Method and secure system for authenticating the radio evolution network
A wireless evolution and security system technology, applied in the field of wireless communication system security, can solve problems such as long development time, security mechanism cannot meet the requirements of roaming across access systems, and complex signaling and user data protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
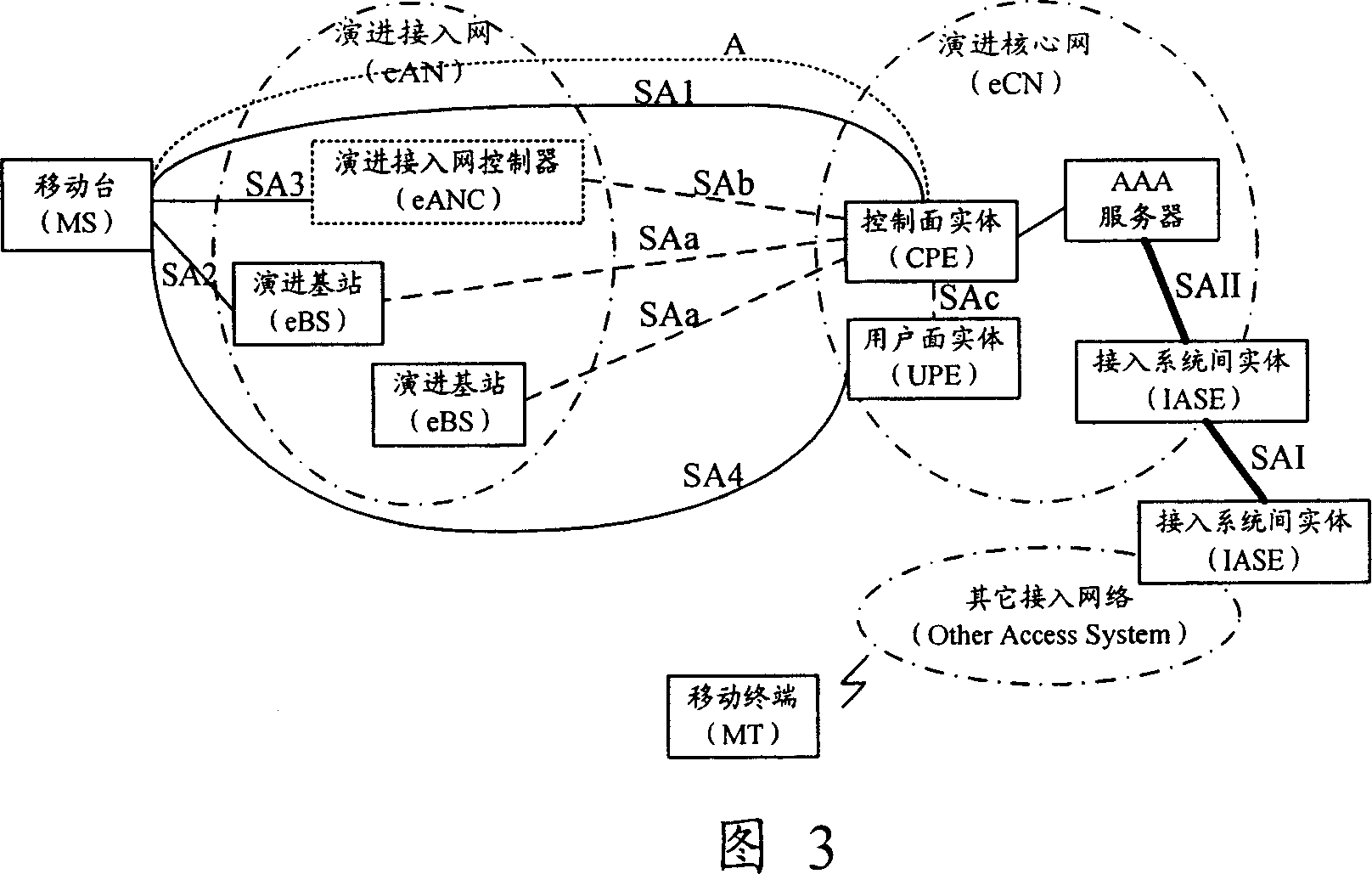
[0089] The core idea of the present invention is: after the mobile station establishes a connection with the wireless evolution access network, the mobile station performs two-way authentication with the wireless evolution network through the core network signaling entity in the wireless evolution core network, and generates a shared key; The station and the core network signaling entity use the generated shared key to establish a security association.
