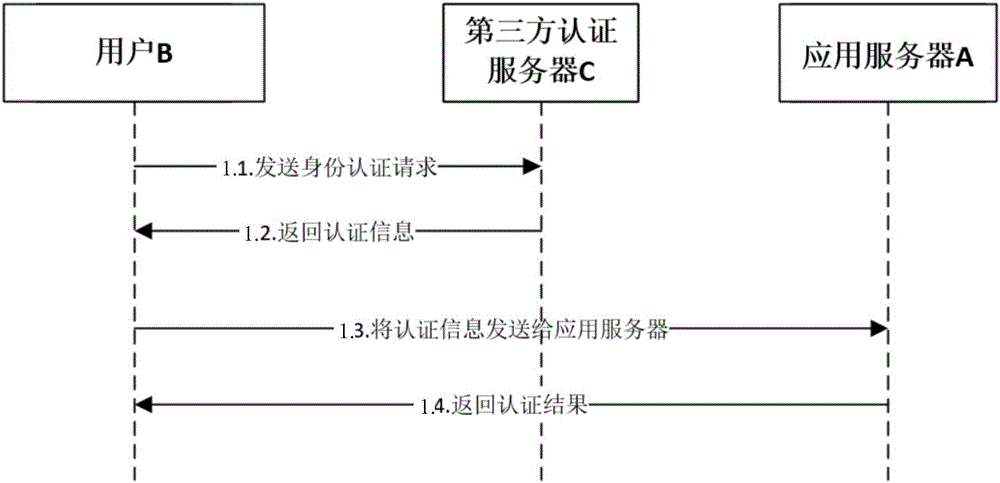
Identity authentication method based on block chain, authentication server and user terminal
An authentication server and identity authentication technology, applied in payment systems, electrical components, transmission systems, etc., can solve problems such as information leakage, user B and application server A risks, and achieve the effect of improving security and optimizing security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
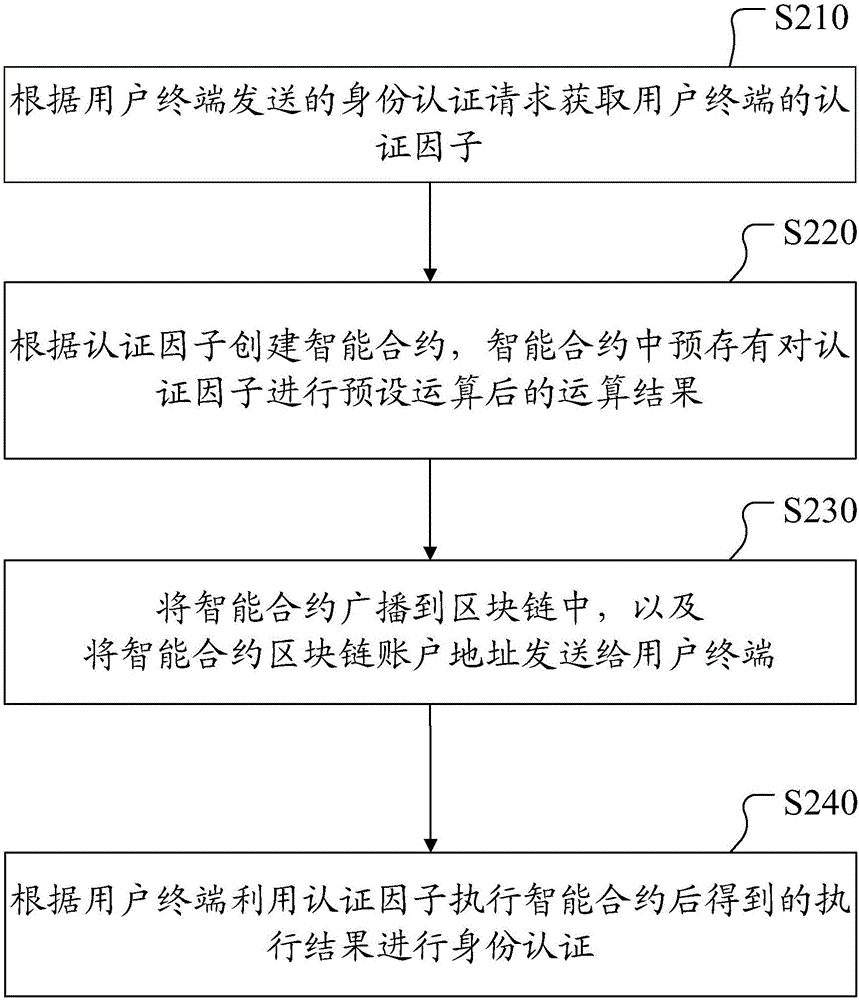
[0024] figure 2 It is a flow chart of a blockchain-based identity authentication method provided in Embodiment 1 of this application. Such as figure 2 As shown, the method includes:
[0025] Step S210: Obtain the authentication factor of the user terminal according to the identity authentication request sent by the user terminal.
