Authentication and secure channel setup for communication handoff scenarios
A communication layer and continuous communication technology, applied in the direction of security devices, wireless communication, electrical components, etc., can solve problems such as seamless switching difficulties
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment approach
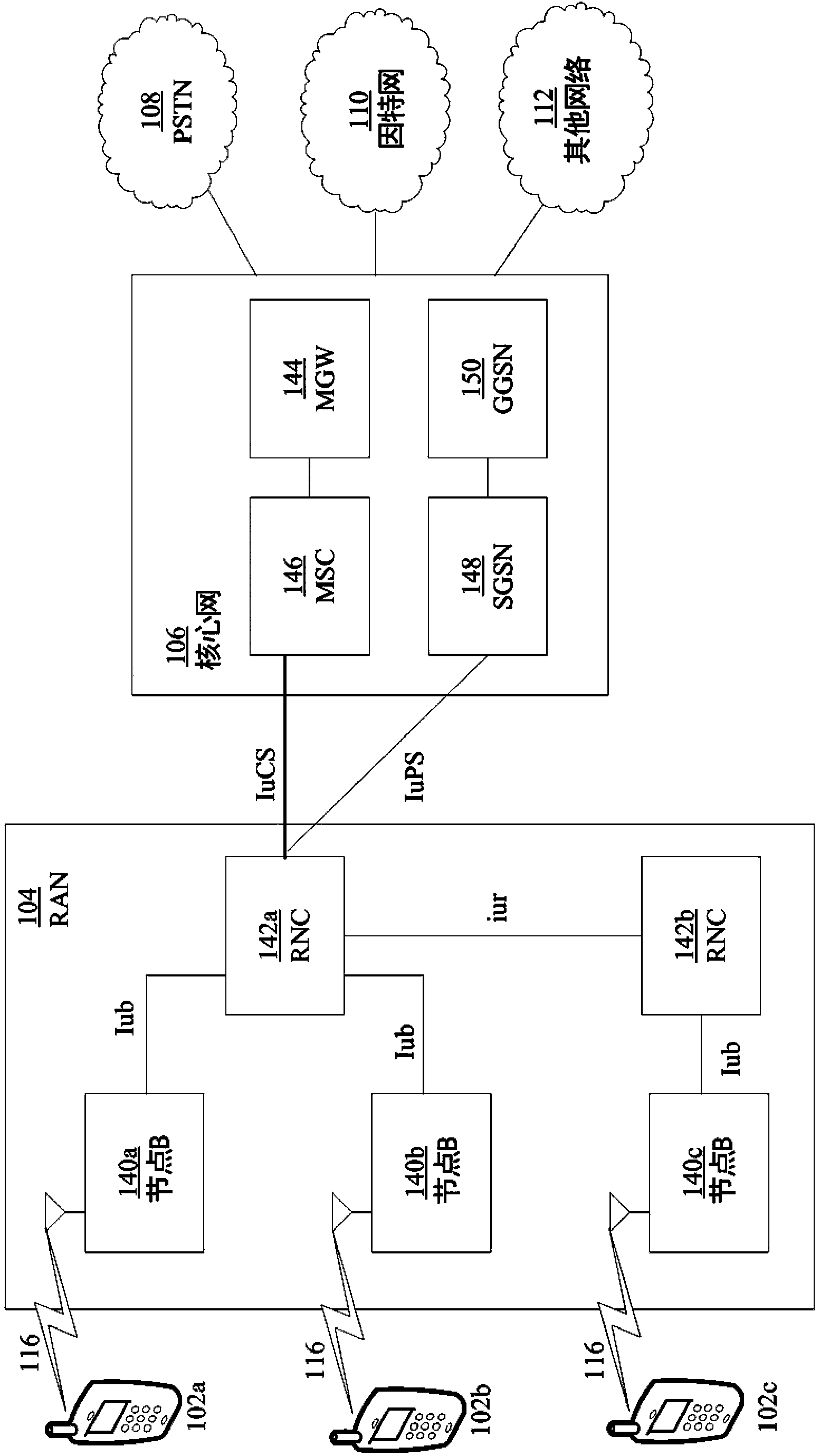
[0098] According to one embodiment, if application-layer security is to be re-established after a handover (e.g., an access-layer handover), binding the security credentials used for such subsequent application-layer authentication to the Forward bootstrapping of security credentials such as those used in handover access layer authentication, certificates used in previous application layer authentication, or even pre-handover access layer authentication.
[0099] In the embodiments described herein, independent identity providers may be used. For example, MNO A 323 may not be an OpenID identity provider and / or identity management functions may be performed by another third party. A third-party identity provider may use a pre-established relationship with the MNO A 323 to act in the role of an OpenID Provider, and use a protocol such as OpenID / EAP-SIM or OpenID / GBA bootstrapping capabilities to provide access stratum credentials 330 from the MNO A 323 Authenticate and Bootstra...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com