Privacy protection method for distributed cloud storage system
A cloud storage system and privacy protection technology, applied in the privacy protection field of distributed cloud storage systems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0142] In order to evaluate the performance of the present invention, the time overhead of some algorithms is measured in the following embodiments.
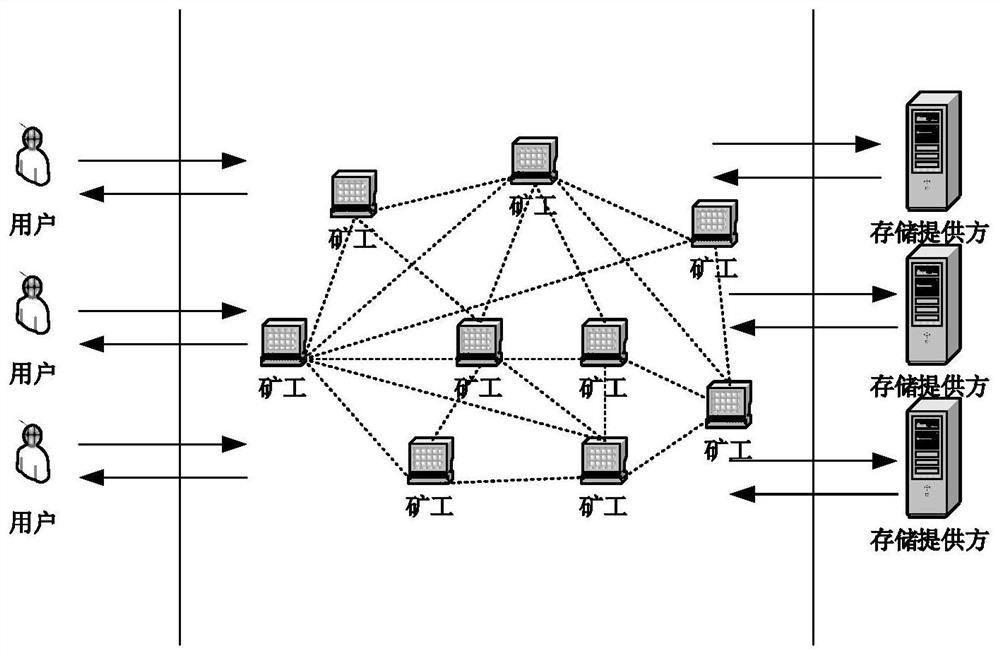
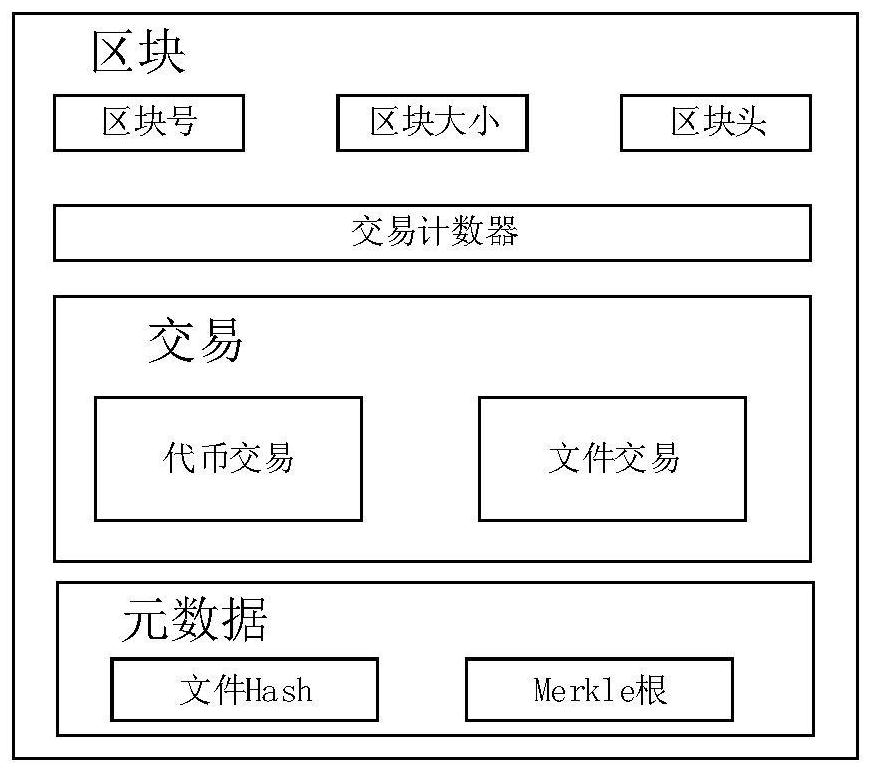
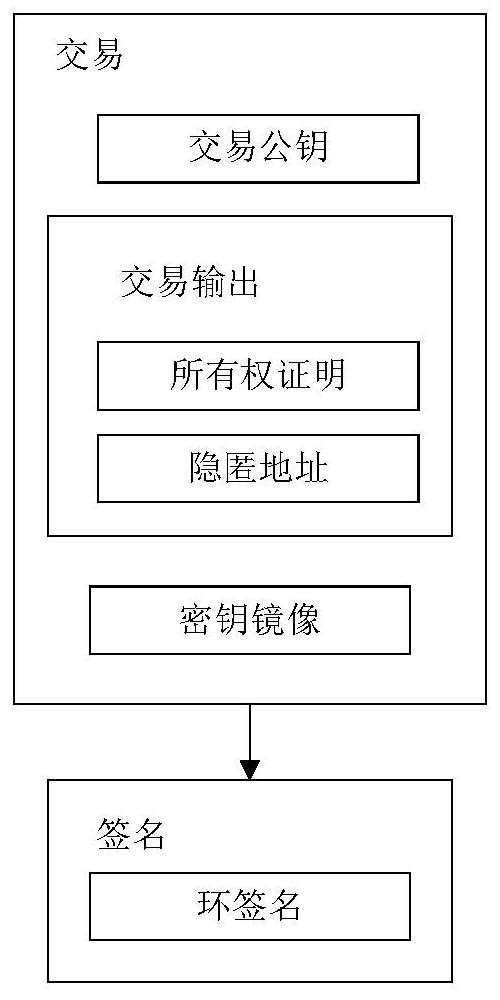
[0143] In order to evaluate the system overhead, the implementation process adopts the open source DigitalNote platform based on the CryptoNote protocol, and completes the implementation of relevant algorithms according to the system requirements. In order to evaluate the system overhead, the test chain experiment environment is deployed locally during the implementation process, among which, three miner nodes and three wallet terminals are deployed locally for experiments, and the time overhead of the main algorithm of the main steps of the system is analyzed, and Measurement of time overhead. Among them, T File Time overhead for client file processing, including file hash operation time, file block operation time, and file block upload time; T Tx The time to generate a transaction operation for the user side, including the t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com