Malicious machine traffic identification method and system
A flow identification and flow technology, applied in transmission systems, digital transmission systems, neural learning methods, etc., can solve problems such as dependence, single identification means, and identification rules relying on expert experience, and achieve the effect of accurate positioning
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] In order to make the object, technical solution and advantages of the present invention clearer, the specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
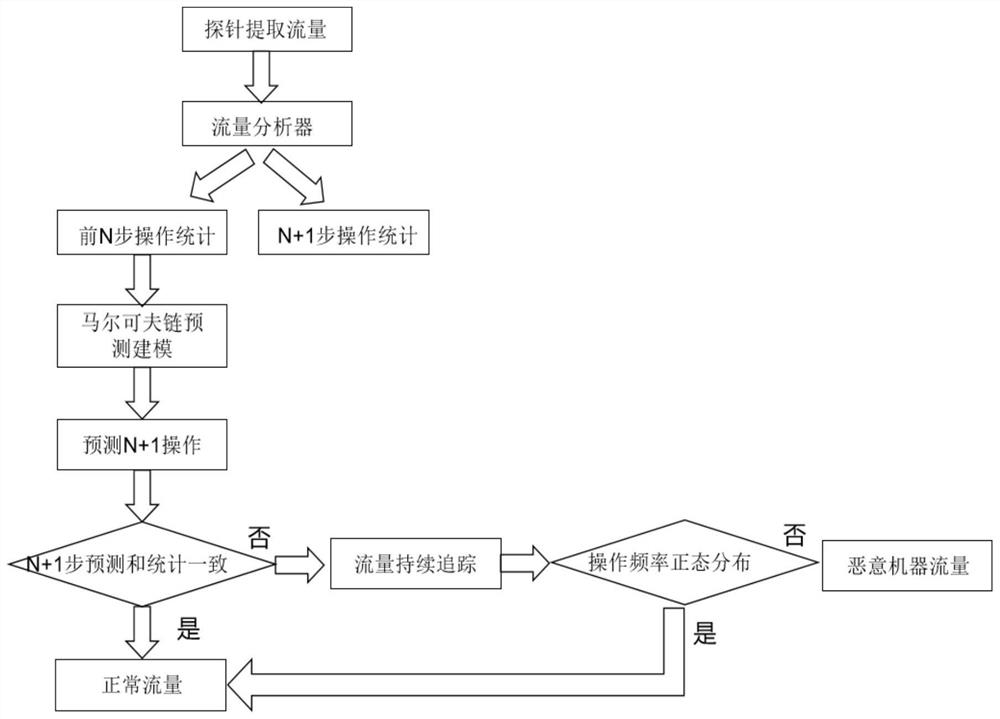
[0024] Such as figure 1 As shown, the present invention provides a kind of malicious machine traffic identification method, comprises the following steps:
[0025] Step 1. Collect a full amount of historical traffic data, decompose the traffic data, and form training samples;
[0026] In practical applications, network traffic data in the current network can be captured through Internet behavior management such as network probes, and the captured network traffic data can be input to the built-in traffic analyzer. The behavior analysis module can conduct preliminary analysis...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com