Safe startup method for Linux embedded system
An embedded system and secure startup technology, which is applied in the direction of program loading/starting, program control devices, etc., can solve the problems of not enough to ensure the security of data information in the file system, and achieve the effect of ensuring confidentiality and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
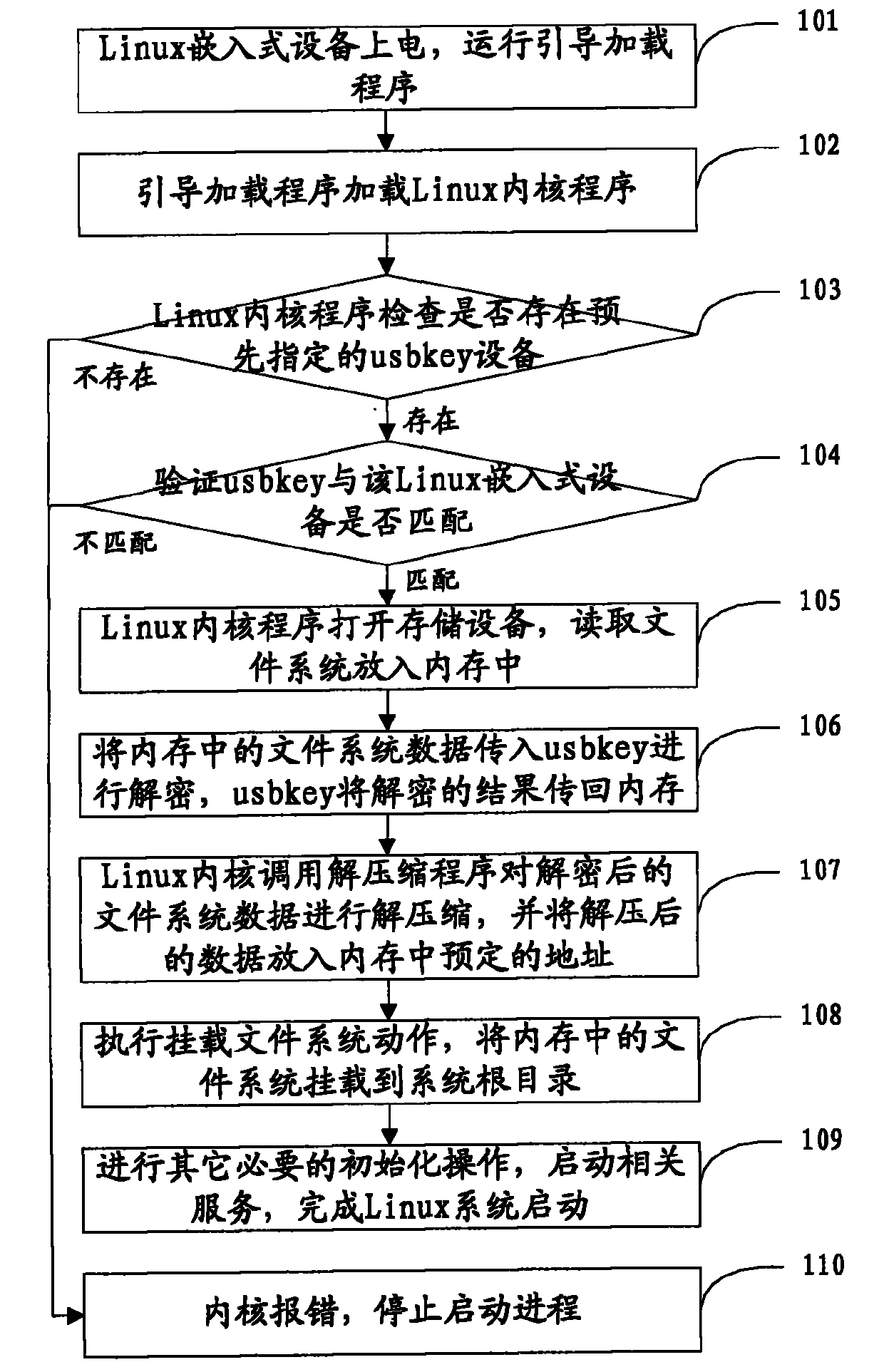
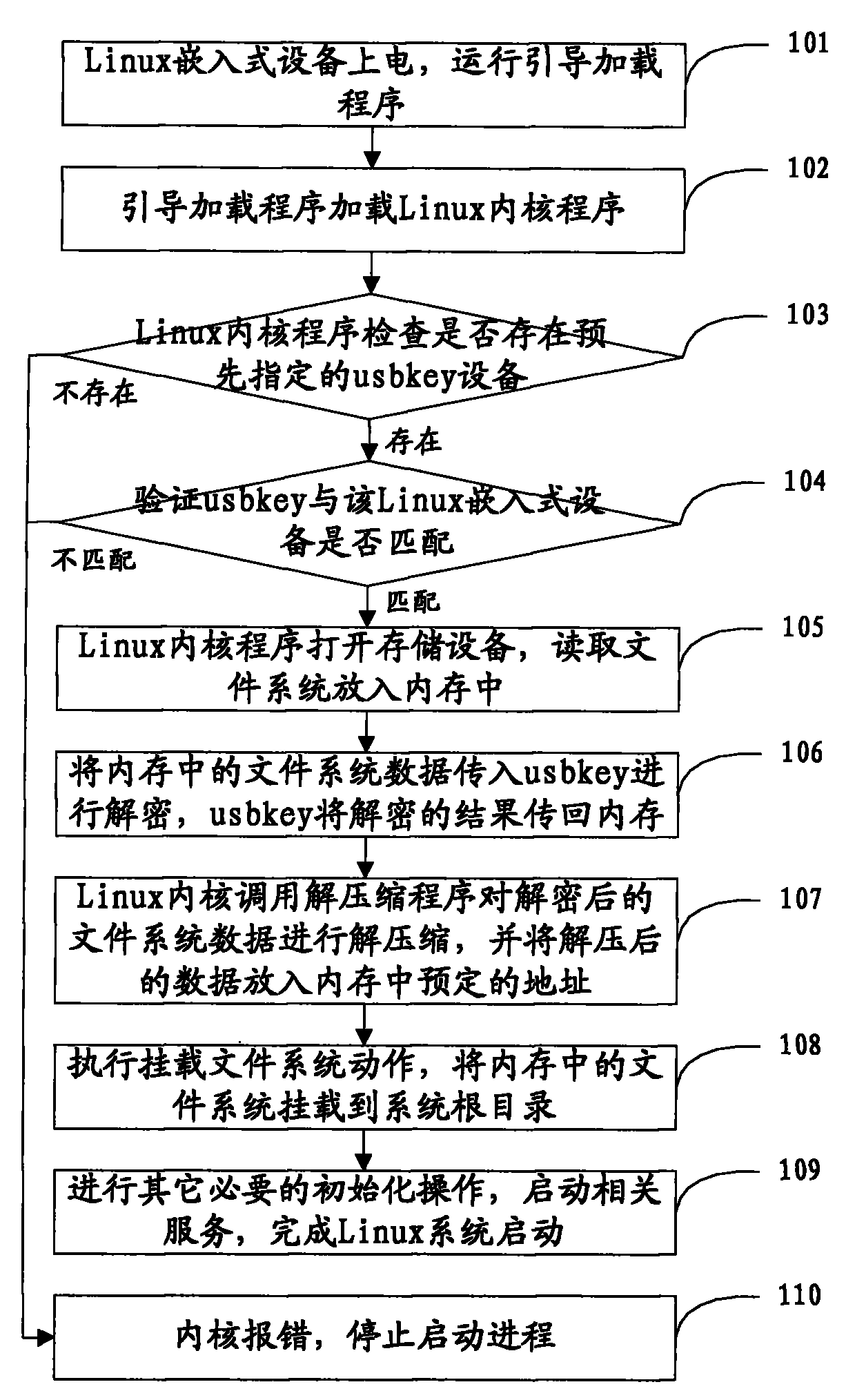
[0060] see figure 1 , the present embodiment adopts at91rm9200 development board, Linux kernel Linux-2.4.19-rmk7, uses usbkey to illustrate as encryption and decryption equipment, provides a kind of secure startup method of Linux embedded system, and this method comprises:
[0061] Step 101. The Linux embedded device is powered on, and the boot loader U-BOOT is run;
[0062] The bootloader is the first piece of code that runs after the Linux embedded device is powered on, and it includes two parts: the boot code (optional) and the BootLoader that are solidified in the firmware (firmware);
[0063] The boot loader is used to initialize hardware devices and establish a memory space map, thereby bringing the system's hardware and software environment to a suitable state, so as to prepare the correct environment for calling the Linux embedded system kernel.
[0064] In the embodiment of the present invention, the boot loader of the embedded device used does not contain boot code,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com