Reinforcing method and device for executable files
A technology for executing files and files, which is applied in the field of information security, can solve problems such as user data being stolen, and achieve the effects of preventing user data from being stolen, improving operating efficiency, and preventing malicious instructions from being implanted
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
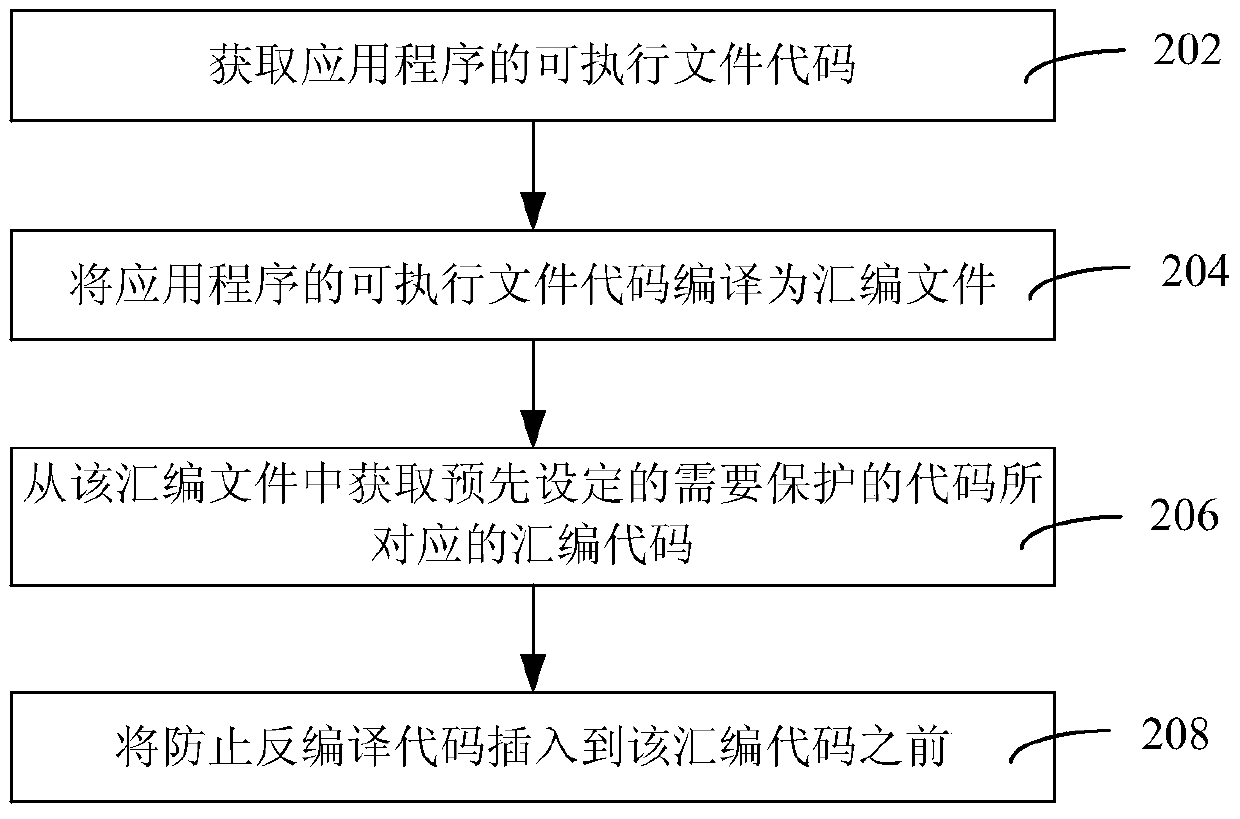
Method used
Image
Examples
Embodiment Construction
[0025] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0026] It can be understood that the terms "first", "second" and the like used in the present invention can be used to describe various elements herein, but these elements are not limited by these terms. These terms are only used to distinguish one element from another element. For example, a first client could be termed a second client, and, similarly, a second client could be termed a first client, without departing from the scope of the present invention. Both the first client and the second client are clients, but they are not the same client.
