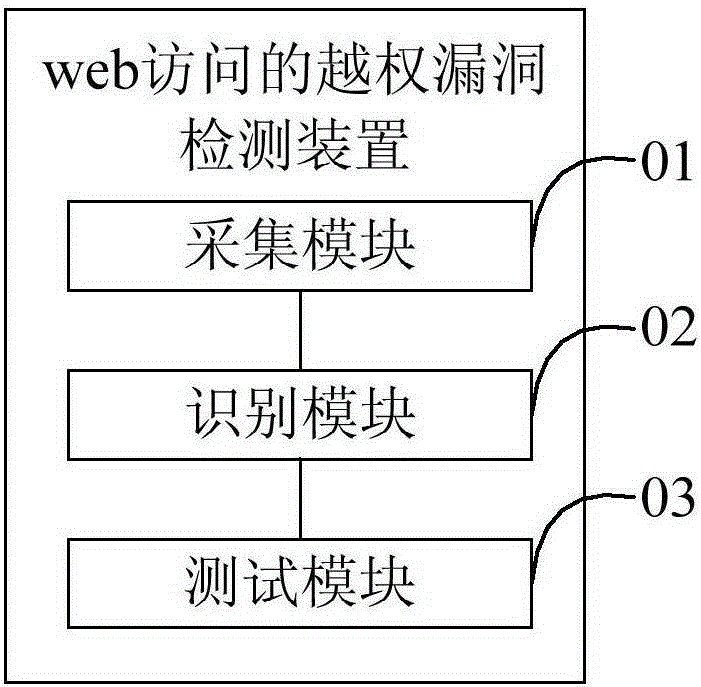
Unauthorized web access vulnerability detecting method and device
A vulnerability detection and vulnerability technology, applied in the field of network security, can solve the problems of user sensitive information leakage, URL unauthorized vulnerability, labor consumption, etc., and achieve the effect of improving detection efficiency and high recognition rate.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0046] The invention provides a method for detecting an unauthorized loophole in web access.
[0047] refer to figure 1 , figure 1 It is a schematic flowchart of the first embodiment of the web access unauthorized vulnerability detection method of the present invention.
[0048]In the first embodiment, the method for detecting an unauthorized vulnerability of web access includes:
[0049] Step S10, collecting HTTP traffic information to be detected within a preset time, the HTTP traffic information including URL parameter information and session identifiers, wherein the URL parameter information includes URL parameters and parameter values;
[0050] In this embodiment, when it is necessary to detect an unauthorized loophole in web access, the hypertext transfer protocol (HyperTextTransferProtocol, referred to as HT...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com