[0026] In the embodiment of the present application, after receiving the identity authentication request sent by the user terminal, the authentication factor of the user terminal is obtained from the identity authentication request. Wherein, the authentication factors included in the request information may be single or multiple. The type of the authentication factor can be a user name type, a user password type, a device fingerprint type, a dynamic code type, a behavior habit type, or a combination of the above types. This embodiment of the present application does not specifically limit it, and those skilled in the art can flexibly set it ac...
Embodiment 2
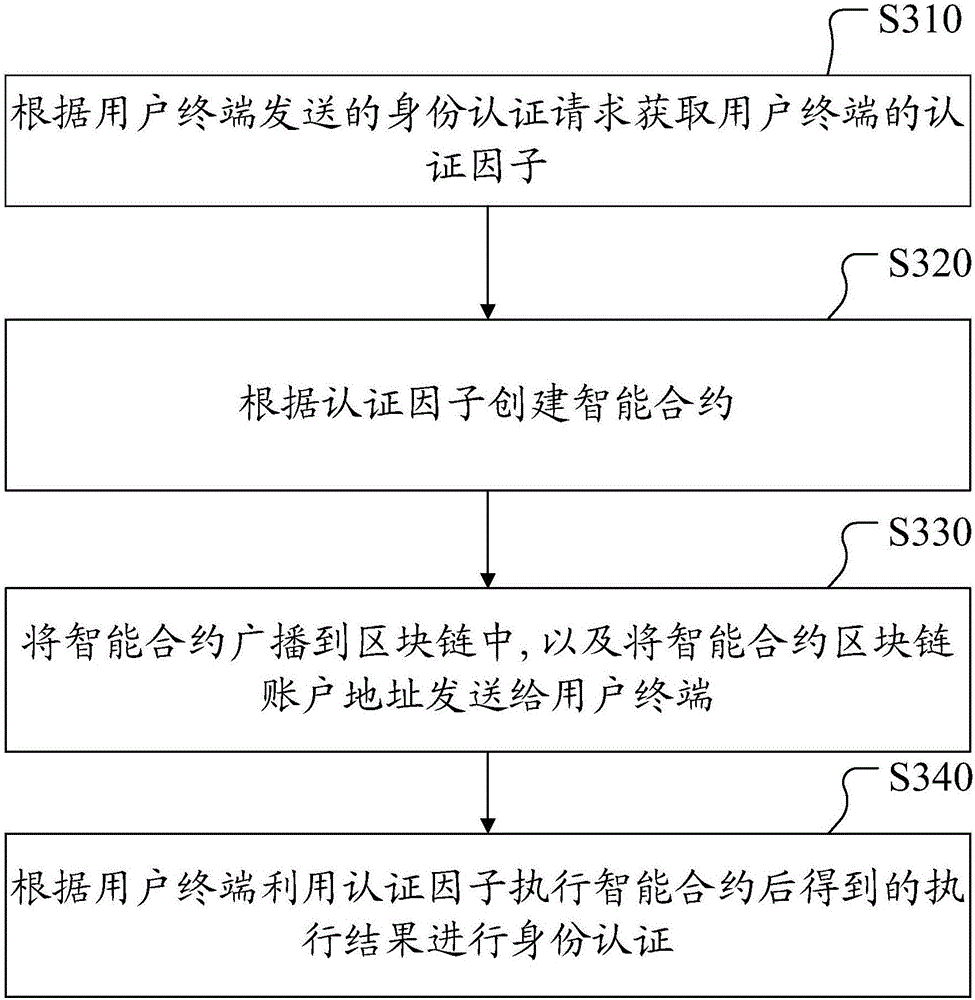
[0035] image 3 It is a flow chart of a blockchain-based identity authentication method provided in Embodiment 2 of this application, and the execution subject of this embodiment is preferably an authentication server. Such as image 3 As shown, the method includes:
[0036] Step S310: Obtain the authentication factor of the user terminal according to the identity authentication request sent by the user terminal.
[0037]In the embodiment of the present application, after receiving the identity authentication request sent by the user terminal, the authentication factor of the user terminal is obtained from the identity authentication request. Wherein, the authentication factors included in the request information may be single or multiple. The type of the authentication factor can be a user name type, a user password type, a device fingerprint type, a dynamic code type, a behavior habit type, or a combination of the above types. This embodiment of the present application d...
Embodiment 3
[0049] Figure 4 It is a flow chart of a blockchain-based identity authentication method provided in Embodiment 3 of the present application, and the execution subject of this embodiment is preferably a user terminal. Such as Figure 4 As shown, the method includes:
[0050] Step S410: Send an identity authentication request including the authentication factor of the user terminal to the authentication server, so that the authentication server can create a smart contract based on the authentication factor, and the smart contract pre-stores the calculation result of the authentication factor.
[0051] Among them, the user terminal actively sends an identity authentication request containing authentication factors to the authentication server, and the authentication request includes a single or multiple authentication factors, including but not limited to user name, user password, device fingerprint, dynamic code, and behavior habits, etc. .
[0052] In other embodiments, the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com