Threat information processing method and device, electronic equipment and medium
An information processing method and basic information technology, applied in electrical components, transmission systems, etc., can solve problems such as poor pertinence, and achieve the effect of improving processing efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
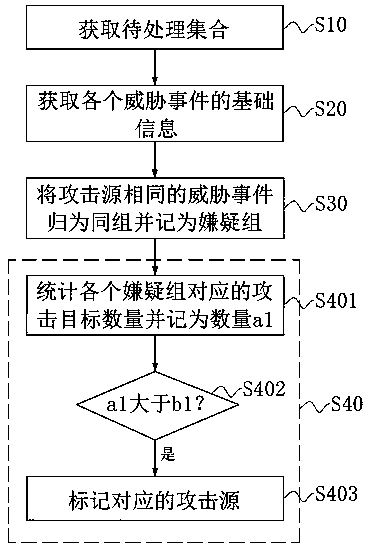
[0043] This embodiment provides a threat information processing method, which aims to solve the problem that it is difficult to make targeted threat prediction for each attack source. Specifically, refer to figure 1 As shown, the threat information processing method specifically includes the following steps S10 to S40.
[0044] In step S10, a set to be processed is acquired, and the event of the set to be processed is recorded as a threat event. Specifically, a process in which an attack source attacks a device in a preset area is an event, and the event is included in the threat information.
[0045] It is worth noting that each event is associated with a corresponding attack type, and a corresponding set is set for the attack type. For example: when the execution device captures a new event, it will attribute the new event to the corresponding set according to the attack type corresponding to the new event.
[0046] The attack types include but are not limited to DDoS att...
Embodiment 2
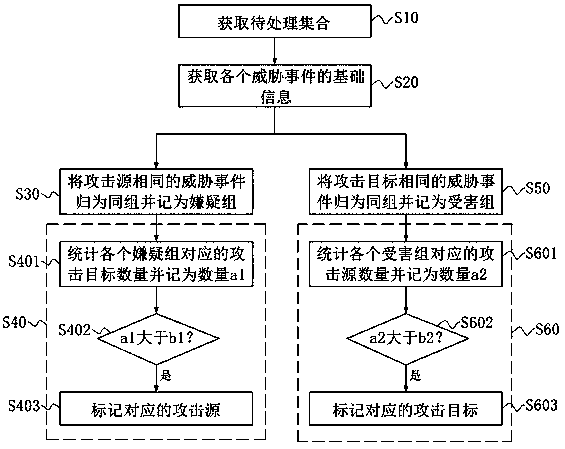
[0060] This embodiment provides a threat information processing method, referring to figure 2 As shown, this embodiment is carried out on the basis of Embodiment 1. Specifically, the threat information processing method further includes the following steps.
[0061] Step S50, group threat events with the same attack target into the same group and record it as a victim group. The threat events in the victim group have the same attack type and the same attack target, so that the corresponding information can be obtained through the analysis of the victim group, so as to make targeted threat predictions for each attack target.
[0062] Specifically, data cleaning is performed on threat data in each victim group, and data cleaning rules can be customized. For example: during data cleaning, remove the data whose attack target is not the specified IP.
[0063] It should be noted that the basic information also includes the occurrence time, and the occurrence time falls within th...
Embodiment 3
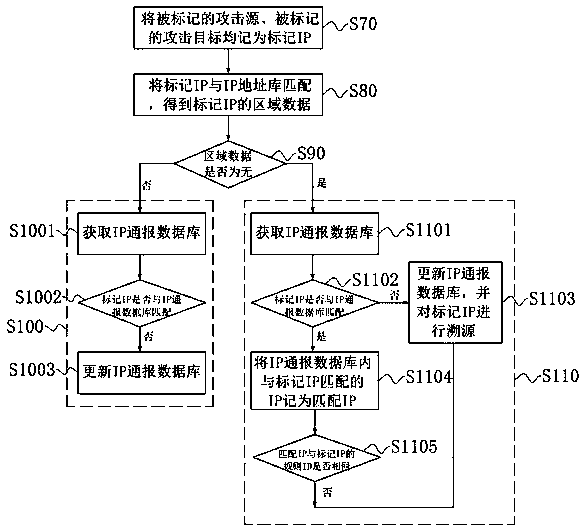
[0069] This embodiment provides a threat information processing method, referring to figure 1 , figure 2 and image 3 As shown, this embodiment is carried out on the basis of Embodiment 1 and / or Embodiment 2. Specifically, the threat information processing method further includes the following steps.
[0070] Step S70, mark the attack source marked in step S403 and the attack target marked in step S603 as marked IP. It is worth noting that the obtained marked IPs can be queued according to preset rules.
[0071] Step S80, matching the marked IP with the IP address database to obtain the area data of the marked IP. It is worth noting that the IPs in the IP address database are associated with regional data, operators, purposes, etc. Wherein, the area data can be None, or it can be a specific volume position.
[0072] Step S90, judging whether the area data is none, if not, execute step S100, enter the processing mode with area; if yes, execute step S110, enter the proces...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com