Two-factor authentication method, system, medium and server for device identification
A device identification and authentication method technology, applied in the Internet field, can solve the problems of high similarity of devices, indistinguishability, and high false acceptance rate of unique authentication, and achieve the effect of improving the accuracy rate and reducing the false acceptance rate and false rejection rate.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
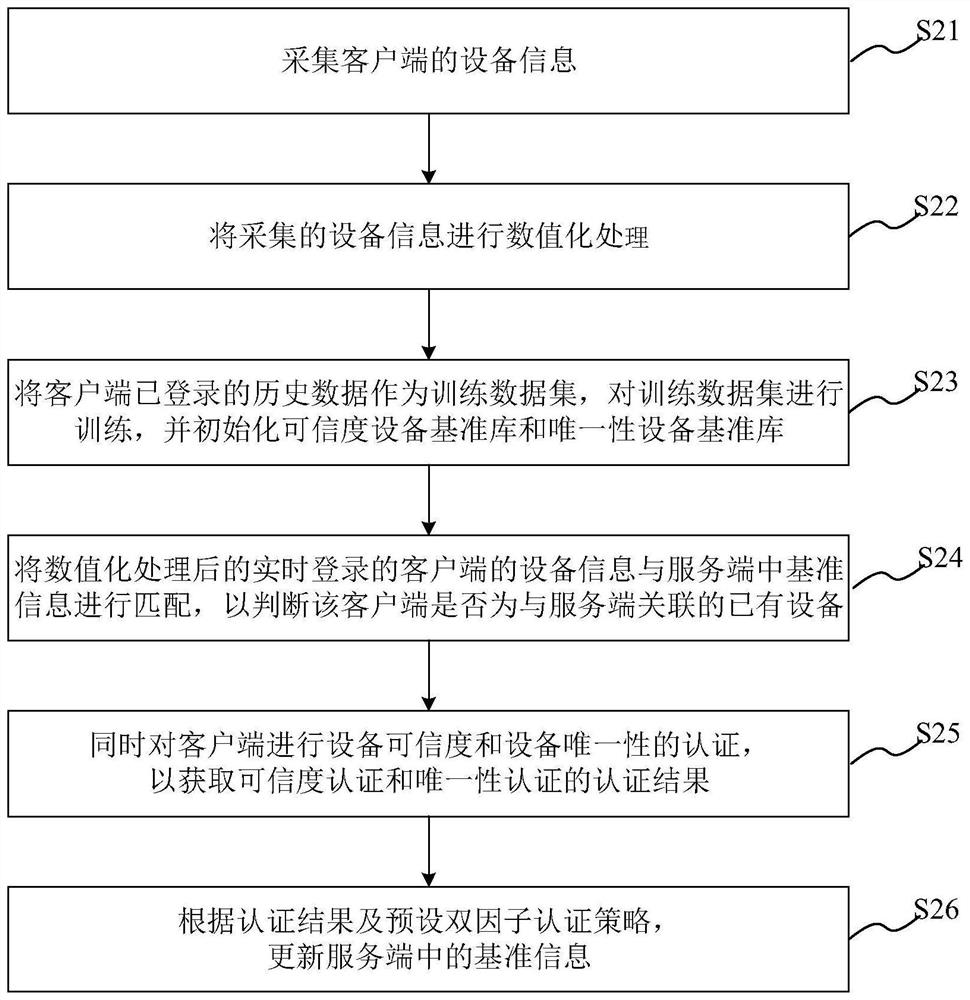
[0028] This embodiment provides a two-factor authentication method oriented to device identification, which is applied to a communication system including at least two clients and a server communicating with the clients; the server is provided with a unique device reference library and Credibility device reference library; the credibility device reference library is used to authenticate the credibility of the client; the uniqueness device reference library is used to authenticate the uniqueness of the client; the device identification-oriented dual Factor authentication methods include:
[0029] collecting device information of the client;
[0030] Matching the real-time logged-in device information of the client with the reference information in the server to determine whether the client is an existing device associated with the server;
[0031] Simultaneously, verifying the credibility and uniqueness of the device on the client, so as to obtain the authentication results of...
Embodiment 2
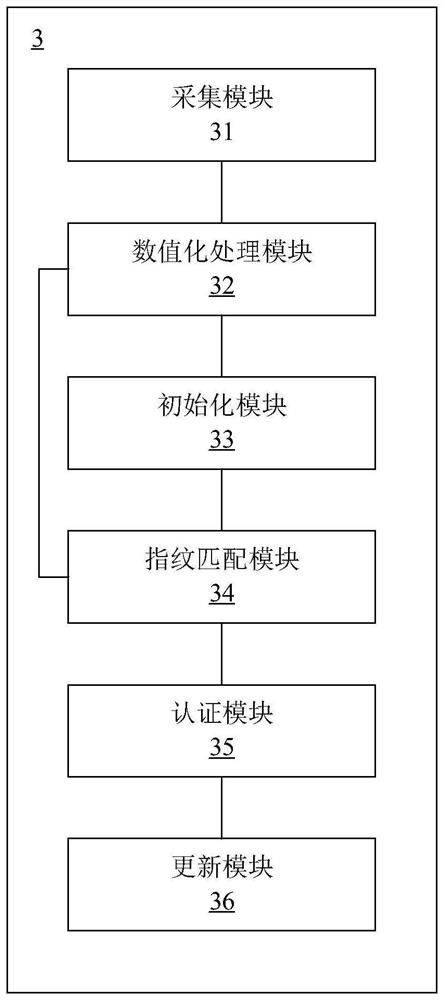
[0076] This embodiment provides a device identification-oriented two-factor authentication system, which is applied to a communication system including at least two clients and a server communicating with the client; the server is provided with a unique device reference library and The credible device reference library; the trusted device reference library is used to authenticate the credibility of the client; the uniqueness device reference library is used to authenticate the uniqueness of the client; comprising:
[0077] A collection module, configured to collect device information of the client;
[0078] A matching module, configured to match the real-time logged-in device information of the client with the reference information in the server to determine whether the client is an existing device associated with the server;
[0079] An authentication module, configured to simultaneously authenticate the client's device credibility and device uniqueness, so as to obtain authe...
Embodiment 3
[0105] This embodiment provides a server, the server includes: a processor, a memory, a transceiver, a communication interface or / and a system bus; the memory and the communication interface are connected to the processor and the transceiver through the system bus and complete mutual communication For communication, the memory is used to store computer programs, the communication interface is used to communicate with other devices, and the processor and transceiver are used to run computer programs, so that the server can execute the steps of the above two-factor authentication method for device identification.
[0106] The system bus mentioned above may be a Peripheral Component Interconnect (PCI for short) bus or an Extended Industry Standard Architecture (EISA for short) bus or the like. The system bus can be divided into address bus, data bus, control bus and so on. For ease of representation, only one thick line is used in the figure, but it does not mean that there is on...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com