Data encryption method, security chip, and computer readable storage medium
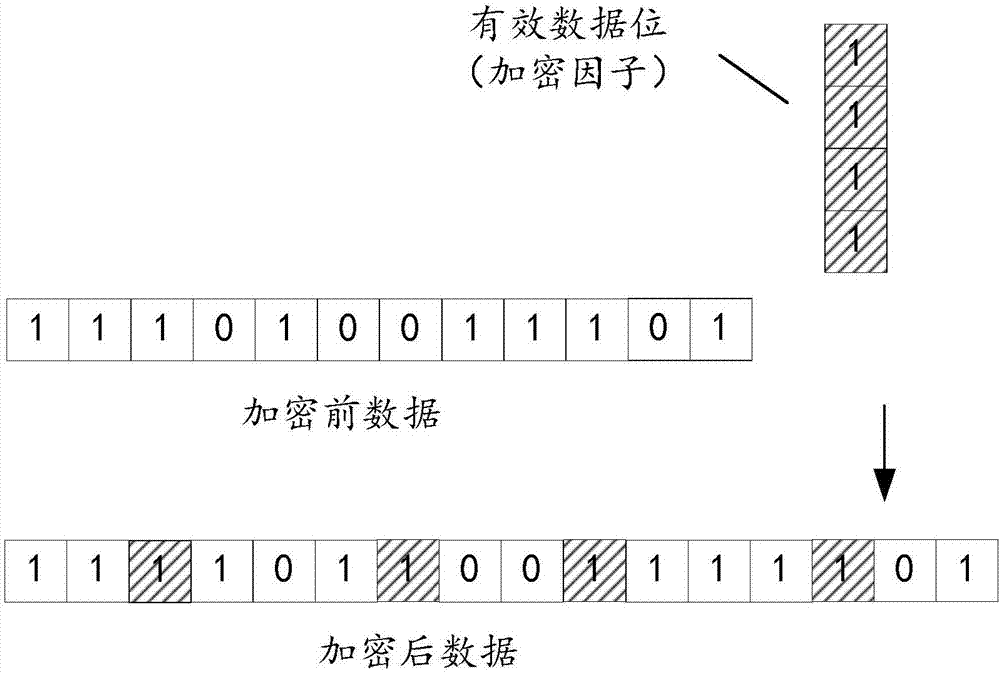
A data encryption and security chip technology, applied in the field of information security, can solve the problems of easy decryption of encrypted data, achieve the effect of increasing the difficulty of cracking, facilitating decryption, and ensuring information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0043] Such as figure 1 as shown, figure 1 It is a schematic diagram of the security chip component modules of the hardware operating environment involved in the solution of the embodiment of the present invention.
[0044] The security chip may include: a processor module 1001 , such as a CPU, a storage module 1002 , and a data monitoring module 1003 . Among them, the data monitoring module 1003 is used to monitor the situation of data transmission, and feed back the data transmission situation to the processor module 1001, and trigger the processor module 1001 to make corresponding instructions, and the data monitoring module 1003 can also call the storage module 1002 to call or / and storage operations, the data monitoring module 1003 may include a counter, or other elements that can realize the above functions. ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com