A network attack anomaly detection method
An anomaly detection and network attack technology, applied in the field of information security, can solve problems such as high false alarm rate, unavailability of detection methods, and reduce the credibility of the detection system, so as to achieve the effect of reducing the false alarm rate
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] All features disclosed in this specification, or steps in all methods or processes disclosed, may be combined in any manner, except for mutually exclusive features and / or steps.
[0040] Any feature disclosed in this specification, unless specifically stated, can be replaced by other alternative features that are equivalent or have similar purposes. That is, unless expressly stated otherwise, each feature is one example only of a series of equivalent or similar features.
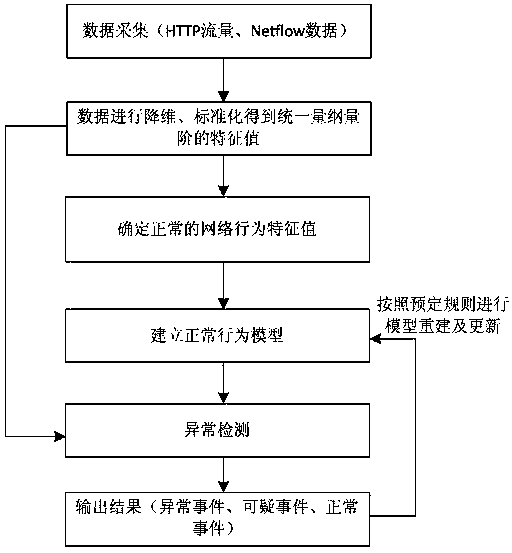
[0041] like figure 1 As shown, a kind of web attack anomaly detection method provided by the present invention comprises the following steps:
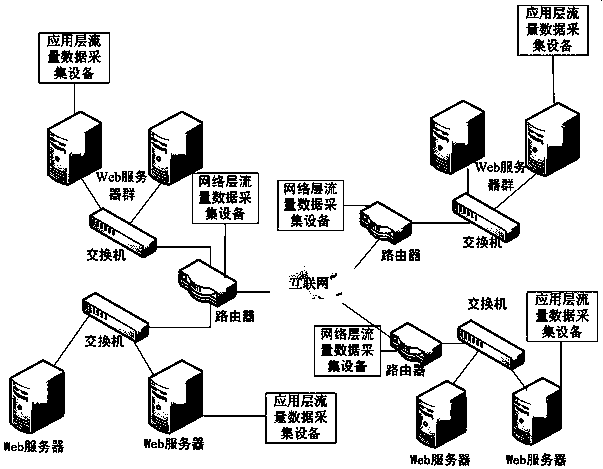
[0042] Step 1: Deploy traffic data collection equipment at network traffic convergence nodes;
[0043] Step 2: Extract network behavior characteristic values from the collected traffic data;
[0044] Step 3: Dimensionality reduction and standardization of network behavior feature values;
[0045] Step 4: Determine the normal network behavior eigenvalues,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com