[0090] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the accompanying drawings and preferred embodiments.
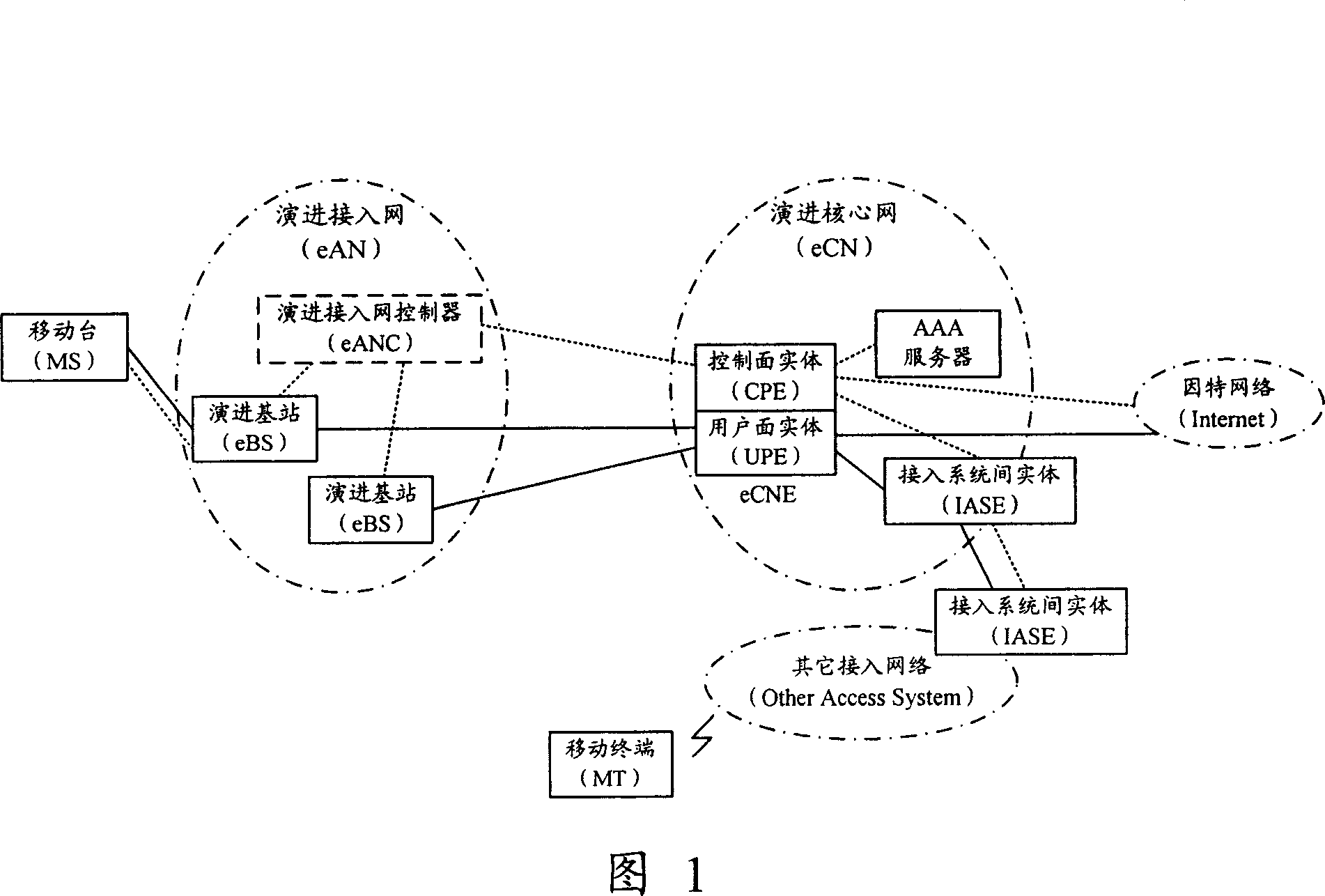
[0091] FIG. 3 is a schematic diagram of the evolved network security system of the present invention. The present invention is described based on the evolved network structure shown in FIG. 1 as an example, but is not limited to be applied to the evolved network shown in FIG. 1 .
[0092]...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com