Communicating with a machine to machine device
a technology of machine to machine device and communication channel, which is applied in the field of communication channel with machine to machine device, can solve the problems of many machine to machine devices, difficult to reach, and difficult management, and achieve the effect of reducing the data overhead of the m2m device and/or the bootstrapping server, reducing or eliminating unnecessary data transfers
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
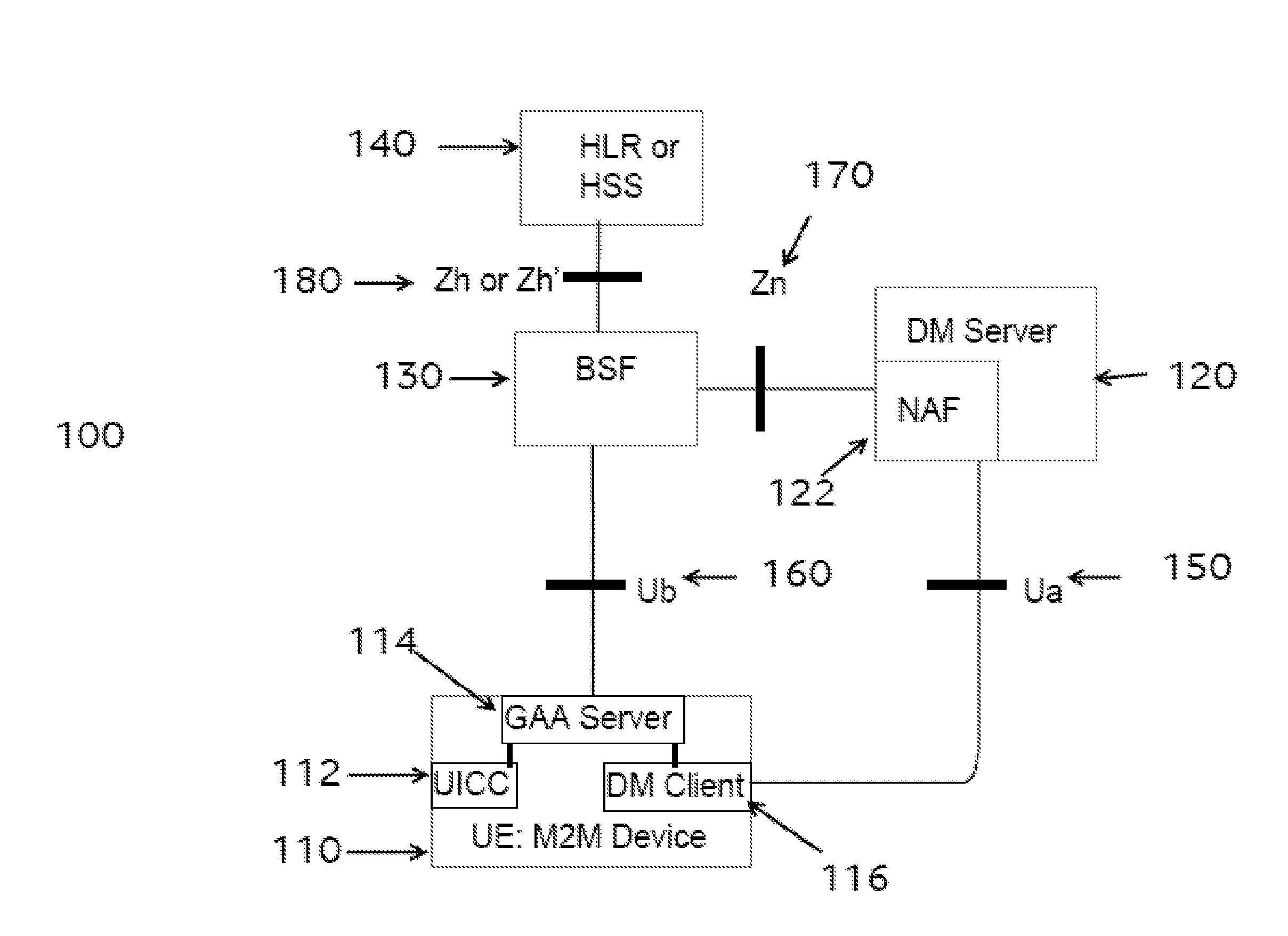
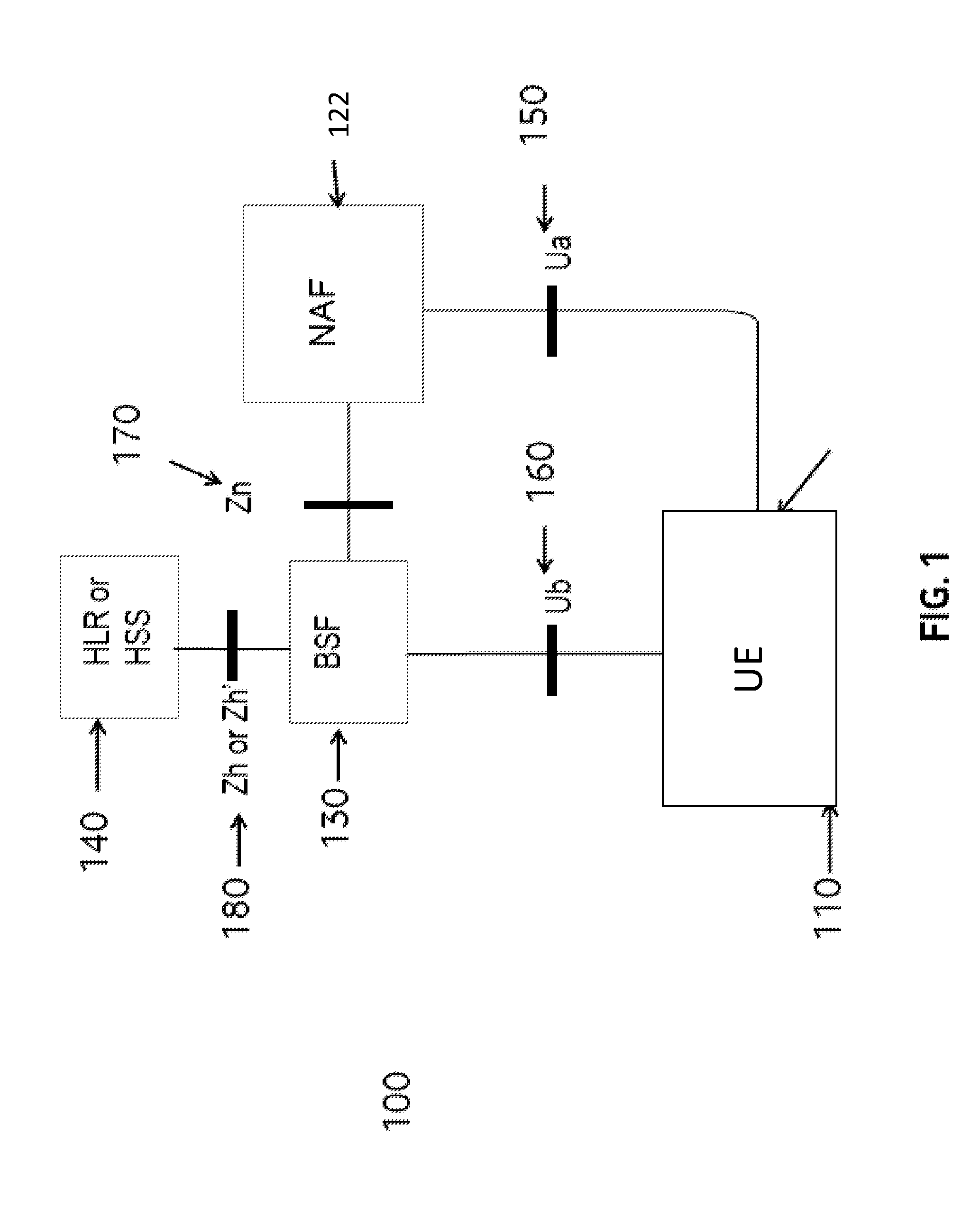
