Terminal data transmission method and device
A data transmission and terminal technology, applied in the computer field, can solve problems such as potential safety hazards
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
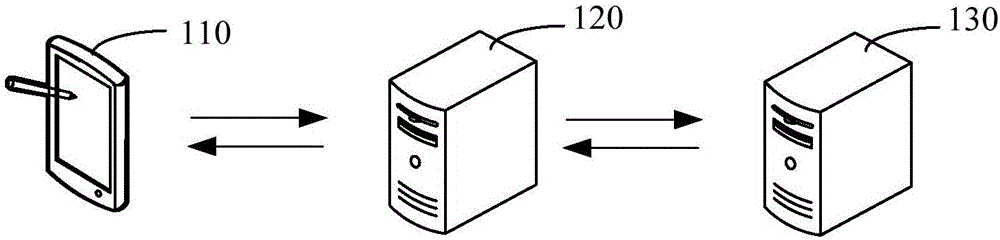
[0025] figure 1 A graph of the application environment running for a data transfer method. Such as figure 1 As shown, the application environment includes a terminal 110, a transfer server 120, and a first server 130, wherein the terminal 110, the transfer server 120, and the first server 130 communicate through a network.
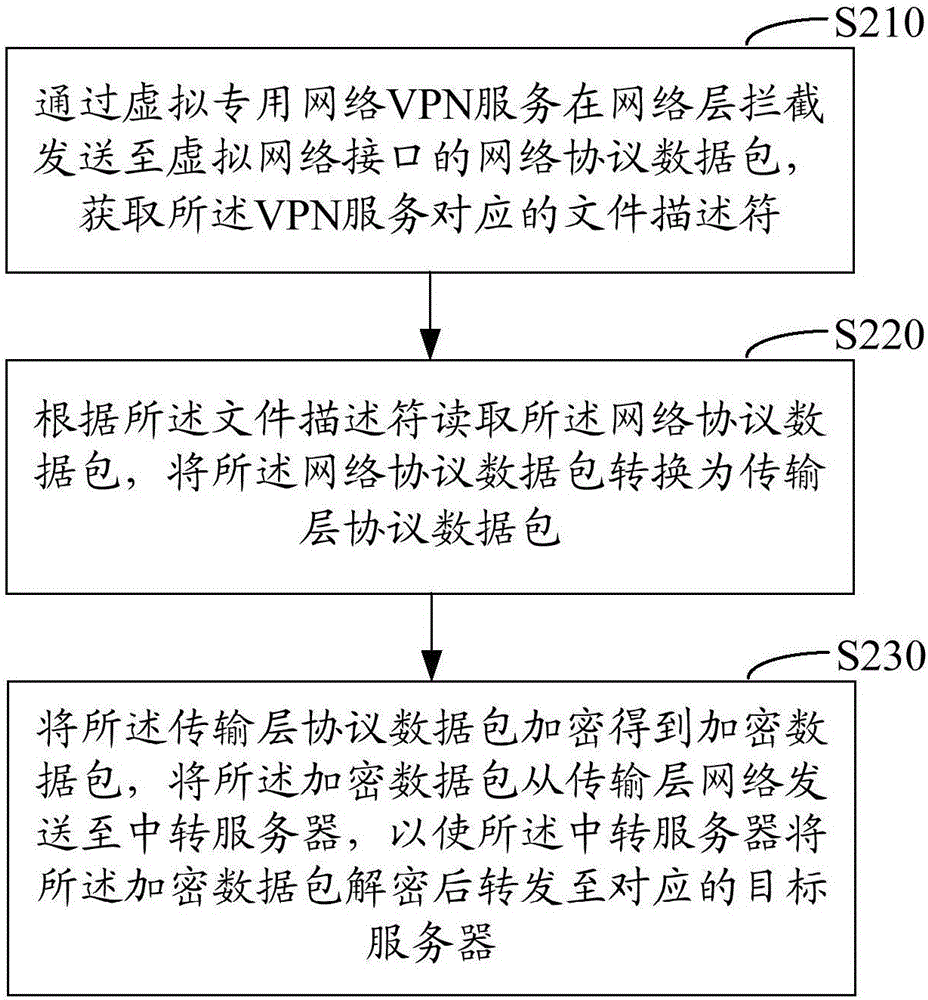
[0026] The terminal 110 may be a smart phone, a tablet computer, a notebook computer, a desktop computer, etc., but is not limited thereto. The terminal 110 converts the network protocol IP data packet sent from the virtual network interface into a transport layer protocol data packet through the VPN service and encrypts it, then sends it from the transport layer network to the transit server 120, and the transit server 120 decrypts it and sends it to the first server 130. The VPN service intercepts IP data packets and converts them into transport layer protocol data packets. The data packets can be encrypted and sent from the transport layer network to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com