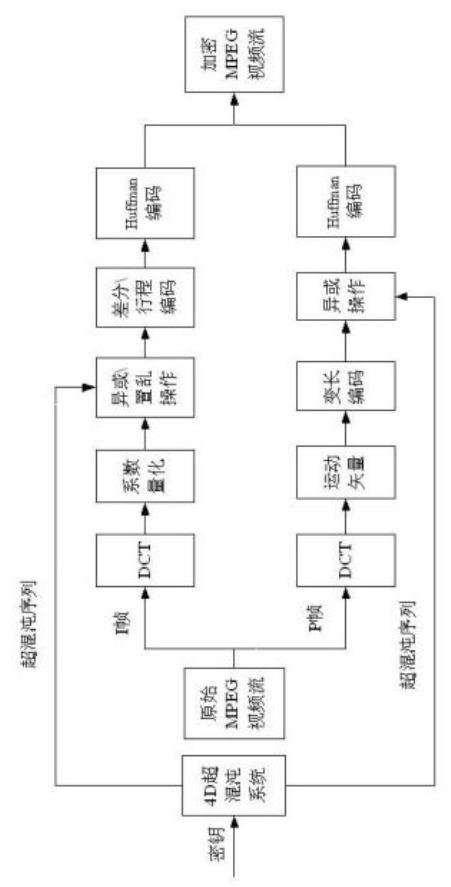
Method for encrypting video streaming information based on hyper-chaotic sequence
An information encryption and hyperchaotic technology, applied in the field of information security, can solve the problems of mutual restriction between encryption algorithm security and encryption speed, and inability to achieve real-time performance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0042] The following example to achieve
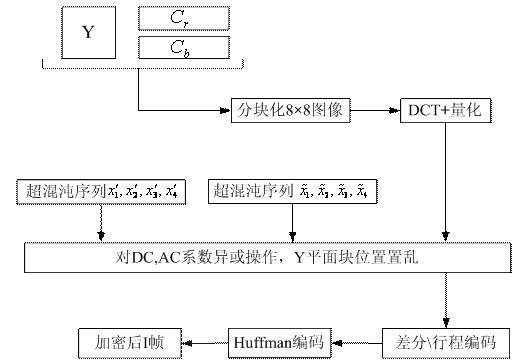
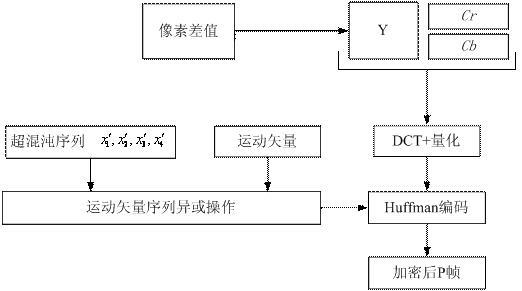
[0043]1, MPEG video stream I frame image is divided into 8 * 8 tiles, use formula (1) to carry out discrete cosine transform to each tile, obtain AC, DC coefficient after quantization;
[0044] 2. Take the initial value x of the hyper-chaotic system 1 (0)=x 2 (0)=x 3 (0)=x 4 (0)=0.1 as the external key, use the fourth-order Runge-Kutta method to iterate the hyperchaotic system for 200000 times, and obtain the hyperchaotic sequence x 1 , x 2 , x 3 , x 4 , use formula (3) to carry out numerical processing on the hyperchaotic sequence, and obtain x′ 1 , x′ 2 , x′ 3 , x′ 4 ; Calculate the m value according to formula (4), select the combination of chaotic sequences;
[0045] 3. The k calculated according to the formula (6) is used as the internal key to change the initial value of the hyper-chaotic system to obtain a new hyper-chaotic sequence
[0046] 4. Use x' 1 , x′ 2 , x′ 3 , x′ 4 The sequence performs XOR operation o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com