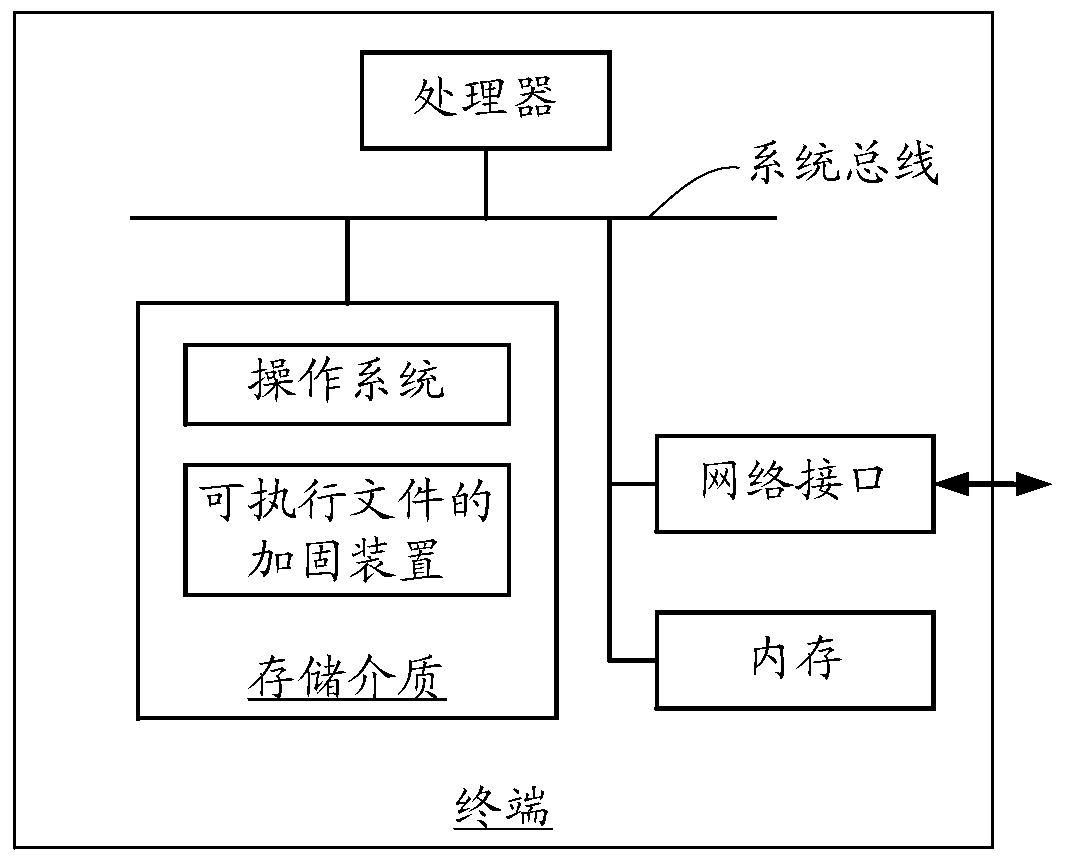
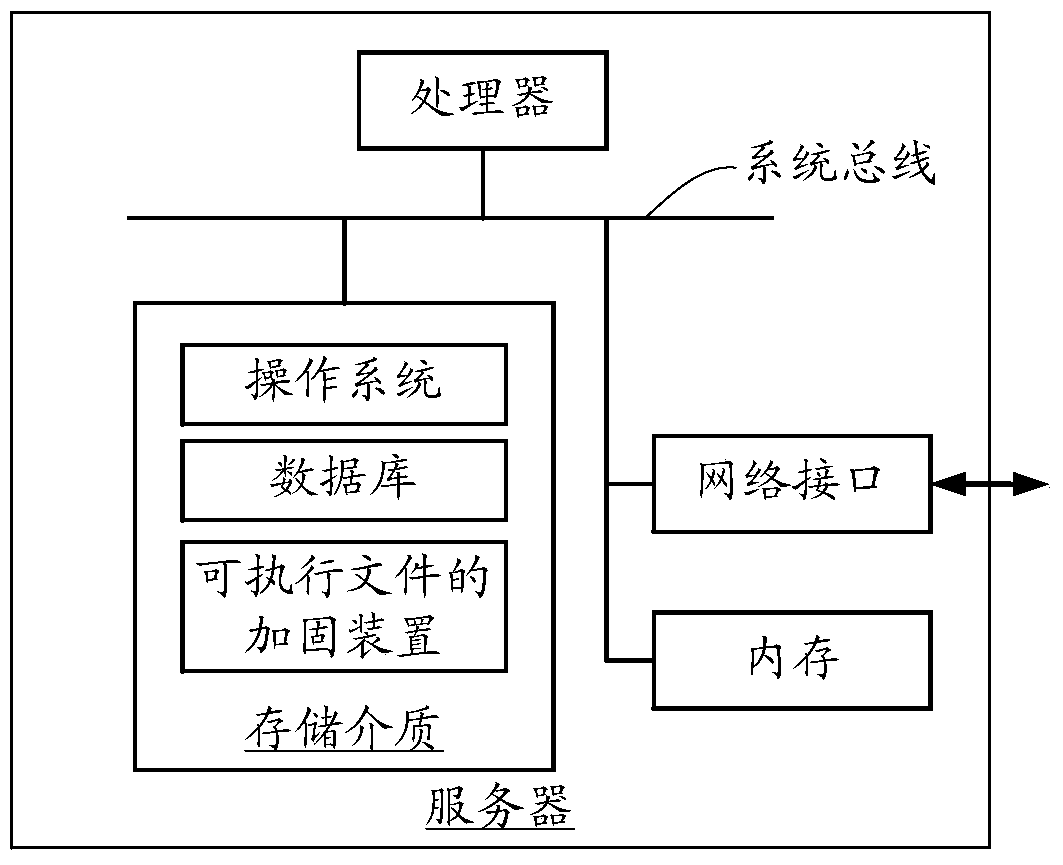
[0027] Figure 1A It is a schematic diagram of ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com