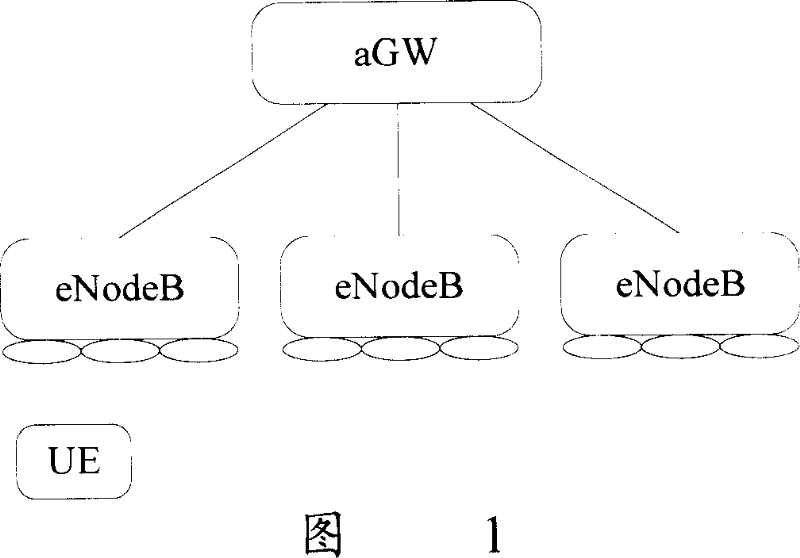
Method for realizing safety warranty in evolution accessing network
A network access and security technology, applied in the field of security assurance, can solve problems such as being attacked, vulnerable to malicious attacks, and data packet loss
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
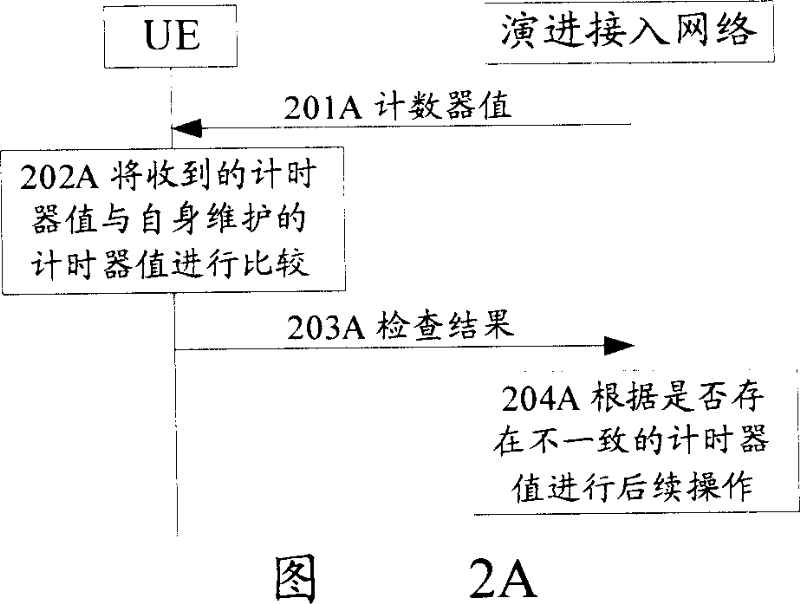
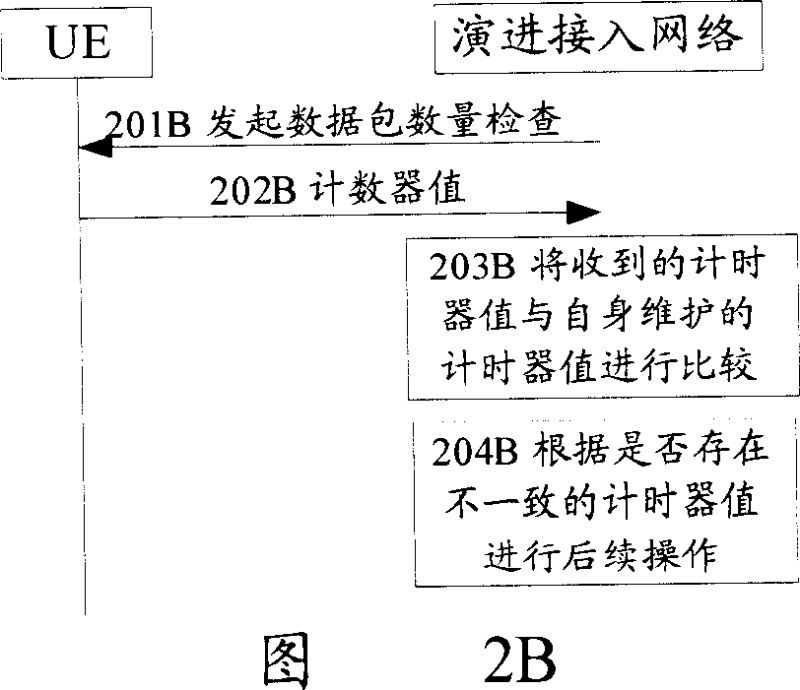
[0035] In the present invention, the UE and the evolved access network respectively maintain one or more counters, and the counter values are used to indicate the amount of data transmitted between the UE and the evolved access network, that is, the counter value varies with the distance between the UE and the evolved access network. When the set conditions are satisfied, the evolved access network initiates a data volume check to the UE, and the UE or the evolved access network compares the counter value provided by the opposite end with the counter value maintained by itself. The evolved access network performs subsequent processing according to the checking result of whether there are counters with inconsistent values.
[0036] The counter mentioned above can...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com