Intelligent network security monitoring system
A monitoring system and network security technology, applied in transmission systems, computer security devices, instruments, etc., can solve the problems of poor system security, slow information monitoring and review rate, and small proportion, so as to improve work efficiency and speed up monitoring. The effect of the audit
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
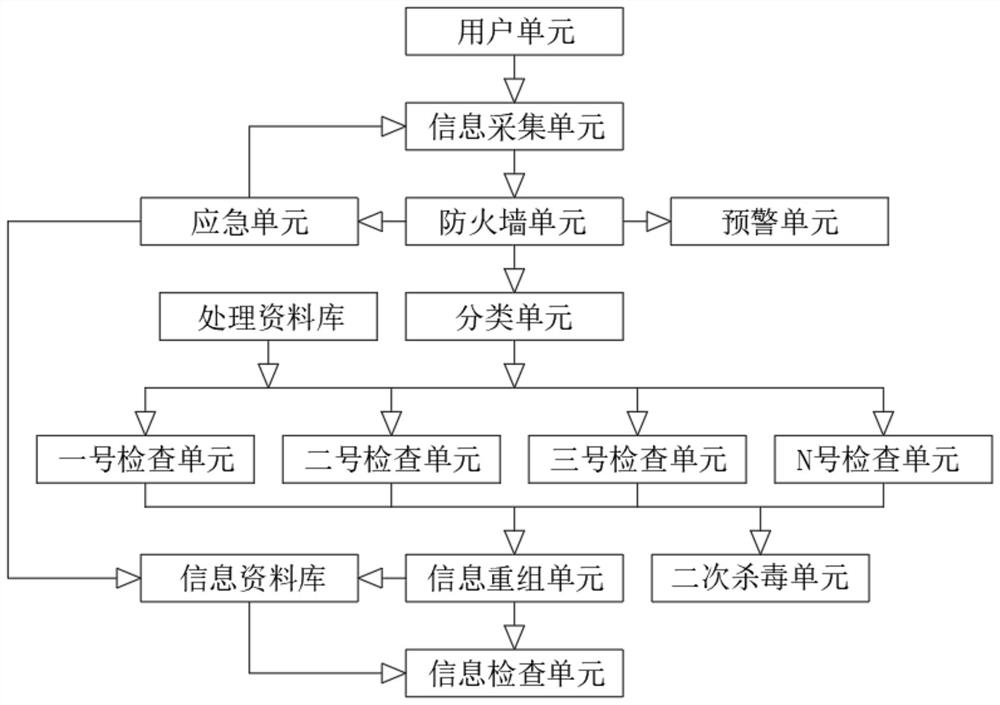
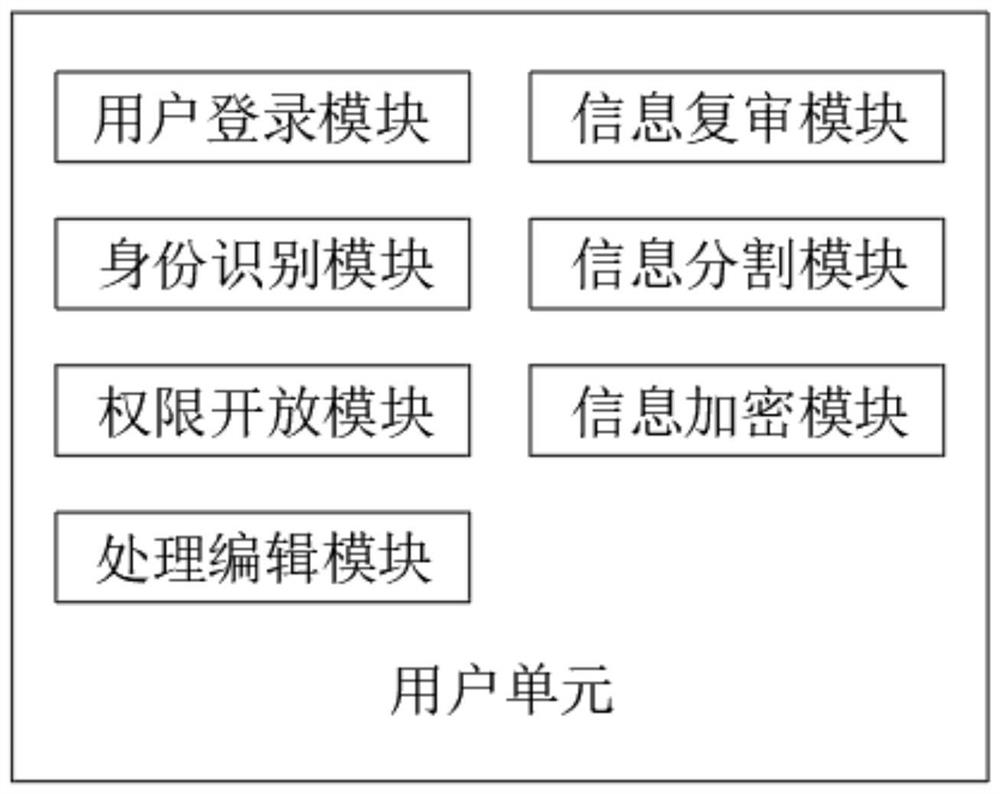
[0031] Such as Figure 1-3 As shown, an intelligent network security monitoring system includes a user unit, an information collection unit, a firewall unit, an emergency unit, an early warning unit, a classification unit, a processing database, a No. 1 inspection unit, a No. 2 inspection unit, and a No. 3 inspection unit , No. N inspection unit, information reorganization unit, information database, secondary antivirus unit and information inspection unit;
[0032] The classification unit classifies according to the proportion of various types of information in each piece of information, including four types of picture information, text information, sound information and video information;
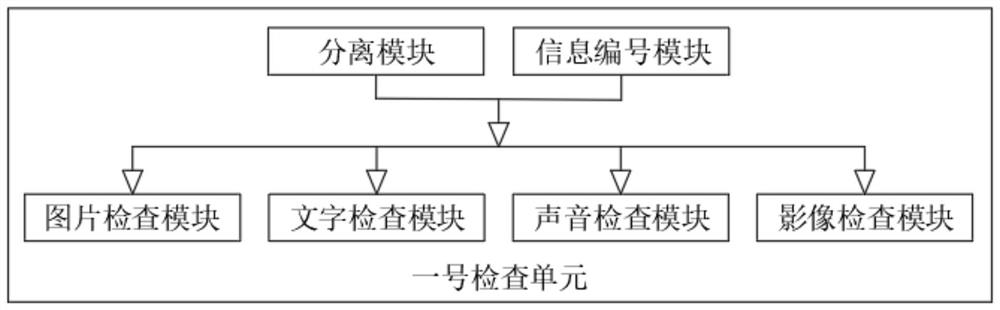
[0033] The No. 1 inspection unit includes a separation module, an information numbering module, a picture inspection module, a text inspection module, a sound inspection module and an image inspection module, and the modules in the No. 2 inspection unit, No. 3 inspection unit, and No. N i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com