Access control method, device and system
An access control and access control strategy technology, applied in the field of network communication, can solve the problem of inaccessible request access control and so on
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
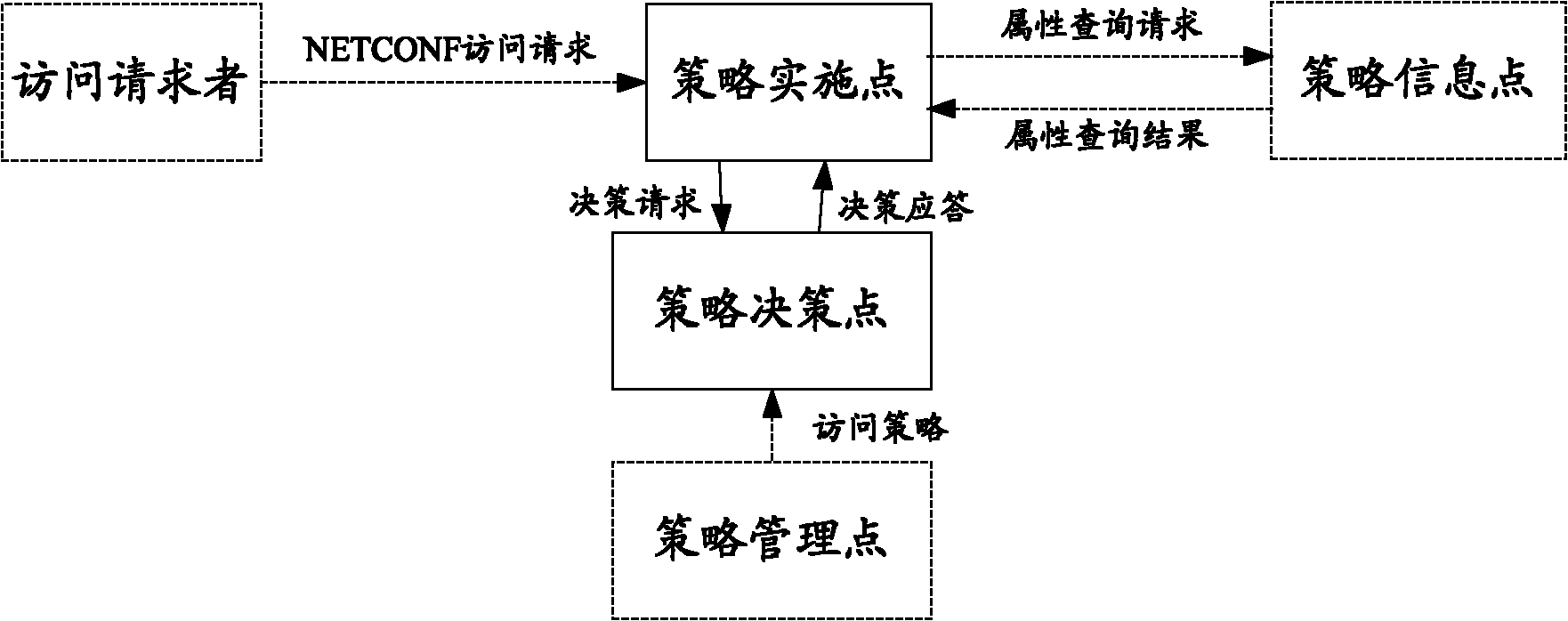
[0022] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings.
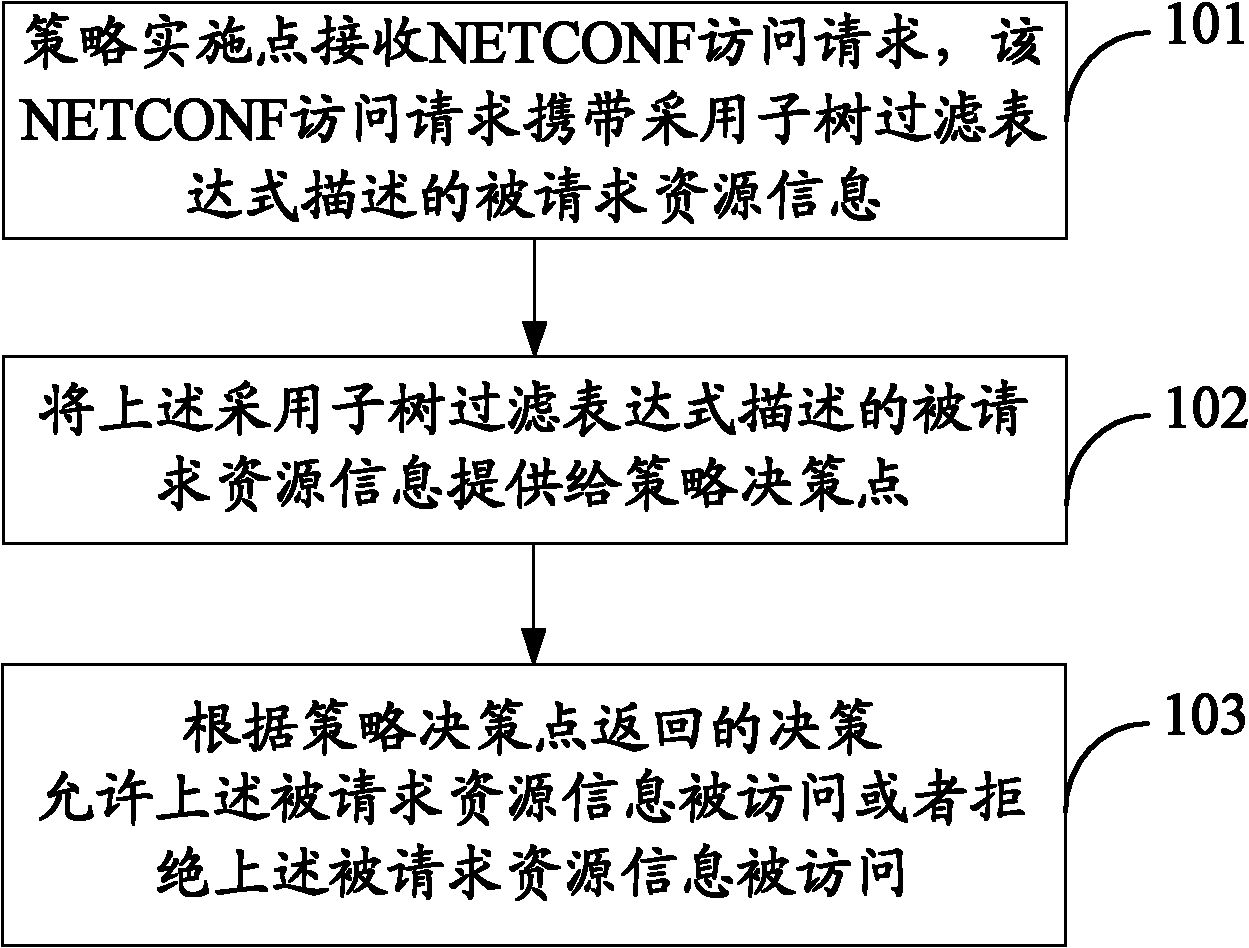
[0023] see figure 1 , an embodiment of the present invention provides an access control method, the method comprising:
