Cryptographic key generation method and system based on identity
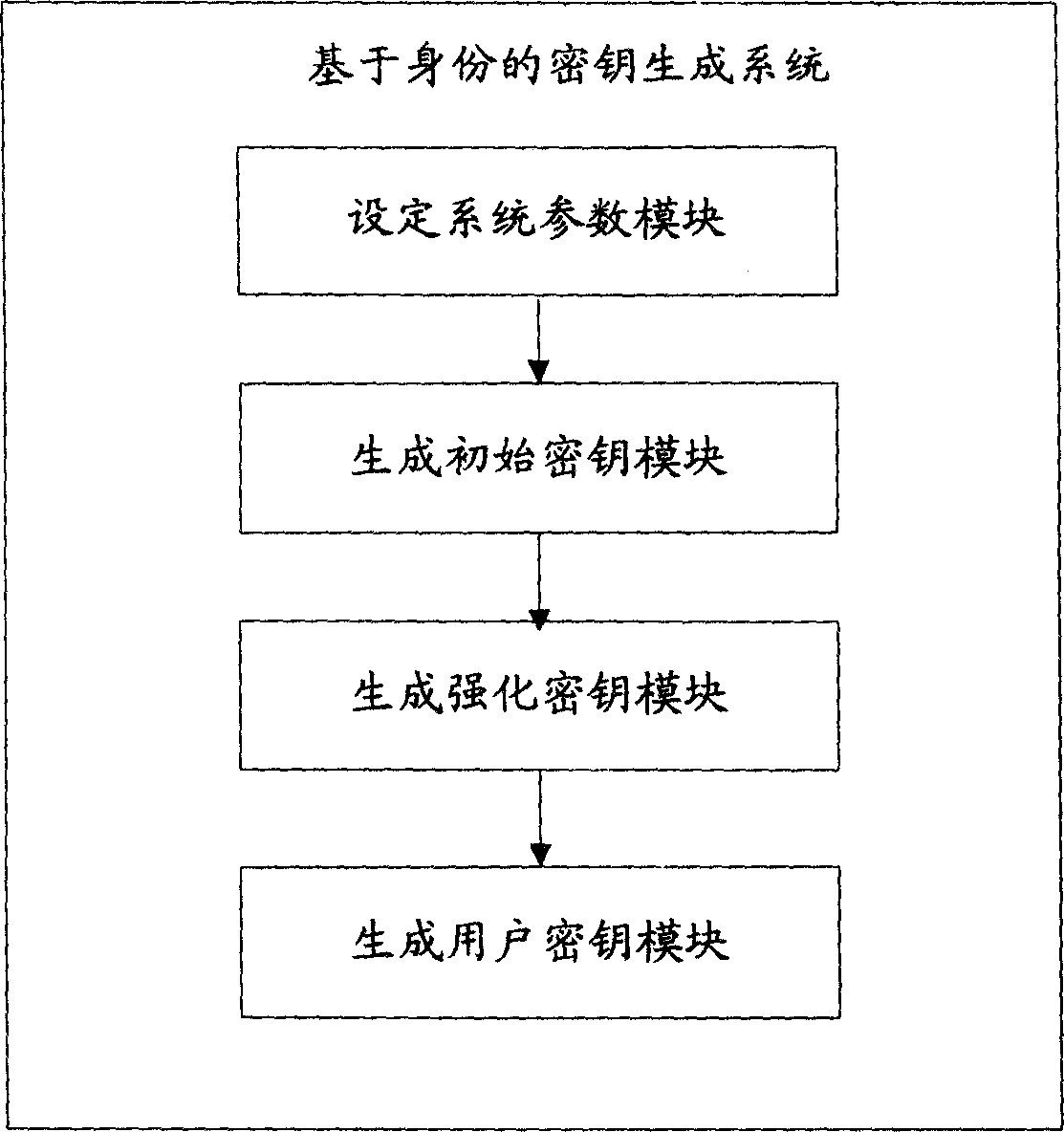
A key generation and key generator technology, applied in the direction of user identity/authority verification, etc., can solve the problems of key escrow and loss of identity authentication, and achieve the effect of preventing impersonation attacks, removing dependencies, and being easy to accept.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] The present invention will be further described below with reference to the drawings and embodiments, but it is not intended to limit the present invention.
