Identity traceability authentication method and system
A technology of identity authentication and authentication method, applied in the direction of user identity/authority verification, transmission system, security device, etc., to achieve the effect of improving security and convenience, enhancing credibility, and repairing potential security risks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0067] The technical solutions of the present invention will be described in further detail below with reference to the accompanying drawings and embodiments.
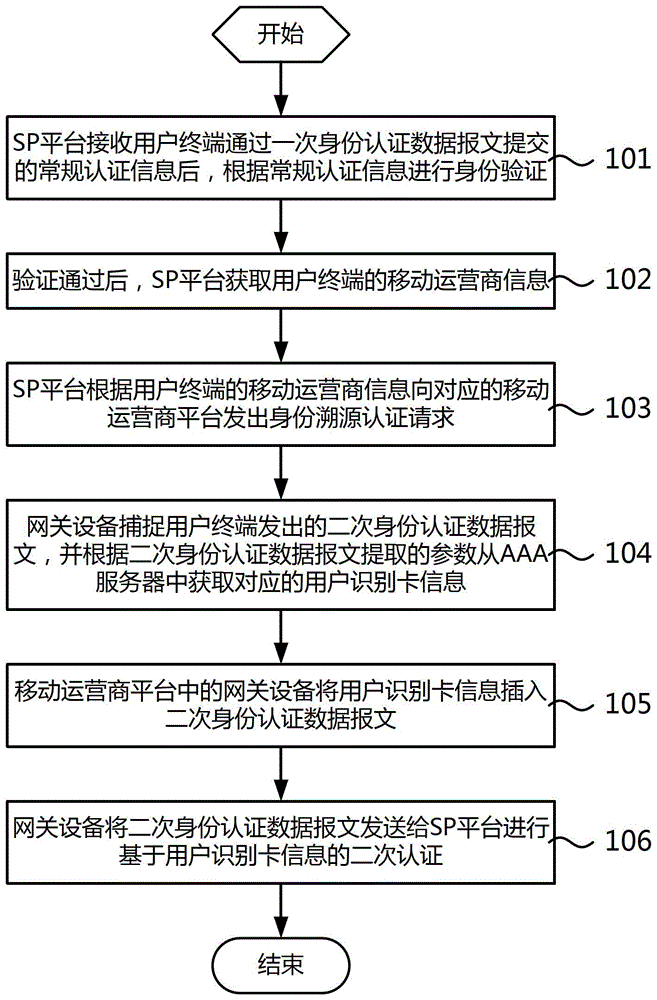
[0068] Such as figure 1 As shown, it is a schematic flowchart of an embodiment of the identity traceability authentication method of the present invention. In this embodiment, the identity traceability authentication process includes:
[0069] Step 101, after receiving the regular authentication information submitted by the user terminal through an identity authentication data message, the SP platform performs identity verification according to the regular authentication information;
[0070] Step 102, after the verification is passed, the SP platform obtains the mobile operator information of the user terminal;
[0071] Step 103, the SP platform sends an identity traceability authentication request to the corresponding mobile operator platform according to the mobile operator information of the user terminal, and th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com