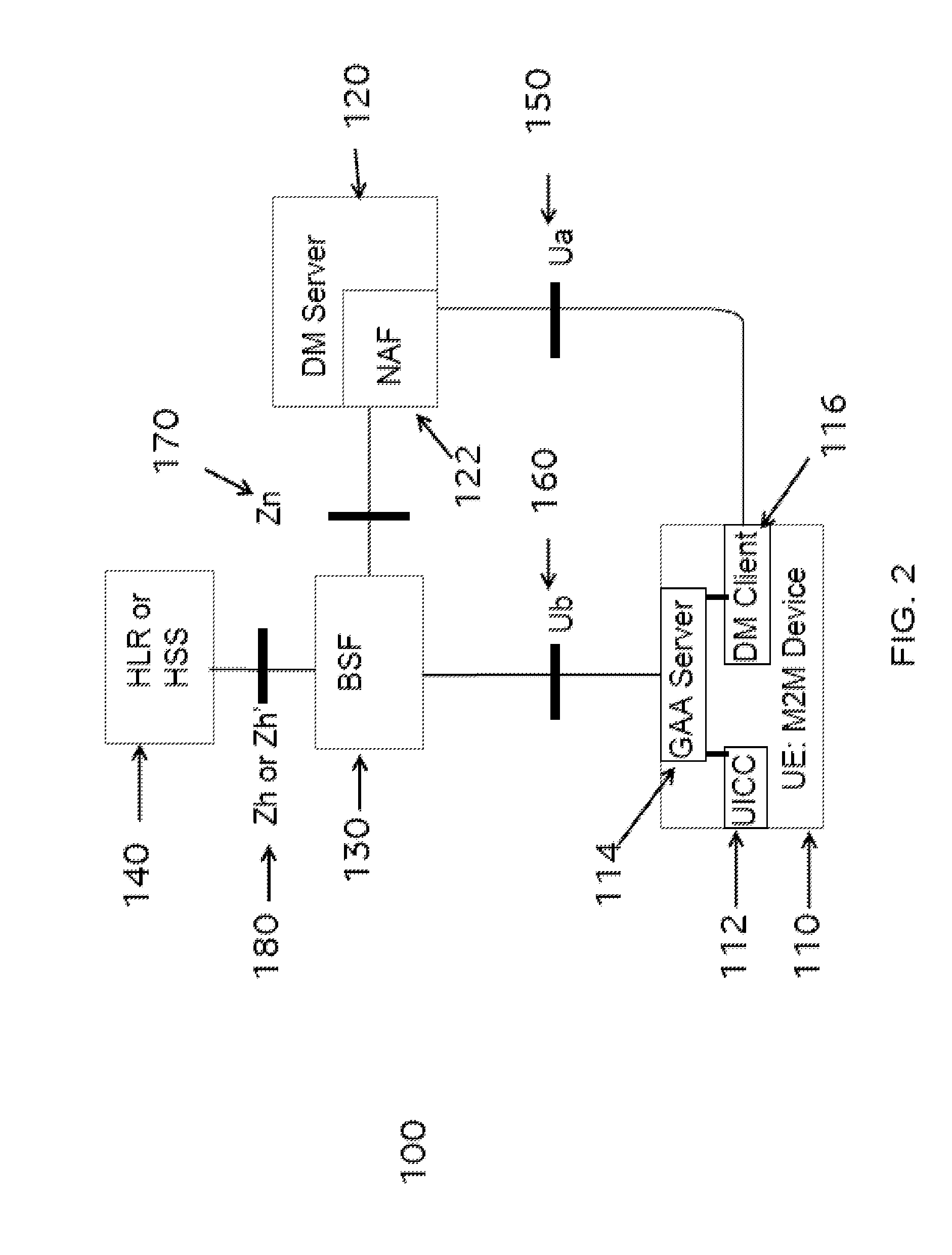
Image
Examples
example object info
[0300]
ObjectObject MultipleObjectIDURNInstances?Mandatory?LWM2M0YesYesSecurity
[0301]Resource Info:
ResourceRange orNameTypeEnumerationUnitsDescriptionsLWM2MString 0-255 bytes—Uniquely identifies theServer URILWM2M Server or LWM2MBootstrap Server, and is in the form: “coaps: / / host:port”,where host is an IP address orFQDN, and port is the UDPport of the Server.BootstrapBoolean—Determines if the currentServerinstance concerns a LWM2MBootstrap Server (true) or astandard LWM2M Server(false)SecurityInteger 0-3—Determines which UDPModechannel security mode is used0: Pre-Shared Key mode1: Raw Public Key mode2: Certificate mode3: NoSec modePublic KeyOpaque—Stores the LWM2M Client'sor IdentityCertificate (Certificate mode),public key (RPK mode) or PSK Identity (PSK mode). The format is defined in Section E.1.1.ServerOpaque—Stores the LWM2M Server's Public Keyor LWM2M Bootstrap or IdentityServer's Certificate (Certificate mode), public key (RPK mode) or PSK Identity (PSK mode). The format is de...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com