[0043] The present invention integrates three technologies: blinding technology, multi-party authorization mechanism and password-based authentication mechanism. The function of blinding is to remove the dependence on the secure channel, and the function of multi-party authorization mechanism is to overcome the impact of a separate key generator on users. The escrow of the private key, based on the password authentication mechanism, is to prevent an attacker from imitating the user or a certain key generator.
[0044] The scheme of the present invention is specifically as follows:
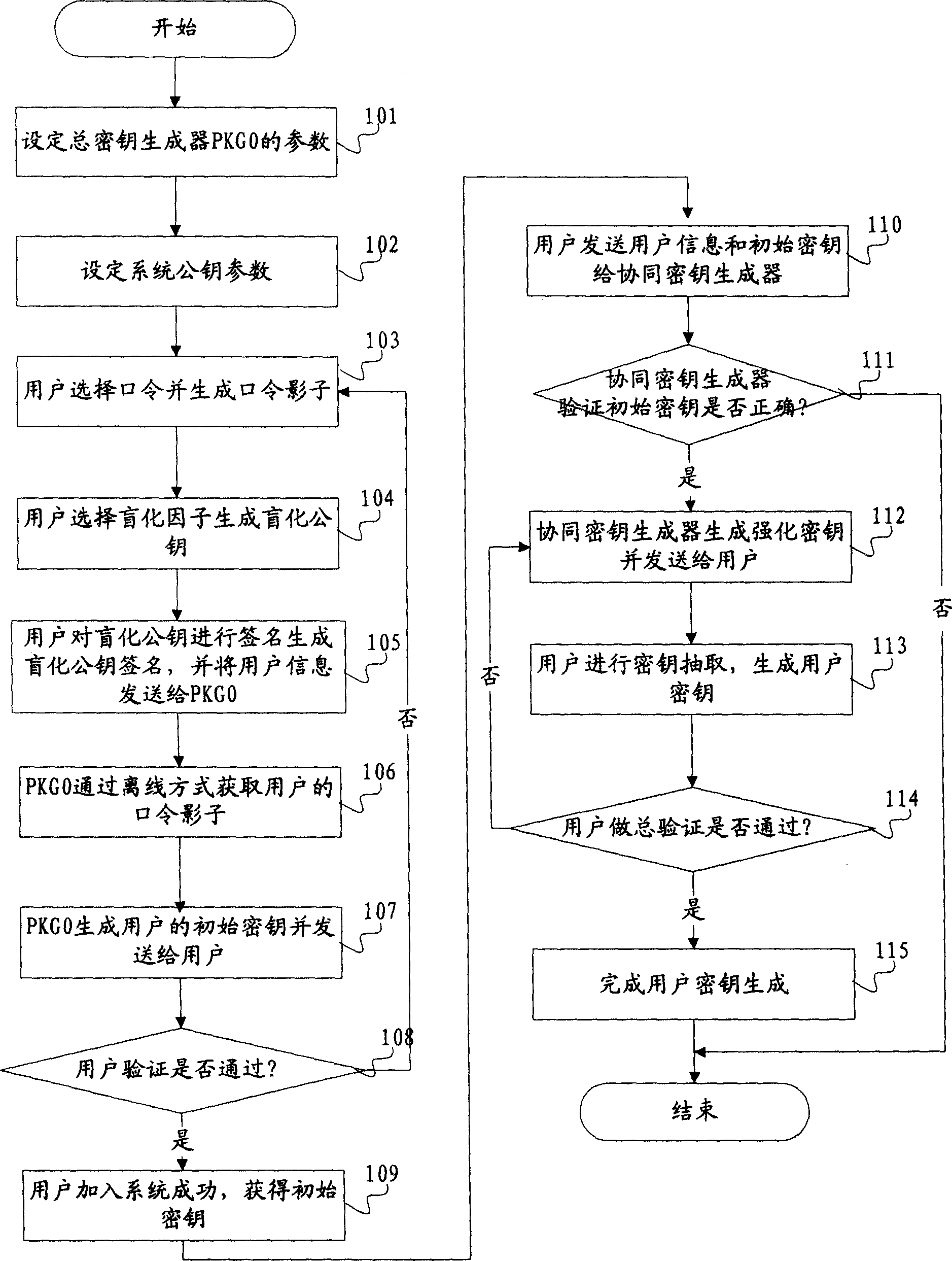
[0045] See figure 1 The present invention provides an identity-based key generation method, the method steps are as follows:
[0046] Step A: Set system parameters; the specific implementation steps are as follows:
[0047]Step 101: Set t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com