Cloud computing environment oriented cognitive intrusion detection method
A cloud computing environment and intrusion detection technology, applied in the field of cloud computing, can solve problems such as inability to judge and prevent security attacks in time, high risk factor of the system, etc., and achieve the effect of enhanced computing ability and strong detection ability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
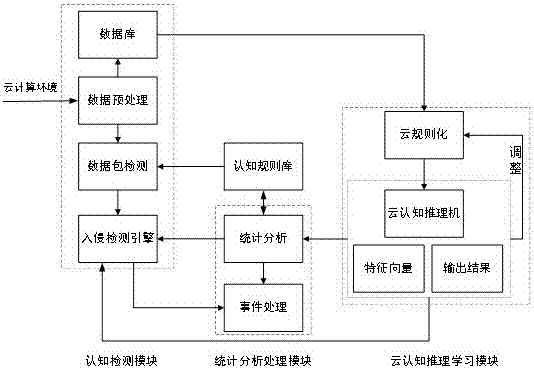
[0041] Such as figure 1As shown, the cloud computing-oriented intrusion detection system with cognitive capabilities includes a cognitive detection module: data preprocessing is responsible for collecting data streams in the network and generating data stream files in a certain format. Data packet detection performs packet detection on the preprocessed data flow, and judges whether the data flow is a known attack form according to the established cognitive rule base, and establishes an attack signature that meets certain rules for the known attack. Including processing method, transport layer protocol type, application layer protocol type, port number, IP address range, remarks, etc.
[0042] Cloud cognitive reasoning learning module: The cloud reasoning learning module evaluates the possibility of intrusion. The input of the reasoning machine is divided into two parts: one part is during intrusion detection (online judgment), and the collector provides the collected network ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com