[0024] 101: A policy enforcement point (Policy Enforcement Point, PEP) receives a NETCONF access request, and the NETCONF access request carries requested resource information described by a subtree filter expression;
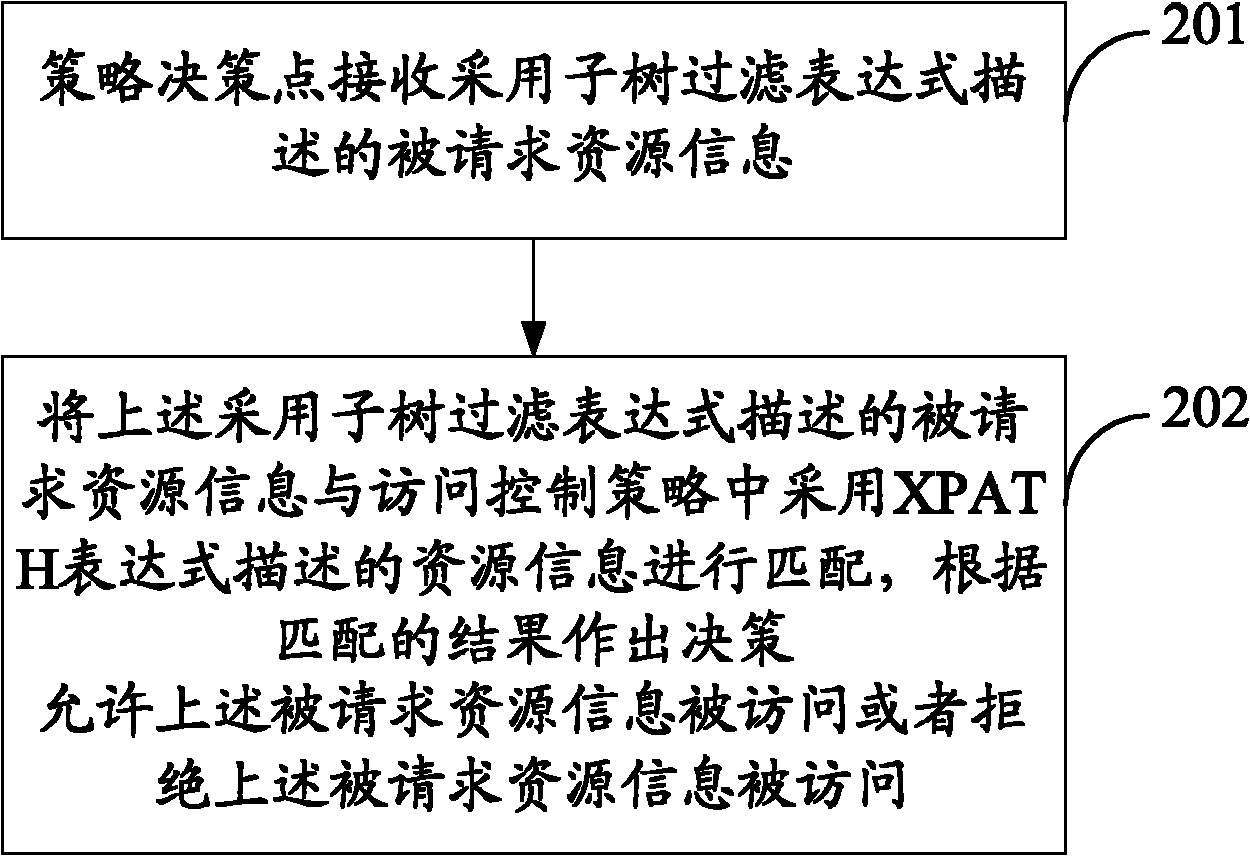
[0025] 102: The policy enforcement point provides the requested resource information described by the subtree filter expression to the policy decision point (Policy Decision Point, PDP), so that the policy decision point can use the requested resource information described by the subtree filter expression Match the resource information described by the XPATH expression in the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com