Security management system and method of dependable computing platform
A technology of security management and trusted computing, applied in the field of information security, it can solve the problems of tampering with security policies, destroying security management centers, attacks, etc., so as to ensure authenticity and integrity, prevent leakage, and ensure confidentiality and integrity. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] Below in conjunction with accompanying drawing of description, specific embodiment of the present invention is described:
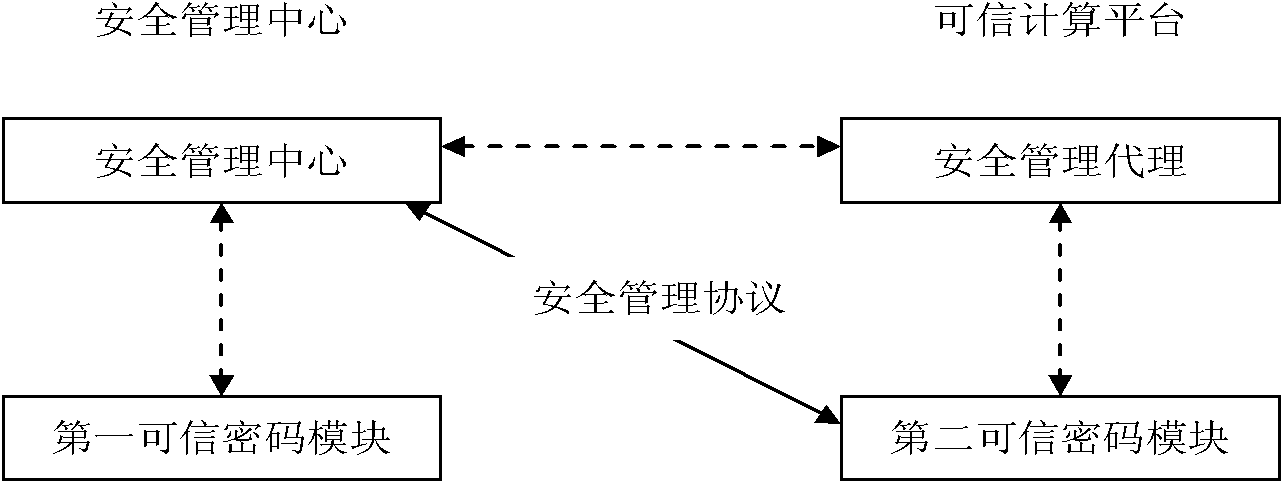
[0038] see figure 1 Shown is a schematic structural diagram of the security policy management system of the present invention. It can be seen from the figure that the structure of the security policy management system consists of a security management center, a first trusted cryptographic module, a second trusted cryptographic module, and a security management agent.
[0039] The first trusted cryptographic module provides signature and signature verification, symmetric encryption and decryption and hash operation services for the security management center.
[0040] The security management center calls the first trusted cryptographic module service to realize the generation, storage and deletion of the security policy; calls the first trusted cryptographic module service to realize the assembly of the security policy management protocol data, and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com